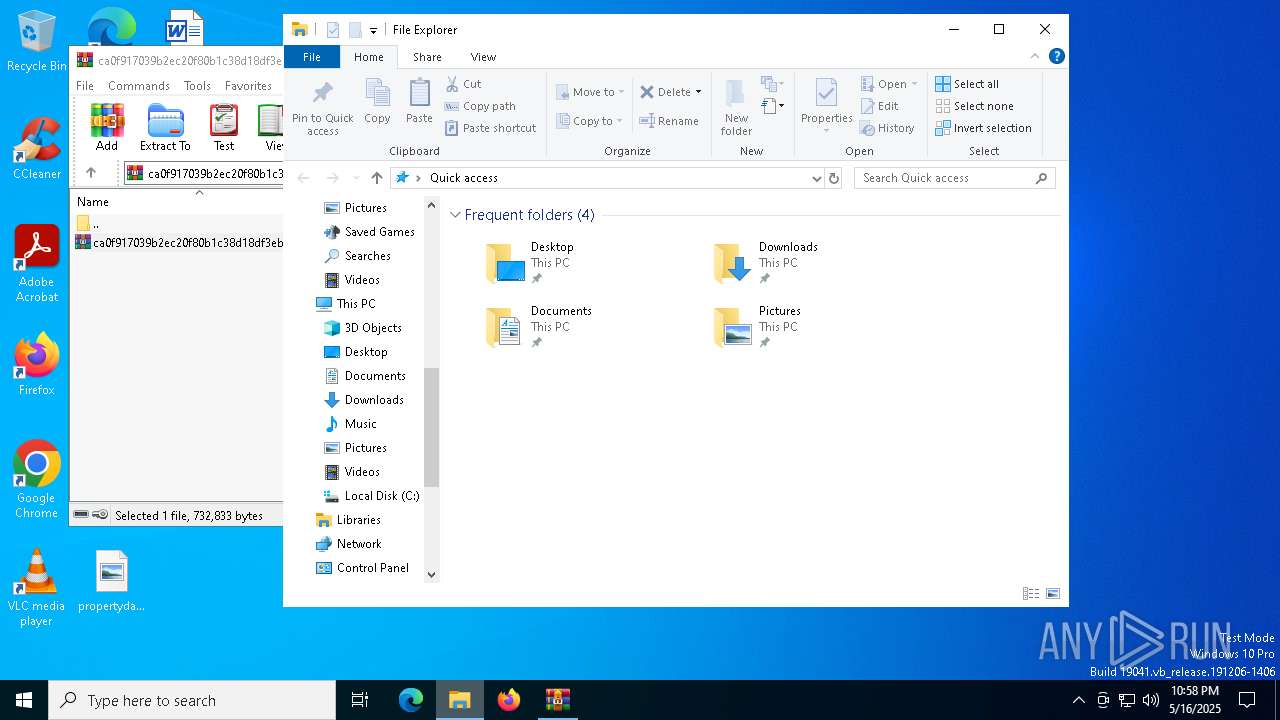
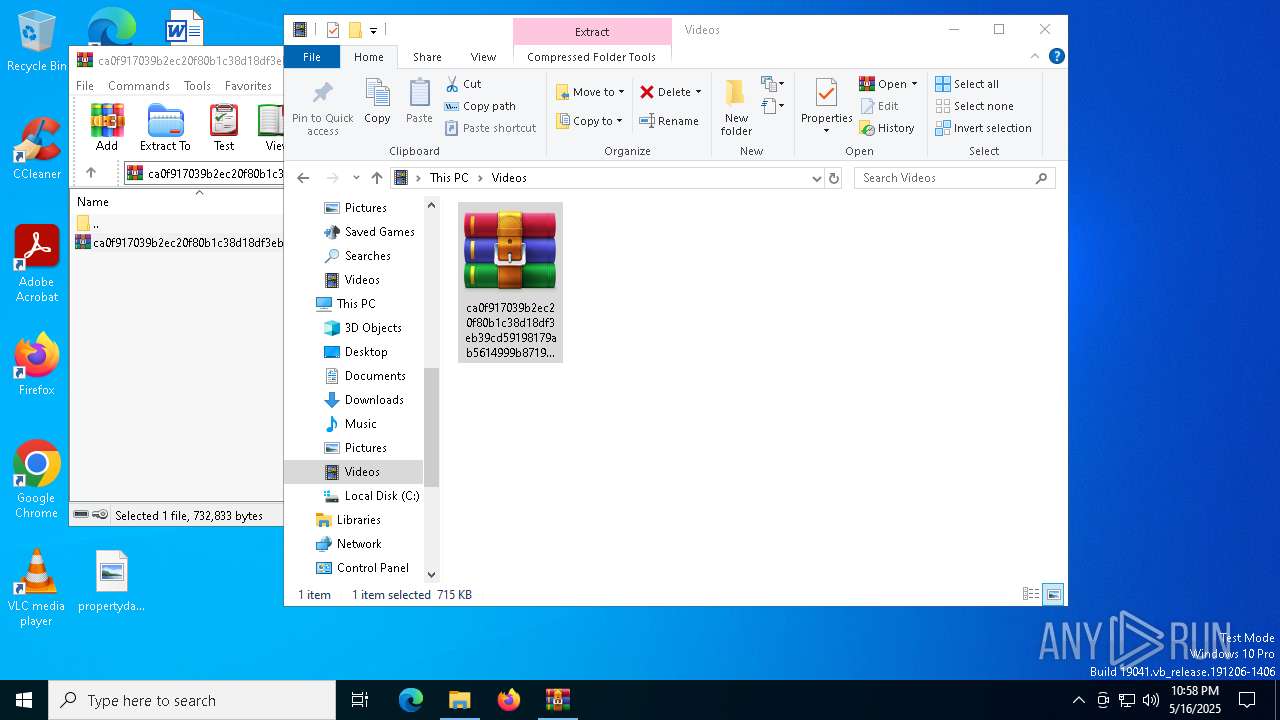
| File name: | ca0f917039b2ec20f80b1c38d18df3eb39cd59198179ab5614999b8719e7dfe3.zip |
| Full analysis: | https://app.any.run/tasks/bfc73e9a-110d-4166-aa7c-0757f62c5309 |
| Verdict: | Malicious activity |
| Threats: | GootLoader is an initial-access-as-a-service malware that operates by delivering the GootKit banking trojan and other malicious payloads. It utilizes techniques such as fileless execution and process injection to avoid detection. The malware is often distributed through SEO poisoning and compromised websites, deceiving users into downloading infected files. |
| Analysis date: | May 16, 2025, 22:57:33 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v5.1 to extract, compression method=AES Encrypted |
| MD5: | 5CE3289021C7B80EC806CBB85182C870 |
| SHA1: | 9BB7CDF8236619CB86639FBF7819CFA5C78447E1 |
| SHA256: | 213C87DF101A44ECBEC452CA61393089E95F2FBD4AF8DED7211F23D0FDB0188D |
| SSDEEP: | 24576:enQcA+tYon0wHDwl36ymPErEaBKdGMil0S0m7rmRapfMv1o5F8Gb3HKGCd+FQPbc:enQcptYon0wHDwl36ymPErEaBKYMil0k |
MALICIOUS
Opens a text file (SCRIPT)
- wscript.exe (PID: 8052)
Gets %appdata% folder path (SCRIPT)
- wscript.exe (PID: 8052)
Accesses environment variables (SCRIPT)
- wscript.exe (PID: 8052)
Access Task Scheduler's settings (SCRIPT)
- wscript.exe (PID: 8052)
Gets username (SCRIPT)
- wscript.exe (PID: 8052)
Gets or sets visibliity for the scheduled task (SCRIPT)
- wscript.exe (PID: 8052)
Gets context to execute command-line operations (SCRIPT)
- wscript.exe (PID: 8052)
Creates a new scheduled task (SCRIPT)
- wscript.exe (PID: 8052)
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 6184)
- cscript.exe (PID: 5332)
Gets a file object corresponding to the file in a specified path (SCRIPT)
- wscript.exe (PID: 8052)
SUSPICIOUS
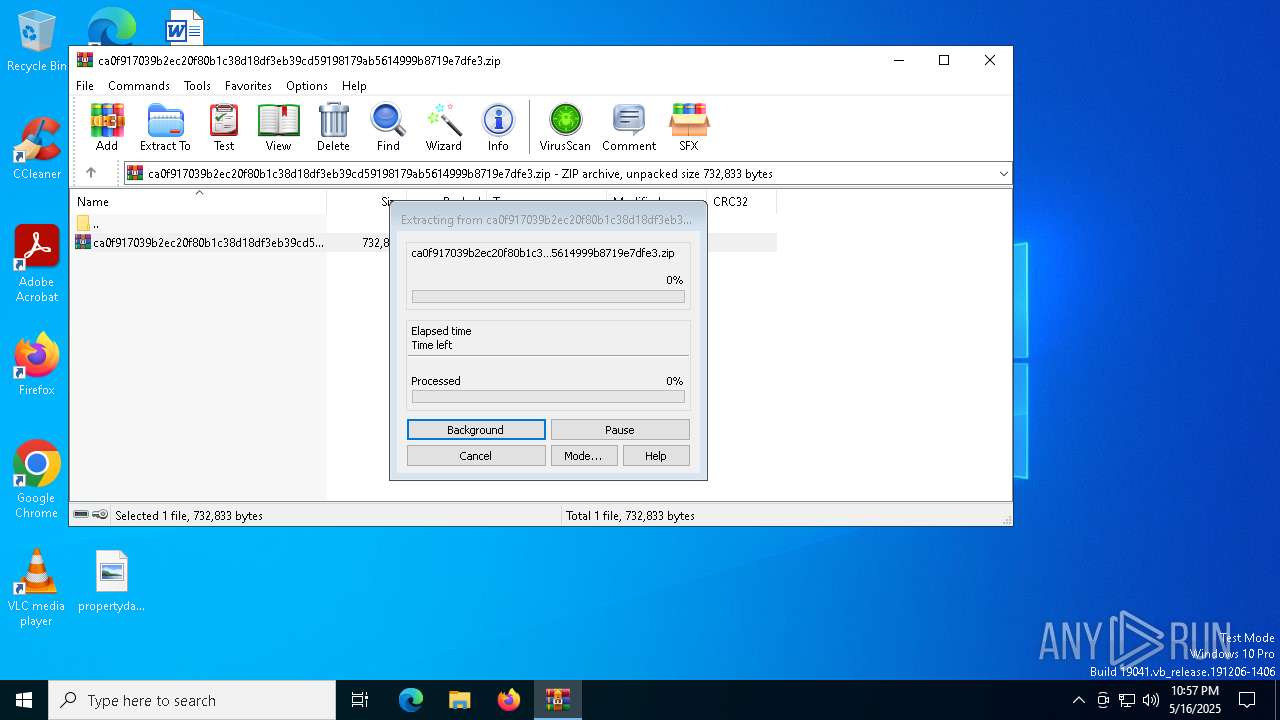
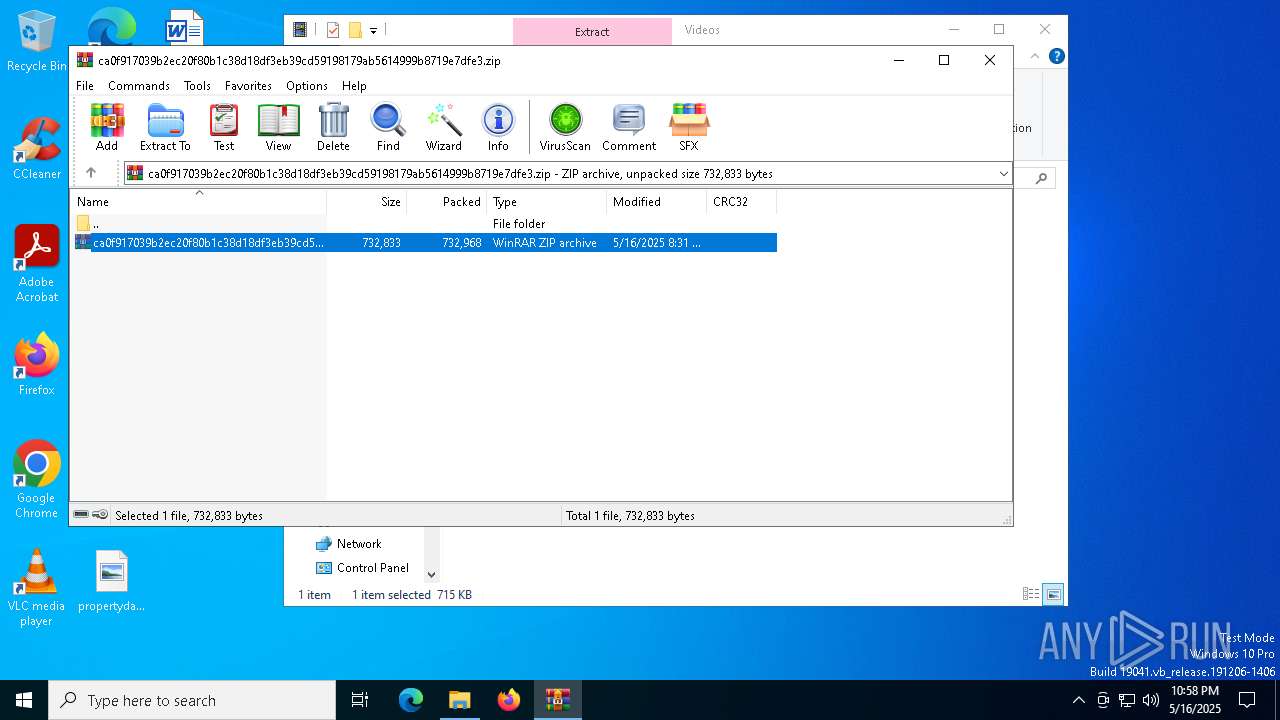
Generic archive extractor
- WinRAR.exe (PID: 7000)
Gets context to manipulate scheduled tasks (SCRIPT)
- wscript.exe (PID: 8052)
Gets a folder of registered tasks (SCRIPT)
- wscript.exe (PID: 8052)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 8052)
Checks whether a specific file exists (SCRIPT)
- wscript.exe (PID: 8052)
Writes binary data to a Stream object (SCRIPT)
- wscript.exe (PID: 8052)
- cscript.exe (PID: 5332)
Gets context to manipulate triggers of a scheduled task (SCRIPT)
- wscript.exe (PID: 8052)
Accesses Scheduled Task settings (SCRIPT)
- wscript.exe (PID: 8052)
Accesses current user name via WMI (SCRIPT)
- wscript.exe (PID: 8052)
Gets scheduled task context (SCRIPT)
- wscript.exe (PID: 8052)
The process executes via Task Scheduler
- wscript.exe (PID: 6184)
The process executes JS scripts
- wscript.exe (PID: 6184)
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 6184)
Runs shell command (SCRIPT)
- wscript.exe (PID: 6184)
- cscript.exe (PID: 5332)
Starts POWERSHELL.EXE for commands execution
- cscript.exe (PID: 5332)
Reads data from a binary Stream object (SCRIPT)
- cscript.exe (PID: 5332)
INFO
Manual execution by a user
- wscript.exe (PID: 8052)
- WinRAR.exe (PID: 7984)
Reads the software policy settings
- slui.exe (PID: 7212)
- slui.exe (PID: 8116)
- powershell.exe (PID: 1452)
Checks proxy server information
- slui.exe (PID: 8116)
Self-termination (SCRIPT)
- wscript.exe (PID: 8052)
- wscript.exe (PID: 6184)
- cscript.exe (PID: 5332)
Reads security settings of Internet Explorer
- cscript.exe (PID: 5332)
- powershell.exe (PID: 1452)
Create files in a temporary directory
- powershell.exe (PID: 1452)
Checks current location (POWERSHELL)
- powershell.exe (PID: 1452)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0003 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2025:05:16 20:31:22 |
| ZipCRC: | 0x1352d341 |
| ZipCompressedSize: | 732968 |
| ZipUncompressedSize: | 732833 |
| ZipFileName: | ca0f917039b2ec20f80b1c38d18df3eb39cd59198179ab5614999b8719e7dfe3.zip |
Total processes
142
Monitored processes
11
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1188 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1452 | poWERsHelL | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5332 | "C:\Windows\System32\cscript.exe" "PROMET~1.JS" | C:\Windows\System32\cscript.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 6184 | "C:\WINDOWS\system32\wscript.EXE" PROMET~1.JS | C:\Windows\System32\wscript.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
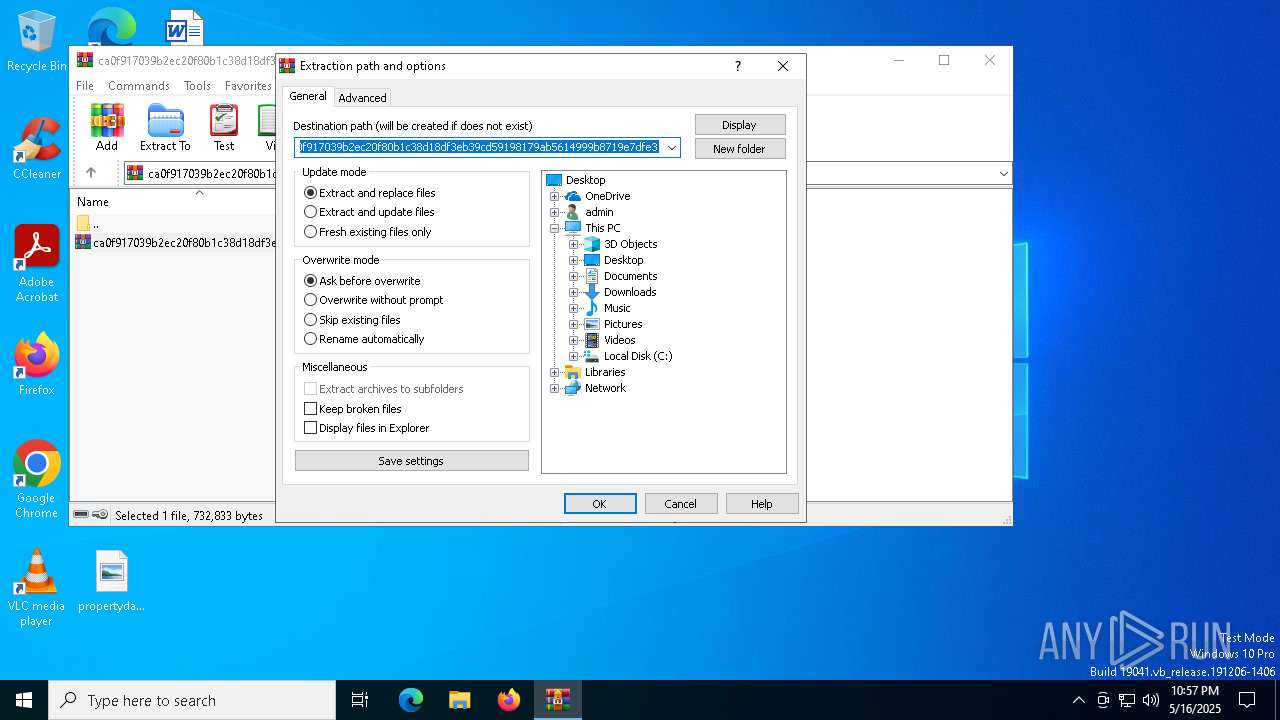
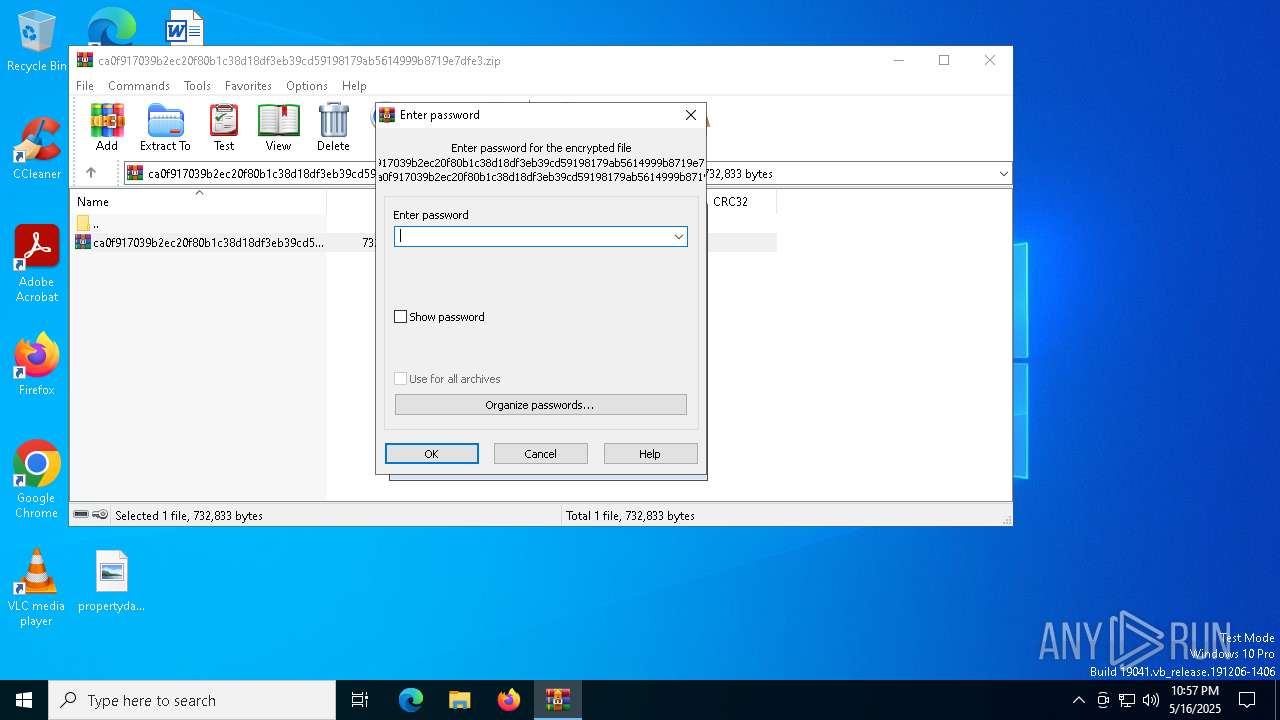
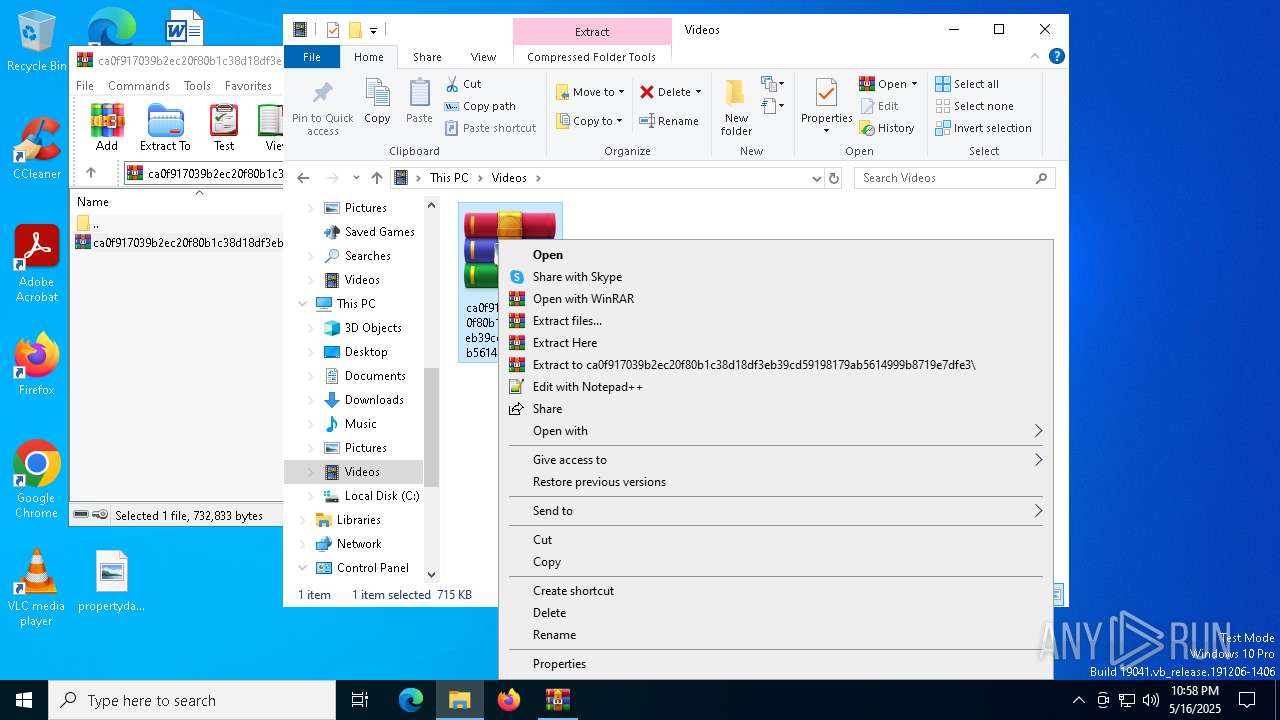
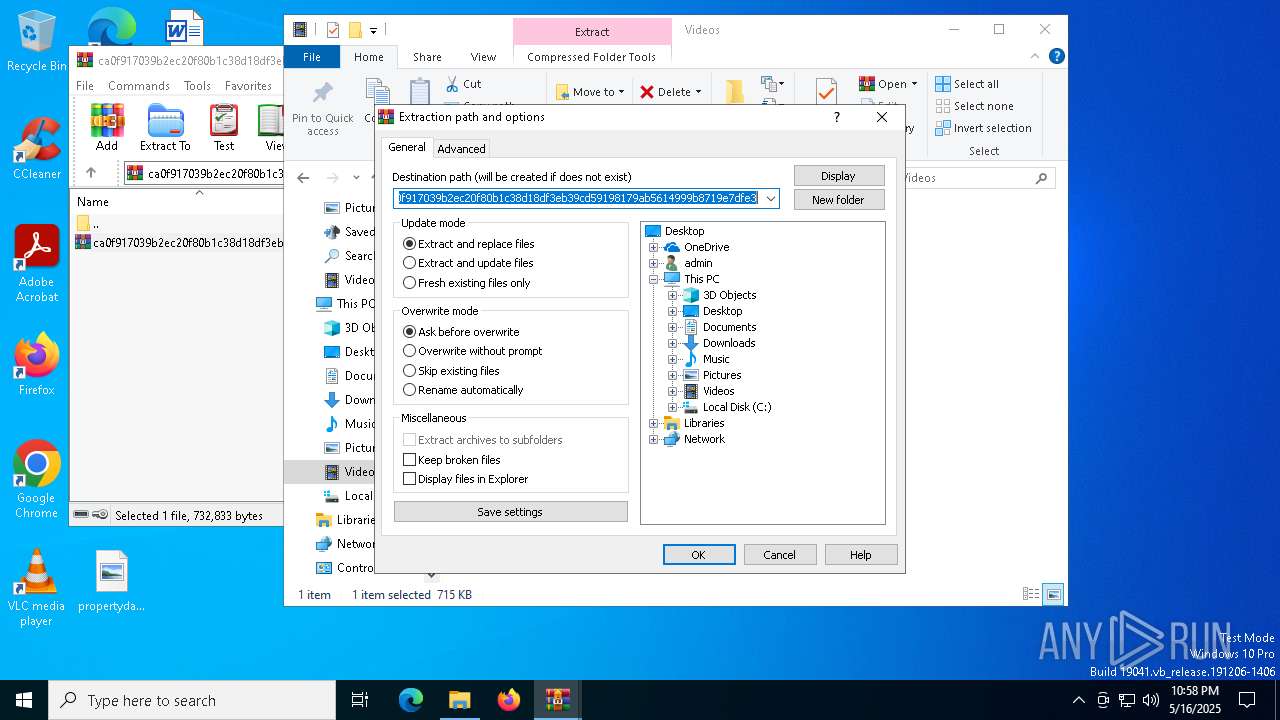
| 7000 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\ca0f917039b2ec20f80b1c38d18df3eb39cd59198179ab5614999b8719e7dfe3.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 7180 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7212 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7748 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
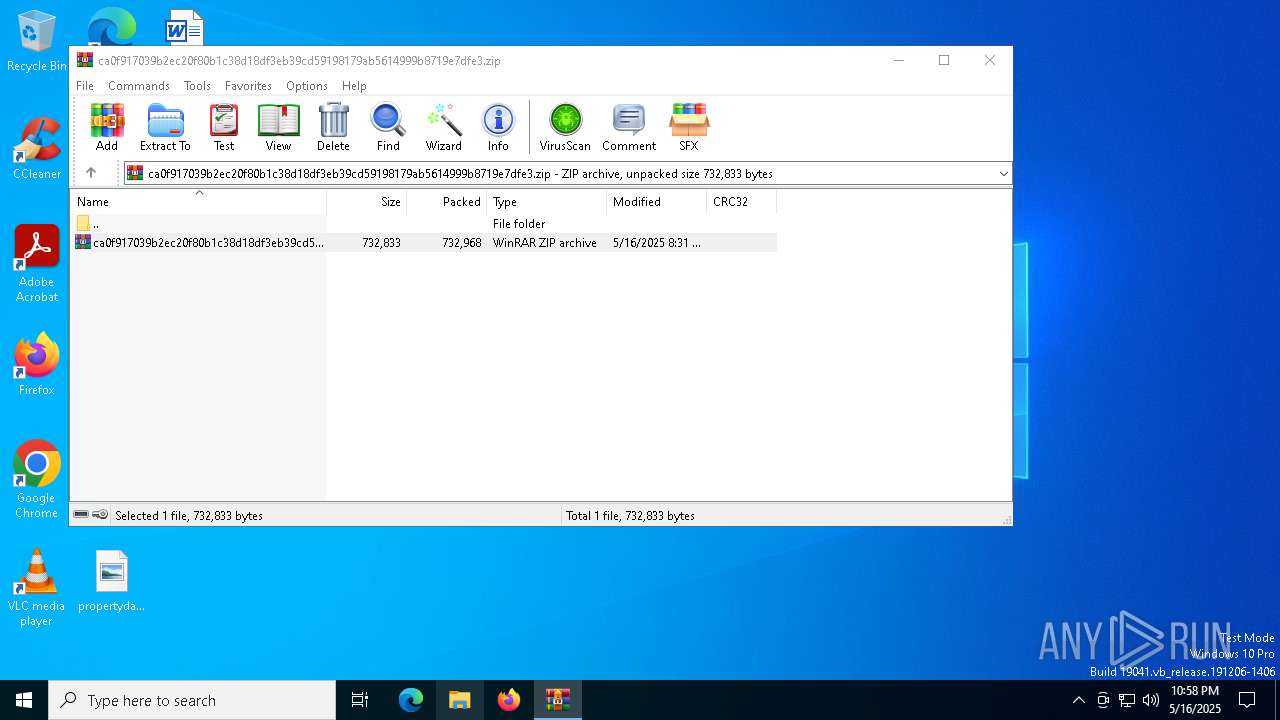
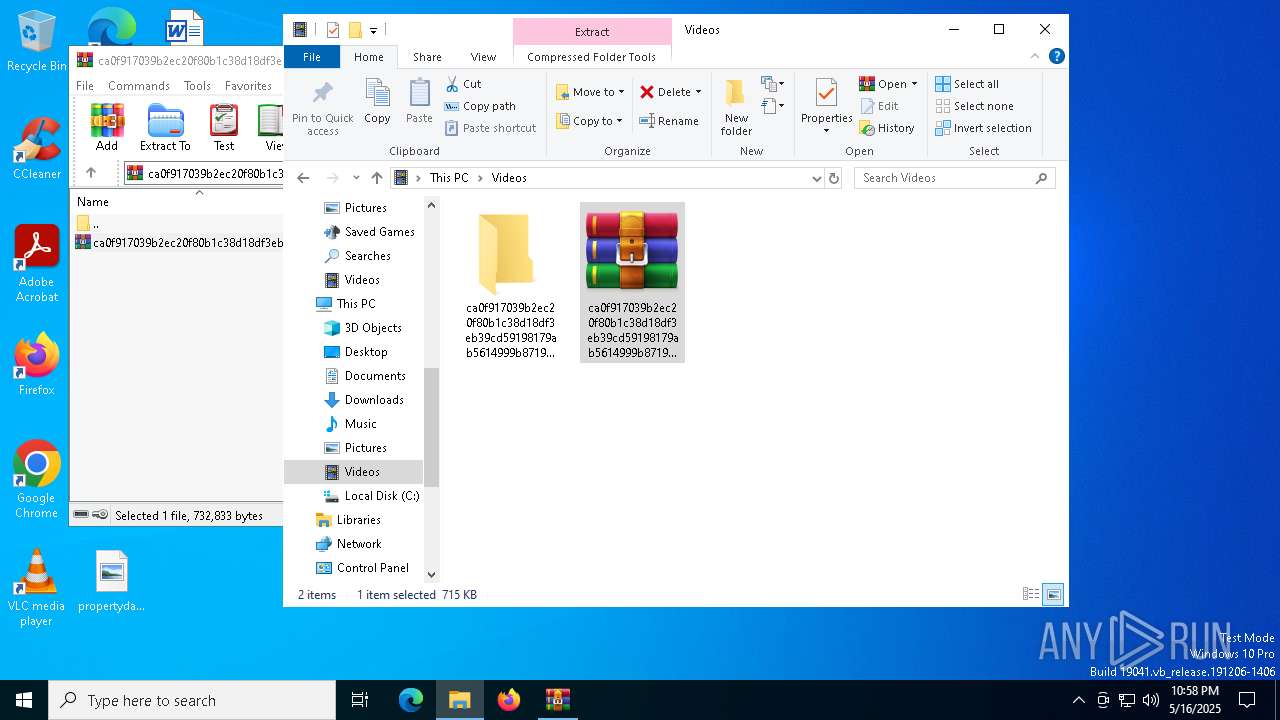
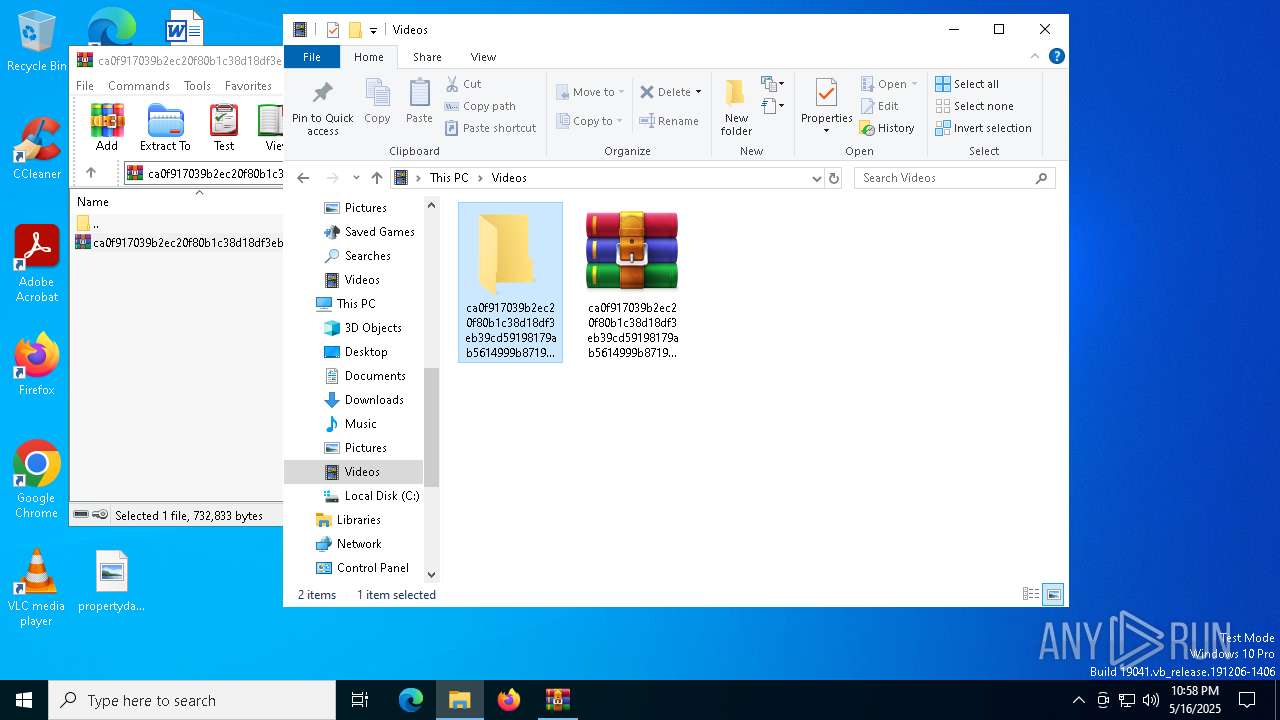
| 7984 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Videos\ca0f917039b2ec20f80b1c38d18df3eb39cd59198179ab5614999b8719e7dfe3.zip" "?\" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
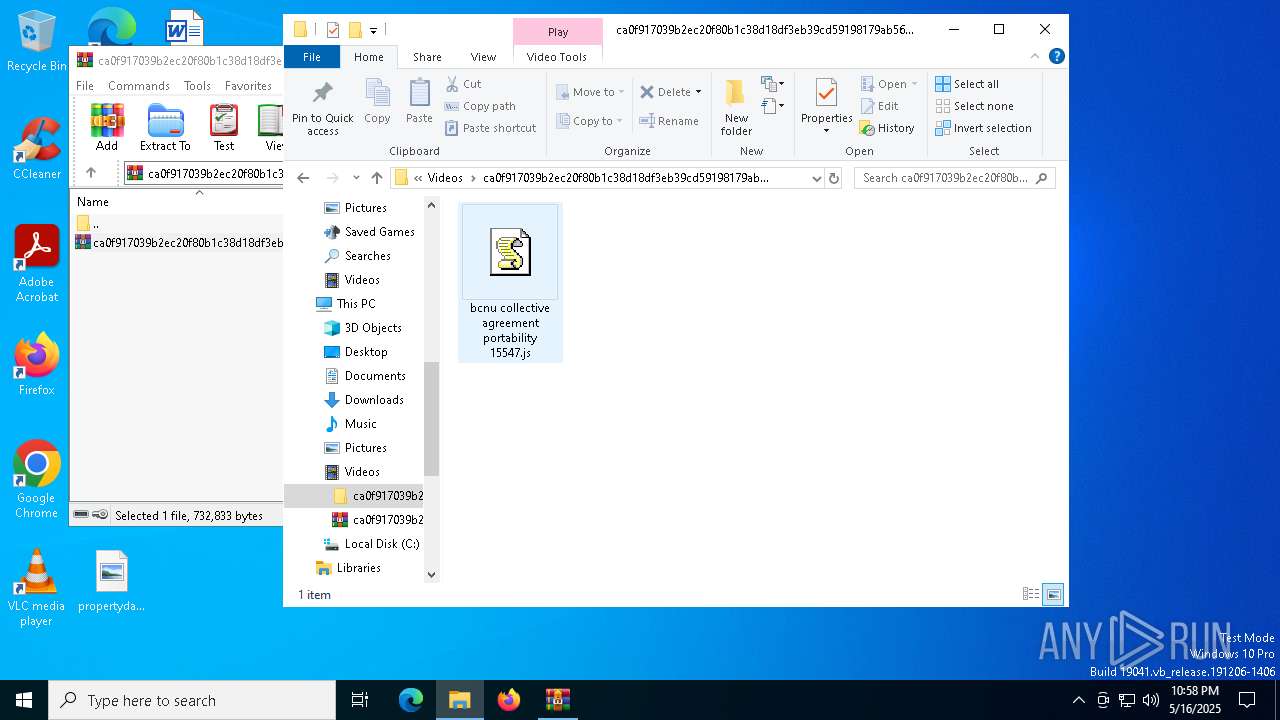
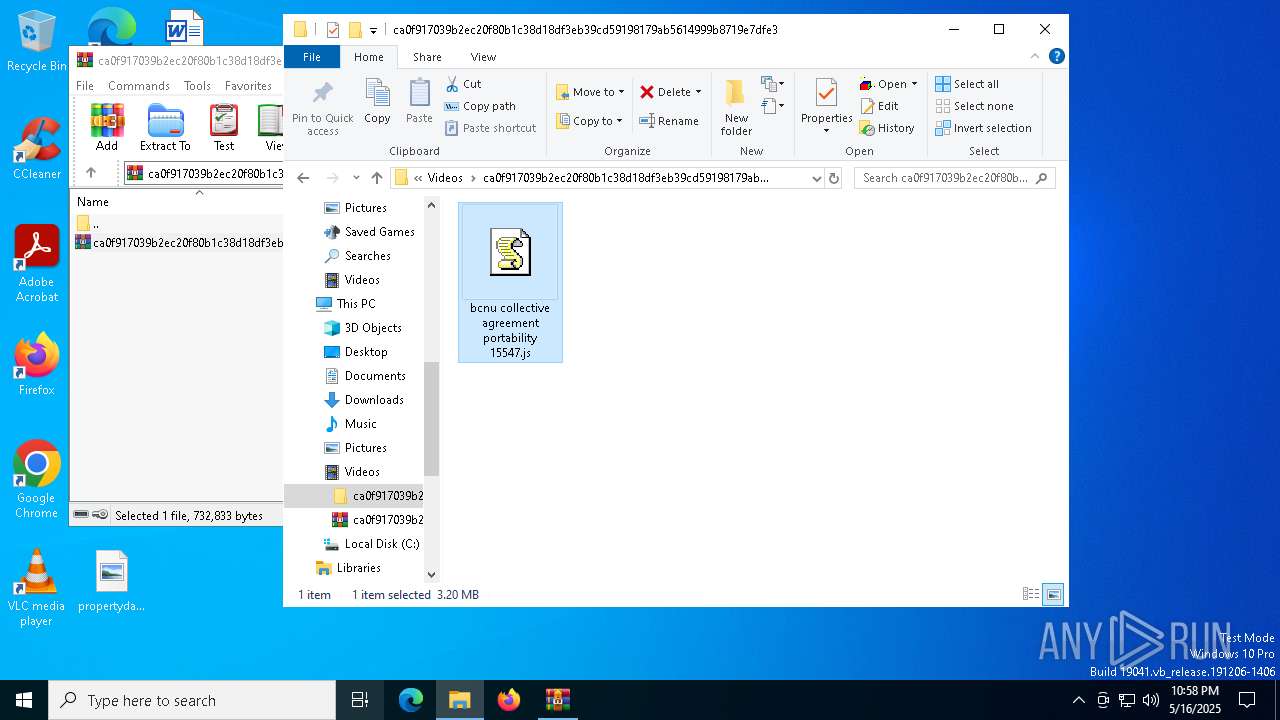
| 8052 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Videos\ca0f917039b2ec20f80b1c38d18df3eb39cd59198179ab5614999b8719e7dfe3\bcnu collective agreement portability 15547.js" | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
Total events
10 177
Read events
10 130
Write events
22
Delete events
25
Modification events
| (PID) Process: | (7000) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7000) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7000) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7000) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\ca0f917039b2ec20f80b1c38d18df3eb39cd59198179ab5614999b8719e7dfe3.zip | |||
| (PID) Process: | (7000) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7000) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7000) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7000) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7000) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
| (PID) Process: | (7000) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 14 |
Value: | |||
Executable files
0
Suspicious files
2
Text files
2
Unknown types
0
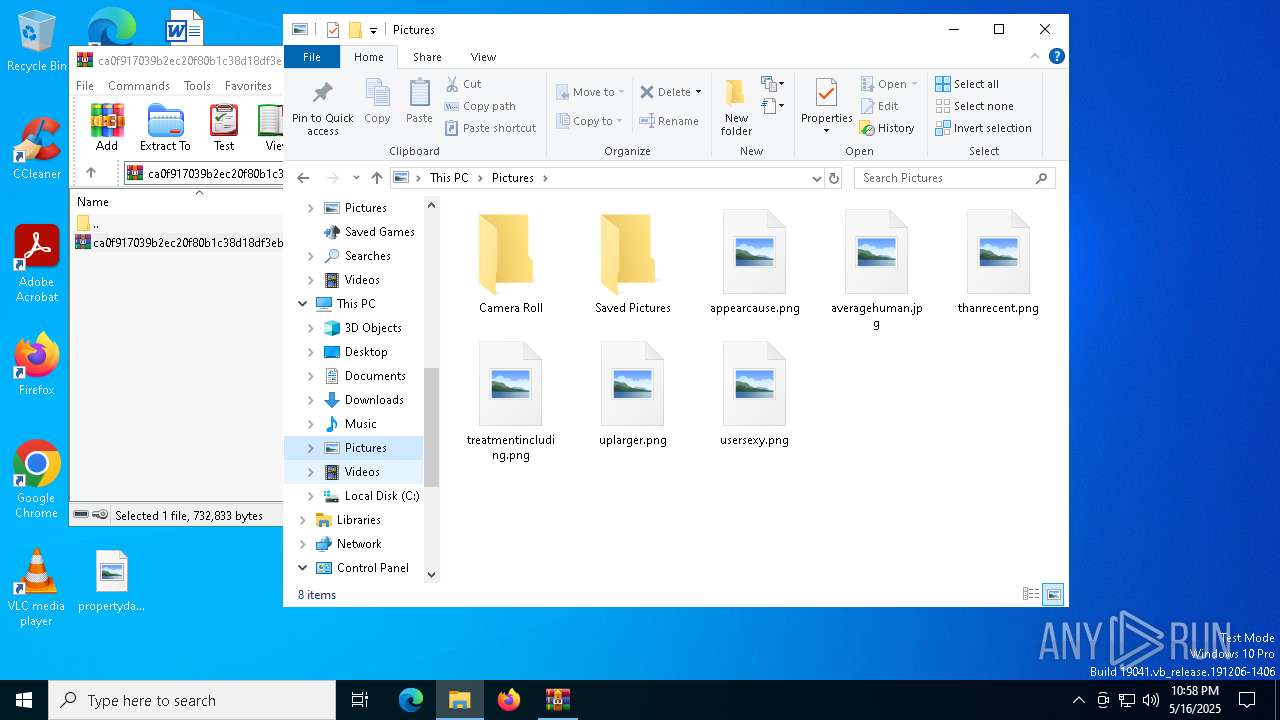
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8052 | wscript.exe | C:\Users\admin\AppData\Roaming\WinRAR\Interest Rate Swaps.log | — | |
MD5:— | SHA256:— | |||
| 8052 | wscript.exe | C:\Users\admin\AppData\Roaming\WinRAR\Promethean Board.js | — | |
MD5:— | SHA256:— | |||
| 1452 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_rrmxrtjq.vn1.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1452 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_3djnzg35.egf.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7984 | WinRAR.exe | C:\Users\admin\Videos\ca0f917039b2ec20f80b1c38d18df3eb39cd59198179ab5614999b8719e7dfe3\bcnu collective agreement portability 15547.js | binary | |
MD5:5D36BDF690724282BB8F8F1629AC7530 | SHA256:992F3DF595B0A9DB1AB7FE95DA799F9C9E65D44C71B73F7D6D5B9951EE528BFE | |||
| 7000 | WinRAR.exe | C:\Users\admin\Videos\ca0f917039b2ec20f80b1c38d18df3eb39cd59198179ab5614999b8719e7dfe3.zip | compressed | |
MD5:C2A78C21AE8579C277A99B564DD97A93 | SHA256:CA0F917039B2EC20F80B1C38D18DF3EB39CD59198179AB5614999B8719E7DFE3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
25
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7836 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7836 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.16.168.124:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
— | — | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6544 | svchost.exe | 20.190.159.71:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2112 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |