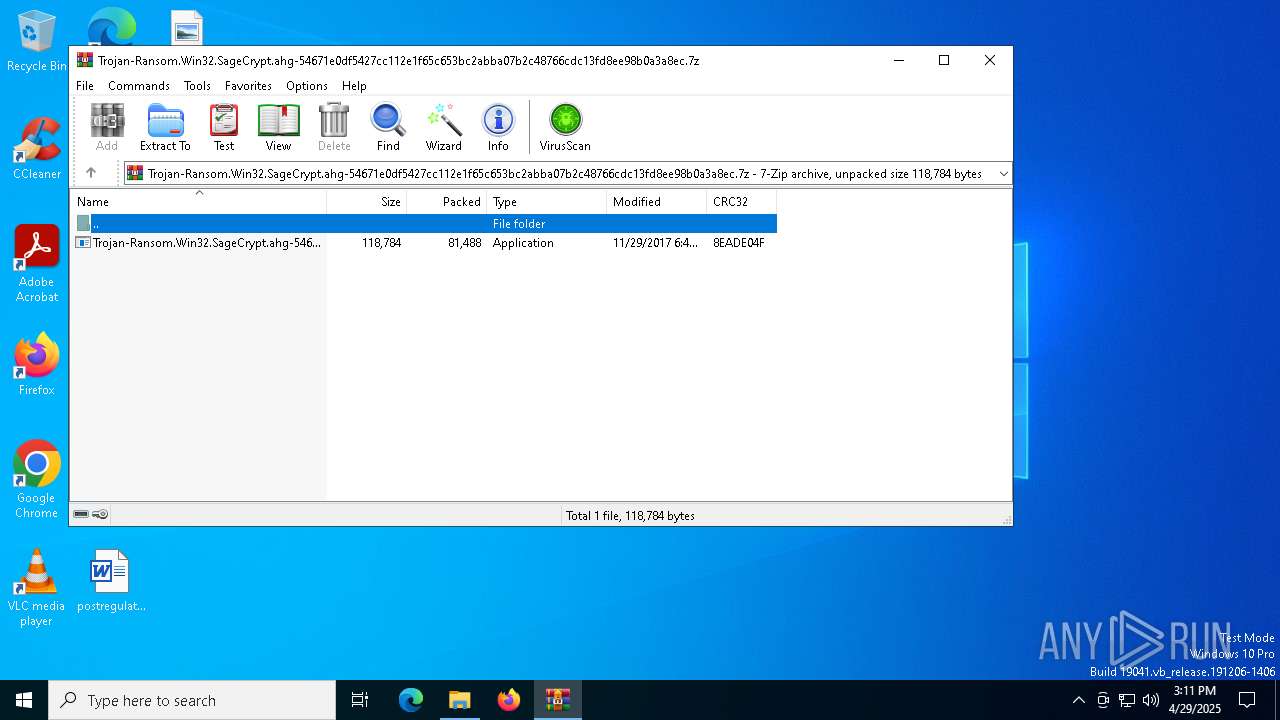
| File name: | Trojan-Ransom.Win32.SageCrypt.ahg-54671e0df5427cc112e1f65c653bc2abba07b2c48766cdc13fd8ee98b0a3a8ec.7z |
| Full analysis: | https://app.any.run/tasks/79496e97-b477-4fb0-92c6-18ffeb81d9fb |
| Verdict: | Malicious activity |
| Threats: | WarZone RAT is a remote access trojan, which is written in C++ and offered as a malware-as-a-service. It packs a wide range of capabilities, from stealing victims’ files and passwords to capturing desktop activities. WarZone RAT is primarily distributed via phishing emails and receives regular updates from its C2. |
| Analysis date: | April 29, 2025, 15:11:38 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | 08B8D8526C8B2EBB0F94F303752FEF0B |
| SHA1: | 375DCC3D4F73FF33464520E5895AB42E7A60CEF5 |
| SHA256: | 225D1954FE297F6A70C767295DDA951827D19C21C68CEE70AA2ECD0CF39411A9 |
| SSDEEP: | 1536:6wS9E/Wv+B8eBaYkH8WxWb2CwRZ7FBZptcBMmTj3Rhnu0A/SYwL27QxTAmX:6p+y+B8ekYk9xW6Z7FBZk/bj27ATAS |
MALICIOUS
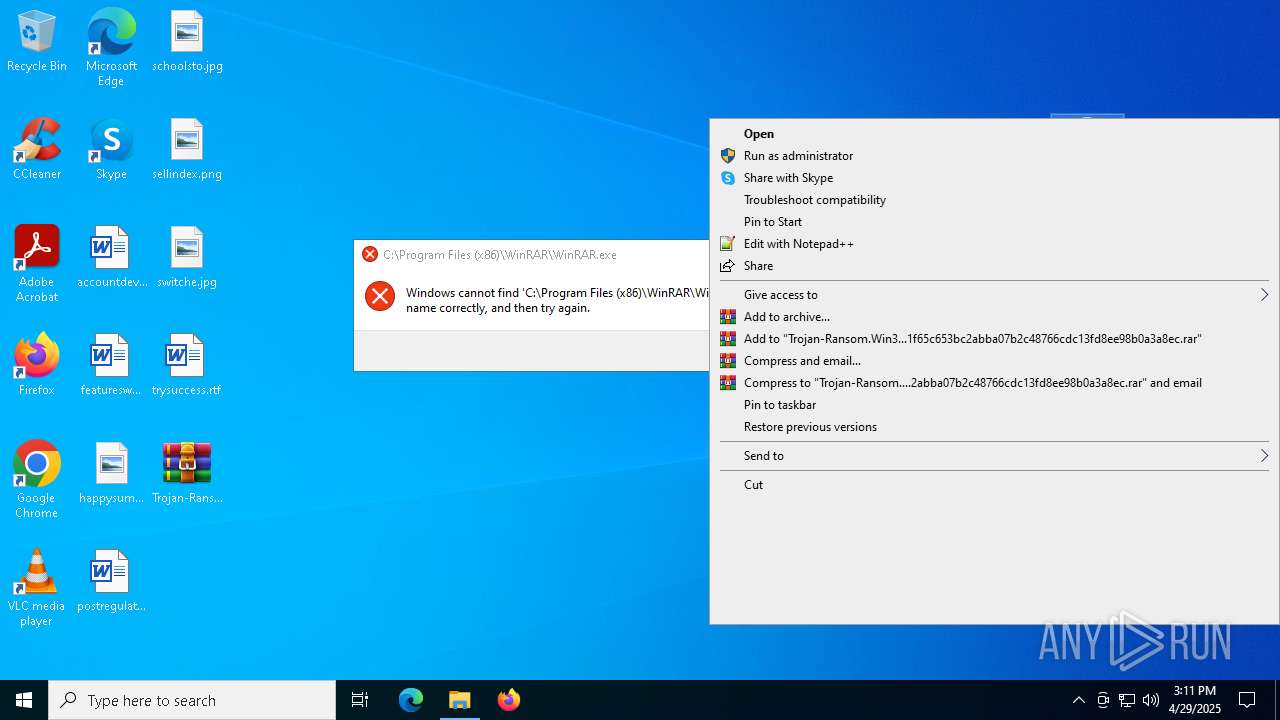
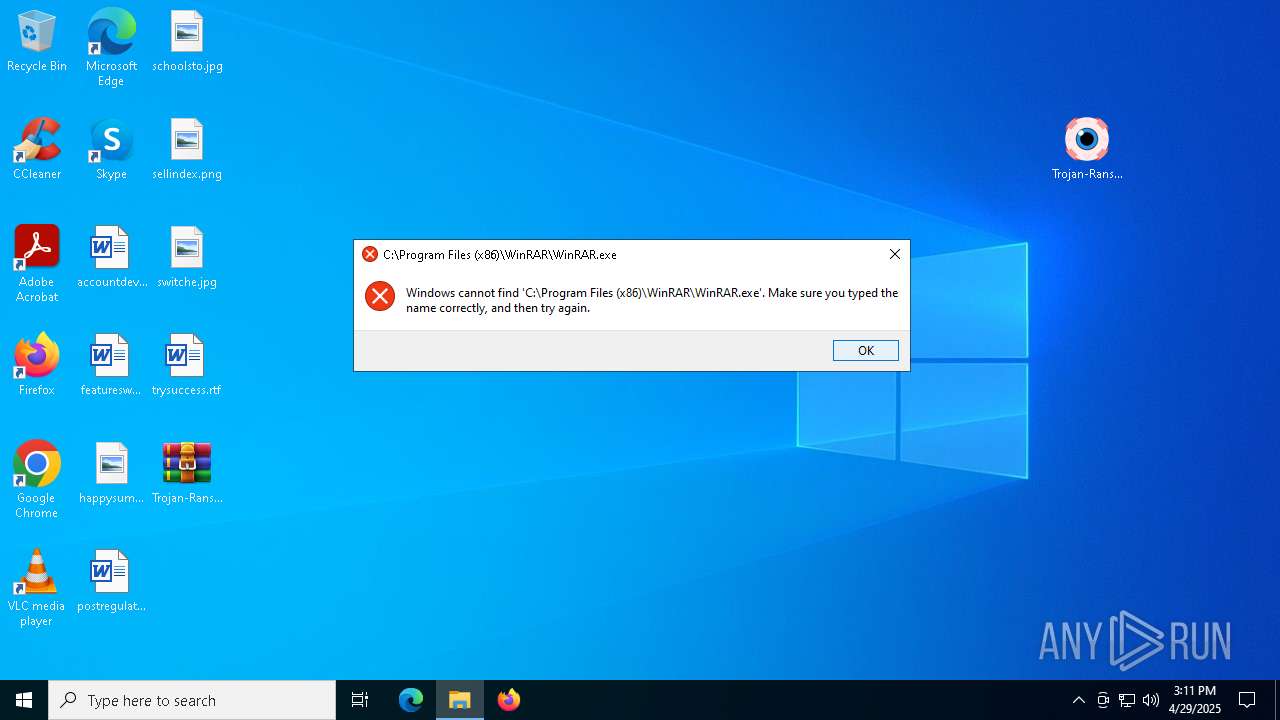
Generic archive extractor
- WinRAR.exe (PID: 4996)
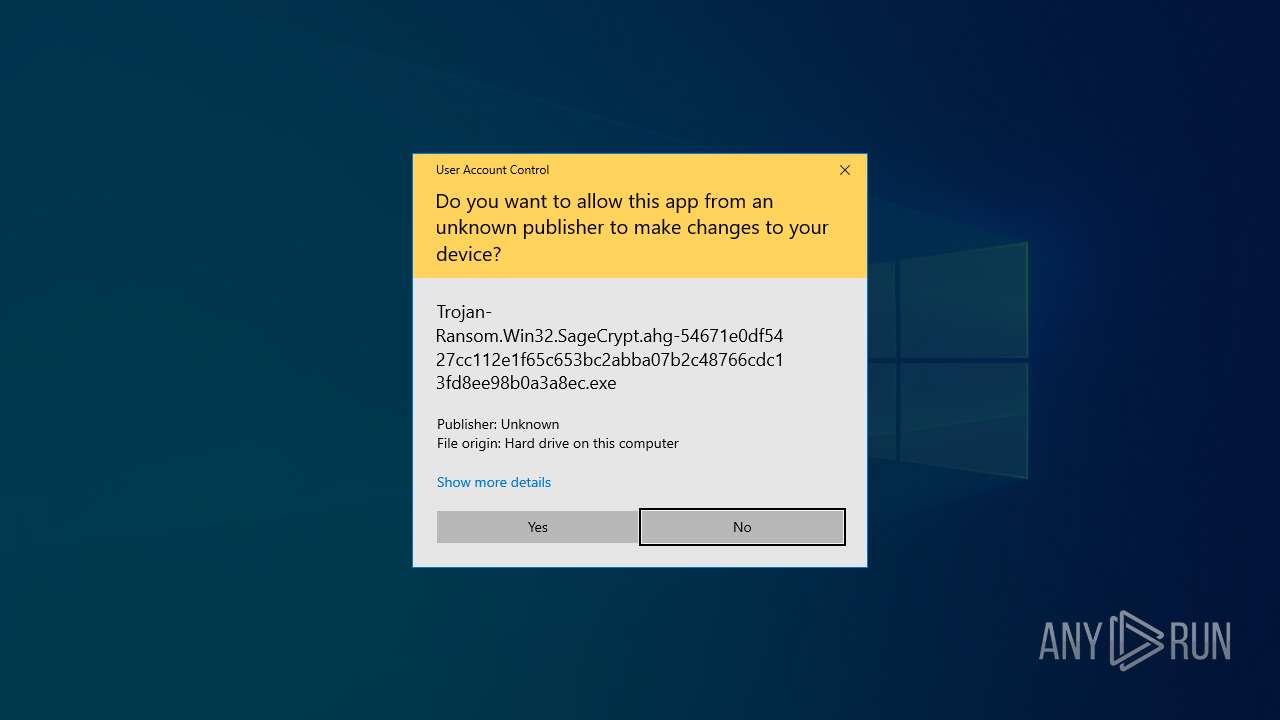
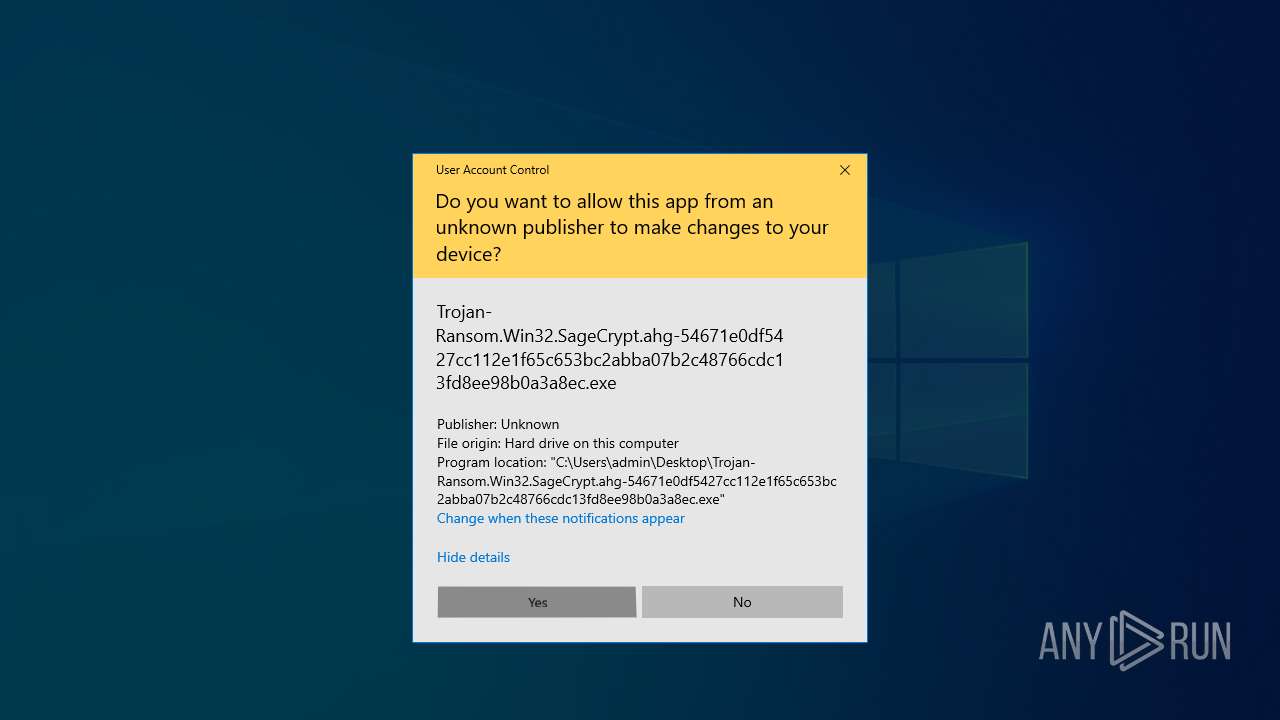
AVEMARIA mutex has been found
- Trojan-Ransom.Win32.SageCrypt.ahg-54671e0df5427cc112e1f65c653bc2abba07b2c48766cdc13fd8ee98b0a3a8ec.exe (PID: 5064)
SUSPICIOUS
Creates file in the systems drive root
- Trojan-Ransom.Win32.SageCrypt.ahg-54671e0df5427cc112e1f65c653bc2abba07b2c48766cdc13fd8ee98b0a3a8ec.exe (PID: 5064)
Application launched itself
- Trojan-Ransom.Win32.SageCrypt.ahg-54671e0df5427cc112e1f65c653bc2abba07b2c48766cdc13fd8ee98b0a3a8ec.exe (PID: 5064)
INFO
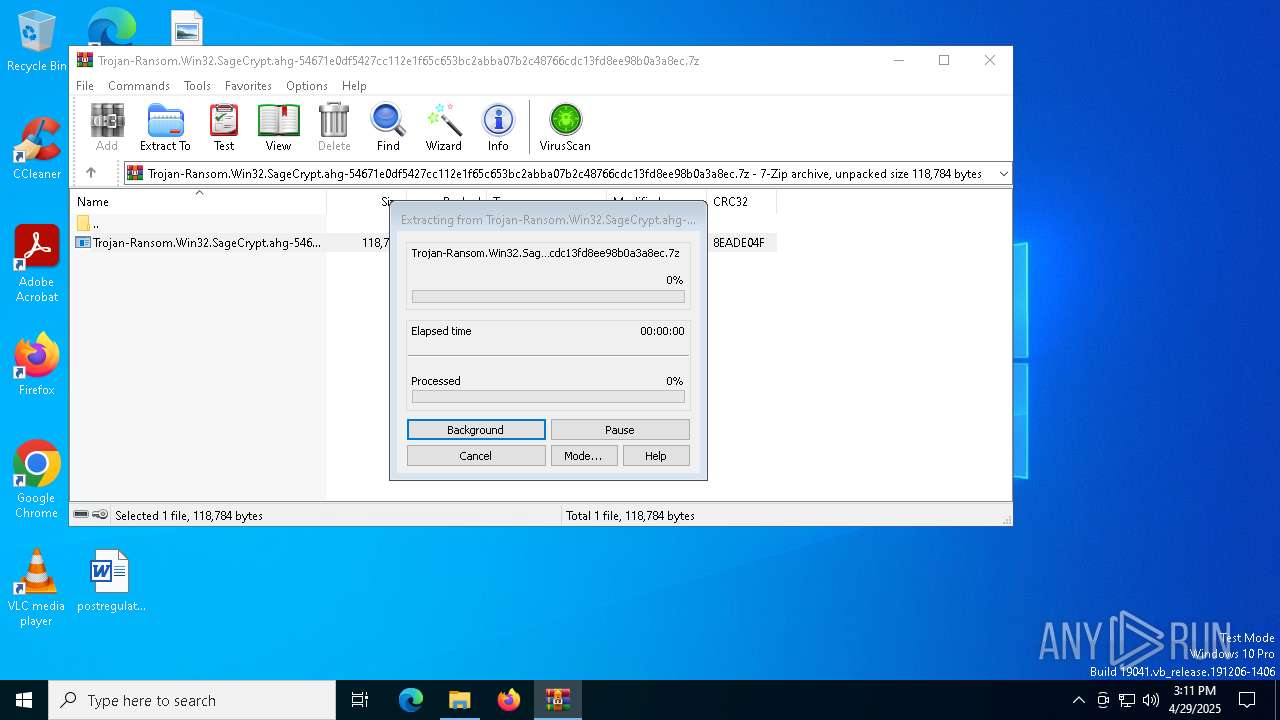
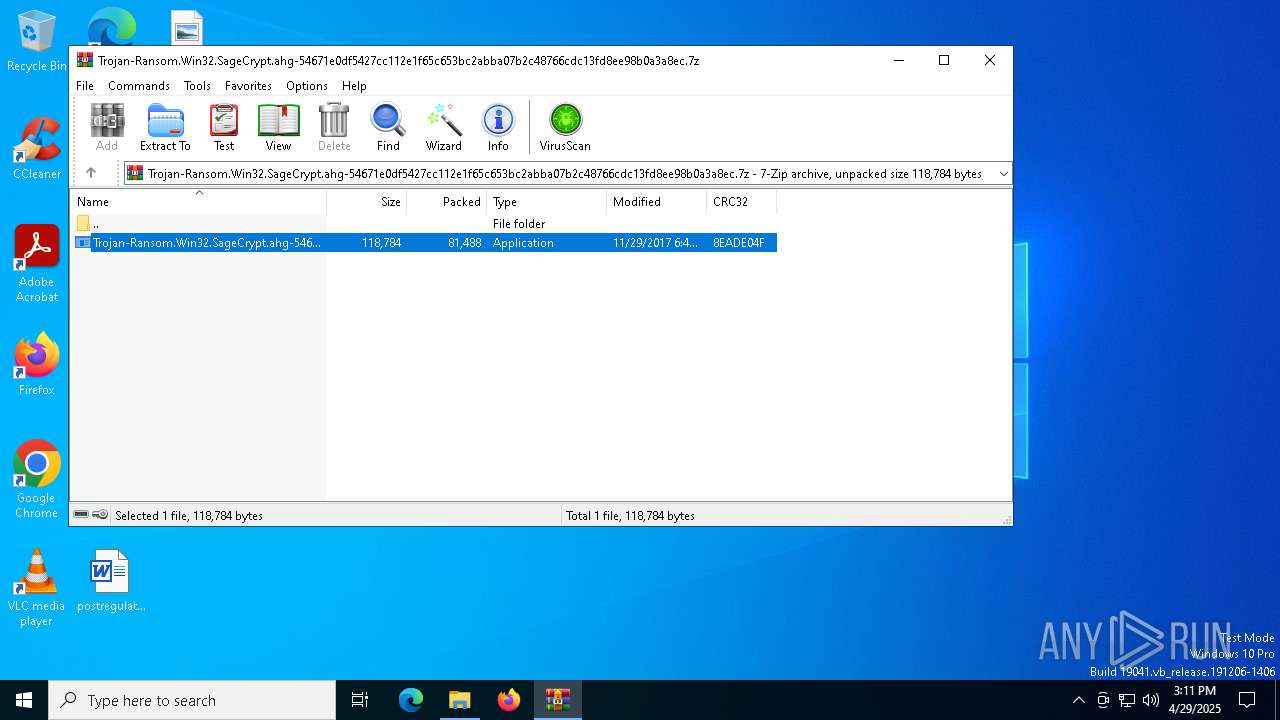
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4996)
Manual execution by a user
- Trojan-Ransom.Win32.SageCrypt.ahg-54671e0df5427cc112e1f65c653bc2abba07b2c48766cdc13fd8ee98b0a3a8ec.exe (PID: 5064)
Checks supported languages
- Trojan-Ransom.Win32.SageCrypt.ahg-54671e0df5427cc112e1f65c653bc2abba07b2c48766cdc13fd8ee98b0a3a8ec.exe (PID: 5064)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
EXIF
ZIP
| FileVersion: | 7z v0.04 |
|---|---|
| ModifyDate: | 2017:11:29 06:48:16+00:00 |
| ArchivedFileName: | Trojan-Ransom.Win32.SageCrypt.ahg-54671e0df5427cc112e1f65c653bc2abba07b2c48766cdc13fd8ee98b0a3a8ec.exe |
Total processes
330
Monitored processes
204
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 632 | C:\Users\admin\Desktop\Trojan-Ransom.Win32.SageCrypt.ahg-54671e0df5427cc112e1f65c653bc2abba07b2c48766cdc13fd8ee98b0a3a8ec.exe | C:\Users\admin\Desktop\Trojan-Ransom.Win32.SageCrypt.ahg-54671e0df5427cc112e1f65c653bc2abba07b2c48766cdc13fd8ee98b0a3a8ec.exe | — | Trojan-Ransom.Win32.SageCrypt.ahg-54671e0df5427cc112e1f65c653bc2abba07b2c48766cdc13fd8ee98b0a3a8ec.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 664 | C:\Users\admin\Desktop\Trojan-Ransom.Win32.SageCrypt.ahg-54671e0df5427cc112e1f65c653bc2abba07b2c48766cdc13fd8ee98b0a3a8ec.exe | C:\Users\admin\Desktop\Trojan-Ransom.Win32.SageCrypt.ahg-54671e0df5427cc112e1f65c653bc2abba07b2c48766cdc13fd8ee98b0a3a8ec.exe | — | Trojan-Ransom.Win32.SageCrypt.ahg-54671e0df5427cc112e1f65c653bc2abba07b2c48766cdc13fd8ee98b0a3a8ec.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 728 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 736 | C:\Users\admin\Desktop\Trojan-Ransom.Win32.SageCrypt.ahg-54671e0df5427cc112e1f65c653bc2abba07b2c48766cdc13fd8ee98b0a3a8ec.exe | C:\Users\admin\Desktop\Trojan-Ransom.Win32.SageCrypt.ahg-54671e0df5427cc112e1f65c653bc2abba07b2c48766cdc13fd8ee98b0a3a8ec.exe | — | Trojan-Ransom.Win32.SageCrypt.ahg-54671e0df5427cc112e1f65c653bc2abba07b2c48766cdc13fd8ee98b0a3a8ec.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 744 | C:\Users\admin\Desktop\Trojan-Ransom.Win32.SageCrypt.ahg-54671e0df5427cc112e1f65c653bc2abba07b2c48766cdc13fd8ee98b0a3a8ec.exe | C:\Users\admin\Desktop\Trojan-Ransom.Win32.SageCrypt.ahg-54671e0df5427cc112e1f65c653bc2abba07b2c48766cdc13fd8ee98b0a3a8ec.exe | — | Trojan-Ransom.Win32.SageCrypt.ahg-54671e0df5427cc112e1f65c653bc2abba07b2c48766cdc13fd8ee98b0a3a8ec.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 864 | C:\Users\admin\Desktop\Trojan-Ransom.Win32.SageCrypt.ahg-54671e0df5427cc112e1f65c653bc2abba07b2c48766cdc13fd8ee98b0a3a8ec.exe | C:\Users\admin\Desktop\Trojan-Ransom.Win32.SageCrypt.ahg-54671e0df5427cc112e1f65c653bc2abba07b2c48766cdc13fd8ee98b0a3a8ec.exe | — | Trojan-Ransom.Win32.SageCrypt.ahg-54671e0df5427cc112e1f65c653bc2abba07b2c48766cdc13fd8ee98b0a3a8ec.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 900 | C:\Users\admin\Desktop\Trojan-Ransom.Win32.SageCrypt.ahg-54671e0df5427cc112e1f65c653bc2abba07b2c48766cdc13fd8ee98b0a3a8ec.exe | C:\Users\admin\Desktop\Trojan-Ransom.Win32.SageCrypt.ahg-54671e0df5427cc112e1f65c653bc2abba07b2c48766cdc13fd8ee98b0a3a8ec.exe | — | Trojan-Ransom.Win32.SageCrypt.ahg-54671e0df5427cc112e1f65c653bc2abba07b2c48766cdc13fd8ee98b0a3a8ec.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 904 | C:\Users\admin\Desktop\Trojan-Ransom.Win32.SageCrypt.ahg-54671e0df5427cc112e1f65c653bc2abba07b2c48766cdc13fd8ee98b0a3a8ec.exe | C:\Users\admin\Desktop\Trojan-Ransom.Win32.SageCrypt.ahg-54671e0df5427cc112e1f65c653bc2abba07b2c48766cdc13fd8ee98b0a3a8ec.exe | — | Trojan-Ransom.Win32.SageCrypt.ahg-54671e0df5427cc112e1f65c653bc2abba07b2c48766cdc13fd8ee98b0a3a8ec.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 960 | C:\Users\admin\Desktop\Trojan-Ransom.Win32.SageCrypt.ahg-54671e0df5427cc112e1f65c653bc2abba07b2c48766cdc13fd8ee98b0a3a8ec.exe | C:\Users\admin\Desktop\Trojan-Ransom.Win32.SageCrypt.ahg-54671e0df5427cc112e1f65c653bc2abba07b2c48766cdc13fd8ee98b0a3a8ec.exe | — | Trojan-Ransom.Win32.SageCrypt.ahg-54671e0df5427cc112e1f65c653bc2abba07b2c48766cdc13fd8ee98b0a3a8ec.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1012 | C:\Users\admin\Desktop\Trojan-Ransom.Win32.SageCrypt.ahg-54671e0df5427cc112e1f65c653bc2abba07b2c48766cdc13fd8ee98b0a3a8ec.exe | C:\Users\admin\Desktop\Trojan-Ransom.Win32.SageCrypt.ahg-54671e0df5427cc112e1f65c653bc2abba07b2c48766cdc13fd8ee98b0a3a8ec.exe | — | Trojan-Ransom.Win32.SageCrypt.ahg-54671e0df5427cc112e1f65c653bc2abba07b2c48766cdc13fd8ee98b0a3a8ec.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
2 032
Read events
2 013
Write events
19
Delete events
0
Modification events
| (PID) Process: | (4996) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (4996) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (4996) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (4996) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Trojan-Ransom.Win32.SageCrypt.ahg-54671e0df5427cc112e1f65c653bc2abba07b2c48766cdc13fd8ee98b0a3a8ec.7z | |||
| (PID) Process: | (4996) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4996) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4996) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4996) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
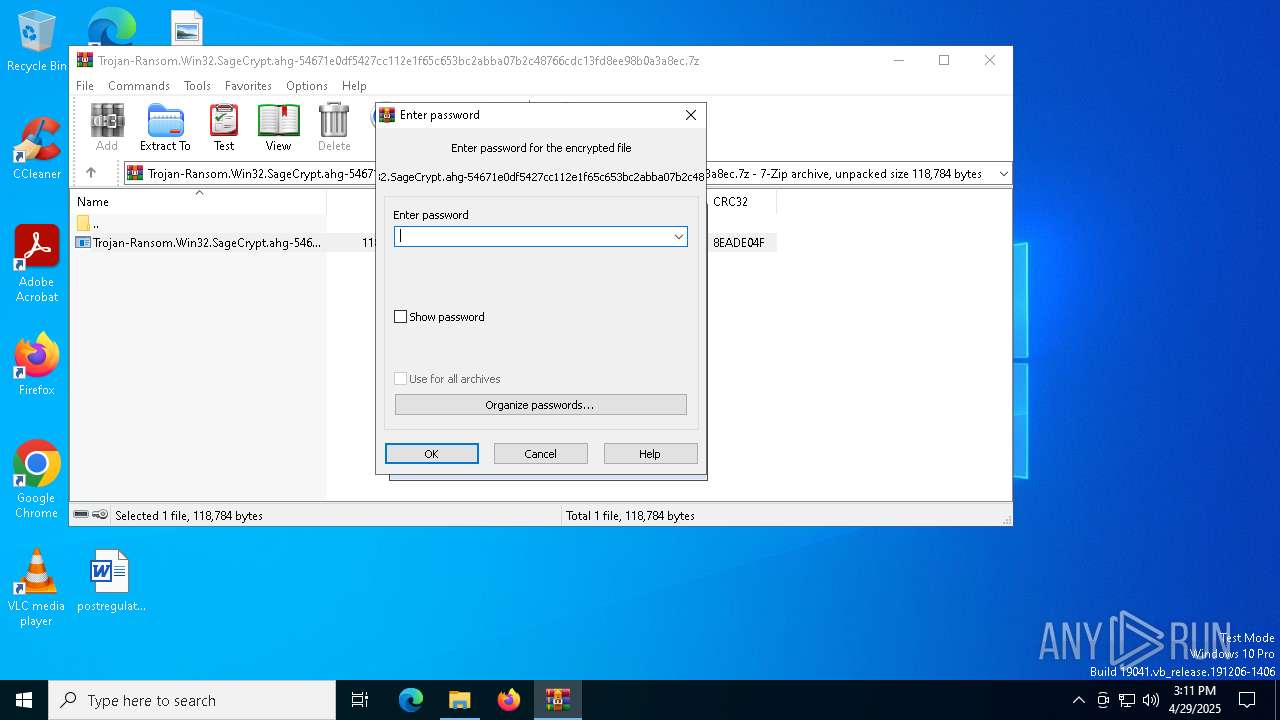
| (PID) Process: | (4996) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (4996) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4996 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb4996.31982\Trojan-Ransom.Win32.SageCrypt.ahg-54671e0df5427cc112e1f65c653bc2abba07b2c48766cdc13fd8ee98b0a3a8ec.exe | executable | |
MD5:AF600B0B81FB51E83BCFB1B89AA27FC1 | SHA256:54671E0DF5427CC112E1F65C653BC2ABBA07B2C48766CDC13FD8EE98B0A3A8EC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
13
DNS requests
8
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.160.17:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |