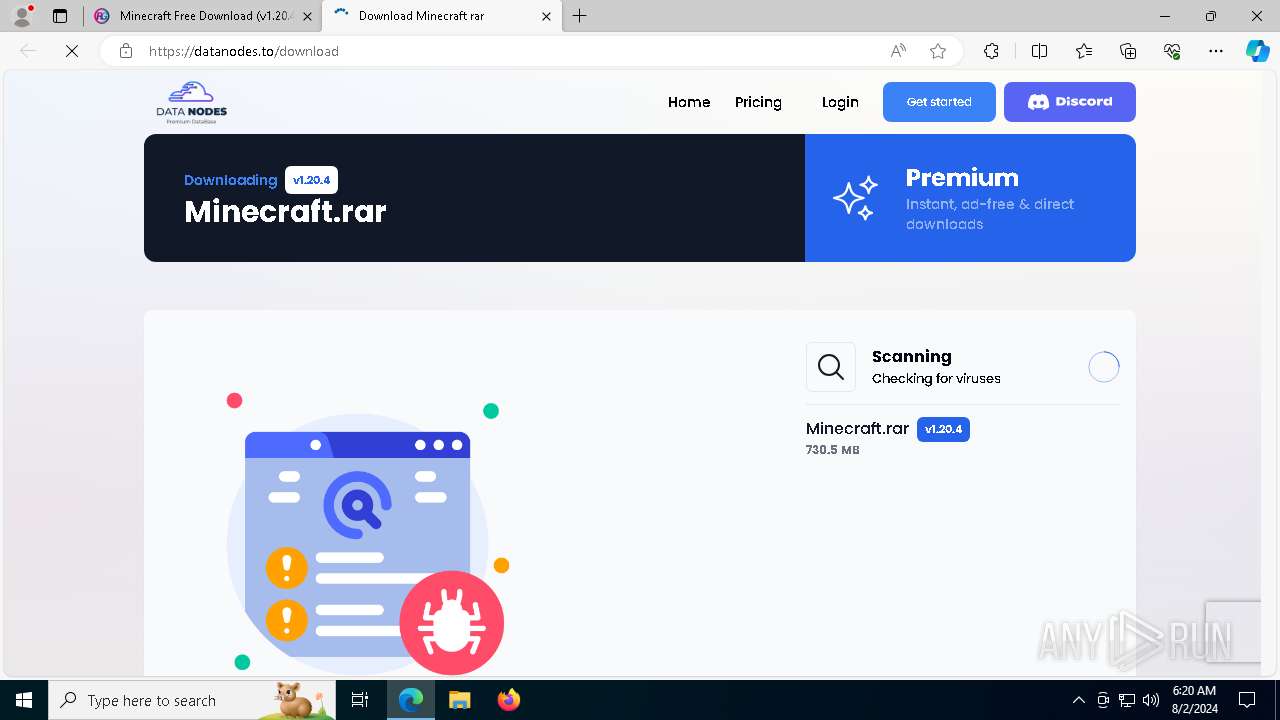
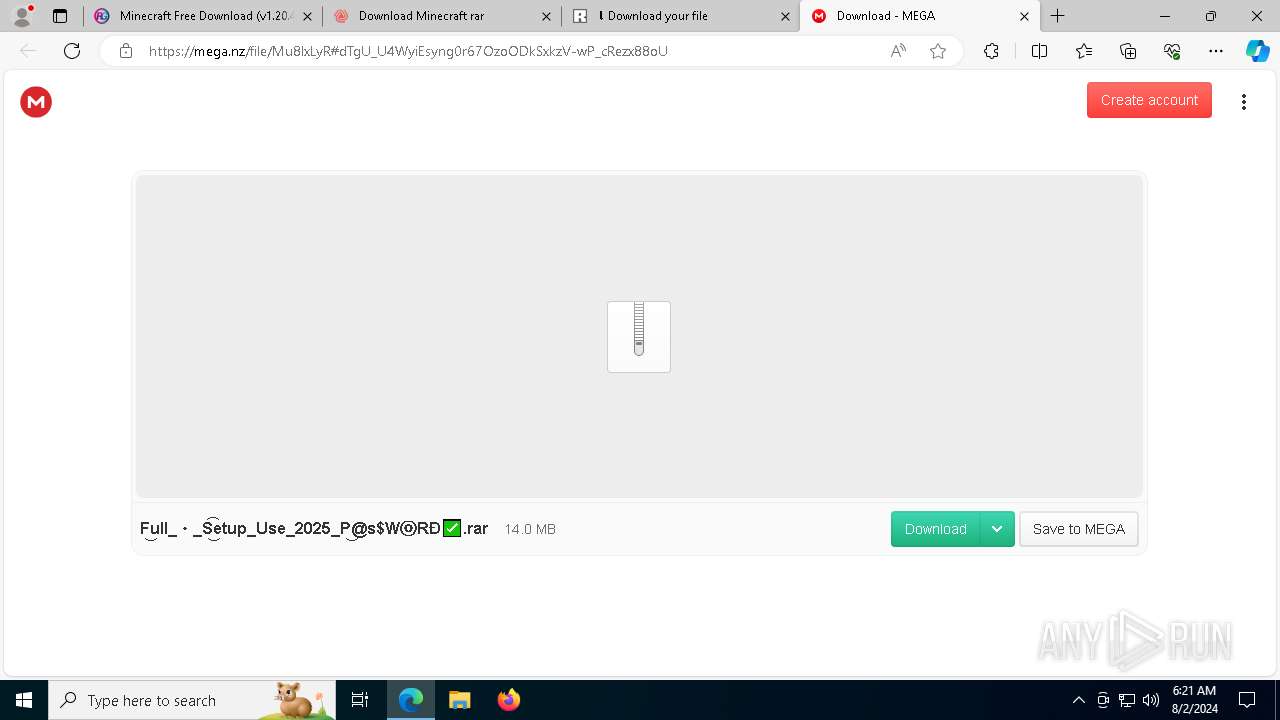
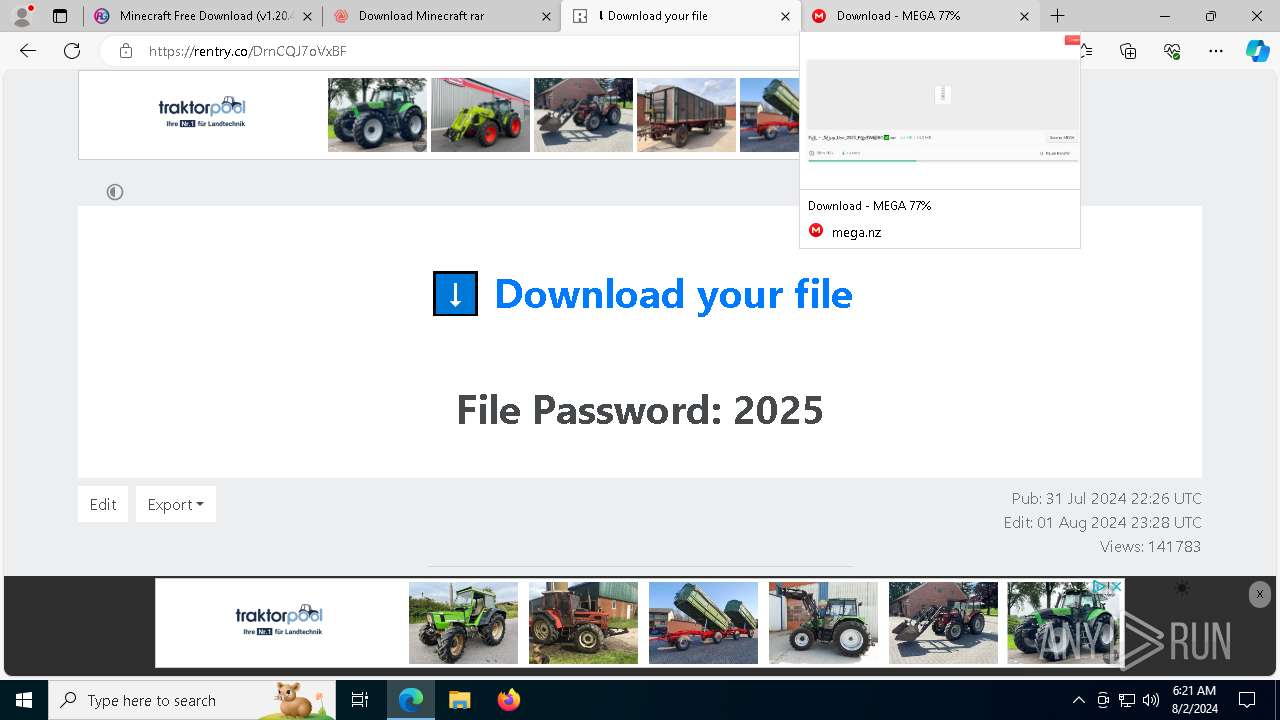
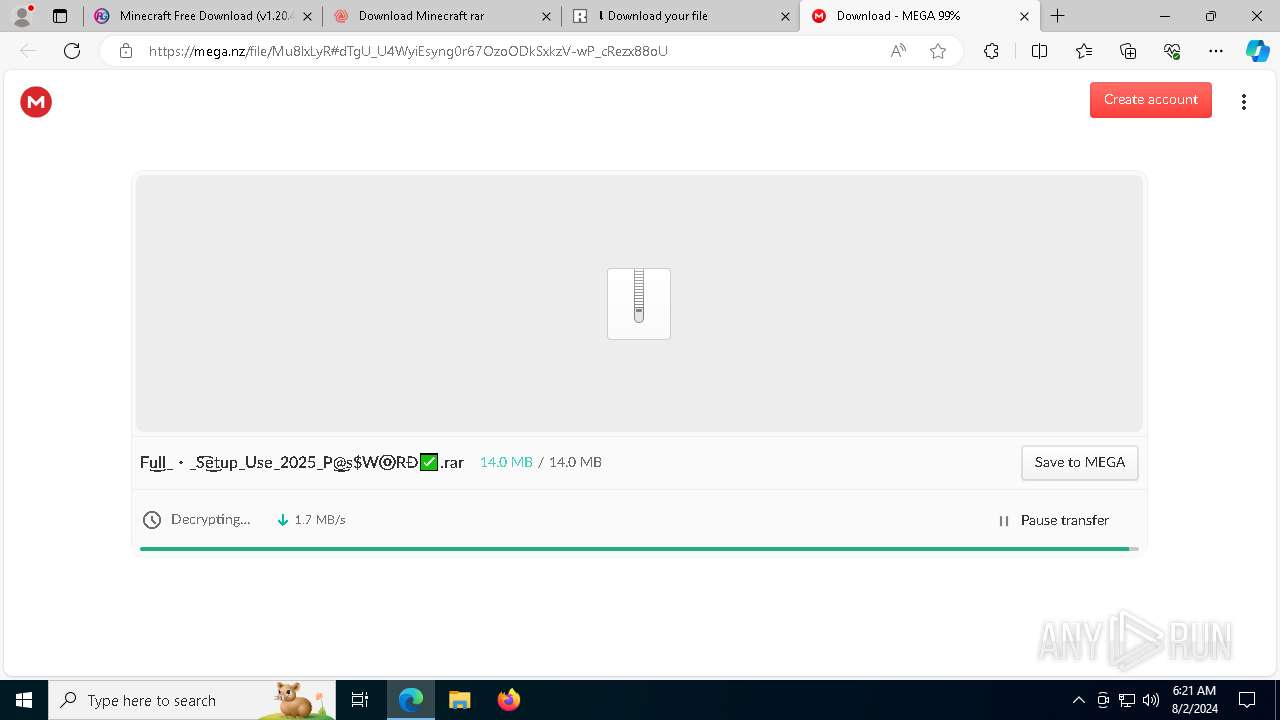
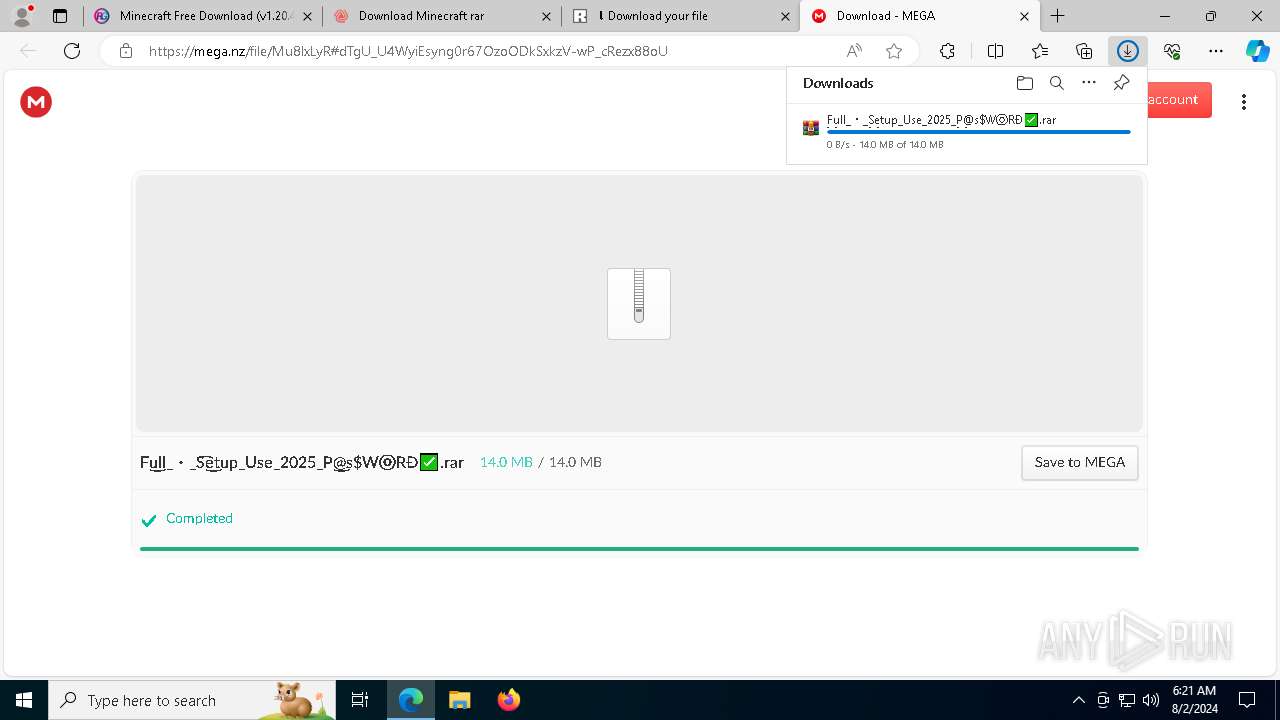
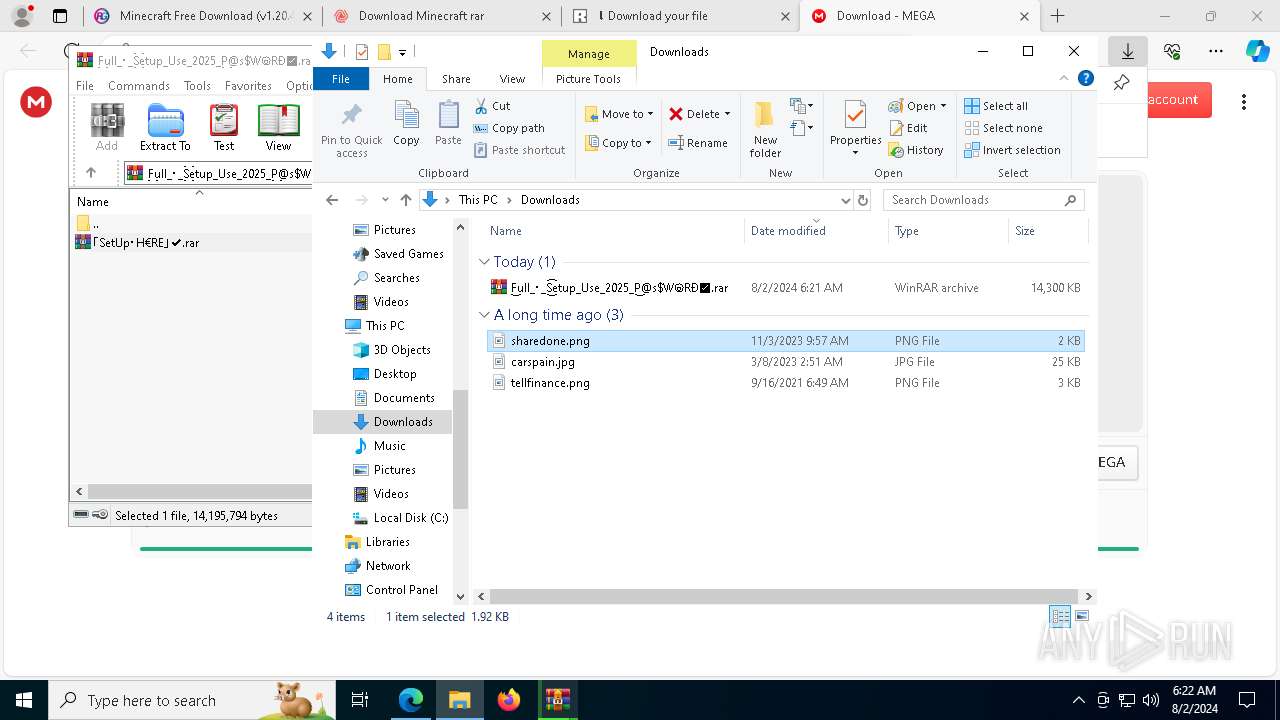
| URL: | repack-games.com |
| Full analysis: | https://app.any.run/tasks/eb6d1090-0911-409e-9f78-318c97d4cf78 |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | August 02, 2024, 06:20:18 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
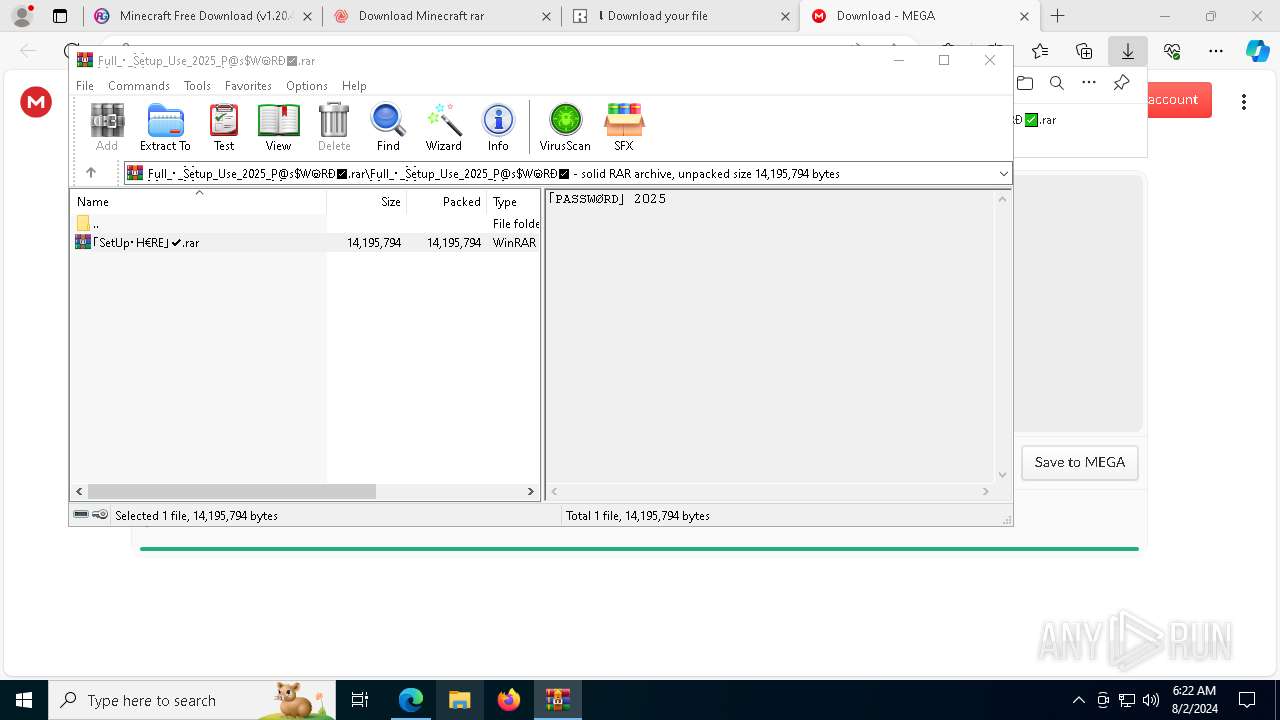
| MD5: | C26D1D92922AAE977154CE9263EB15B8 |
| SHA1: | C119AA1E5301ABAE1FAE27EAC37C28398FA2500C |
| SHA256: | 24CAD237155B90F8E2DA10A4A4952F9887B6ABA5AEF8CB07941CA5518C251998 |
| SSDEEP: | 3:sHIK:Y |
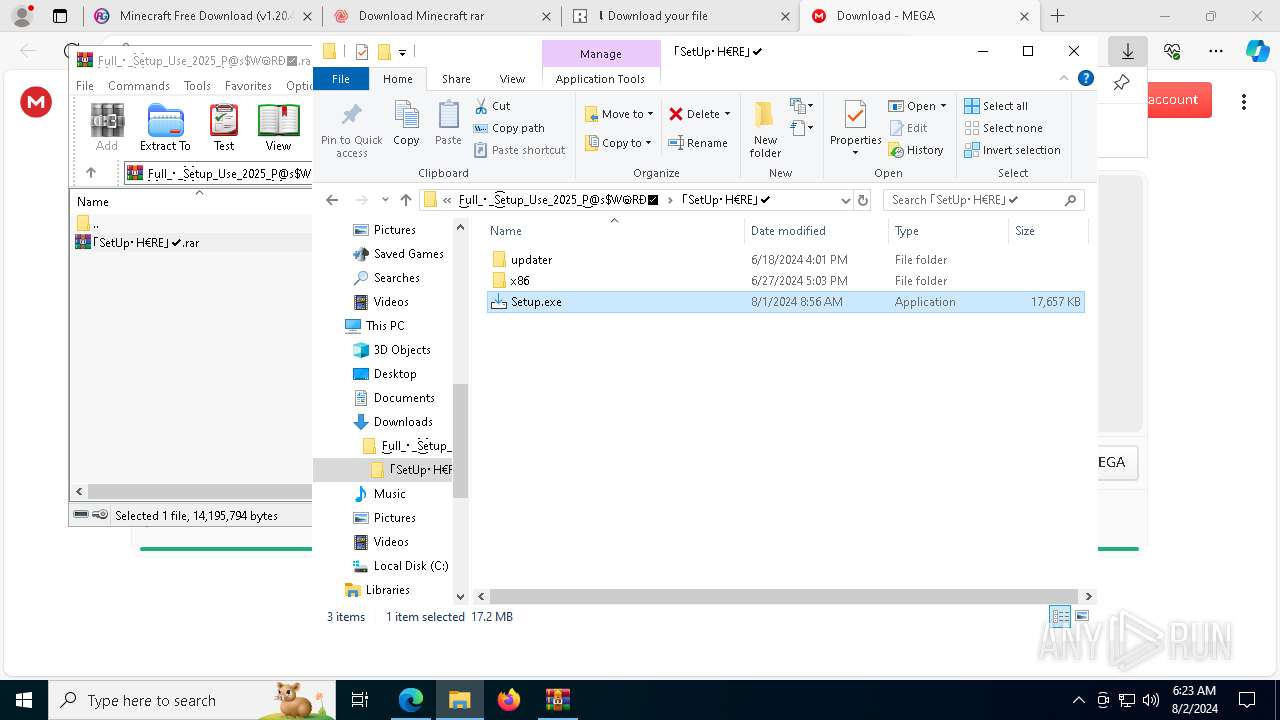
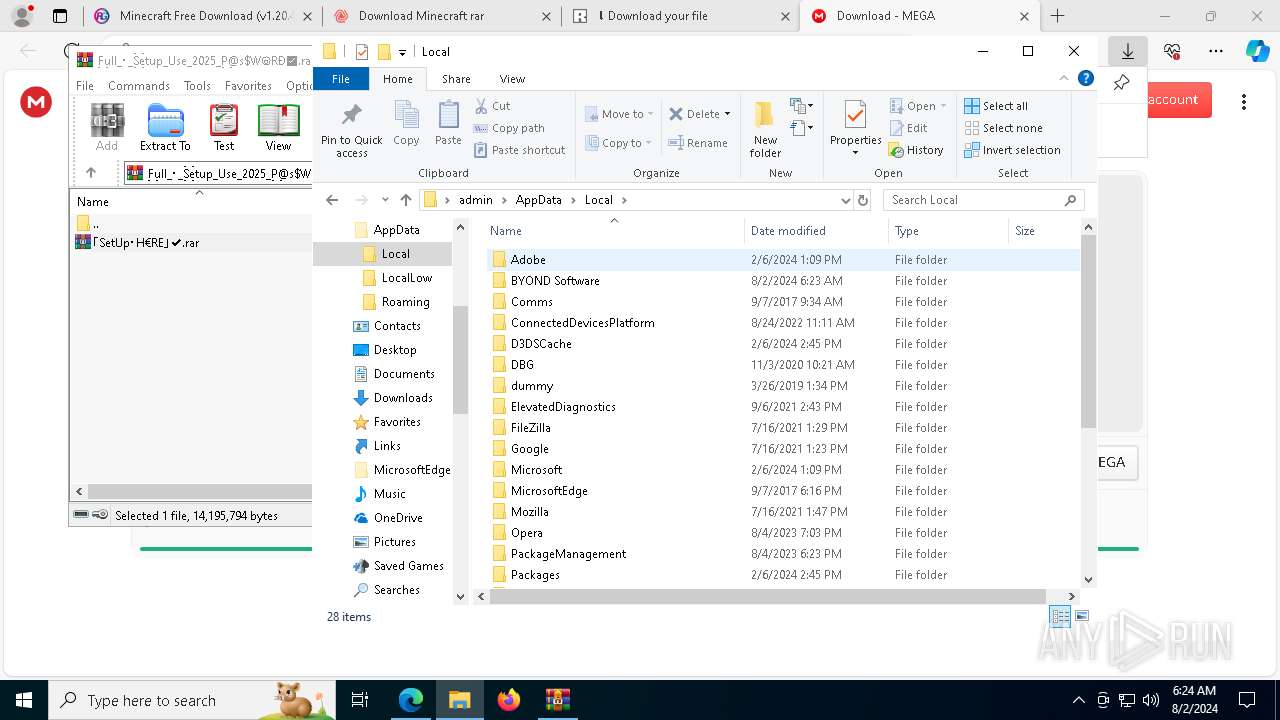
MALICIOUS
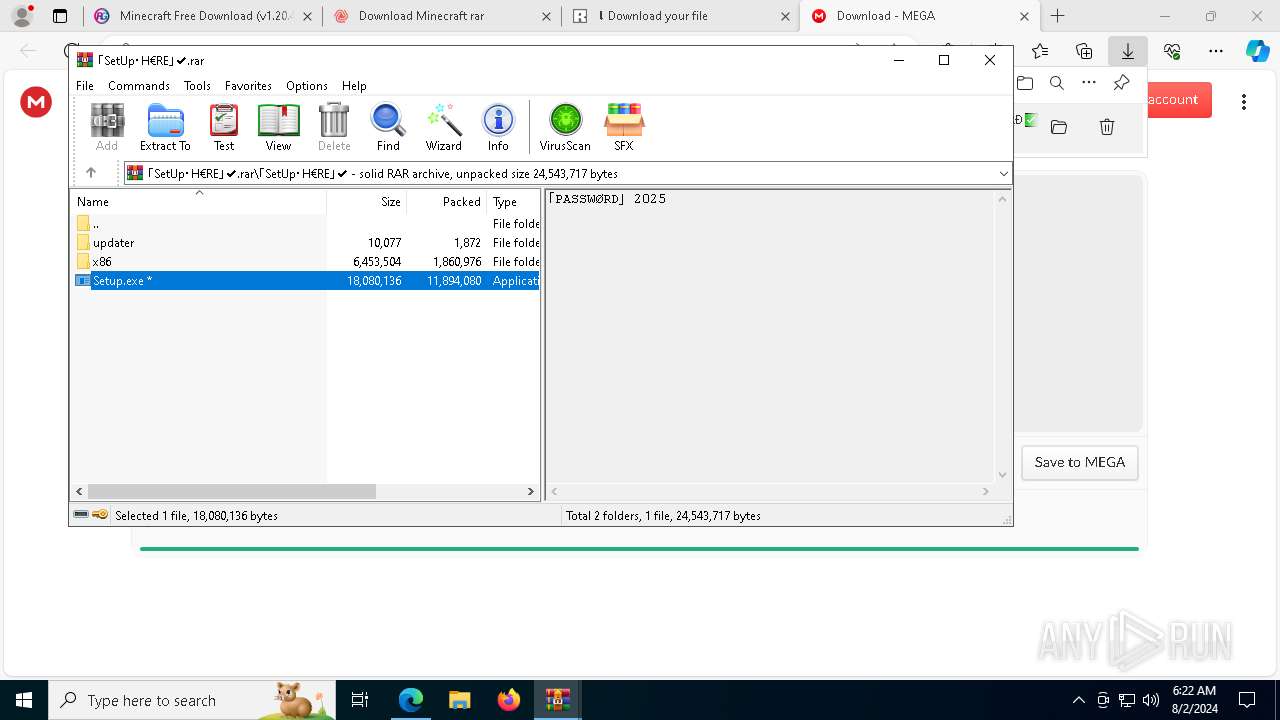
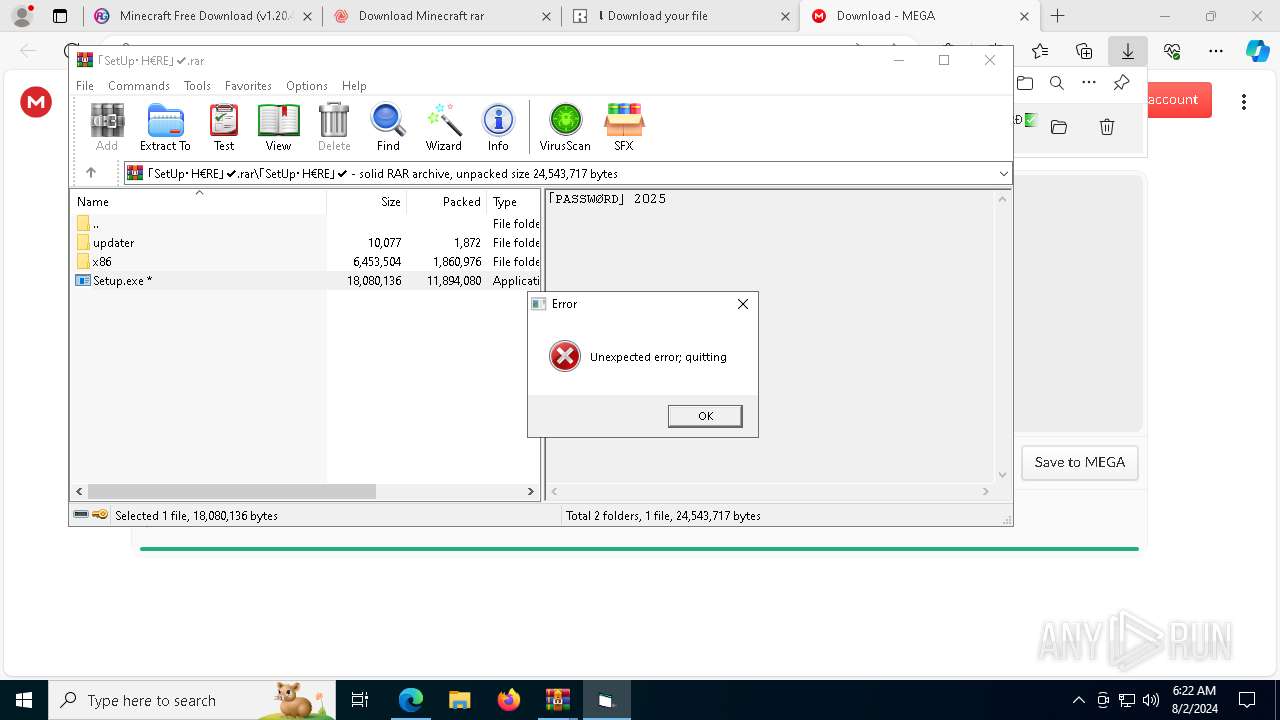
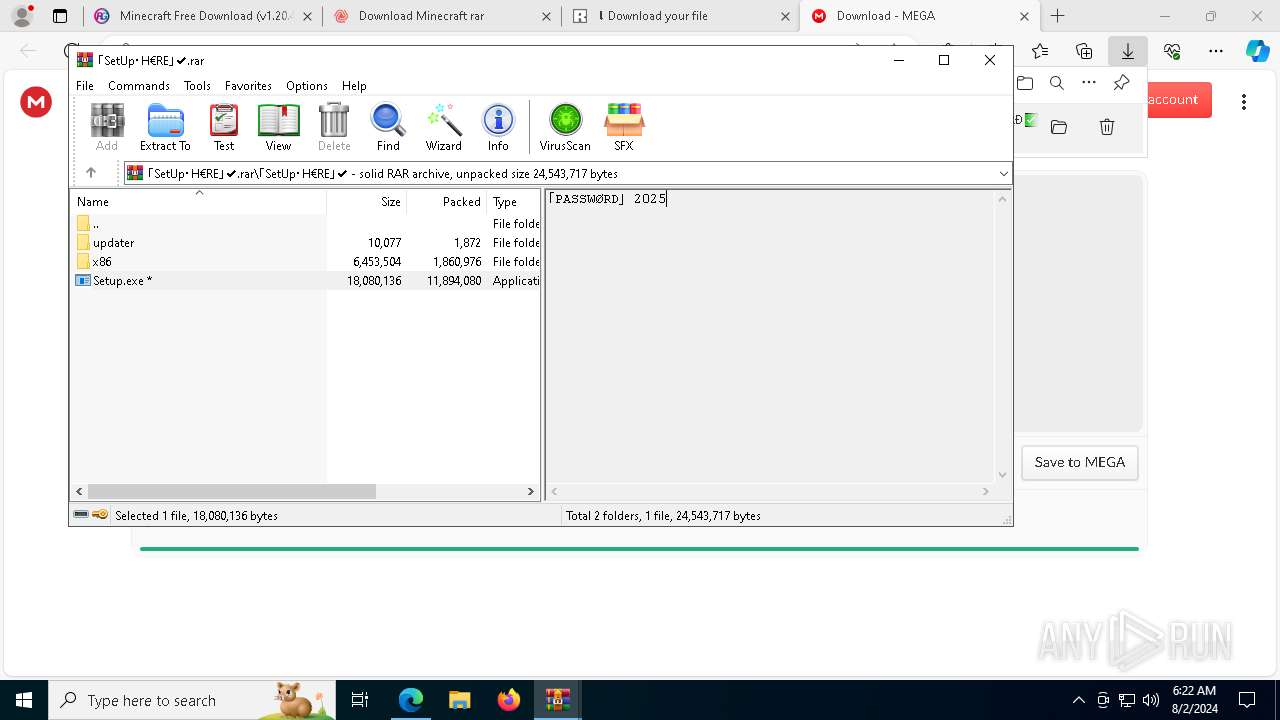
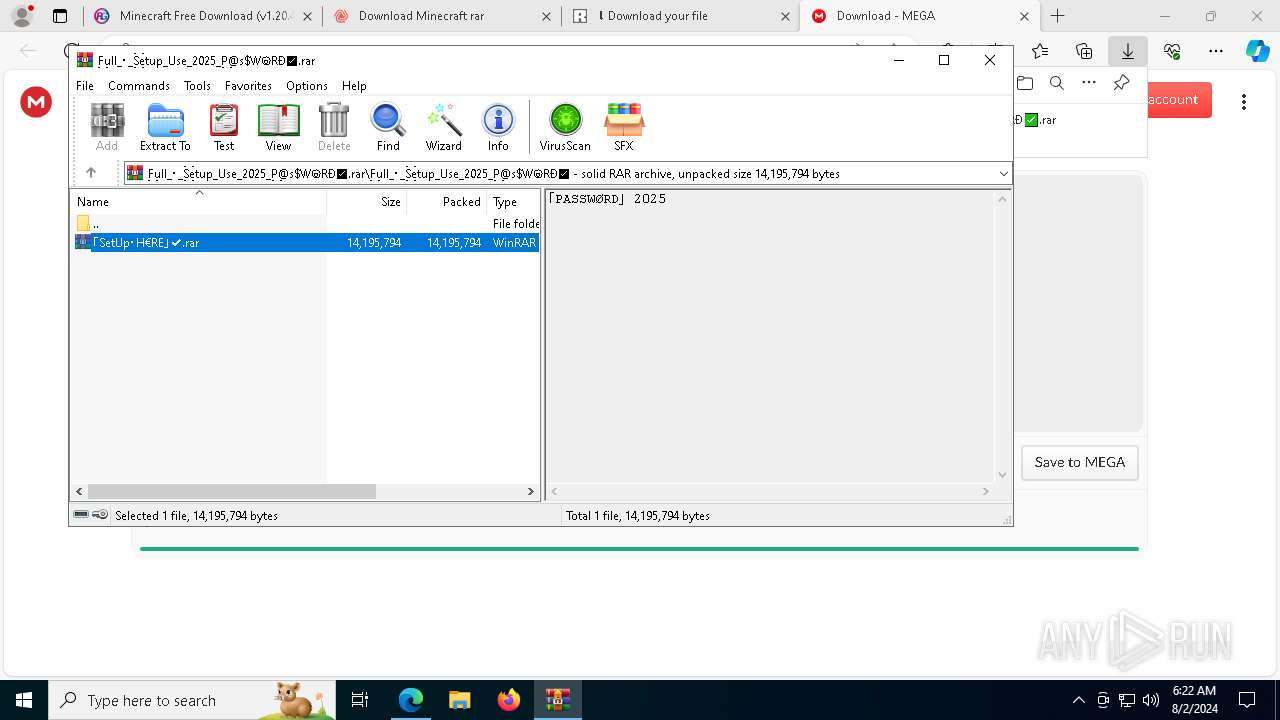
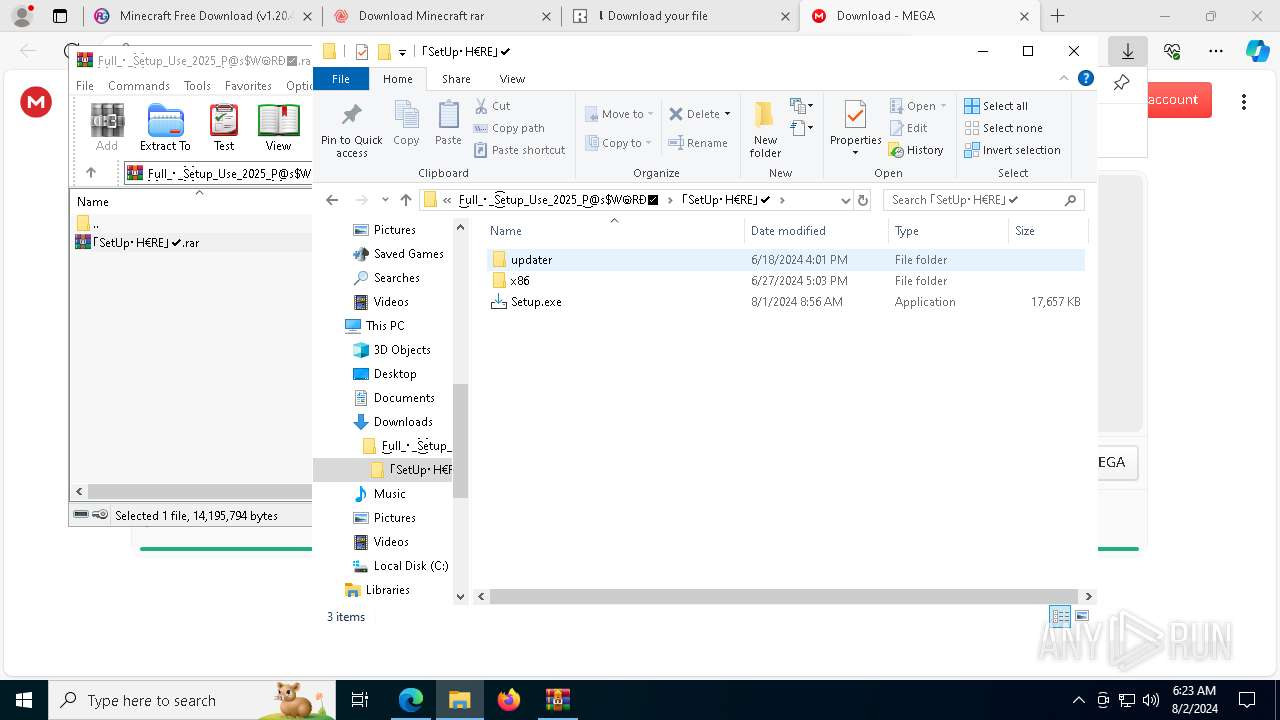
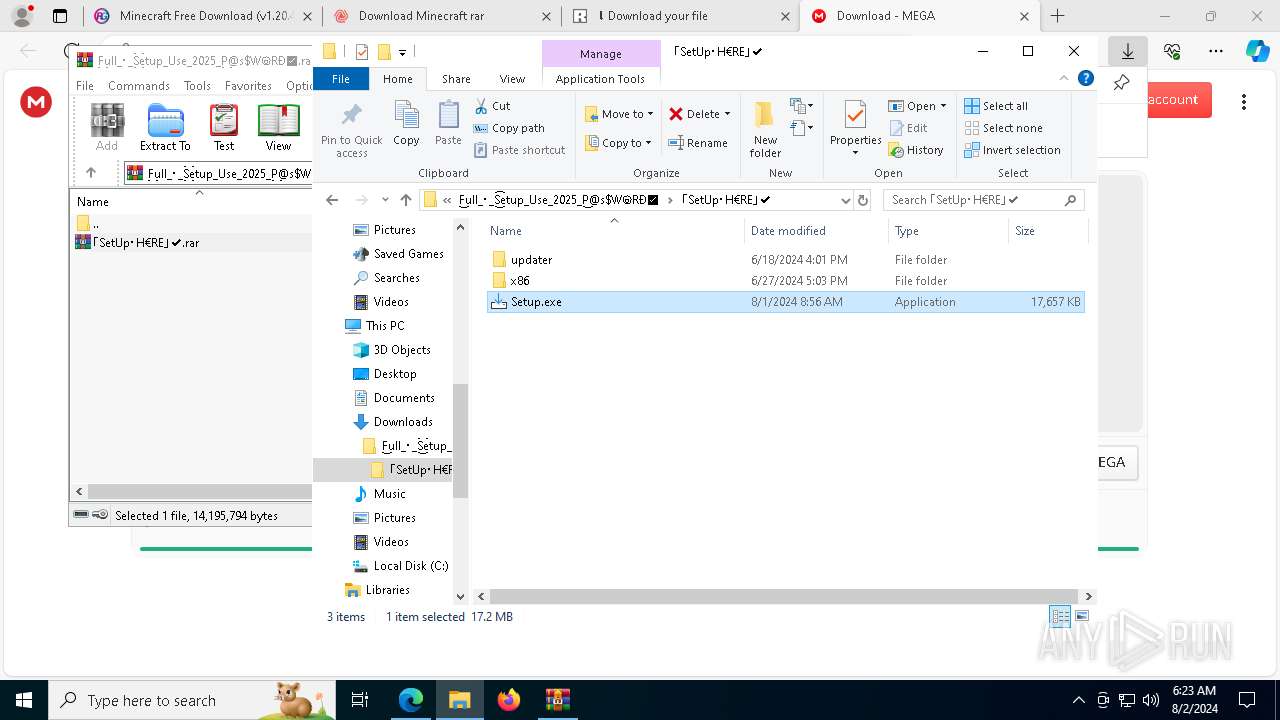
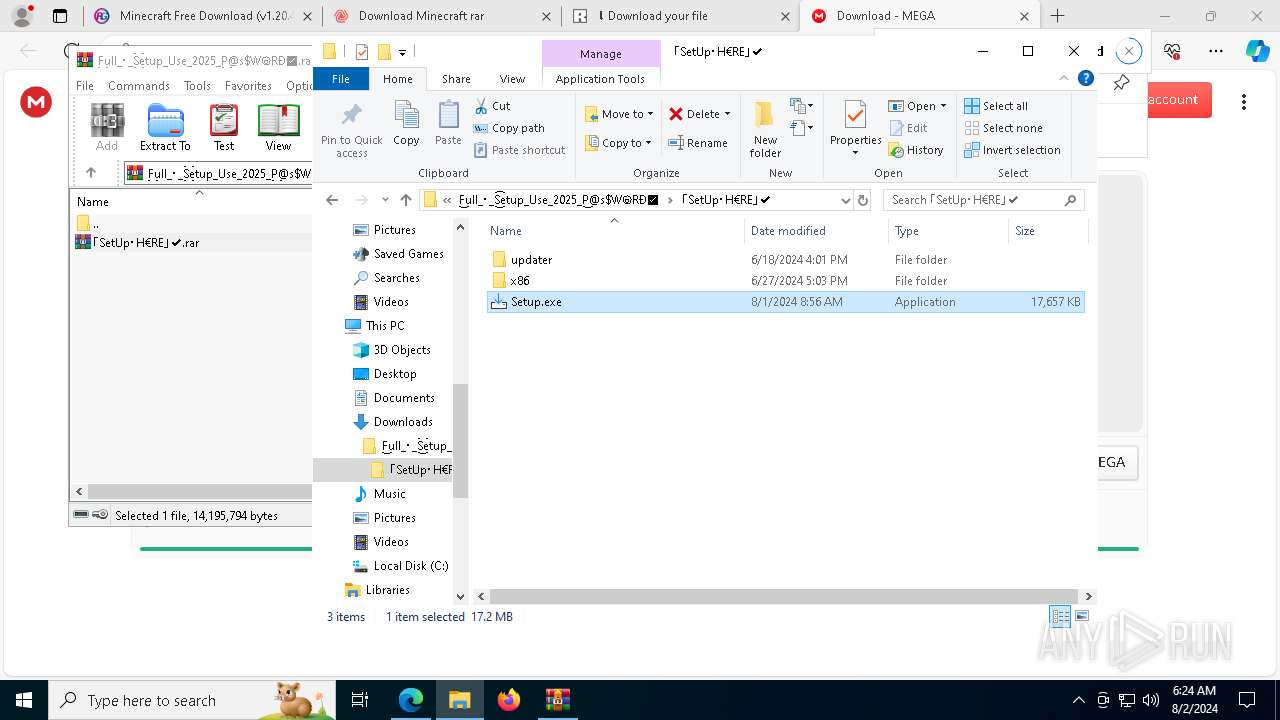
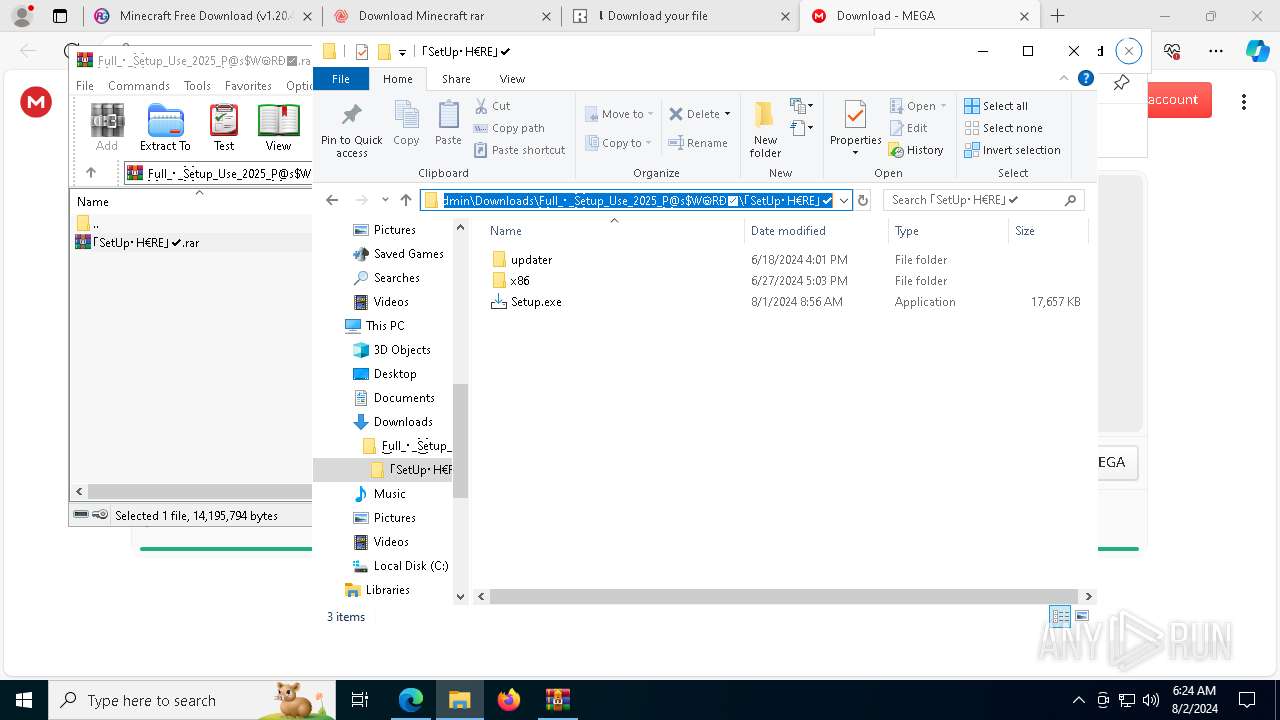
Drops the executable file immediately after the start
- Setup.exe (PID: 3876)
- Setup.tmp (PID: 3660)
- Setup.exe (PID: 7428)
- Setup.tmp (PID: 7256)
- LogiAiPromptBuilder.exe (PID: 2096)
- more.com (PID: 10196)
- BuntEatable.pif (PID: 9044)
- 6UEZ70WBJOZRUV1LTO4RJ3OSDCJM67.exe (PID: 9484)
- Setup.tmp (PID: 7992)
- Setup.exe (PID: 7696)
- Setup.exe (PID: 10124)
- Setup.tmp (PID: 9916)
- Setup.exe (PID: 9948)
- Setup.tmp (PID: 5328)
- Setup.exe (PID: 2336)
- Setup.exe (PID: 6272)
- Setup.tmp (PID: 7896)
- Setup.tmp (PID: 4692)
- Setup.exe (PID: 6968)
- Setup.tmp (PID: 2524)
- BuntEatable.pif (PID: 8788)
Antivirus name has been found in the command line (generic signature)
- cmd.exe (PID: 3864)
- tasklist.exe (PID: 3008)
- find.exe (PID: 4208)
- cmd.exe (PID: 5916)
- tasklist.exe (PID: 10180)
- find.exe (PID: 4424)
- tasklist.exe (PID: 6192)
- tasklist.exe (PID: 9448)
- find.exe (PID: 7696)
- cmd.exe (PID: 7176)
- find.exe (PID: 7260)
- cmd.exe (PID: 2536)
- find.exe (PID: 9524)
- tasklist.exe (PID: 3008)
- cmd.exe (PID: 7204)
- tasklist.exe (PID: 9024)
- find.exe (PID: 9040)
- cmd.exe (PID: 3660)
- tasklist.exe (PID: 4020)
- cmd.exe (PID: 3548)
- find.exe (PID: 8128)
- cmd.exe (PID: 5632)
- tasklist.exe (PID: 2900)
- find.exe (PID: 8056)
- cmd.exe (PID: 5284)
- find.exe (PID: 7656)
- find.exe (PID: 1020)
- tasklist.exe (PID: 9892)
- tasklist.exe (PID: 6048)
- cmd.exe (PID: 6948)
- cmd.exe (PID: 7024)
- tasklist.exe (PID: 1292)
- cmd.exe (PID: 4924)
- cmd.exe (PID: 6228)
- find.exe (PID: 10056)
- tasklist.exe (PID: 8184)
- find.exe (PID: 2876)
- tasklist.exe (PID: 9812)
- cmd.exe (PID: 9656)
- cmd.exe (PID: 3116)
- tasklist.exe (PID: 9896)
- find.exe (PID: 9100)
- tasklist.exe (PID: 1860)
- find.exe (PID: 10128)
- find.exe (PID: 9184)
LUMMA has been detected (YARA)
- BuntEatable.pif (PID: 9044)
- BuntEatable.pif (PID: 8788)
LUMMA has been detected (SURICATA)
- BuntEatable.pif (PID: 9044)
- BuntEatable.pif (PID: 8788)
Stealers network behavior
- BuntEatable.pif (PID: 9044)
- BuntEatable.pif (PID: 8788)
Actions looks like stealing of personal data
- BuntEatable.pif (PID: 9044)
- BuntEatable.pif (PID: 8788)
Changes powershell execution policy (Bypass)
- BuntEatable.pif (PID: 9044)
- BuntEatable.pif (PID: 8788)
Bypass execution policy to execute commands
- powershell.exe (PID: 9772)
- powershell.exe (PID: 6752)
Probably downloads file via BitsAdmin (POWERSHELL)
- powershell.exe (PID: 9772)
- powershell.exe (PID: 6752)
Modifies registry (POWERSHELL)
- powershell.exe (PID: 6752)
AMADEY has been detected (SURICATA)
- explorer.exe (PID: 9112)
Connects to the CnC server
- explorer.exe (PID: 9112)
SUSPICIOUS
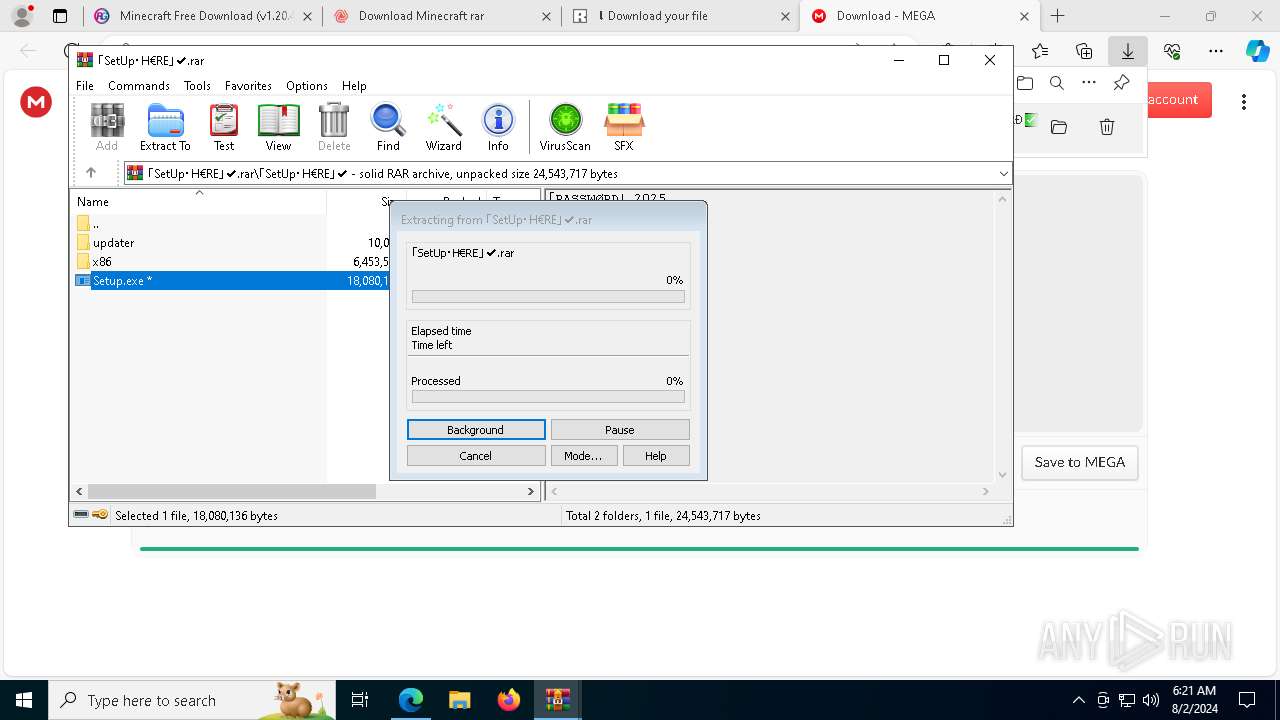
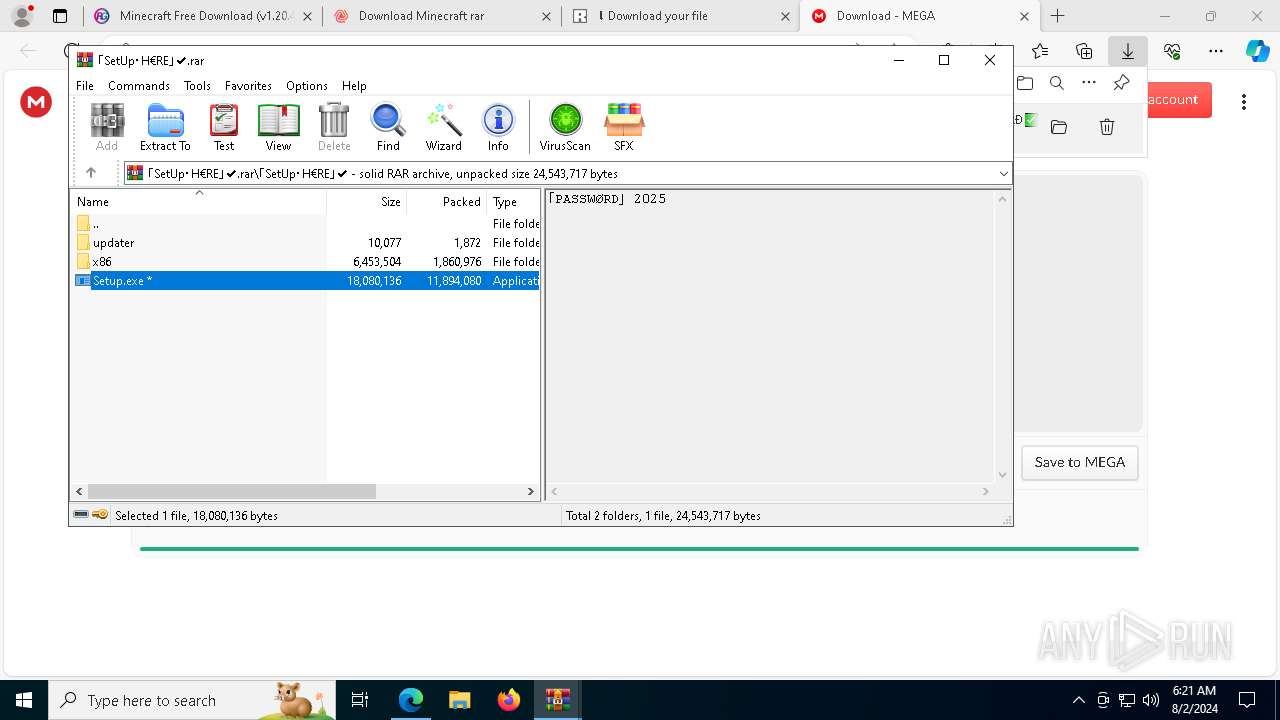
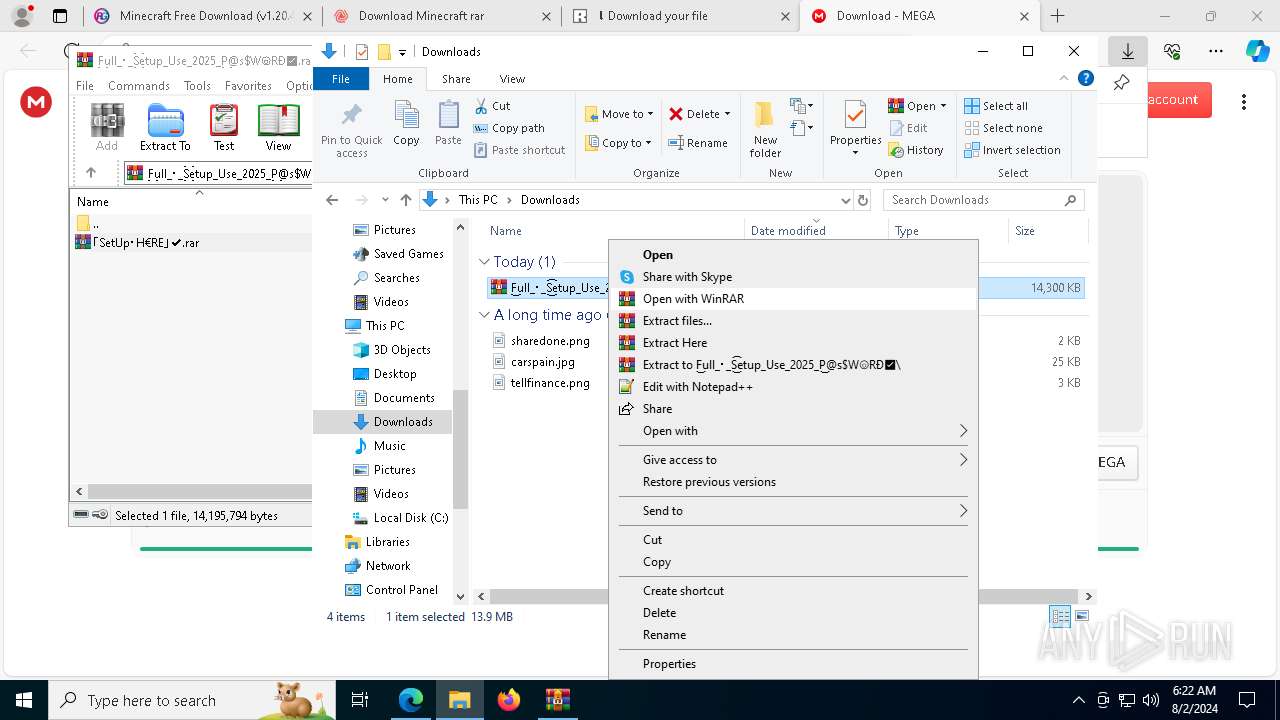
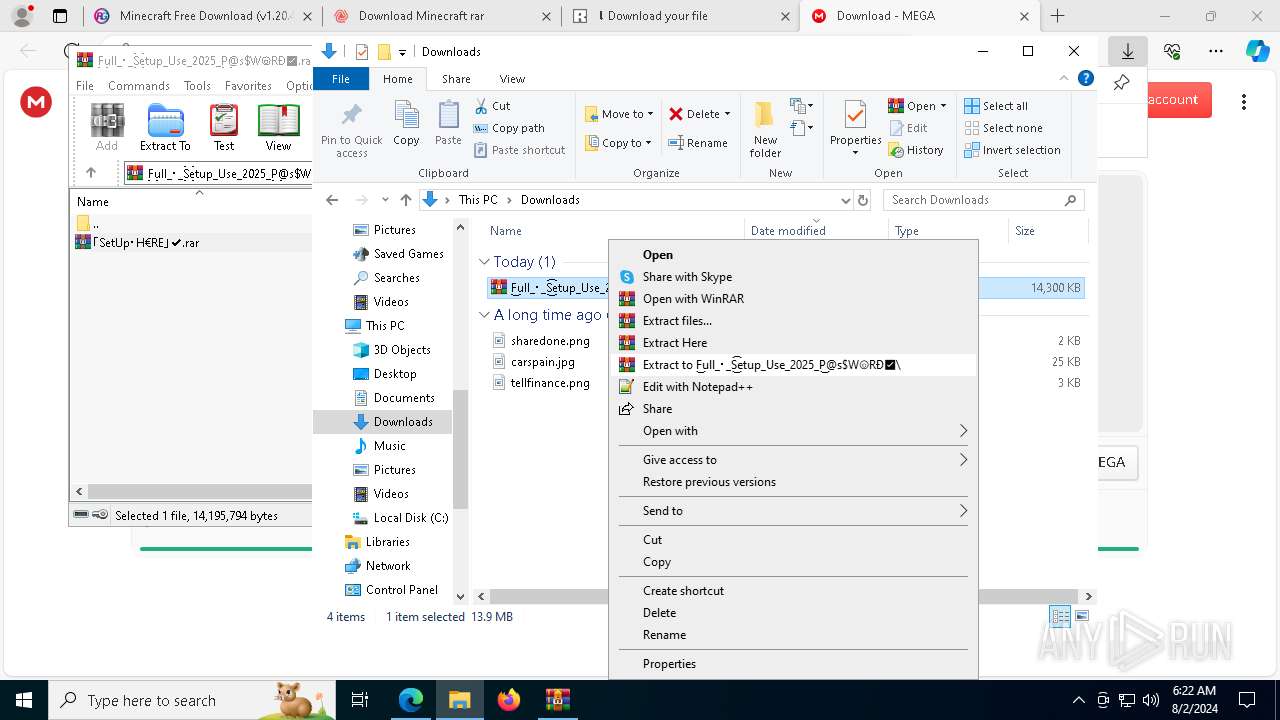
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 9972)
- WinRAR.exe (PID: 10124)
- Setup.tmp (PID: 3660)
- Setup.tmp (PID: 7256)
- Setup.tmp (PID: 7992)
- Setup.tmp (PID: 5328)
- Setup.tmp (PID: 4692)
- Setup.tmp (PID: 9916)
- Setup.tmp (PID: 7896)
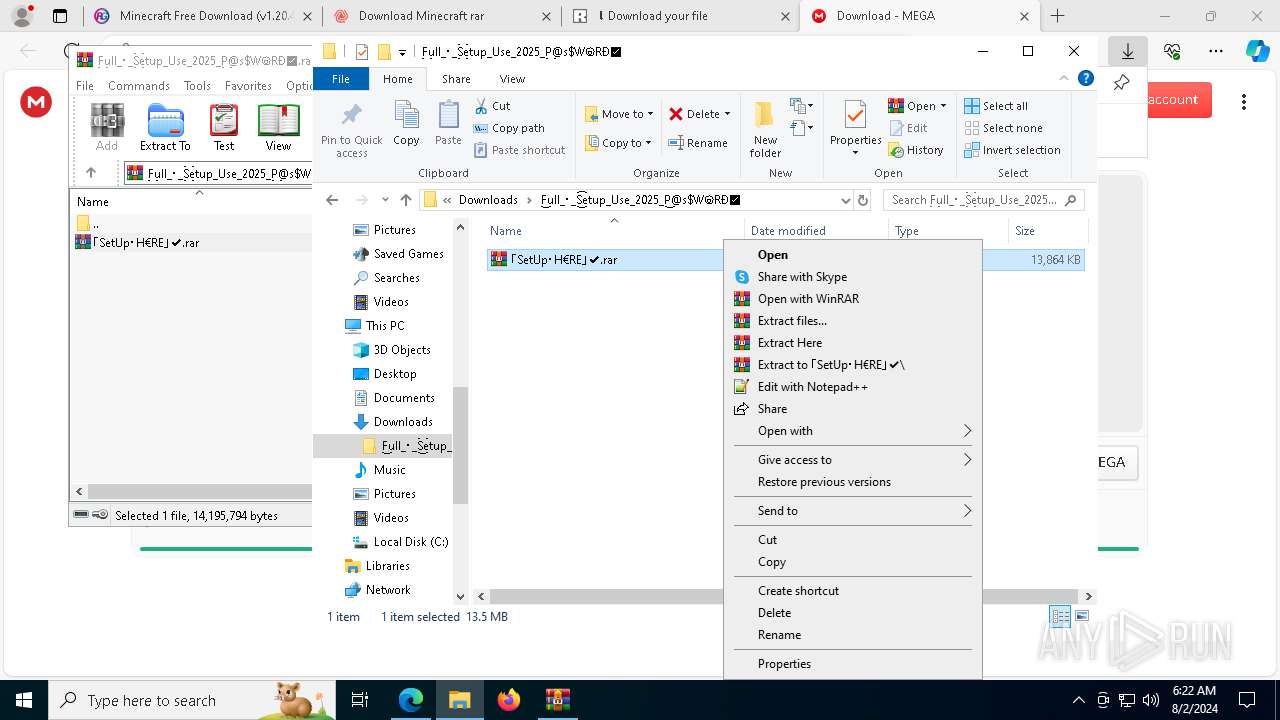
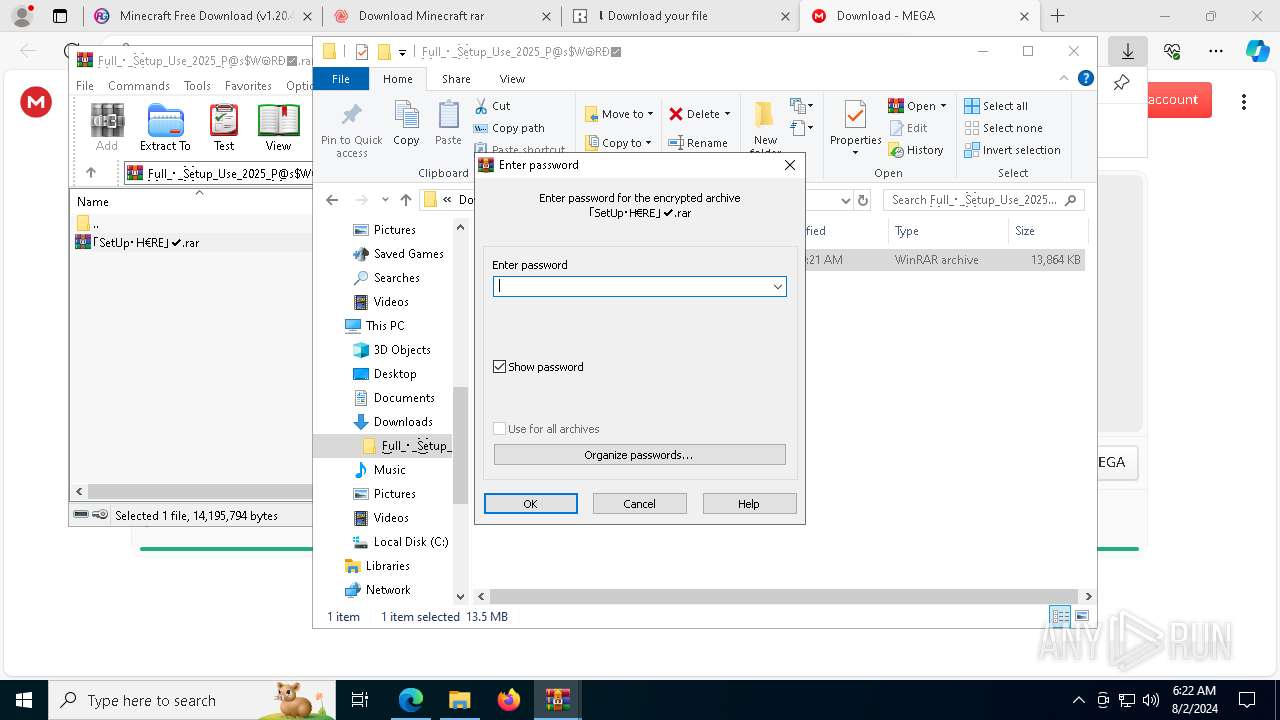
Application launched itself
- WinRAR.exe (PID: 9972)
Process drops legitimate windows executable
- WinRAR.exe (PID: 10124)
- Setup.tmp (PID: 7256)
- LogiAiPromptBuilder.exe (PID: 2096)
- WinRAR.exe (PID: 9000)
- Setup.tmp (PID: 9916)
- Setup.tmp (PID: 7896)
- Setup.tmp (PID: 2524)
Executable content was dropped or overwritten
- Setup.exe (PID: 3876)
- Setup.tmp (PID: 3660)
- Setup.exe (PID: 7428)
- Setup.tmp (PID: 7256)
- more.com (PID: 10196)
- LogiAiPromptBuilder.exe (PID: 2096)
- BuntEatable.pif (PID: 9044)
- Setup.exe (PID: 10124)
- 6UEZ70WBJOZRUV1LTO4RJ3OSDCJM67.exe (PID: 9484)
- Setup.tmp (PID: 7992)
- Setup.exe (PID: 7696)
- Setup.tmp (PID: 9916)
- Setup.exe (PID: 9948)
- Setup.exe (PID: 2336)
- Setup.tmp (PID: 5328)
- Setup.exe (PID: 6272)
- Setup.tmp (PID: 7896)
- Setup.tmp (PID: 4692)
- Setup.exe (PID: 6968)
- Setup.tmp (PID: 2524)
- BuntEatable.pif (PID: 8788)
Reads the Windows owner or organization settings
- Setup.tmp (PID: 3660)
- Setup.tmp (PID: 7256)
- Setup.tmp (PID: 7992)
- Setup.tmp (PID: 5328)
- Setup.tmp (PID: 9916)
- Setup.tmp (PID: 7896)
- Setup.tmp (PID: 4692)
- Setup.tmp (PID: 2524)
Reads the date of Windows installation
- Setup.tmp (PID: 3660)
- Setup.tmp (PID: 7256)
- Setup.tmp (PID: 7992)
- Setup.tmp (PID: 5328)
- Setup.tmp (PID: 4692)
- Setup.tmp (PID: 9916)
- Setup.tmp (PID: 7896)
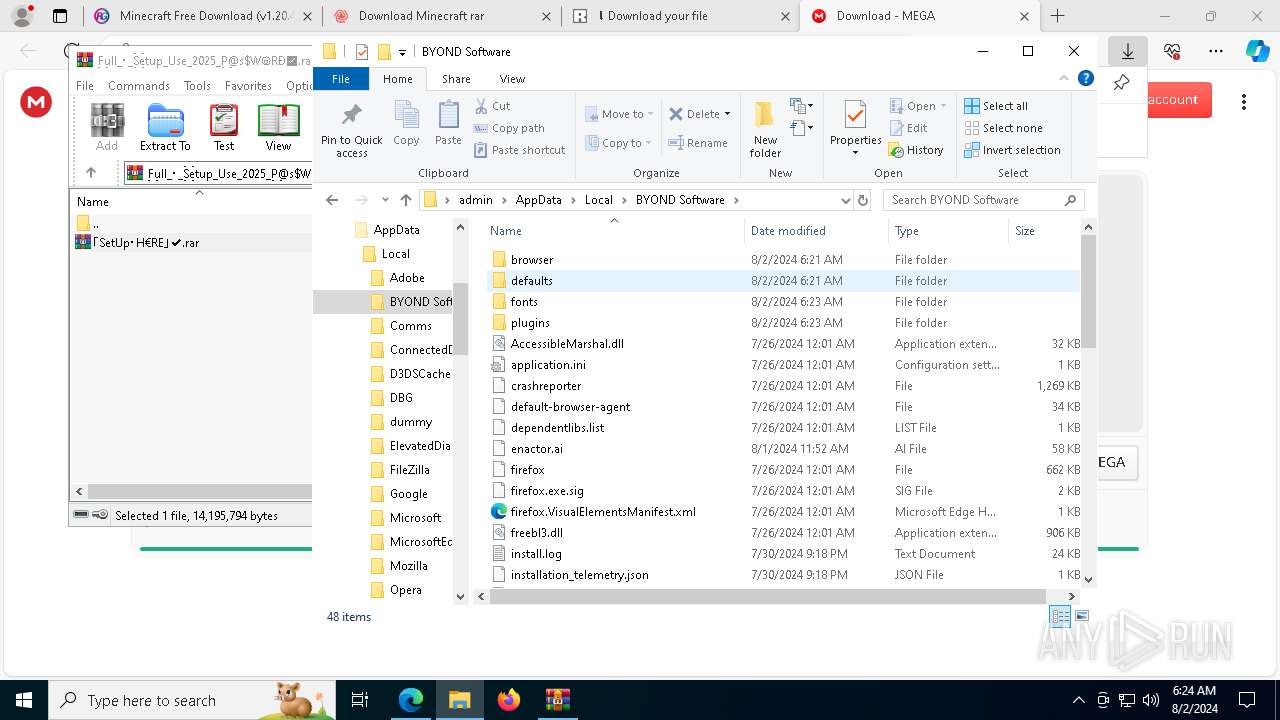
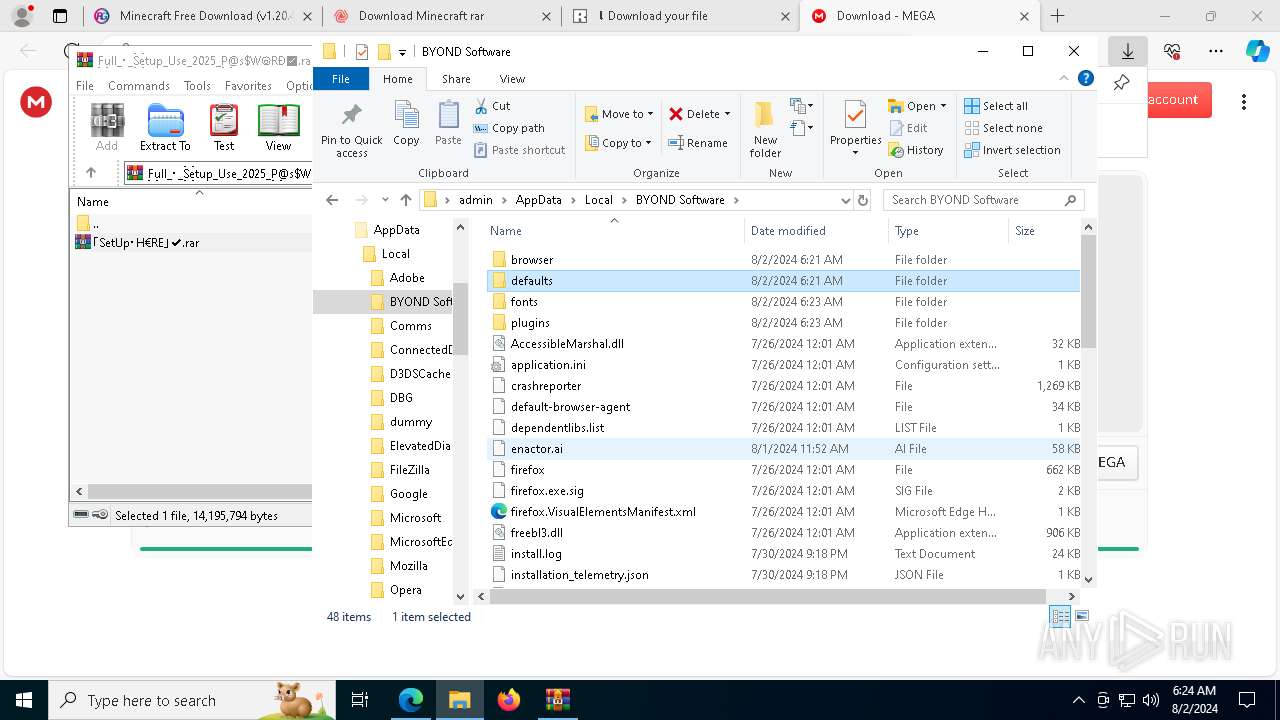
The process drops Mozilla's DLL files
- Setup.tmp (PID: 7256)
- Setup.tmp (PID: 9916)
- Setup.tmp (PID: 7896)
- Setup.tmp (PID: 2524)
Get information on the list of running processes
- cmd.exe (PID: 3864)
- cmd.exe (PID: 7912)
- Setup.tmp (PID: 7256)
- cmd.exe (PID: 5916)
- cmd.exe (PID: 7176)
- cmd.exe (PID: 7204)
- cmd.exe (PID: 2536)
- cmd.exe (PID: 3548)
- Setup.tmp (PID: 9916)
- cmd.exe (PID: 3540)
- cmd.exe (PID: 5632)
- cmd.exe (PID: 5284)
- cmd.exe (PID: 6948)
- cmd.exe (PID: 3660)
- cmd.exe (PID: 8996)
- cmd.exe (PID: 4924)
- Setup.tmp (PID: 7896)
- cmd.exe (PID: 7024)
- cmd.exe (PID: 3116)
- cmd.exe (PID: 6228)
- cmd.exe (PID: 9656)
The process drops C-runtime libraries
- Setup.tmp (PID: 7256)
- LogiAiPromptBuilder.exe (PID: 2096)
- Setup.tmp (PID: 9916)
- Setup.tmp (PID: 7896)
- Setup.tmp (PID: 2524)
Runs PING.EXE to delay simulation
- Setup.tmp (PID: 7256)
- Setup.tmp (PID: 9916)
- Setup.tmp (PID: 7896)
Starts CMD.EXE for commands execution
- Setup.tmp (PID: 7256)
- PQYIVVB7XP1R5EPWGRREG9H1VS5S0YS.exe (PID: 9544)
- Setup.tmp (PID: 9916)
- Setup.tmp (PID: 7896)
- KJFU714L8NCQZKRR6MFMIPW3QNISAZN.exe (PID: 7248)
Starts application with an unusual extension
- LogiAiPromptBuilder.exe (PID: 2096)
- more.com (PID: 10196)
- more.com (PID: 232)
- more.com (PID: 6240)
- LogiAiPromptBuilder.exe (PID: 6952)
- LogiAiPromptBuilder.exe (PID: 7672)
Drops a file with a rarely used extension (PIF)
- more.com (PID: 10196)
Searches for installed software
- BuntEatable.pif (PID: 9044)
- BuntEatable.pif (PID: 8788)
Starts POWERSHELL.EXE for commands execution
- BuntEatable.pif (PID: 9044)
- BuntEatable.pif (PID: 8788)
The process executes Powershell scripts
- BuntEatable.pif (PID: 9044)
- BuntEatable.pif (PID: 8788)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 9772)
- powershell.exe (PID: 6752)
Extracts files to a directory (POWERSHELL)
- powershell.exe (PID: 9772)
- powershell.exe (PID: 6752)
Found regular expressions for crypto-addresses (YARA)
- MSBuild.exe (PID: 5504)
Contacting a server suspected of hosting an CnC
- explorer.exe (PID: 9112)
INFO
Application launched itself
- msedge.exe (PID: 6332)
Reads the computer name
- identity_helper.exe (PID: 7320)
- Setup.tmp (PID: 3660)
- Setup.tmp (PID: 7256)
- StrCmp.exe (PID: 1536)
- more.com (PID: 10196)
- LogiAiPromptBuilder.exe (PID: 2096)
- BuntEatable.pif (PID: 9044)
- PQYIVVB7XP1R5EPWGRREG9H1VS5S0YS.exe (PID: 9544)
- 6UEZ70WBJOZRUV1LTO4RJ3OSDCJM67.exe (PID: 9484)
- Setup.tmp (PID: 9916)
- Setup.tmp (PID: 7992)
- Setup.tmp (PID: 5328)
- Setup.tmp (PID: 7896)
- Setup.tmp (PID: 4692)
- Setup.tmp (PID: 2524)
- LogiAiPromptBuilder.exe (PID: 6952)
- StrCmp.exe (PID: 9040)
- LogiAiPromptBuilder.exe (PID: 7672)
- more.com (PID: 6240)
- TextInputHost.exe (PID: 7024)
- more.com (PID: 232)
- BuntEatable.pif (PID: 8788)
- StrCmp.exe (PID: 9952)
- KJFU714L8NCQZKRR6MFMIPW3QNISAZN.exe (PID: 7248)
- BuntEatable.pif (PID: 9004)
- OG6QKWUMT2DVBPIL.exe (PID: 6192)
Reads Environment values
- identity_helper.exe (PID: 7320)
- Setup.exe (PID: 3876)
- Setup.tmp (PID: 3660)
- Setup.exe (PID: 7428)
- Setup.tmp (PID: 7256)
- Setup.exe (PID: 10124)
- Setup.exe (PID: 7696)
- Setup.tmp (PID: 9916)
- Setup.tmp (PID: 7992)
- Setup.tmp (PID: 5328)
- Setup.tmp (PID: 7896)
- Setup.exe (PID: 2336)
- Setup.exe (PID: 9948)
- Setup.exe (PID: 6272)
- Setup.exe (PID: 6968)
- Setup.tmp (PID: 4692)
- Setup.tmp (PID: 2524)
Reads Microsoft Office registry keys
- msedge.exe (PID: 6332)
Attempting to use instant messaging service
- msedge.exe (PID: 6688)
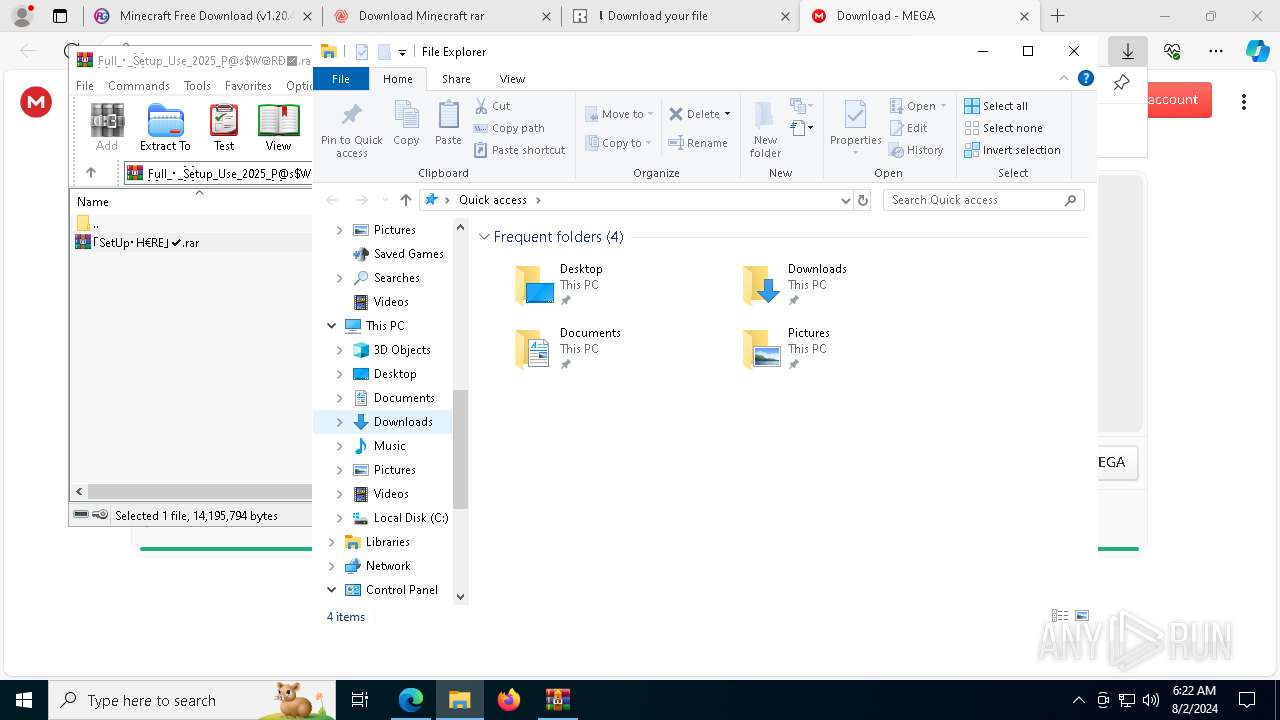
The process uses the downloaded file
- WinRAR.exe (PID: 9972)
- msedge.exe (PID: 9524)
- msedge.exe (PID: 6332)
- WinRAR.exe (PID: 4308)
Checks supported languages
- identity_helper.exe (PID: 7320)
- Setup.exe (PID: 3876)
- Setup.tmp (PID: 3660)
- Setup.tmp (PID: 7256)
- Setup.exe (PID: 7428)
- StrCmp.exe (PID: 1536)
- more.com (PID: 10196)
- LogiAiPromptBuilder.exe (PID: 2096)
- BuntEatable.pif (PID: 9044)
- 6UEZ70WBJOZRUV1LTO4RJ3OSDCJM67.exe (PID: 9484)
- PQYIVVB7XP1R5EPWGRREG9H1VS5S0YS.exe (PID: 9544)
- MSBuild.exe (PID: 5504)
- Setup.exe (PID: 10124)
- Setup.exe (PID: 7696)
- Setup.tmp (PID: 9916)
- Setup.tmp (PID: 7992)
- Setup.exe (PID: 9948)
- Setup.tmp (PID: 5328)
- Setup.exe (PID: 2336)
- Setup.tmp (PID: 7896)
- Setup.exe (PID: 6272)
- Setup.tmp (PID: 4692)
- Setup.exe (PID: 6968)
- Setup.tmp (PID: 2524)
- StrCmp.exe (PID: 9040)
- LogiAiPromptBuilder.exe (PID: 6952)
- LogiAiPromptBuilder.exe (PID: 7672)
- StrCmp.exe (PID: 9952)
- more.com (PID: 232)
- TextInputHost.exe (PID: 7024)
- BuntEatable.pif (PID: 8788)
- more.com (PID: 6240)
- BuntEatable.pif (PID: 9004)
- OG6QKWUMT2DVBPIL.exe (PID: 6192)
- KJFU714L8NCQZKRR6MFMIPW3QNISAZN.exe (PID: 7248)
- MSBuild.exe (PID: 7068)
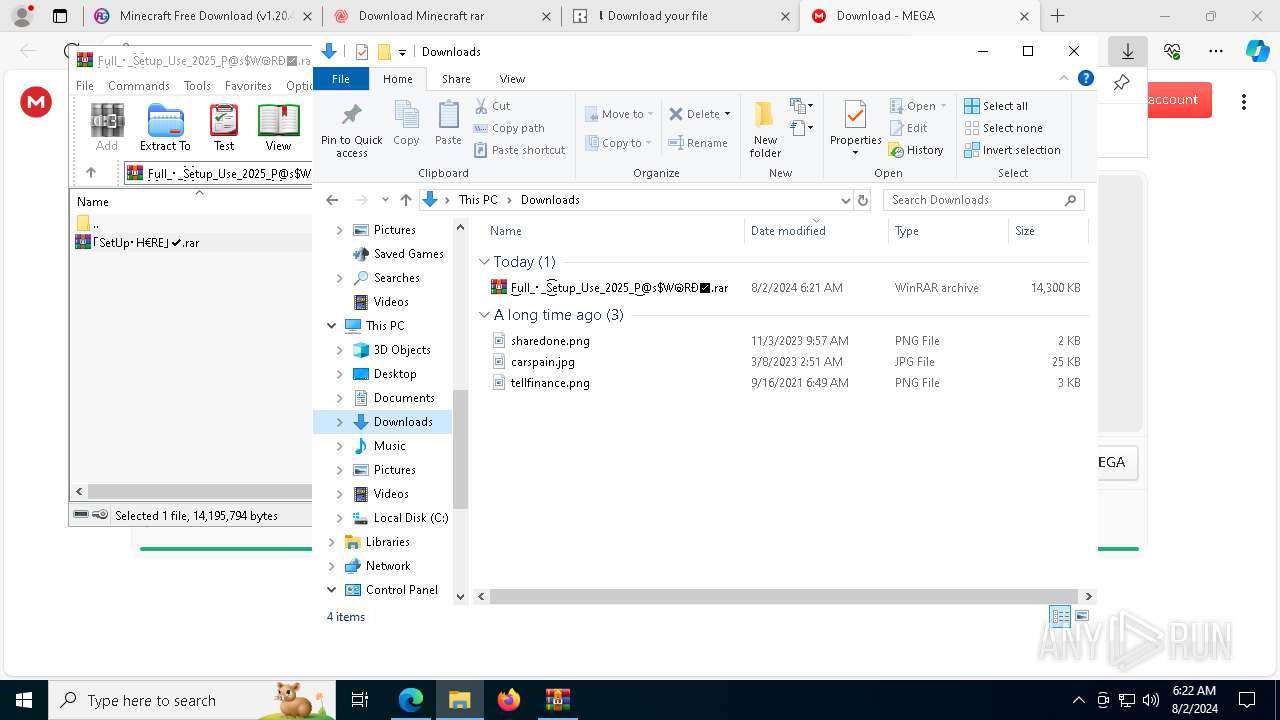
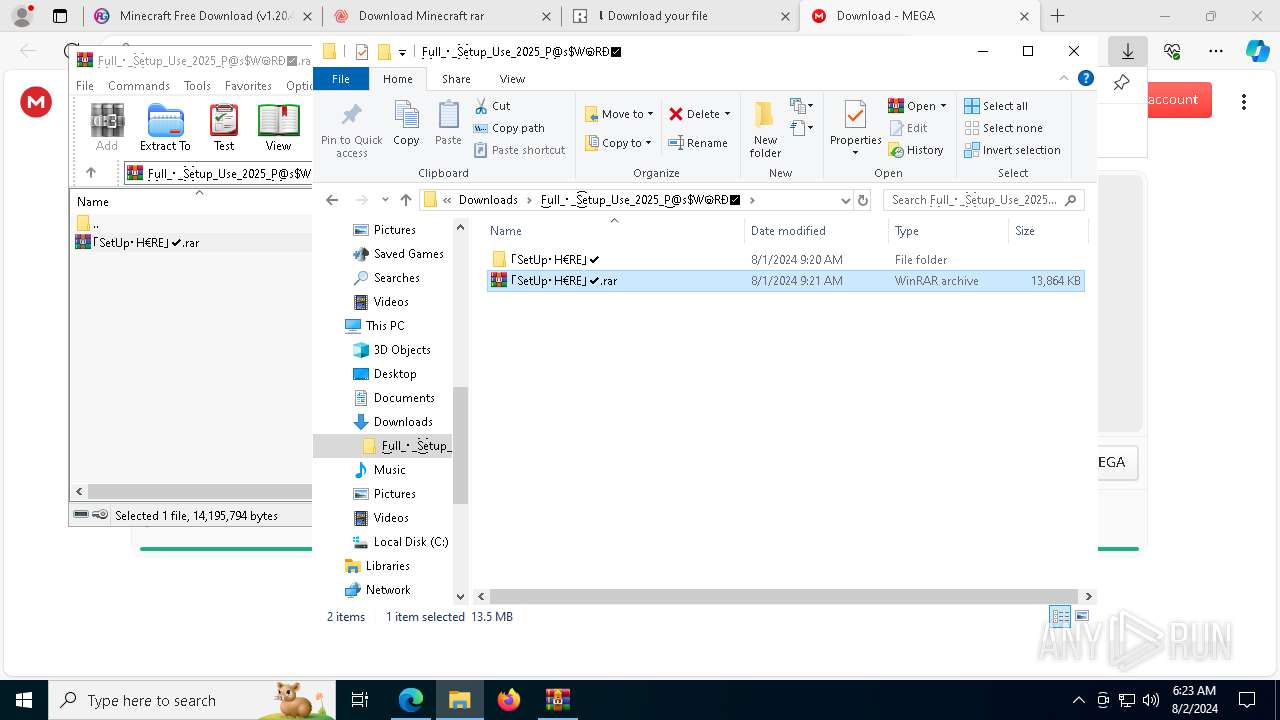
Drops the executable file immediately after the start
- msedge.exe (PID: 6332)
- WinRAR.exe (PID: 10124)
- WinRAR.exe (PID: 9000)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 10124)
- WinRAR.exe (PID: 9000)
Create files in a temporary directory
- Setup.exe (PID: 3876)
- Setup.tmp (PID: 3660)
- Setup.exe (PID: 7428)
- Setup.tmp (PID: 7256)
- LogiAiPromptBuilder.exe (PID: 2096)
- more.com (PID: 10196)
- BuntEatable.pif (PID: 9044)
- PQYIVVB7XP1R5EPWGRREG9H1VS5S0YS.exe (PID: 9544)
- Setup.exe (PID: 10124)
- Setup.tmp (PID: 7992)
- Setup.exe (PID: 7696)
- Setup.tmp (PID: 9916)
- Setup.exe (PID: 9948)
- Setup.tmp (PID: 5328)
- Setup.exe (PID: 2336)
- Setup.exe (PID: 6272)
- Setup.tmp (PID: 7896)
- Setup.exe (PID: 6968)
- Setup.tmp (PID: 4692)
- Setup.tmp (PID: 2524)
- more.com (PID: 232)
- more.com (PID: 6240)
- LogiAiPromptBuilder.exe (PID: 6952)
- LogiAiPromptBuilder.exe (PID: 7672)
- BuntEatable.pif (PID: 8788)
- KJFU714L8NCQZKRR6MFMIPW3QNISAZN.exe (PID: 7248)
Process checks computer location settings
- Setup.tmp (PID: 3660)
- Setup.tmp (PID: 7256)
- Setup.tmp (PID: 7992)
- Setup.tmp (PID: 5328)
- Setup.tmp (PID: 4692)
- Setup.tmp (PID: 9916)
- Setup.tmp (PID: 7896)
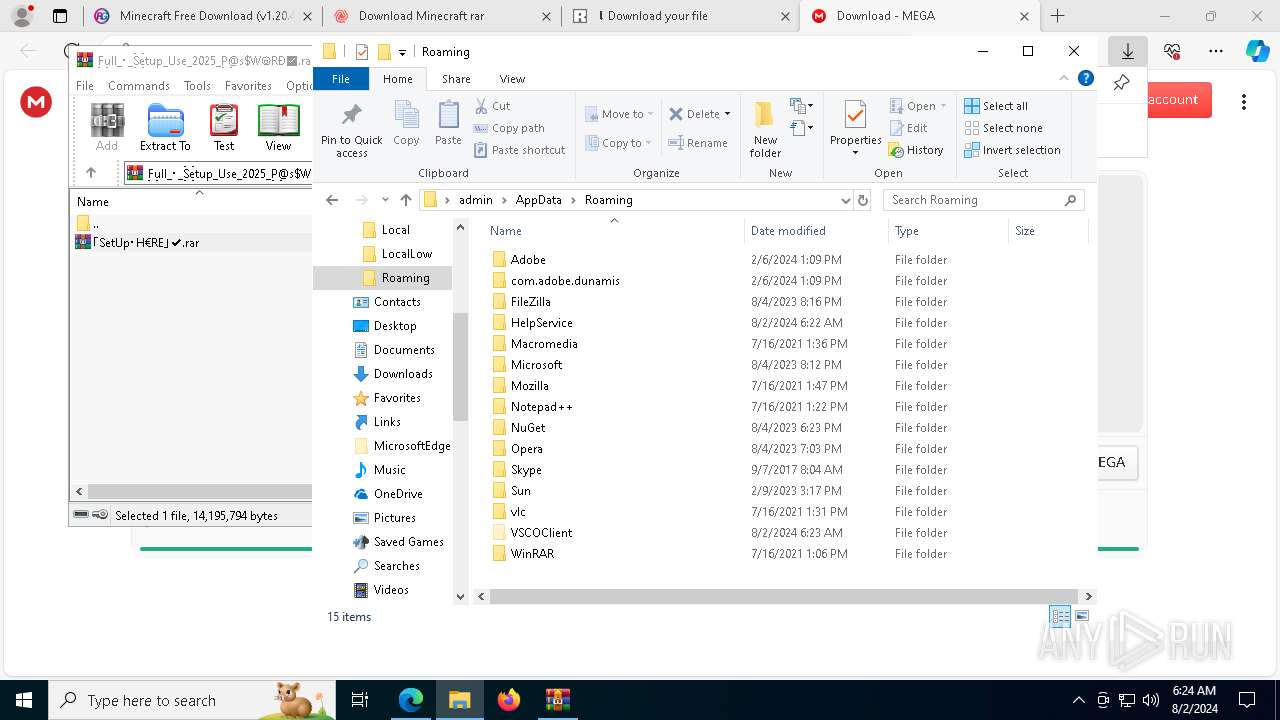
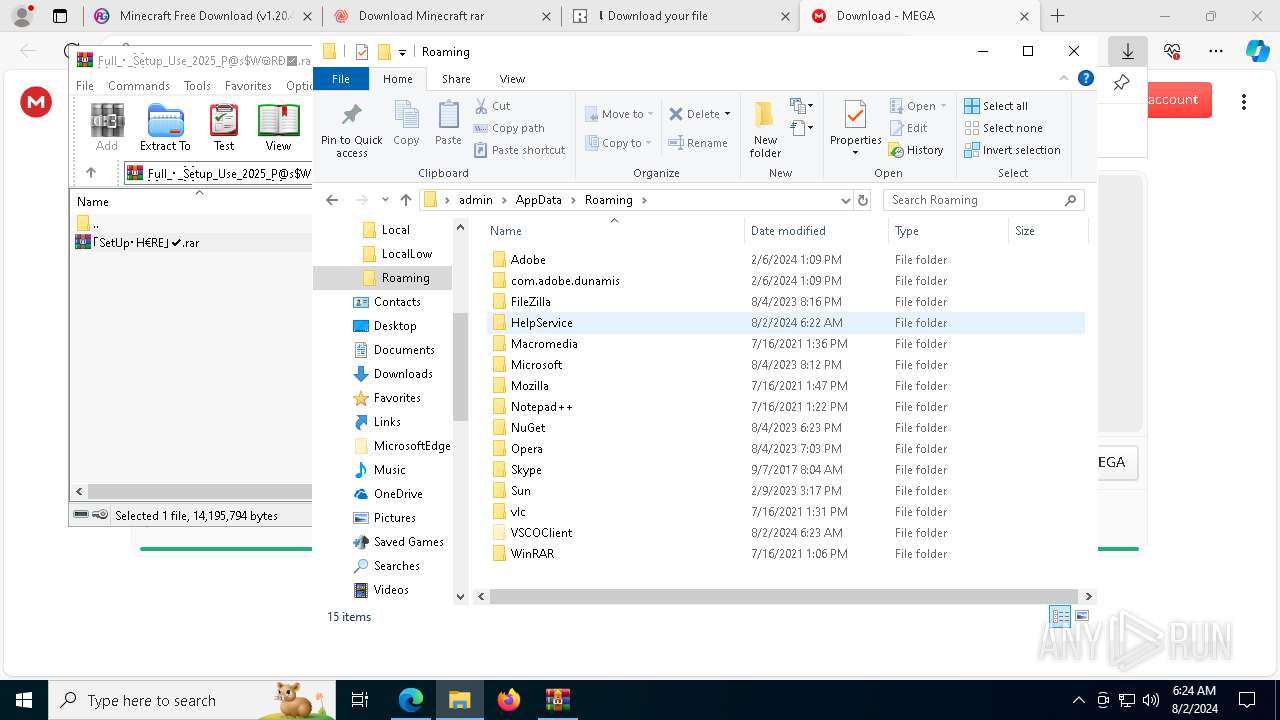
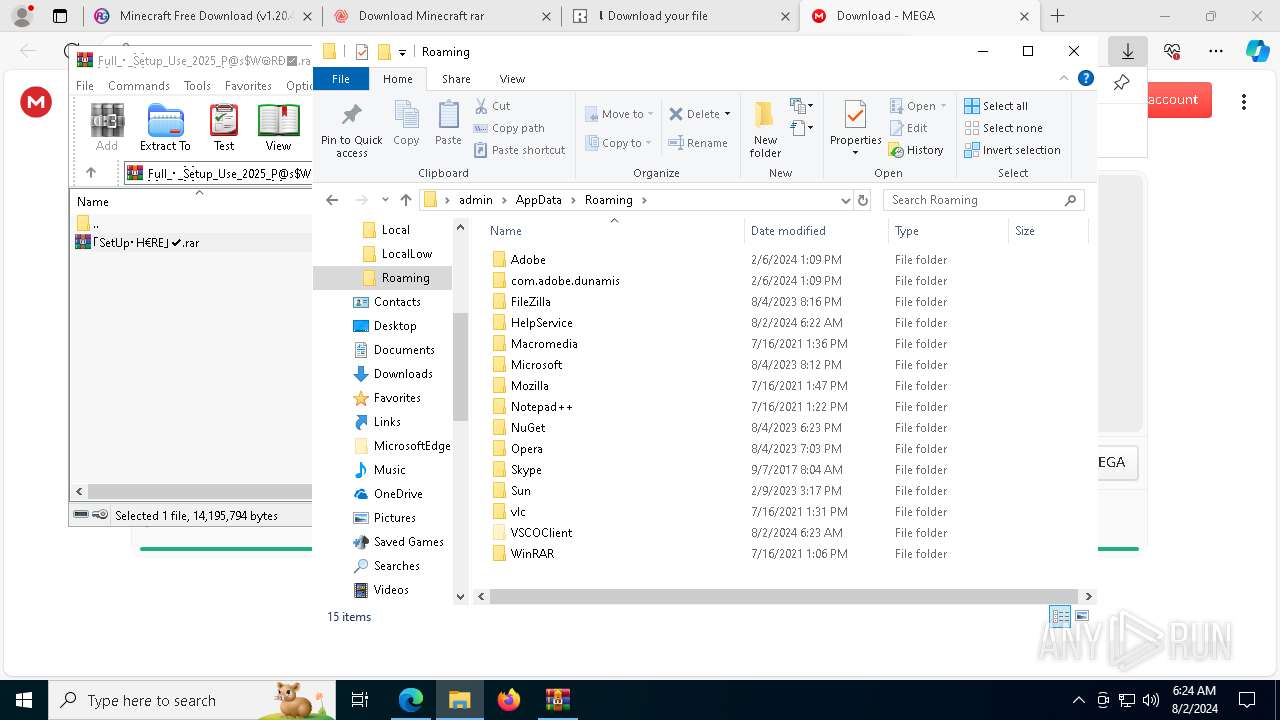
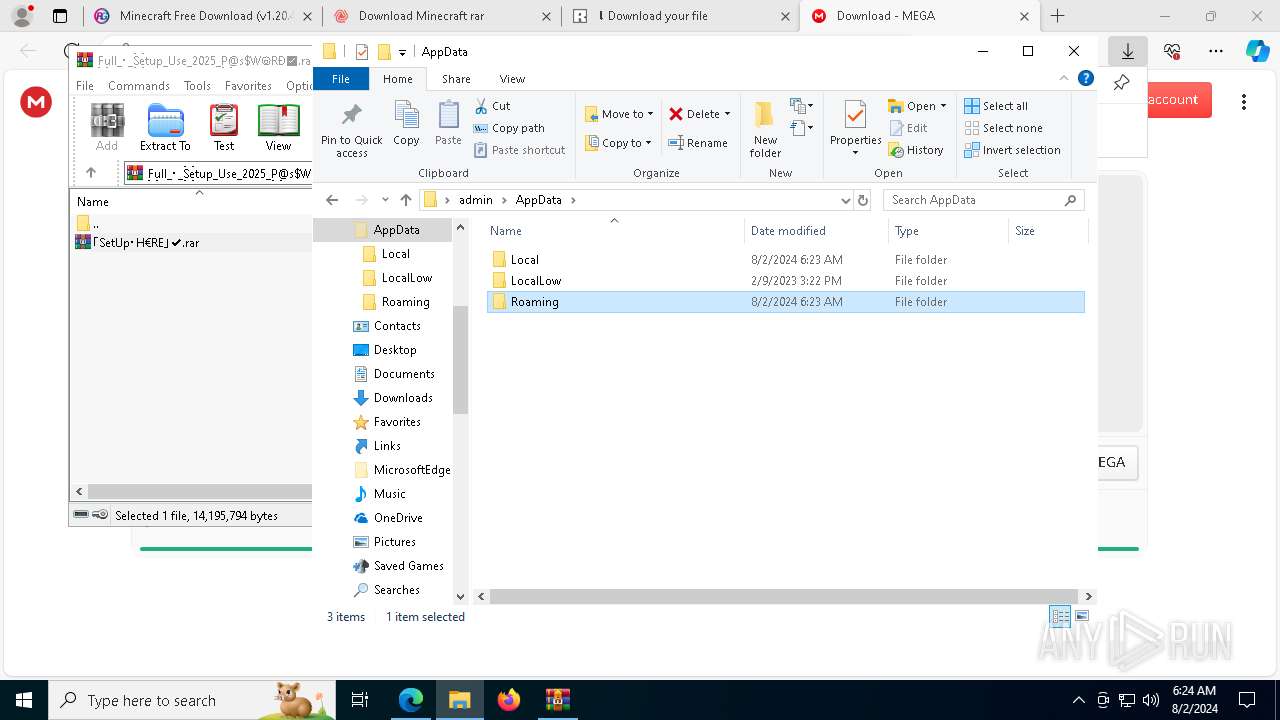
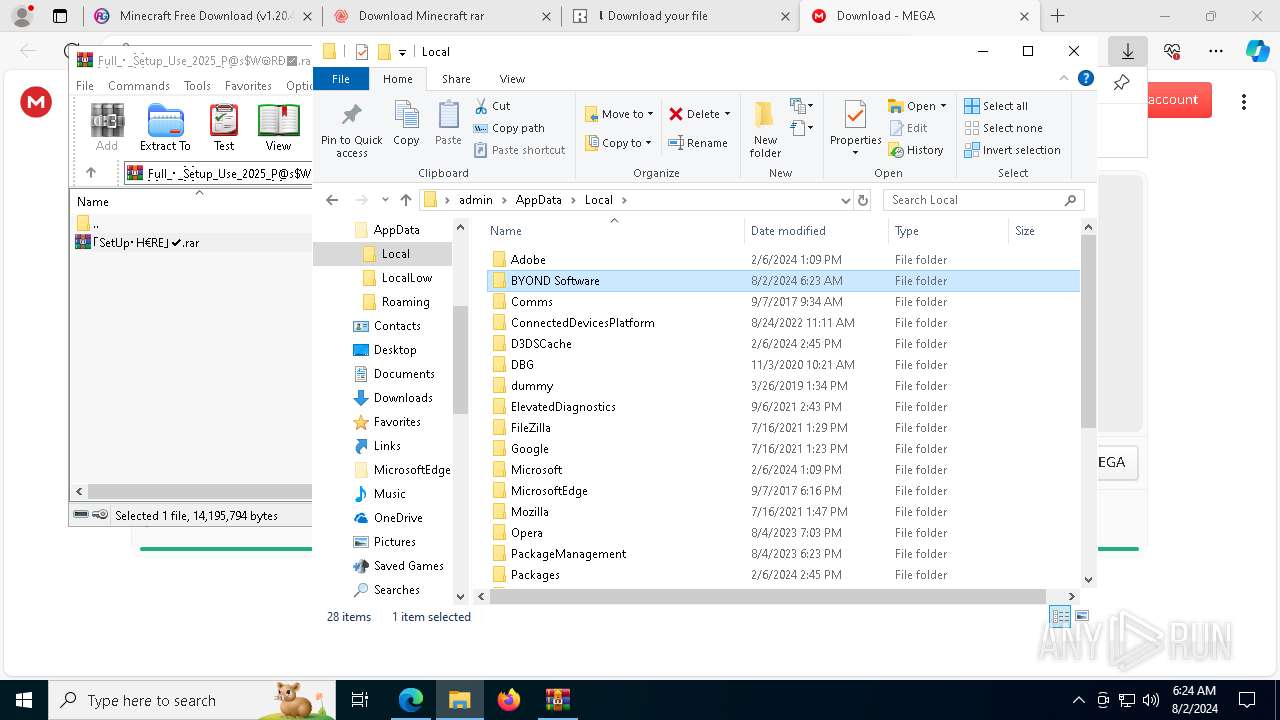
Creates files or folders in the user directory
- Setup.tmp (PID: 7256)
- LogiAiPromptBuilder.exe (PID: 2096)
- 6UEZ70WBJOZRUV1LTO4RJ3OSDCJM67.exe (PID: 9484)
- Setup.tmp (PID: 9916)
- Setup.tmp (PID: 7896)
- Setup.tmp (PID: 2524)
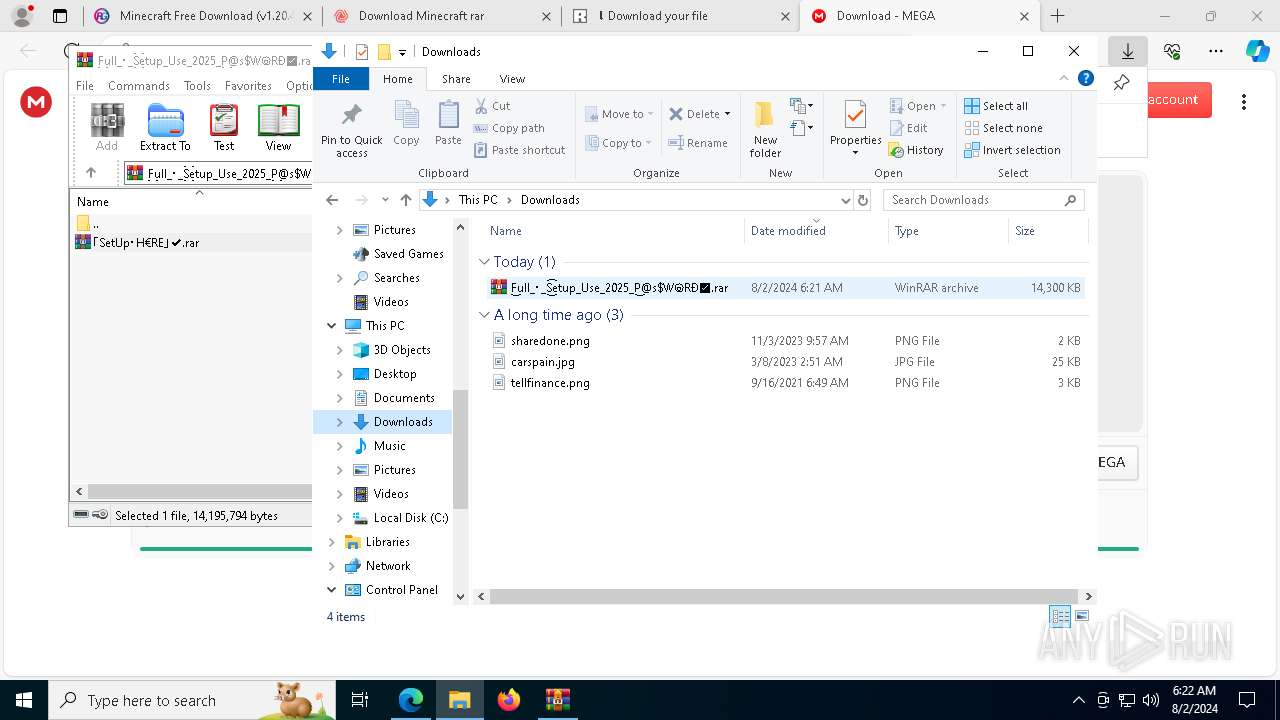
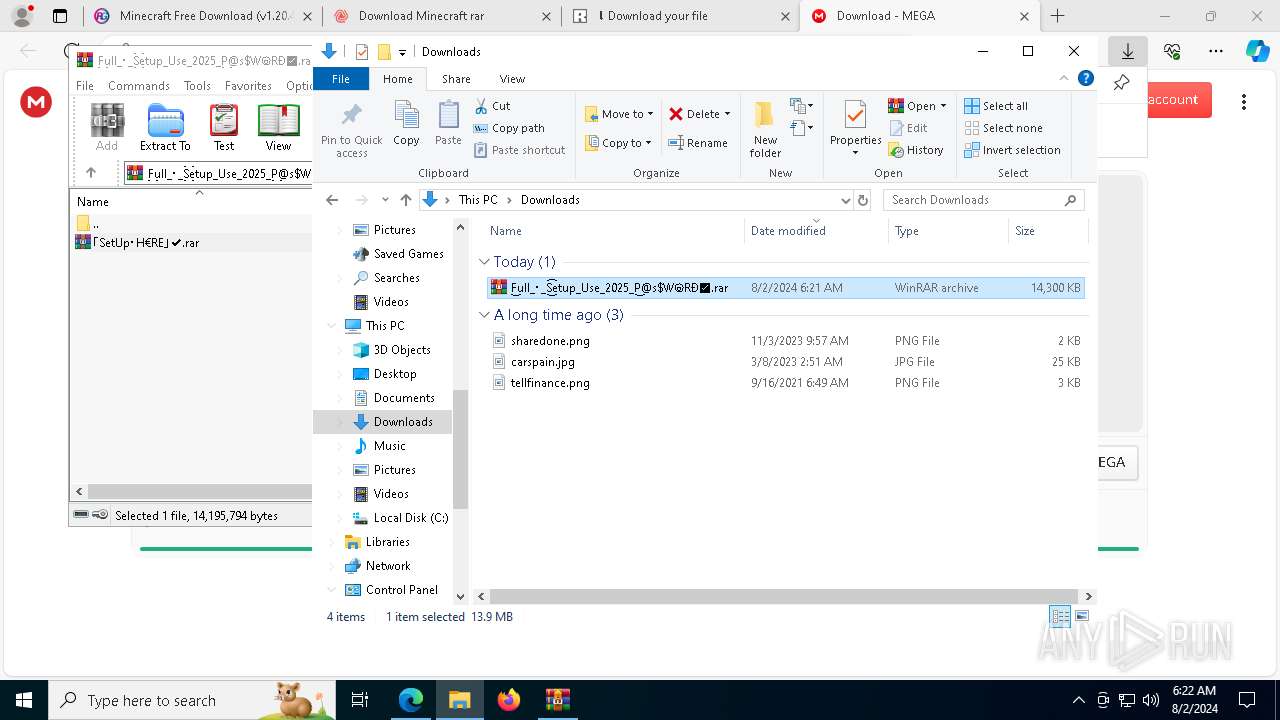
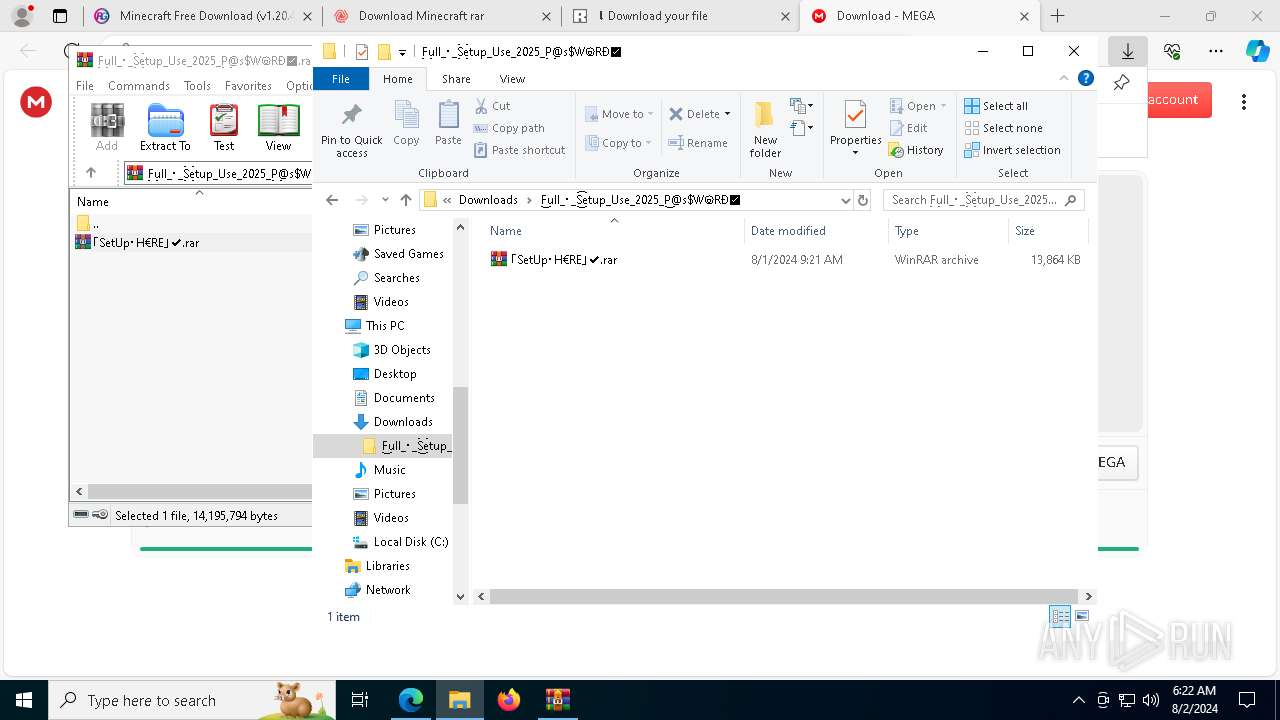
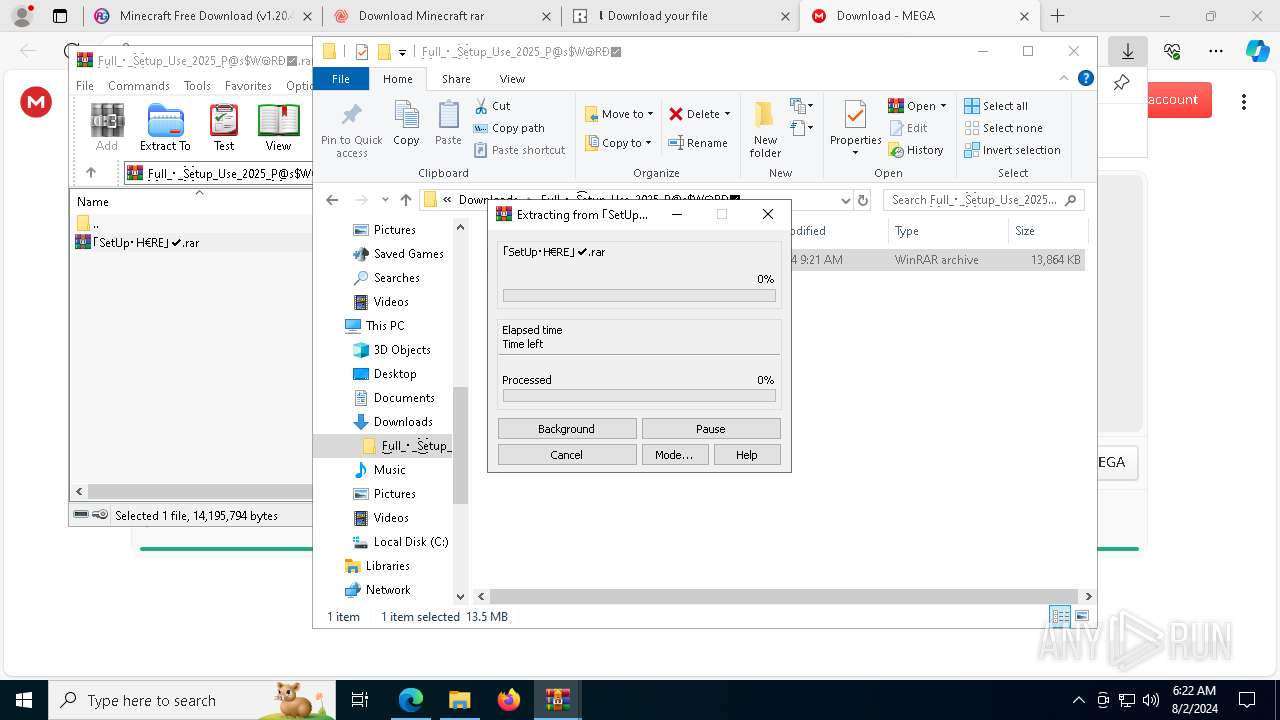
Manual execution by a user
- WinRAR.exe (PID: 4308)
- WinRAR.exe (PID: 9000)
- Setup.exe (PID: 10124)
- Setup.exe (PID: 9948)
- Setup.exe (PID: 6272)
Reads the software policy settings
- BuntEatable.pif (PID: 9044)
- BuntEatable.pif (PID: 8788)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 9772)
- powershell.exe (PID: 6752)
Reads the machine GUID from the registry
- 6UEZ70WBJOZRUV1LTO4RJ3OSDCJM67.exe (PID: 9484)
- OG6QKWUMT2DVBPIL.exe (PID: 6192)
Creates files in the program directory
- MSBuild.exe (PID: 5504)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 9772)
- powershell.exe (PID: 6752)
Reads security settings of Internet Explorer
- explorer.exe (PID: 9112)
Checks proxy server information
- explorer.exe (PID: 9112)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Lumma
(PID) Process(9044) BuntEatable.pif
C2 (9)declaredczxi.shop
replacedoxcjzp.shop
bindceasdiwozx.shop
arriveoxpzxo.shop
roundpleaddysxz.shop
applyzxcksdia.shop
contemplateodszsv.shop
catchddkxozvp.shop
conformfucdioz.shop
(PID) Process(8788) BuntEatable.pif
C2 (9)declaredczxi.shop
replacedoxcjzp.shop
bindceasdiwozx.shop
arriveoxpzxo.shop
roundpleaddysxz.shop
applyzxcksdia.shop
contemplateodszsv.shop
catchddkxozvp.shop
conformfucdioz.shop
Total processes
357
Monitored processes
216
Malicious processes
35
Suspicious processes
14
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 232 | C:\WINDOWS\SysWOW64\more.com | C:\Windows\SysWOW64\more.com | — | LogiAiPromptBuilder.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: More Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 320 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 368 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --no-appcompat-clear --mojo-platform-channel-handle=11500 --field-trial-handle=2408,i,9160493033131470794,8692569779207914294,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 752 | C:\WINDOWS\SysWOW64\cmd.exe | C:\Windows\SysWOW64\cmd.exe | — | PQYIVVB7XP1R5EPWGRREG9H1VS5S0YS.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 936 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --onnx-enabled-for-ee --no-appcompat-clear --mojo-platform-channel-handle=6884 --field-trial-handle=2408,i,9160493033131470794,8692569779207914294,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1020 | find /I "sophoshealth.exe" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1120 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=57 --mojo-platform-channel-handle=10020 --field-trial-handle=2408,i,9160493033131470794,8692569779207914294,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1292 | tasklist /FI "IMAGENAME eq avastui.exe" /FO CSV /NH | C:\Windows\System32\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1536 | C:\Users\admin\AppData\Roaming\HelpService\BNEUQQMTTZQGRKAXUFVC\StrCmp.exe | C:\Users\admin\AppData\Roaming\HelpService\BNEUQQMTTZQGRKAXUFVC\StrCmp.exe | — | LogiAiPromptBuilder.exe | |||||||||||
User: admin Company: aaa Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 1860 | tasklist /FI "IMAGENAME eq sophoshealth.exe" /FO CSV /NH | C:\Windows\System32\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
73 219
Read events
72 783
Write events
393
Delete events
43
Modification events
| (PID) Process: | (6332) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6332) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6332) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (6332) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (6332) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6332) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (6332) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6332) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge |
| Operation: | write | Name: | UsageStatsInSample |
Value: 1 | |||
| (PID) Process: | (6332) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6332) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | urlstats |
Value: 0 | |||
Executable files
362
Suspicious files
516
Text files
331
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6332 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RFe580e.TMP | — | |
MD5:— | SHA256:— | |||
| 6332 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6332 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RFe580e.TMP | — | |
MD5:— | SHA256:— | |||
| 6332 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RFe581e.TMP | — | |
MD5:— | SHA256:— | |||
| 6332 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6332 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6332 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RFe581e.TMP | — | |
MD5:— | SHA256:— | |||
| 6332 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6332 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RFe586c.TMP | — | |
MD5:— | SHA256:— | |||
| 6332 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
36
TCP/UDP connections
488
DNS requests
630
Threats
47
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2456 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6688 | msedge.exe | GET | 304 | 95.101.54.195:80 | http://apps.identrust.com/roots/dstrootcax3.p7c | unknown | — | — | whitelisted |
7200 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6688 | msedge.exe | GET | 304 | 2.23.197.184:80 | http://x1.i.lencr.org/ | unknown | — | — | whitelisted |
6688 | msedge.exe | GET | 304 | 2.23.197.184:80 | http://r3.i.lencr.org/ | unknown | — | — | whitelisted |
7564 | svchost.exe | HEAD | 200 | 2.19.126.155:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/369e8e41-5ce3-4eb8-9826-427d58ae27b0?P1=1723174733&P2=404&P3=2&P4=PmOuMkQ9VDOOJEgEiB0O5pR%2bLBa4u0GQ7IqtSLwZs2ySgcjle8mZrVB0heZp6IG%2fmS%2fZjphvF6cXFNeIp%2fQrZw%3d%3d | unknown | — | — | whitelisted |
7564 | svchost.exe | GET | 206 | 2.19.126.155:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/369e8e41-5ce3-4eb8-9826-427d58ae27b0?P1=1723174733&P2=404&P3=2&P4=PmOuMkQ9VDOOJEgEiB0O5pR%2bLBa4u0GQ7IqtSLwZs2ySgcjle8mZrVB0heZp6IG%2fmS%2fZjphvF6cXFNeIp%2fQrZw%3d%3d | unknown | — | — | whitelisted |
7564 | svchost.exe | GET | 206 | 2.19.126.155:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/369e8e41-5ce3-4eb8-9826-427d58ae27b0?P1=1723174733&P2=404&P3=2&P4=PmOuMkQ9VDOOJEgEiB0O5pR%2bLBa4u0GQ7IqtSLwZs2ySgcjle8mZrVB0heZp6IG%2fmS%2fZjphvF6cXFNeIp%2fQrZw%3d%3d | unknown | — | — | whitelisted |
7564 | svchost.exe | GET | 206 | 2.19.126.155:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/369e8e41-5ce3-4eb8-9826-427d58ae27b0?P1=1723174733&P2=404&P3=2&P4=PmOuMkQ9VDOOJEgEiB0O5pR%2bLBa4u0GQ7IqtSLwZs2ySgcjle8mZrVB0heZp6IG%2fmS%2fZjphvF6cXFNeIp%2fQrZw%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1984 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1184 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6688 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6332 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6688 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
6688 | msedge.exe | 13.107.246.42:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
6688 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
repack-games.com |
| unknown |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
www.bing.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6688 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
6688 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
6688 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
6688 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
6688 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
6688 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
6688 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
6688 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
6688 | msedge.exe | Misc activity | ET INFO Observed Pastebin Service Domain (rentry .co in TLS SNI) |
6688 | msedge.exe | Misc activity | ET INFO Observed Pastebin Service Domain (rentry .co in TLS SNI) |
1 ETPRO signatures available at the full report