| URL: | https://qipracticeexchange.org/tbh9v |
| Full analysis: | https://app.any.run/tasks/f3cc40d6-e0b4-4edd-880c-0beaa104982b |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | December 31, 2024, 14:13:40 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 3D5EC7051222FB2EBBD25CE6B4FA2EE8 |
| SHA1: | DAB3933BE27AE69A689308A0F8F19D7EBF089D44 |
| SHA256: | 213401494C9A42B53F0E30593D681CC3E75D1B7CA6A6833A2B1ABD6B6935DF7B |
| SSDEEP: | 3:N8VK5E2Ap:2w5hG |
MALICIOUS
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 7532)
- powershell.exe (PID: 7616)
- powershell.exe (PID: 6880)
- powershell.exe (PID: 7416)
- powershell.exe (PID: 7768)
- powershell.exe (PID: 7944)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 7616)
- powershell.exe (PID: 7532)
- powershell.exe (PID: 6880)
- powershell.exe (PID: 7416)
- powershell.exe (PID: 7768)
- powershell.exe (PID: 7944)
Request from PowerShell that ran from MSHTA.EXE
- powershell.exe (PID: 7616)
- powershell.exe (PID: 7532)
- powershell.exe (PID: 6880)
- powershell.exe (PID: 7416)
- powershell.exe (PID: 7768)
- powershell.exe (PID: 7944)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2192)
XWORM has been detected (YARA)
- RegSvcs.exe (PID: 7940)
XWORM has been detected (SURICATA)
- RegSvcs.exe (PID: 7940)
Connects to the CnC server
- svchost.exe (PID: 2192)
- RegSvcs.exe (PID: 7940)
Changes the autorun value in the registry
- RegSvcs.exe (PID: 5268)
SUSPICIOUS
Found IP address in command line
- powershell.exe (PID: 7532)
- powershell.exe (PID: 7616)
- powershell.exe (PID: 6880)
- powershell.exe (PID: 7944)
- powershell.exe (PID: 7416)
- powershell.exe (PID: 7768)
Obfuscated call of IEX
- powershell.exe (PID: 7532)
- powershell.exe (PID: 7616)
- powershell.exe (PID: 6880)
- powershell.exe (PID: 7416)
- powershell.exe (PID: 7944)
- powershell.exe (PID: 7768)
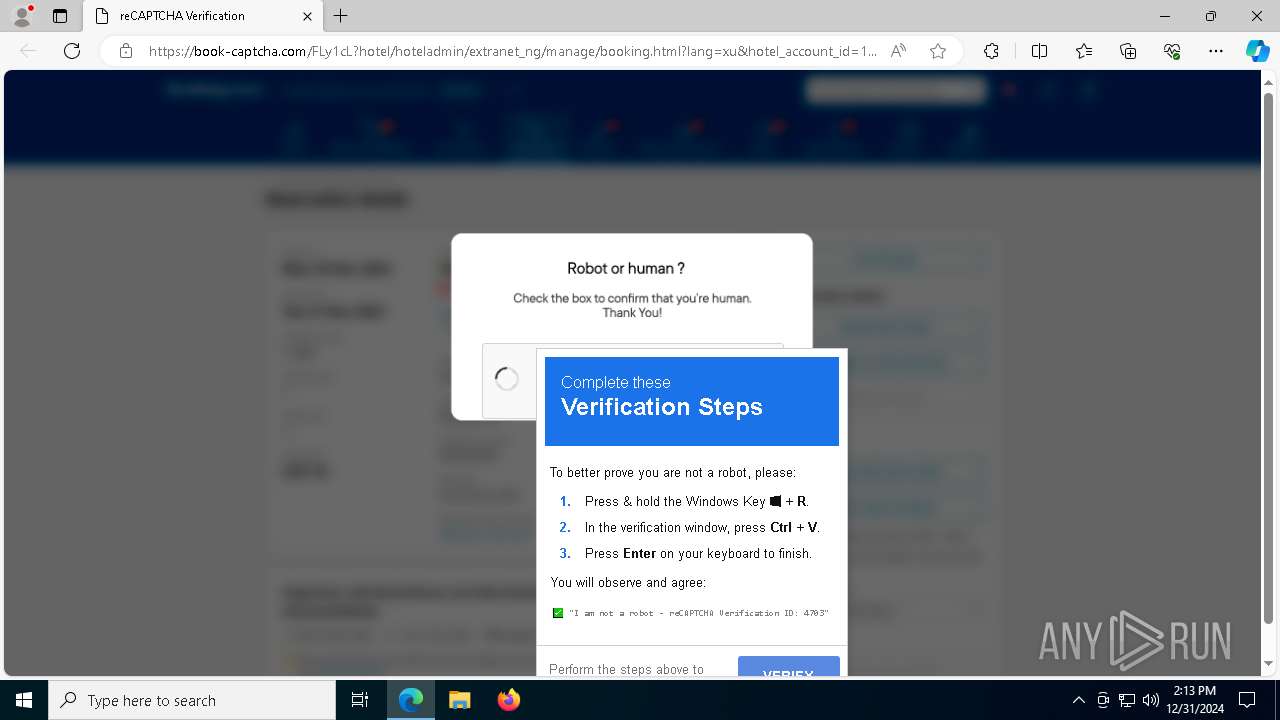
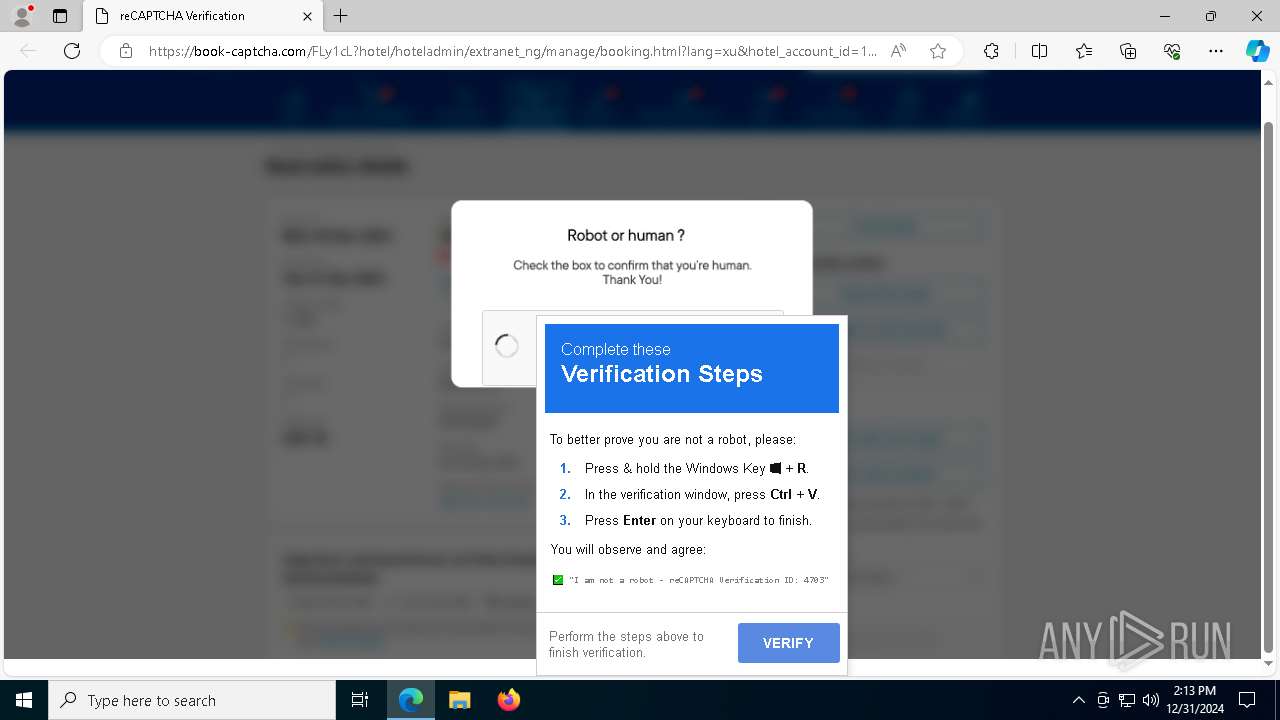
Starts POWERSHELL.EXE for commands execution
- mshta.exe (PID: 7292)
- mshta.exe (PID: 628)
Probably obfuscated PowerShell command line is found
- mshta.exe (PID: 7292)
- mshta.exe (PID: 628)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 7616)
- powershell.exe (PID: 7532)
- powershell.exe (PID: 6880)
- powershell.exe (PID: 7768)
- powershell.exe (PID: 7416)
- powershell.exe (PID: 7944)
Process uses IPCONFIG to clear DNS cache
- powershell.exe (PID: 7532)
- powershell.exe (PID: 7616)
- powershell.exe (PID: 6880)
- powershell.exe (PID: 7768)
- powershell.exe (PID: 7944)
- powershell.exe (PID: 7416)
Connects to the server without a host name
- powershell.exe (PID: 7532)
- powershell.exe (PID: 7616)
- powershell.exe (PID: 6880)
- powershell.exe (PID: 7768)
- powershell.exe (PID: 7416)
- powershell.exe (PID: 7944)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2192)
- RegSvcs.exe (PID: 7940)
Connects to unusual port
- RegSvcs.exe (PID: 7940)
INFO
Reads the software policy settings
- SearchApp.exe (PID: 5064)
- RegSvcs.exe (PID: 8036)
Checks supported languages
- identity_helper.exe (PID: 3696)
- SearchApp.exe (PID: 5064)
- RegSvcs.exe (PID: 7940)
- RegSvcs.exe (PID: 8024)
- RegSvcs.exe (PID: 5268)
- RegSvcs.exe (PID: 7076)
- RegSvcs.exe (PID: 6772)
Reads the computer name
- identity_helper.exe (PID: 3696)
- RegSvcs.exe (PID: 8024)
- RegSvcs.exe (PID: 8036)
- RegSvcs.exe (PID: 5268)
- RegSvcs.exe (PID: 6772)
Reads Environment values
- identity_helper.exe (PID: 3696)
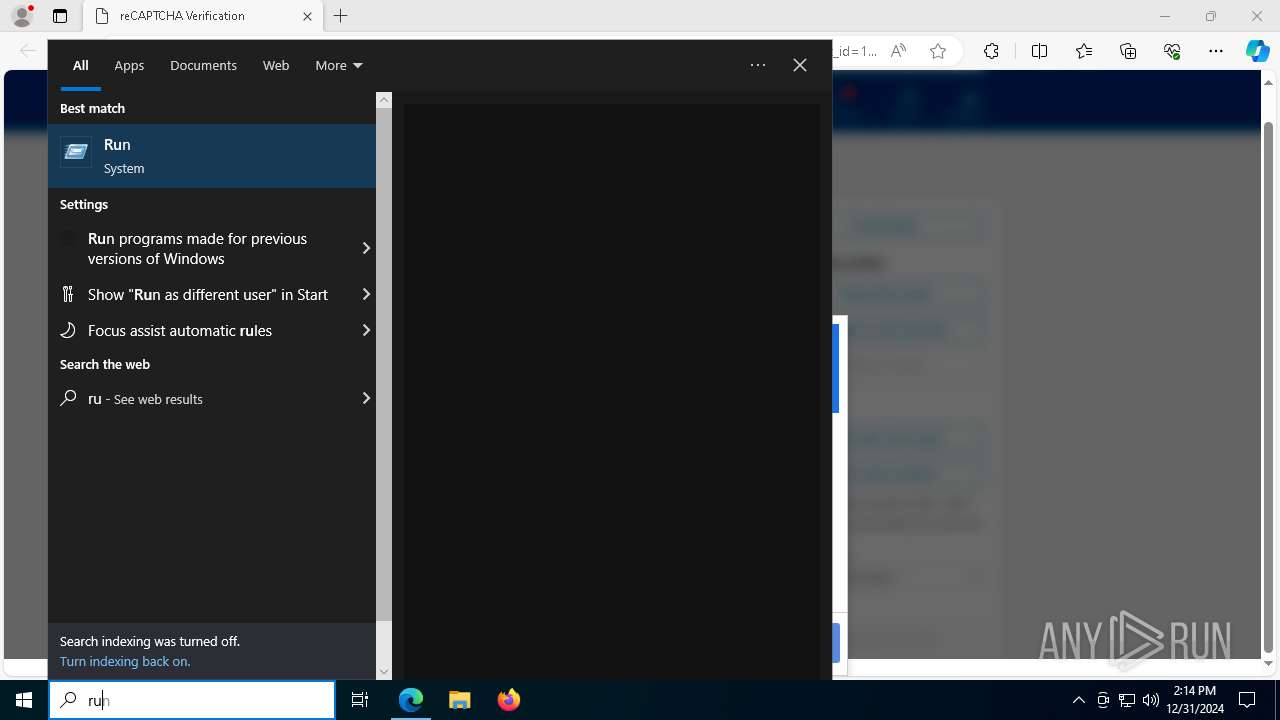
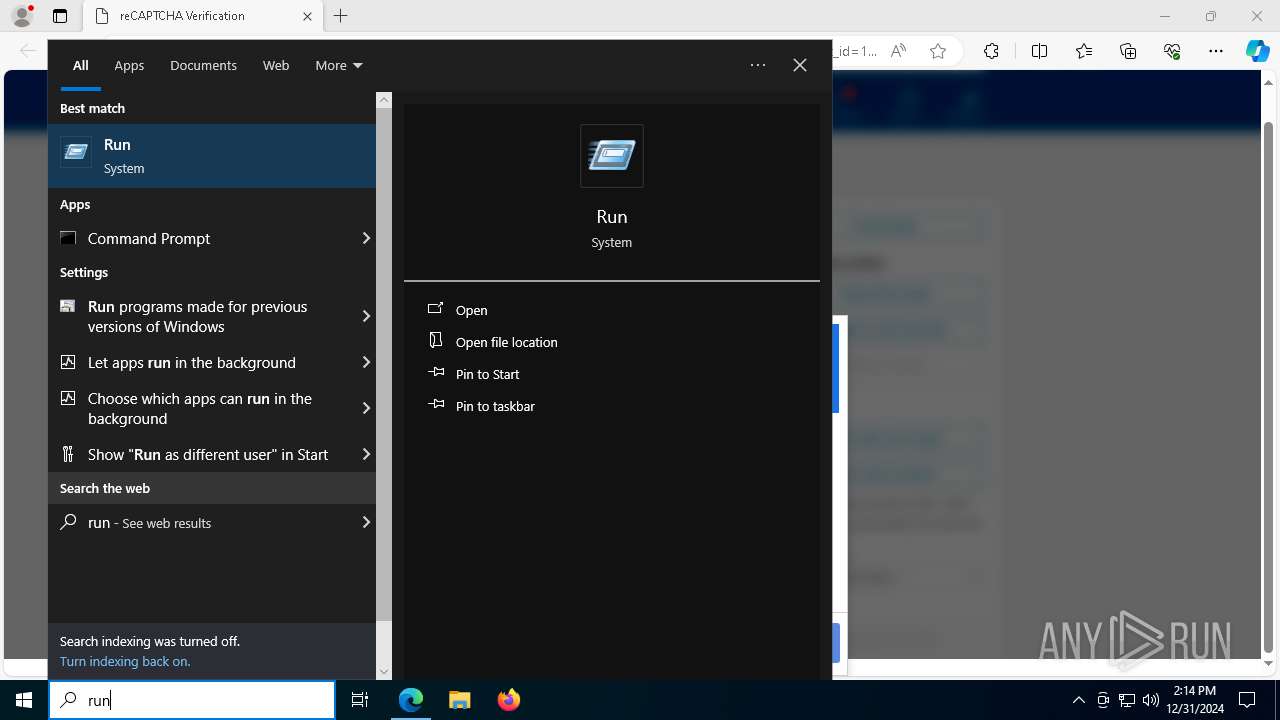
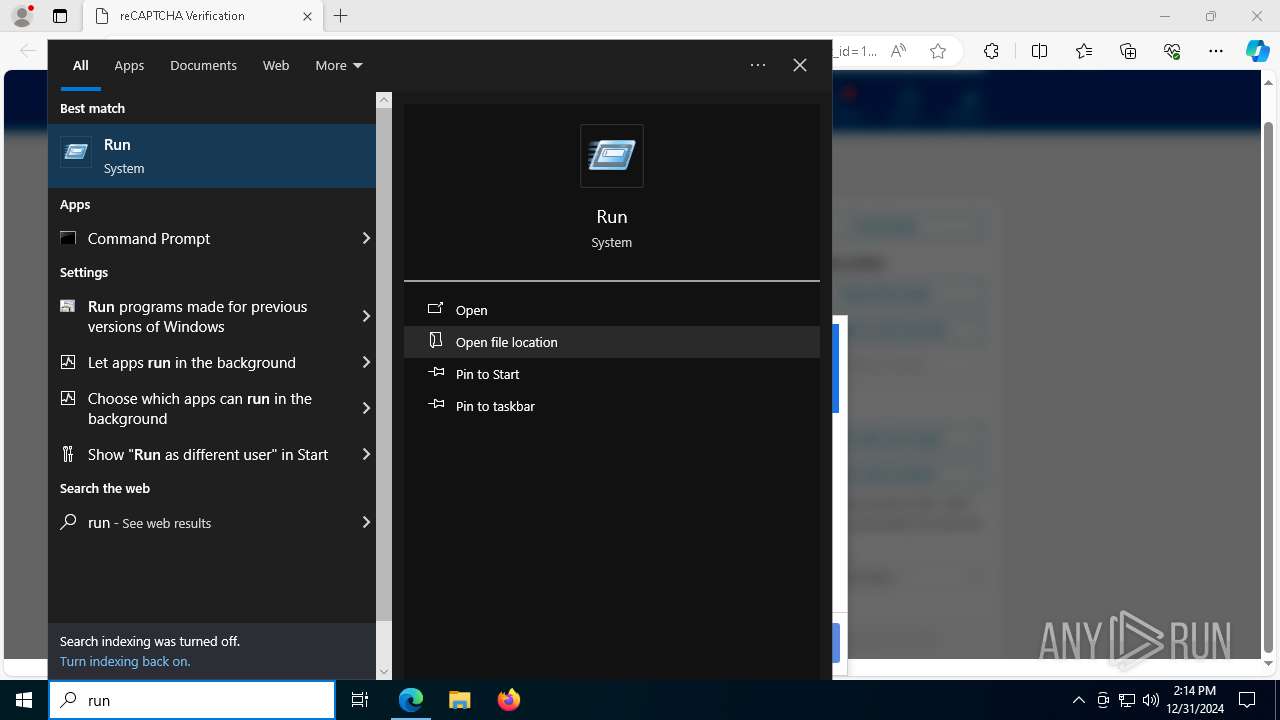
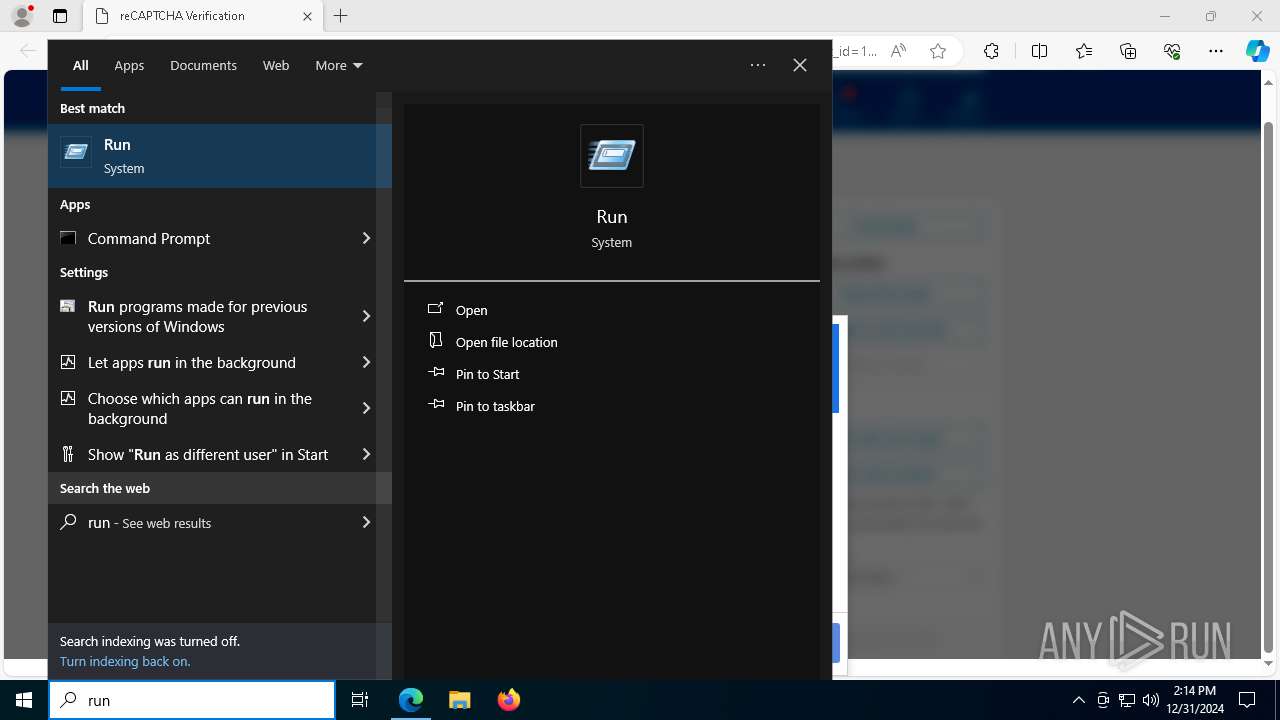
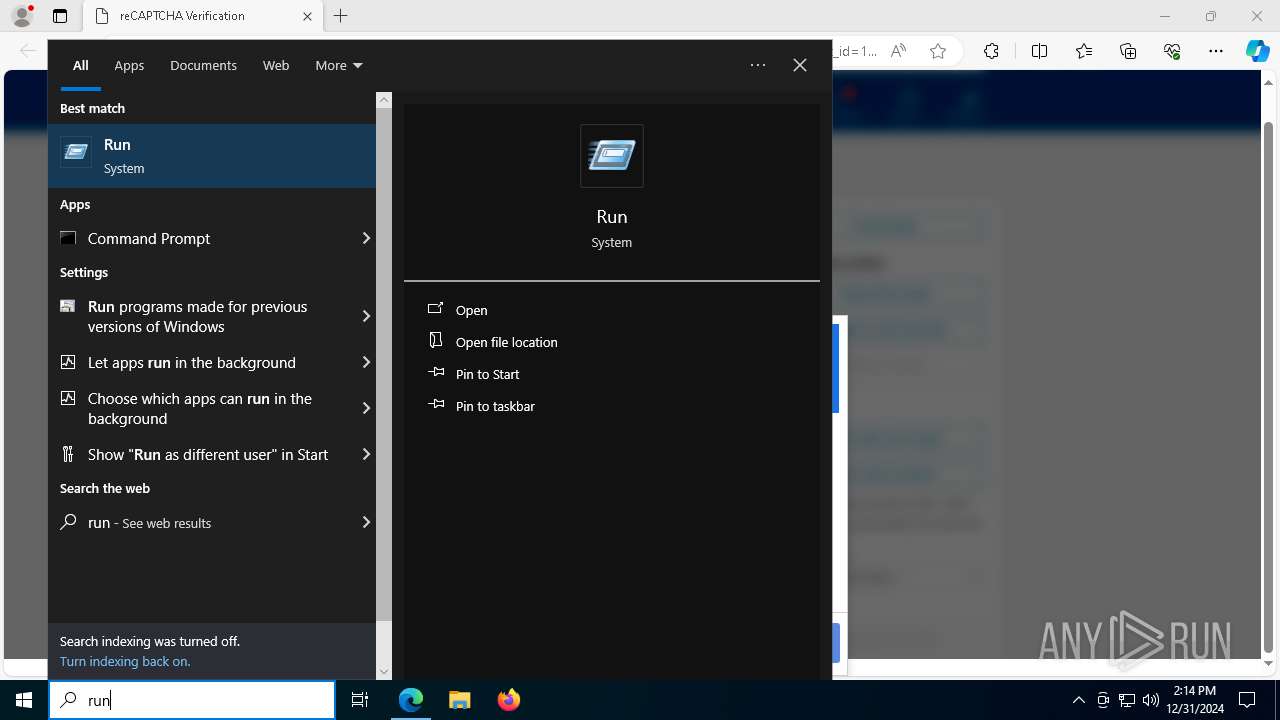
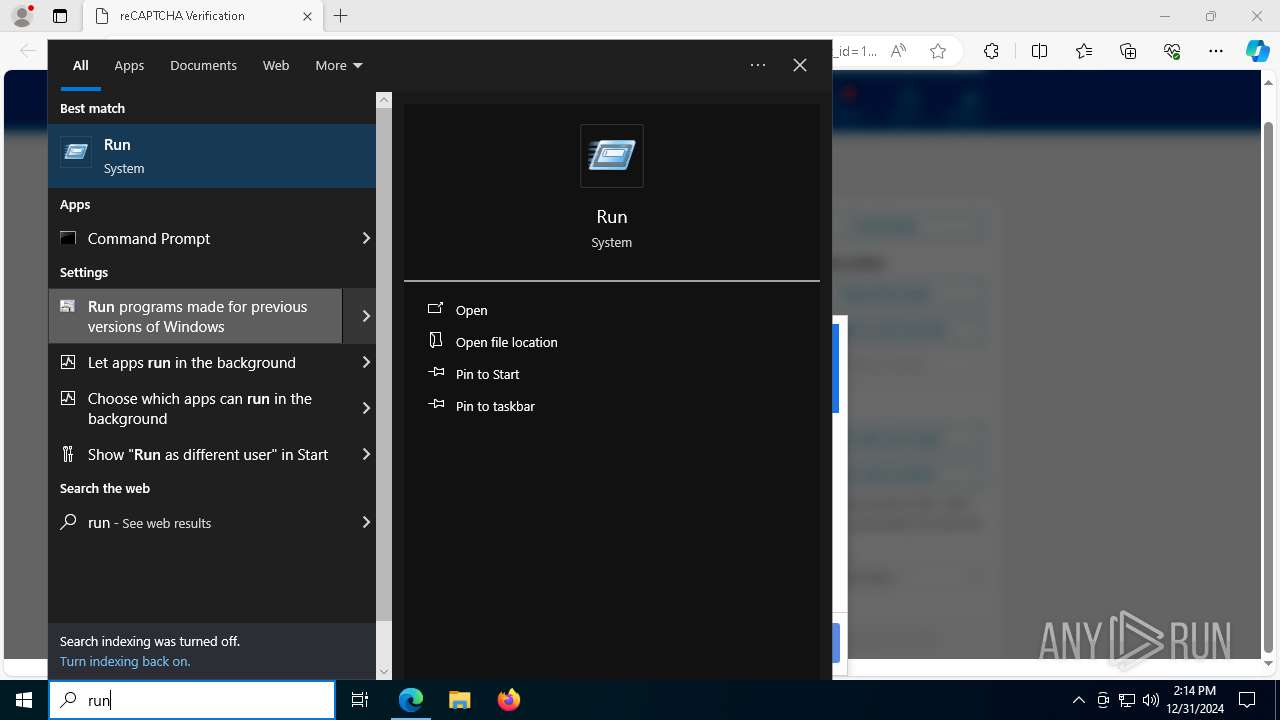
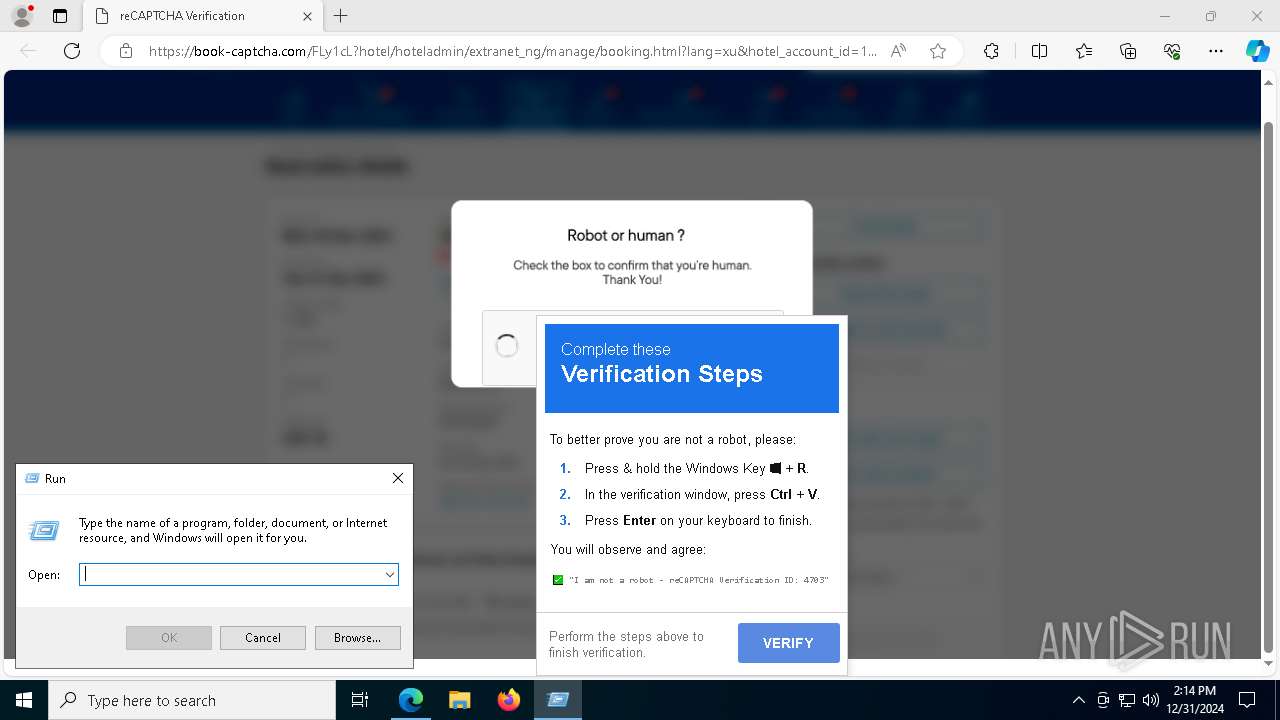
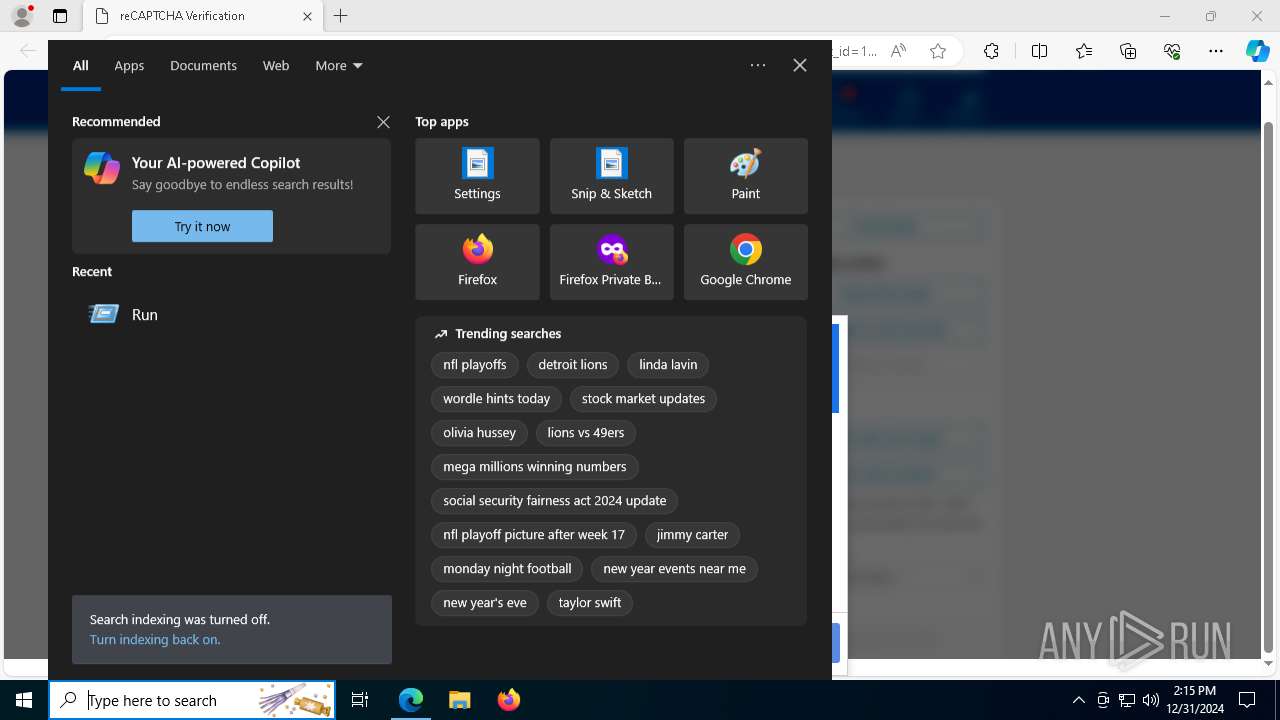
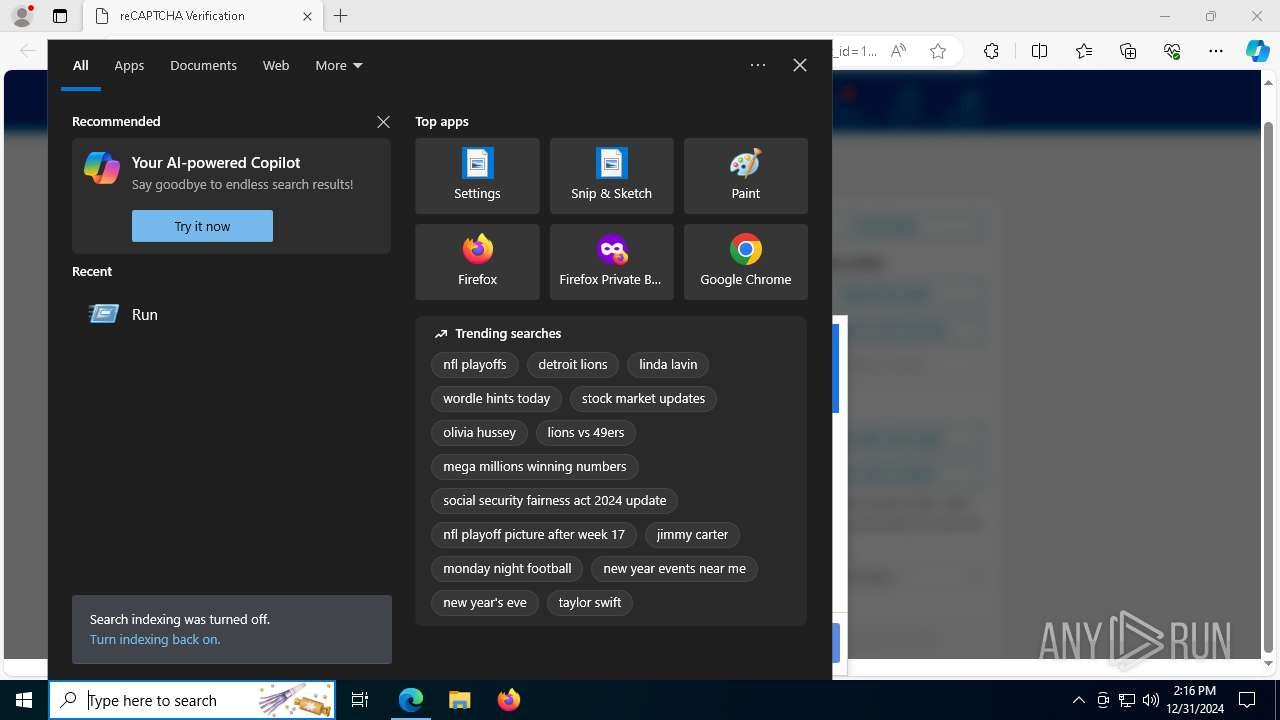
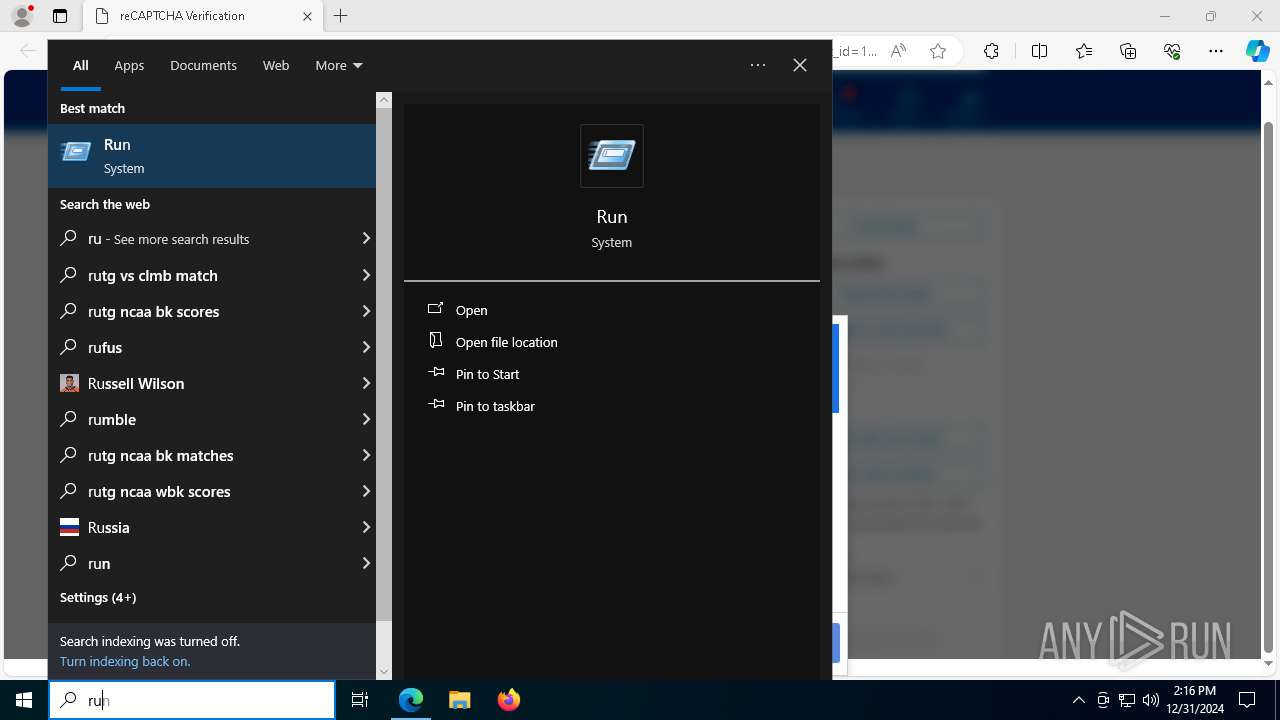
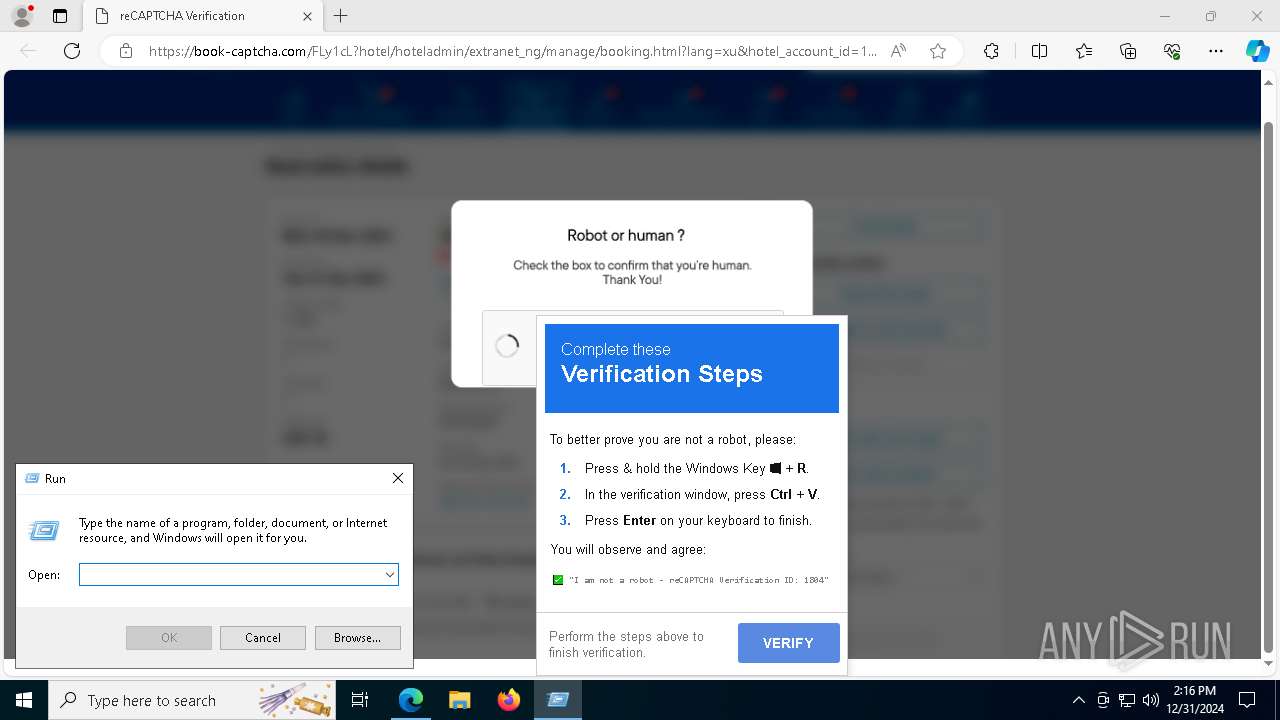
Manual execution by a user
- mshta.exe (PID: 7292)
- mshta.exe (PID: 628)
Reads the machine GUID from the registry
- SearchApp.exe (PID: 5064)
- RegSvcs.exe (PID: 7076)
Checks proxy server information
- mshta.exe (PID: 7292)
- powershell.exe (PID: 7416)
- mshta.exe (PID: 628)
Process checks computer location settings
- SearchApp.exe (PID: 5064)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 7616)
- powershell.exe (PID: 7532)
- powershell.exe (PID: 6880)
- powershell.exe (PID: 7416)
- powershell.exe (PID: 7944)
- powershell.exe (PID: 7768)
The process uses the downloaded file
- mshta.exe (PID: 7292)
- mshta.exe (PID: 628)
Application launched itself
- msedge.exe (PID: 2940)
The sample compiled with english language support
- msedge.exe (PID: 5160)
Executable content was dropped or overwritten
- msedge.exe (PID: 5160)
Reads Internet Explorer settings
- mshta.exe (PID: 628)
Disables trace logs
- powershell.exe (PID: 7416)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
194
Monitored processes
64
Malicious processes
11
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
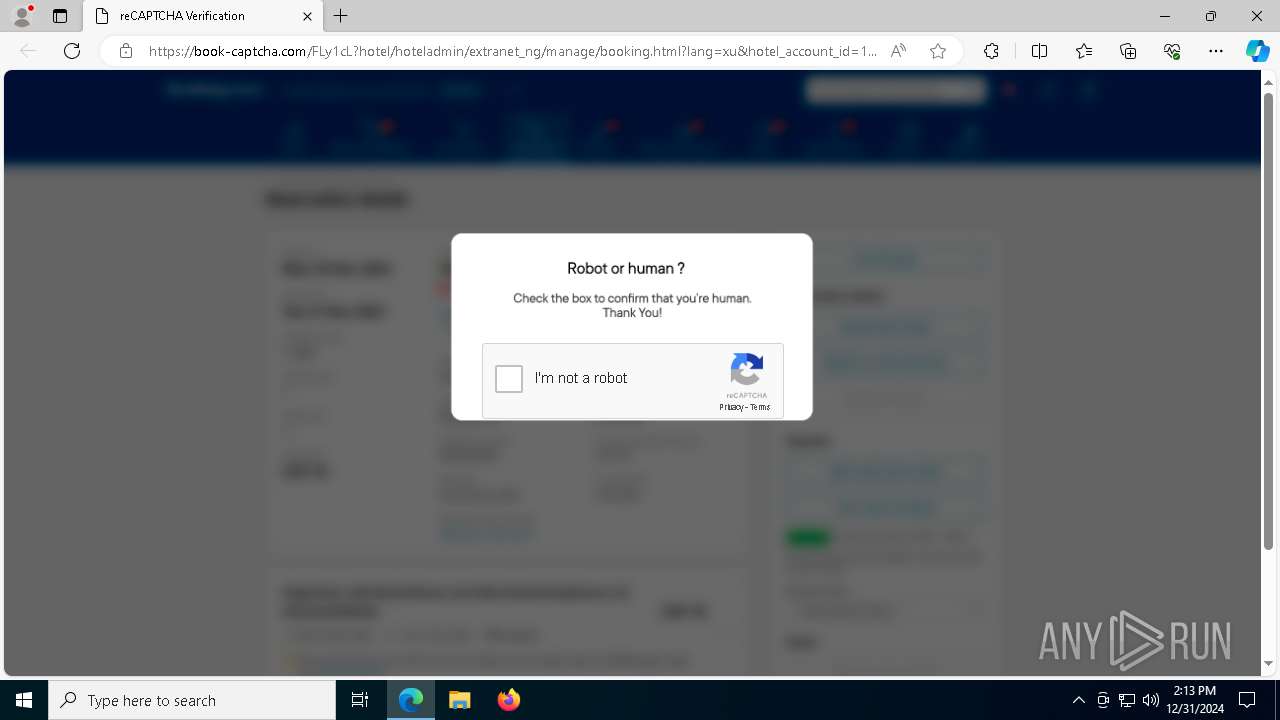
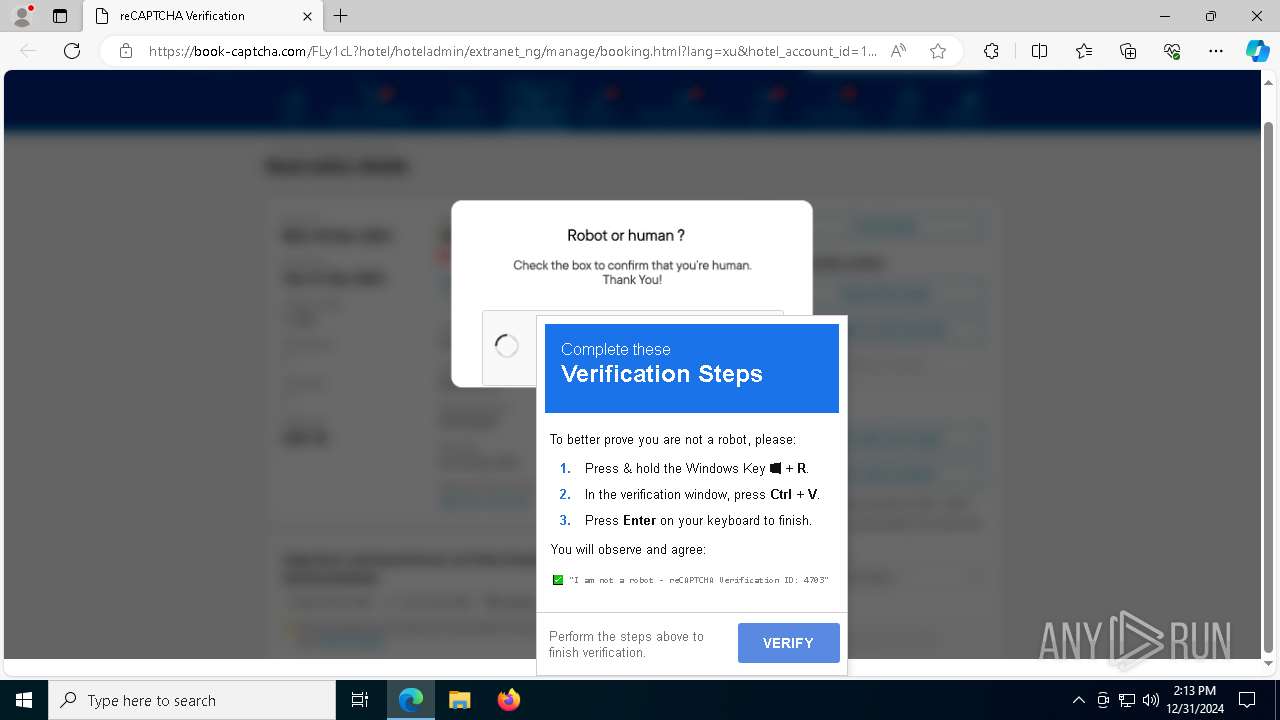
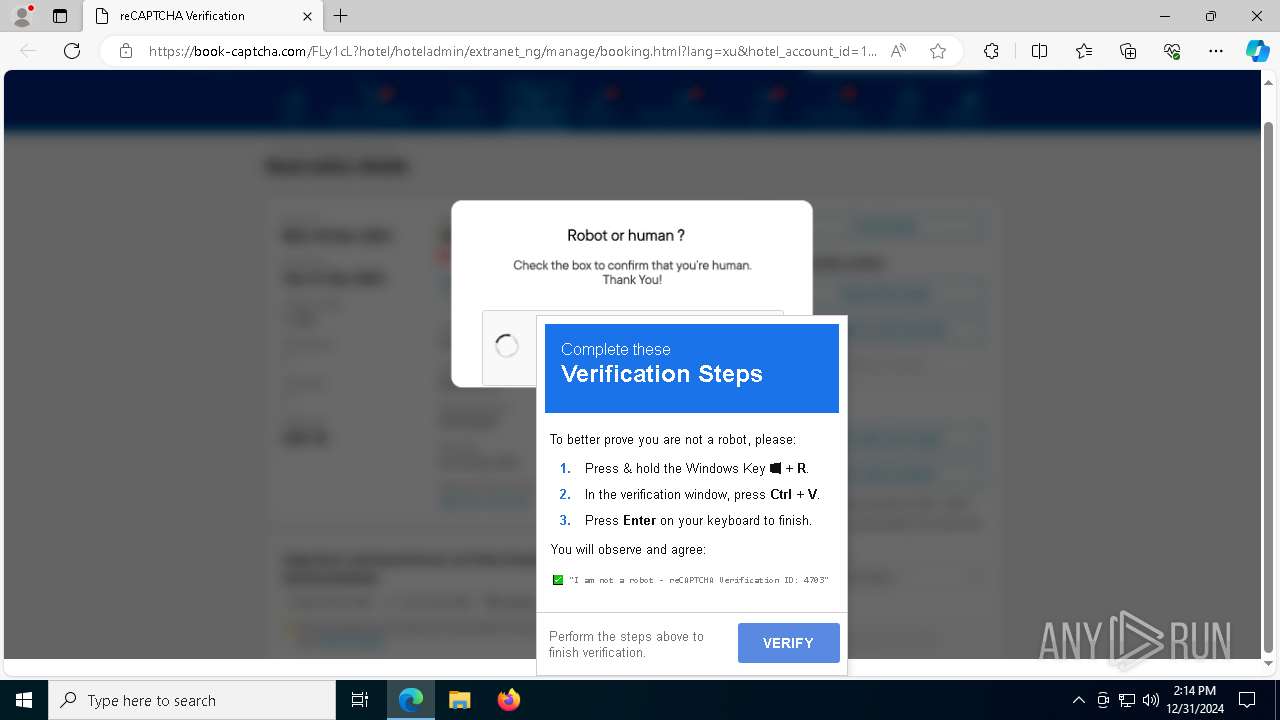
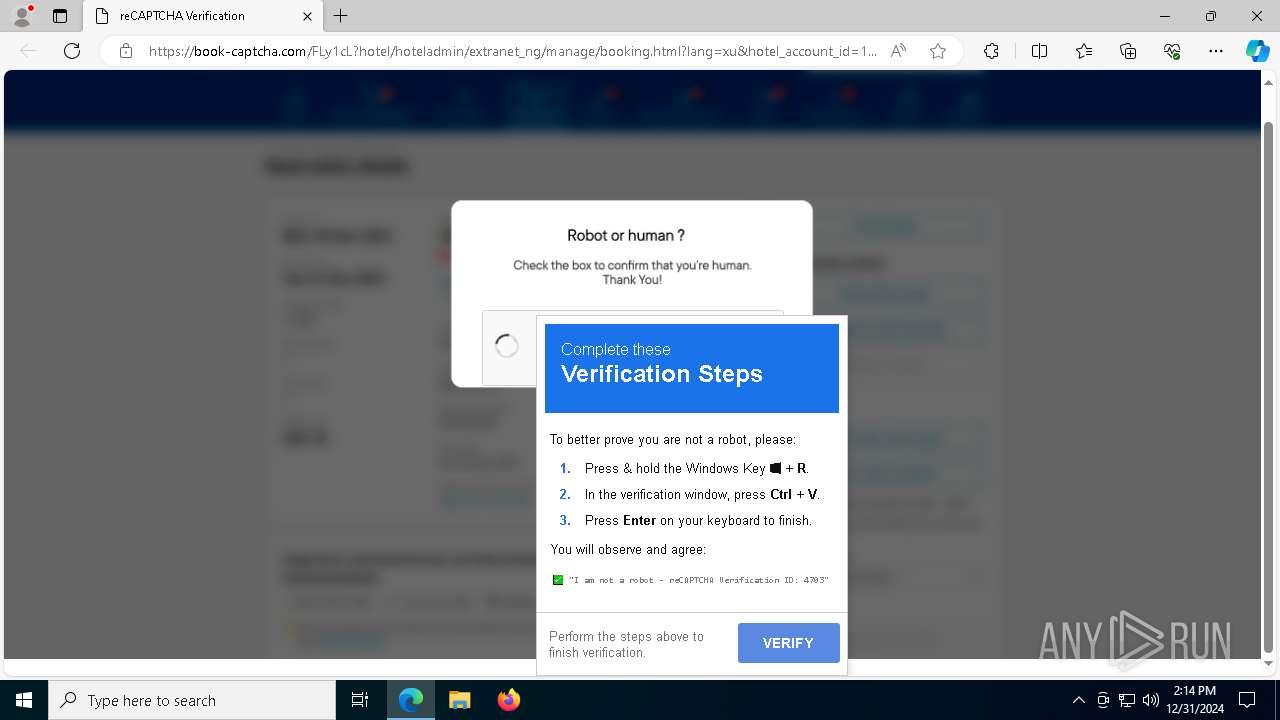
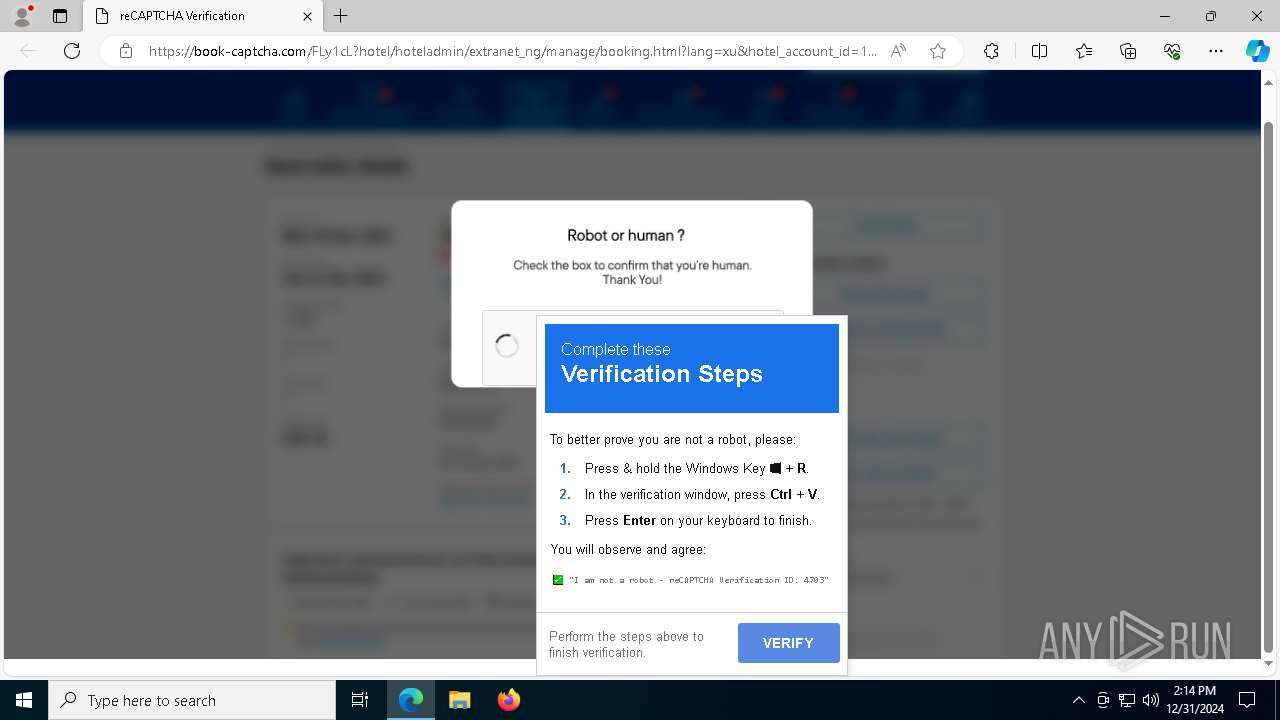
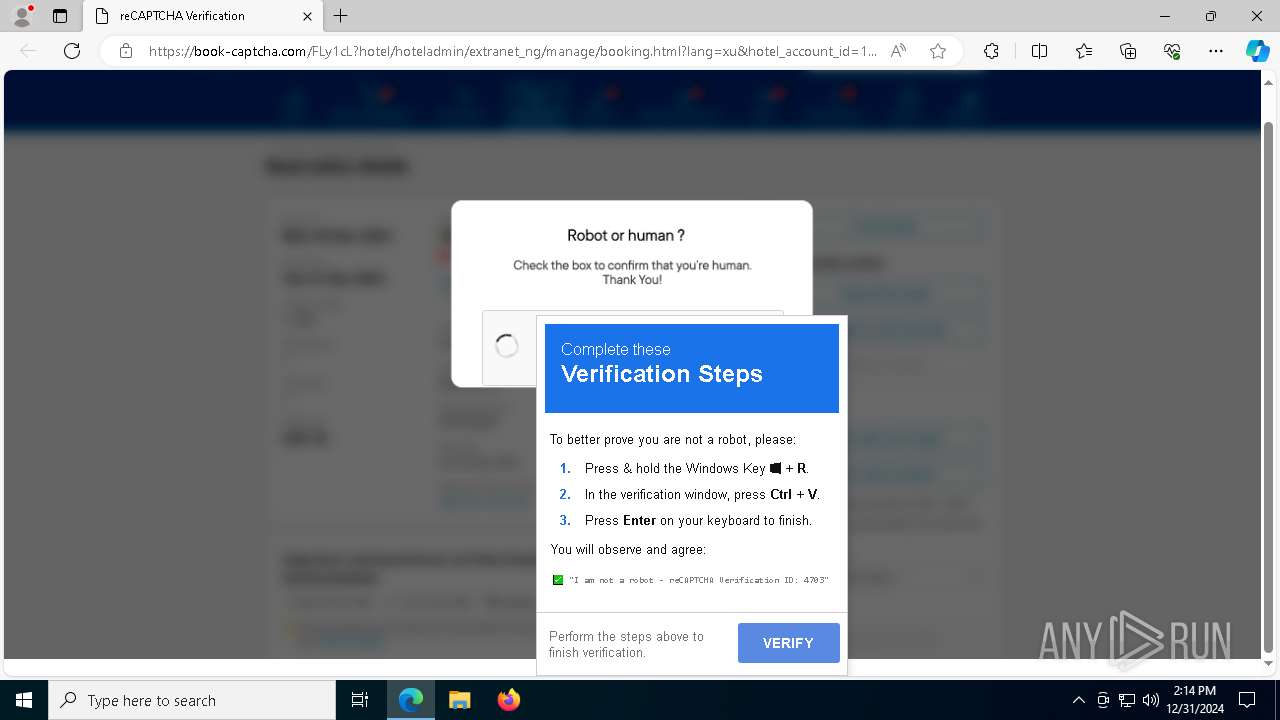
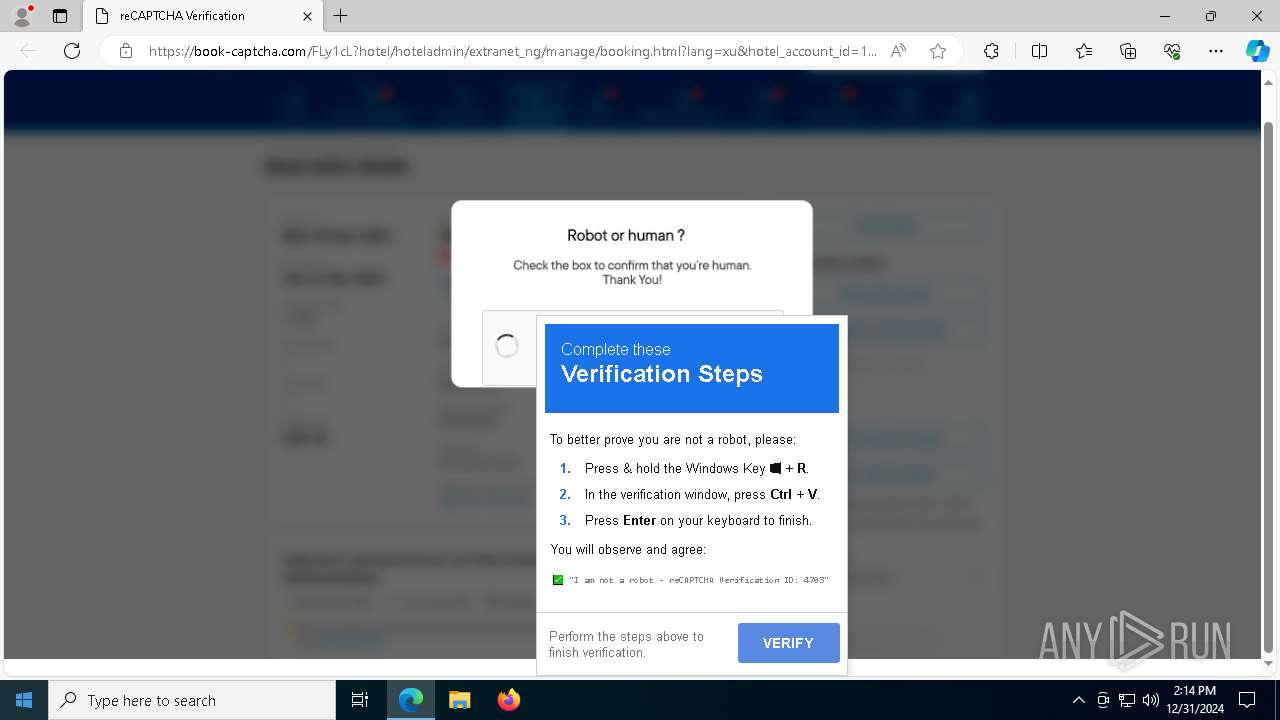
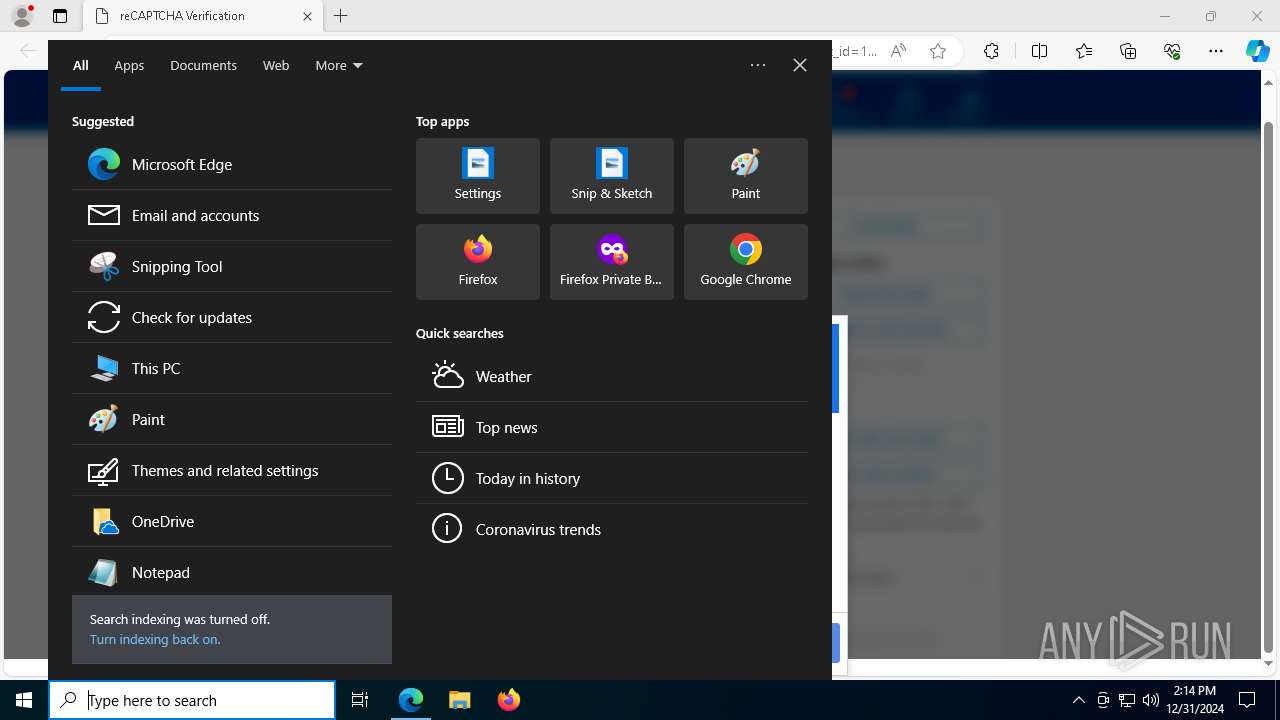
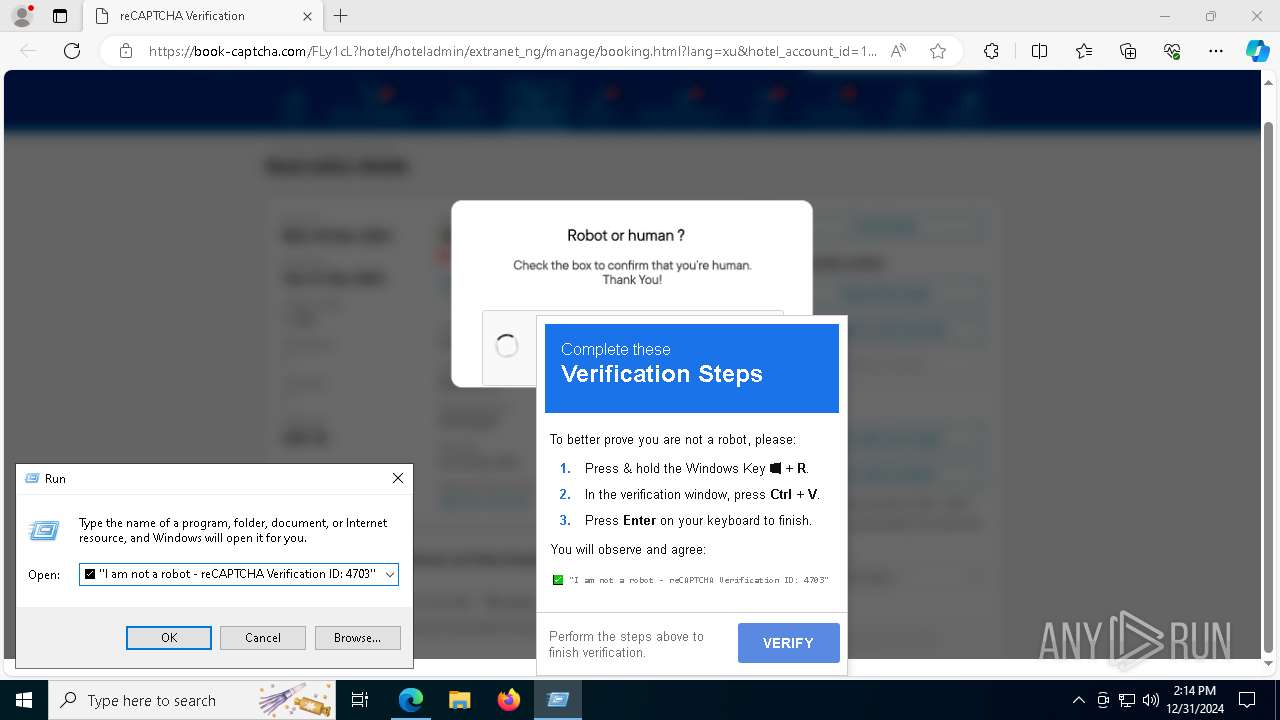
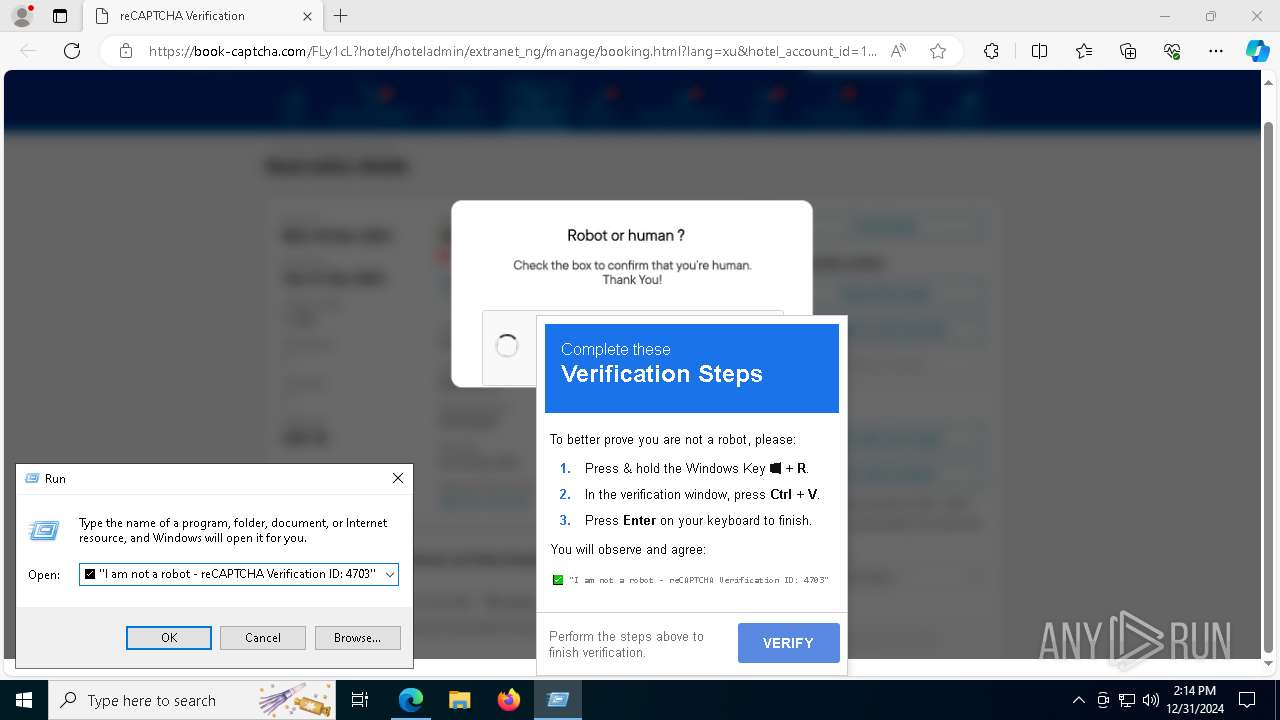
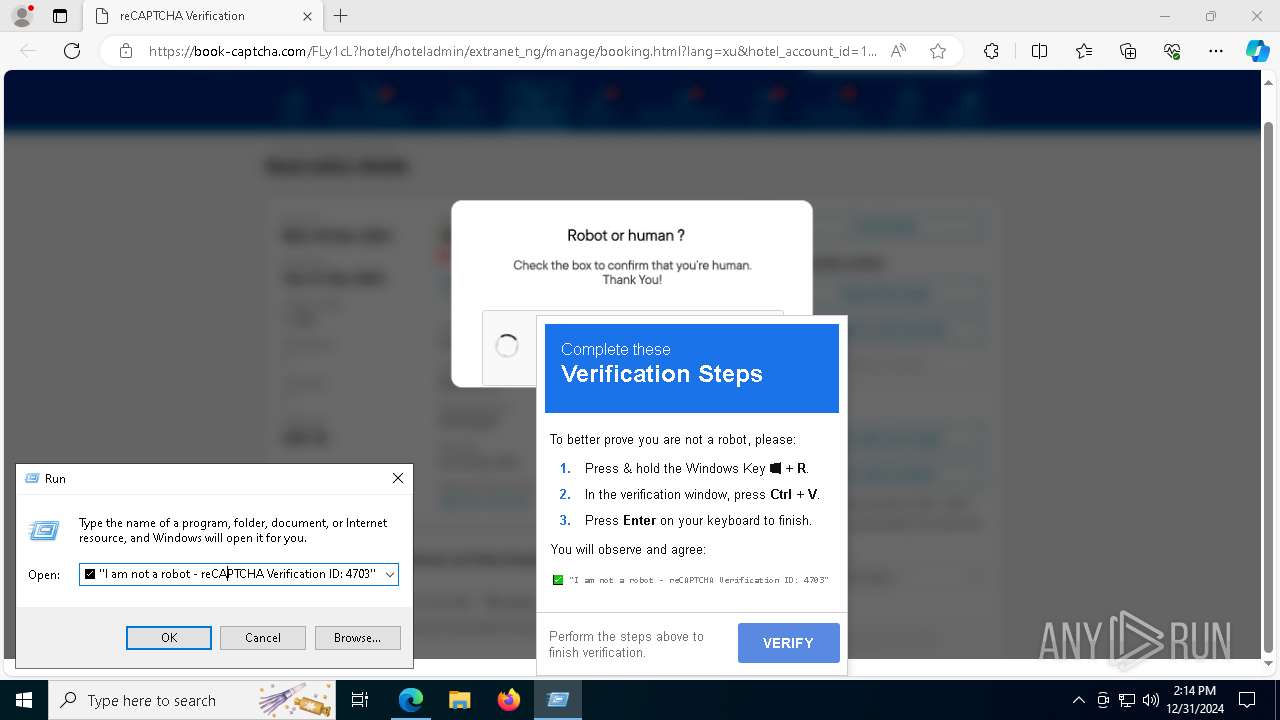
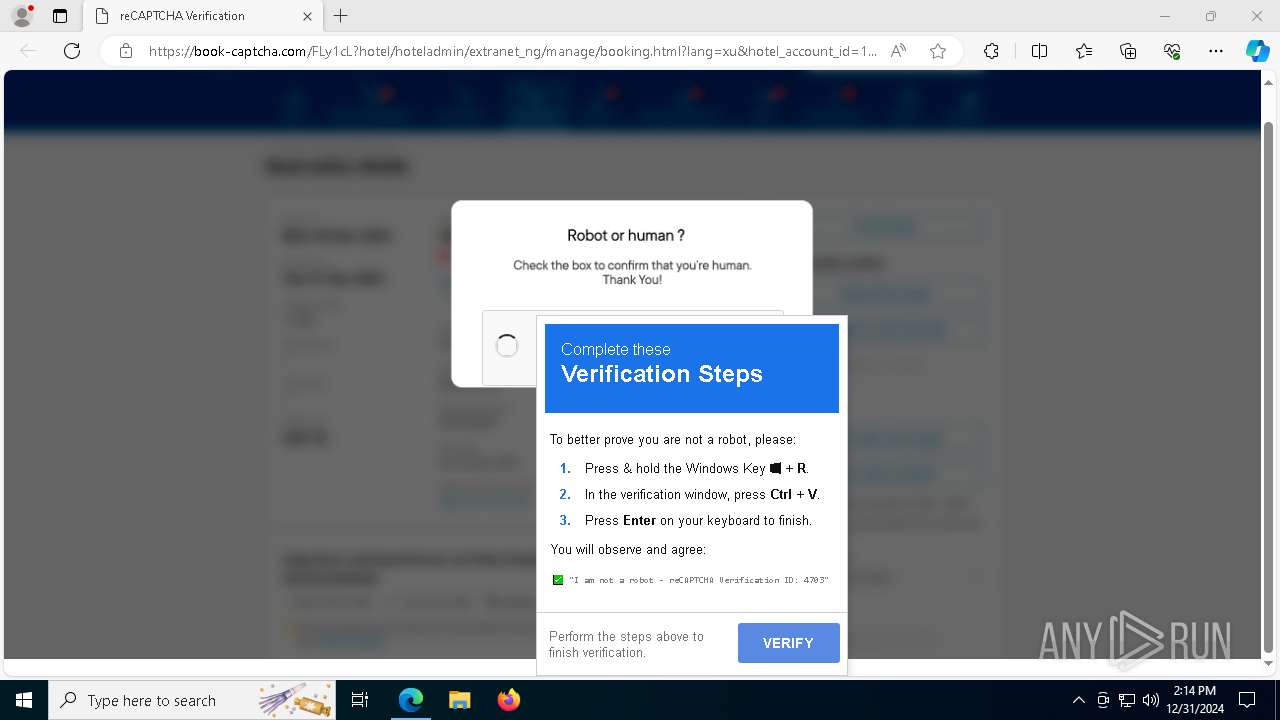
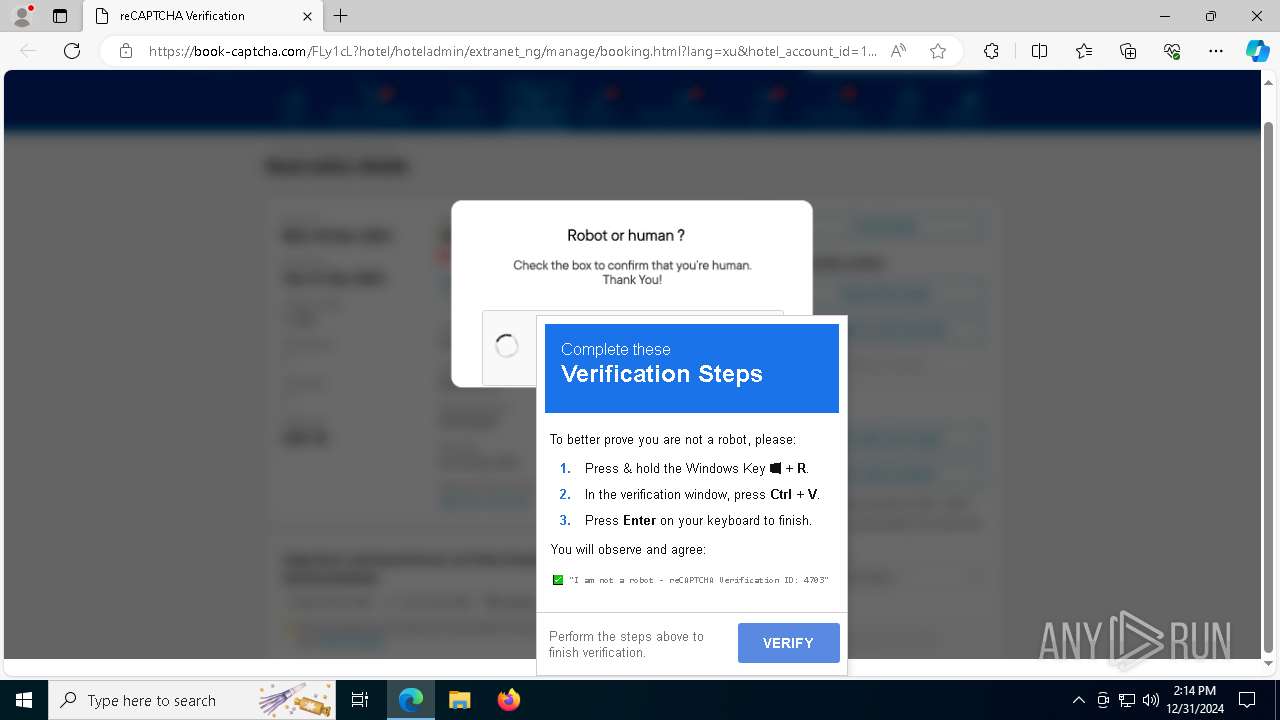
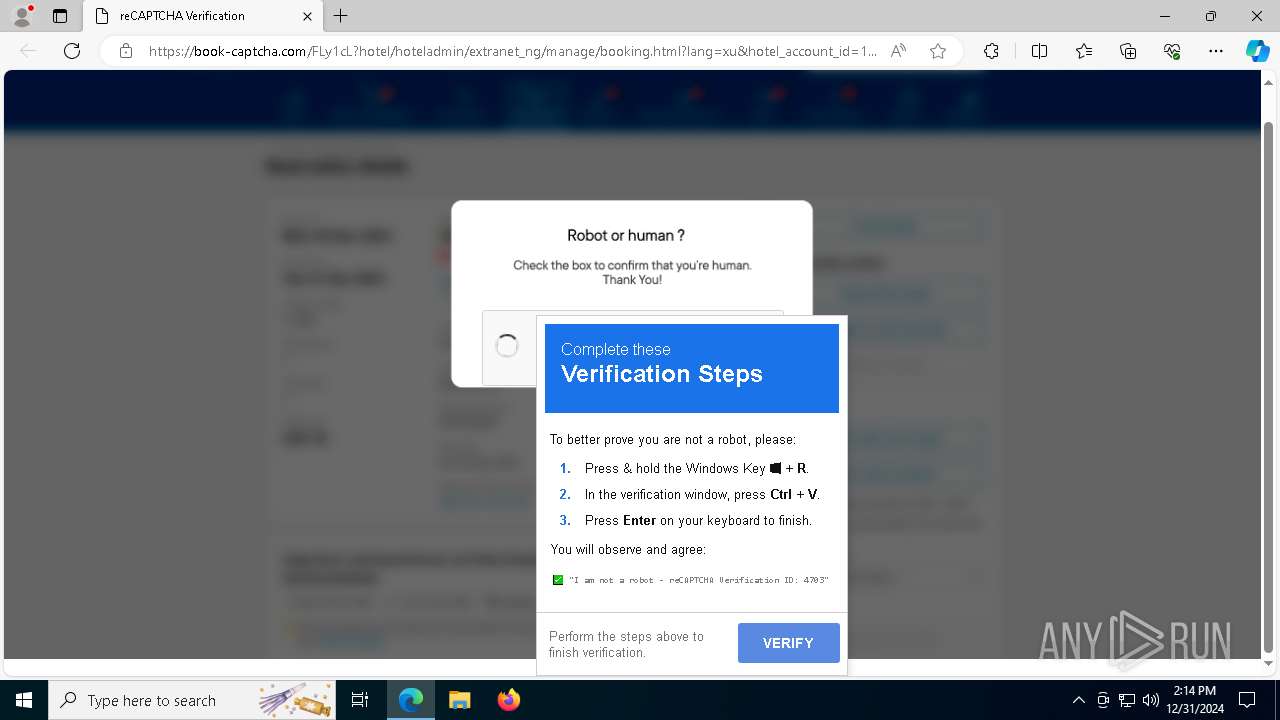
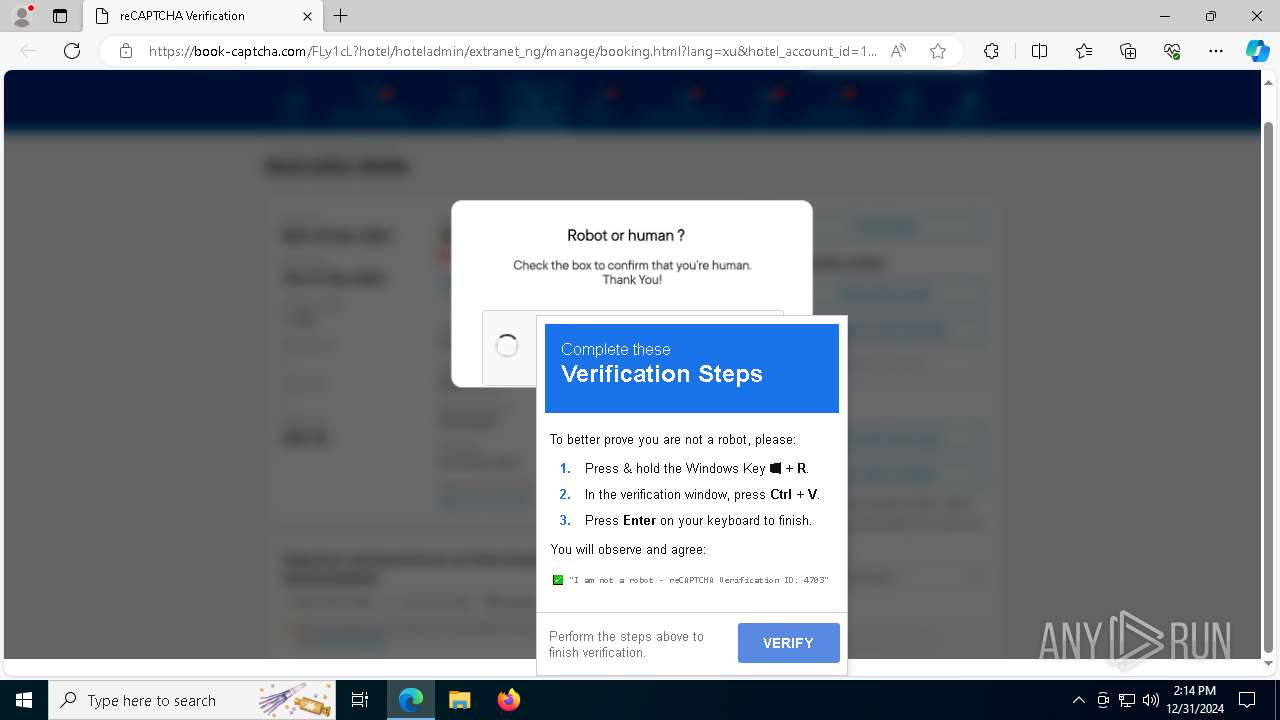
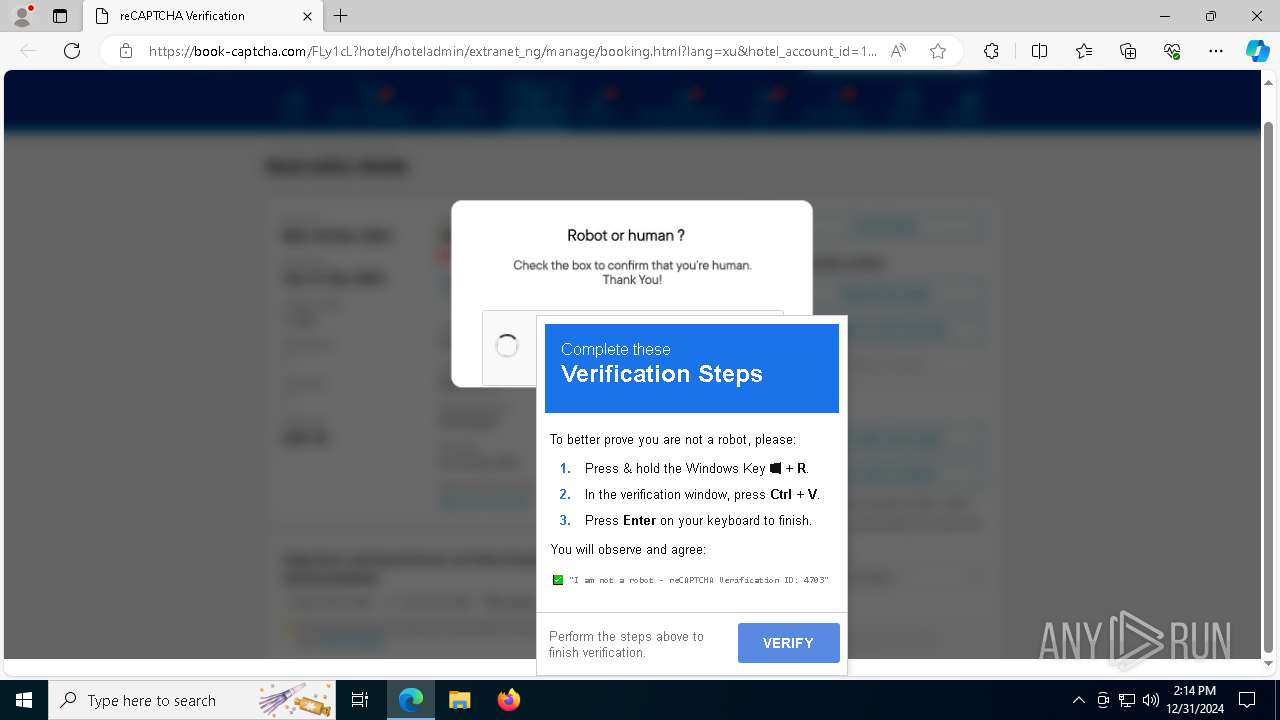
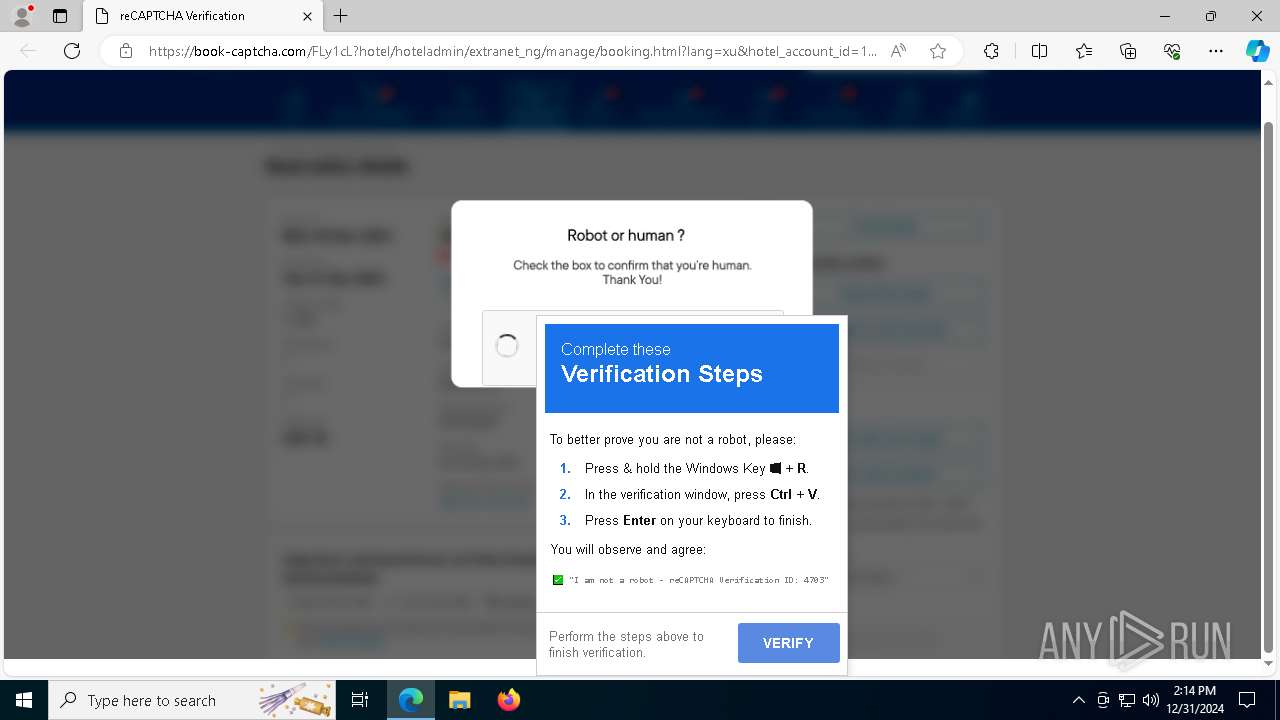
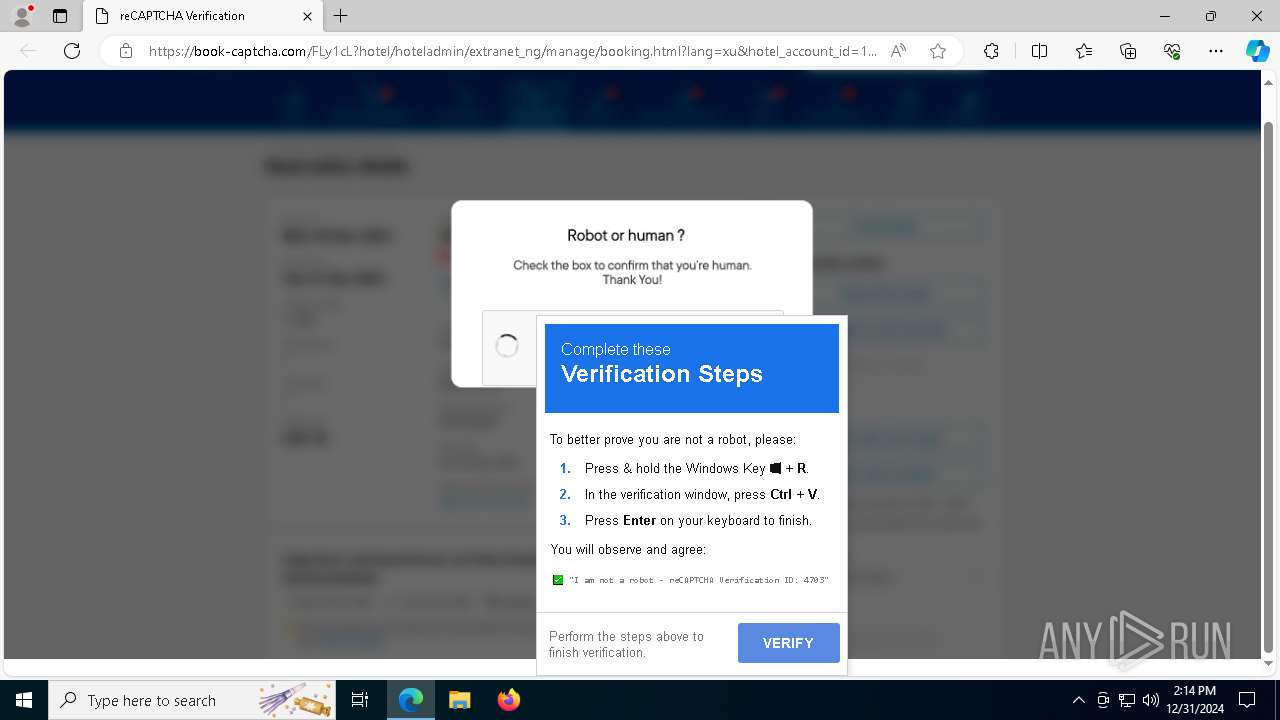
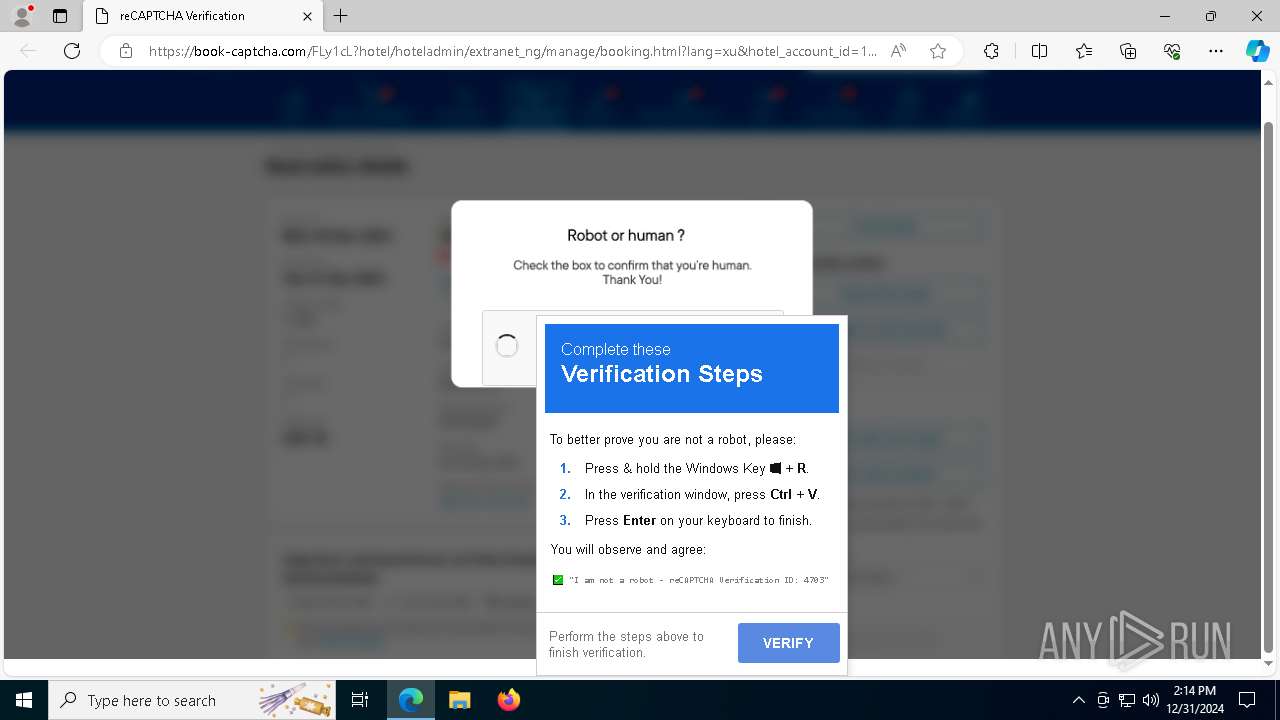
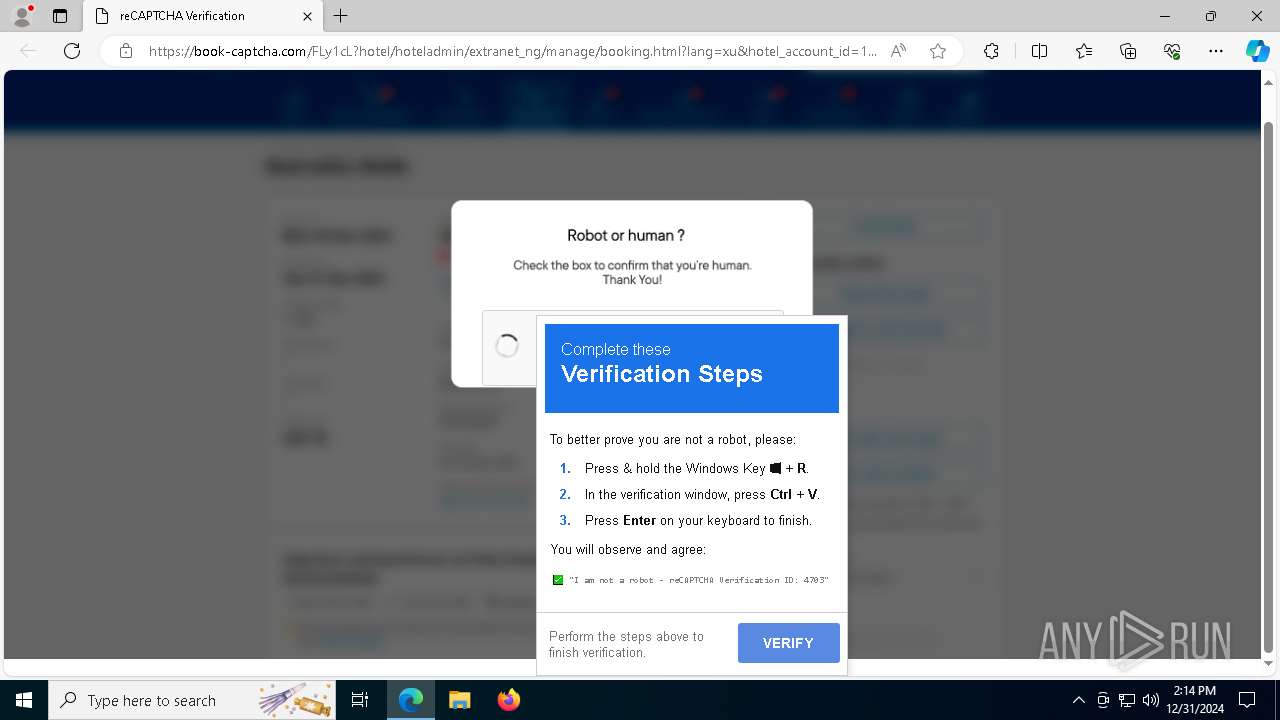
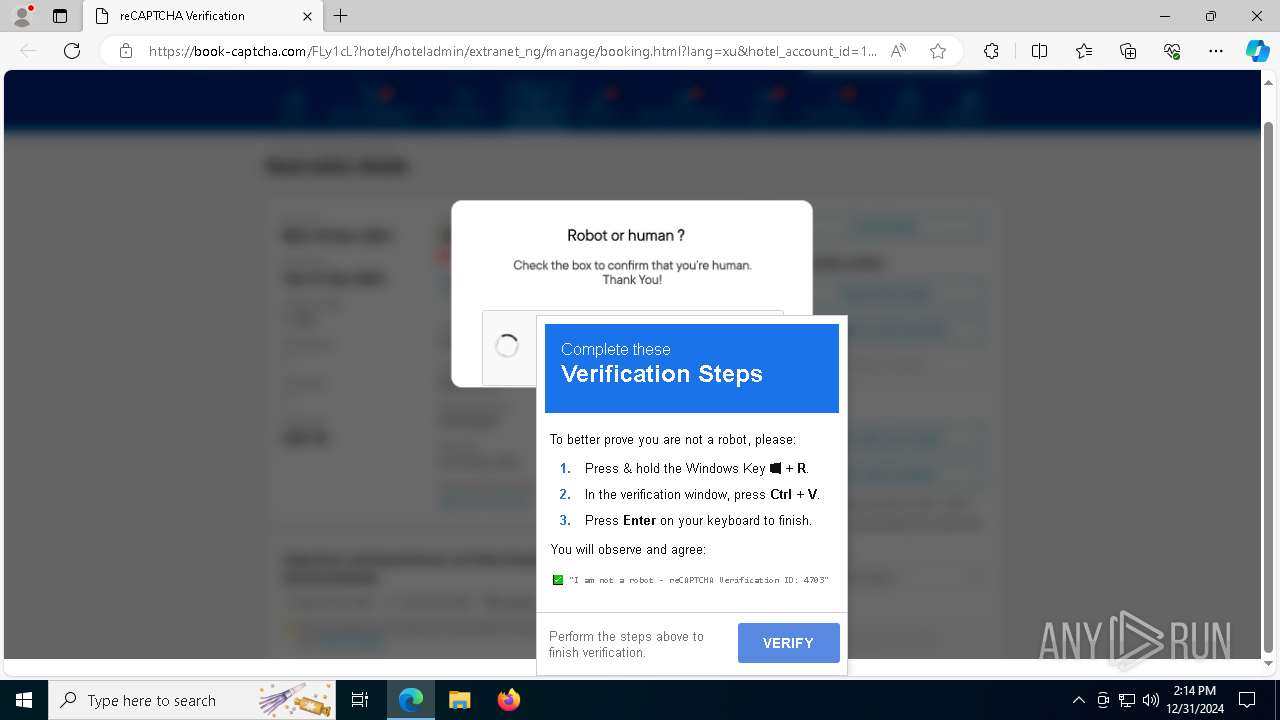
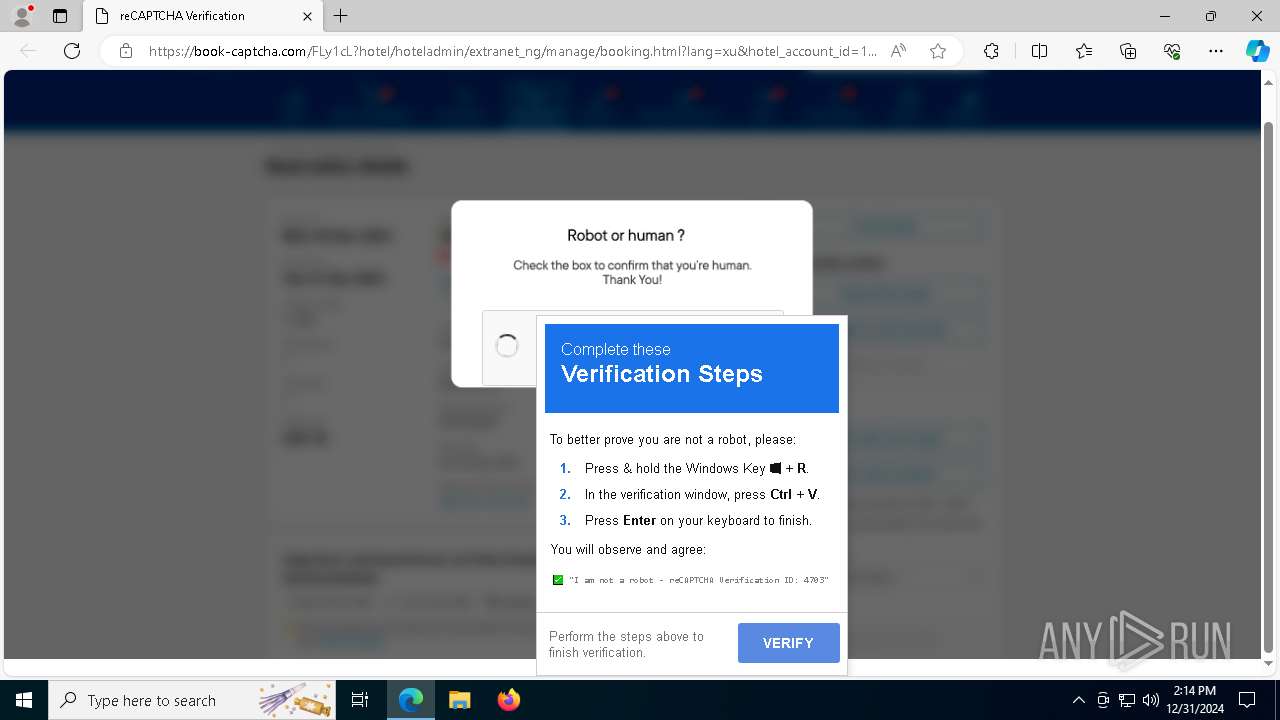
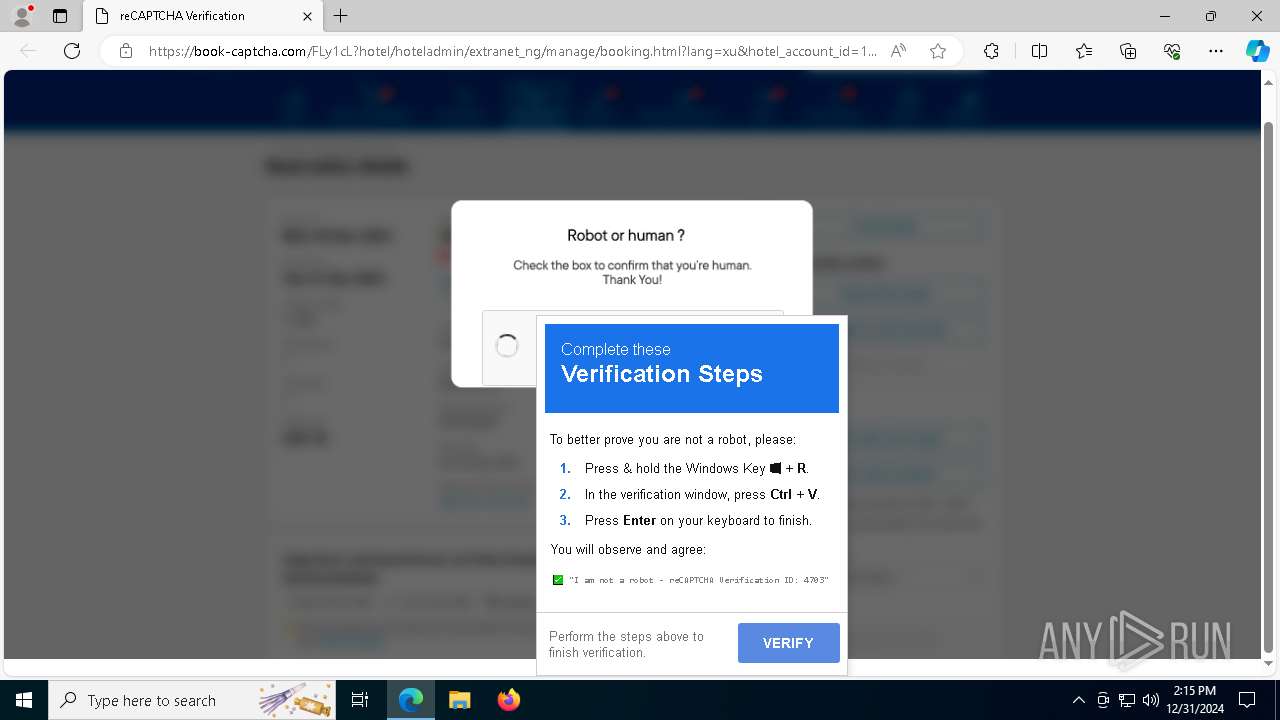
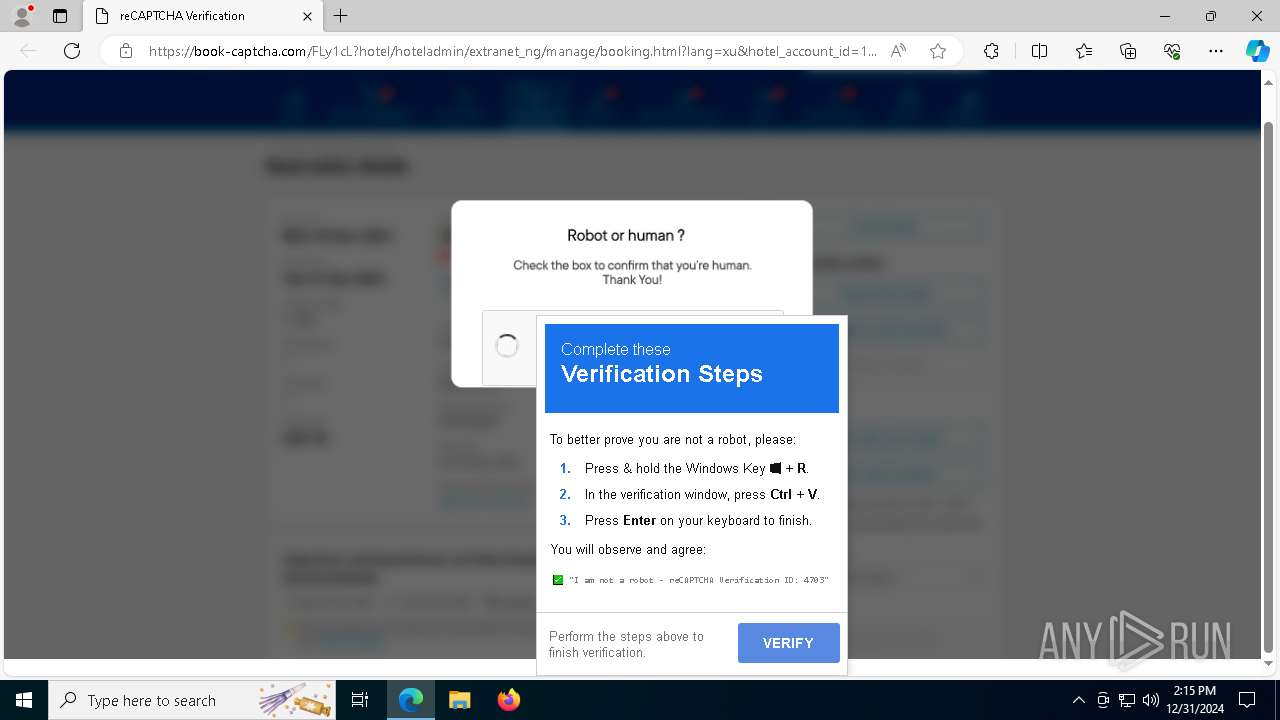
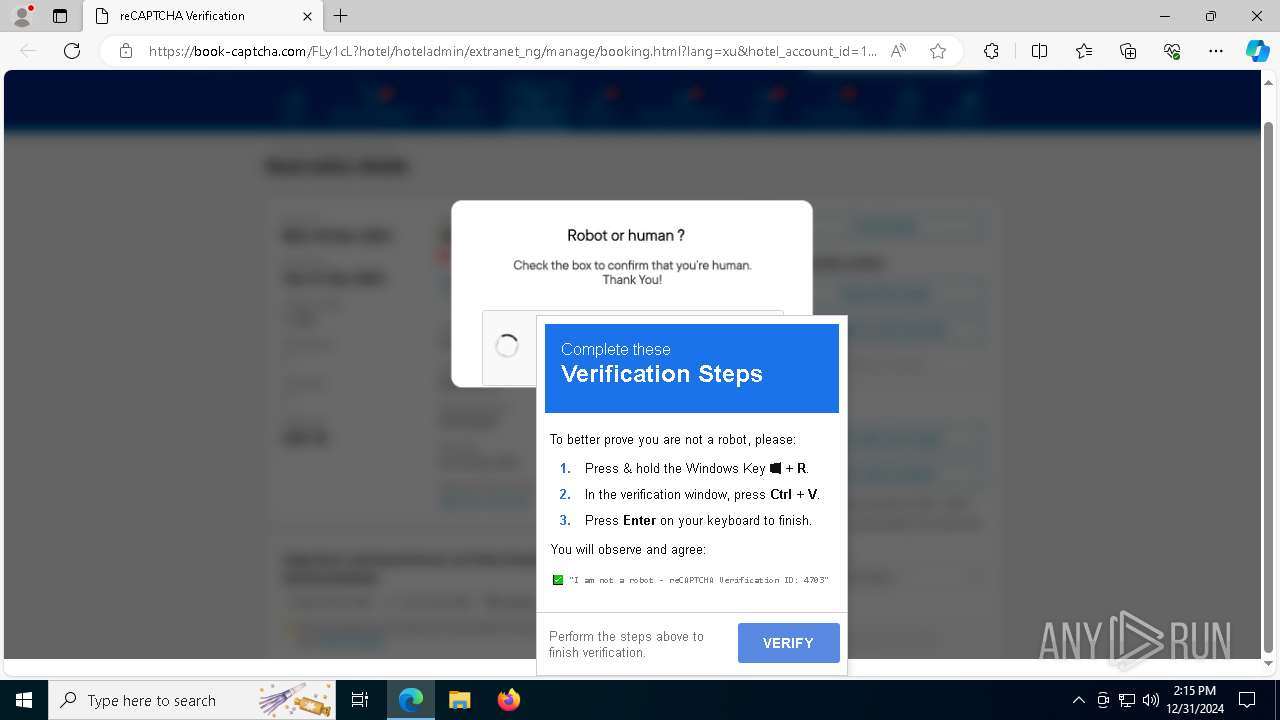
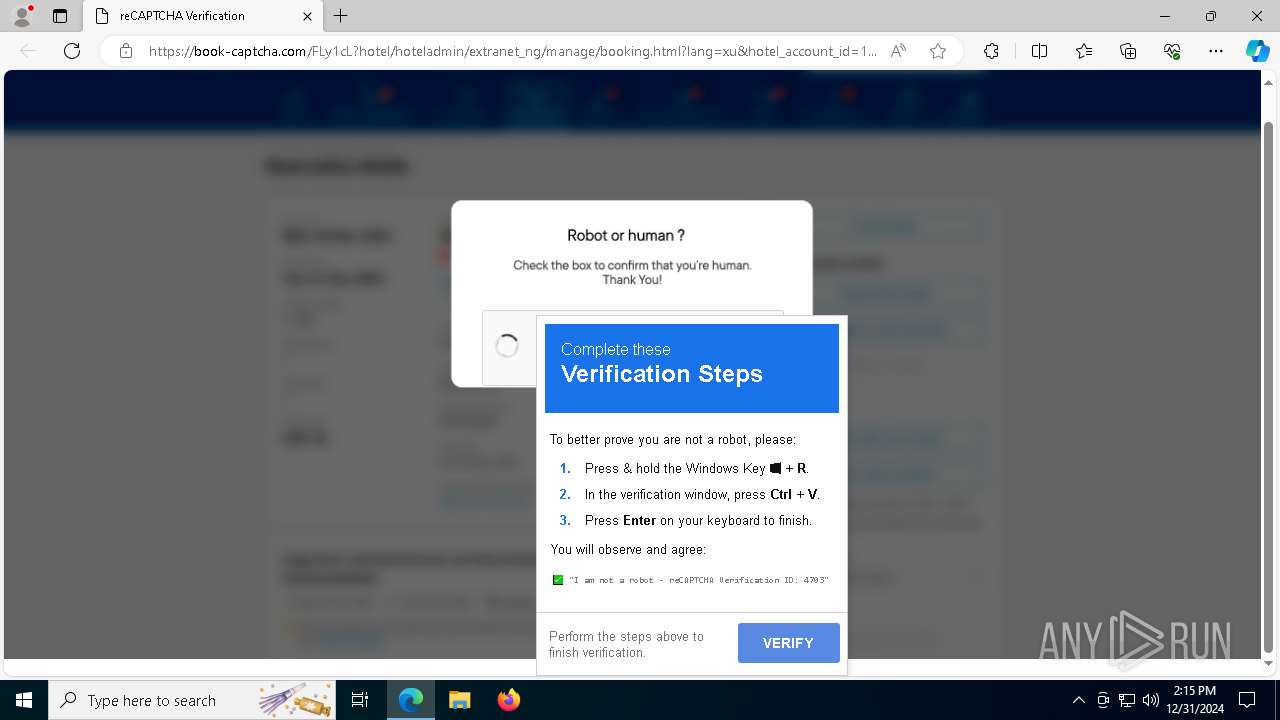
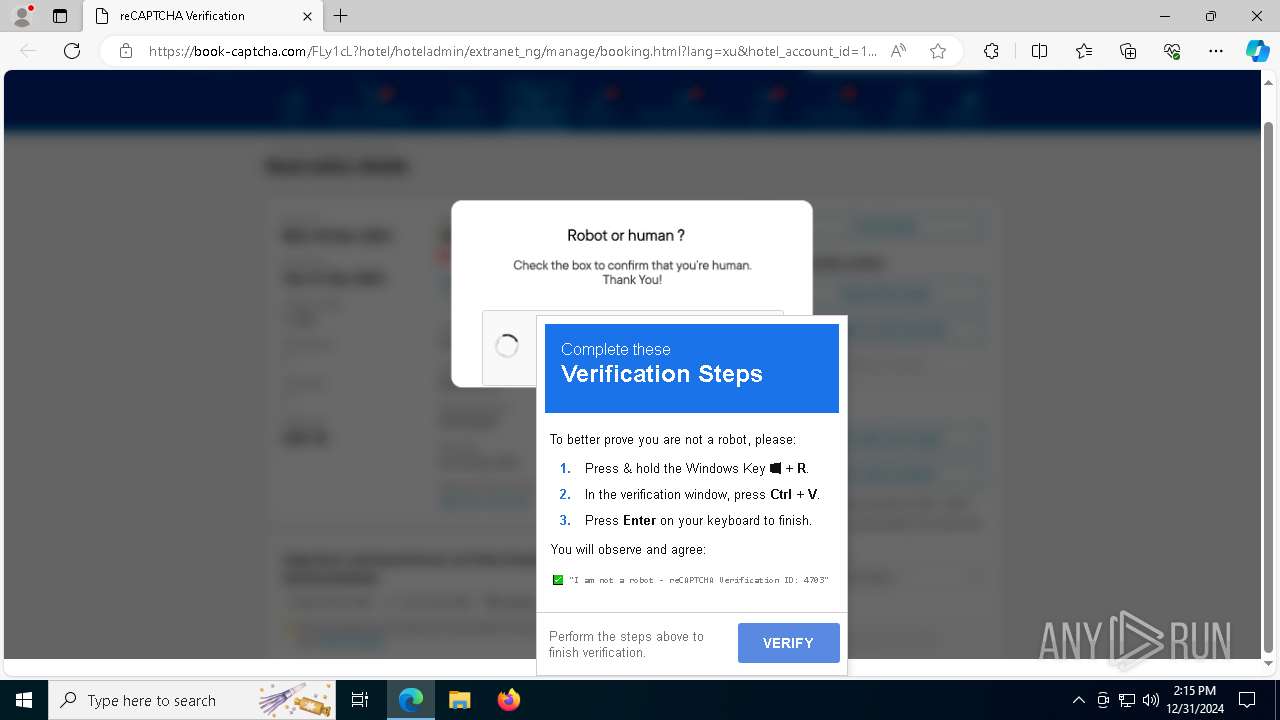
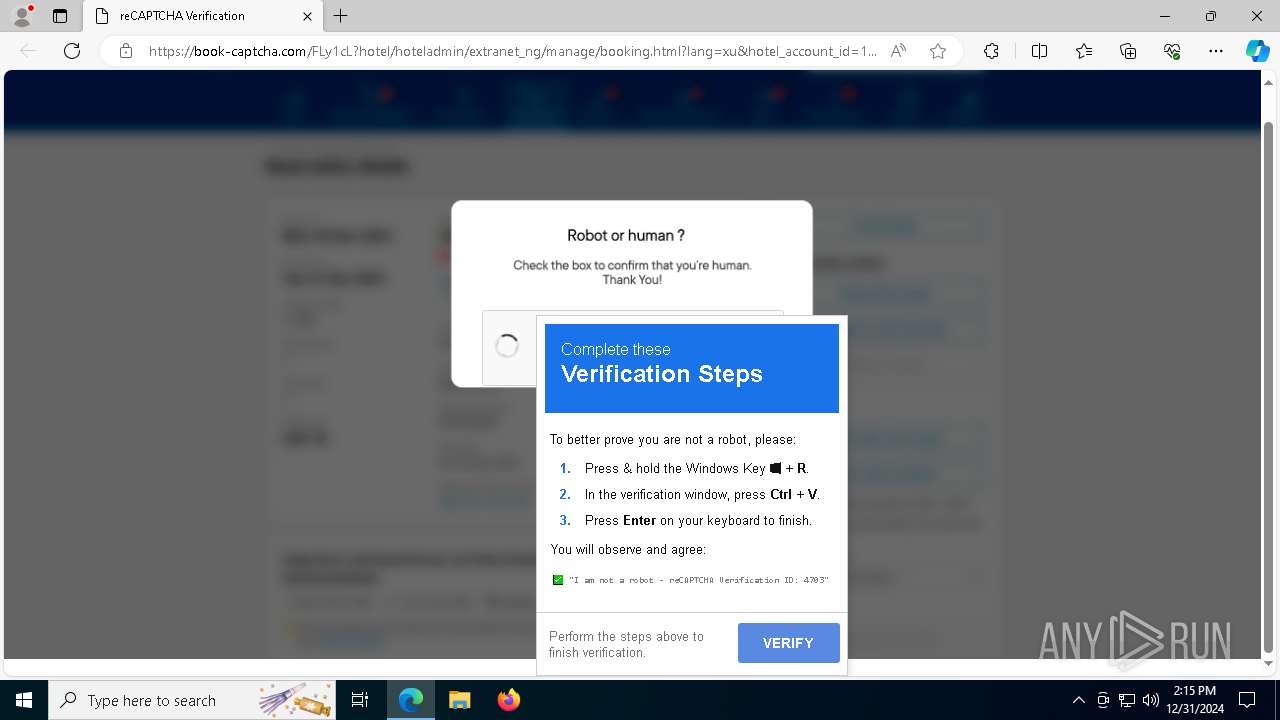
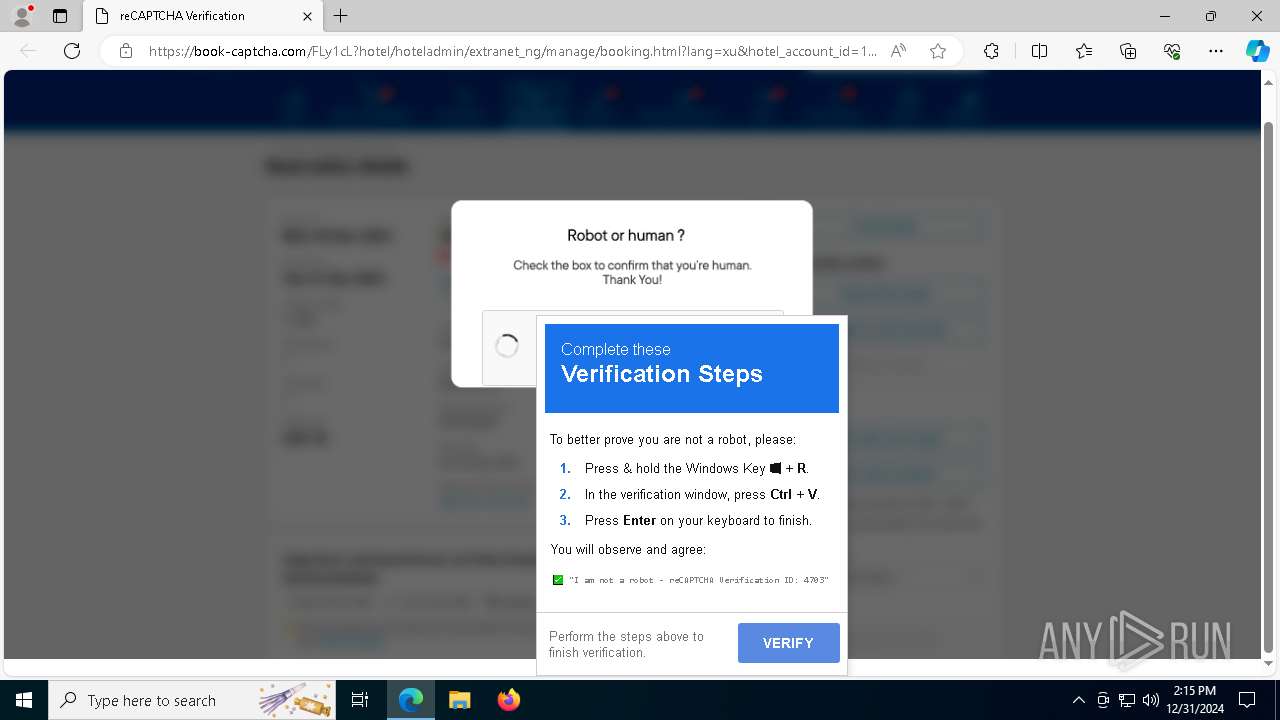
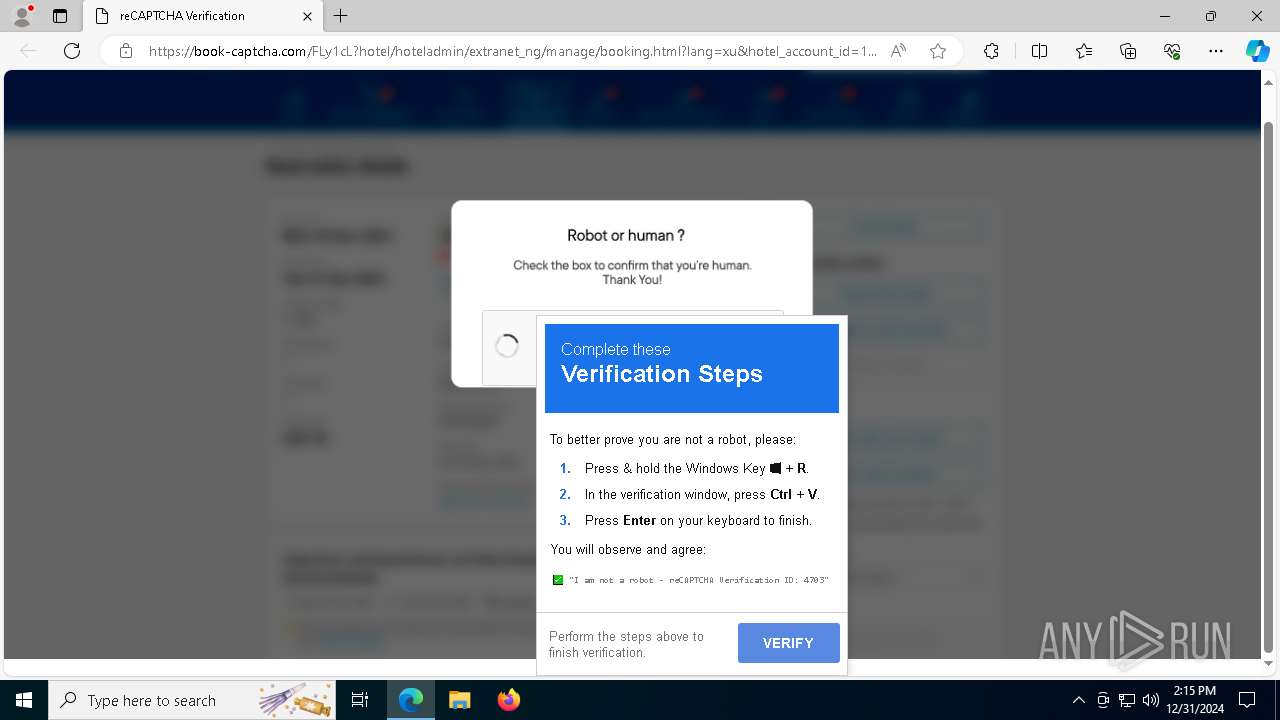
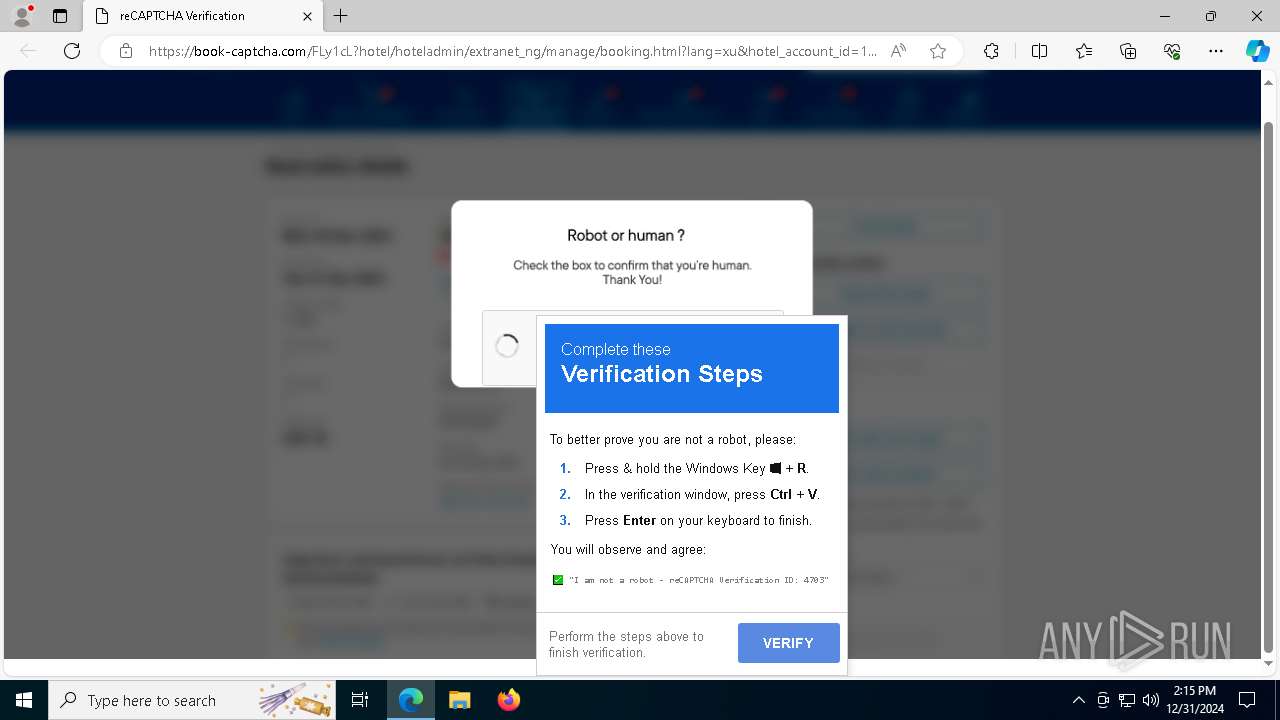
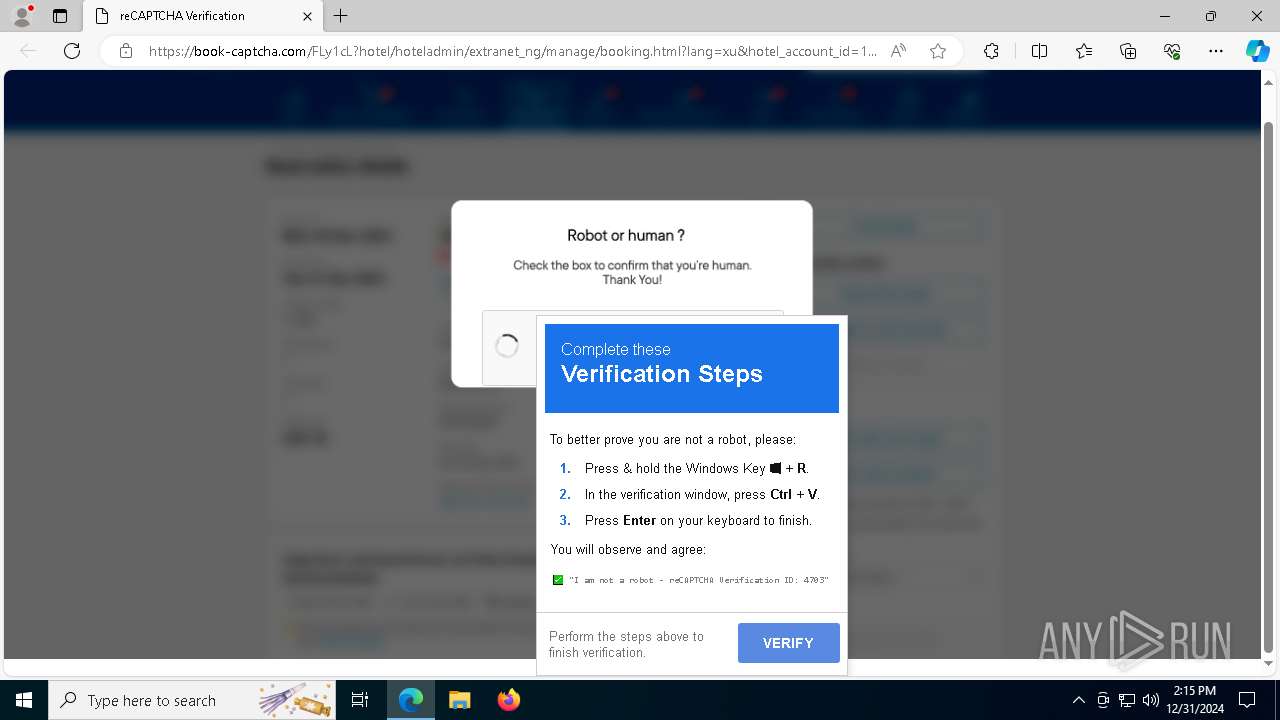
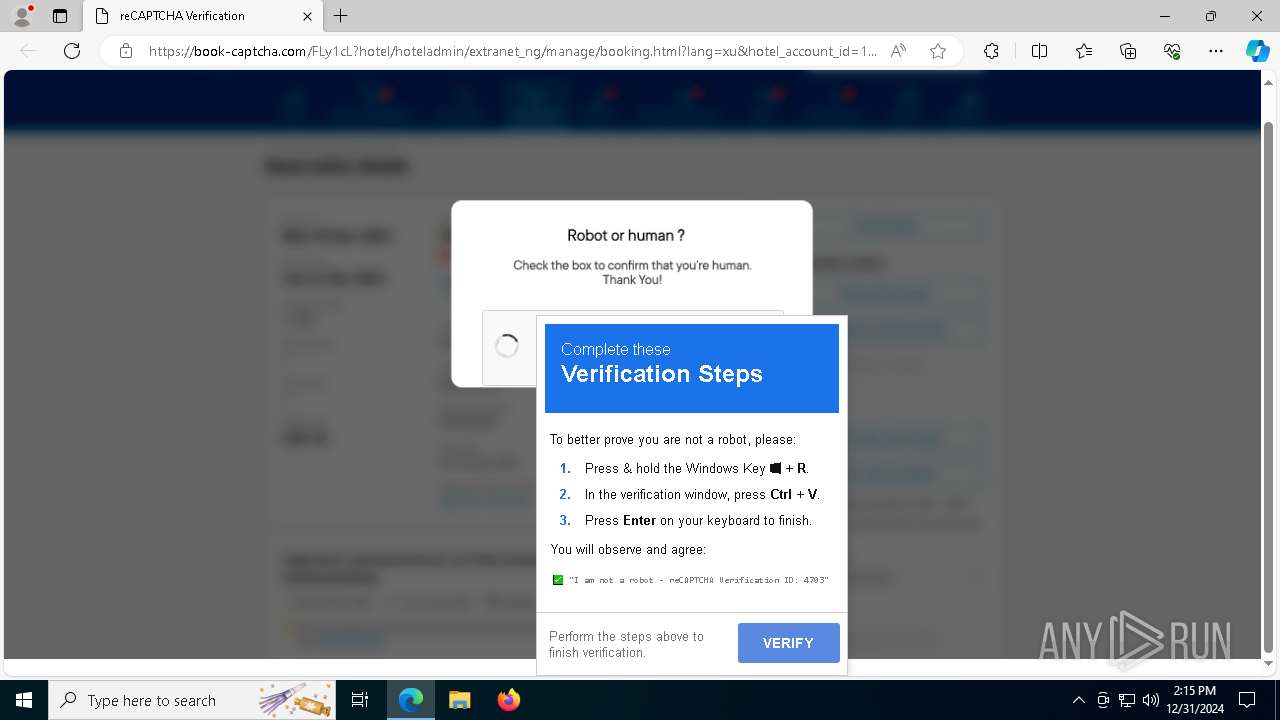
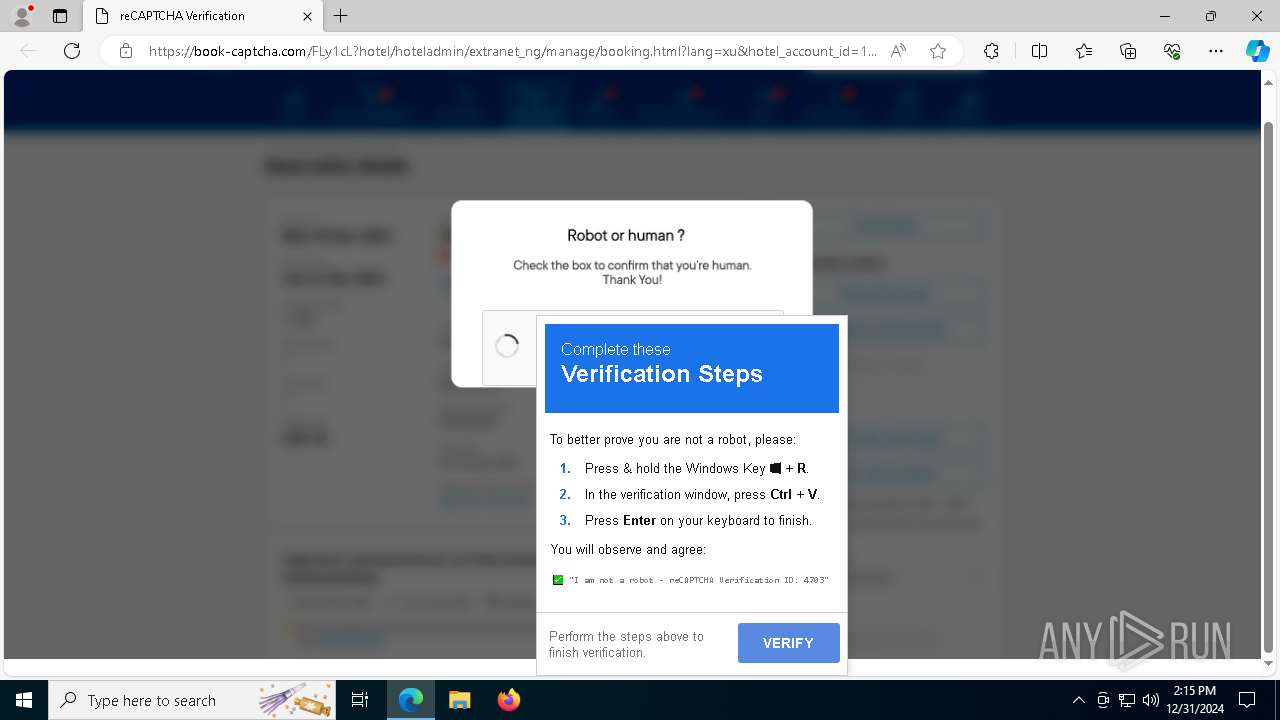
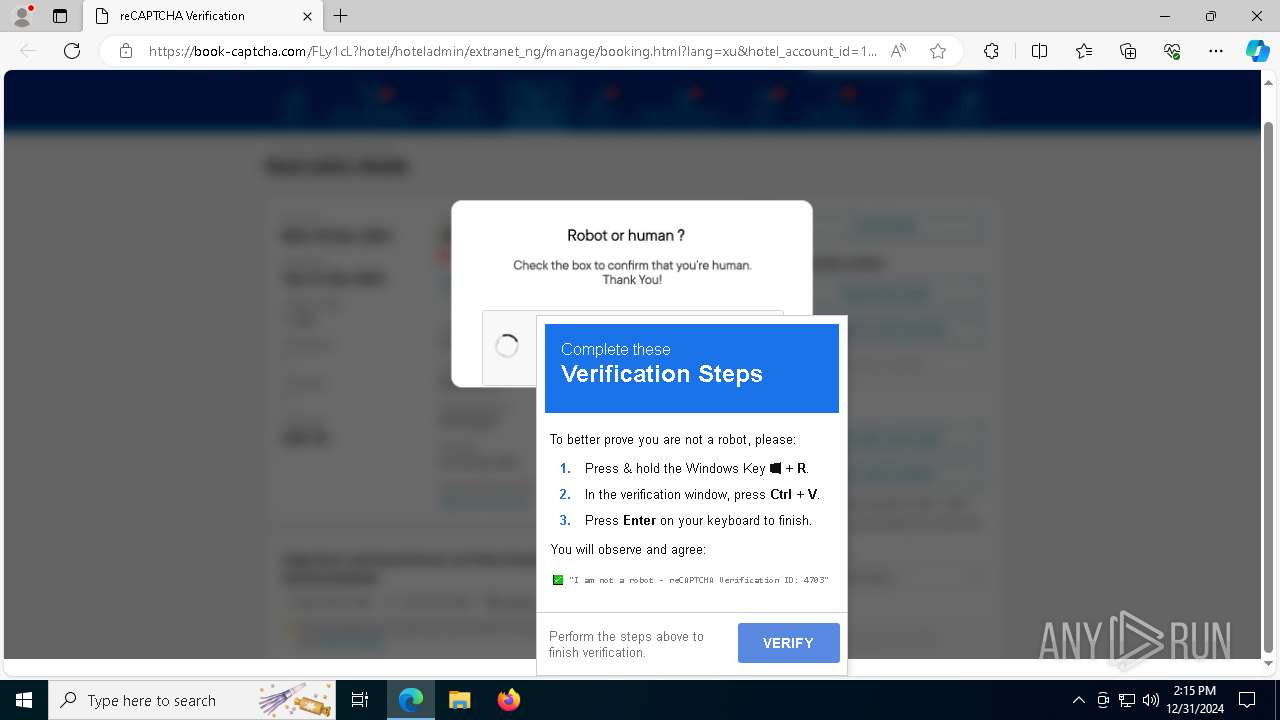
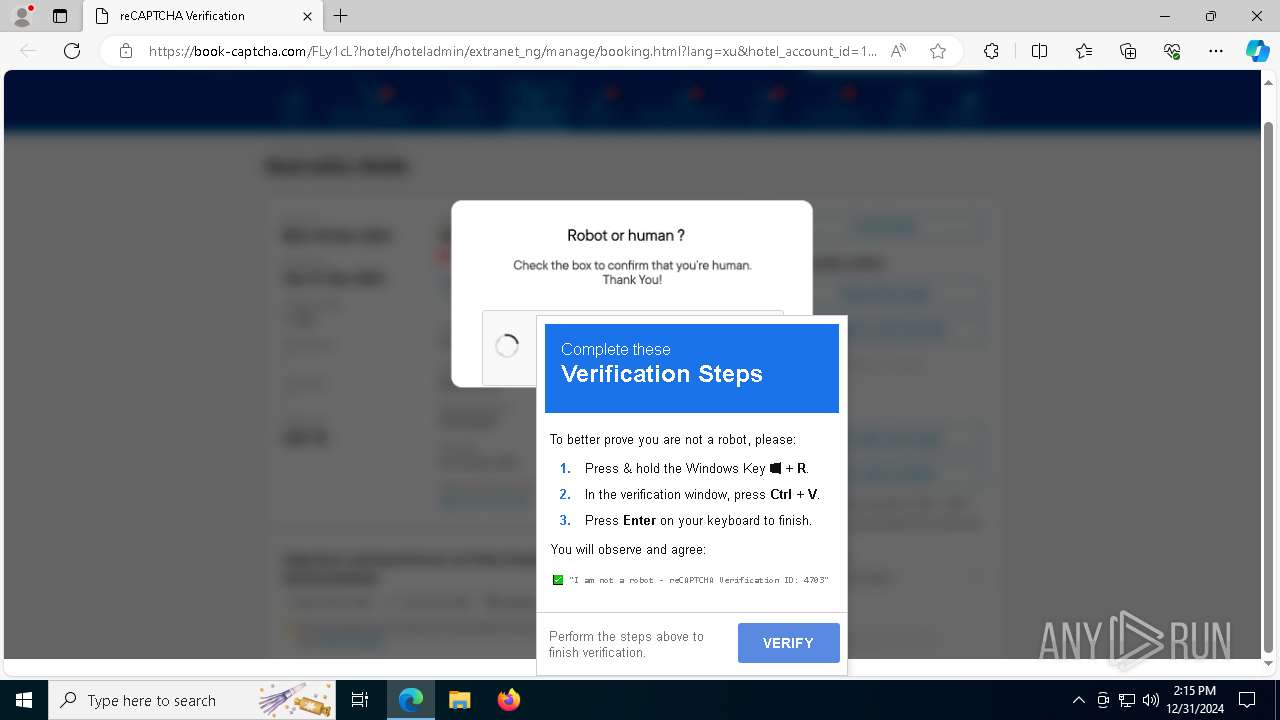
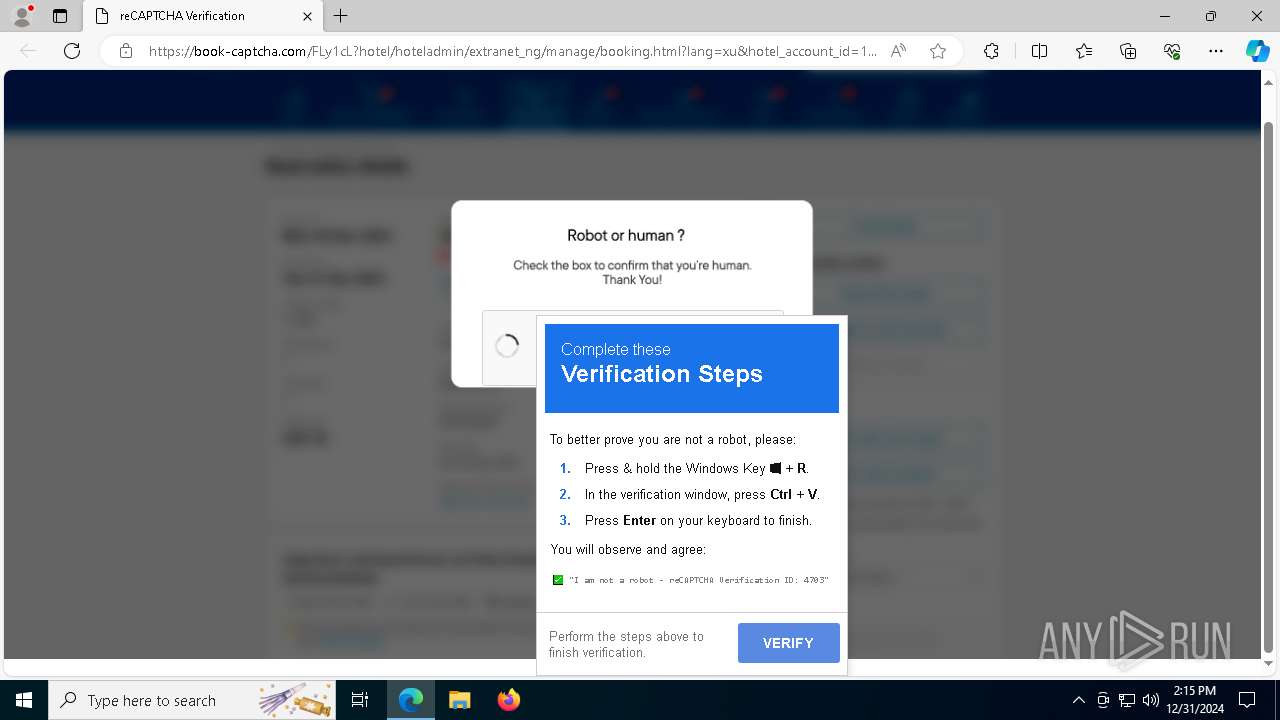
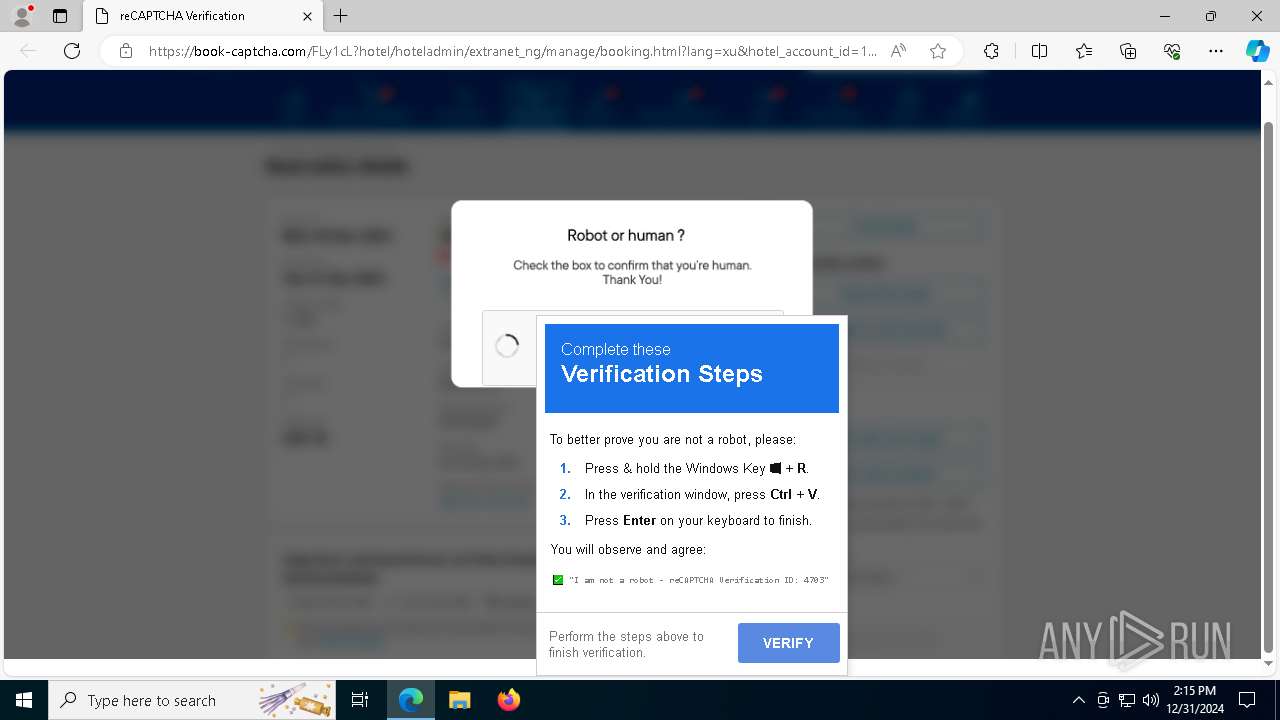
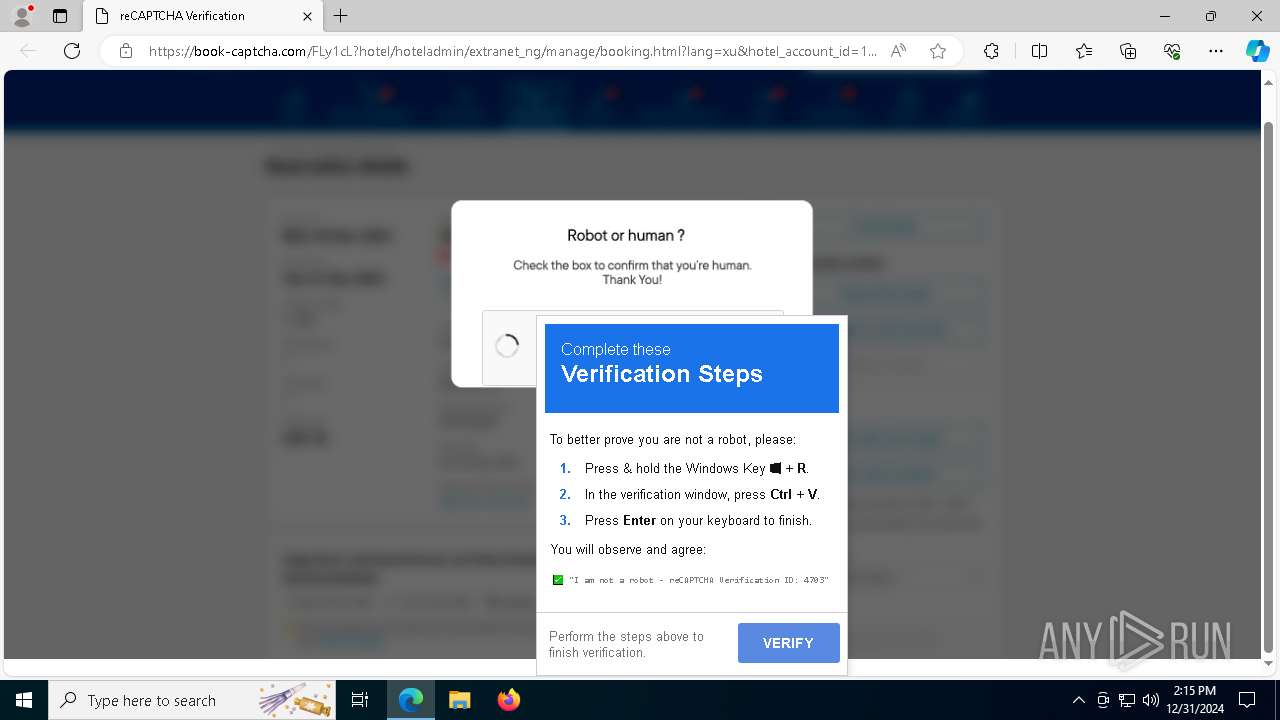
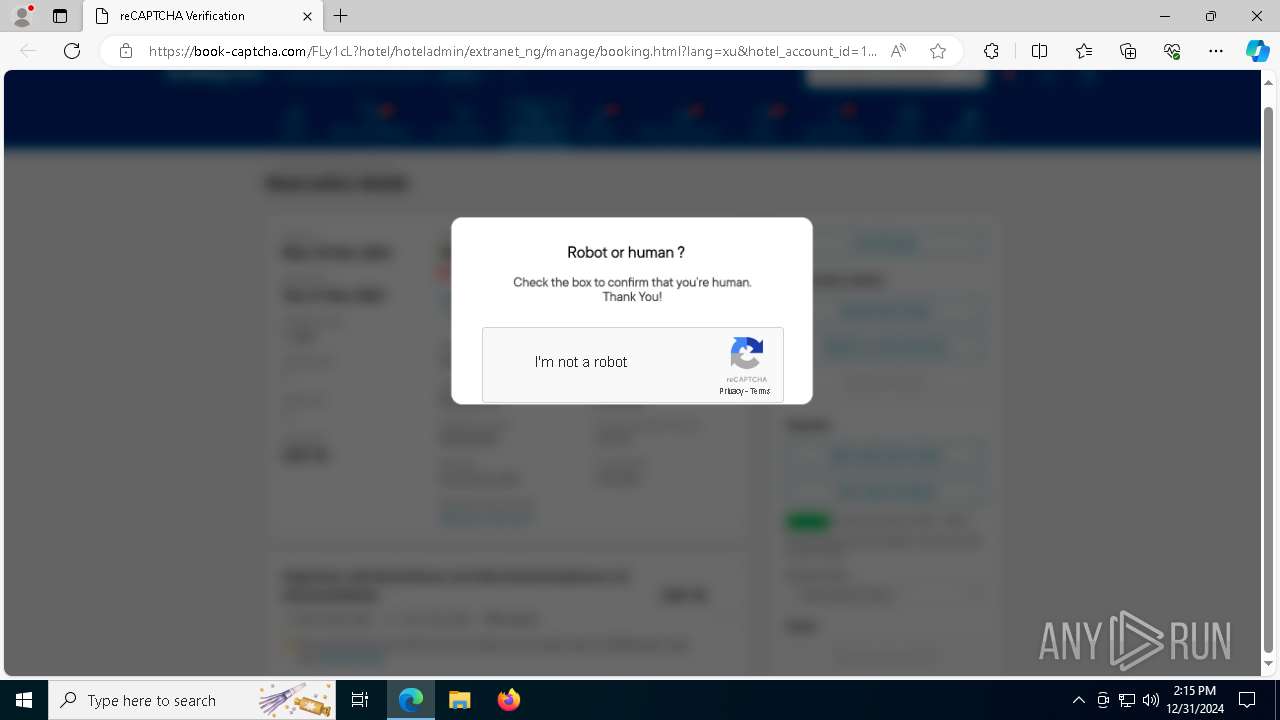
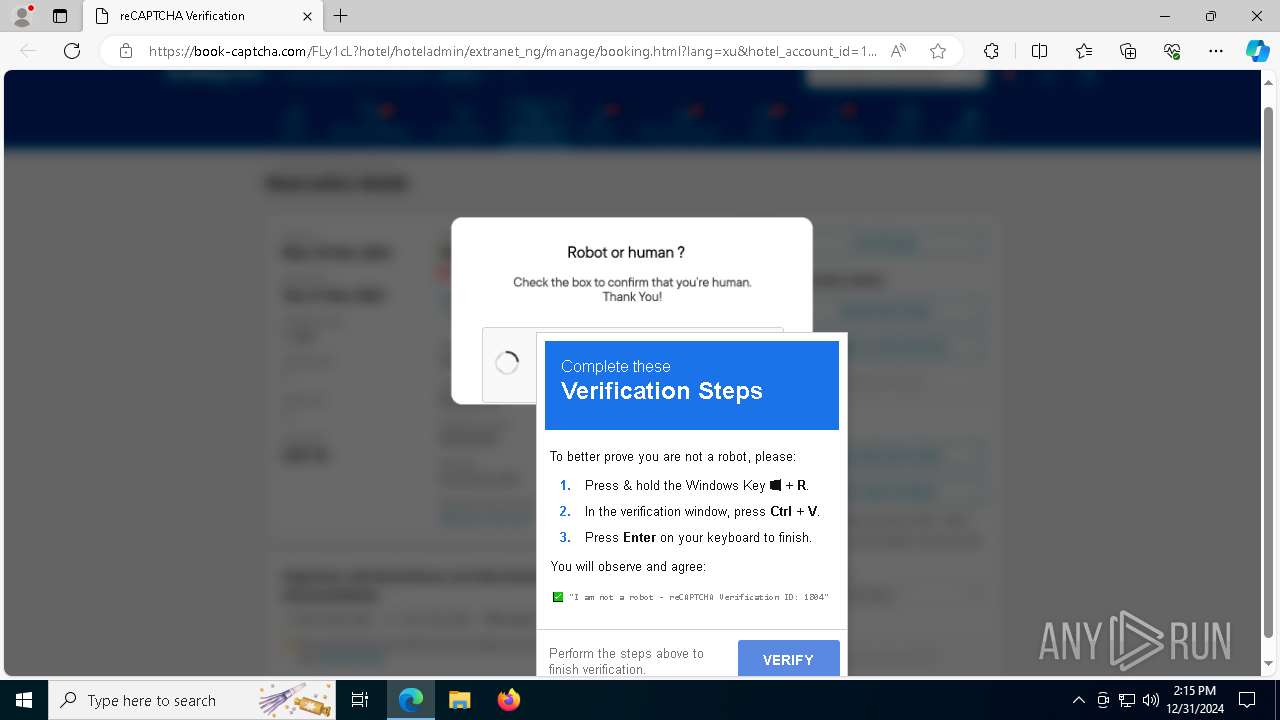
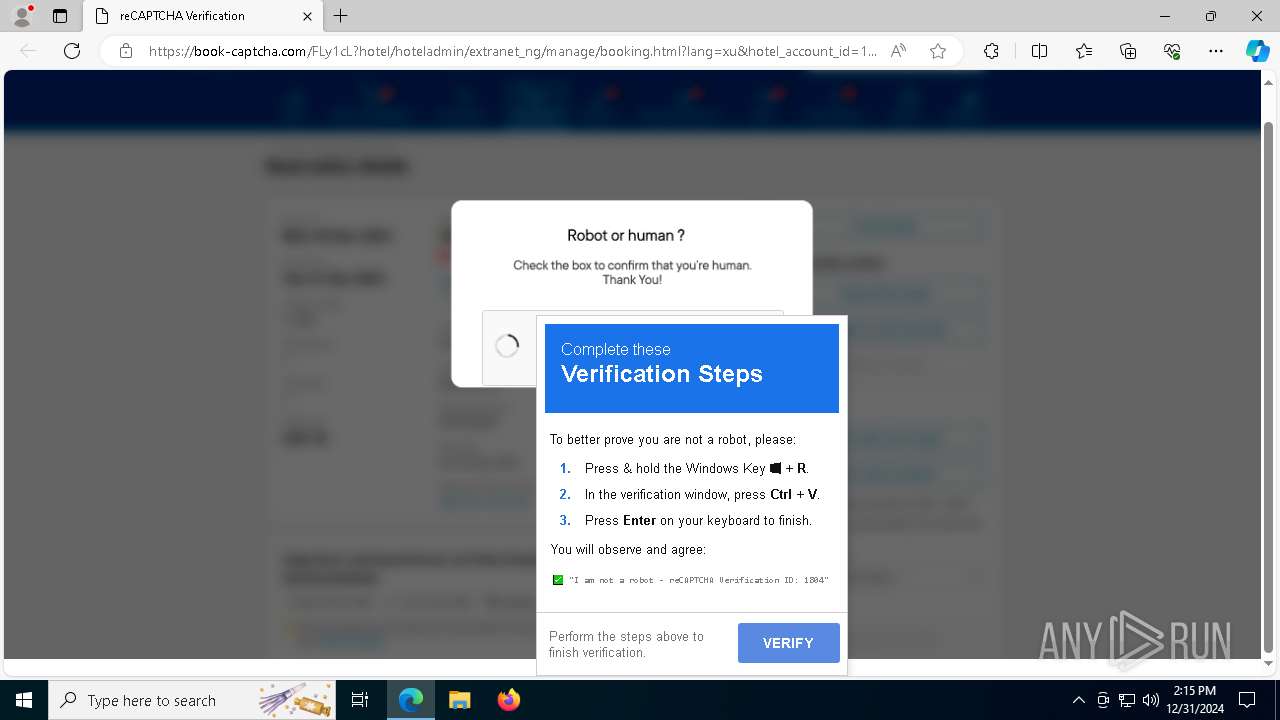
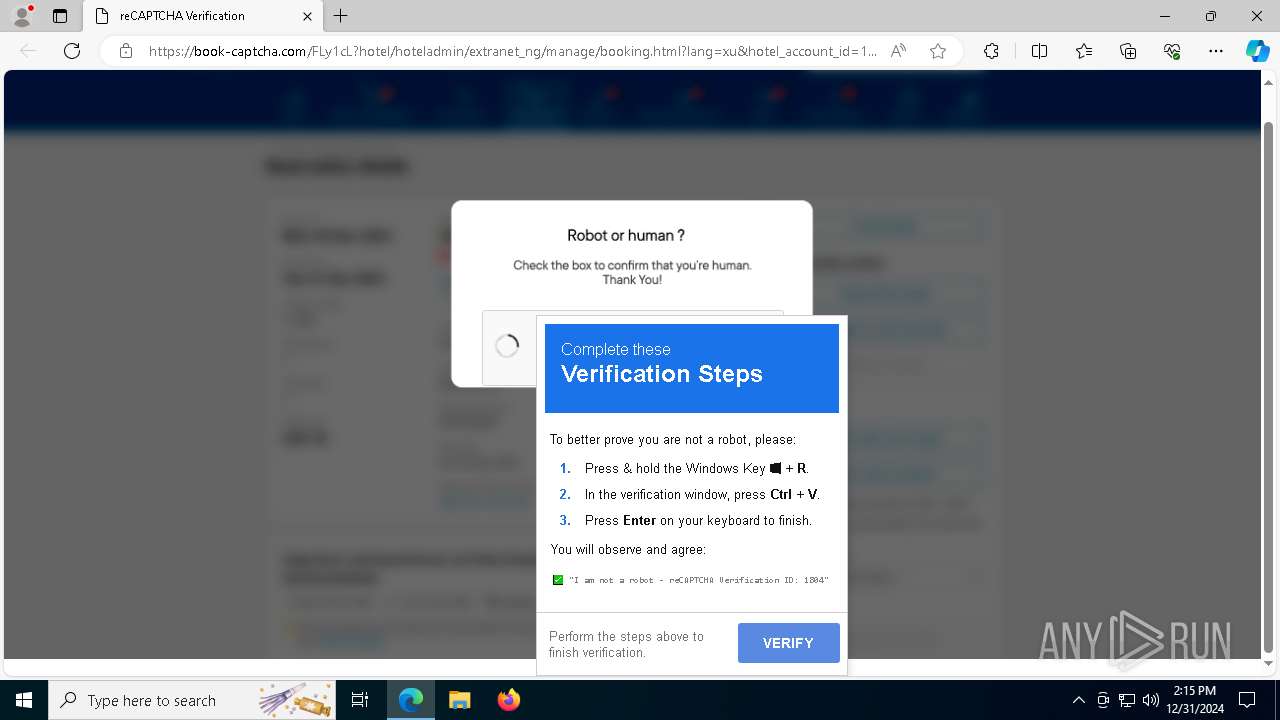
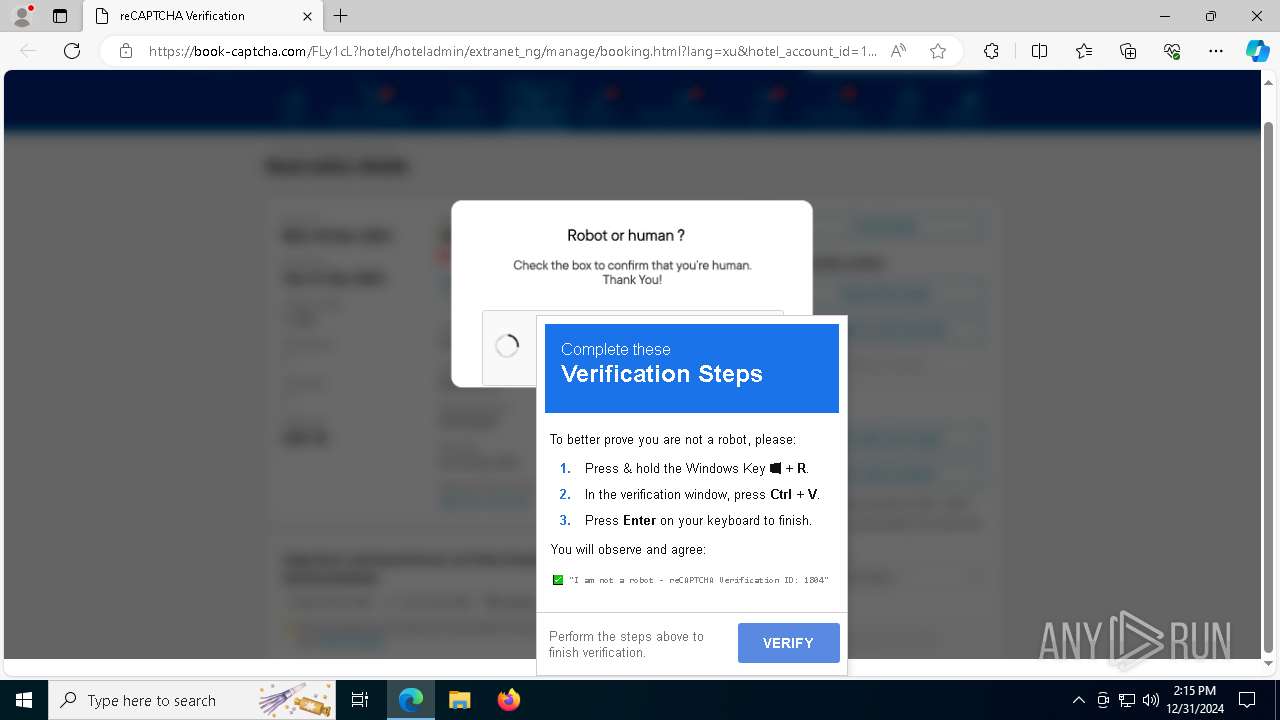
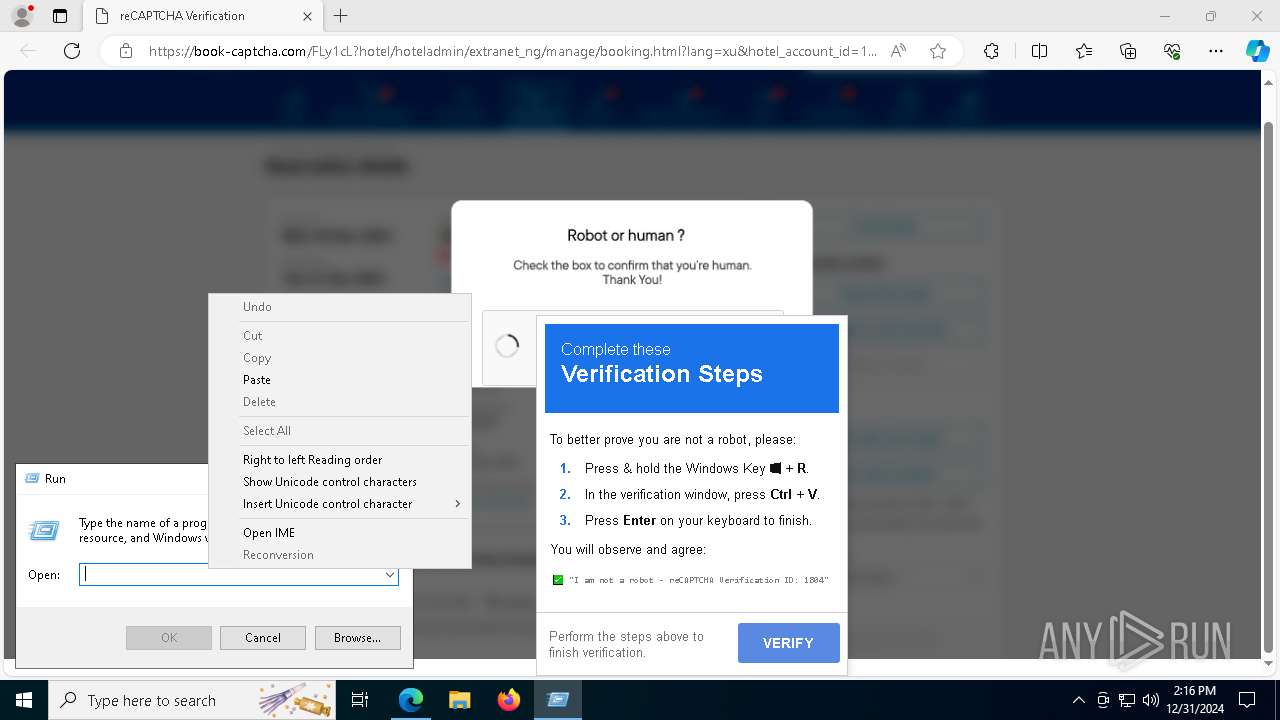
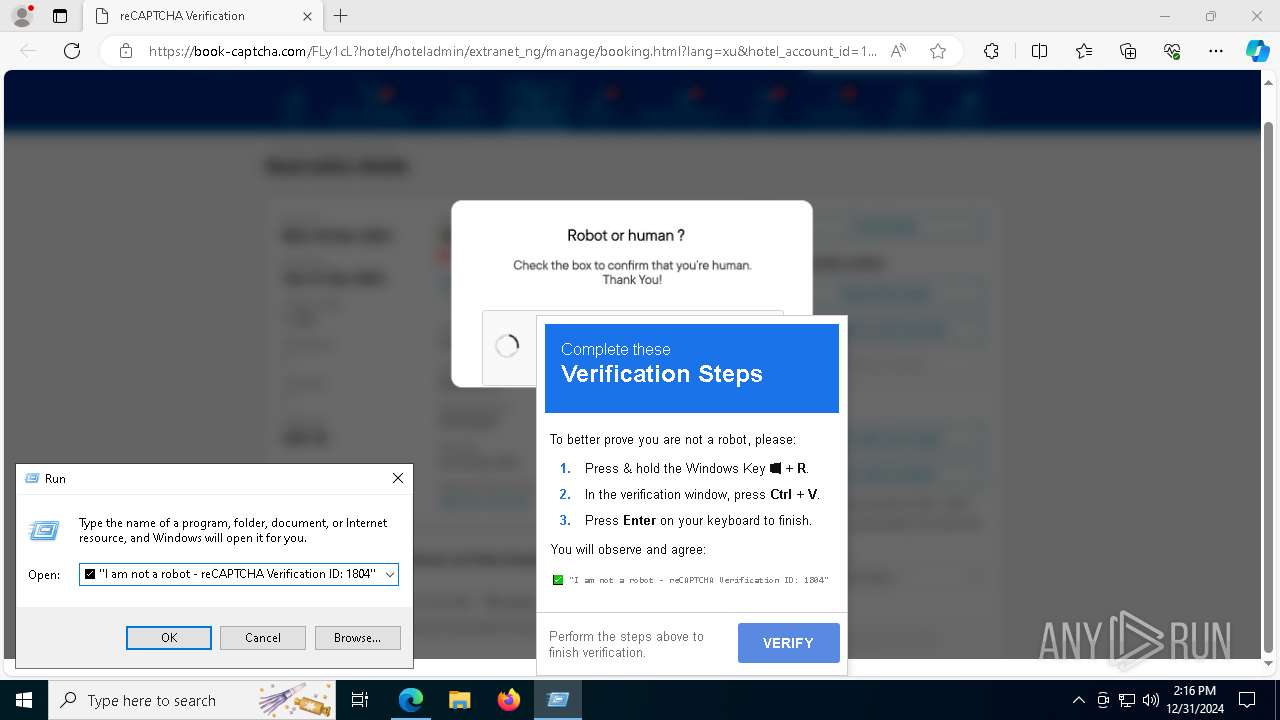
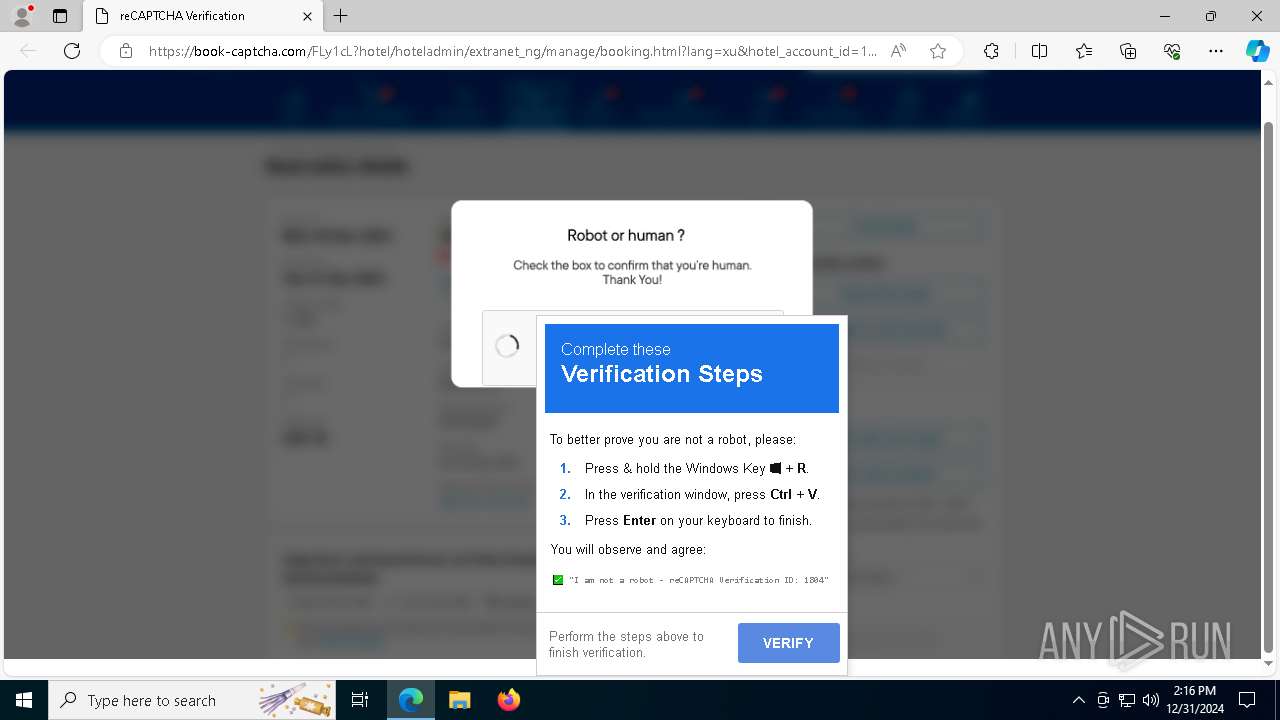
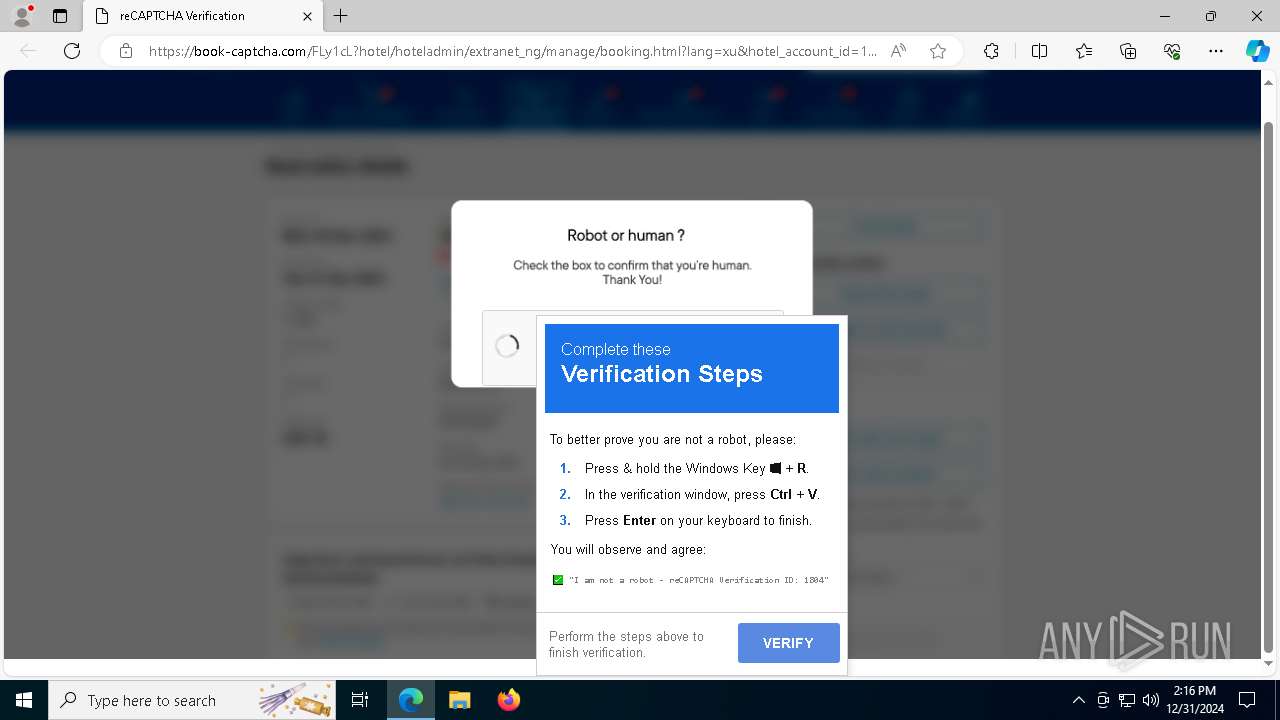
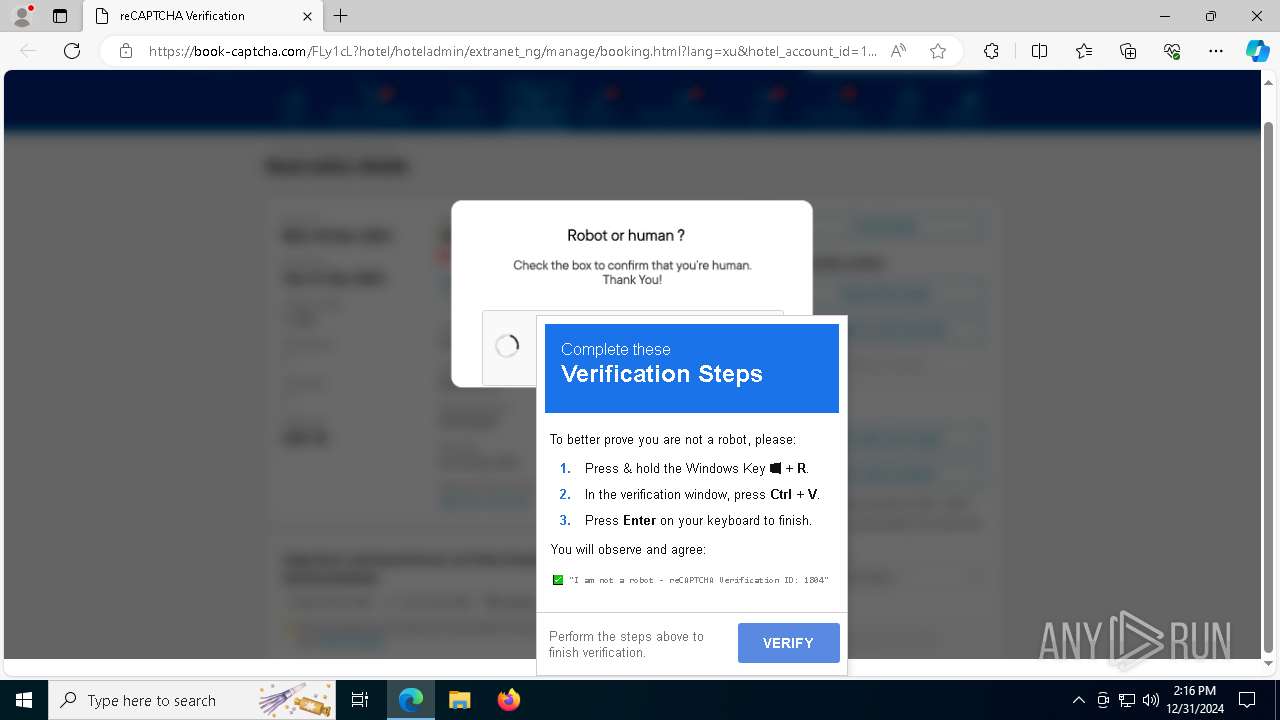
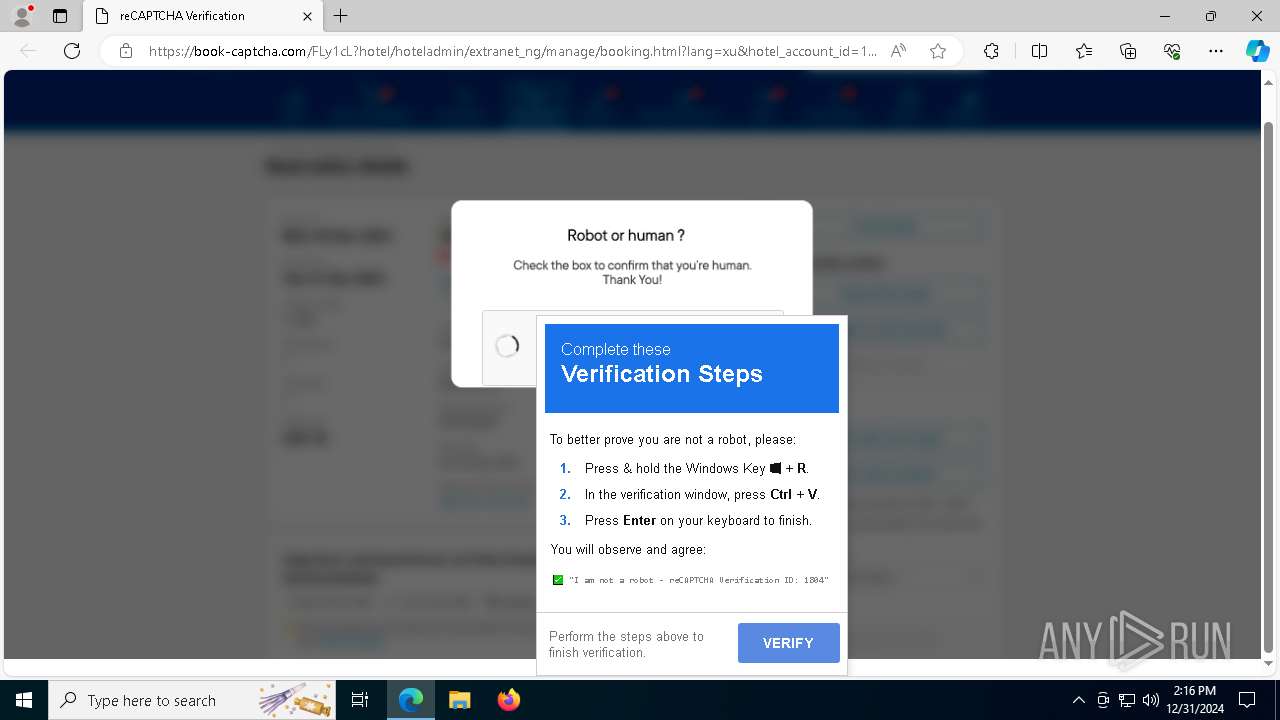
| 628 | "C:\WINDOWS\system32\mshta.exe" https://book-captcha.com/recaptcha-verify.html # ✅ ''I am not a robot - reCAPTCHA Verification ID: 1804'' | C:\Windows\System32\mshta.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1144 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1476 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2012 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6244 --field-trial-handle=2292,i,1017750220945343161,9732062007334867490,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2940 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://qipracticeexchange.org/tbh9v" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3060 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3620 | "C:\WINDOWS\system32\ipconfig.exe" /flushdns | C:\Windows\System32\ipconfig.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: IP Configuration Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3696 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=3736 --field-trial-handle=2292,i,1017750220945343161,9732062007334867490,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3744 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --onnx-enabled-for-ee --no-appcompat-clear --mojo-platform-channel-handle=6064 --field-trial-handle=2292,i,1017750220945343161,9732062007334867490,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
41 872
Read events
41 753
Write events
117
Delete events
2
Modification events
| (PID) Process: | (2940) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2940) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2940) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2940) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2940) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: B914EFD127892F00 | |||
| (PID) Process: | (2940) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: A1CCFBD127892F00 | |||
| (PID) Process: | (2940) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393894 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {211C85B7-B63C-4AF7-A56D-A5F326A27F29} | |||
| (PID) Process: | (2940) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393894 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {4D87F819-BA20-4C3A-AD52-C33823B92EF3} | |||
| (PID) Process: | (2940) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393894 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {123AFBED-6111-4AE9-A939-A350751121E6} | |||
| (PID) Process: | (5064) SearchApp.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.search_cw5n1h2txyewy\Internet Explorer\DOMStorage\bing.com |
| Operation: | write | Name: | Total |
Value: 50667 | |||
Executable files
5
Suspicious files
400
Text files
191
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2940 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1351fb.TMP | — | |
MD5:— | SHA256:— | |||
| 2940 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2940 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1351fb.TMP | — | |
MD5:— | SHA256:— | |||
| 2940 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2940 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF13520b.TMP | — | |
MD5:— | SHA256:— | |||
| 2940 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2940 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF13521b.TMP | — | |
MD5:— | SHA256:— | |||
| 2940 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2940 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF13521b.TMP | — | |
MD5:— | SHA256:— | |||
| 2940 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
54
TCP/UDP connections
100
DNS requests
105
Threats
48
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.53.42.18:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.37.237.227:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.37.237.227:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6808 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
7800 | SIHClient.exe | GET | 200 | 23.37.237.227:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7800 | SIHClient.exe | GET | 200 | 23.37.237.227:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7532 | powershell.exe | GET | 200 | 176.113.115.170:80 | http://176.113.115.170/1/1.png | unknown | — | — | malicious |
7292 | mshta.exe | GET | 200 | 95.101.54.131:80 | http://e6.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBTUejiAQejpjQc4fOz2ttjyD6VkMQQUDcXM%2FZvuFAWhTDCCpT5eisNYCdICEgSKvIRVPTUE7Qog0MOwY8O94Q%3D%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5580 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.53.42.18:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
4712 | MoUsoCoreWorker.exe | 23.37.237.227:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 23.37.237.227:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2940 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
— | — | 193.3.19.63:443 | qipracticeexchange.org | OOO Network of data-centers Selectel | RU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
qipracticeexchange.org |
| unknown |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6216 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Image hosting service ImgBB |
— | — | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 30 |
2192 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (scentniej .buzz) |
2192 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (hummskitnj .buzz) |
2192 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (prisonyfork .buzz) |
2192 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (inherineau .buzz) |
2192 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (screwamusresz .buzz) |
2192 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (rebuildeso .buzz) |
2192 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (appliacnesot .buzz) |
2192 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (cashfuzysao .buzz) |
29 ETPRO signatures available at the full report