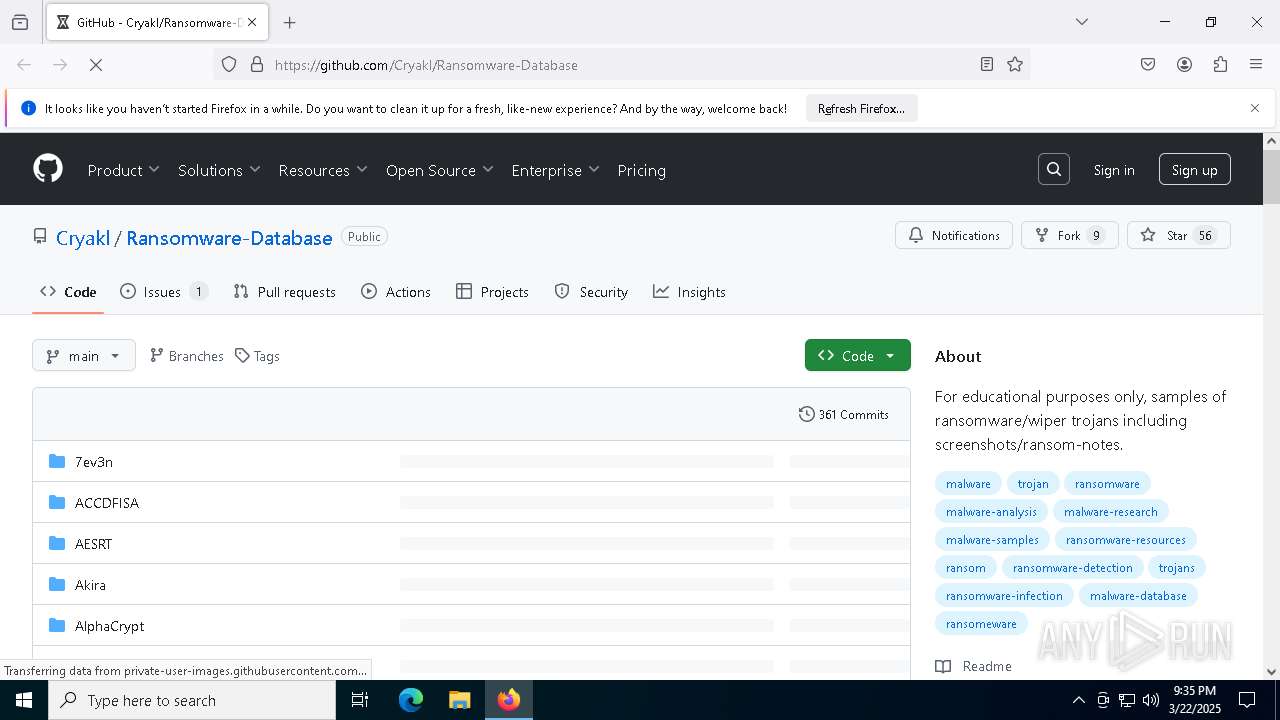
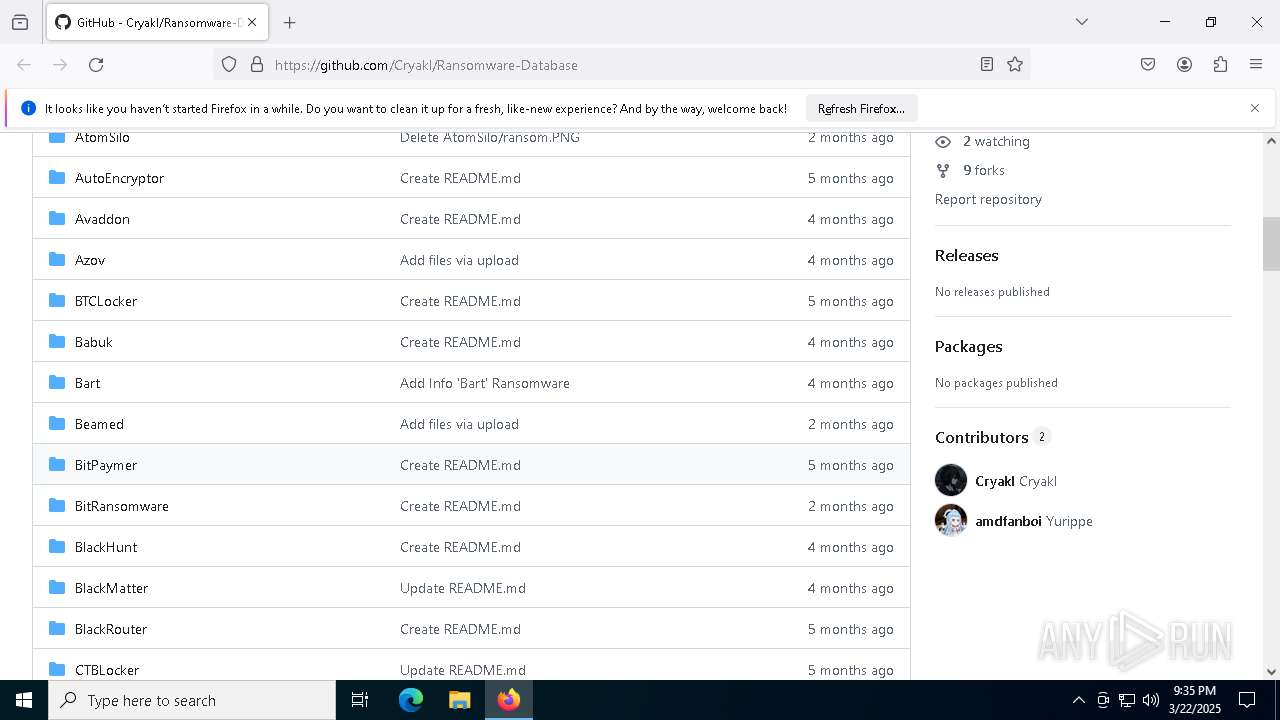
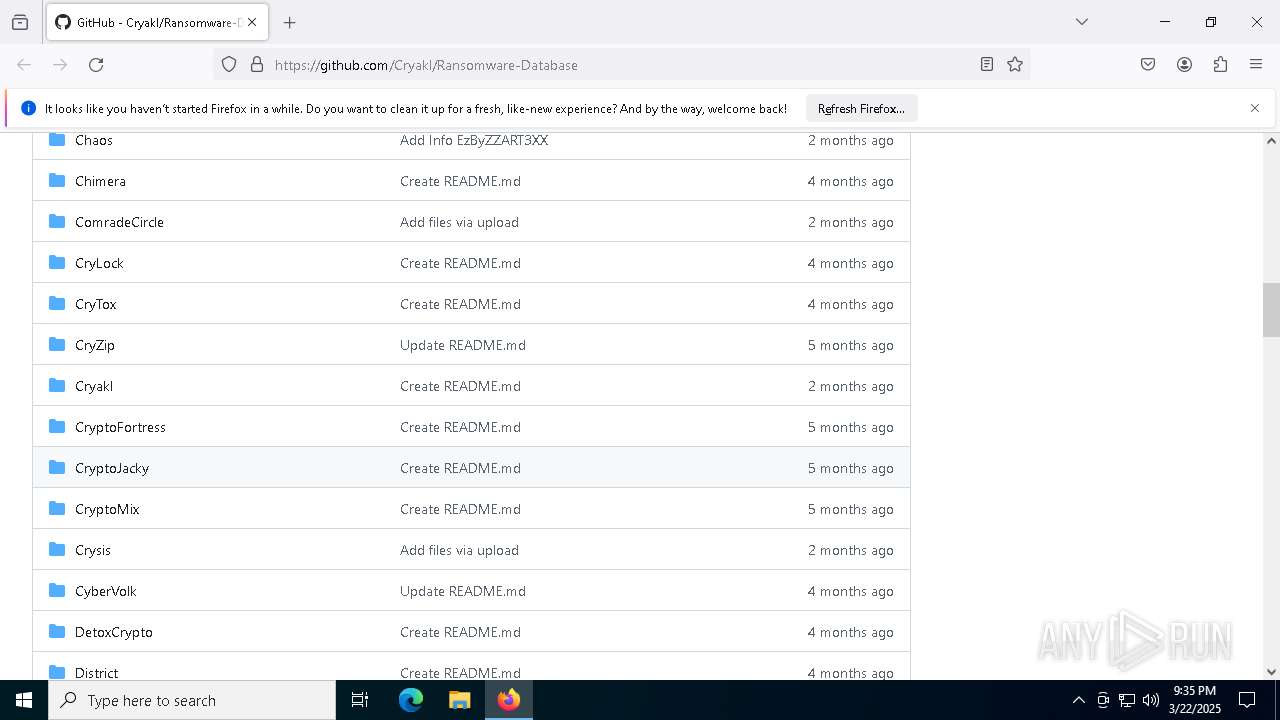
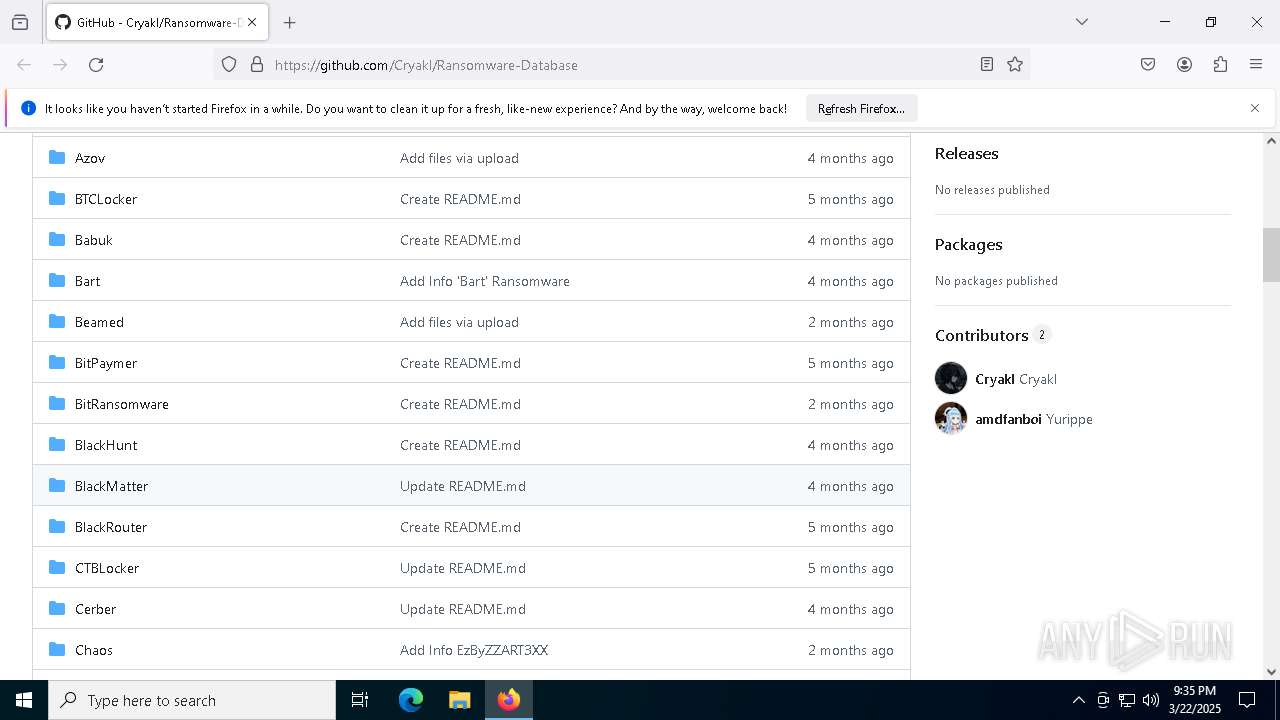
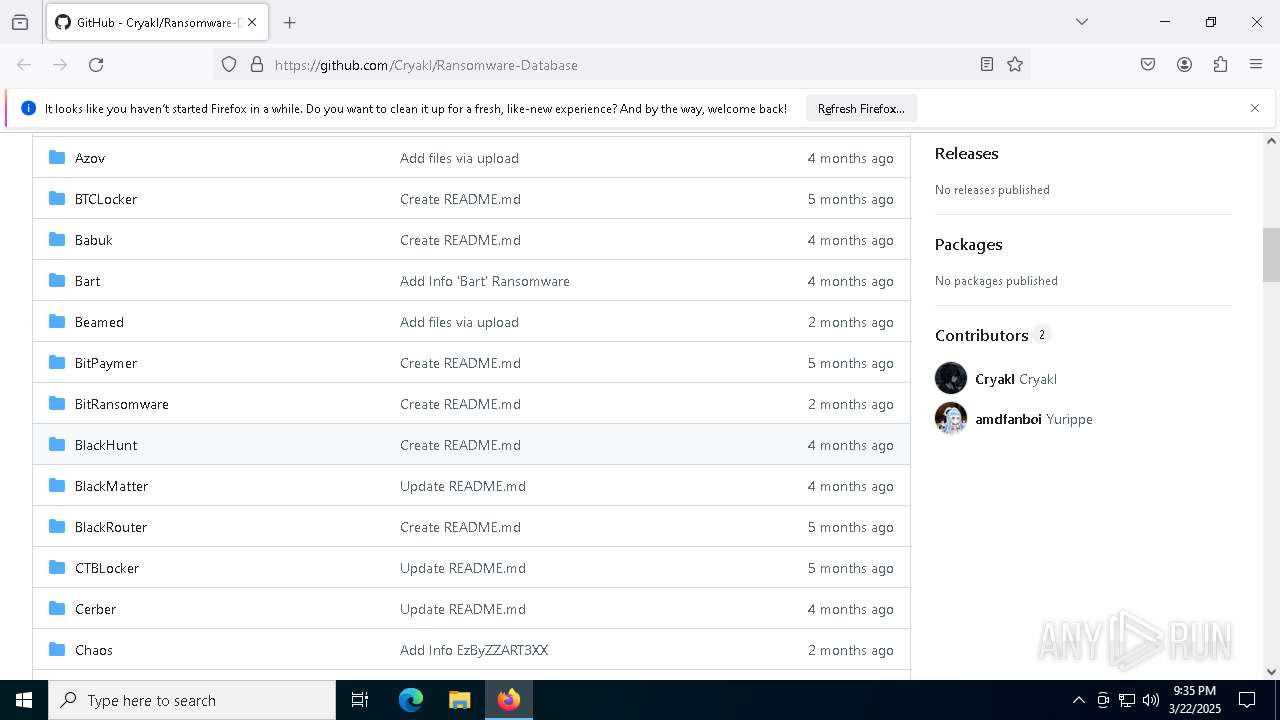
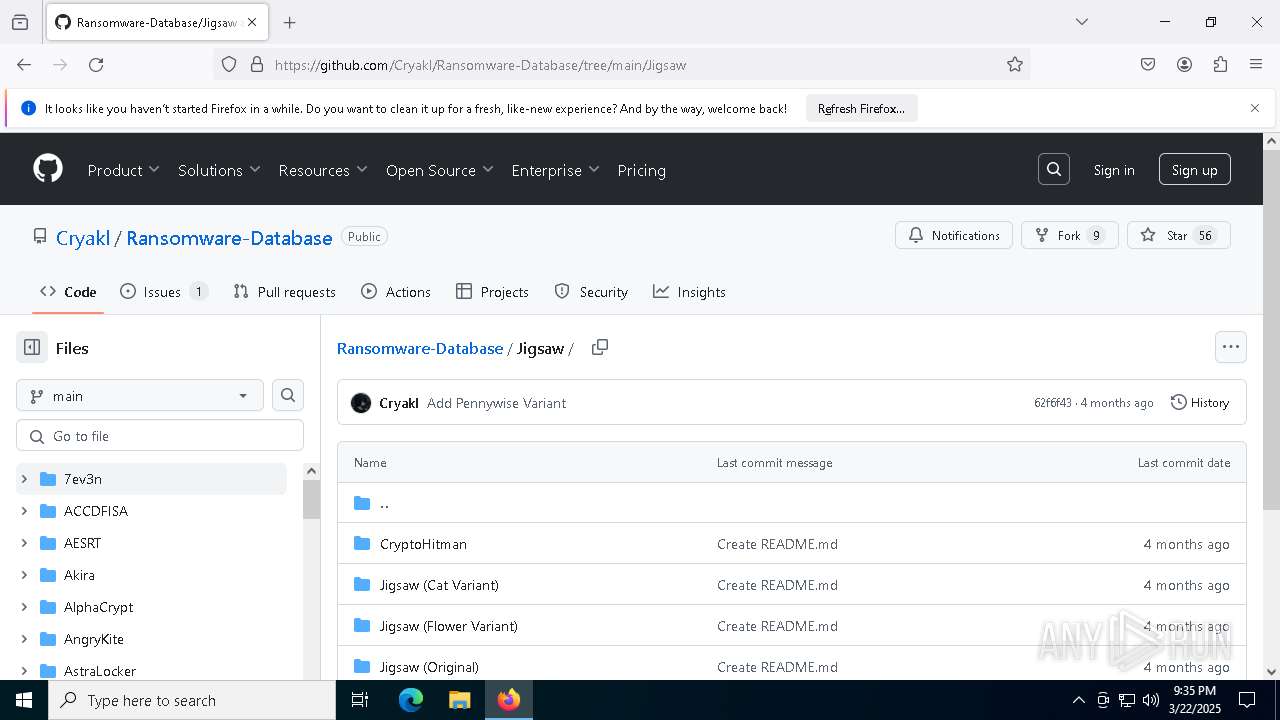
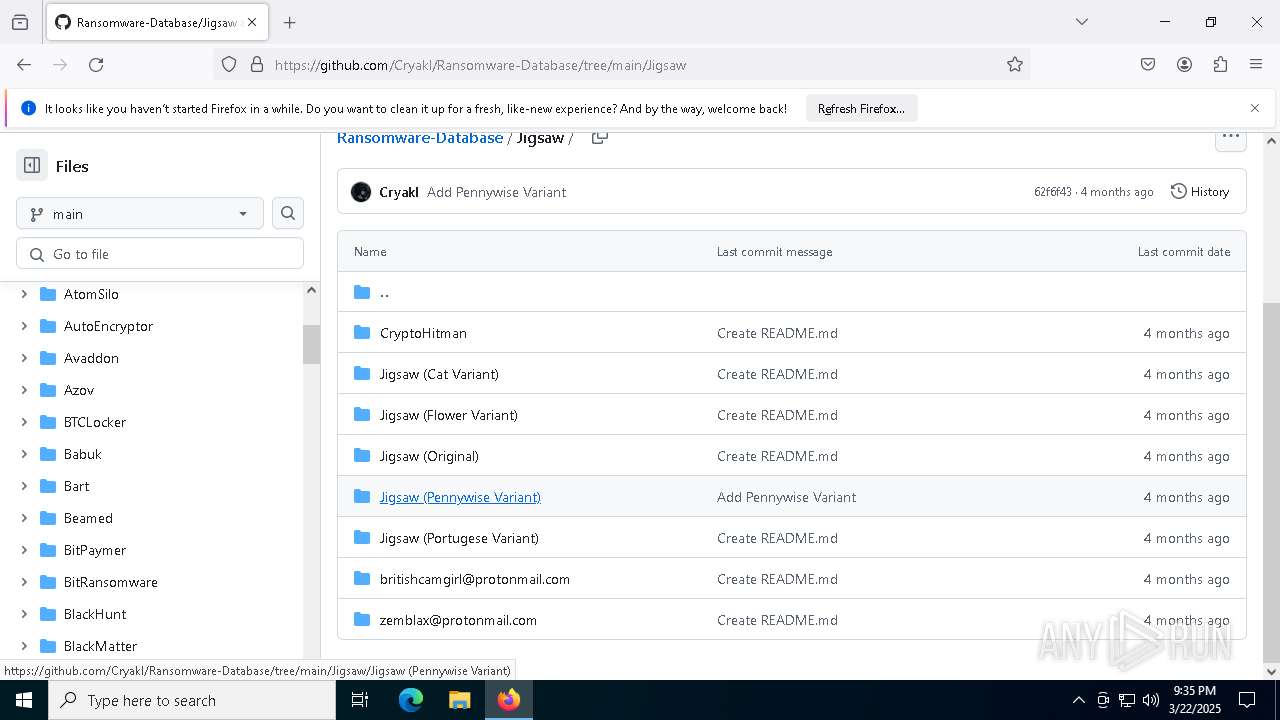
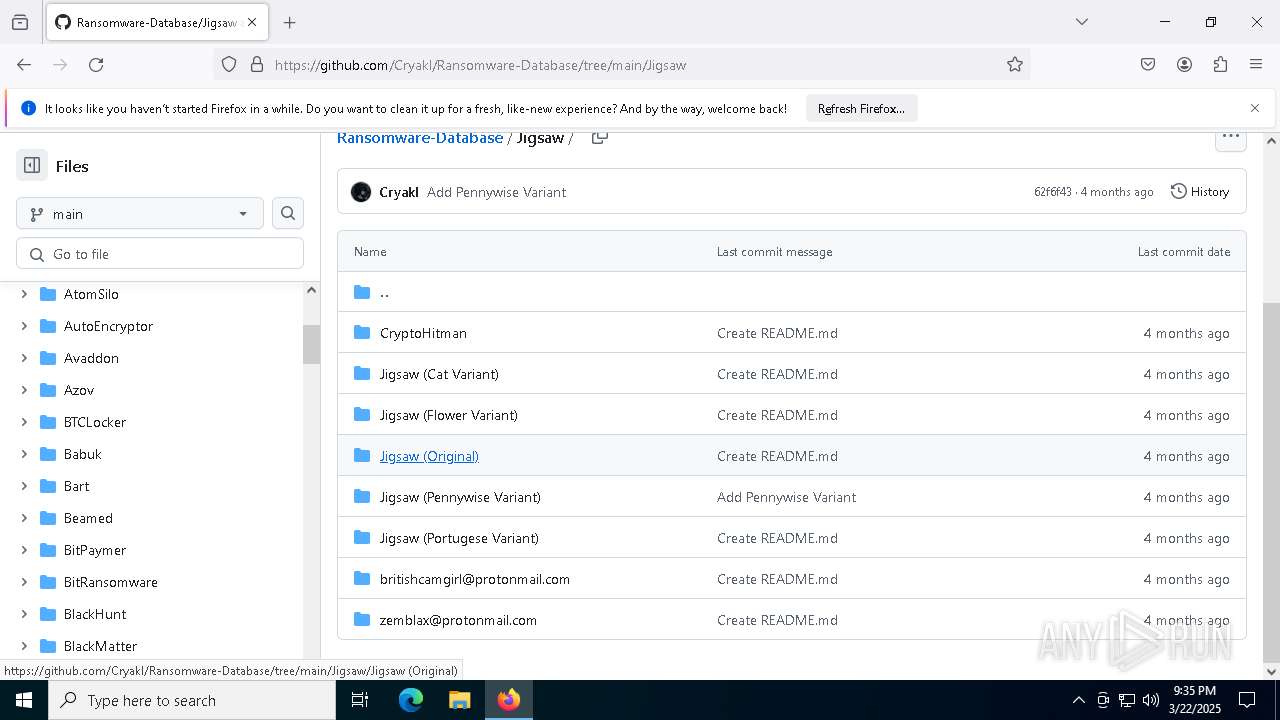
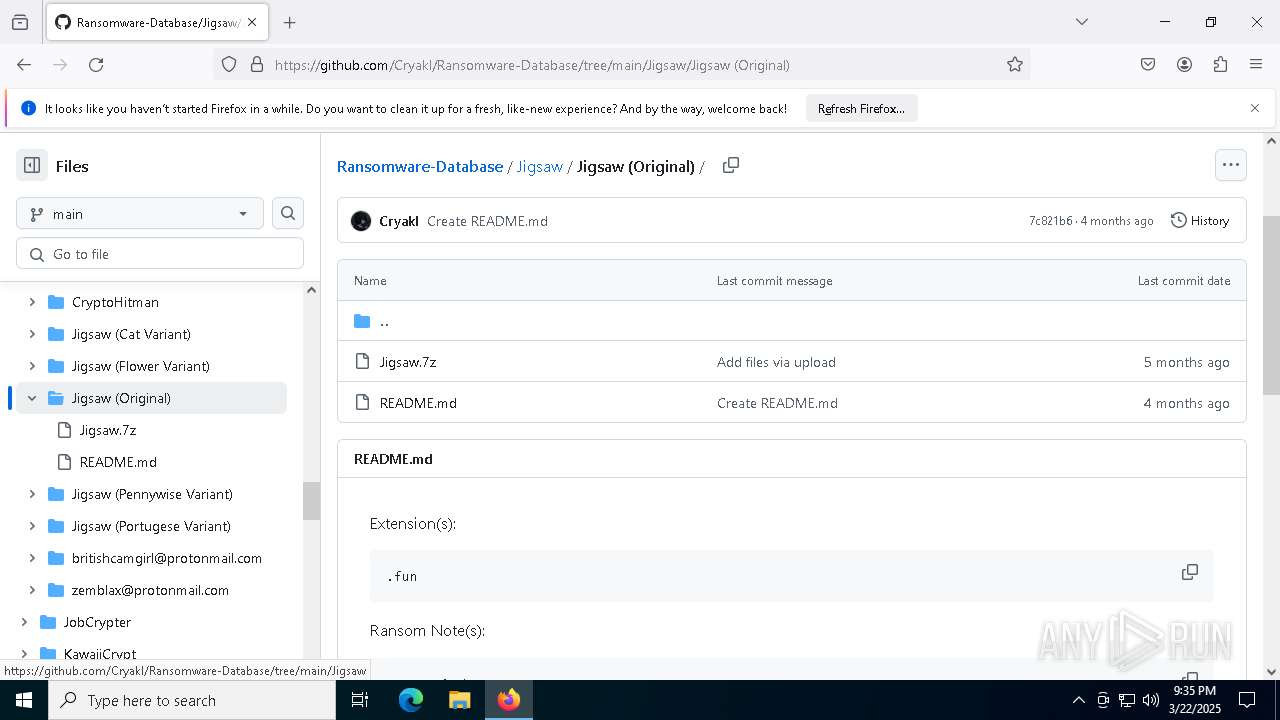
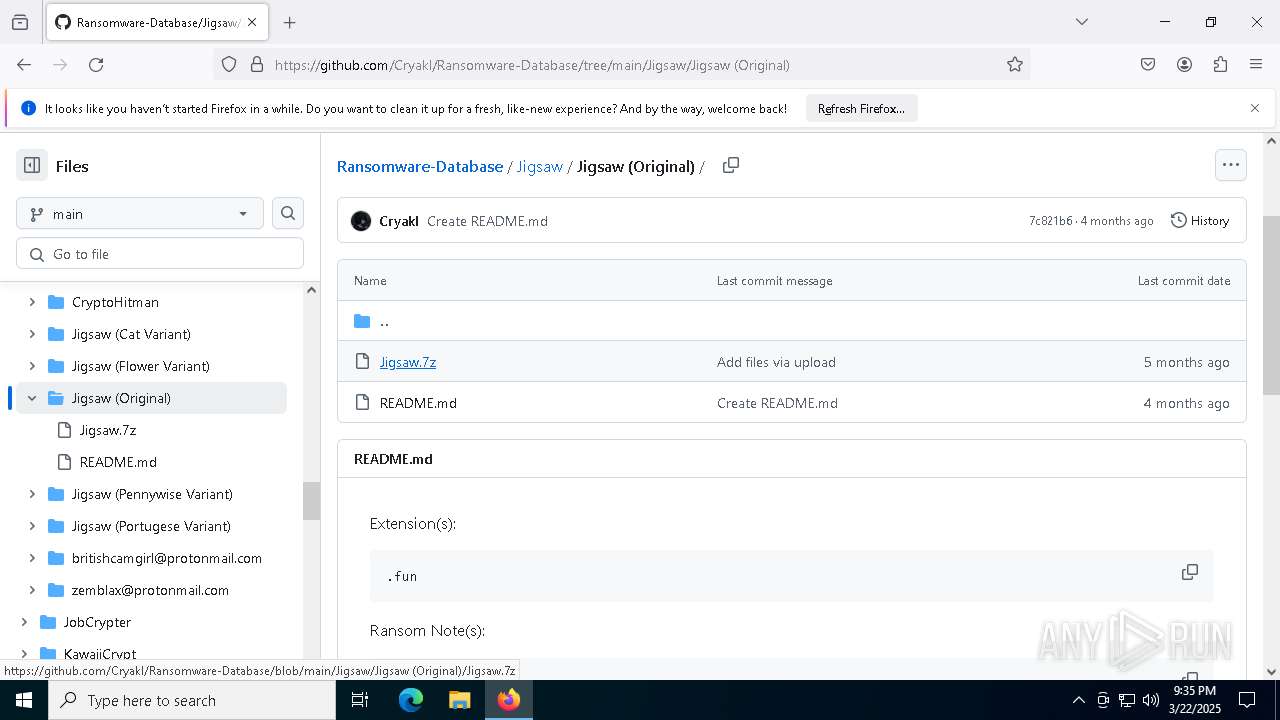
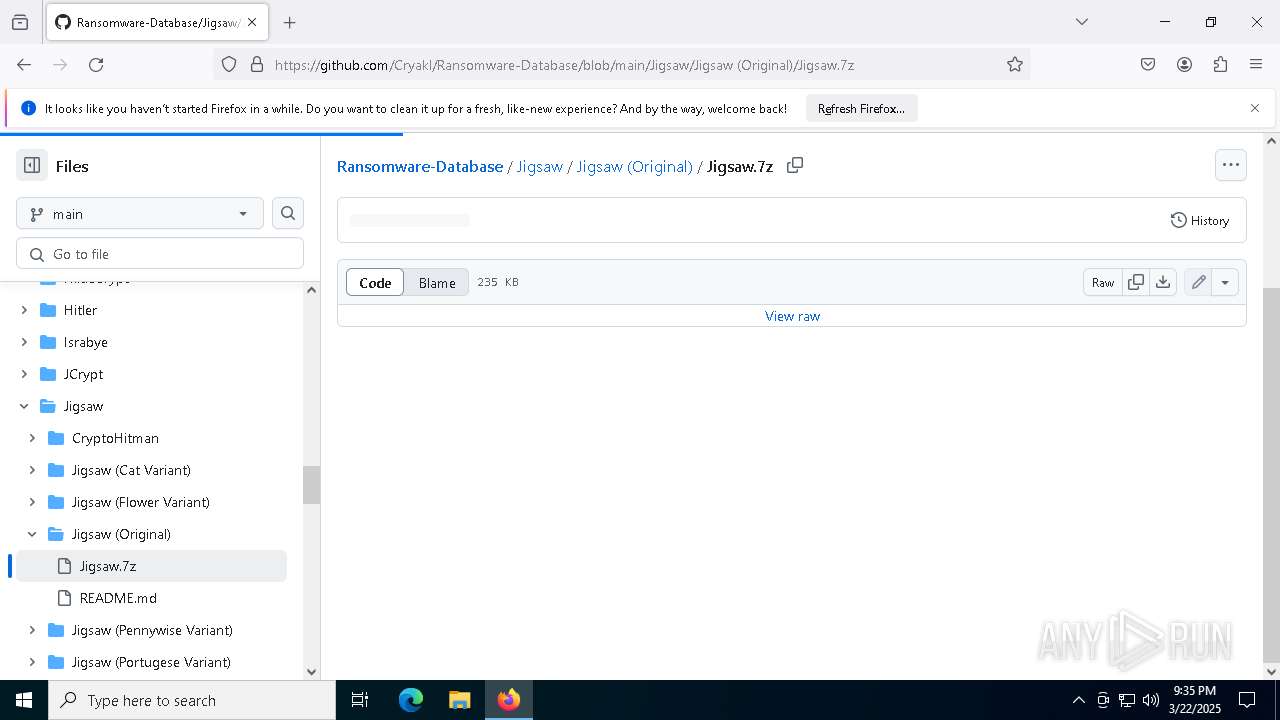
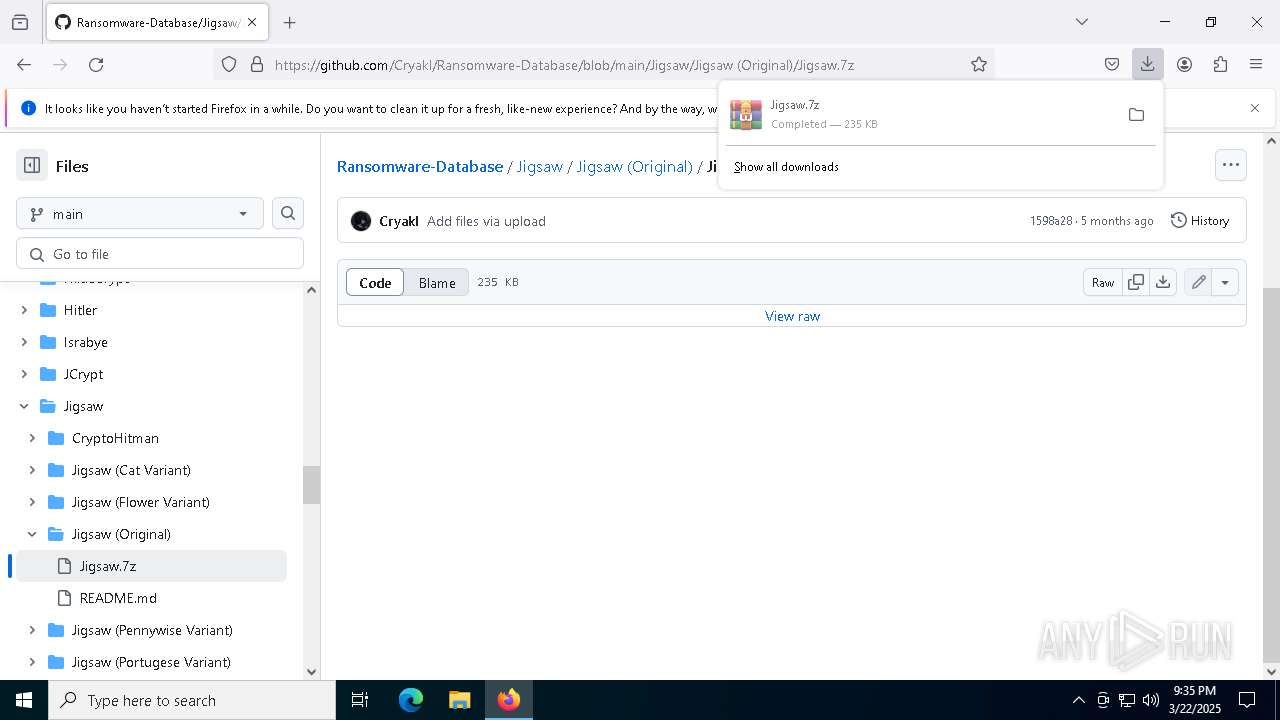
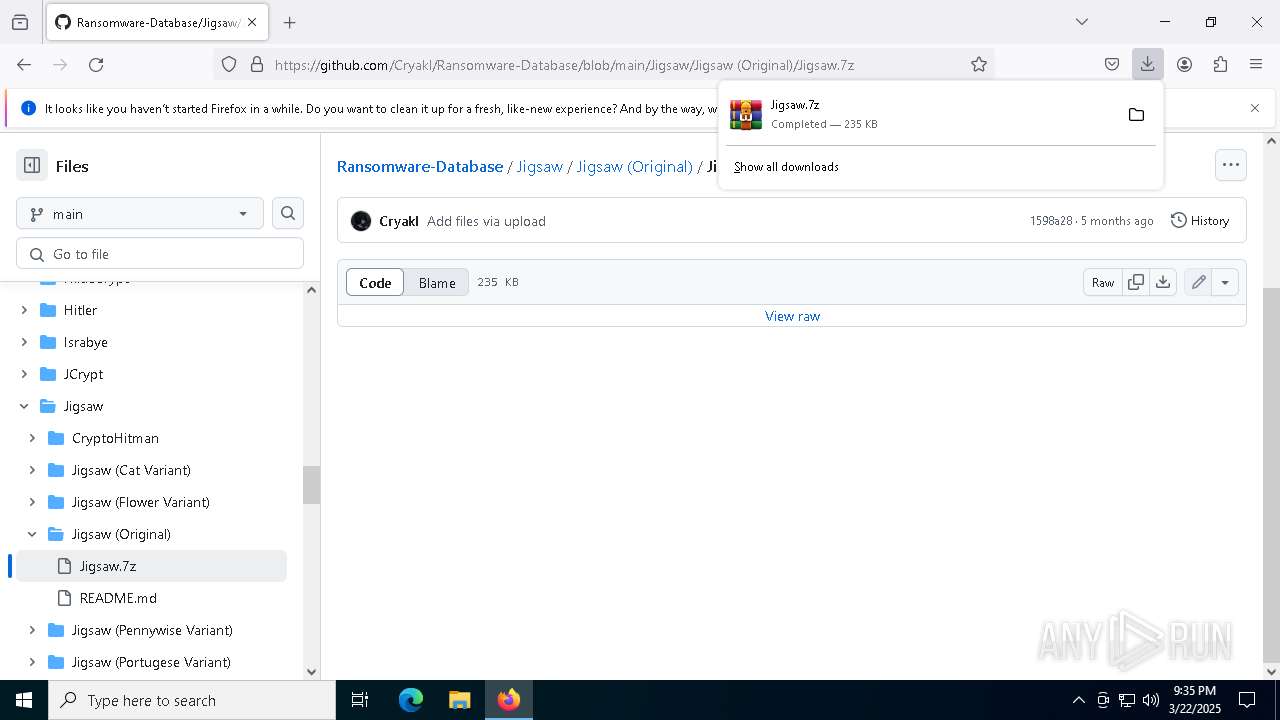
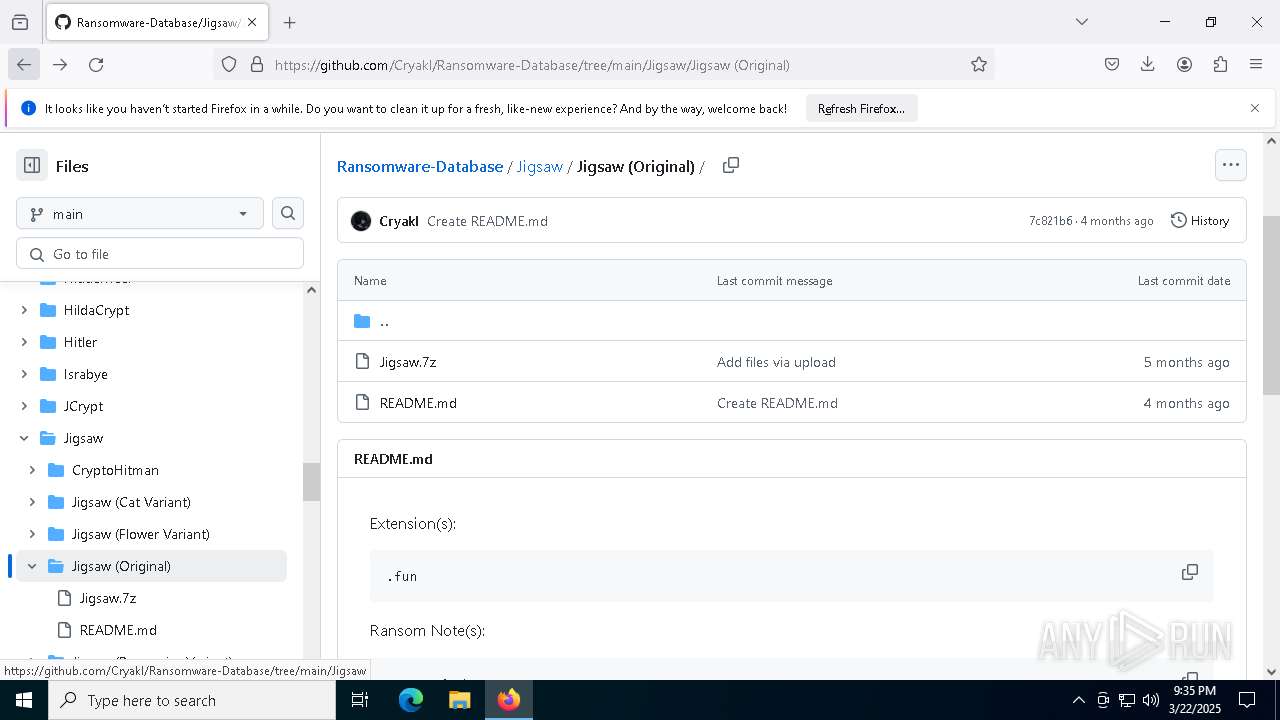
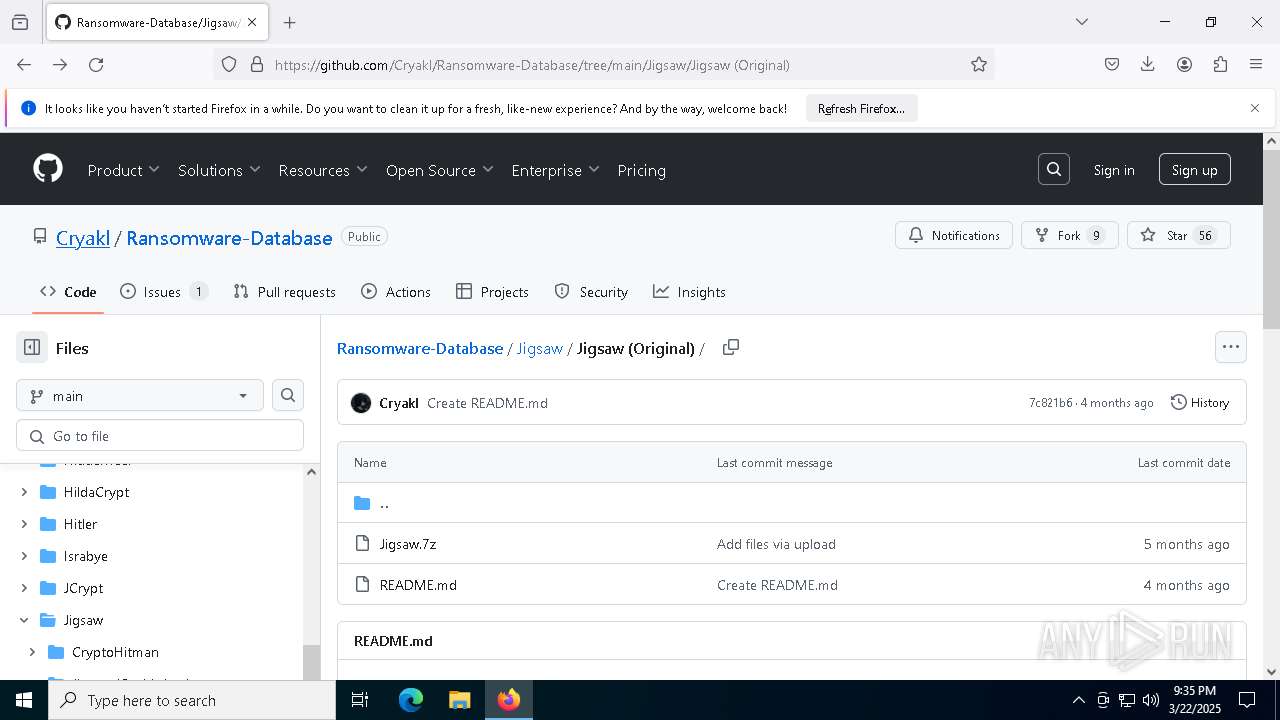
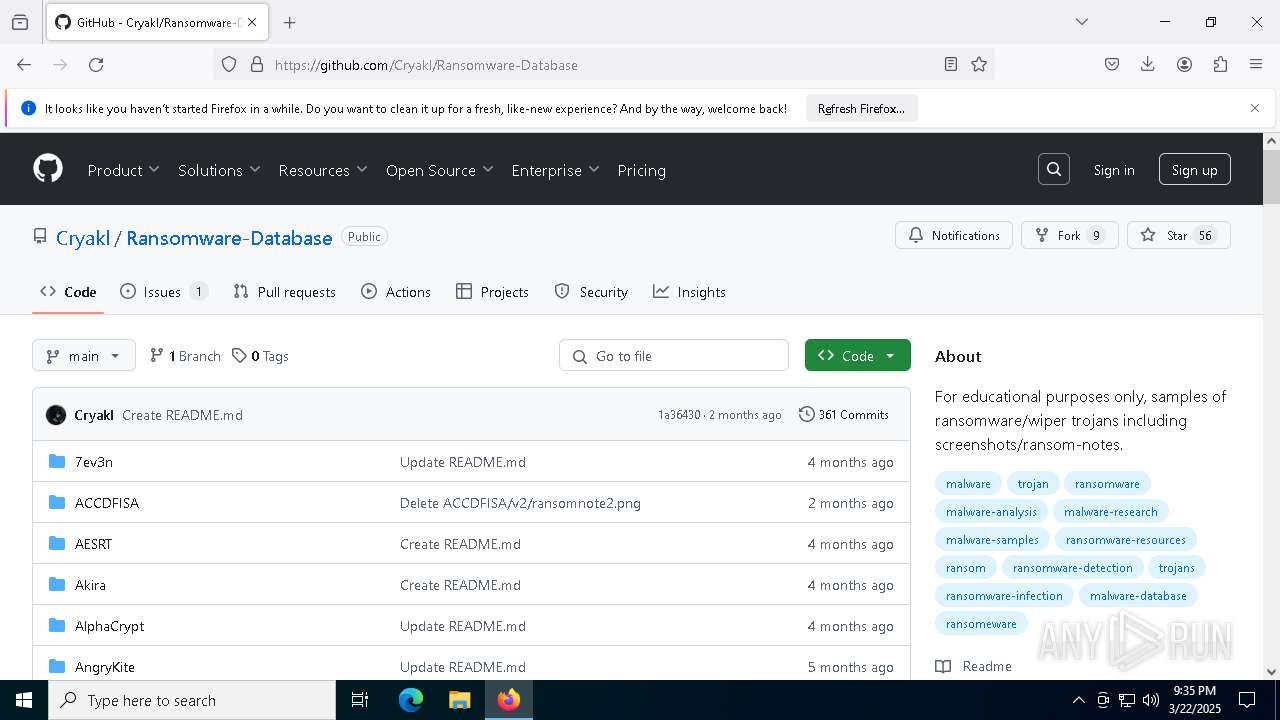
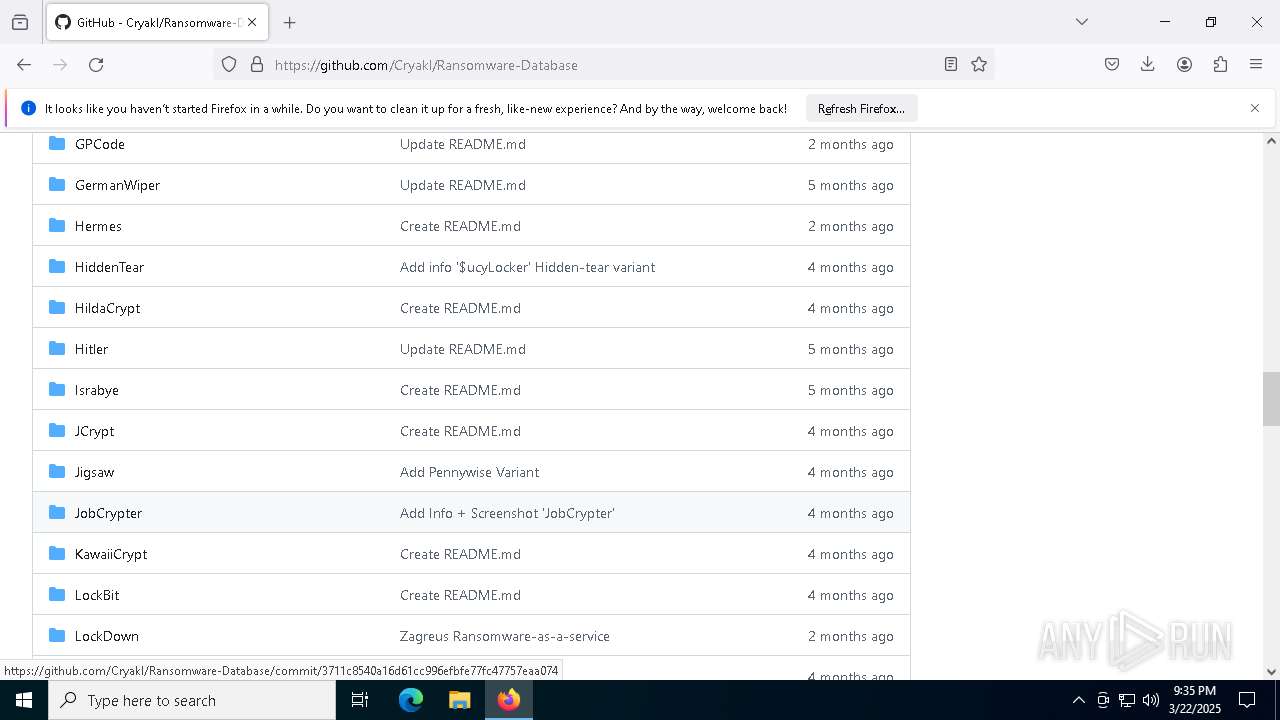
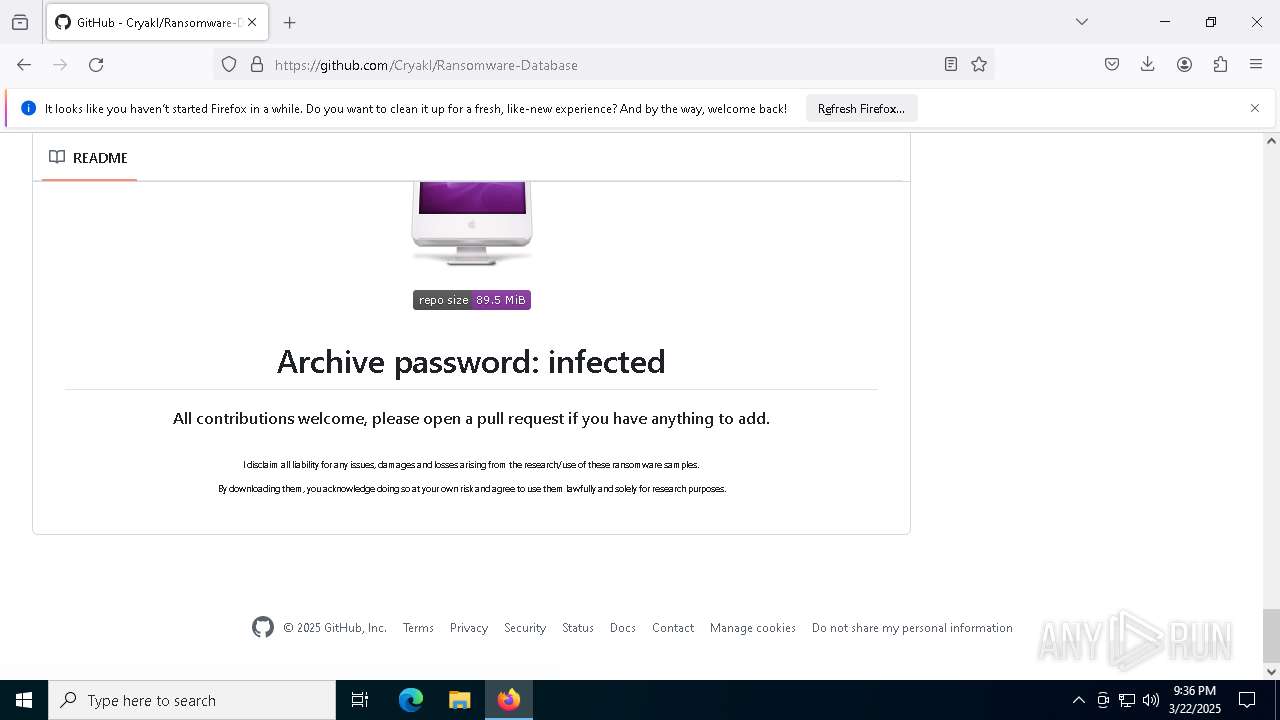
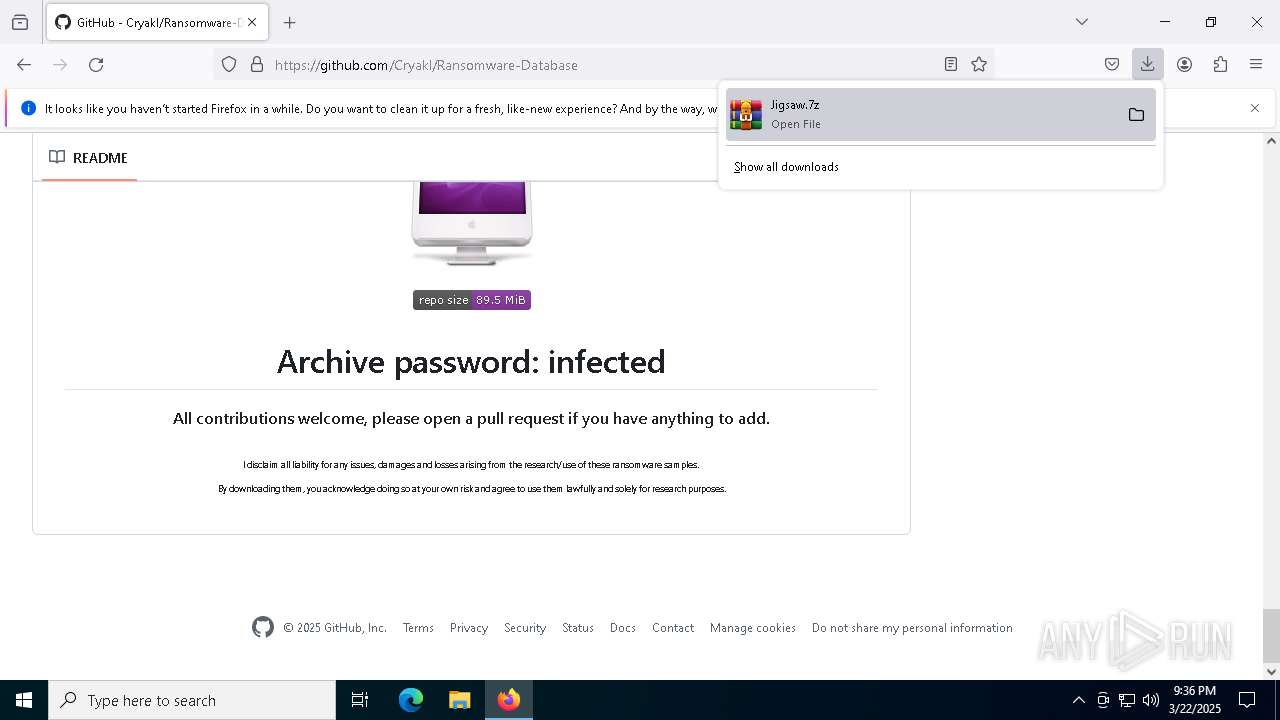
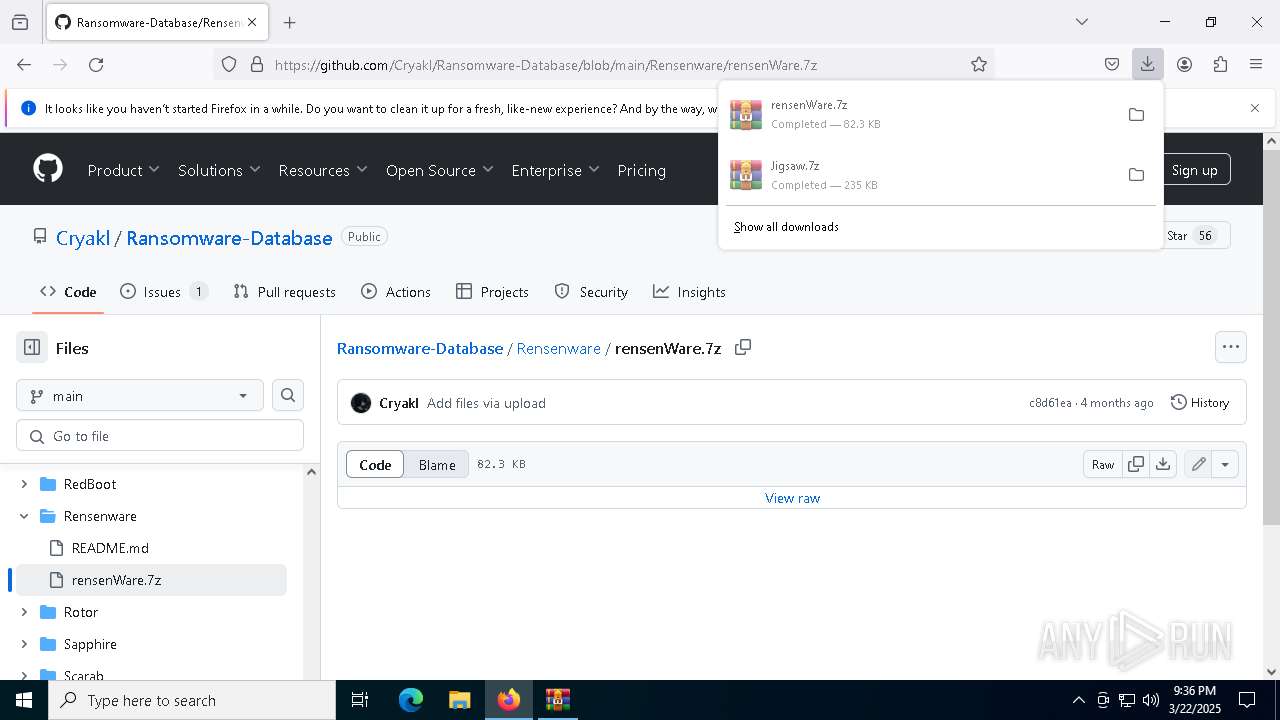
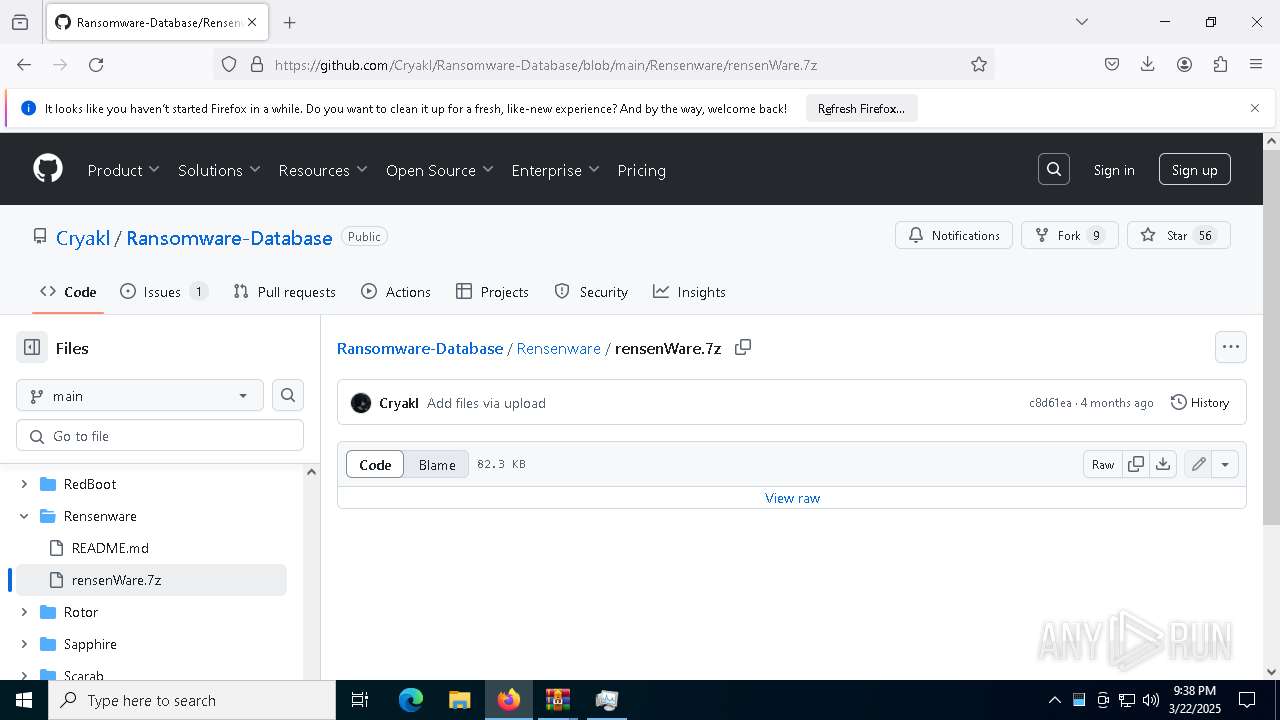
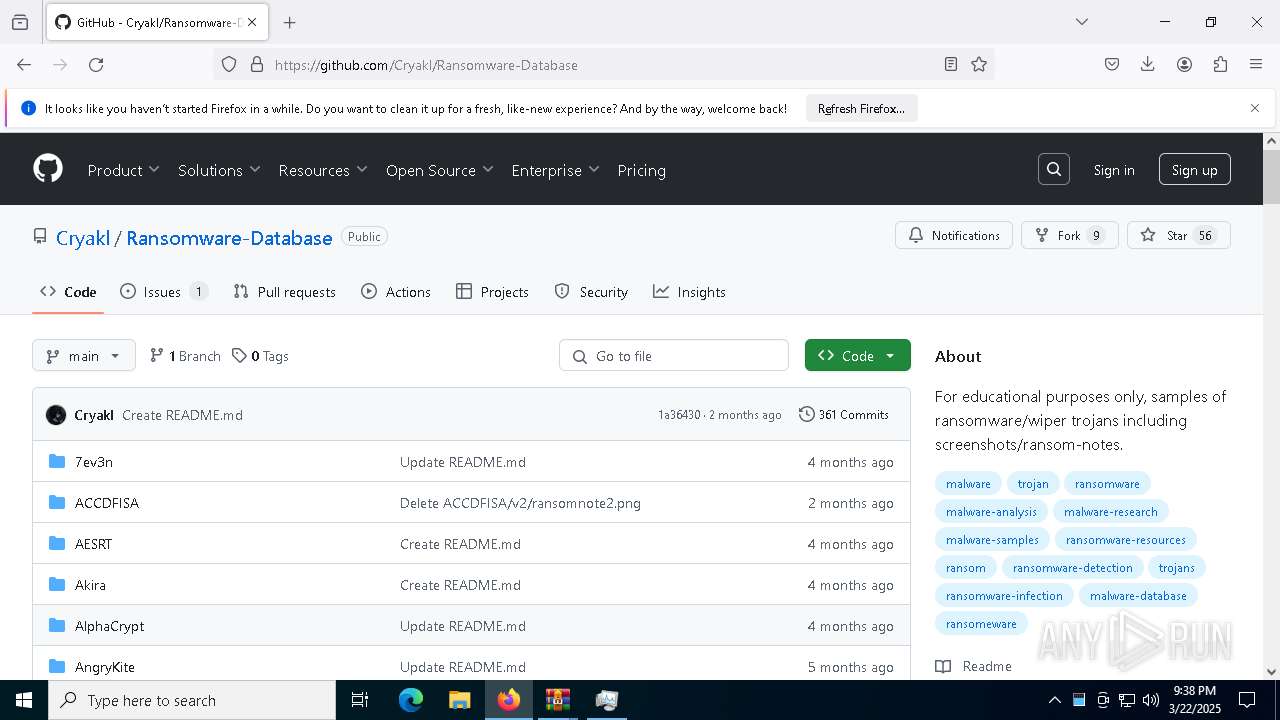
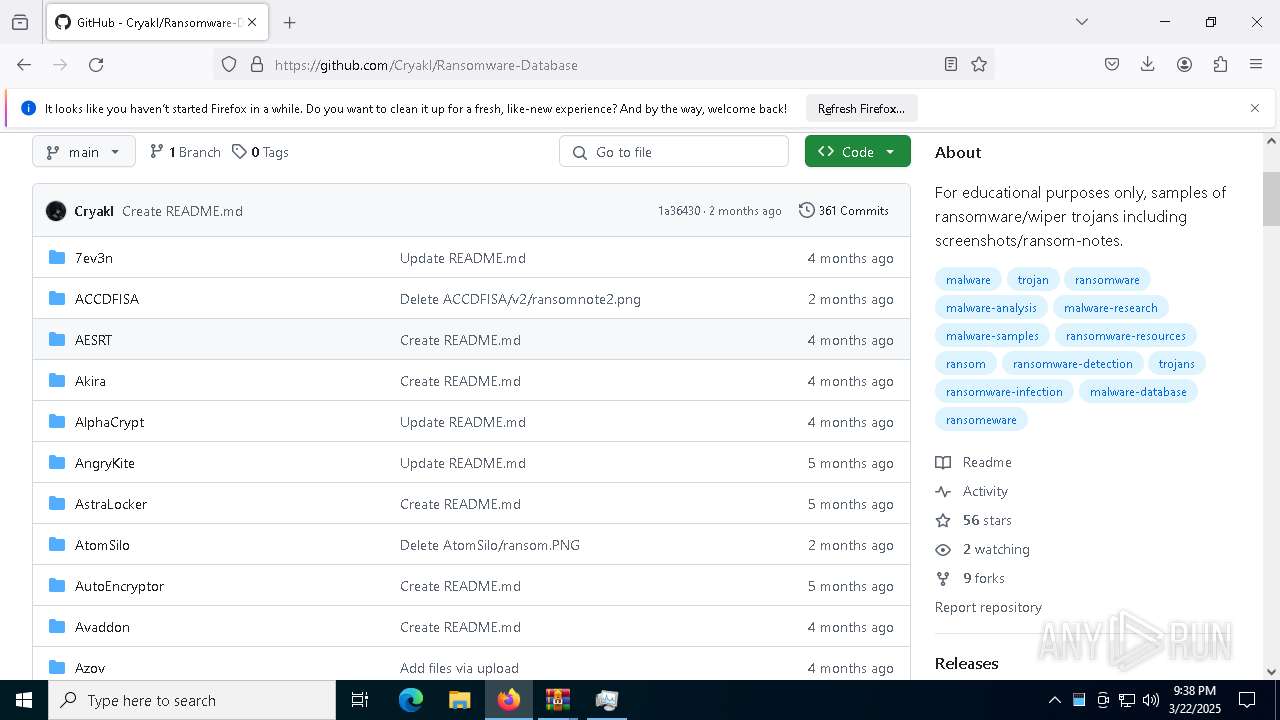
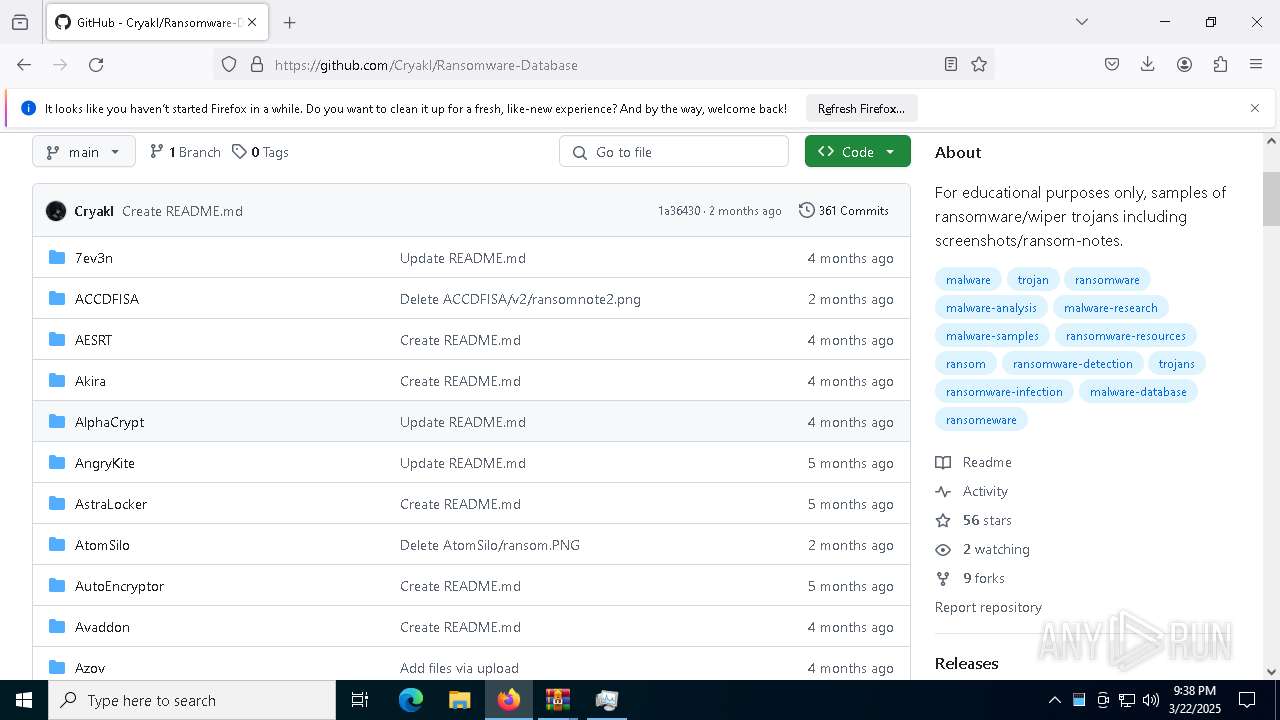
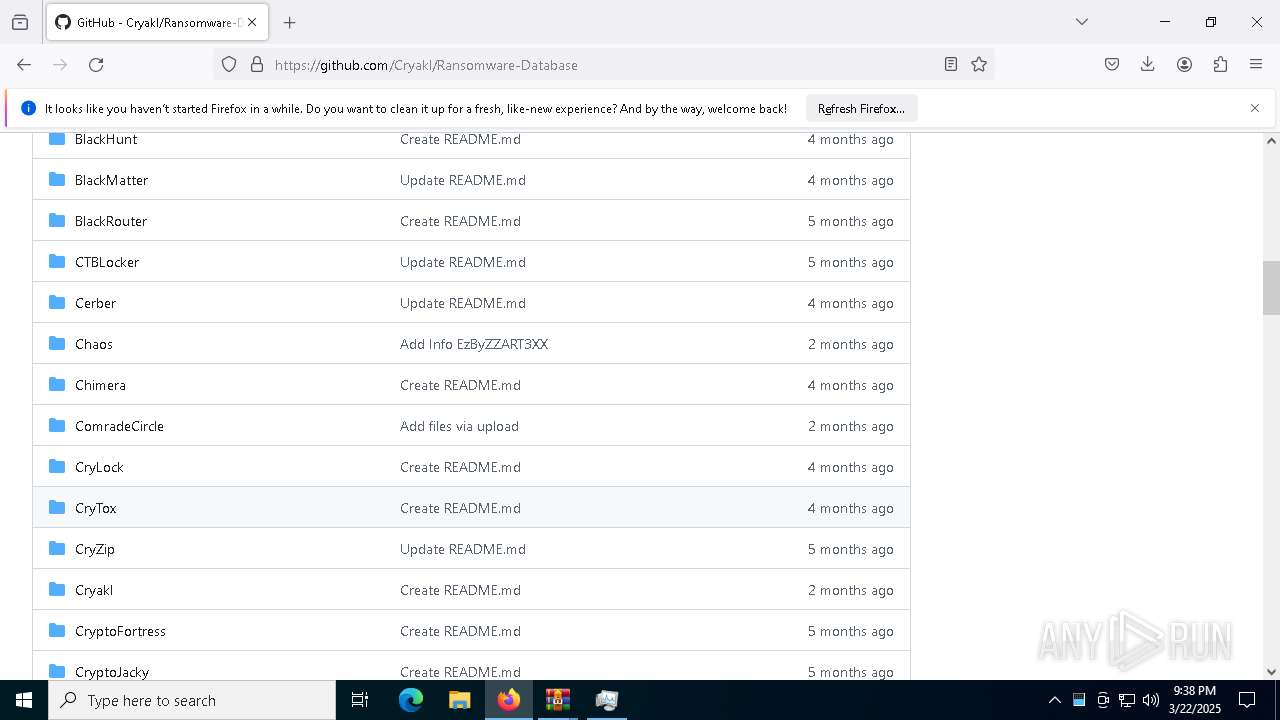
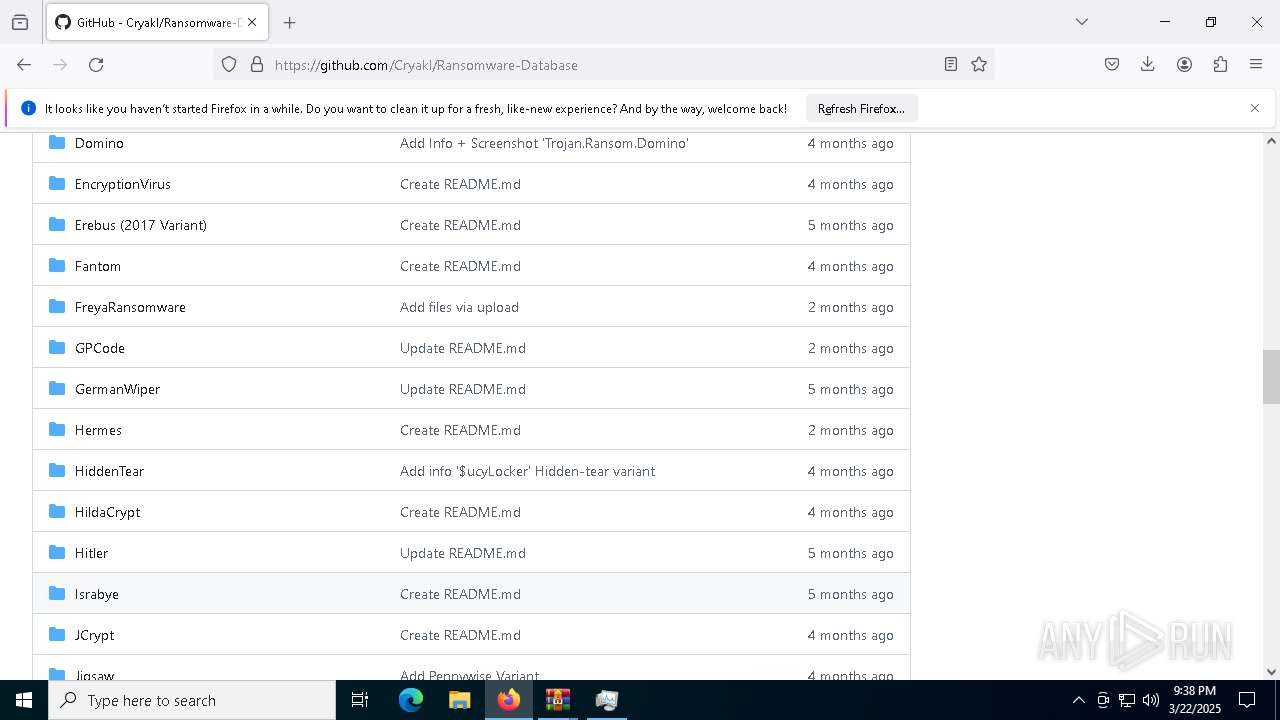
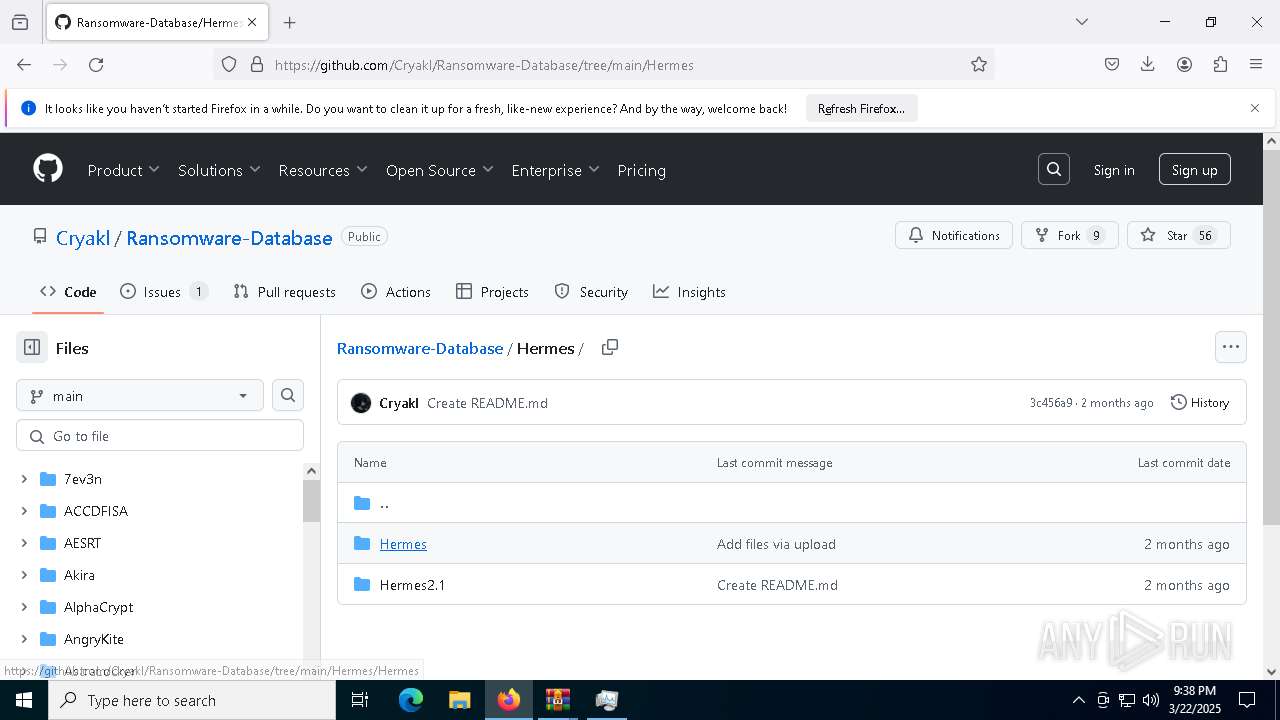
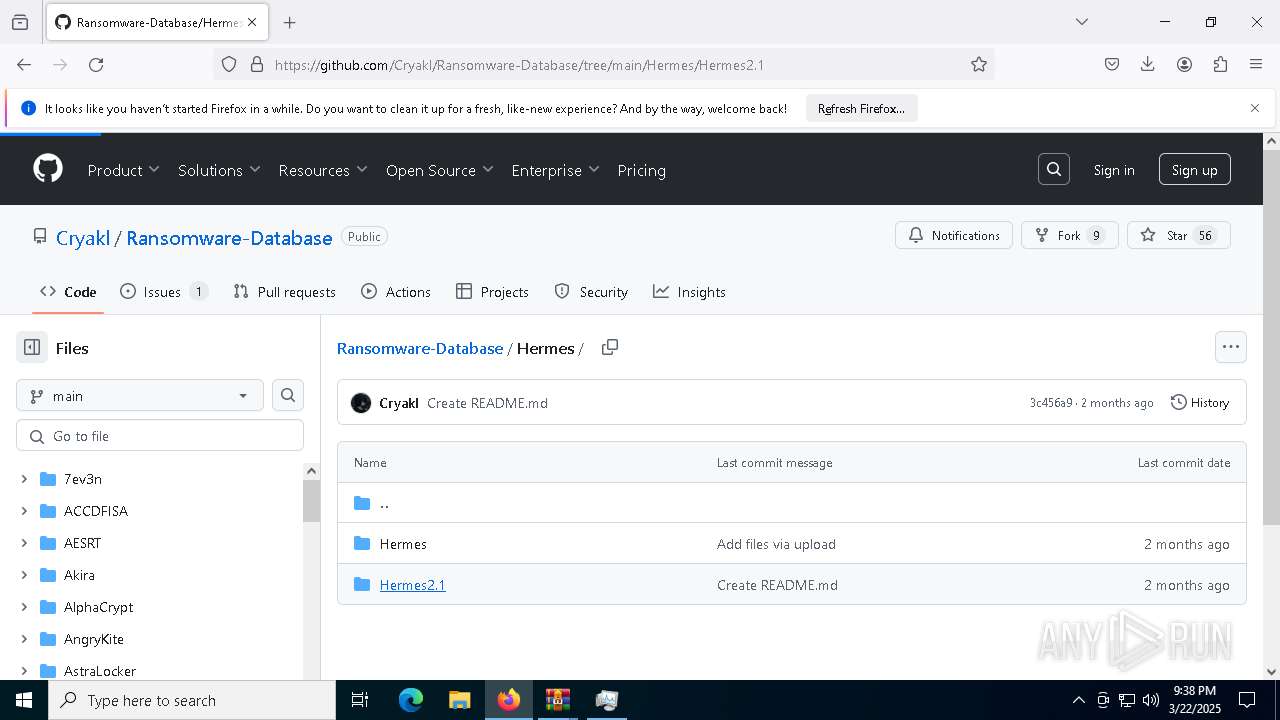
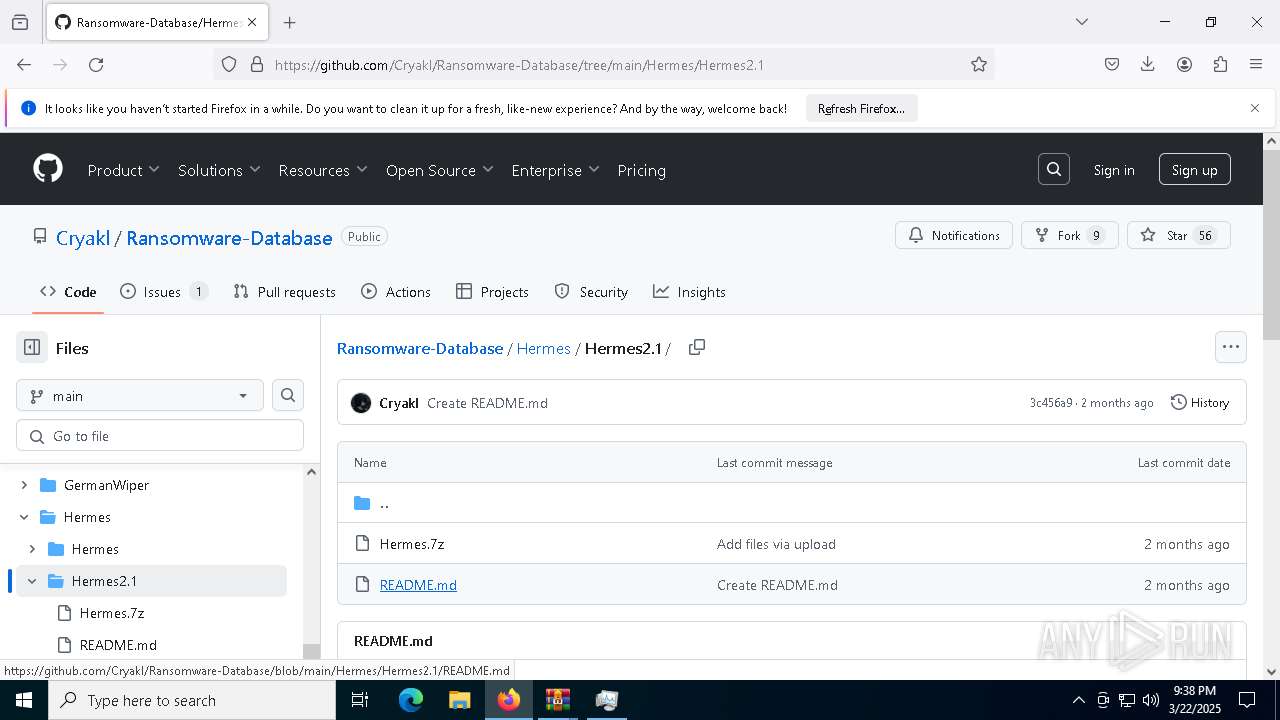
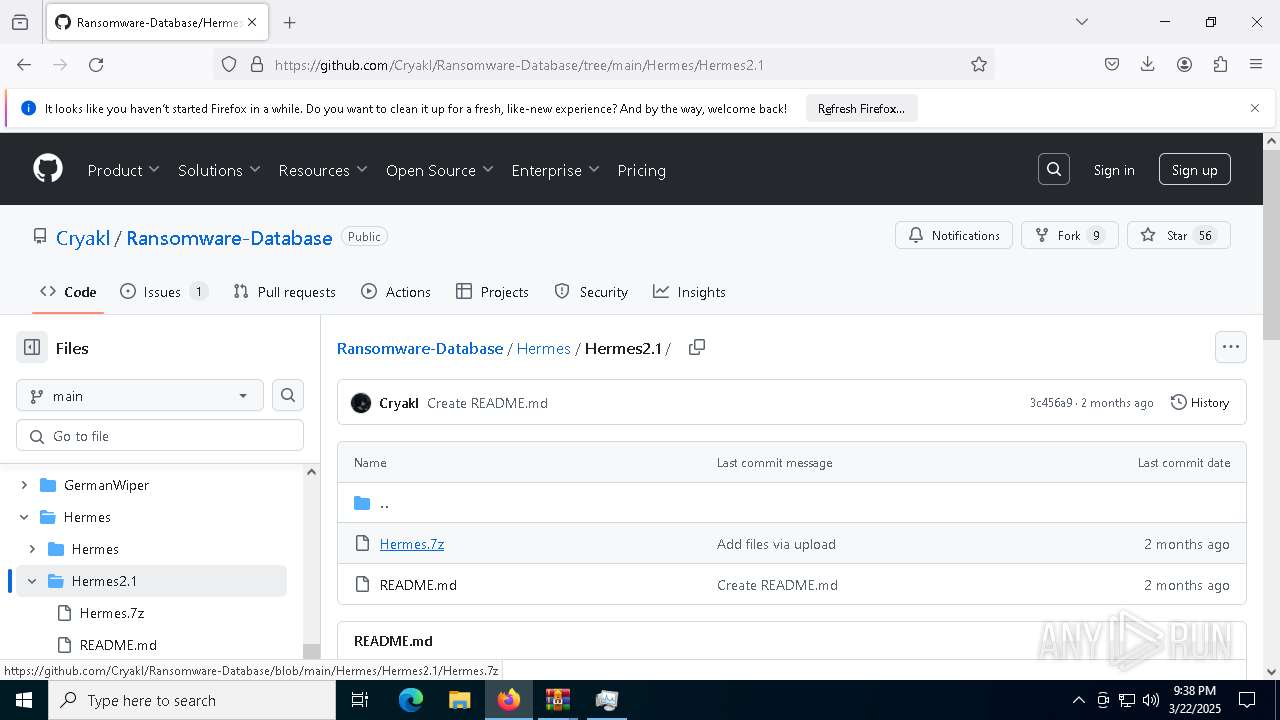
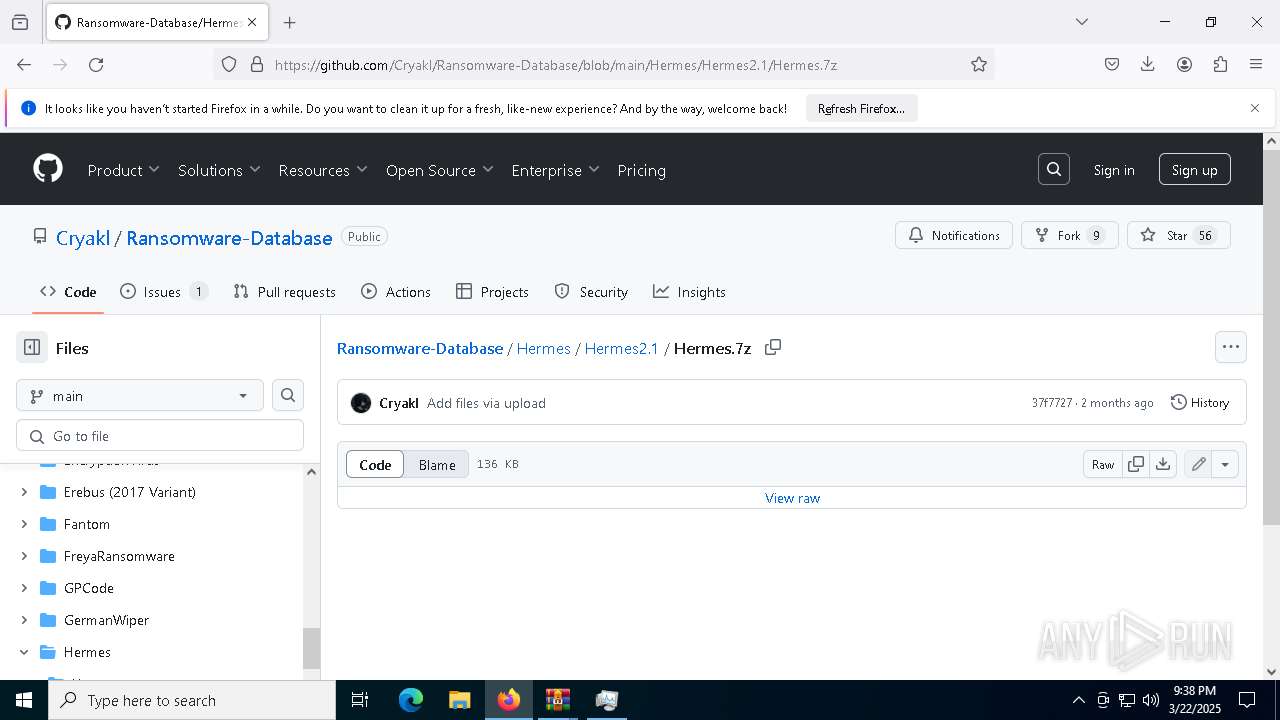
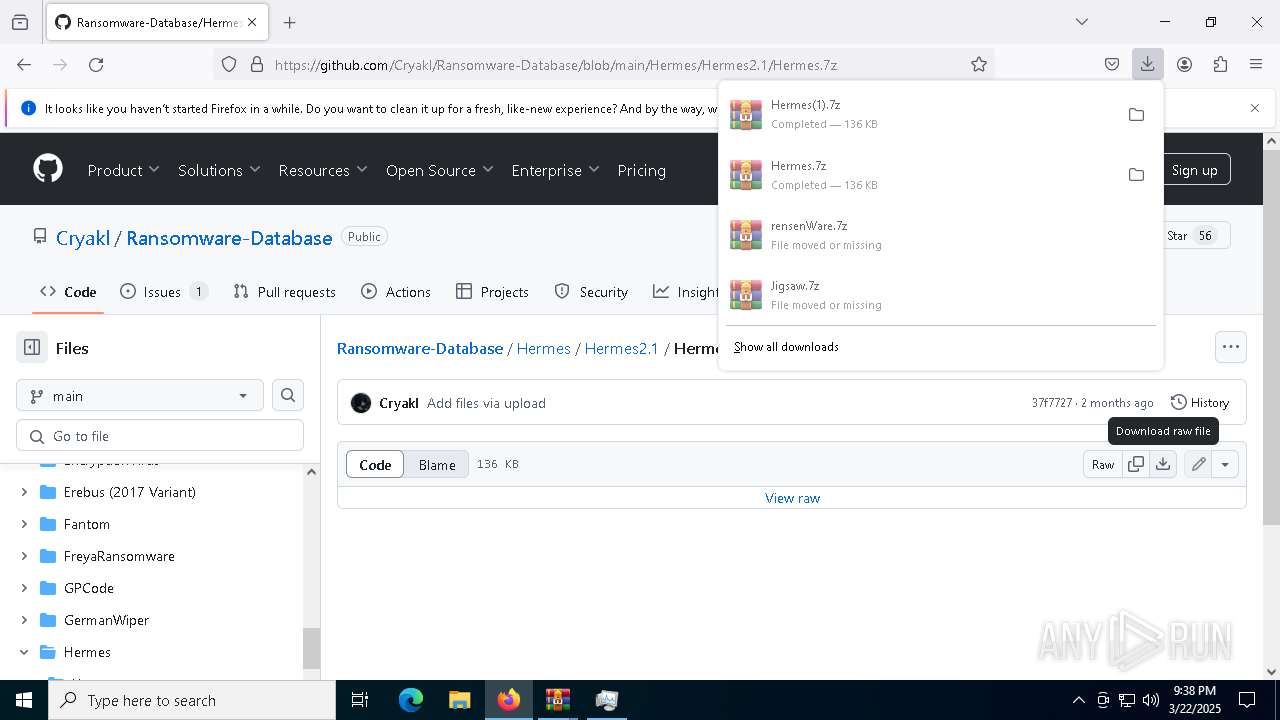
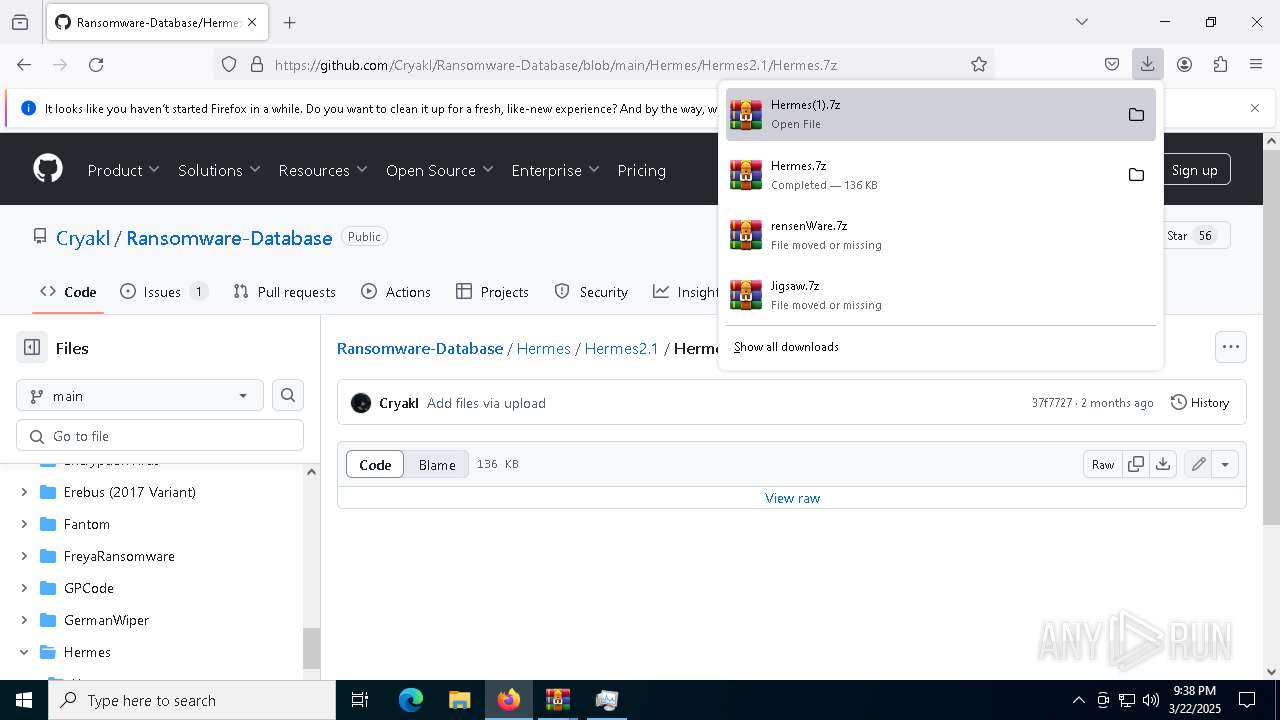
| URL: | https://github.com/Cryakl/Ransomware-Database |
| Full analysis: | https://app.any.run/tasks/23cddddd-20ab-4e7b-bcc3-a236fbce8c16 |
| Verdict: | Malicious activity |
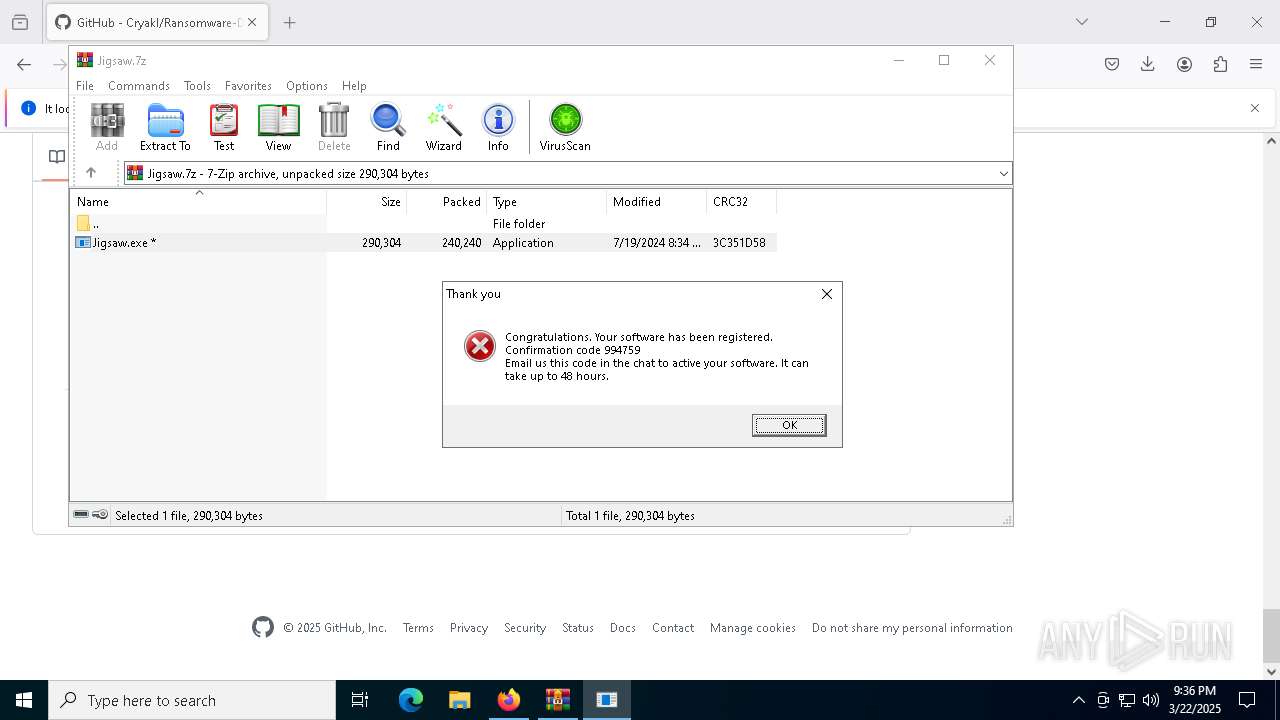
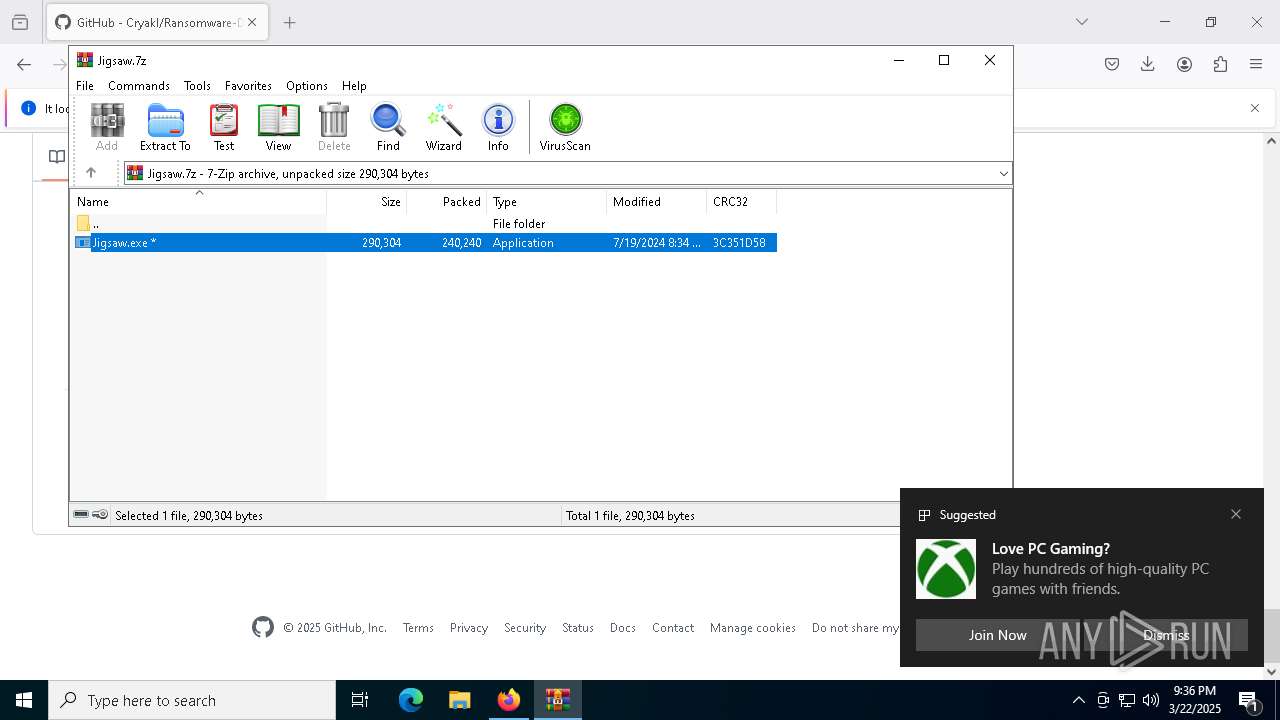
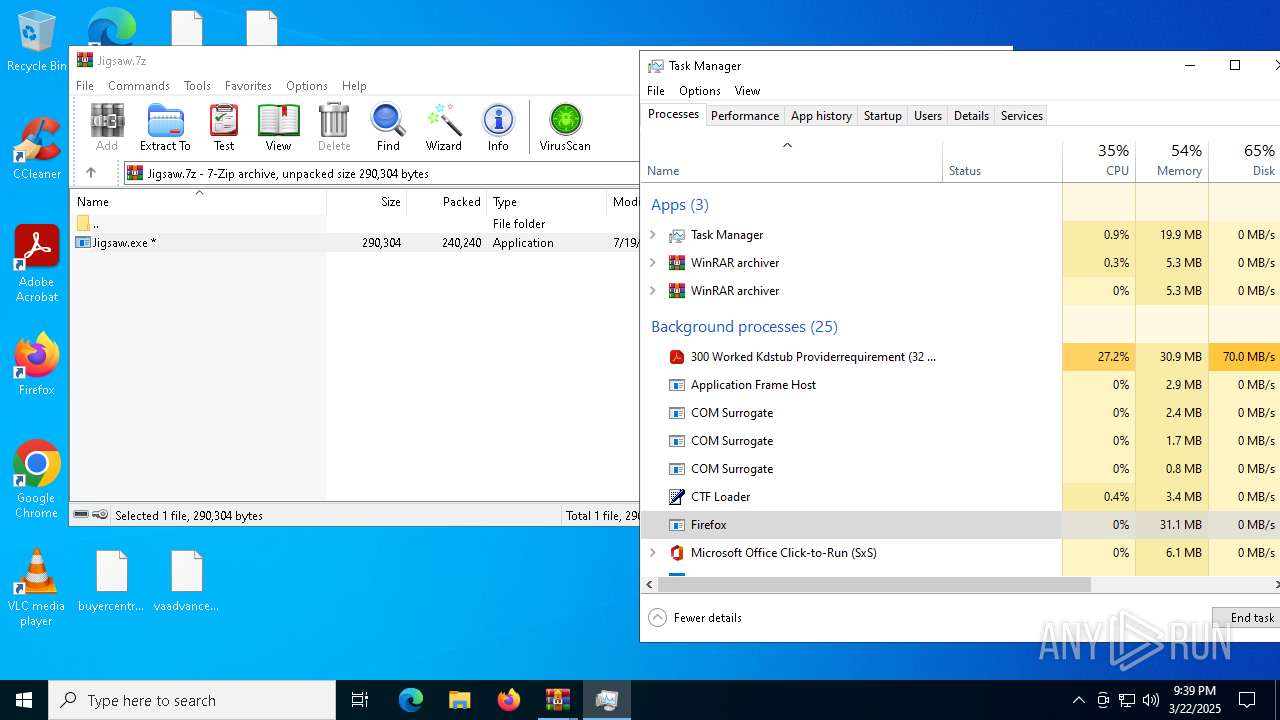
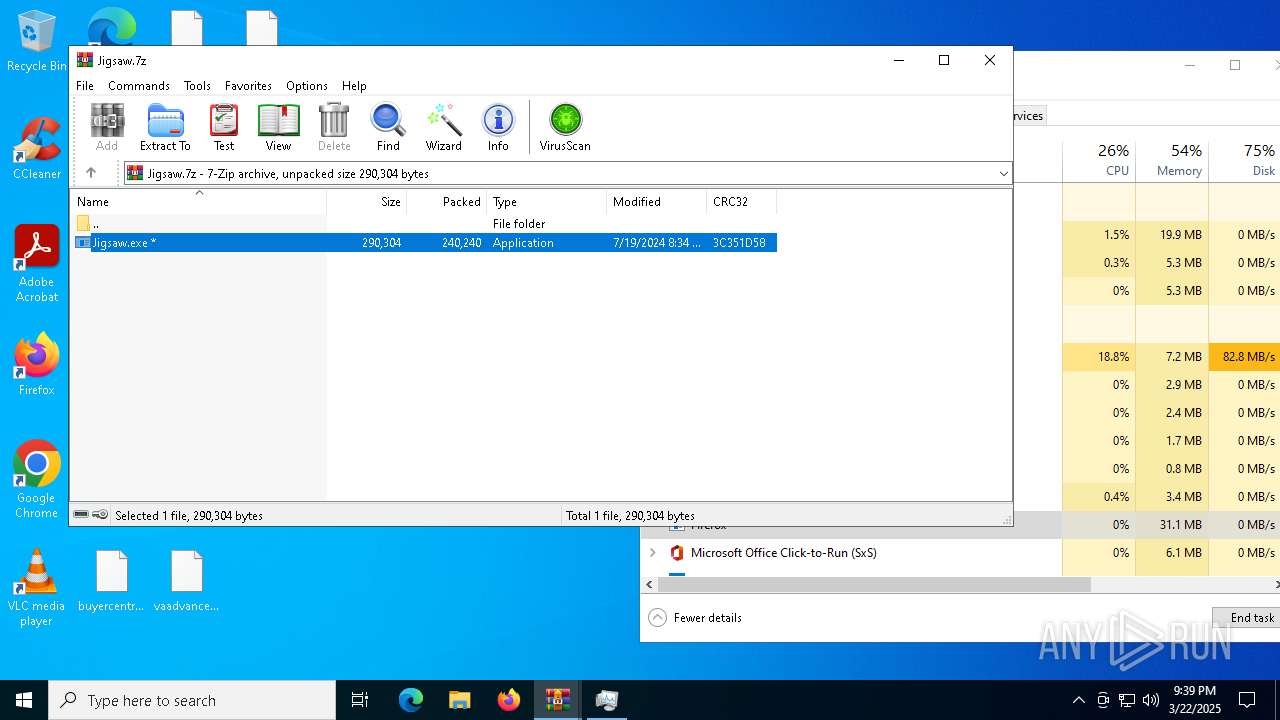
| Threats: | The Jigsaw ransomware, initially detected in 2016, encrypts files on compromised systems and requires a ransom payment in Bitcoin. If the ransom is not paid, the malware starts deleting files, increasing the pressure on victims to comply. Its source code is publicly accessible, allowing various threat actors to customize and repurpose the malware for different objectives. |
| Analysis date: | March 22, 2025, 21:35:17 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 48822409D7D56E68EA5BAD4F921C232C |
| SHA1: | 32806BF6750F505BB5B6FFF266E289C11C23506B |
| SHA256: | 20F7D194C032C497EF9AC6A8344DFD46F2A0E026B684A783BA9F4A4D2177FD85 |
| SSDEEP: | 3:N8tEdJE3EIIREHI:2uPehIkI |
MALICIOUS
Changes the autorun value in the registry
- Jigsaw.exe (PID: 9044)
JIGSAW has been detected
- Jigsaw.exe (PID: 9044)
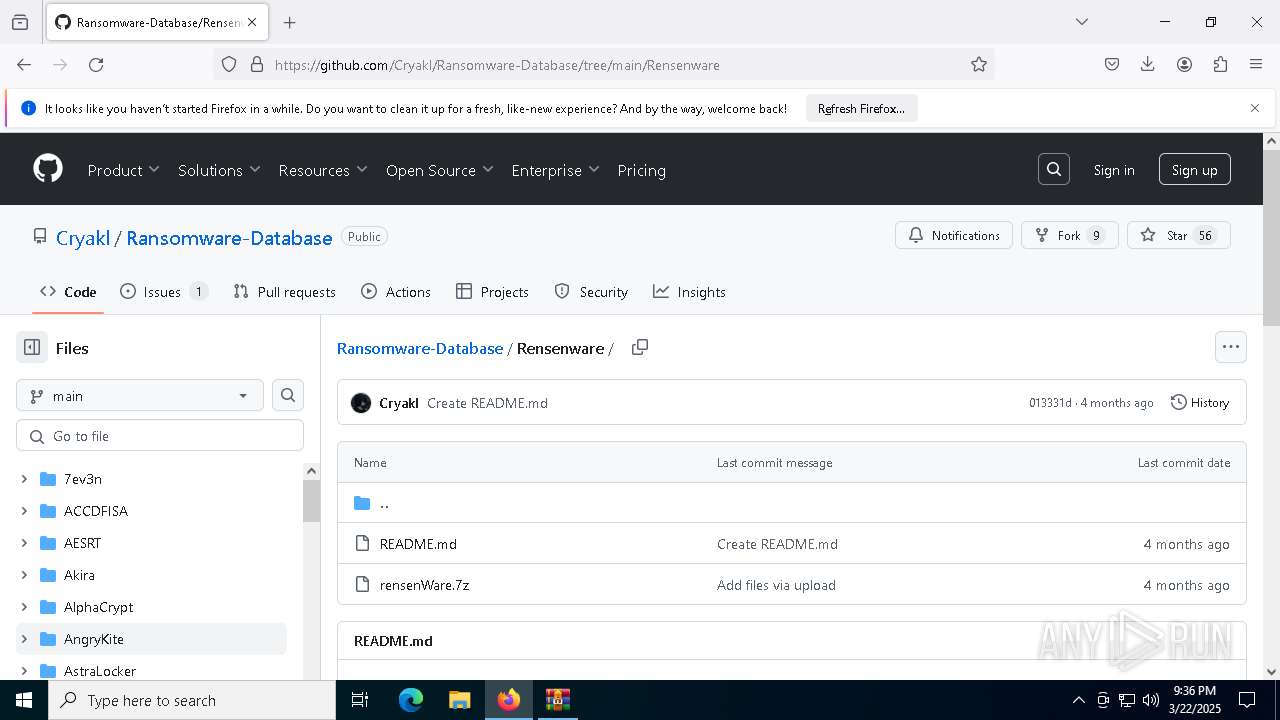
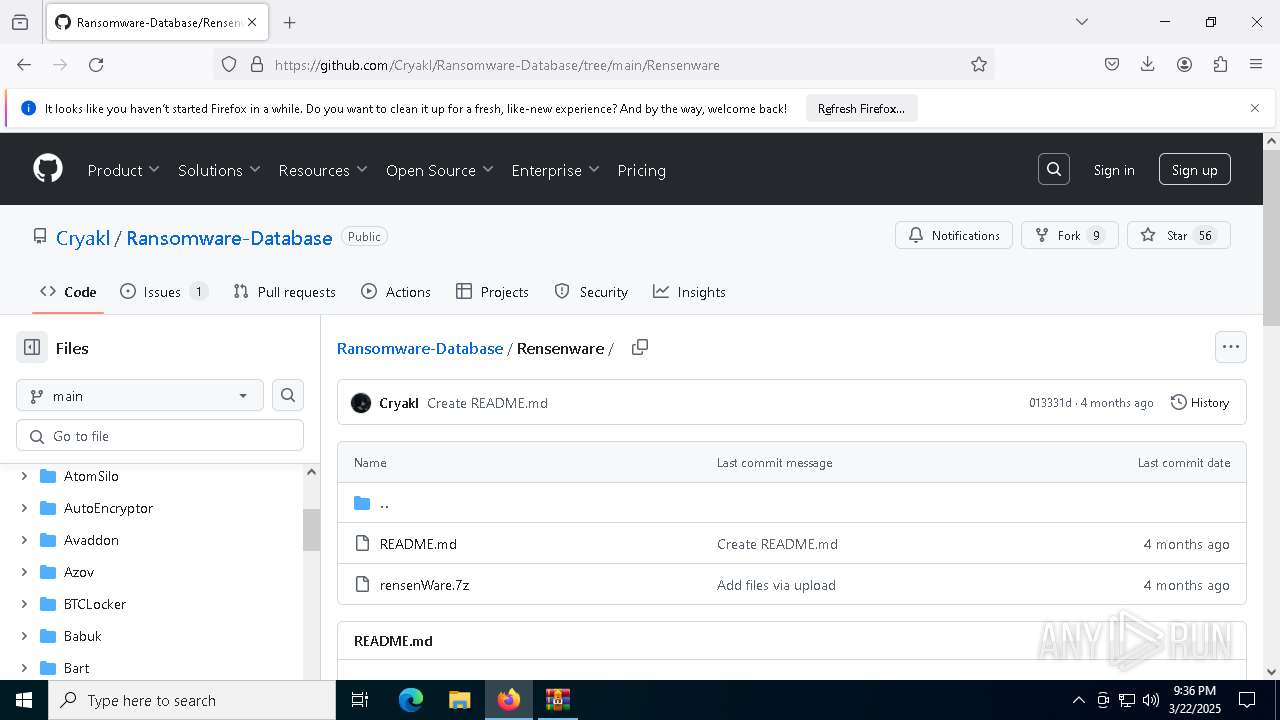
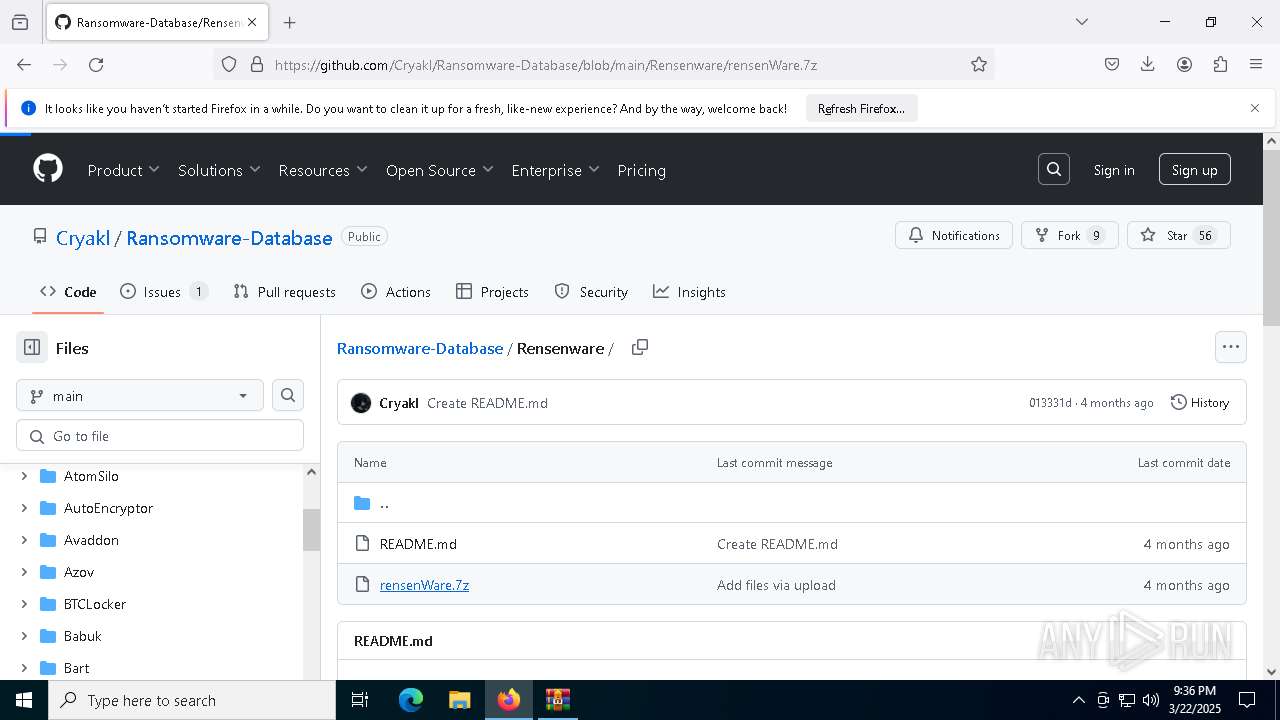
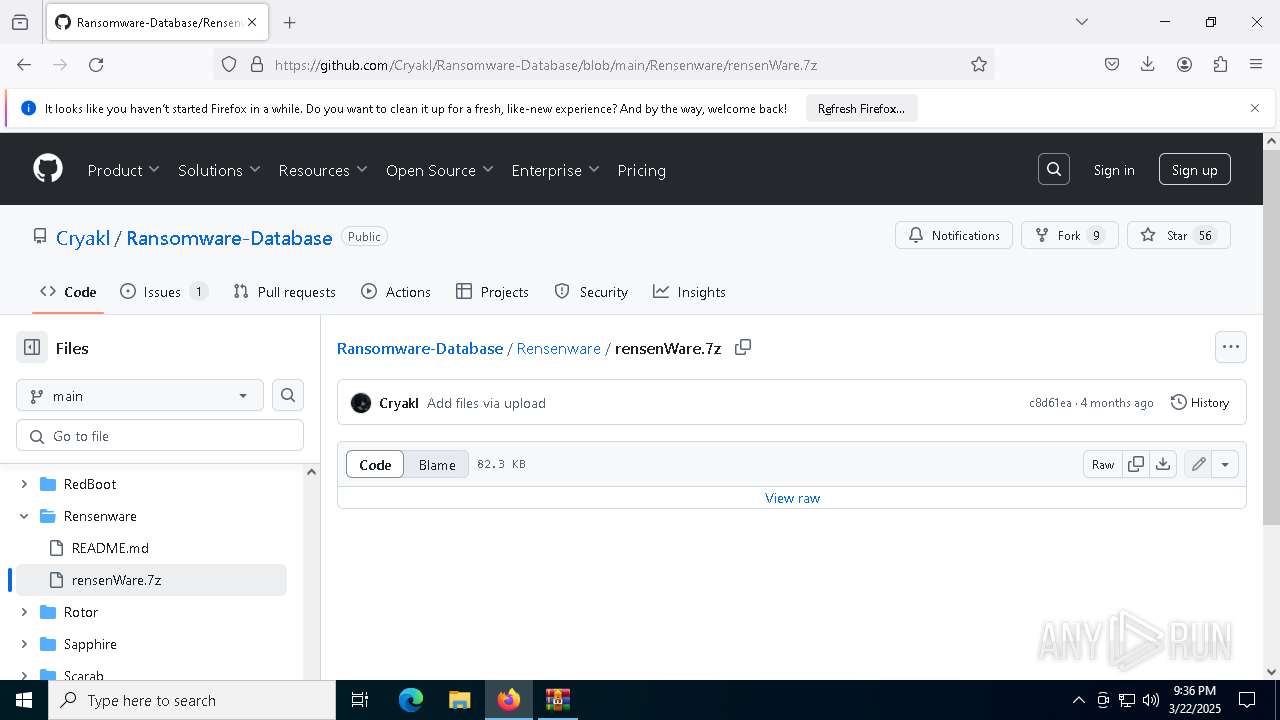
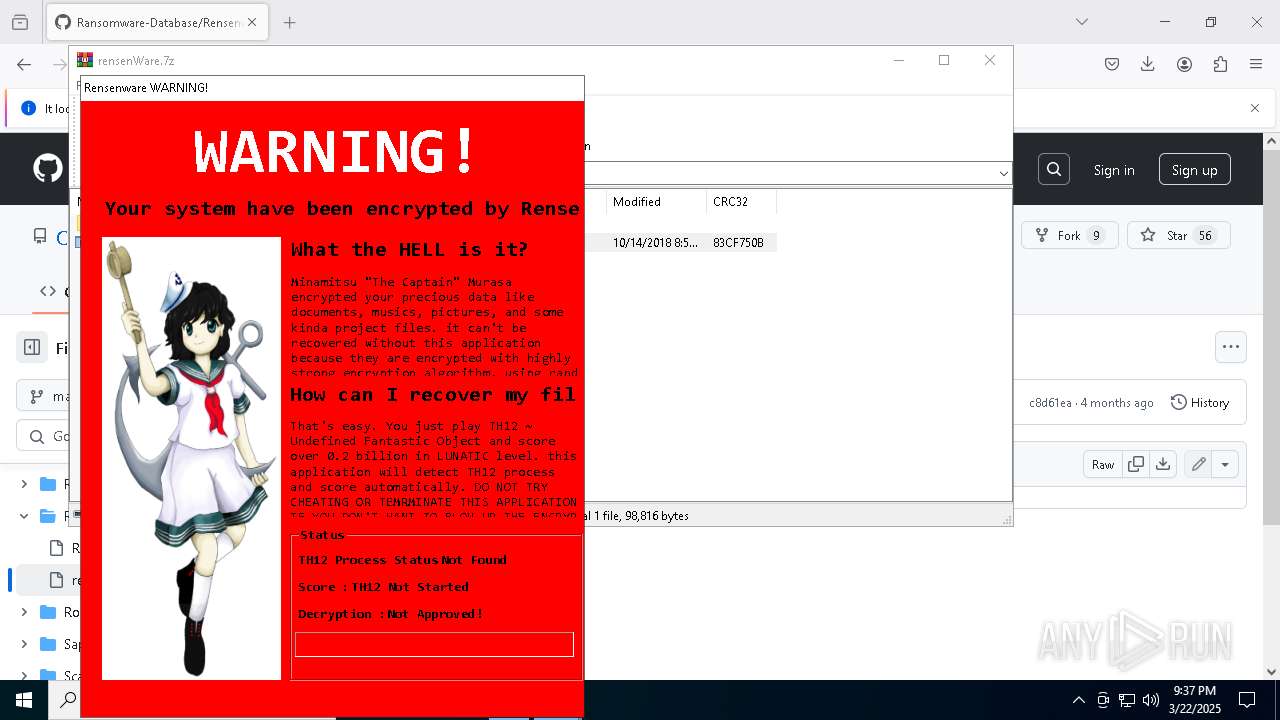
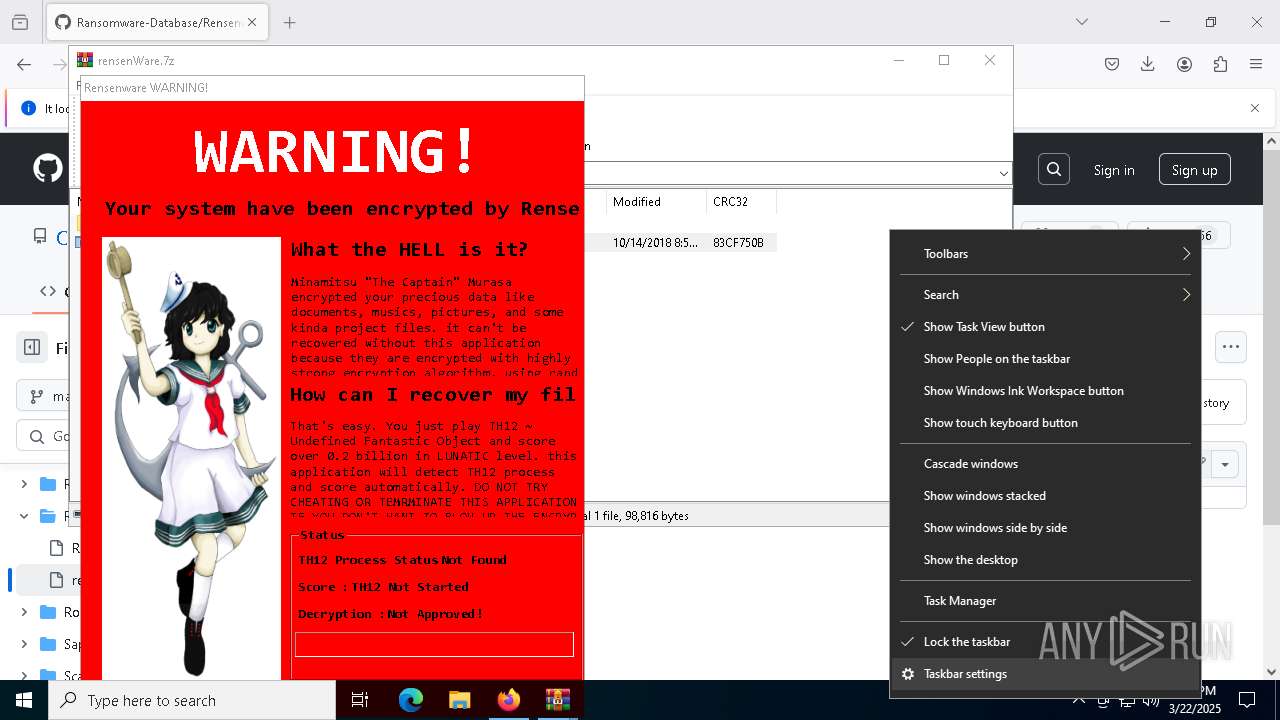
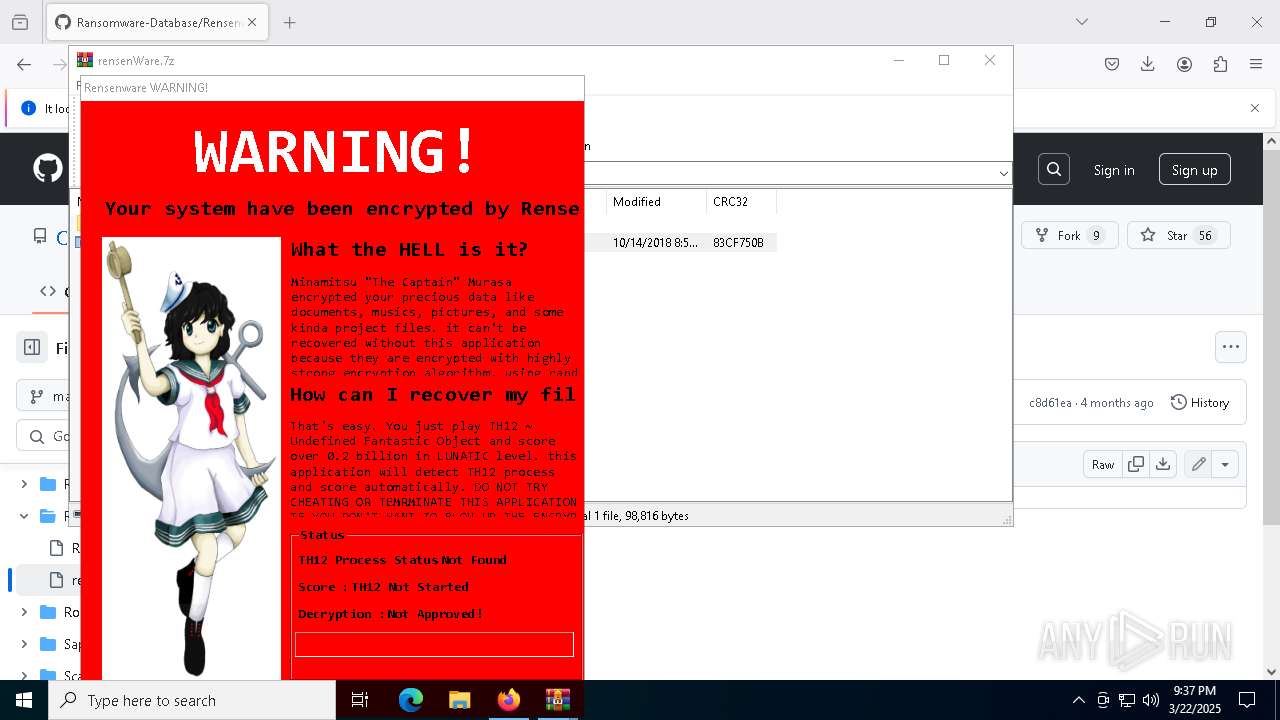
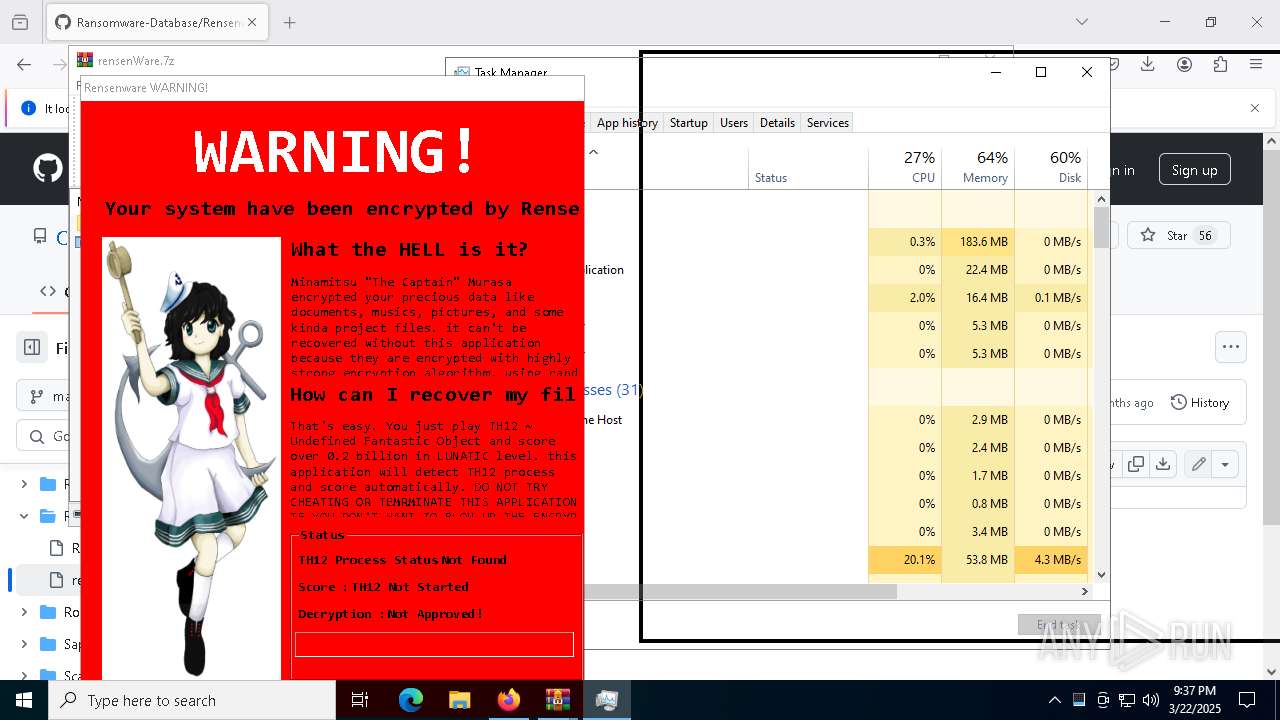
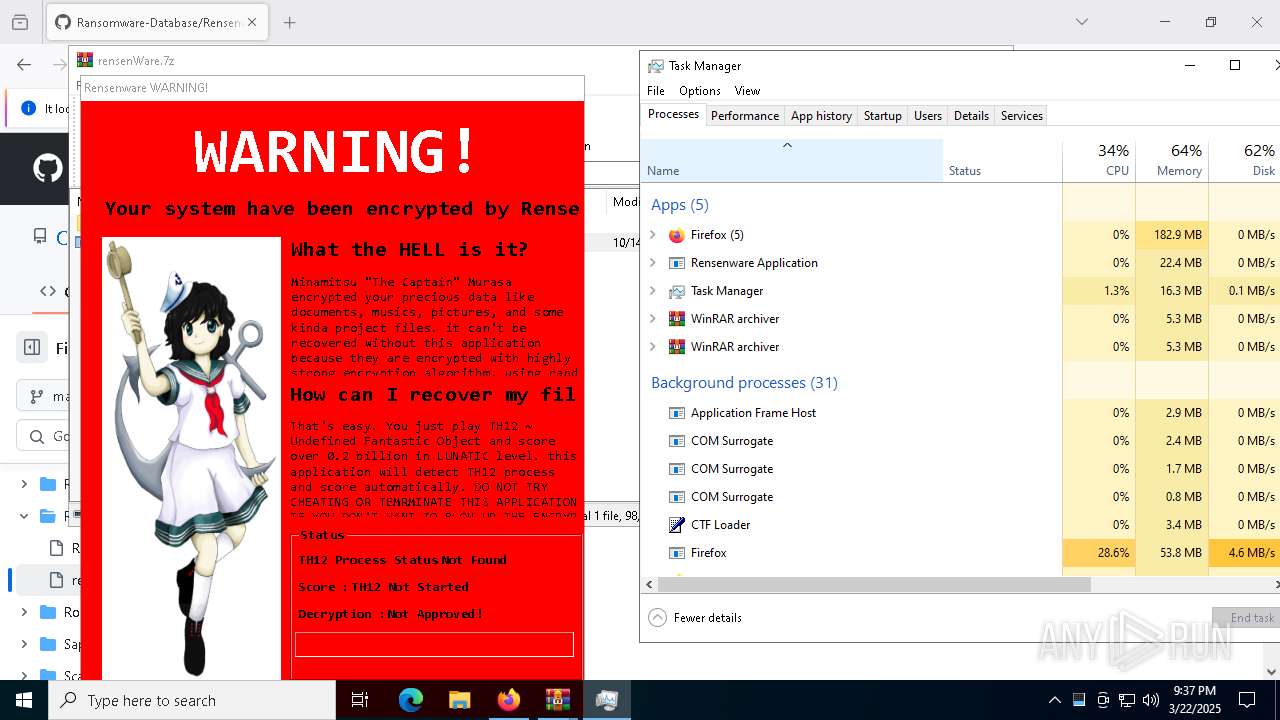
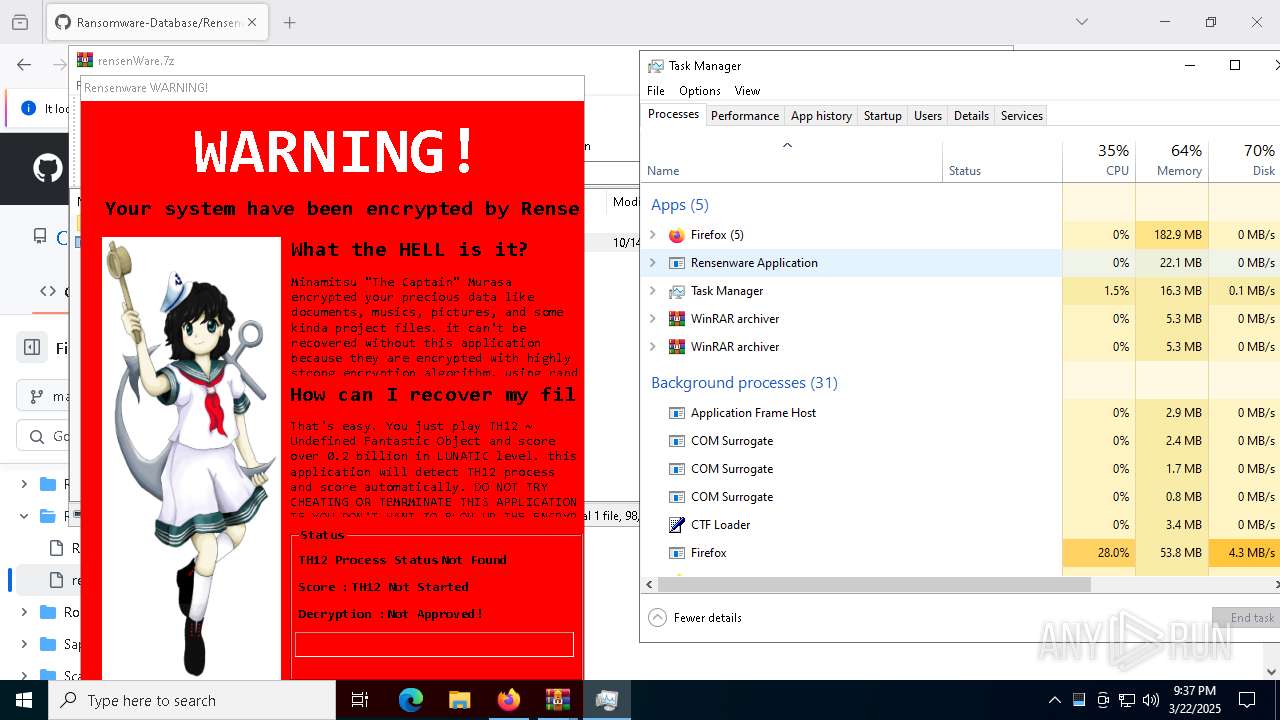
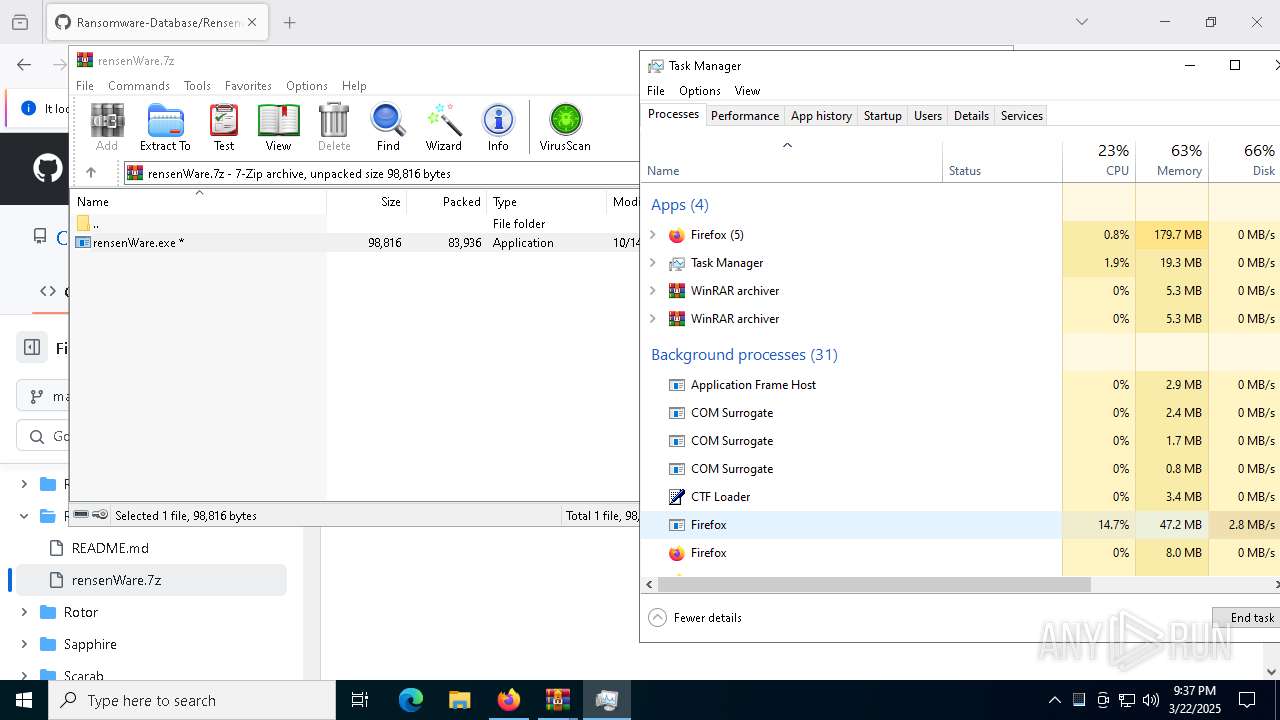
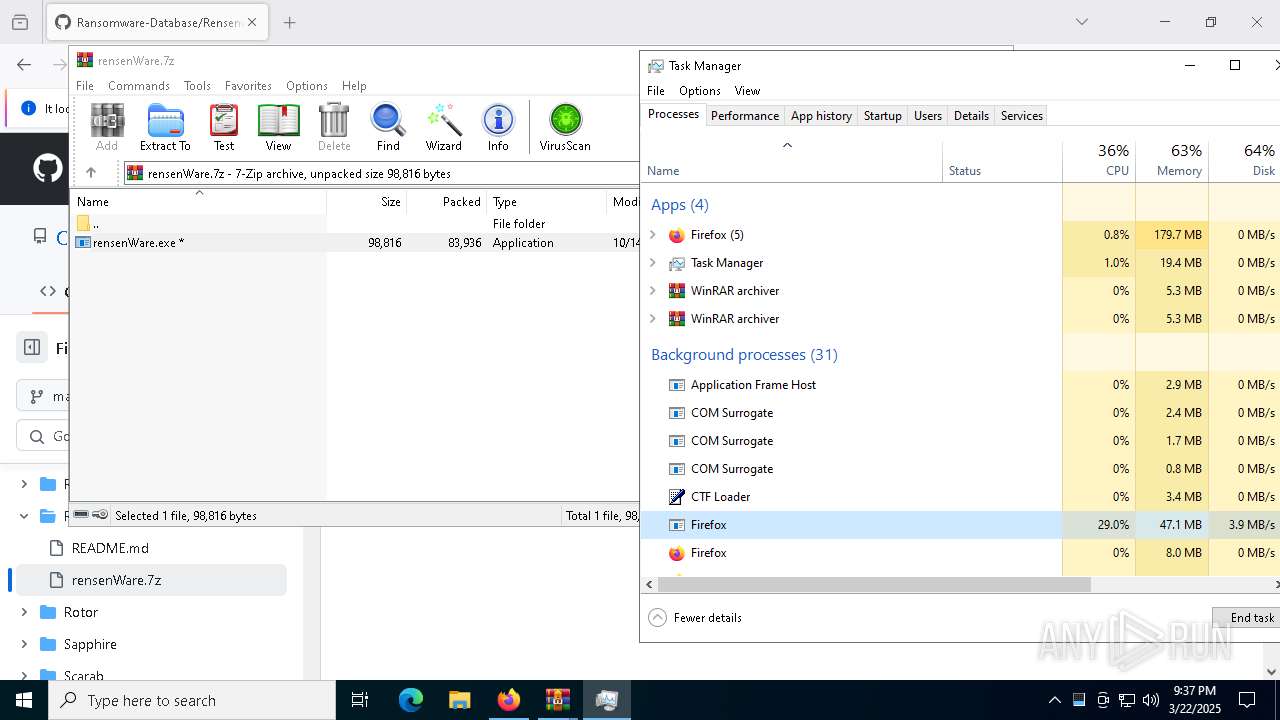
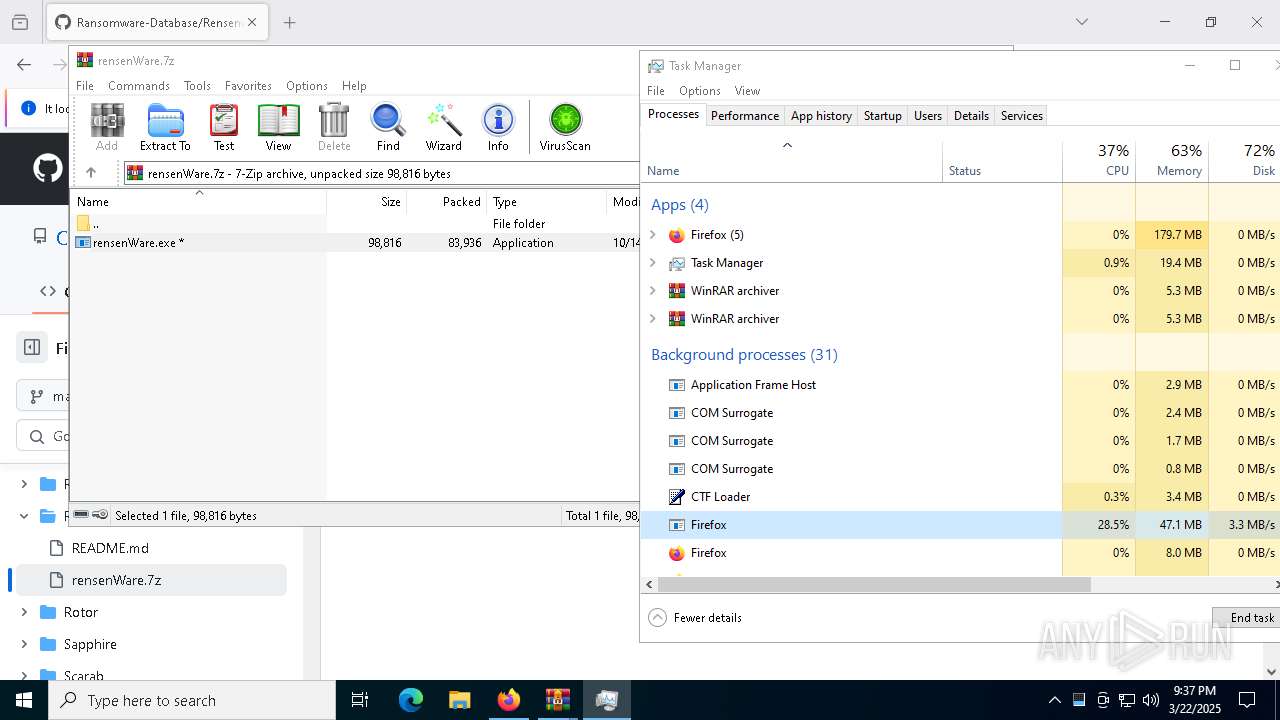
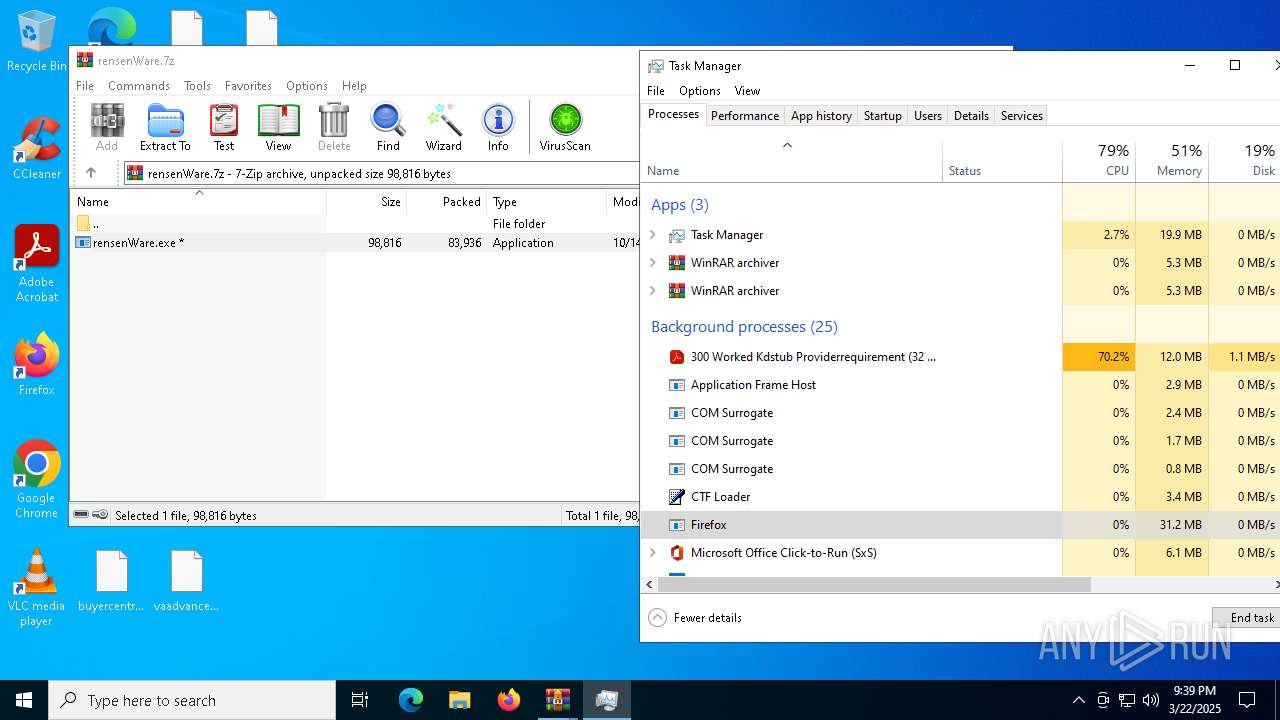
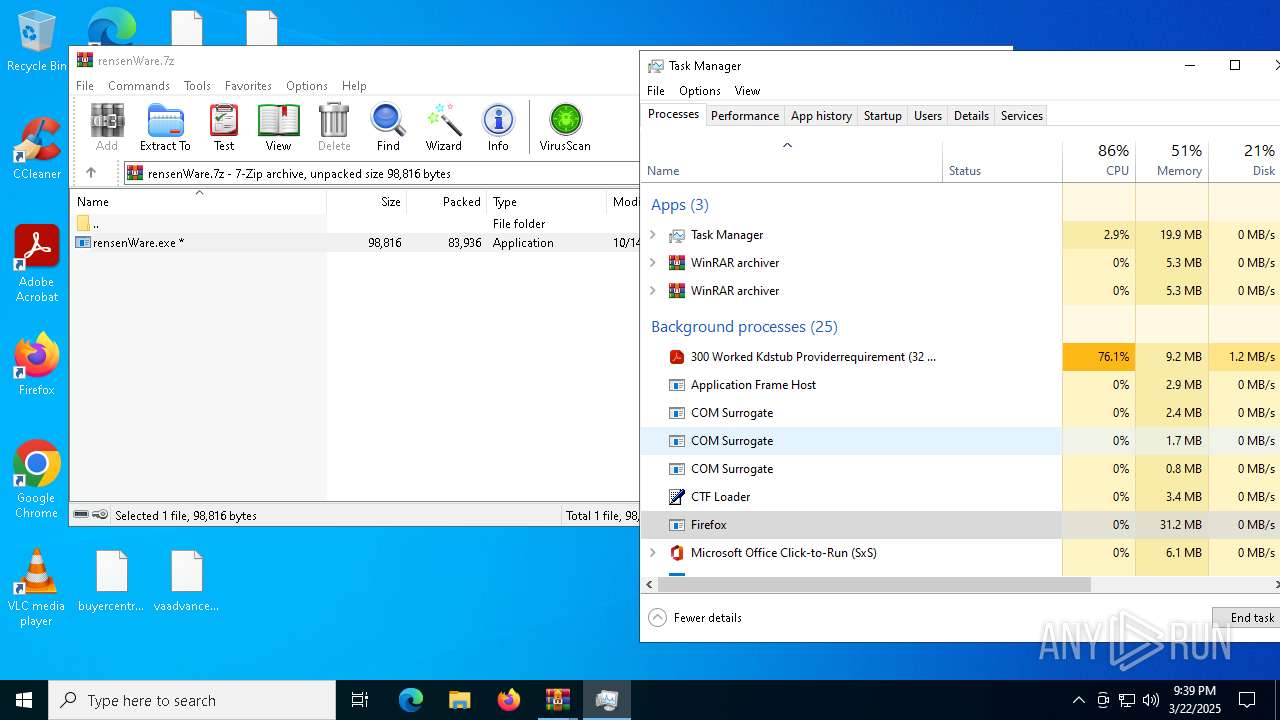
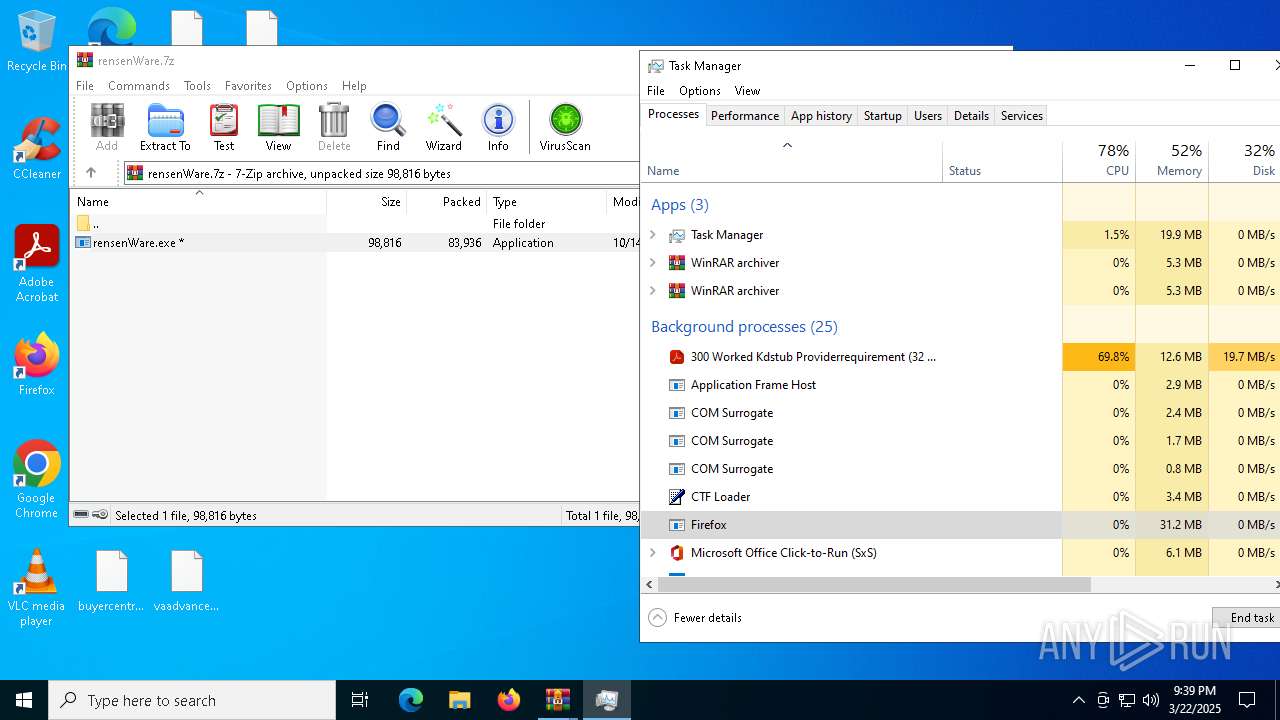
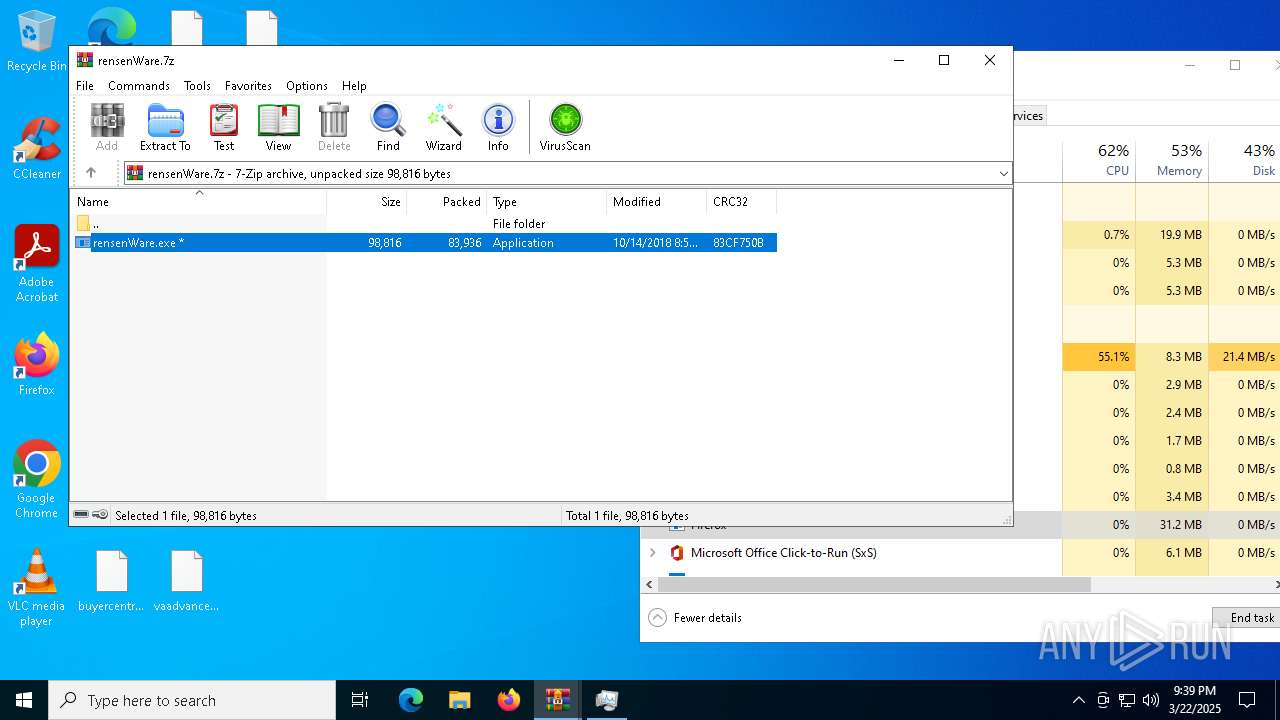
Actions looks like stealing of personal data
- rensenWare.exe (PID: 8460)
- drpbx.exe (PID: 9100)
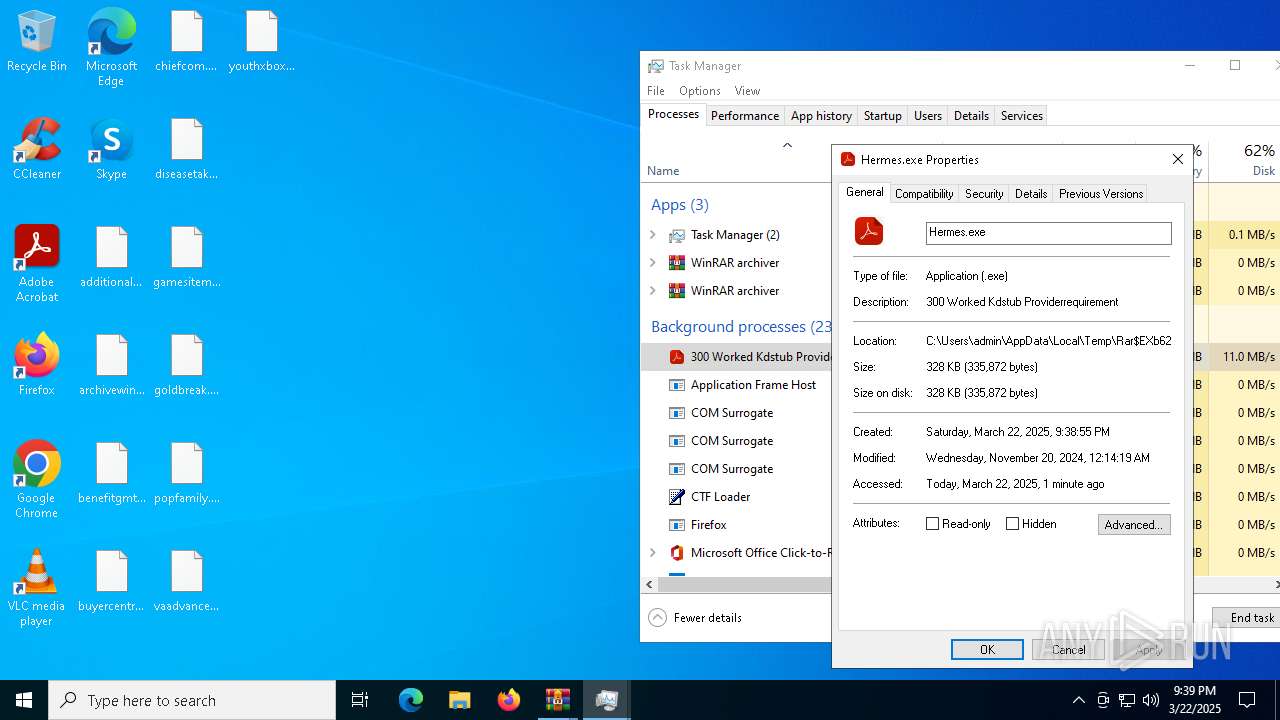
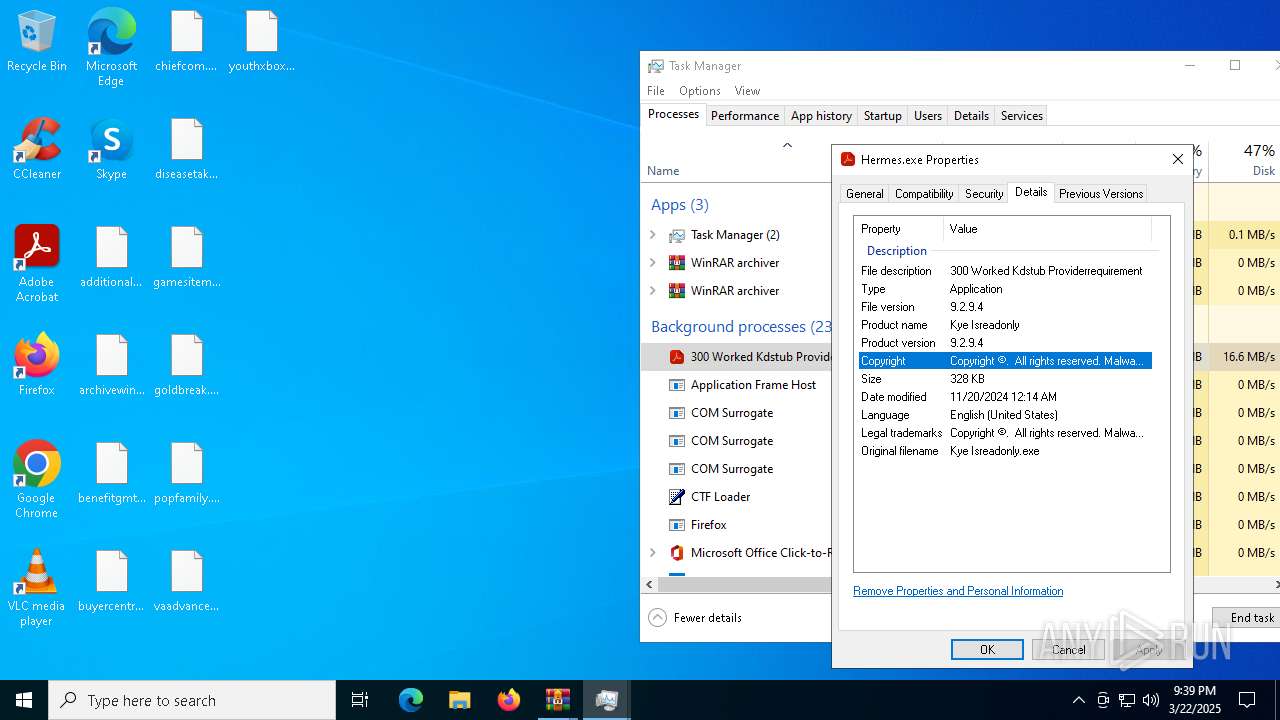
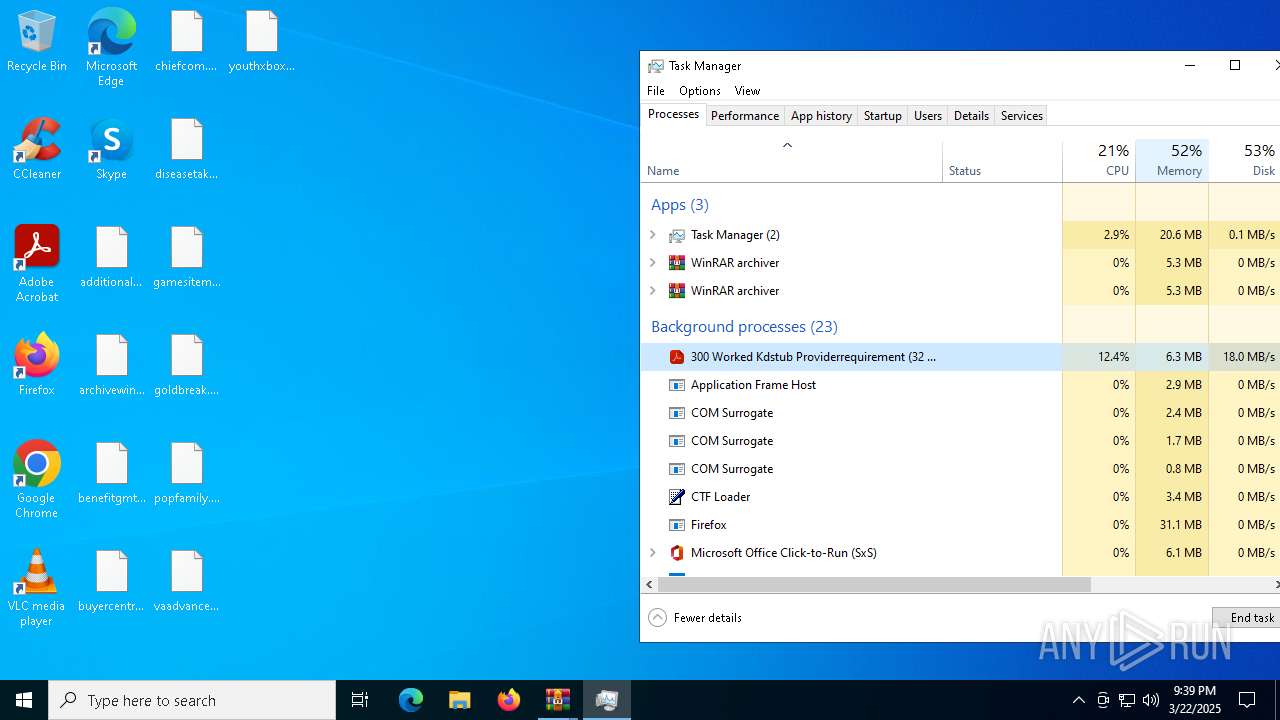
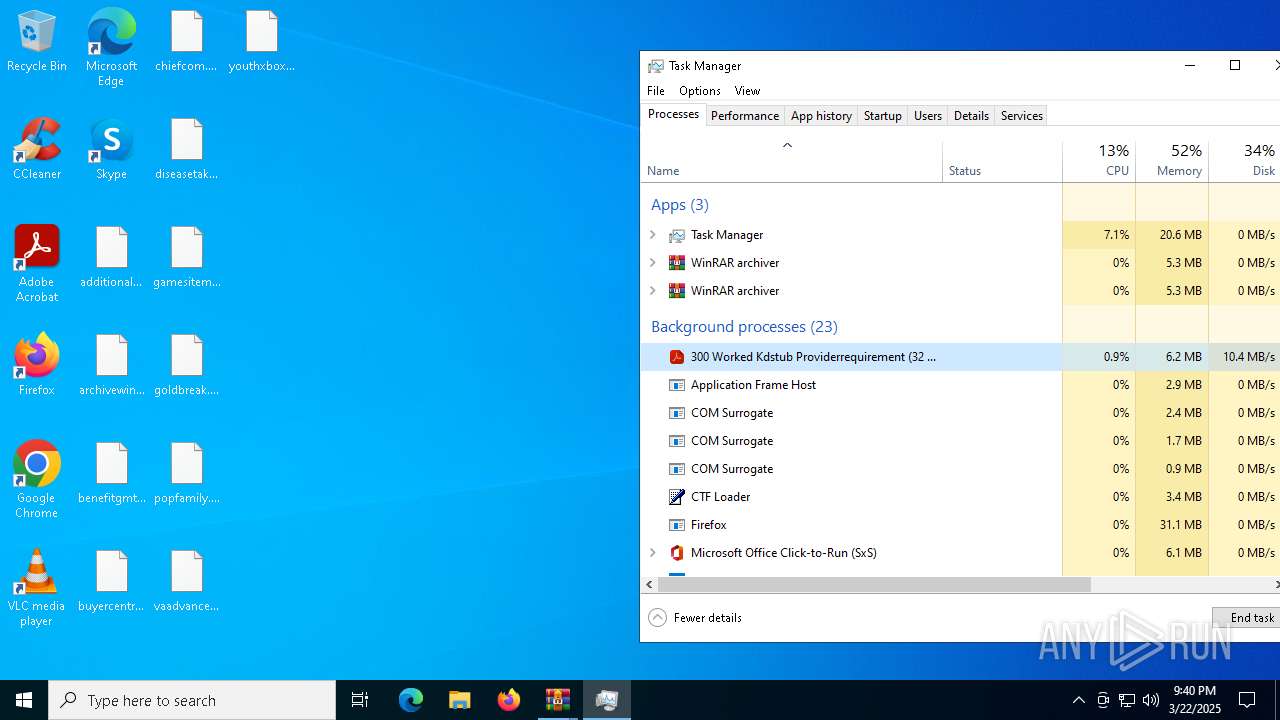
- Hermes.exe (PID: 7764)
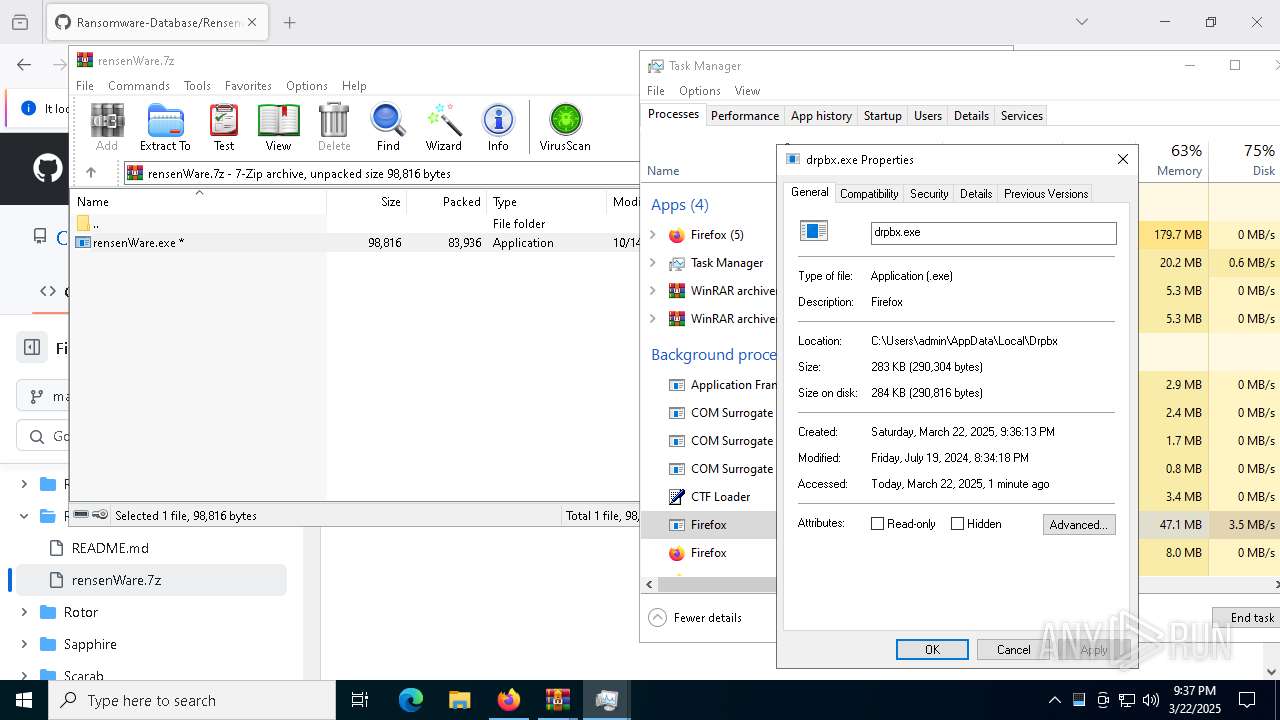
RANSOMWARE has been detected
- drpbx.exe (PID: 9100)
- Hermes.exe (PID: 7764)
Steals credentials from Web Browsers
- drpbx.exe (PID: 9100)
SUSPICIOUS
Reads security settings of Internet Explorer
- Jigsaw.exe (PID: 9044)
- WinRAR.exe (PID: 8968)
- WinRAR.exe (PID: 728)
- ShellExperienceHost.exe (PID: 6800)
- WinRAR.exe (PID: 6248)
Reads the date of Windows installation
- Jigsaw.exe (PID: 9044)
Starts itself from another location
- Jigsaw.exe (PID: 9044)
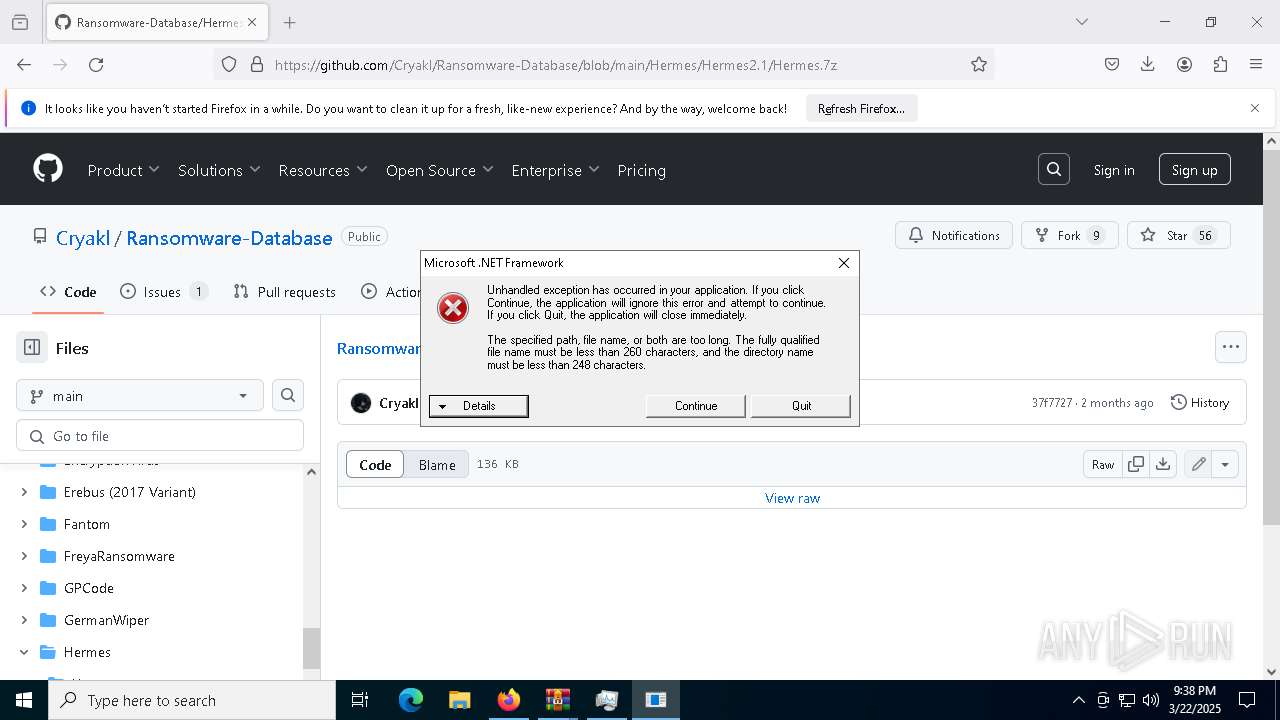
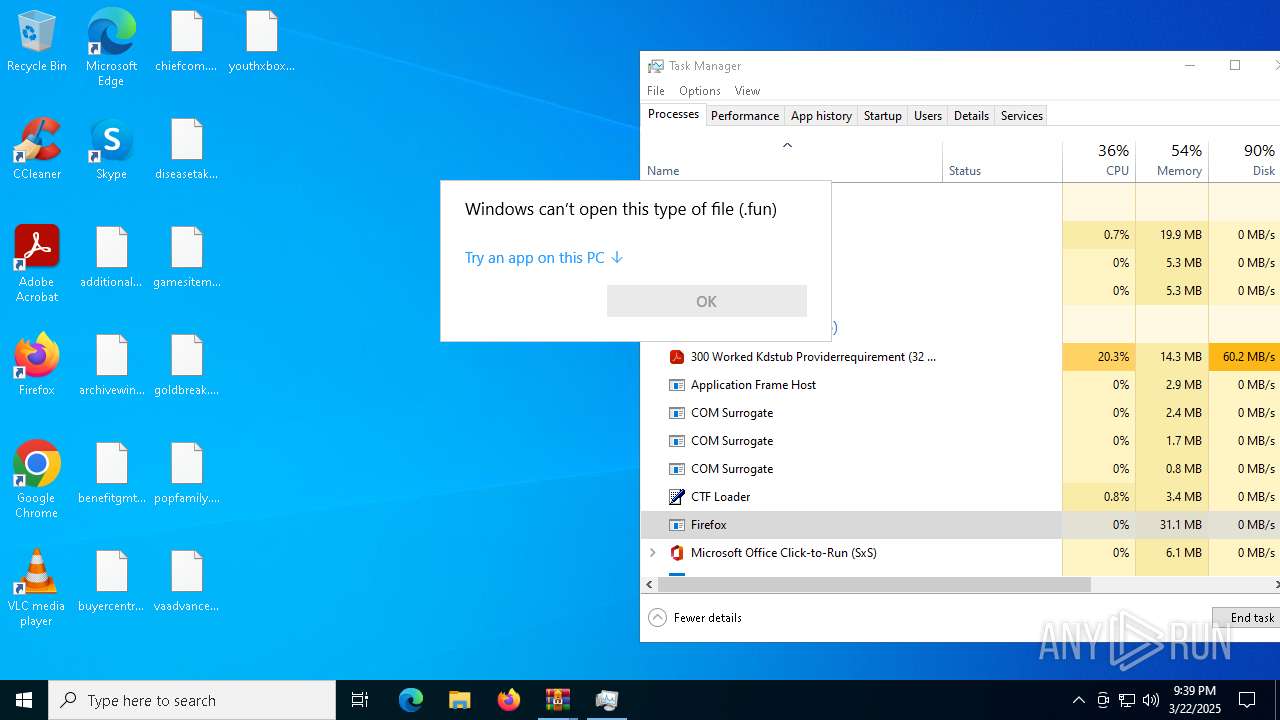
Executable content was dropped or overwritten
- Jigsaw.exe (PID: 9044)
Creates file in the systems drive root
- drpbx.exe (PID: 9100)
- Hermes.exe (PID: 7764)
INFO
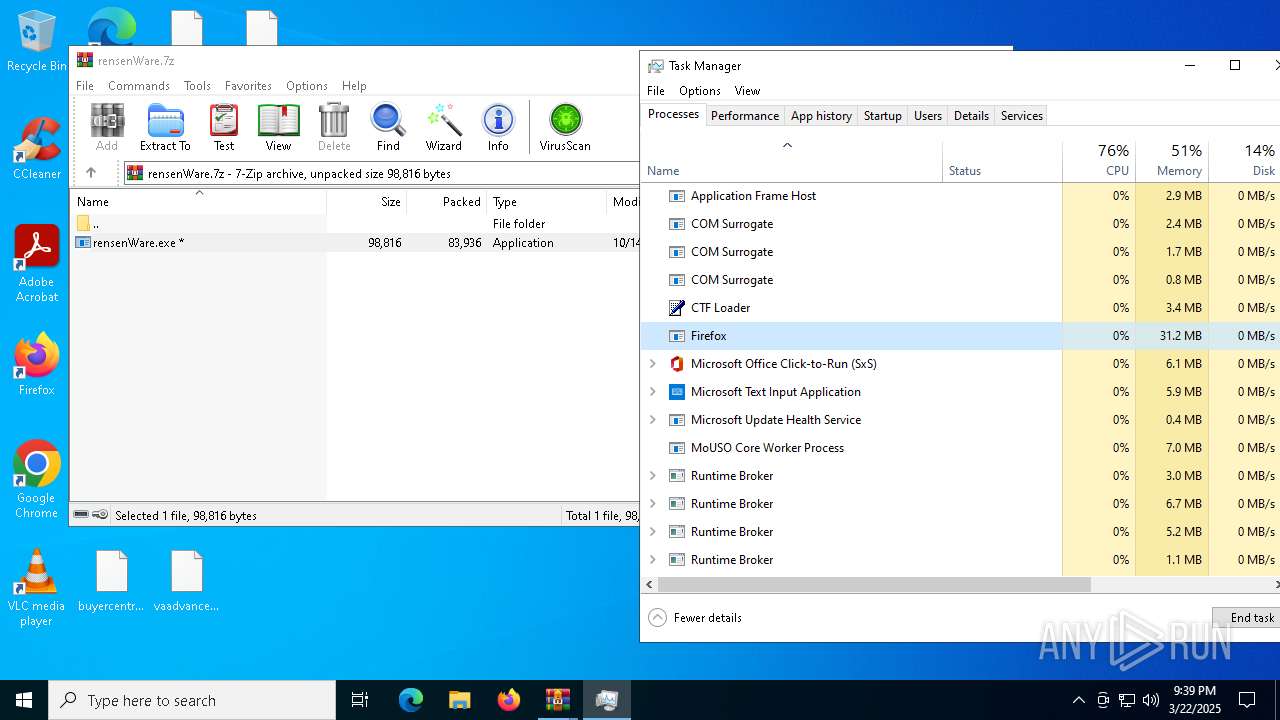
Application launched itself
- firefox.exe (PID: 7296)
- firefox.exe (PID: 7316)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 8836)
- Jigsaw.exe (PID: 9044)
- drpbx.exe (PID: 9100)
- Hermes.exe (PID: 7764)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 8836)
- slui.exe (PID: 3008)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 8628)
- BackgroundTransferHost.exe (PID: 8836)
- BackgroundTransferHost.exe (PID: 7324)
- BackgroundTransferHost.exe (PID: 1676)
- BackgroundTransferHost.exe (PID: 6268)
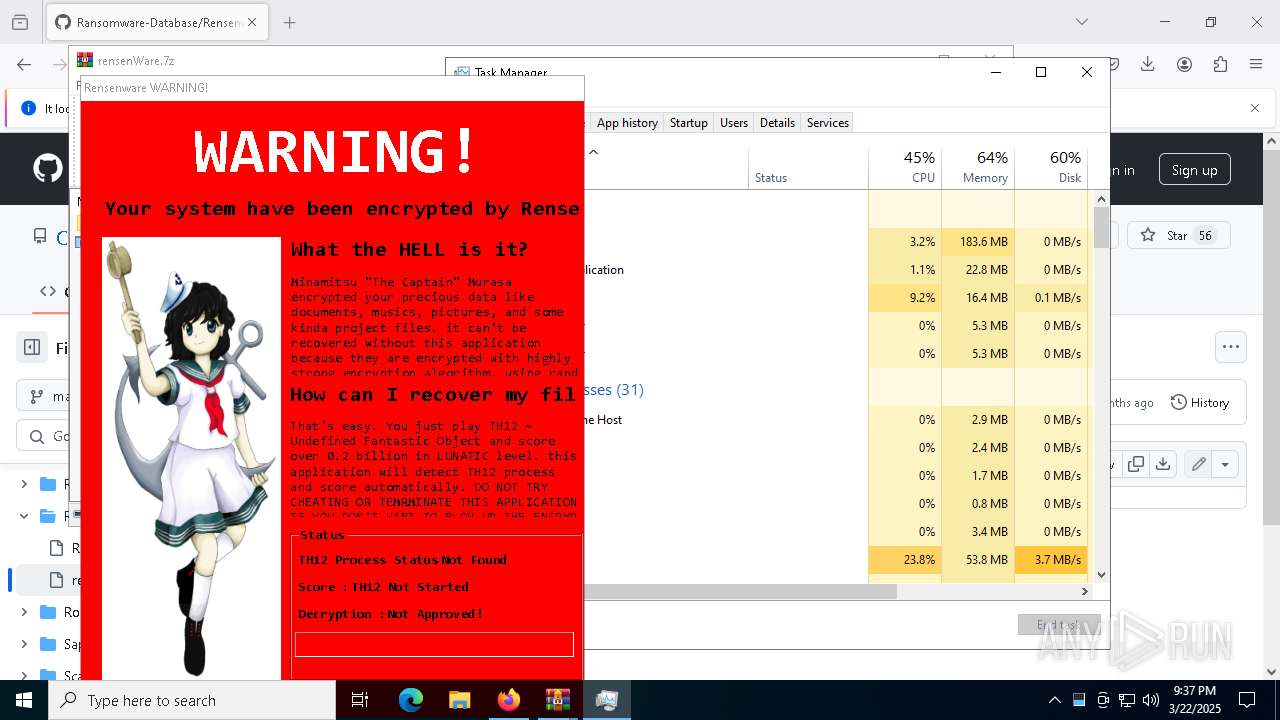
- Taskmgr.exe (PID: 7288)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 8836)
- slui.exe (PID: 3008)
- slui.exe (PID: 2236)
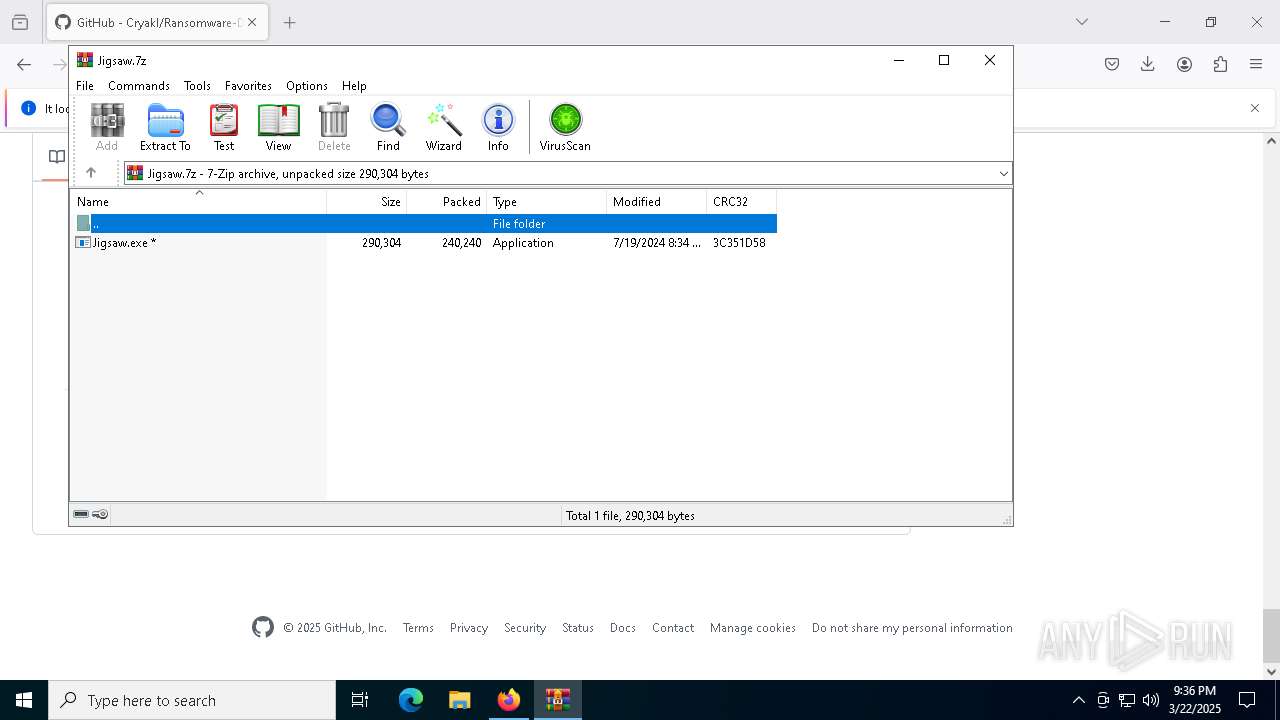
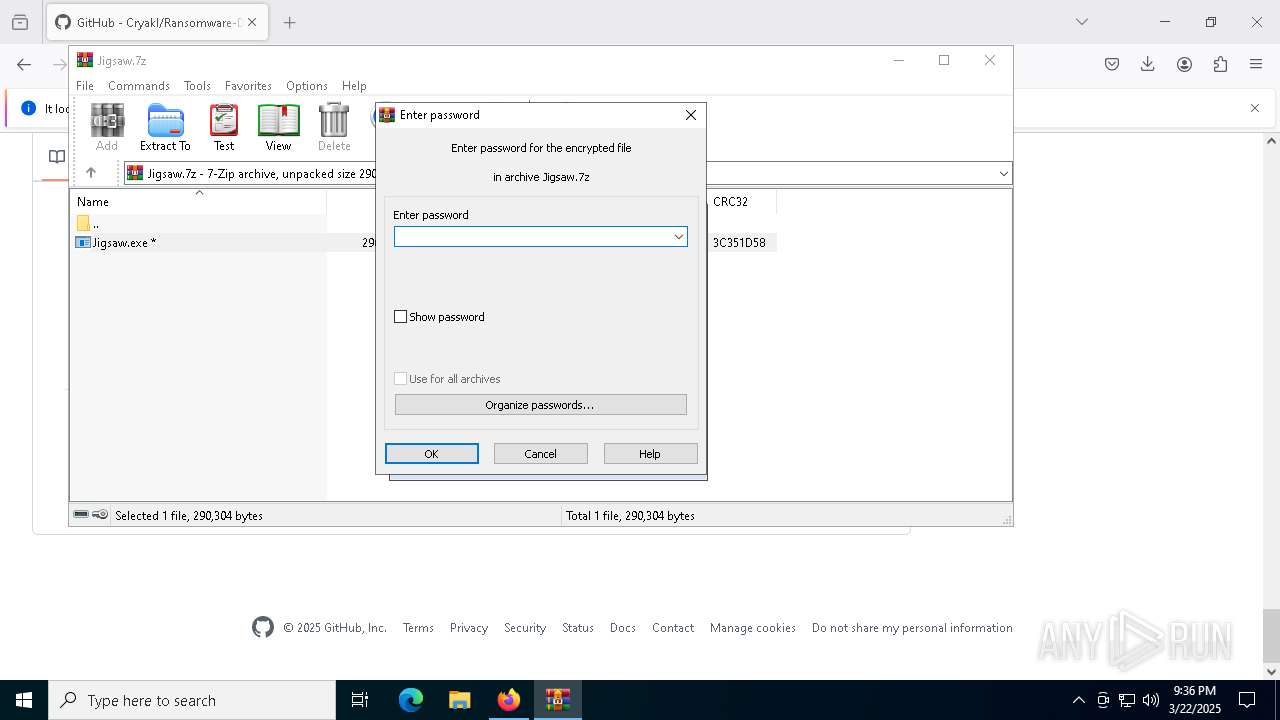
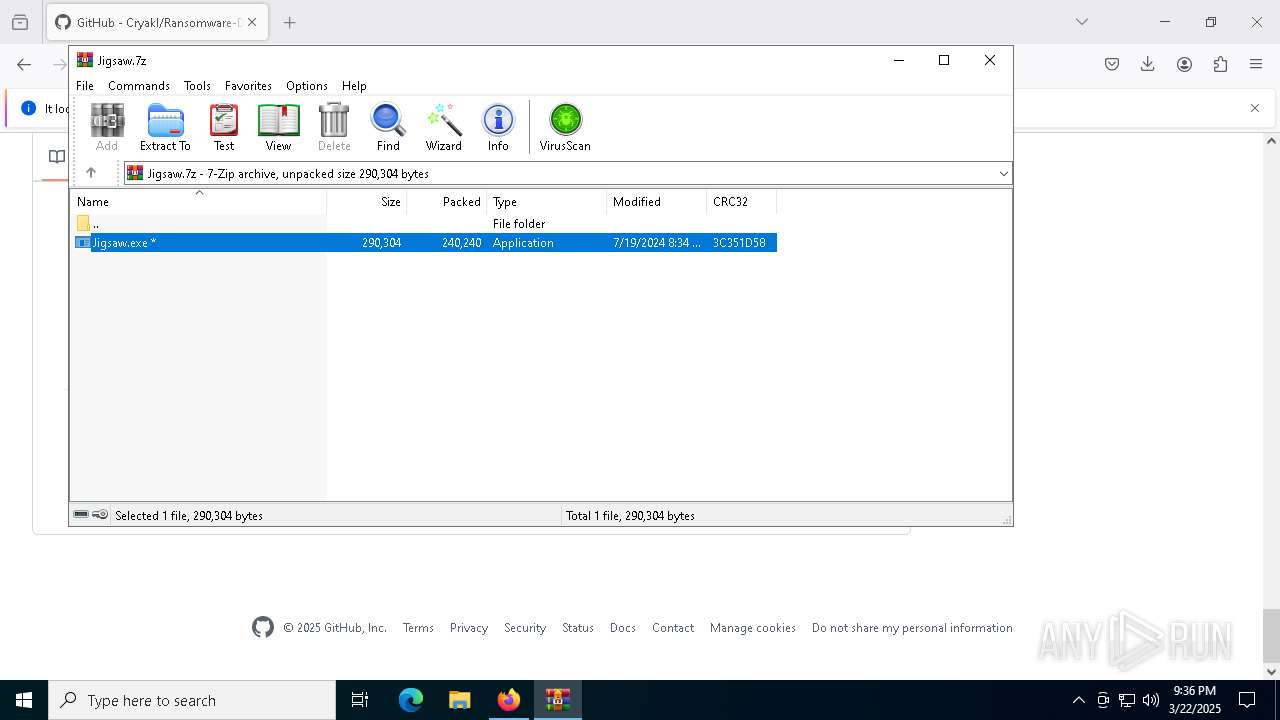
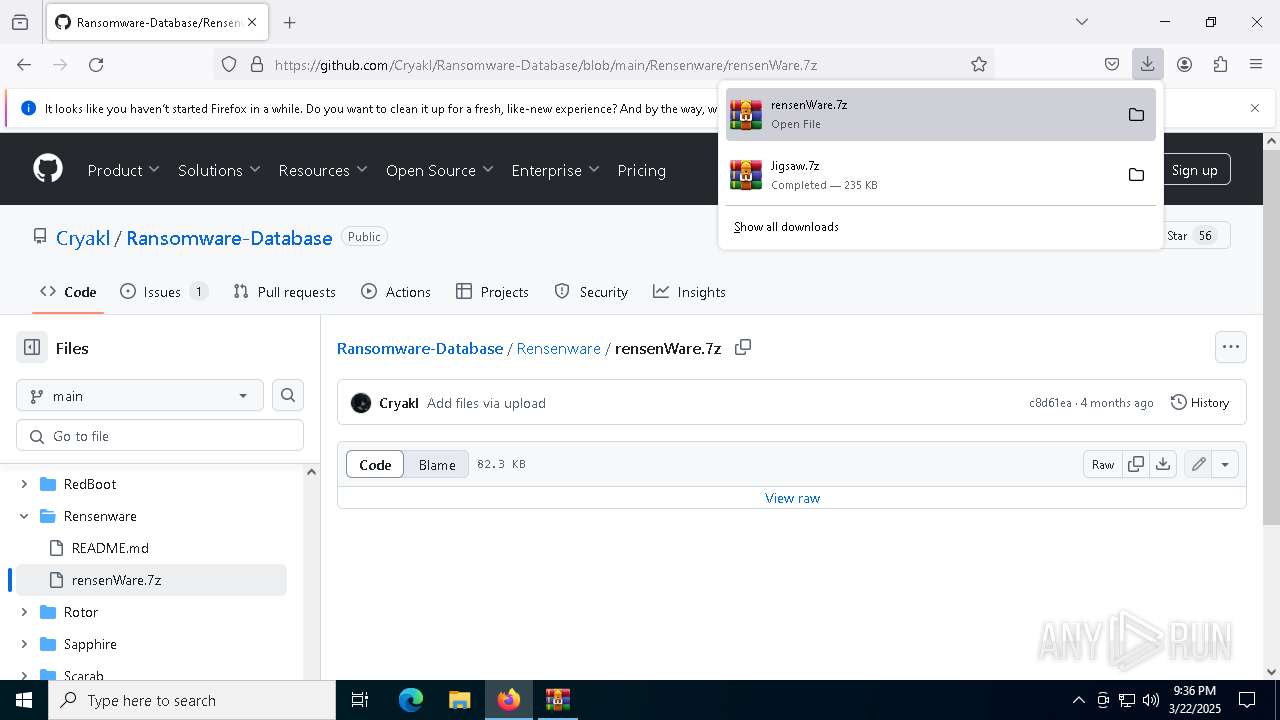
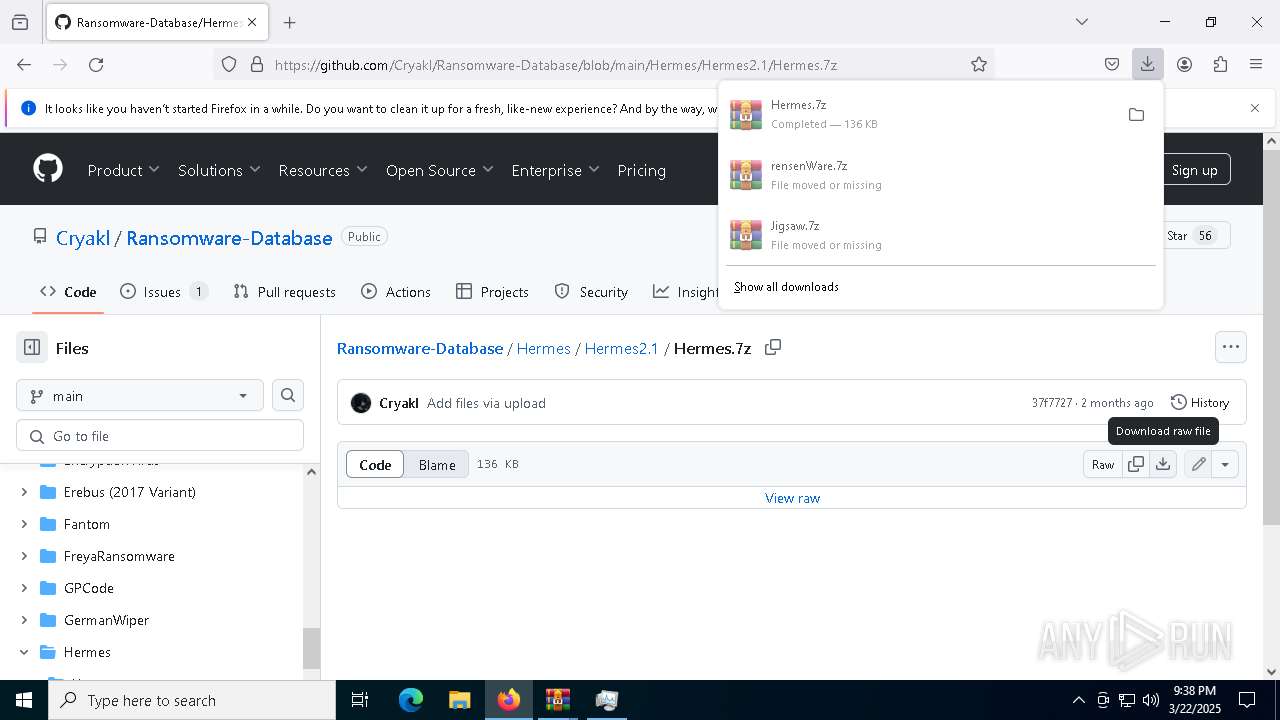
Autorun file from Downloads
- firefox.exe (PID: 7316)
Reads the computer name
- drpbx.exe (PID: 9100)
- ShellExperienceHost.exe (PID: 6800)
- Jigsaw.exe (PID: 9044)
- rensenWare.exe (PID: 8460)
- Hermes.exe (PID: 7764)
Checks supported languages
- drpbx.exe (PID: 9100)
- ShellExperienceHost.exe (PID: 6800)
- Jigsaw.exe (PID: 9044)
- rensenWare.exe (PID: 8460)
- Hermes.exe (PID: 7764)
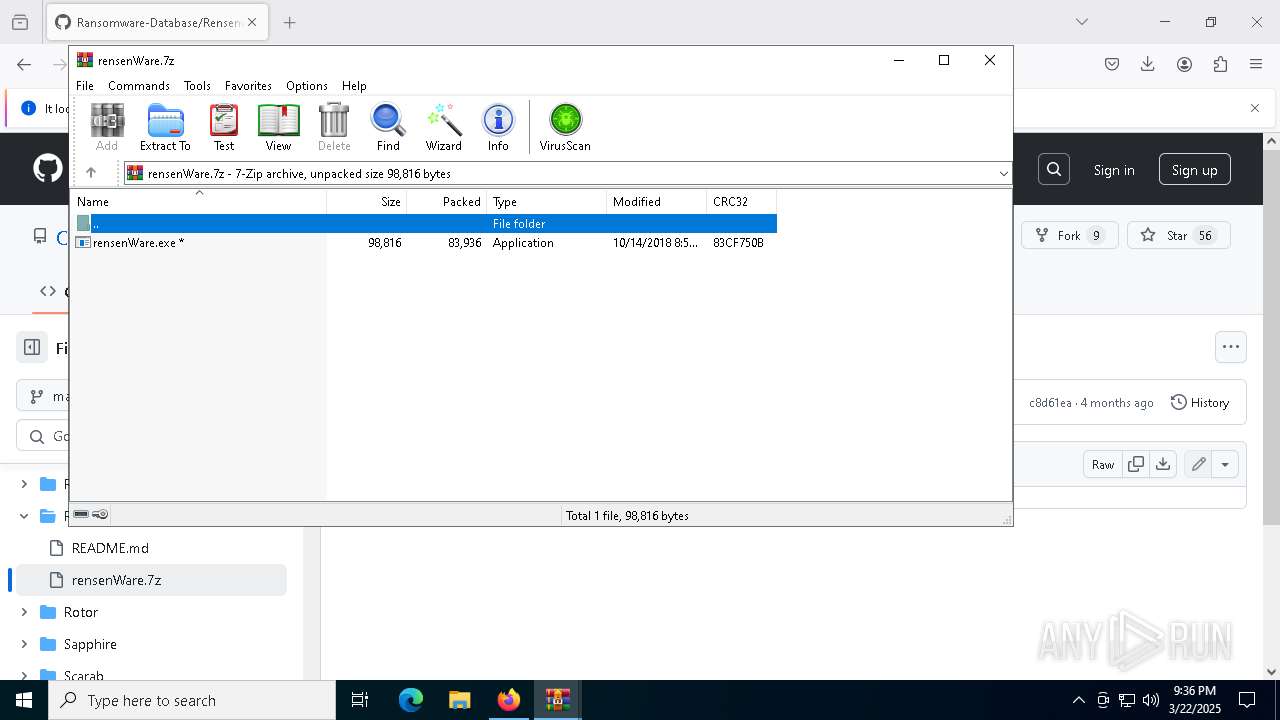
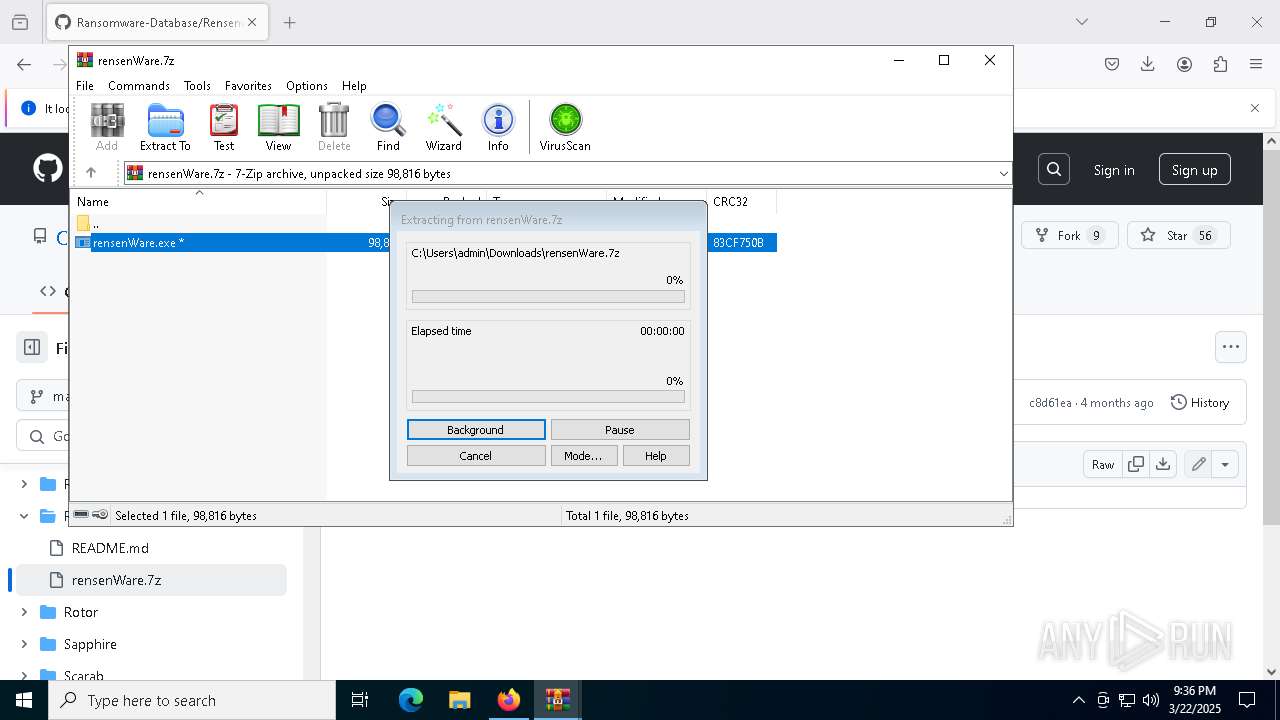
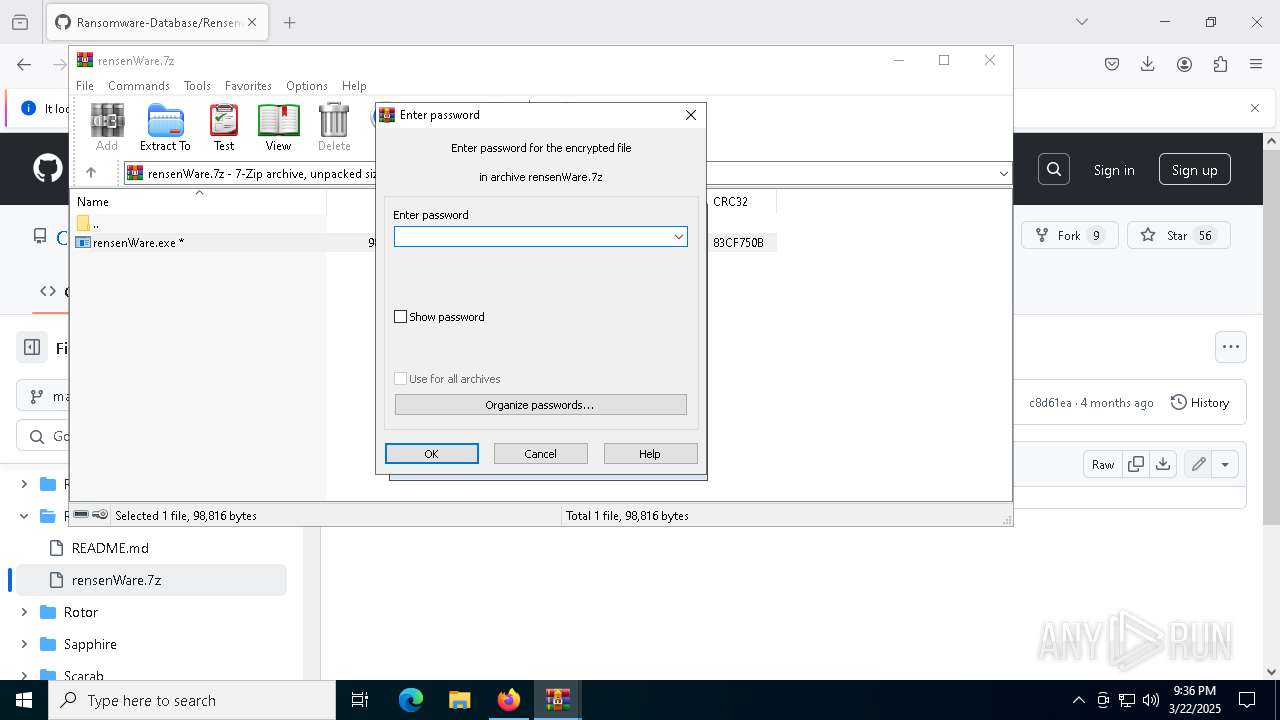
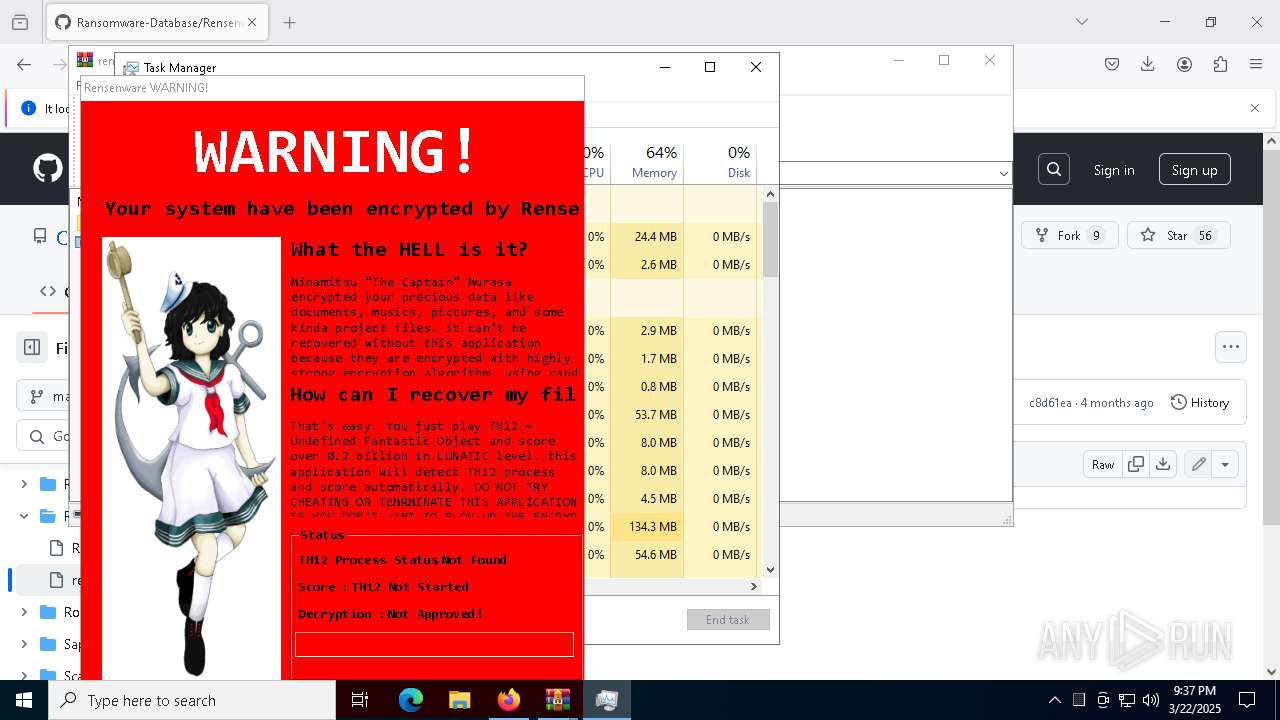
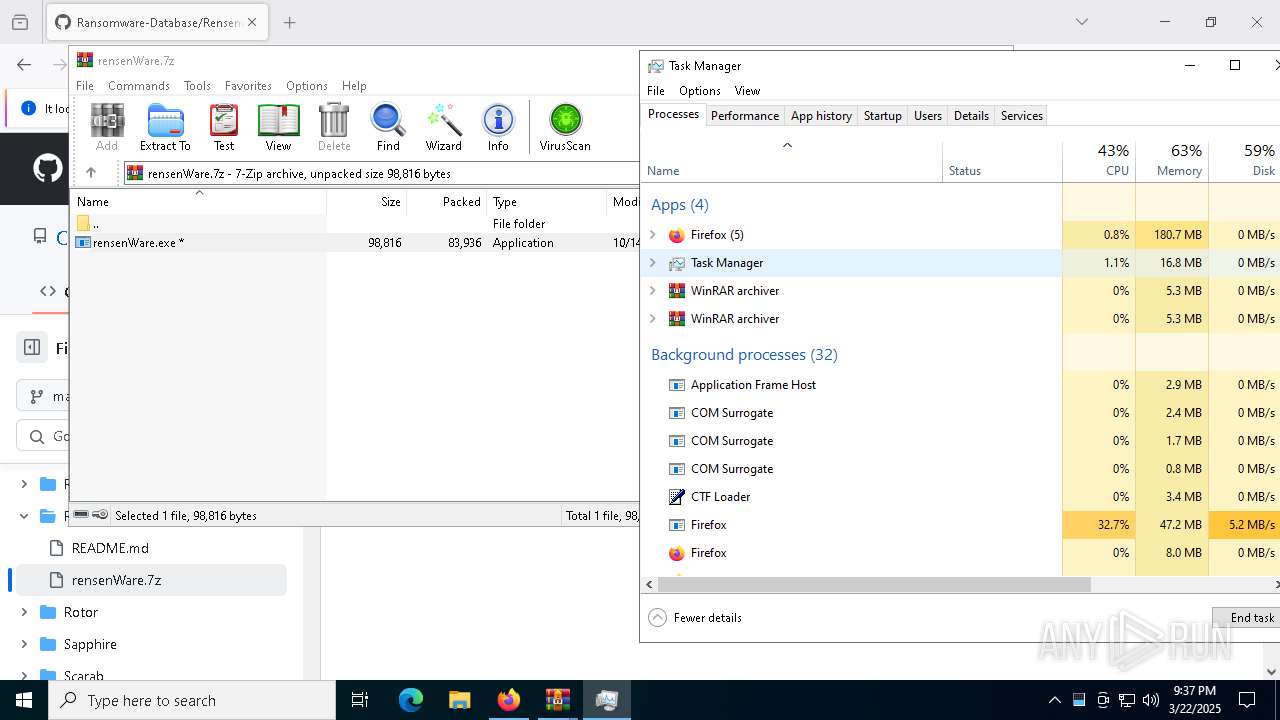
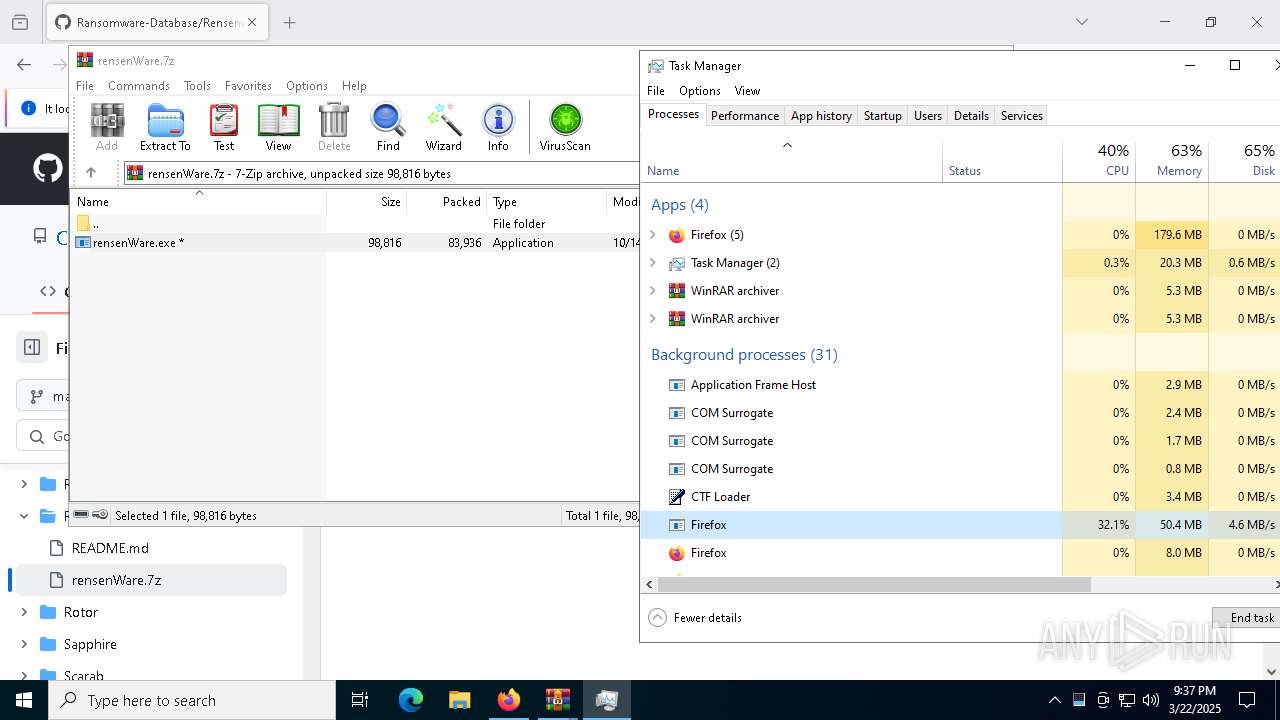
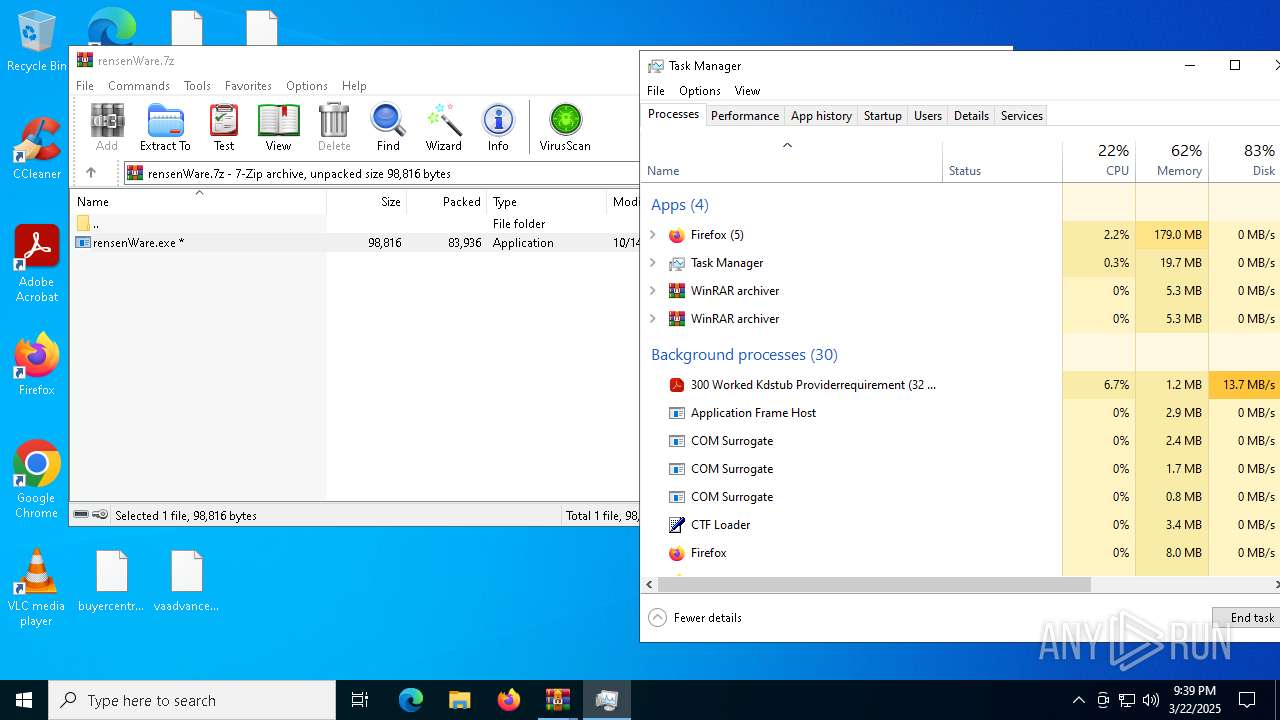
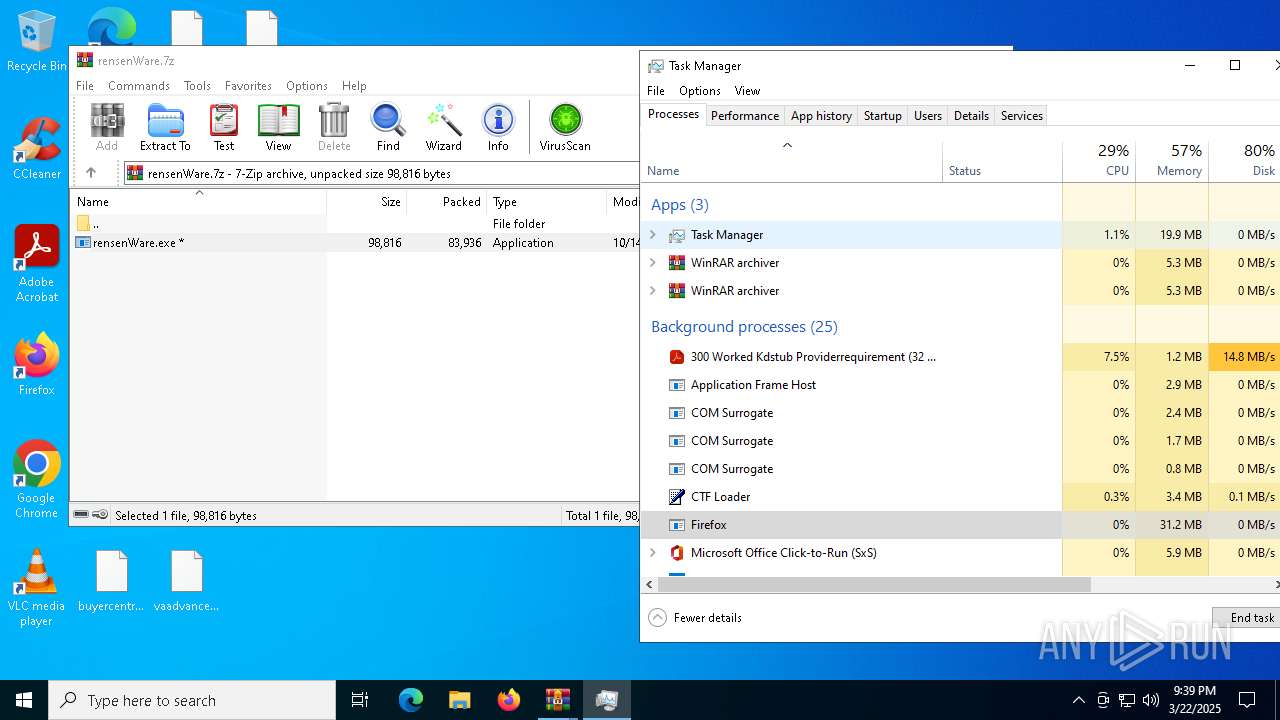
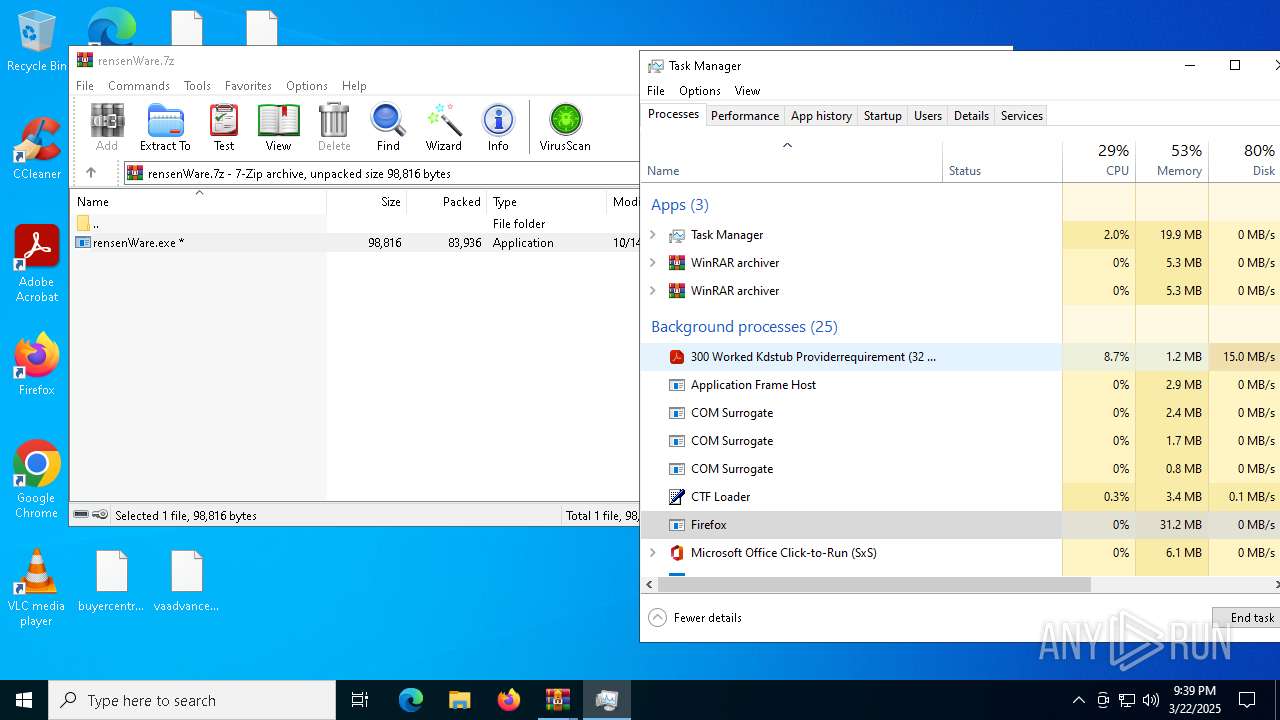
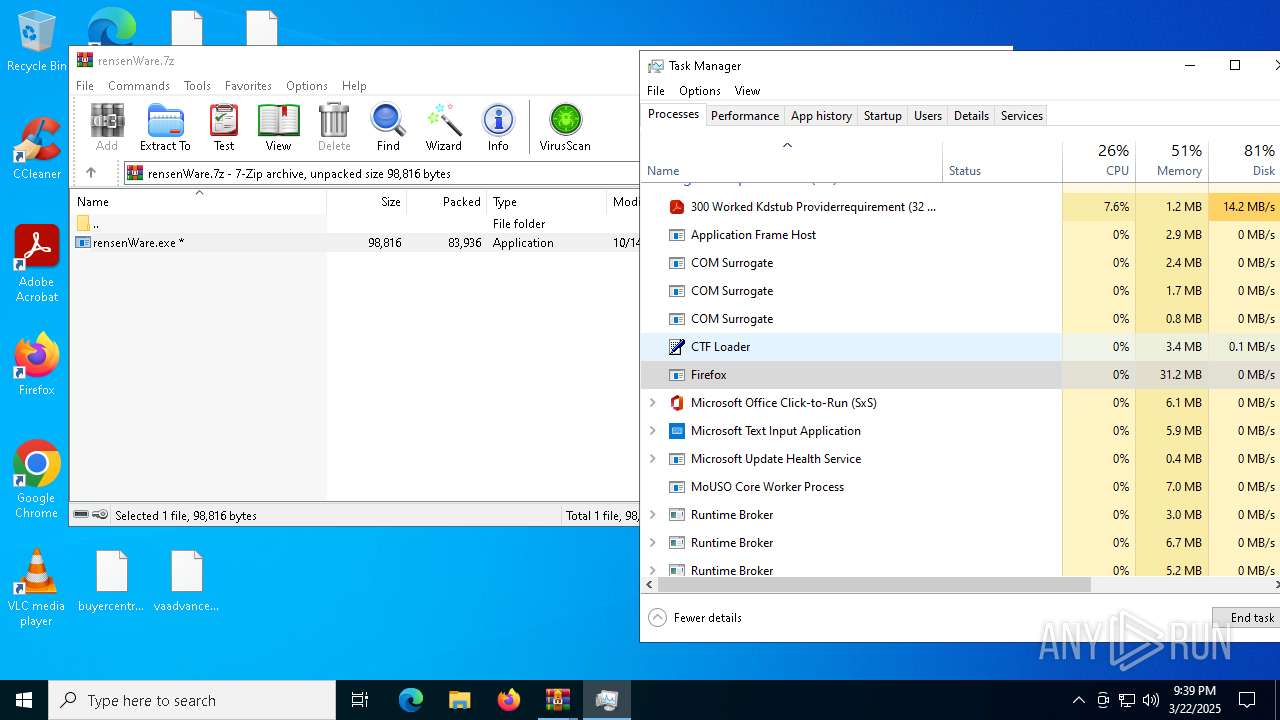
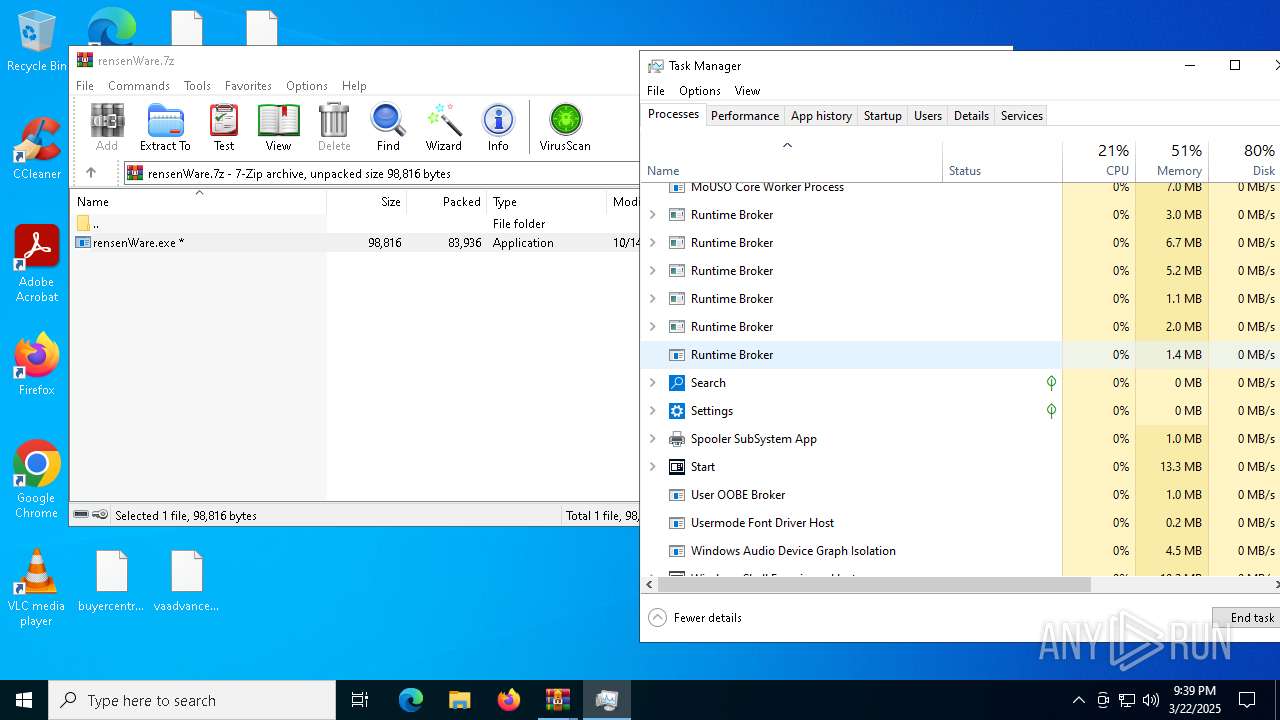
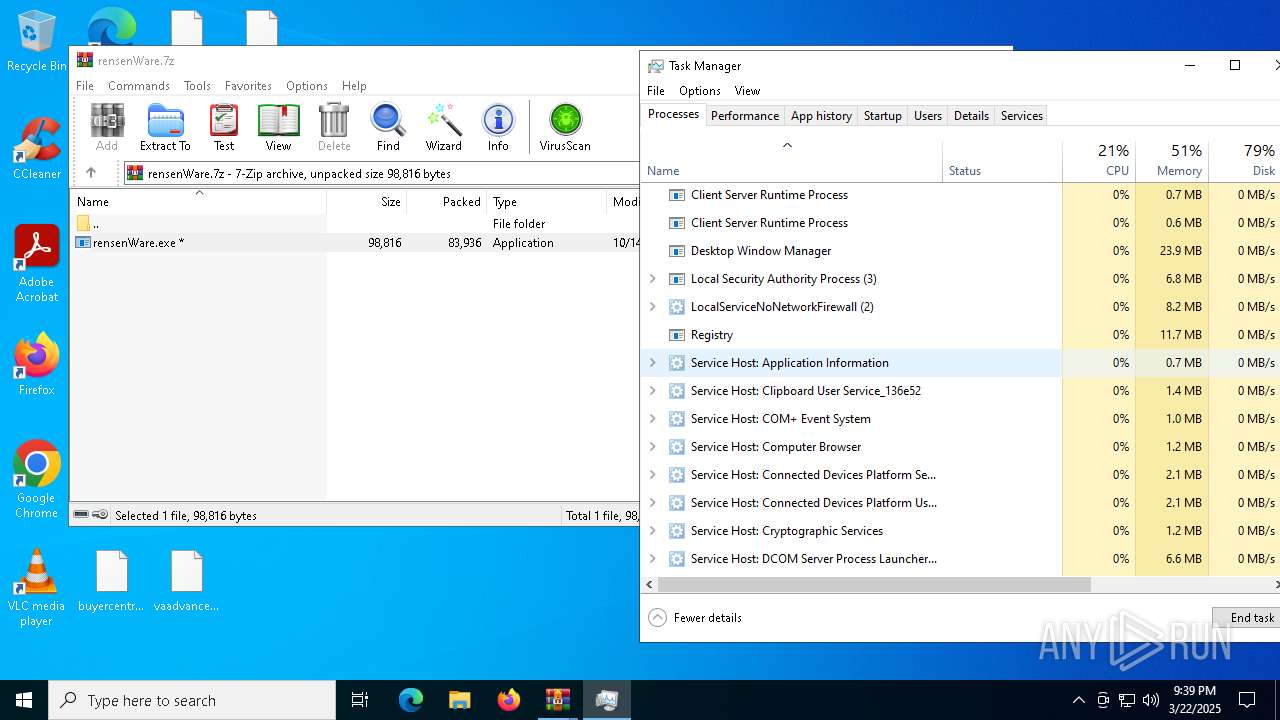
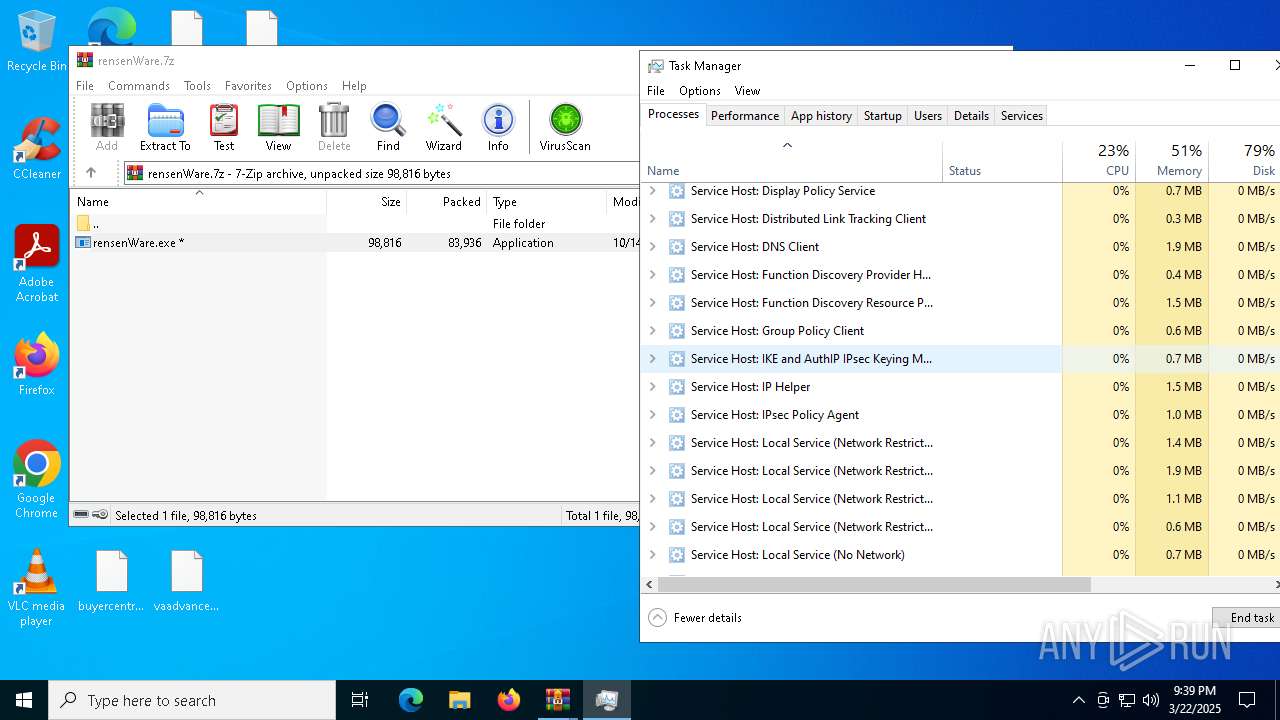
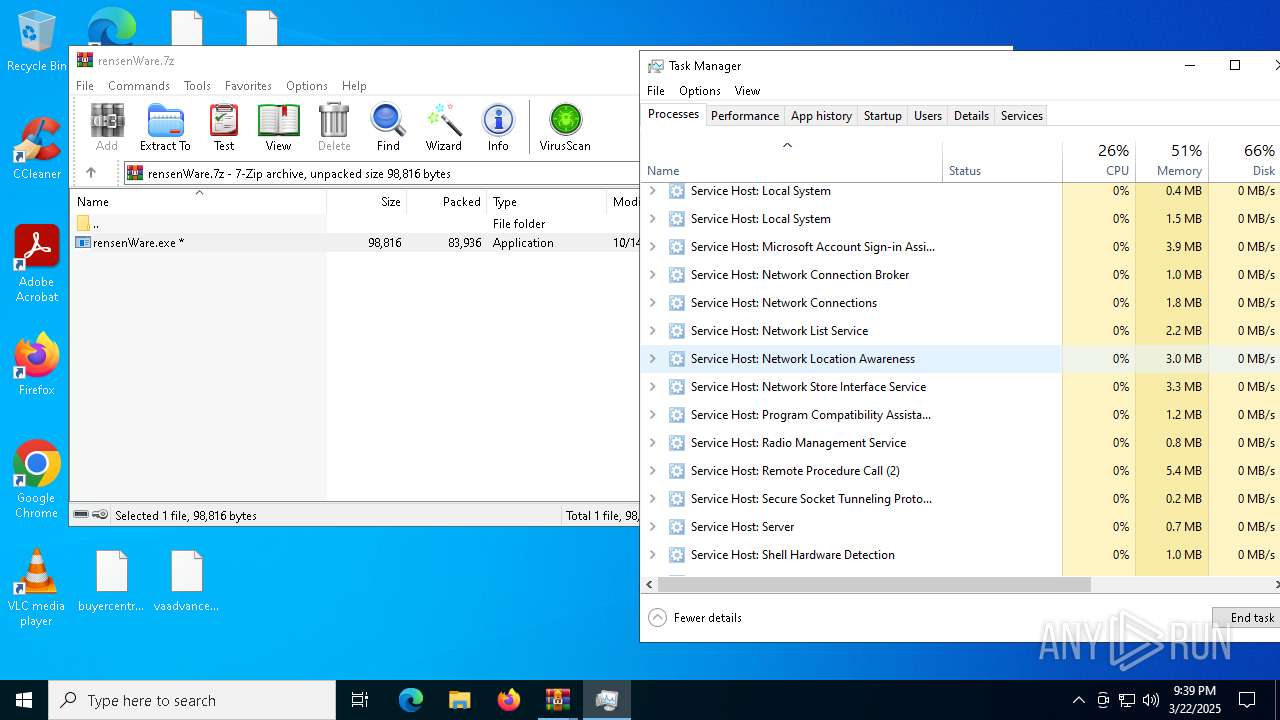
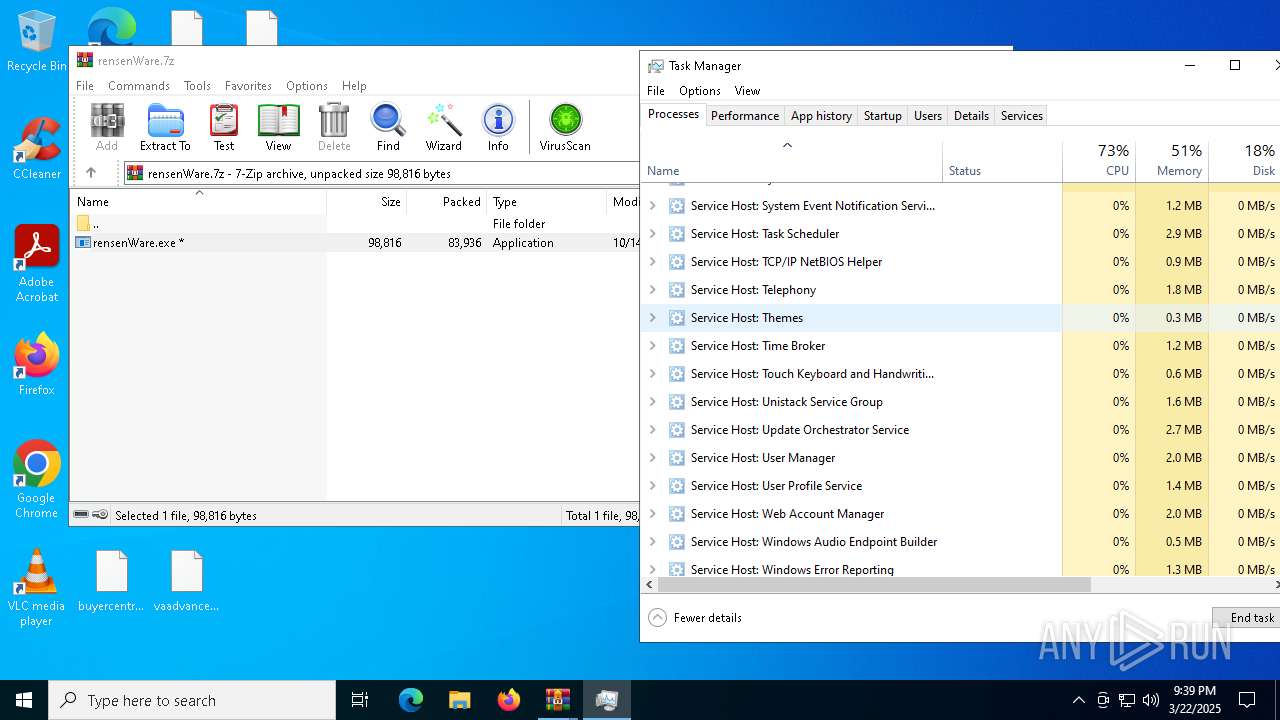
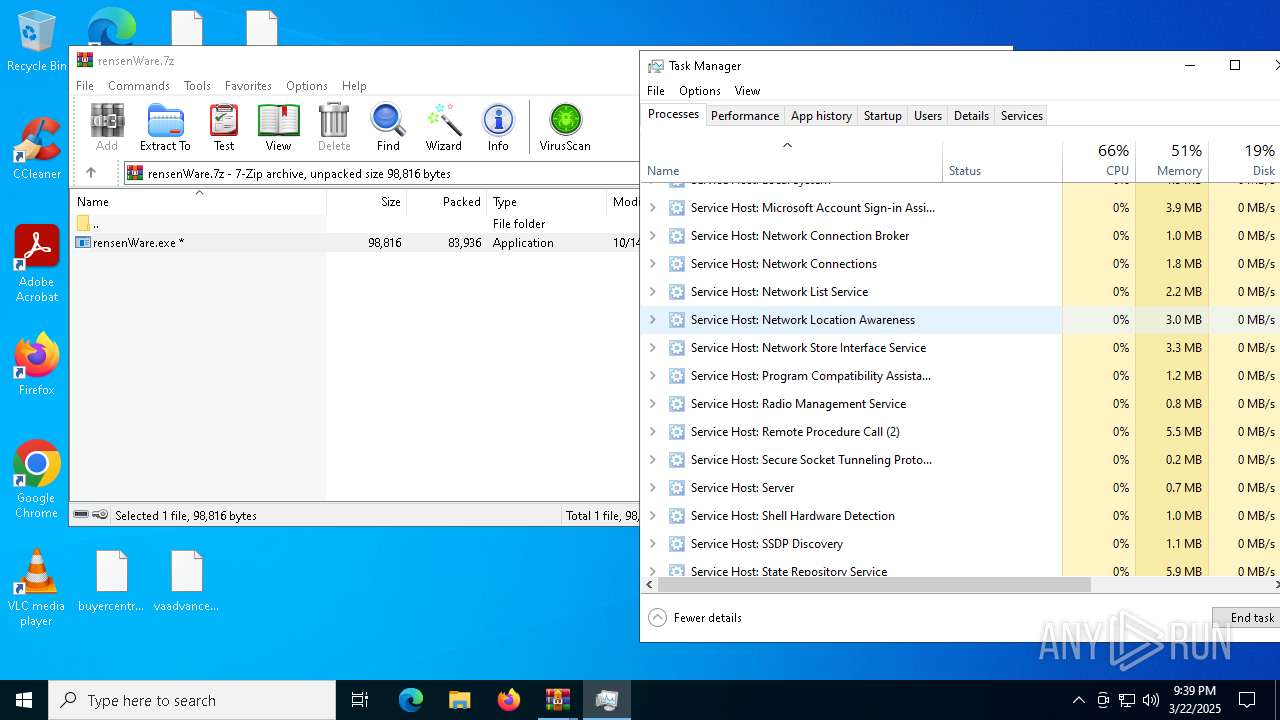
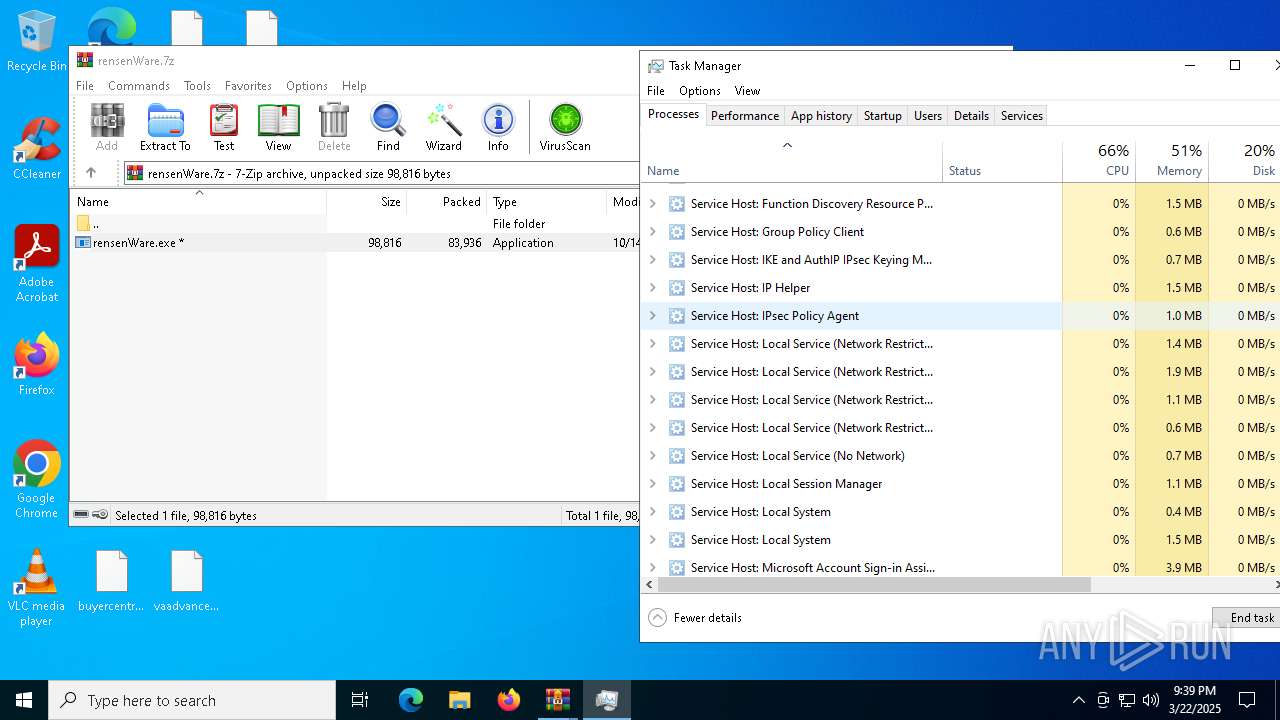
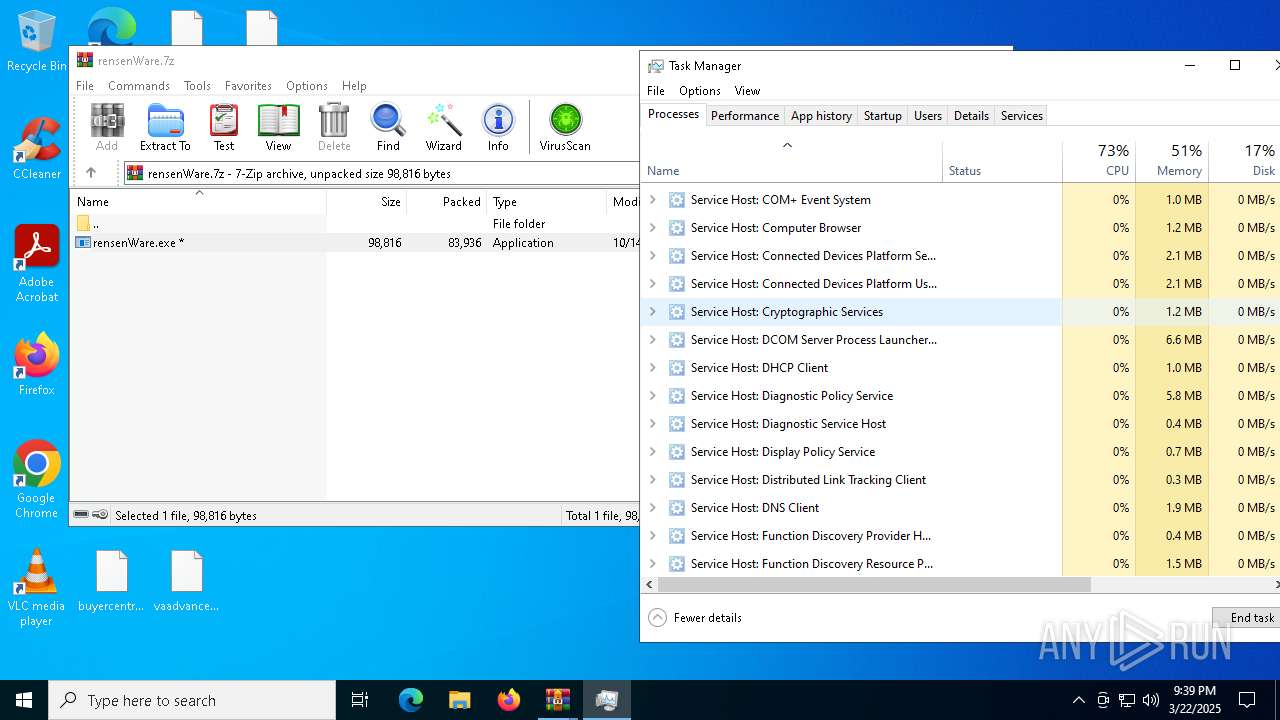
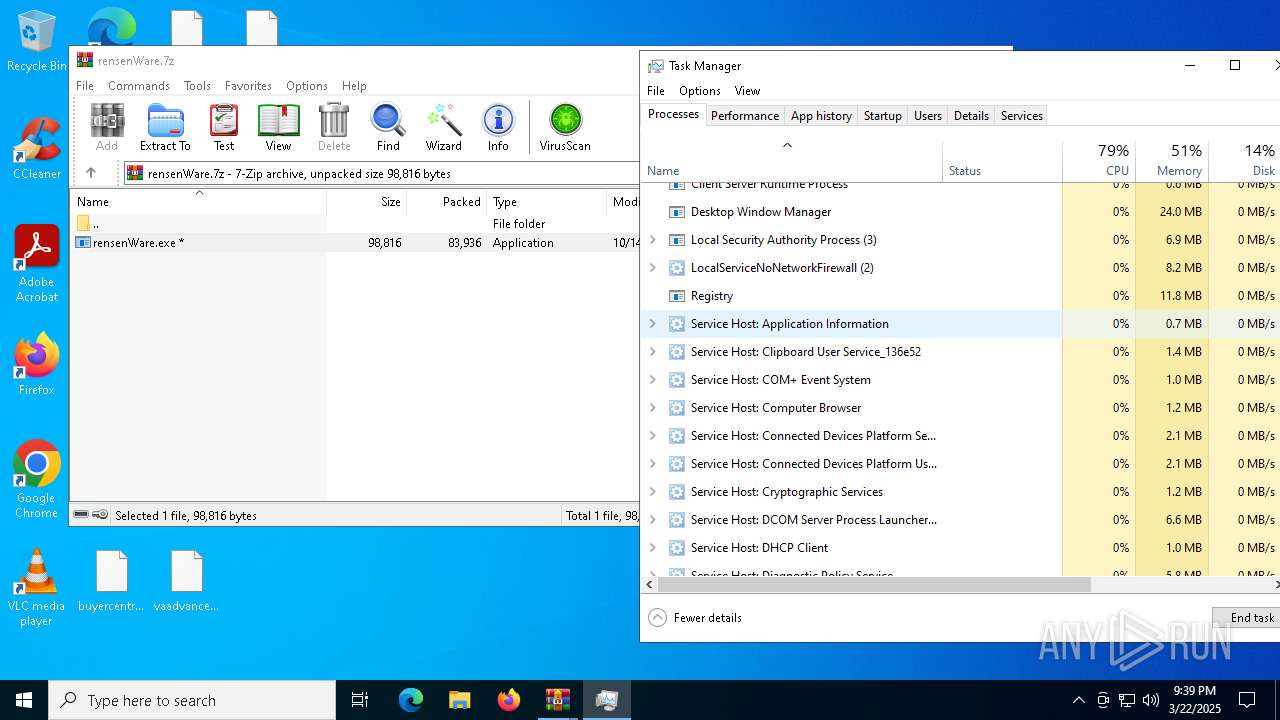
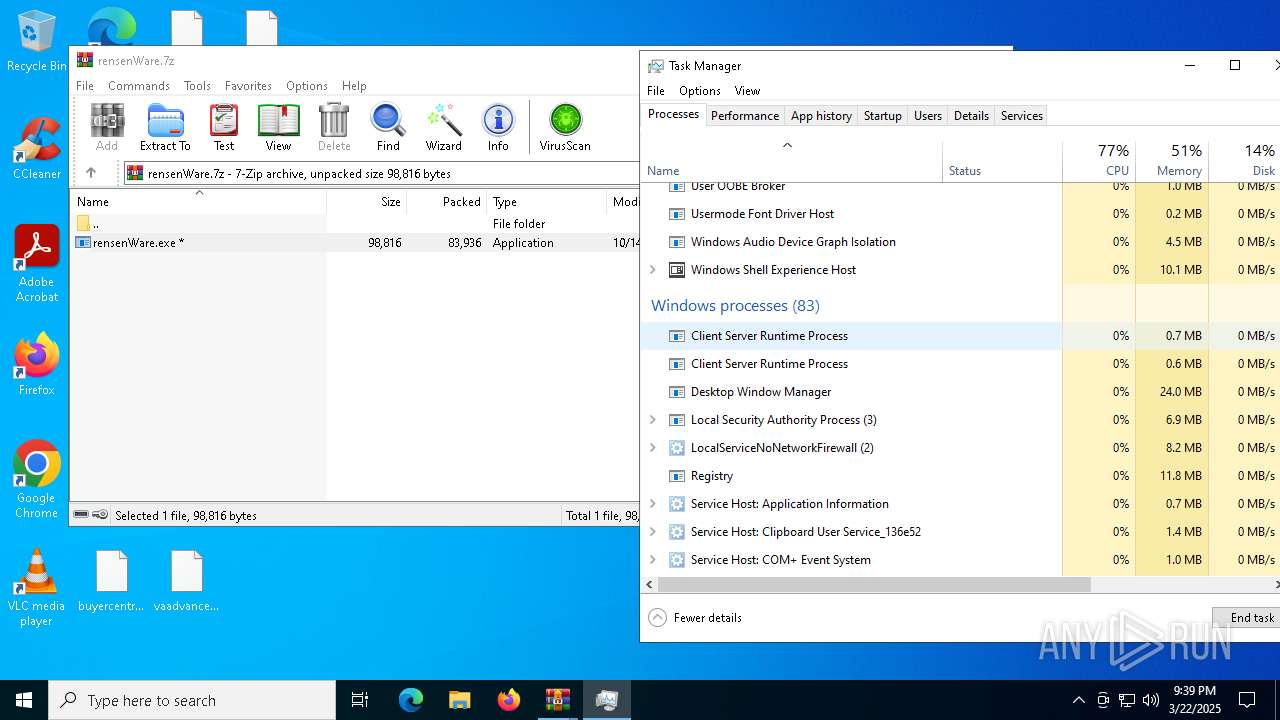
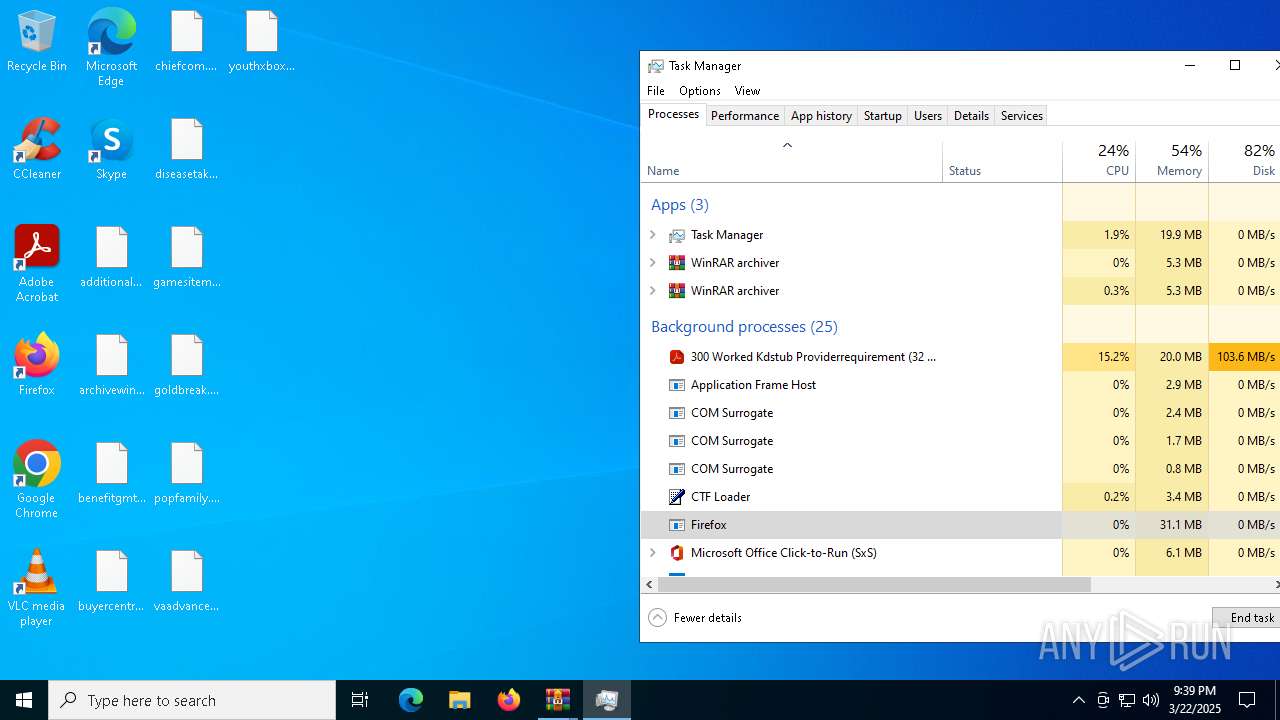
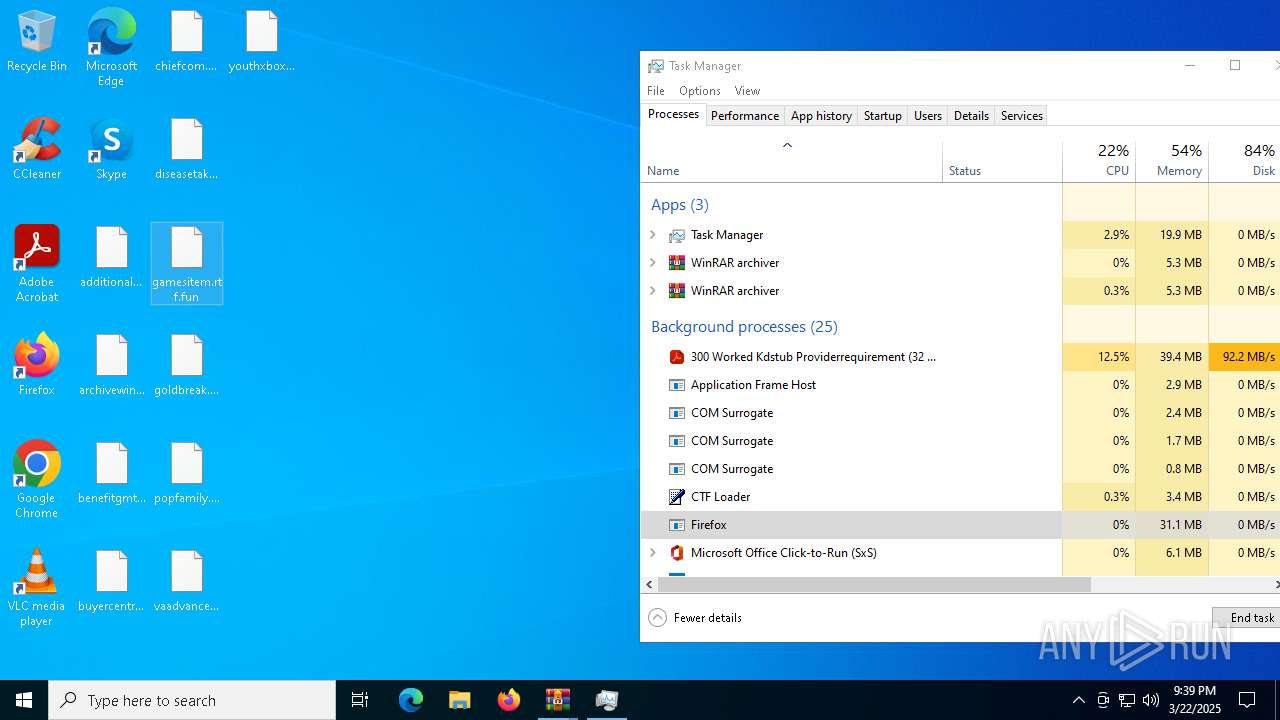
Manual execution by a user
- WinRAR.exe (PID: 8968)
- WinRAR.exe (PID: 728)
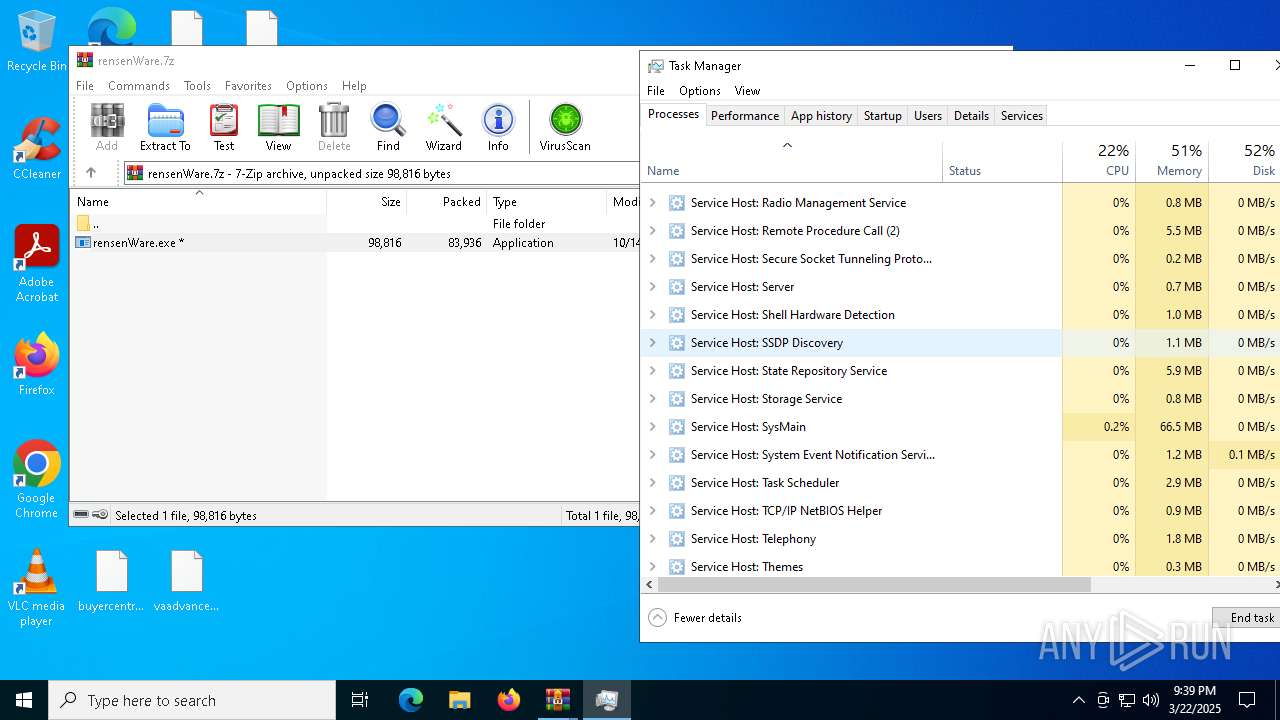
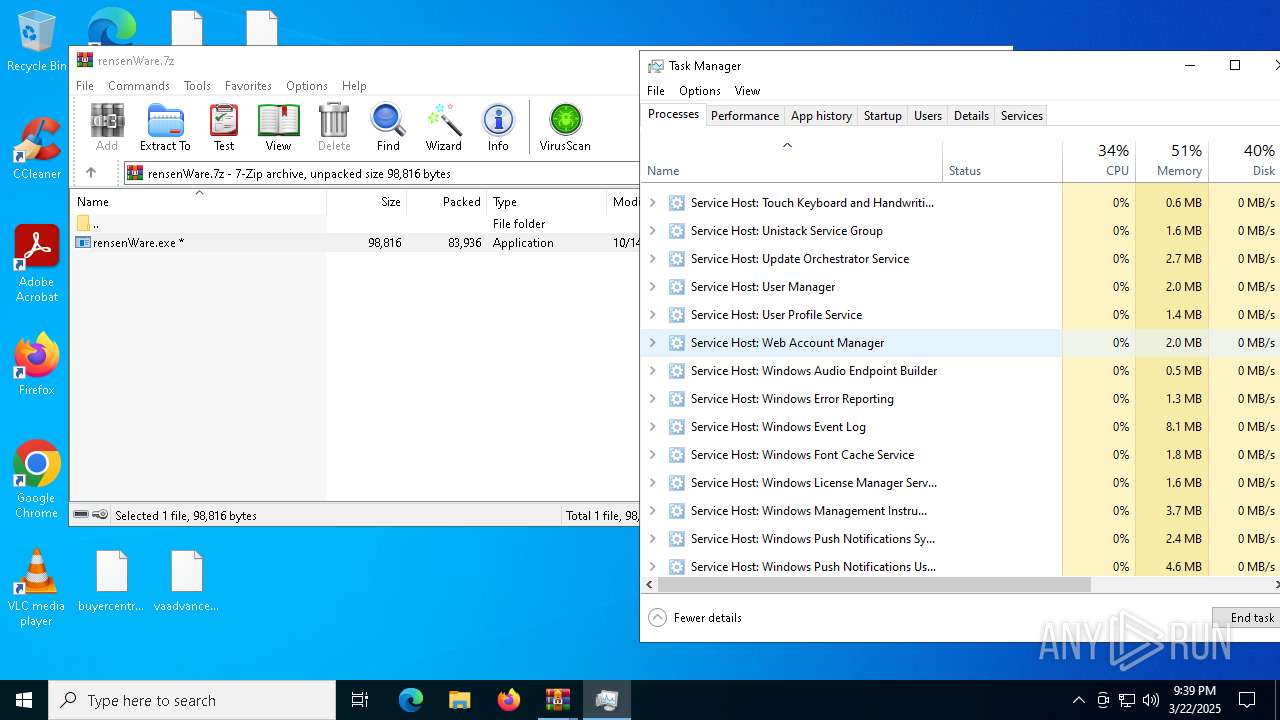
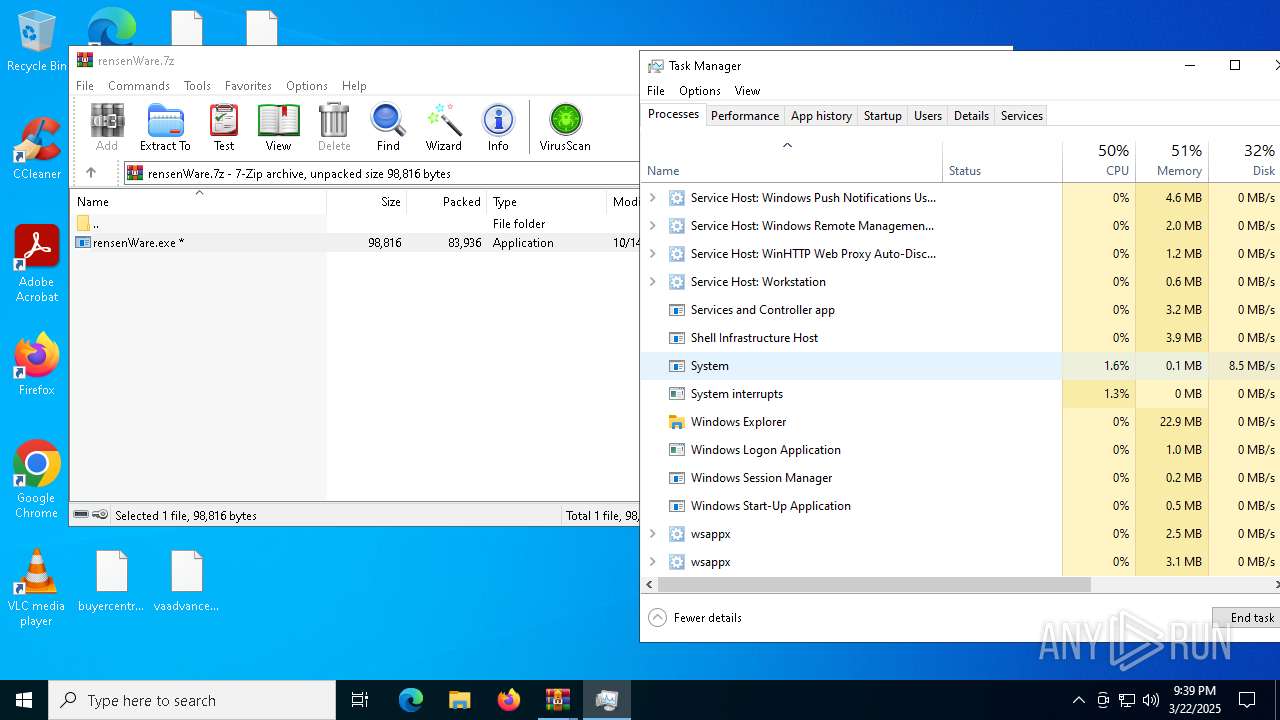
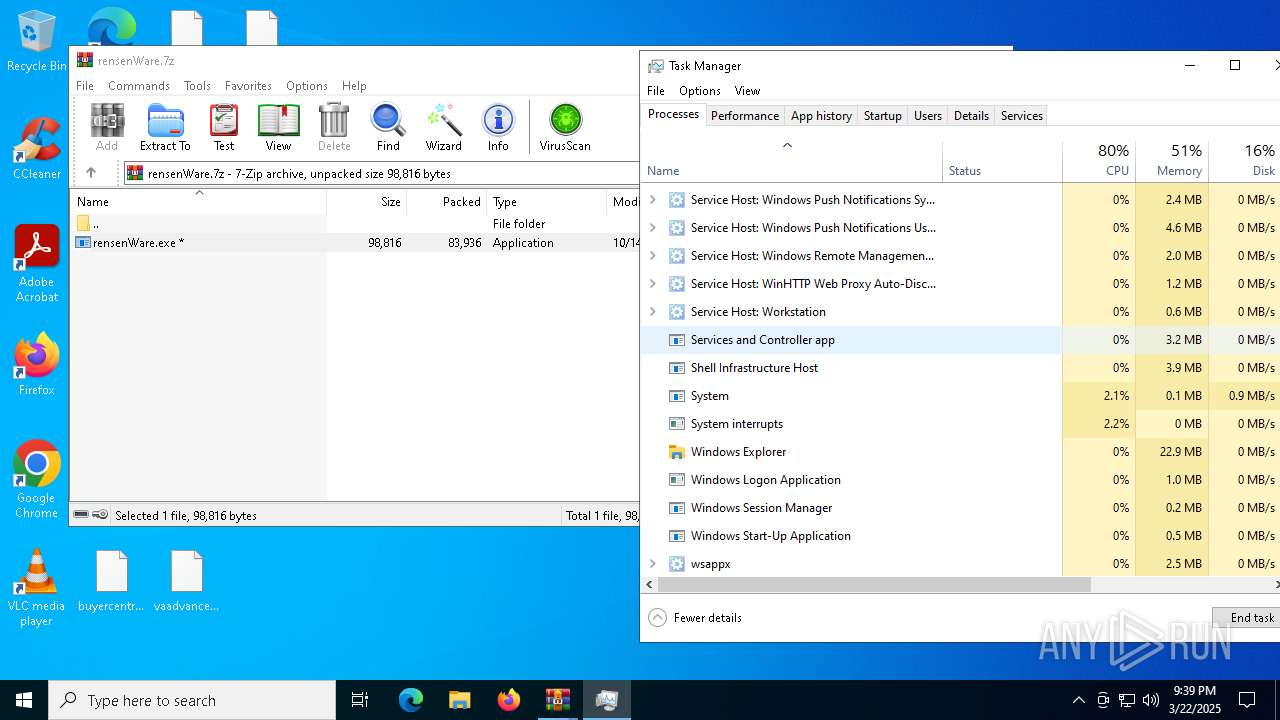
- Taskmgr.exe (PID: 8716)
- Taskmgr.exe (PID: 7288)
- WinRAR.exe (PID: 6248)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 8968)
- WinRAR.exe (PID: 728)
- WinRAR.exe (PID: 6248)
Process checks computer location settings
- Jigsaw.exe (PID: 9044)
Reads the machine GUID from the registry
- drpbx.exe (PID: 9100)
- rensenWare.exe (PID: 8460)
- Hermes.exe (PID: 7764)
Creates files in the program directory
- drpbx.exe (PID: 9100)
- Hermes.exe (PID: 7764)
Confuser has been detected (YARA)
- drpbx.exe (PID: 9100)
Create files in a temporary directory
- drpbx.exe (PID: 9100)
- Hermes.exe (PID: 7764)
The sample compiled with english language support
- WinRAR.exe (PID: 6248)
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 85436)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
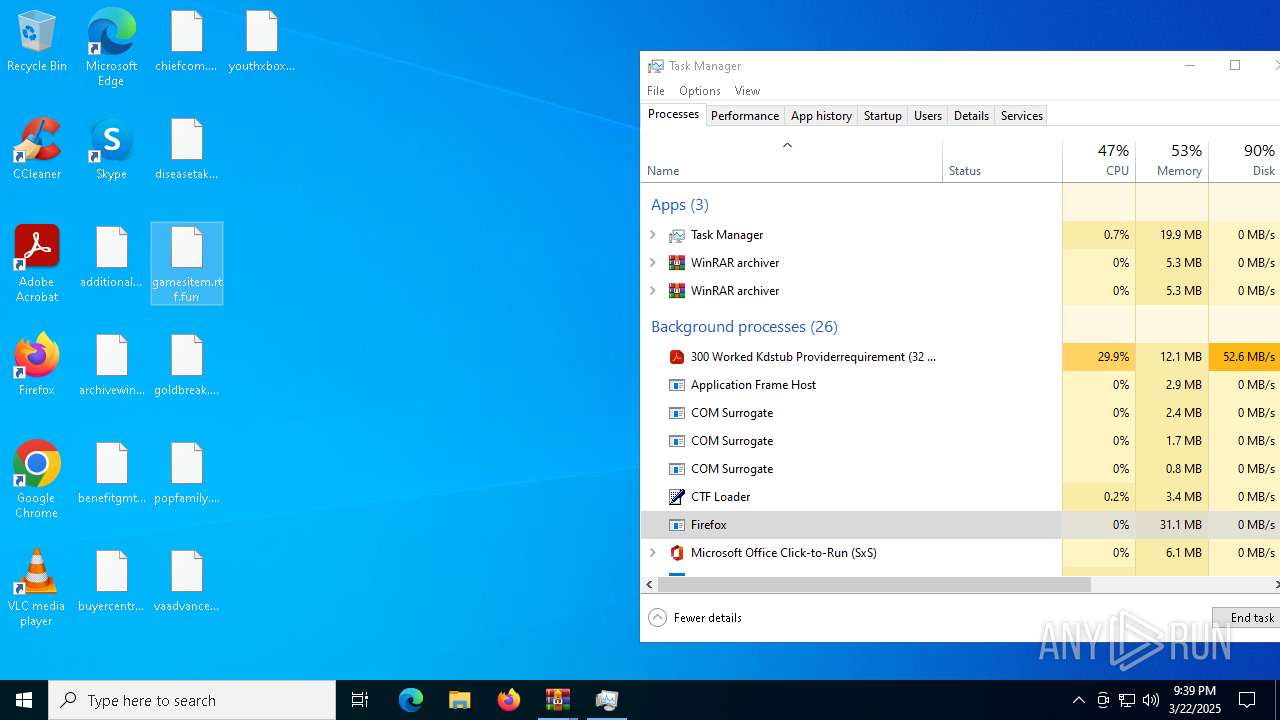
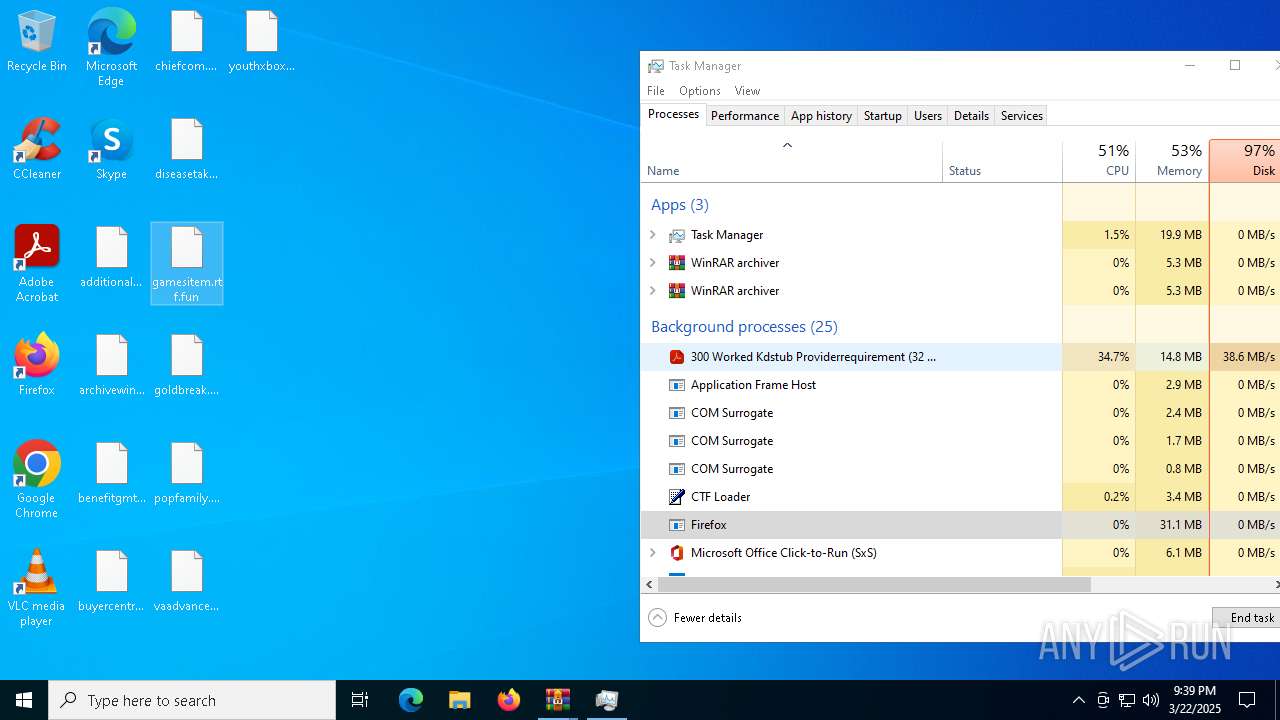
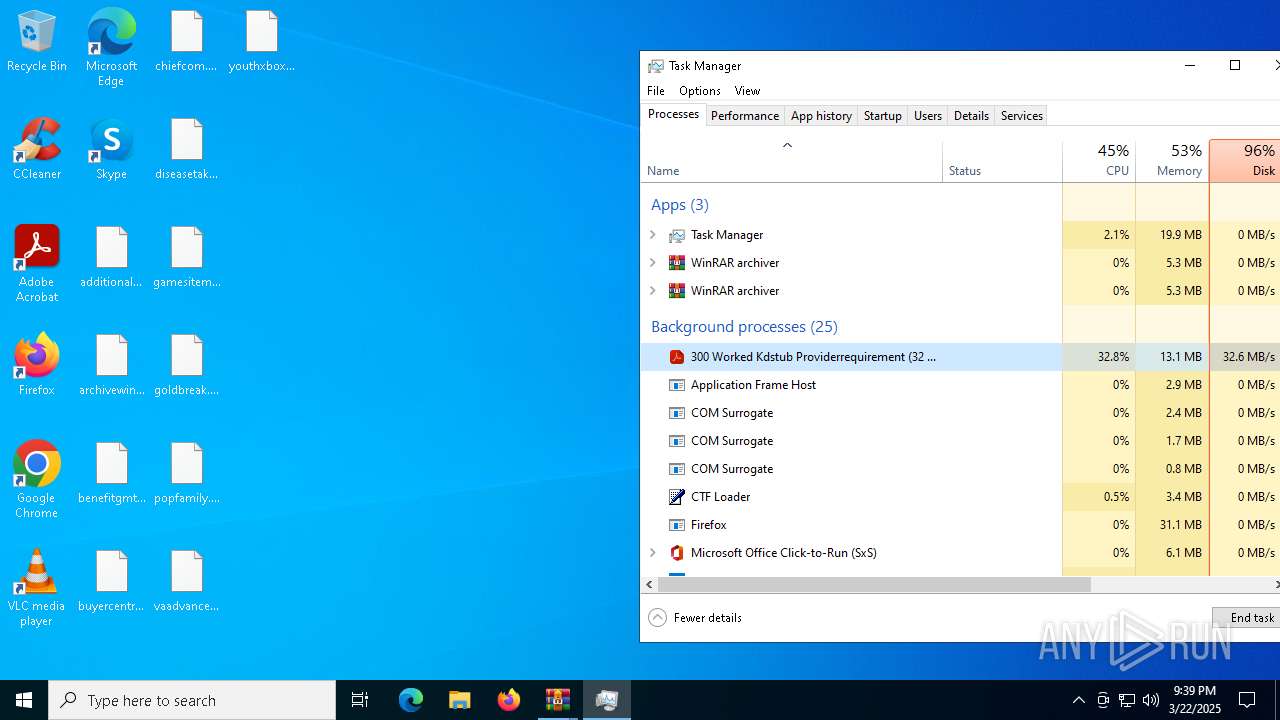
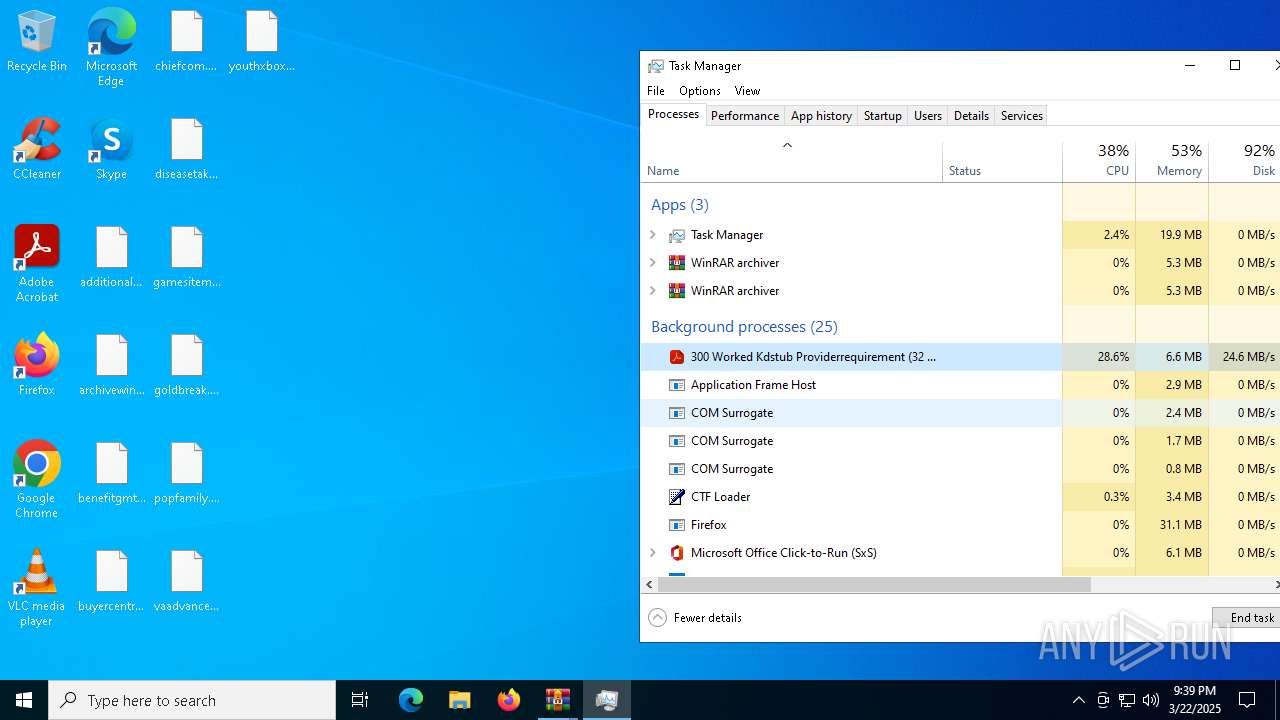
Total processes
172
Monitored processes
30
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 616 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5104 -childID 4 -isForBrowser -prefsHandle 5096 -prefMapHandle 2568 -prefsLen 31251 -prefMapSize 244583 -jsInitHandle 1280 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {7bb3614b-b2b9-4879-897a-0c1fe910addd} 7316 "\\.\pipe\gecko-crash-server-pipe.7316" 2c0671d8690 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 728 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\rensenWare.7z" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 1676 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1764 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2136 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4740 -parentBuildID 20240213221259 -sandboxingKind 0 -prefsHandle 4680 -prefMapHandle 4700 -prefsLen 36588 -prefMapSize 244583 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {4e488391-e261-4f4d-867b-c8212e2650ae} 7316 "\\.\pipe\gecko-crash-server-pipe.7316" 2c0661a8b10 utility | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 1 Version: 123.0 Modules
| |||||||||||||||
| 2236 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3008 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4112 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4864 -childID 5 -isForBrowser -prefsHandle 5008 -prefMapHandle 5012 -prefsLen 38057 -prefMapSize 244583 -jsInitHandle 1280 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {c9c5b1aa-1a59-40dc-9d8a-5a18687dae15} 7316 "\\.\pipe\gecko-crash-server-pipe.7316" 2c0671d8310 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 6044 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5212 -childID 6 -isForBrowser -prefsHandle 4984 -prefMapHandle 5204 -prefsLen 31251 -prefMapSize 244583 -jsInitHandle 1280 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {8e9025c5-8474-4f17-b5b5-5825004a6cc9} 7316 "\\.\pipe\gecko-crash-server-pipe.7316" 2c0671d8d90 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
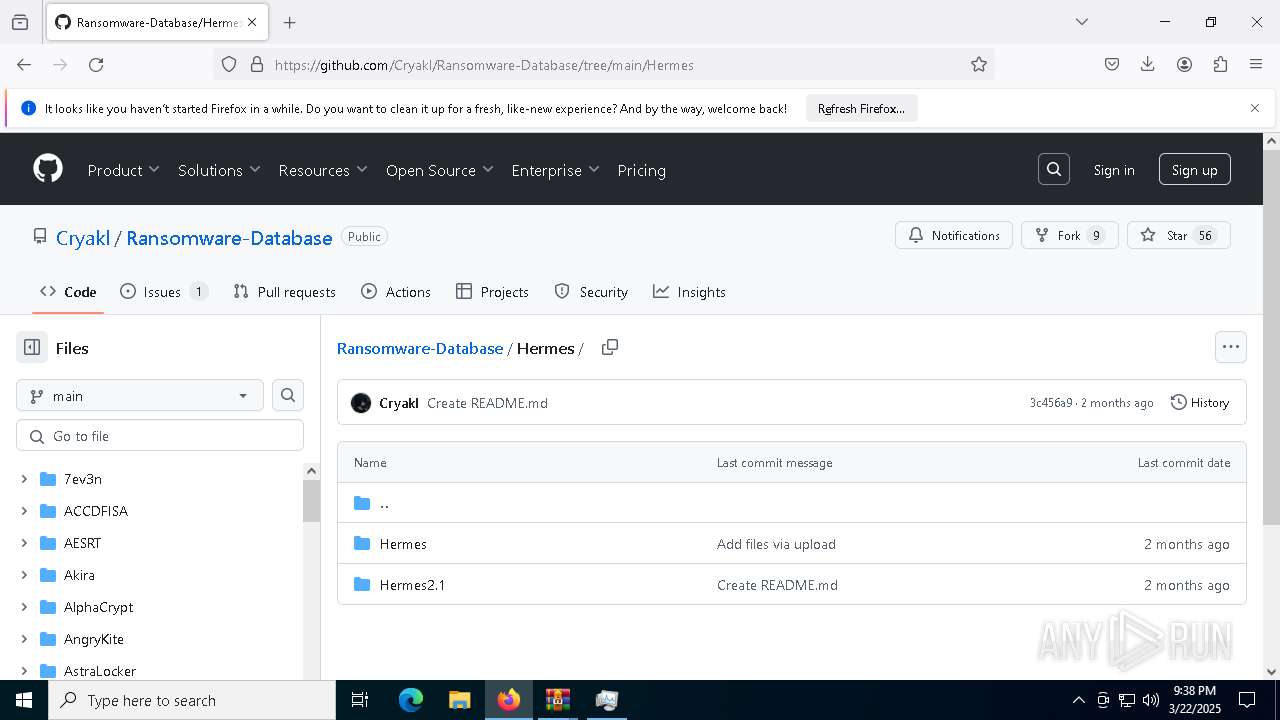
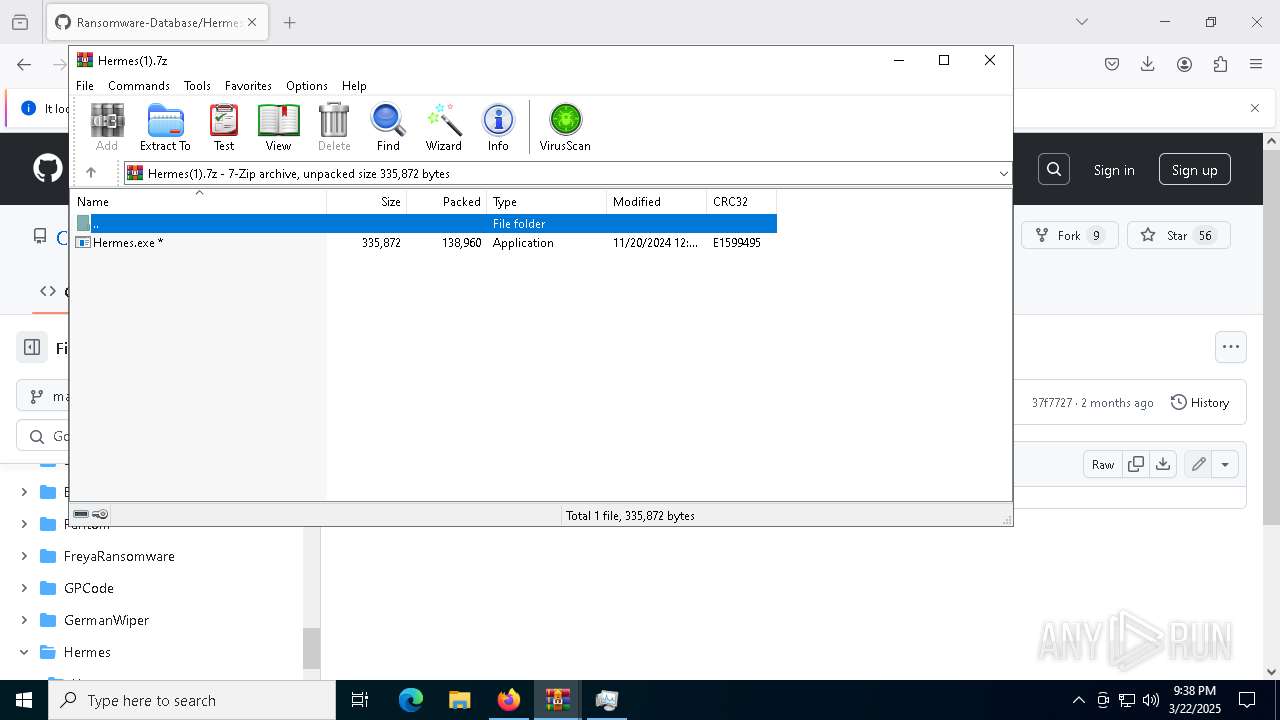
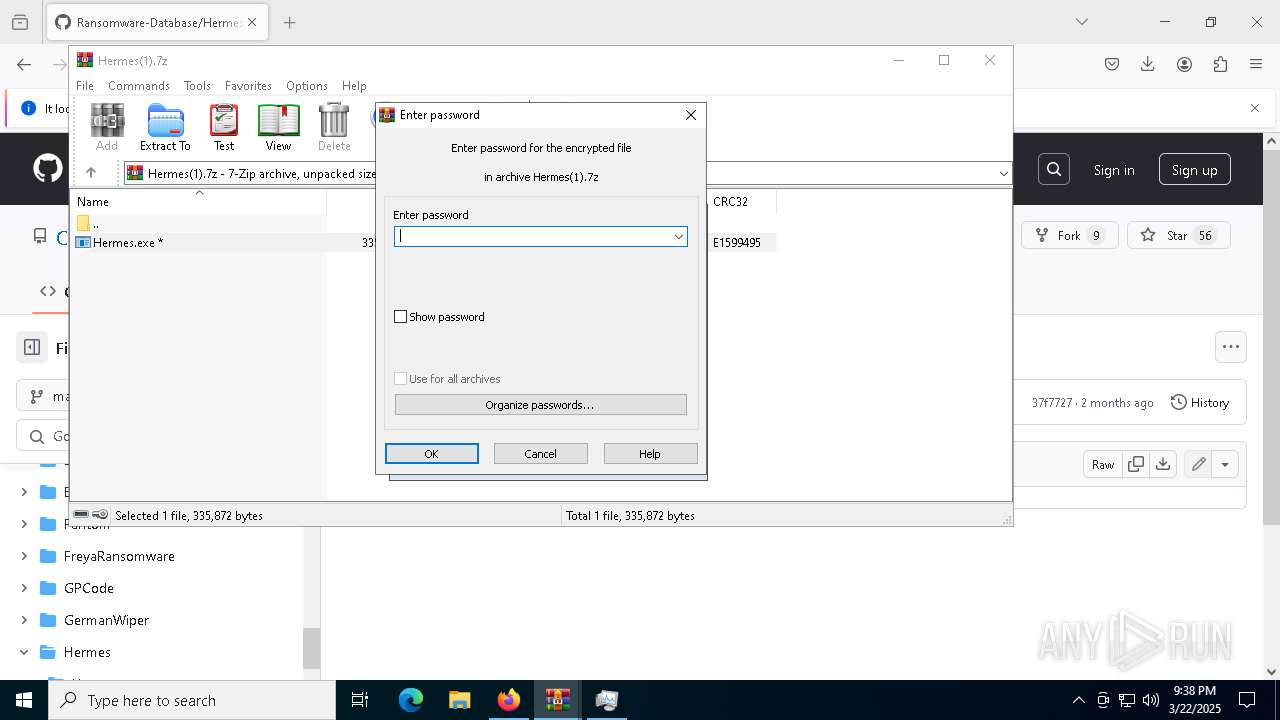
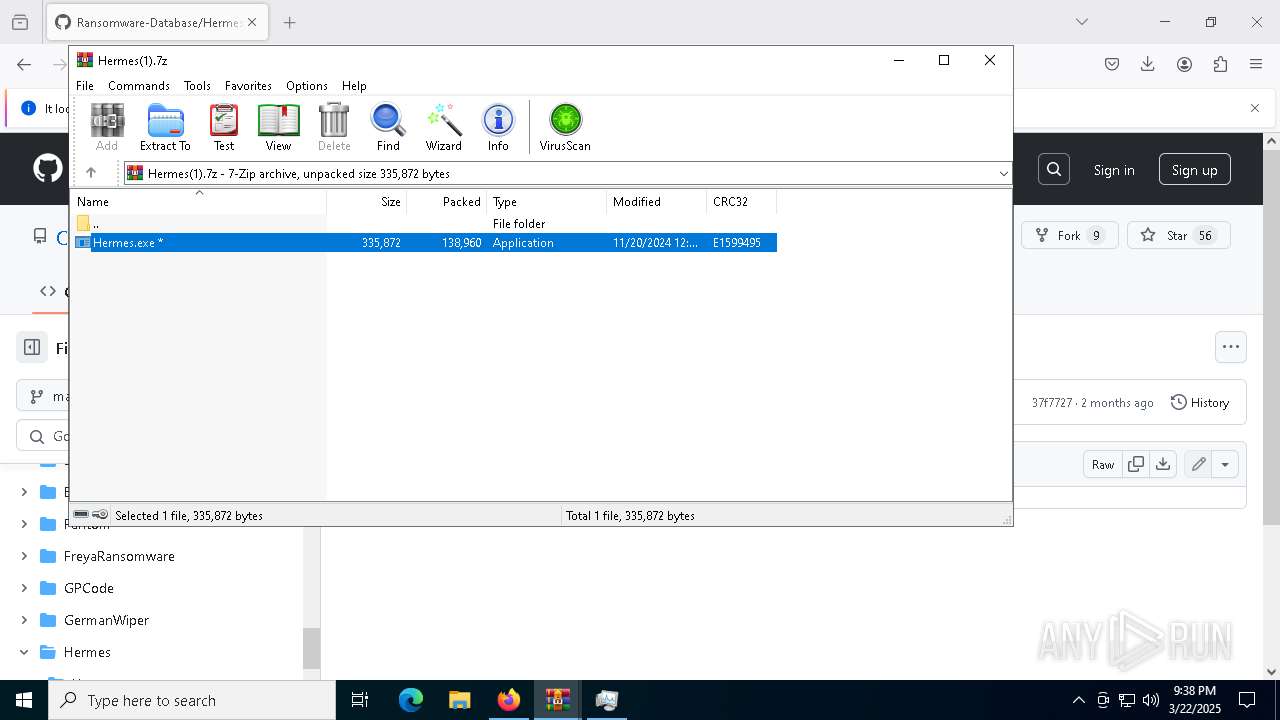
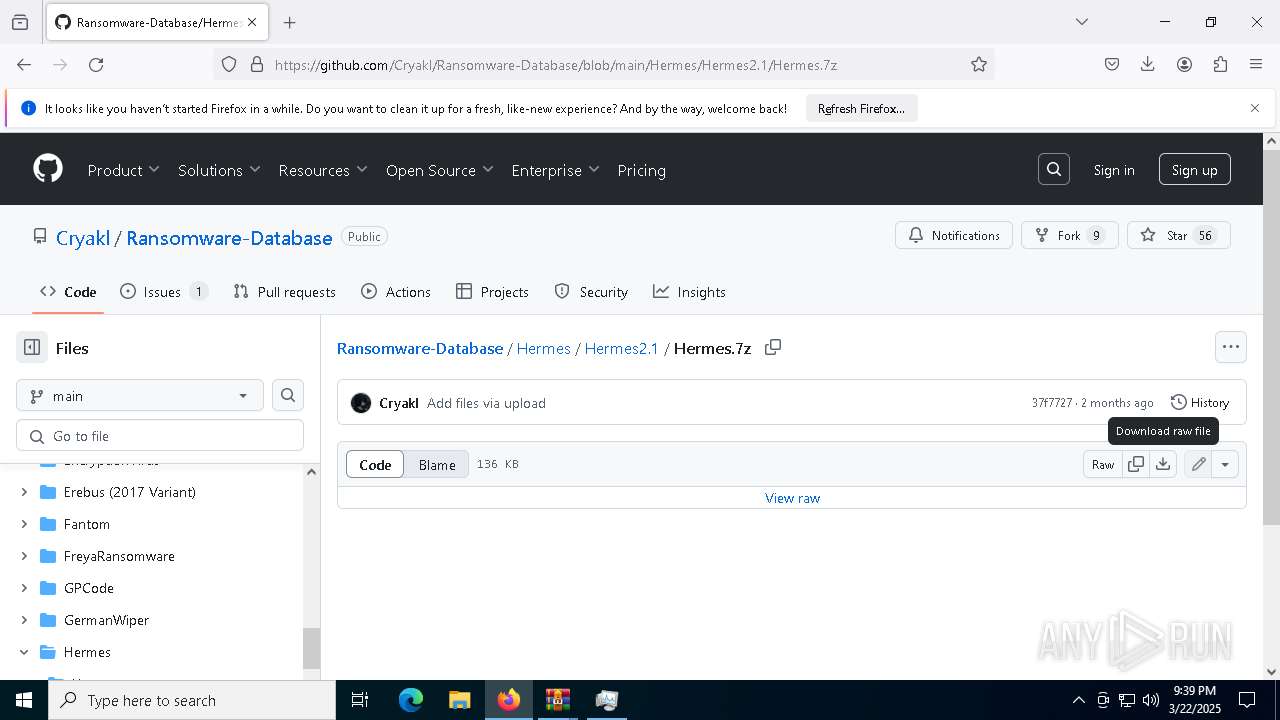
| 6248 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\Hermes(1).7z" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
56 968
Read events
56 910
Write events
57
Delete events
1
Modification events
| (PID) Process: | (7316) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (8628) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (8628) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (8628) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (8836) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (8836) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (8836) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7324) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7324) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7324) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
16
Suspicious files
4 939
Text files
66
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7316 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 7316 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:297E88D7CEB26E549254EC875649F4EB | SHA256:8B75D4FB1845BAA06122888D11F6B65E6A36B140C54A72CC13DF390FD7C95702 | |||
| 7316 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs.js | text | |
MD5:43166E49193D344D6813152243DEFE82 | SHA256:41006EA8B0C5715084D049D6904D40D9352A1C4EB84FECDC80DC78A54D116346 | |||
| 7316 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 7316 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7316 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7316 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3561288849sdhlie.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7316 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\2823318777ntouromlalnodry--naod.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7316 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs-1.js | text | |
MD5:43166E49193D344D6813152243DEFE82 | SHA256:41006EA8B0C5715084D049D6904D40D9352A1C4EB84FECDC80DC78A54D116346 | |||
| 7316 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\SiteSecurityServiceState.bin | binary | |
MD5:18871E8114BDFE31E056F60FE5DBF9B0 | SHA256:AA07E227121171B851F7202696A0C00ACB3390A7B8FC222EC81D44FAAD5B9F2C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
91
DNS requests
156
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7316 | firefox.exe | POST | 200 | 172.217.18.3:80 | http://o.pki.goog/s/wr3/UTA | unknown | — | — | whitelisted |
7316 | firefox.exe | POST | 200 | 2.16.2.73:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 23.63.118.230:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7316 | firefox.exe | POST | 200 | 23.63.118.230:80 | http://ocsp.digicert.com/ | unknown | — | — | whitelisted |
7316 | firefox.exe | POST | 200 | 2.16.2.73:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
6560 | backgroundTaskHost.exe | GET | 200 | 23.63.118.230:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.48.23.162:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7316 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
7316 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
7316 | firefox.exe | POST | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.48.23.162:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
7316 | firefox.exe | 140.82.121.3:443 | github.com | GITHUB | US | whitelisted |
7316 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
7316 | firefox.exe | 172.217.16.202:443 | safebrowsing.googleapis.com | GOOGLE | US | whitelisted |
7316 | firefox.exe | 34.117.188.166:443 | contile.services.mozilla.com | — | — | whitelisted |
7316 | firefox.exe | 34.107.243.93:443 | push.services.mozilla.com | GOOGLE | US | whitelisted |
7316 | firefox.exe | 172.217.18.3:80 | o.pki.goog | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
github.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
spocs.getpocket.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |