| File name: | 2025-05-18_a8aa678fb6185135029f2ce7ee2e1c25_black-basta_cobalt-strike_satacom |
| Full analysis: | https://app.any.run/tasks/e2262505-64ae-4601-bca3-0500c119890d |
| Verdict: | Malicious activity |
| Threats: | Quasar is a very popular RAT in the world thanks to its code being available in open-source. This malware can be used to control the victim’s computer remotely. |
| Analysis date: | May 18, 2025, 05:16:42 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 7 sections |
| MD5: | A8AA678FB6185135029F2CE7EE2E1C25 |
| SHA1: | 82F4E09CFA14FC4B90AEF33FE049B56FEBA56FA6 |
| SHA256: | 22A5105CF9E4B64E4ADE150BA42A9E691C04844F60D4CC7065615E11D2EDF967 |
| SSDEEP: | 98304:w1T2Q6lr2Moo5RbDmRxiJ6yiVhUo895kIPYjA7AWP0c8T2DE6f7Iev6O3MdYeWqk:lmUEbLbwH3e3t27WQyreqdLZ5 |
MALICIOUS
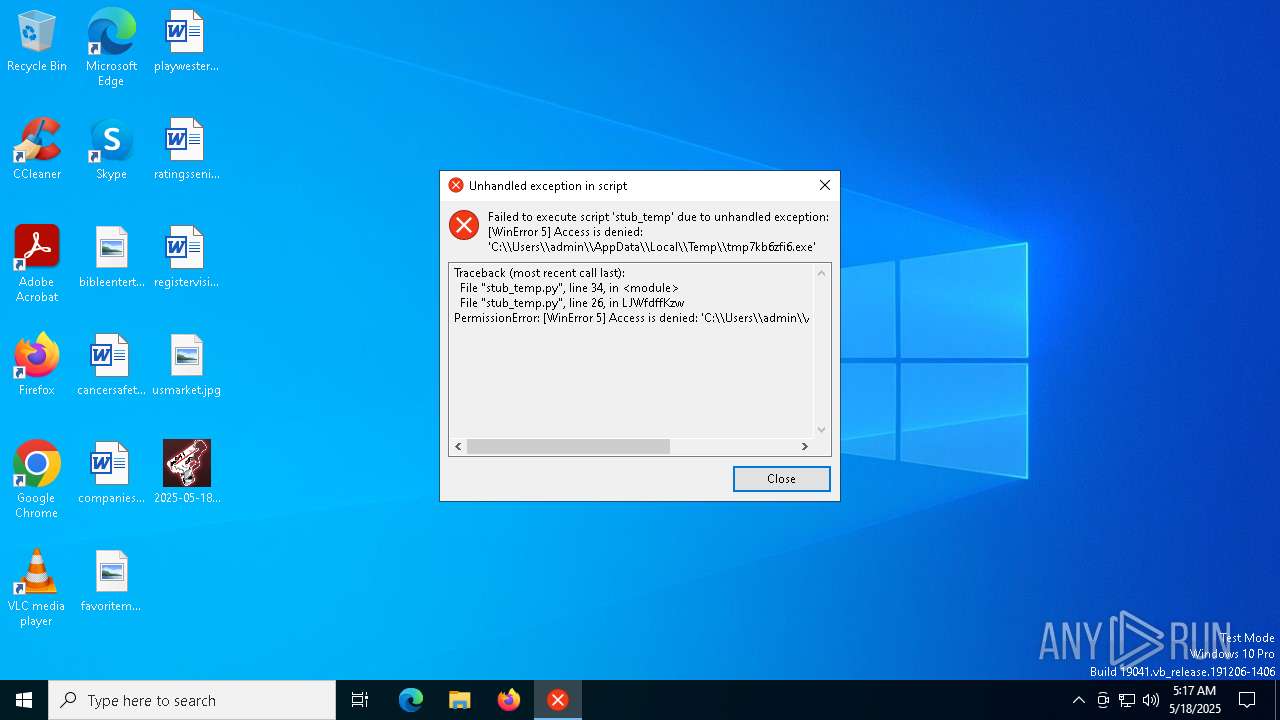
QUASAR has been detected (YARA)
- tmp7kb6zfi6.exe (PID: 7428)
SUSPICIOUS
The process drops C-runtime libraries
- 2025-05-18_a8aa678fb6185135029f2ce7ee2e1c25_black-basta_cobalt-strike_satacom.exe (PID: 7352)
Process drops python dynamic module
- 2025-05-18_a8aa678fb6185135029f2ce7ee2e1c25_black-basta_cobalt-strike_satacom.exe (PID: 7352)
Process drops legitimate windows executable
- 2025-05-18_a8aa678fb6185135029f2ce7ee2e1c25_black-basta_cobalt-strike_satacom.exe (PID: 7352)
Executable content was dropped or overwritten
- 2025-05-18_a8aa678fb6185135029f2ce7ee2e1c25_black-basta_cobalt-strike_satacom.exe (PID: 7352)
- 2025-05-18_a8aa678fb6185135029f2ce7ee2e1c25_black-basta_cobalt-strike_satacom.exe (PID: 7392)
Application launched itself
- 2025-05-18_a8aa678fb6185135029f2ce7ee2e1c25_black-basta_cobalt-strike_satacom.exe (PID: 7352)
Loads Python modules
- 2025-05-18_a8aa678fb6185135029f2ce7ee2e1c25_black-basta_cobalt-strike_satacom.exe (PID: 7392)
Reads security settings of Internet Explorer
- 2025-05-18_a8aa678fb6185135029f2ce7ee2e1c25_black-basta_cobalt-strike_satacom.exe (PID: 7392)
Reads the date of Windows installation
- 2025-05-18_a8aa678fb6185135029f2ce7ee2e1c25_black-basta_cobalt-strike_satacom.exe (PID: 7392)
There is functionality for taking screenshot (YARA)
- tmp7kb6zfi6.exe (PID: 7428)
INFO
Reads the computer name
- 2025-05-18_a8aa678fb6185135029f2ce7ee2e1c25_black-basta_cobalt-strike_satacom.exe (PID: 7352)
- 2025-05-18_a8aa678fb6185135029f2ce7ee2e1c25_black-basta_cobalt-strike_satacom.exe (PID: 7392)
- tmp7kb6zfi6.exe (PID: 7428)
Checks supported languages
- 2025-05-18_a8aa678fb6185135029f2ce7ee2e1c25_black-basta_cobalt-strike_satacom.exe (PID: 7352)
- 2025-05-18_a8aa678fb6185135029f2ce7ee2e1c25_black-basta_cobalt-strike_satacom.exe (PID: 7392)
- tmp7kb6zfi6.exe (PID: 7428)
Create files in a temporary directory
- 2025-05-18_a8aa678fb6185135029f2ce7ee2e1c25_black-basta_cobalt-strike_satacom.exe (PID: 7352)
- 2025-05-18_a8aa678fb6185135029f2ce7ee2e1c25_black-basta_cobalt-strike_satacom.exe (PID: 7392)
The sample compiled with english language support
- 2025-05-18_a8aa678fb6185135029f2ce7ee2e1c25_black-basta_cobalt-strike_satacom.exe (PID: 7352)
Process checks computer location settings
- 2025-05-18_a8aa678fb6185135029f2ce7ee2e1c25_black-basta_cobalt-strike_satacom.exe (PID: 7392)
Reads Environment values
- tmp7kb6zfi6.exe (PID: 7428)
Reads the machine GUID from the registry
- tmp7kb6zfi6.exe (PID: 7428)
Checks proxy server information
- slui.exe (PID: 7680)
Reads the software policy settings
- slui.exe (PID: 7680)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Quasar
(PID) Process(7428) tmp7kb6zfi6.exe
Version1.4.1
C2 (2)7.tcp.eu.ngrok.io:16881
Sub_Dir.cache
Install_Namesystemhelper.exe
Mutex915c20ea-728d-4e78-963c-d08d6ba1ec9b
Startupwinupdate32
Tagsystemhelper
LogDirLogs
SignatureBseB8csngrIWO0D6p8aoOURxodMukGVjMieDGf+FJ0Hw97D48fnnS9FVkXty270avNb7h1empMwxDLbvTF7bTRQGqMrXafglR4Bc7RiISJErJHe9aMPNIILm0CZsfZSgRq5RLGfYoFqH0emSakSI+Odt0V4+ug4e1bLqD36ffyvWwhyW1Scxpa82Zbmx14pWq3kY4r2J+MzW0GMW7ej0UivSFD3S3XgI+mYULJGhd884litsk5jYi+S/dYV62KAggL2h75tTRYt68inOdIRVycx2JS5I72SnwAfokEIrsqDM...
CertificateMIIE9DCCAtygAwIBAgIQAL30S7yOc5gfjcx1GnGVITANBgkqhkiG9w0BAQ0FADAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMCAXDTI1MDUxMjE2MjgyM1oYDzk5OTkxMjMxMjM1OTU5WjAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEAyHSLn74quKrJOH/Oa9uxN26emD+OgKv45h/aR+A84+V47LJKCHevz6WBZSUrakXhfktTNIvt...
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:05:17 00:06:27+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.42 |
| CodeSize: | 173568 |
| InitializedDataSize: | 365056 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xce20 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
123
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 7352 | "C:\Users\admin\Desktop\2025-05-18_a8aa678fb6185135029f2ce7ee2e1c25_black-basta_cobalt-strike_satacom.exe" | C:\Users\admin\Desktop\2025-05-18_a8aa678fb6185135029f2ce7ee2e1c25_black-basta_cobalt-strike_satacom.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 7392 | "C:\Users\admin\Desktop\2025-05-18_a8aa678fb6185135029f2ce7ee2e1c25_black-basta_cobalt-strike_satacom.exe" | C:\Users\admin\Desktop\2025-05-18_a8aa678fb6185135029f2ce7ee2e1c25_black-basta_cobalt-strike_satacom.exe | 2025-05-18_a8aa678fb6185135029f2ce7ee2e1c25_black-basta_cobalt-strike_satacom.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 7428 | "C:\Users\admin\AppData\Local\Temp\tmp7kb6zfi6.exe" | C:\Users\admin\AppData\Local\Temp\tmp7kb6zfi6.exe | 2025-05-18_a8aa678fb6185135029f2ce7ee2e1c25_black-basta_cobalt-strike_satacom.exe | ||||||||||||
User: admin Company: Microsoft Corp Integrity Level: MEDIUM Description: System Maintenance Tool Version: 1.0.1.1 Modules
Quasar(PID) Process(7428) tmp7kb6zfi6.exe Version1.4.1 C2 (2)7.tcp.eu.ngrok.io:16881 Sub_Dir.cache Install_Namesystemhelper.exe Mutex915c20ea-728d-4e78-963c-d08d6ba1ec9b Startupwinupdate32 Tagsystemhelper LogDirLogs SignatureBseB8csngrIWO0D6p8aoOURxodMukGVjMieDGf+FJ0Hw97D48fnnS9FVkXty270avNb7h1empMwxDLbvTF7bTRQGqMrXafglR4Bc7RiISJErJHe9aMPNIILm0CZsfZSgRq5RLGfYoFqH0emSakSI+Odt0V4+ug4e1bLqD36ffyvWwhyW1Scxpa82Zbmx14pWq3kY4r2J+MzW0GMW7ej0UivSFD3S3XgI+mYULJGhd884litsk5jYi+S/dYV62KAggL2h75tTRYt68inOdIRVycx2JS5I72SnwAfokEIrsqDM... CertificateMIIE9DCCAtygAwIBAgIQAL30S7yOc5gfjcx1GnGVITANBgkqhkiG9w0BAQ0FADAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMCAXDTI1MDUxMjE2MjgyM1oYDzk5OTkxMjMxMjM1OTU5WjAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEAyHSLn74quKrJOH/Oa9uxN26emD+OgKv45h/aR+A84+V47LJKCHevz6WBZSUrakXhfktTNIvt... | |||||||||||||||
| 7680 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
4 028
Read events
4 028
Write events
0
Delete events
0
Modification events
Executable files
104
Suspicious files
1
Text files
14
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7352 | 2025-05-18_a8aa678fb6185135029f2ce7ee2e1c25_black-basta_cobalt-strike_satacom.exe | C:\Users\admin\AppData\Local\Temp\_MEI73522\Crypto\Cipher\_raw_aesni.pyd | executable | |
MD5:22008913F02D3EB99106167F47310C84 | SHA256:1299671282571743D7E88B445750916433DC2DF80C4696AB7B2B0438B0855B83 | |||
| 7352 | 2025-05-18_a8aa678fb6185135029f2ce7ee2e1c25_black-basta_cobalt-strike_satacom.exe | C:\Users\admin\AppData\Local\Temp\_MEI73522\Crypto\Cipher\_raw_blowfish.pyd | executable | |
MD5:C7F70FBFB429D18144BCEAFF5FCC268B | SHA256:C883025EA591713C9C8CFA9DA76C528F7A75BDD0853B877A55C4C639DBAA595F | |||
| 7352 | 2025-05-18_a8aa678fb6185135029f2ce7ee2e1c25_black-basta_cobalt-strike_satacom.exe | C:\Users\admin\AppData\Local\Temp\_MEI73522\Crypto\Cipher\_chacha20.pyd | executable | |
MD5:0114E07B71F554D9696789BA4100062F | SHA256:ECB6C3CCB37BEE0A8B2A5C31C15ACA500C6AEEDDE825A749479660F65CCED39D | |||
| 7352 | 2025-05-18_a8aa678fb6185135029f2ce7ee2e1c25_black-basta_cobalt-strike_satacom.exe | C:\Users\admin\AppData\Local\Temp\_MEI73522\Crypto\Cipher\_Salsa20.pyd | executable | |
MD5:B27444F62C2050FE3DF13A92663FA174 | SHA256:10037AE4A433426966098AF1C7FCB8DA3F9BF6698C629B9EFA098EEB20ABED5E | |||
| 7352 | 2025-05-18_a8aa678fb6185135029f2ce7ee2e1c25_black-basta_cobalt-strike_satacom.exe | C:\Users\admin\AppData\Local\Temp\_MEI73522\Crypto\Cipher\_ARC4.pyd | executable | |
MD5:657643049554B6FF747D7FE645E4CCC7 | SHA256:0EC5270929B9A8E347BE684E2699D2C72A965B3304045475BBC06F3965CBC6B5 | |||
| 7352 | 2025-05-18_a8aa678fb6185135029f2ce7ee2e1c25_black-basta_cobalt-strike_satacom.exe | C:\Users\admin\AppData\Local\Temp\_MEI73522\Crypto\Cipher\_pkcs1_decode.pyd | executable | |
MD5:8F5AF0BA701B493041777FC34185B7B7 | SHA256:4BE10912BFC5F2372CC030CC9EA94E83048683481FBD7F26BA7F95641AC9E9B4 | |||
| 7352 | 2025-05-18_a8aa678fb6185135029f2ce7ee2e1c25_black-basta_cobalt-strike_satacom.exe | C:\Users\admin\AppData\Local\Temp\_MEI73522\Crypto\Cipher\_raw_aes.pyd | executable | |
MD5:A927B92173974652EE1570F53A5B419D | SHA256:3A01018171AEEFAE474A6791F0318DAA3373731B7D0F3C165118DF5C12DA3B41 | |||
| 7352 | 2025-05-18_a8aa678fb6185135029f2ce7ee2e1c25_black-basta_cobalt-strike_satacom.exe | C:\Users\admin\AppData\Local\Temp\_MEI73522\Crypto\Cipher\_raw_des.pyd | executable | |
MD5:36836C859F54C2D6D6E7210E691B90D3 | SHA256:042DD37D6E721953EA7F4C9A2174DE9C57F6E9581636227724AC64B9318BA108 | |||
| 7352 | 2025-05-18_a8aa678fb6185135029f2ce7ee2e1c25_black-basta_cobalt-strike_satacom.exe | C:\Users\admin\AppData\Local\Temp\_MEI73522\Crypto\Cipher\_raw_ctr.pyd | executable | |
MD5:0A69F60B07A3D347BBCA4E02A796A397 | SHA256:D175DF6236B884968C059A61A4058273EEFB05C6B470EB79E8011AD2AE1ECE0C | |||
| 7352 | 2025-05-18_a8aa678fb6185135029f2ce7ee2e1c25_black-basta_cobalt-strike_satacom.exe | C:\Users\admin\AppData\Local\Temp\_MEI73522\Crypto\Cipher\_raw_cfb.pyd | executable | |
MD5:26ED0DD5AC8C656A62246A9C9F3E935C | SHA256:96F26FFAA3131134785F8C6F97A70F00AE1058A928514863838D88E8D6F406F9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
24
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2104 | svchost.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2140 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7680 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |