| File name: | cs2.exe |
| Full analysis: | https://app.any.run/tasks/d2209cdd-5415-4fa0-b0c5-4bae814fc767 |
| Verdict: | Malicious activity |
| Threats: | Blank Grabber is an infostealer written in Python. It is designed to steal a wide array of data, such as browser login credentials, crypto wallets, Telegram sessions, and Discord tokens. It is an open-source malware, with its code available on GitHub and regularly receiving updates. Blank Grabber builder’s simple interface lets threat actors even with basic skills to deploy it and conduct attacks. |
| Analysis date: | June 04, 2025, 17:36:38 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 7 sections |
| MD5: | 4D6ADAC236A0FEE1051CFAAC571ADE12 |
| SHA1: | 77429B11664FA8A8E3BBBD5A55230CA631068134 |
| SHA256: | 240296107A1AEB74A67E6CA382C667B667FFD54B4AE980FE401EFE2215D0EB5A |
| SSDEEP: | 98304:gCYzBUmRnOzhJ8QKCt7bm6GpJ0SDaVj0HbiAiYMq4OSIeJzxBL7jPSPQvJVfPVNi:tZqM8YgBjfh |
MALICIOUS
Executing a file with an untrusted certificate
- cs2.exe (PID: 7316)
- cs2.exe (PID: 7000)
- cs2.exe (PID: 1072)
BlankGrabber has been detected
- cs2.exe (PID: 7316)
- cs2.exe (PID: 7000)
Adds path to the Windows Defender exclusion list
- cs2.exe (PID: 1072)
- cmd.exe (PID: 7888)
- cmd.exe (PID: 6540)
- .scr (PID: 6004)
- cmd.exe (PID: 776)
- .scr (PID: 7080)
- cmd.exe (PID: 7136)
Antivirus name has been found in the command line (generic signature)
- cmd.exe (PID: 7492)
- cmd.exe (PID: 4476)
- cmd.exe (PID: 7472)
Changes settings for protection against network attacks (IPS)
- powershell.exe (PID: 2392)
- powershell.exe (PID: 6336)
- powershell.exe (PID: 7836)
Changes settings for sending potential threat samples to Microsoft servers
- powershell.exe (PID: 2392)
- powershell.exe (PID: 6336)
- powershell.exe (PID: 7836)
Changes settings for real-time protection
- powershell.exe (PID: 2392)
- powershell.exe (PID: 6336)
- powershell.exe (PID: 7836)
Changes settings for checking scripts for malicious actions
- powershell.exe (PID: 2392)
- powershell.exe (PID: 6336)
- powershell.exe (PID: 7836)
Changes settings for reporting to Microsoft Active Protection Service (MAPS)
- powershell.exe (PID: 2392)
- powershell.exe (PID: 6336)
- powershell.exe (PID: 7836)
Changes antivirus protection settings for downloading files from the Internet (IOAVProtection)
- powershell.exe (PID: 2392)
- powershell.exe (PID: 6336)
- powershell.exe (PID: 7836)
Changes Windows Defender settings
- cmd.exe (PID: 7492)
- cmd.exe (PID: 7888)
- cmd.exe (PID: 6540)
- cmd.exe (PID: 776)
- cmd.exe (PID: 4476)
- cmd.exe (PID: 7472)
- cmd.exe (PID: 7136)
Changes Controlled Folder Access settings
- powershell.exe (PID: 2392)
- powershell.exe (PID: 6336)
- powershell.exe (PID: 7836)
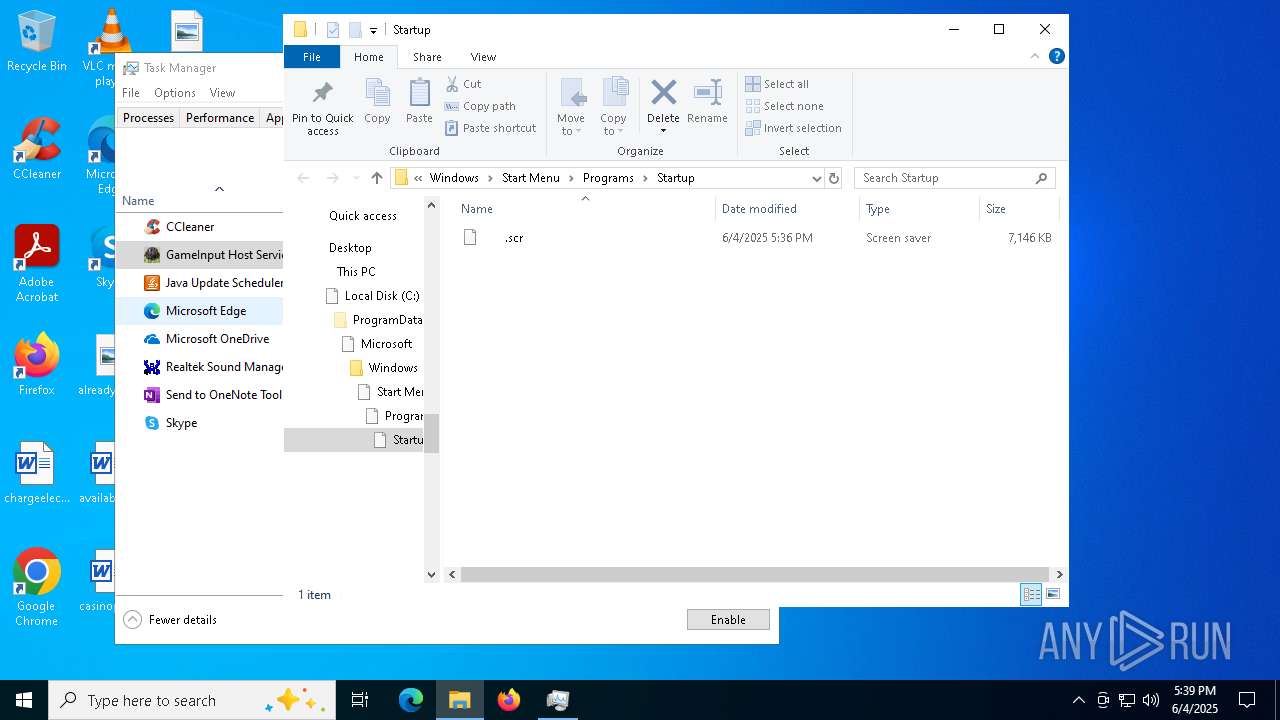
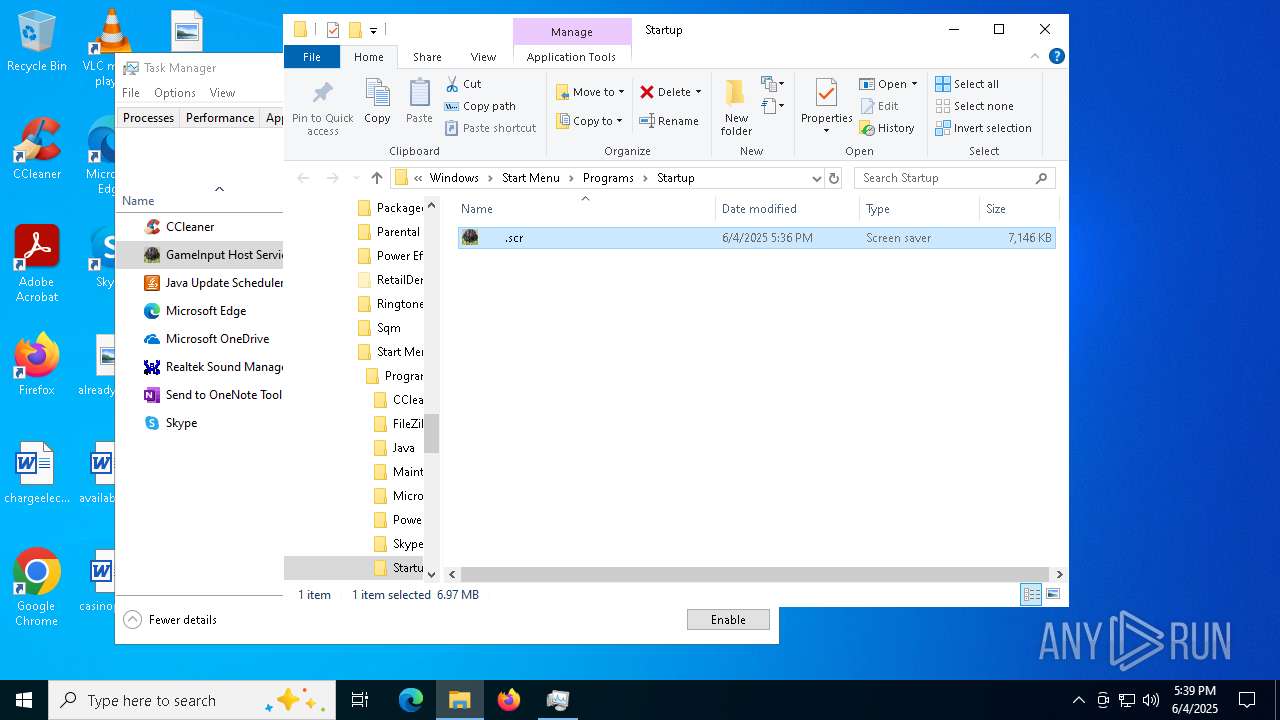
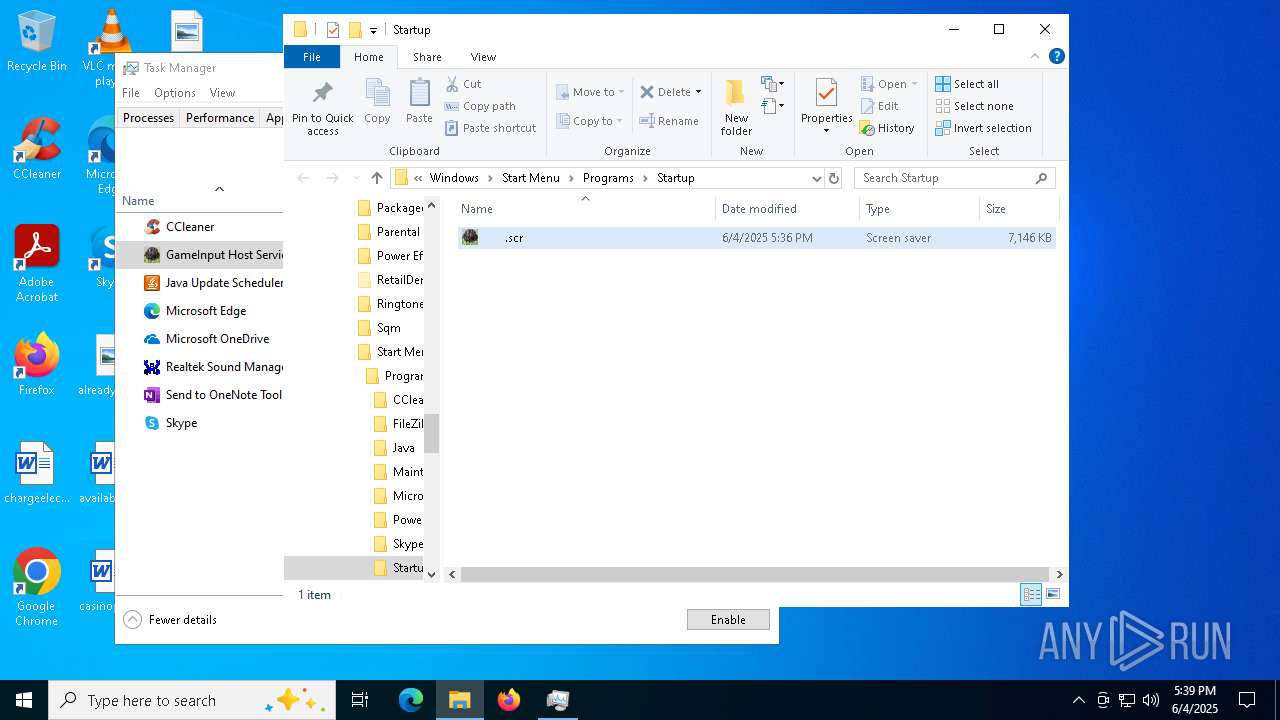
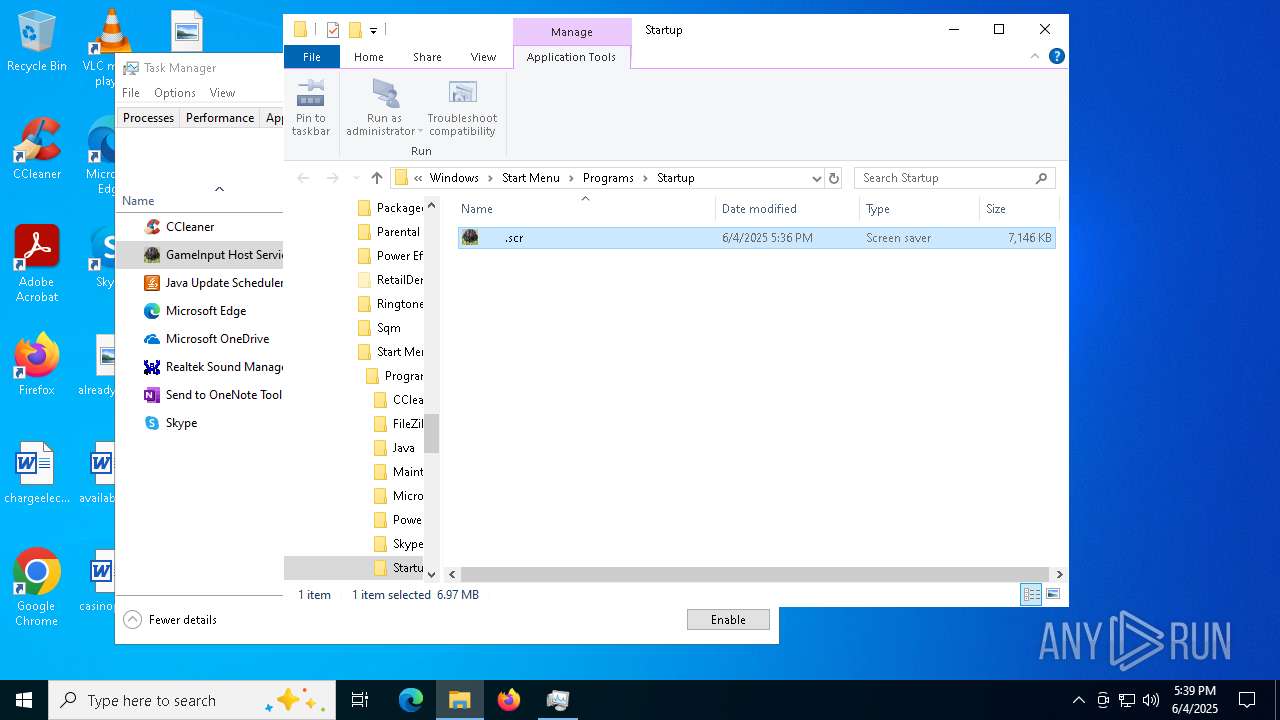
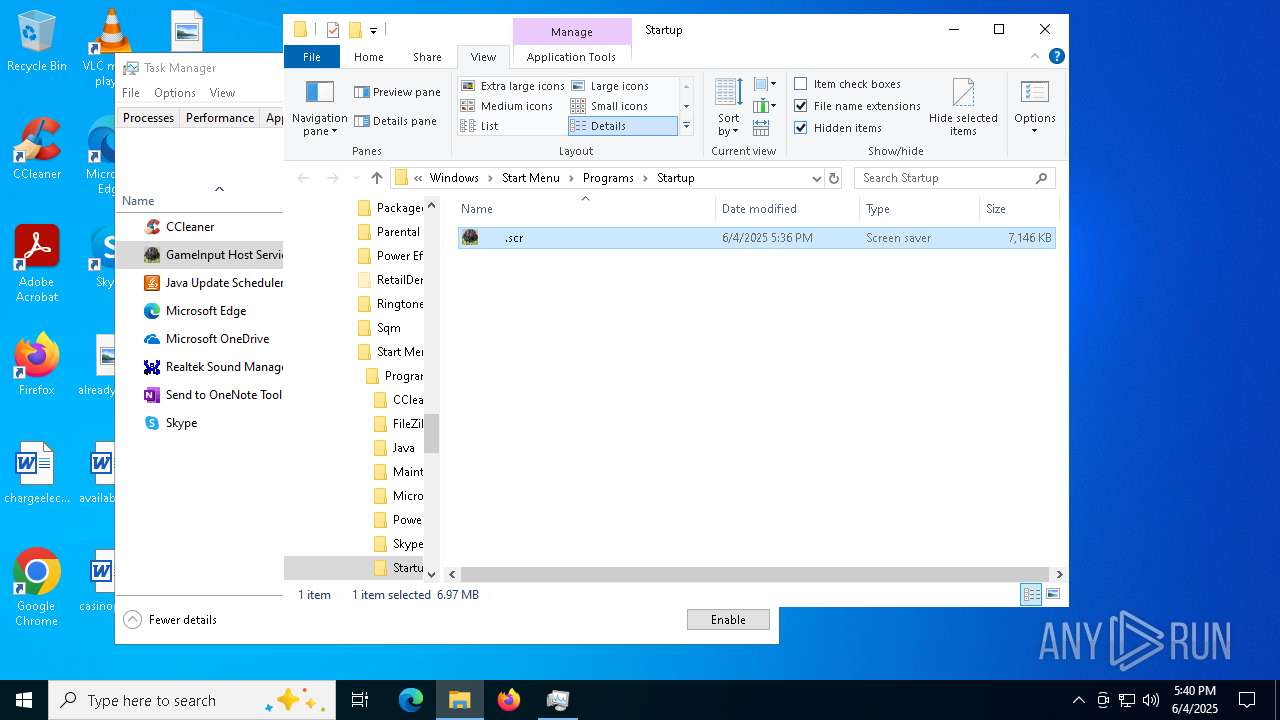
Create files in the Startup directory
- cs2.exe (PID: 1072)
Steals credentials from Web Browsers
- cs2.exe (PID: 1072)
Actions looks like stealing of personal data
- cs2.exe (PID: 1072)
Bypass execution policy to execute commands
- powershell.exe (PID: 7436)
- powershell.exe (PID: 6384)
- powershell.exe (PID: 1812)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 5324)
- cmd.exe (PID: 6708)
- cmd.exe (PID: 7196)
Resets Windows Defender malware definitions to the base version
- MpCmdRun.exe (PID: 6248)
- MpCmdRun.exe (PID: 8056)
- MpCmdRun.exe (PID: 5944)
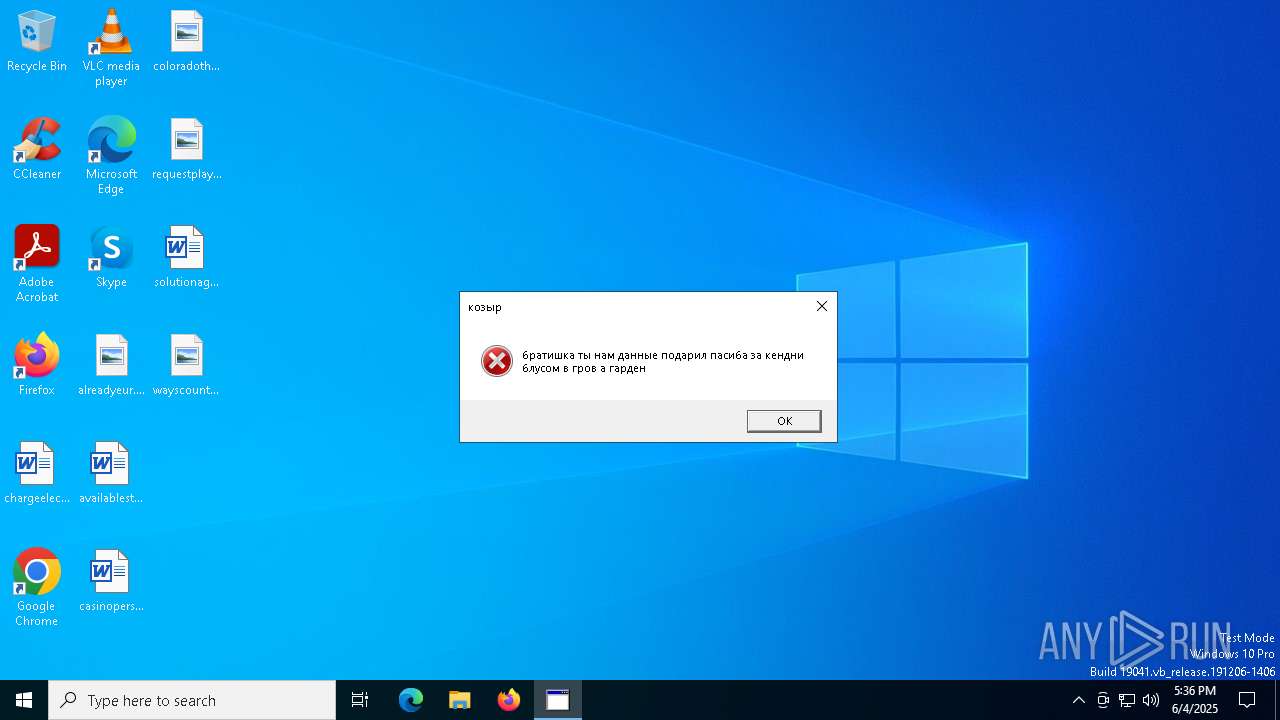
Steals Growtopia credentials and data (YARA)
- cs2.exe (PID: 1072)
UMBRALSTEALER has been detected (YARA)
- cs2.exe (PID: 1072)
Stealers network behavior
- cs2.exe (PID: 1072)
BLANKGRABBER has been detected (SURICATA)
- cs2.exe (PID: 1072)
- .scr (PID: 6004)
- .scr (PID: 7080)
Starts CMD.EXE for self-deleting
- cs2.exe (PID: 1072)
DISCORDGRABBER has been detected (YARA)
- cs2.exe (PID: 1072)
SUSPICIOUS
Process drops legitimate windows executable
- cs2.exe (PID: 7316)
- cs2.exe (PID: 7000)
- cs2.exe (PID: 1072)
- .scr (PID: 5468)
- .scr (PID: 7644)
Starts a Microsoft application from unusual location
- cs2.exe (PID: 7316)
- cs2.exe (PID: 5304)
- cs2.exe (PID: 7000)
- cs2.exe (PID: 1072)
The process drops C-runtime libraries
- cs2.exe (PID: 7316)
- cs2.exe (PID: 7000)
- .scr (PID: 5468)
- .scr (PID: 7644)
Application launched itself
- cs2.exe (PID: 7316)
- cs2.exe (PID: 5304)
- cs2.exe (PID: 7000)
- .scr (PID: 5468)
- .scr (PID: 7644)
Executable content was dropped or overwritten
- cs2.exe (PID: 7316)
- cs2.exe (PID: 7000)
- cs2.exe (PID: 1072)
- csc.exe (PID: 6564)
- .scr (PID: 5468)
- csc.exe (PID: 8096)
- .scr (PID: 7644)
- csc.exe (PID: 6432)
Process drops python dynamic module
- cs2.exe (PID: 7316)
- cs2.exe (PID: 7000)
- .scr (PID: 5468)
- .scr (PID: 7644)
Reads the date of Windows installation
- cs2.exe (PID: 5304)
Reads security settings of Internet Explorer
- cs2.exe (PID: 5304)
Found strings related to reading or modifying Windows Defender settings
- cs2.exe (PID: 1072)
- .scr (PID: 6004)
- .scr (PID: 7080)
Starts CMD.EXE for commands execution
- cs2.exe (PID: 1072)
- .scr (PID: 6004)
- .scr (PID: 7080)
Script disables Windows Defender's real-time protection
- cmd.exe (PID: 7492)
- cmd.exe (PID: 4476)
- cmd.exe (PID: 7472)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7492)
- cmd.exe (PID: 7888)
- cmd.exe (PID: 6540)
- cmd.exe (PID: 660)
- cmd.exe (PID: 5324)
- cmd.exe (PID: 3868)
- cmd.exe (PID: 8072)
- cmd.exe (PID: 5568)
- cmd.exe (PID: 6816)
- cmd.exe (PID: 4476)
- cmd.exe (PID: 776)
- cmd.exe (PID: 6708)
- cmd.exe (PID: 6428)
- cmd.exe (PID: 7436)
- cmd.exe (PID: 7084)
- cmd.exe (PID: 6340)
- cmd.exe (PID: 6184)
- cmd.exe (PID: 7136)
- cmd.exe (PID: 7472)
- cmd.exe (PID: 3888)
- cmd.exe (PID: 7196)
- cmd.exe (PID: 5480)
- cmd.exe (PID: 5540)
- cmd.exe (PID: 4876)
- cmd.exe (PID: 3576)
Script disables Windows Defender's IPS
- cmd.exe (PID: 7492)
- cmd.exe (PID: 4476)
- cmd.exe (PID: 7472)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 7888)
- cmd.exe (PID: 6540)
- cmd.exe (PID: 776)
- cmd.exe (PID: 7136)
Executes JavaScript directly as a command
- cmd.exe (PID: 3872)
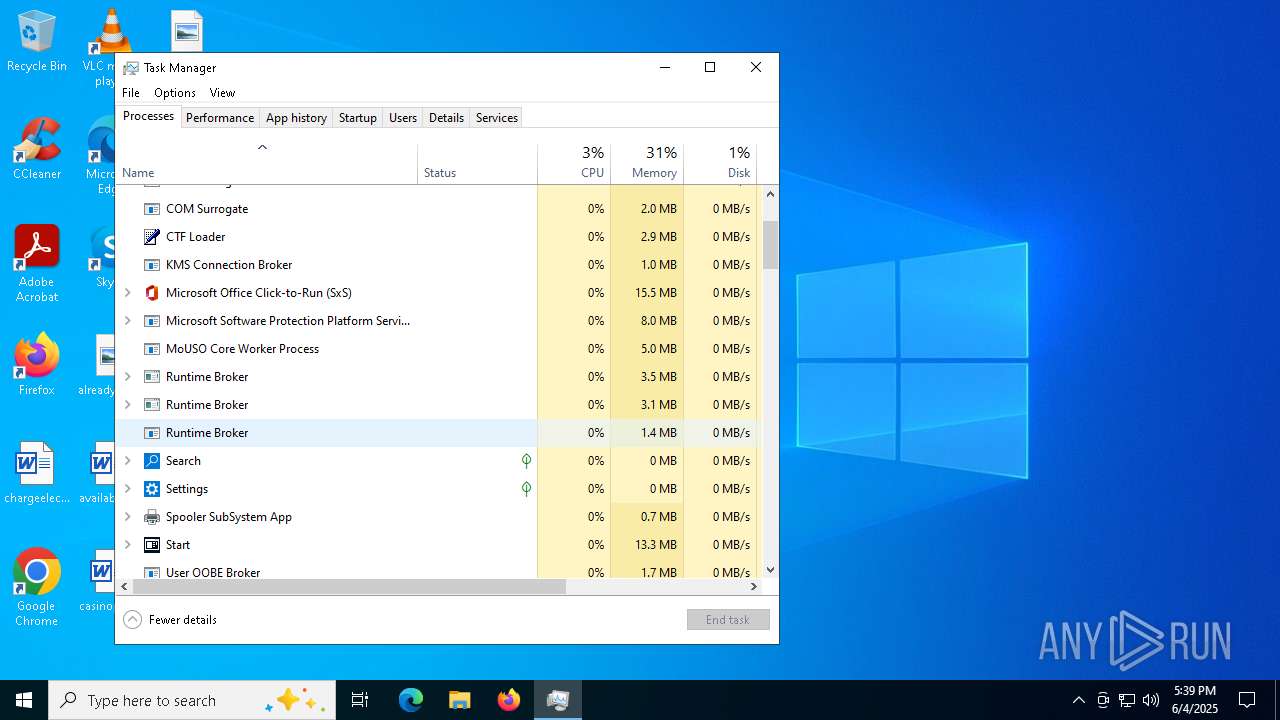
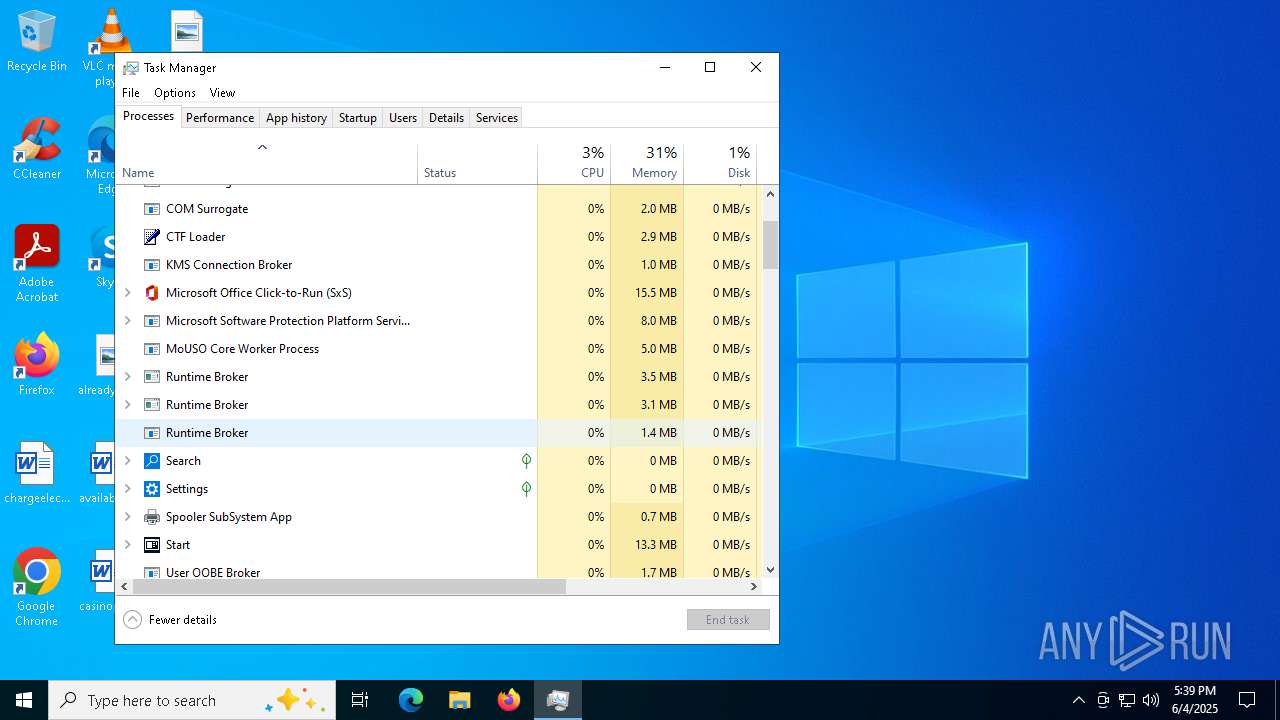
Get information on the list of running processes
- cmd.exe (PID: 4228)
- cmd.exe (PID: 6576)
- cs2.exe (PID: 1072)
- cmd.exe (PID: 2504)
- cmd.exe (PID: 6044)
- .scr (PID: 6004)
- cmd.exe (PID: 5928)
- cmd.exe (PID: 7100)
- cmd.exe (PID: 6204)
- cmd.exe (PID: 7116)
- cmd.exe (PID: 6432)
- .scr (PID: 7080)
- cmd.exe (PID: 7672)
- cmd.exe (PID: 6976)
- cmd.exe (PID: 1032)
- cmd.exe (PID: 7268)
- cmd.exe (PID: 7016)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 4756)
- cmd.exe (PID: 4608)
- cmd.exe (PID: 444)
- cmd.exe (PID: 6236)
- cmd.exe (PID: 6272)
- cmd.exe (PID: 6916)
- cmd.exe (PID: 7628)
- cmd.exe (PID: 4600)
- cmd.exe (PID: 2964)
Checks for external IP
- svchost.exe (PID: 2196)
- cs2.exe (PID: 1072)
- svchost.exe (PID: 2184)
- .scr (PID: 6004)
- .scr (PID: 7080)
Uses WMIC.EXE to obtain a list of video controllers
- cmd.exe (PID: 1168)
- cmd.exe (PID: 7676)
- cmd.exe (PID: 7496)
- cmd.exe (PID: 6852)
- cmd.exe (PID: 6952)
- cmd.exe (PID: 6328)
- cmd.exe (PID: 776)
- cmd.exe (PID: 7216)
- cmd.exe (PID: 4644)
Accesses video controller name via WMI (SCRIPT)
- WMIC.exe (PID: 8104)
- WMIC.exe (PID: 8048)
- WMIC.exe (PID: 6668)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 4040)
Accesses product unique identifier via WMI (SCRIPT)
- WMIC.exe (PID: 7584)
- WMIC.exe (PID: 644)
Uses SYSTEMINFO.EXE to read the environment
- cmd.exe (PID: 7344)
- cmd.exe (PID: 3996)
- cmd.exe (PID: 2124)
Uses NETSH.EXE to obtain data on the network
- cmd.exe (PID: 7968)
- cmd.exe (PID: 6276)
- cmd.exe (PID: 6460)
Starts application with an unusual extension
- cmd.exe (PID: 1760)
- cmd.exe (PID: 1184)
- cmd.exe (PID: 8008)
- cmd.exe (PID: 3008)
- cmd.exe (PID: 2692)
- cmd.exe (PID: 7456)
- .scr (PID: 5468)
- cmd.exe (PID: 6360)
- cmd.exe (PID: 7324)
- cmd.exe (PID: 7616)
- cmd.exe (PID: 7832)
- cmd.exe (PID: 7532)
- cmd.exe (PID: 7700)
- .scr (PID: 7644)
- cmd.exe (PID: 7024)
- cmd.exe (PID: 1996)
- cmd.exe (PID: 3900)
- cmd.exe (PID: 4308)
- cmd.exe (PID: 5552)
- cmd.exe (PID: 4060)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 5324)
- cmd.exe (PID: 6708)
- cmd.exe (PID: 7196)
Accesses antivirus product name via WMI (SCRIPT)
- WMIC.exe (PID: 4188)
BASE64 encoded PowerShell command has been detected
- cmd.exe (PID: 5324)
- cmd.exe (PID: 6708)
- cmd.exe (PID: 7196)
Base64-obfuscated command line is found
- cmd.exe (PID: 5324)
- cmd.exe (PID: 6708)
- cmd.exe (PID: 7196)
CSC.EXE is used to compile C# code
- csc.exe (PID: 6564)
- csc.exe (PID: 8096)
- csc.exe (PID: 6432)
The executable file from the user directory is run by the CMD process
- rar.exe (PID: 4120)
- rar.exe (PID: 7800)
- rar.exe (PID: 5488)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 7988)
- cmd.exe (PID: 7732)
- cmd.exe (PID: 6928)
Accesses operating system name via WMI (SCRIPT)
- WMIC.exe (PID: 8000)
Captures screenshot (POWERSHELL)
- powershell.exe (PID: 7436)
Possible usage of Discord/Telegram API has been detected (YARA)
- cs2.exe (PID: 1072)
There is functionality for taking screenshot (YARA)
- cs2.exe (PID: 1072)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 7788)
- cmd.exe (PID: 7976)
- cmd.exe (PID: 1248)
Hides command output
- cmd.exe (PID: 7200)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 7200)
The process executes via Task Scheduler
- PLUGScheduler.exe (PID: 780)
INFO
The sample compiled with english language support
- cs2.exe (PID: 7316)
- cs2.exe (PID: 7000)
- cs2.exe (PID: 1072)
- .scr (PID: 5468)
- .scr (PID: 7644)
Checks supported languages
- cs2.exe (PID: 7316)
- cs2.exe (PID: 5304)
- cs2.exe (PID: 7000)
- cs2.exe (PID: 1072)
- tree.com (PID: 6644)
- tree.com (PID: 6620)
- tree.com (PID: 4172)
- tree.com (PID: 4428)
- csc.exe (PID: 6564)
- cvtres.exe (PID: 7356)
- tree.com (PID: 7724)
- tree.com (PID: 5776)
- rar.exe (PID: 4120)
- MpCmdRun.exe (PID: 6248)
Reads the computer name
- cs2.exe (PID: 7316)
- cs2.exe (PID: 5304)
- cs2.exe (PID: 7000)
- cs2.exe (PID: 1072)
- MpCmdRun.exe (PID: 6248)
Create files in a temporary directory
- cs2.exe (PID: 7316)
- cs2.exe (PID: 7000)
- cs2.exe (PID: 1072)
- csc.exe (PID: 6564)
- cvtres.exe (PID: 7356)
- MpCmdRun.exe (PID: 6248)
- rar.exe (PID: 4120)
Process checks computer location settings
- cs2.exe (PID: 5304)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 8048)
- WMIC.exe (PID: 7584)
- WMIC.exe (PID: 8104)
- WMIC.exe (PID: 4188)
- WMIC.exe (PID: 8000)
- WMIC.exe (PID: 2392)
- WMIC.exe (PID: 644)
- WMIC.exe (PID: 6668)
Launching a file from the Startup directory
- cs2.exe (PID: 1072)
Creates files in the program directory
- cs2.exe (PID: 1072)
Reads Internet Explorer settings
- mshta.exe (PID: 2660)
The Powershell gets current clipboard
- powershell.exe (PID: 6660)
- powershell.exe (PID: 6864)
- powershell.exe (PID: 6392)
Checks the directory tree
- tree.com (PID: 6644)
- tree.com (PID: 6620)
- tree.com (PID: 4172)
- tree.com (PID: 4428)
- tree.com (PID: 7724)
- tree.com (PID: 5776)
- tree.com (PID: 7140)
- tree.com (PID: 7472)
- tree.com (PID: 7592)
- tree.com (PID: 7676)
- tree.com (PID: 7796)
- tree.com (PID: 7900)
- tree.com (PID: 2704)
- tree.com (PID: 784)
- tree.com (PID: 6924)
- tree.com (PID: 5132)
- tree.com (PID: 6256)
- tree.com (PID: 952)
Reads the machine GUID from the registry
- csc.exe (PID: 6564)
- rar.exe (PID: 4120)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7960)
- powershell.exe (PID: 7544)
- powershell.exe (PID: 6496)
- powershell.exe (PID: 7468)
- powershell.exe (PID: 2392)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 2392)
- powershell.exe (PID: 7544)
- powershell.exe (PID: 7960)
Displays MAC addresses of computer network adapters
- getmac.exe (PID: 5540)
- getmac.exe (PID: 6800)
- getmac.exe (PID: 6620)
PyInstaller has been detected (YARA)
- cs2.exe (PID: 7000)
- cs2.exe (PID: 1072)
Attempting to use instant messaging service
- svchost.exe (PID: 2196)
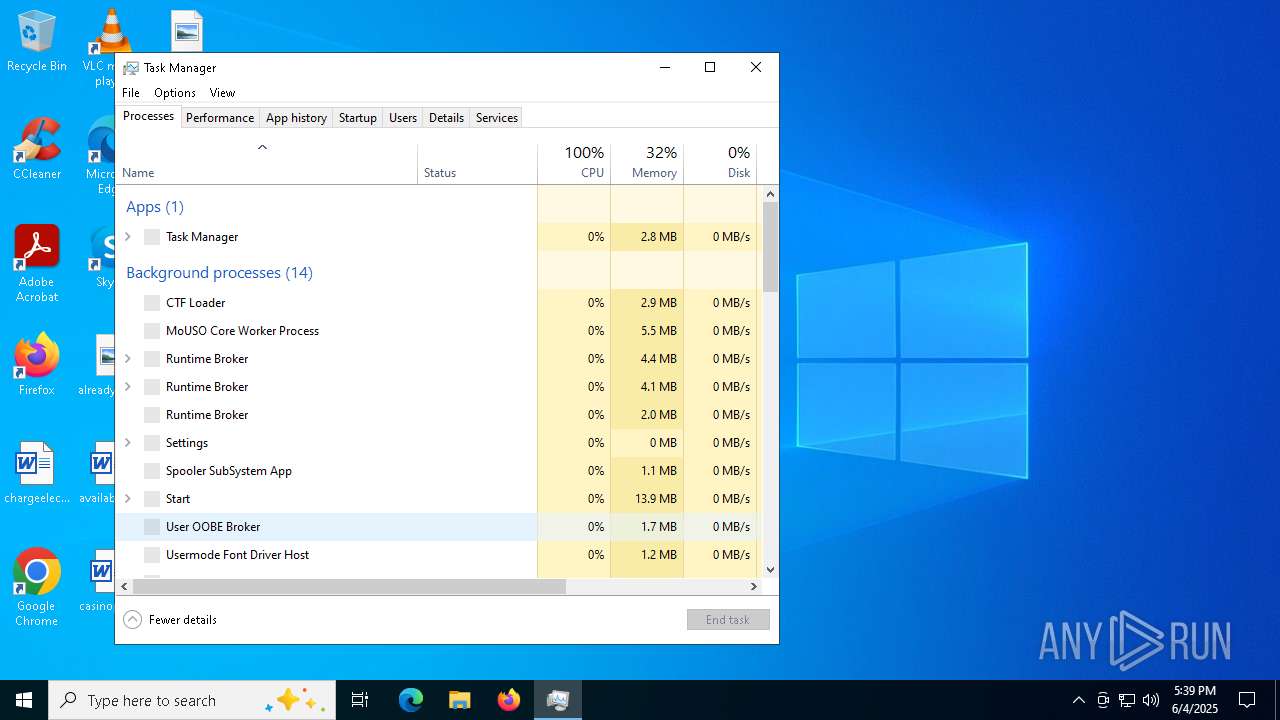
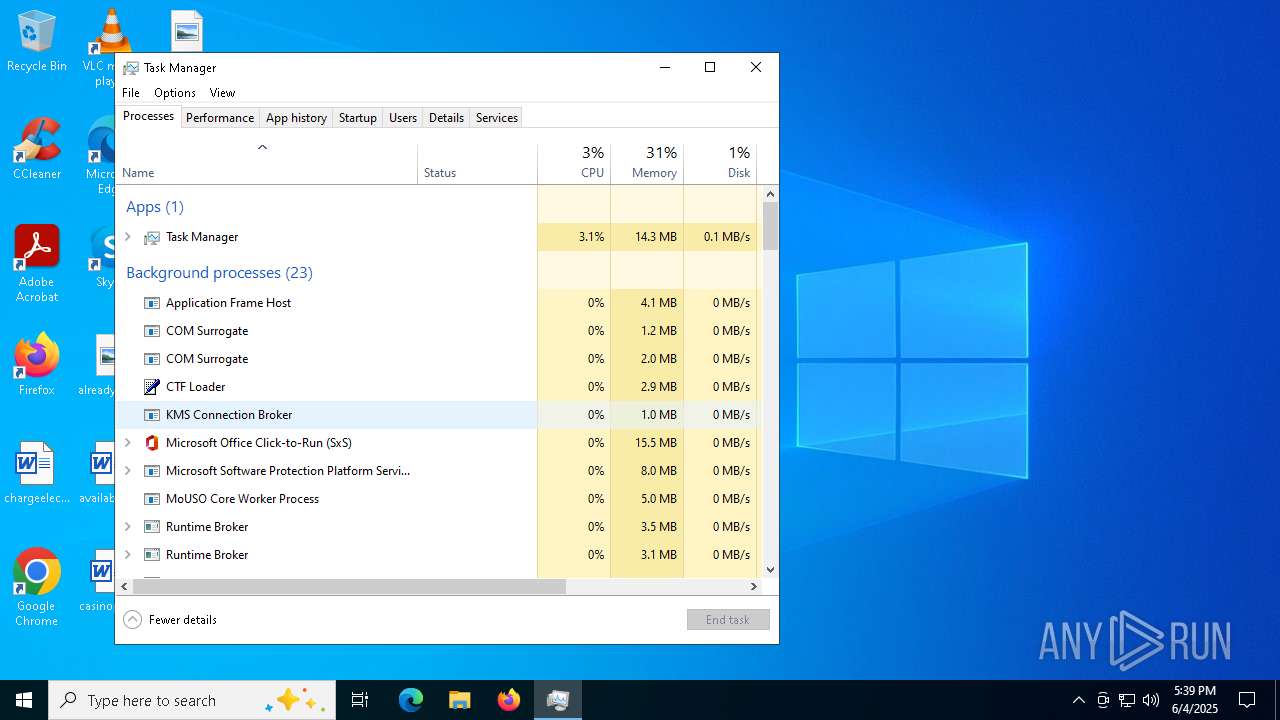
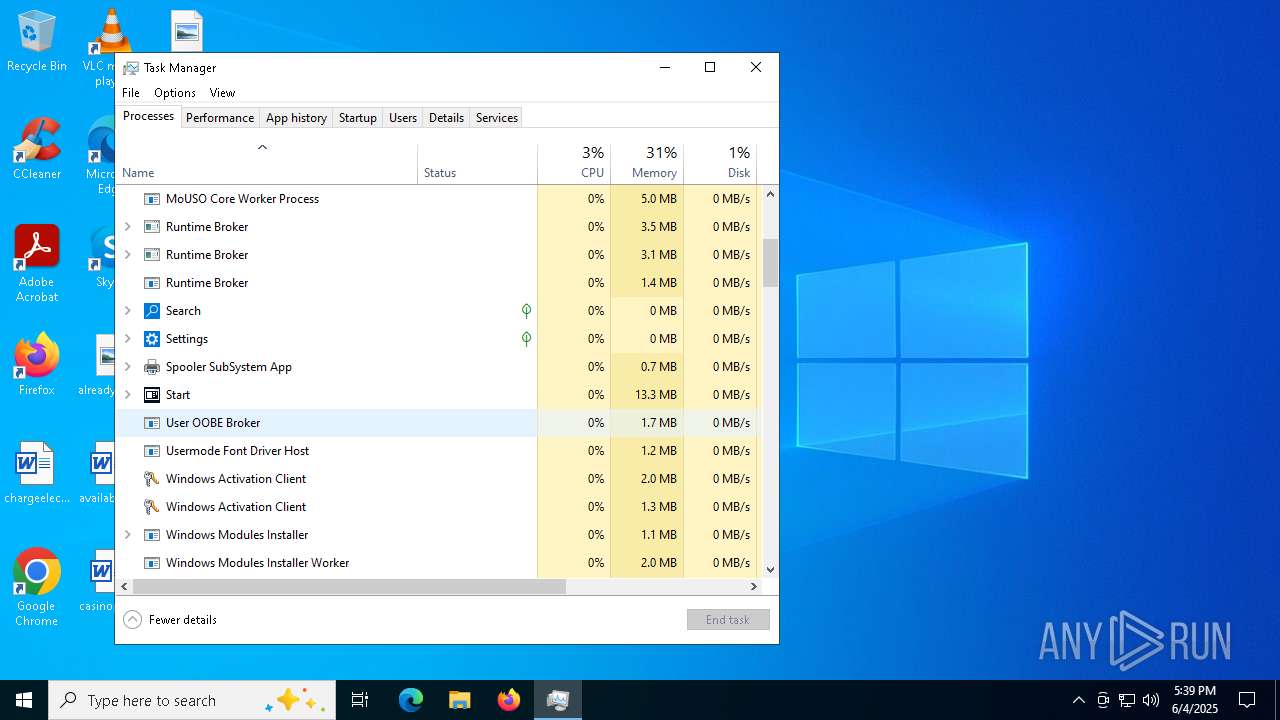
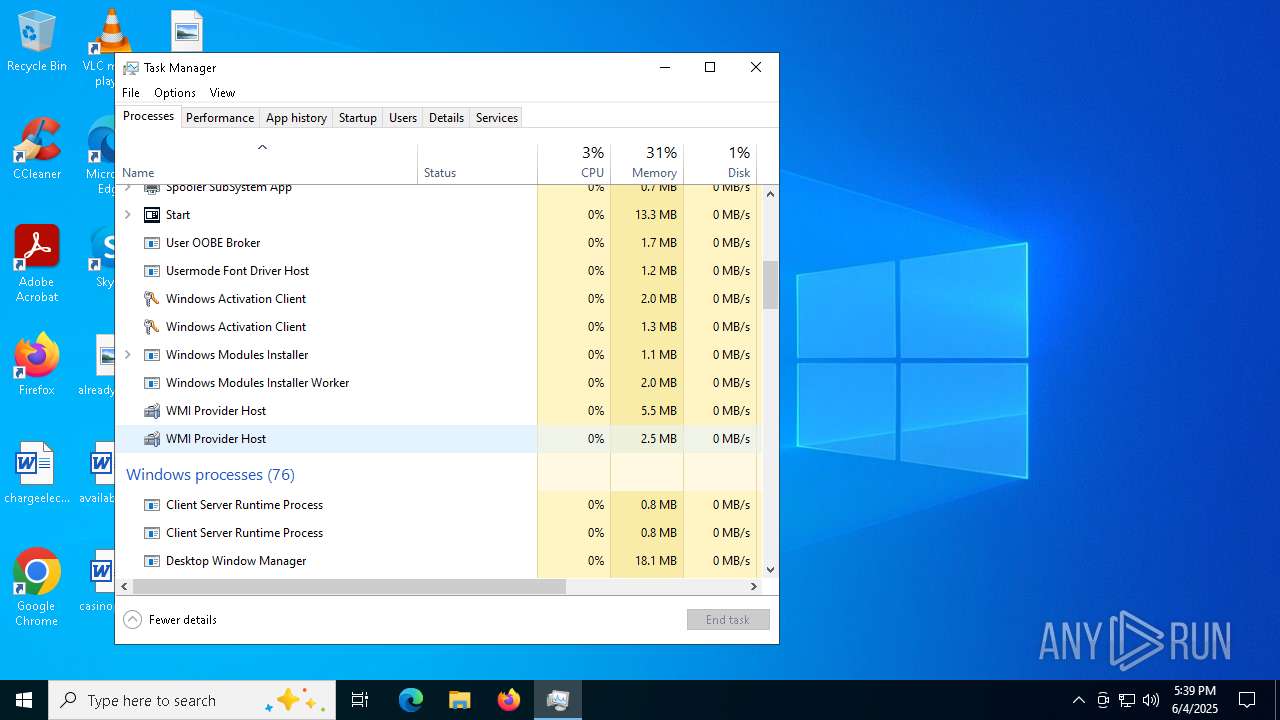
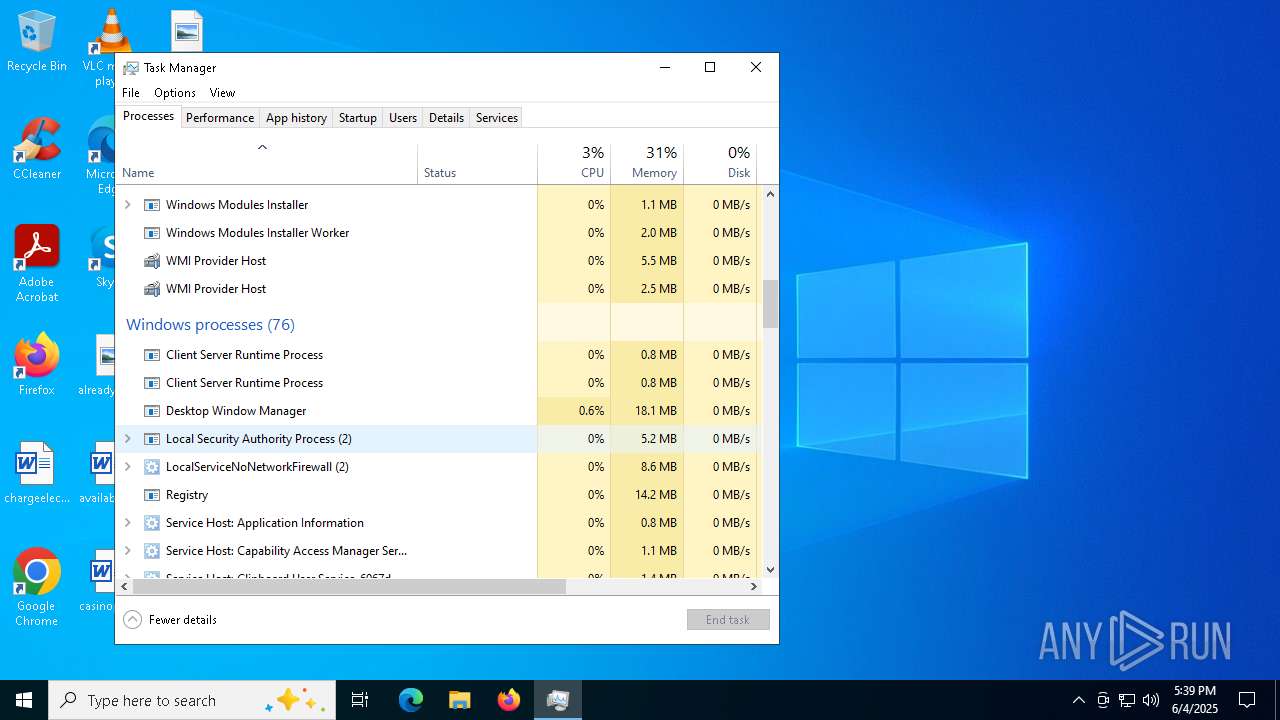
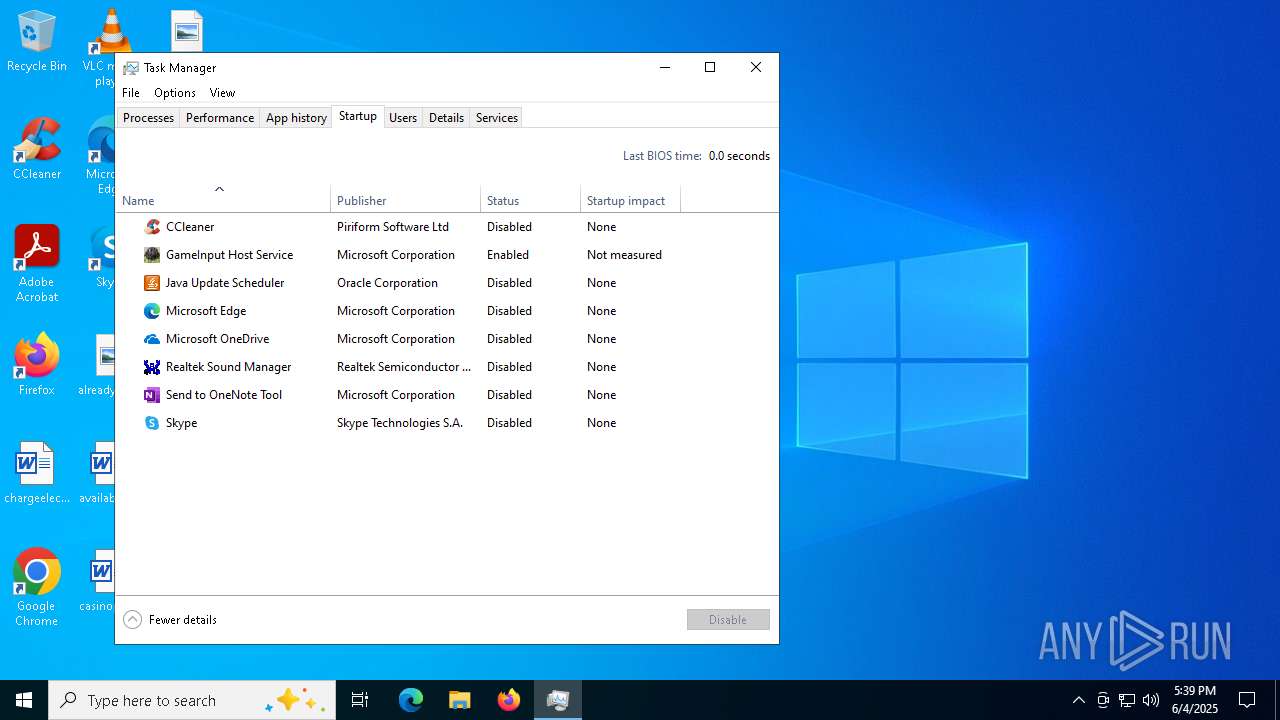
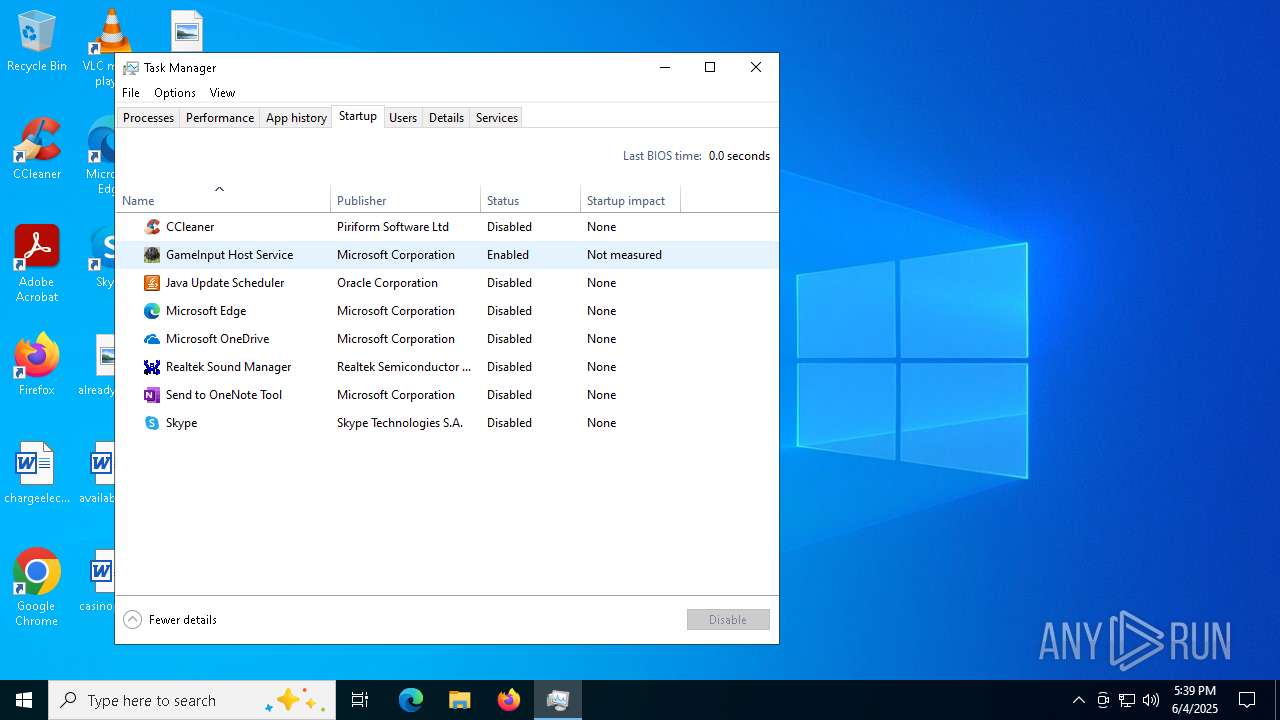
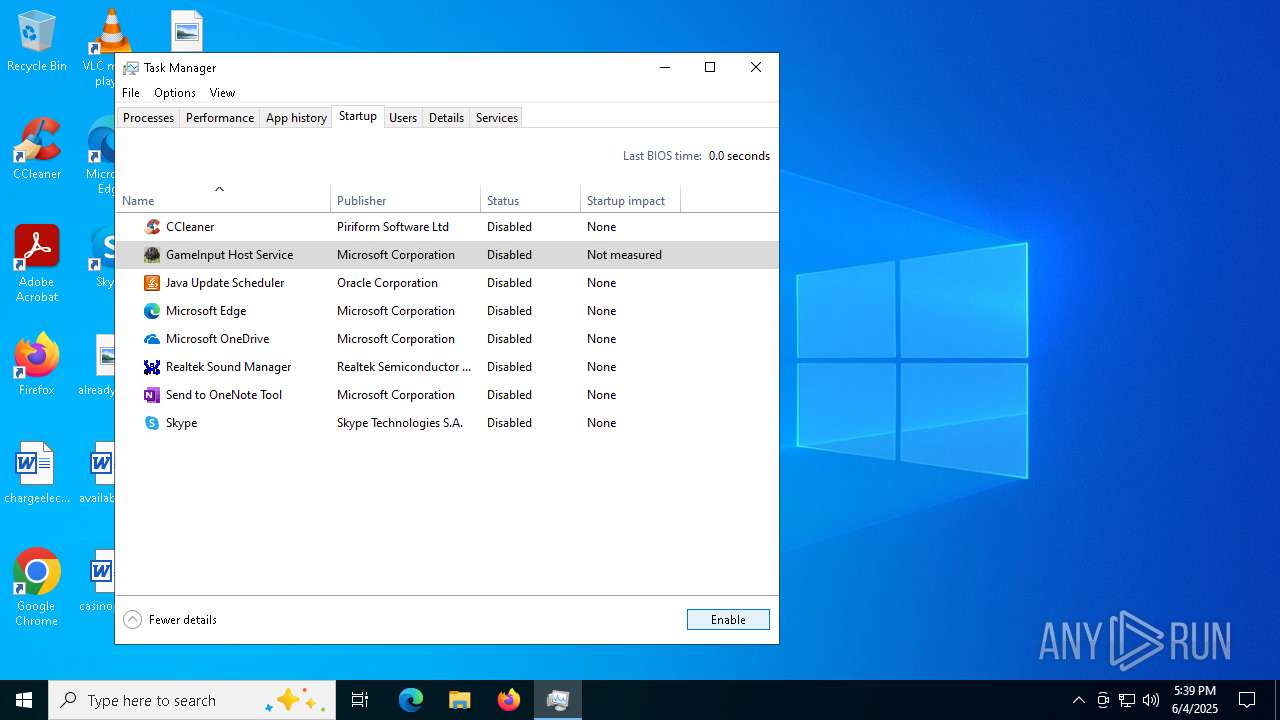
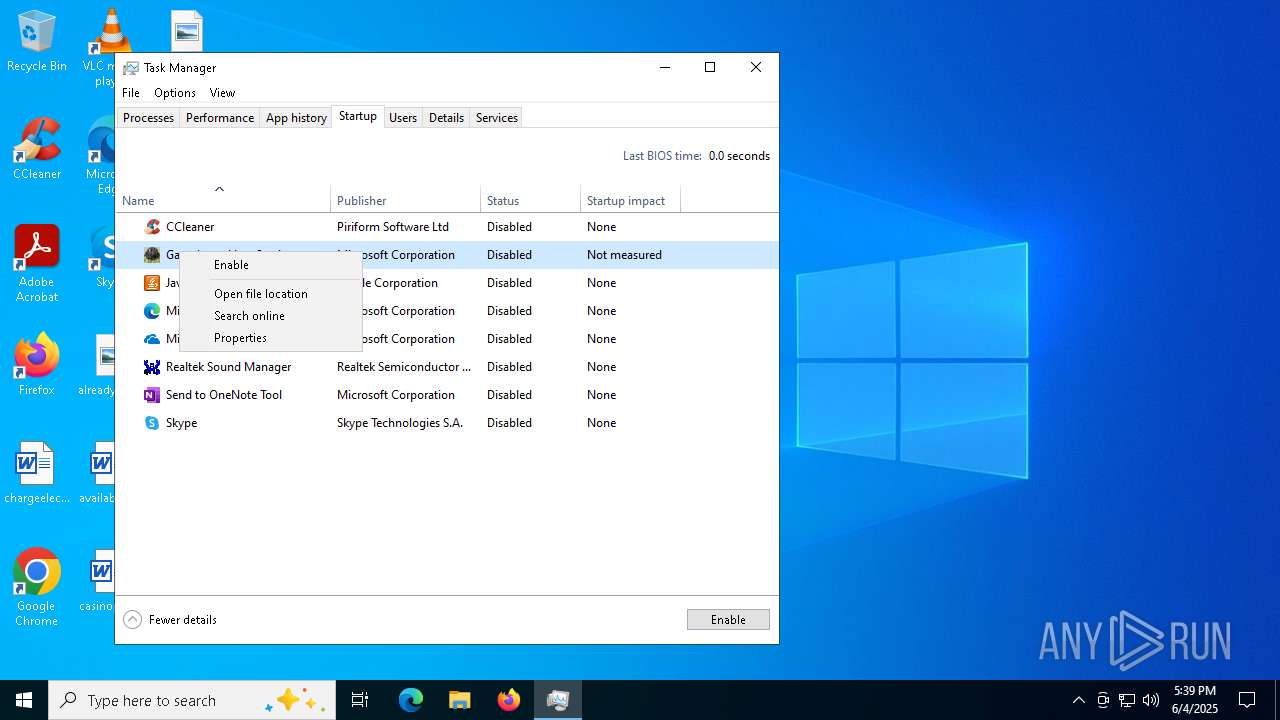
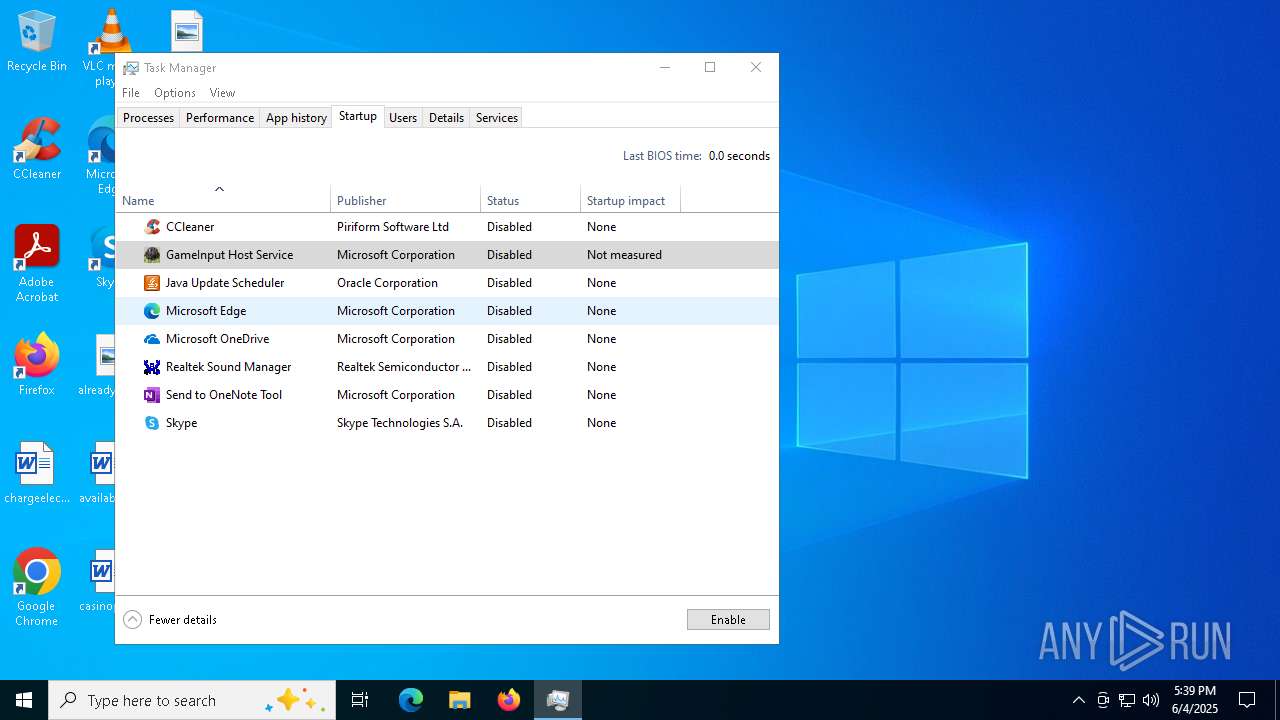
Manual execution by a user
- .scr (PID: 5468)
- Taskmgr.exe (PID: 7288)
- Taskmgr.exe (PID: 7304)
- .scr (PID: 7644)
Application launched itself
- msedge.exe (PID: 7316)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
ims-api
(PID) Process(1072) cs2.exe
Discord-Webhook-Tokens (1)1379371262014656604/b5R5D7QWcnfgPGJLgllZuHLcbDrAdhbAjcYFqqA5Vh9qfZHm8nZLnsHe-i2wPf2TP2FL
Discord-Info-Links
1379371262014656604/b5R5D7QWcnfgPGJLgllZuHLcbDrAdhbAjcYFqqA5Vh9qfZHm8nZLnsHe-i2wPf2TP2FL
Get Webhook Infohttps://discord.com/api/webhooks/1379371262014656604/b5R5D7QWcnfgPGJLgllZuHLcbDrAdhbAjcYFqqA5Vh9qfZHm8nZLnsHe-i2wPf2TP2FL
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:06:03 08:11:50+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.43 |
| CodeSize: | 173568 |
| InitializedDataSize: | 149504 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xce30 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.2309.19041.5794 |
| ProductVersionNumber: | 0.2309.19041.5794 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | GameInput Host Service |
| FileVersion: | 0.2309.19041.5794 |
| InternalName: | GameInputHostService |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | GameInputSvc.exe |
| ProductName: | Microsoft GameInput |
| ProductVersion: | 0.2309.19041.5794 |
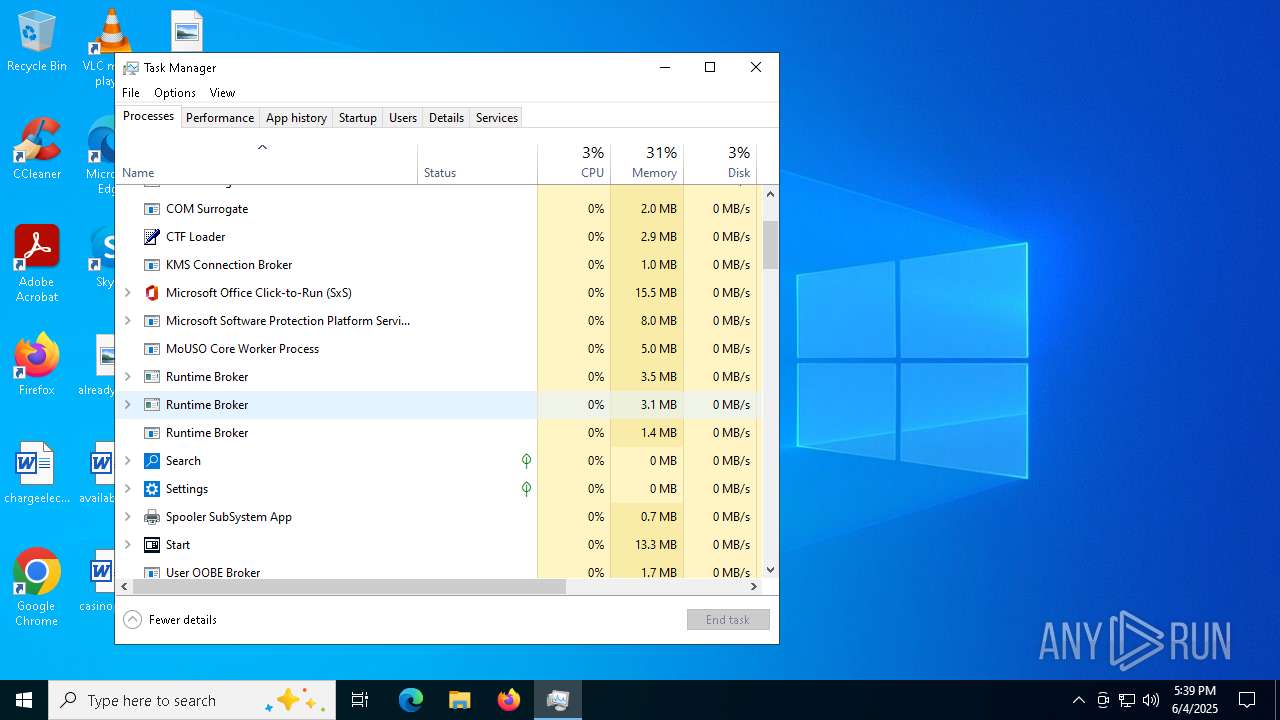
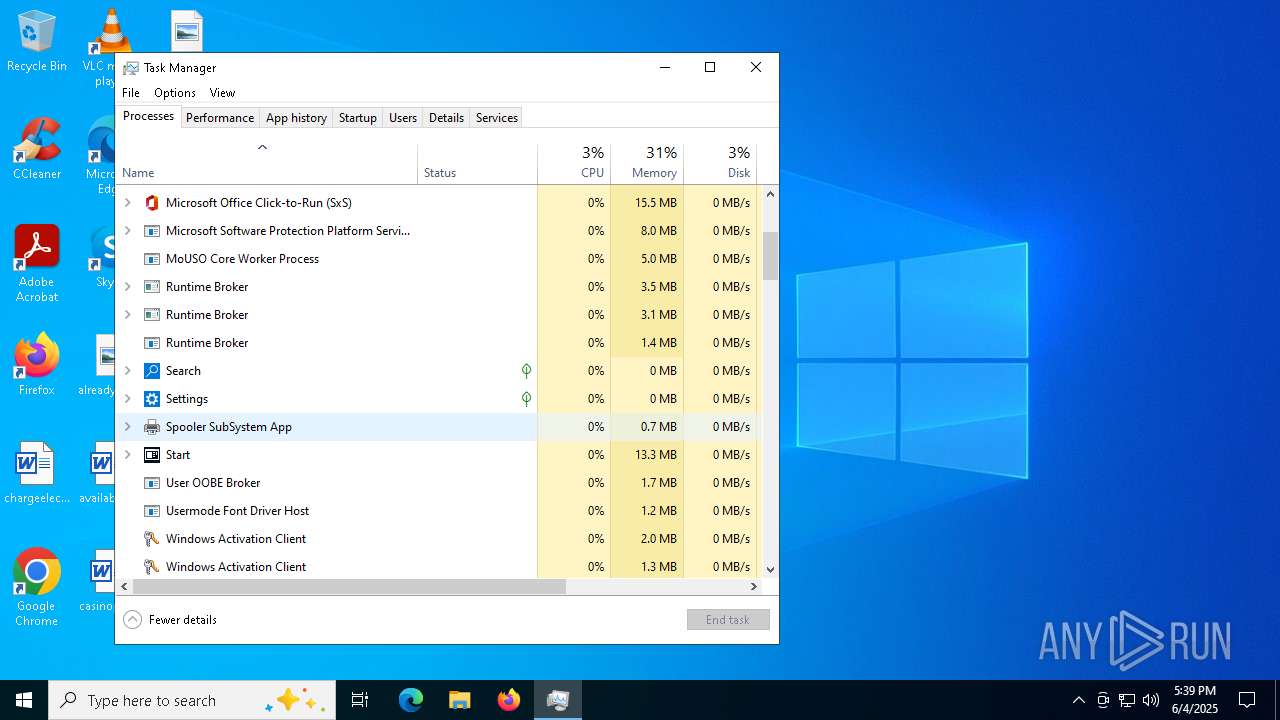
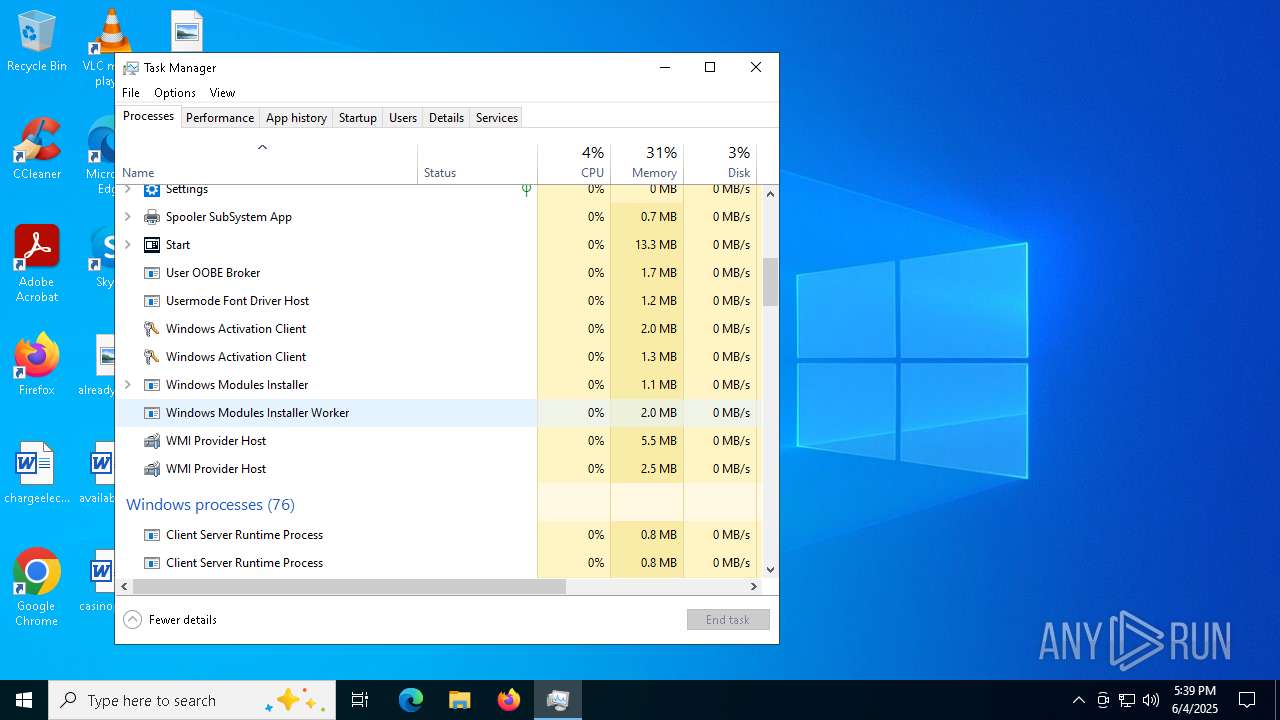
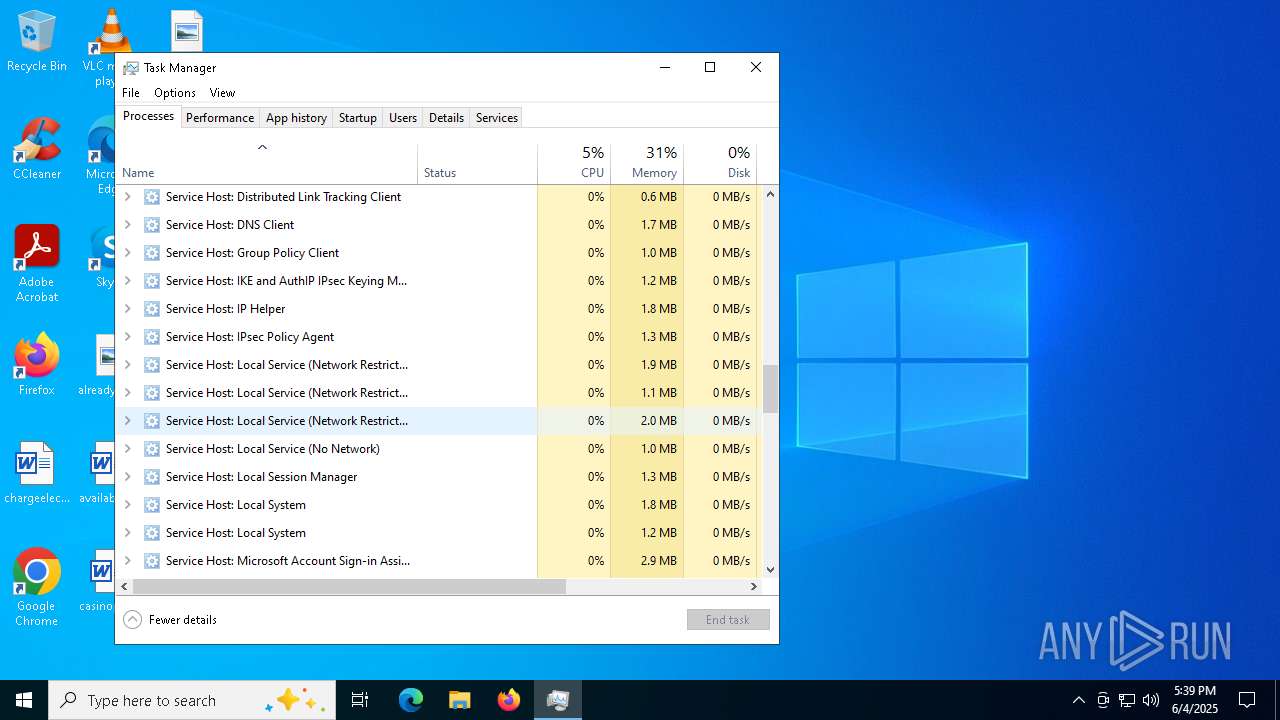
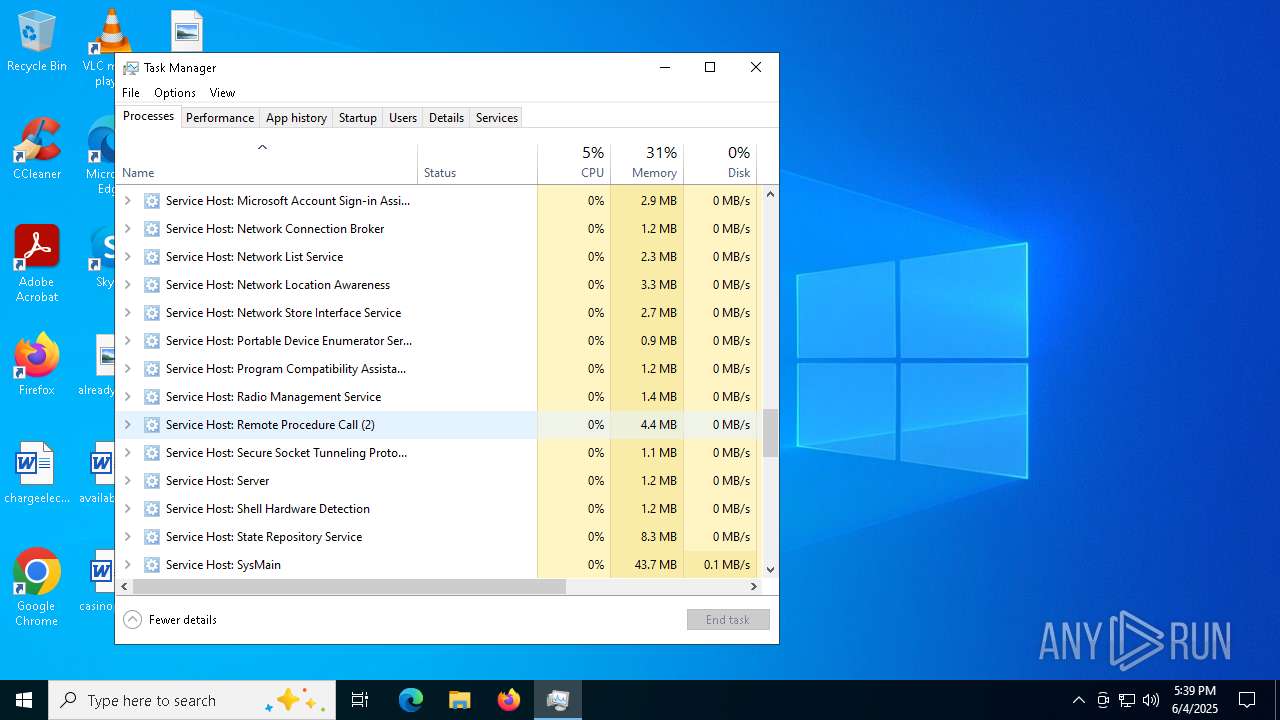
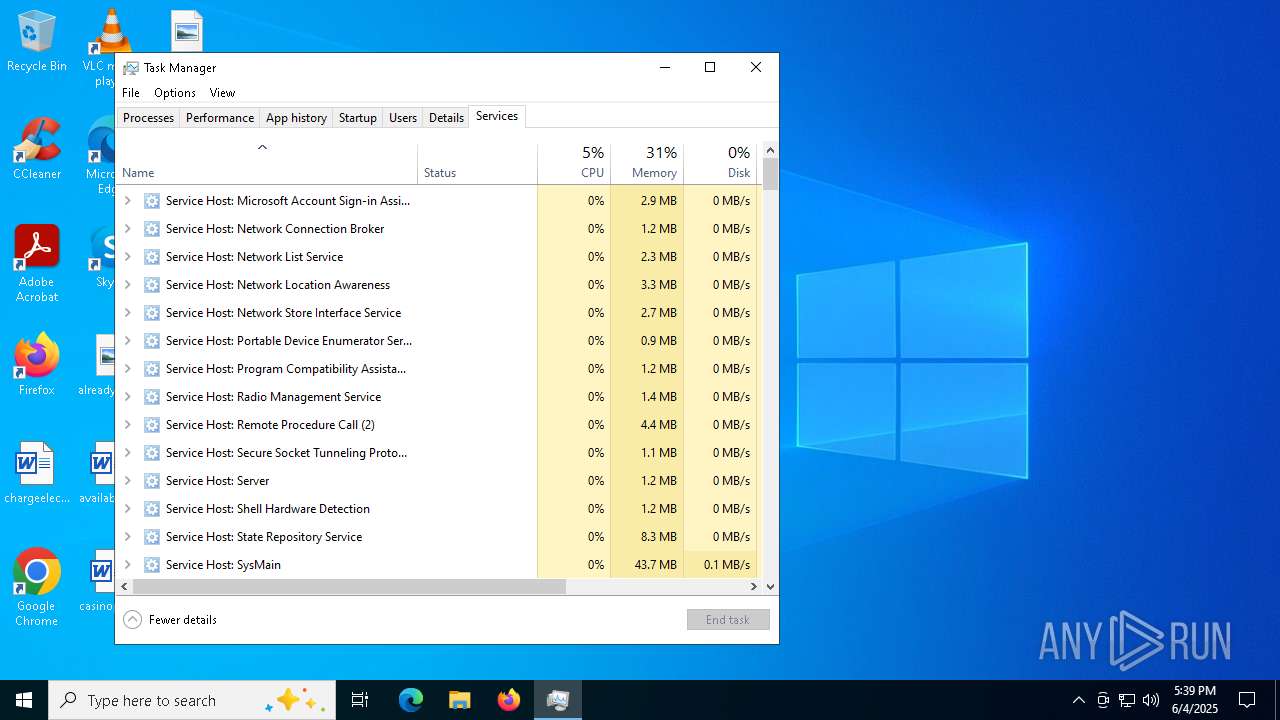
Total processes
598
Monitored processes
334
Malicious processes
21
Suspicious processes
9
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 232 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 240 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 444 | C:\WINDOWS\system32\cmd.exe /c "wmic csproduct get uuid" | C:\Windows\System32\cmd.exe | — | cs2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 552 | wmic csproduct get uuid | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 556 | powershell Get-ItemPropertyValue -Path HKCU:SOFTWARE\Roblox\RobloxStudioBrowser\roblox.com -Name .ROBLOSECURITY | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 632 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 644 | wmic csproduct get uuid | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 660 | C:\WINDOWS\system32\cmd.exe /c "powershell Get-Clipboard" | C:\Windows\System32\cmd.exe | — | cs2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 660 | netsh wlan show profile | C:\Windows\System32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 736 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
156 531
Read events
156 513
Write events
17
Delete events
1
Modification events
| (PID) Process: | (1072) cs2.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Multimedia\DrawDib |
| Operation: | write | Name: | 1280x720x32(BGR 0) |
Value: 31,31,31,31 | |||
| (PID) Process: | (7204) TiWorker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Component Based Servicing |
| Operation: | write | Name: | SessionIdHigh |
Value: 31184247 | |||
| (PID) Process: | (7204) TiWorker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Component Based Servicing |
| Operation: | write | Name: | SessionIdLow |
Value: | |||
| (PID) Process: | (7316) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7316) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7316) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7316) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
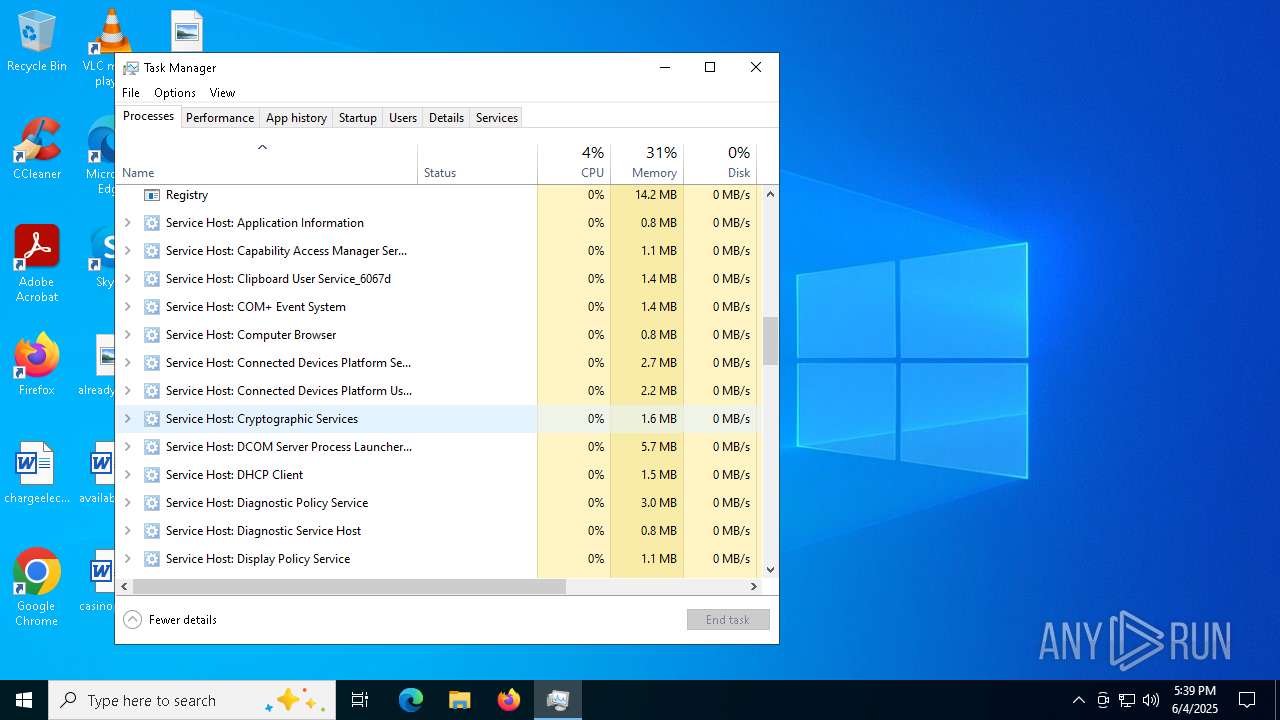
| (PID) Process: | (7288) Taskmgr.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\TaskManager |
| Operation: | delete value | Name: | Preferences |
Value: | |||
| (PID) Process: | (7288) Taskmgr.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\TaskManager |
| Operation: | write | Name: | Preferences |
Value: 0D00000060000000600000006800000068000000E3010000DC010000000001000000008000000080D8010080DF010080000100016B00000034000000130300008C020000E80300000000000000000000000000000F000000010000000000000058AAF298F67F00000000000000000000000000002E0100001E0000008990000000000000FF00000001015002000000000D0000000000000098AAF298F67F00000000000000000000FFFFFFFF960000001E0000008B900000010000000000000000101001000000000300000000000000B0AAF298F67F00000000000000000000FFFFFFFF780000001E0000008C900000020000000000000001021200000000000400000000000000C8AAF298F67F00000000000000000000FFFFFFFF960000001E0000008D900000030000000000000000011001000000000200000000000000E8AAF298F67F00000000000000000000FFFFFFFF320000001E0000008A90000004000000000000000008200100000000050000000000000000ABF298F67F00000000000000000000FFFFFFFFC80000001E0000008E90000005000000000000000001100100000000060000000000000028ABF298F67F00000000000000000000FFFFFFFF040100001E0000008F90000006000000000000000001100100000000070000000000000050ABF298F67F00000000000000000000FFFFFFFF49000000490000009090000007000000000000000004250000000000080000000000000080AAF298F67F00000000000000000000FFFFFFFF49000000490000009190000008000000000000000004250000000000090000000000000070ABF298F67F00000000000000000000FFFFFFFF490000004900000092900000090000000000000000042508000000000A0000000000000088ABF298F67F00000000000000000000FFFFFFFF4900000049000000939000000A0000000000000000042508000000000B00000000000000A8ABF298F67F00000000000000000000FFFFFFFF490000004900000039A000000B0000000000000000042509000000001C00000000000000C8ABF298F67F00000000000000000000FFFFFFFFC8000000490000003AA000000C0000000000000000011009000000001D00000000000000F0ABF298F67F00000000000000000000FFFFFFFF64000000490000004CA000000D0000000000000000021508000000001E0000000000000010ACF298F67F00000000000000000000FFFFFFFF64000000490000004DA000000E000000000000000002150800000000030000000A000000010000000000000058AAF298F67F0000000000000000000000000000D70000001E0000008990000000000000FF00000001015002000000000400000000000000C8AAF298F67F0000000000000000000001000000960000001E0000008D900000010000000000000001011000000000000300000000000000B0AAF298F67F00000000000000000000FFFFFFFF640000001E0000008C900000020000000000000000021000000000000C0000000000000040ACF298F67F0000000000000000000003000000640000001E00000094900000030000000000000001021000000000000D0000000000000068ACF298F67F00000000000000000000FFFFFFFF640000001E00000095900000040000000000000000011001000000000E0000000000000090ACF298F67F0000000000000000000005000000320000001E00000096900000050000000000000001042001000000000F00000000000000B8ACF298F67F0000000000000000000006000000320000001E00000097900000060000000000000001042001000000001000000000000000D8ACF298F67F0000000000000000000007000000460000001E00000098900000070000000000000001011001000000001100000000000000F8ACF298F67F00000000000000000000FFFFFFFF640000001E0000009990000008000000000000000001100100000000060000000000000028ABF298F67F0000000000000000000009000000040100001E0000008F9000000900000000000000010110010000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000040000000B000000010000000000000058AAF298F67F0000000000000000000000000000D70000001E0000009E90000000000000FF0000000101500200000000120000000000000020ADF298F67F00000000000000000000FFFFFFFF2D0000001E0000009B90000001000000000000000004200100000000140000000000000040ADF298F67F00000000000000000000FFFFFFFF640000001E0000009D90000002000000000000000001100100000000130000000000000068ADF298F67F00000000000000000000FFFFFFFF640000001E0000009C900000030000000000000000011001000000000300000000000000B0AAF298F67F00000000000000000000FFFFFFFF640000001E0000008C90000004000000000000000102100000000000070000000000000050ABF298F67F000000000000000000000500000049000000490000009090000005000000000000000104210000000000080000000000000080AAF298F67F000000000000000000000600000049000000490000009190000006000000000000000104210000000000090000000000000070ABF298F67F0000000000000000000007000000490000004900000092900000070000000000000001042108000000000A0000000000000088ABF298F67F0000000000000000000008000000490000004900000093900000080000000000000001042108000000000B00000000000000A8ABF298F67F0000000000000000000009000000490000004900000039A00000090000000000000001042109000000001C00000000000000C8ABF298F67F000000000000000000000A00000064000000490000003AA000000A00000000000000000110090000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000200000008000000010000000000000058AAF298F67F0000000000000000000000000000C60000001E000000B090000000000000FF0000000101500200000000150000000000000088ADF298F67F00000000000000000000FFFFFFFF6B0000001E000000B1900000010000000000000000042500000000001600000000000000B8ADF298F67F00000000000000000000FFFFFFFF6B0000001E000000B2900000020000000000000000042500000000001800000000000000E0ADF298F67F00000000000000000000FFFFFFFF6B0000001E000000B490000003000000000000000004250000000000170000000000000008AEF298F67F00000000000000000000FFFFFFFF6B0000001E000000B390000004000000000000000004250000000000190000000000000040AEF298F67F00000000000000000000FFFFFFFFA00000001E000000B5900000050000000000000000042001000000001A0000000000000070AEF298F67F00000000000000000000FFFFFFFF7D0000001E000000B6900000060000000000000000042001000000001B00000000000000A0AEF298F67F00000000000000000000FFFFFFFF7D0000001E000000B790000007000000000000000004200100000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000010000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000DA00000000000000000000000000000000000000000000009D200000200000009100000064000000320000006400000050000000320000003200000028000000500000003C0000005000000050000000320000005000000050000000500000005000000050000000500000002800000050000000230000002300000023000000230000005000000050000000500000003200000032000000320000007800000078000000500000003C00000050000000500000009700000032000000780000003200000050000000500000005000000050000000000000000100000002000000030000000400000005000000060000000700000008000000090000000A0000000B0000000C0000000D0000000E0000000F000000100000001100000012000000130000001400000015000000160000001700000018000000190000001A0000001B0000001C0000001D0000001E0000001F000000200000002100000022000000230000002400000025000000260000002700000028000000290000002A0000002B0000002C00000000000000000000001F00000000000000B400000032000000D8000000640000006400000000000000000000000000000000000000000000000000000000000000000000000000000000000000DA000000000000000000000000000000000000009D200000200000009100000064000000320000009700000050000000320000003200000028000000500000003C000000500000005000000032000000500000005000000050000000500000005000000050000000500000002800000050000000230000002300000023000000230000005000000050000000500000003200000032000000320000007800000078000000500000003C0000005000000064000000780000003200000078000000780000003200000050000000500000005000000050000000C8000000000000000100000002000000030000000400000005000000060000000700000008000000090000000A0000000B0000000C0000000D0000000E0000000F000000100000001100000012000000130000001400000015000000160000001700000018000000190000001A0000001B0000001C0000001D0000001E0000001F000000200000002100000022000000230000002400000025000000260000002700000028000000290000002A0000002B0000002C0000002D0000002E0000002F00000000000000000000001F00000000000000B400000032000000D8000000640000006400000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000100000002000000030000000400000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000001000000000000000000000000000000 | |||
| (PID) Process: | (7288) Taskmgr.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\StartupApproved\Run |
| Operation: | write | Name: | Skype for Desktop |
Value: 03000000FD1CB01610C7D901 | |||
Executable files
76
Suspicious files
16
Text files
149
Unknown types
74
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7316 | cs2.exe | C:\Users\admin\AppData\Local\Temp\_MEI73162\_decimal.pyd | executable | |
MD5:7BA541DEFE3739A888BE466C999C9787 | SHA256:F90EFA10D90D940CDE48AAFE02C13A0FC0A1F0BE7F3714856B7A1435F5DECF29 | |||
| 7316 | cs2.exe | C:\Users\admin\AppData\Local\Temp\_MEI73162\_lzma.pyd | executable | |
MD5:8D9E1BB65A192C8446155A723C23D4C5 | SHA256:1549FE64B710818950AA9BF45D43FE278CE59F3B87B3497D2106FF793EFA6CF7 | |||
| 7316 | cs2.exe | C:\Users\admin\AppData\Local\Temp\_MEI73162\_queue.pyd | executable | |
MD5:FBBBFBCDCF0A7C1611E27F4B3B71079E | SHA256:699C1F0F0387511EF543C0DF7EF81A13A1CFFDE4CE4CD43A1BAF47A893B99163 | |||
| 7316 | cs2.exe | C:\Users\admin\AppData\Local\Temp\_MEI73162\base_library.zip | compressed | |
MD5:0DFE0D720F9B74605DAF7008E4F8EB08 | SHA256:746FFF4D46501F14600C42C24262E4E27D4A817D3CB68C539535483B1AD492B0 | |||
| 7316 | cs2.exe | C:\Users\admin\AppData\Local\Temp\_MEI73162\_sqlite3.pyd | executable | |
MD5:D678600C8AF1EEEAA5D8C1D668190608 | SHA256:D6960F4426C09A12488EB457E62506C49A58D62A1CB16FBC3AE66B260453C2ED | |||
| 7316 | cs2.exe | C:\Users\admin\AppData\Local\Temp\_MEI73162\_socket.pyd | executable | |
MD5:4351D7086E5221398B5B78906F4E84AC | SHA256:A0FA25EEF91825797F01754B7D7CF5106E355CF21322E926632F90AF01280ABE | |||
| 7316 | cs2.exe | C:\Users\admin\AppData\Local\Temp\_MEI73162\_ssl.pyd | executable | |
MD5:156B1FA2F11C73ED25F63EE20E6E4B26 | SHA256:A9B5F6C7A94FB6BFAF82024F906465FF39F9849E4A72A98A9B03FC07BF26DA51 | |||
| 7316 | cs2.exe | C:\Users\admin\AppData\Local\Temp\_MEI73162\blank.aes | binary | |
MD5:75AF3BFEB4DB8195A640DB5882FB5CFB | SHA256:4425D322D0BEBC4214F99DCFD5CFAF3A634B1C16032B75AA1A7EF50F0C2D266A | |||
| 7316 | cs2.exe | C:\Users\admin\AppData\Local\Temp\_MEI73162\VCRUNTIME140.dll | executable | |
MD5:F12681A472B9DD04A812E16096514974 | SHA256:D66C3B47091CEB3F8D3CC165A43D285AE919211A0C0FCB74491EE574D8D464F8 | |||
| 7316 | cs2.exe | C:\Users\admin\AppData\Local\Temp\_MEI73162\rar.exe | executable | |
MD5:9C223575AE5B9544BC3D69AC6364F75E | SHA256:90341AC8DCC9EC5F9EFE89945A381EB701FE15C3196F594D9D9F0F67B4FC2213 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
57
DNS requests
38
Threats
27
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1072 | cs2.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=hosting | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1072 | cs2.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/json/?fields=225545 | unknown | — | — | whitelisted |
4212 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4212 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5308 | SearchApp.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
7080 | .scr | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=hosting | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
7212 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7572 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1072 | cs2.exe | 208.95.112.1:80 | ip-api.com | TUT-AS | US | whitelisted |
1072 | cs2.exe | 142.250.186.163:443 | gstatic.com | GOOGLE | US | whitelisted |
6544 | svchost.exe | 20.190.160.17:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
blank-t99dj.in |
| unknown |
ip-api.com |
| whitelisted |
gstatic.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
2196 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
1072 | cs2.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |
2196 | svchost.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
1072 | cs2.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |
2196 | svchost.exe | Misc activity | ET INFO Discord Chat Service Domain in DNS Lookup (discord .com) |
1072 | cs2.exe | A Network Trojan was detected | STEALER [ANY.RUN] BlankGrabber (SkochGrabber) Generic External IP Check |
1072 | cs2.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
1072 | cs2.exe | Misc activity | ET INFO Observed Discord Service Domain (discord .com) in TLS SNI |
2184 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |