| File name: | Blackmatter-Sample2.exe |
| Full analysis: | https://app.any.run/tasks/d0845b4b-9ee7-48e3-b3cb-2f88f6d29e25 |
| Verdict: | Malicious activity |
| Threats: | BlackMatter is a ransomware strain operating as a Ransomware-as-a-Service (RaaS), designed to encrypt files, remove recovery options, and extort victims across critical industries. Emerging in 2021, it quickly became a major concern due to its ability to evade defenses, spread across networks, and cause large-scale operational disruption, forcing security teams to act against a highly destructive and persistent threat. |
| Analysis date: | June 25, 2025, 19:43:44 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | 598C53BFEF81E489375F09792E487F1A |
| SHA1: | 80A29BD2C349A8588EDF42653ED739054F9A10F5 |
| SHA256: | 22D7D67C3AF10B1A37F277EBABE2D1EB4FD25AFBD6437D4377400E148BCC08D6 |
| SSDEEP: | 1536:U9RGGhm6IvmhXfwdO3uRMEjupuWbAOHaSCIVP:bmhXodgu6ZpuVb |
MALICIOUS
Known privilege escalation attack
- dllhost.exe (PID: 3556)
BLACKMATTER has been detected (SURICATA)
- svchost.exe (PID: 2200)
- Blackmatter-Sample2.exe (PID: 4236)
RANSOMWARE has been detected
- Blackmatter-Sample2.exe (PID: 4236)
Connects to the CnC server
- svchost.exe (PID: 2200)
- Blackmatter-Sample2.exe (PID: 4236)
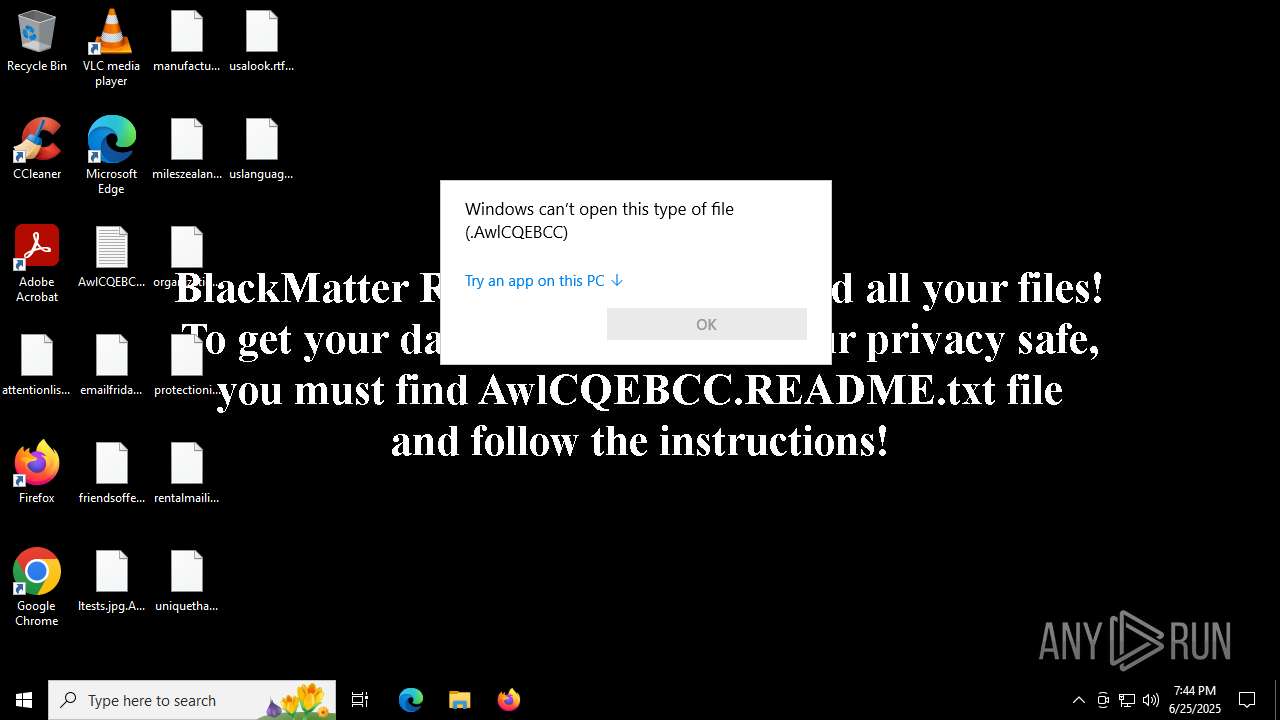
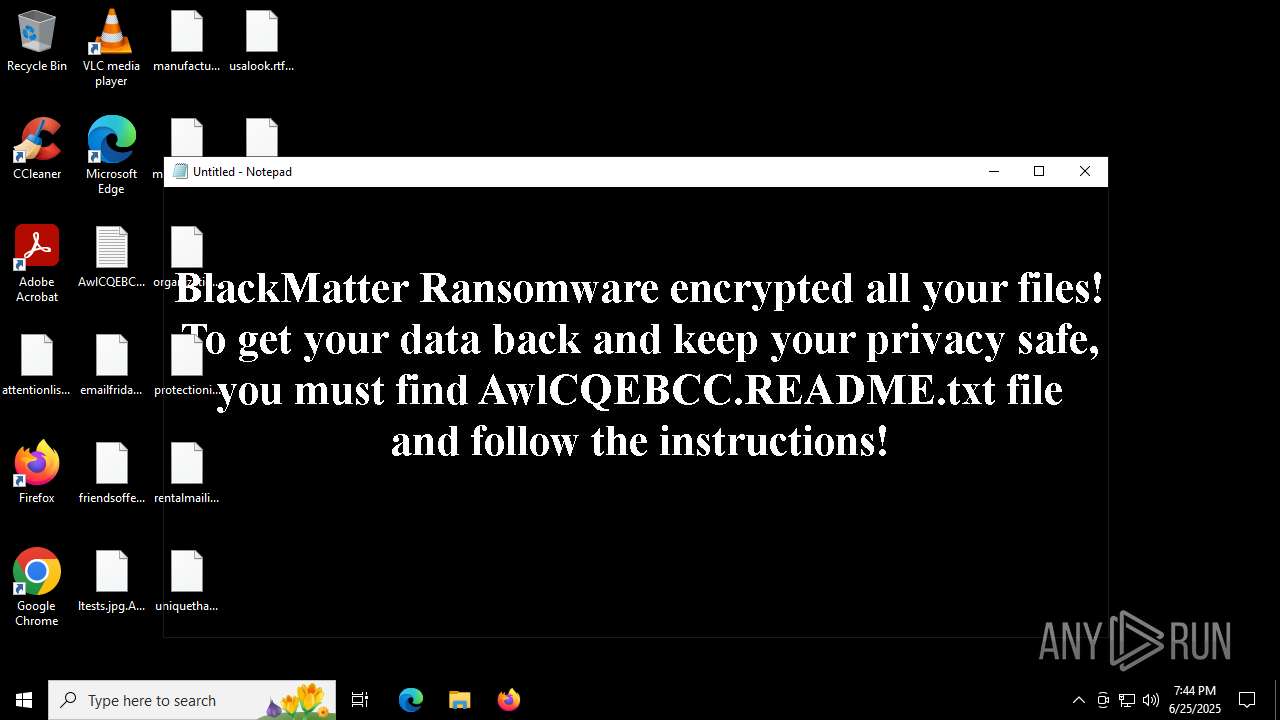
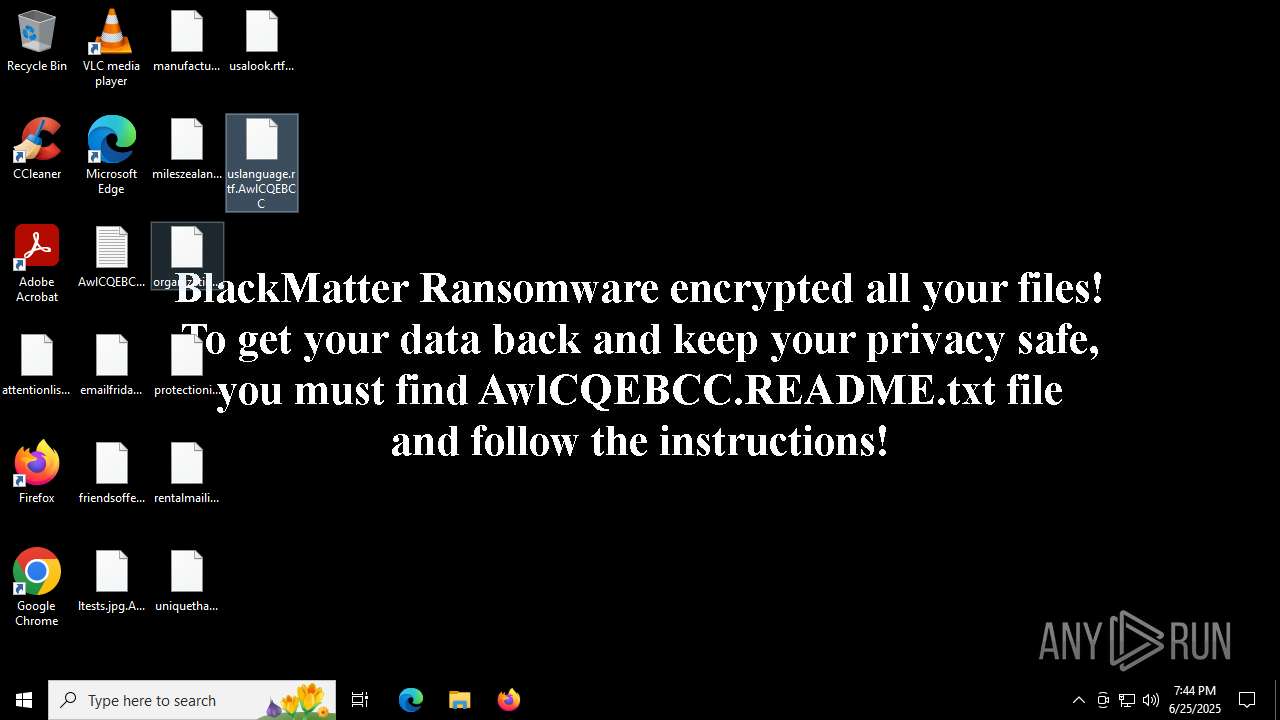
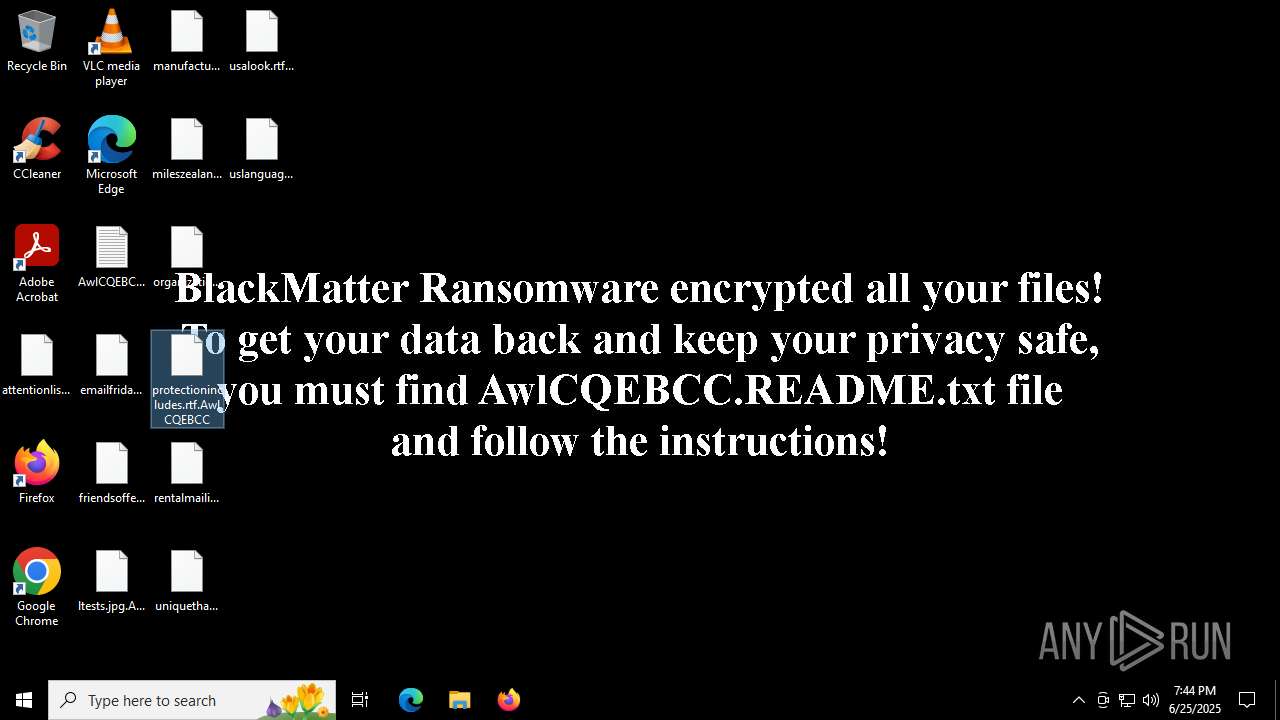
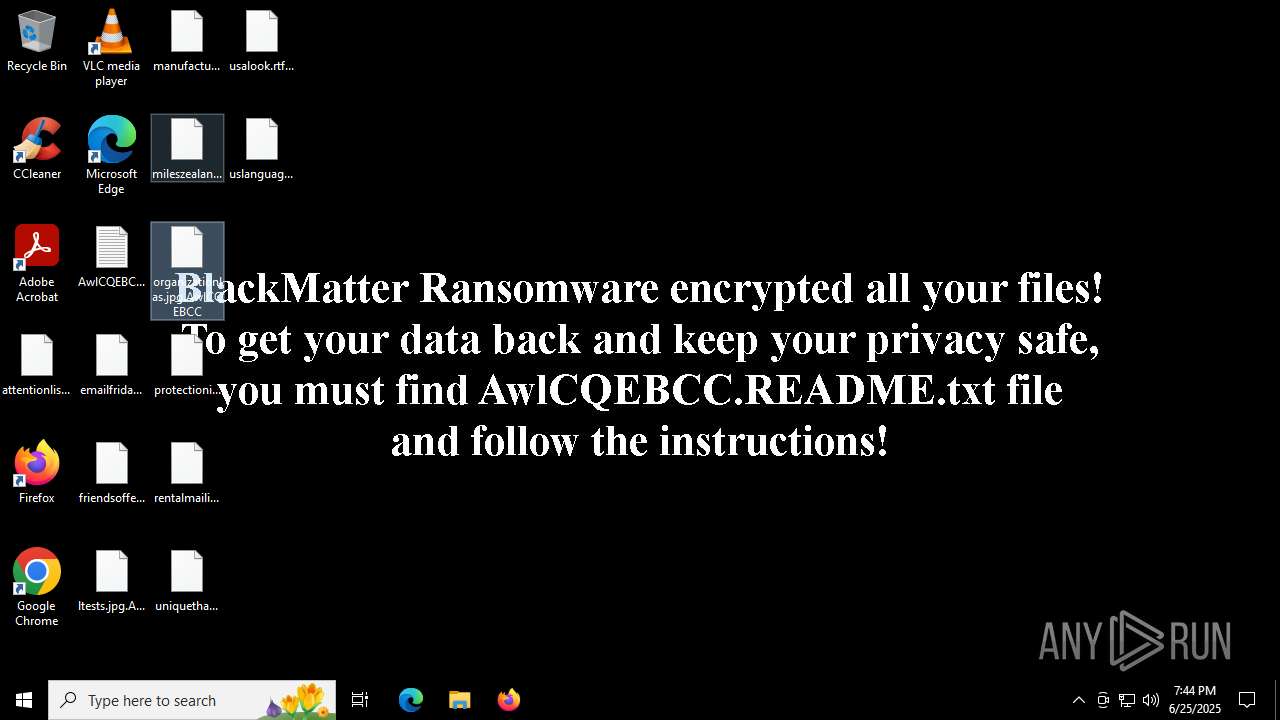
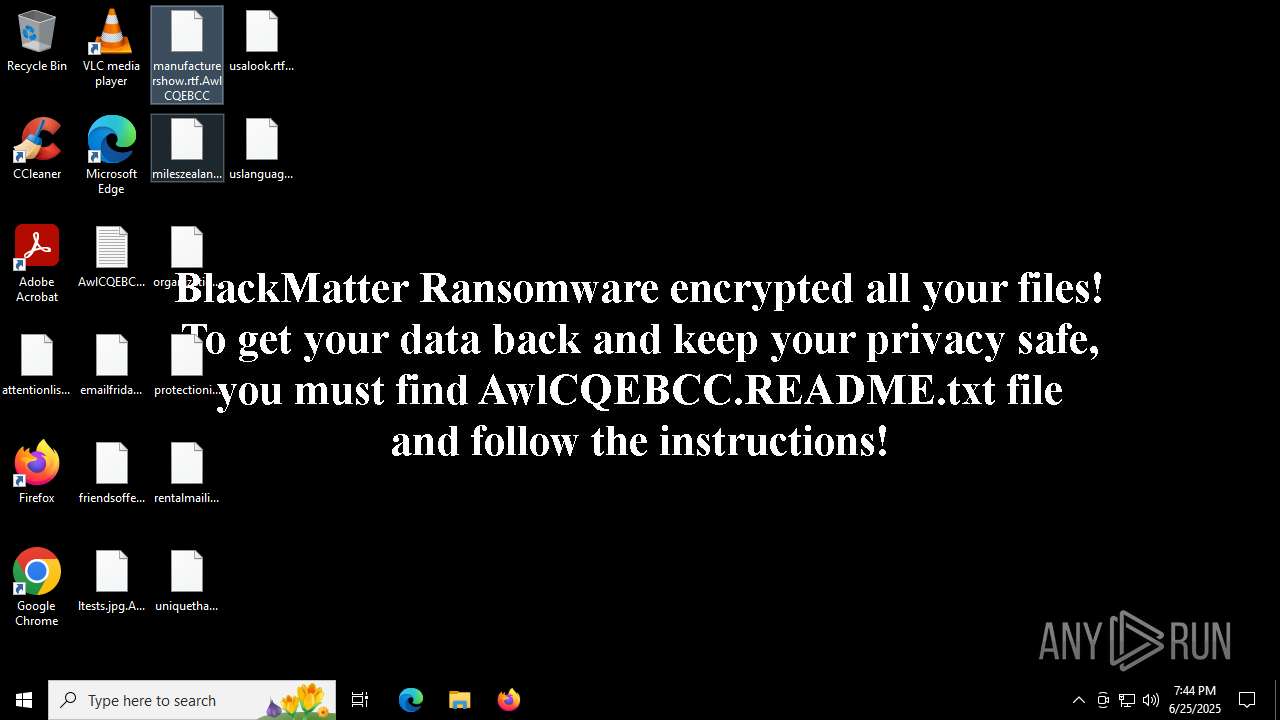
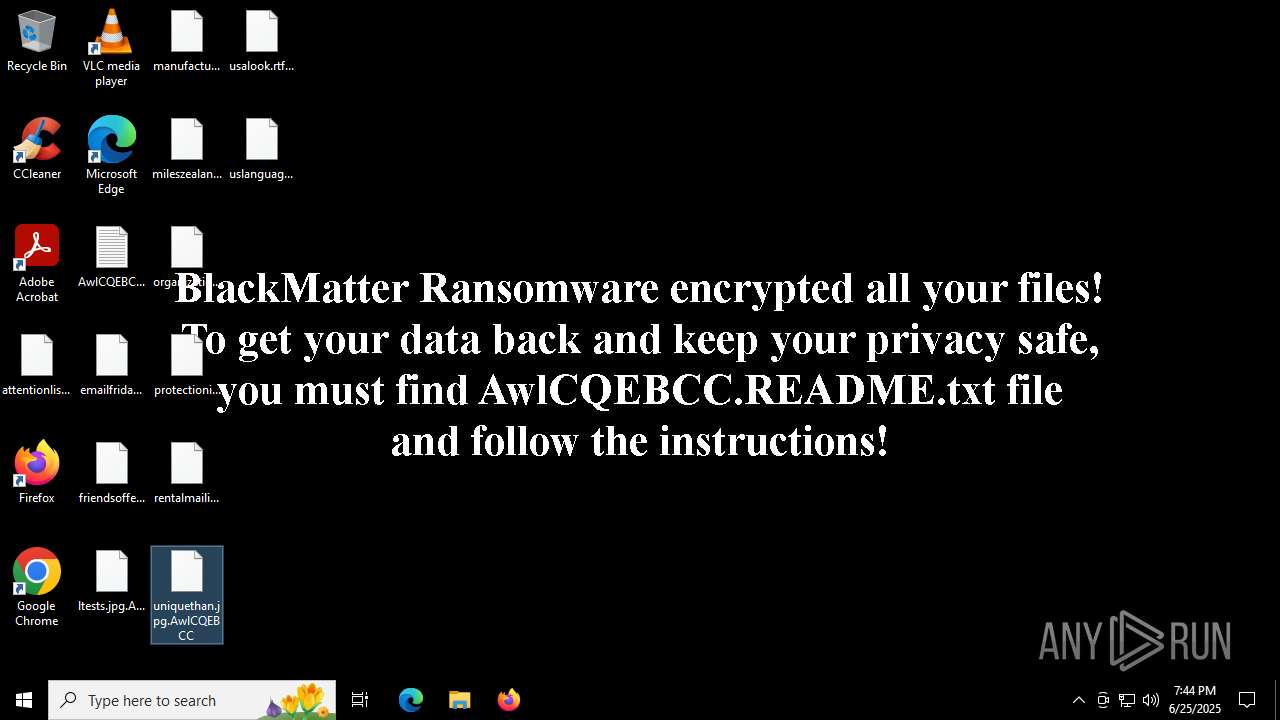
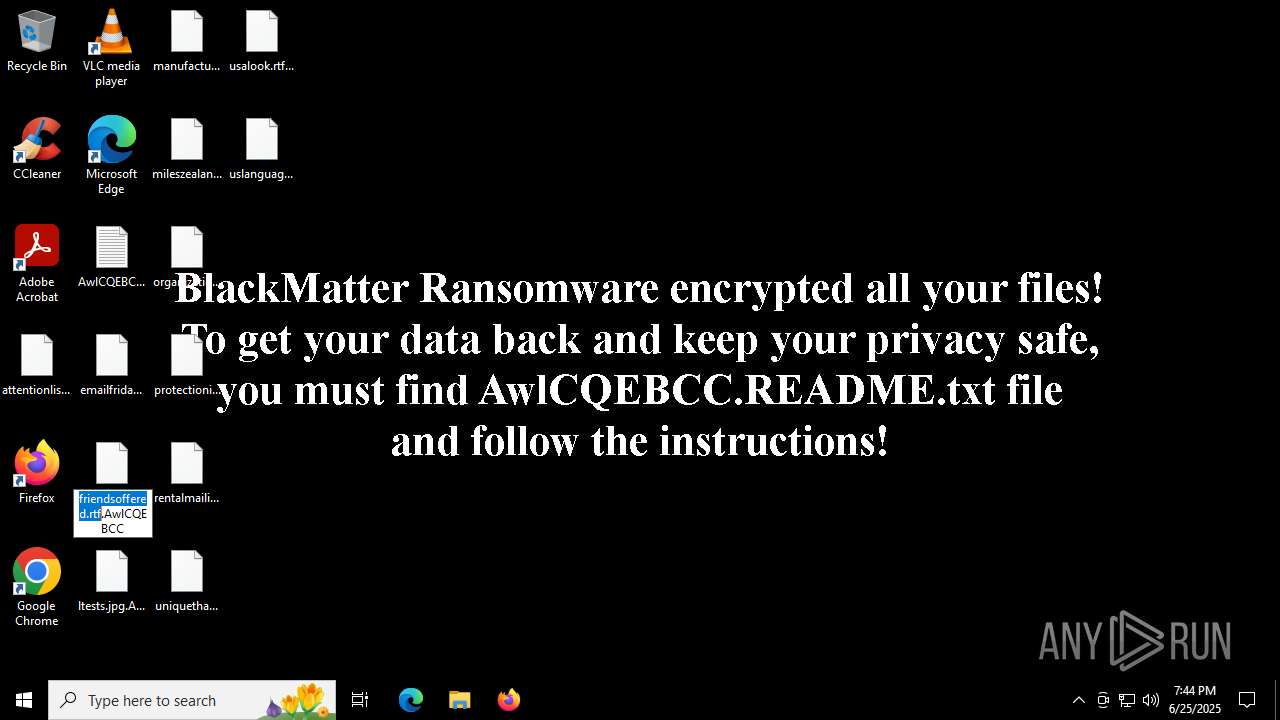
Renames files like ransomware
- Blackmatter-Sample2.exe (PID: 4236)
SUSPICIOUS
Reads security settings of Internet Explorer
- Blackmatter-Sample2.exe (PID: 4236)
Executes as Windows Service
- VSSVC.exe (PID: 304)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2200)
- Blackmatter-Sample2.exe (PID: 4236)
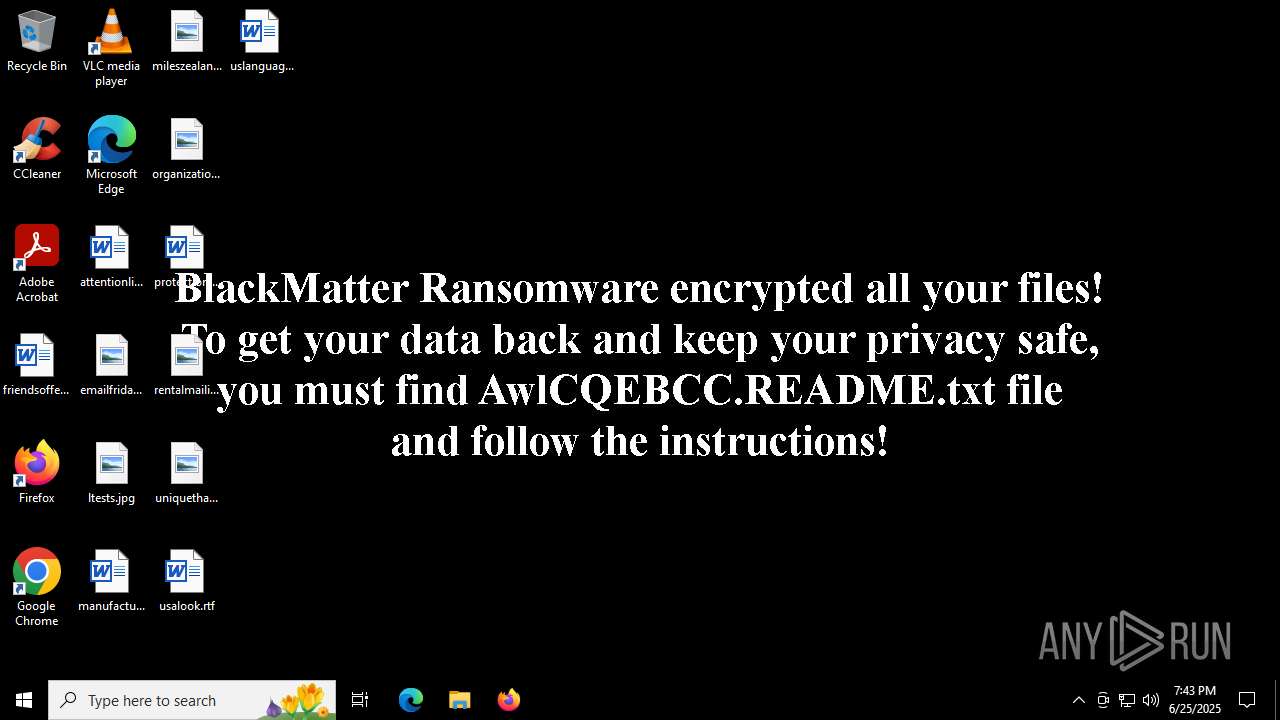
Changes the desktop background image
- Blackmatter-Sample2.exe (PID: 4236)
INFO
Reads the machine GUID from the registry
- Blackmatter-Sample2.exe (PID: 6212)
- Blackmatter-Sample2.exe (PID: 4236)
Reads security settings of Internet Explorer
- dllhost.exe (PID: 3556)
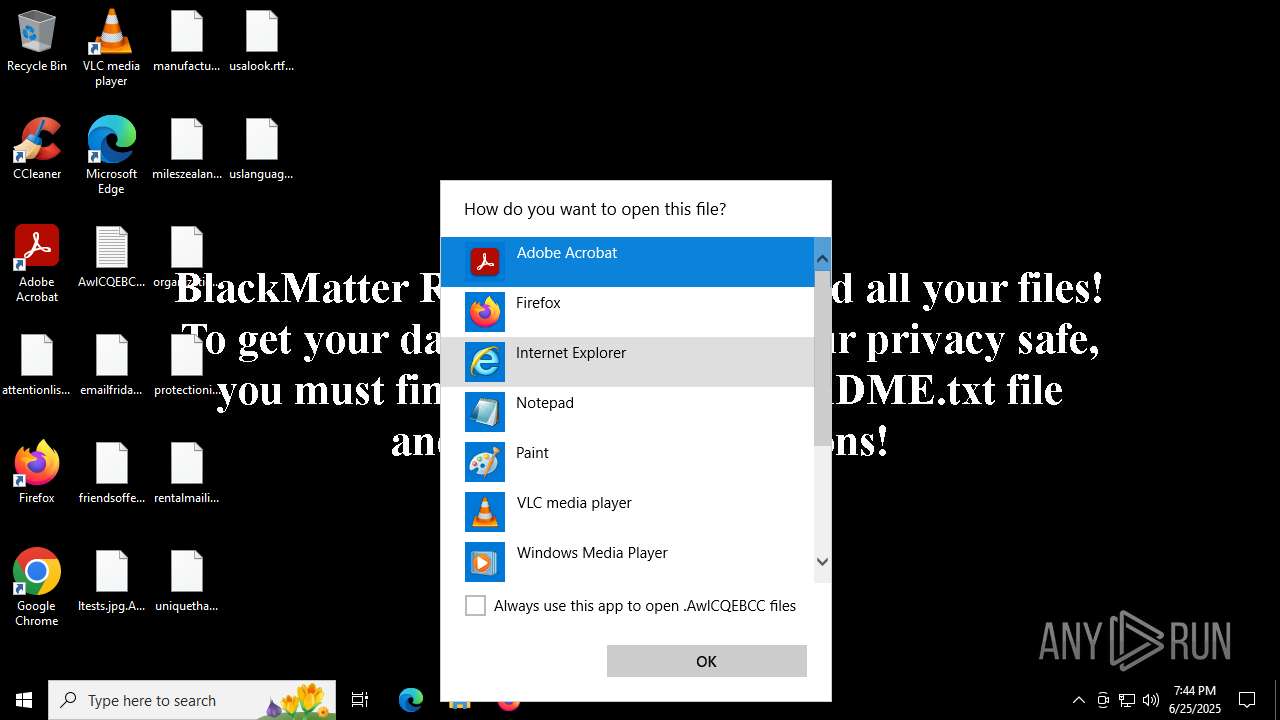
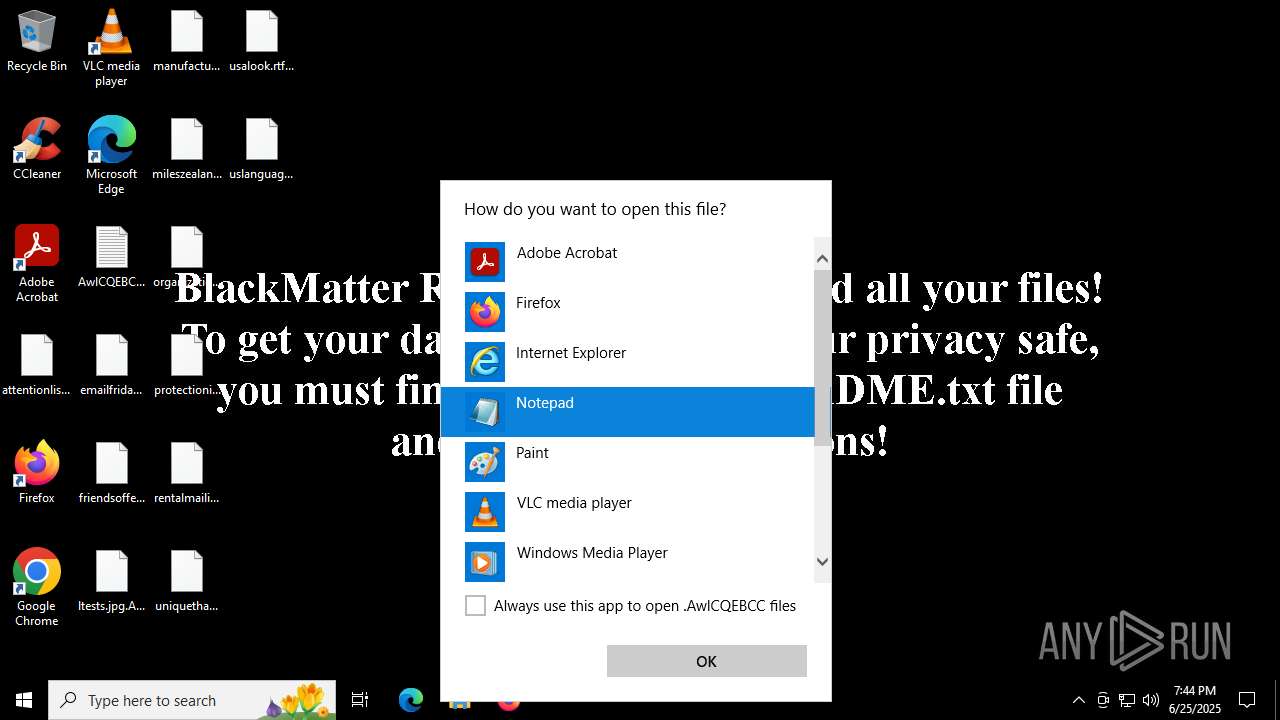
- OpenWith.exe (PID: 4552)
- notepad.exe (PID: 4884)
Reads the computer name
- Blackmatter-Sample2.exe (PID: 6212)
- Blackmatter-Sample2.exe (PID: 4236)
Checks supported languages
- Blackmatter-Sample2.exe (PID: 6212)
- Blackmatter-Sample2.exe (PID: 4236)
Reads product name
- Blackmatter-Sample2.exe (PID: 4236)
Reads Environment values
- Blackmatter-Sample2.exe (PID: 4236)
Checks proxy server information
- Blackmatter-Sample2.exe (PID: 4236)
Creates files or folders in the user directory
- Blackmatter-Sample2.exe (PID: 4236)
Reads the software policy settings
- Blackmatter-Sample2.exe (PID: 4236)
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 4552)
- OpenWith.exe (PID: 5476)
Creates files in the program directory
- Blackmatter-Sample2.exe (PID: 4236)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (38.3) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (26.2) |
| .exe | | | Win16/32 Executable Delphi generic (12) |
| .exe | | | Generic Win/DOS Executable (11.6) |
| .exe | | | DOS Executable Generic (11.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:07:23 20:51:18+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.12 |
| CodeSize: | 56320 |
| InitializedDataSize: | 9728 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xe8d5 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
145
Monitored processes
9
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 304 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2200 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3556 | C:\WINDOWS\SysWOW64\DllHost.exe /Processid:{3E5FC7F9-9A51-4367-9063-A120244FBEC7} | C:\Windows\SysWOW64\dllhost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4236 | "C:\Users\admin\AppData\Local\Temp\Blackmatter-Sample2.exe" | C:\Users\admin\AppData\Local\Temp\Blackmatter-Sample2.exe | dllhost.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
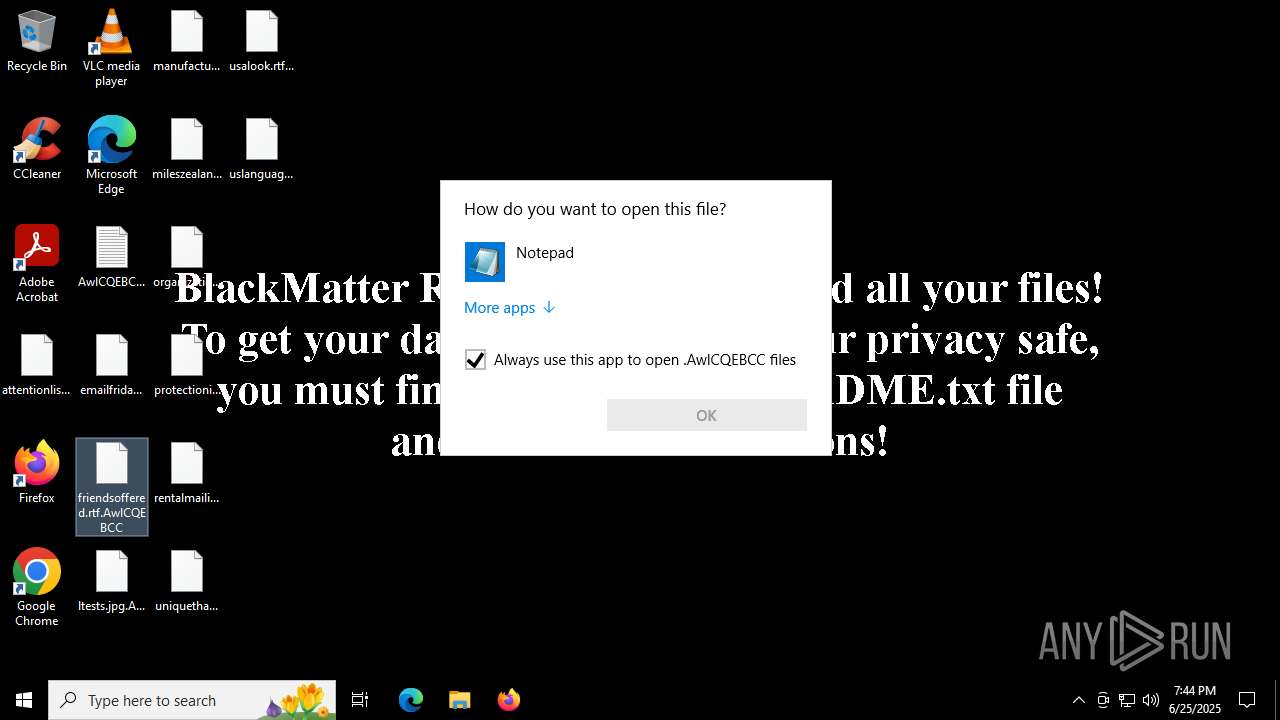
| 4552 | C:\WINDOWS\system32\OpenWith.exe -Embedding | C:\Windows\System32\OpenWith.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4644 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4884 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\uslanguage.rtf.AwlCQEBCC | C:\Windows\System32\notepad.exe | — | OpenWith.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5476 | C:\WINDOWS\system32\OpenWith.exe -Embedding | C:\Windows\System32\OpenWith.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6212 | "C:\Users\admin\AppData\Local\Temp\Blackmatter-Sample2.exe" | C:\Users\admin\AppData\Local\Temp\Blackmatter-Sample2.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
3 285
Read events
3 279
Write events
5
Delete events
1
Modification events
| (PID) Process: | (4236) Blackmatter-Sample2.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4236) Blackmatter-Sample2.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4236) Blackmatter-Sample2.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (4236) Blackmatter-Sample2.exe | Key: | HKEY_CURRENT_USER\Control Panel\Desktop |
| Operation: | write | Name: | WallPaper |
Value: C:\ProgramData\AwlCQEBCC.bmp | |||
| (PID) Process: | (4236) Blackmatter-Sample2.exe | Key: | HKEY_CURRENT_USER\Control Panel\Desktop |
| Operation: | write | Name: | WallpaperStyle |
Value: 10 | |||
| (PID) Process: | (4236) Blackmatter-Sample2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\AwlCQEBCC |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
0
Suspicious files
49
Text files
98
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4236 | Blackmatter-Sample2.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\223DE96EE265046957A660ED7C9DD9E7_EFF9B9BA98DEAA773F261FA85A0B1771 | binary | |
MD5:B9EAD95963C7B345A2D5AB6CA1E75790 | SHA256:669B416DC3D331126DA934AB1AD3BAE7ED2BECB2094CF580A4EB09EDB9022F90 | |||
| 4236 | Blackmatter-Sample2.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\223DE96EE265046957A660ED7C9DD9E7_EFF9B9BA98DEAA773F261FA85A0B1771 | der | |
MD5:AA01D73389C5B794417EF66AA16733B5 | SHA256:DEB902EDA18D03DFD8F1843B62CF7EA4B450884C09F2F4870D1E38D20D6980B3 | |||
| 4236 | Blackmatter-Sample2.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\85E98AB9E20E0472C146F08ADBCF5FD9_436DD954C48579A90F36D53DDCA5EE35 | der | |
MD5:2694A5823CAAEC88317959E136FE0236 | SHA256:765F9F7B7D596CE3757DD7CD453D833B6BD56BBCFC926C95080B4F5241917E1D | |||
| 4236 | Blackmatter-Sample2.exe | C:\Users\Administrator\Searches\Everywhere.search-ms.AwlCQEBCC | xml | |
MD5:0FA26B6C98419B5E7C00EFFFB5835612 | SHA256:4094D158E3B0581BA433A46D0DCE62F99D8C0FD1B50BB4D0517DDC0A4A1FDE24 | |||
| 4236 | Blackmatter-Sample2.exe | C:\AwlCQEBCC.README.txt | text | |
MD5:F66968C47A64569E2281F65A95991BE0 | SHA256:4B950C763006E7C4569DF8742855CEC31BF82F835BD7E2BDCB5F128DB34C82BF | |||
| 4236 | Blackmatter-Sample2.exe | C:\Users\Administrator\Searches\Indexed Locations.search-ms.AwlCQEBCC | xml | |
MD5:B6ACBEB59959AA5412A7565423EA7BAB | SHA256:99653A38C445AE1D4C373EE672339FD47FD098E0D0ADA5F0BE70E3B2BF711D38 | |||
| 4236 | Blackmatter-Sample2.exe | C:\Users\Administrator\Searches\winrt--{S-1-5-21-1693682860-607145093-2874071422-500}-.searchconnector-ms.AwlCQEBCC | xml | |
MD5:F26188A4891D18E9C99D55118E1A06AE | SHA256:4EABB8A700B57032952A8AE8353B400D14A688690F92F15F9B84520E016CF5C7 | |||
| 4236 | Blackmatter-Sample2.exe | C:\Users\Administrator\Searches\AwlCQEBCC.README.txt | text | |
MD5:F66968C47A64569E2281F65A95991BE0 | SHA256:4B950C763006E7C4569DF8742855CEC31BF82F835BD7E2BDCB5F128DB34C82BF | |||
| 4236 | Blackmatter-Sample2.exe | C:\Users\Administrator\Saved Games\AwlCQEBCC.README.txt | text | |
MD5:F66968C47A64569E2281F65A95991BE0 | SHA256:4B950C763006E7C4569DF8742855CEC31BF82F835BD7E2BDCB5F128DB34C82BF | |||
| 4236 | Blackmatter-Sample2.exe | C:\Users\Administrator\Pictures\AwlCQEBCC.README.txt | text | |
MD5:F66968C47A64569E2281F65A95991BE0 | SHA256:4B950C763006E7C4569DF8742855CEC31BF82F835BD7E2BDCB5F128DB34C82BF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
28
DNS requests
20
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4236 | Blackmatter-Sample2.exe | GET | 200 | 192.124.249.22:80 | http://ocsp.godaddy.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQdI2%2BOBkuXH93foRUj4a7lAr4rGwQUOpqFBxBnKLbv9r0FQW4gwZTaD94CAQc%3D | unknown | — | — | whitelisted |
4236 | Blackmatter-Sample2.exe | GET | 200 | 192.124.249.22:80 | http://ocsp.godaddy.com//MEowSDBGMEQwQjAJBgUrDgMCGgUABBS2CA1fbGt26xPkOKX4ZguoUjM0TgQUQMK9J47MNIMwojPX%2B2yz8LQsgM4CCQDVVyUFdQxn%2Fw%3D%3D | unknown | — | — | whitelisted |
4236 | Blackmatter-Sample2.exe | POST | 405 | 3.33.130.190:80 | http://mojobiden.com/?fWOK2C3Yn=Px4nFcHsOCS8kOVZPG&AbH3=2DPXlPVAOfLG3&Hr1DYWh1O=gqI42FpFbdbdVKyB | unknown | — | — | malicious |
4236 | Blackmatter-Sample2.exe | POST | 405 | 3.33.130.190:80 | http://mojobiden.com/?xkyRmw=Umt&N5WE1=M1FXJ&P3L13=JuIL&WCxnLEpB=knuUL&GqgPR=vyHEoI&8J6oKv=OELrAsJ&Y1p2USY=61Yh4R&xeLvt=I9XA&mSV9=gcMasxxXB | unknown | — | — | malicious |
5612 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2368 | SIHClient.exe | GET | 200 | 23.32.97.216:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2368 | SIHClient.exe | GET | 200 | 23.32.97.216:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3388 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4236 | Blackmatter-Sample2.exe | 3.33.130.190:443 | mojobiden.com | AMAZON-02 | US | malicious |
4236 | Blackmatter-Sample2.exe | 192.124.249.22:80 | ocsp.godaddy.com | SUCURI-SEC | US | whitelisted |
4236 | Blackmatter-Sample2.exe | 3.33.130.190:80 | mojobiden.com | AMAZON-02 | US | malicious |
2336 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
5612 | svchost.exe | 20.190.160.5:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
paymenthacks.com |
| malicious |
mojobiden.com |
| malicious |
ocsp.godaddy.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2200 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE BlackMatter CnC Domain in DNS Lookup (mojobiden .com) |
2200 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE BlackMatter CnC Domain in DNS Lookup (paymenthacks .com) |
4236 | Blackmatter-Sample2.exe | Malware Command and Control Activity Detected | ET MALWARE BlackMatter CnC Activity |
4236 | Blackmatter-Sample2.exe | Malware Command and Control Activity Detected | ET MALWARE BlackMatter CnC Activity |
4236 | Blackmatter-Sample2.exe | Malware Command and Control Activity Detected | ET MALWARE BlackMatter CnC Activity |
4236 | Blackmatter-Sample2.exe | Malware Command and Control Activity Detected | ET MALWARE BlackMatter CnC Activity |
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |