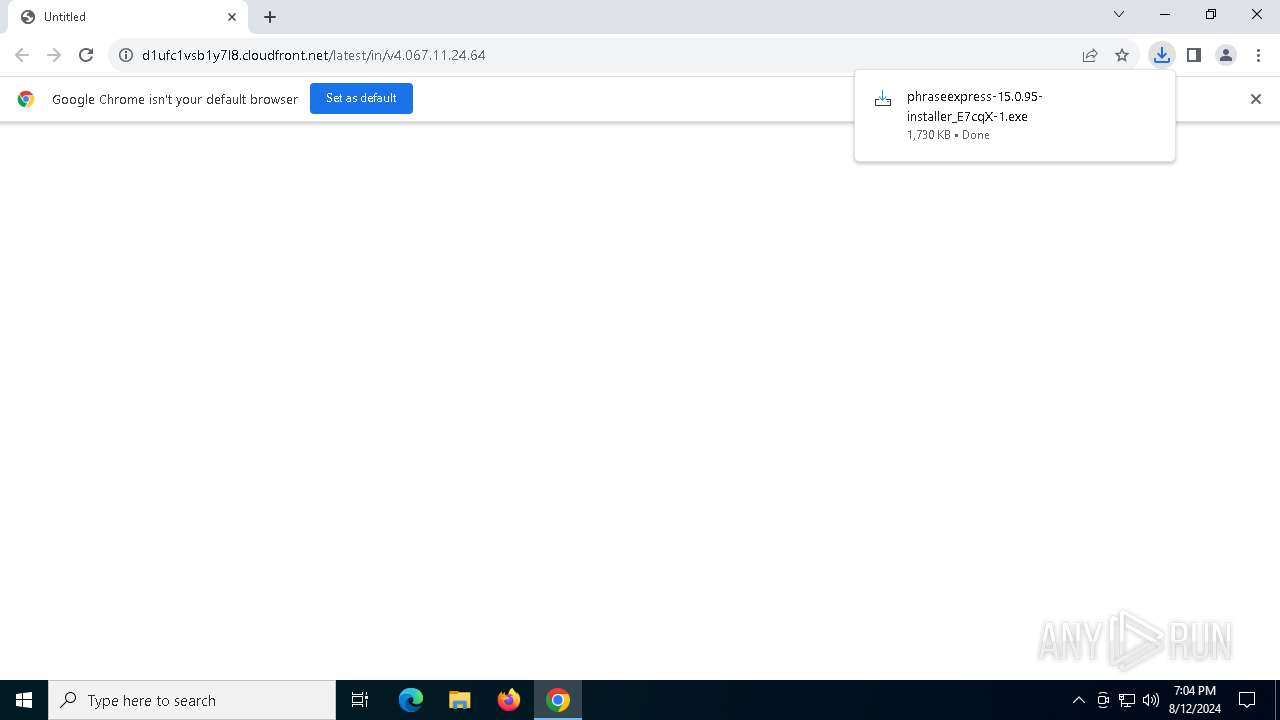
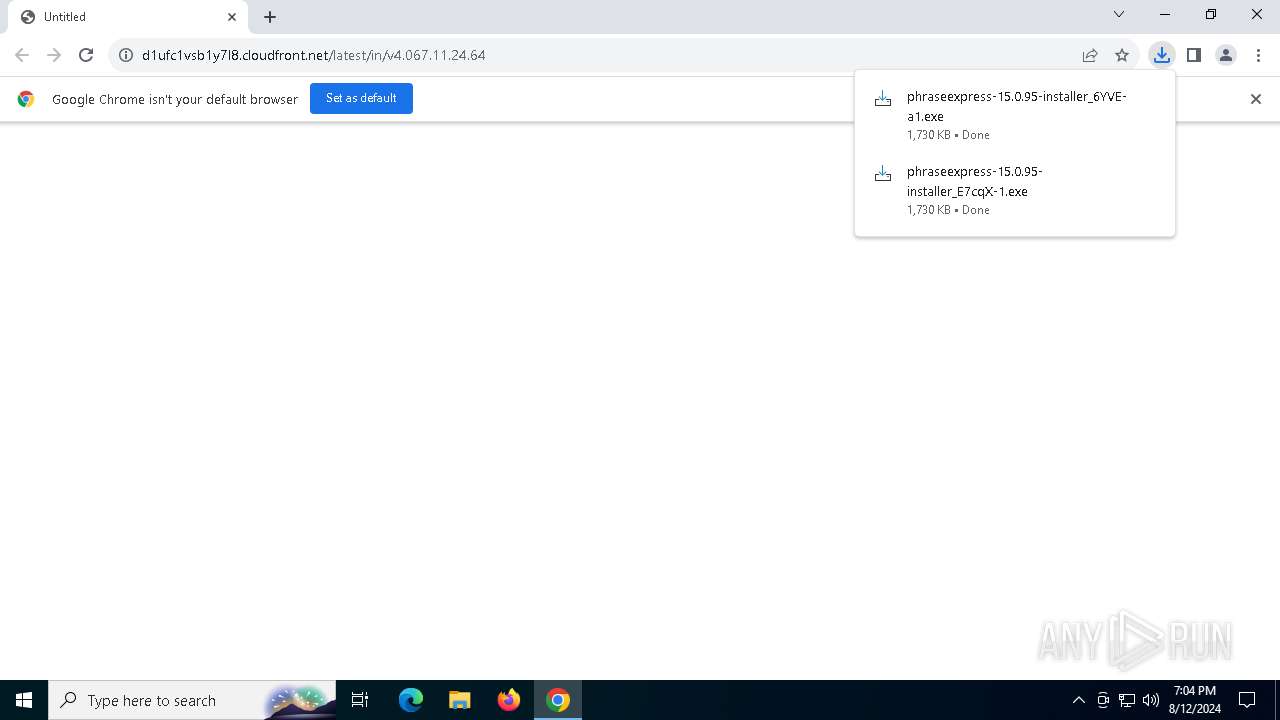
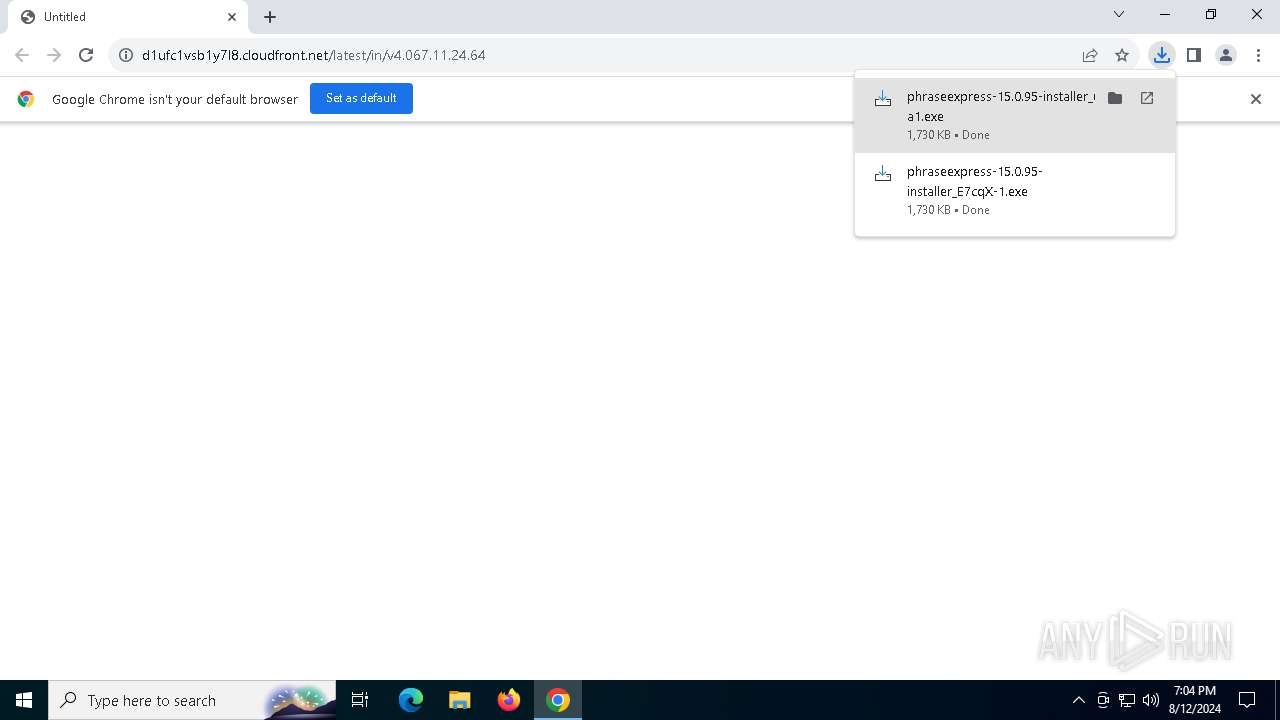
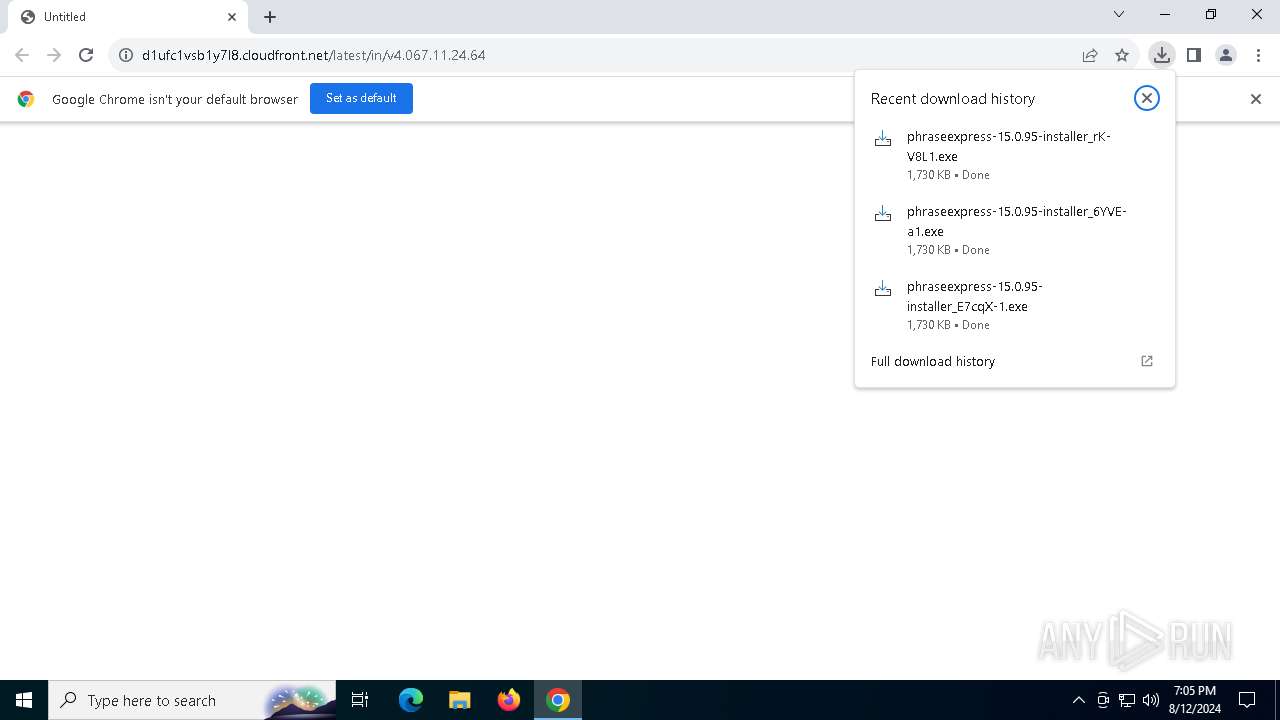
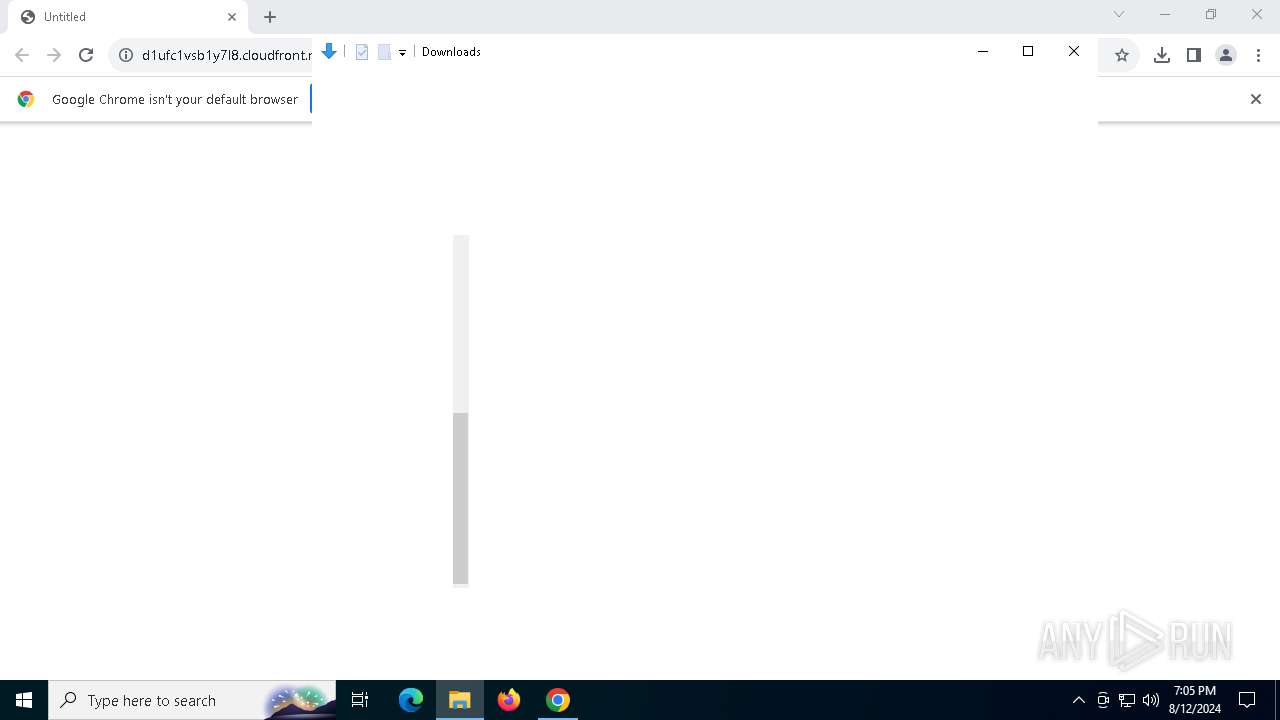
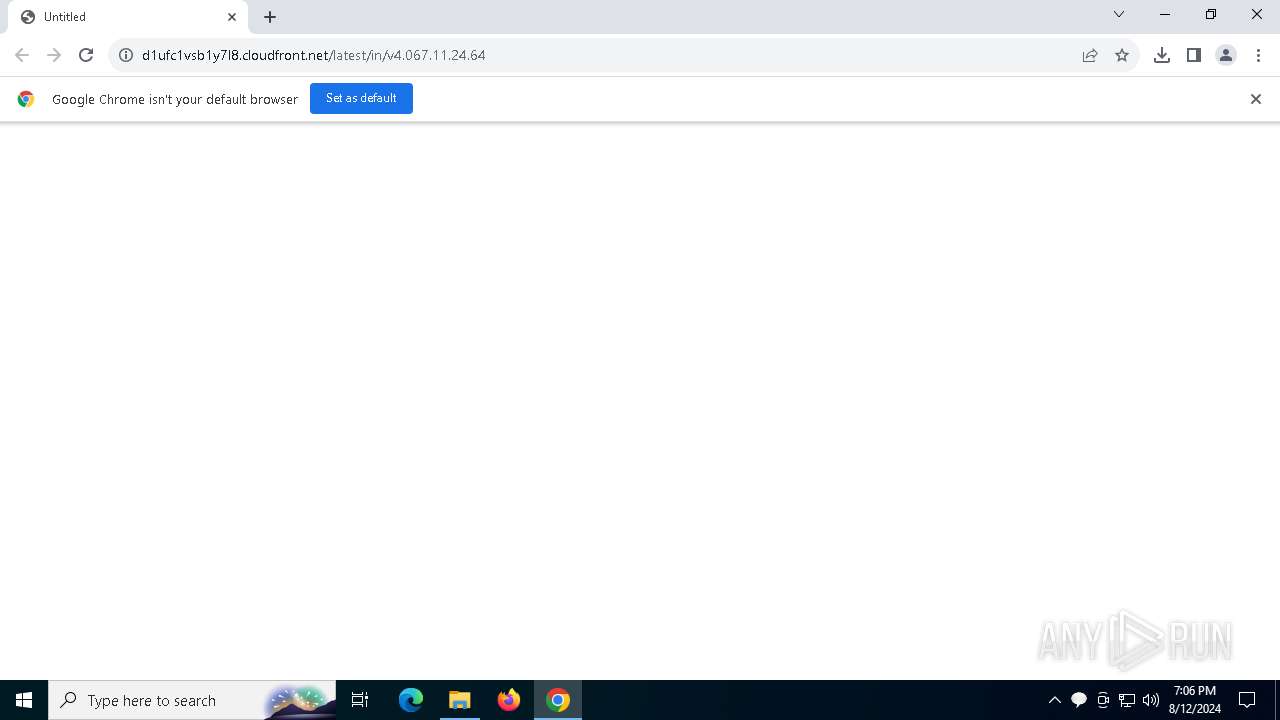
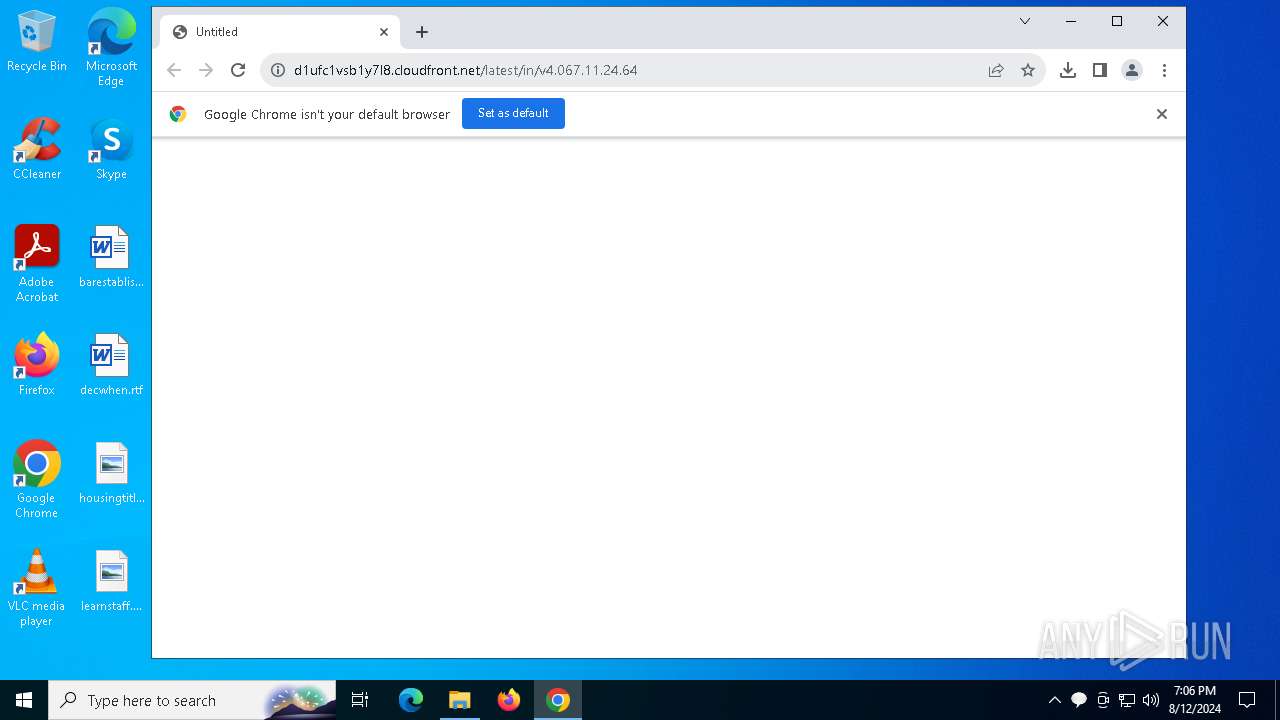
| URL: | https://d1ufc1vsb1y7l8.cloudfront.net/latest/in/v4.067.11.24.64 |
| Full analysis: | https://app.any.run/tasks/1b5a496f-6ec6-4f8f-9771-63f07c2ee59c |
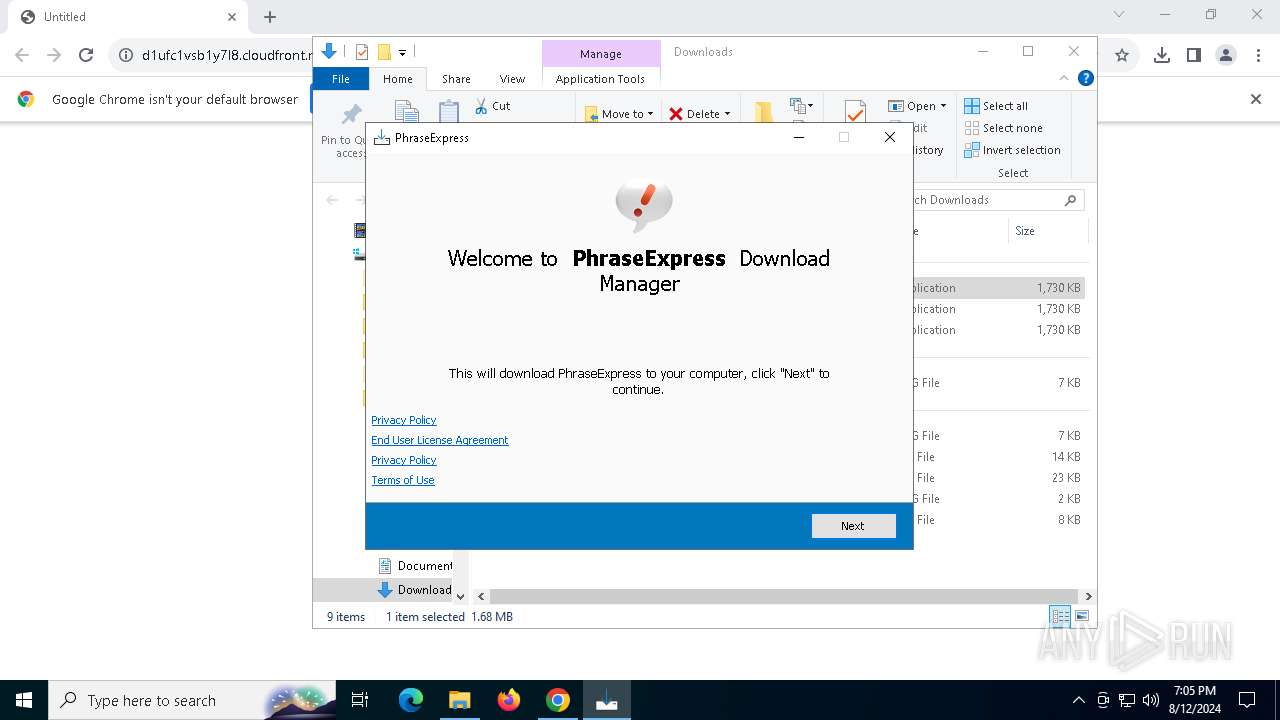
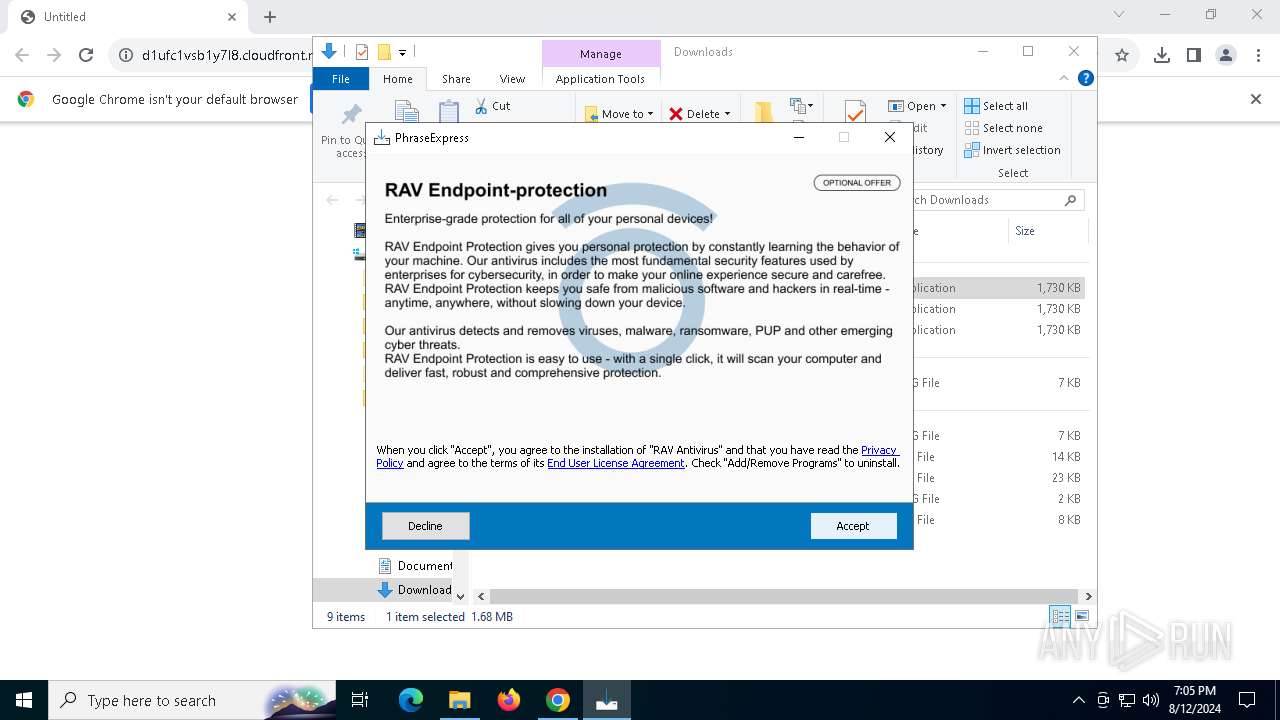
| Verdict: | Malicious activity |
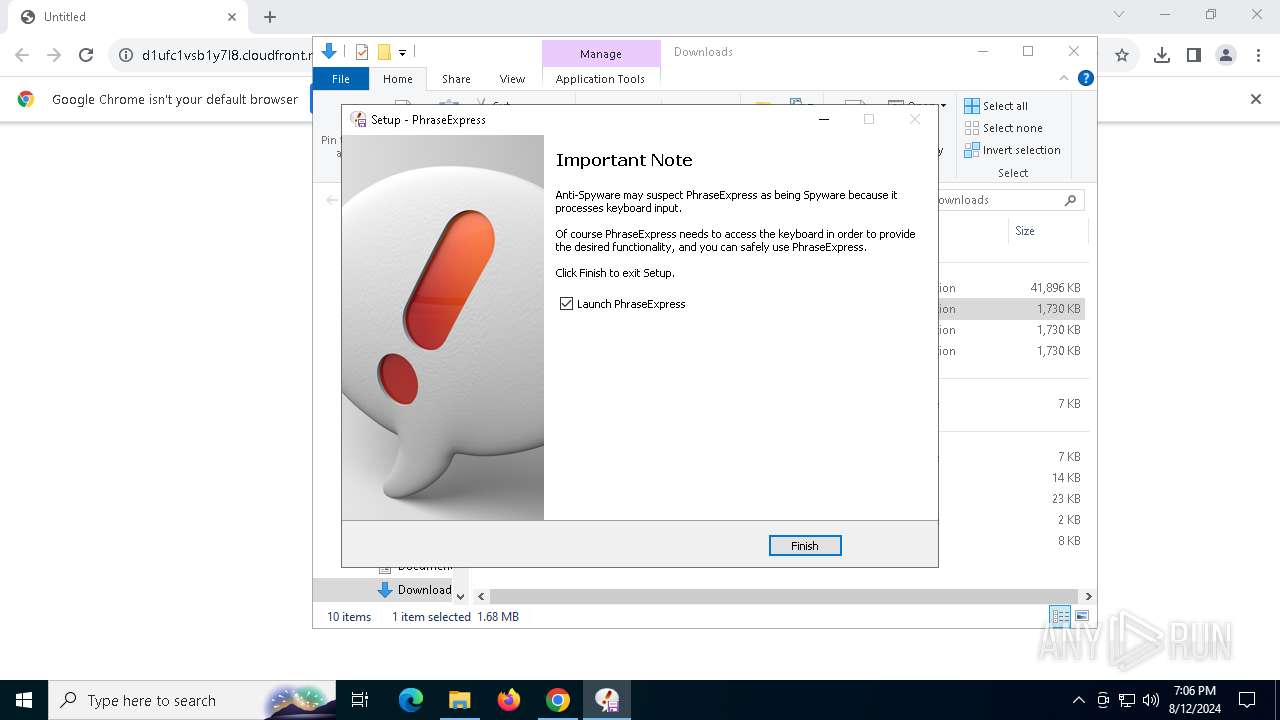
| Threats: | AZORult can steal banking information, including passwords and credit card details, as well as cryptocurrency. This constantly updated information stealer malware should not be taken lightly, as it continues to be an active threat. |
| Analysis date: | August 12, 2024, 19:04:27 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | C39E8A441C3F05AE96B2505717578D9B |
| SHA1: | 2A6931A4FD57DBCAE812CDDD570274974253EBA9 |
| SHA256: | 21F0DC7F46B5E983AB56425781FE6C3ACB3368D8378044EF4B38954112CAED9E |
| SSDEEP: | 3:N8Mwa6JeKQIl/038Tw9d:2M4zQV3Yw9d |
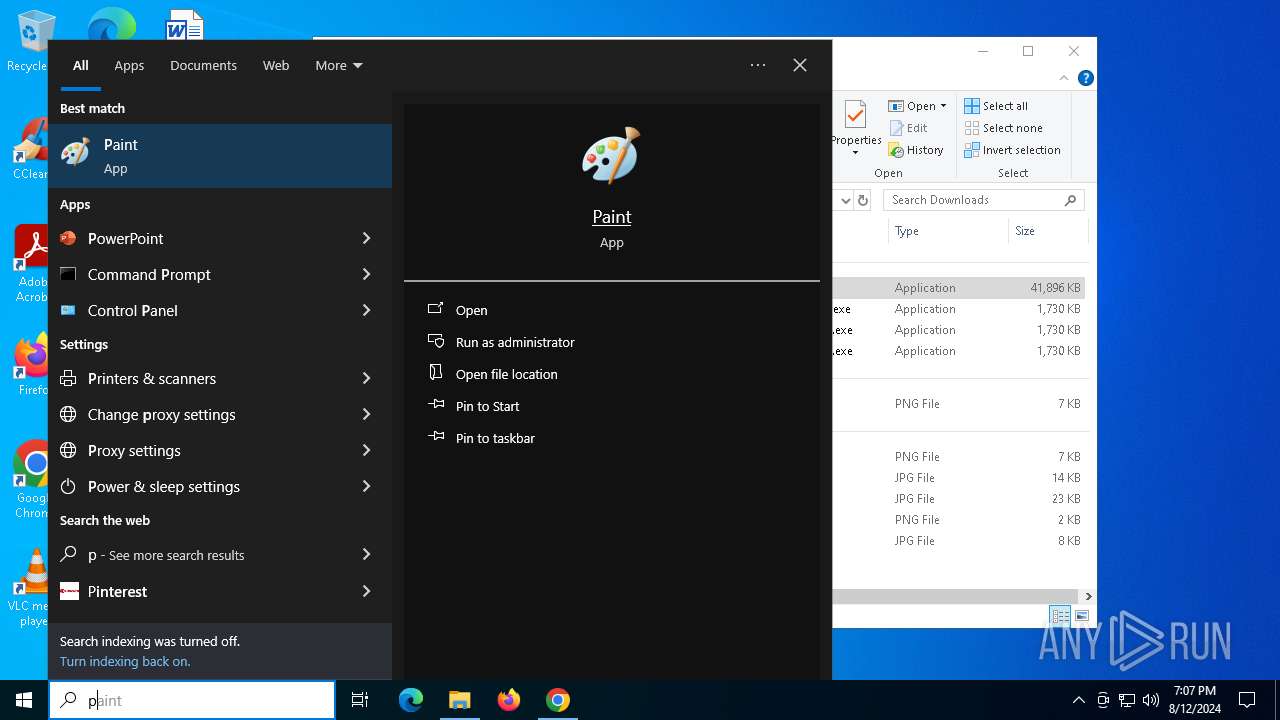
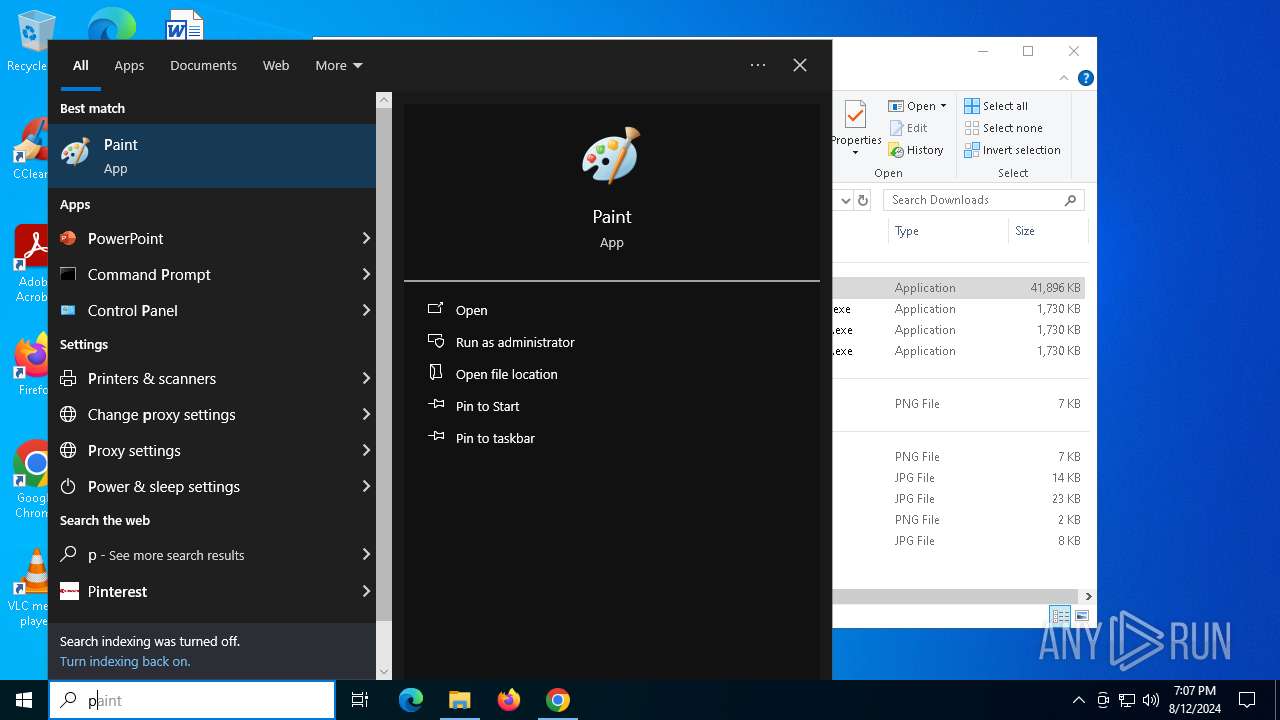
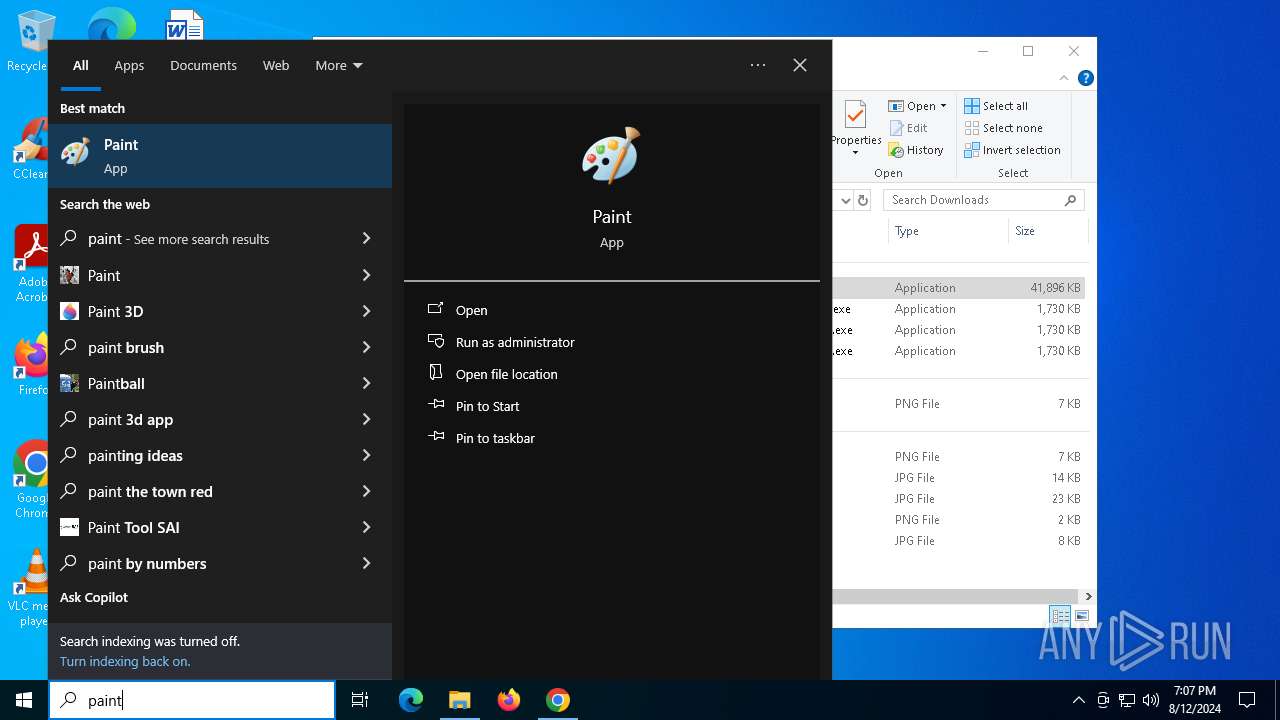
MALICIOUS
Actions looks like stealing of personal data
- UnifiedStub-installer.exe (PID: 7980)
- rsEngineSvc.exe (PID: 7408)
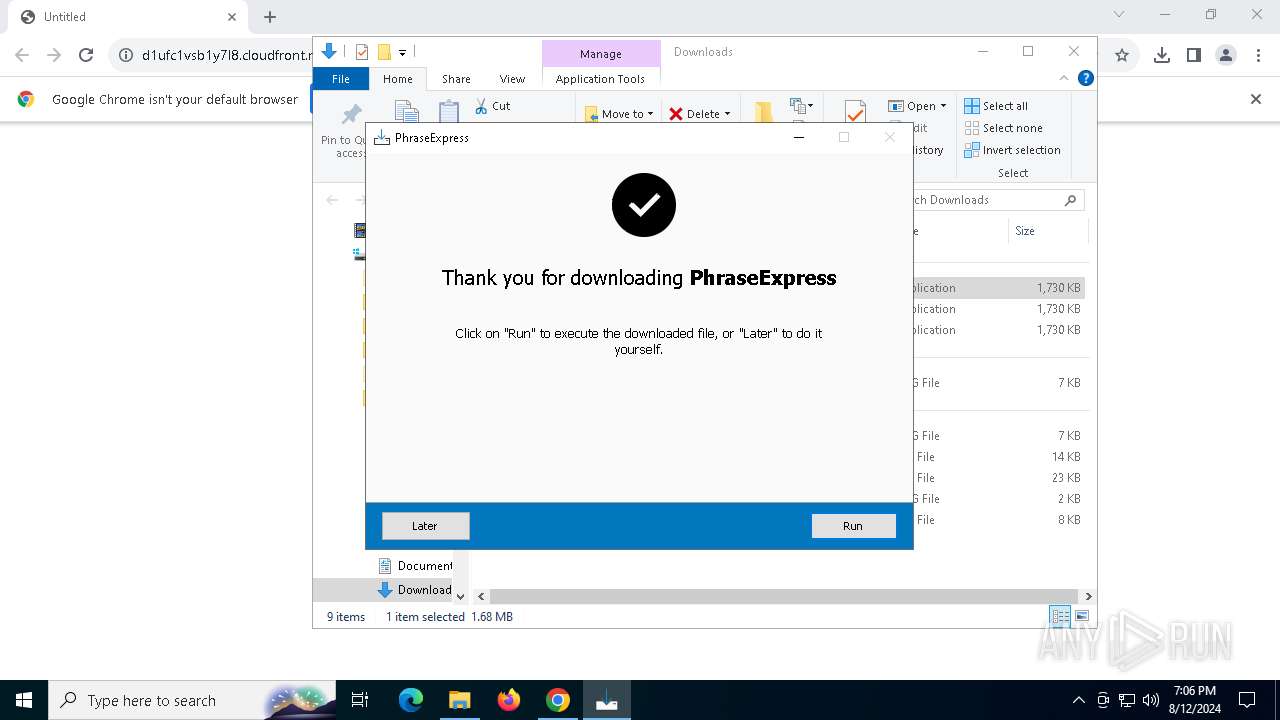
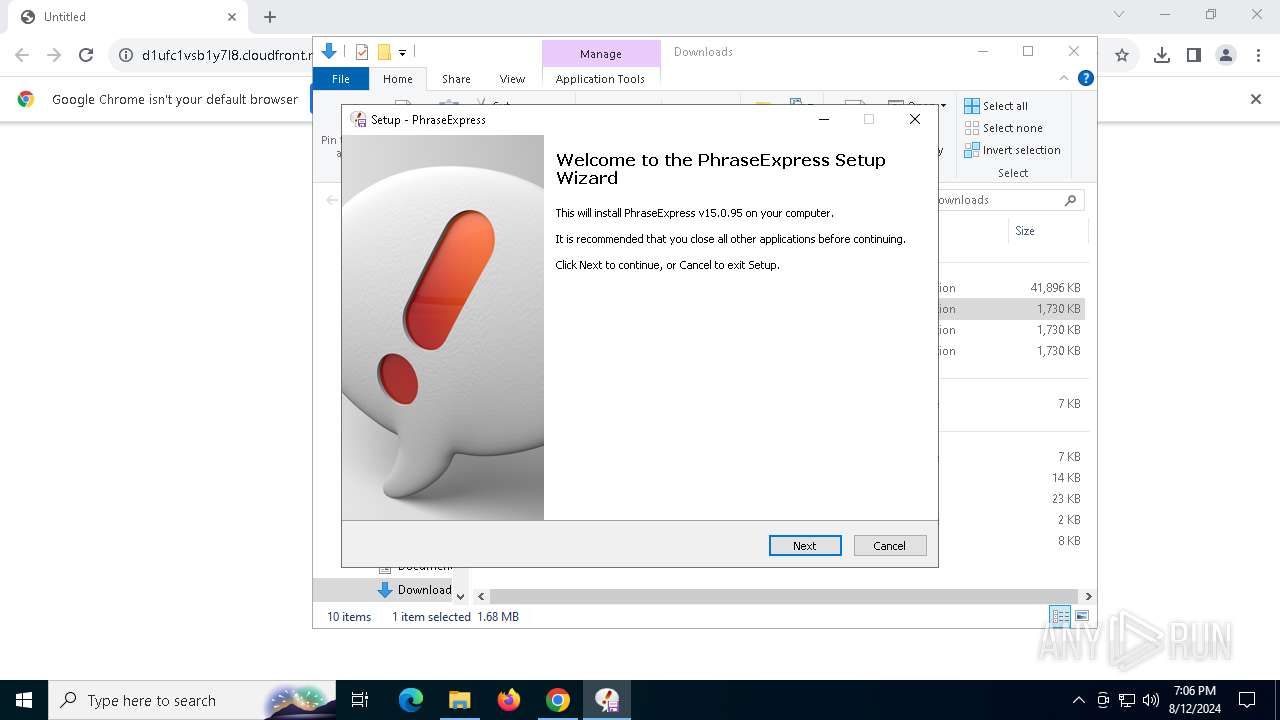
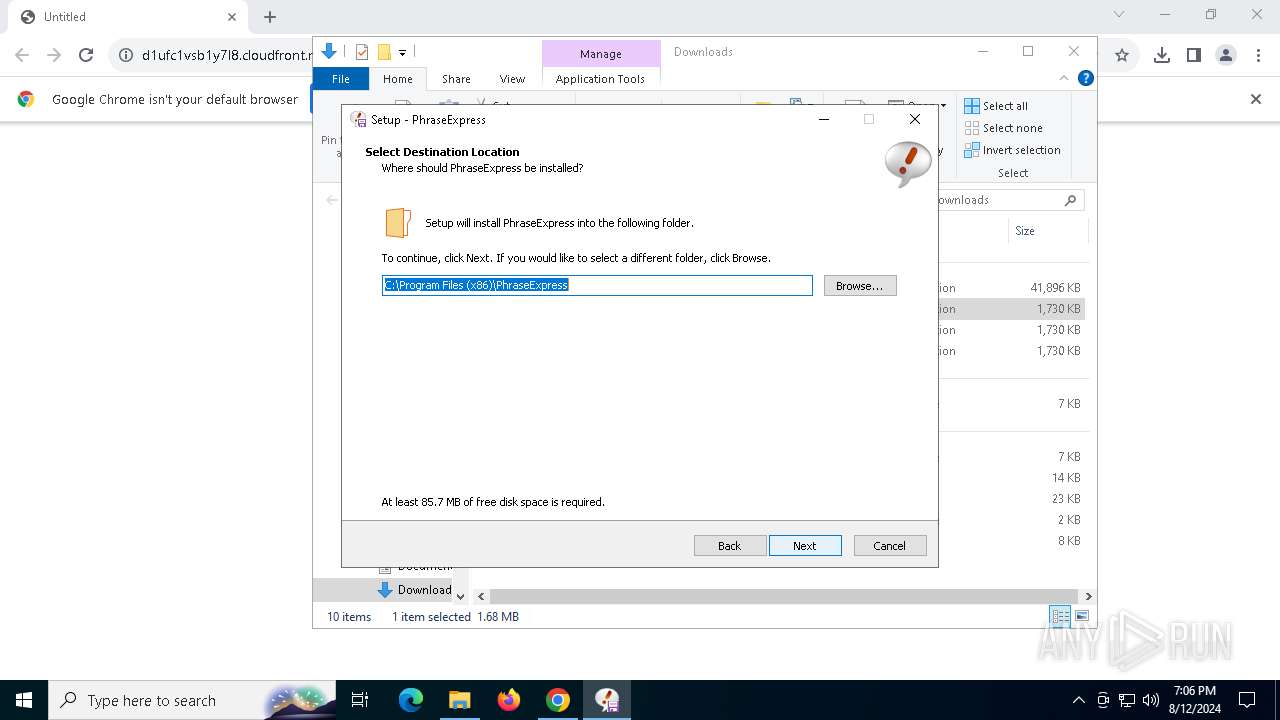
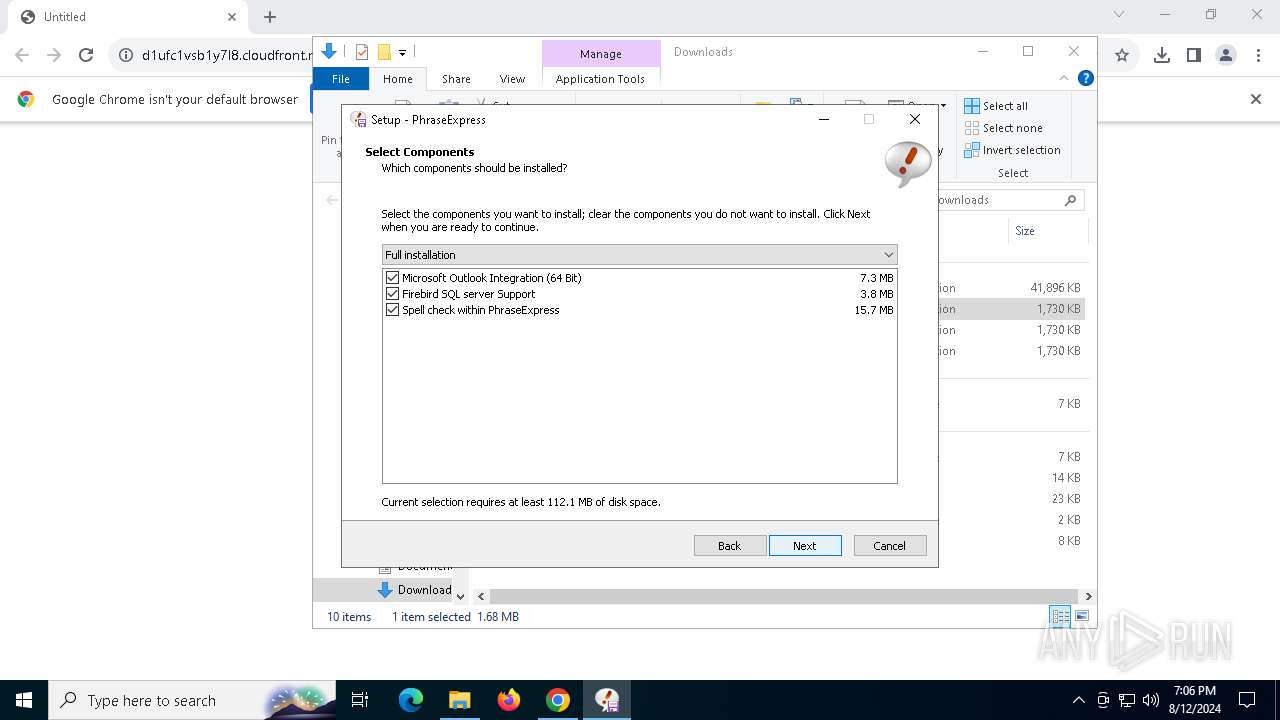
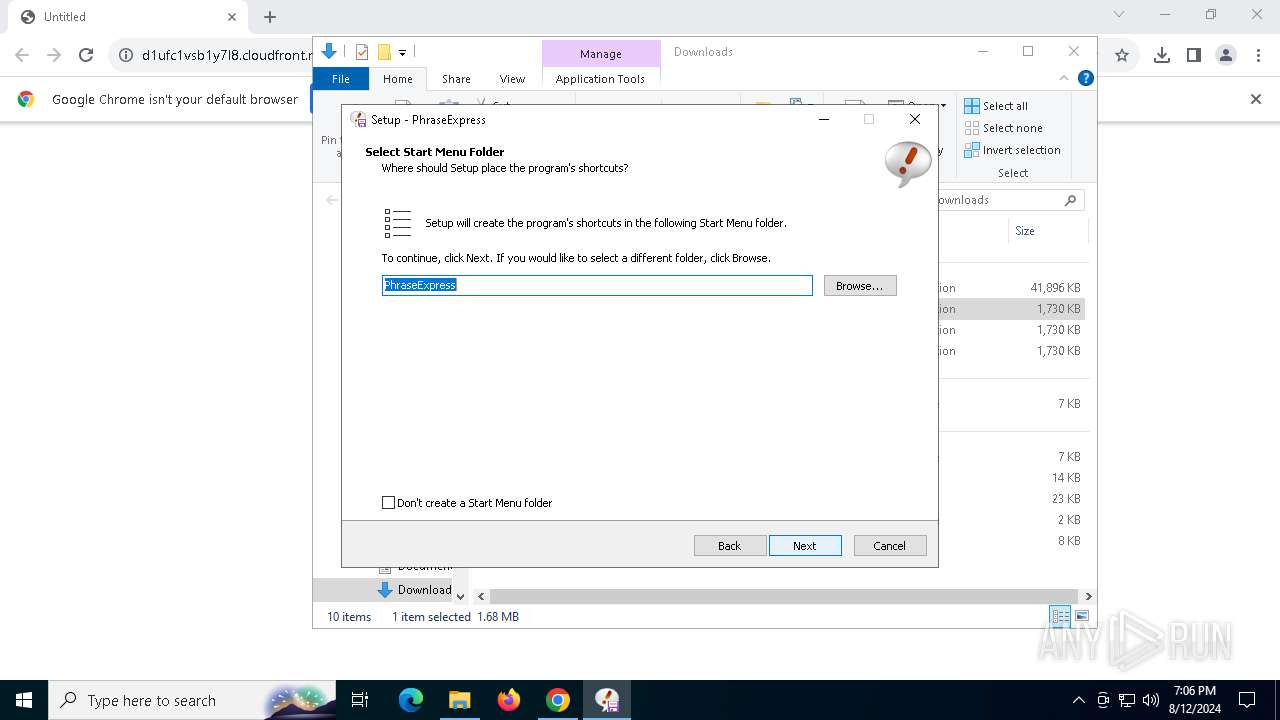
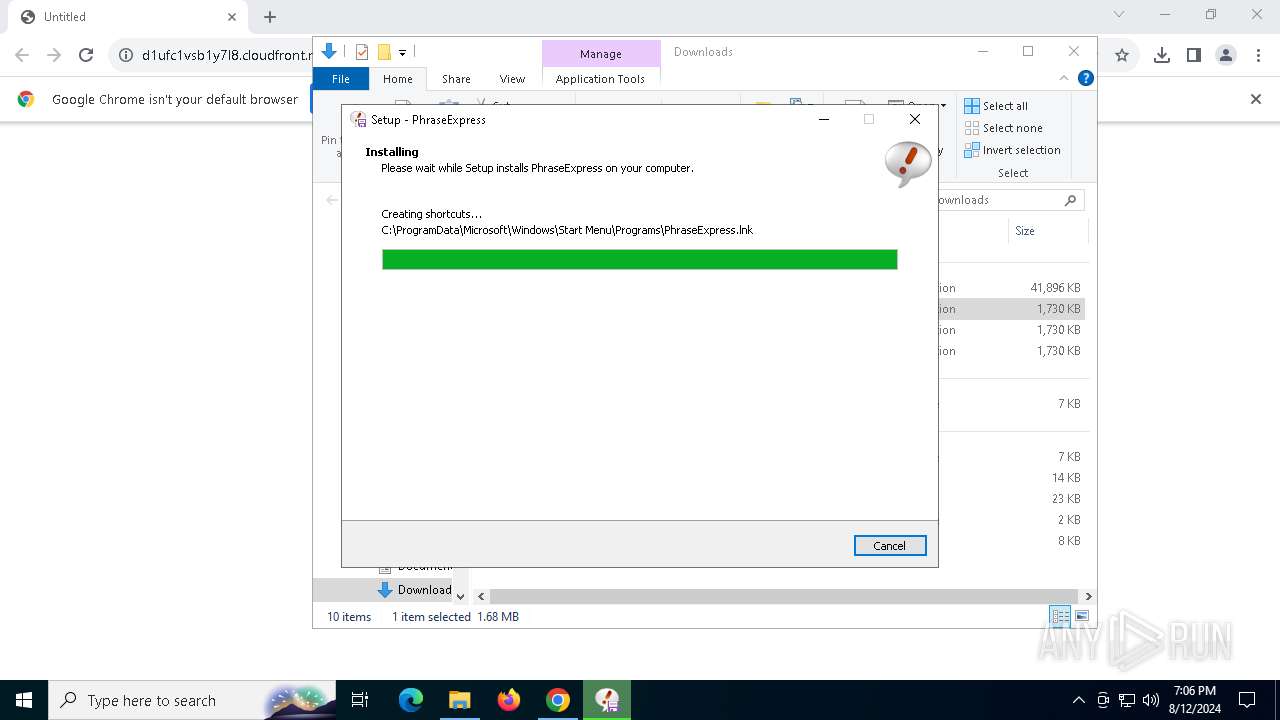
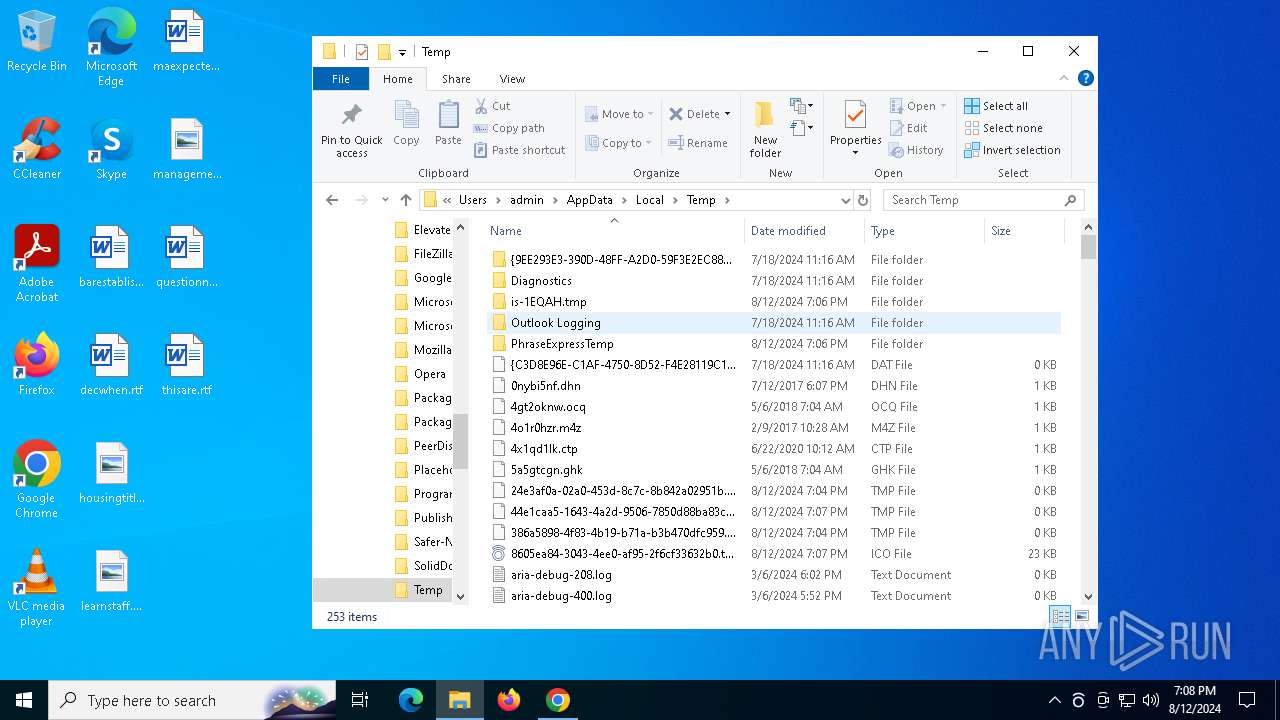
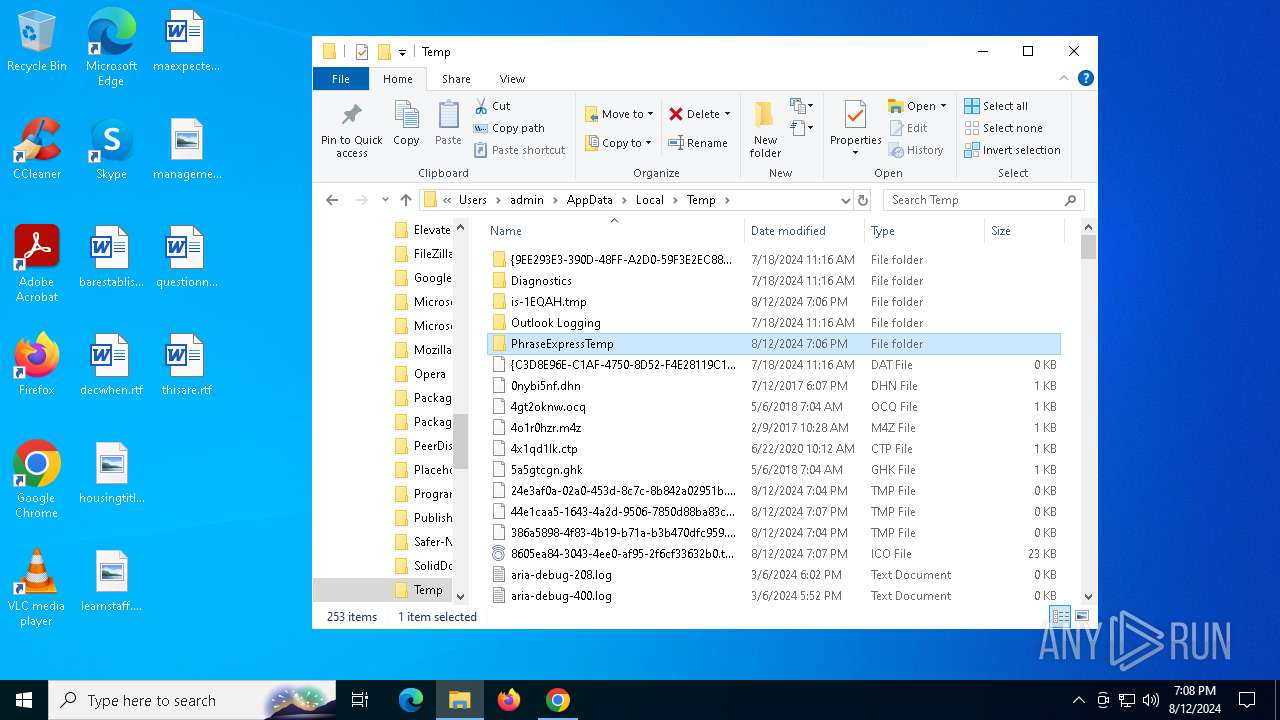
Create files in the Startup directory
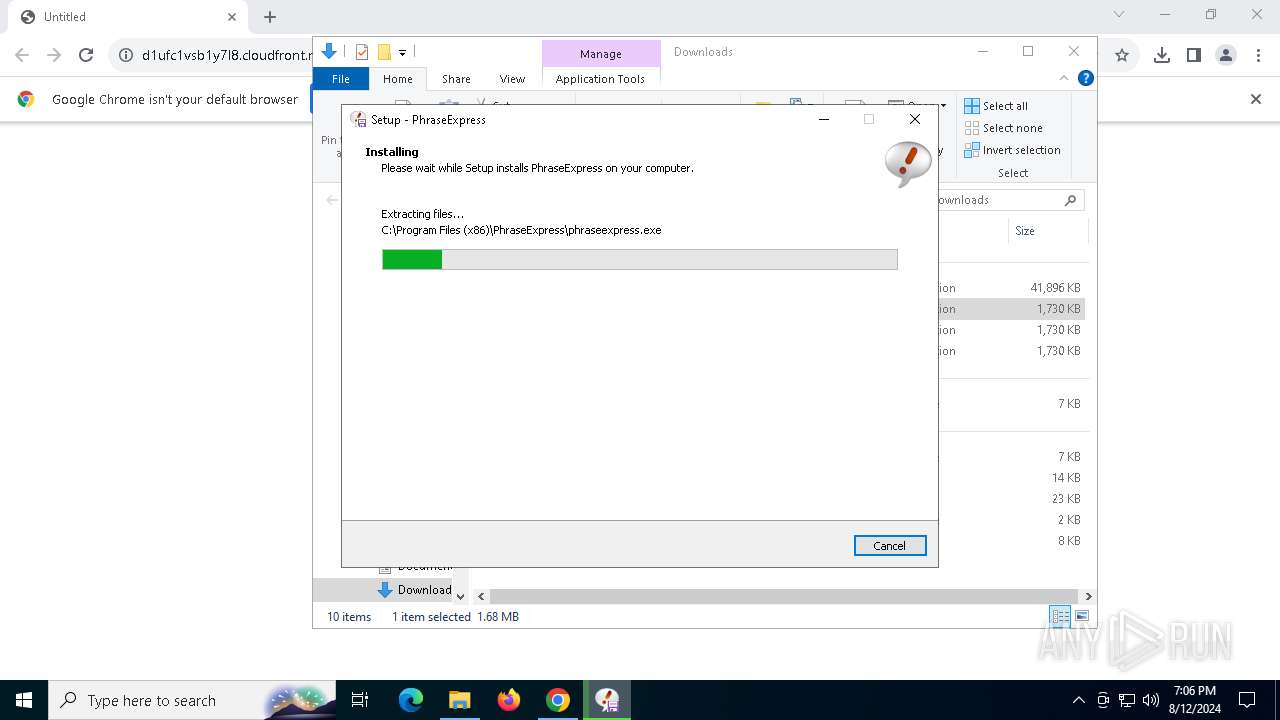
- phraseexpress-15.0.95-installer.tmp (PID: 6700)
Registers / Runs the DLL via REGSVR32.EXE
- phraseexpress-15.0.95-installer.tmp (PID: 6700)
AZORULT has been detected (YARA)
- phraseexpress.exe (PID: 7504)
Changes the autorun value in the registry
- rundll32.exe (PID: 5292)
SUSPICIOUS
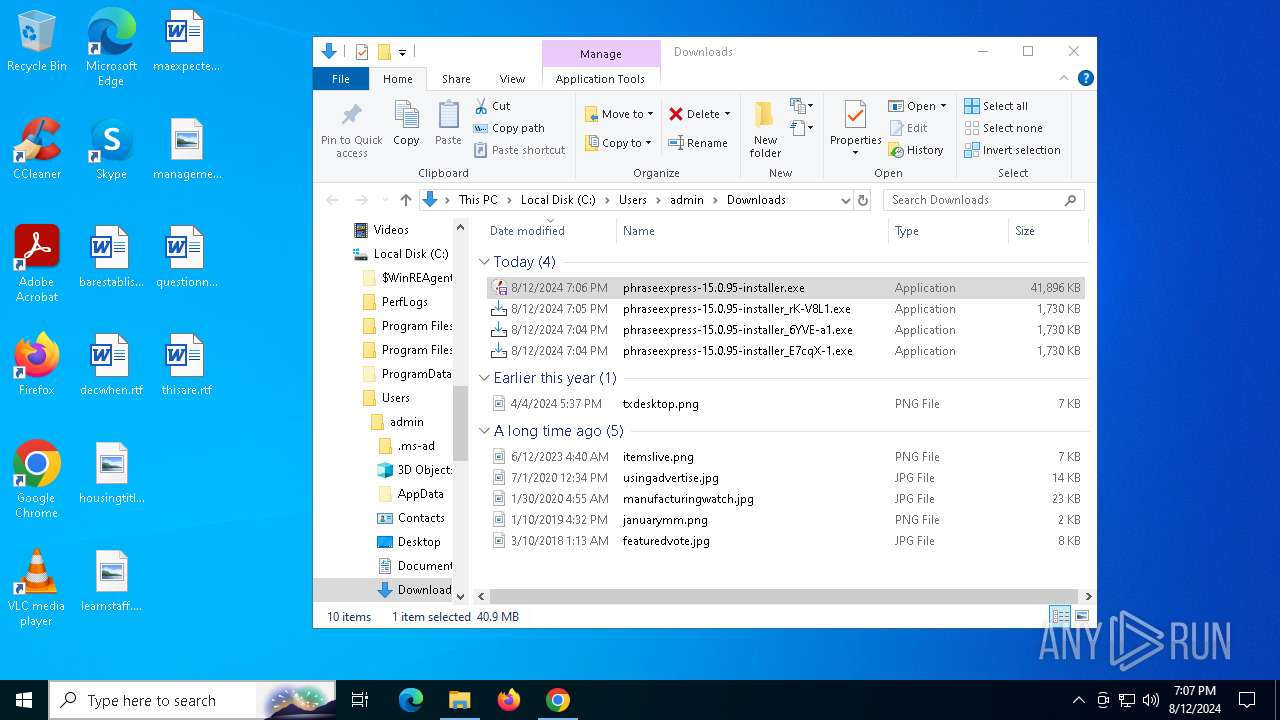
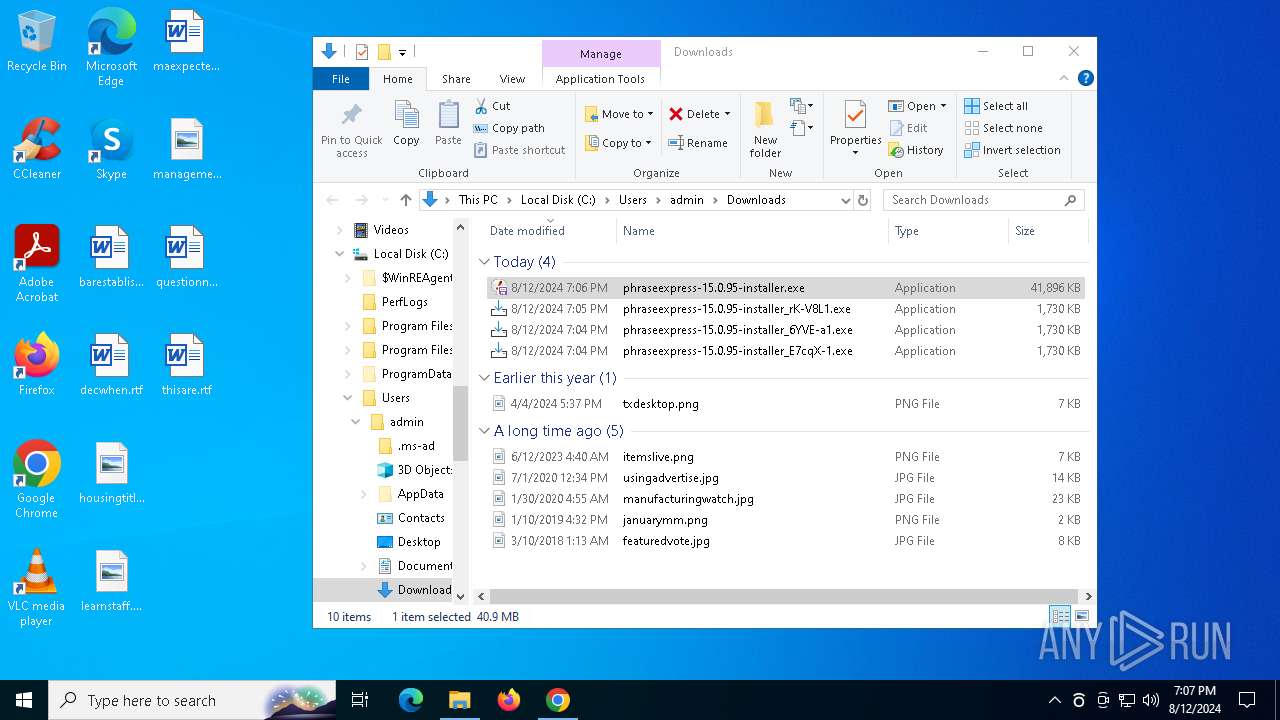
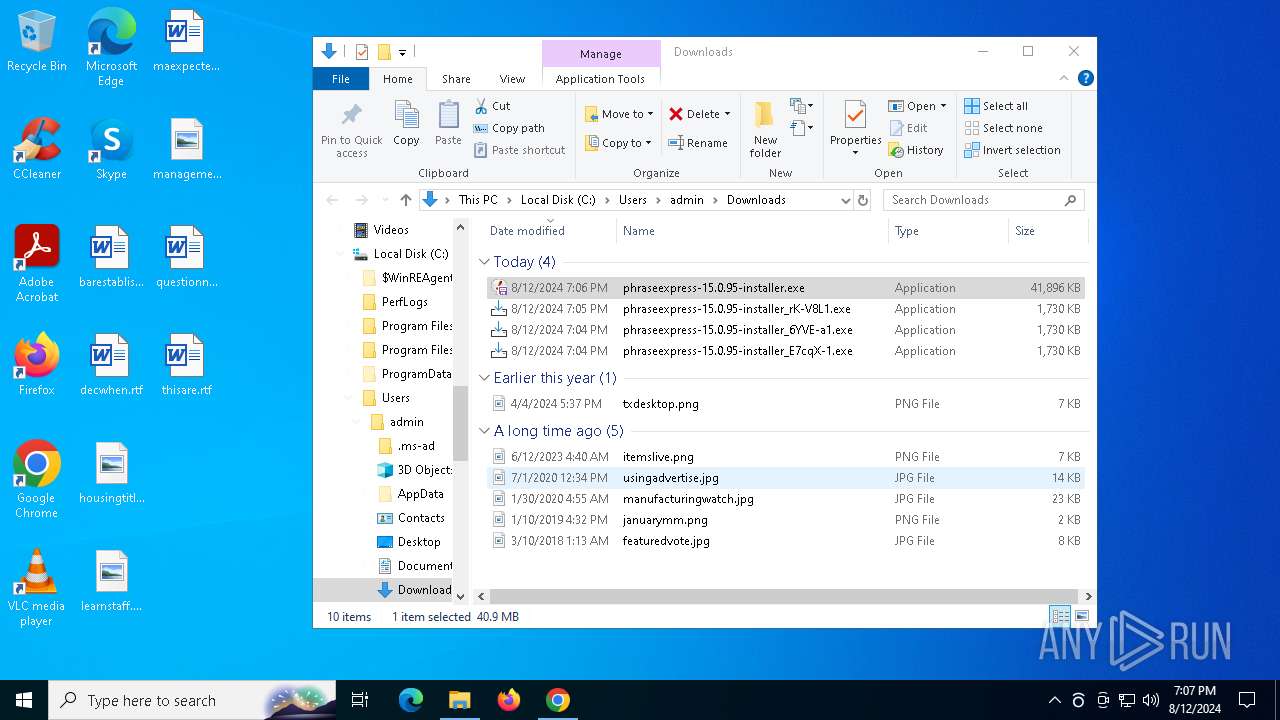
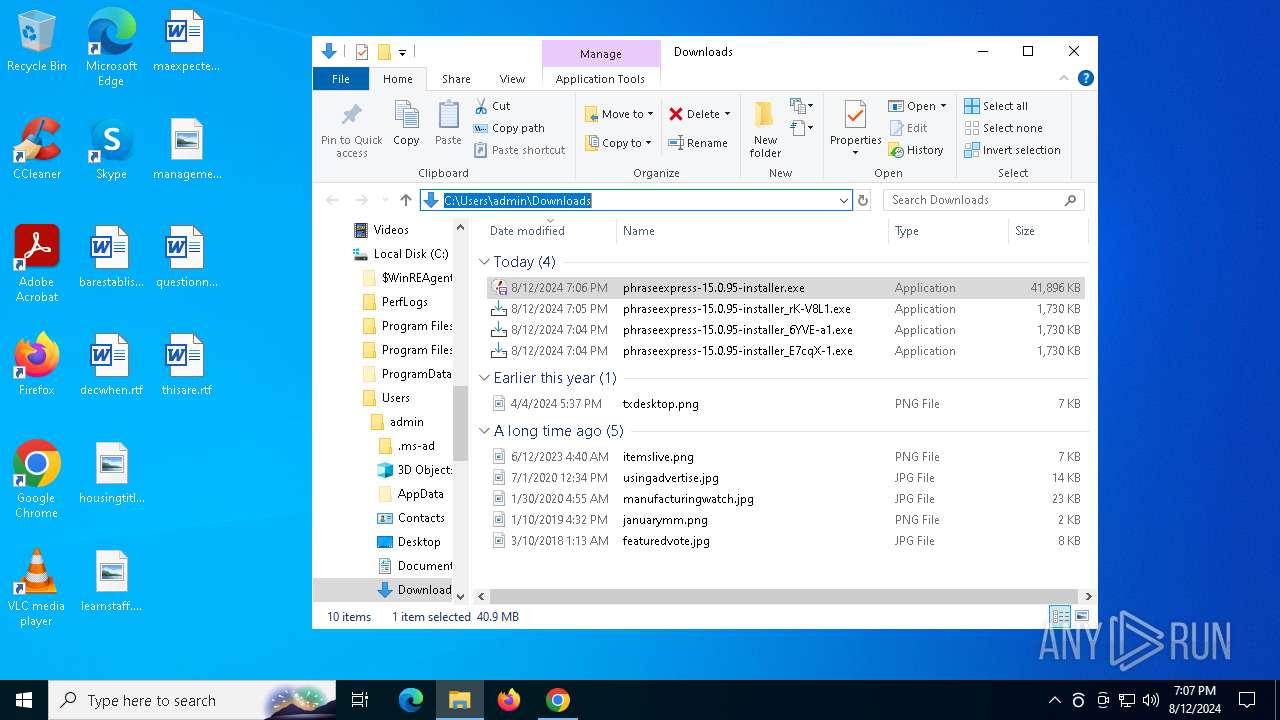
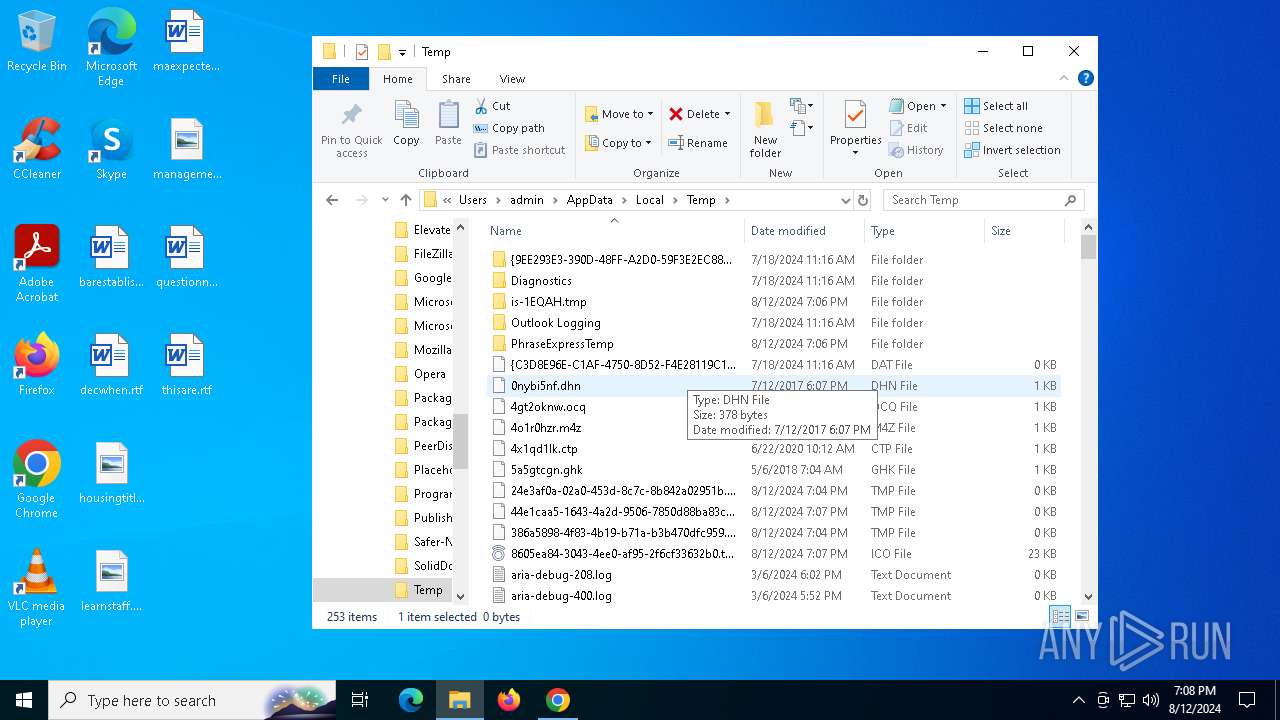
Creates file in the systems drive root
- explorer.exe (PID: 4552)
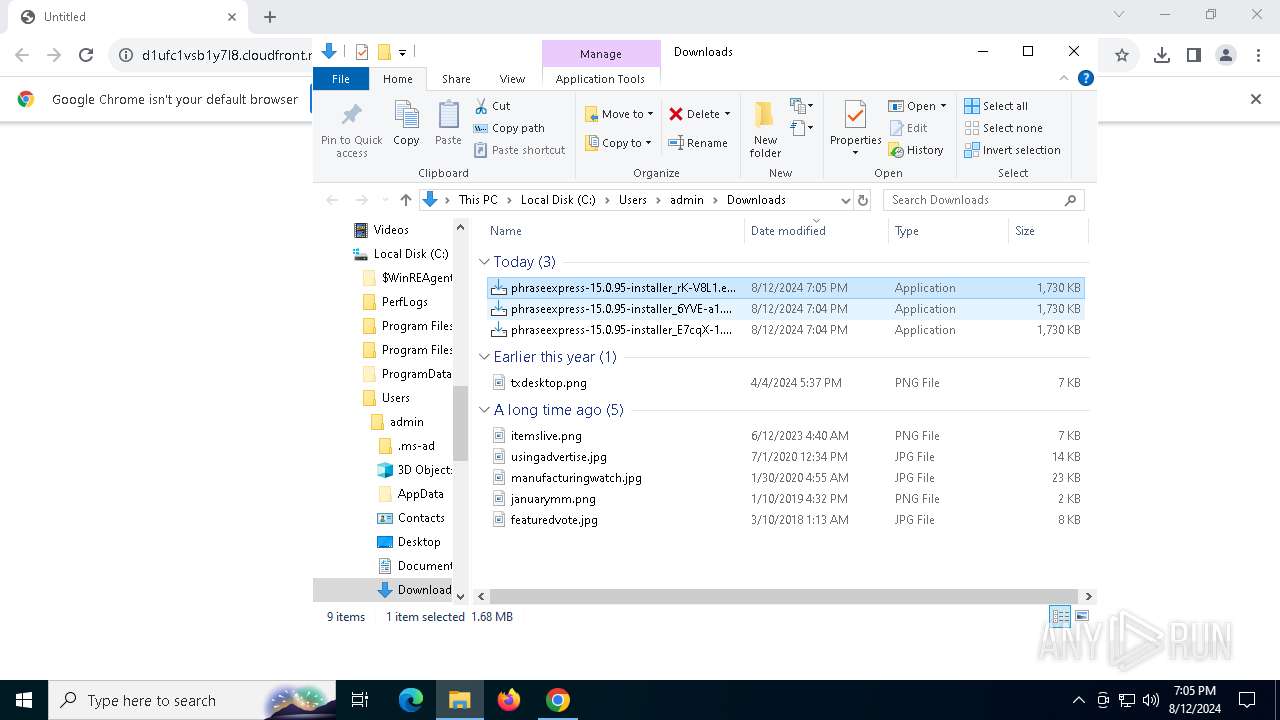
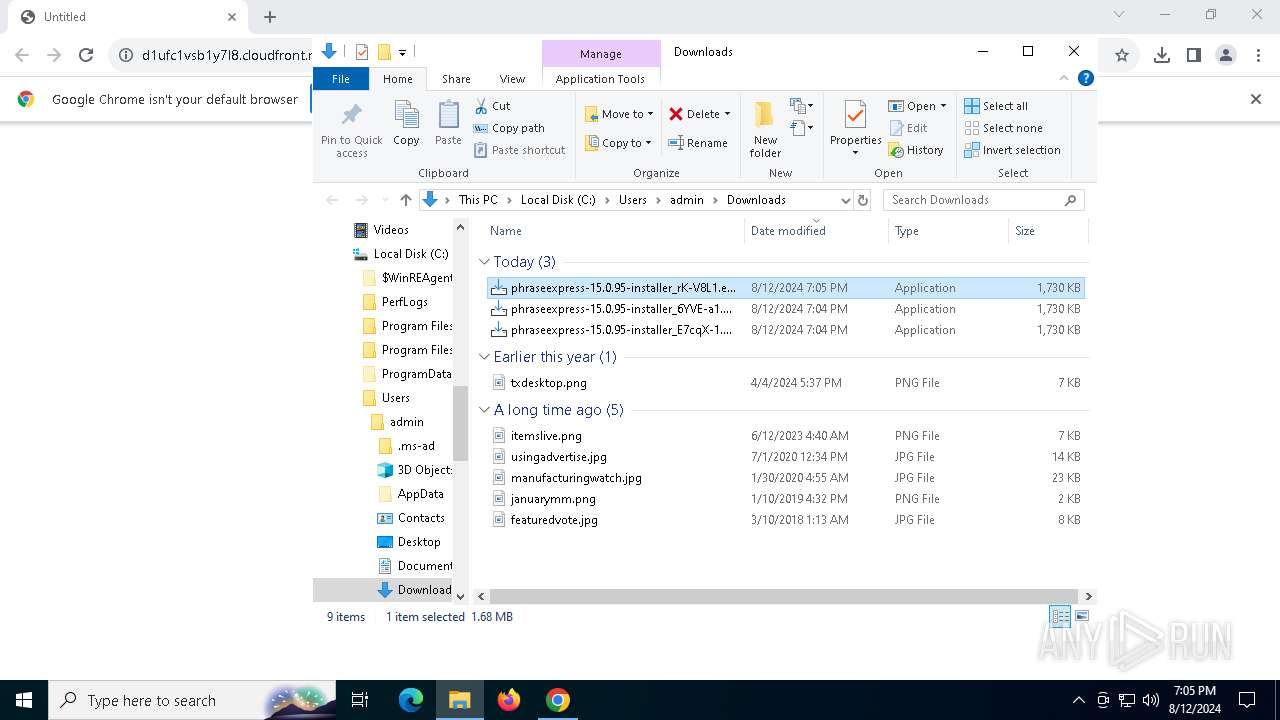
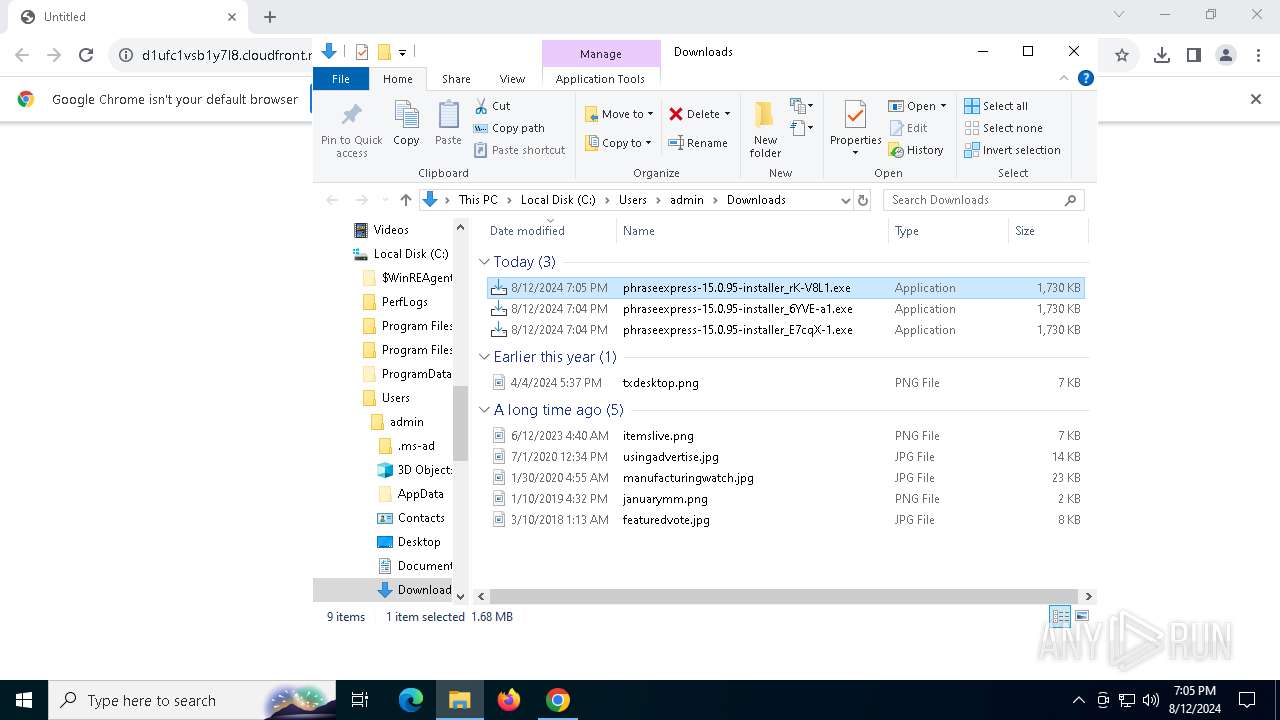
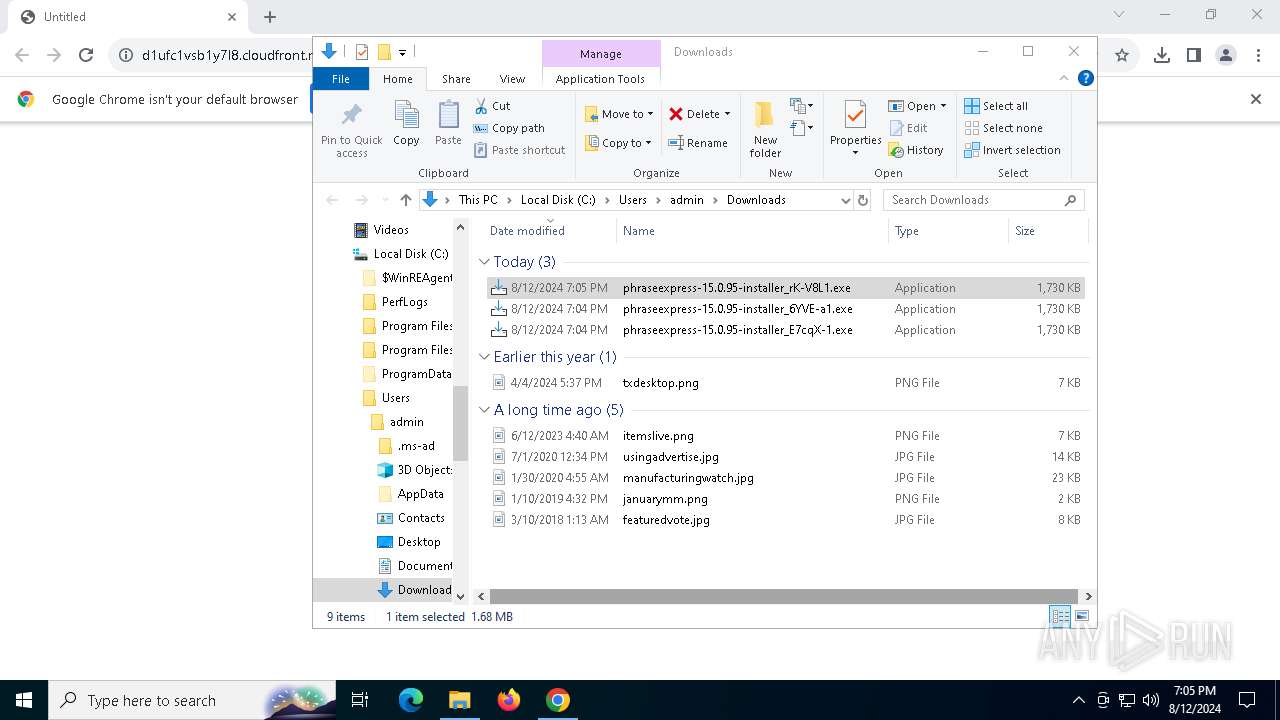
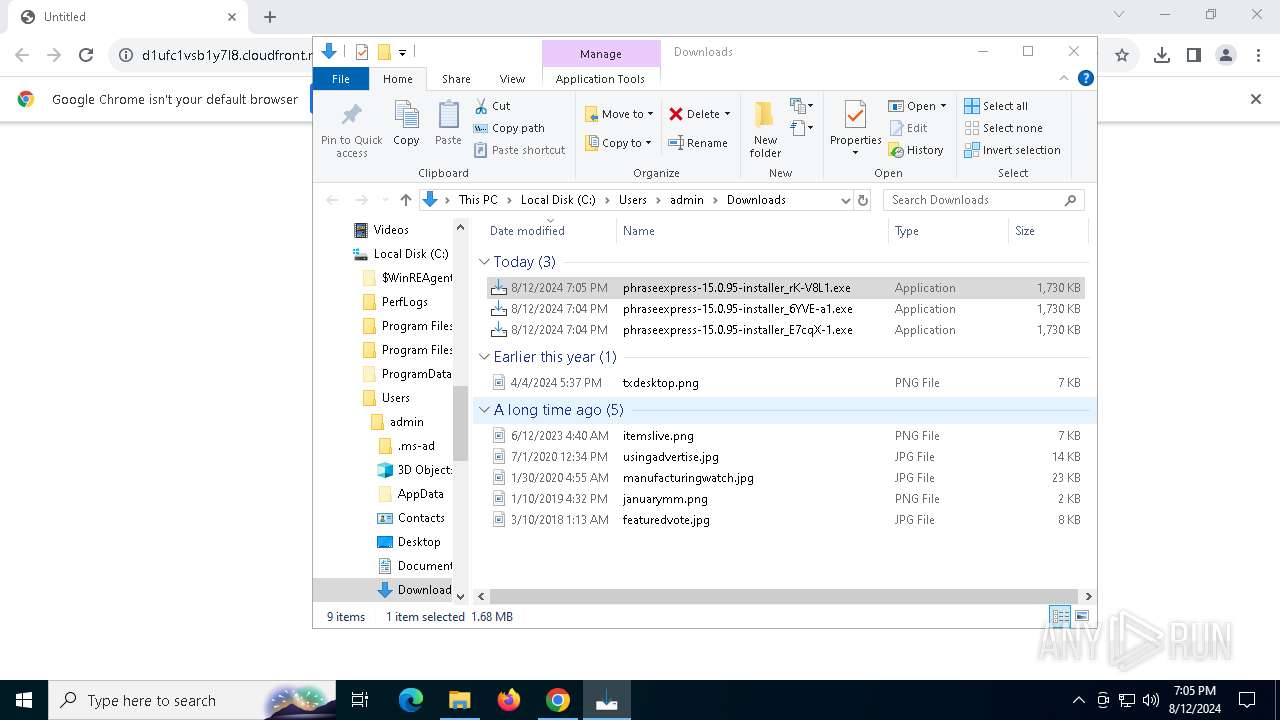
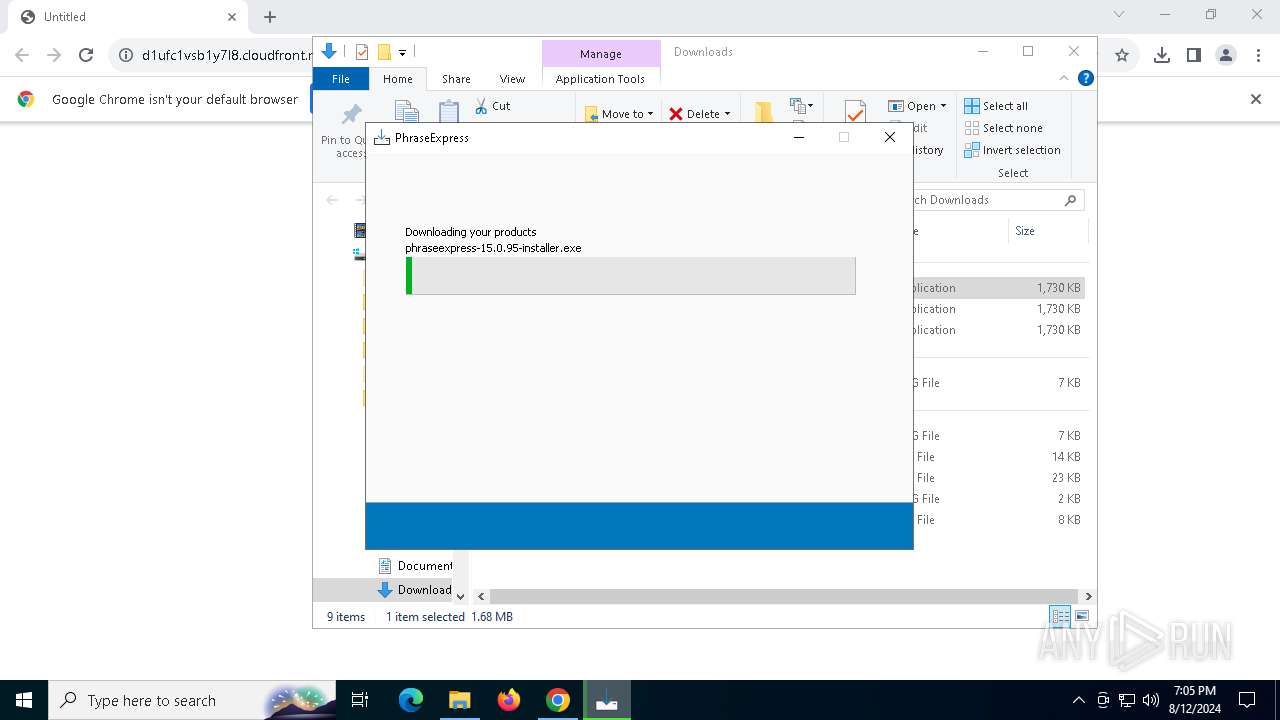
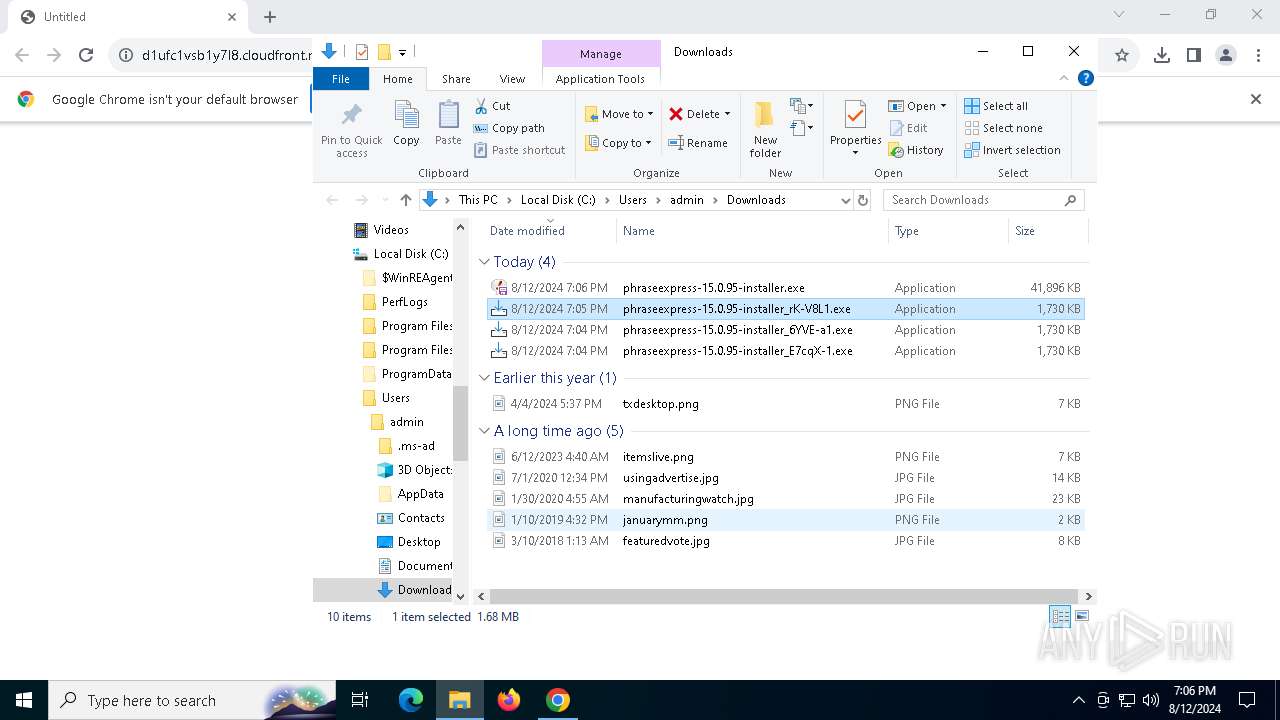
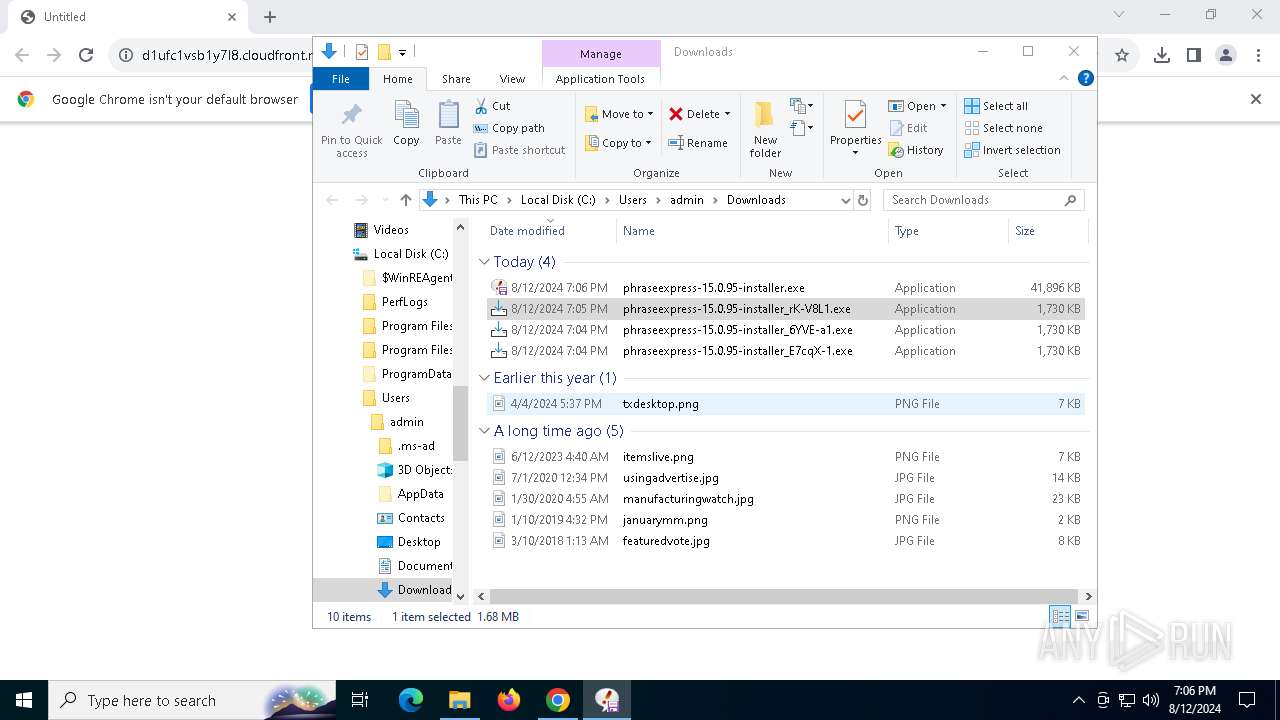
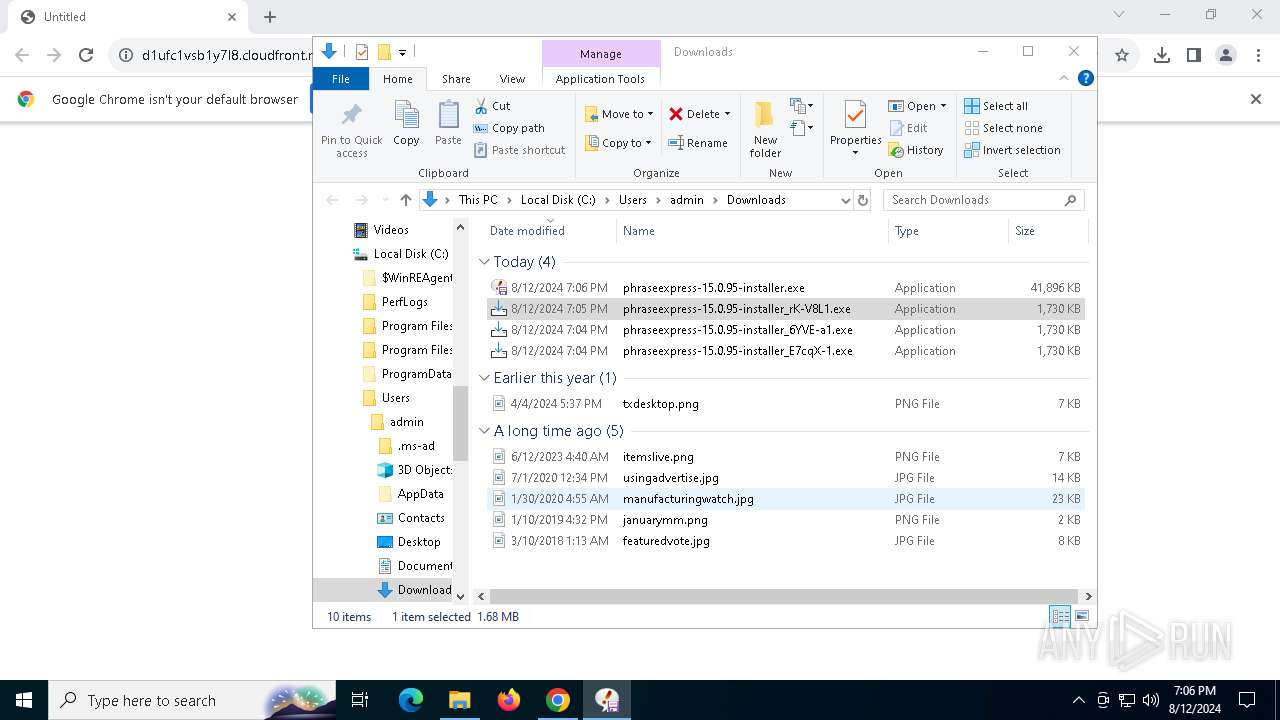
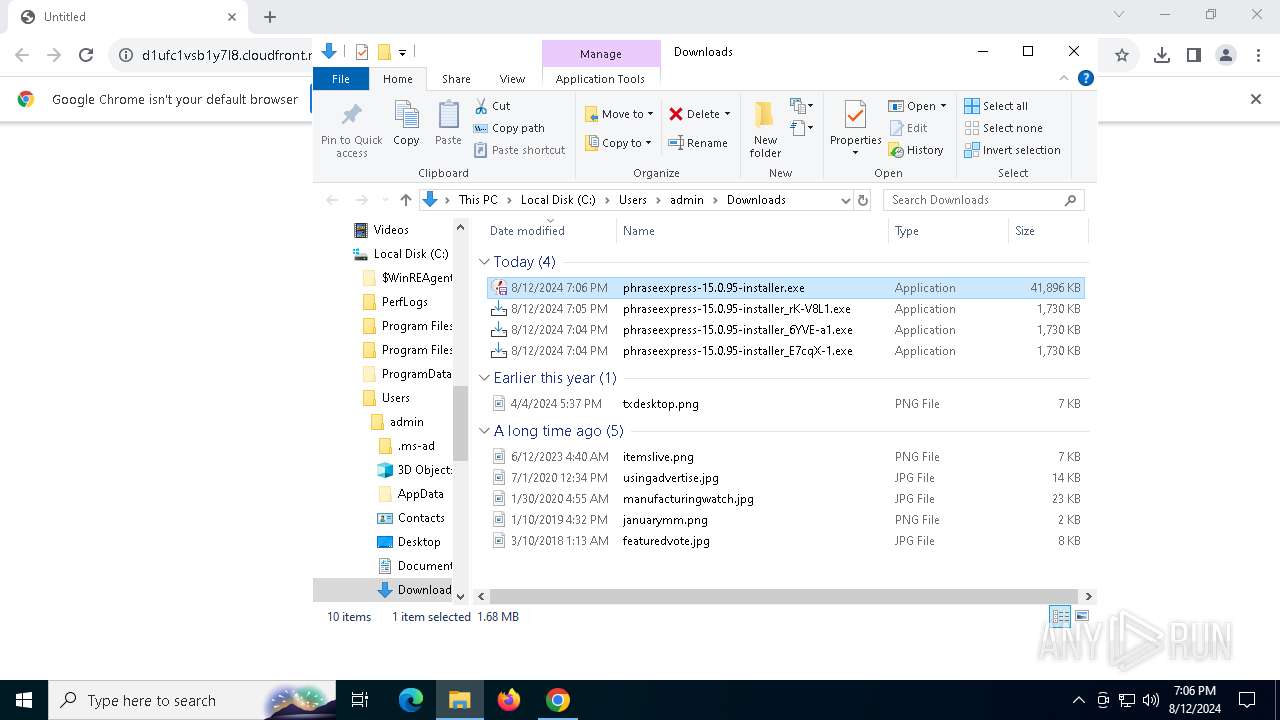
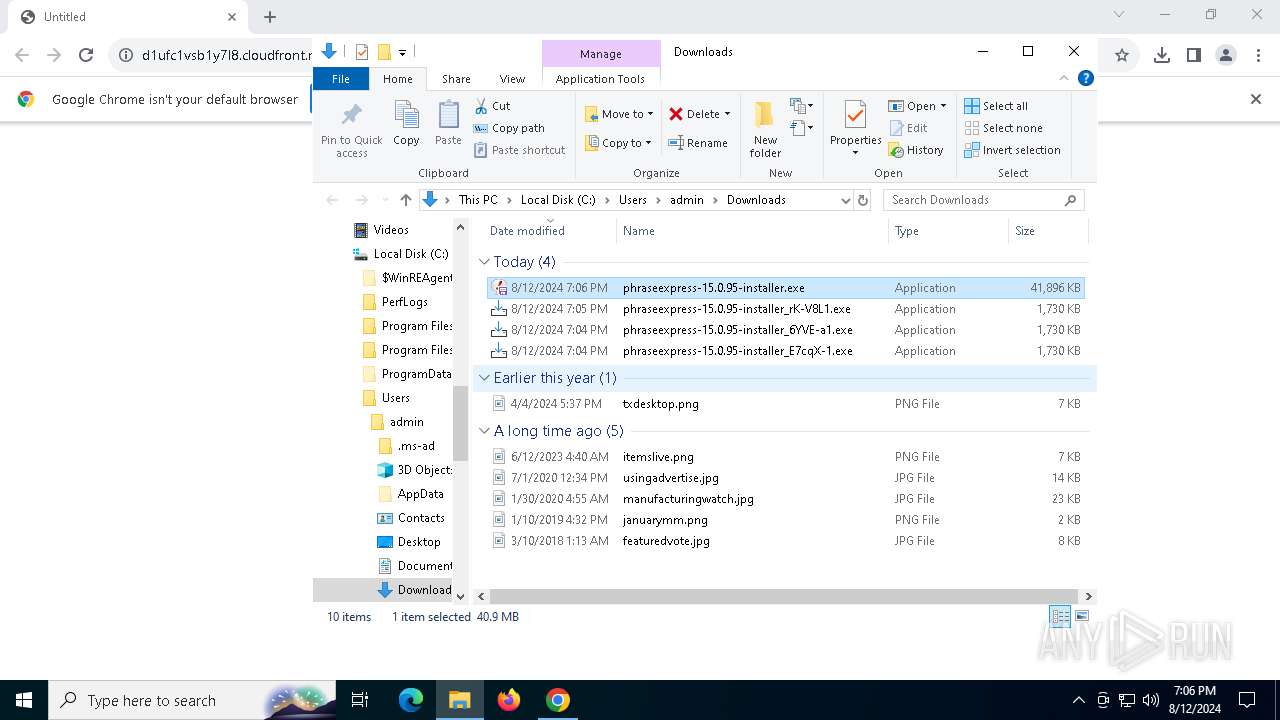
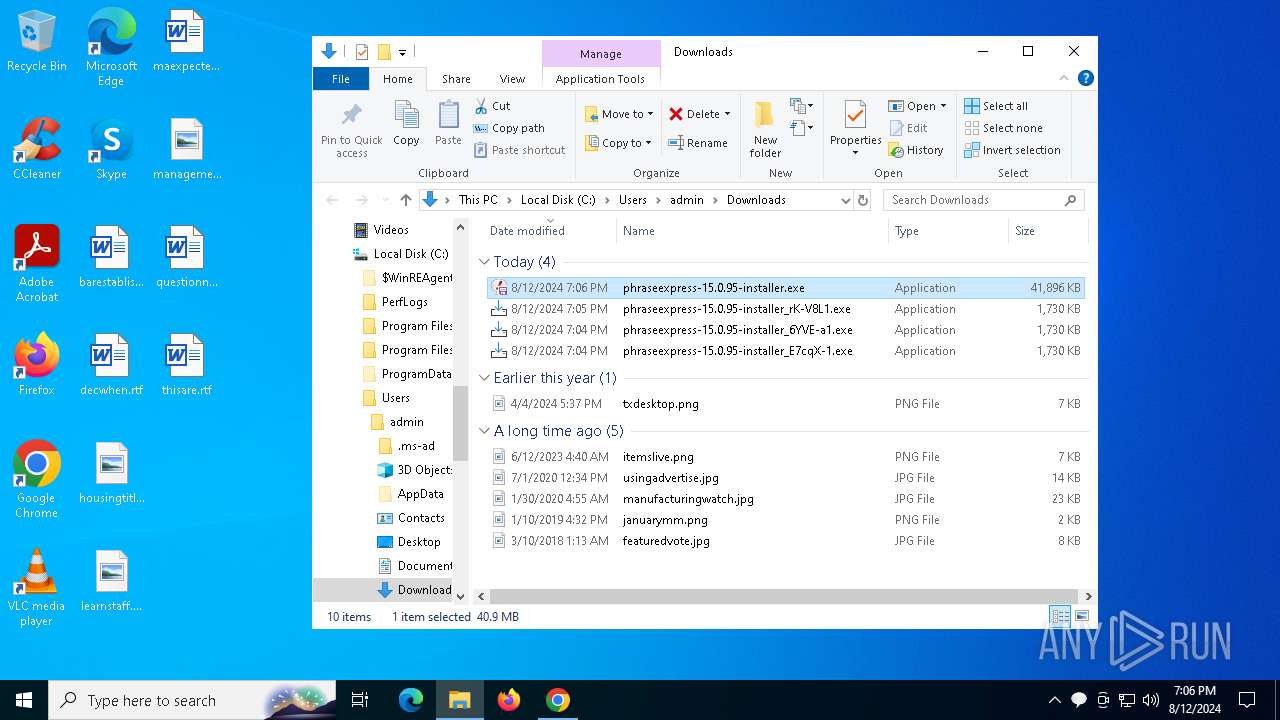
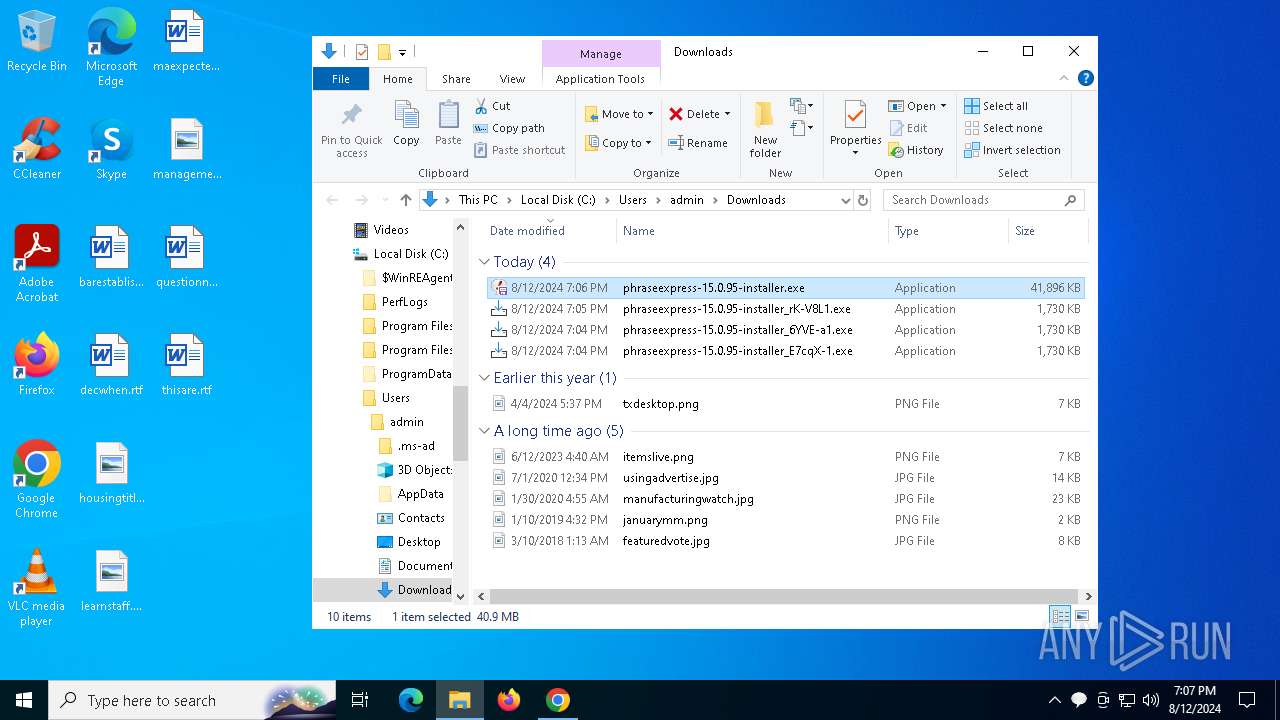
Drops the executable file immediately after the start
- phraseexpress-15.0.95-installer_rK-V8L1.exe (PID: 7456)
- phraseexpress-15.0.95-installer_rK-V8L1.exe (PID: 7224)
- phraseexpress-15.0.95-installer_rK-V8L1.tmp (PID: 7212)
- component0.exe (PID: 2700)
- x55vf2cy.exe (PID: 6336)
- UnifiedStub-installer.exe (PID: 7980)
- phraseexpress-15.0.95-installer.exe (PID: 8056)
- phraseexpress-15.0.95-installer.tmp (PID: 6700)
- msiexec.exe (PID: 300)
Reads security settings of Internet Explorer
- phraseexpress-15.0.95-installer_rK-V8L1.tmp (PID: 7460)
- phraseexpress-15.0.95-installer_rK-V8L1.tmp (PID: 7212)
- component0.exe (PID: 2700)
- UnifiedStub-installer.exe (PID: 7980)
- rsWSC.exe (PID: 6436)
- rsEngineSvc.exe (PID: 7828)
- rsEDRSvc.exe (PID: 8040)
- rsEngineSvc.exe (PID: 7408)
Reads the date of Windows installation
- phraseexpress-15.0.95-installer_rK-V8L1.tmp (PID: 7460)
- phraseexpress-15.0.95-installer_rK-V8L1.tmp (PID: 7212)
- component0.exe (PID: 2700)
- rsEDRSvc.exe (PID: 6556)
- rsEngineSvc.exe (PID: 7408)
Executable content was dropped or overwritten
- phraseexpress-15.0.95-installer_rK-V8L1.exe (PID: 7224)
- phraseexpress-15.0.95-installer_rK-V8L1.tmp (PID: 7212)
- component0.exe (PID: 2700)
- x55vf2cy.exe (PID: 6336)
- phraseexpress-15.0.95-installer_rK-V8L1.exe (PID: 7456)
- UnifiedStub-installer.exe (PID: 7980)
- phraseexpress-15.0.95-installer.exe (PID: 8056)
- phraseexpress-15.0.95-installer.tmp (PID: 6700)
Reads the Windows owner or organization settings
- phraseexpress-15.0.95-installer_rK-V8L1.tmp (PID: 7212)
- phraseexpress-15.0.95-installer.tmp (PID: 6700)
- msiexec.exe (PID: 300)
Creates a software uninstall entry
- UnifiedStub-installer.exe (PID: 7980)
Process drops legitimate windows executable
- x55vf2cy.exe (PID: 6336)
- phraseexpress-15.0.95-installer.tmp (PID: 6700)
- msiexec.exe (PID: 300)
- UnifiedStub-installer.exe (PID: 7980)
Searches for installed software
- UnifiedStub-installer.exe (PID: 7980)
- phraseexpress-15.0.95-installer.tmp (PID: 6700)
Executes as Windows Service
- rsSyncSvc.exe (PID: 8128)
- rsWSC.exe (PID: 964)
- rsClientSvc.exe (PID: 1812)
- rsEngineSvc.exe (PID: 7408)
- rsEDRSvc.exe (PID: 6556)
- WmiApSrv.exe (PID: 7628)
Executes application which crashes
- phraseexpress-15.0.95-installer_rK-V8L1.tmp (PID: 7212)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 5088)
- msiexec.exe (PID: 300)
Uses NETSH.EXE to add a firewall rule or allowed programs
- phraseexpress-15.0.95-installer.tmp (PID: 6700)
The process drops C-runtime libraries
- msiexec.exe (PID: 300)
- UnifiedStub-installer.exe (PID: 7980)
The process creates files with name similar to system file names
- UnifiedStub-installer.exe (PID: 7980)
Drops 7-zip archiver for unpacking
- UnifiedStub-installer.exe (PID: 7980)
Checks Windows Trust Settings
- UnifiedStub-installer.exe (PID: 7980)
- rsWSC.exe (PID: 6436)
- rsEngineSvc.exe (PID: 7828)
- rsWSC.exe (PID: 964)
- rsEDRSvc.exe (PID: 8040)
- msiexec.exe (PID: 300)
- rsEngineSvc.exe (PID: 7408)
- rsEDRSvc.exe (PID: 6556)
Drops a system driver (possible attempt to evade defenses)
- UnifiedStub-installer.exe (PID: 7980)
Adds/modifies Windows certificates
- UnifiedStub-installer.exe (PID: 7980)
Creates or modifies Windows services
- UnifiedStub-installer.exe (PID: 7980)
- rundll32.exe (PID: 5292)
Creates files in the driver directory
- UnifiedStub-installer.exe (PID: 7980)
Uses RUNDLL32.EXE to load library
- UnifiedStub-installer.exe (PID: 7980)
Uses WEVTUTIL.EXE to install publishers and event logs from the manifest
- UnifiedStub-installer.exe (PID: 7980)
Reads the BIOS version
- rsEDRSvc.exe (PID: 6556)
- rsEngineSvc.exe (PID: 7408)
Dropped object may contain URLs of mainers pools
- rsEngineSvc.exe (PID: 7408)
Process checks is Powershell's Script Block Logging on
- rsEDRSvc.exe (PID: 6556)
Application launched itself
- rsAppUI.exe (PID: 1076)
The process checks if it is being run in the virtual environment
- rsEngineSvc.exe (PID: 7408)
INFO
Reads security settings of Internet Explorer
- explorer.exe (PID: 4552)
- runonce.exe (PID: 6080)
Reads Microsoft Office registry keys
- chrome.exe (PID: 6788)
- phraseexpress-15.0.95-installer.tmp (PID: 6700)
- explorer.exe (PID: 4552)
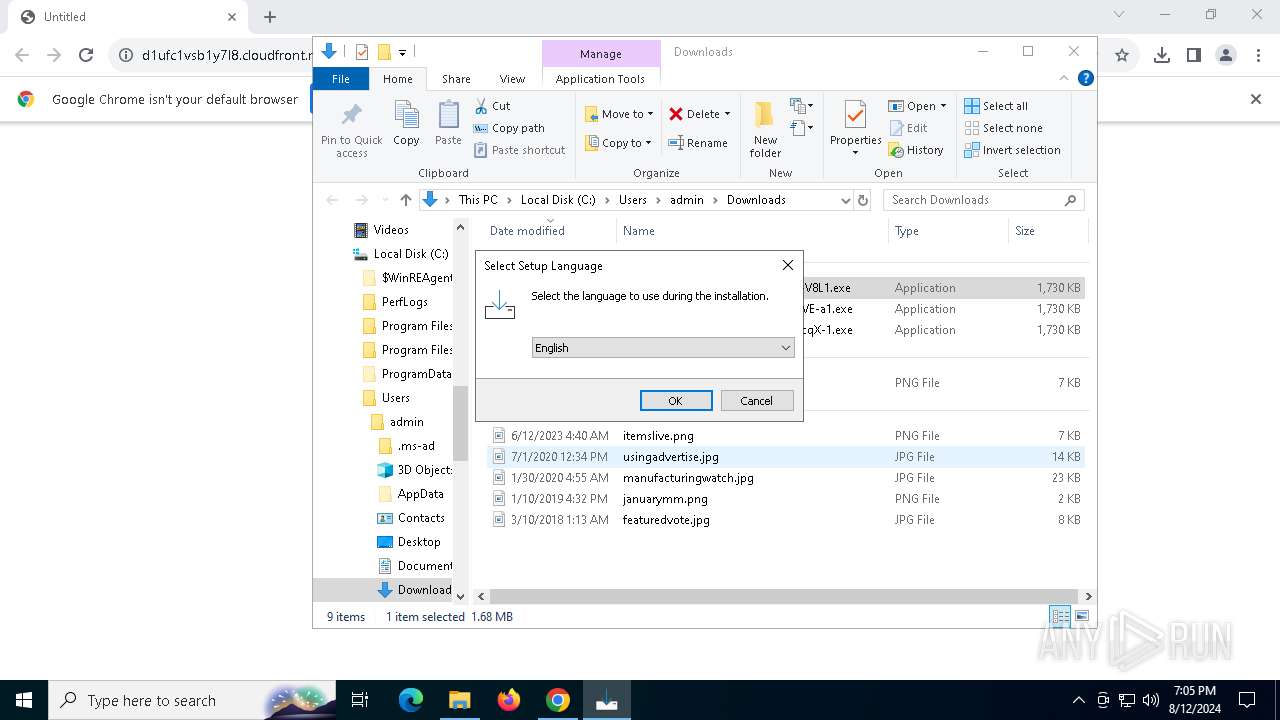
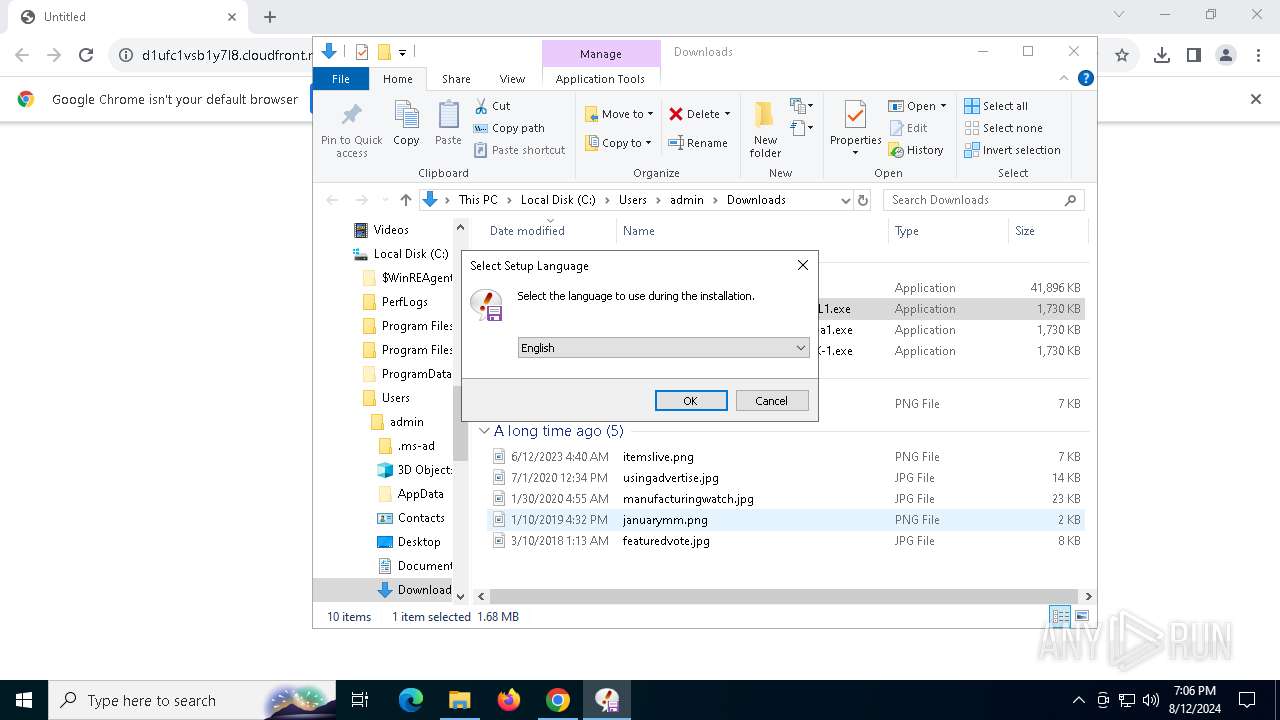
Checks supported languages
- TextInputHost.exe (PID: 7812)
- phraseexpress-15.0.95-installer_rK-V8L1.exe (PID: 7456)
- phraseexpress-15.0.95-installer_rK-V8L1.tmp (PID: 7460)
- phraseexpress-15.0.95-installer_rK-V8L1.exe (PID: 7224)
- phraseexpress-15.0.95-installer_rK-V8L1.tmp (PID: 7212)
- component0.exe (PID: 2700)
- x55vf2cy.exe (PID: 6336)
- UnifiedStub-installer.exe (PID: 7980)
- phraseexpress-15.0.95-installer.exe (PID: 8056)
- rsSyncSvc.exe (PID: 4364)
- rsSyncSvc.exe (PID: 8128)
- phraseexpress-15.0.95-installer.tmp (PID: 6700)
- msiexec.exe (PID: 300)
- msiexec.exe (PID: 1360)
- msiexec.exe (PID: 6448)
- msiexec.exe (PID: 1128)
- phraseexpress.exe (PID: 7504)
- rsWSC.exe (PID: 964)
- rsWSC.exe (PID: 6436)
- rsClientSvc.exe (PID: 1116)
- rsClientSvc.exe (PID: 1812)
- rsEngineSvc.exe (PID: 7828)
- rsEngineSvc.exe (PID: 7408)
- rsEDRSvc.exe (PID: 8040)
- rsHelper.exe (PID: 3372)
- rsEDRSvc.exe (PID: 6556)
- EPP.exe (PID: 7460)
- rsAppUI.exe (PID: 6444)
- rsAppUI.exe (PID: 7500)
- rsAppUI.exe (PID: 6644)
- rsAppUI.exe (PID: 3180)
- rsLitmus.A.exe (PID: 8060)
- rsAppUI.exe (PID: 1076)
The process uses the downloaded file
- chrome.exe (PID: 4276)
- chrome.exe (PID: 7920)
- chrome.exe (PID: 4708)
- explorer.exe (PID: 4552)
Reads the computer name
- TextInputHost.exe (PID: 7812)
- phraseexpress-15.0.95-installer_rK-V8L1.tmp (PID: 7212)
- component0.exe (PID: 2700)
- phraseexpress-15.0.95-installer_rK-V8L1.tmp (PID: 7460)
- rsSyncSvc.exe (PID: 4364)
- rsSyncSvc.exe (PID: 8128)
- phraseexpress-15.0.95-installer.tmp (PID: 6700)
- UnifiedStub-installer.exe (PID: 7980)
- msiexec.exe (PID: 300)
- msiexec.exe (PID: 6448)
- msiexec.exe (PID: 1360)
- msiexec.exe (PID: 1128)
- phraseexpress.exe (PID: 7504)
- rsWSC.exe (PID: 6436)
- rsWSC.exe (PID: 964)
- rsClientSvc.exe (PID: 1812)
- rsClientSvc.exe (PID: 1116)
- rsEngineSvc.exe (PID: 7828)
- rsEngineSvc.exe (PID: 7408)
- rsEDRSvc.exe (PID: 8040)
- rsHelper.exe (PID: 3372)
- rsEDRSvc.exe (PID: 6556)
- rsAppUI.exe (PID: 1076)
- rsAppUI.exe (PID: 6444)
- rsAppUI.exe (PID: 7500)
Executable content was dropped or overwritten
- chrome.exe (PID: 6788)
- msiexec.exe (PID: 300)
Checks proxy server information
- explorer.exe (PID: 4552)
- phraseexpress-15.0.95-installer_rK-V8L1.tmp (PID: 7212)
- component0.exe (PID: 2700)
- UnifiedStub-installer.exe (PID: 7980)
- WerFault.exe (PID: 7076)
- WerFault.exe (PID: 7864)
- rsWSC.exe (PID: 6436)
- rsAppUI.exe (PID: 1076)
Reads the software policy settings
- explorer.exe (PID: 4552)
- phraseexpress-15.0.95-installer_rK-V8L1.tmp (PID: 7212)
- component0.exe (PID: 2700)
- UnifiedStub-installer.exe (PID: 7980)
- WerFault.exe (PID: 7076)
- WerFault.exe (PID: 7864)
- msiexec.exe (PID: 300)
- rsWSC.exe (PID: 6436)
- rsEngineSvc.exe (PID: 7828)
- rsWSC.exe (PID: 964)
- rsEDRSvc.exe (PID: 8040)
- rsEngineSvc.exe (PID: 7408)
- rsEDRSvc.exe (PID: 6556)
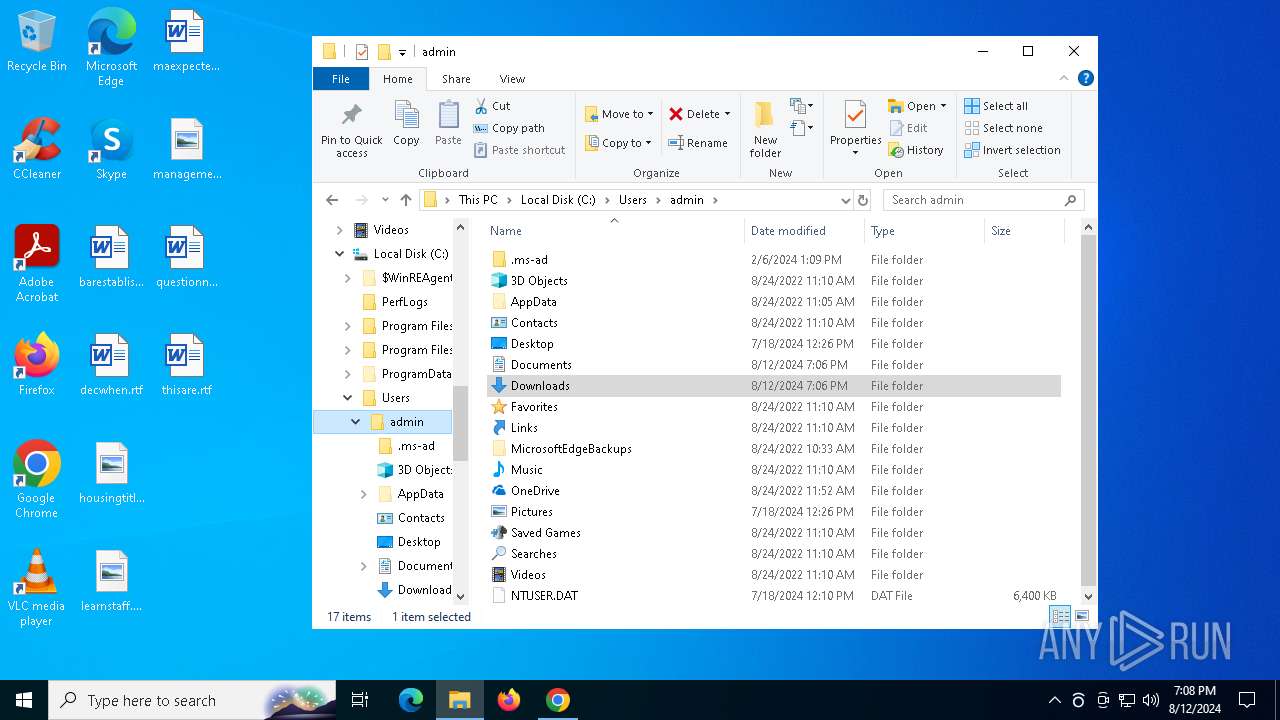
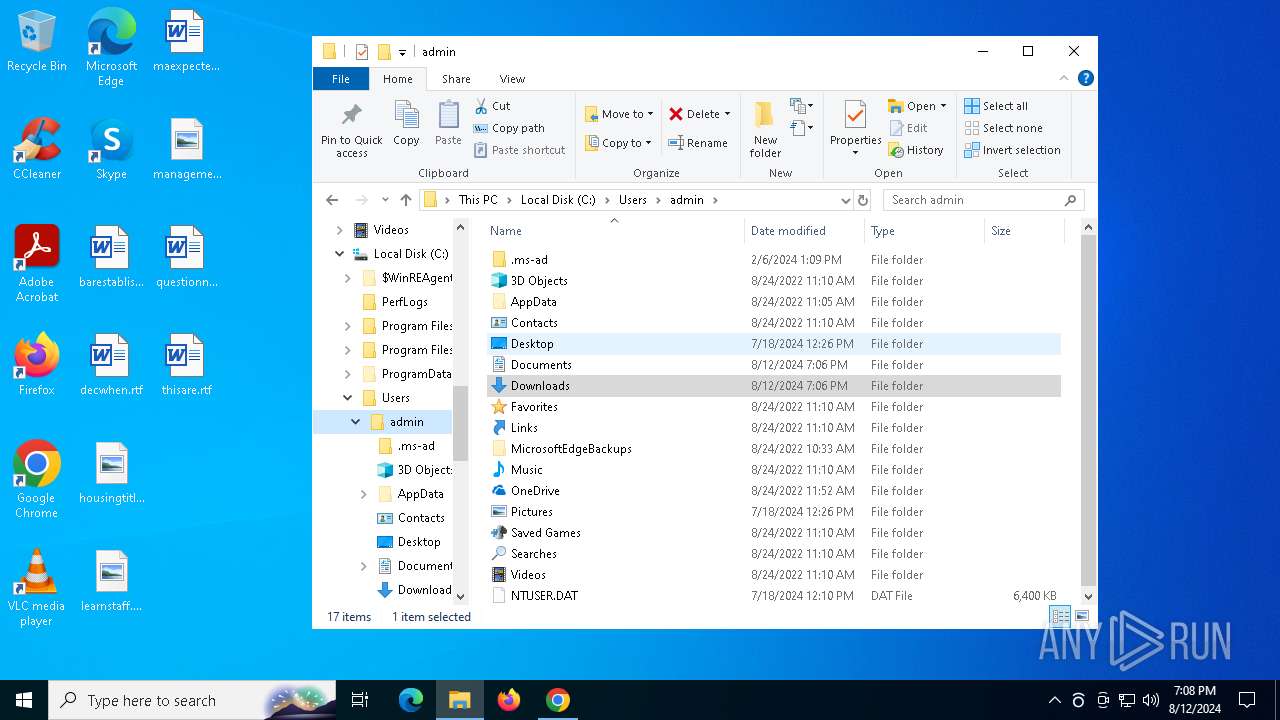
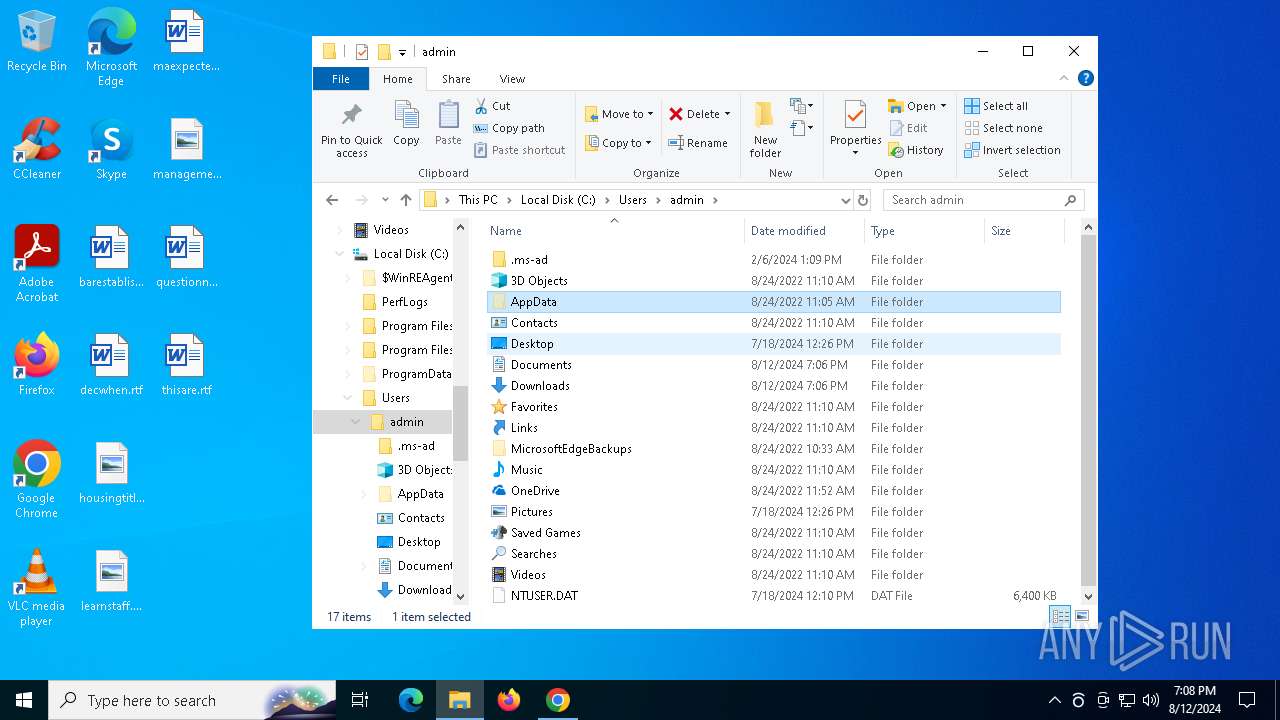
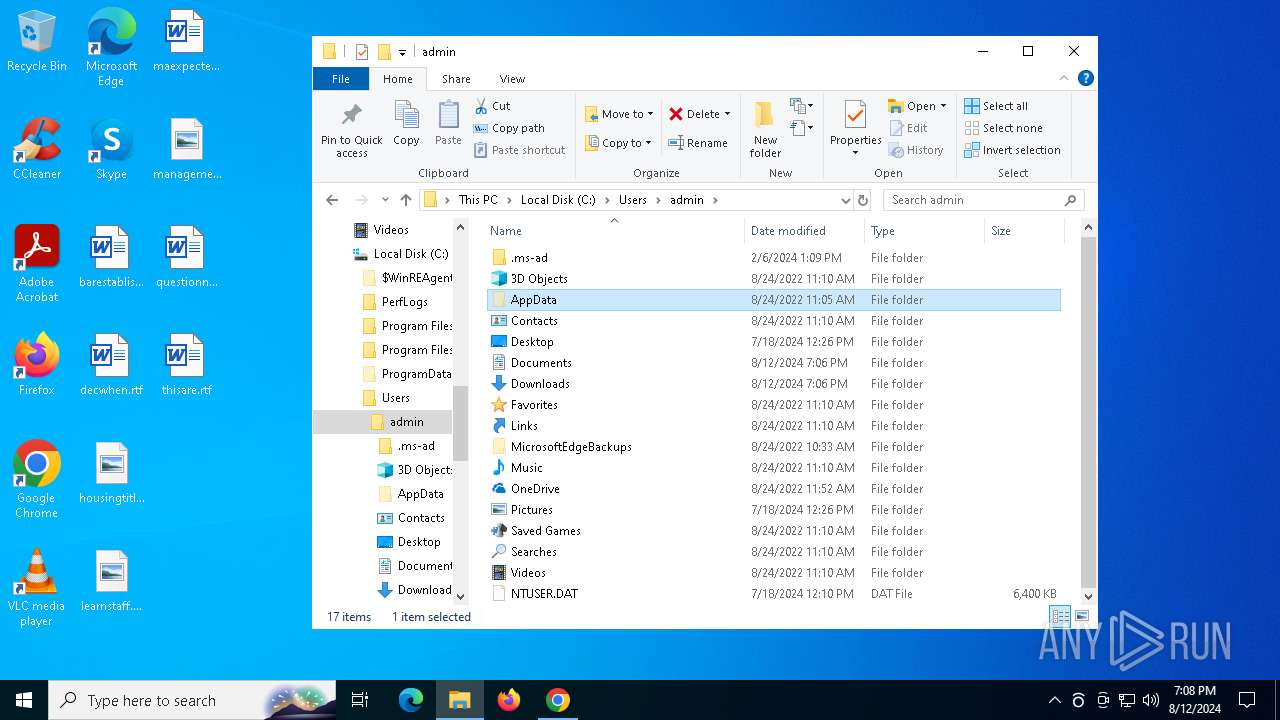
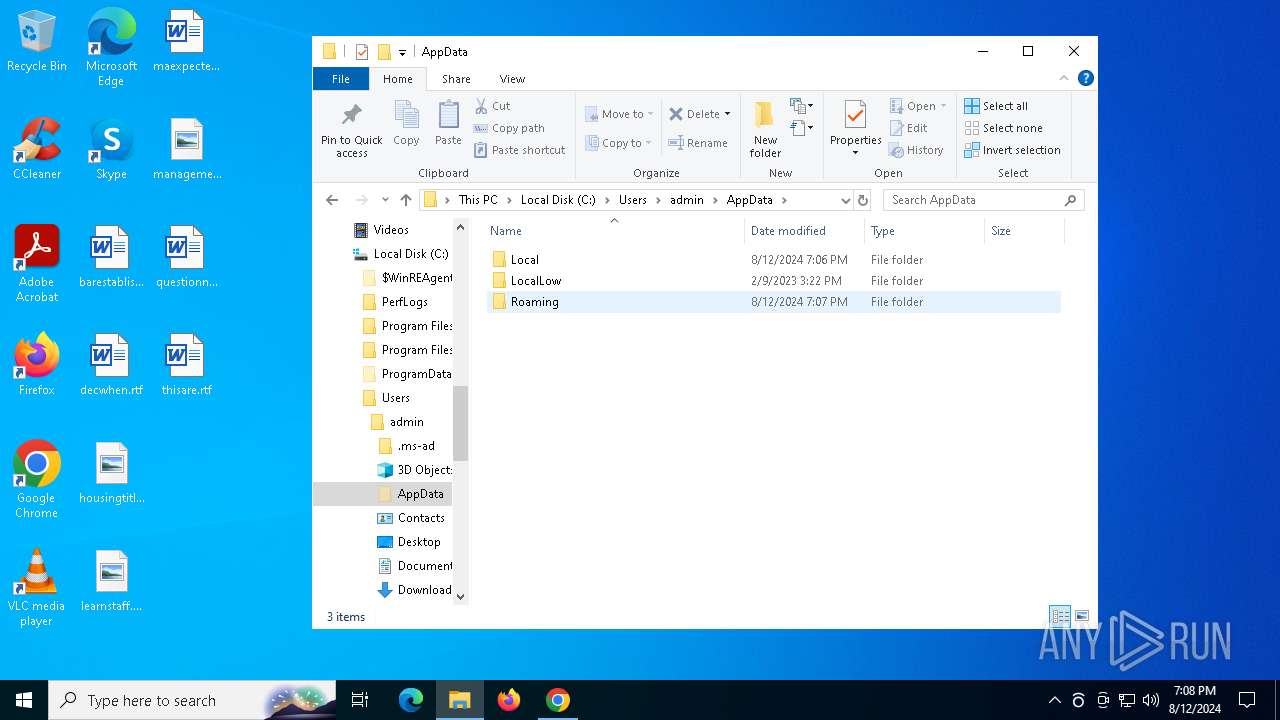
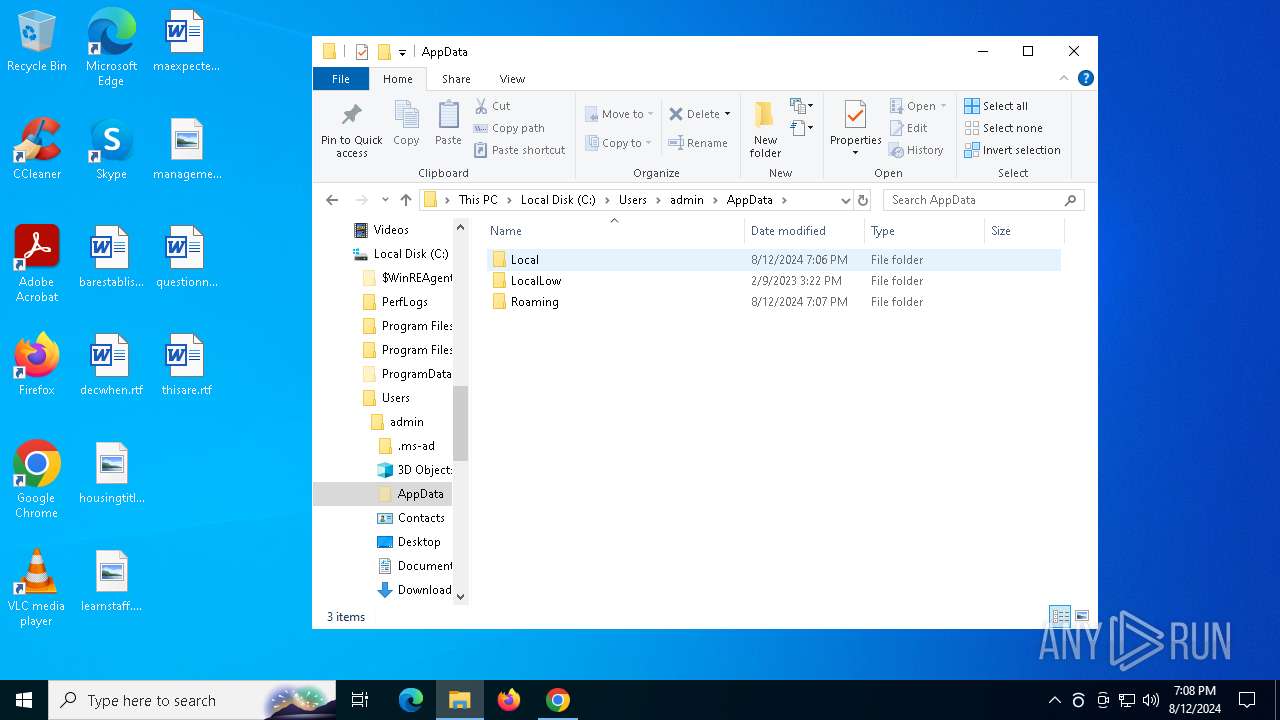
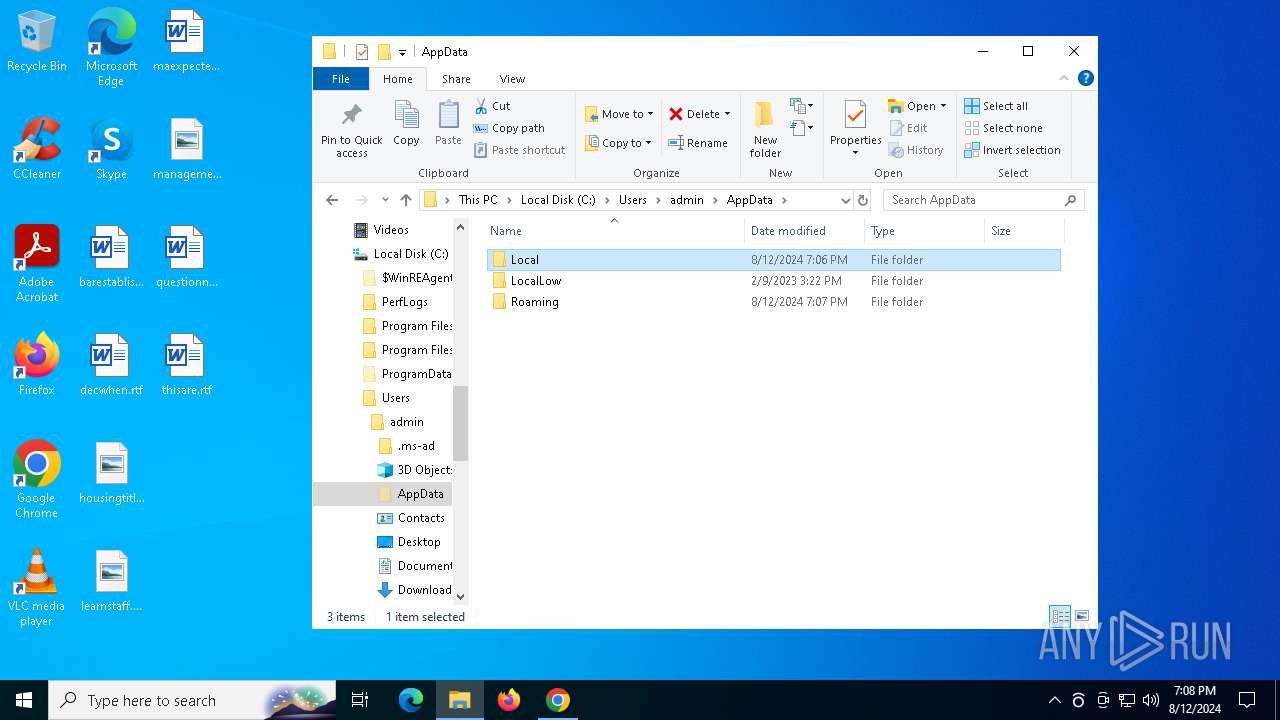
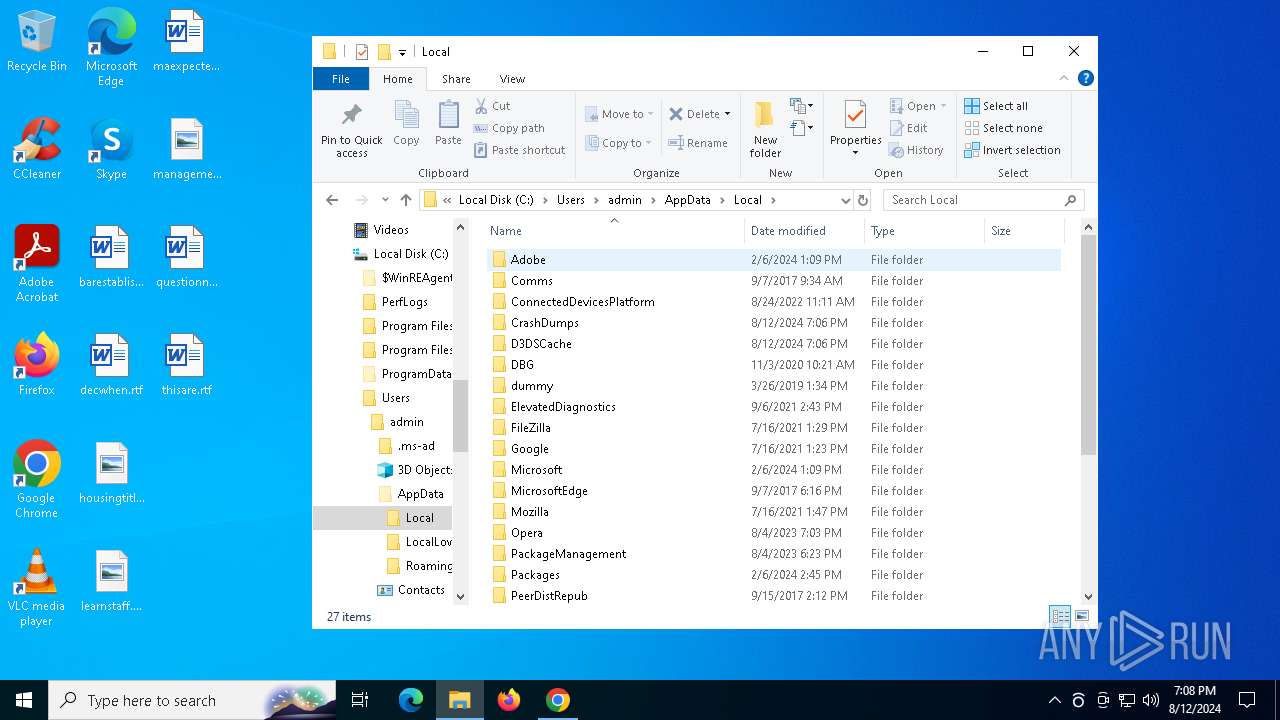
Creates files or folders in the user directory
- explorer.exe (PID: 4552)
- WerFault.exe (PID: 7076)
- WerFault.exe (PID: 7864)
- msiexec.exe (PID: 300)
- phraseexpress.exe (PID: 7504)
- UnifiedStub-installer.exe (PID: 7980)
- rsWSC.exe (PID: 6436)
- rsEngineSvc.exe (PID: 7408)
- rsAppUI.exe (PID: 1076)
- rsAppUI.exe (PID: 7500)
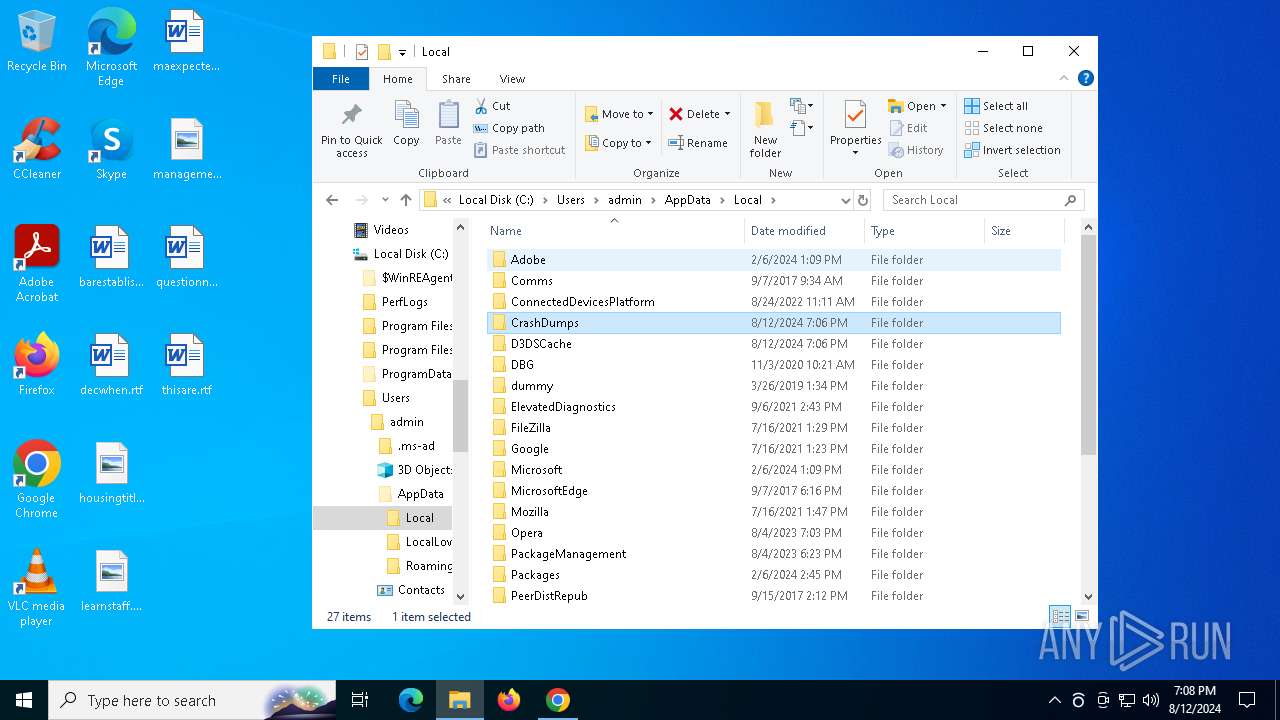
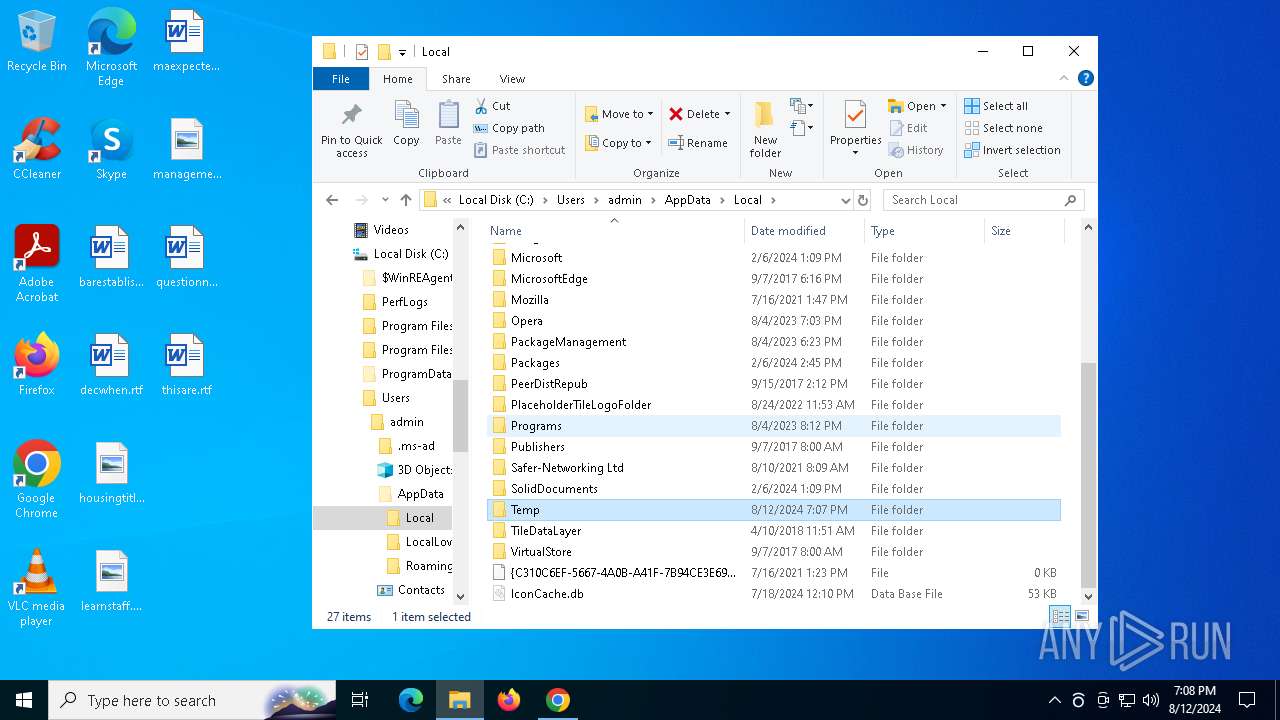
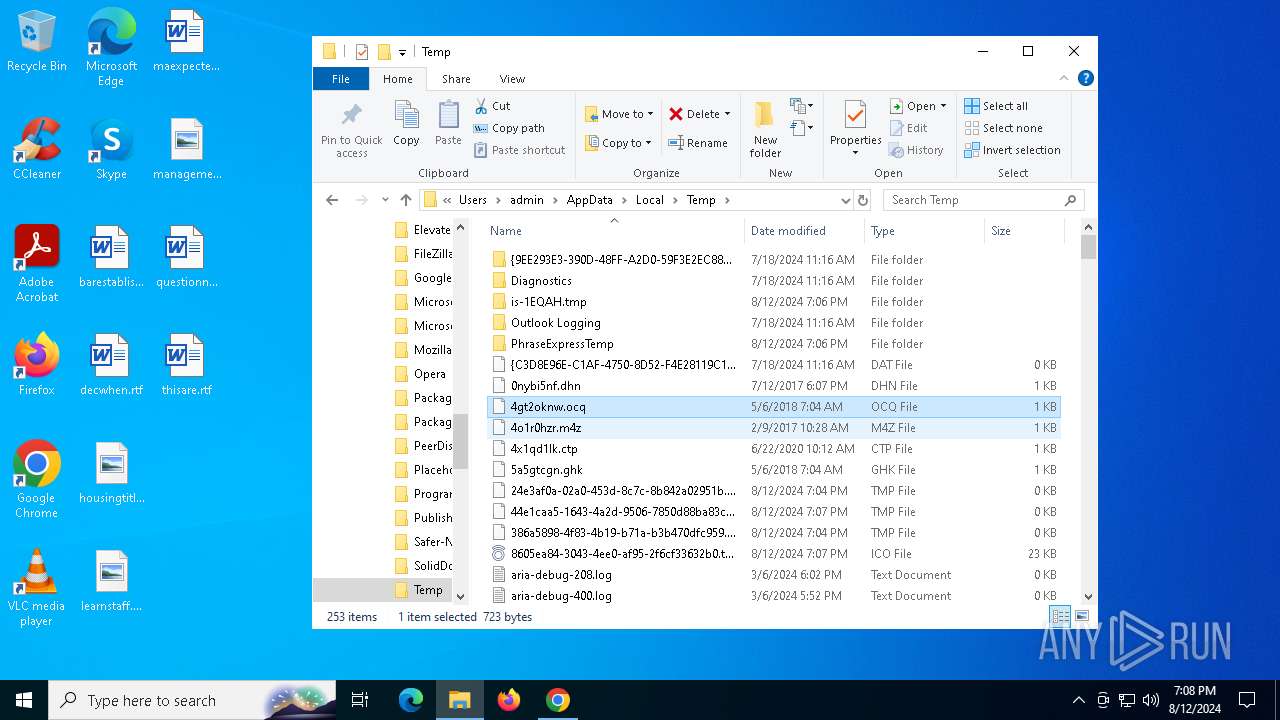
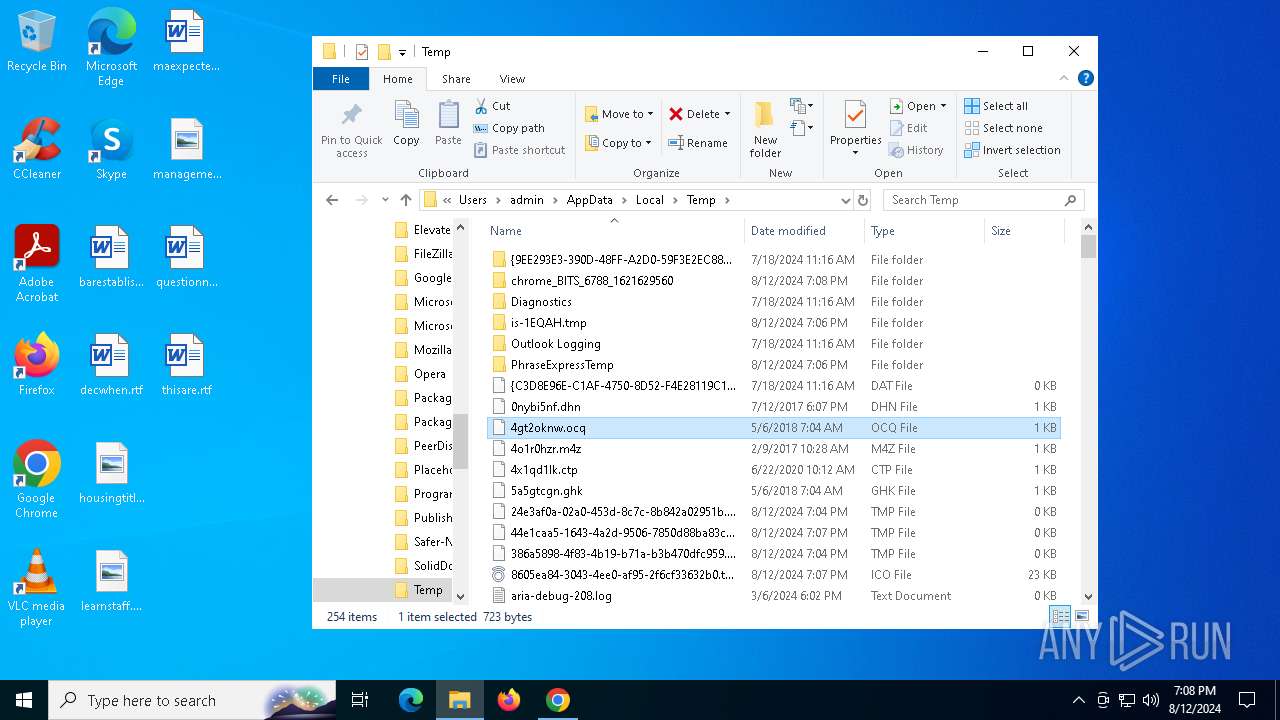
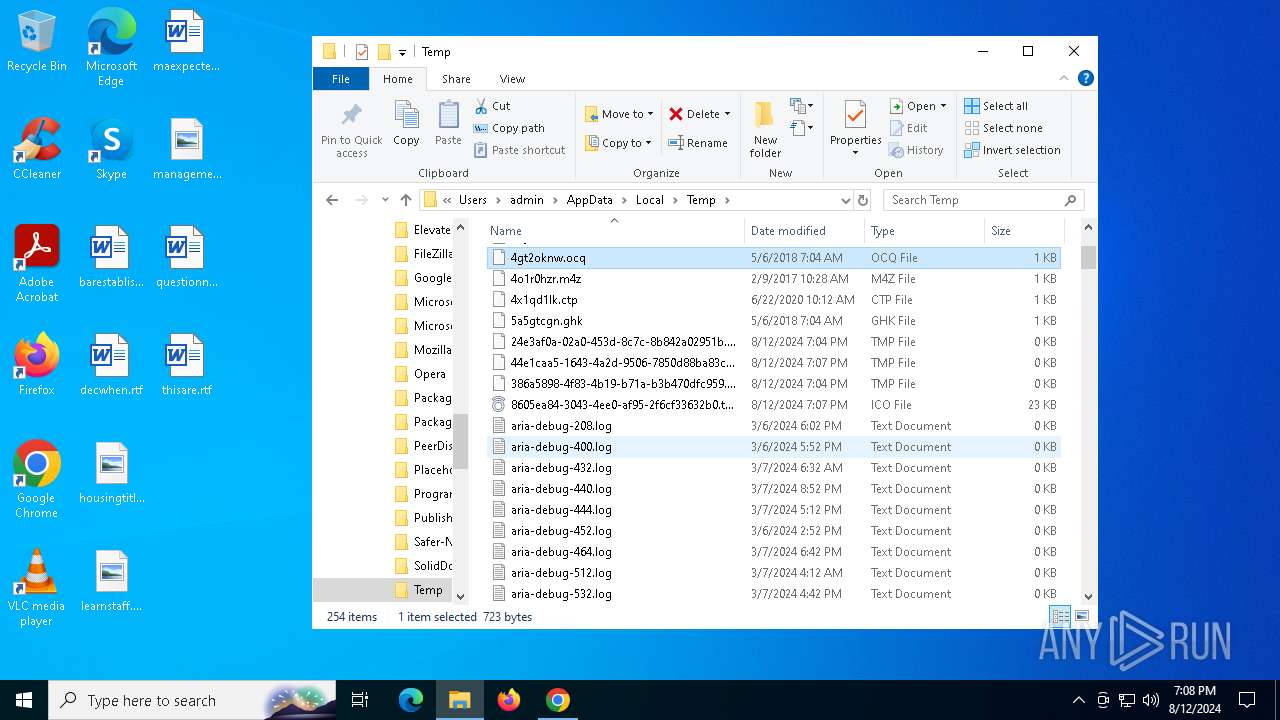
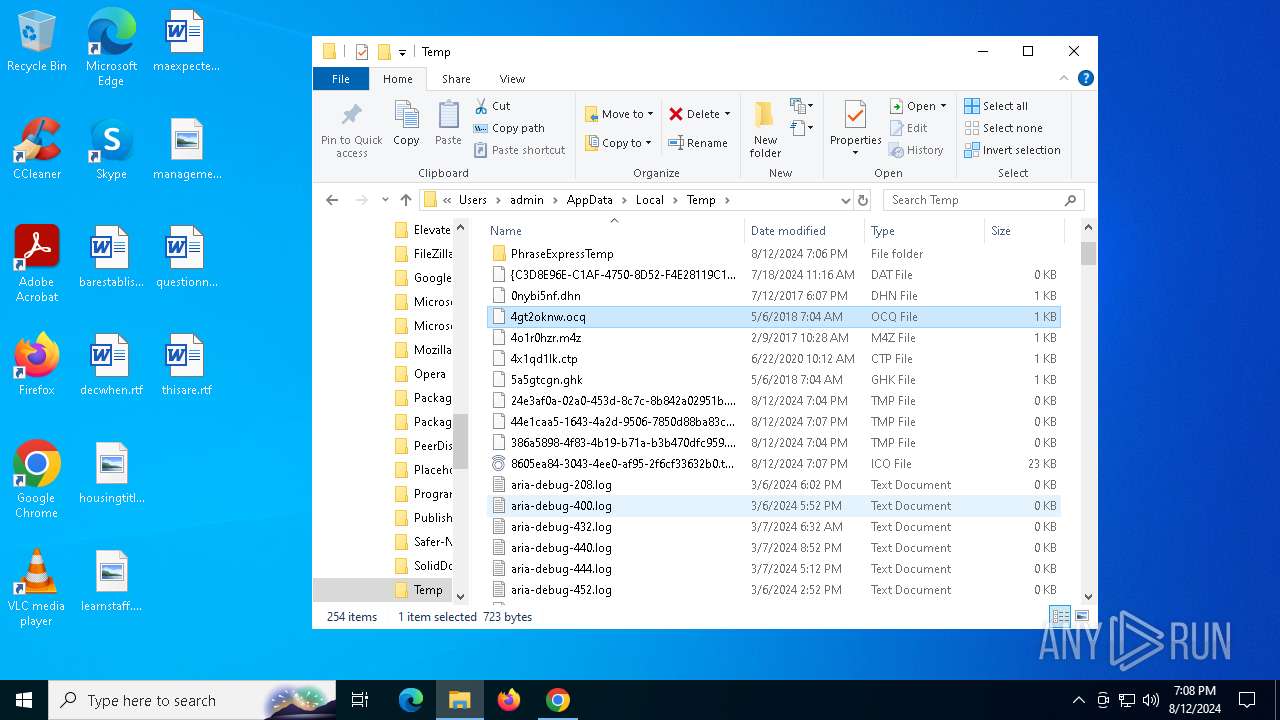
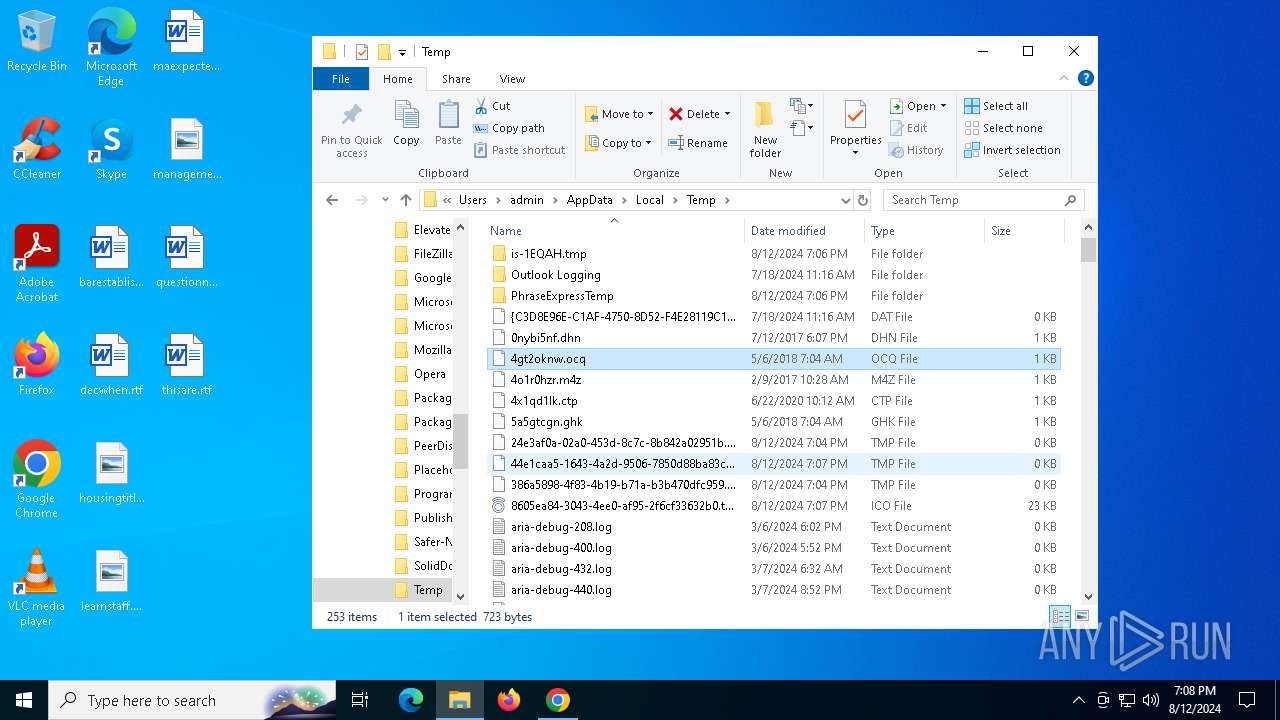
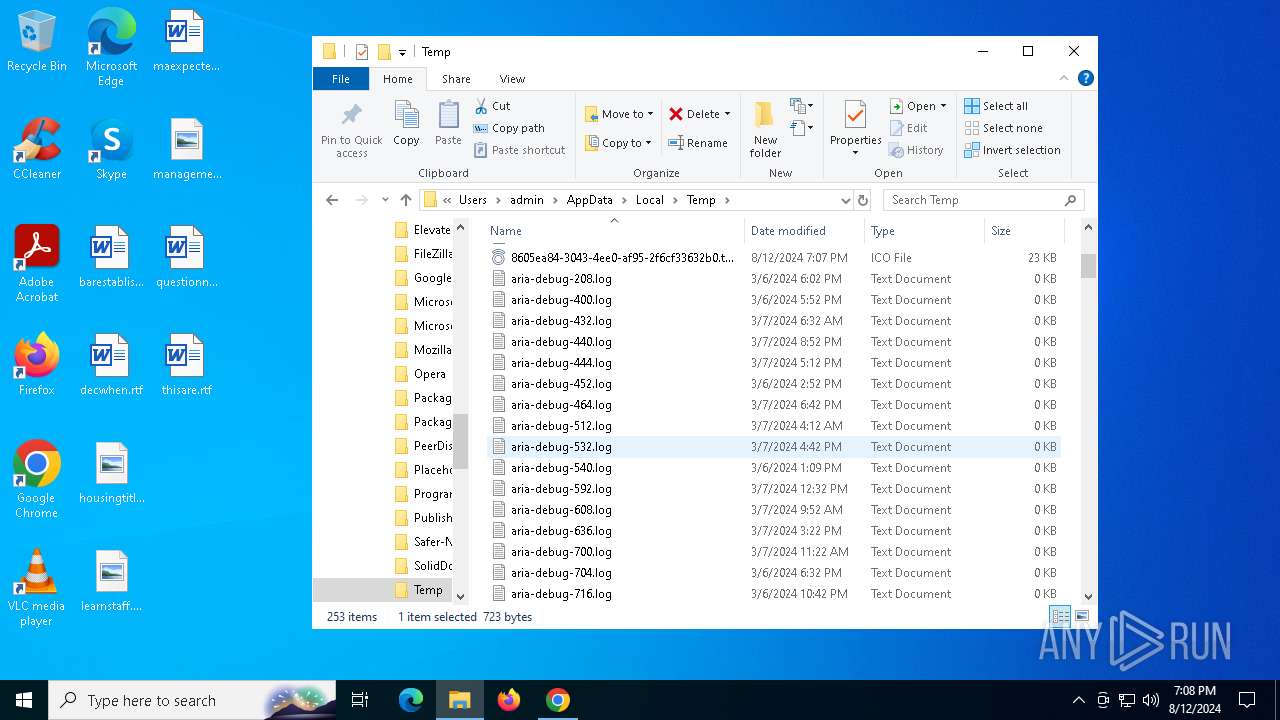
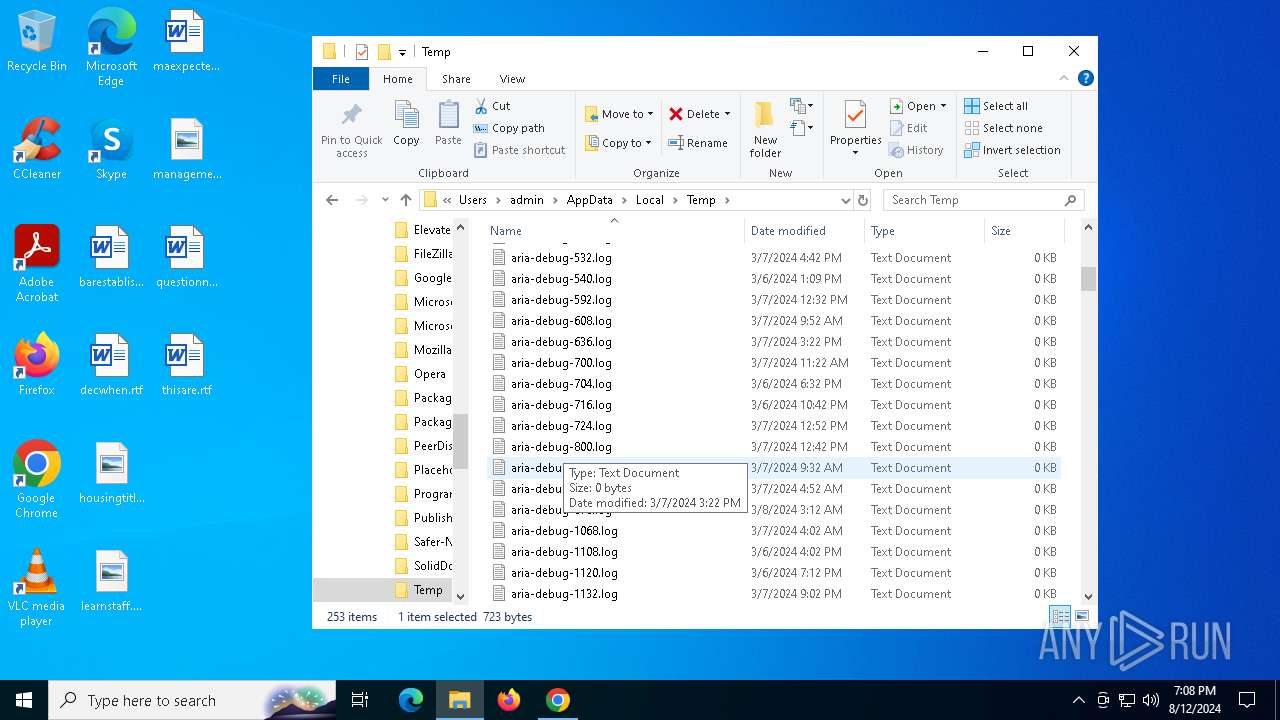
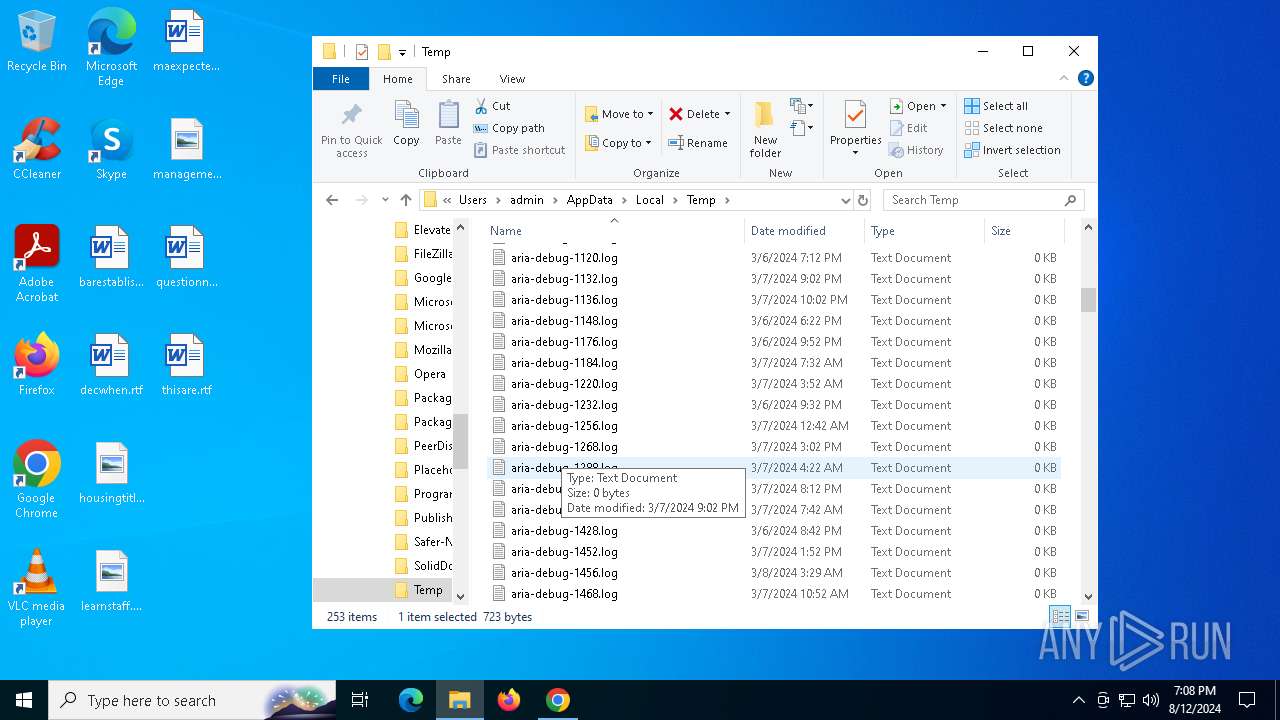
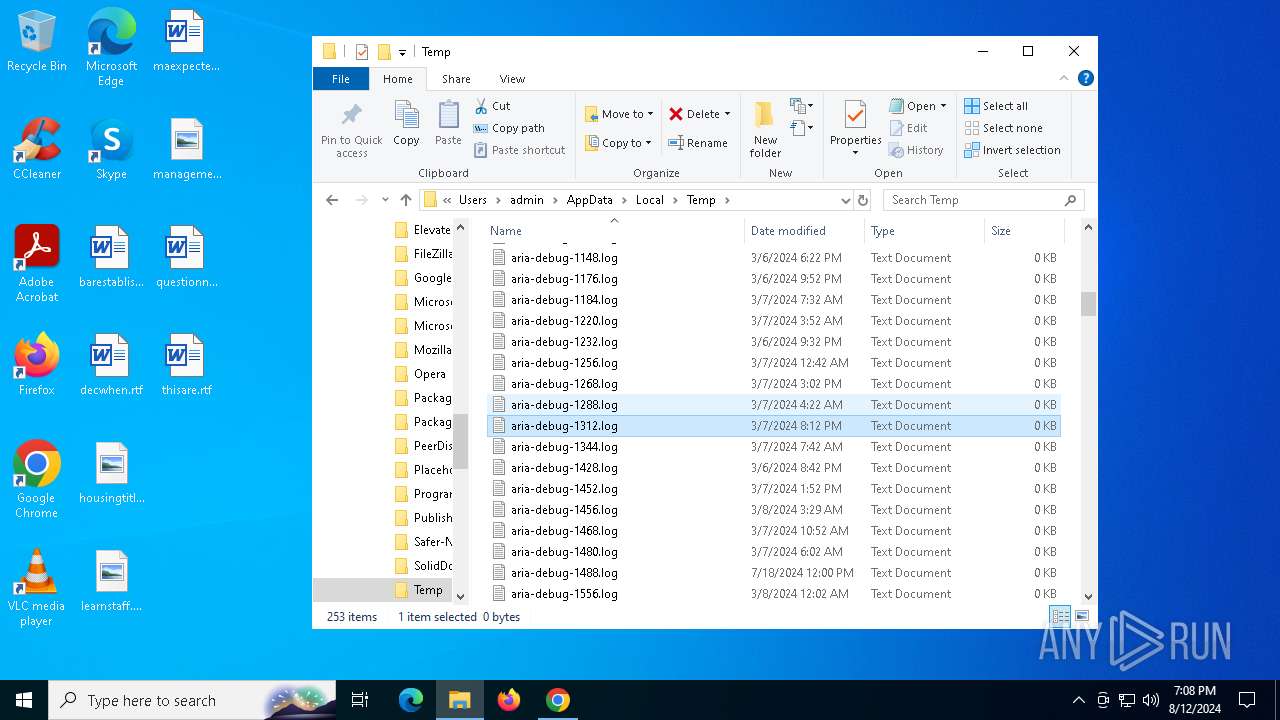
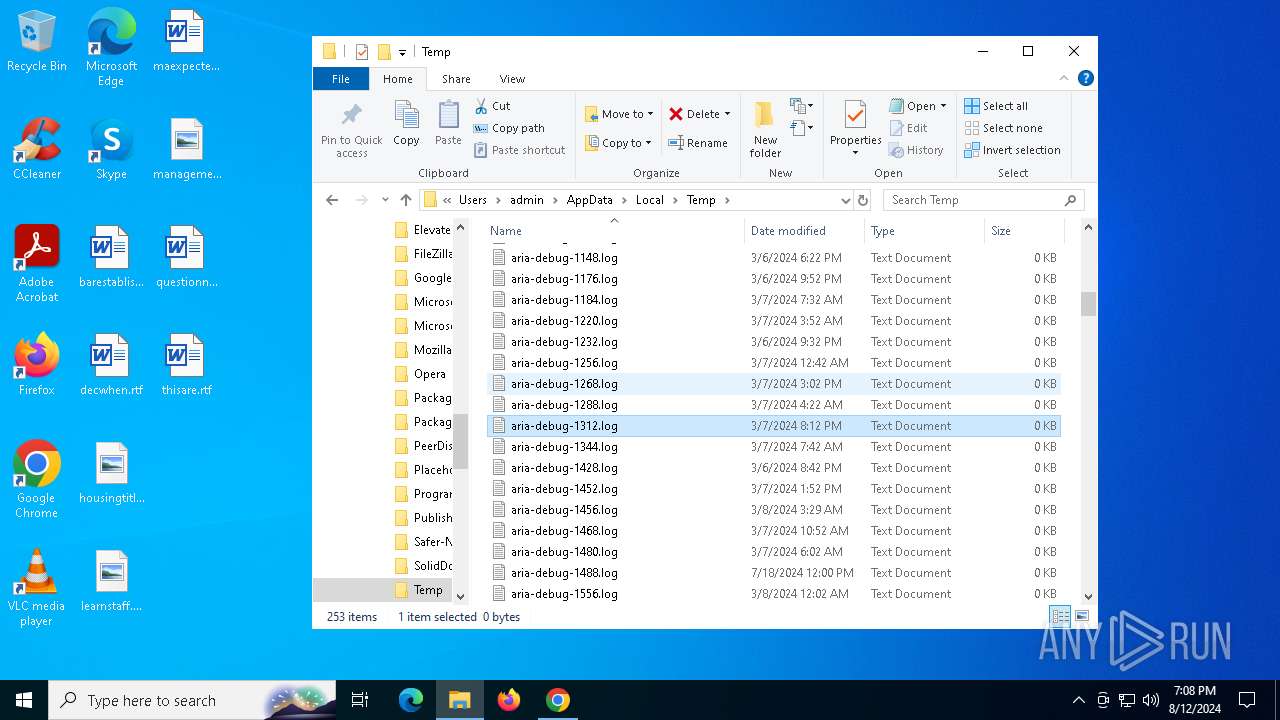
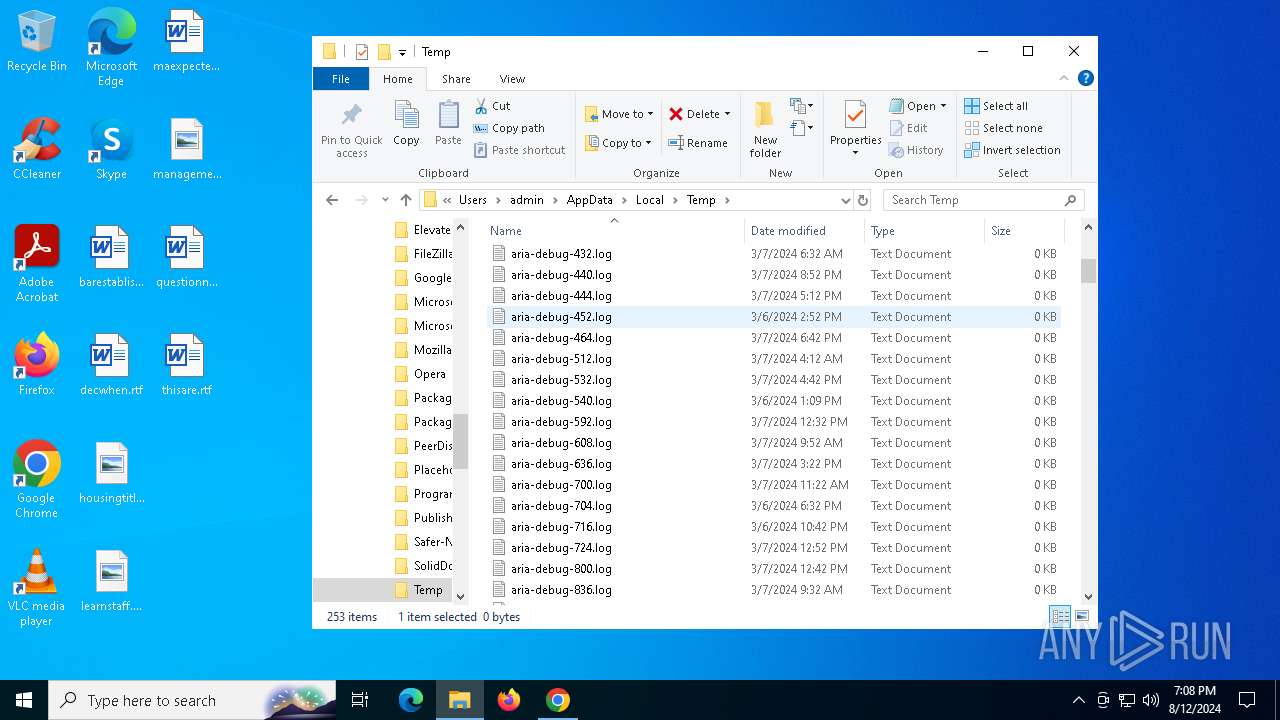
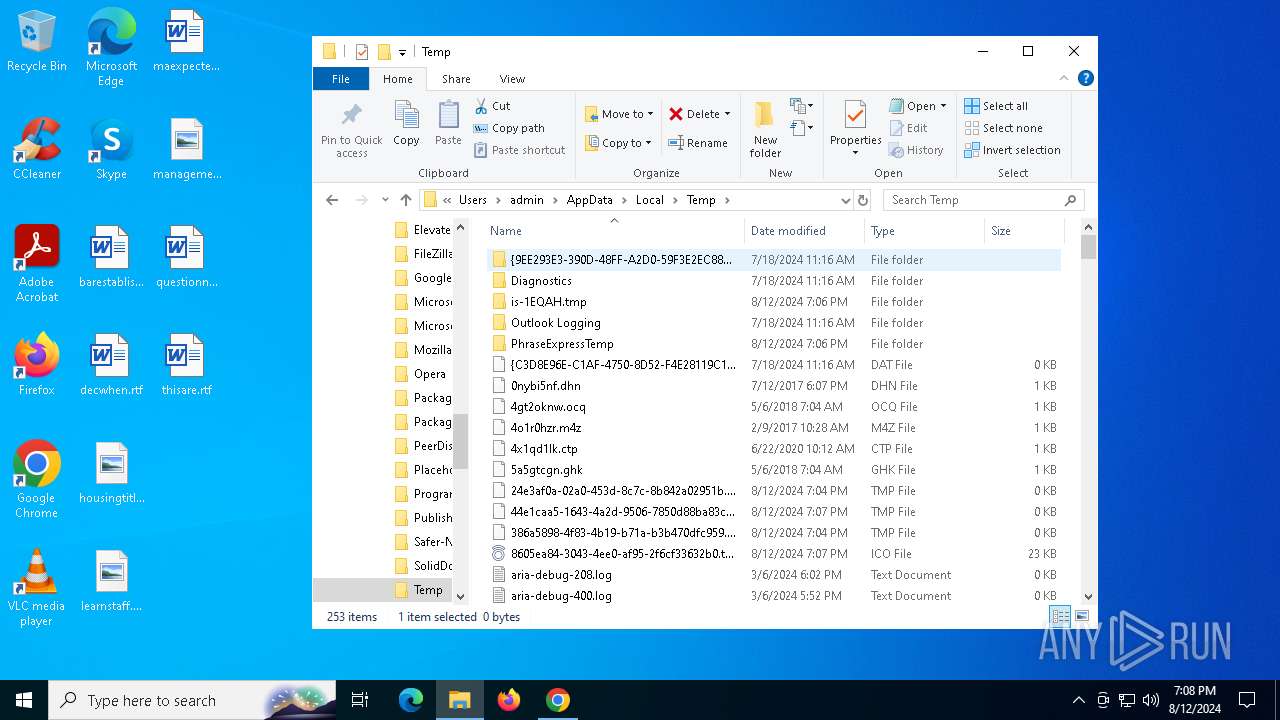
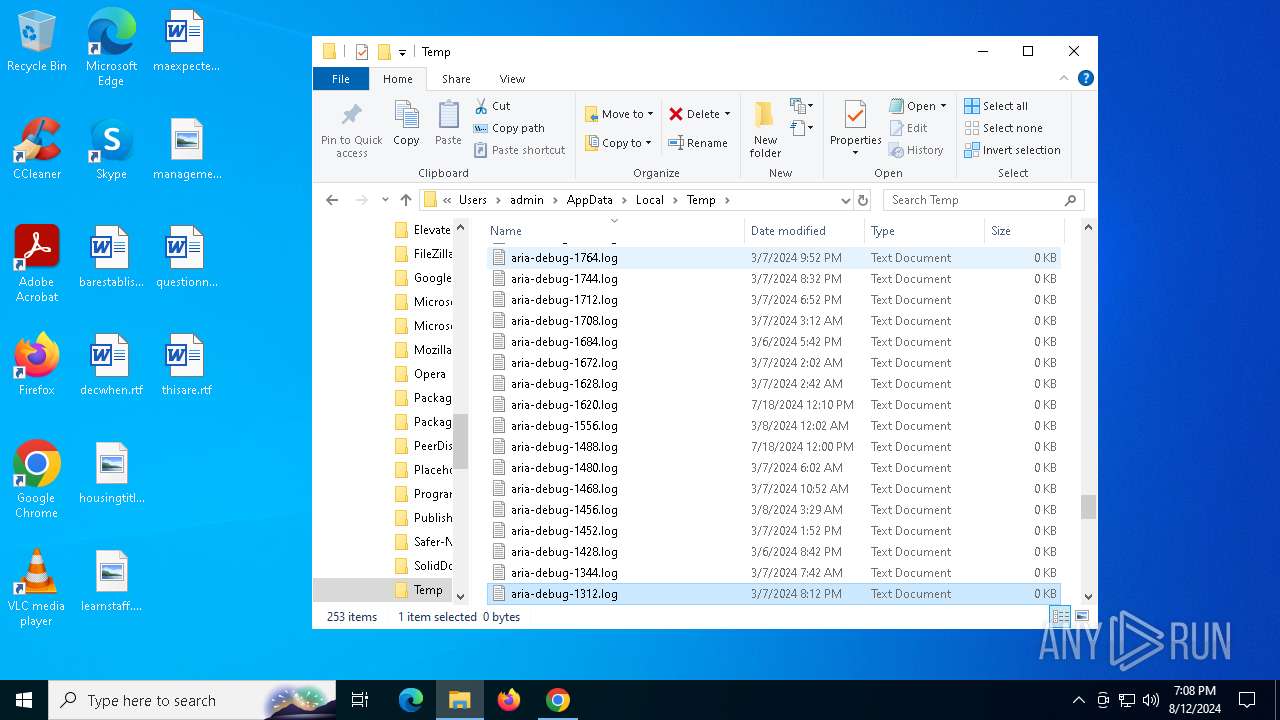
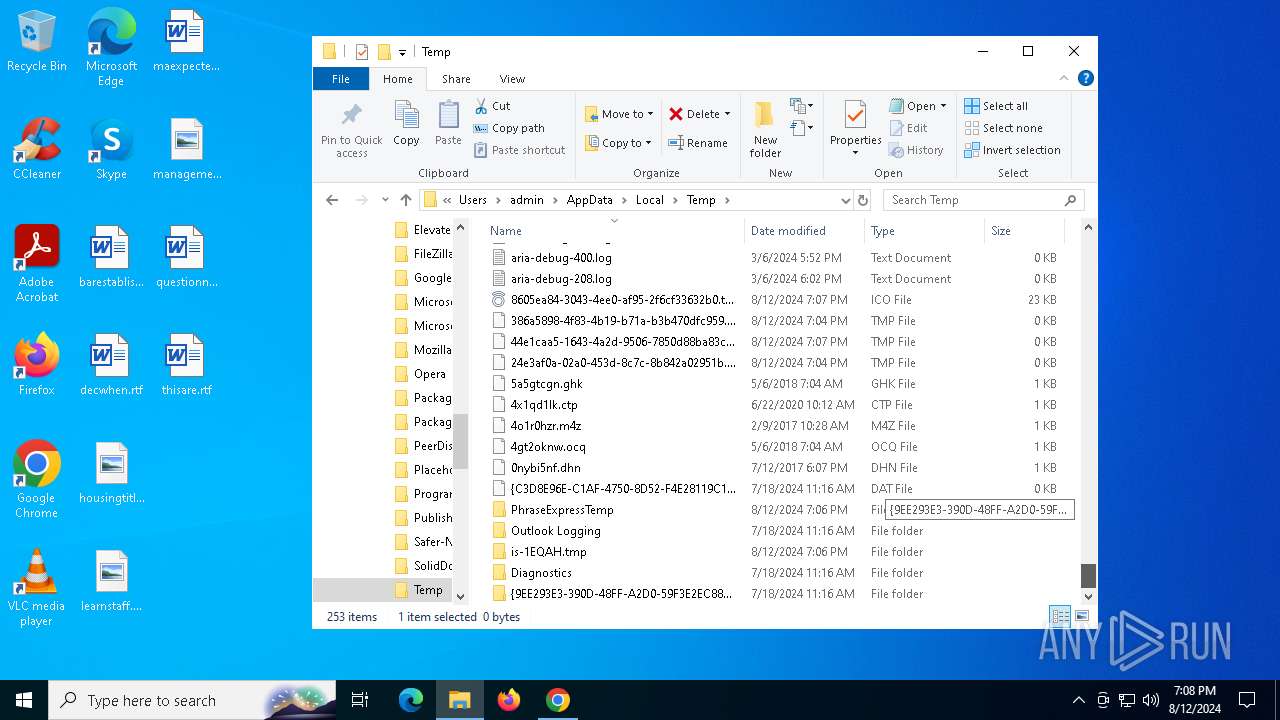
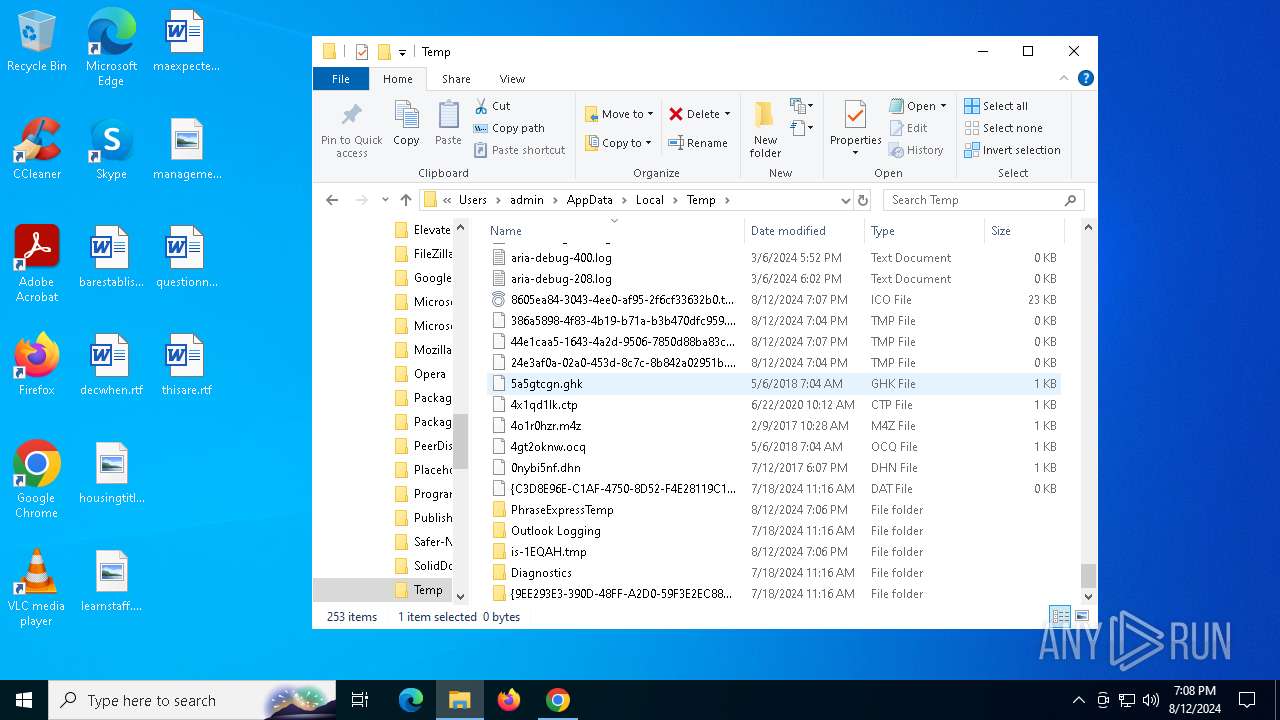
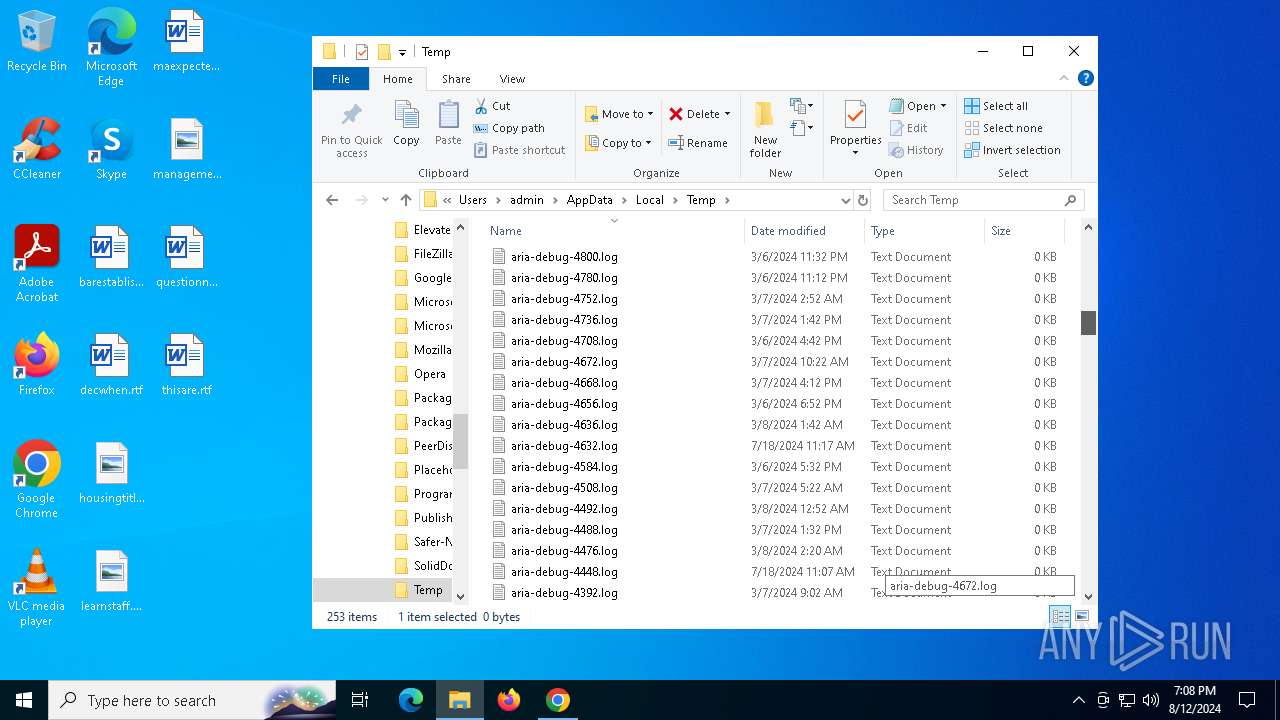
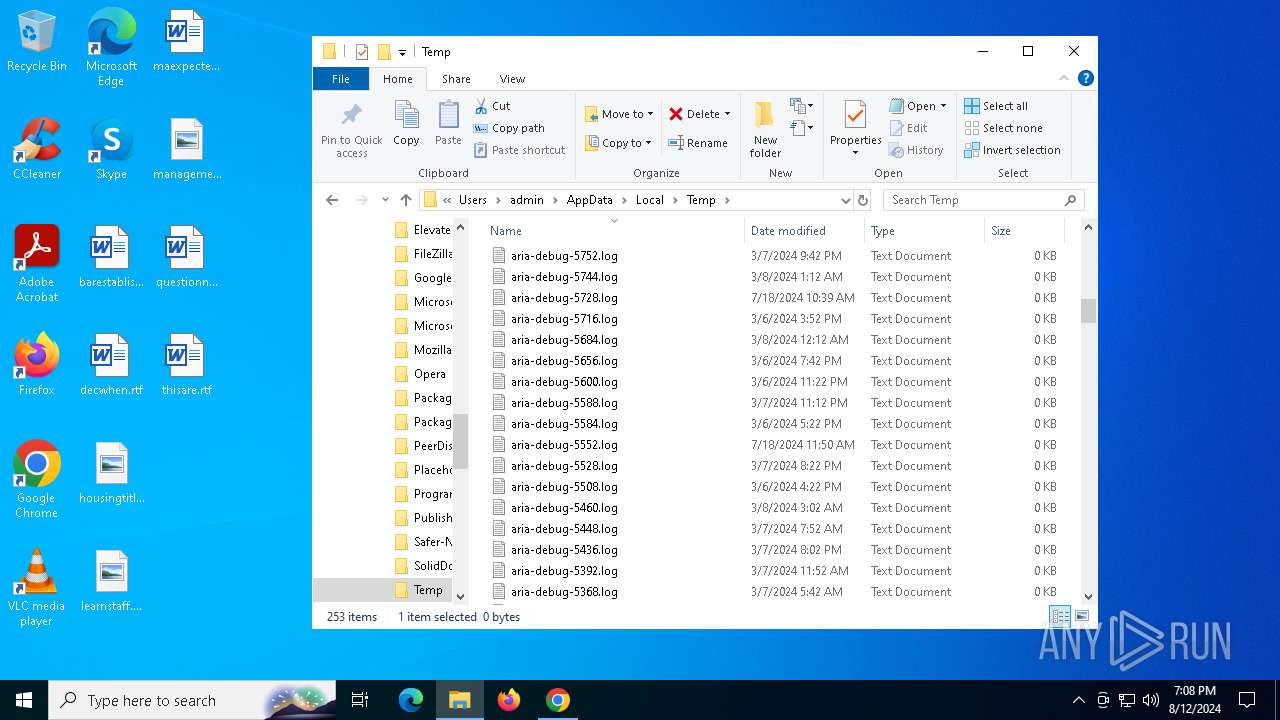
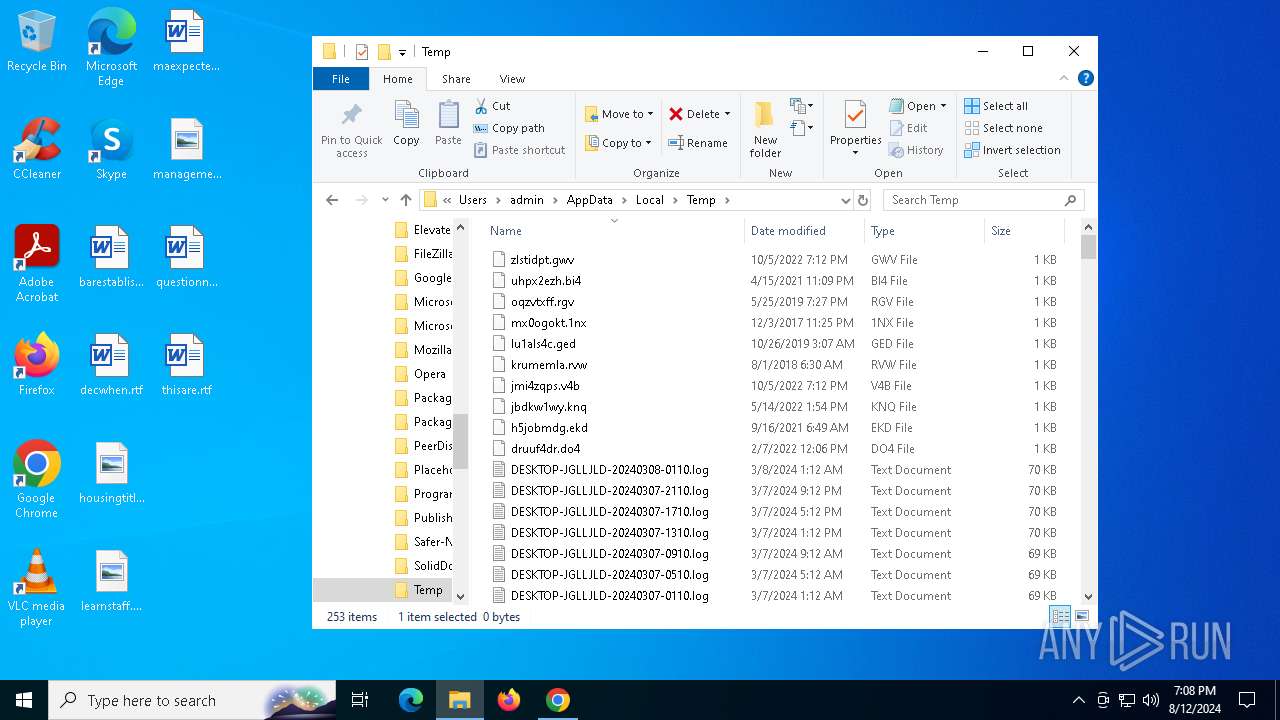
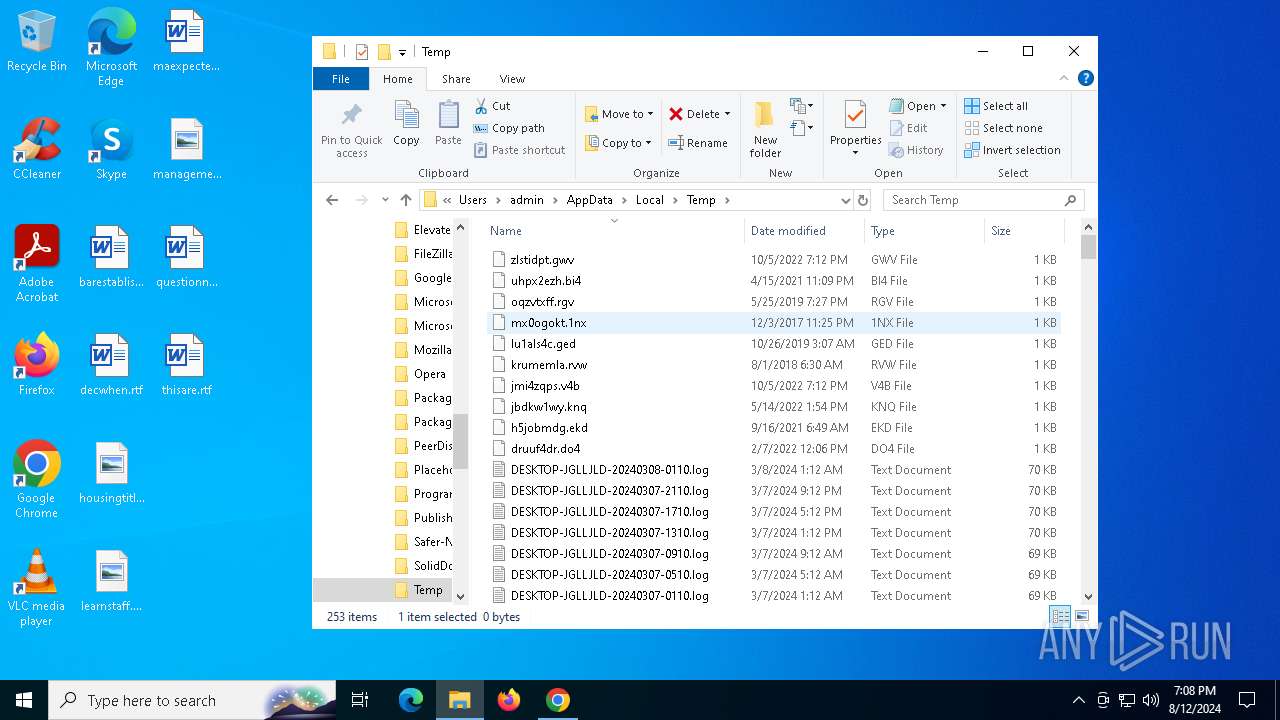
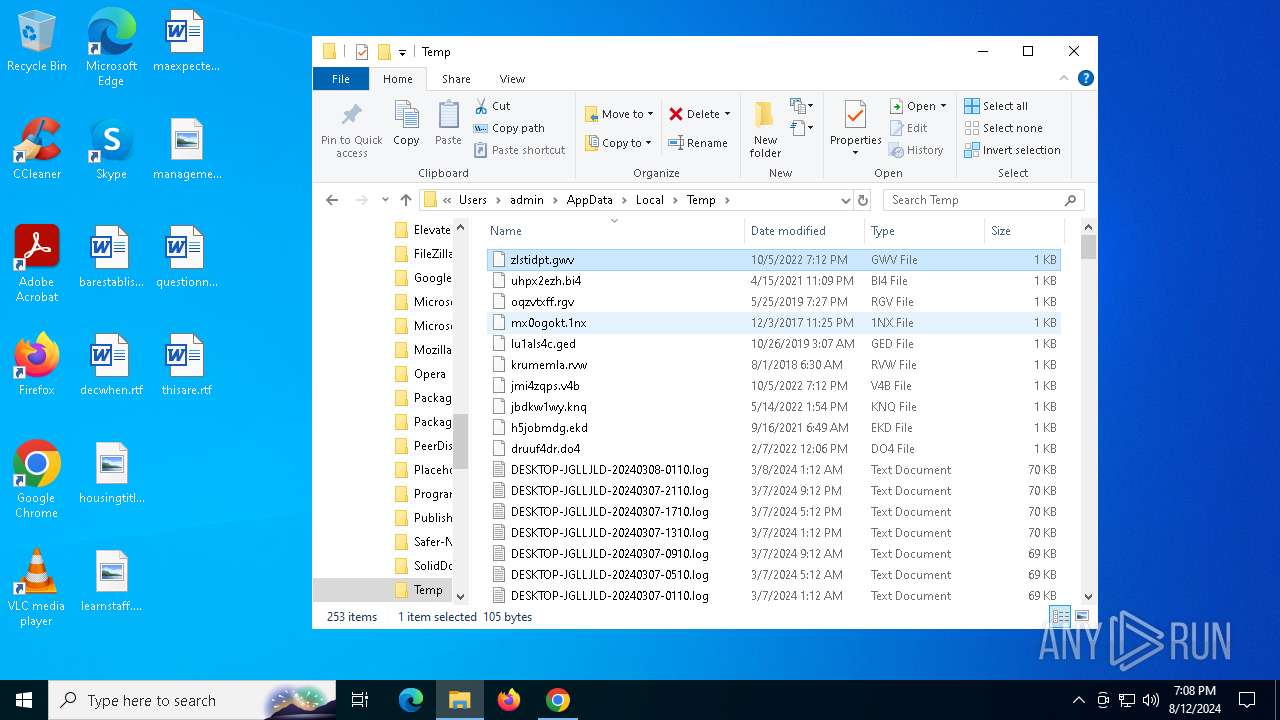
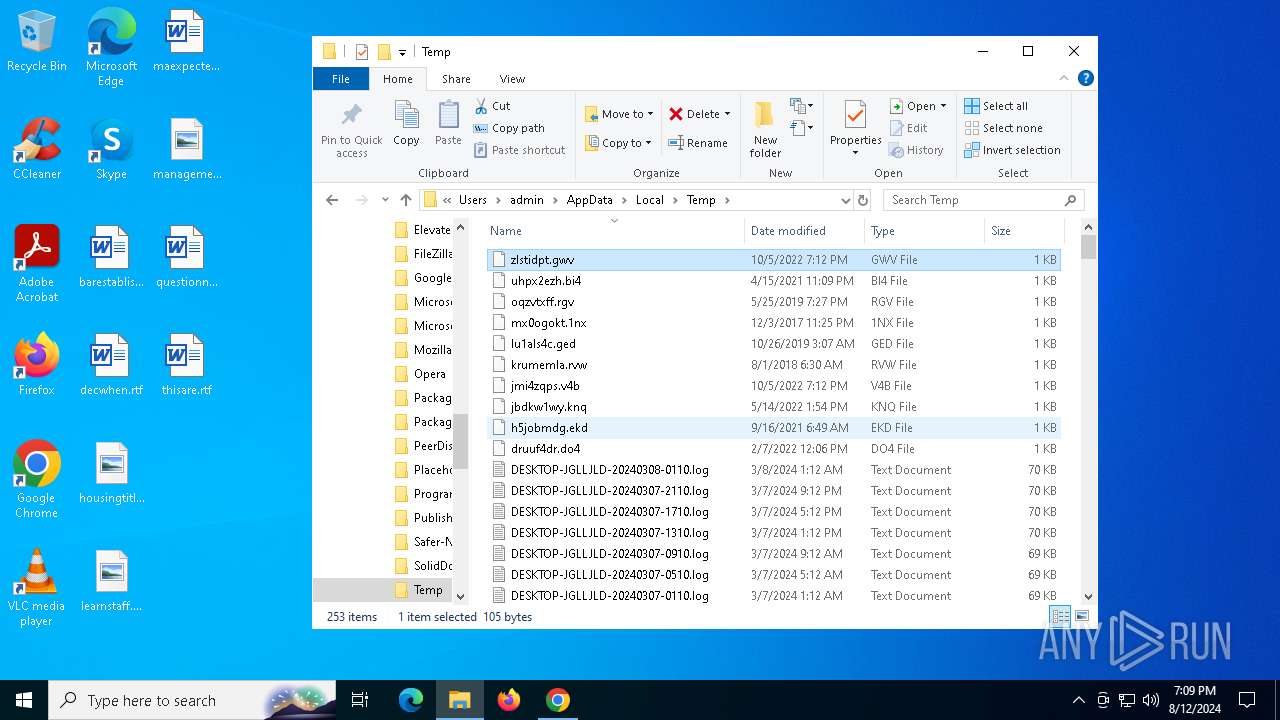
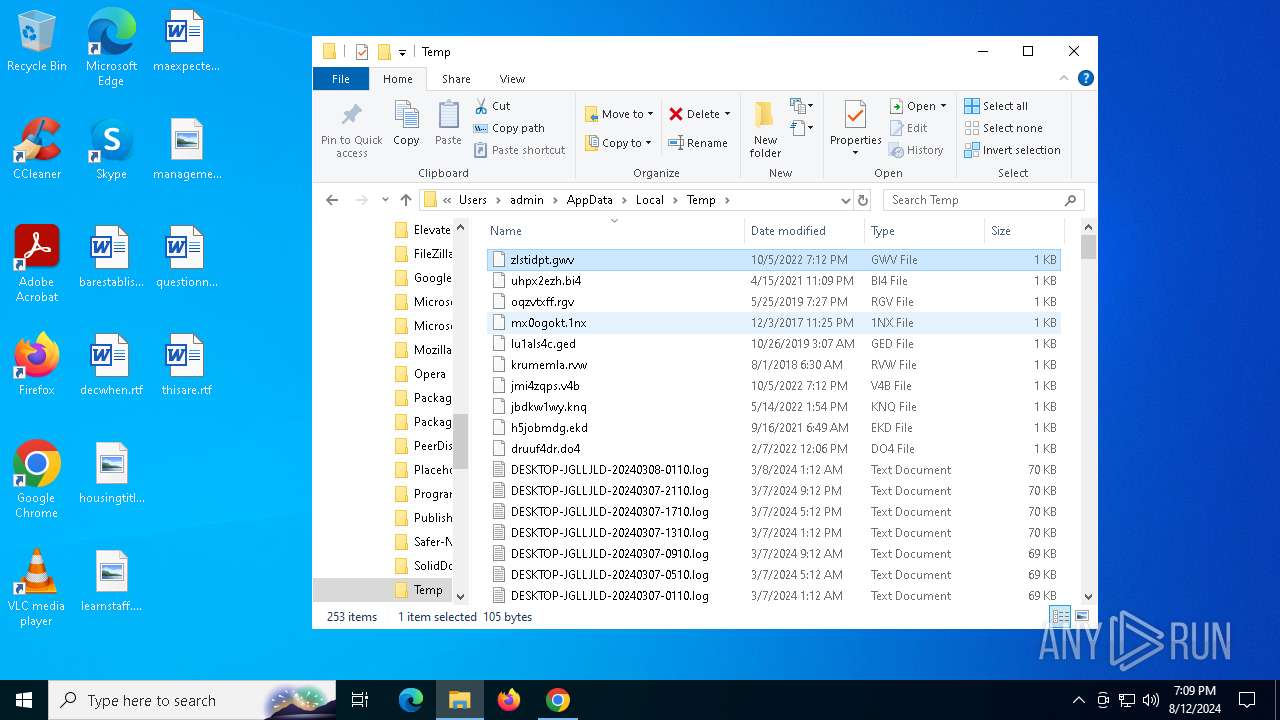
Create files in a temporary directory
- phraseexpress-15.0.95-installer_rK-V8L1.exe (PID: 7456)
- phraseexpress-15.0.95-installer_rK-V8L1.exe (PID: 7224)
- phraseexpress-15.0.95-installer_rK-V8L1.tmp (PID: 7212)
- component0.exe (PID: 2700)
- x55vf2cy.exe (PID: 6336)
- phraseexpress-15.0.95-installer.exe (PID: 8056)
- phraseexpress-15.0.95-installer.tmp (PID: 6700)
- UnifiedStub-installer.exe (PID: 7980)
- rsAppUI.exe (PID: 1076)
Process checks computer location settings
- phraseexpress-15.0.95-installer_rK-V8L1.tmp (PID: 7460)
- phraseexpress-15.0.95-installer_rK-V8L1.tmp (PID: 7212)
- component0.exe (PID: 2700)
- rsAppUI.exe (PID: 6644)
- rsAppUI.exe (PID: 1076)
- rsAppUI.exe (PID: 3180)
Application launched itself
- chrome.exe (PID: 6788)
- msiexec.exe (PID: 300)
Reads the machine GUID from the registry
- phraseexpress-15.0.95-installer_rK-V8L1.tmp (PID: 7212)
- component0.exe (PID: 2700)
- UnifiedStub-installer.exe (PID: 7980)
- rsWSC.exe (PID: 6436)
- rsWSC.exe (PID: 964)
- rsEngineSvc.exe (PID: 7828)
- rsEngineSvc.exe (PID: 7408)
- rsEDRSvc.exe (PID: 8040)
- rsHelper.exe (PID: 3372)
- rsEDRSvc.exe (PID: 6556)
- rsAppUI.exe (PID: 1076)
- msiexec.exe (PID: 300)
Reads Environment values
- component0.exe (PID: 2700)
- UnifiedStub-installer.exe (PID: 7980)
- rsEngineSvc.exe (PID: 7408)
- rsEDRSvc.exe (PID: 6556)
- rsAppUI.exe (PID: 1076)
Disables trace logs
- component0.exe (PID: 2700)
- UnifiedStub-installer.exe (PID: 7980)
- rsEngineSvc.exe (PID: 7408)
- rsEDRSvc.exe (PID: 6556)
Creates files in the program directory
- UnifiedStub-installer.exe (PID: 7980)
- phraseexpress-15.0.95-installer.tmp (PID: 6700)
- rsWSC.exe (PID: 6436)
- rsEngineSvc.exe (PID: 7828)
- rsEDRSvc.exe (PID: 8040)
- rsEngineSvc.exe (PID: 7408)
- rsEDRSvc.exe (PID: 6556)
Creates a software uninstall entry
- phraseexpress-15.0.95-installer.tmp (PID: 6700)
- msiexec.exe (PID: 300)
.NET Reactor protector has been detected
- UnifiedStub-installer.exe (PID: 7980)
- rsWSC.exe (PID: 964)
- rsEDRSvc.exe (PID: 6556)
- rsHelper.exe (PID: 3372)
- rsEngineSvc.exe (PID: 7408)
Reads the time zone
- runonce.exe (PID: 6080)
- rsEDRSvc.exe (PID: 6556)
- rsEngineSvc.exe (PID: 7408)
Reads product name
- rsEDRSvc.exe (PID: 6556)
- rsAppUI.exe (PID: 1076)
- rsEngineSvc.exe (PID: 7408)
Reads CPU info
- rsEDRSvc.exe (PID: 6556)
- rsEngineSvc.exe (PID: 7408)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
226
Monitored processes
81
Malicious processes
15
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 876 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoABAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=5516 --field-trial-handle=1884,i,6700221146191719877,5123668629668536986,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 964 | "C:\Program Files\ReasonLabs\EPP\rsWSC.exe" | C:\Program Files\ReasonLabs\EPP\rsWSC.exe | services.exe | ||||||||||||
User: SYSTEM Company: Reason Software Company Inc. Integrity Level: SYSTEM Description: rsWSC Version: 6.0.3.0 Modules
| |||||||||||||||
| 1076 | "C:\Program Files\ReasonLabs\Common\Client\v1.4.2\rsAppUI.exe" "c:\program files\reasonlabs\EPP\ui\app.asar" --engine-path="c:\program files\reasonlabs\EPP" --minimized --first-run | C:\Program Files\ReasonLabs\Common\Client\v1.4.2\rsAppUI.exe | — | EPP.exe | |||||||||||
User: admin Company: Reason Cybersecurity Ltd. Integrity Level: MEDIUM Description: ReasonLabs Application Version: 1.4.2 Modules
| |||||||||||||||
| 1116 | "C:\Program Files\ReasonLabs\EPP\rsClientSvc.exe" -i | C:\Program Files\ReasonLabs\EPP\rsClientSvc.exe | — | UnifiedStub-installer.exe | |||||||||||
User: admin Company: Reason Software Company Inc. Integrity Level: HIGH Description: Reason Client Service Exit code: 0 Version: 5.34.0 Modules
| |||||||||||||||
| 1128 | C:\Windows\System32\MsiExec.exe -Embedding 5772CCFAA4A81030D258D4A901D942DB E Global\MSI0000 | C:\Windows\System32\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1360 | C:\Windows\System32\MsiExec.exe -Embedding EAA0B91E348A3125E07BD3A126619F25 | C:\Windows\System32\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1372 | "C:\WINDOWS\system32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\is-B0UFI.tmp\sqlncli.msi" /quiet IACCEPTSQLNCLILICENSETERMS=YES | C:\Windows\SysWOW64\msiexec.exe | — | phraseexpress-15.0.95-installer.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1688 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4820 --field-trial-handle=1884,i,6700221146191719877,5123668629668536986,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1812 | "C:\Program Files\ReasonLabs\EPP\rsClientSvc.exe" | C:\Program Files\ReasonLabs\EPP\rsClientSvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Reason Software Company Inc. Integrity Level: SYSTEM Description: Reason Client Service Version: 5.34.0 Modules
| |||||||||||||||
Total events
157 280
Read events
156 265
Write events
909
Delete events
106
Modification events
| (PID) Process: | (4552) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Security and Maintenance\Checks\{C8E6F269-B90A-4053-A3BE-499AFCEC98C4}.check.0 |
| Operation: | write | Name: | CheckSetting |
Value: 23004100430042006C006F0062000000000000000000000001000000740065006D000000 | |||
| (PID) Process: | (4552) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:00000000000A0188 |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456033BCEE44DE41B4E8AEC331E84F566D2 | |||
| (PID) Process: | (4552) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FeatureUsage\AppBadgeUpdated |
| Operation: | write | Name: | Chrome |
Value: 5 | |||
| (PID) Process: | (6788) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6788) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6788) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (6788) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (6788) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6788) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (6788) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
Executable files
569
Suspicious files
315
Text files
144
Unknown types
360
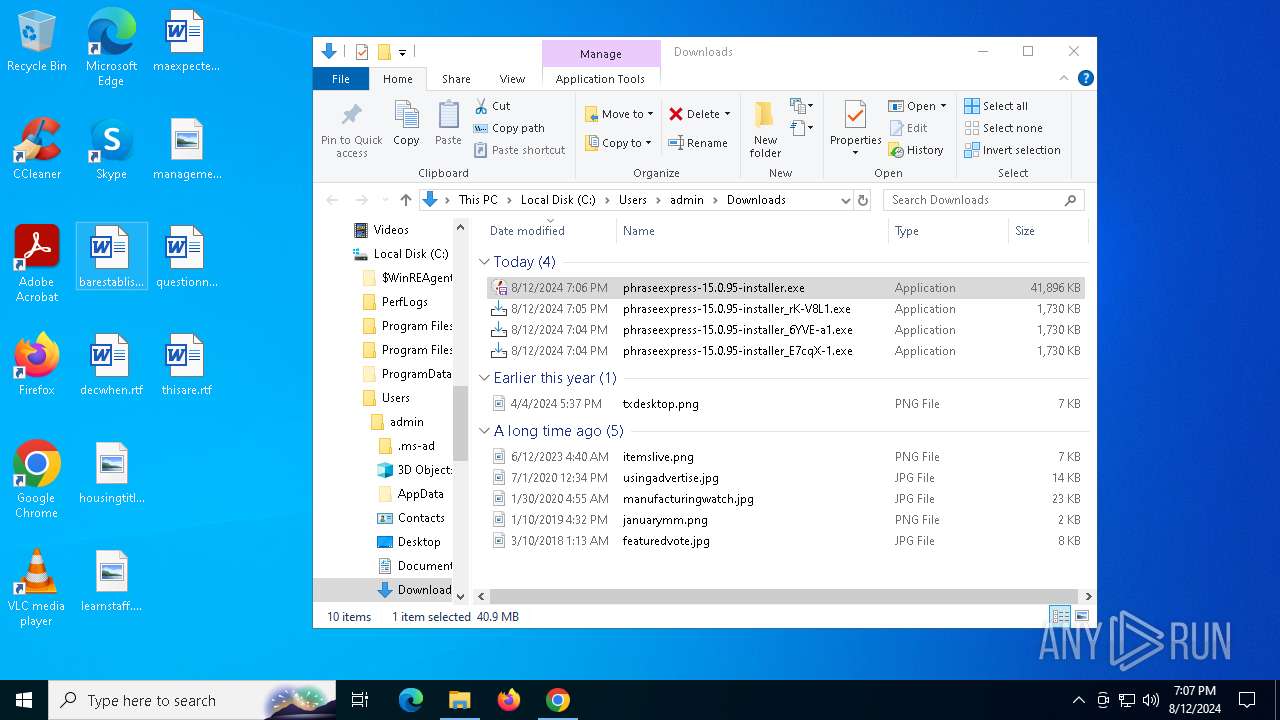
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RFe609a.TMP | — | |
MD5:— | SHA256:— | |||
| 6788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RFe60aa.TMP | — | |
MD5:— | SHA256:— | |||
| 6788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFe607b.TMP | text | |
MD5:8F45965291AB2DA10EEB049FB6E917C6 | SHA256:8A0DE526945B27CDBBD87357C85FDDD37B572370F894CB0A5AC533FD465D2166 | |||
| 6788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RFe6175.TMP | text | |
MD5:390E3C6EDCE7036BB6F52670DC24ABAD | SHA256:D6F1B47CD05A8E1FAD989DEEC22ED67EA9A013C2DE0CCAFD68A539F69BD0DD70 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
68
TCP/UDP connections
113
DNS requests
58
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5924 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6504 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6496 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
4552 | explorer.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
4552 | explorer.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
6252 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/dvn6tjyuqqxdoyobslkdwn7pvi_2024.4.15.1148/ggkkehgbnfjpeggfpleeakpidbkibbmn_2024.4.15.1148_all_ad7h2np2zton5orbcmedhdzcqjqa.crx3 | unknown | — | — | whitelisted |
4552 | explorer.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEA%2BxsQGVent7YEITi9TM8qM%3D | unknown | — | — | whitelisted |
6252 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/dvn6tjyuqqxdoyobslkdwn7pvi_2024.4.15.1148/ggkkehgbnfjpeggfpleeakpidbkibbmn_2024.4.15.1148_all_ad7h2np2zton5orbcmedhdzcqjqa.crx3 | unknown | — | — | whitelisted |
6252 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/dvn6tjyuqqxdoyobslkdwn7pvi_2024.4.15.1148/ggkkehgbnfjpeggfpleeakpidbkibbmn_2024.4.15.1148_all_ad7h2np2zton5orbcmedhdzcqjqa.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1420 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1792 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5336 | SearchApp.exe | 104.126.37.155:443 | www.bing.com | Akamai International B.V. | DE | unknown |
5924 | svchost.exe | 40.126.32.140:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
5924 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
5336 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
— | — | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
d1ufc1vsb1y7l8.cloudfront.net |
| whitelisted |
accounts.google.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
rsEngineSvc.exe | Native library pre-loader is trying to load native SQLite library "C:\Program Files\ReasonLabs\EPP\x64\SQLite.Interop.dll"...
|
rsEDRSvc.exe | Native library pre-loader is trying to load native SQLite library "C:\Program Files\ReasonLabs\EDR\x64\SQLite.Interop.dll"...
|