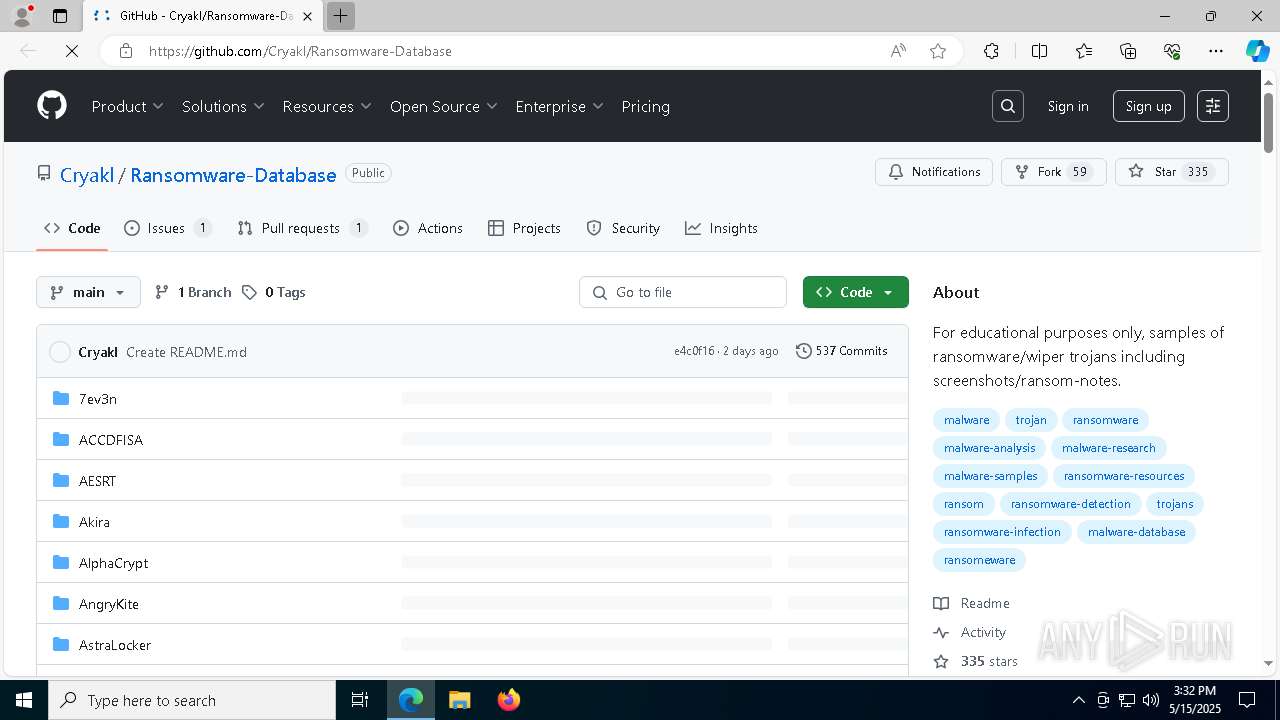
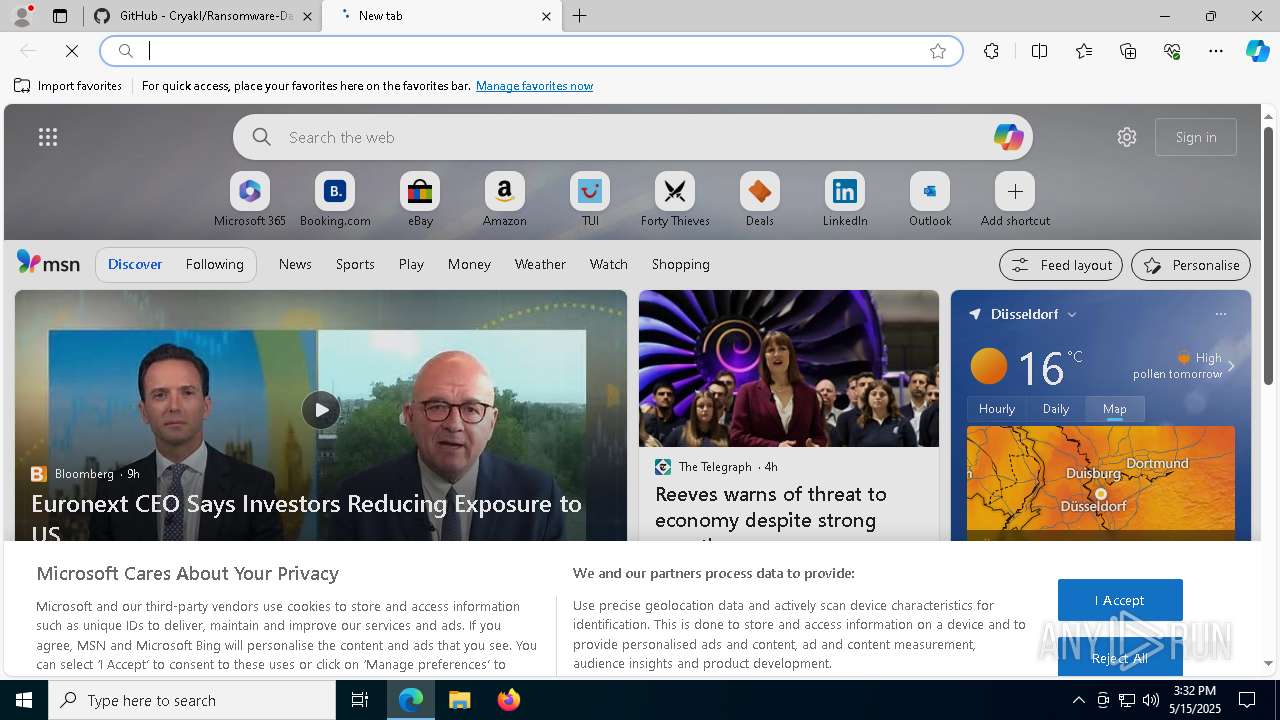
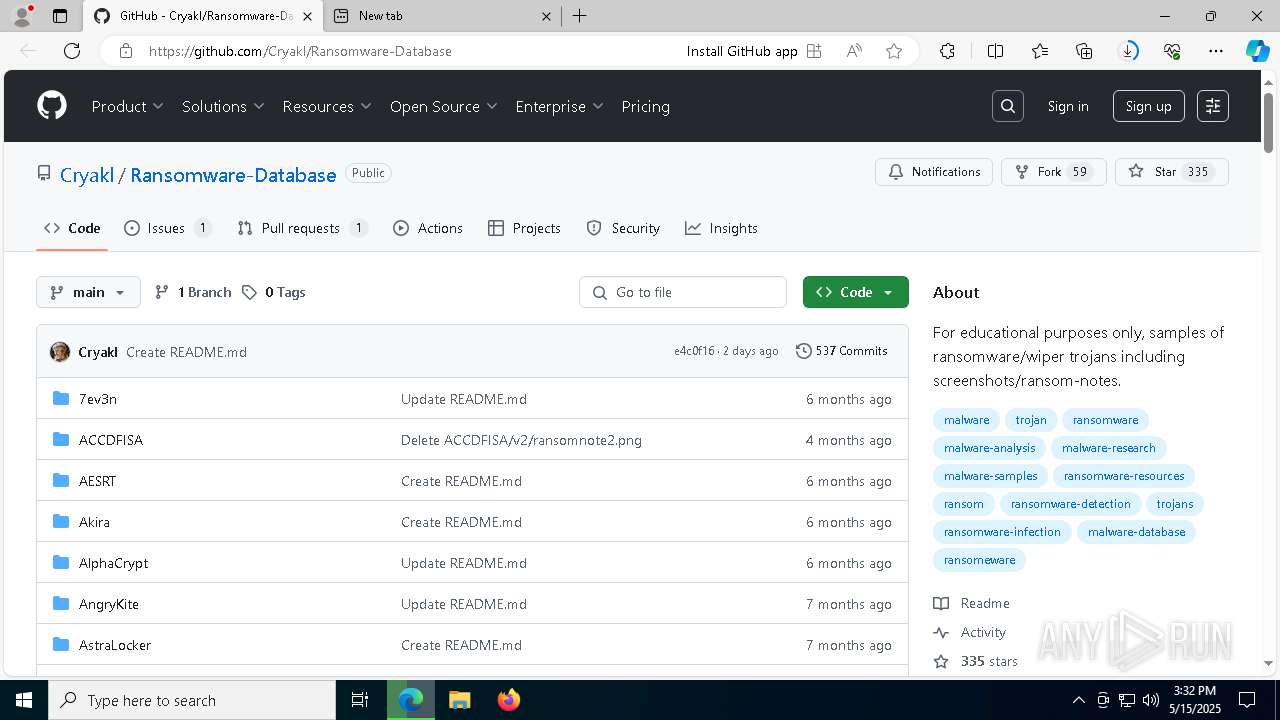
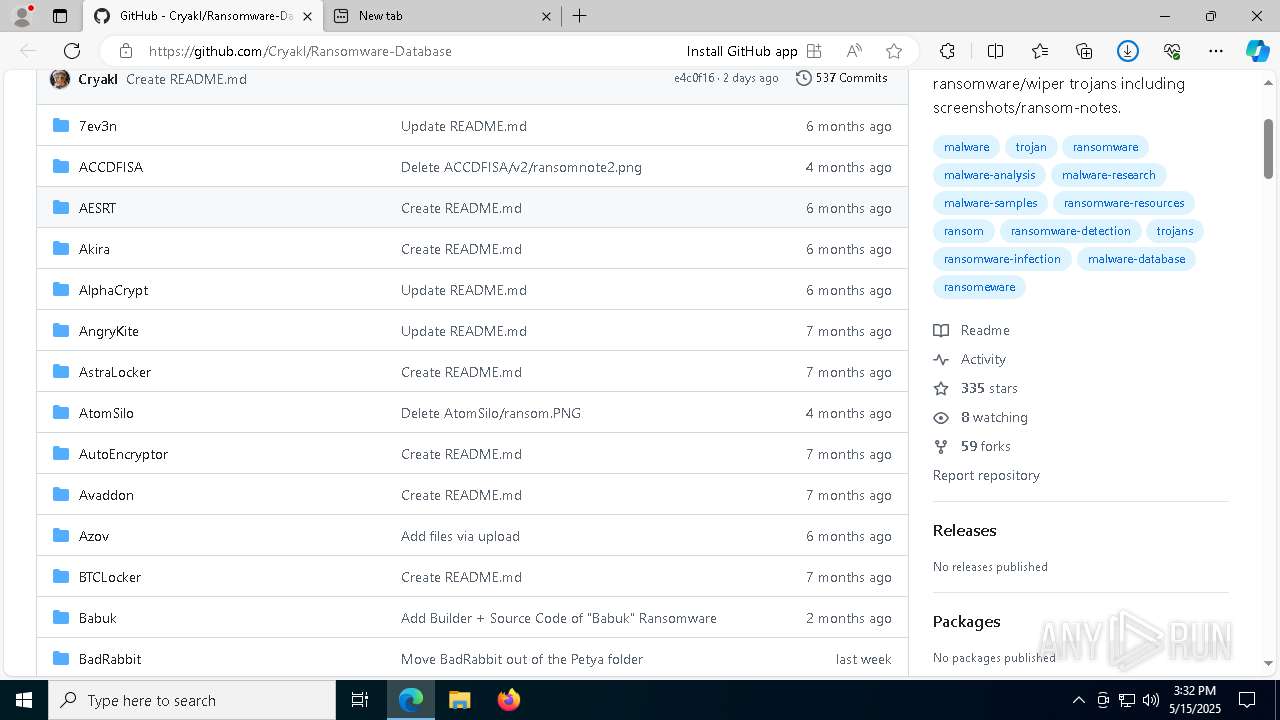
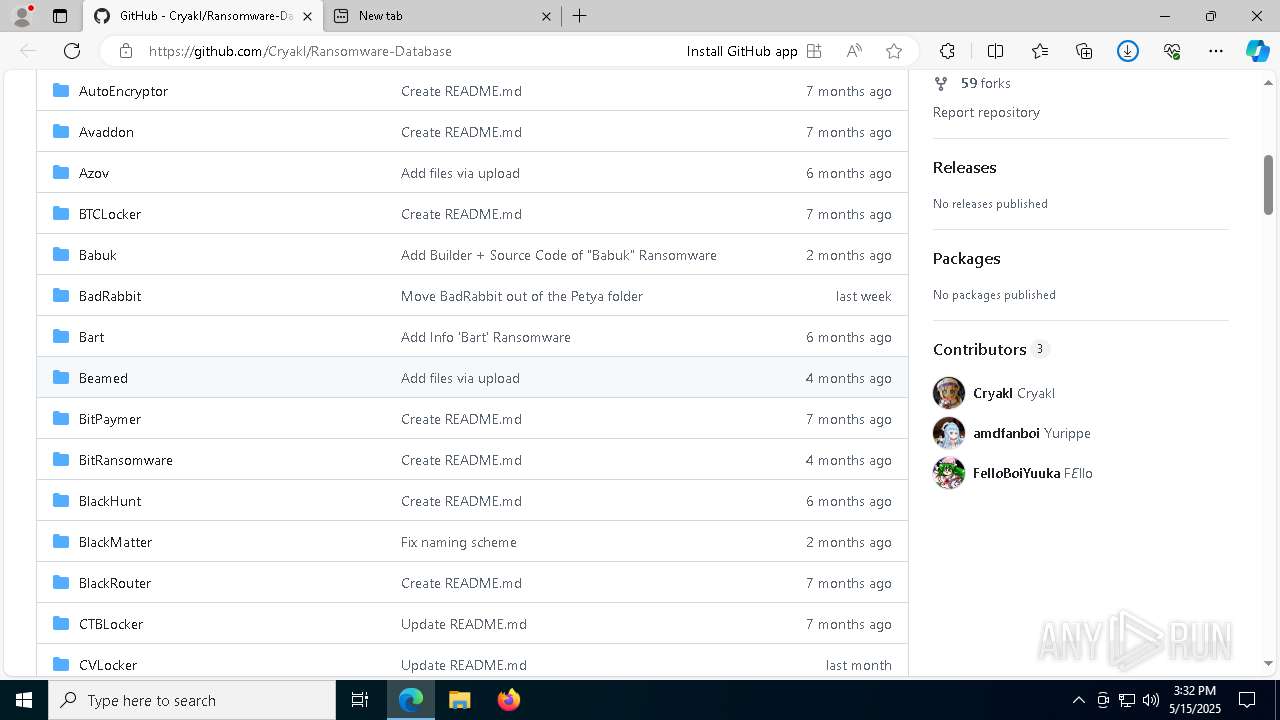
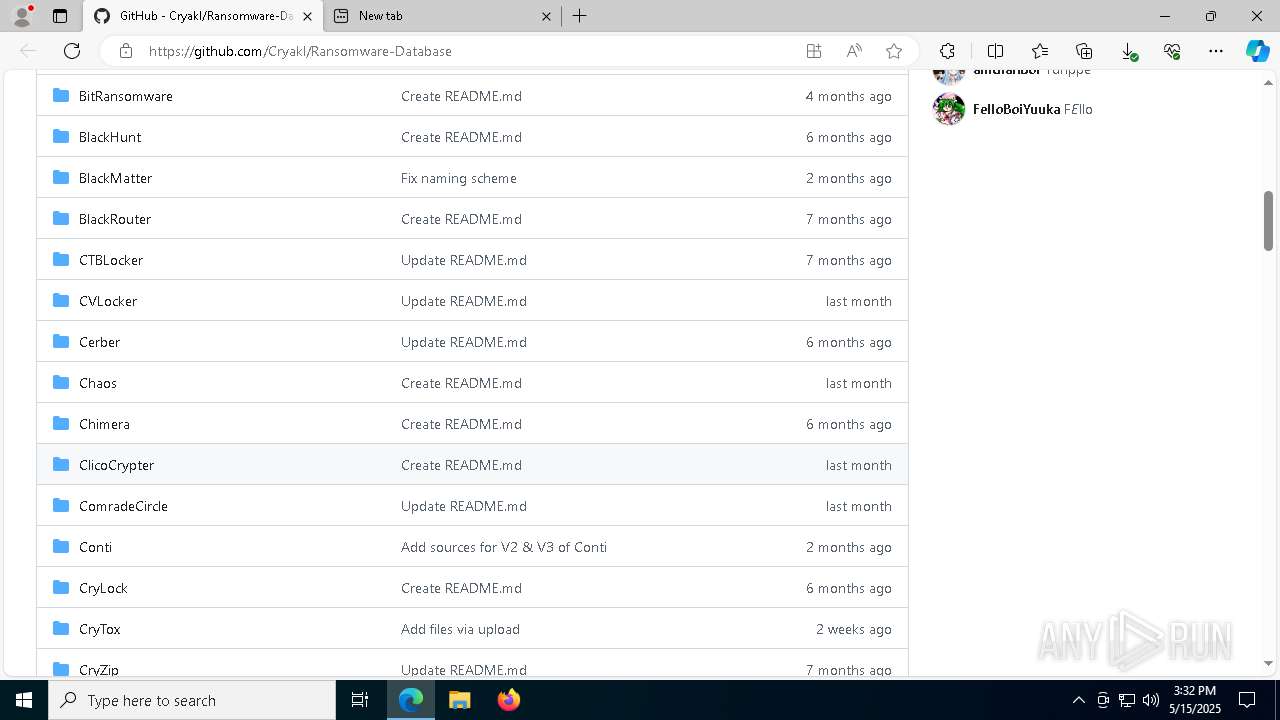
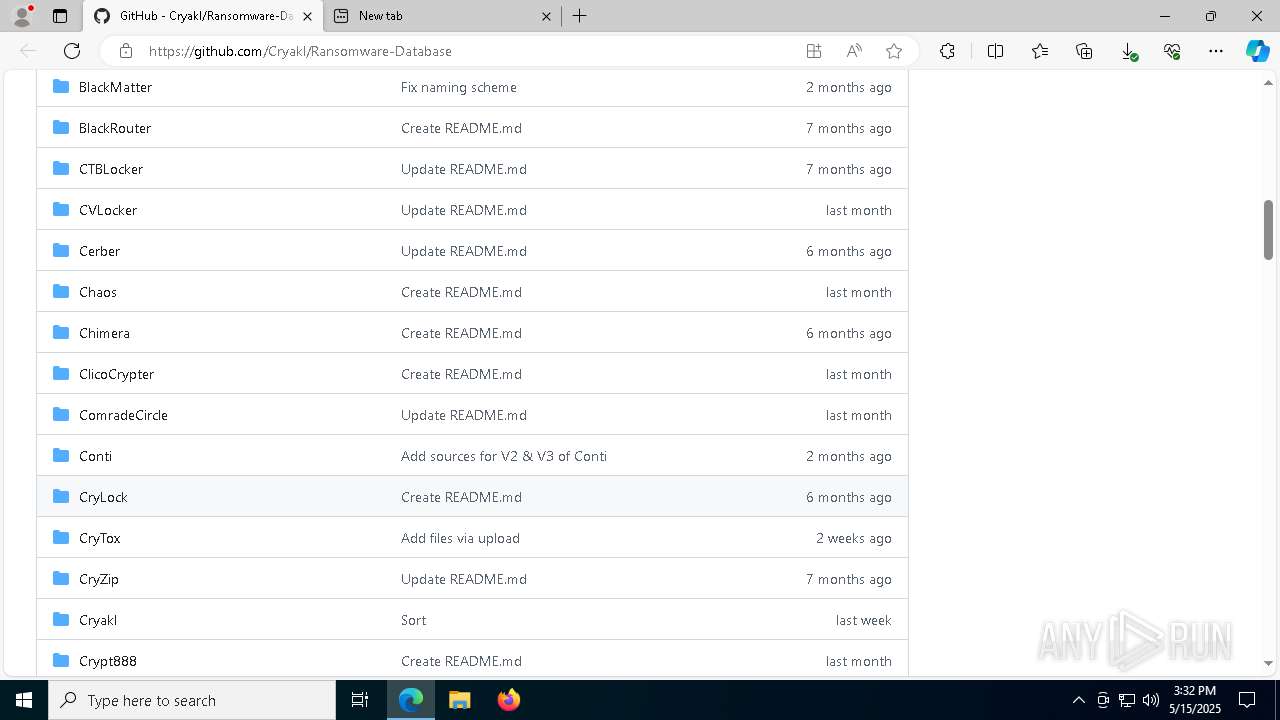
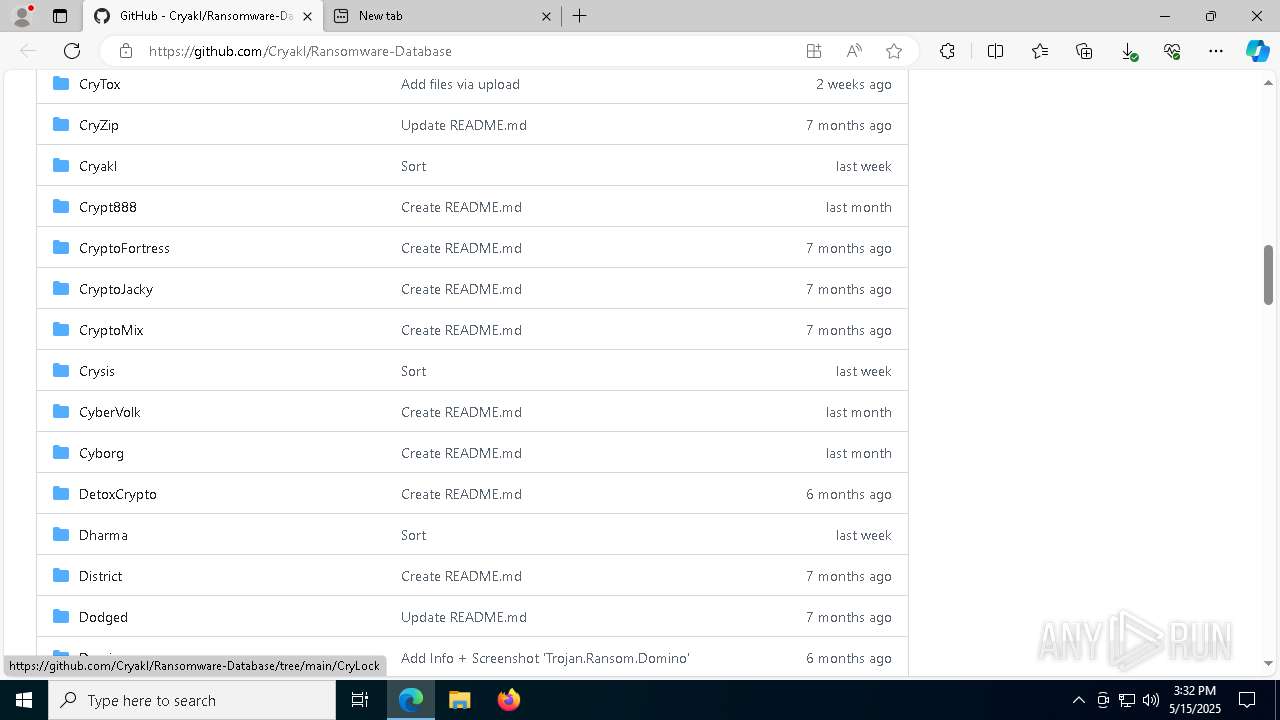
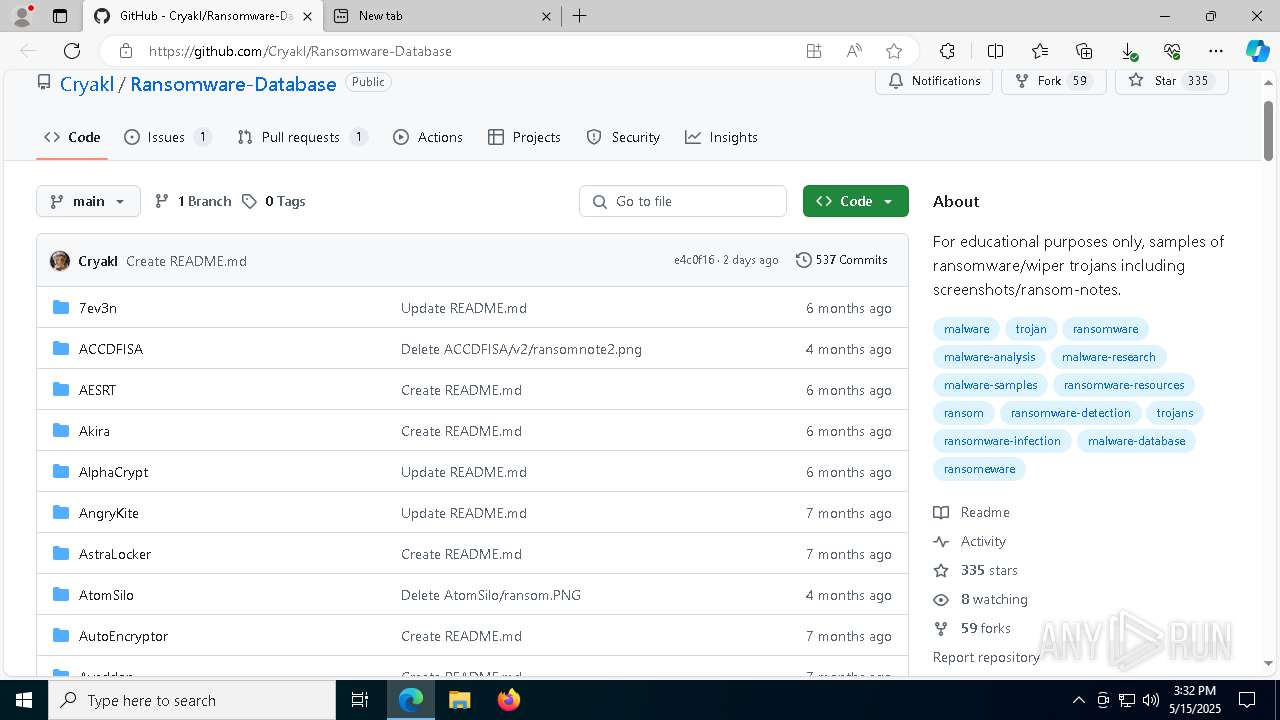
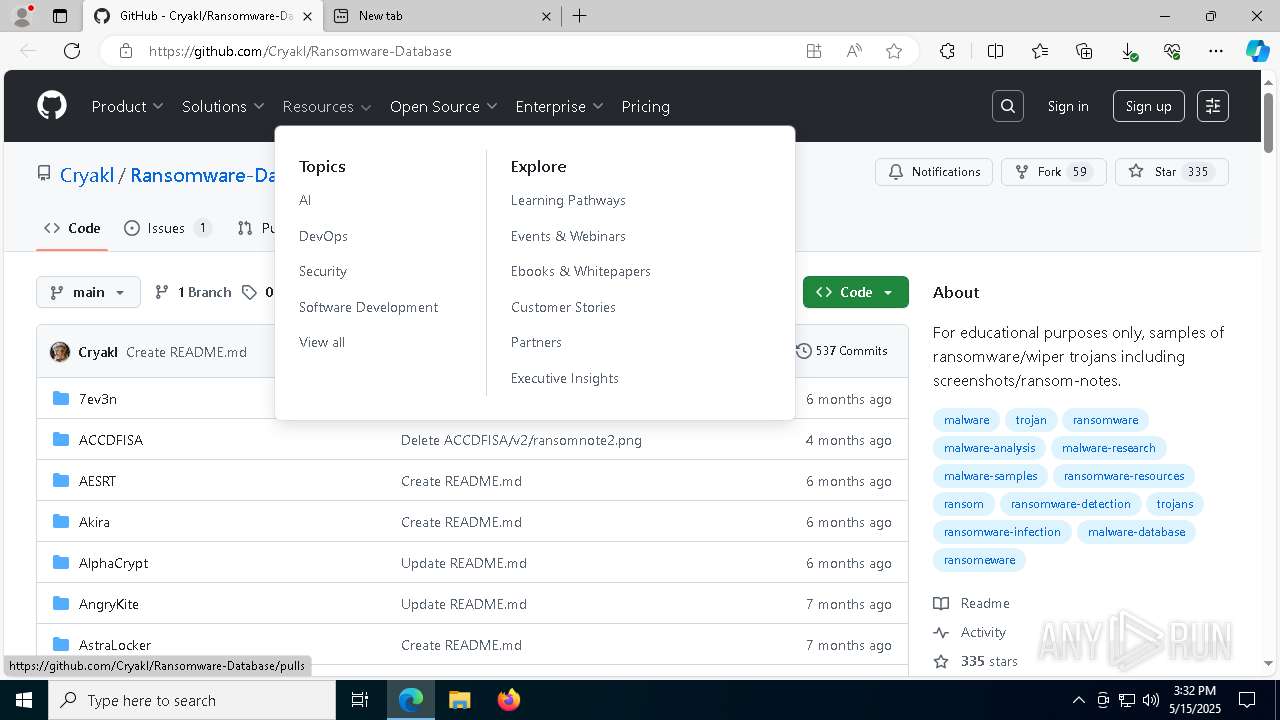
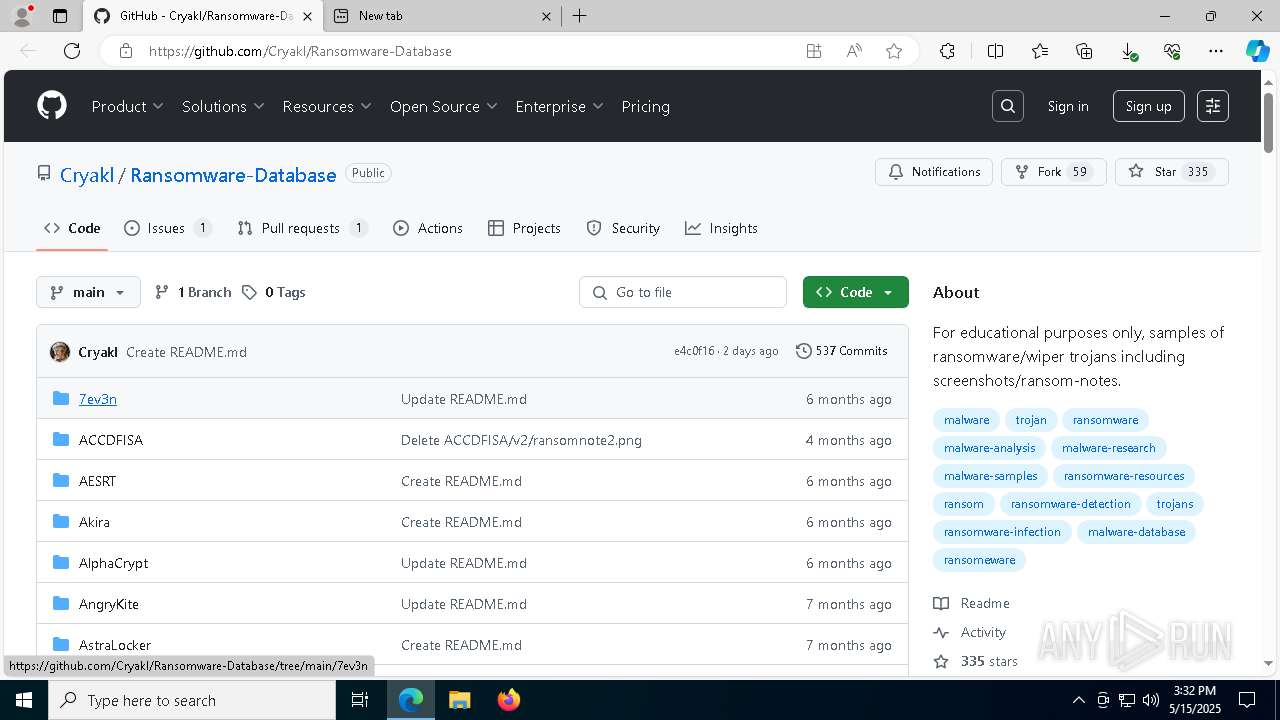
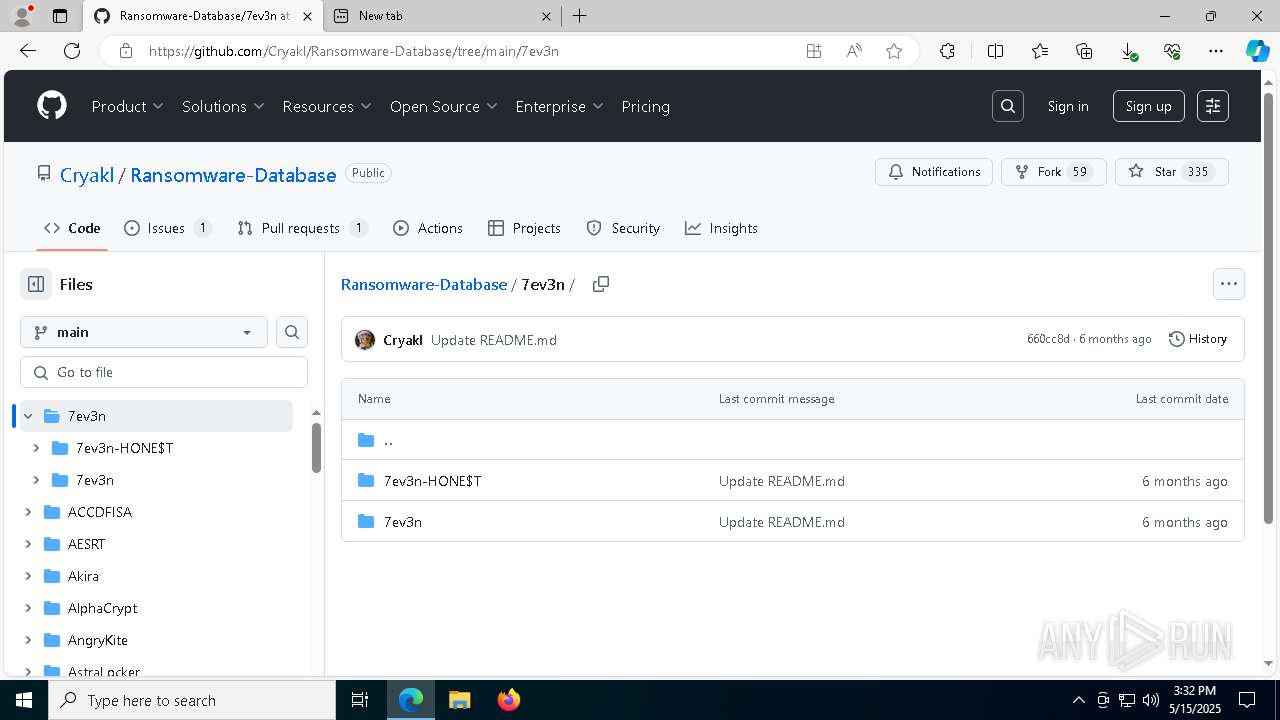
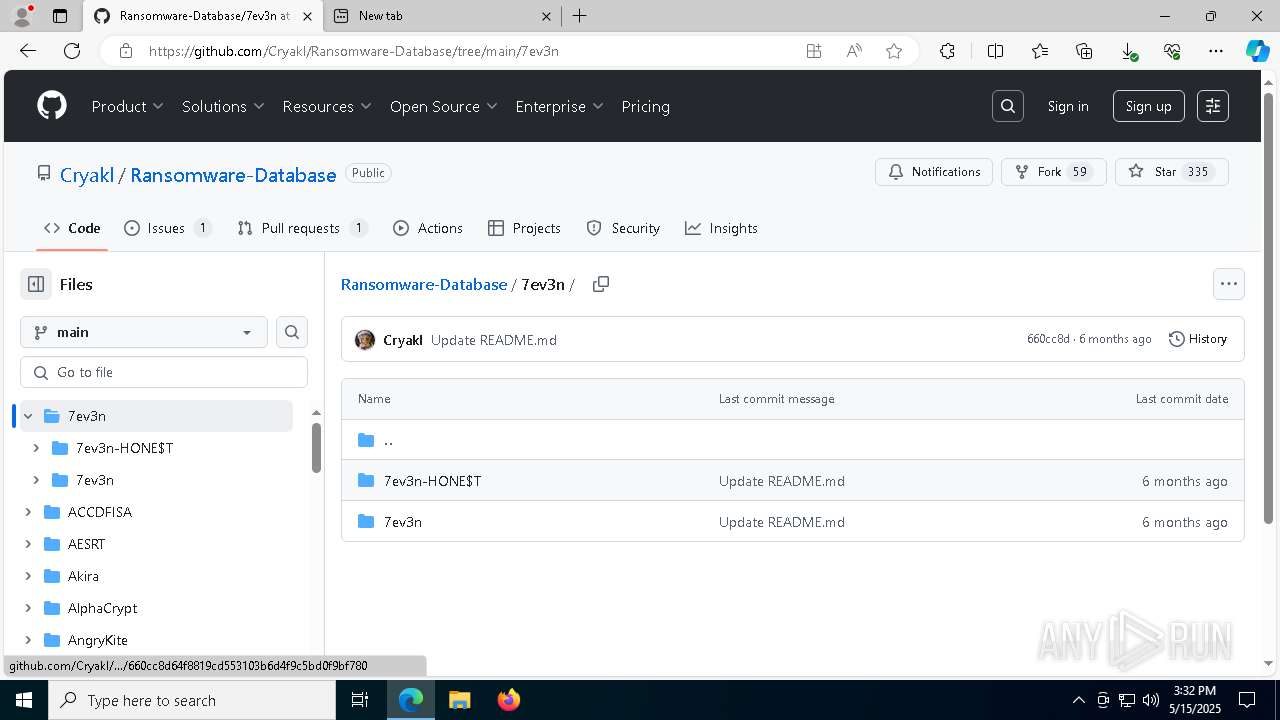
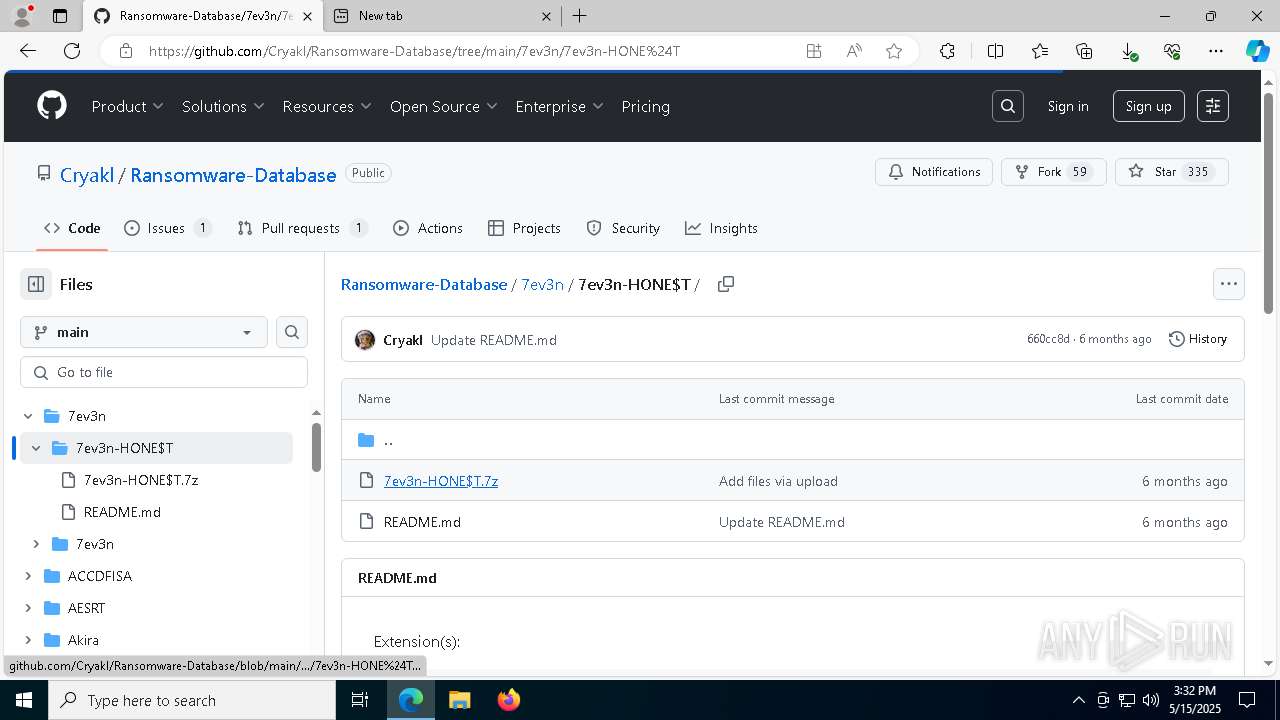
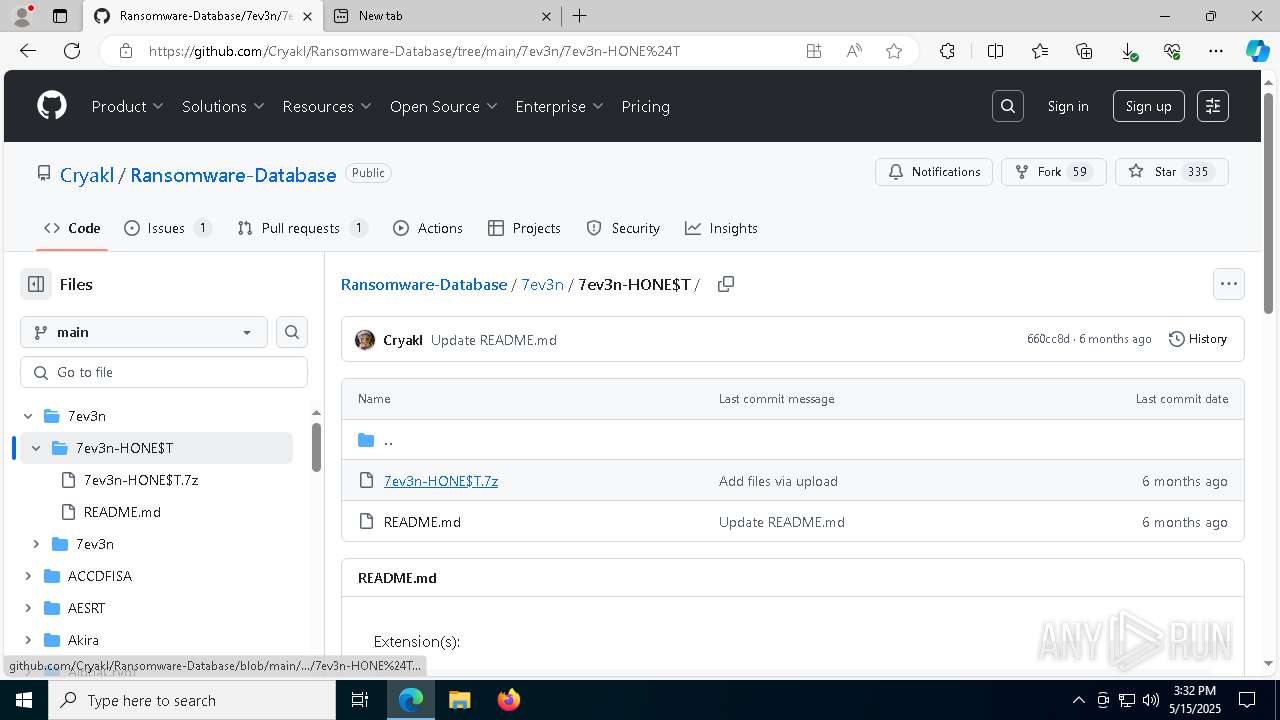
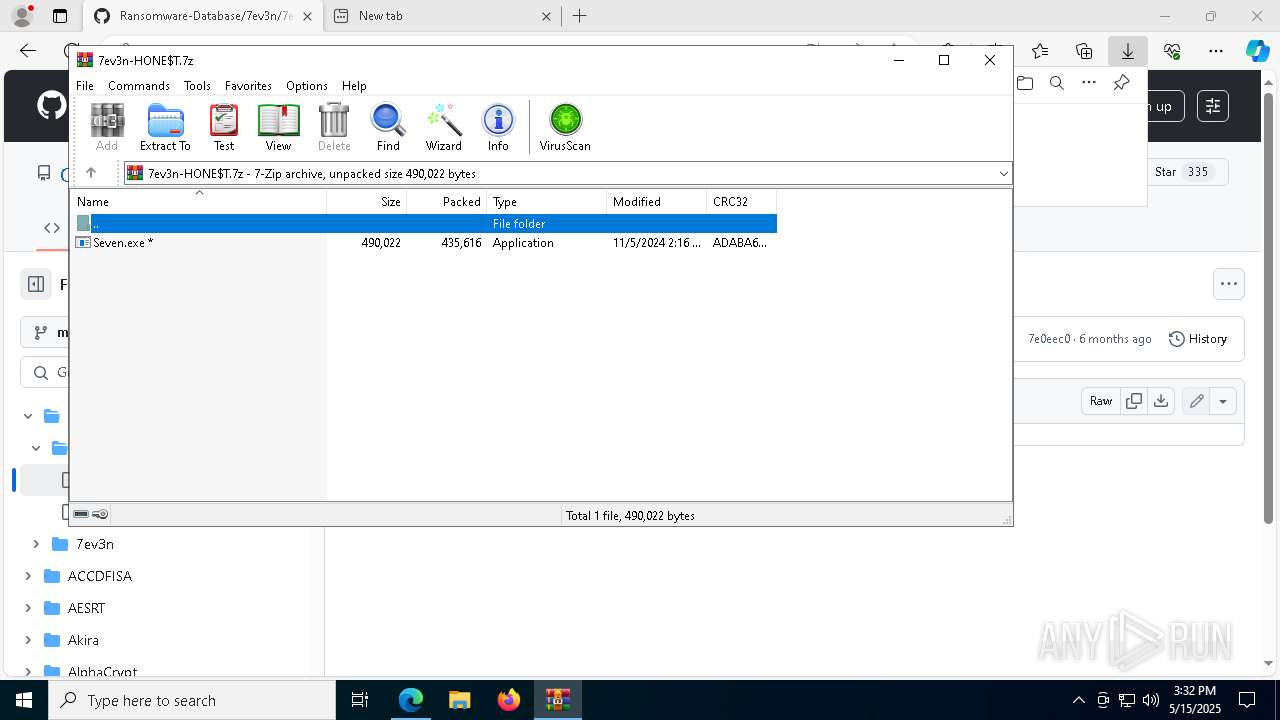
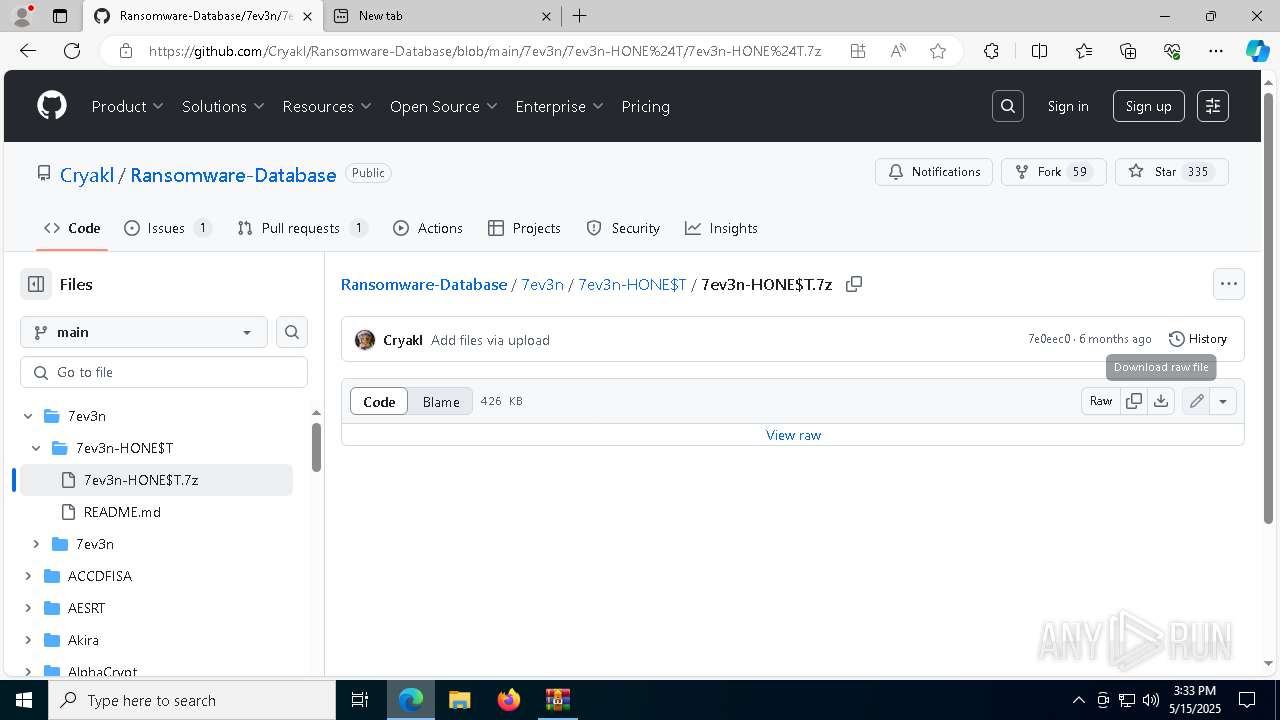
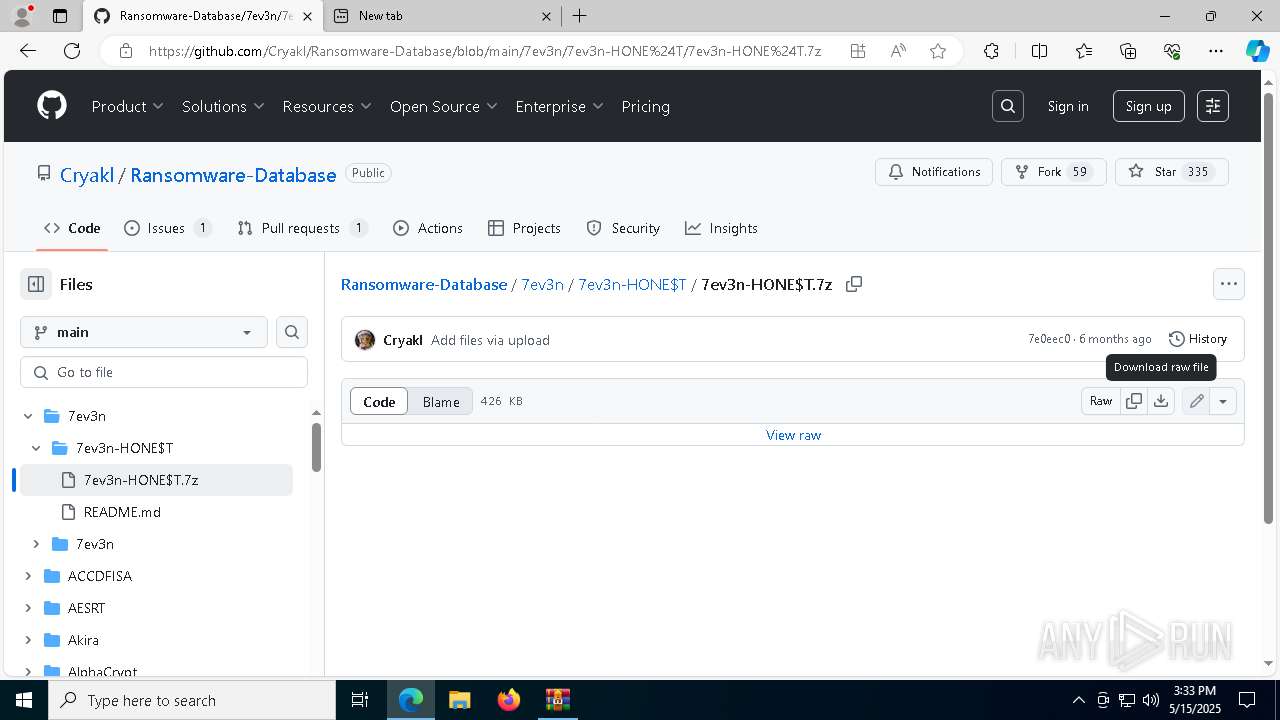
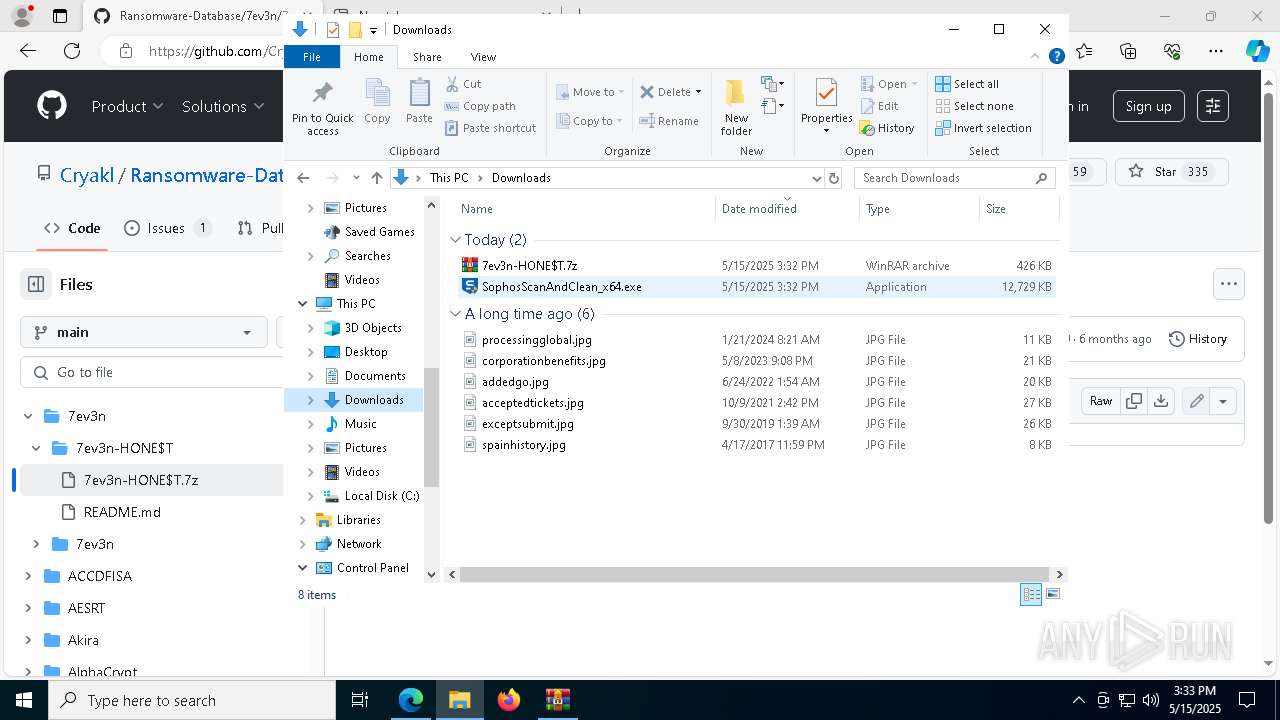
| URL: | https://github.com/Cryakl/Ransomware-Database |
| Full analysis: | https://app.any.run/tasks/33f41f7b-bfeb-4082-aca5-22beb58292e5 |
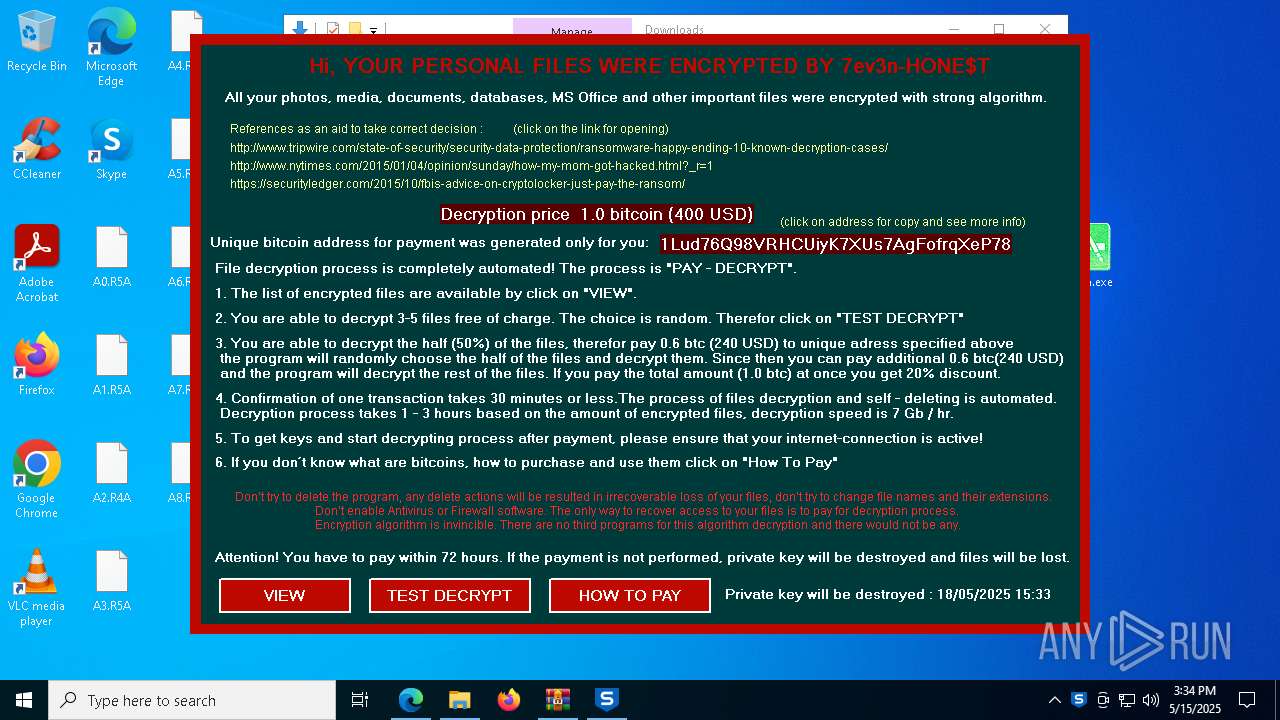
| Verdict: | Malicious activity |
| Threats: | WarZone RAT is a remote access trojan, which is written in C++ and offered as a malware-as-a-service. It packs a wide range of capabilities, from stealing victims’ files and passwords to capturing desktop activities. WarZone RAT is primarily distributed via phishing emails and receives regular updates from its C2. |
| Analysis date: | May 15, 2025, 15:32:06 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 48822409D7D56E68EA5BAD4F921C232C |
| SHA1: | 32806BF6750F505BB5B6FFF266E289C11C23506B |
| SHA256: | 20F7D194C032C497EF9AC6A8344DFD46F2A0E026B684A783BA9F4A4D2177FD85 |
| SSDEEP: | 3:N8tEdJE3EIIREHI:2uPehIkI |
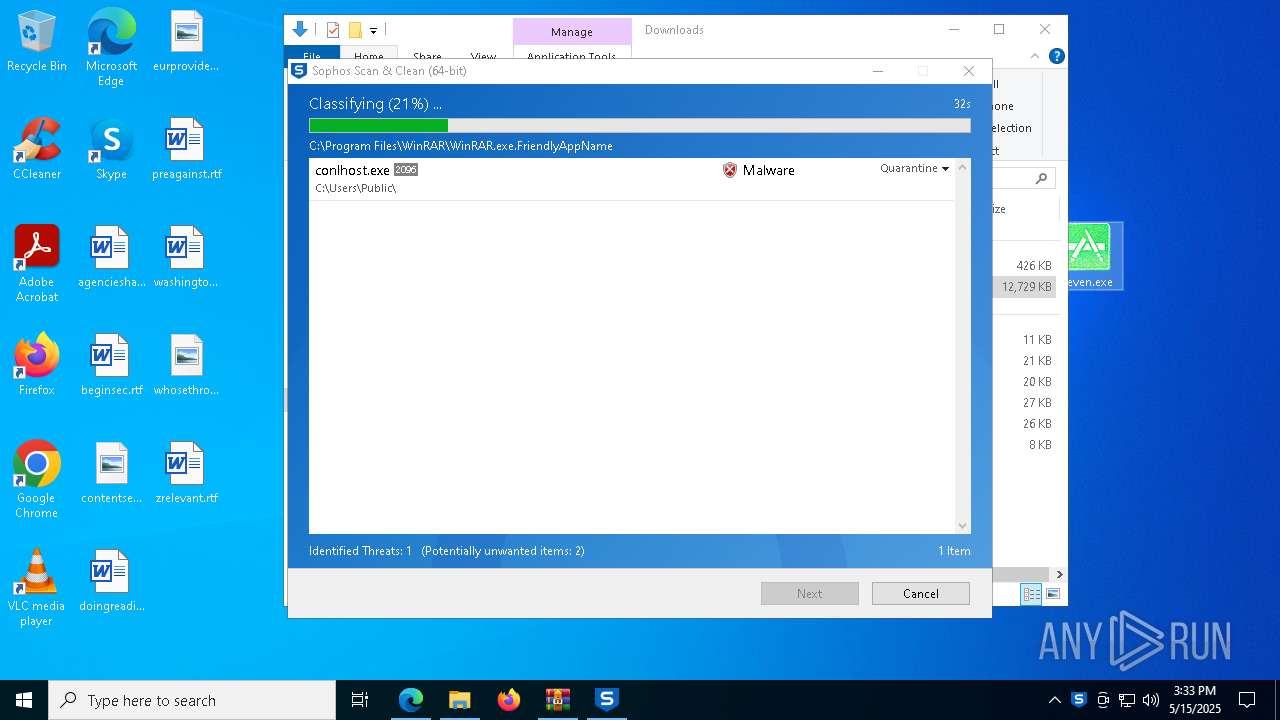
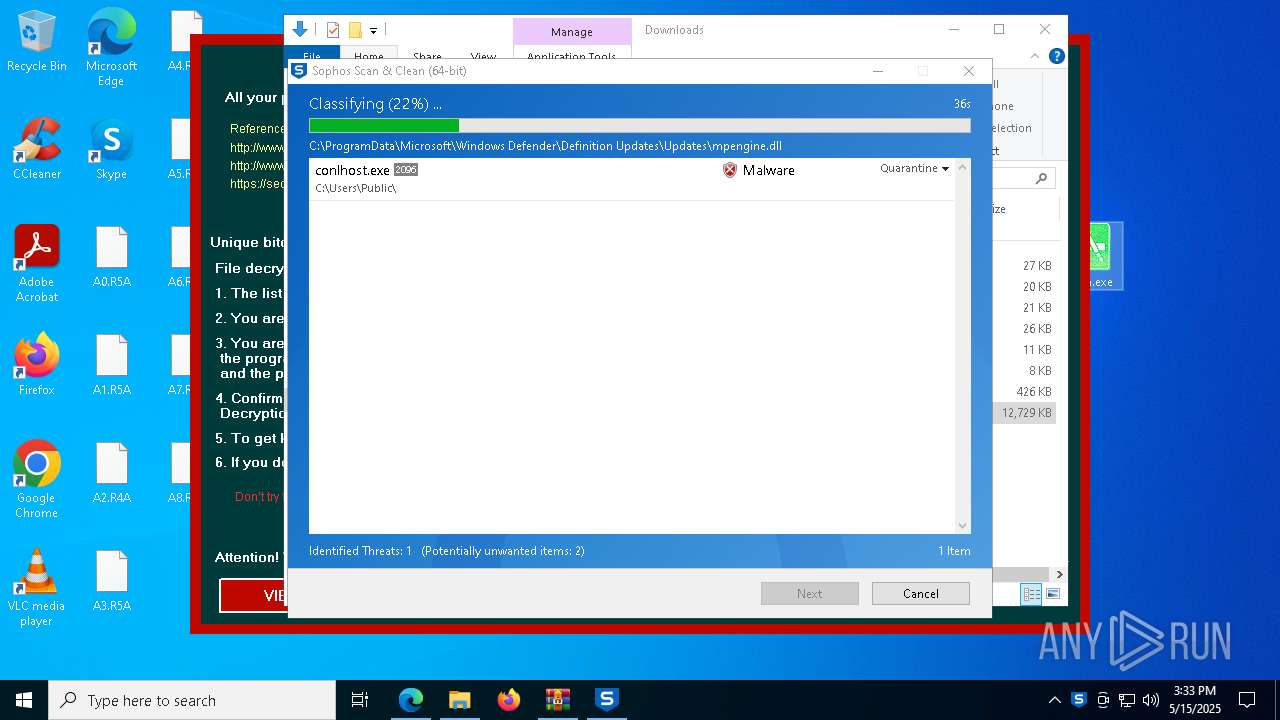
MALICIOUS
AVEMARIA mutex has been found
- Seven.exe (PID: 7500)
SUSPICIOUS
Creates file in the systems drive root
- Seven.exe (PID: 7500)
Application launched itself
- Seven.exe (PID: 7500)
- conlhost.exe (PID: 2096)
- Seven.exe (PID: 4572)
- Seven.exe (PID: 7864)
The process creates files with name similar to system file names
- Seven.exe (PID: 1180)
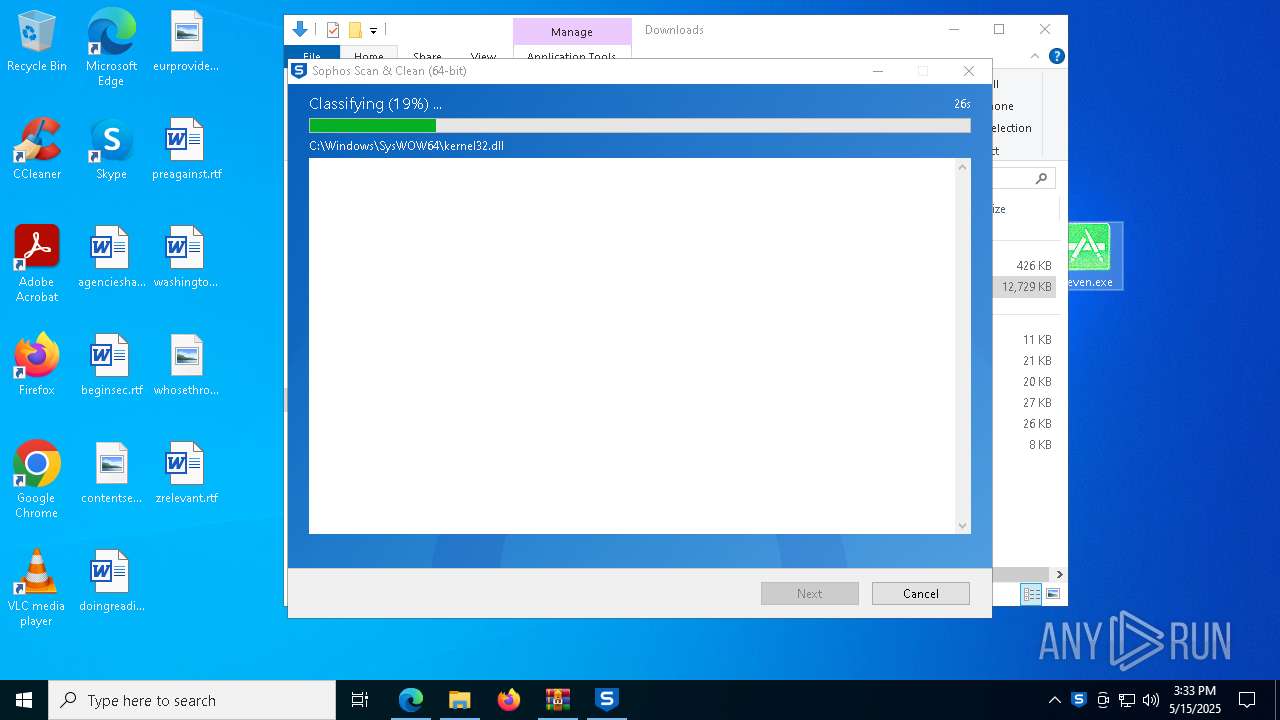
Executable content was dropped or overwritten
- Seven.exe (PID: 1180)
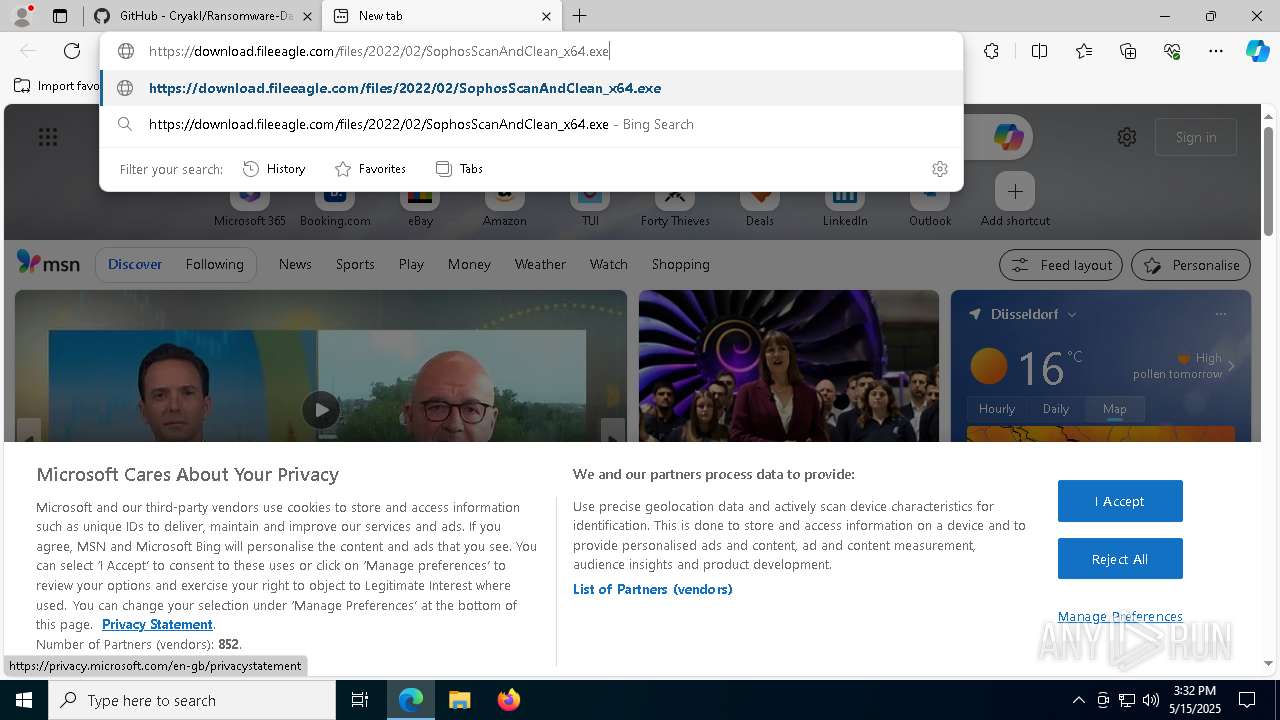
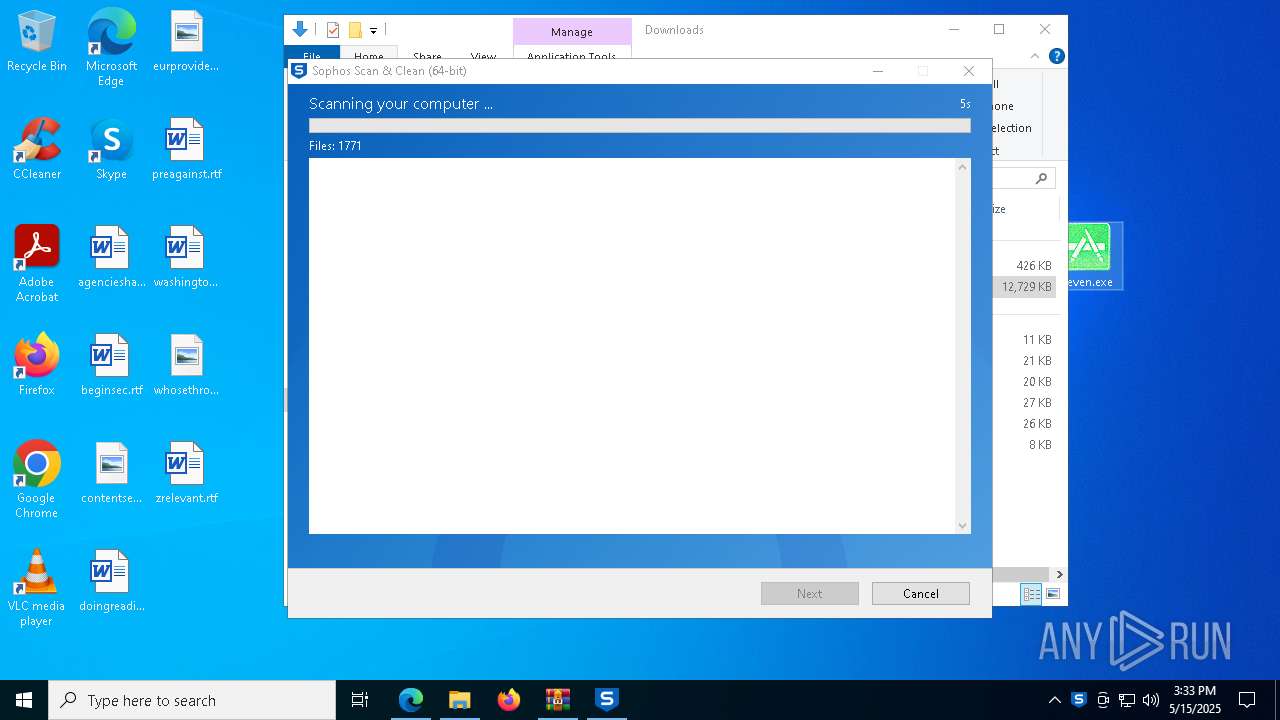
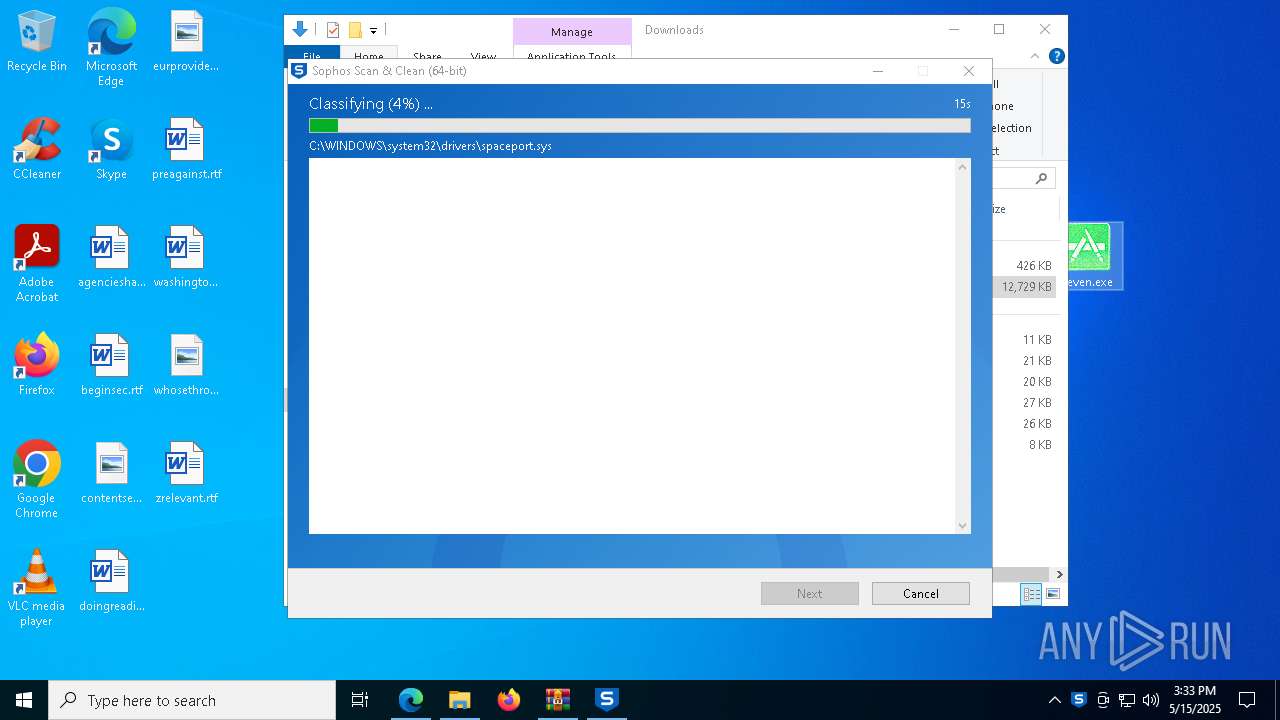
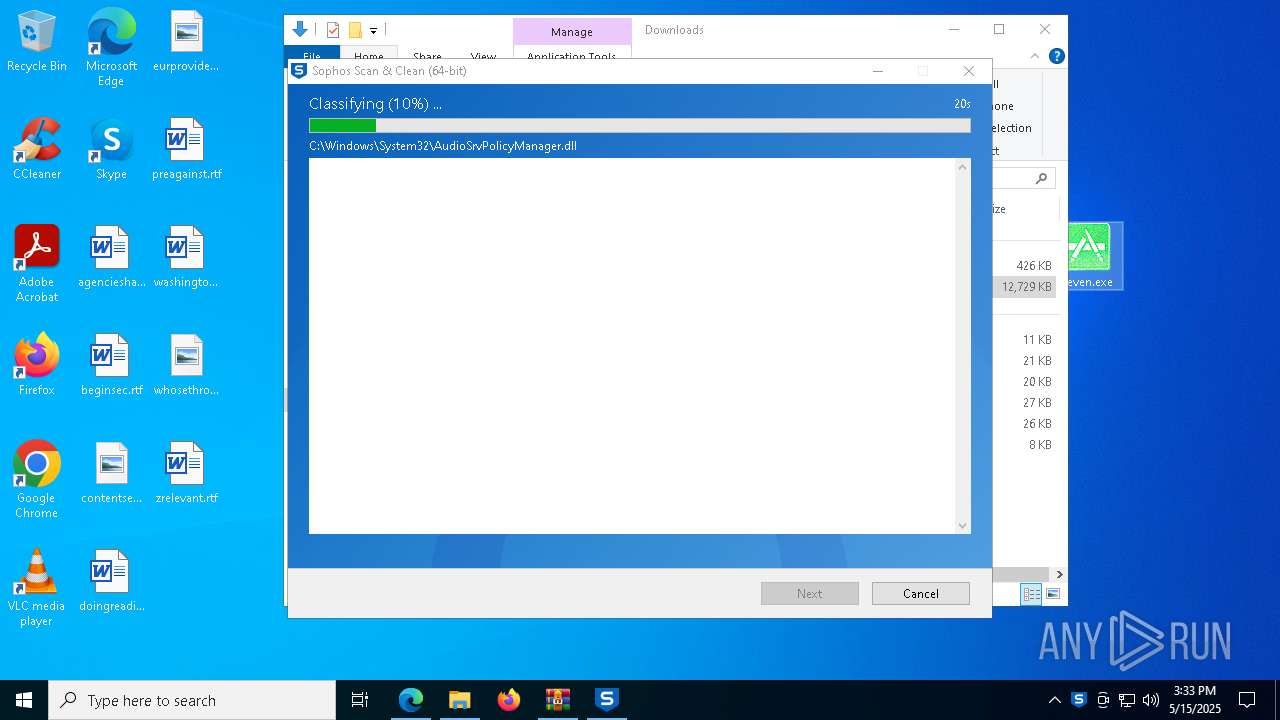
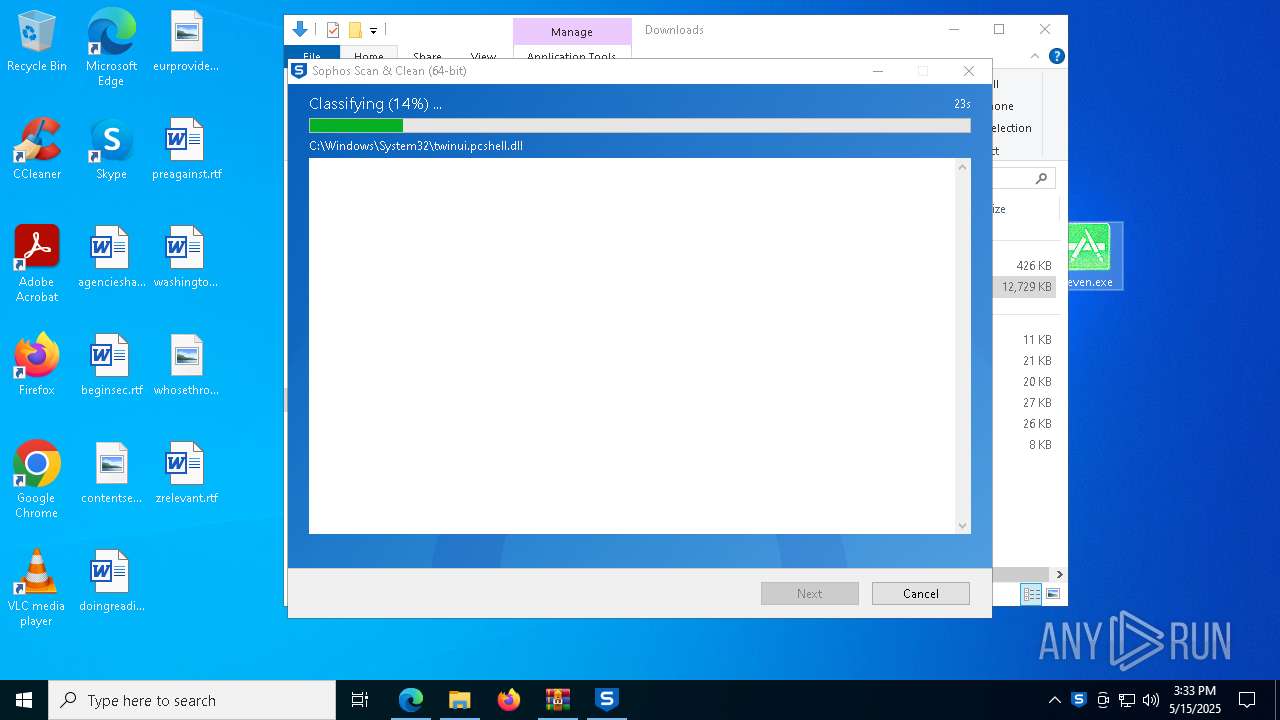
- SophosScanAndClean_x64.exe (PID: 2984)
Reads security settings of Internet Explorer
- Seven.exe (PID: 1180)
- SophosScanAndClean_x64.exe (PID: 2984)
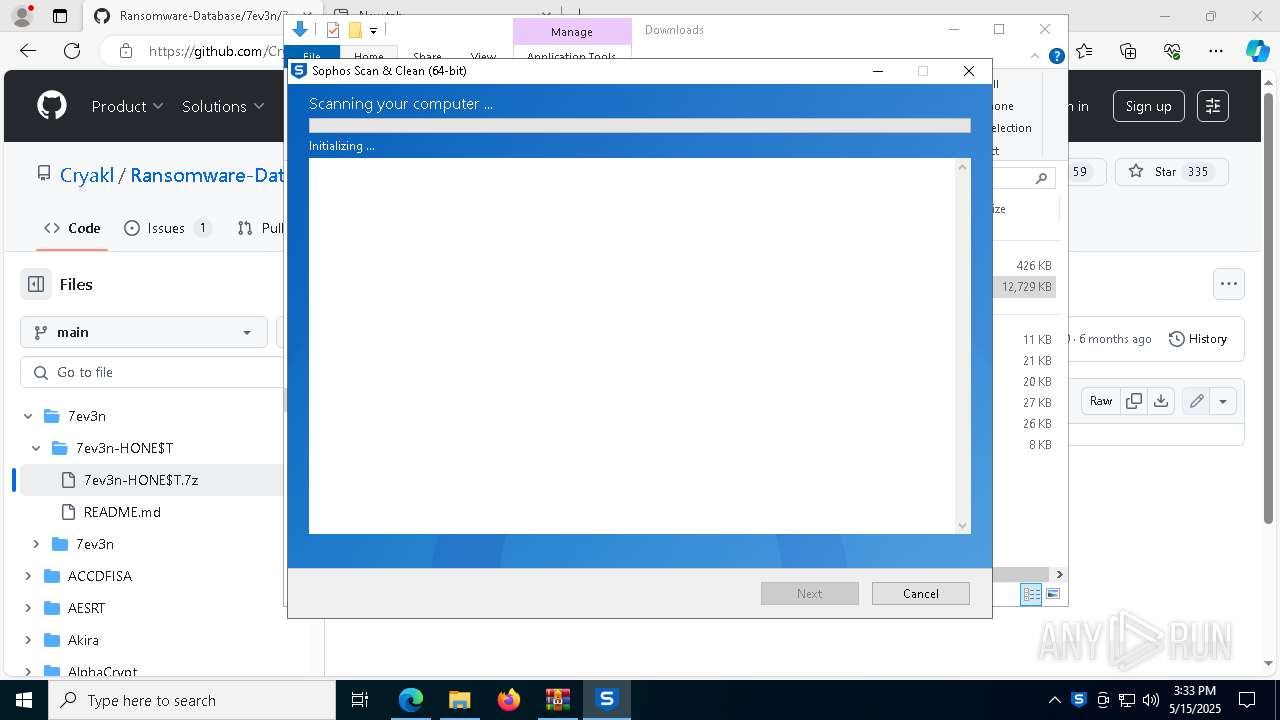
Cleans NTFS data stream (Zone Identifier)
- SophosScanAndClean_x64.exe (PID: 2984)
Creates files in the driver directory
- SophosScanAndClean_x64.exe (PID: 2984)
Drops a system driver (possible attempt to evade defenses)
- SophosScanAndClean_x64.exe (PID: 2984)
Starts itself from another location
- Seven.exe (PID: 1180)
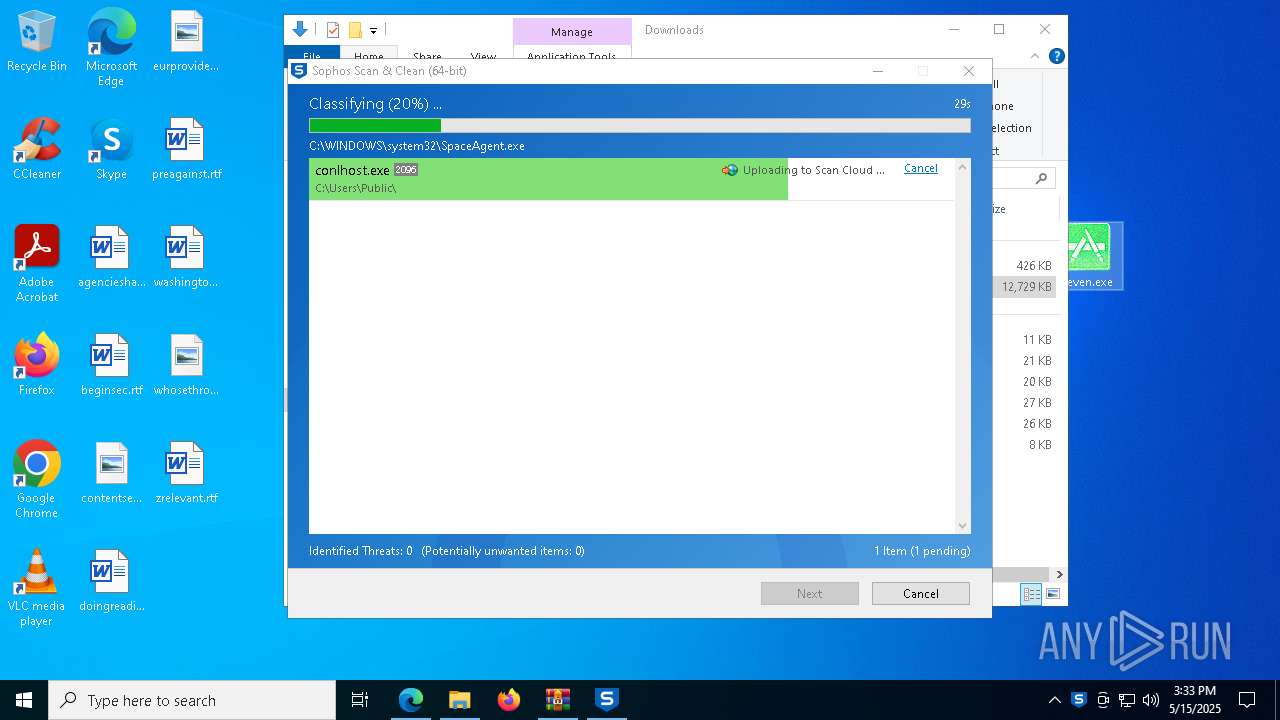
Likely accesses (executes) a file from the Public directory
- conlhost.exe (PID: 2096)
- conlhost.exe (PID: 7904)
- cmd.exe (PID: 8040)
- reg.exe (PID: 5044)
Executing commands from a ".bat" file
- conlhost.exe (PID: 7904)
Read startup parameters
- SophosScanAndClean_x64.exe (PID: 2984)
Uses REG/REGEDIT.EXE to modify registry
- conlhost.exe (PID: 7904)
- Seven.exe (PID: 6964)
- Seven.exe (PID: 4284)
Starts CMD.EXE for commands execution
- conlhost.exe (PID: 7904)
INFO
Reads the computer name
- identity_helper.exe (PID: 2096)
- Seven.exe (PID: 1180)
- identity_helper.exe (PID: 7860)
- SophosScanAndClean_x64.exe (PID: 2984)
Checks supported languages
- identity_helper.exe (PID: 2096)
- Seven.exe (PID: 7500)
- Seven.exe (PID: 1180)
- identity_helper.exe (PID: 7860)
- SophosScanAndClean_x64.exe (PID: 2984)
- conlhost.exe (PID: 2096)
- Seven.exe (PID: 7864)
Reads Environment values
- identity_helper.exe (PID: 2096)
- identity_helper.exe (PID: 7860)
Application launched itself
- msedge.exe (PID: 3156)
Executable content was dropped or overwritten
- msedge.exe (PID: 7356)
- msedge.exe (PID: 3156)
- WinRAR.exe (PID: 904)
- msedge.exe (PID: 1912)
Reads Microsoft Office registry keys
- msedge.exe (PID: 3156)
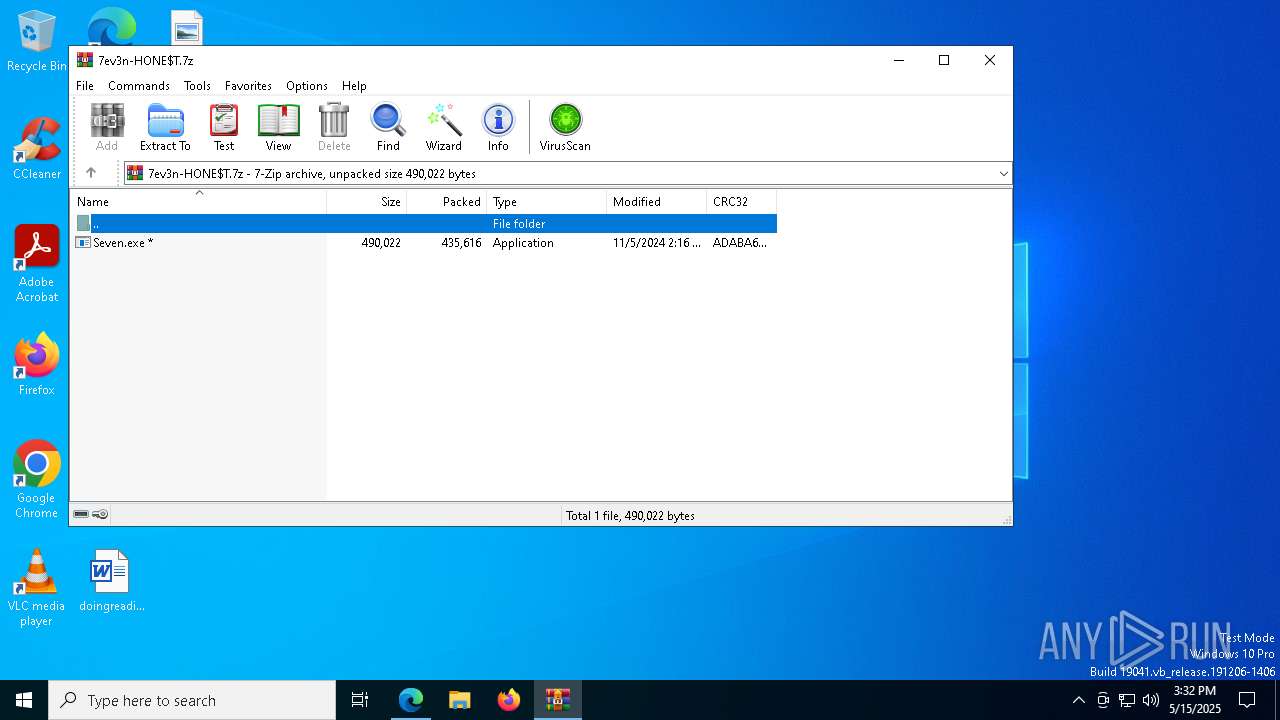
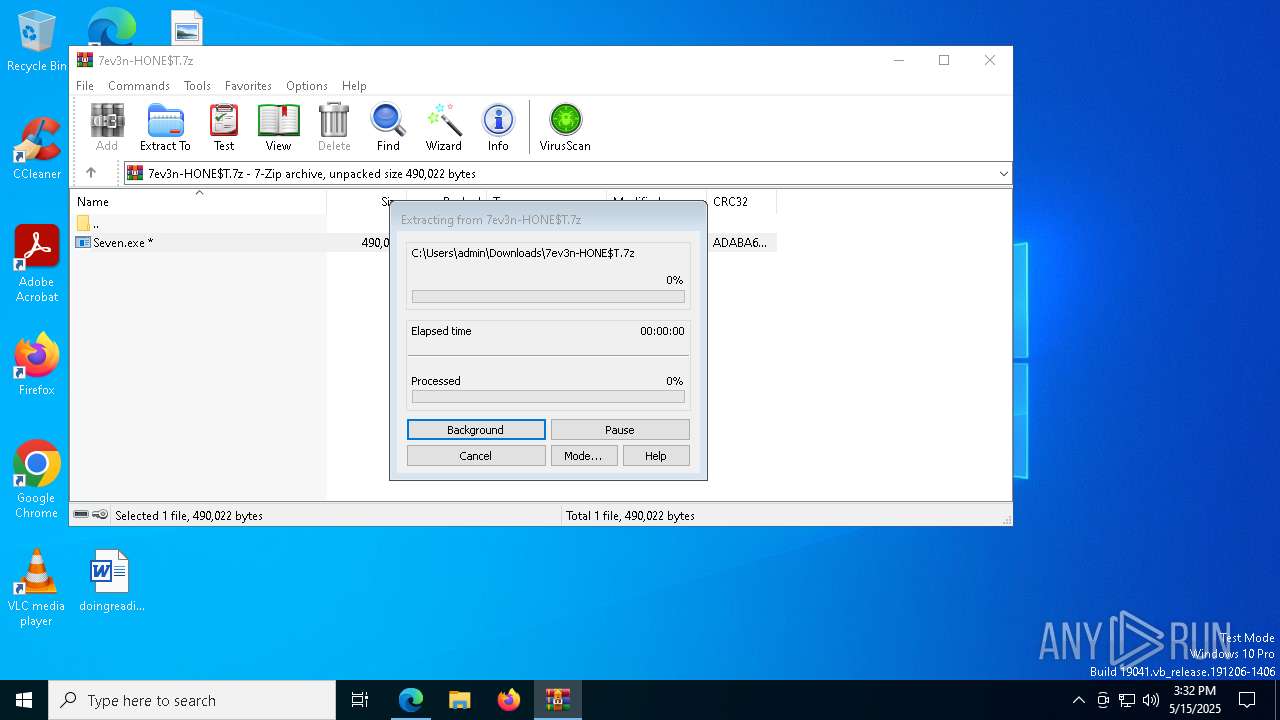
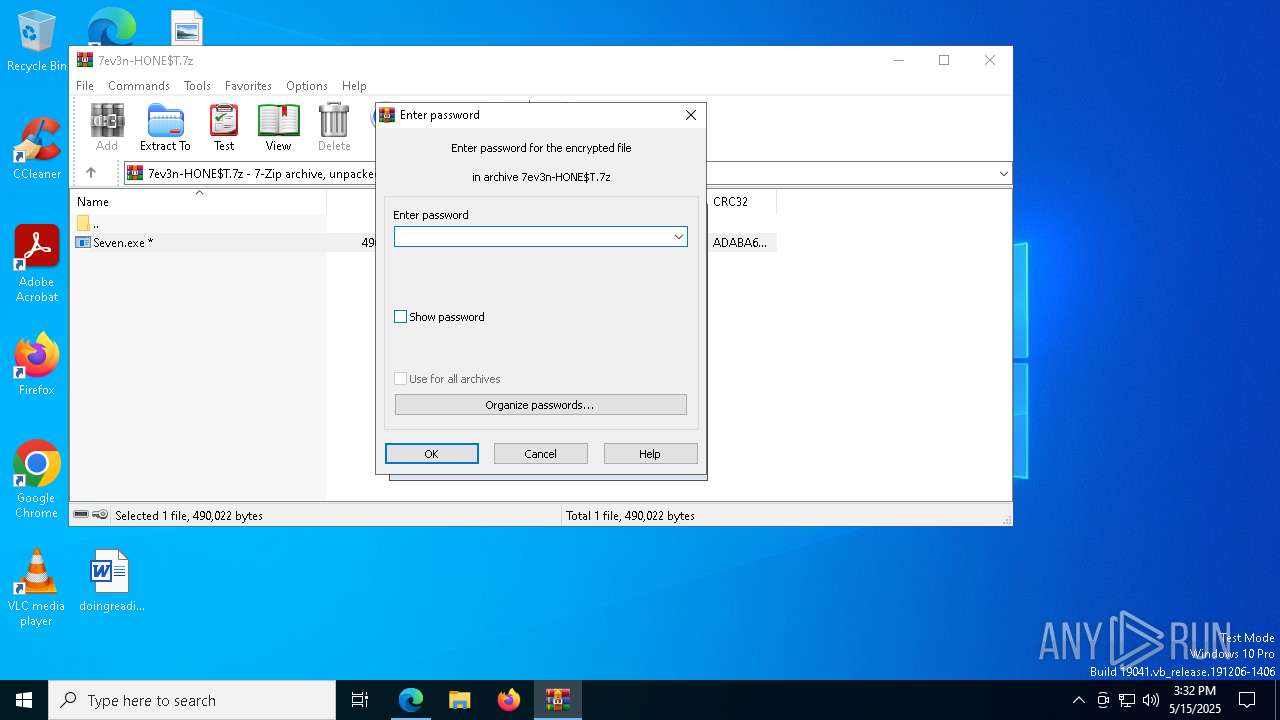
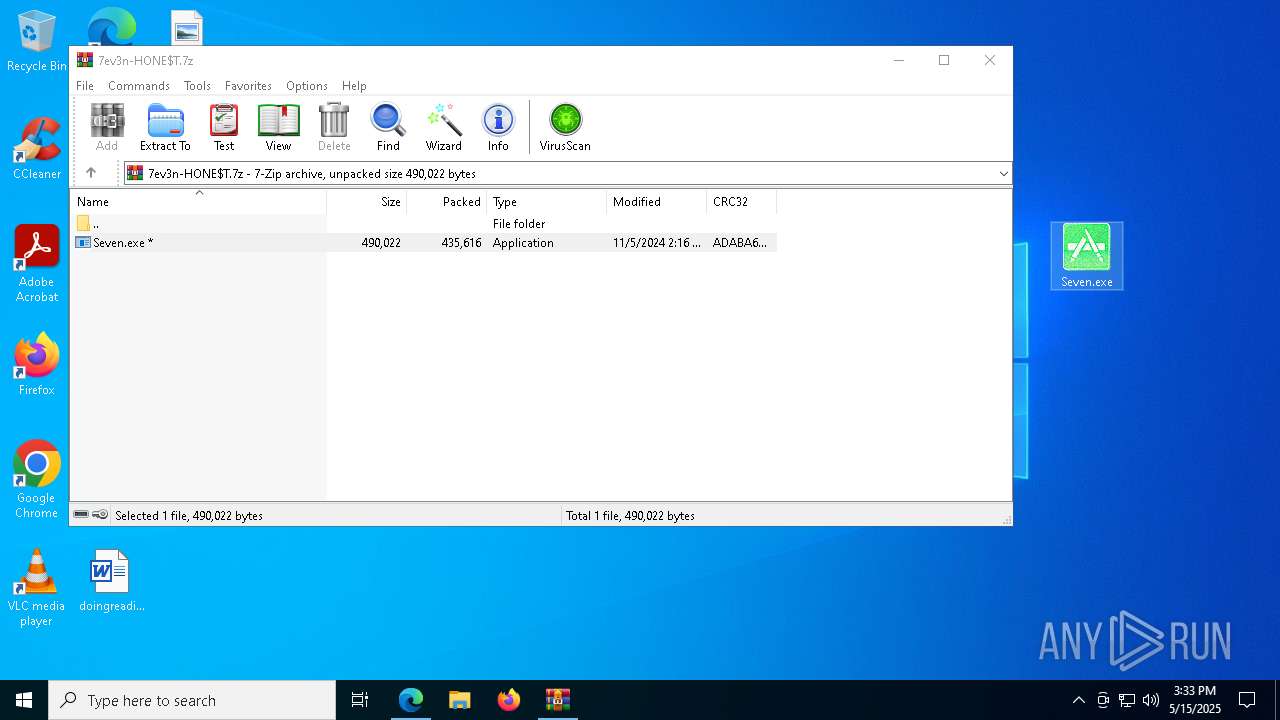
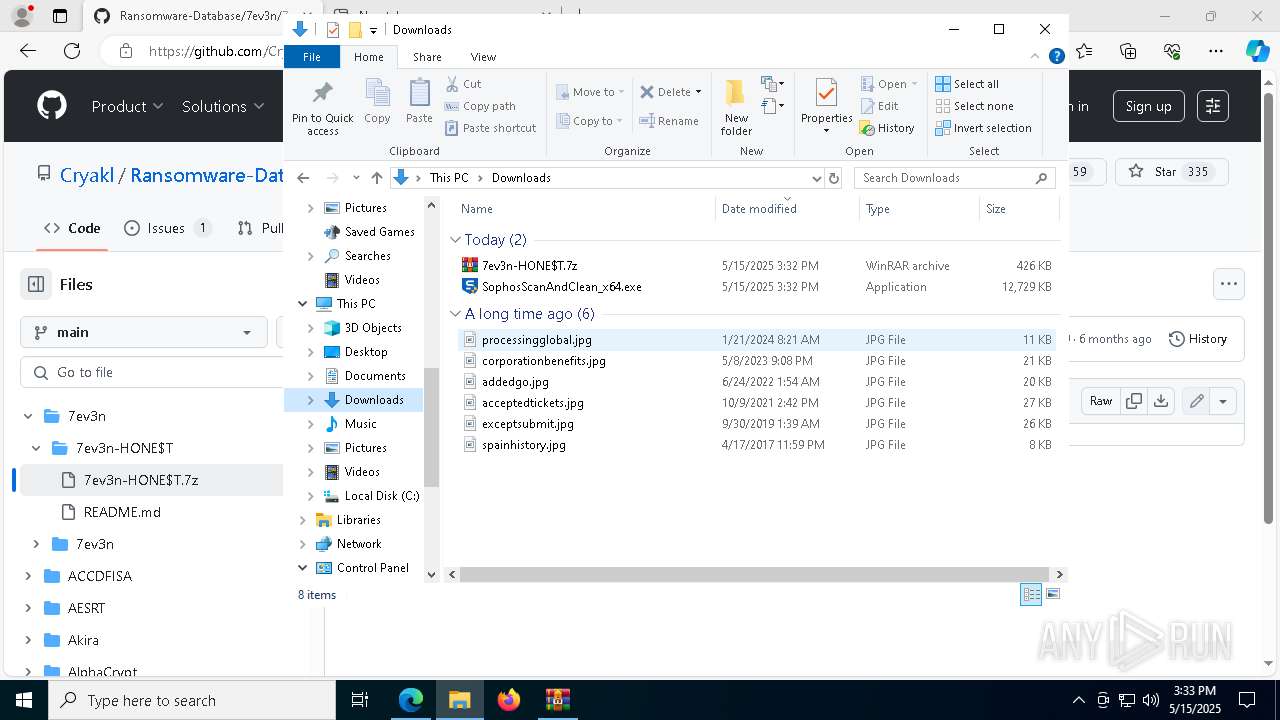
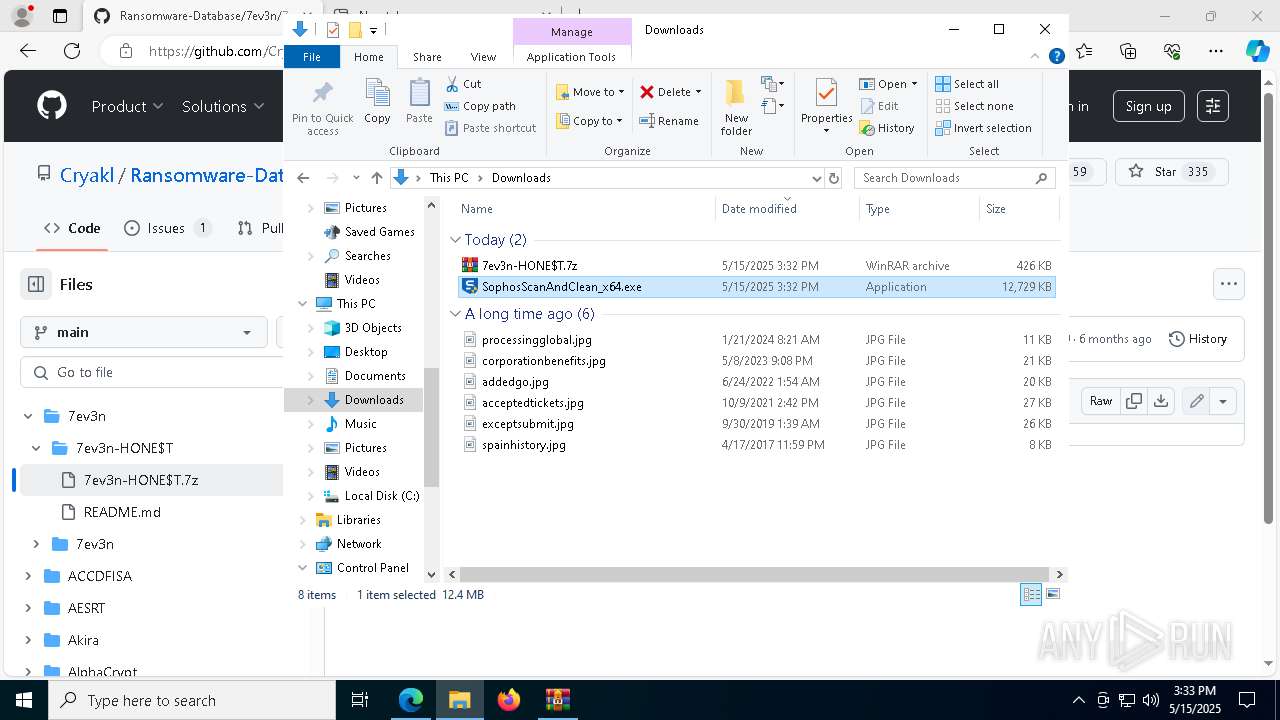
Manual execution by a user
- Seven.exe (PID: 7500)
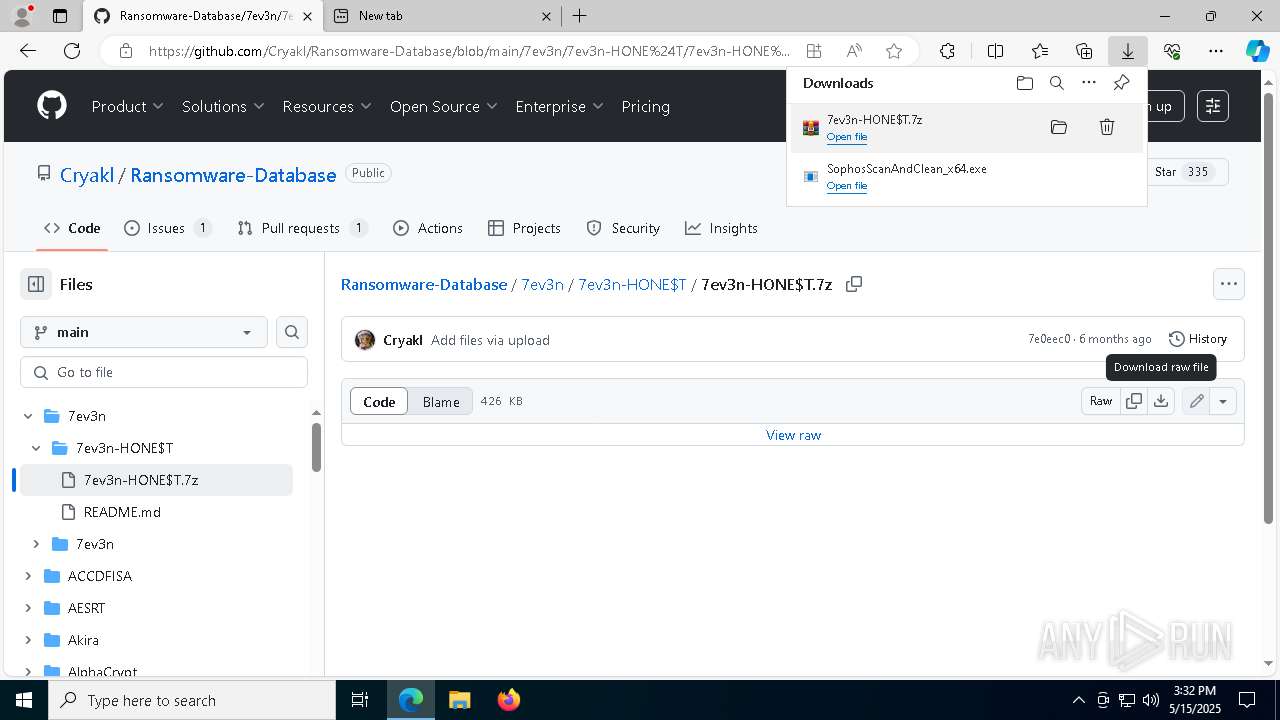
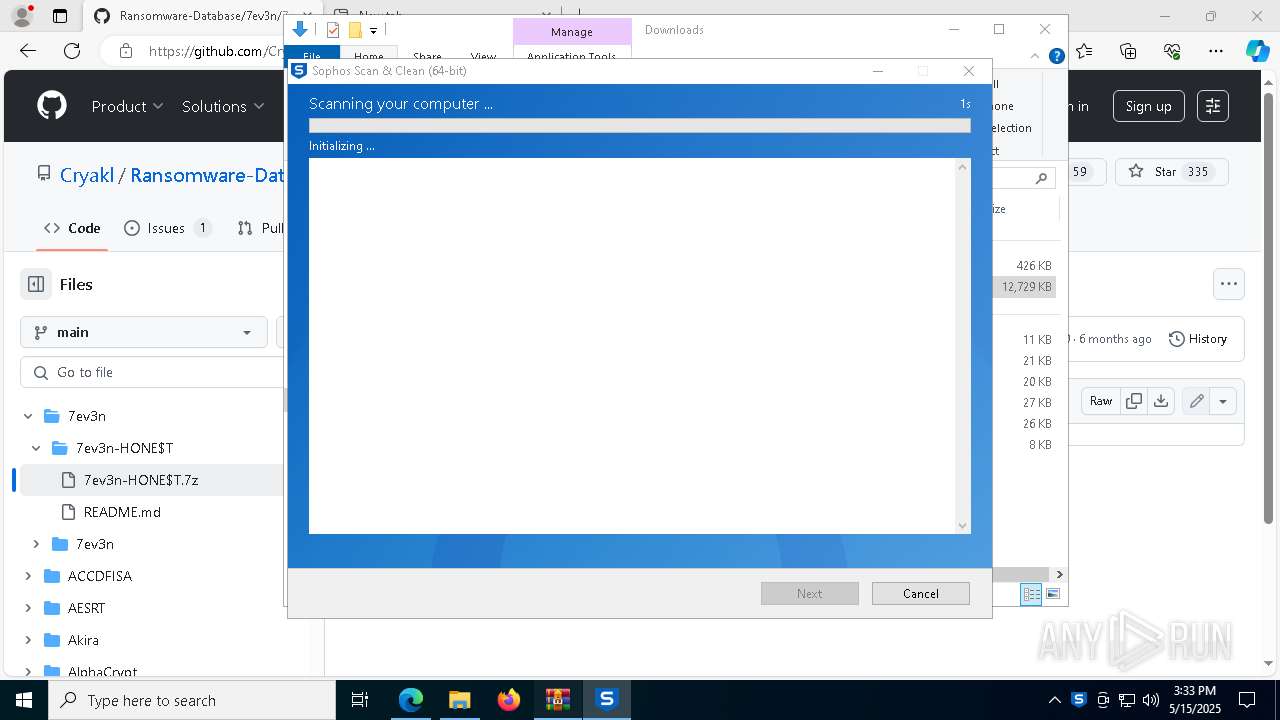
- SophosScanAndClean_x64.exe (PID: 872)
- SophosScanAndClean_x64.exe (PID: 2984)
- Seven.exe (PID: 7864)
- Seven.exe (PID: 4572)
Reads the machine GUID from the registry
- Seven.exe (PID: 1180)
Creates files in the program directory
- SophosScanAndClean_x64.exe (PID: 2984)
Reads the software policy settings
- SophosScanAndClean_x64.exe (PID: 2984)
- slui.exe (PID: 8092)
Checks proxy server information
- Seven.exe (PID: 1180)
- SophosScanAndClean_x64.exe (PID: 2984)
The sample compiled with english language support
- msedge.exe (PID: 1912)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
220
Monitored processes
85
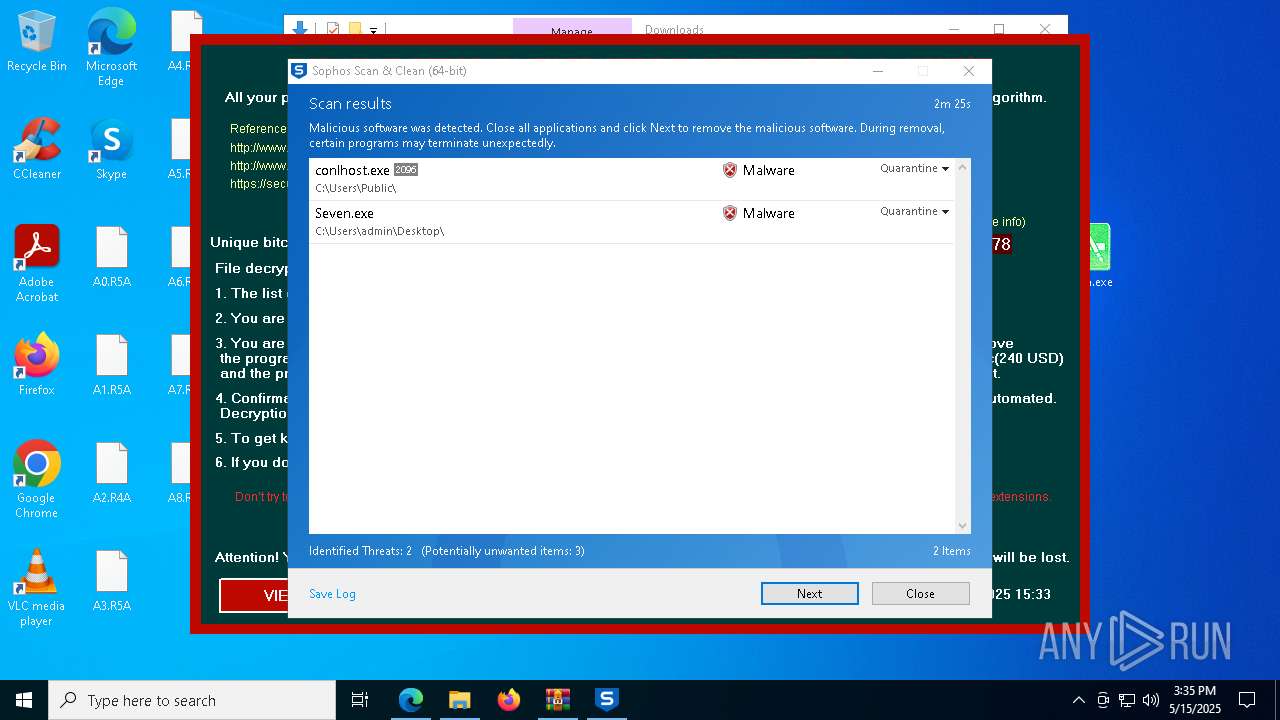
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | REG ADD "HKEY_CURRENT_USER\SOFTWARE" /v "crypted" /t REG_SZ /d "1" /reg:64 | C:\Windows\SysWOW64\reg.exe | — | conlhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 300 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6380 --field-trial-handle=2468,i,1813303791065408512,8136246299486432539,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 516 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5940 --field-trial-handle=2468,i,1813303791065408512,8136246299486432539,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 516 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6672 --field-trial-handle=2468,i,1813303791065408512,8136246299486432539,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 744 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=38 --mojo-platform-channel-handle=6948 --field-trial-handle=2468,i,1813303791065408512,8136246299486432539,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 864 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5628 --field-trial-handle=2468,i,1813303791065408512,8136246299486432539,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 872 | "C:\Users\admin\Downloads\SophosScanAndClean_x64.exe" | C:\Users\admin\Downloads\SophosScanAndClean_x64.exe | — | explorer.exe | |||||||||||
User: admin Company: Sophos Limited Integrity Level: MEDIUM Description: Sophos Scan & Clean Exit code: 3221226540 Version: 1, 0, 1 Modules
| |||||||||||||||
| 900 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6660 --field-trial-handle=2468,i,1813303791065408512,8136246299486432539,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
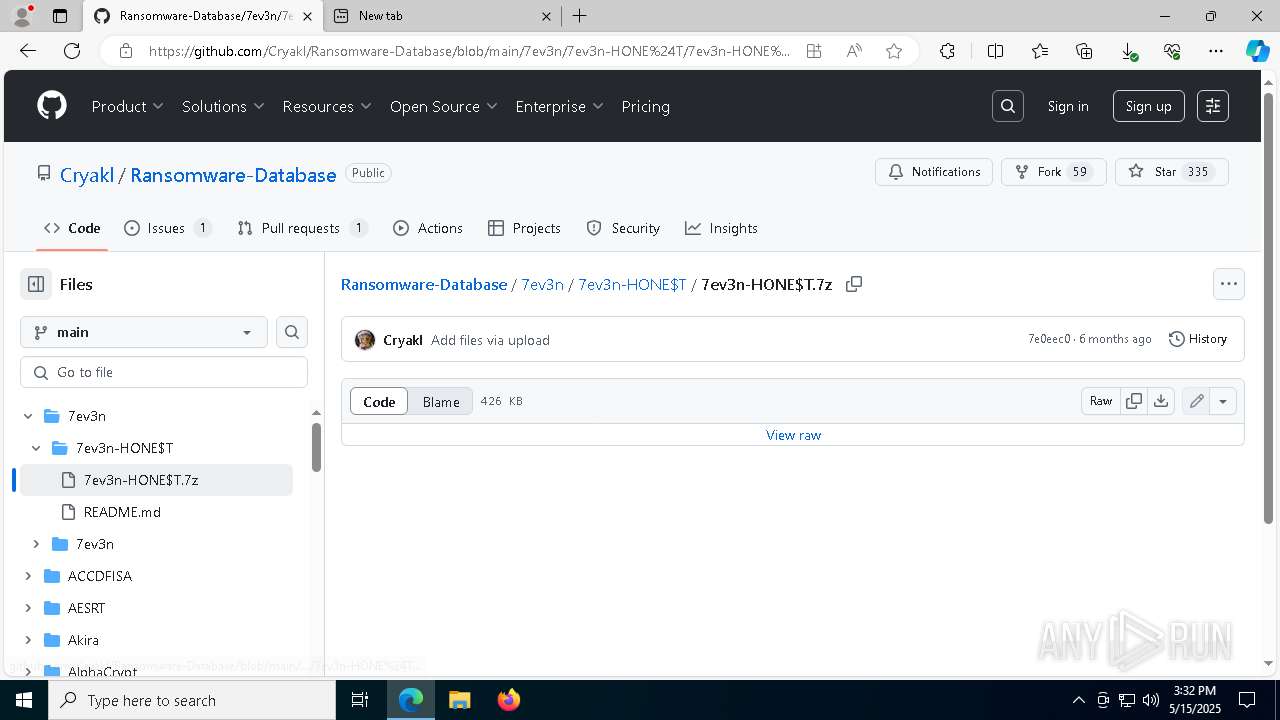
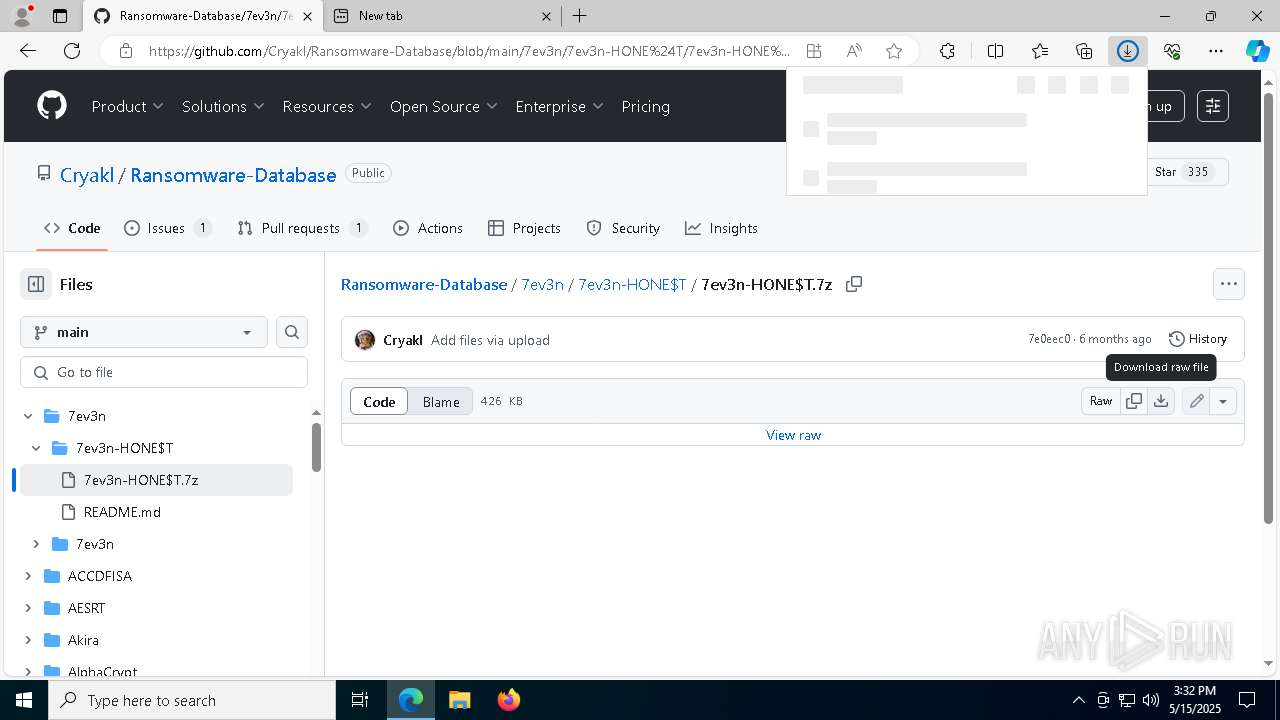
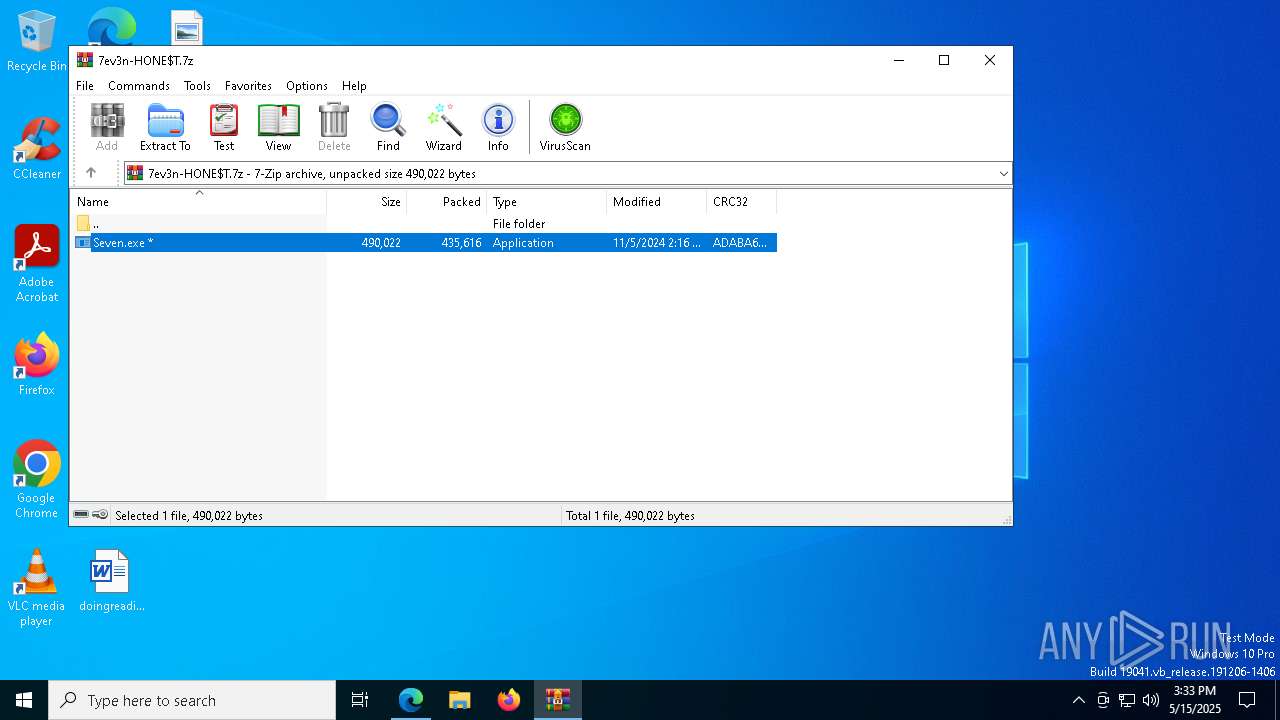
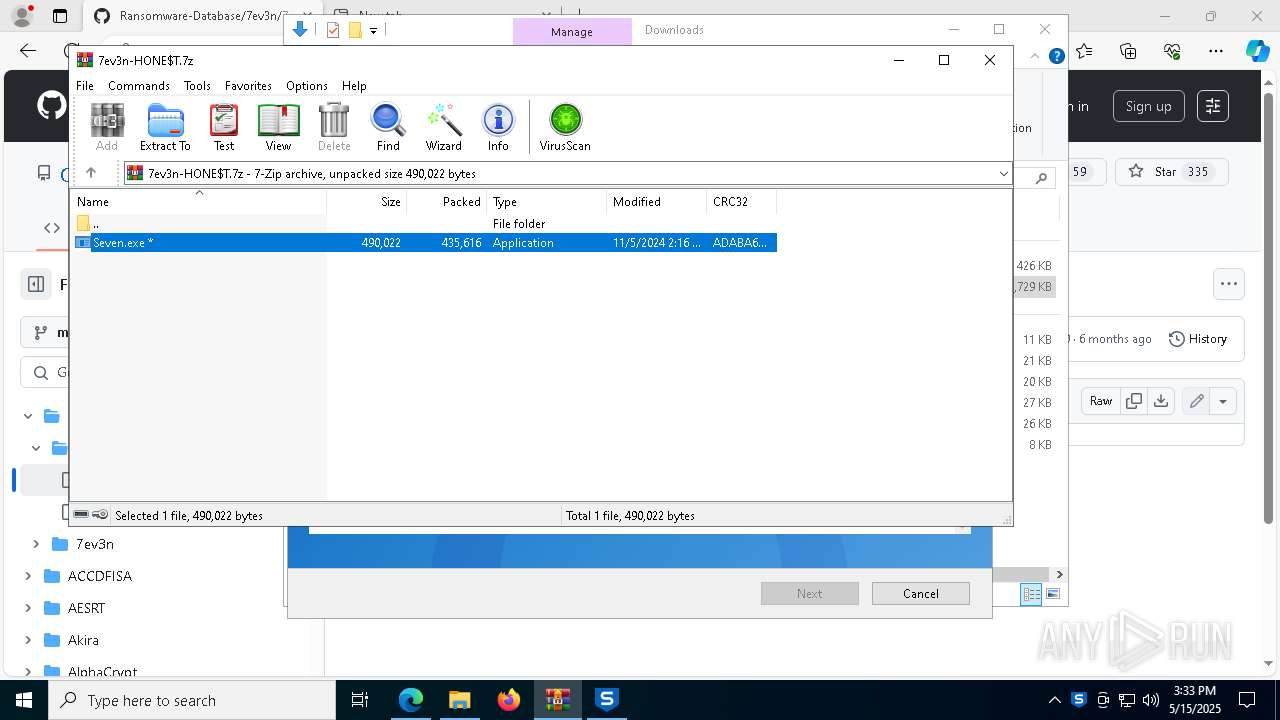
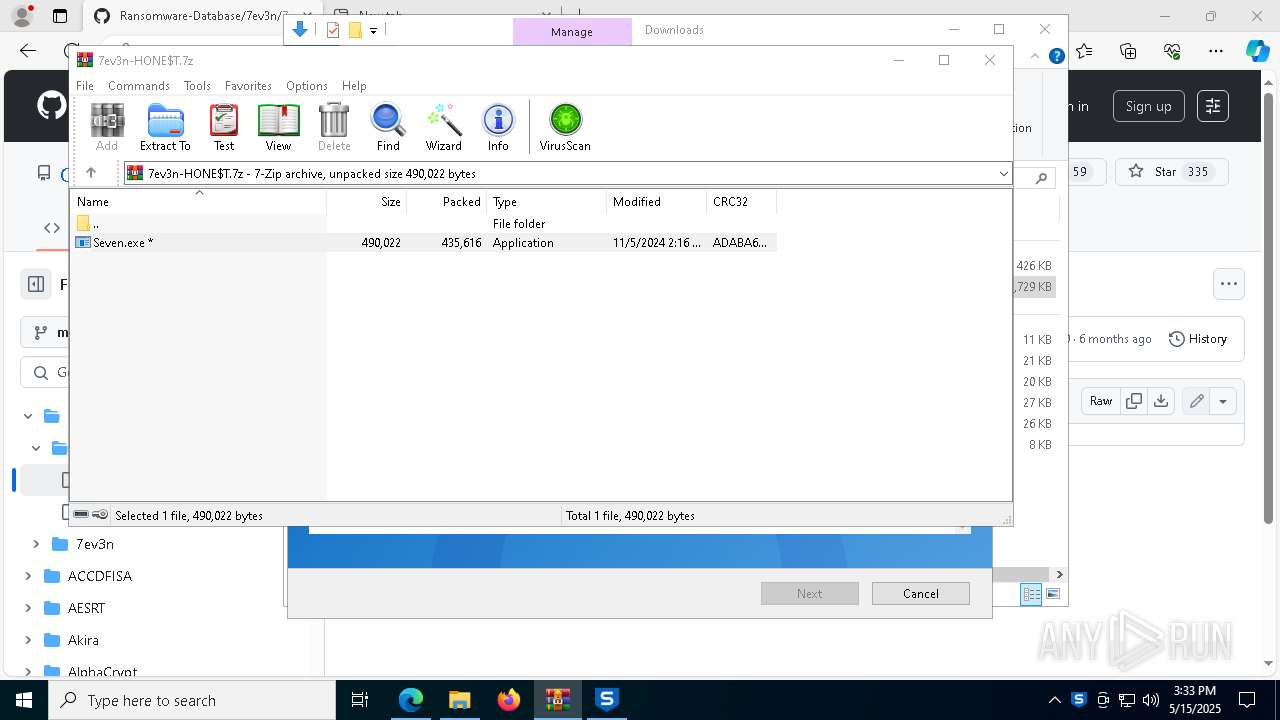
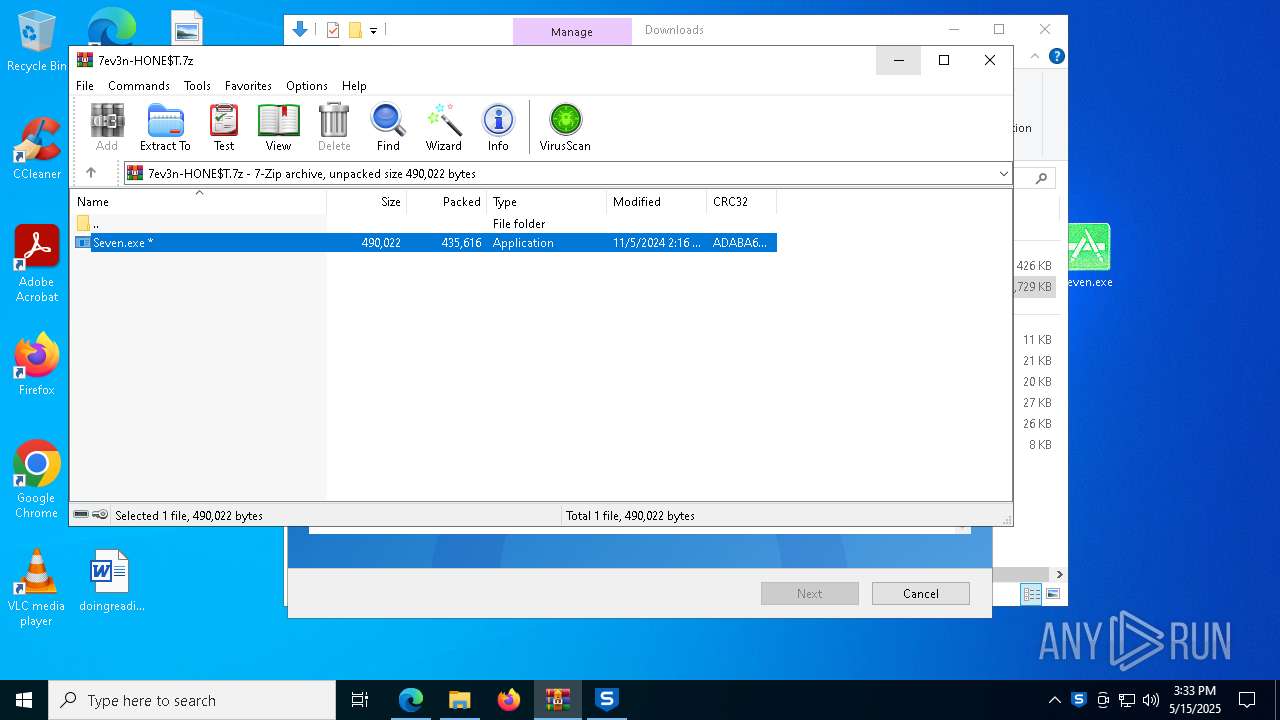
| 904 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\7ev3n-HONE$T.7z" | C:\Program Files\WinRAR\WinRAR.exe | msedge.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 976 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x300,0x304,0x308,0x2f8,0x310,0x7ffc88165fd8,0x7ffc88165fe4,0x7ffc88165ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
50 303
Read events
50 214
Write events
82
Delete events
7
Modification events
| (PID) Process: | (3156) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: AD0332A7C4932F00 | |||
| (PID) Process: | (3156) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3156) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3156) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3156) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3156) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 37403BA7C4932F00 | |||
| (PID) Process: | (3156) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197198 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {4C2F2CC0-BEF4-4239-974A-3B84AA1C0E78} | |||
| (PID) Process: | (3156) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197198 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {CEF9E8F0-7C66-4026-A303-CDD12B9693A6} | |||
| (PID) Process: | (3156) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197198 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {AF30DFA1-259A-4F3D-8BF2-676ECE0756FA} | |||
| (PID) Process: | (3156) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197198 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {82F30EA7-7245-4A13-9234-B667B23F882D} | |||
Executable files
42
Suspicious files
939
Text files
159
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3156 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10ba2a.TMP | — | |
MD5:— | SHA256:— | |||
| 3156 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3156 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10ba3a.TMP | — | |
MD5:— | SHA256:— | |||
| 3156 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3156 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10ba49.TMP | — | |
MD5:— | SHA256:— | |||
| 3156 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3156 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF10bac6.TMP | — | |
MD5:— | SHA256:— | |||
| 3156 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3156 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10bac6.TMP | — | |
MD5:— | SHA256:— | |||
| 3156 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
46
TCP/UDP connections
147
DNS requests
136
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
8008 | svchost.exe | GET | 206 | 23.48.23.27:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/84d3e481-77df-49da-bc37-0a994069ddb9?P1=1747705080&P2=404&P3=2&P4=AAAF%2bfIu13dgvhHkbwhQKkAiADN2z8d9noQmuGNHv4kQRhJub5GhLm7n4E2sIDZNRbeMlG9EEyihD8xfFbMS4A%3d%3d | unknown | — | — | whitelisted |
8008 | svchost.exe | GET | 206 | 23.48.23.27:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/84d3e481-77df-49da-bc37-0a994069ddb9?P1=1747705080&P2=404&P3=2&P4=AAAF%2bfIu13dgvhHkbwhQKkAiADN2z8d9noQmuGNHv4kQRhJub5GhLm7n4E2sIDZNRbeMlG9EEyihD8xfFbMS4A%3d%3d | unknown | — | — | whitelisted |
8008 | svchost.exe | GET | 206 | 23.48.23.27:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/84d3e481-77df-49da-bc37-0a994069ddb9?P1=1747705080&P2=404&P3=2&P4=AAAF%2bfIu13dgvhHkbwhQKkAiADN2z8d9noQmuGNHv4kQRhJub5GhLm7n4E2sIDZNRbeMlG9EEyihD8xfFbMS4A%3d%3d | unknown | — | — | whitelisted |
8008 | svchost.exe | GET | 206 | 23.48.23.27:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/84d3e481-77df-49da-bc37-0a994069ddb9?P1=1747705080&P2=404&P3=2&P4=AAAF%2bfIu13dgvhHkbwhQKkAiADN2z8d9noQmuGNHv4kQRhJub5GhLm7n4E2sIDZNRbeMlG9EEyihD8xfFbMS4A%3d%3d | unknown | — | — | whitelisted |
8008 | svchost.exe | GET | 206 | 23.48.23.27:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/84d3e481-77df-49da-bc37-0a994069ddb9?P1=1747705080&P2=404&P3=2&P4=AAAF%2bfIu13dgvhHkbwhQKkAiADN2z8d9noQmuGNHv4kQRhJub5GhLm7n4E2sIDZNRbeMlG9EEyihD8xfFbMS4A%3d%3d | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7964 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8008 | svchost.exe | HEAD | 200 | 23.48.23.27:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1747705079&P2=404&P3=2&P4=hZrNFMaeiZLCEz57UPskpidlKMcXJtAfEwV8LnEe%2fHVoZHXOiJB1db%2fW0JdNq1d89%2bQX0MtpXDa430gyGeDGKQ%3d%3d | unknown | — | — | whitelisted |
7964 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2984 | SophosScanAndClean_x64.exe | GET | 200 | 52.174.35.5:80 | http://scan.hitmanpro.com/banner.aspx?lc=en&v=1.0.1.0&c=sac | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7356 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3156 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7356 | msedge.exe | 140.82.121.4:443 | github.com | GITHUB | US | whitelisted |
7356 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7356 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7356 | msedge.exe | 40.90.65.34:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7356 | msedge.exe | 185.199.111.154:443 | github.githubassets.com | FASTLY | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
github.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
www.bing.com |
| whitelisted |
github.githubassets.com |
| whitelisted |
avatars.githubusercontent.com |
| whitelisted |
user-images.githubusercontent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7356 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
7356 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |