| File name: | 2160eb92e3866fecd97877790fbc2b59105588ddcdab5c54acd58033b9b6a8b7 |
| Full analysis: | https://app.any.run/tasks/363be95f-0ac2-406e-abc3-ebc15926710b |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | October 14, 2024, 12:24:35 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
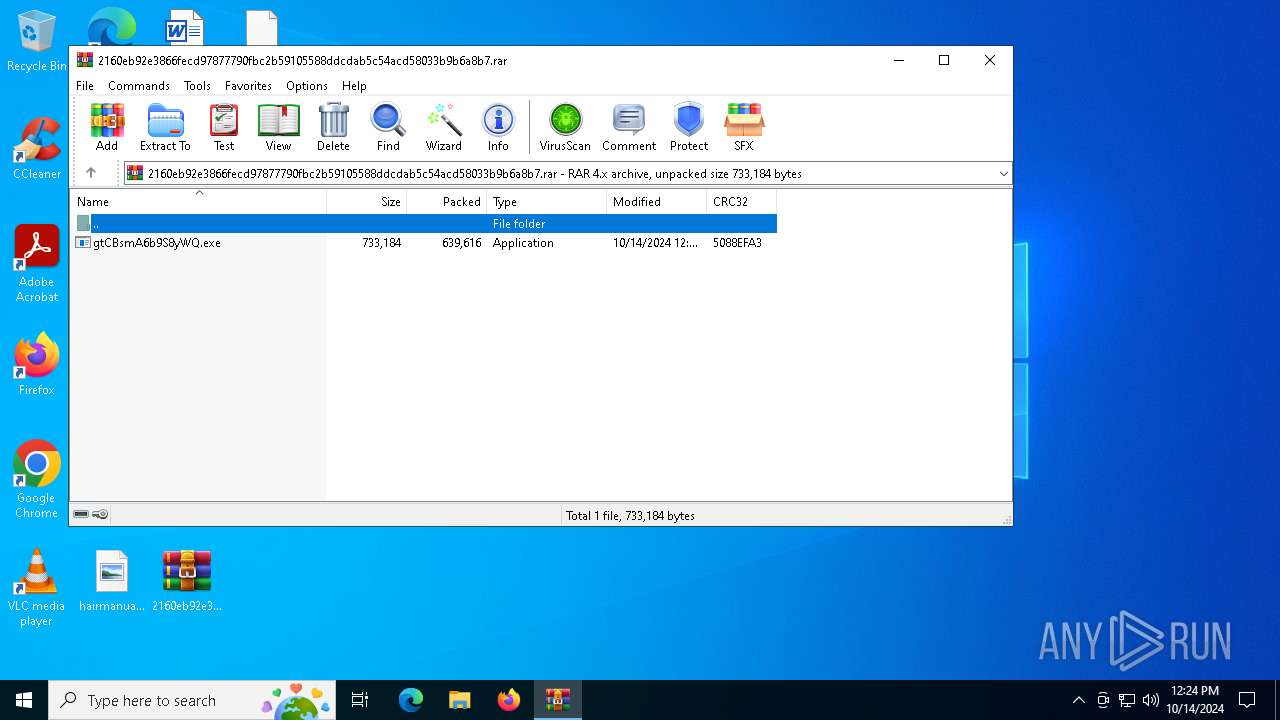
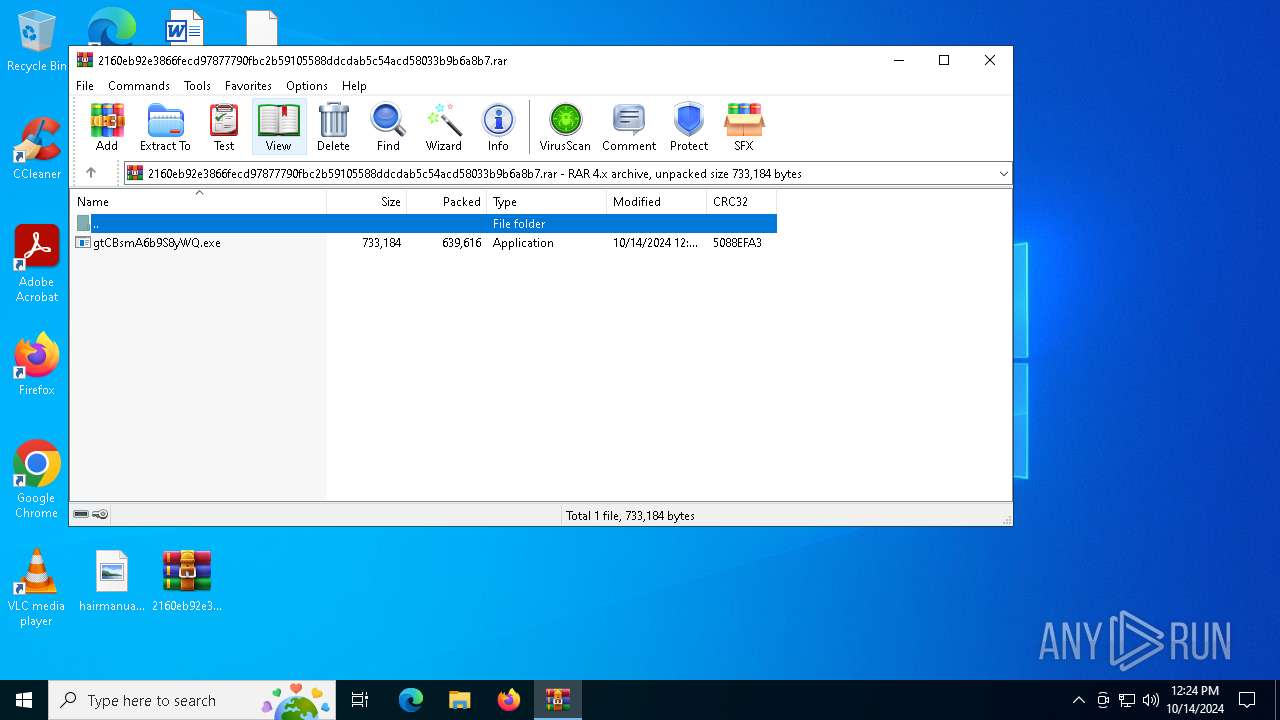
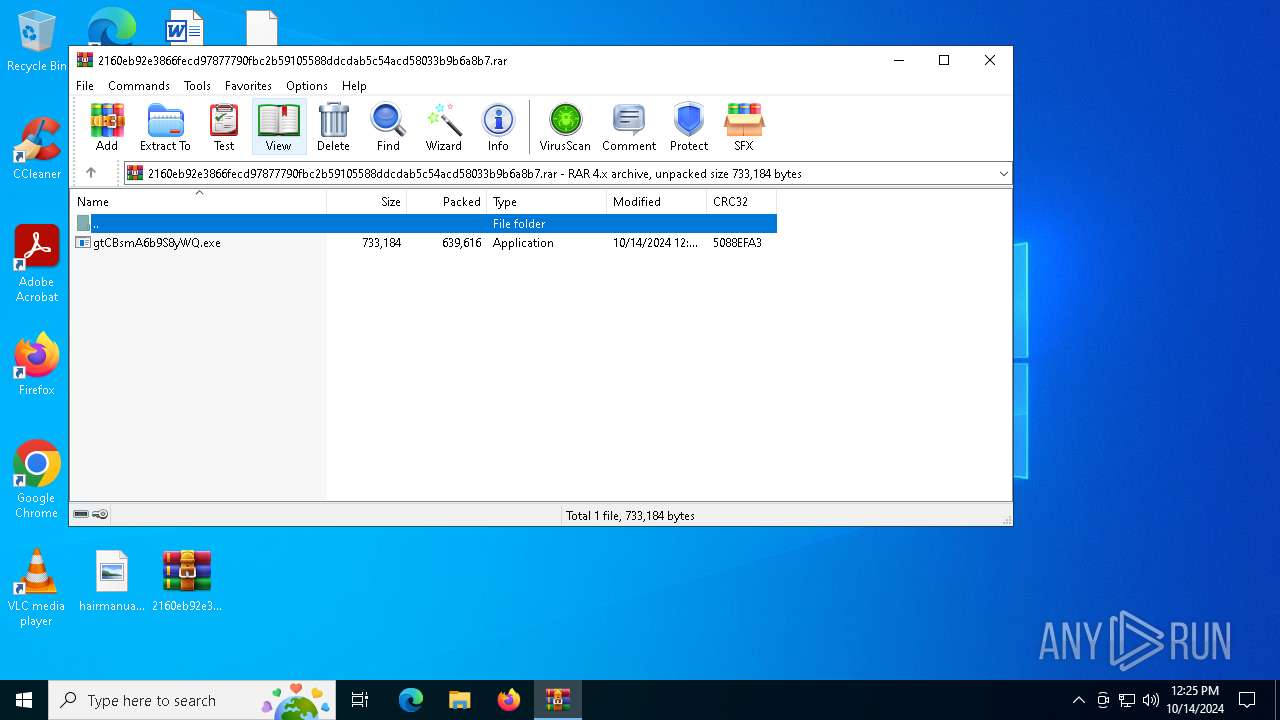
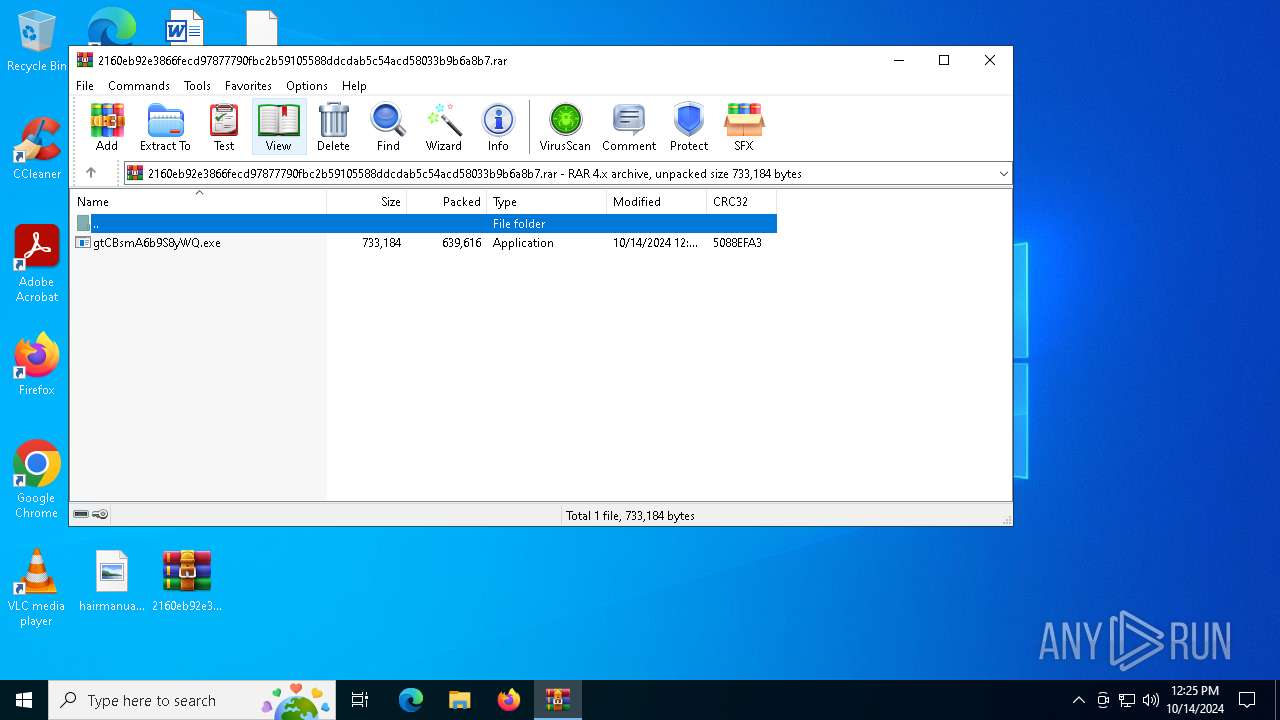
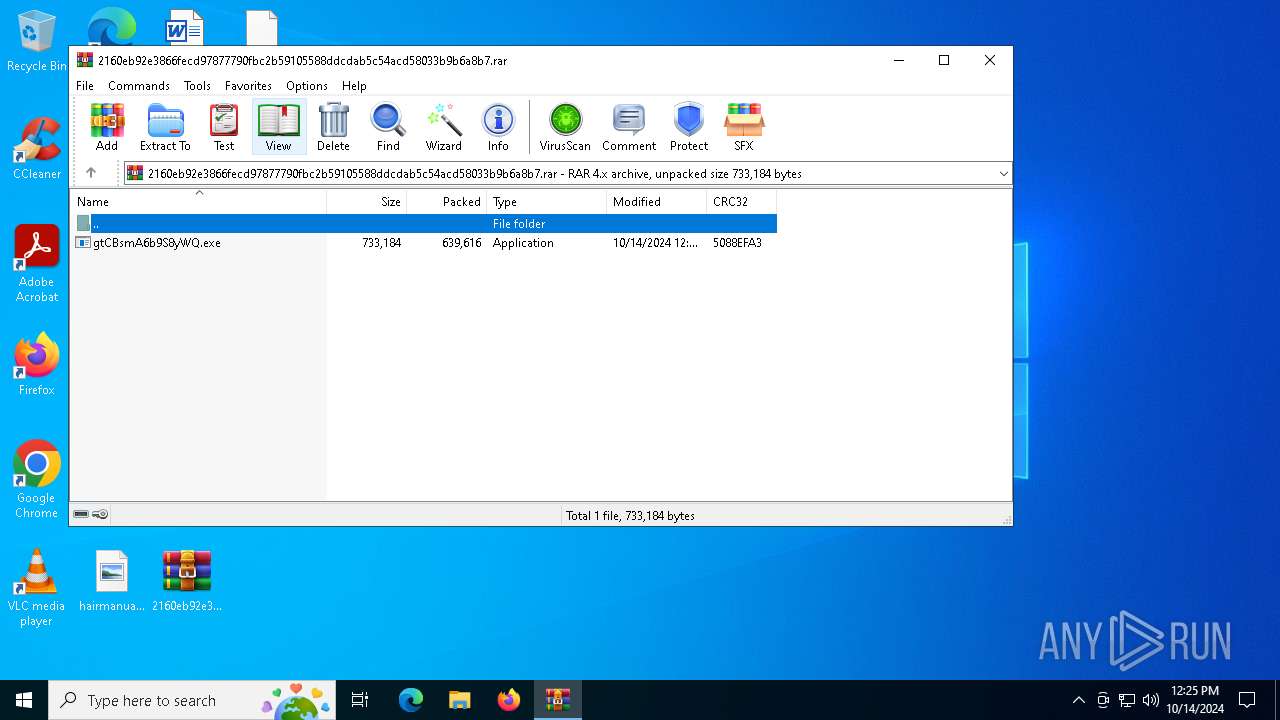
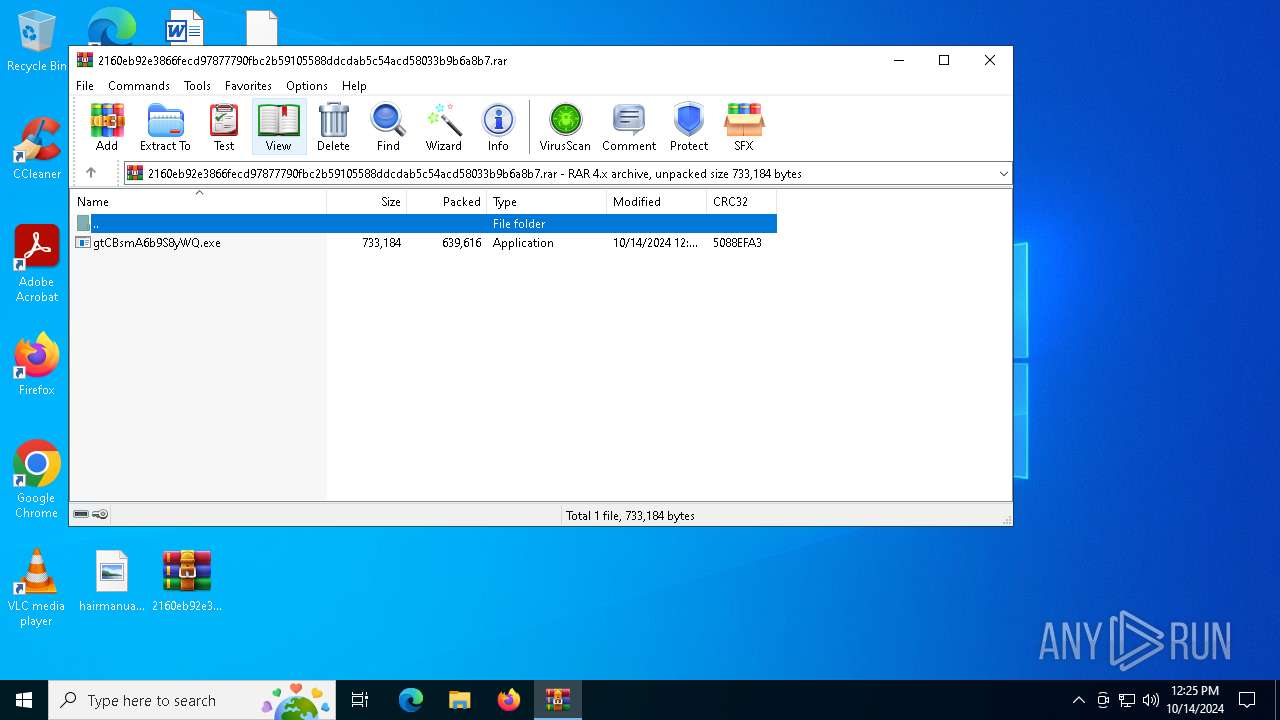
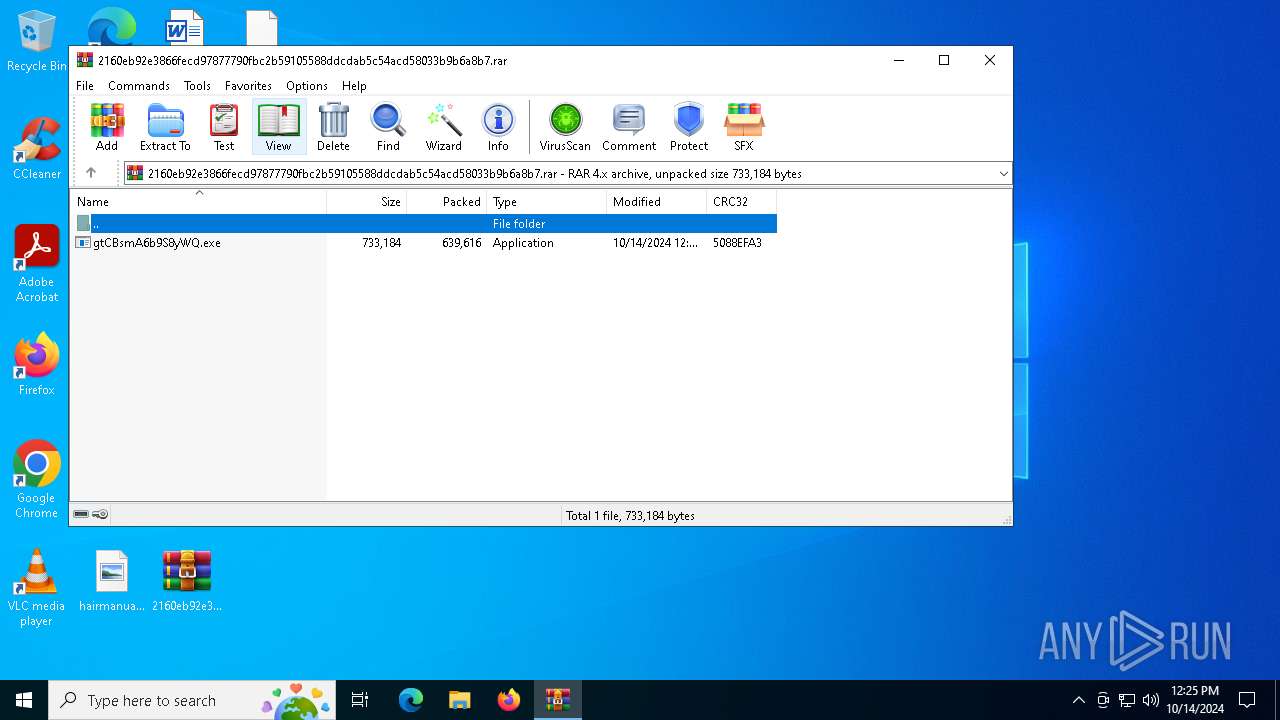
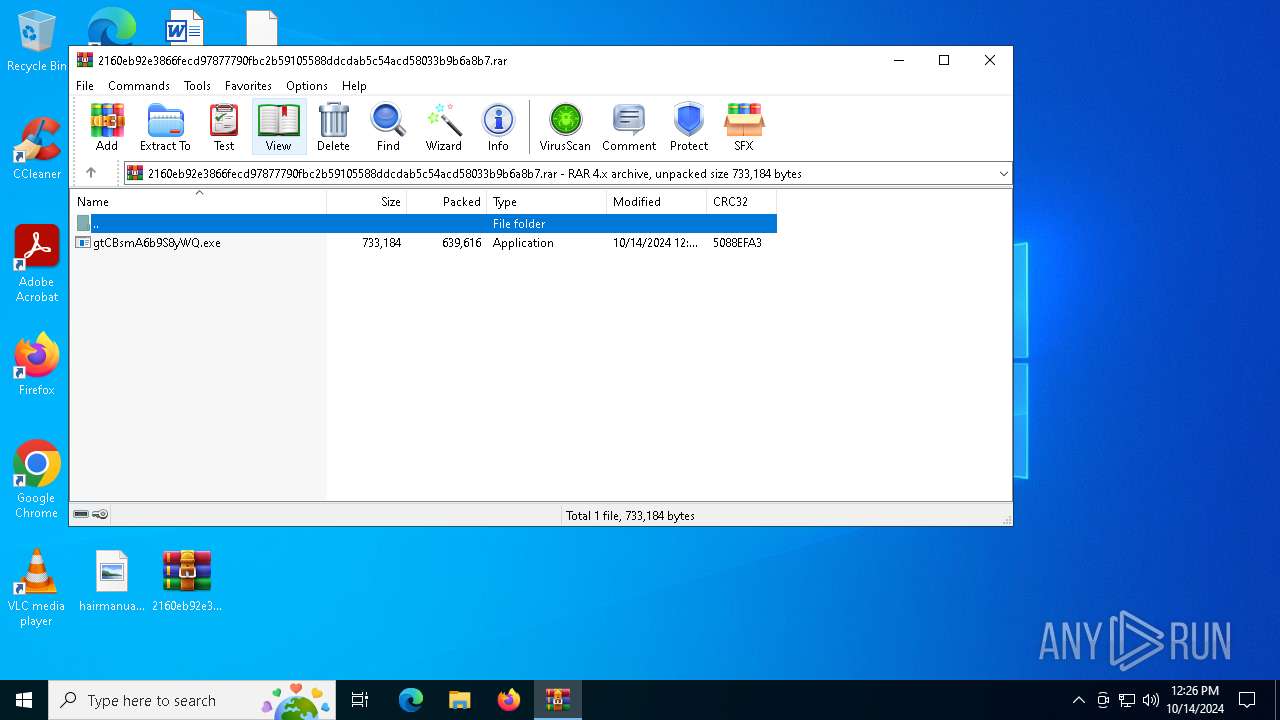
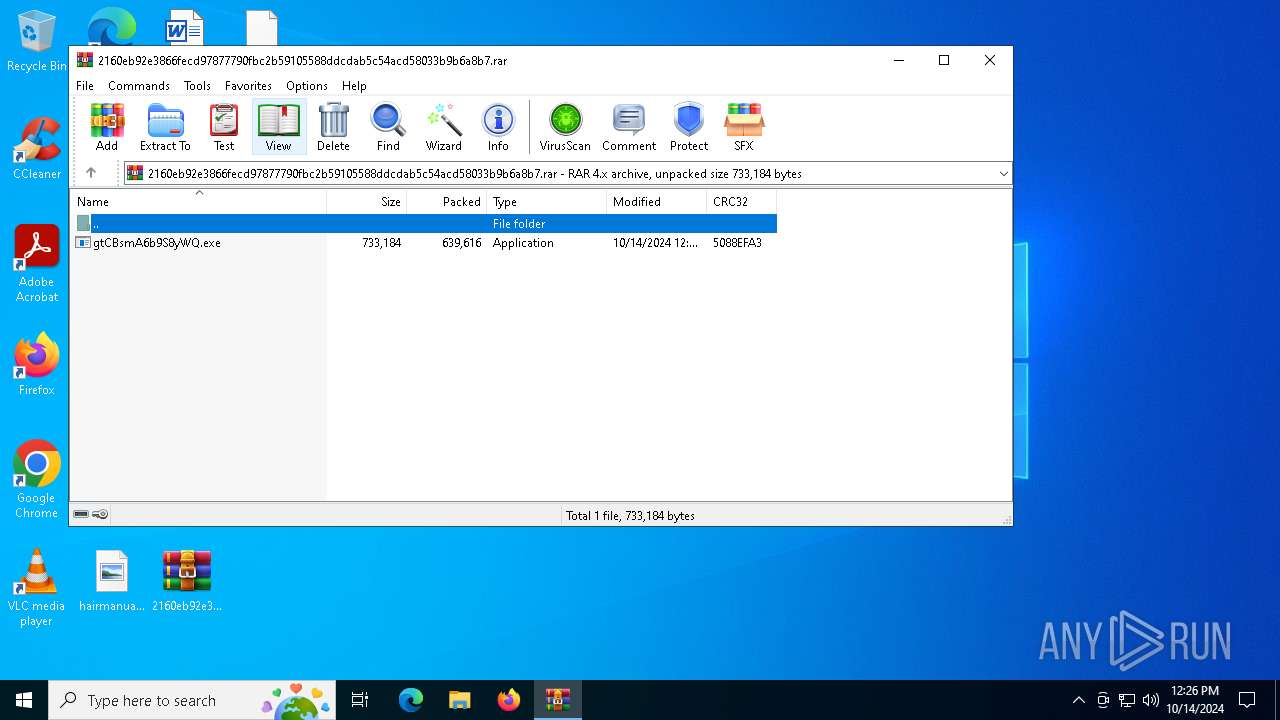
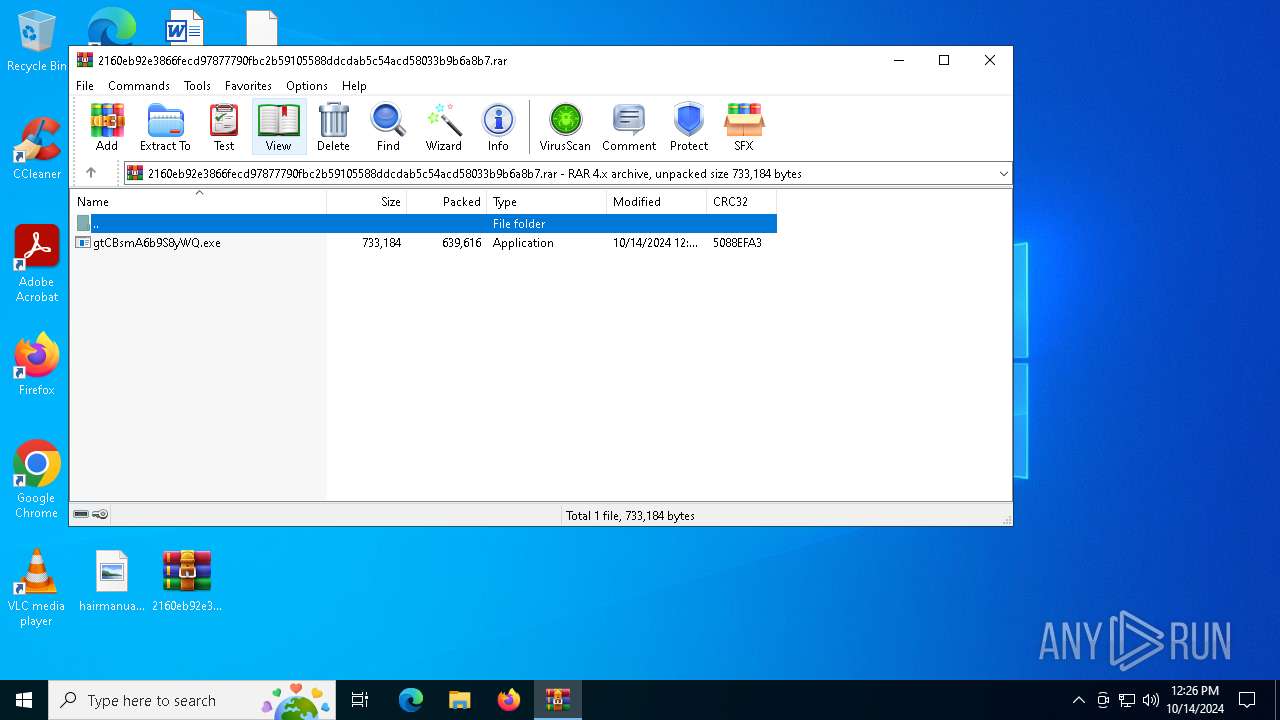
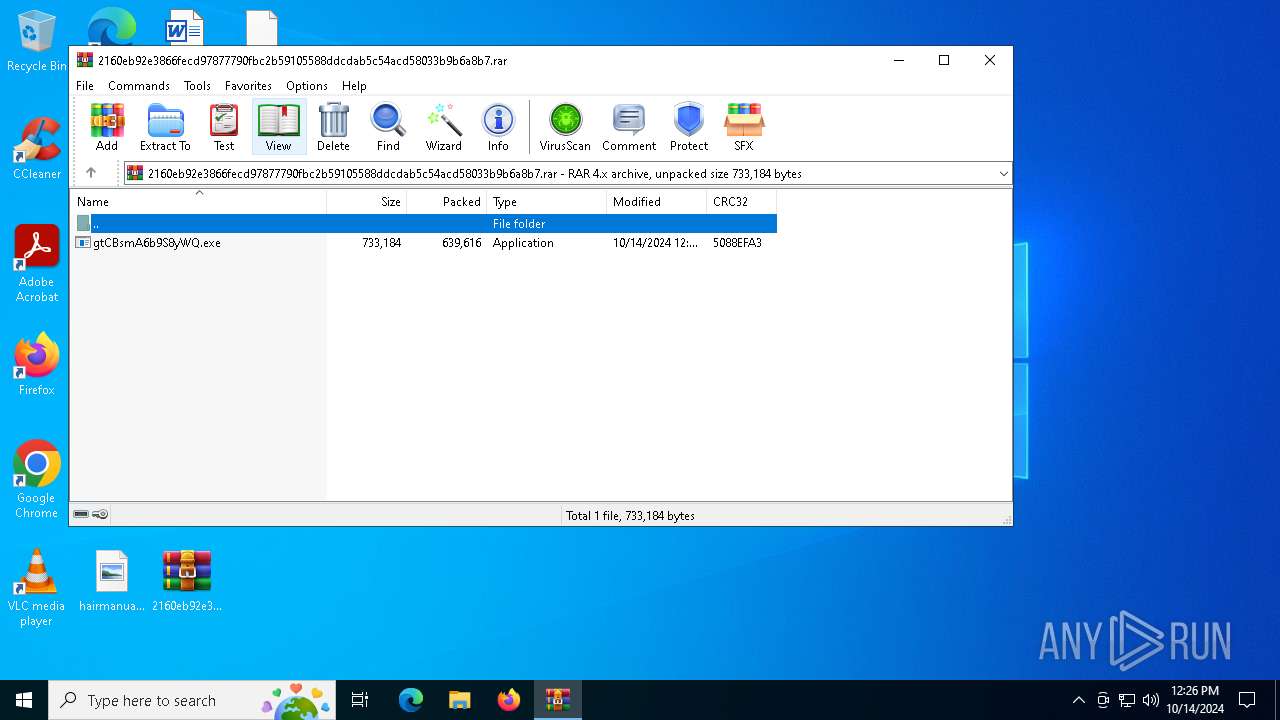
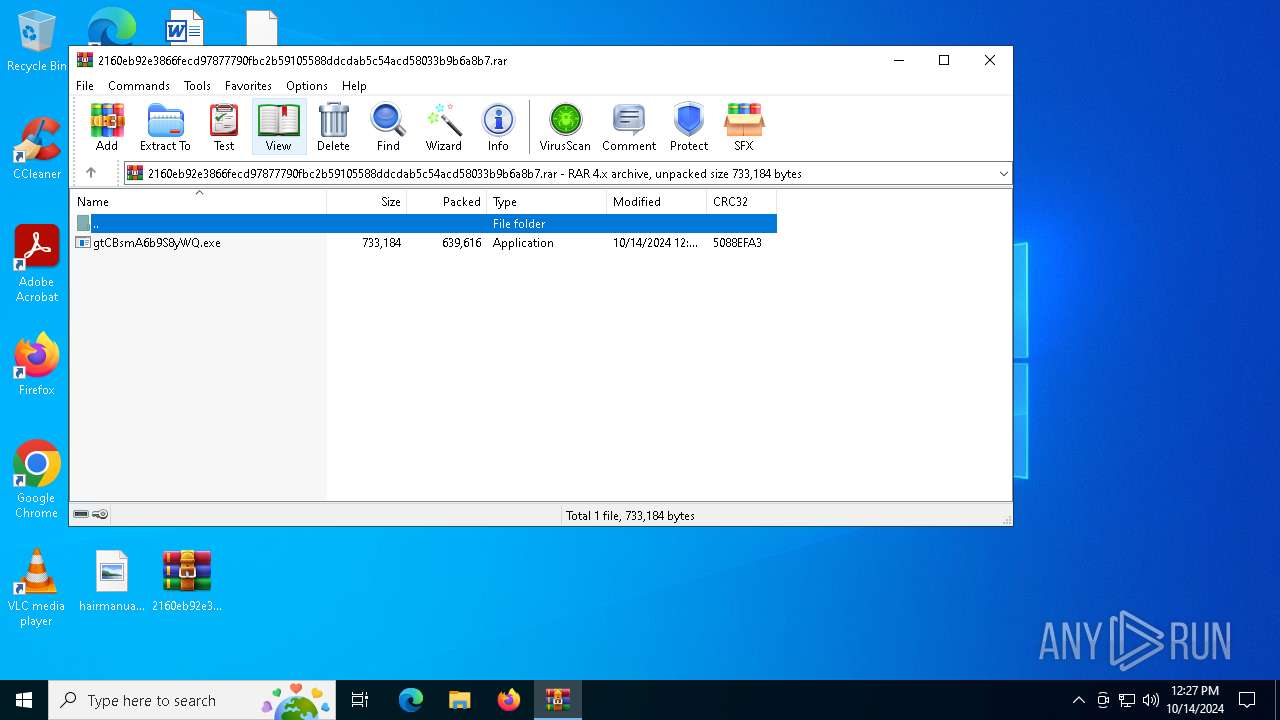
| MIME: | application/x-rar |
| File info: | RAR archive data, v4, os: Win32 |
| MD5: | 9865E0AC101137CE7AA269B9DBB732BB |
| SHA1: | F60A9A5E1E118FB4B3188BE49EC58A97E922C06C |
| SHA256: | 2160EB92E3866FECD97877790FBC2B59105588DDCDAB5C54ACD58033B9B6A8B7 |
| SSDEEP: | 24576:NF3tSPBpHCpAsse2i/iJVcZLZQzyobtxwoHFTrHH7ZAS8B:NF3tSPBpHCpAsszi/iJVcZLZQzyobtxo |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 6432)
Attempt to transmit an email message via SMTP
- gtCBsmA6b9S8yWQ.exe (PID: 7164)
AGENTTESLA has been detected (YARA)
- gtCBsmA6b9S8yWQ.exe (PID: 7164)
Stealers network behavior
- gtCBsmA6b9S8yWQ.exe (PID: 7164)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 6432)
Application launched itself
- gtCBsmA6b9S8yWQ.exe (PID: 764)
Checks for external IP
- svchost.exe (PID: 2172)
- gtCBsmA6b9S8yWQ.exe (PID: 7164)
Connects to SMTP port
- gtCBsmA6b9S8yWQ.exe (PID: 7164)
The process connected to a server suspected of theft
- gtCBsmA6b9S8yWQ.exe (PID: 7164)
INFO
Checks supported languages
- gtCBsmA6b9S8yWQ.exe (PID: 764)
Reads the machine GUID from the registry
- gtCBsmA6b9S8yWQ.exe (PID: 764)
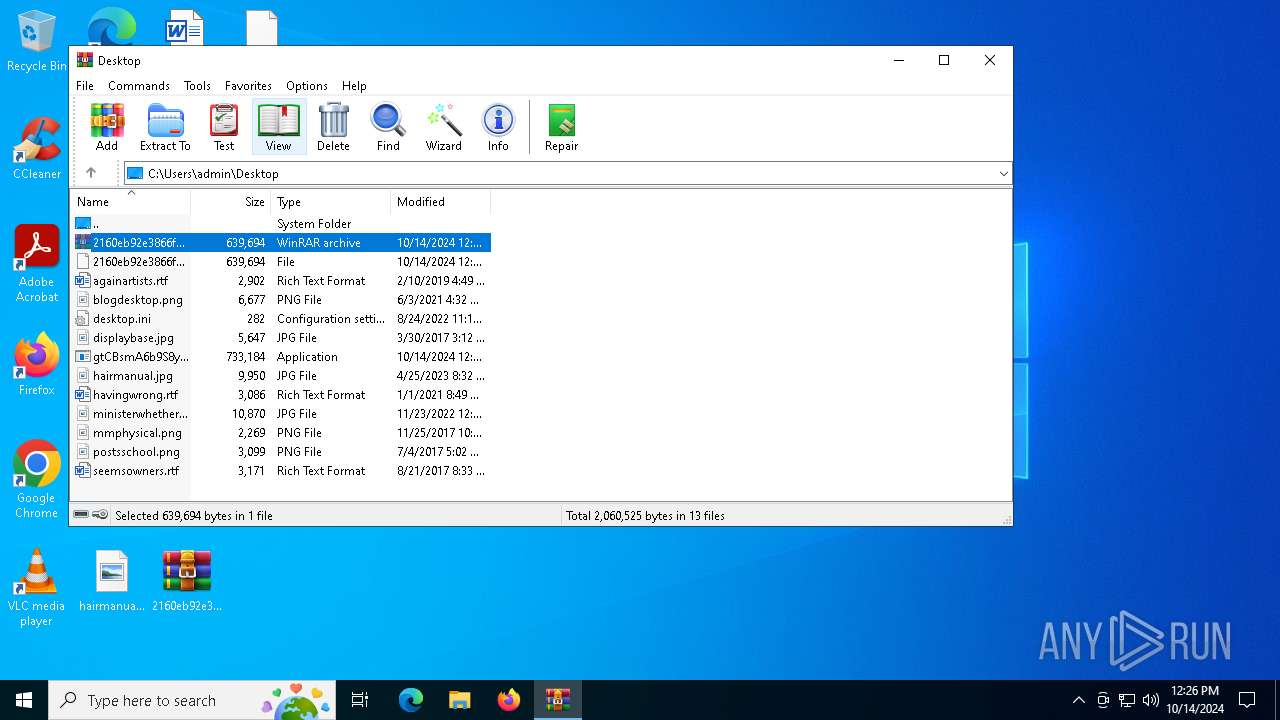
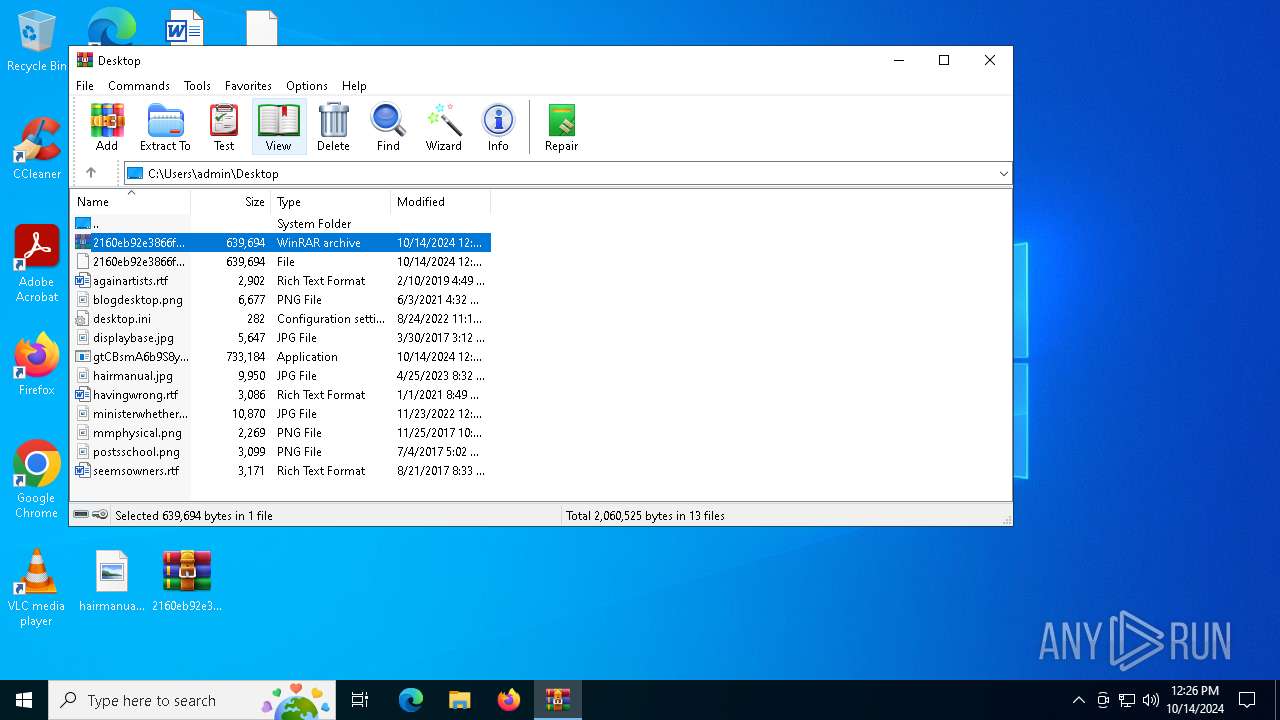
Manual execution by a user
- gtCBsmA6b9S8yWQ.exe (PID: 764)
Reads the computer name
- gtCBsmA6b9S8yWQ.exe (PID: 764)
Attempt to transmit an email message via SMTP
- gtCBsmA6b9S8yWQ.exe (PID: 7164)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AgentTesla
(PID) Process(7164) gtCBsmA6b9S8yWQ.exe
Protocolsmtp
Hostmail.apexrnun.com
Port587
Usernameroocckkbtwo@apexrnun.com
PasswordTsHZsTv}Jnj5E5Bn
TRiD
| .rar | | | RAR compressed archive (v-4.x) (58.3) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (41.6) |
EXIF
ZIP
| CompressedSize: | 639656 |
|---|---|
| UncompressedSize: | 733184 |
| OperatingSystem: | Win32 |
| ModifyDate: | 2024:10:14 00:59:24 |
| PackingMethod: | Normal |
| ArchivedFileName: | gtCBsmA6b9S8yWQ.exe |
Total processes
129
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
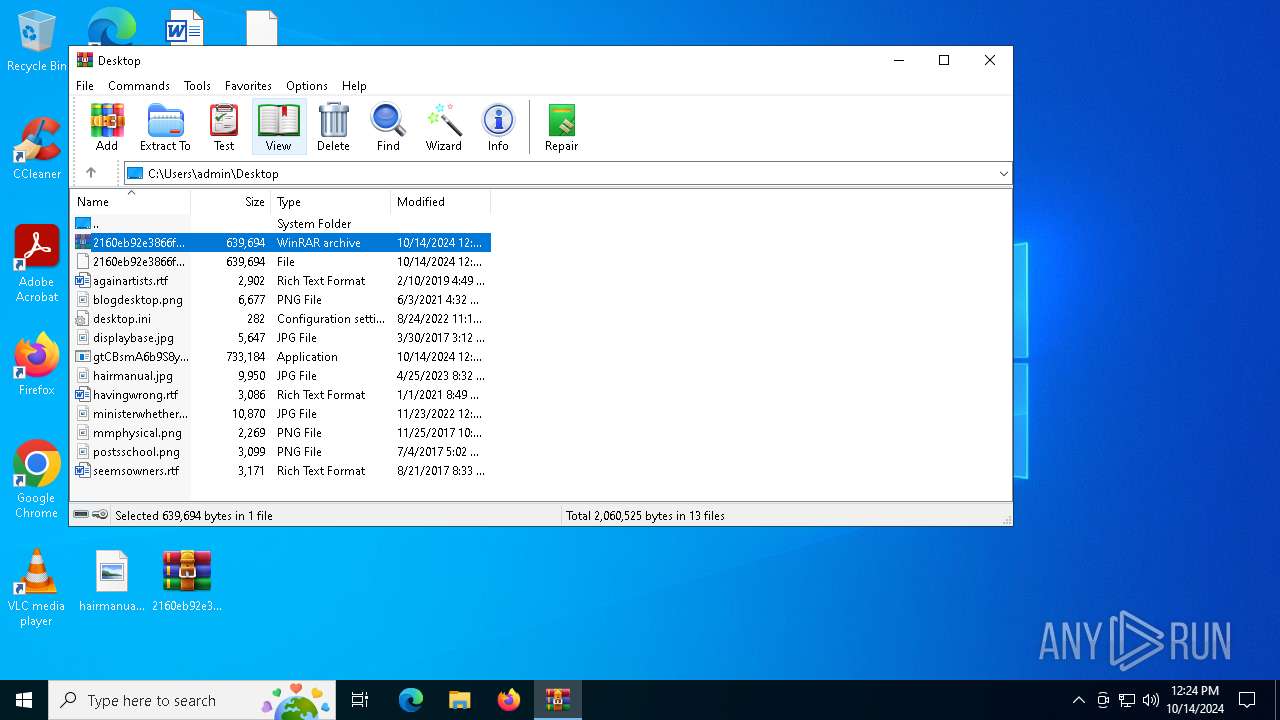
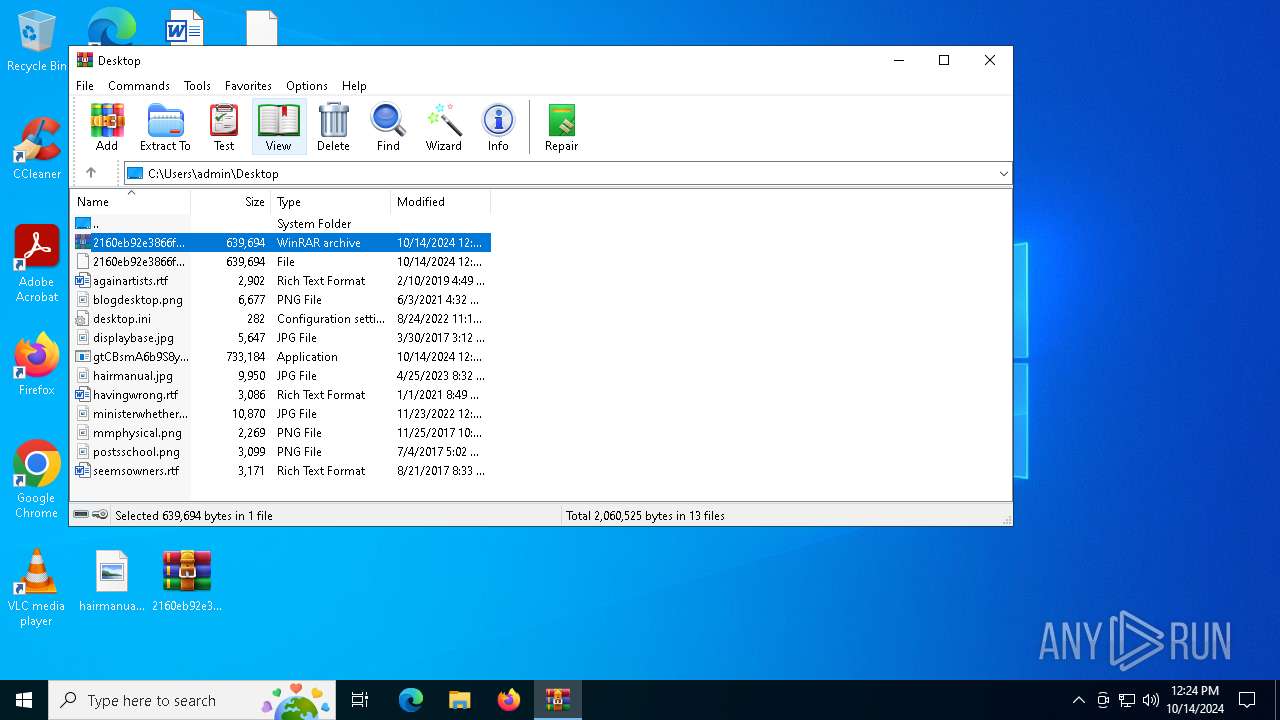
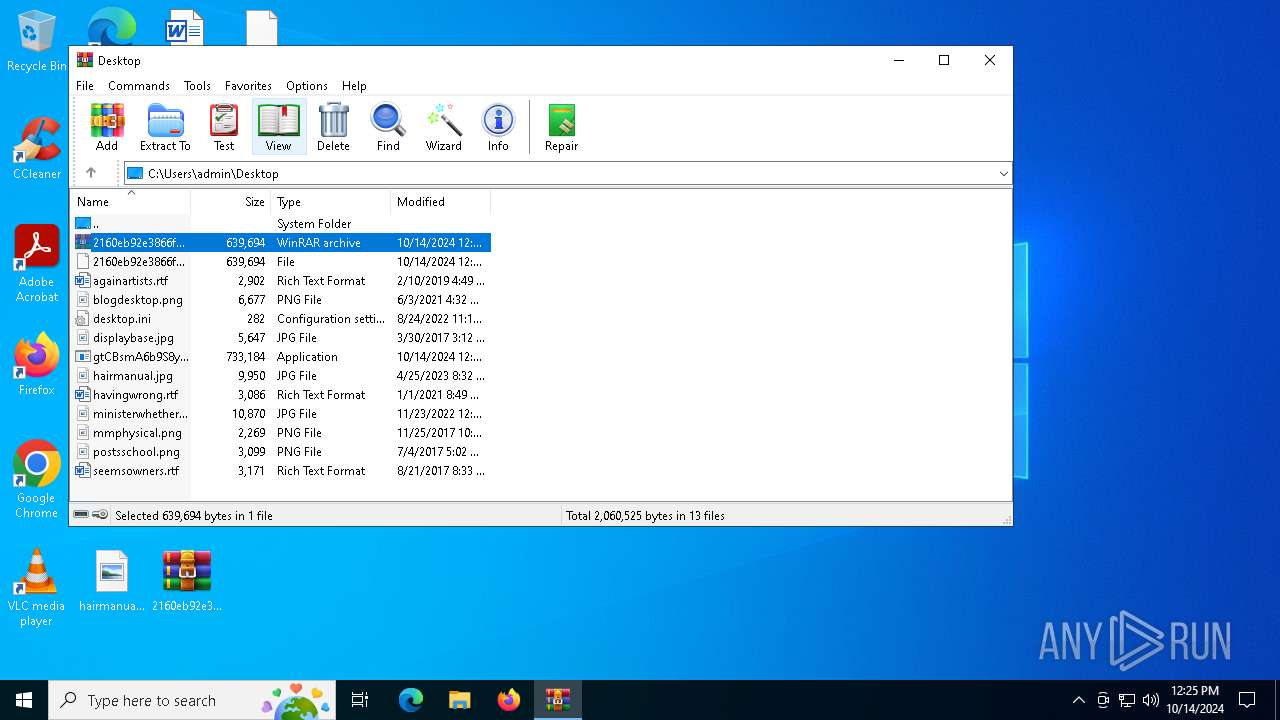
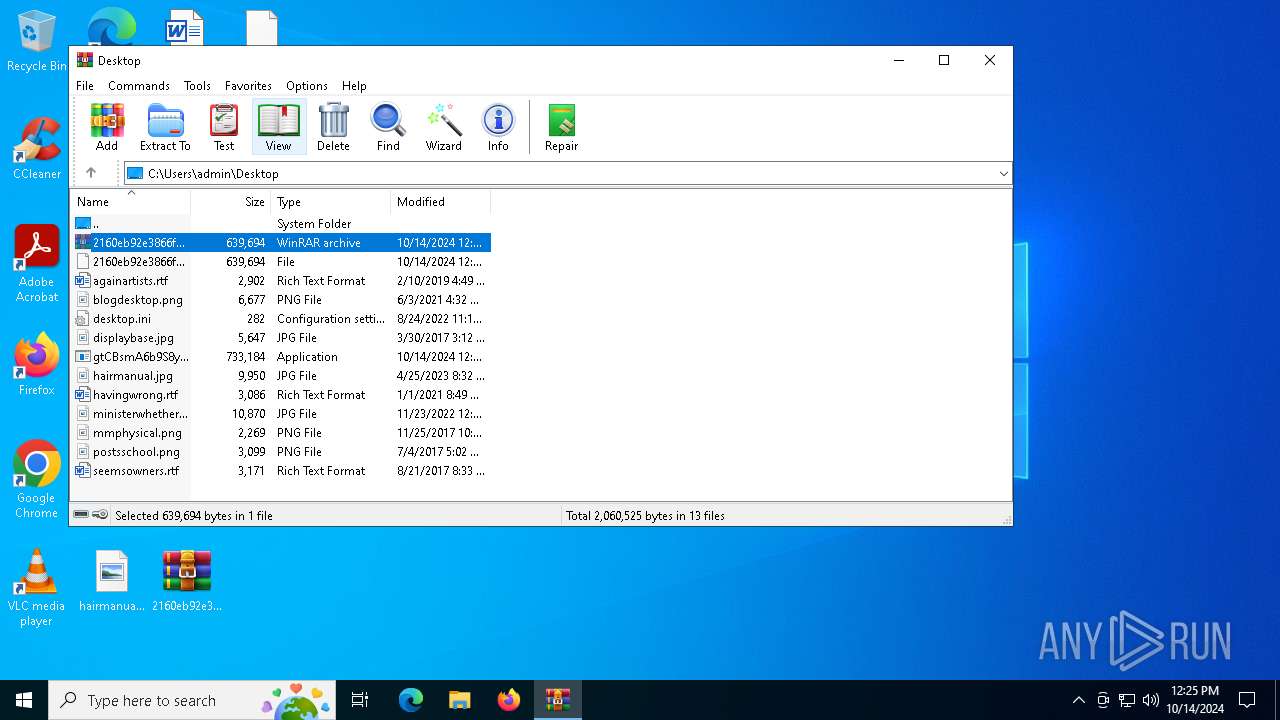
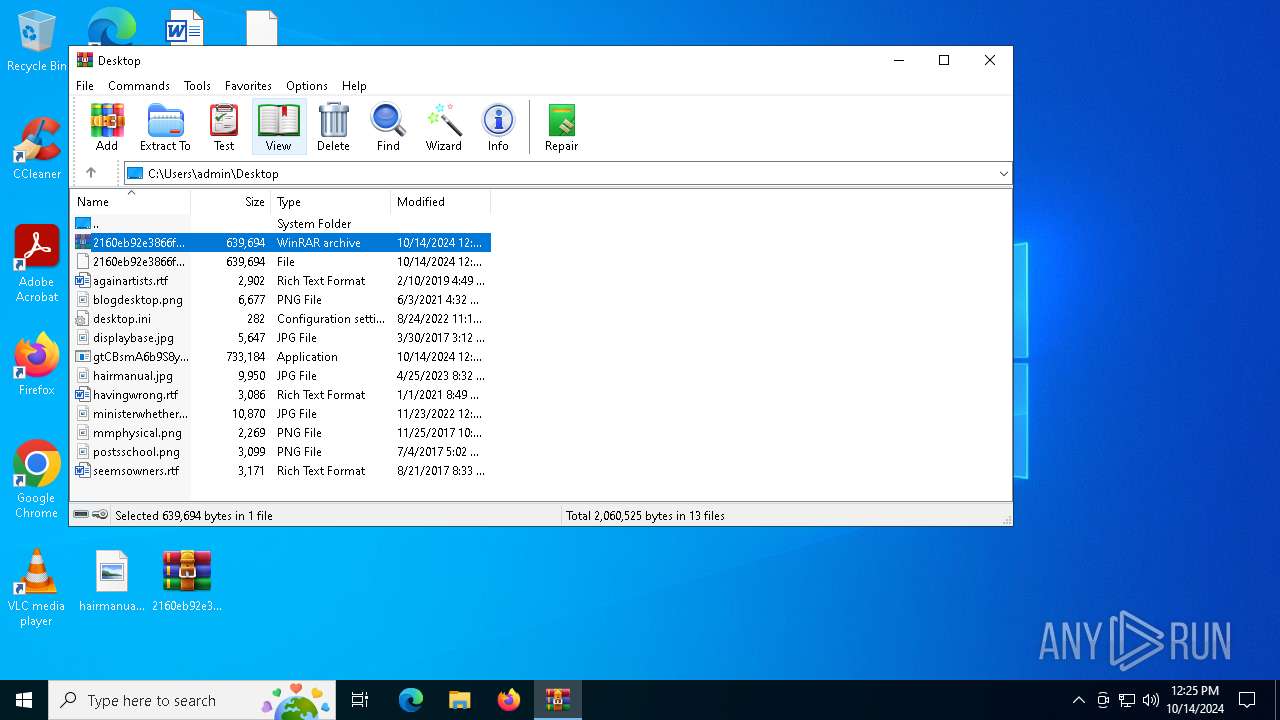
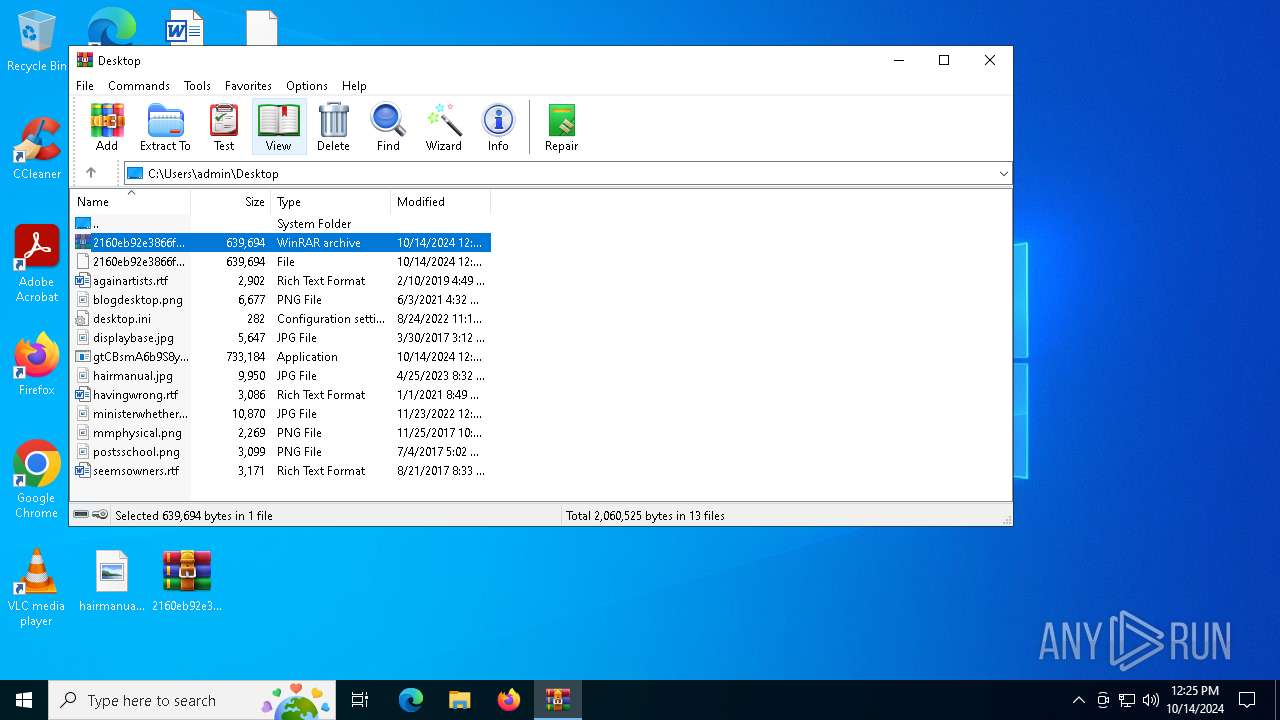
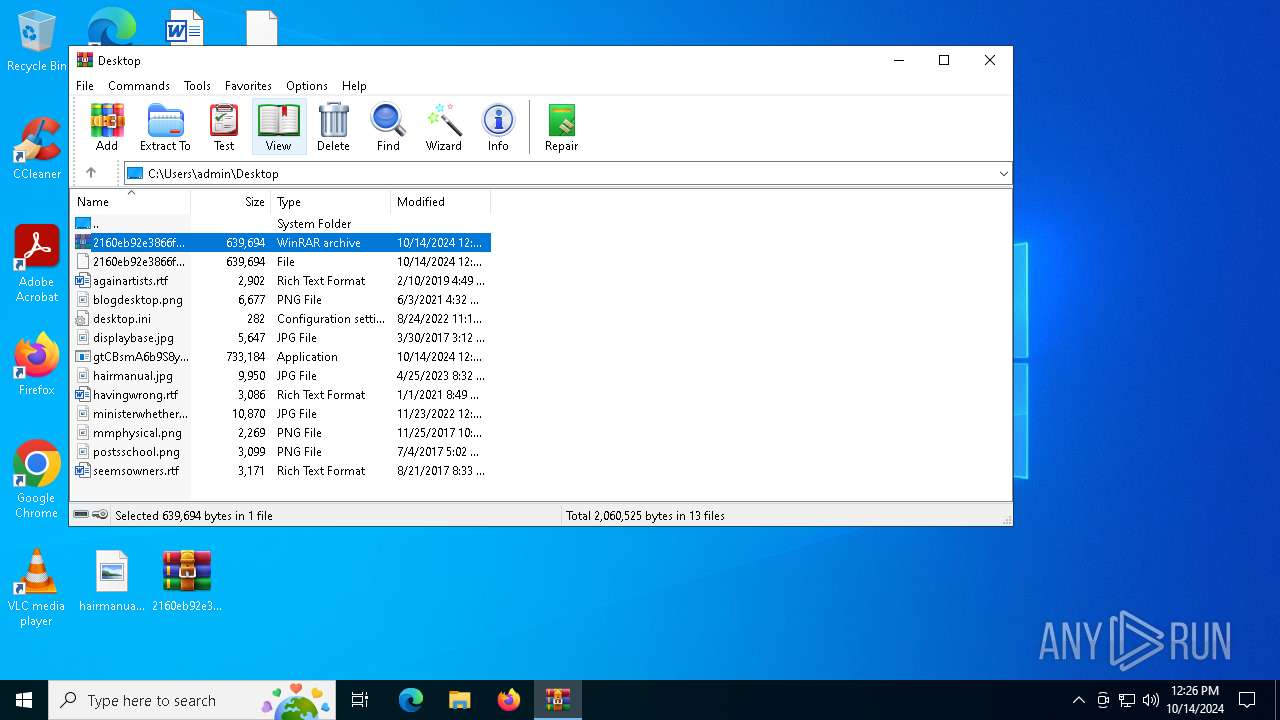
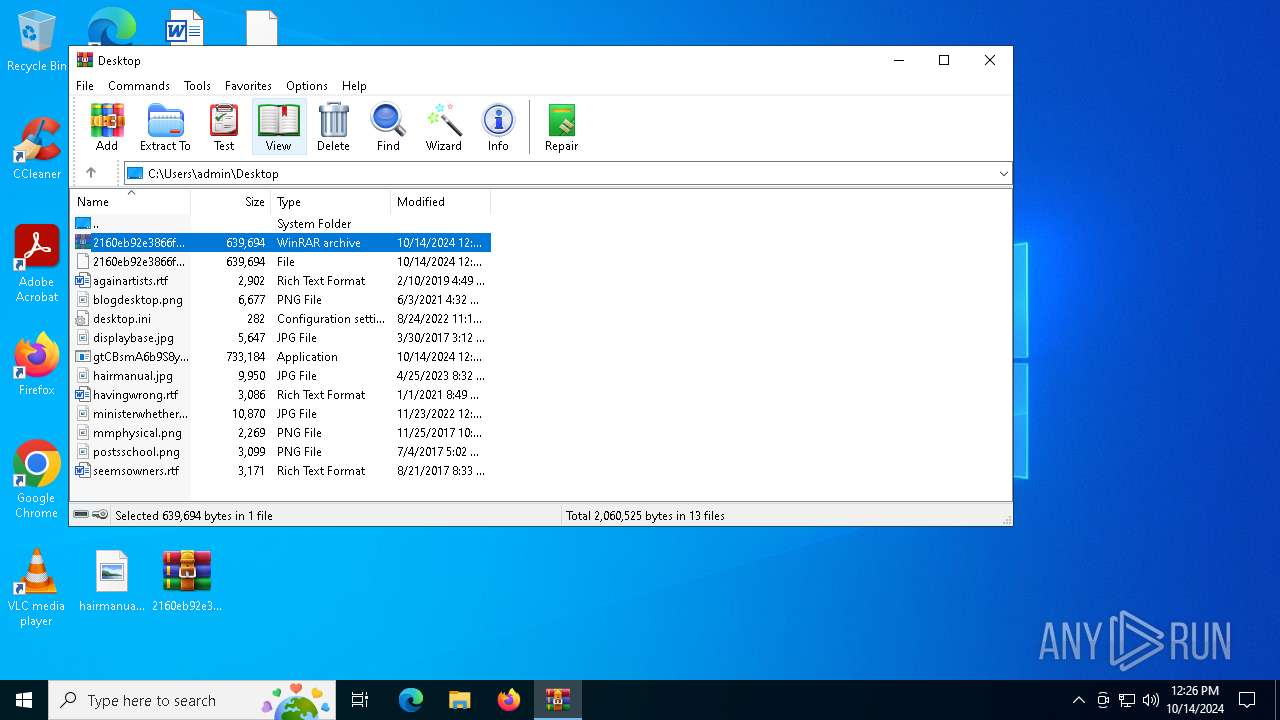
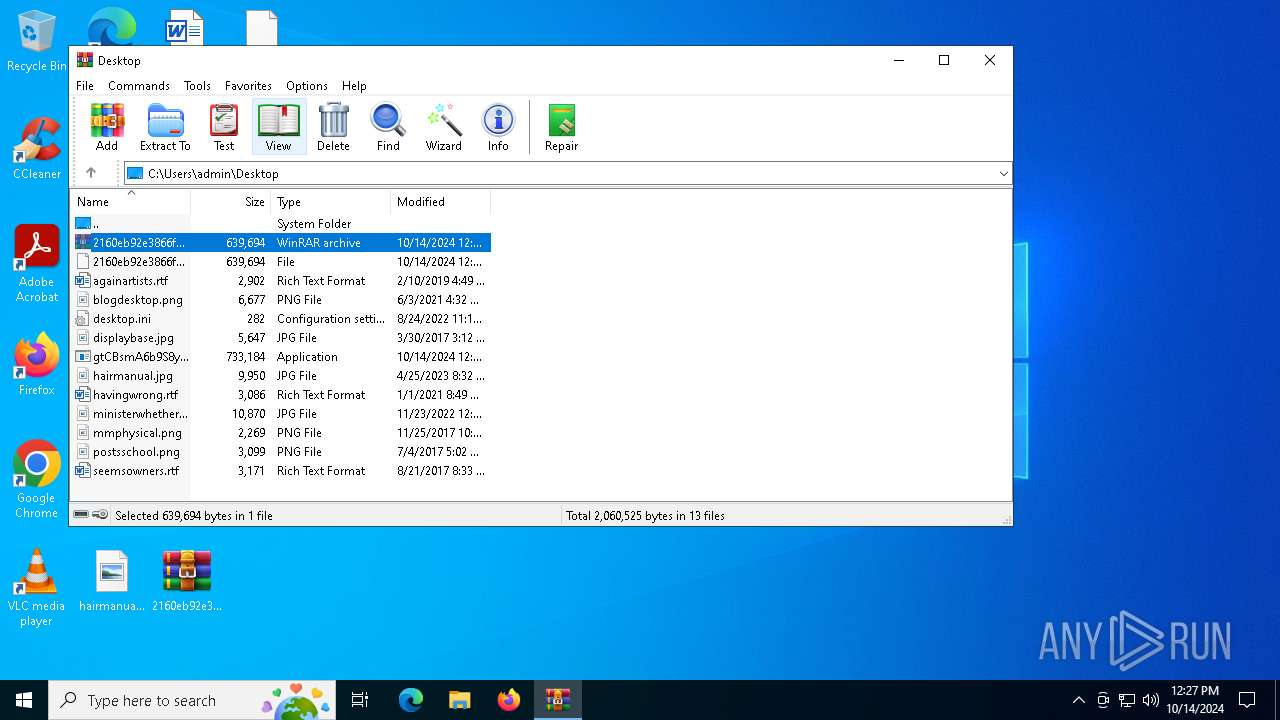
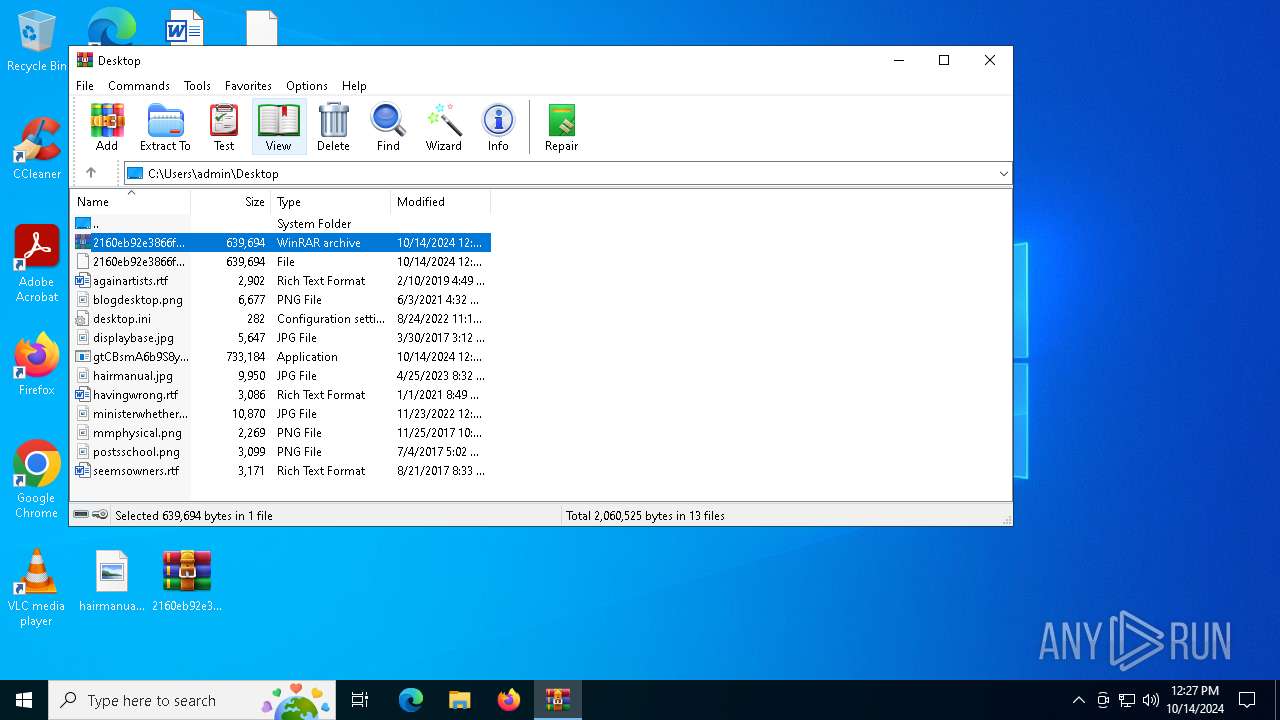
| 764 | "C:\Users\admin\Desktop\gtCBsmA6b9S8yWQ.exe" | C:\Users\admin\Desktop\gtCBsmA6b9S8yWQ.exe | — | explorer.exe | |||||||||||
User: admin Company: PacholukMidterm01 Integrity Level: MEDIUM Description: PacholukMidterm01 Exit code: 0 Version: 3.0.0.0 Modules
| |||||||||||||||
| 2172 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3964 | "C:\Users\admin\Desktop\gtCBsmA6b9S8yWQ.exe" | C:\Users\admin\Desktop\gtCBsmA6b9S8yWQ.exe | — | gtCBsmA6b9S8yWQ.exe | |||||||||||
User: admin Company: PacholukMidterm01 Integrity Level: MEDIUM Description: PacholukMidterm01 Exit code: 4294967295 Version: 3.0.0.0 Modules
| |||||||||||||||
| 6432 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\2160eb92e3866fecd97877790fbc2b59105588ddcdab5c54acd58033b9b6a8b7.rar | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 7164 | "C:\Users\admin\Desktop\gtCBsmA6b9S8yWQ.exe" | C:\Users\admin\Desktop\gtCBsmA6b9S8yWQ.exe | gtCBsmA6b9S8yWQ.exe | ||||||||||||
User: admin Company: PacholukMidterm01 Integrity Level: MEDIUM Description: PacholukMidterm01 Version: 3.0.0.0 Modules
AgentTesla(PID) Process(7164) gtCBsmA6b9S8yWQ.exe Protocolsmtp Hostmail.apexrnun.com Port587 Usernameroocckkbtwo@apexrnun.com PasswordTsHZsTv}Jnj5E5Bn | |||||||||||||||
Total events
4 806
Read events
4 659
Write events
147
Delete events
0
Modification events
| (PID) Process: | (6432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (6432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\2160eb92e3866fecd97877790fbc2b59105588ddcdab5c54acd58033b9b6a8b7.rar | |||
| (PID) Process: | (6432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
| (PID) Process: | (6432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | psize |
Value: 80 | |||
| (PID) Process: | (6432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
23
DNS requests
8
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1764 | RUXIMICS.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6944 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6944 | svchost.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7164 | gtCBsmA6b9S8yWQ.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=hosting | unknown | — | — | shared |
1764 | RUXIMICS.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6944 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1764 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5488 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6944 | svchost.exe | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5488 | MoUsoCoreWorker.exe | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1764 | RUXIMICS.exe | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5488 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
6944 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
ip-api.com |
| shared |
mail.apexrnun.com |
| malicious |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2172 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
2172 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
7164 | gtCBsmA6b9S8yWQ.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External Hosting Lookup by ip-api |
7164 | gtCBsmA6b9S8yWQ.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
7164 | gtCBsmA6b9S8yWQ.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 32 |
7164 | gtCBsmA6b9S8yWQ.exe | Misc activity | SUSPICIOUS [ANY.RUN] Sent Host Name in HTTP POST Body |
7164 | gtCBsmA6b9S8yWQ.exe | Successful Credential Theft Detected | STEALER [ANY.RUN] Attempt to exfiltrate via SMTP |
7164 | gtCBsmA6b9S8yWQ.exe | Misc activity | INFO [ANY.RUN] SMTP email client opens transfer with server (EHLO) |