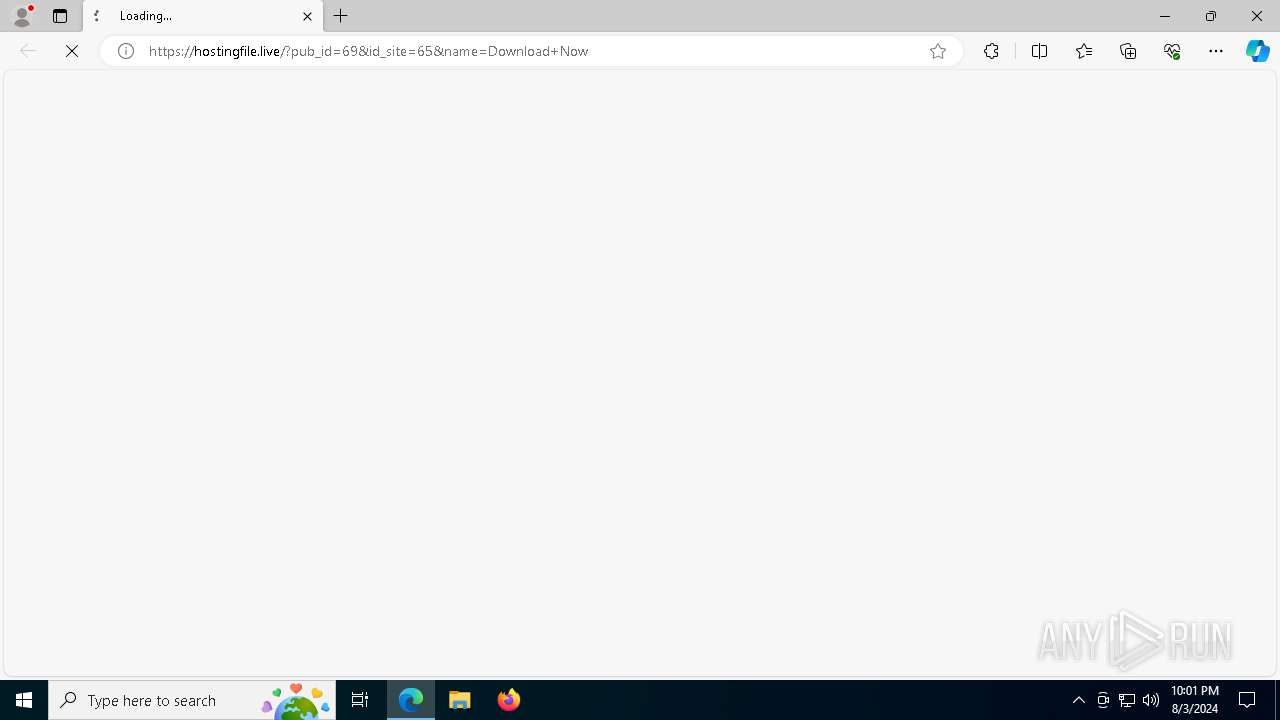
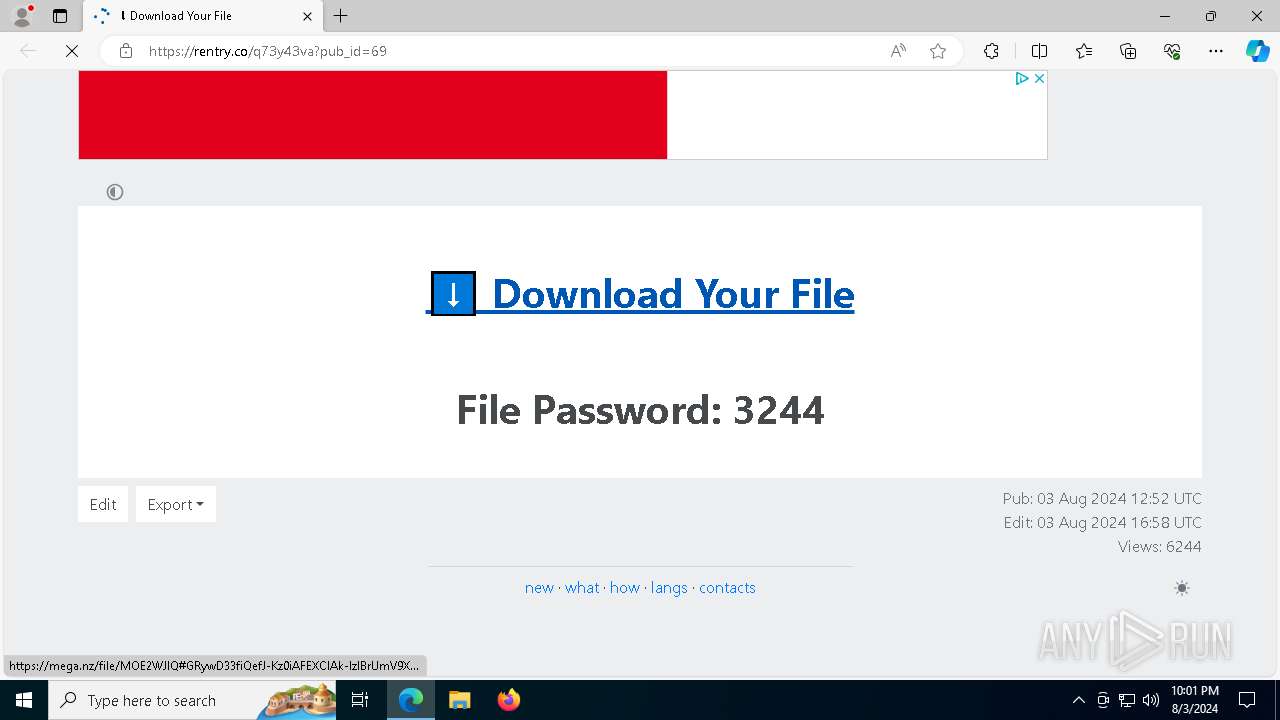
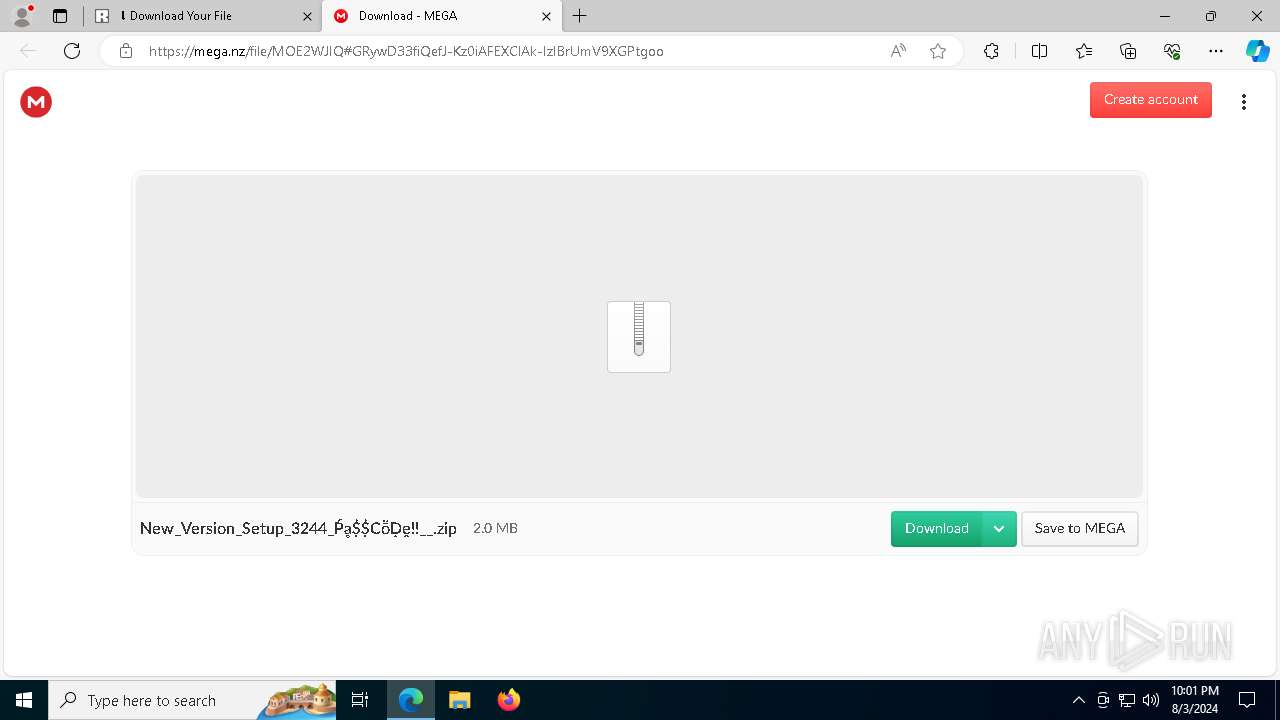
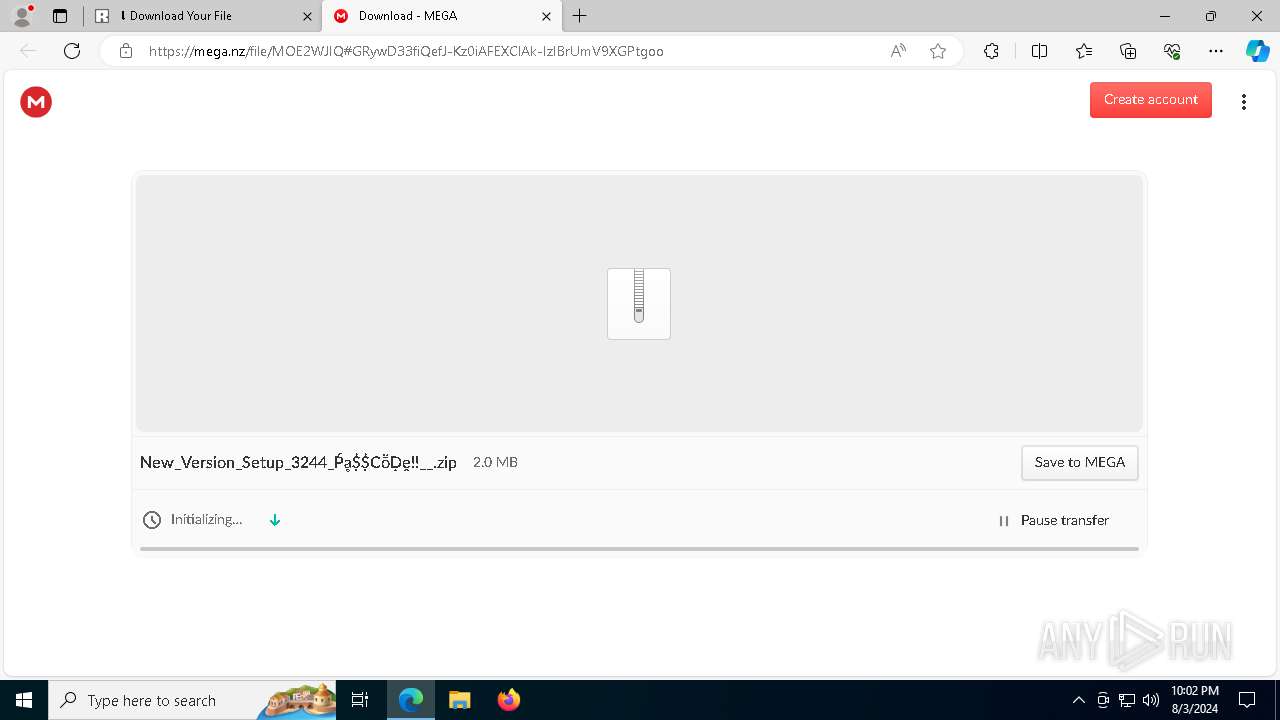
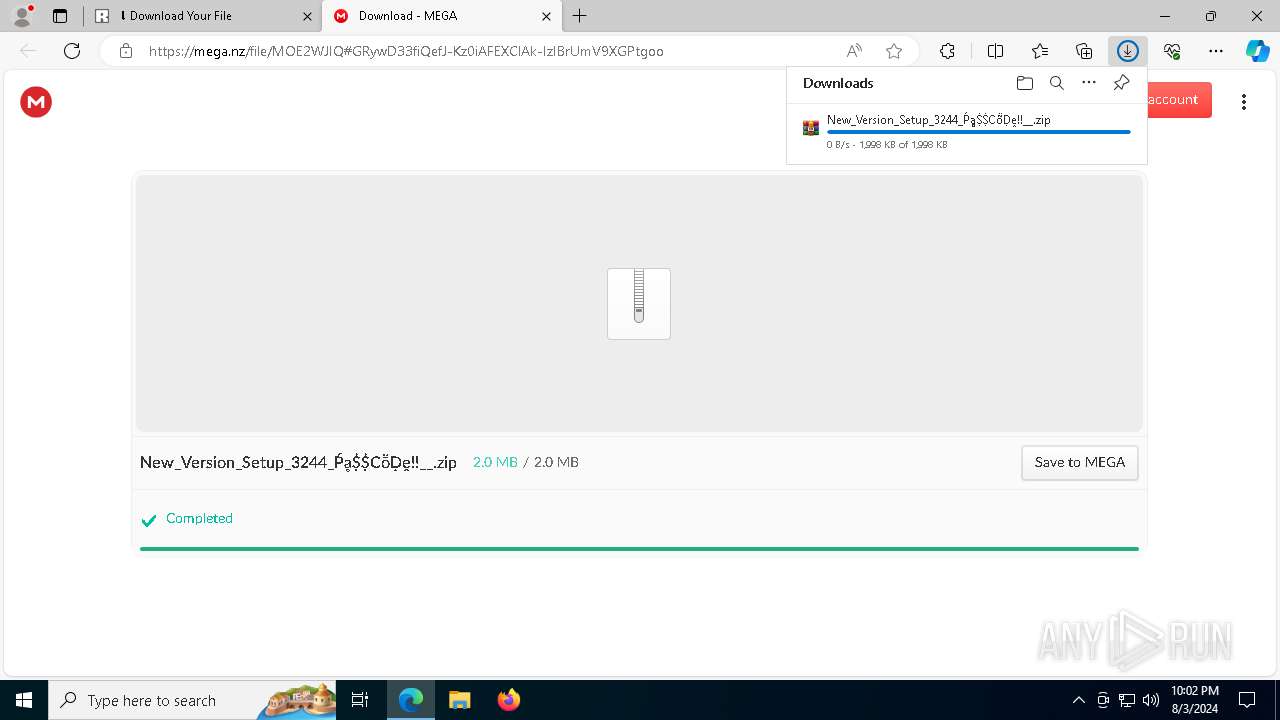
| URL: | https://hostingfile.live/?pub_id=69&id_site=65&name=Download+Now |
| Full analysis: | https://app.any.run/tasks/a98bf396-875d-4878-aa82-6b011b9adcae |
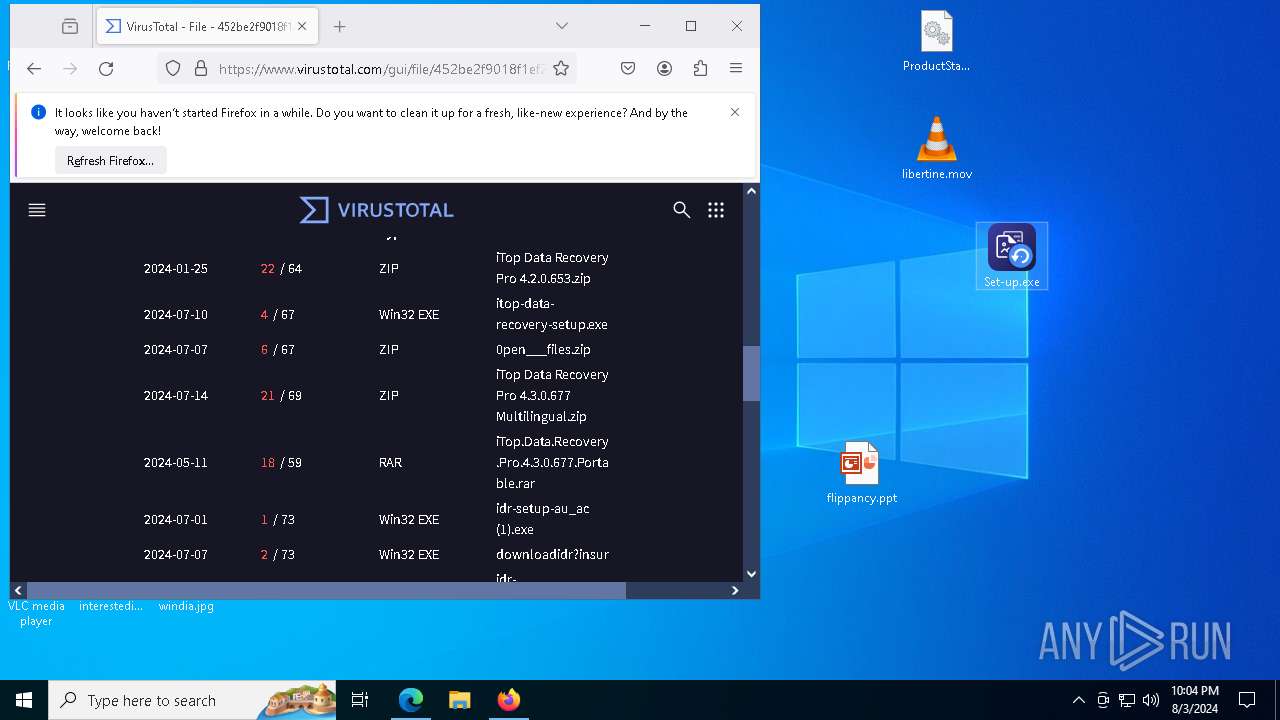
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | August 03, 2024, 22:01:44 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
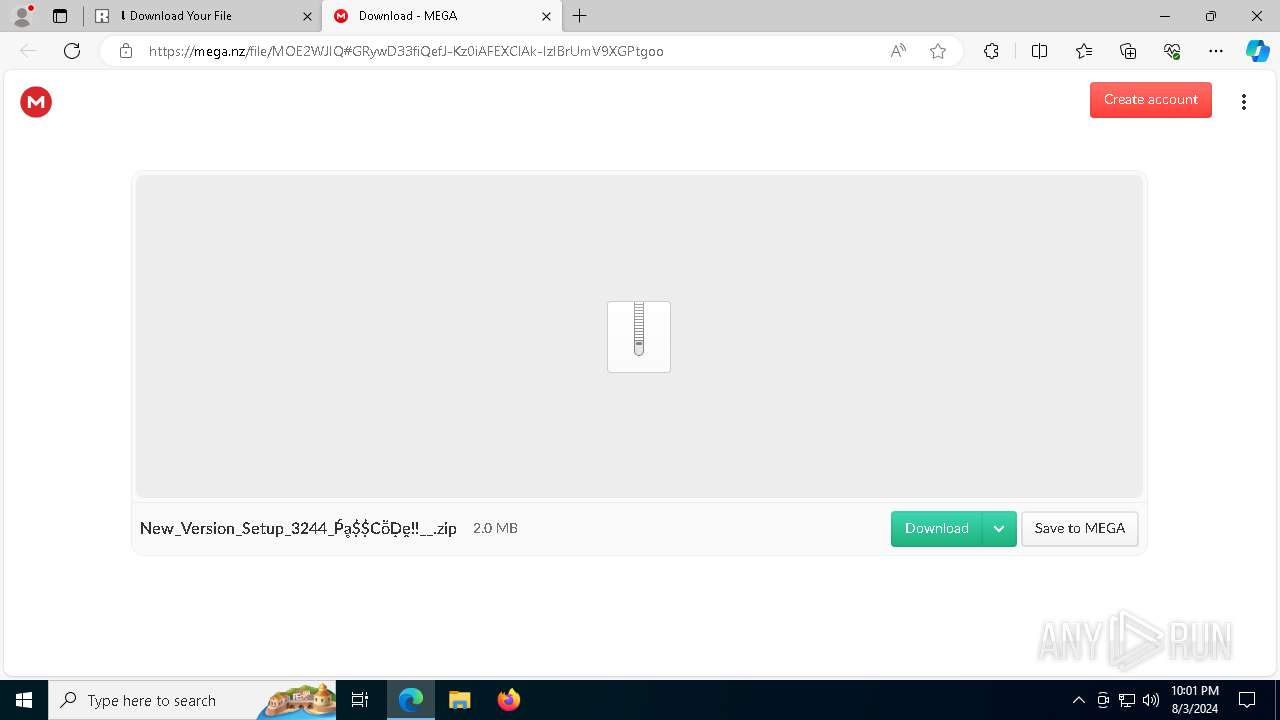
| MD5: | D24D757EB2F4D8AD89CBEF9CE061CD48 |
| SHA1: | FAAC998AE7C4A8B5E307353AA44ABD7DA7A38709 |
| SHA256: | 211373BDDBA4EB86A3B825D9D00EE3B5AD19ECDFF1261F9C8B24BC2F7EC79102 |
| SSDEEP: | 3:N82WqzA9SC6HauR9TQXE4t4eS:22WqzAcXaeWXE4w |
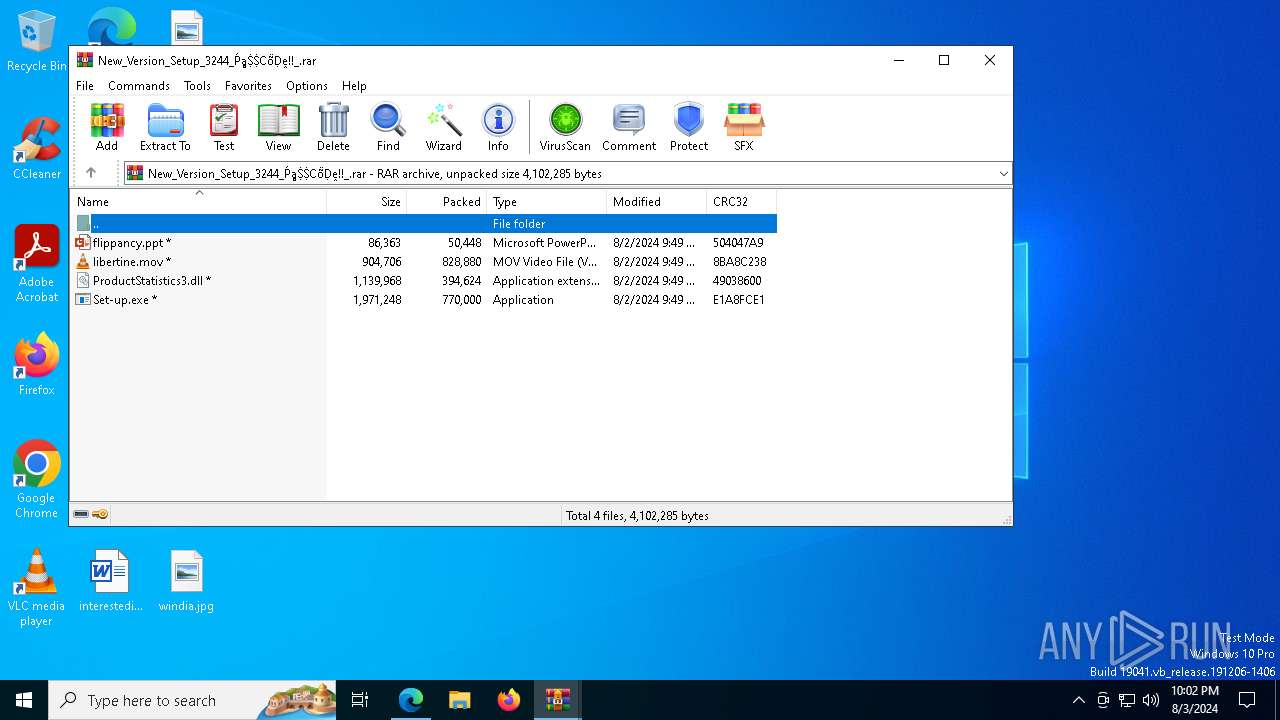
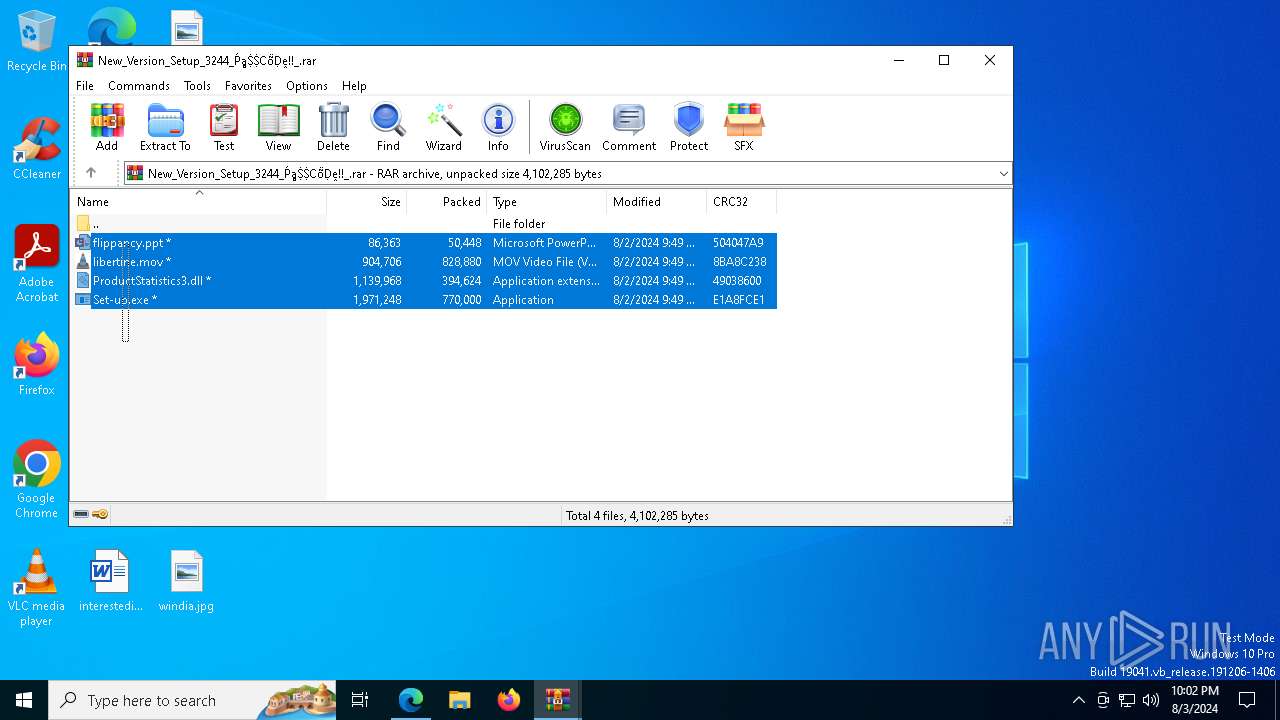
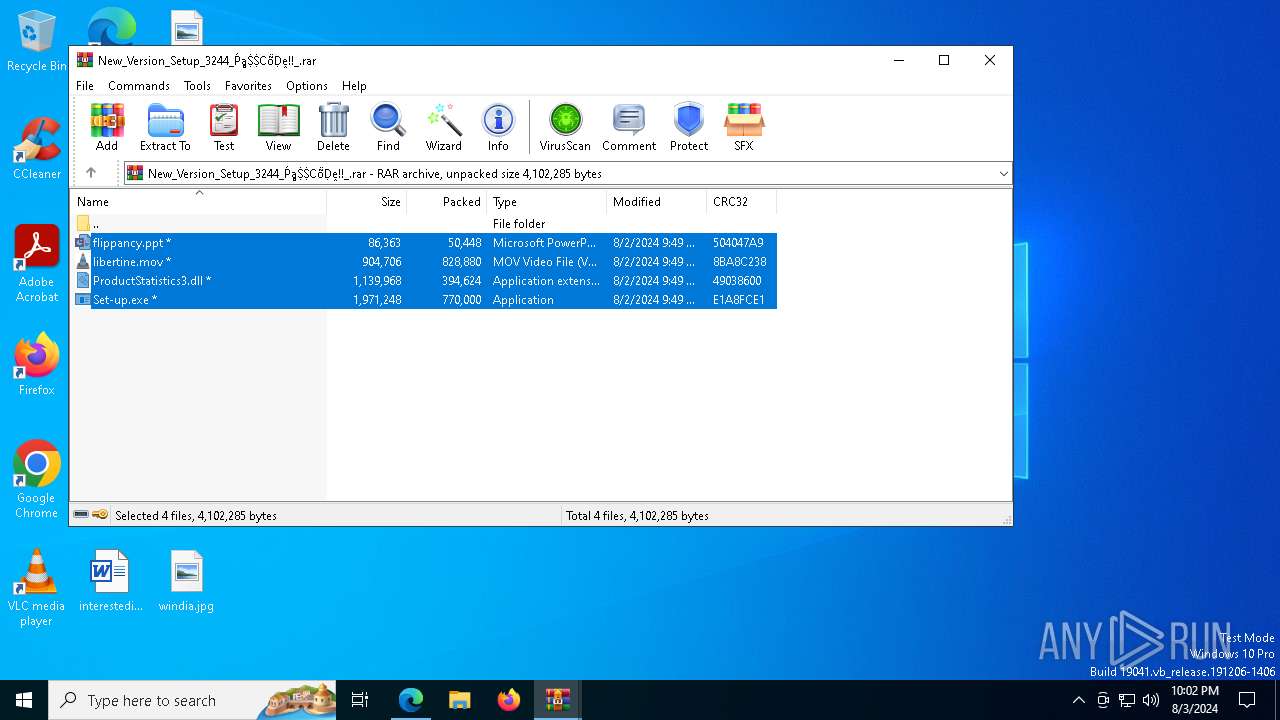
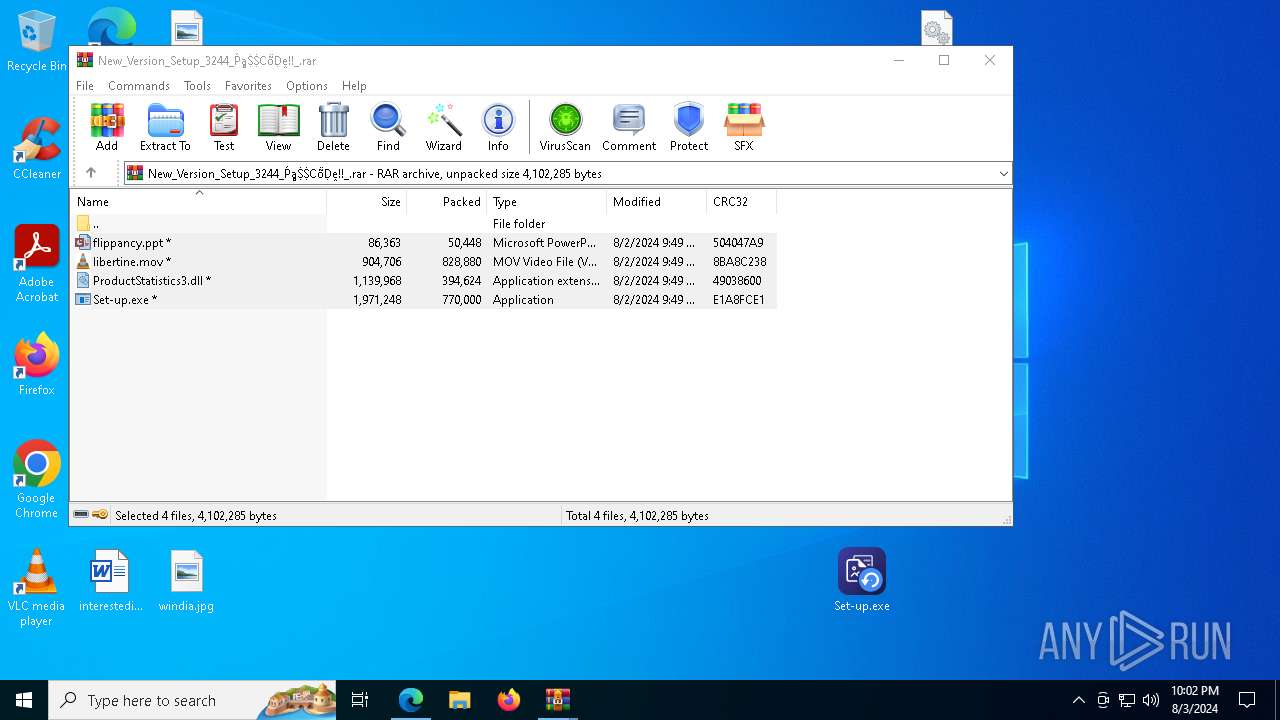
MALICIOUS
Drops the executable file immediately after the start
- Set-up.exe (PID: 9248)
- MN0ZYTFJX731UBU5L9.exe (PID: 7544)
- Set-up.exe (PID: 7052)
Changes powershell execution policy (Bypass)
- SearchIndexer.exe (PID: 3904)
- SearchIndexer.exe (PID: 8368)
Probably downloads file via BitsAdmin (POWERSHELL)
- powershell.exe (PID: 7364)
- powershell.exe (PID: 2468)
Bypass execution policy to execute commands
- powershell.exe (PID: 7364)
- powershell.exe (PID: 2468)
LUMMA has been detected (YARA)
- SearchIndexer.exe (PID: 8368)
Modifies registry (POWERSHELL)
- powershell.exe (PID: 2468)
SUSPICIOUS
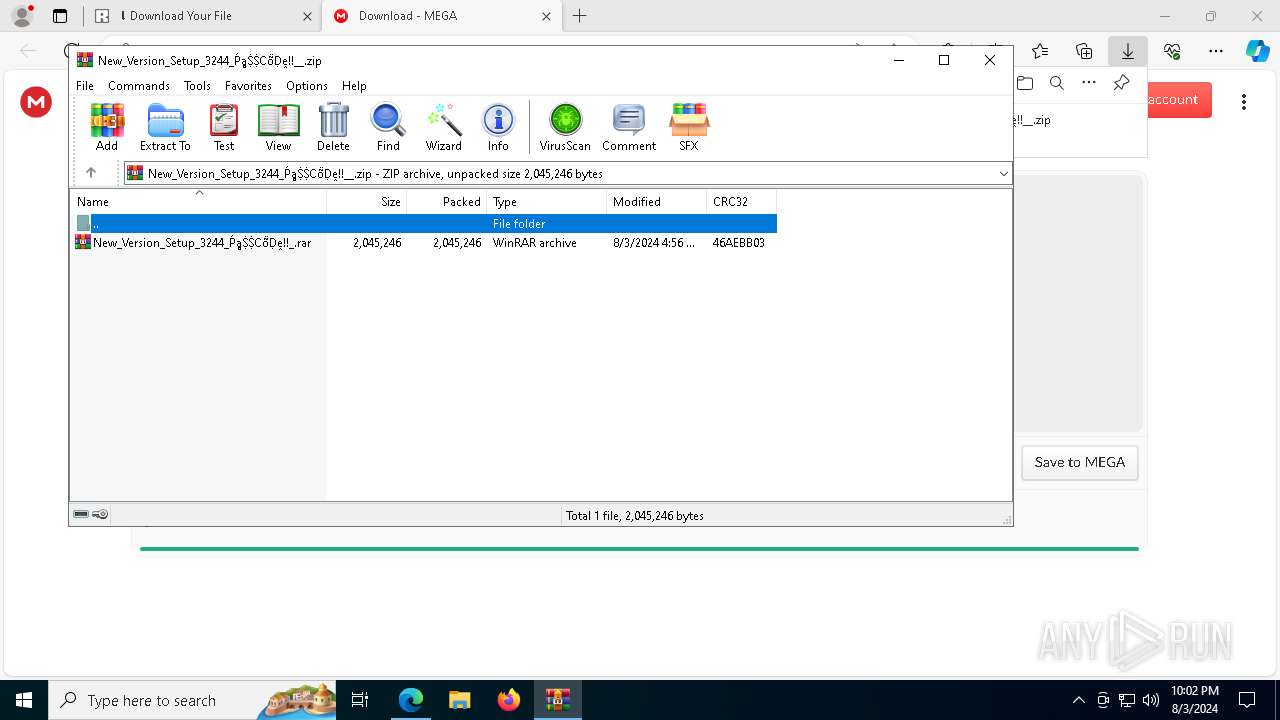
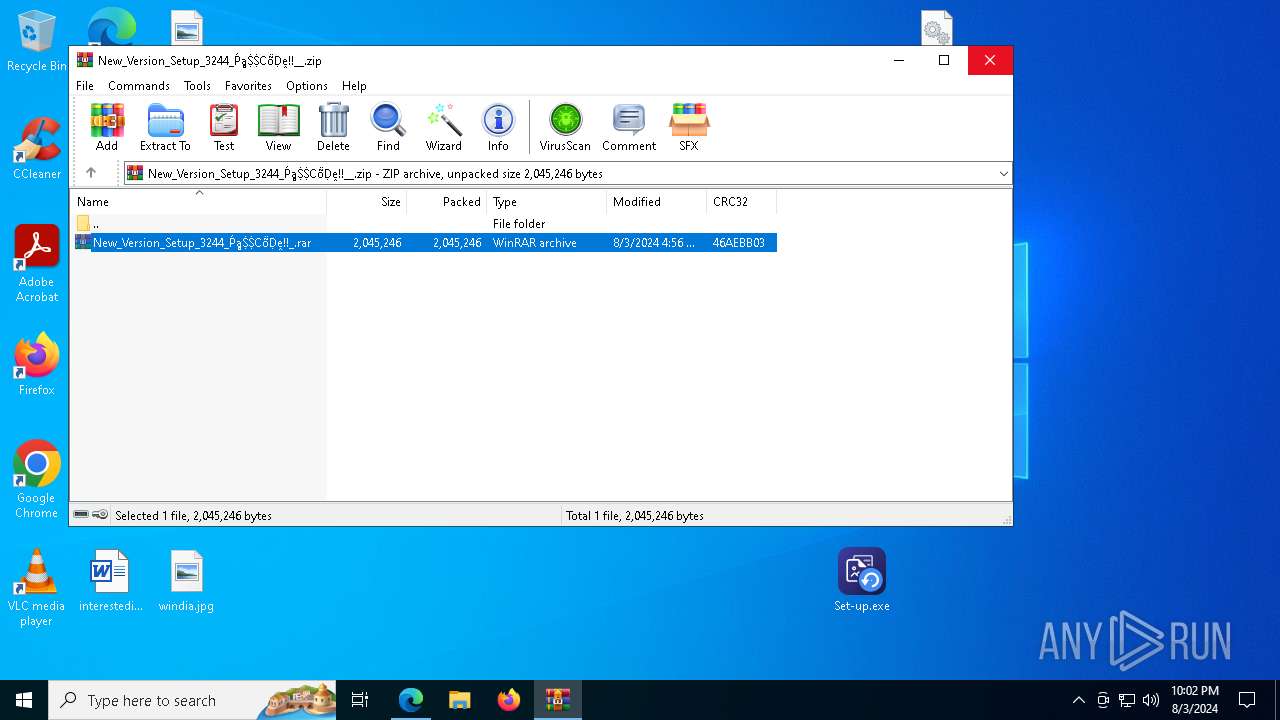
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 8500)
Application launched itself
- WinRAR.exe (PID: 8500)
Executable content was dropped or overwritten
- Set-up.exe (PID: 9248)
- SearchIndexer.exe (PID: 3904)
- SearchIndexer.exe (PID: 8368)
- MN0ZYTFJX731UBU5L9.exe (PID: 7544)
- Set-up.exe (PID: 7052)
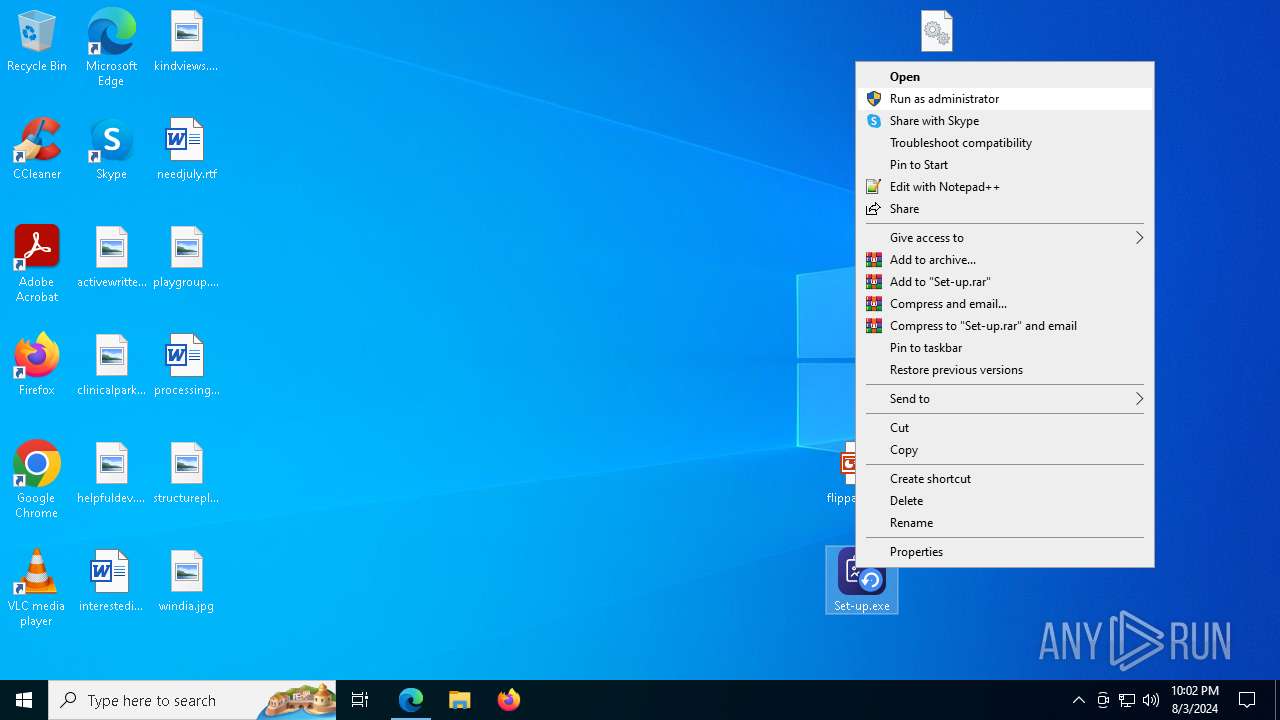
Starts application with an unusual extension
- Set-up.exe (PID: 9248)
- Set-up.exe (PID: 10196)
- Set-up.exe (PID: 6944)
- Set-up.exe (PID: 5632)
- Set-up.exe (PID: 7052)
Searches for installed software
- SearchIndexer.exe (PID: 3904)
- SearchIndexer.exe (PID: 8368)
The process executes Powershell scripts
- SearchIndexer.exe (PID: 3904)
- SearchIndexer.exe (PID: 8368)
Starts CMD.EXE for commands execution
- G87GNVRHHXSIL7AC.exe (PID: 9788)
- 43670DR1X0JHOMOUFMQCR6Y41.exe (PID: 9956)
Starts POWERSHELL.EXE for commands execution
- SearchIndexer.exe (PID: 3904)
- SearchIndexer.exe (PID: 8368)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 7364)
- powershell.exe (PID: 2468)
Extracts files to a directory (POWERSHELL)
- powershell.exe (PID: 7364)
- powershell.exe (PID: 2468)
Found regular expressions for crypto-addresses (YARA)
- MSBuild.exe (PID: 3904)
INFO
Reads Microsoft Office registry keys
- msedge.exe (PID: 6372)
- firefox.exe (PID: 3552)
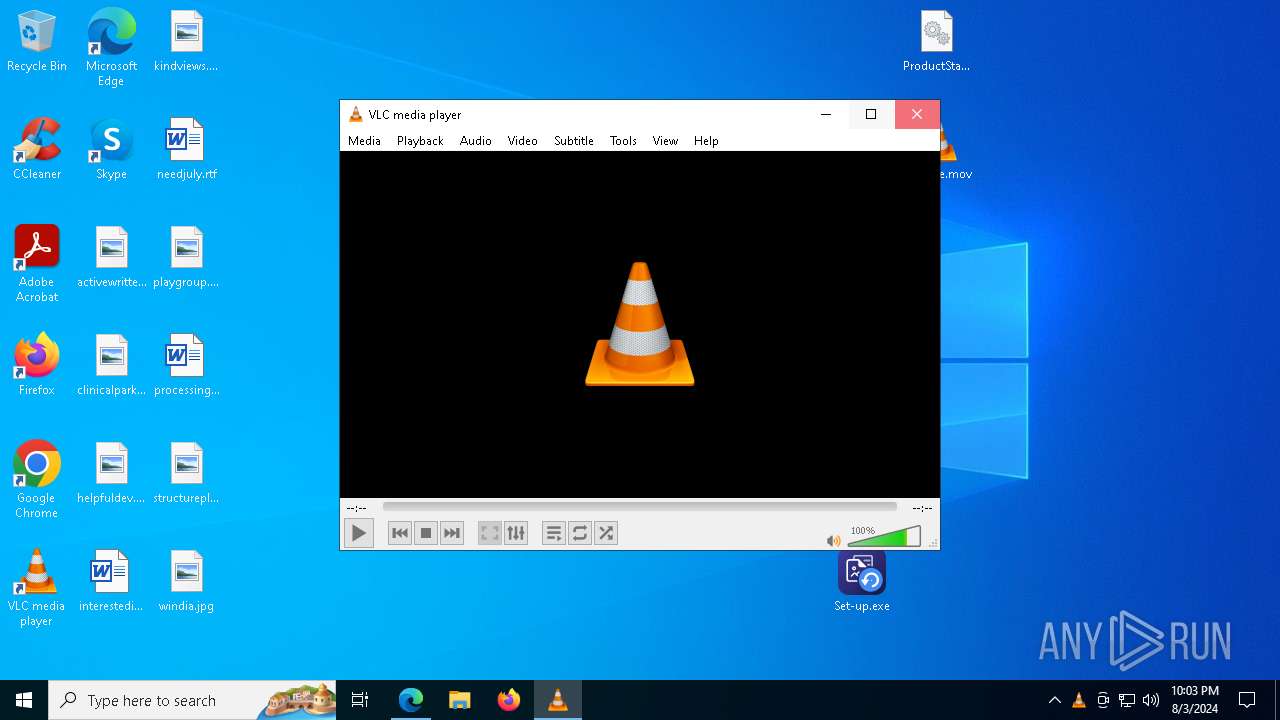
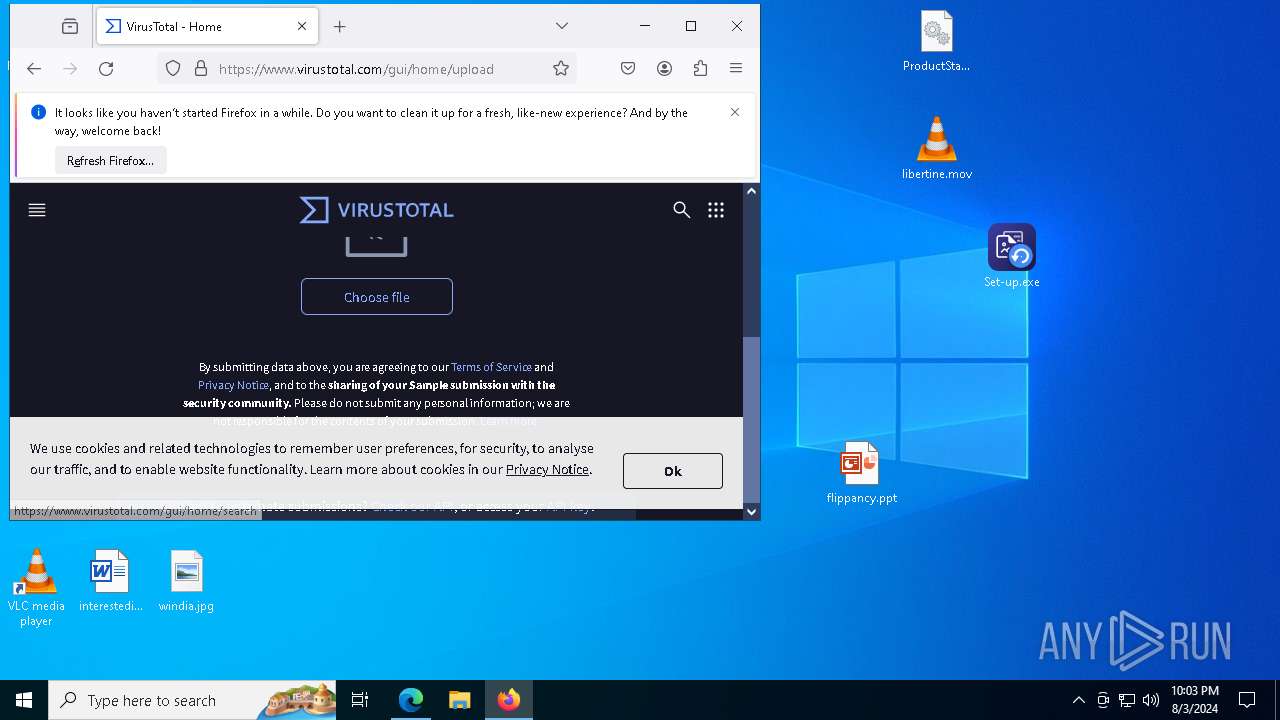
Manual execution by a user
- Set-up.exe (PID: 9248)
- Set-up.exe (PID: 10196)
- Set-up.exe (PID: 6944)
- vlc.exe (PID: 9228)
- Set-up.exe (PID: 10140)
- Set-up.exe (PID: 6236)
- Set-up.exe (PID: 5632)
- Set-up.exe (PID: 7044)
- firefox.exe (PID: 9564)
- Set-up.exe (PID: 7052)
Reads the computer name
- Set-up.exe (PID: 9248)
- identity_helper.exe (PID: 9336)
- StrCmp.exe (PID: 1452)
- more.com (PID: 9588)
- Set-up.exe (PID: 10196)
- more.com (PID: 9168)
- Set-up.exe (PID: 6944)
- Set-up.exe (PID: 5632)
- more.com (PID: 7048)
- more.com (PID: 300)
- Set-up.exe (PID: 10140)
- Set-up.exe (PID: 7044)
- vlc.exe (PID: 9228)
- G87GNVRHHXSIL7AC.exe (PID: 9788)
- TextInputHost.exe (PID: 9480)
- MN0ZYTFJX731UBU5L9.exe (PID: 7544)
- WL4I4ABF7N6K3OAKN2VMHN4QWY.exe (PID: 5500)
- 43670DR1X0JHOMOUFMQCR6Y41.exe (PID: 9956)
- Set-up.exe (PID: 7052)
- more.com (PID: 3980)
- Set-up.exe (PID: 6236)
Reads Environment values
- identity_helper.exe (PID: 9336)
Application launched itself
- msedge.exe (PID: 6372)
- firefox.exe (PID: 9564)
- firefox.exe (PID: 3552)
The process uses the downloaded file
- msedge.exe (PID: 1288)
- msedge.exe (PID: 6372)
- WinRAR.exe (PID: 8500)
Checks supported languages
- StrCmp.exe (PID: 1452)
- identity_helper.exe (PID: 9336)
- Set-up.exe (PID: 9248)
- more.com (PID: 9588)
- more.com (PID: 7048)
- more.com (PID: 9168)
- Set-up.exe (PID: 6944)
- Set-up.exe (PID: 5632)
- more.com (PID: 300)
- vlc.exe (PID: 9228)
- Set-up.exe (PID: 10140)
- Set-up.exe (PID: 7044)
- Set-up.exe (PID: 6236)
- Set-up.exe (PID: 10196)
- MN0ZYTFJX731UBU5L9.exe (PID: 7544)
- G87GNVRHHXSIL7AC.exe (PID: 9788)
- TextInputHost.exe (PID: 9480)
- 43670DR1X0JHOMOUFMQCR6Y41.exe (PID: 9956)
- WL4I4ABF7N6K3OAKN2VMHN4QWY.exe (PID: 5500)
- MSBuild.exe (PID: 3904)
- Set-up.exe (PID: 7052)
- more.com (PID: 3980)
- MSBuild.exe (PID: 9492)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 10140)
Creates files or folders in the user directory
- Set-up.exe (PID: 9248)
- MN0ZYTFJX731UBU5L9.exe (PID: 7544)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 10140)
- SearchIndexer.exe (PID: 3904)
- SearchIndexer.exe (PID: 8368)
Create files in a temporary directory
- more.com (PID: 9588)
- Set-up.exe (PID: 5632)
- Set-up.exe (PID: 6944)
- more.com (PID: 9168)
- more.com (PID: 7048)
- more.com (PID: 300)
- SearchIndexer.exe (PID: 3904)
- Set-up.exe (PID: 9248)
- Set-up.exe (PID: 10196)
- G87GNVRHHXSIL7AC.exe (PID: 9788)
- SearchIndexer.exe (PID: 8368)
- 43670DR1X0JHOMOUFMQCR6Y41.exe (PID: 9956)
- Set-up.exe (PID: 7052)
Reads the software policy settings
- SearchIndexer.exe (PID: 3904)
- SearchIndexer.exe (PID: 8368)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7364)
- powershell.exe (PID: 2468)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7364)
- powershell.exe (PID: 2468)
Reads the machine GUID from the registry
- MN0ZYTFJX731UBU5L9.exe (PID: 7544)
- WL4I4ABF7N6K3OAKN2VMHN4QWY.exe (PID: 5500)
.NET Reactor protector has been detected
- MN0ZYTFJX731UBU5L9.exe (PID: 7544)
Creates files in the program directory
- MSBuild.exe (PID: 3904)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Lumma
(PID) Process(8368) SearchIndexer.exe
C2 (9)boattyownerwrv.shop
definitonizmnx.shop
assumedtribsosp.shop
chippyfroggsyhz.shop
budgetttysnzm.shop
creepydxzoxmj.shop
elephanntys.shop
empiredzmwnx.shop
rainbowmynsjn.shop
Total processes
270
Monitored processes
132
Malicious processes
10
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 32 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=2296 -parentBuildID 20240213221259 -prefsHandle 2288 -prefMapHandle 2284 -prefsLen 30537 -prefMapSize 244343 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {2a83b262-a392-40cb-a893-139c6ffbf432} 3552 "\\.\pipe\gecko-crash-server-pipe.3552" 213c1680510 socket | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 300 | C:\WINDOWS\SysWOW64\more.com | C:\Windows\SysWOW64\more.com | — | Set-up.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: More Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 304 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_xpay_wallet.mojom.EdgeXPayWalletService --lang=en-US --service-sandbox-type=utility --no-appcompat-clear --mojo-platform-channel-handle=5260 --field-trial-handle=2344,i,3301618997404443290,1377699098985545605,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 888 | C:\WINDOWS\SysWOW64\SearchIndexer.exe | C:\Windows\SysWOW64\SearchIndexer.exe | — | more.com | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Windows Search Indexer Exit code: 0 Version: 7.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1236 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=1904 -parentBuildID 20240213221259 -prefsHandle 1816 -prefMapHandle 1580 -prefsLen 30537 -prefMapSize 244343 -appDir "C:\Program Files\Mozilla Firefox\browser" - {6d704d54-4cd4-43e3-9ebf-d972ce2e9a7d} 3552 "\\.\pipe\gecko-crash-server-pipe.3552" 213ce1e3e10 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 1 Version: 123.0 Modules
| |||||||||||||||
| 1288 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=7736 --field-trial-handle=2344,i,3301618997404443290,1377699098985545605,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1452 | C:\Users\admin\AppData\Roaming\SWBarchive\VJMFEXWCSVUMHLXGDV\StrCmp.exe | C:\Users\admin\AppData\Roaming\SWBarchive\VJMFEXWCSVUMHLXGDV\StrCmp.exe | — | Set-up.exe | |||||||||||
User: admin Company: aaa Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 1692 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=11464 --field-trial-handle=2344,i,3301618997404443290,1377699098985545605,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1700 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5456 -parentBuildID 20240213221259 -sandboxingKind 0 -prefsHandle 5432 -prefMapHandle 5448 -prefsLen 36339 -prefMapSize 244343 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {09119ba2-79a8-4e28-8395-7c1566a934ab} 3552 "\\.\pipe\gecko-crash-server-pipe.3552" 213d3b59f10 utility | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 1 Version: 123.0 Modules
| |||||||||||||||
| 2180 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5512 --field-trial-handle=2344,i,3301618997404443290,1377699098985545605,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
59 658
Read events
59 330
Write events
324
Delete events
4
Modification events
| (PID) Process: | (6372) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6372) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6372) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (6372) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (6372) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6372) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (6372) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6372) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge |
| Operation: | write | Name: | UsageStatsInSample |
Value: 1 | |||
| (PID) Process: | (6372) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: C2EFBCDF647D2F00 | |||
| (PID) Process: | (6372) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
18
Suspicious files
402
Text files
136
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RFe48eb.TMP | — | |
MD5:— | SHA256:— | |||
| 6372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RFe48eb.TMP | — | |
MD5:— | SHA256:— | |||
| 6372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RFe48fb.TMP | — | |
MD5:— | SHA256:— | |||
| 6372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RFe491a.TMP | — | |
MD5:— | SHA256:— | |||
| 6372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RFe493a.TMP | — | |
MD5:— | SHA256:— | |||
| 6372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
61
TCP/UDP connections
444
DNS requests
529
Threats
32
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4168 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4292 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6712 | msedge.exe | GET | 200 | 192.229.221.95:80 | http://cacerts.rapidssl.com/RapidSSLTLSRSACAG1.crt | unknown | — | — | whitelisted |
6220 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
7156 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/369e8e41-5ce3-4eb8-9826-427d58ae27b0?P1=1723185666&P2=404&P3=2&P4=C7nILby69gmSvnvOXnqwDvY6kjyn329M%2fRdSXdi6mWk5Hbhx63v7E%2fk4gV%2f5lgbC2r6gZTo4Ja1%2fVFpyzLUlRQ%3d%3d | unknown | — | — | whitelisted |
7156 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/369e8e41-5ce3-4eb8-9826-427d58ae27b0?P1=1723185666&P2=404&P3=2&P4=C7nILby69gmSvnvOXnqwDvY6kjyn329M%2fRdSXdi6mWk5Hbhx63v7E%2fk4gV%2f5lgbC2r6gZTo4Ja1%2fVFpyzLUlRQ%3d%3d | unknown | — | — | whitelisted |
7156 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/369e8e41-5ce3-4eb8-9826-427d58ae27b0?P1=1723185666&P2=404&P3=2&P4=C7nILby69gmSvnvOXnqwDvY6kjyn329M%2fRdSXdi6mWk5Hbhx63v7E%2fk4gV%2f5lgbC2r6gZTo4Ja1%2fVFpyzLUlRQ%3d%3d | unknown | — | — | whitelisted |
7156 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/369e8e41-5ce3-4eb8-9826-427d58ae27b0?P1=1723185666&P2=404&P3=2&P4=C7nILby69gmSvnvOXnqwDvY6kjyn329M%2fRdSXdi6mWk5Hbhx63v7E%2fk4gV%2f5lgbC2r6gZTo4Ja1%2fVFpyzLUlRQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3268 | RUXIMICS.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
2120 | MoUsoCoreWorker.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4084 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6712 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6372 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6712 | msedge.exe | 188.114.97.3:443 | hostingfile.live | — | — | unknown |
6712 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
hostingfile.live |
| unknown |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
zipfilemediafree.xyz |
| unknown |
www.bing.com |
| whitelisted |
xpaywalletcdn.azureedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
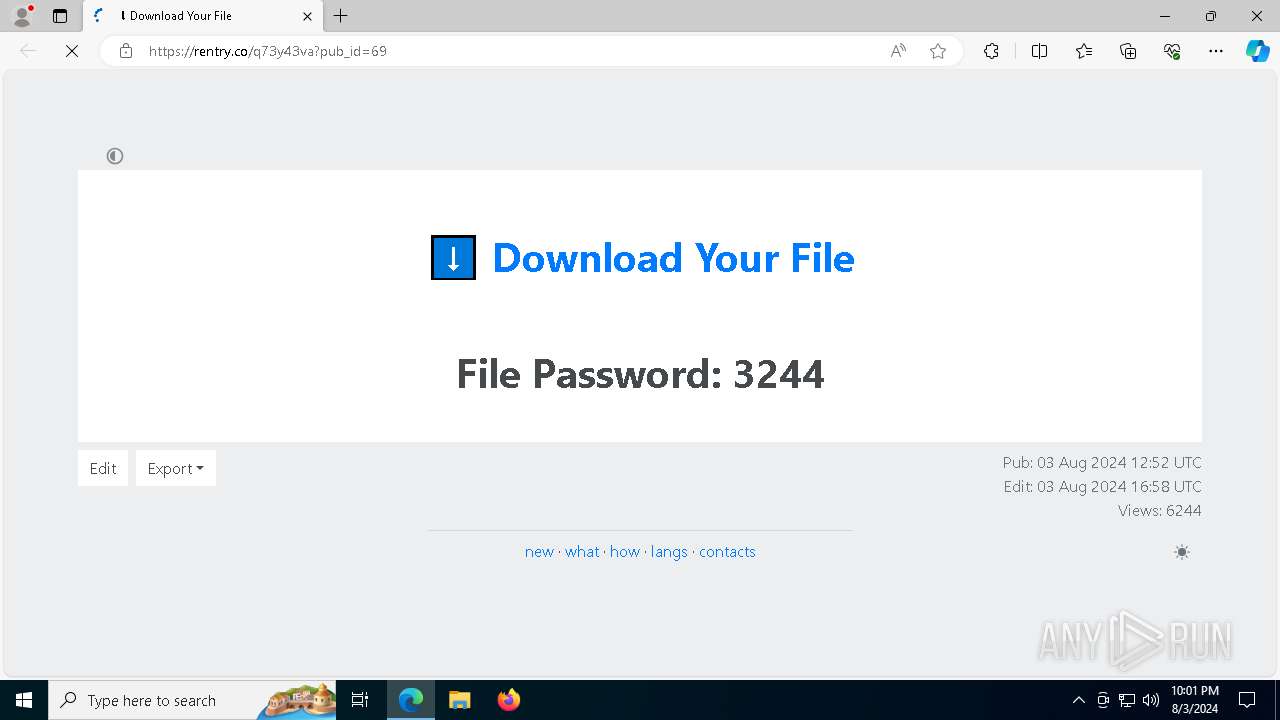
6712 | msedge.exe | Misc activity | ET INFO Observed Pastebin Service Domain (rentry .co in TLS SNI) |
6712 | msedge.exe | Misc activity | ET INFO Pastebin Service Domain in DNS Lookup (rentry .co) |
6712 | msedge.exe | Misc activity | ET INFO Observed Pastebin Service Domain (rentry .co in TLS SNI) |
6712 | msedge.exe | Misc activity | ET INFO Pastebin Service Domain in DNS Lookup (rentry .co) |
6712 | msedge.exe | Misc activity | ET INFO Pastebin Service Domain in DNS Lookup (rentry .co) |
6712 | msedge.exe | Misc activity | ET INFO Observed Pastebin Service Domain (rentry .co in TLS SNI) |
6712 | msedge.exe | Misc activity | ET INFO Pastebin Service Domain in DNS Lookup (rentry .co) |
6712 | msedge.exe | Misc activity | ET INFO Observed Pastebin Service Domain (rentry .co in TLS SNI) |
6712 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
6712 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
Process | Message |
|---|---|
vlc.exe | main libvlc debug: VLC media player - 3.0.11 Vetinari
|
vlc.exe | main libvlc debug: Copyright © 1996-2020 the VideoLAN team
|
vlc.exe | main libvlc debug: revision 3.0.11-0-gdc0c5ced72
|
vlc.exe | main libvlc debug: configured with ../extras/package/win32/../../../configure '--enable-update-check' '--enable-lua' '--enable-faad' '--enable-flac' '--enable-theora' '--enable-avcodec' '--enable-merge-ffmpeg' '--enable-dca' '--enable-mpc' '--enable-libass' '--enable-schroedinger' '--enable-realrtsp' '--enable-live555' '--enable-dvdread' '--enable-shout' '--enable-goom' '--enable-caca' '--enable-qt' '--enable-skins2' '--enable-sse' '--enable-mmx' '--enable-libcddb' '--enable-zvbi' '--disable-telx' '--enable-nls' '--host=x86_64-w64-mingw32' '--with-breakpad=https://win.crashes.videolan.org' 'host_alias=x86_64-w64-mingw32' 'PKG_CONFIG_LIBDIR=/home/jenkins/workspace/vlc-release/windows/vlc-release-win32-x64/contrib/x86_64-w64-mingw32/lib/pkgconfig'
|
vlc.exe | main libvlc debug: using multimedia timers as clock source
|
vlc.exe | main libvlc debug: min period: 1 ms, max period: 1000000 ms
|
vlc.exe | main libvlc debug: searching plug-in modules
|
vlc.exe | main libvlc debug: loading plugins cache file C:\Program Files\VideoLAN\VLC\plugins\plugins.dat
|
vlc.exe | main libvlc debug: recursively browsing `C:\Program Files\VideoLAN\VLC\plugins'
|
vlc.exe | main libvlc debug: plug-ins loaded: 494 modules
|