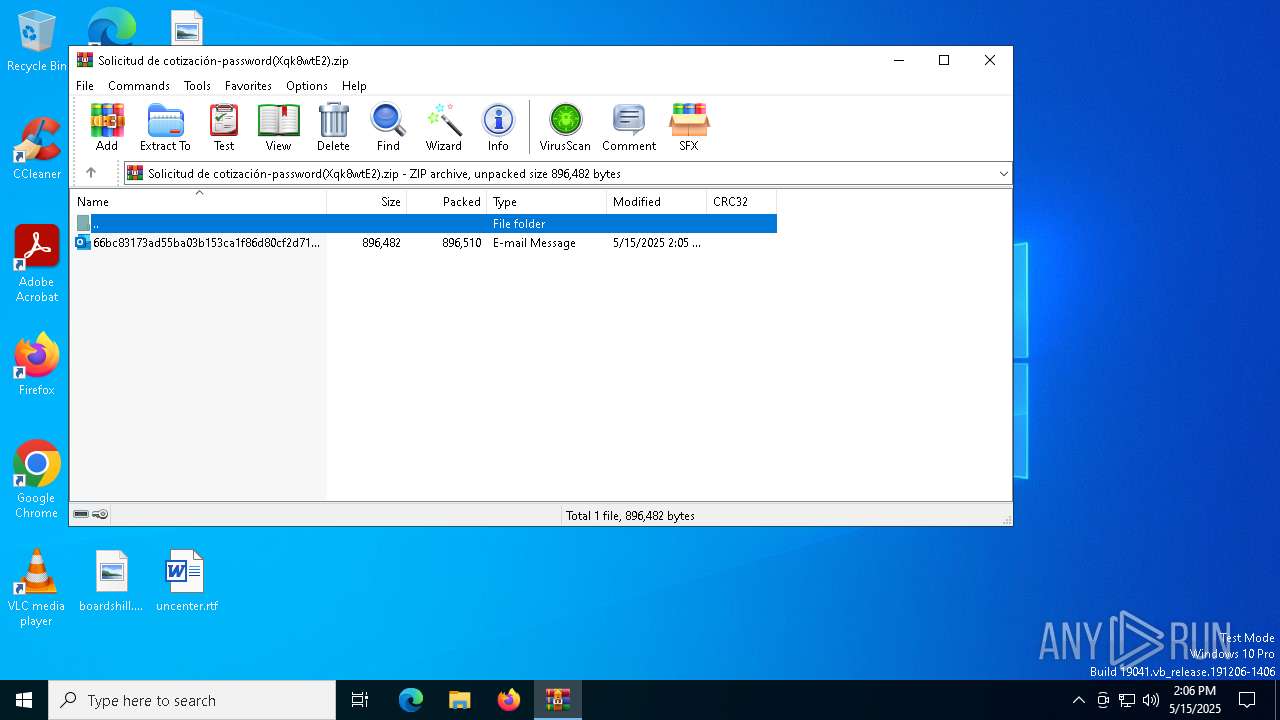
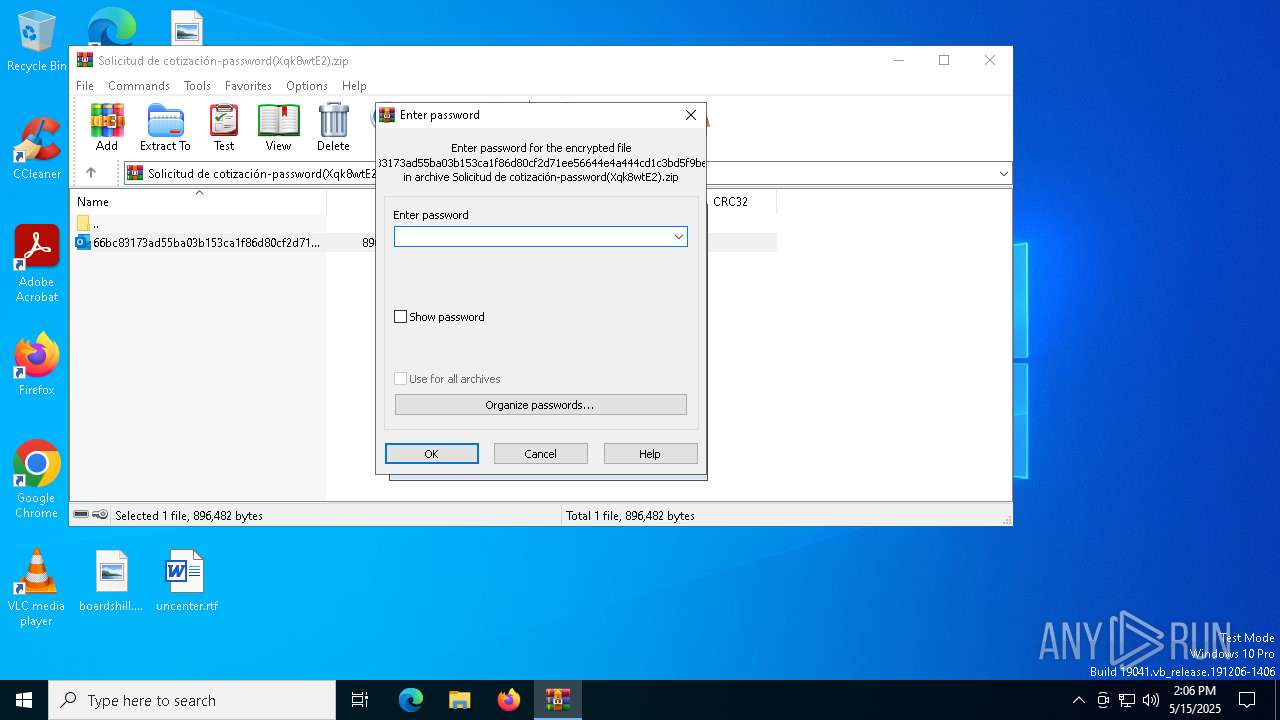
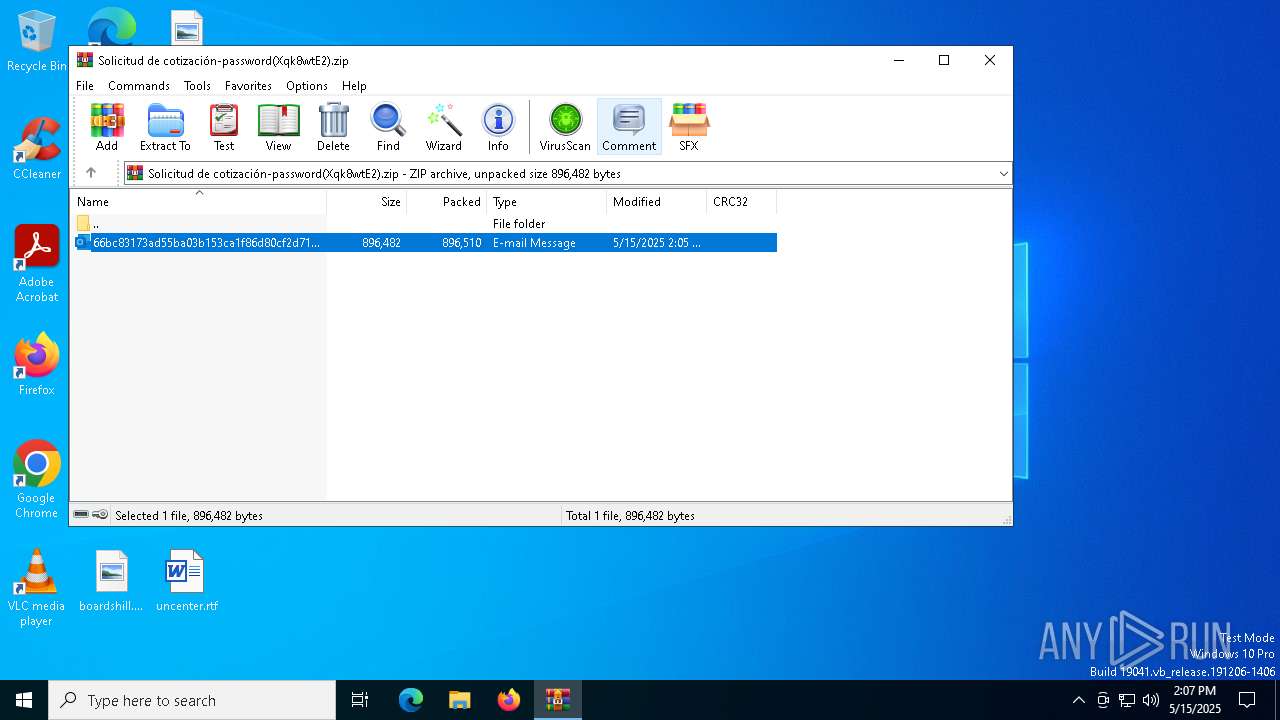
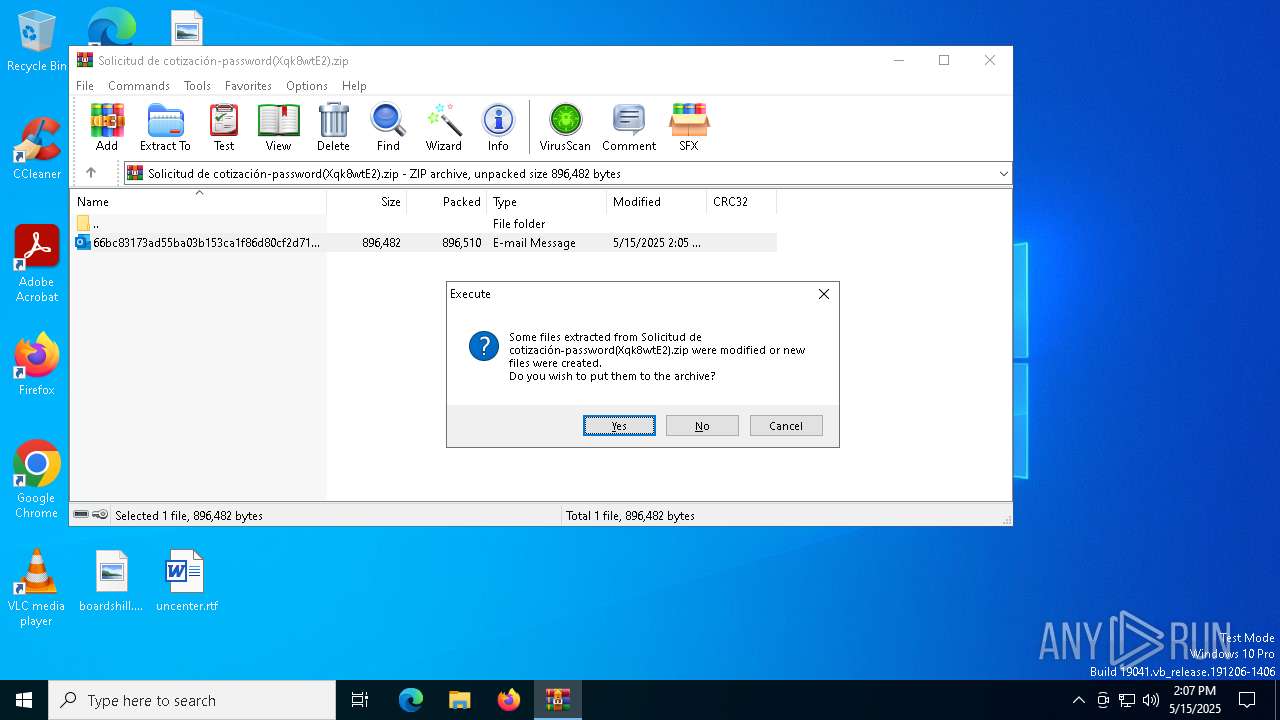
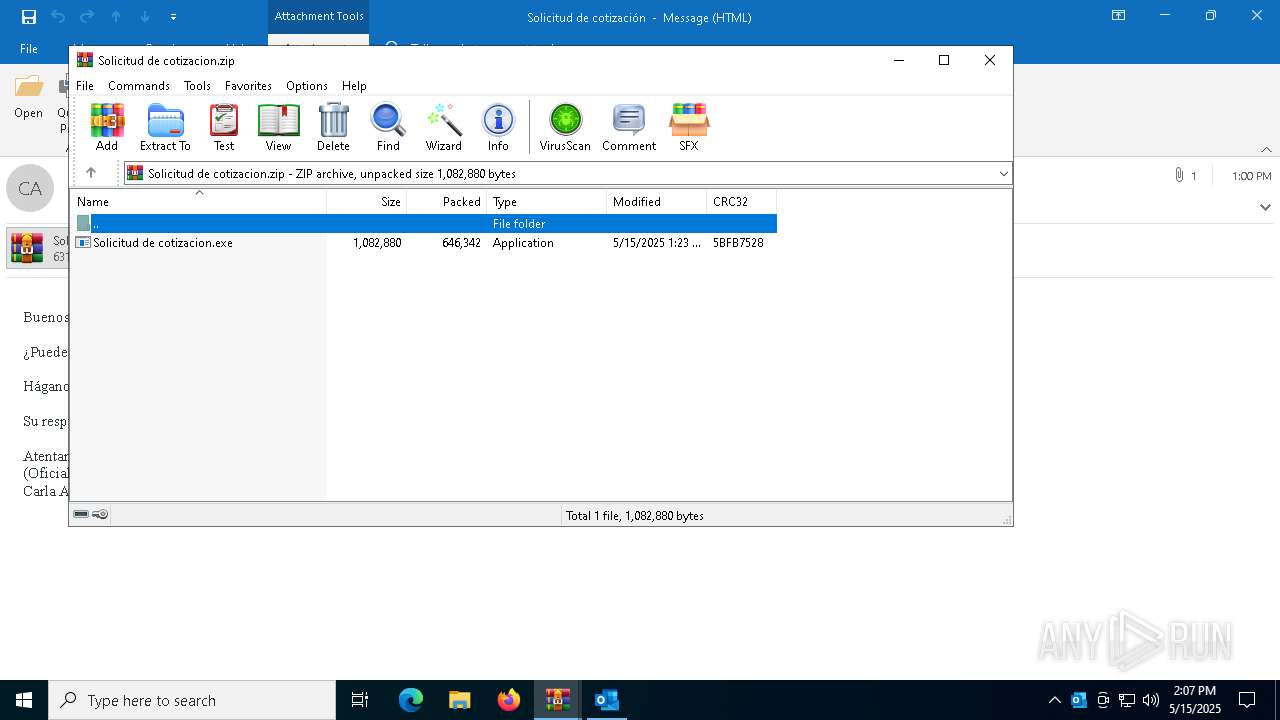
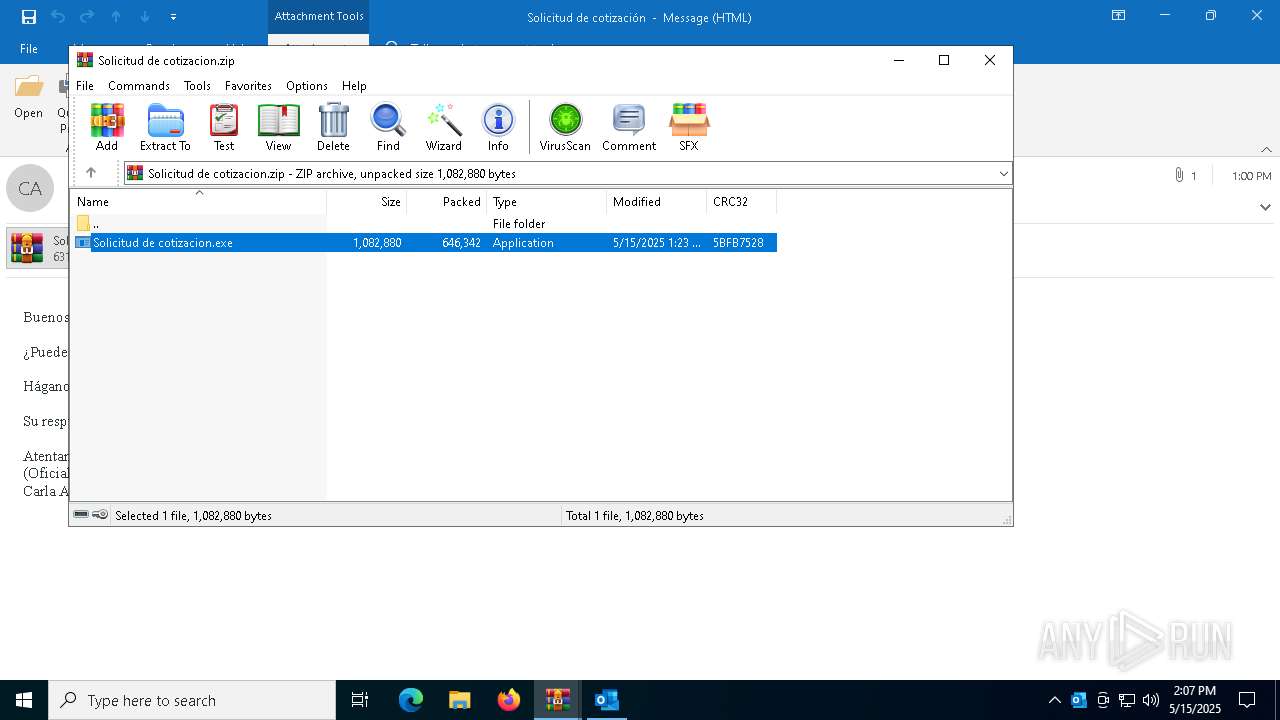
| File name: | Solicitud de cotización-password(Xqk8wtE2).zip |
| Full analysis: | https://app.any.run/tasks/8a5384de-4a11-43be-adc9-912692c9bbbc |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | May 15, 2025, 14:06:21 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v5.1 to extract, compression method=AES Encrypted |
| MD5: | DDEC176C98C49BD894CCF11F6E098E6B |
| SHA1: | 2512223E71F60A5F2E31336A55550A0C9E6B2F4E |
| SHA256: | 2328F9A928090F027339CF8158250A8285C6151A9924F5E0334F8FBD0B5ABDAD |
| SSDEEP: | 49152:uDa3pF7kcV3basv/phw4iNUlhHPNSSQRw7KKju6GwU69ocz7CA5EJvfJC:xpF7kSOShhNReRTKjCy6cz |
MALICIOUS
Actions looks like stealing of personal data
- RegSvcs.exe (PID: 4740)
- RegSvcs.exe (PID: 5436)
Steals credentials from Web Browsers
- RegSvcs.exe (PID: 5436)
- RegSvcs.exe (PID: 4740)
AGENTTESLA has been detected (SURICATA)
- RegSvcs.exe (PID: 5436)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 6644)
- WinRAR.exe (PID: 4220)
Reads Microsoft Outlook installation path
- WinRAR.exe (PID: 4220)
Connects to SMTP port
- RegSvcs.exe (PID: 4740)
- RegSvcs.exe (PID: 5436)
Checks for external IP
- RegSvcs.exe (PID: 4740)
- svchost.exe (PID: 2196)
- RegSvcs.exe (PID: 5436)
Contacting a server suspected of hosting an CnC
- RegSvcs.exe (PID: 5436)
INFO
Reads Microsoft Office registry keys
- WinRAR.exe (PID: 4220)
The sample compiled with english language support
- WinRAR.exe (PID: 4220)
- OUTLOOK.EXE (PID: 4920)
- WinRAR.exe (PID: 6644)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6644)
Checks supported languages
- Solicitud de cotizacion.exe (PID: 960)
- Solicitud de cotizacion.exe (PID: 2320)
- RegSvcs.exe (PID: 4740)
- Solicitud de cotizacion.exe (PID: 6576)
- RegSvcs.exe (PID: 5436)
- RegSvcs.exe (PID: 5156)
Create files in a temporary directory
- Solicitud de cotizacion.exe (PID: 960)
- Solicitud de cotizacion.exe (PID: 6576)
- Solicitud de cotizacion.exe (PID: 2320)
Reads the computer name
- RegSvcs.exe (PID: 4740)
- RegSvcs.exe (PID: 5156)
Reads the machine GUID from the registry
- RegSvcs.exe (PID: 4740)
- RegSvcs.exe (PID: 5436)
Reads mouse settings
- Solicitud de cotizacion.exe (PID: 6576)
Checks proxy server information
- RegSvcs.exe (PID: 4740)
Reads the software policy settings
- slui.exe (PID: 3896)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0801 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2025:05:15 14:05:40 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | 896510 |
| ZipUncompressedSize: | 896482 |
| ZipFileName: | 66bc83173ad55ba03b153ca1f86d80cf2d71ee56644e4a444cd1c3bd5f9be9a4.eml |
Total processes
148
Monitored processes
14
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 920 | "C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe" "FD2DA5EE-96C2-4C2B-9751-0A9F833D64A1" "2BFEF715-5AB9-41DD-A6D3-399F11040593" "4920" | C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Artificial Intelligence (AI) Host for the Microsoft® Windows® Operating System and Platform x64. Version: 0.12.2.0 Modules
| |||||||||||||||
| 960 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa6644.35055\Solicitud de cotizacion.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa6644.35055\Solicitud de cotizacion.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2320 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa6644.35155\Solicitud de cotizacion.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa6644.35155\Solicitud de cotizacion.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3896 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4172 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4220 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Solicitud de cotización-password(Xqk8wtE2).zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 4740 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa6644.35055\Solicitud de cotizacion.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegSvcs.exe | Solicitud de cotizacion.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Services Installation Utility Exit code: 4294967295 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
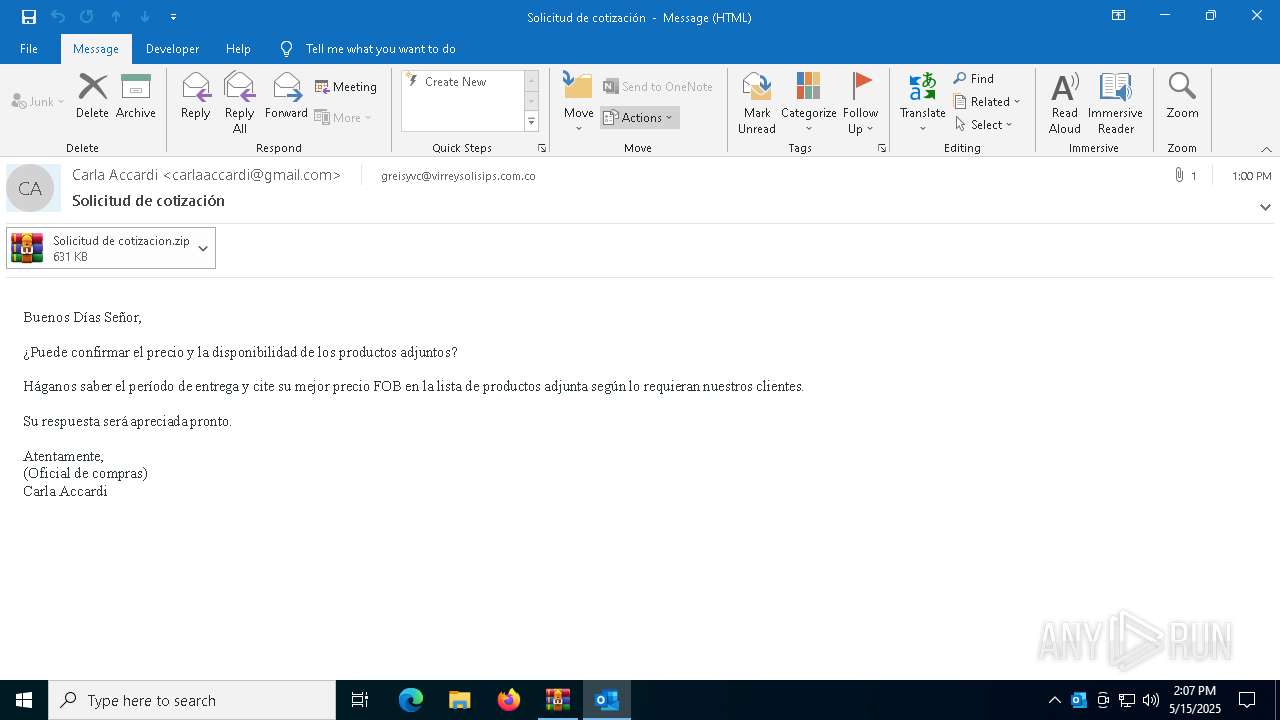
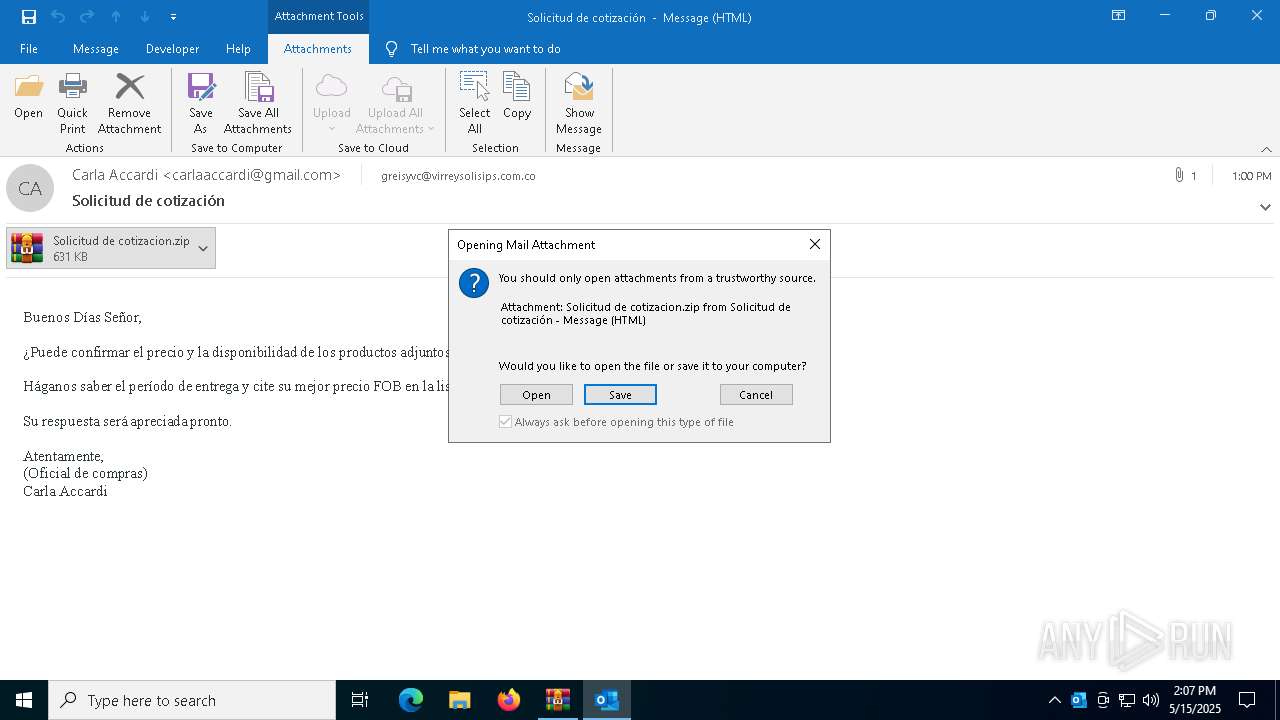
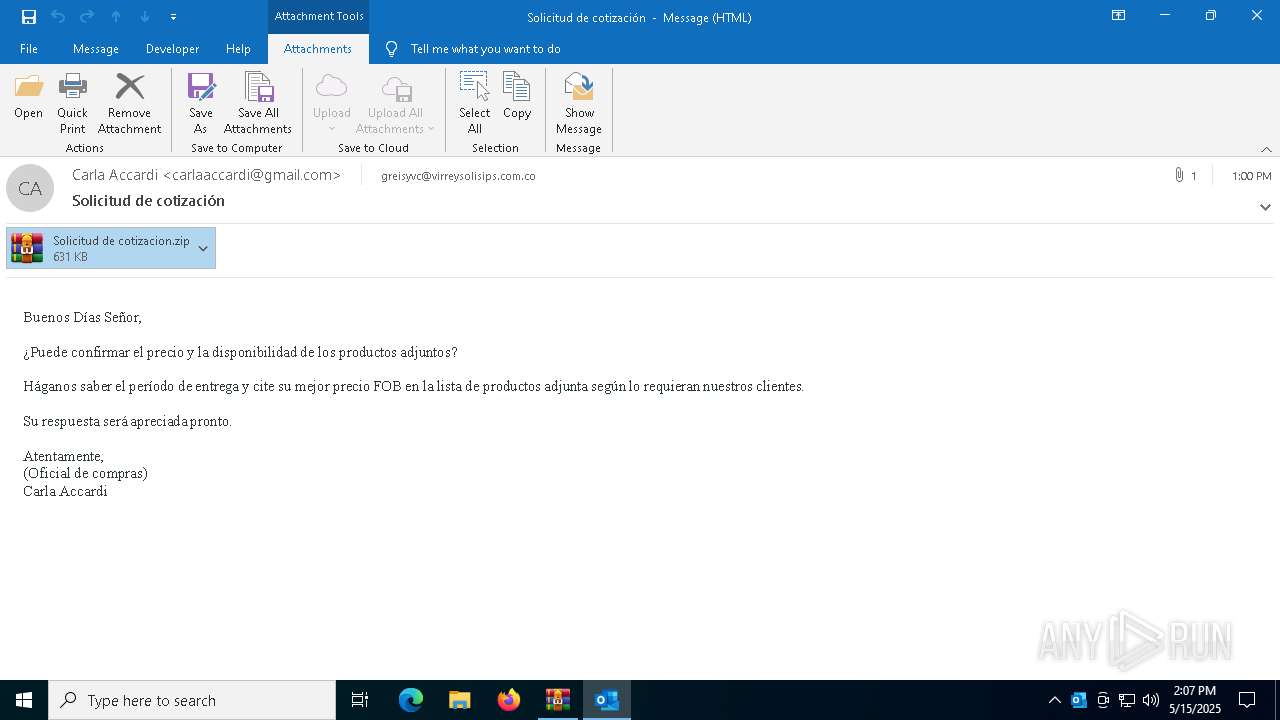
| 4920 | "C:\Program Files\Microsoft Office\Root\Office16\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\Rar$DIb4220.31451\66bc83173ad55ba03b153ca1f86d80cf2d71ee56644e4a444cd1c3bd5f9be9a4.eml" | C:\Program Files\Microsoft Office\root\Office16\OUTLOOK.EXE | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Version: 16.0.16026.20146 Modules
| |||||||||||||||
| 5156 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa6644.35155\Solicitud de cotizacion.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegSvcs.exe | — | Solicitud de cotizacion.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Services Installation Utility Exit code: 4294967295 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
Total events
19 017
Read events
17 787
Write events
1 090
Delete events
140
Modification events
| (PID) Process: | (4220) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (4220) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (4220) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (4220) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Solicitud de cotización-password(Xqk8wtE2).zip | |||
| (PID) Process: | (4220) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4220) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4220) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4220) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4220) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.eml\OpenWithProgids |
| Operation: | write | Name: | Outlook.File.eml.15 |
Value: | |||
| (PID) Process: | (4220) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {5FA29220-36A1-40F9-89C6-F4B384B7642E} {886D8EEB-8CF2-4446-8D02-CDBA1DBDCF99} 0xFFFF |
Value: 01000000000000004804B4A1A2C5DB01 | |||
Executable files
3
Suspicious files
15
Text files
8
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4920 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook1.pst | — | |
MD5:— | SHA256:— | |||
| 4920 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\olk53F9.tmp | compressed | |
MD5:79D5B00B923838AF827ABE556C5F8CF6 | SHA256:E8C97E81AB380ACE9327A86D7BB35CD3201AACE482B51B3FCD4ED9F2D0E67173 | |||
| 4920 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\56a61aeb75d8f5be186c26607f4bb213abe7c5ec.tbres | binary | |
MD5:83E7E876DE0029584AC8D9F5CFF4DF0D | SHA256:90766E3F39CBC74E21158C1455132DC75E58C028A63D3D0EECACB1A733EABAEC | |||
| 4220 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb4220.31451\66bc83173ad55ba03b153ca1f86d80cf2d71ee56644e4a444cd1c3bd5f9be9a4.eml:OECustomProperty | binary | |
MD5:B57C148DBD38D0A66682928A57C39A07 | SHA256:F2C28DB2FA3F038C6ADCBA0085AF58B60ADEC4BAFC23F6FFB8AD4C3D8049704B | |||
| 4220 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb4220.31451\66bc83173ad55ba03b153ca1f86d80cf2d71ee56644e4a444cd1c3bd5f9be9a4.eml | html | |
MD5:F9B4738241764A53592109CC4CF7C425 | SHA256:6E26DE6BDD5385B97F918F95D0A37ED1F3DAA58418F4106C34B5ECDF1FE30D2F | |||
| 4920 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\089d66ba04a8cec4bdc5267f42f39cf84278bb67.tbres | binary | |
MD5:8D67A873C857ED7E315051FF7A7875AB | SHA256:A053E21E8A1874593F0A926714006D27BE633B53A66E87B807C35AFBA91EF260 | |||
| 4920 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\WebServiceCache\AllUsers\officeclient.microsoft.com\3A008838-51DC-490F-A41B-388AD778A4B8 | xml | |
MD5:FC7C87A2D6AE04198CCE93B0376A76F3 | SHA256:34106A62B9CEA8727C07023A11E12A848DE22362B9D414D582B6F2A81974DACD | |||
| 4920 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Content.Outlook\N9V57KIH\Solicitud de cotizacion.zip:Zone.Identifier | text | |
MD5:FBCCF14D504B7B2DBCB5A5BDA75BD93B | SHA256:EACD09517CE90D34BA562171D15AC40D302F0E691B439F91BE1B6406E25F5913 | |||
| 4920 | OUTLOOK.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_6372E0472AFF76BB926C97818BC773B9 | binary | |
MD5:3D88568176C5F17E81FDFFEBC5771F6F | SHA256:5F50C6911DD6C2ECEEB5894A34AF6DCB08D6FFA68565FC5F5A1A852DCB4E5FE1 | |||
| 4920 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\AddInClassifierCache\OfficeSharedEntitiesUpdated.bin | text | |
MD5:5E1DF4B23071C31CCF610A612C2F4F7E | SHA256:4B3DA4F63D5D01C5C9C45AC081B9DAECE4B389FFD323D2E1D262867465ECE18E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
35
DNS requests
26
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.20.245.137:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3272 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4920 | OUTLOOK.EXE | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
3272 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4920 | OUTLOOK.EXE | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
4740 | RegSvcs.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=hosting | unknown | — | — | whitelisted |
5436 | RegSvcs.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=hosting | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 2.20.245.137:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.159.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3272 | SIHClient.exe | 172.202.163.200:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | GB | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
ecs.office.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
2196 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
4740 | RegSvcs.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |
4740 | RegSvcs.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External Hosting Lookup by ip-api |
4740 | RegSvcs.exe | Misc activity | INFO [ANY.RUN] SMTP email client opens transfer with server (EHLO) |
5436 | RegSvcs.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |
5436 | RegSvcs.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External Hosting Lookup by ip-api |
5436 | RegSvcs.exe | Malware Command and Control Activity Detected | ET MALWARE MSIL/Kryptik.XSY Data Exfil via SMTP |
5436 | RegSvcs.exe | Misc activity | INFO [ANY.RUN] SMTP email client opens transfer with server (EHLO) |
5436 | RegSvcs.exe | A Network Trojan was detected | STEALER [ANY.RUN] AgentTesla Exfiltration SMTP (Base64 encoded) |