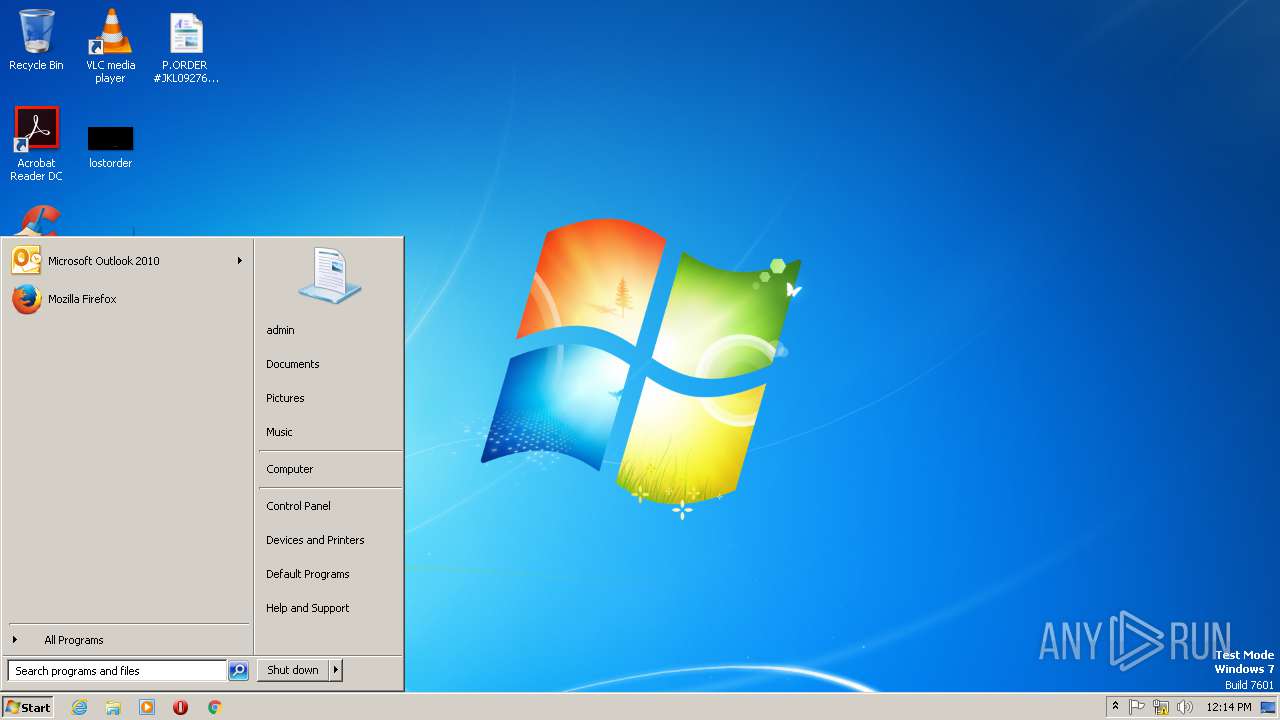
| File name: | P.ORDER #JKL0927634944112018 pdf.exe |
| Full analysis: | https://app.any.run/tasks/ed4a793f-ecbf-45b1-8caa-0a63b7220afb |
| Verdict: | Malicious activity |
| Threats: | Hawkeye often gets installed in a bundle with other malware. This is a Trojan and keylogger that is used to retrieve private information such as passwords and login credentials. This is an advanced malware that features strong anti-evasion functions. |
| Analysis date: | November 14, 2018, 12:12:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 4E520E64857F774E2C4AACC64924D436 |
| SHA1: | 47519D090B25F552F7F764E46442E37EC7527F99 |
| SHA256: | 2114306EFF8A8D2BDC295AC3AAB3654F5DEF83208F6FC81FB5FCF4FEBE3AE0DA |
| SSDEEP: | 12288:OLTGIGF3rB3iztvh3znyycZVmLmOq4jKaEn++tPclebF6+/Y6H:OLT03AtZzyycZVsQ4jW++tPcli02H |
MALICIOUS
Changes the autorun value in the registry
- startapp.exe (PID: 192)
Writes to a start menu file
- startapp.exe (PID: 2996)
Detected Hawkeye Keylogger
- startapp.exe (PID: 192)
Actions looks like stealing of personal data
- vbc.exe (PID: 2676)
SUSPICIOUS
Application launched itself
- startapp.exe (PID: 2996)
Executable content was dropped or overwritten
- P.ORDER #JKL0927634944112018 pdf.exe (PID: 1204)
- startapp.exe (PID: 192)
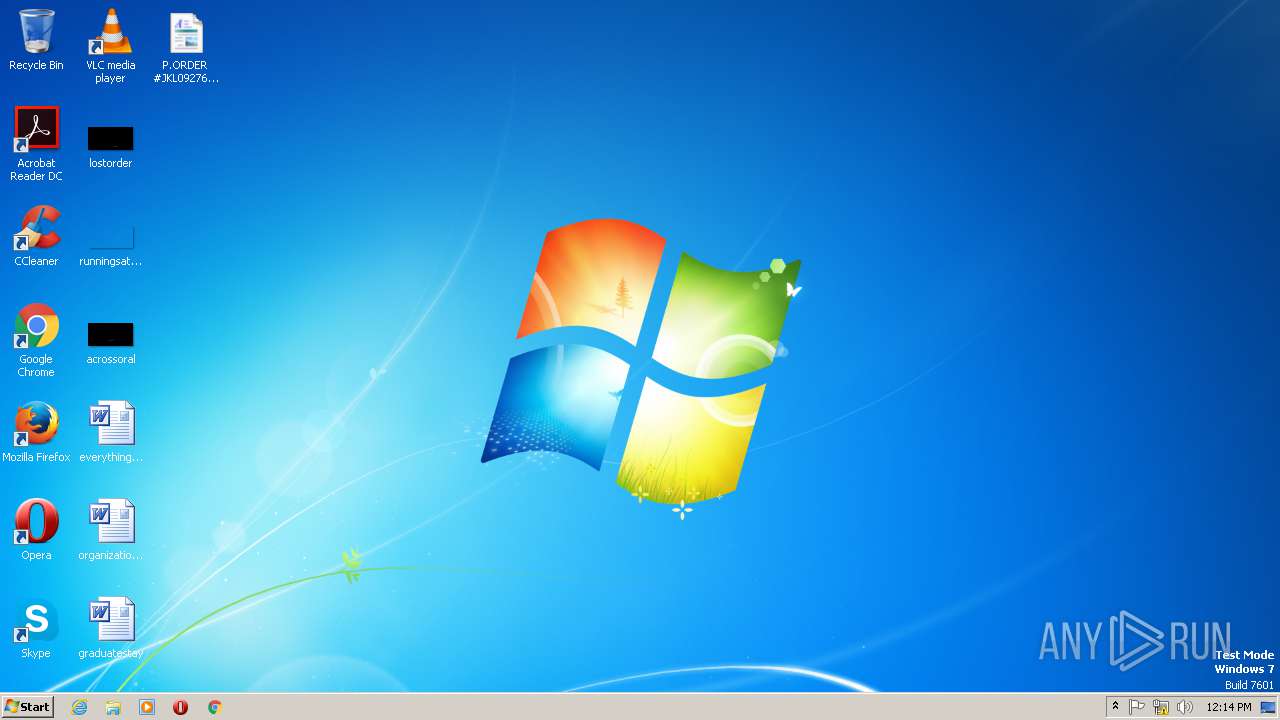
Creates files in the user directory
- startapp.exe (PID: 2996)
- P.ORDER #JKL0927634944112018 pdf.exe (PID: 1204)
- startapp.exe (PID: 192)
Starts itself from another location
- P.ORDER #JKL0927634944112018 pdf.exe (PID: 1204)
Checks for external IP
- startapp.exe (PID: 192)
Connects to SMTP port
- startapp.exe (PID: 192)
Executes scripts
- startapp.exe (PID: 192)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (38.2) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (37.5) |
| .dll | | | Win32 Dynamic Link Library (generic) (9.2) |
| .exe | | | Win32 Executable (generic) (6.3) |
| .exe | | | Win16/32 Executable Delphi generic (2.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:02:08 05:27:09+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 557056 |
| InitializedDataSize: | 12288 |
| UninitializedDataSize: | 323584 |
| EntryPoint: | 0xd7ae0 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 08-Feb-1992 04:27:09 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 08-Feb-1992 04:27:09 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x0004F000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00050000 | 0x00088000 | 0x00087E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.85407 |
.rsrc | 0x000D8000 | 0x00003000 | 0x00002600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.55471 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.79909 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
2 | 6.72869 | 308 | Latin 1 / Western European | UNKNOWN | RT_CURSOR |
3 | 6.75321 | 308 | Latin 1 / Western European | UNKNOWN | RT_CURSOR |
4 | 6.86093 | 308 | Latin 1 / Western European | UNKNOWN | RT_CURSOR |
5 | 6.92804 | 308 | Latin 1 / Western European | UNKNOWN | RT_CURSOR |
6 | 6.89684 | 308 | Latin 1 / Western European | UNKNOWN | RT_CURSOR |
7 | 6.92161 | 308 | Latin 1 / Western European | UNKNOWN | RT_CURSOR |
175 | 7.70295 | 8553 | Latin 1 / Western European | English - United States | RT_CURSOR |
176 | 7.7394 | 8553 | Latin 1 / Western European | English - United States | RT_CURSOR |
177 | 7.77635 | 8553 | Latin 1 / Western European | English - United States | RT_CURSOR |
Imports
KERNEL32.DLL |
advapi32.dll |
comctl32.dll |
comdlg32.dll |
gdi32.dll |
oleaut32.dll |
user32.dll |
version.dll |
winmm.dll |
Total processes
41
Monitored processes
6
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 192 | "C:\Users\admin\AppData\Roaming\startup\startapp.exe" | C:\Users\admin\AppData\Roaming\startup\startapp.exe | startapp.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1204 | "C:\Users\admin\Desktop\P.ORDER #JKL0927634944112018 pdf.exe" | C:\Users\admin\Desktop\P.ORDER #JKL0927634944112018 pdf.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2332 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe /stext "C:\Users\admin\AppData\Local\Temp\holderwb.txt" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | — | startapp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 8.0.50727.5483 Modules
| |||||||||||||||
| 2676 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe /stext "C:\Users\admin\AppData\Local\Temp\holdermail.txt" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | startapp.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 8.0.50727.5483 Modules
| |||||||||||||||
| 2996 | "C:\Users\admin\AppData\Roaming\startup\startapp.exe" | C:\Users\admin\AppData\Roaming\startup\startapp.exe | P.ORDER #JKL0927634944112018 pdf.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3032 | "C:\Users\admin\AppData\Roaming\startup\startapp.exe" 2 192 606375 | C:\Users\admin\AppData\Roaming\startup\startapp.exe | — | startapp.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
39
Read events
19
Write events
20
Delete events
0
Modification events
| (PID) Process: | (192) startapp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Tracing |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (192) startapp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Tracing\startapp_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (192) startapp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Tracing\startapp_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (192) startapp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Tracing\startapp_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (192) startapp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Tracing\startapp_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (192) startapp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Tracing\startapp_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (192) startapp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Tracing\startapp_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (192) startapp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Tracing\startapp_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (192) startapp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Tracing\startapp_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (192) startapp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Tracing\startapp_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
Executable files
2
Suspicious files
0
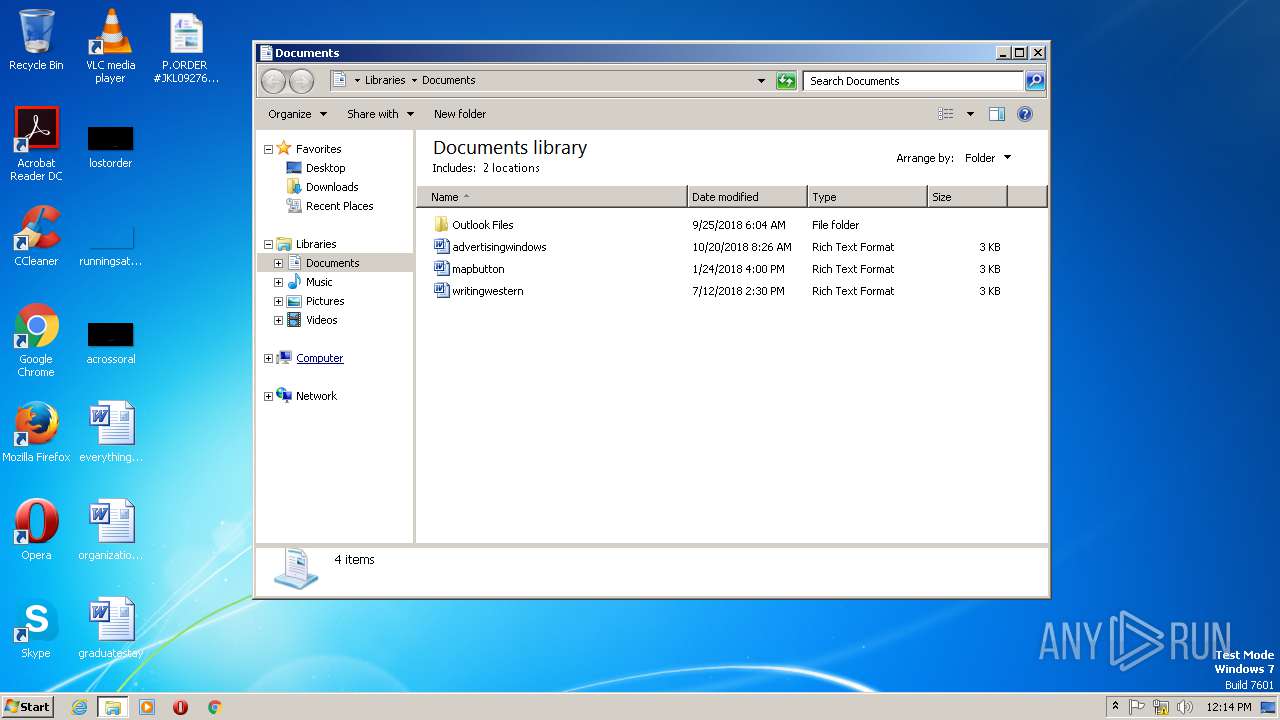
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1204 | P.ORDER #JKL0927634944112018 pdf.exe | C:\Users\admin\AppData\Roaming\startup\startapp.exe:ZoneIdentifier | — | |
MD5:— | SHA256:— | |||
| 2676 | vbc.exe | C:\Users\admin\AppData\Local\Temp\holdermail.txt | — | |
MD5:— | SHA256:— | |||
| 2332 | vbc.exe | C:\Users\admin\AppData\Local\Temp\bhv811B.tmp | — | |
MD5:— | SHA256:— | |||
| 2332 | vbc.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WebCache\WebCacheV01.dat | — | |
MD5:— | SHA256:— | |||
| 2332 | vbc.exe | C:\Users\admin\AppData\Local\Temp\holderwb.txt | — | |
MD5:— | SHA256:— | |||
| 2996 | startapp.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\startup.vbs | text | |
MD5:— | SHA256:— | |||
| 192 | startapp.exe | C:\Users\admin\AppData\Roaming\pidloc.txt | text | |
MD5:— | SHA256:— | |||
| 1204 | P.ORDER #JKL0927634944112018 pdf.exe | C:\Users\admin\AppData\Roaming\startup\startapp.exe | executable | |
MD5:— | SHA256:— | |||
| 192 | startapp.exe | C:\Users\admin\AppData\Roaming\pid.txt | text | |
MD5:58A2FC6ED39FD083F55D4182BF88826D | SHA256:EB3BE230BBD2844B1F5D8F2E4FAB9FFBA8AB22CFEEB69C4C1361993BA4F377B9 | |||
| 192 | startapp.exe | C:\Users\admin\AppData\Roaming\WindowsUpdate.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
3
DNS requests
2
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
192 | startapp.exe | GET | 403 | 104.16.16.96:80 | http://whatismyipaddress.com/ | US | text | 100 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
192 | startapp.exe | 104.16.16.96:80 | whatismyipaddress.com | Cloudflare Inc | US | shared |
192 | startapp.exe | 103.103.197.38:587 | smtp.zoho.in | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
whatismyipaddress.com |
| shared |
smtp.zoho.in |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
192 | startapp.exe | A Network Trojan was detected | MALWARE [PTsecurity] Spyware.HawkEyeKeyLogger (IP Chck) |
2 ETPRO signatures available at the full report