| File name: | AsyncClient.exe |
| Full analysis: | https://app.any.run/tasks/d46f398a-85ef-4c2a-b16b-53a1fd3f6ba4 |
| Verdict: | Malicious activity |
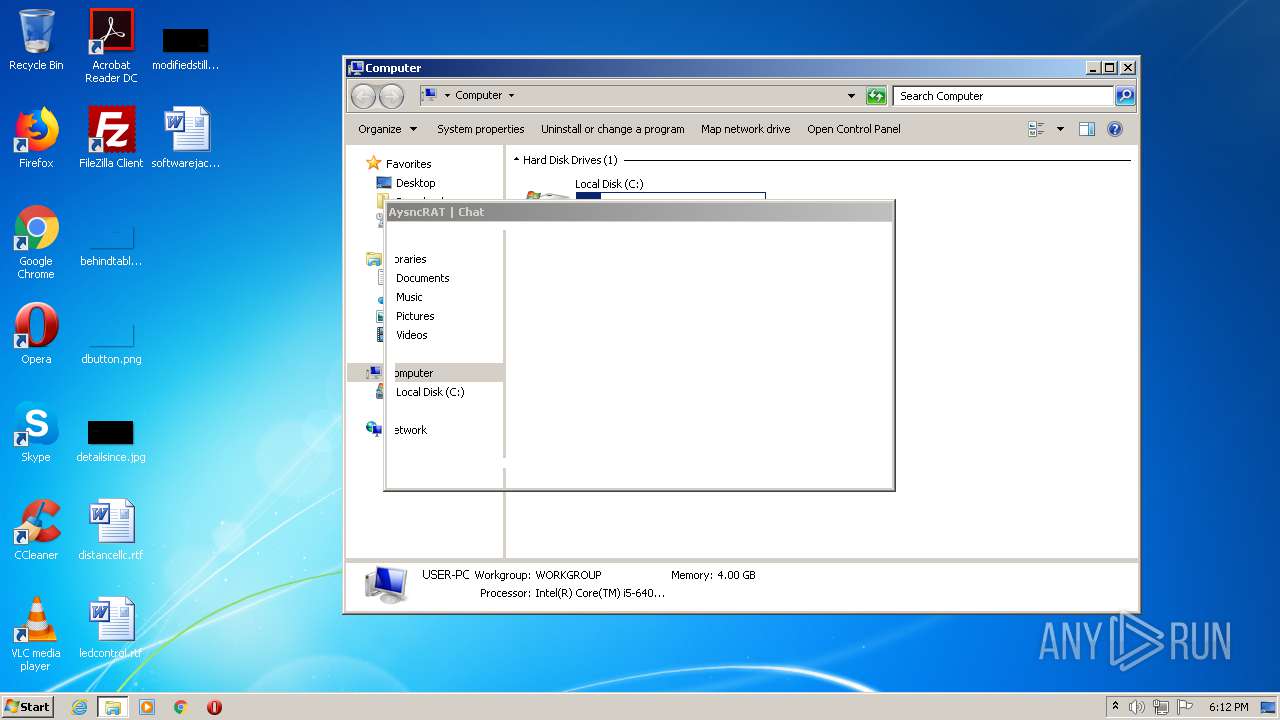
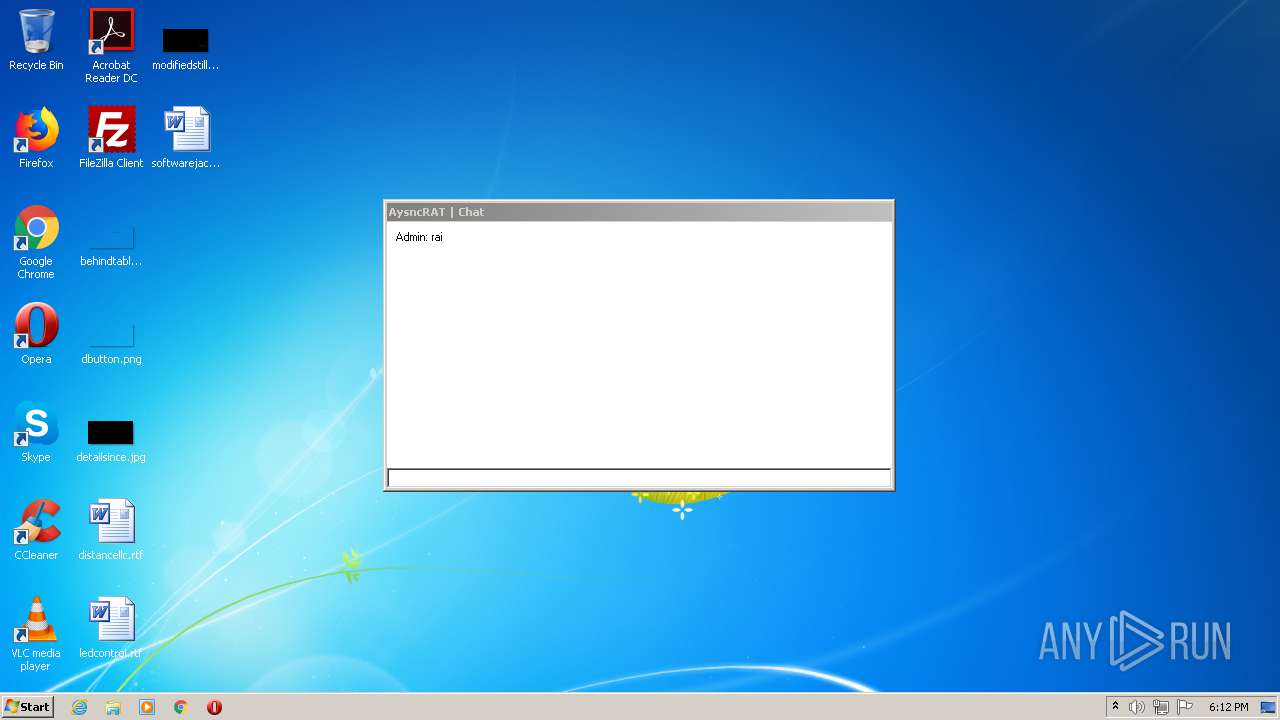
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | August 08, 2020, 17:09:43 |
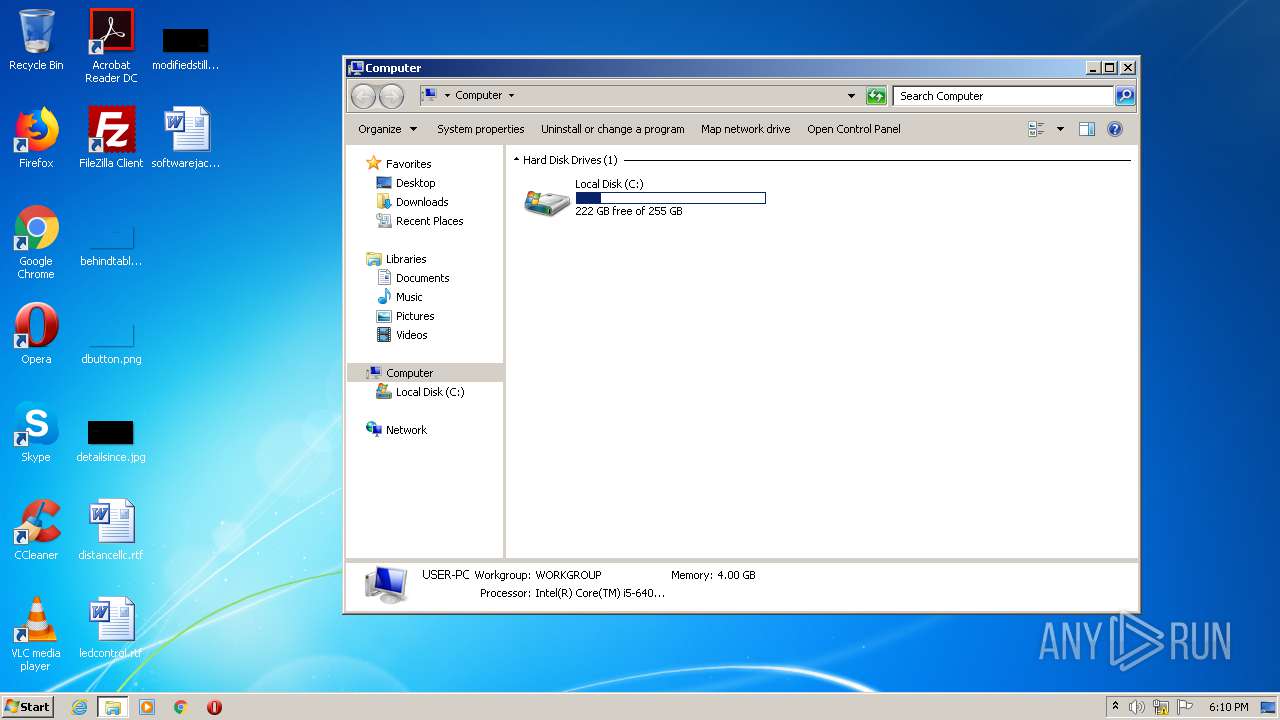
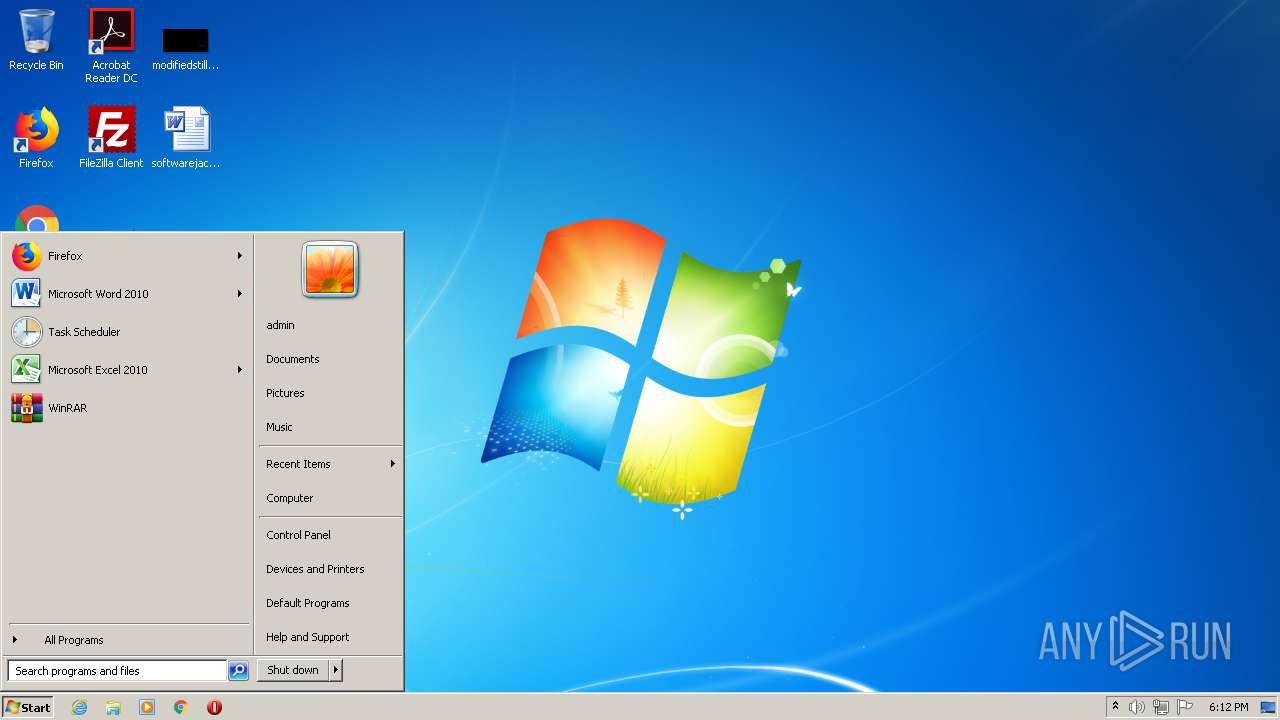
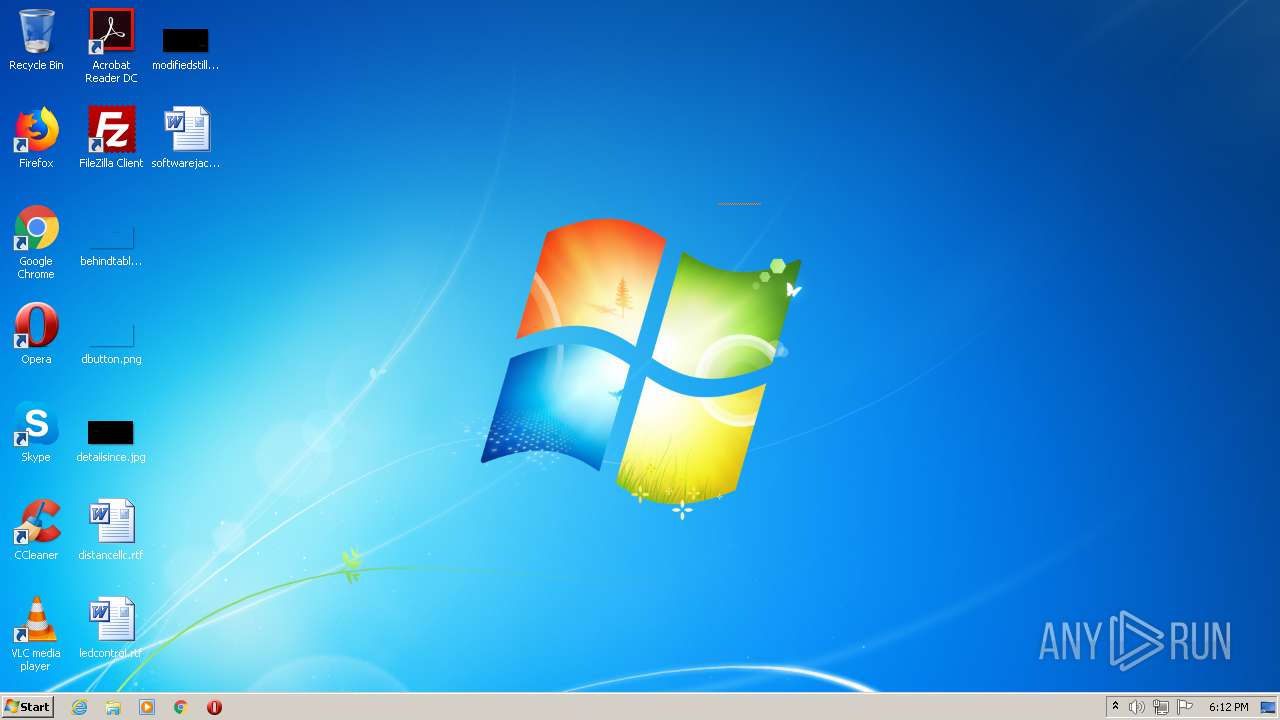
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 08390E31A7B39201D7E4F9E9F5FEE8DE |
| SHA1: | DE954065080F33FA524A75ED5B495CE8B53CB46B |
| SHA256: | 20B98F56DC1CBFACFD0C3908545088BBC62E2E513D4AF2C677FDC9178B1A39F0 |
| SSDEEP: | 768:8uqc9T944nD5WUxiVDmo2qrvcbnBi6SPIXn3LiMUodRq0b+wI4fF4LHjePgB/aqT:8uqc9T9xy2VBZ7Xn3LiIrb+7Q4LHjeot |
MALICIOUS
ASYNCRAT was detected
- AsyncClient.exe (PID: 2932)
SUSPICIOUS
No suspicious indicators.INFO
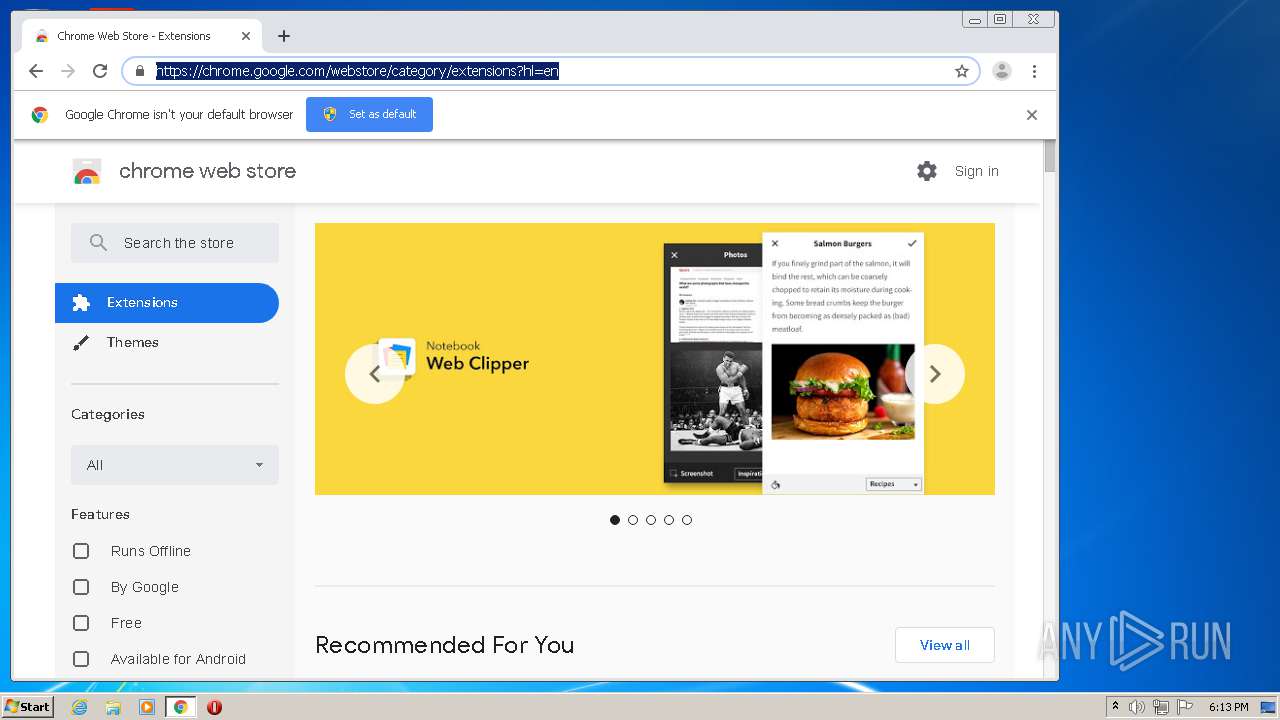
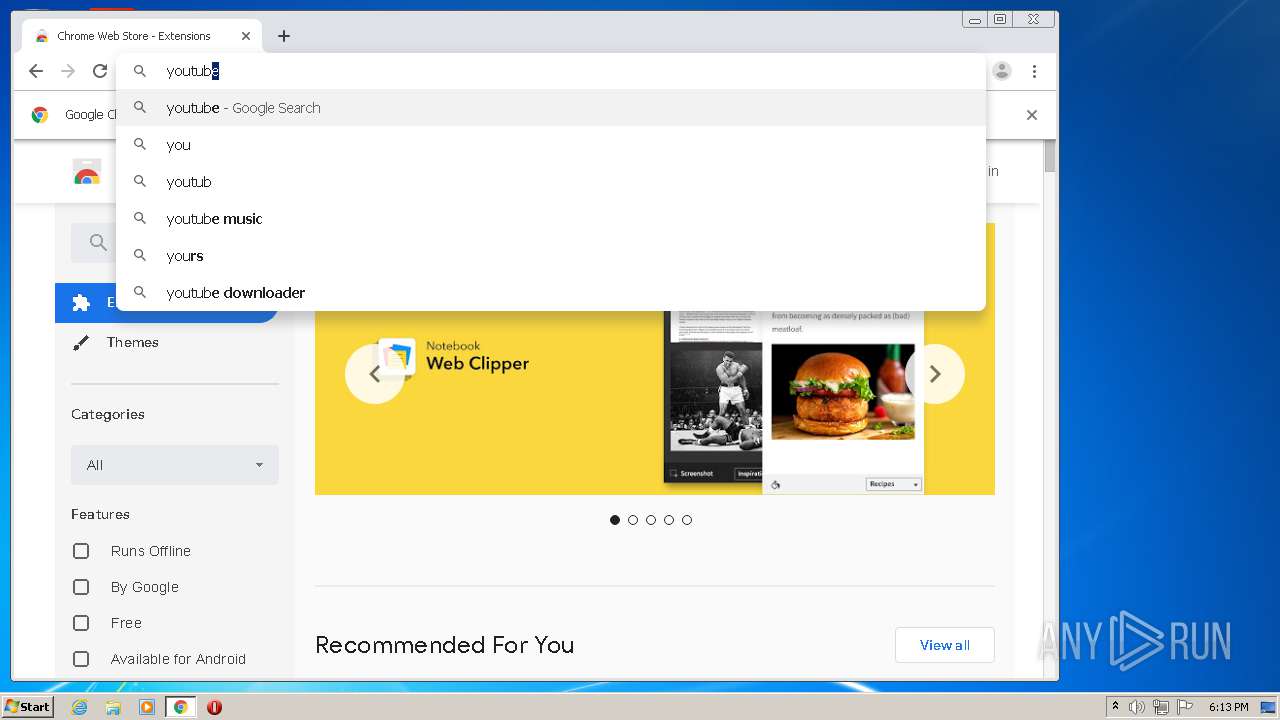
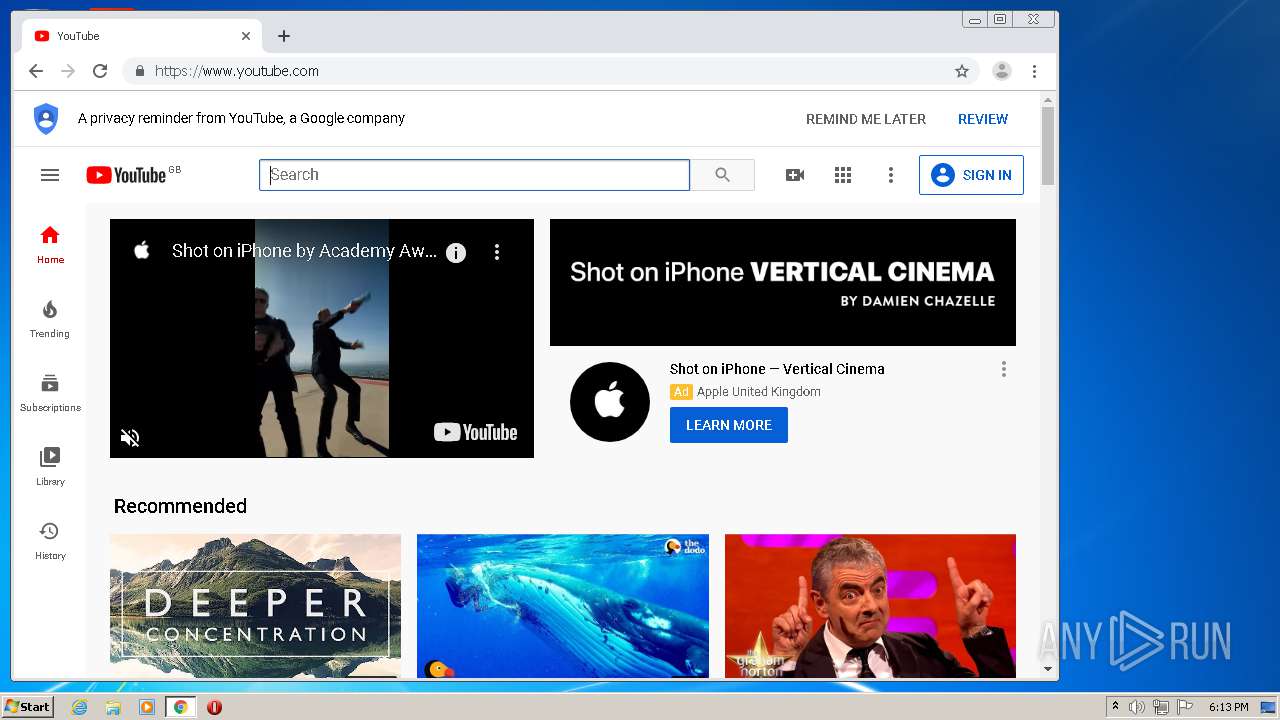
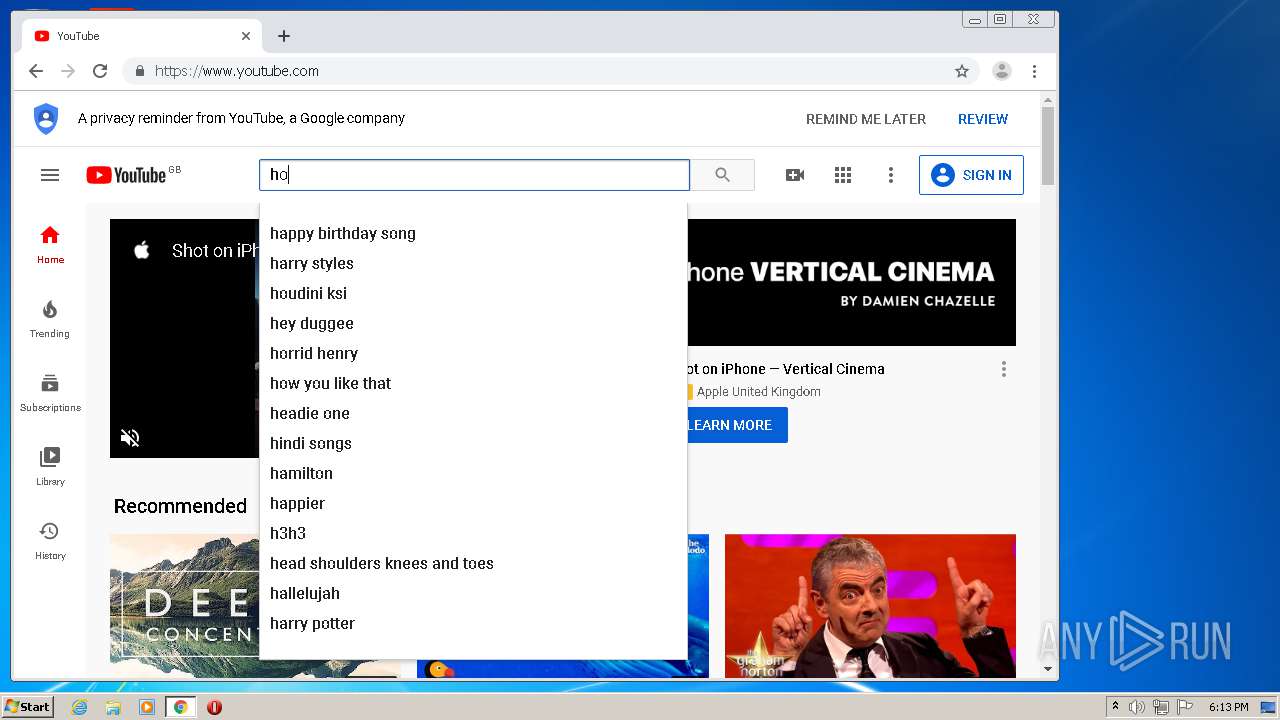
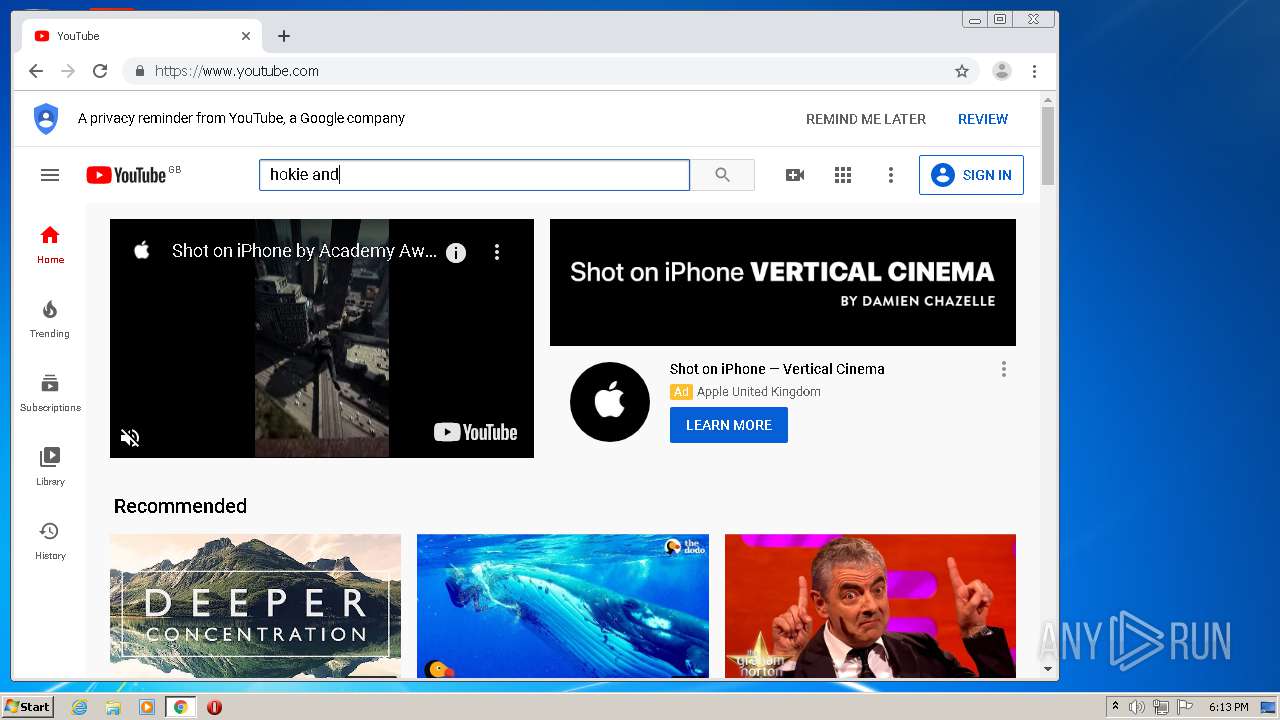
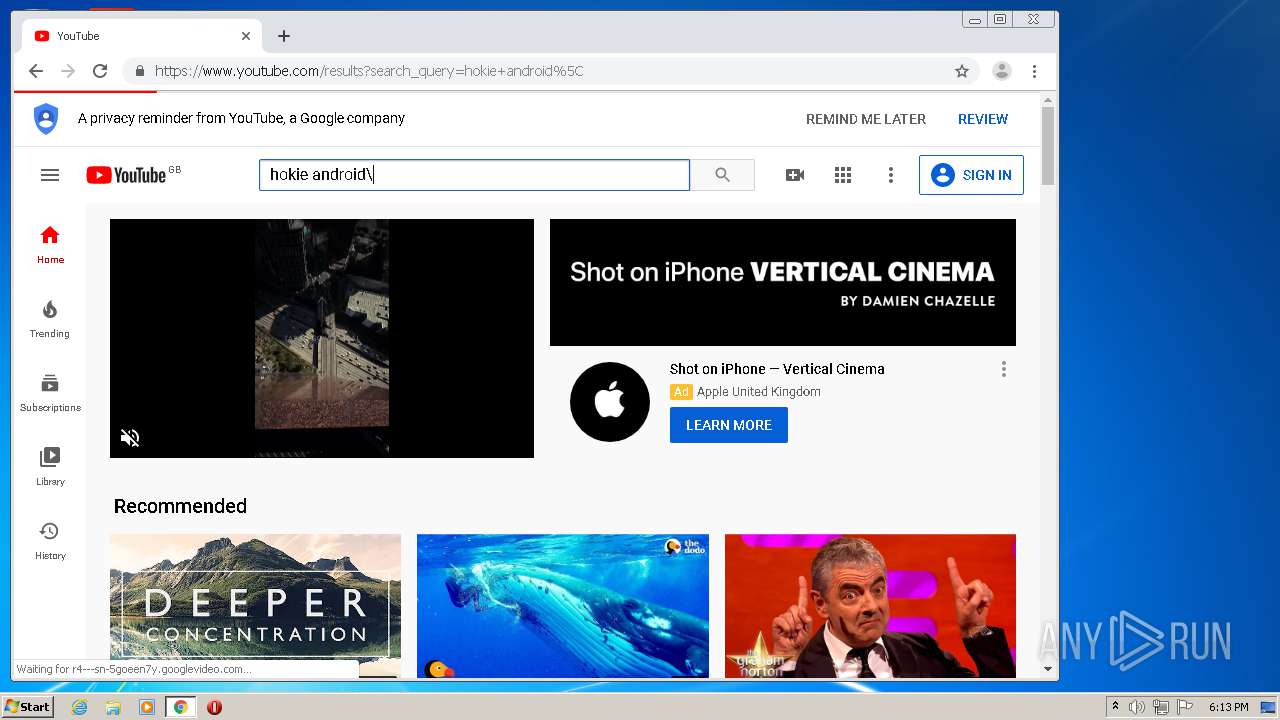
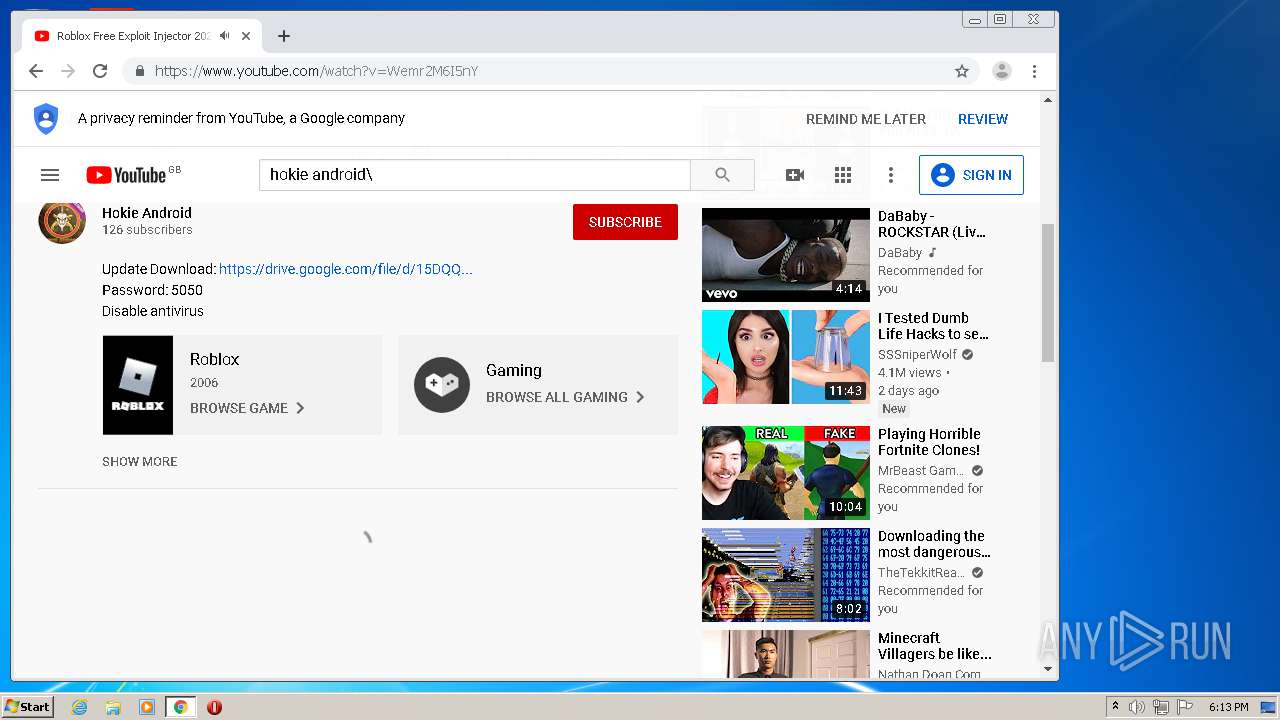
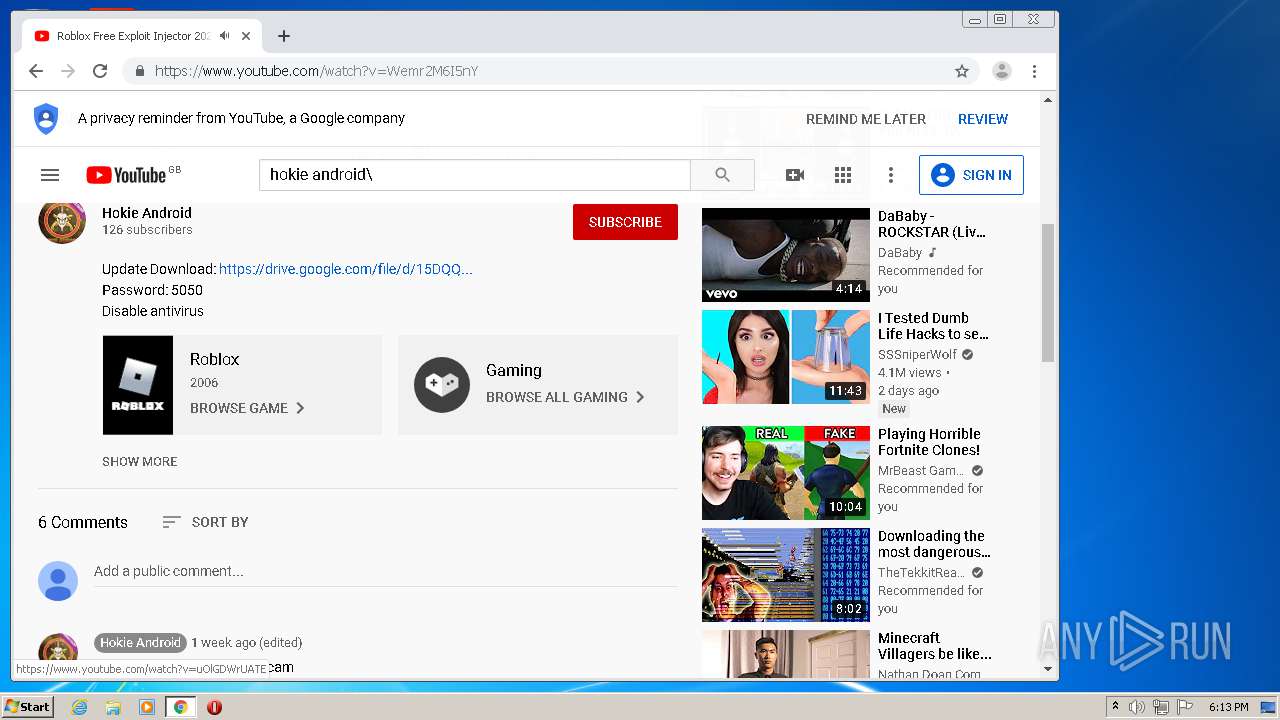
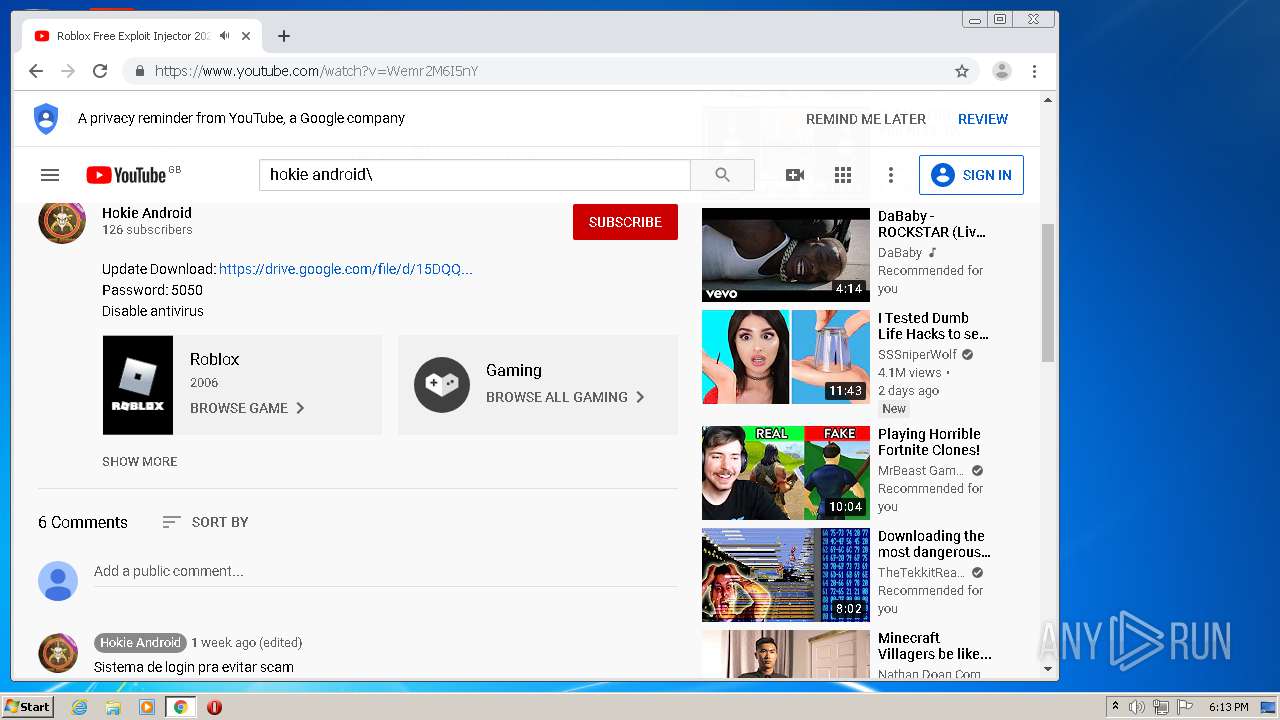
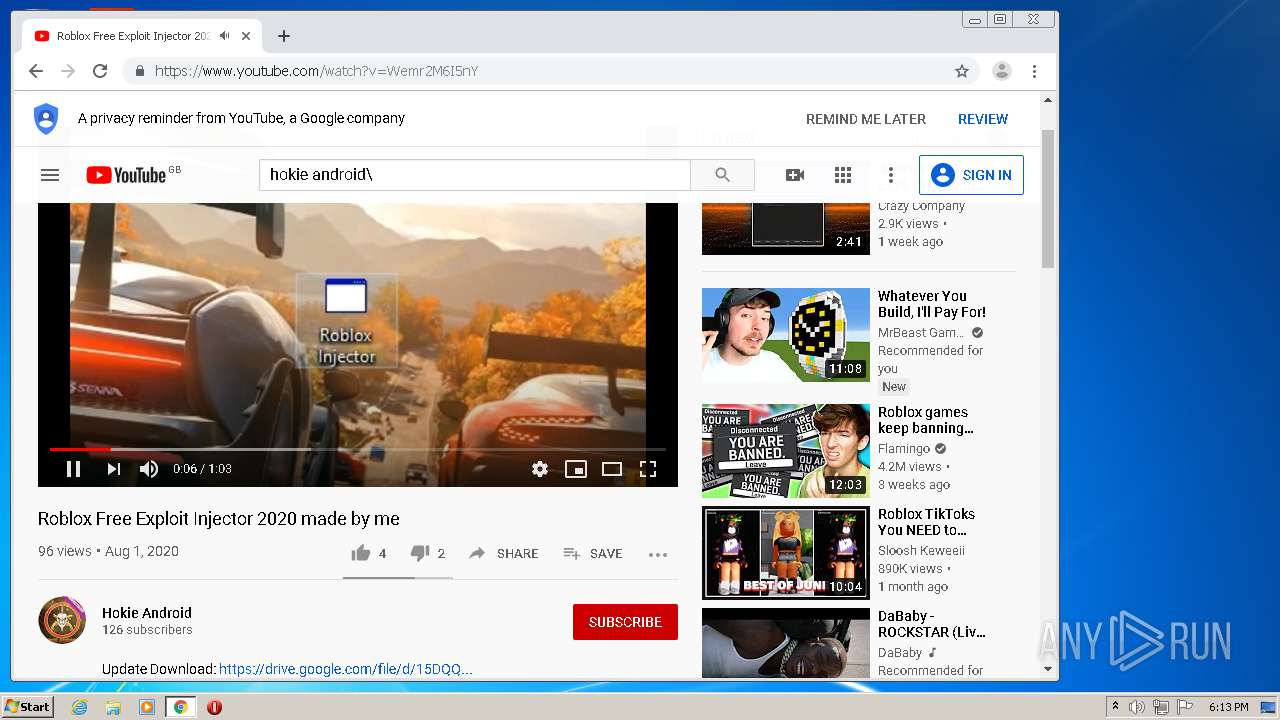
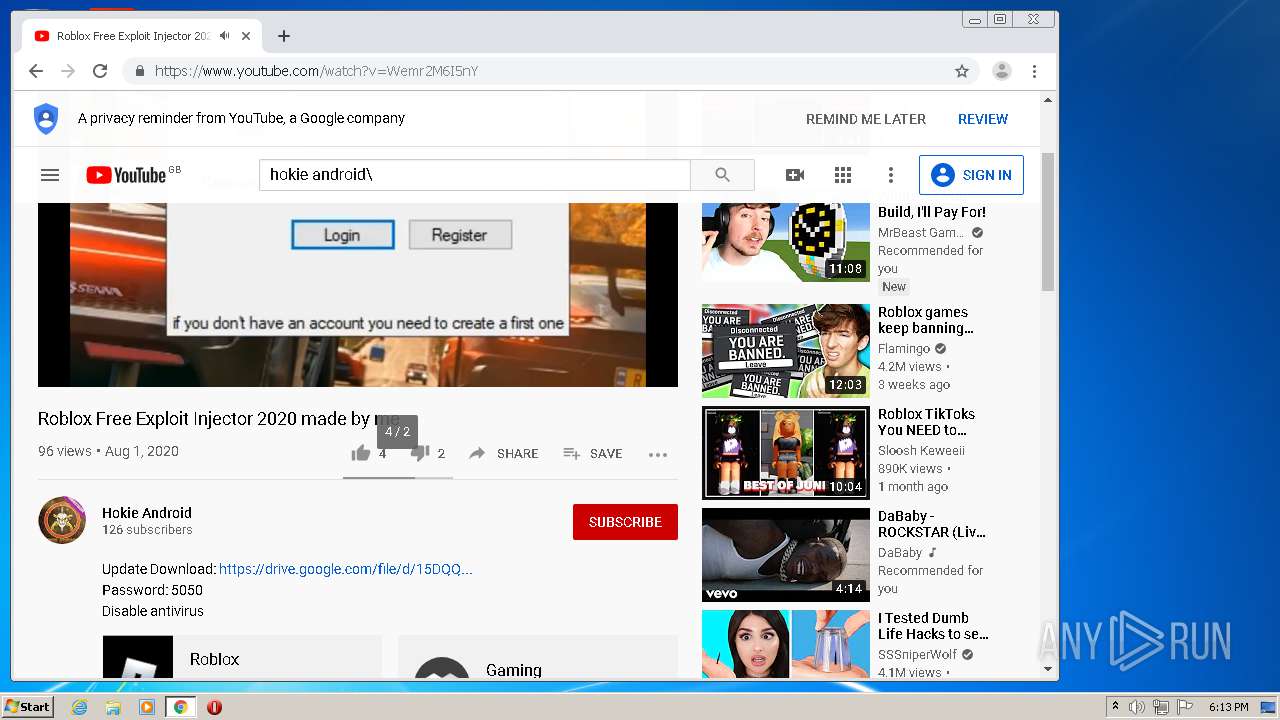
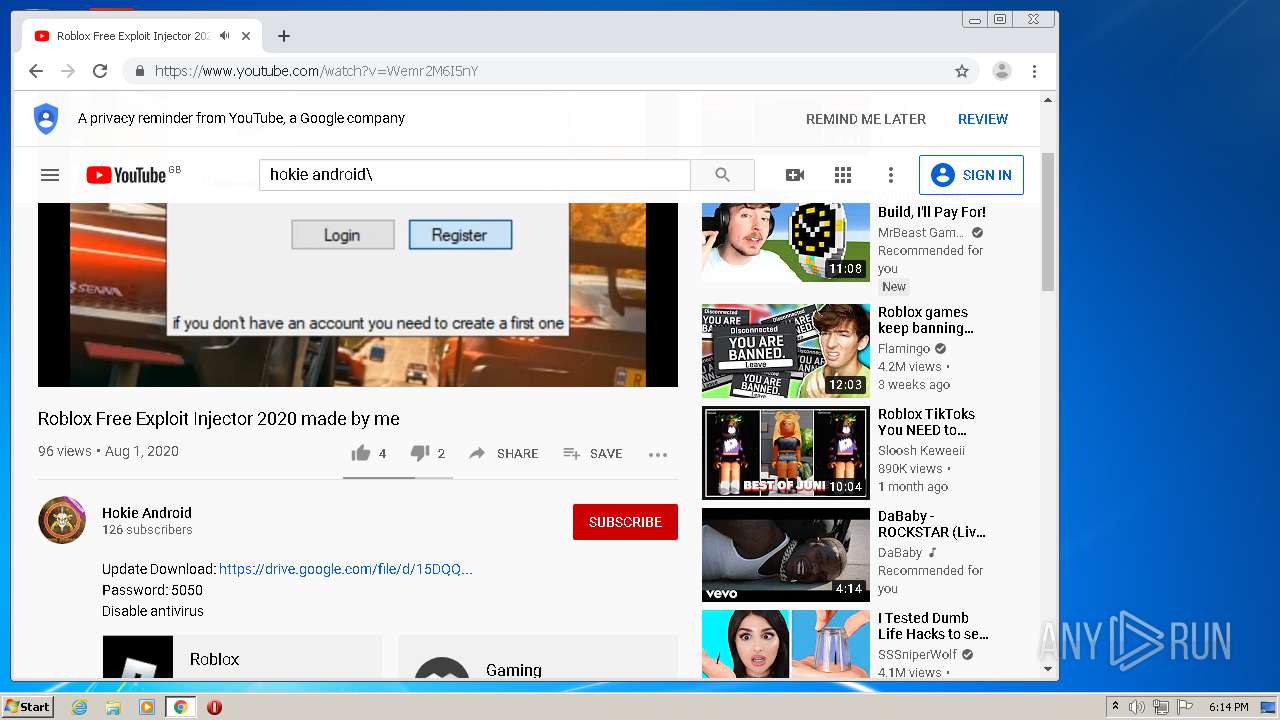
Manual execution by user
- chrome.exe (PID: 2148)
Application launched itself
- chrome.exe (PID: 2148)
Reads settings of System Certificates
- chrome.exe (PID: 1496)
- AsyncClient.exe (PID: 2932)
Reads the hosts file
- chrome.exe (PID: 2148)
- chrome.exe (PID: 1496)
Reads Internet Cache Settings
- chrome.exe (PID: 2148)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:05:10 07:24:51+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 45568 |
| InitializedDataSize: | 3072 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xd0ce |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
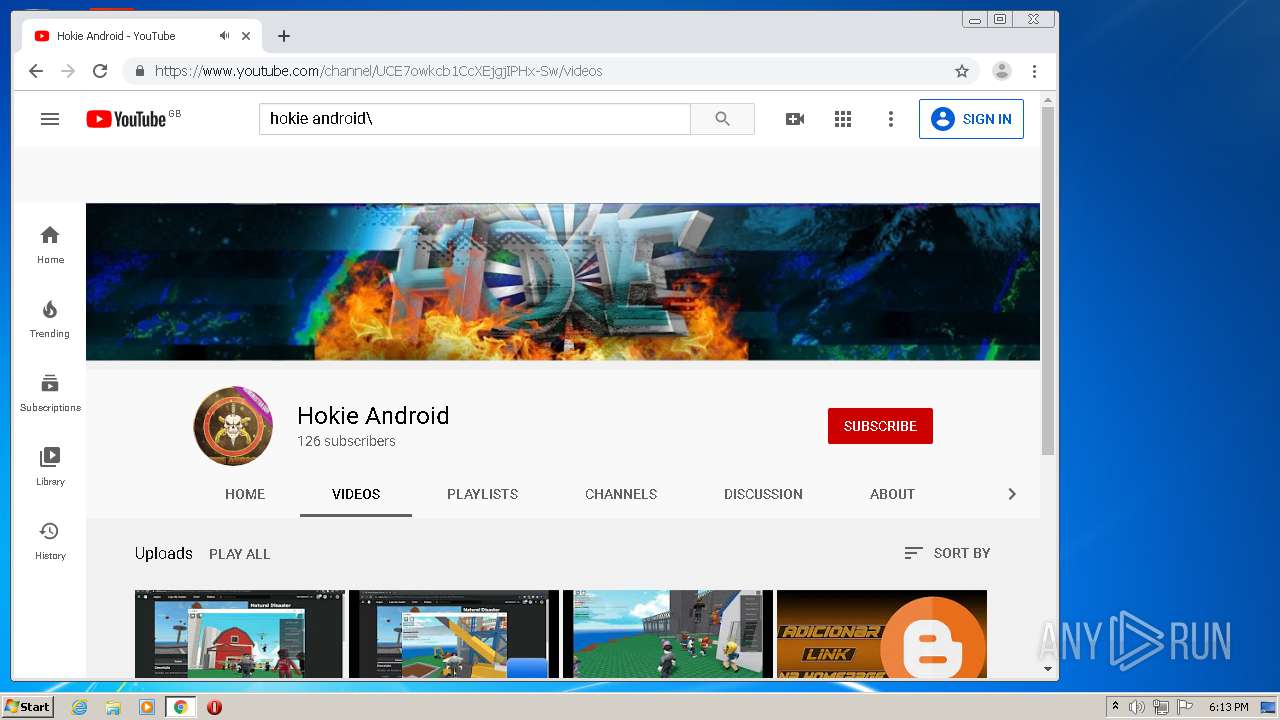
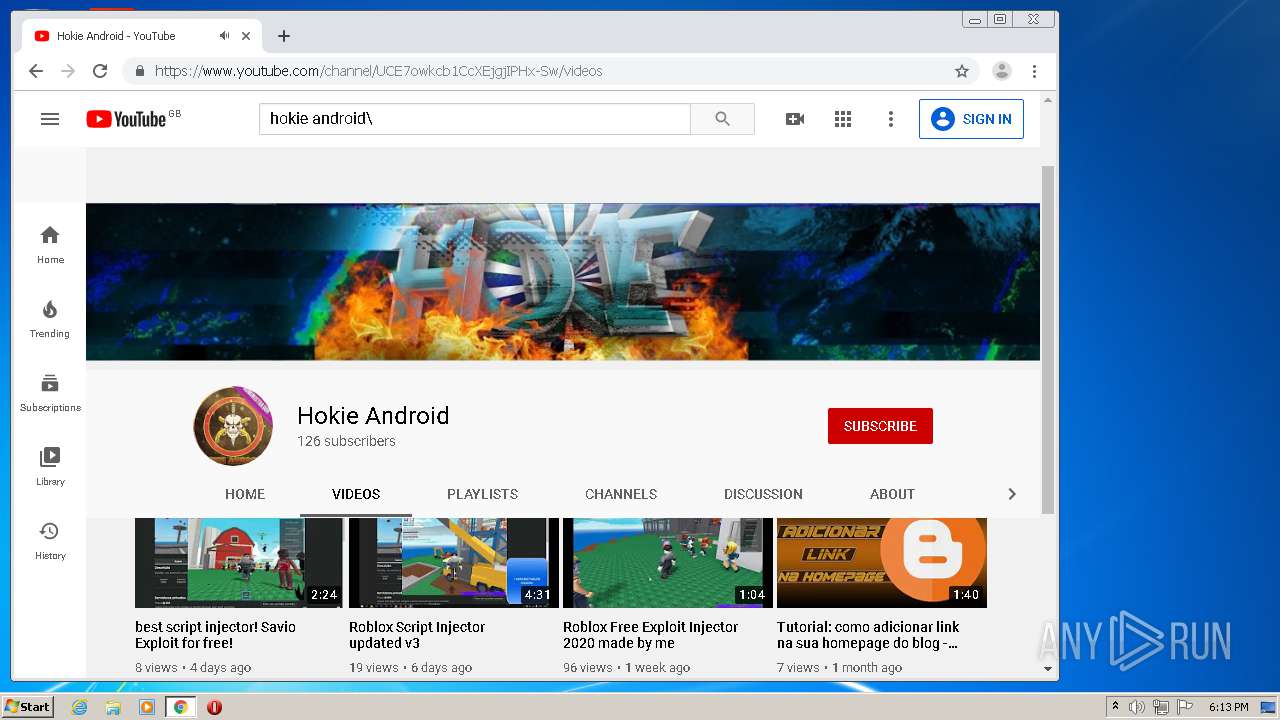
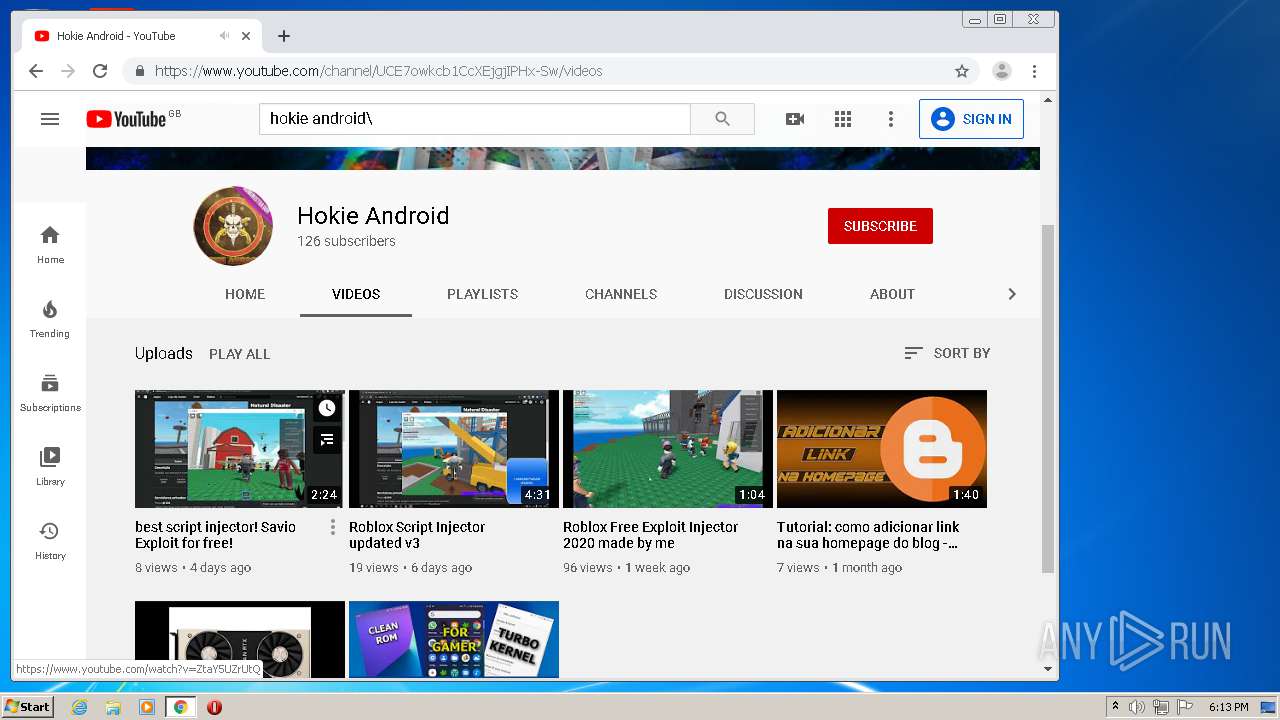
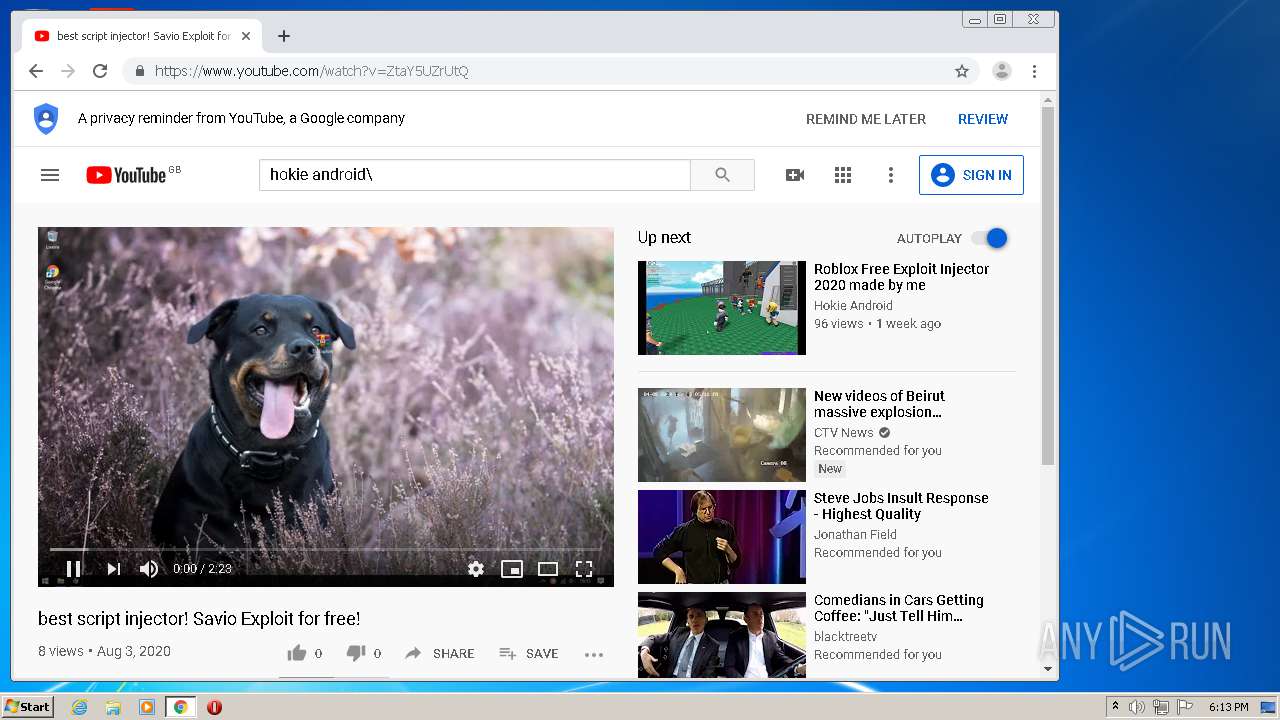
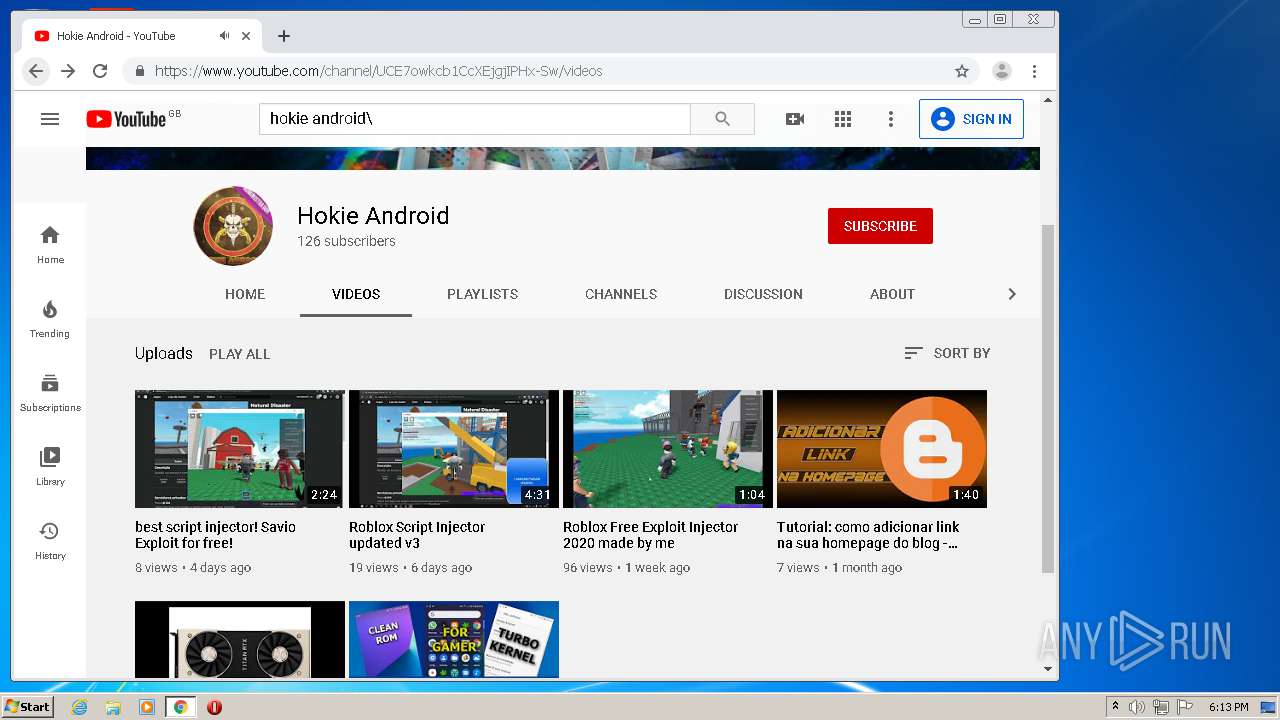
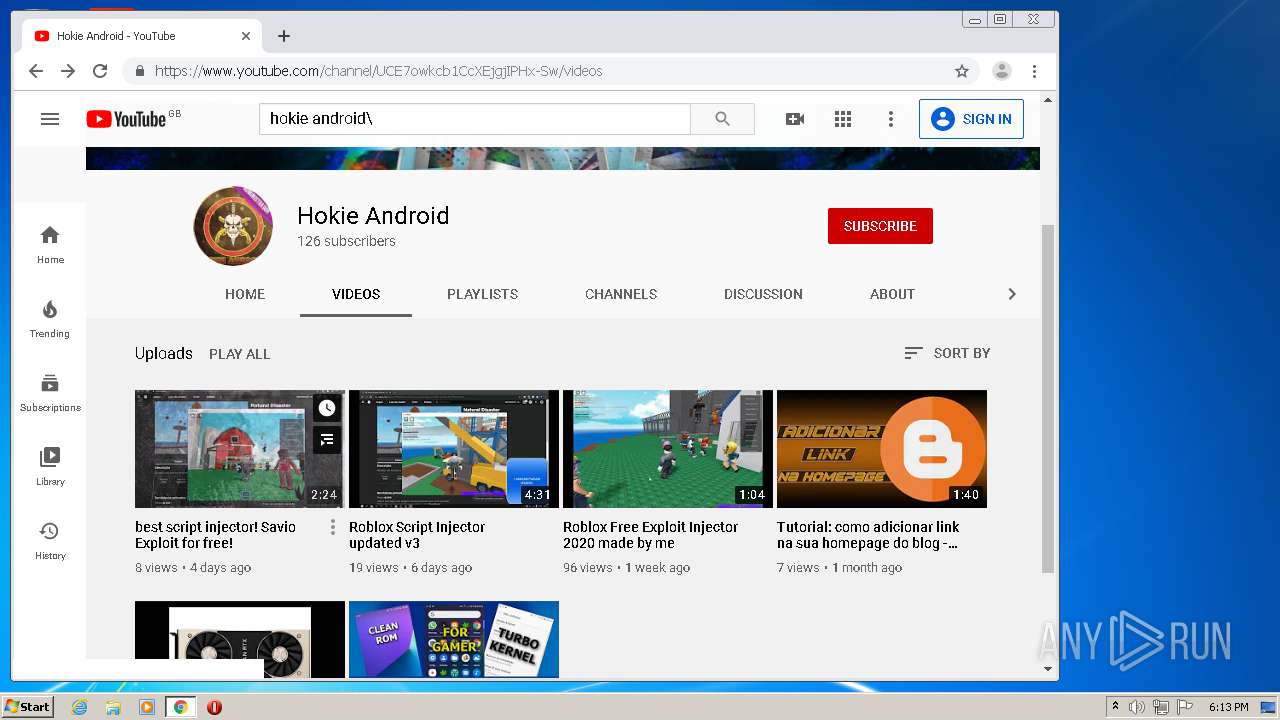
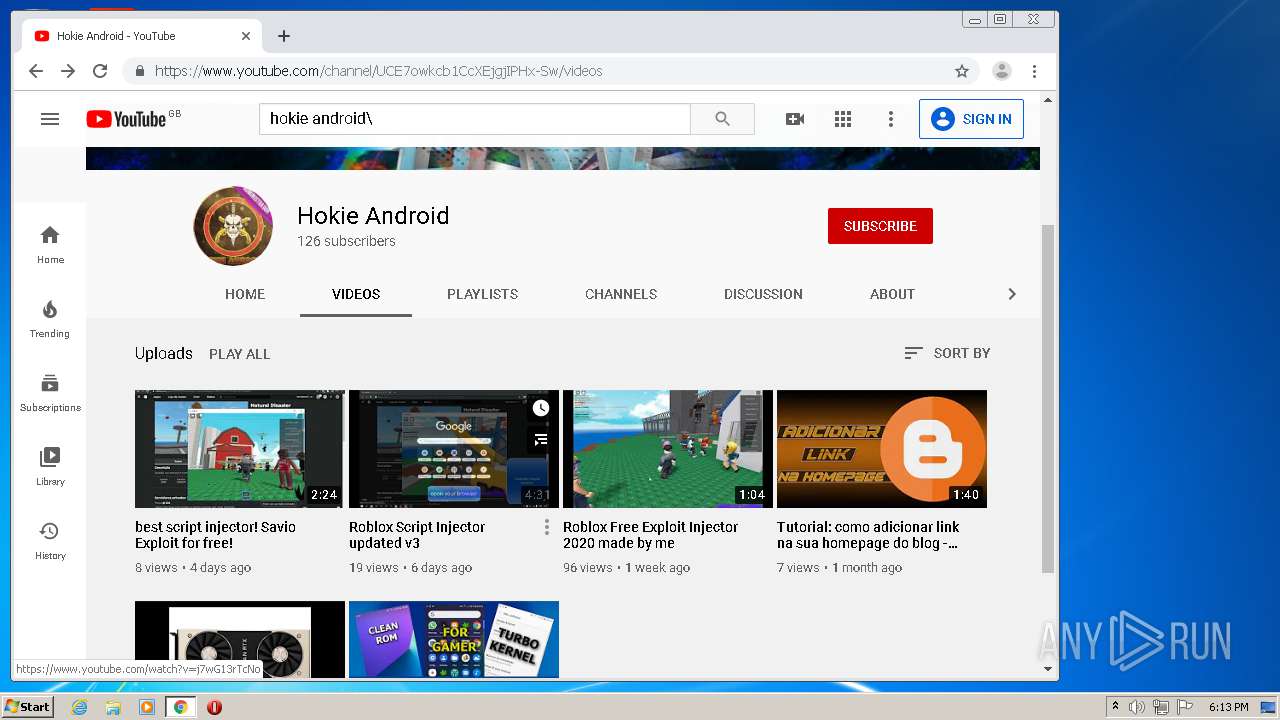
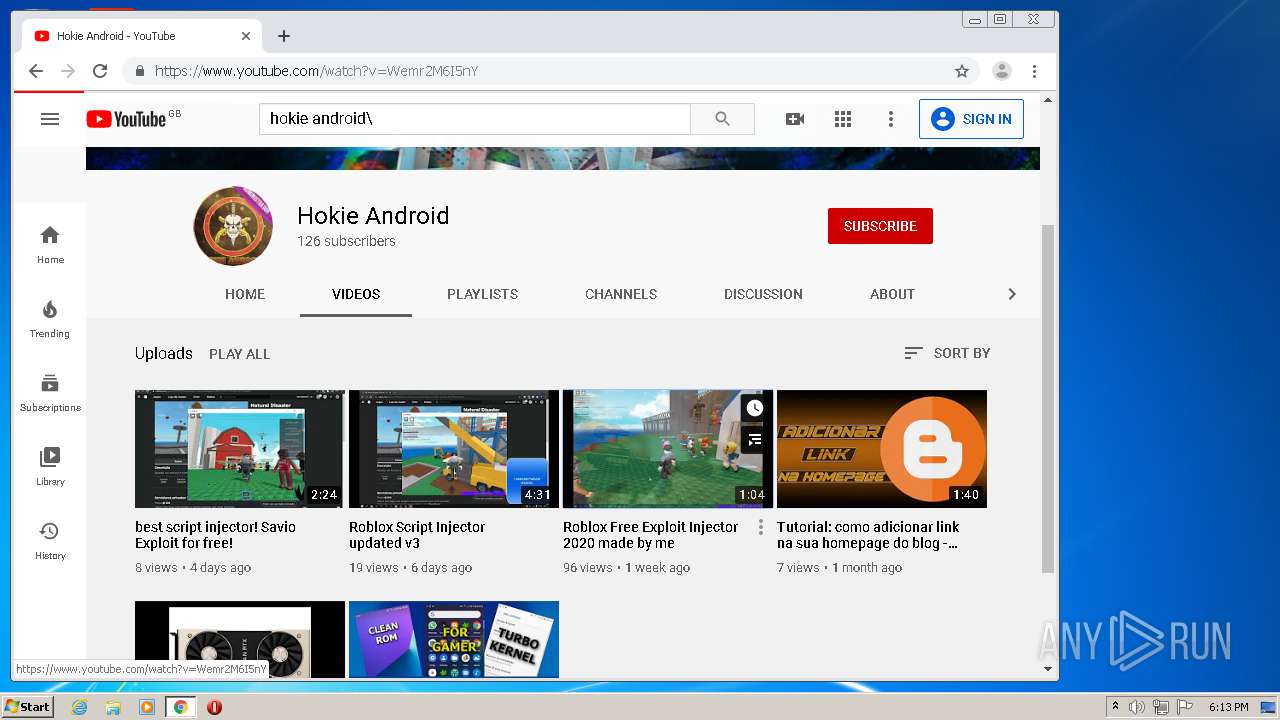
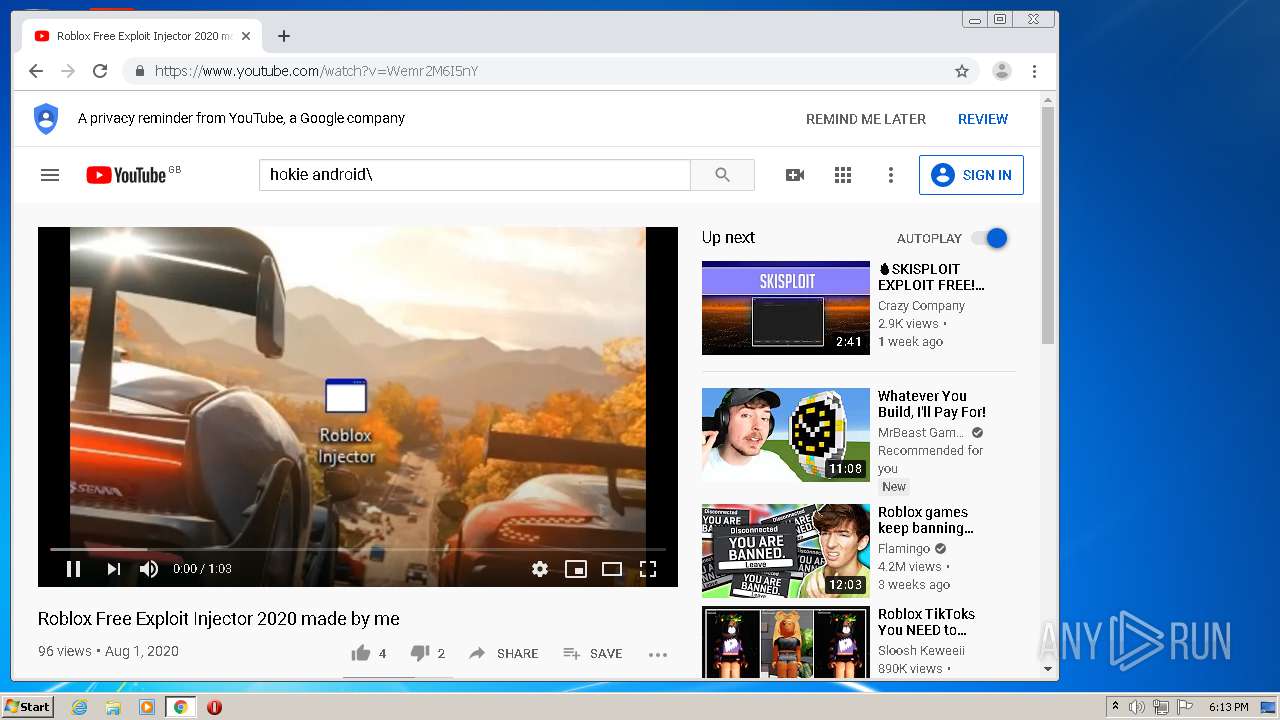
| FileDescription: | Savio Exploit |
| FileVersion: | 1.0.0.0 |
| InternalName: | Savio Exploit.exe |
| LegalCopyright: | Copyright © 2020 |
| LegalTrademarks: | - |
| OriginalFileName: | Savio Exploit.exe |
| ProductName: | Savio AIM |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 10-May-2020 05:24:51 |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | Savio Exploit |
| FileVersion: | 1.0.0.0 |
| InternalName: | Savio Exploit.exe |
| LegalCopyright: | Copyright © 2020 |
| LegalTrademarks: | - |
| OriginalFilename: | Savio Exploit.exe |
| ProductName: | Savio AIM |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 10-May-2020 05:24:51 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x0000B0D4 | 0x0000B200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.62433 |
.rsrc | 0x0000E000 | 0x00000868 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.12353 |
.reloc | 0x00010000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.0776332 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.22615 | 1171 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
Imports
mscoree.dll |
Total processes
71
Monitored processes
28
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,10181984481314244801,2278853538655064322,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3811949009595581952 --mojo-platform-channel-handle=2888 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 608 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=988,10181984481314244801,2278853538655064322,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=6637548972868168633 --mojo-platform-channel-handle=1000 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 924 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,10181984481314244801,2278853538655064322,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=2299995249026313067 --mojo-platform-channel-handle=3944 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1064 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,10181984481314244801,2278853538655064322,131072 --enable-features=PasswordImport --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=671984490854480516 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2236 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1496 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,10181984481314244801,2278853538655064322,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=5368469539509418858 --mojo-platform-channel-handle=1548 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1764 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,10181984481314244801,2278853538655064322,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=6453609132361950031 --mojo-platform-channel-handle=2768 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
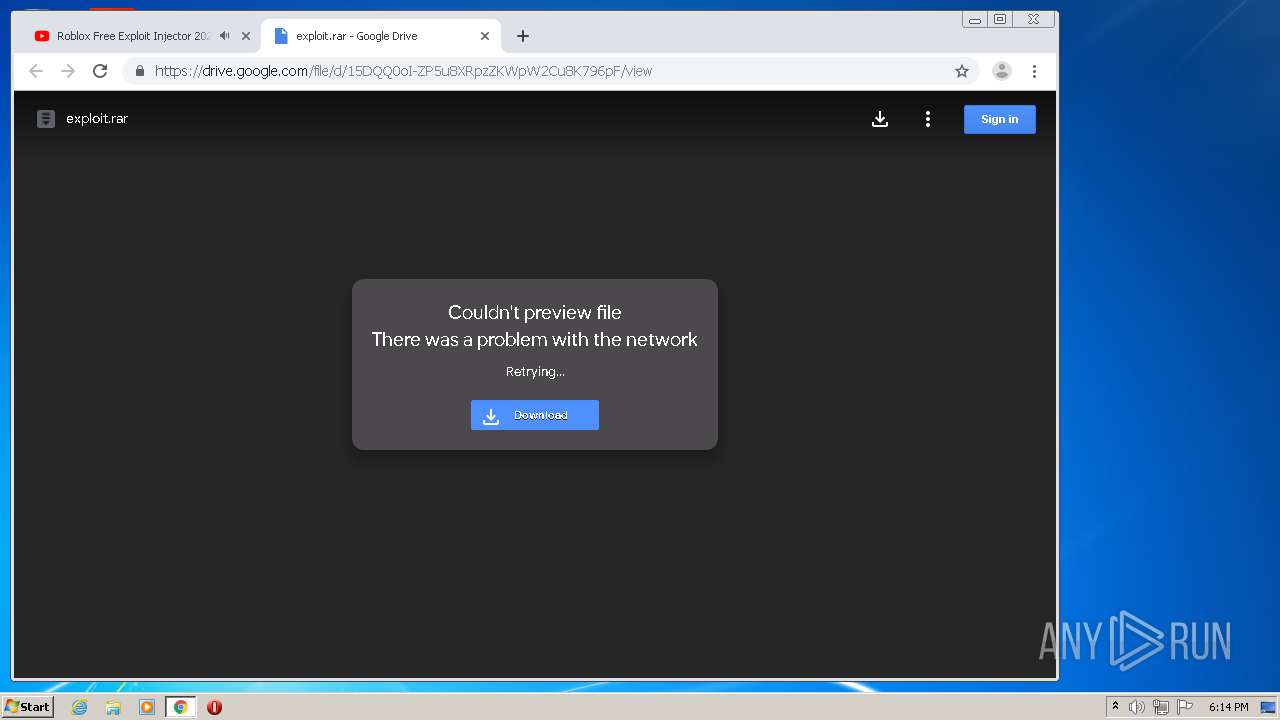
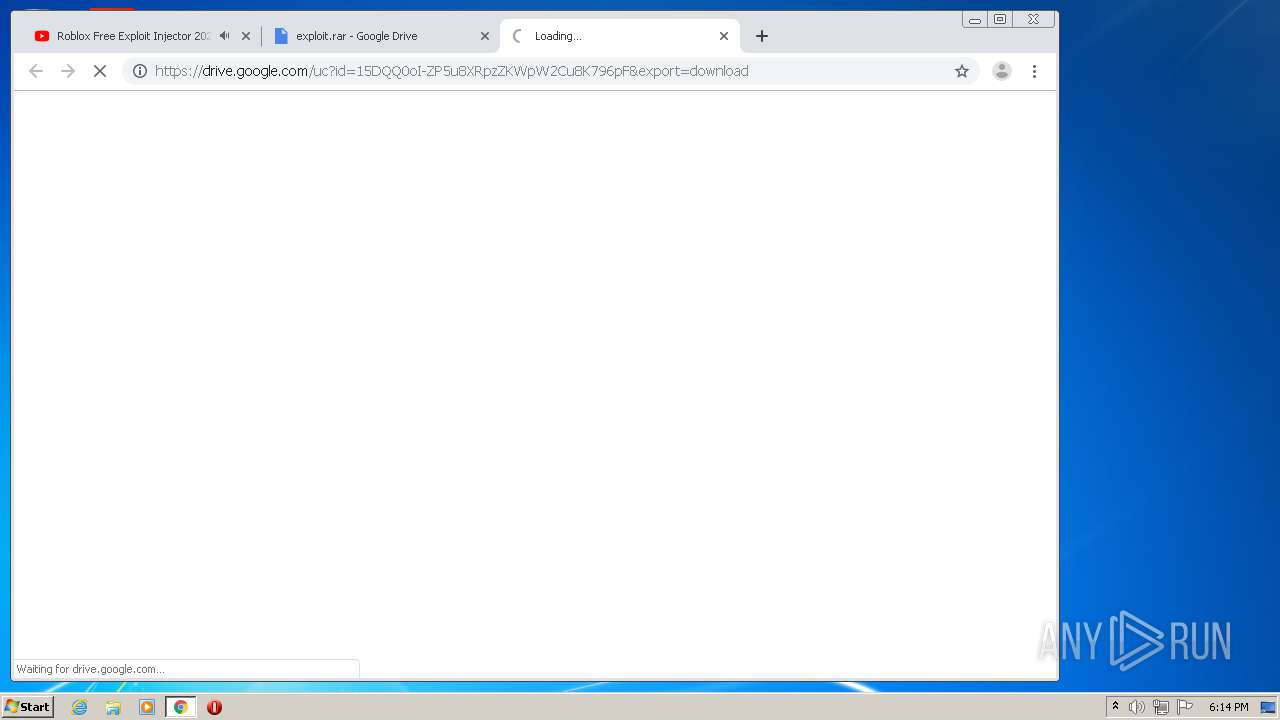
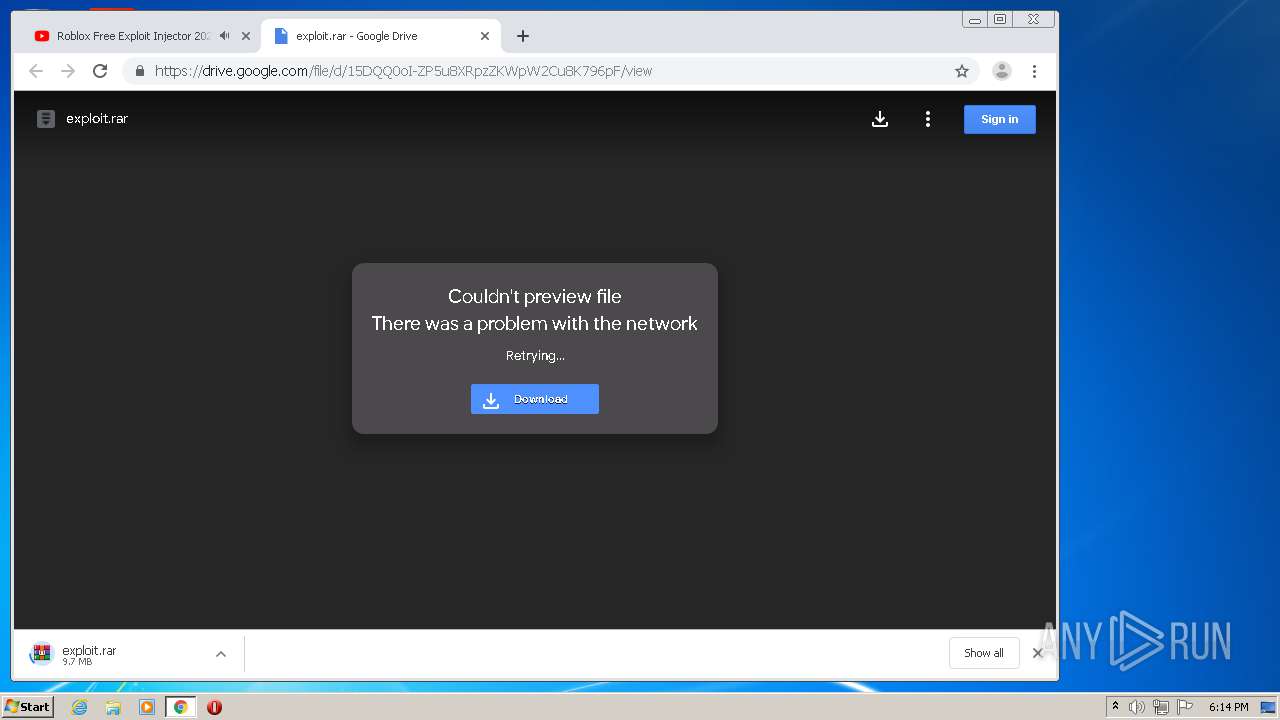
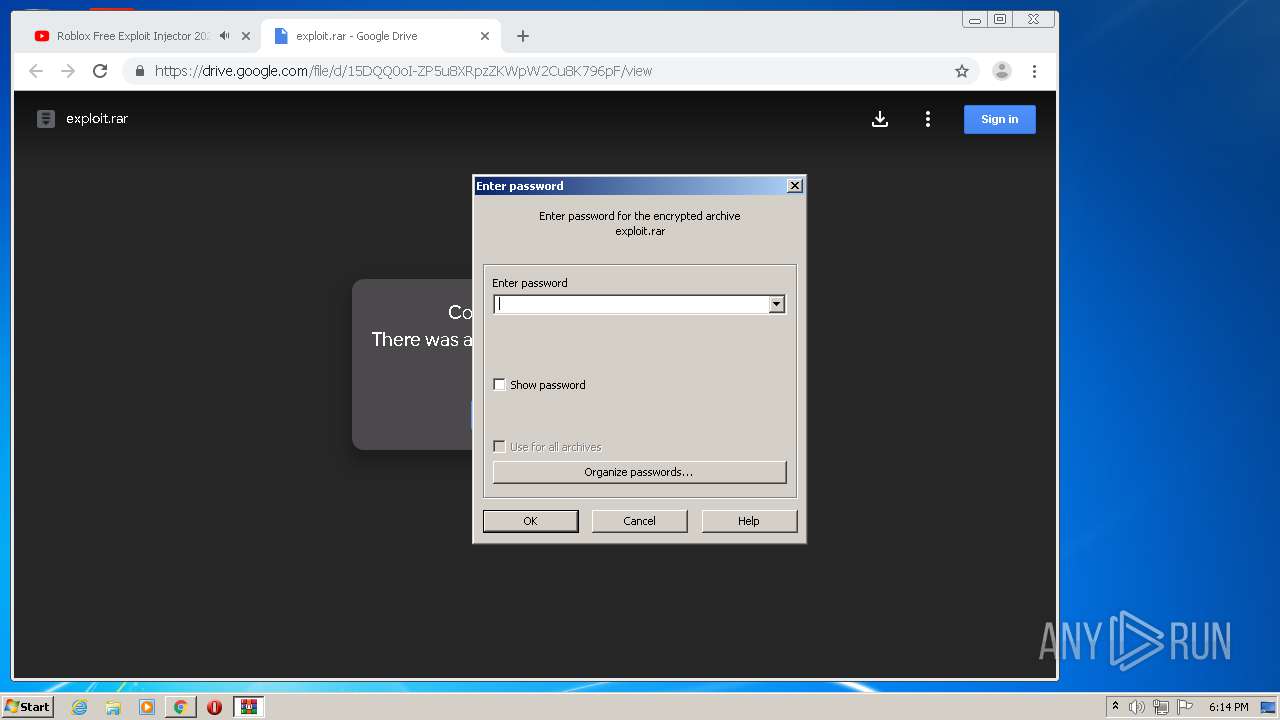
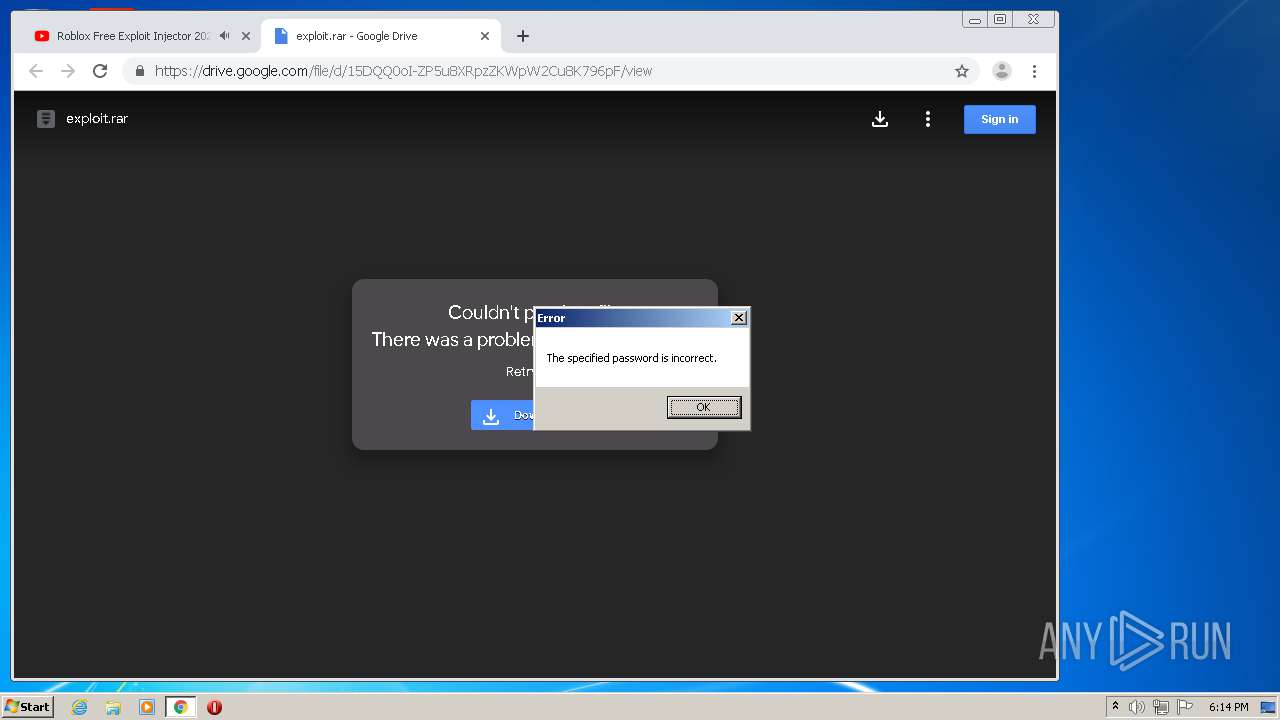
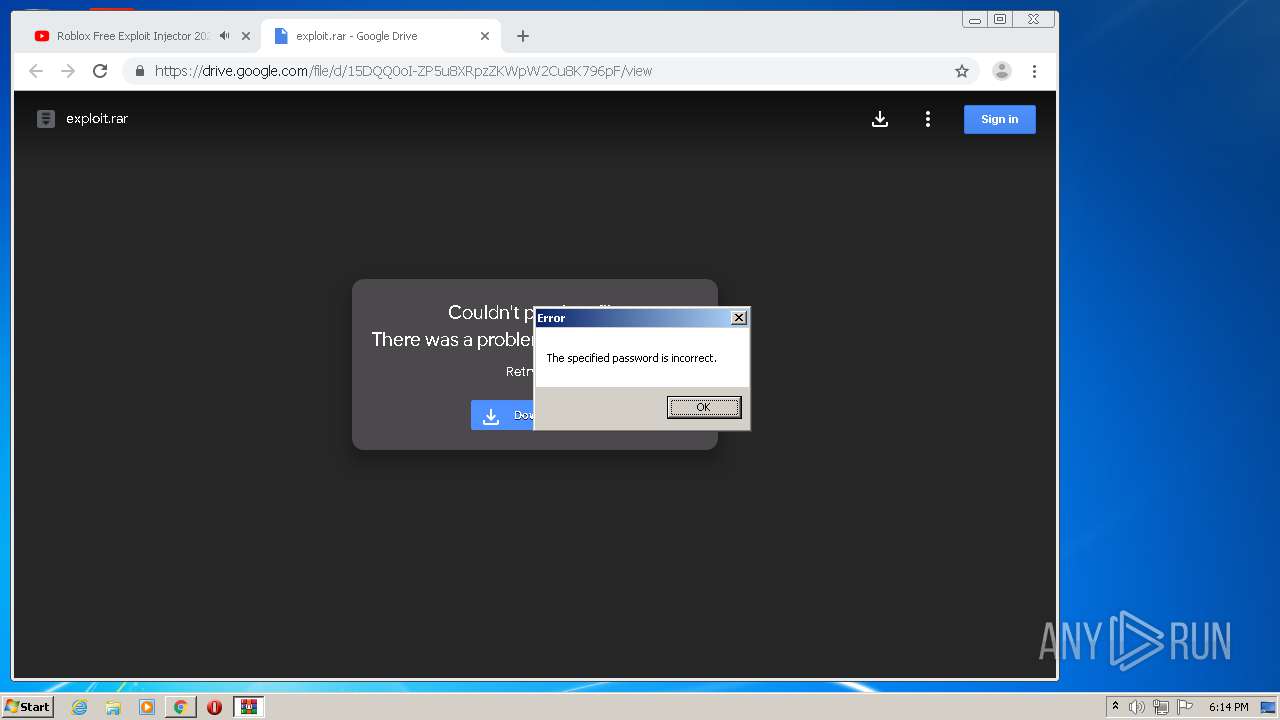
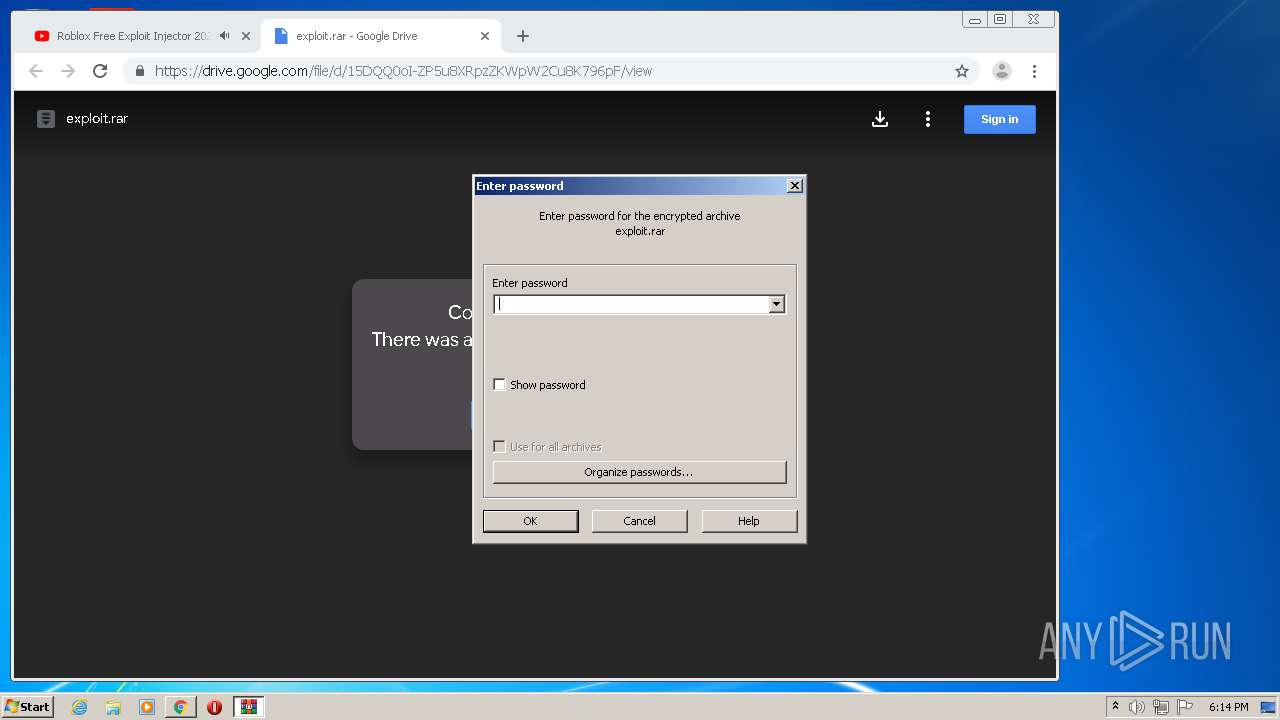
| 2084 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\exploit.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | chrome.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2148 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2244 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,10181984481314244801,2278853538655064322,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11772215853891273720 --mojo-platform-channel-handle=3296 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2384 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,10181984481314244801,2278853538655064322,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5209687540039555773 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2936 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 554
Read events
1 426
Write events
123
Delete events
5
Modification events
| (PID) Process: | (2932) AsyncClient.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\137\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2932) AsyncClient.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\137\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\p2pcollab.dll,-8042 |
Value: Peer to Peer Trust | |||
| (PID) Process: | (2932) AsyncClient.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\137\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\qagentrt.dll,-10 |
Value: System Health Authentication | |||
| (PID) Process: | (2932) AsyncClient.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\137\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dnsapi.dll,-103 |
Value: Domain Name System (DNS) Server Trust | |||
| (PID) Process: | (2932) AsyncClient.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\137\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\fveui.dll,-843 |
Value: BitLocker Drive Encryption | |||
| (PID) Process: | (2932) AsyncClient.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\137\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\fveui.dll,-844 |
Value: BitLocker Data Recovery Agent | |||
| (PID) Process: | (2616) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2148-13241380382327328 |
Value: 259 | |||
| (PID) Process: | (2148) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2148) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2148) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
Executable files
0
Suspicious files
153
Text files
138
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2932 | AsyncClient.exe | C:\Users\admin\AppData\Local\Temp\Cab9C66.tmp | — | |
MD5:— | SHA256:— | |||
| 2932 | AsyncClient.exe | C:\Users\admin\AppData\Local\Temp\Tar9C67.tmp | — | |
MD5:— | SHA256:— | |||
| 2932 | AsyncClient.exe | C:\Users\admin\AppData\Local\Temp\Cab9C77.tmp | — | |
MD5:— | SHA256:— | |||
| 2932 | AsyncClient.exe | C:\Users\admin\AppData\Local\Temp\Tar9C78.tmp | — | |
MD5:— | SHA256:— | |||
| 2932 | AsyncClient.exe | C:\Users\admin\AppData\Local\Temp\Cab9D44.tmp | — | |
MD5:— | SHA256:— | |||
| 2932 | AsyncClient.exe | C:\Users\admin\AppData\Local\Temp\Tar9D55.tmp | — | |
MD5:— | SHA256:— | |||
| 2932 | AsyncClient.exe | C:\Users\admin\AppData\Local\Temp\Cab9DF2.tmp | — | |
MD5:— | SHA256:— | |||
| 2932 | AsyncClient.exe | C:\Users\admin\AppData\Local\Temp\Tar9DF3.tmp | — | |
MD5:— | SHA256:— | |||
| 2932 | AsyncClient.exe | C:\Users\admin\AppData\Local\Temp\Cab9E42.tmp | — | |
MD5:— | SHA256:— | |||
| 2932 | AsyncClient.exe | C:\Users\admin\AppData\Local\Temp\Tar9E43.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
371
DNS requests
54
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2932 | AsyncClient.exe | GET | 304 | 2.16.186.81:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | compressed | 56.7 Kb | whitelisted |
2932 | AsyncClient.exe | GET | 304 | 2.16.186.81:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | compressed | 56.7 Kb | whitelisted |
2932 | AsyncClient.exe | GET | 200 | 2.16.186.81:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | compressed | 56.7 Kb | whitelisted |
2932 | AsyncClient.exe | GET | 304 | 2.16.186.81:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | compressed | 56.7 Kb | whitelisted |
2932 | AsyncClient.exe | GET | 304 | 2.16.186.81:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | compressed | 56.7 Kb | whitelisted |
2932 | AsyncClient.exe | GET | 304 | 2.16.186.81:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | compressed | 56.7 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2932 | AsyncClient.exe | 10.9.154.134:2119 | — | — | — | unknown |
2932 | AsyncClient.exe | 10.9.154.134:7777 | — | — | — | unknown |
2932 | AsyncClient.exe | 2.16.186.81:80 | www.download.windowsupdate.com | Akamai International B.V. | — | whitelisted |
1496 | chrome.exe | 172.217.18.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1496 | chrome.exe | 216.58.212.131:443 | www.gstatic.com | Google Inc. | US | whitelisted |
1496 | chrome.exe | 216.58.212.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2932 | AsyncClient.exe | 193.161.193.99:7777 | HKAndro-60817.portmap.host | OOO Bitree Networks | RU | malicious |
1496 | chrome.exe | 216.58.212.168:443 | ssl.google-analytics.com | Google Inc. | US | whitelisted |
1496 | chrome.exe | 172.217.22.97:443 | lh3.googleusercontent.com | Google Inc. | US | whitelisted |
1496 | chrome.exe | 216.58.207.42:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
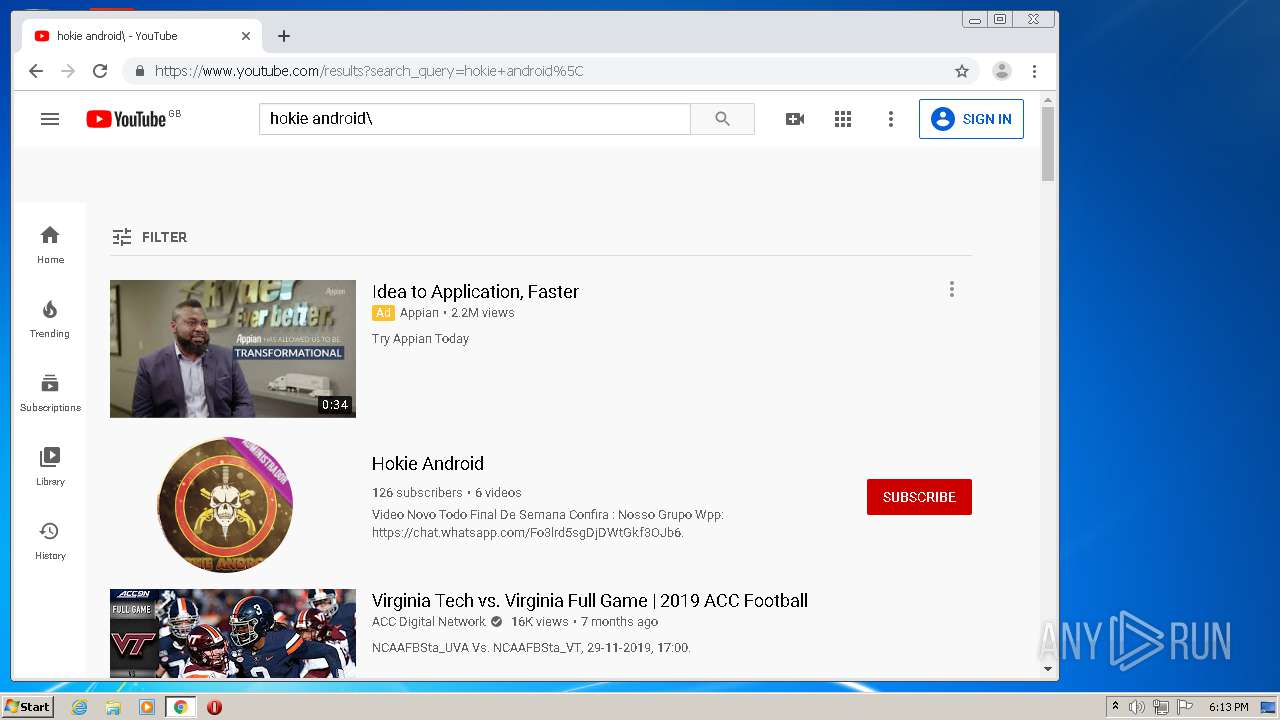
HKAndro-60817.portmap.host |
| malicious |
www.download.windowsupdate.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
clients2.google.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1048 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query to a Reverse Proxy Service Observed |
2932 | AsyncClient.exe | A Network Trojan was detected | MALWARE [PTsecurity] AsyncRAT |
2932 | AsyncClient.exe | A Network Trojan was detected | MALWARE [PTsecurity] AsyncRAT |
1 ETPRO signatures available at the full report