| File name: | random.exe |
| Full analysis: | https://app.any.run/tasks/e7d678a6-ce29-4903-af4f-db19b7986d4d |
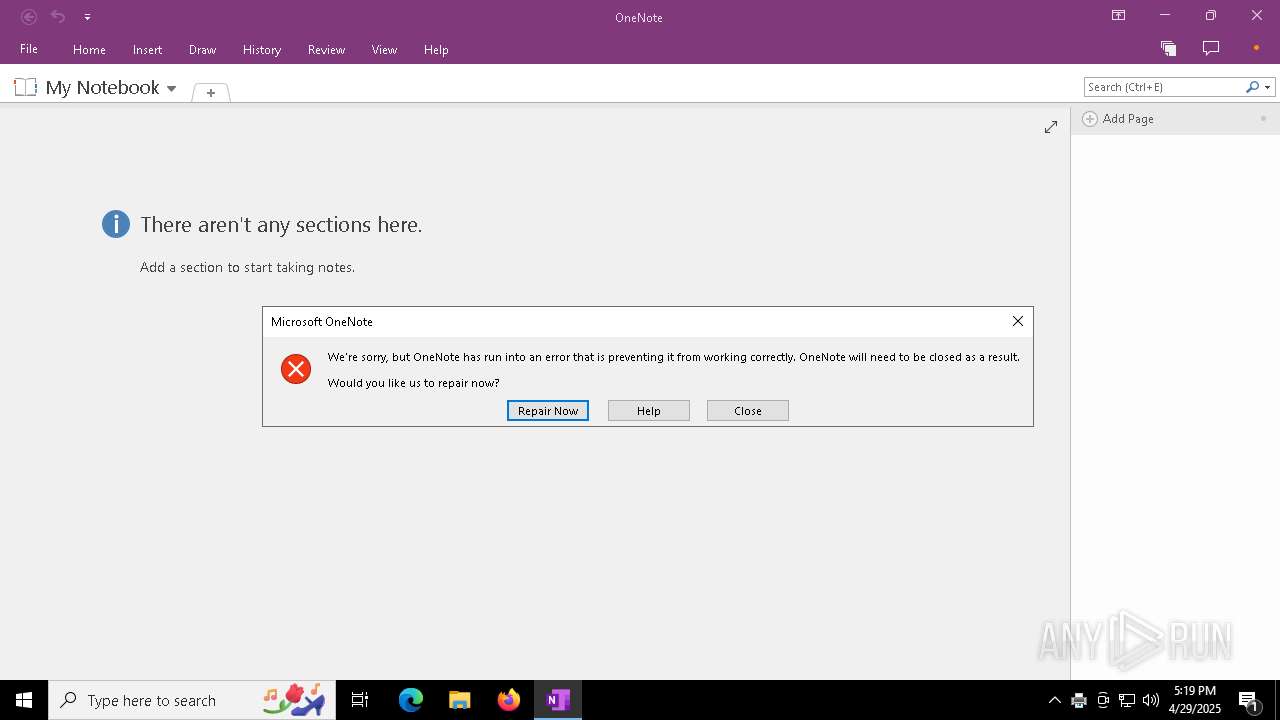
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | April 29, 2025, 17:15:19 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | C26F5B3A535624ADED99E4355236CD44 |
| SHA1: | EE6489180479F156168056CD7BDC9221D41CB46C |
| SHA256: | 24B769CFC837DCB73FFA2319D43961F023D1F01AD311C1FDAEB4BAF0C7EC3EAE |
| SSDEEP: | 49152:2PPkzemqoSut3Jh4+QQ/btosJwIA4hHmZlKH2Tw/Pq83zw0bCjvk9G661QGtfHXx:kP/mp7t3T4+B/btosJwIA4hHmZlKH2TR |
MALICIOUS
Uses Task Scheduler to run other applications
- cmd.exe (PID: 7388)
Run PowerShell with an invisible window
- powershell.exe (PID: 7560)
Request from PowerShell that ran from MSHTA.EXE
- powershell.exe (PID: 7560)
AMADEY has been found (auto)
- powershell.exe (PID: 7560)
- TempTXZLIBIONCBHROYEZROJRFGSUJFBTNEC.EXE (PID: 7204)
Script downloads file (POWERSHELL)
- powershell.exe (PID: 7560)
AMADEY has been detected (SURICATA)
- saved.exe (PID: 2852)
Connects to the CnC server
- saved.exe (PID: 2852)
- svchost.exe (PID: 2196)
Known privilege escalation attack
- dllhost.exe (PID: 900)
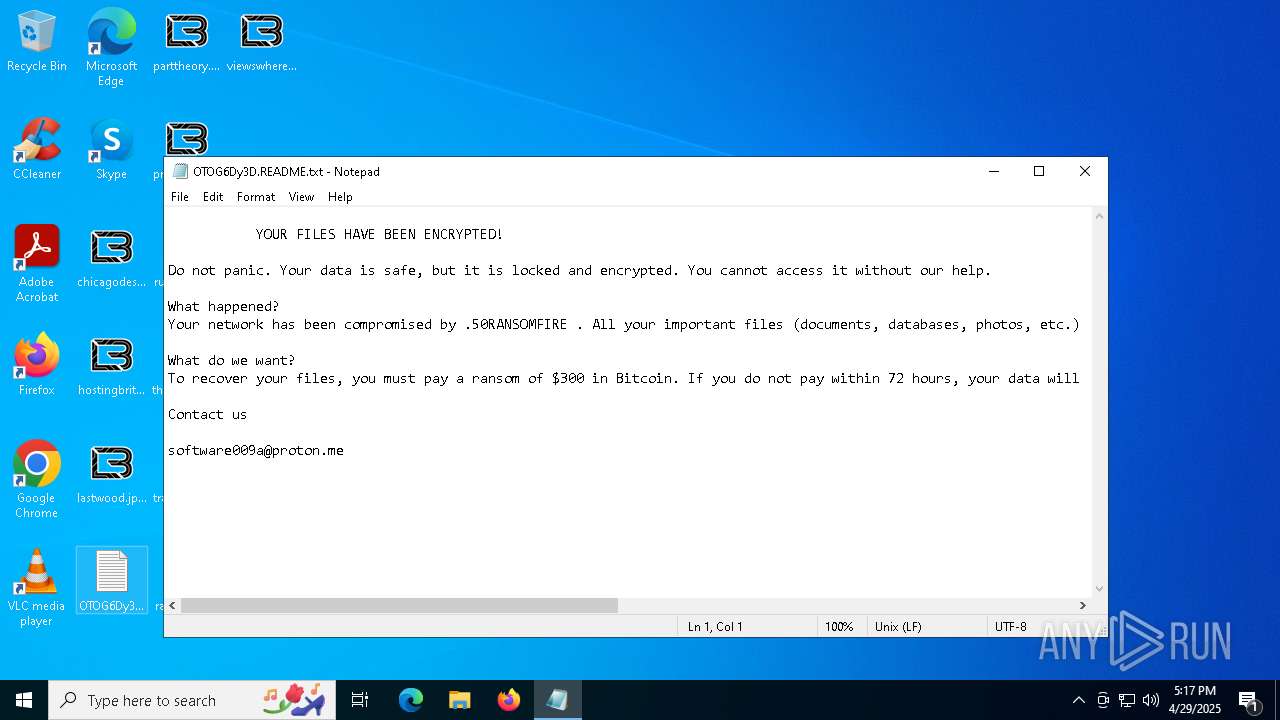
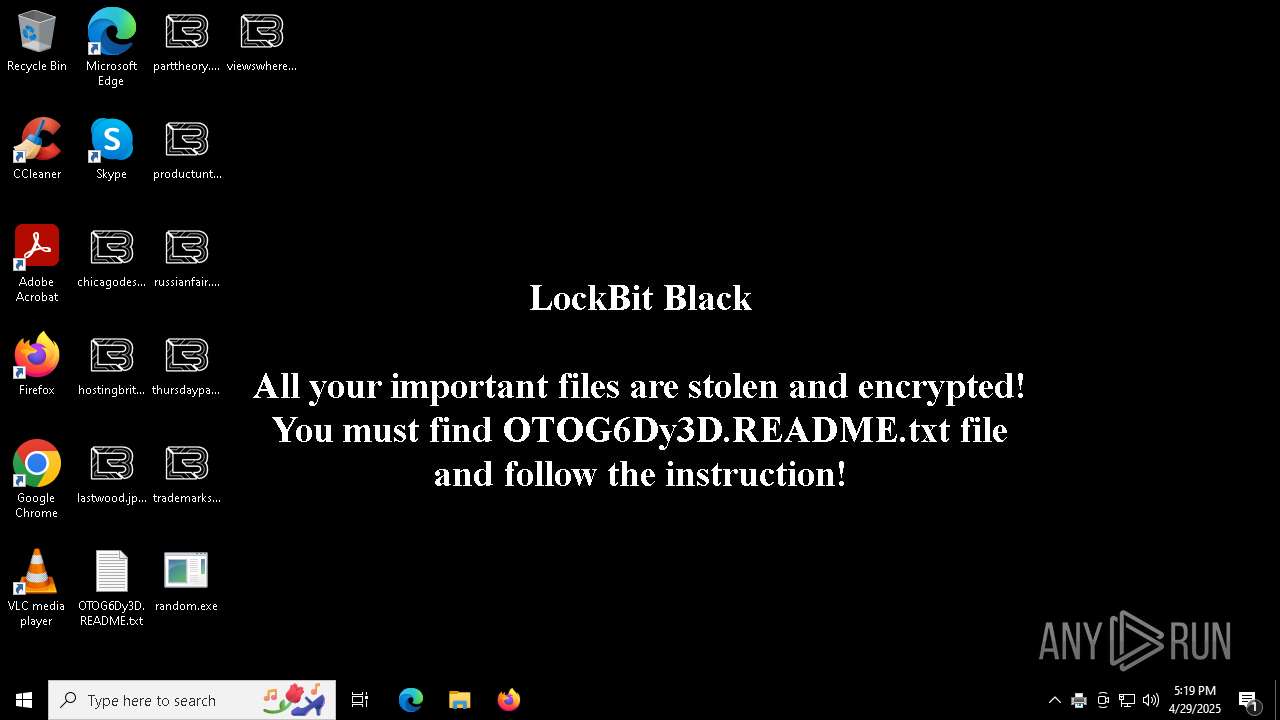
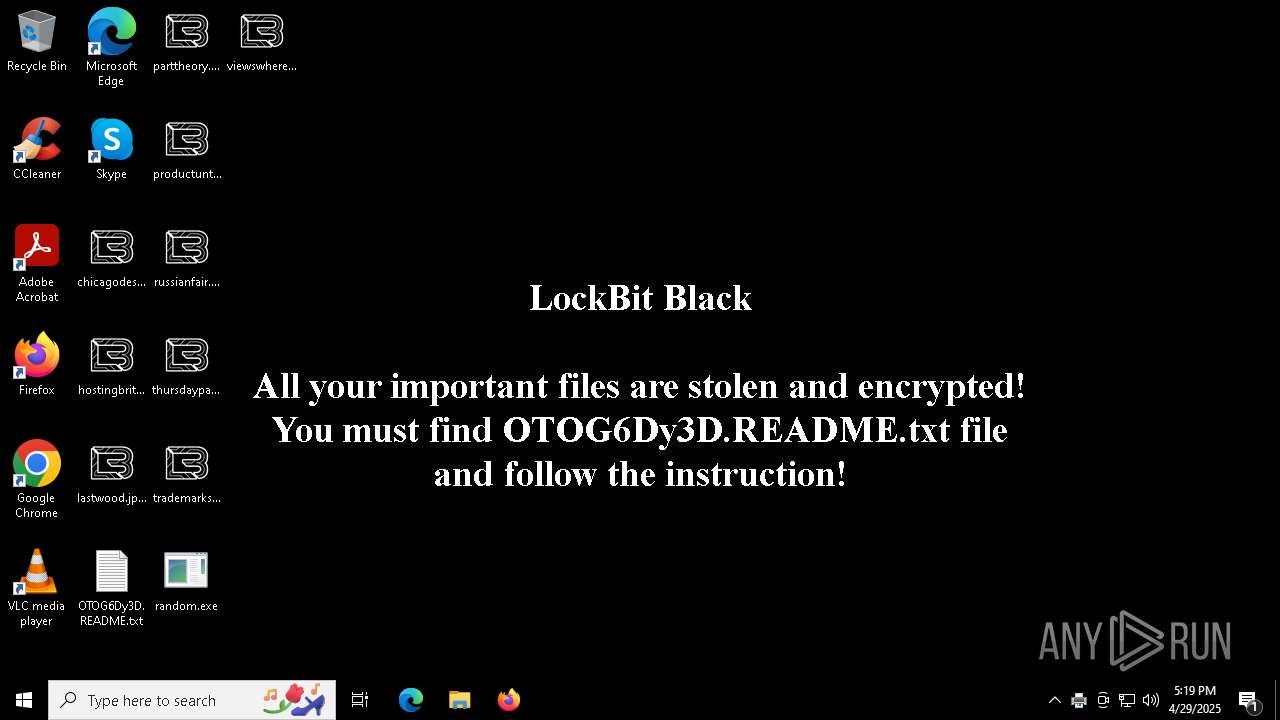
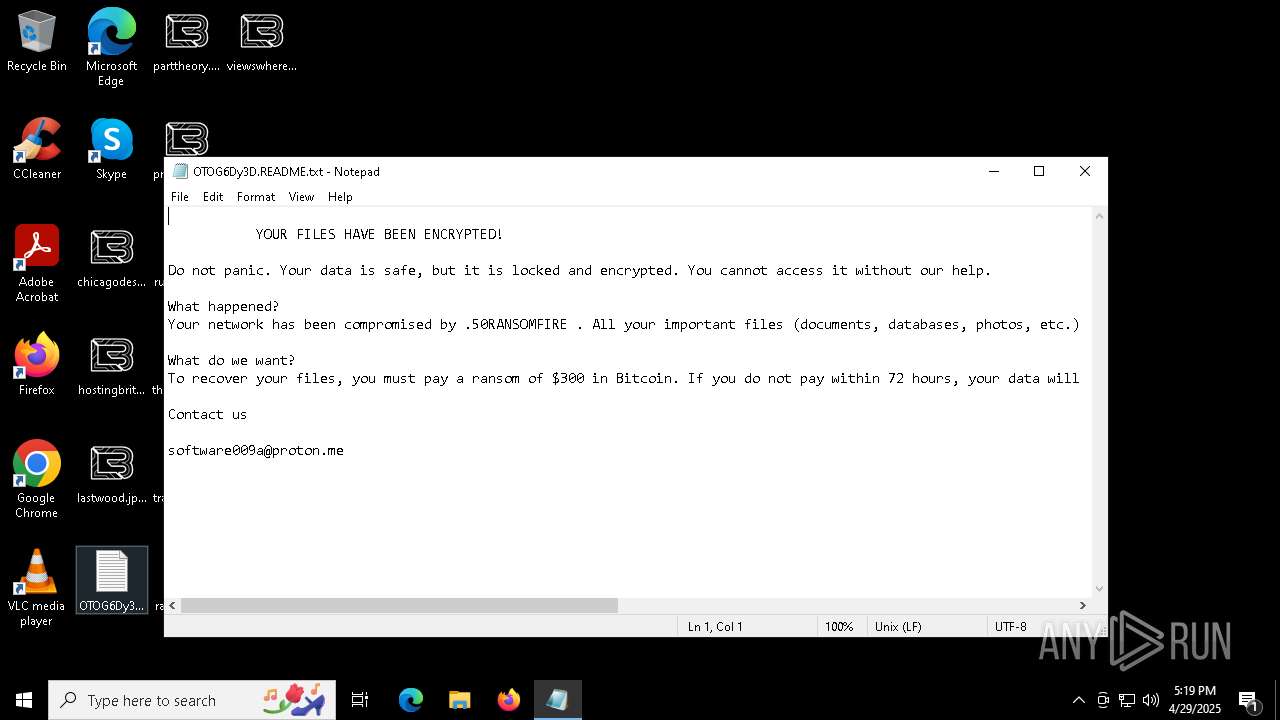
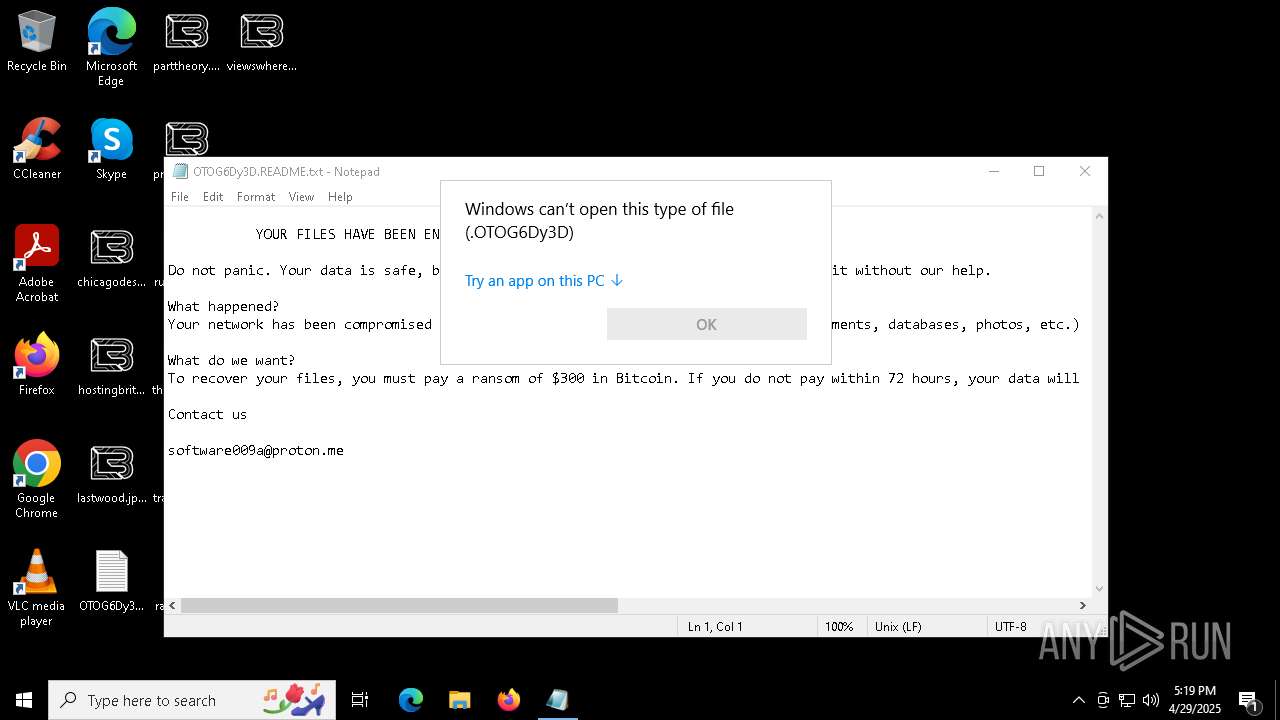
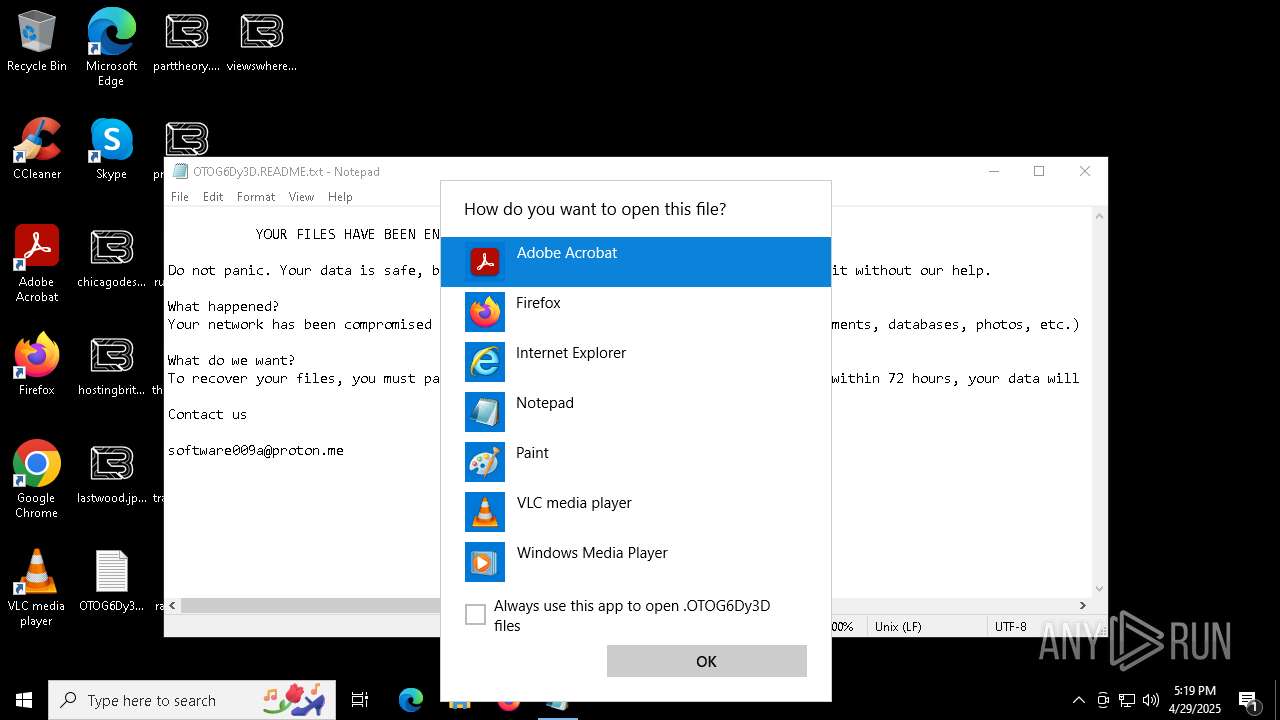
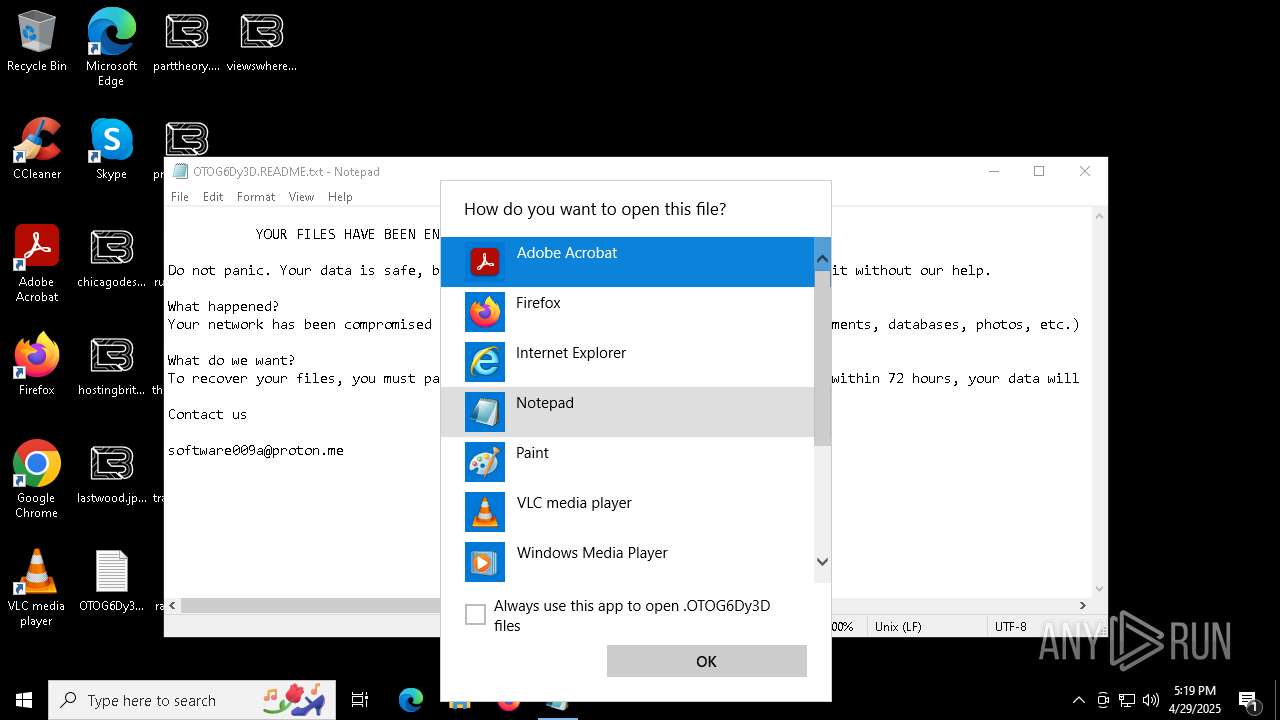
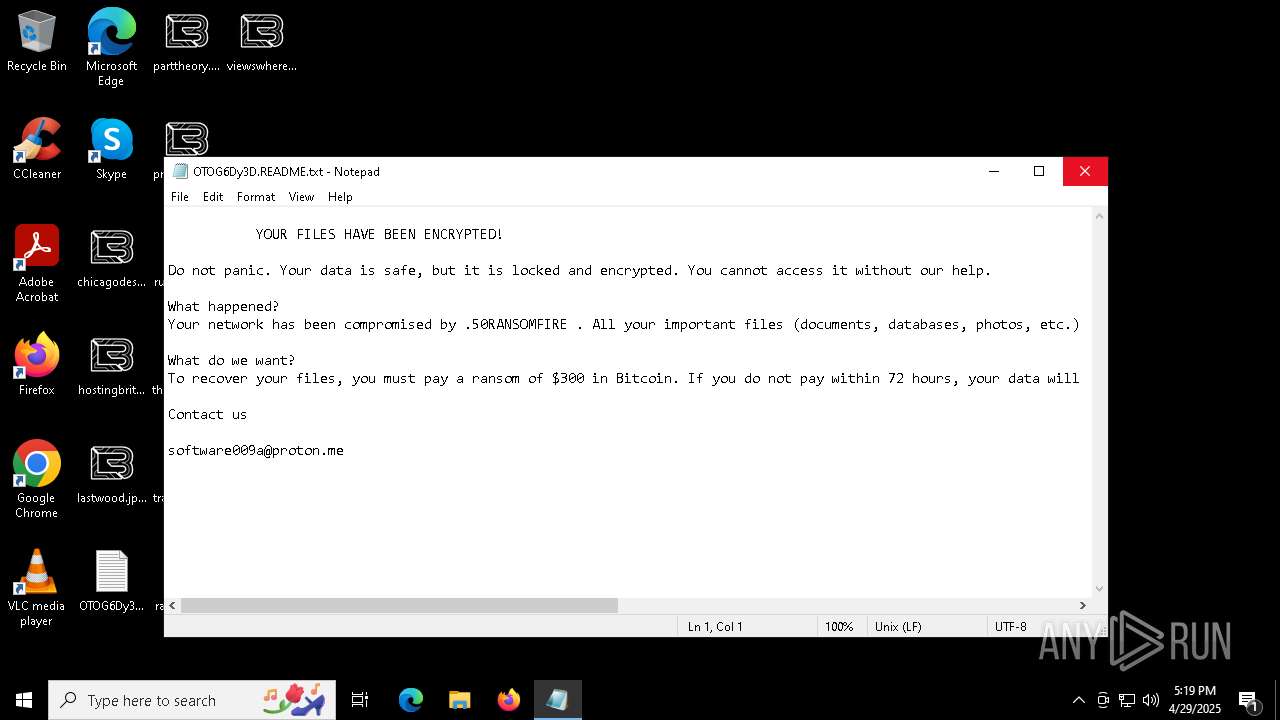
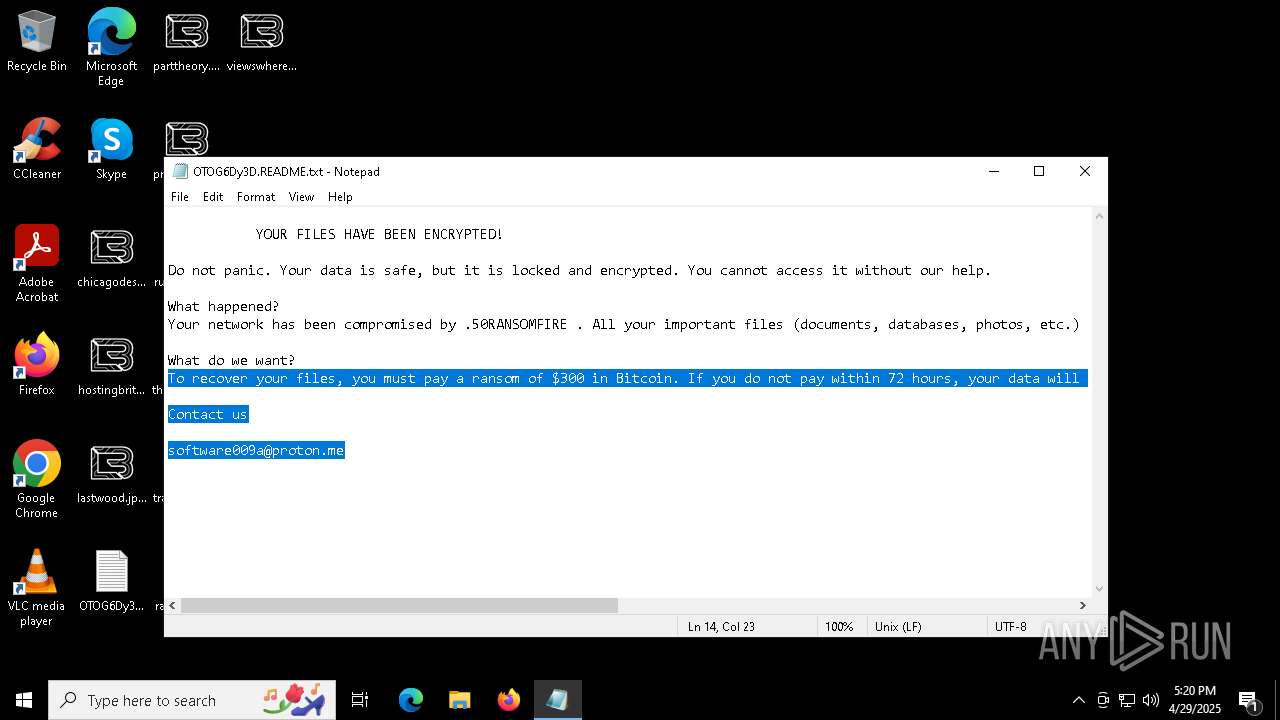
Renames files like ransomware
- 2zRpurD.exe (PID: 7192)
RANSOMWARE has been detected
- 2zRpurD.exe (PID: 7192)
[YARA] LockBit is detected
- 2zRpurD.exe (PID: 7192)
Changes the autorun value in the registry
- bot.exe (PID: 7824)
- windows.exe (PID: 8012)
- EfXjr0K.exe (PID: 8152)
AMADEY has been detected (YARA)
- saved.exe (PID: 2852)
LUMMA mutex has been found
- MSBuild.exe (PID: 208)
- 27fdd41747.exe (PID: 7680)
- MSBuild.exe (PID: 1244)
Actions looks like stealing of personal data
- MSBuild.exe (PID: 208)
- MSBuild.exe (PID: 1244)
- 27fdd41747.exe (PID: 7680)
Steals credentials from Web Browsers
- MSBuild.exe (PID: 208)
- MSBuild.exe (PID: 1244)
- 27fdd41747.exe (PID: 7680)
Stealers network behavior
- svchost.exe (PID: 2196)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2196)
- MSBuild.exe (PID: 1244)
RHADAMANTHYS mutex has been found
- fa2c6a485f.exe (PID: 7488)
- svchost.exe (PID: 7388)
UPATRE has been detected (SURICATA)
- svchost.exe (PID: 7388)
- svchost.exe (PID: 3292)
LUMMA has been detected (YARA)
- MSBuild.exe (PID: 208)
PURECRYPTER has been detected (YARA)
- MSBuild.exe (PID: 720)
Adds path to the Windows Defender exclusion list
- jYKC9dZ.exe (PID: 5304)
- cmd.exe (PID: 8568)
Changes Windows Defender settings
- cmd.exe (PID: 8568)
RHADAMANTHYS has been detected (YARA)
- svchost.exe (PID: 3292)
LOCKBIT3 has been detected
- 20A7.tmp (PID: 8184)
SUSPICIOUS
Starts CMD.EXE for commands execution
- random.exe (PID: 7368)
- jYKC9dZ.exe (PID: 5304)
- 20A7.tmp (PID: 8184)
Manipulates environment variables
- powershell.exe (PID: 7560)
Found IP address in command line
- powershell.exe (PID: 7560)
Connects to the server without a host name
- powershell.exe (PID: 7560)
- saved.exe (PID: 2852)
Starts POWERSHELL.EXE for commands execution
- mshta.exe (PID: 7428)
- cmd.exe (PID: 8568)
- cmd.exe (PID: 8800)
Starts process via Powershell
- powershell.exe (PID: 7560)
Probably download files using WebClient
- mshta.exe (PID: 7428)
Process requests binary or script from the Internet
- powershell.exe (PID: 7560)
- saved.exe (PID: 2852)
Executable content was dropped or overwritten
- powershell.exe (PID: 7560)
- TempTXZLIBIONCBHROYEZROJRFGSUJFBTNEC.EXE (PID: 7204)
- saved.exe (PID: 2852)
- EfXjr0K.exe (PID: 8152)
- powershell.exe (PID: 8816)
- 2zRpurD.exe (PID: 7192)
Potential Corporate Privacy Violation
- powershell.exe (PID: 7560)
- saved.exe (PID: 2852)
Starts itself from another location
- TempTXZLIBIONCBHROYEZROJRFGSUJFBTNEC.EXE (PID: 7204)
- EfXjr0K.exe (PID: 8152)
Reads security settings of Internet Explorer
- TempTXZLIBIONCBHROYEZROJRFGSUJFBTNEC.EXE (PID: 7204)
- saved.exe (PID: 2852)
- ShellExperienceHost.exe (PID: 5204)
Contacting a server suspected of hosting an CnC
- saved.exe (PID: 2852)
- svchost.exe (PID: 2196)
- MSBuild.exe (PID: 1244)
Write to the desktop.ini file (may be used to cloak folders)
- 2zRpurD.exe (PID: 7192)
There is functionality for enable RDP (YARA)
- saved.exe (PID: 2852)
There is functionality for taking screenshot (YARA)
- saved.exe (PID: 2852)
- windows.exe (PID: 8012)
- MSBuild.exe (PID: 208)
The process executes via Task Scheduler
- saved.exe (PID: 8084)
- saved.exe (PID: 8700)
- saved.exe (PID: 5796)
- saved.exe (PID: 1056)
- saved.exe (PID: 6416)
The process checks if it is being run in the virtual environment
- saved.exe (PID: 2852)
- svchost.exe (PID: 7388)
Connects to unusual port
- bot.exe (PID: 7824)
- windows.exe (PID: 8012)
- MSBuild.exe (PID: 720)
- svchost.exe (PID: 7388)
- dllhost.exe (PID: 9064)
- svchost.exe (PID: 3292)
Process drops legitimate windows executable
- saved.exe (PID: 2852)
Checks for external IP
- svchost.exe (PID: 2196)
Starts a Microsoft application from unusual location
- 1xtPr6S.exe (PID: 6080)
- 47Q6wZM.exe (PID: 3300)
- AJ2naPd.exe (PID: 7364)
Reads the BIOS version
- 27fdd41747.exe (PID: 7680)
- fa2c6a485f.exe (PID: 7488)
Possibly patching Antimalware Scan Interface function (YARA)
- bot.exe (PID: 7824)
Found regular expressions for crypto-addresses (YARA)
- windows.exe (PID: 8012)
Executes application which crashes
- fa2c6a485f.exe (PID: 7488)
Searches for installed software
- MSBuild.exe (PID: 1244)
- 27fdd41747.exe (PID: 7680)
- MSBuild.exe (PID: 208)
Uses TASKKILL.EXE to kill process
- AwFCMAP.exe (PID: 6736)
Multiple wallet extension IDs have been found
- MSBuild.exe (PID: 208)
- svchost.exe (PID: 3292)
Application launched itself
- jYKC9dZ.exe (PID: 7196)
Uses TASKKILL.EXE to kill Browsers
- AwFCMAP.exe (PID: 6736)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 8568)
Downloads file from URI via Powershell
- powershell.exe (PID: 8816)
Hides command output
- cmd.exe (PID: 4112)
Starts application with an unusual extension
- 2zRpurD.exe (PID: 7192)
INFO
Reads mouse settings
- random.exe (PID: 7368)
The sample compiled with english language support
- random.exe (PID: 7368)
- saved.exe (PID: 2852)
Create files in a temporary directory
- random.exe (PID: 7368)
- TempTXZLIBIONCBHROYEZROJRFGSUJFBTNEC.EXE (PID: 7204)
- saved.exe (PID: 2852)
- 2zRpurD.exe (PID: 7192)
Reads the computer name
- random.exe (PID: 7368)
- TempTXZLIBIONCBHROYEZROJRFGSUJFBTNEC.EXE (PID: 7204)
- saved.exe (PID: 2852)
- 2zRpurD.exe (PID: 7416)
- 2zRpurD.exe (PID: 7192)
- ShellExperienceHost.exe (PID: 5204)
- bot.exe (PID: 7824)
- windows.exe (PID: 8012)
- EfXjr0K.exe (PID: 8152)
- MSBuild.exe (PID: 208)
- MSBuild.exe (PID: 720)
- 27fdd41747.exe (PID: 7680)
- MSBuild.exe (PID: 1244)
Reads Internet Explorer settings
- mshta.exe (PID: 7428)
Checks supported languages
- random.exe (PID: 7368)
- TempTXZLIBIONCBHROYEZROJRFGSUJFBTNEC.EXE (PID: 7204)
- saved.exe (PID: 2852)
- ShellExperienceHost.exe (PID: 5204)
- 2zRpurD.exe (PID: 7416)
- 2zRpurD.exe (PID: 7192)
- bot.exe (PID: 7824)
- EfXjr0K.exe (PID: 8152)
- saved.exe (PID: 8084)
- windows.exe (PID: 8012)
- MSBuild.exe (PID: 208)
- 1xtPr6S.exe (PID: 6080)
- AJ2naPd.exe (PID: 7364)
- MSBuild.exe (PID: 720)
- 47Q6wZM.exe (PID: 3300)
- 27fdd41747.exe (PID: 7680)
- MSBuild.exe (PID: 1244)
- fa2c6a485f.exe (PID: 7488)
- zb7jDew.exe (PID: 4400)
Disables trace logs
- powershell.exe (PID: 7560)
- windows.exe (PID: 8012)
Checks proxy server information
- powershell.exe (PID: 7560)
- saved.exe (PID: 2852)
- windows.exe (PID: 8012)
The executable file from the user directory is run by the Powershell process
- TempTXZLIBIONCBHROYEZROJRFGSUJFBTNEC.EXE (PID: 7204)
Process checks computer location settings
- TempTXZLIBIONCBHROYEZROJRFGSUJFBTNEC.EXE (PID: 7204)
- saved.exe (PID: 2852)
Creates files or folders in the user directory
- saved.exe (PID: 2852)
- 2zRpurD.exe (PID: 7192)
- EfXjr0K.exe (PID: 8152)
Reads the machine GUID from the registry
- 2zRpurD.exe (PID: 7416)
- bot.exe (PID: 7824)
- windows.exe (PID: 8012)
- EfXjr0K.exe (PID: 8152)
- MSBuild.exe (PID: 720)
Reads security settings of Internet Explorer
- dllhost.exe (PID: 900)
Creates files in the program directory
- 2zRpurD.exe (PID: 7192)
- bot.exe (PID: 7824)
Reads the software policy settings
- bot.exe (PID: 7824)
- windows.exe (PID: 8012)
- MSBuild.exe (PID: 208)
- MSBuild.exe (PID: 1244)
- 27fdd41747.exe (PID: 7680)
Reads Environment values
- windows.exe (PID: 8012)
- EfXjr0K.exe (PID: 8152)
Manual execution by a user
- svchost.exe (PID: 7388)
- svchost.exe (PID: 3292)
- notepad.exe (PID: 8596)
- notepad.exe (PID: 8112)
Application launched itself
- chrome.exe (PID: 8096)
- msedge.exe (PID: 7732)
.NET Reactor protector has been detected
- MSBuild.exe (PID: 720)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Amadey
(PID) Process(2852) saved.exe
C2185.39.17.163
URLhttp://185.39.17.163/Su8kud7i/index.php
Version5.34
Options
Drop directoryc13dbdc4fa
Drop namesaved.exe
Strings (125)S-%lu-
og:
clip.dll
ProgramData\
shell32.dll
<c>
vs:
Programs
&&
VideoID
ESET
av:
\App
0000043f
Doctor Web
:::
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders
------
rundll32.exe
00000422
185.39.17.163
0123456789
st=s
00000419
Content-Type: application/x-www-form-urlencoded
/Plugins/
msi
ar:
GetNativeSystemInfo
Norton
-%lu
Sophos
zip
SOFTWARE\Microsoft\Windows NT\CurrentVersion
"
Content-Type: application/octet-stream
|
+++
" && ren
pc:
#
d1
cmd /C RMDIR /s/q
Bitdefender
Comodo
<d>
Kaspersky Lab
DefaultSettings.YResolution
Main
c13dbdc4fa
-executionpolicy remotesigned -File "
&& Exit"
ProductName
&unit=
2022
Panda Security
=
Rem
cmd
\0000
id:
sd:
--
/quiet
rundll32
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Shell Folders
%-lu
random
GET
"taskkill /f /im "
Content-Disposition: form-data; name="data"; filename="
00000423
5.34
2016
?scr=1
ComputerName
Keyboard Layout\Preload
Powershell.exe
POST
http://
AVAST Software
SYSTEM\CurrentControlSet\Control\UnitedVideo\CONTROL\VIDEO\
ps1
DefaultSettings.XResolution
Startup
CurrentBuild
e3
cred.dll|clip.dll|
------
WinDefender
wb
https://
Avira
2025
" && timeout 1 && del
cred.dll
un:
SYSTEM\ControlSet001\Services\BasicDisplay\Video
rb
SYSTEM\CurrentControlSet\Control\ComputerName\ComputerName
360TotalSecurity
SOFTWARE\Microsoft\Windows\CurrentVersion\Run
saved.exe
e1
lv:
/Su8kud7i/index.php
shutdown -s -t 0
/k
e2
SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce
exe
%USERPROFILE%
-unicode-
r=
.jpg
dll
Content-Type: multipart/form-data; boundary=----
2019
bi:
\
"
kernel32.dll
os:
abcdefghijklmnopqrstuvwxyz0123456789-_
dm:
AVG
Lumma
(PID) Process(208) MSBuild.exe
C2 (9)parakehjet.run/kewk
buzzarddf.live/ktnt
zenithcorde.top/auid
bearjk.live/benj
techguidet.digital/apdo
techsyncq.run/riid
btcgeared.live/lbak
vecturar.top/zsia
fishgh.digital/tequ
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:04:29 05:31:02+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.16 |
| CodeSize: | 633856 |
| InitializedDataSize: | 326144 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x20577 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (British) |
| CharacterSet: | Unicode |
Total processes
264
Monitored processes
115
Malicious processes
25
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe | 1xtPr6S.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: MSBuild.exe Version: 4.8.9037.0 built by: NET481REL1 Modules
Lumma(PID) Process(208) MSBuild.exe C2 (9)parakehjet.run/kewk buzzarddf.live/ktnt zenithcorde.top/auid bearjk.live/benj techguidet.digital/apdo techsyncq.run/riid btcgeared.live/lbak vecturar.top/zsia fishgh.digital/tequ | |||||||||||||||
| 300 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=3036 --field-trial-handle=1908,i,15565823040787506581,16477650208691236281,262144 --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 444 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --extension-process --renderer-sub-type=extension --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=11 --mojo-platform-channel-handle=4880 --field-trial-handle=2284,i,1703685750291076152,12281541744437558602,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 456 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --extension-process --renderer-sub-type=extension --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=10 --mojo-platform-channel-handle=4652 --field-trial-handle=2284,i,1703685750291076152,12281541744437558602,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 516 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\lastwood.jpg.OTOG6Dy3D | C:\Windows\System32\notepad.exe | — | OpenWith.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 720 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe | AJ2naPd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: MSBuild.exe Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 736 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe | — | 1xtPr6S.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: MSBuild.exe Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 812 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=3052 --field-trial-handle=1908,i,15565823040787506581,16477650208691236281,262144 --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 900 | C:\WINDOWS\SysWOW64\DllHost.exe /Processid:{3E5FC7F9-9A51-4367-9063-A120244FBEC7} | C:\Windows\SysWOW64\dllhost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1056 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler --user-data-dir=C:\Users\admin\AppData\Local\Temp\chrFCCC.tmp /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler --database=C:\Users\admin\AppData\Local\Temp\chrFCCC.tmp\Crashpad --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=122.0.6261.70 --initial-client-data=0x224,0x228,0x22c,0x200,0x230,0x7ffc84c7dc40,0x7ffc84c7dc4c,0x7ffc84c7dc58 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
58 928
Read events
56 119
Write events
2 790
Delete events
19
Modification events
| (PID) Process: | (7428) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7428) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7428) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (7560) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (7560) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (7560) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (7560) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (7560) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (7560) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (7560) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
Executable files
56
Suspicious files
2 329
Text files
2 500
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7192 | 2zRpurD.exe | C:\$Recycle.Bin\S-1-5-18\desktop.ini | binary | |
MD5:FB1F8FDCBFDC0ACBEB12BF388D4BB124 | SHA256:C148D00F3DB8144C341EEB6CDFA7B986E90F0A19E40347B2F9F5AF4CD7F66014 | |||
| 7560 | powershell.exe | C:\Users\admin\AppData\Local\TempTXZLIBIONCBHROYEZROJRFGSUJFBTNEC.EXE | executable | |
MD5:F6C20A18AFEAC04964A6CCAD6BE59731 | SHA256:CE75F9DEDE6D4E93549D35B816898113B6BEFAB9EF0AADF8949D4887C2C34BEA | |||
| 2852 | saved.exe | C:\Users\admin\AppData\Local\Temp\10057920101\2zRpurD.exe | executable | |
MD5:FBA45177BFEA84F712A65C383AB7DEA0 | SHA256:DA3BF442394BA82F5B1222FF2D8355FD2D6789A0DFB5BF0B43DDE7BB1AB42875 | |||
| 7560 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:EFD9DB3AC02C6BB00818B1FC13D15980 | SHA256:584FB4156D028D6E1F8CF845660696F4D2D63794D132A2E86E63C9C1FB97A831 | |||
| 7204 | TempTXZLIBIONCBHROYEZROJRFGSUJFBTNEC.EXE | C:\Windows\Tasks\saved.job | binary | |
MD5:FDE232F686AE186544782D632C811722 | SHA256:D9E21544B839FE431D8C8D046EB75A19BA0FC403A9CB94D65C1ACCE1524187C8 | |||
| 7204 | TempTXZLIBIONCBHROYEZROJRFGSUJFBTNEC.EXE | C:\Users\admin\AppData\Local\Temp\c13dbdc4fa\saved.exe | executable | |
MD5:F6C20A18AFEAC04964A6CCAD6BE59731 | SHA256:CE75F9DEDE6D4E93549D35B816898113B6BEFAB9EF0AADF8949D4887C2C34BEA | |||
| 2852 | saved.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\2zRpurD[1].exe | executable | |
MD5:FBA45177BFEA84F712A65C383AB7DEA0 | SHA256:DA3BF442394BA82F5B1222FF2D8355FD2D6789A0DFB5BF0B43DDE7BB1AB42875 | |||
| 7192 | 2zRpurD.exe | C:\$Recycle.Bin\S-1-5-18\AAAAAAAAAAA | binary | |
MD5:FB1F8FDCBFDC0ACBEB12BF388D4BB124 | SHA256:C148D00F3DB8144C341EEB6CDFA7B986E90F0A19E40347B2F9F5AF4CD7F66014 | |||
| 7368 | random.exe | C:\Users\admin\AppData\Local\Temp\bY0FKxQHk.hta | html | |
MD5:C6666B62C0C34B72381B8019F360B172 | SHA256:DA9753CC10AE6DFB0FE57413C180BF45617FF4EDDA6D8A37BFD71A69E845D5CC | |||
| 7560 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_0d1tffql.ffl.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
39
TCP/UDP connections
1 815
DNS requests
69
Threats
51
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.31:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2852 | saved.exe | POST | 200 | 185.39.17.163:80 | http://185.39.17.163/Su8kud7i/index.php | unknown | — | — | malicious |
7560 | powershell.exe | GET | 200 | 185.39.17.162:80 | http://185.39.17.162/testmine/random.exe | unknown | — | — | malicious |
2852 | saved.exe | GET | 200 | 185.39.17.162:80 | http://185.39.17.162/files/7244183739/2zRpurD.exe | unknown | — | — | malicious |
2852 | saved.exe | POST | 200 | 185.39.17.163:80 | http://185.39.17.163/Su8kud7i/index.php | unknown | — | — | malicious |
2852 | saved.exe | POST | 200 | 185.39.17.163:80 | http://185.39.17.163/Su8kud7i/index.php | unknown | — | — | malicious |
2852 | saved.exe | GET | 200 | 185.39.17.162:80 | http://185.39.17.162/files/ScrapeSeller/bot.exe | unknown | — | — | malicious |
6476 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2656 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.31:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6544 | svchost.exe | 40.126.32.133:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
7560 | powershell.exe | 185.39.17.162:80 | — | Joint Stock Company Tagnet | RU | malicious |
2852 | saved.exe | 185.39.17.163:80 | — | Joint Stock Company Tagnet | RU | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
maksimbolshayashopa.live |
| unknown |
brolyx95.duckdns.org |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7560 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
7560 | powershell.exe | Misc activity | ET INFO Packed Executable Download |
7560 | powershell.exe | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
7560 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
7560 | powershell.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |
2852 | saved.exe | Malware Command and Control Activity Detected | BOTNET [ANY.RUN] Amadey HTTP POST Request (st=s) |
2852 | saved.exe | Malware Command and Control Activity Detected | ET MALWARE Amadey CnC Response |
2852 | saved.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
2852 | saved.exe | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
2852 | saved.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |