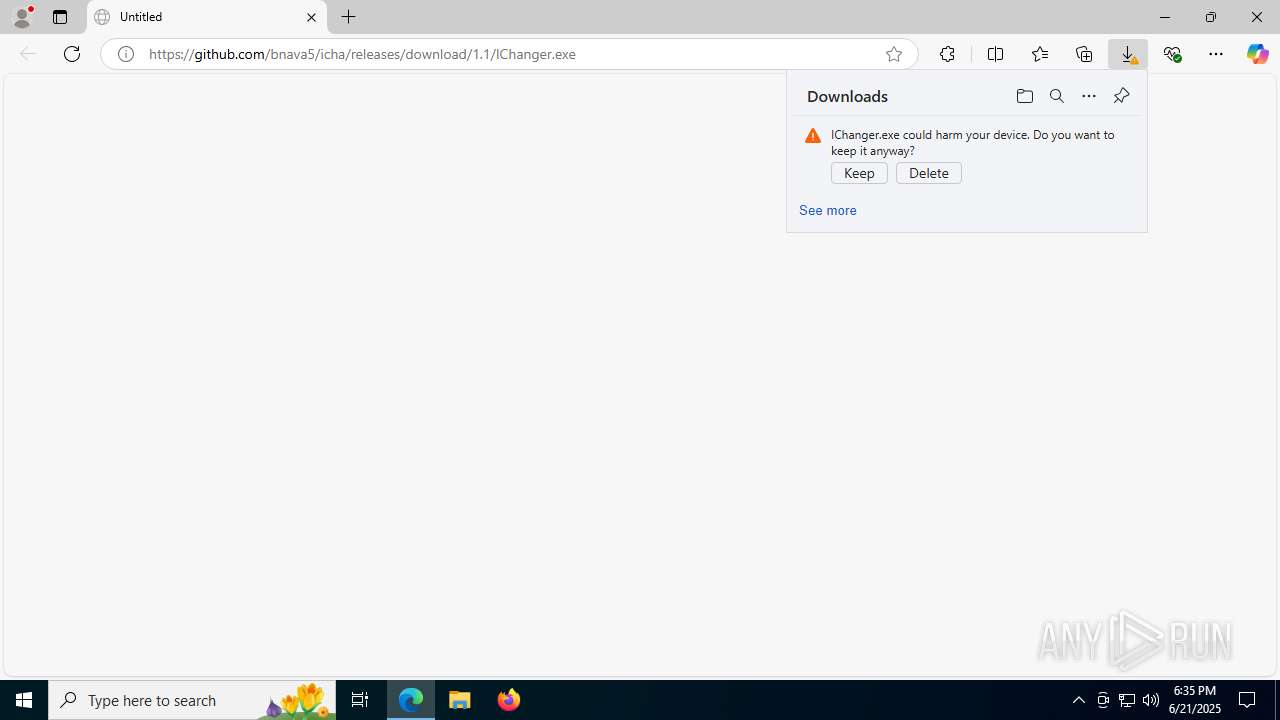
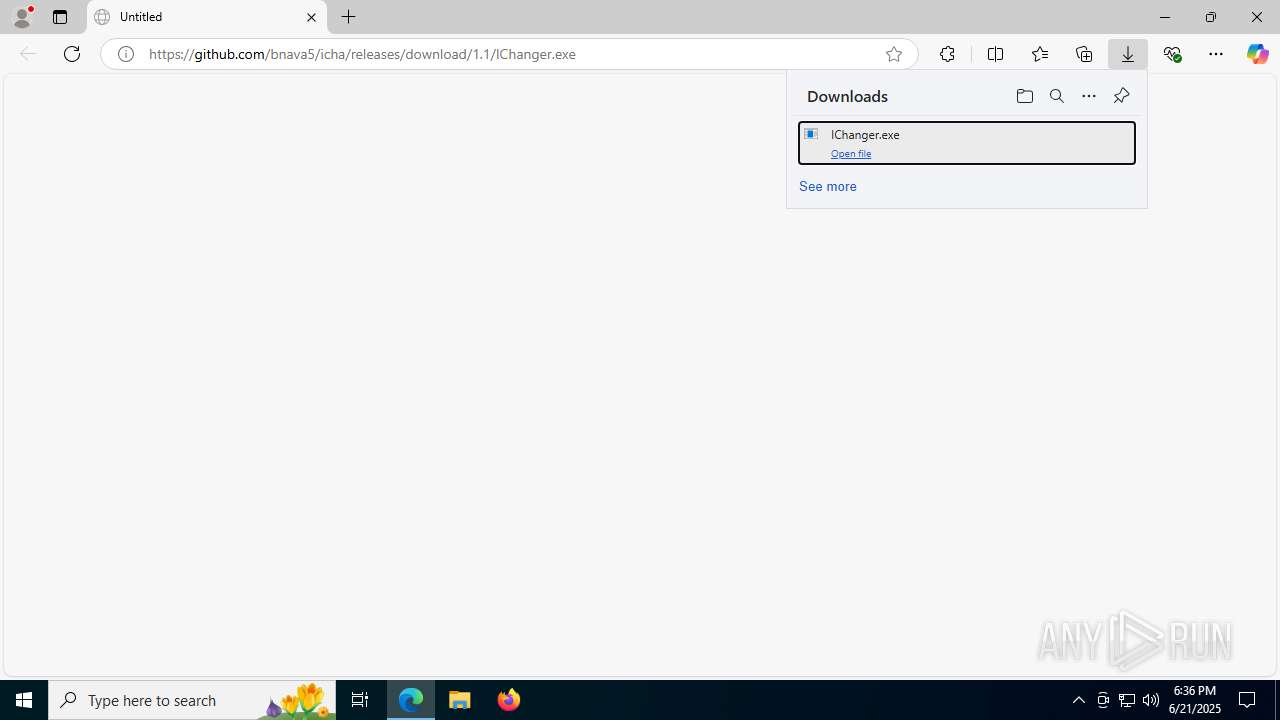
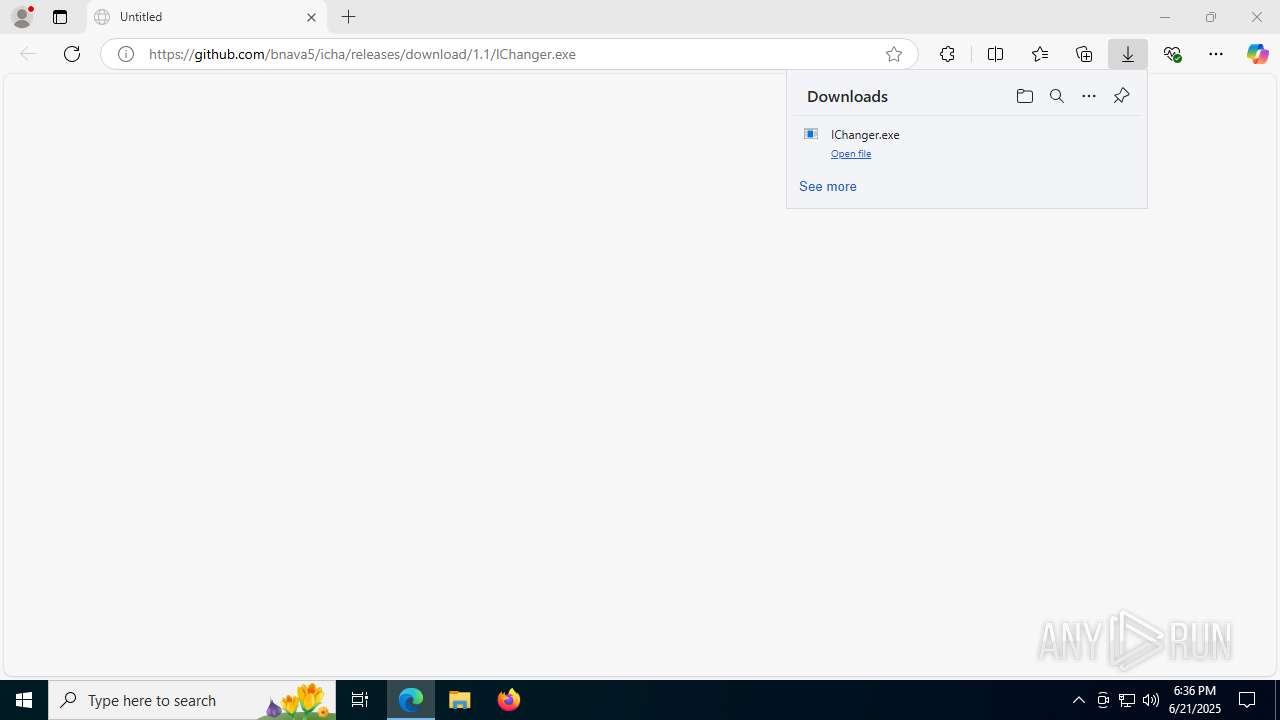
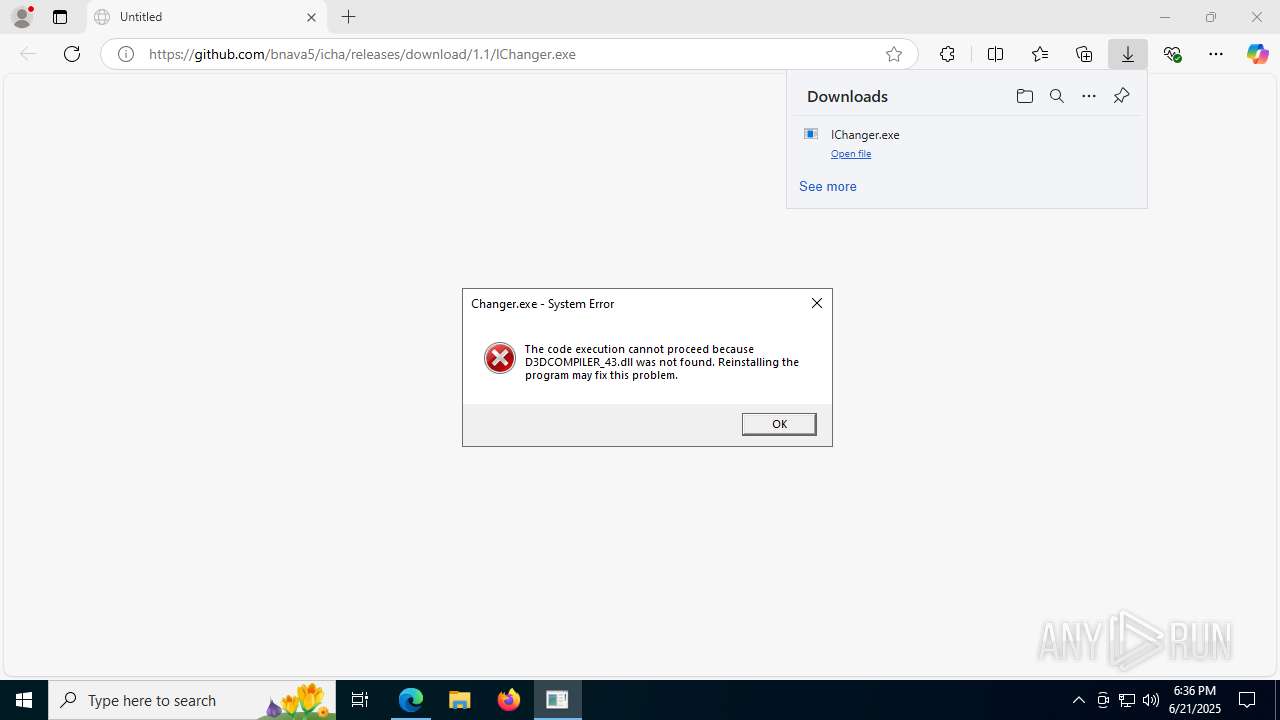
| URL: | https://github.com/bnava5/icha/releases/download/1.1/IChanger.exe |
| Full analysis: | https://app.any.run/tasks/8308ff43-9df1-457c-a8a0-0b0a269354b8 |
| Verdict: | Malicious activity |
| Threats: | A botnet is a group of internet-connected devices that are controlled by a single individual or group, often without the knowledge or consent of the device owners. These devices can be used to launch a variety of malicious attacks, such as distributed denial-of-service (DDoS) attacks, spam campaigns, and data theft. Botnet malware is the software that is used to infect devices and turn them into part of a botnet. |
| Analysis date: | June 21, 2025, 18:35:23 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | A86B37A8D664506E2C9B994C4EC1D783 |
| SHA1: | 7C0D0E2C3D5BFE24FD7E492A163B60787D22D85E |
| SHA256: | 2198BD931DA88E04CD685AE4360A1223A34A3BD079BA74AC444A6CD1E9A237A1 |
| SSDEEP: | 3:N8tEd3mEQckCUPbA:2uic6Pk |
MALICIOUS
Executing a file with an untrusted certificate
- IChanger.exe (PID: 8152)
- IChanger.exe (PID: 4692)
Bypass execution policy to execute commands
- powershell.exe (PID: 1740)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 4040)
Adds process to the Windows Defender exclusion list
- WinTemp64.exe (PID: 7328)
Changes Windows Defender settings
- WinTemp64.exe (PID: 7328)
Downloads files via BITSADMIN.EXE
- cmd.exe (PID: 4040)
Changes the autorun value in the registry
- WinTemp64.exe (PID: 7328)
Starts REAGENTC.EXE to disable the Windows Recovery Environment
- ReAgentc.exe (PID: 7096)
BOTNET has been found (auto)
- svchost.exe (PID: 7200)
MINER has been detected (SURICATA)
- cmd.exe (PID: 5900)
- cmd.exe (PID: 6532)
- cmd.exe (PID: 7752)
Connects to the CnC server
- cmd.exe (PID: 5900)
- cmd.exe (PID: 7752)
- cmd.exe (PID: 6532)
SUSPICIOUS
Reads security settings of Internet Explorer
- IChanger.exe (PID: 8152)
- WinTemp64.exe (PID: 7328)
Executable content was dropped or overwritten
- IChanger.exe (PID: 8152)
- WinTemp64.exe (PID: 7328)
- svchost.exe (PID: 7200)
Executing commands from a ".bat" file
- wscript.exe (PID: 1352)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 1352)
- WinTemp64.exe (PID: 7328)
- svchost.exe (PID: 7200)
Reads the date of Windows installation
- IChanger.exe (PID: 8152)
The process executes VB scripts
- IChanger.exe (PID: 8152)
The process executes Powershell scripts
- cmd.exe (PID: 4040)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 4040)
- WinTemp64.exe (PID: 7328)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 4040)
The executable file from the user directory is run by the CMD process
- WinTemp64.exe (PID: 7328)
Script adds exclusion process to Windows Defender
- WinTemp64.exe (PID: 7328)
Runs shell command (SCRIPT)
- wscript.exe (PID: 1352)
Script adds exclusion path to Windows Defender
- WinTemp64.exe (PID: 7328)
Takes ownership (TAKEOWN.EXE)
- cmd.exe (PID: 4984)
Uses ICACLS.EXE to modify access control lists
- cmd.exe (PID: 7580)
- cmd.exe (PID: 7788)
Uses powercfg.exe to modify the power settings
- cmd.exe (PID: 7908)
- cmd.exe (PID: 4020)
- cmd.exe (PID: 7676)
- cmd.exe (PID: 6836)
- cmd.exe (PID: 6956)
- cmd.exe (PID: 7724)
- cmd.exe (PID: 7740)
There is functionality for taking screenshot (YARA)
- IChanger.exe (PID: 8152)
Hides command output
- cmd.exe (PID: 5720)
Checks for external IP
- svchost.exe (PID: 7200)
Potential Corporate Privacy Violation
- cmd.exe (PID: 5900)
- cmd.exe (PID: 7752)
- cmd.exe (PID: 6532)
Connects to unusual port
- cmd.exe (PID: 5900)
- cmd.exe (PID: 7752)
- cmd.exe (PID: 6532)
INFO
Executable content was dropped or overwritten
- msedge.exe (PID: 3888)
Application launched itself
- msedge.exe (PID: 3888)
Reads Environment values
- identity_helper.exe (PID: 7540)
Checks supported languages
- identity_helper.exe (PID: 7540)
- IChanger.exe (PID: 8152)
- WinTemp64.exe (PID: 7328)
Reads the computer name
- identity_helper.exe (PID: 7540)
- IChanger.exe (PID: 8152)
- WinTemp64.exe (PID: 7328)
Create files in a temporary directory
- IChanger.exe (PID: 8152)
- WinTemp64.exe (PID: 7328)
- svchost.exe (PID: 7200)
Process checks computer location settings
- IChanger.exe (PID: 8152)
Reads Microsoft Office registry keys
- IChanger.exe (PID: 8152)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 1740)
- powershell.exe (PID: 7336)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 1740)
- powershell.exe (PID: 7336)
Creates files or folders in the user directory
- WinTemp64.exe (PID: 7328)
Uses Task Scheduler to autorun other applications (AUTOMATE)
- WinTemp64.exe (PID: 7328)
Launching a file from a Registry key
- WinTemp64.exe (PID: 7328)
Checks proxy server information
- WinTemp64.exe (PID: 7328)
- svchost.exe (PID: 7200)
- slui.exe (PID: 6472)
Reads the machine GUID from the registry
- WinTemp64.exe (PID: 7328)
Reads the software policy settings
- WinTemp64.exe (PID: 7328)
- slui.exe (PID: 6472)
Reads security settings of Internet Explorer
- svchost.exe (PID: 7200)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
220
Monitored processes
80
Malicious processes
8
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 316 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1136 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2796,i,14539826291553989644,9451433560568055433,262144 --variations-seed-version --mojo-platform-channel-handle=2808 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1352 | "C:\WINDOWS\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\RarSFX0\run.vbs" | C:\Windows\System32\wscript.exe | — | IChanger.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 1388 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1740 | powershell.exe -ExecutionPolicy Bypass -File "C:\Users\admin\AppData\Local\Temp\WinTempPs.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1752 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6324,i,14539826291553989644,9451433560568055433,262144 --variations-seed-version --mojo-platform-channel-handle=6176 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1896 | powercfg /change standby-timeout-ac 0 | C:\Windows\System32\powercfg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Power Settings Command-Line Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2064 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2188 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | schtasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2212 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --always-read-main-dll --field-trial-handle=4308,i,14539826291553989644,9451433560568055433,262144 --variations-seed-version --mojo-platform-channel-handle=4316 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
22 641
Read events
22 548
Write events
33
Delete events
60
Modification events
| (PID) Process: | (3888) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3888) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3888) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3888) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3888) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3888) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3888) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 82AFD886AF962F00 | |||
| (PID) Process: | (3888) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328486 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {51FD9525-64C4-4193-B533-DEC133896851} | |||
| (PID) Process: | (3888) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 9DD6EF86AF962F00 | |||
| (PID) Process: | (3888) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
Executable files
16
Suspicious files
102
Text files
46
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3888 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF1765fd.TMP | — | |
MD5:— | SHA256:— | |||
| 3888 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3888 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF17660d.TMP | — | |
MD5:— | SHA256:— | |||
| 3888 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3888 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF17660d.TMP | — | |
MD5:— | SHA256:— | |||
| 3888 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3888 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF17661c.TMP | — | |
MD5:— | SHA256:— | |||
| 3888 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3888 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF17660d.TMP | — | |
MD5:— | SHA256:— | |||
| 3888 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
69
DNS requests
60
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7864 | svchost.exe | HEAD | 200 | 208.89.74.19:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4c4fdee0-d69c-42b7-bf5c-3ec046e9dfc9?P1=1750712030&P2=404&P3=2&P4=TggO2QcBdCIu118rllcF3FOA2PIzlI4wmgnnz4jlzv6dU596AxO8H%2bUxcxf6PdZA4ugmqD25Gm1hM7hV52fbyg%3d%3d | unknown | — | — | whitelisted |
7864 | svchost.exe | GET | 206 | 208.89.74.19:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4c4fdee0-d69c-42b7-bf5c-3ec046e9dfc9?P1=1750712030&P2=404&P3=2&P4=TggO2QcBdCIu118rllcF3FOA2PIzlI4wmgnnz4jlzv6dU596AxO8H%2bUxcxf6PdZA4ugmqD25Gm1hM7hV52fbyg%3d%3d | unknown | — | — | whitelisted |
4084 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:Zw5n7JghP0Ax4PNY-gJ1tQJ2_sgfWQP3kERwMvLRCb8&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
8144 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8144 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2524 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7200 | svchost.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.usertrust.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBSr83eyJy3njhjVpn5bEpfc6MXawQQUOuEJhtTPGcKWdnRJdtzgNcZjY5oCEQDzZE5rbgBQI34JRr174fUd | unknown | — | — | whitelisted |
7328 | WinTemp64.exe | GET | 200 | 142.250.185.131:80 | http://c.pki.goog/r/r4.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
888 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4084 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4084 | msedge.exe | 140.82.121.3:443 | github.com | GITHUB | US | whitelisted |
4084 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4084 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4084 | msedge.exe | 142.250.185.131:443 | update.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
github.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
objects.githubusercontent.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
www.bing.com |
| whitelisted |
edgeassetservice.azureedge.net |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7200 | svchost.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External IP Lookup by HTTP (api .ipify .org) |
7200 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup api.ipify.org |
2200 | svchost.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
5900 | cmd.exe | Potential Corporate Privacy Violation | ET INFO Cryptocurrency Miner Checkin |
5900 | cmd.exe | Potential Corporate Privacy Violation | ET INFO Cryptocurrency Miner Checkin |
7752 | cmd.exe | Potential Corporate Privacy Violation | ET INFO Cryptocurrency Miner Checkin |
7752 | cmd.exe | Potential Corporate Privacy Violation | ET INFO Cryptocurrency Miner Checkin |
6532 | cmd.exe | Potential Corporate Privacy Violation | ET INFO Cryptocurrency Miner Checkin |
7200 | svchost.exe | Device Retrieving External IP Address Detected | SUSPICIOUS [ANY.RUN] An IP address was received from the server as a result of an HTTP request |
6532 | cmd.exe | Potential Corporate Privacy Violation | ET INFO Cryptocurrency Miner Checkin |