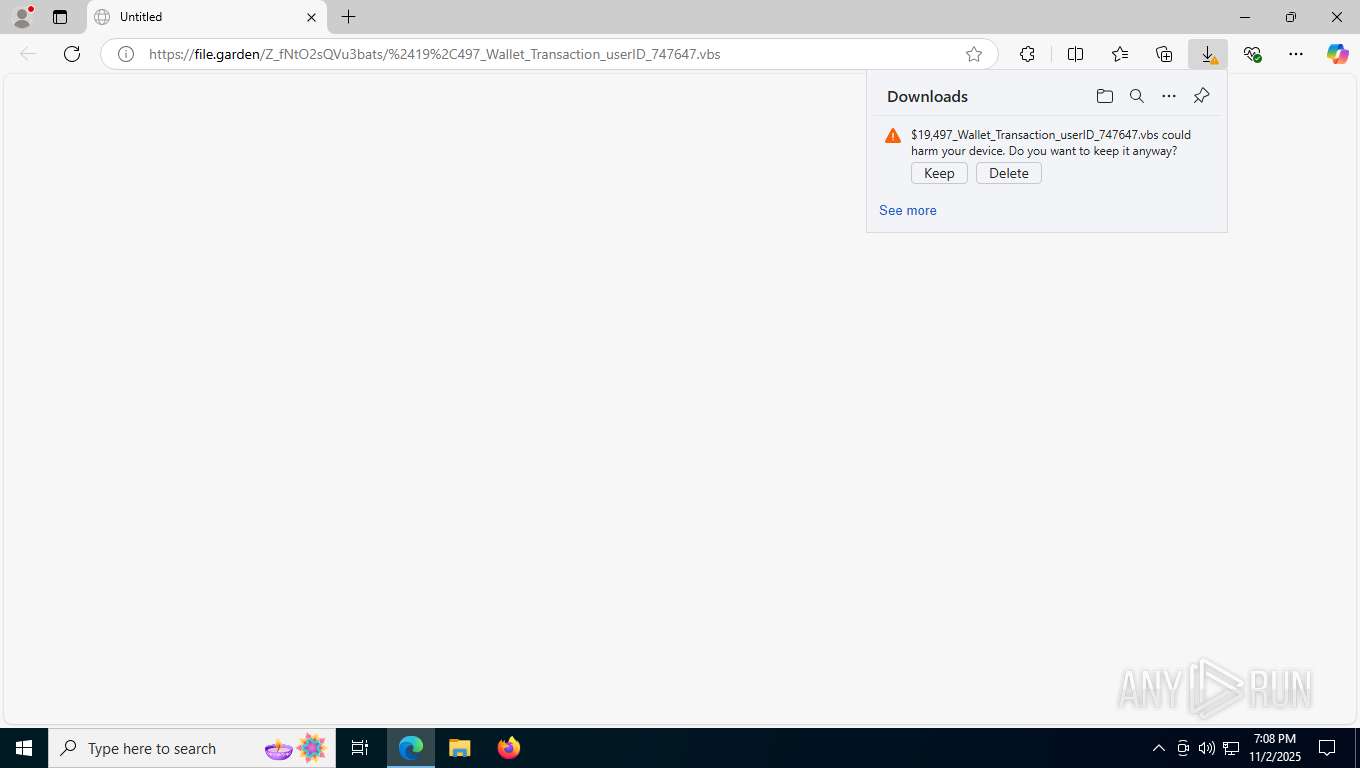
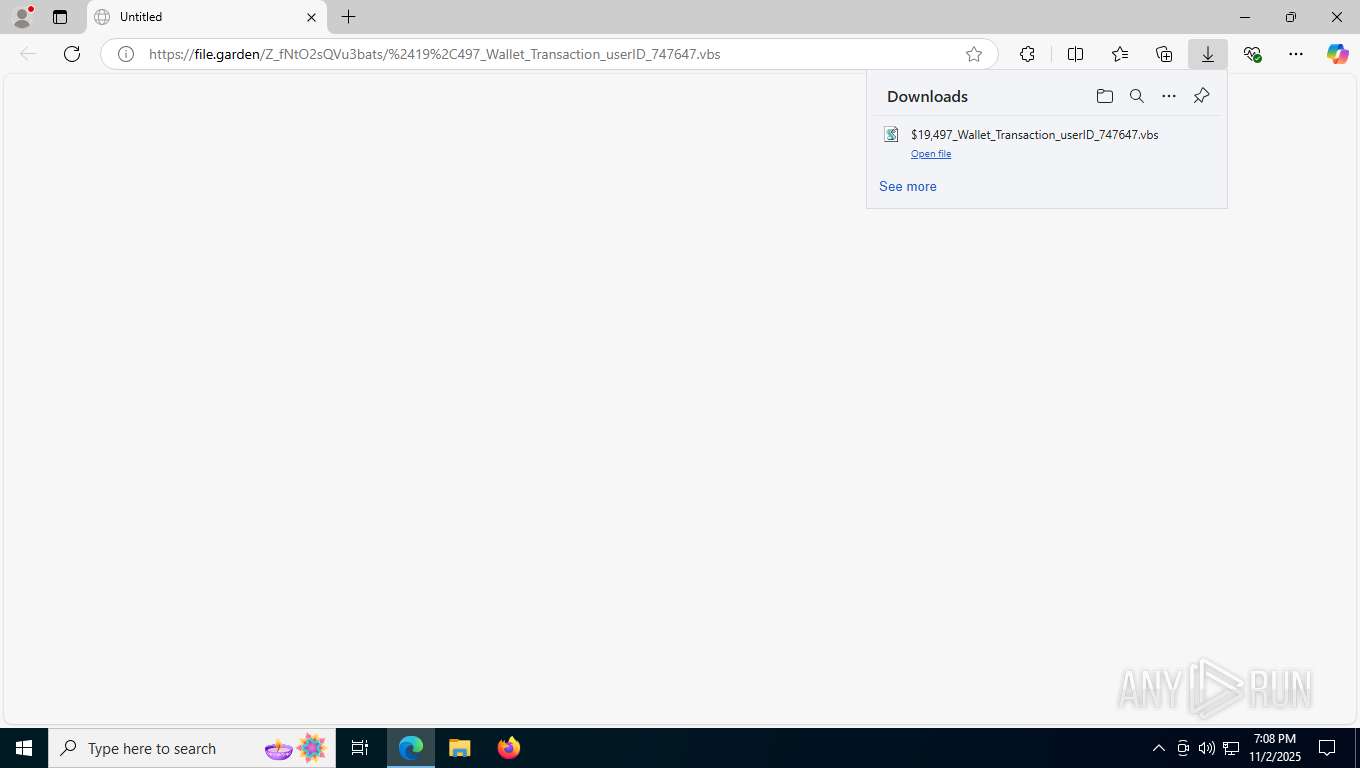
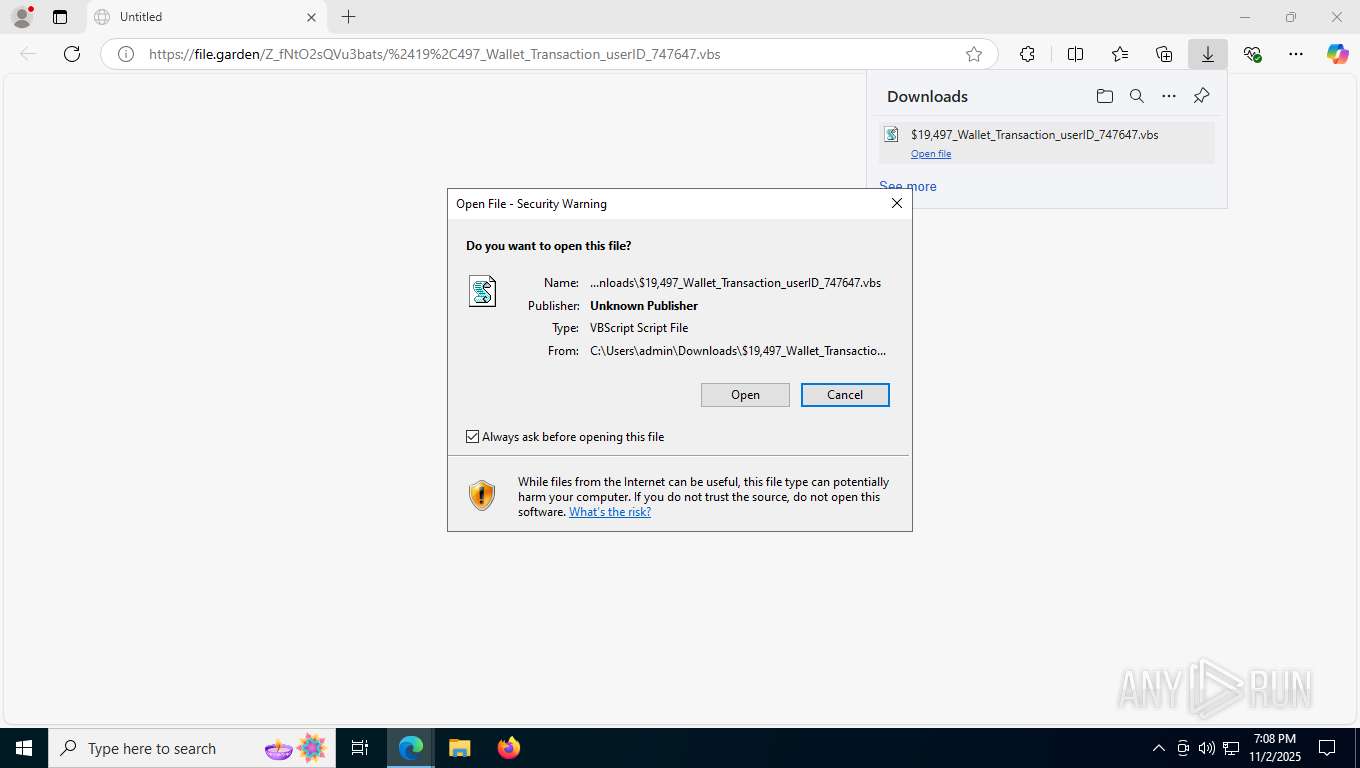
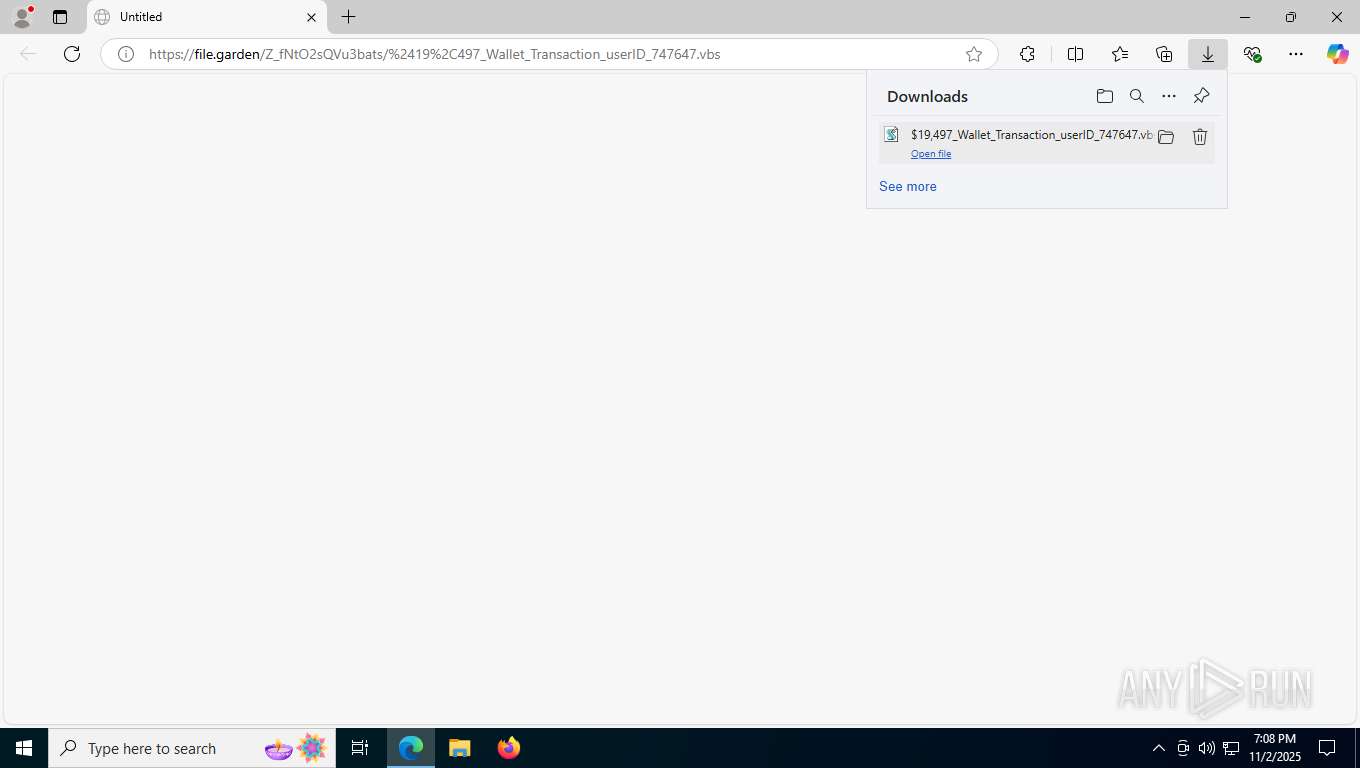
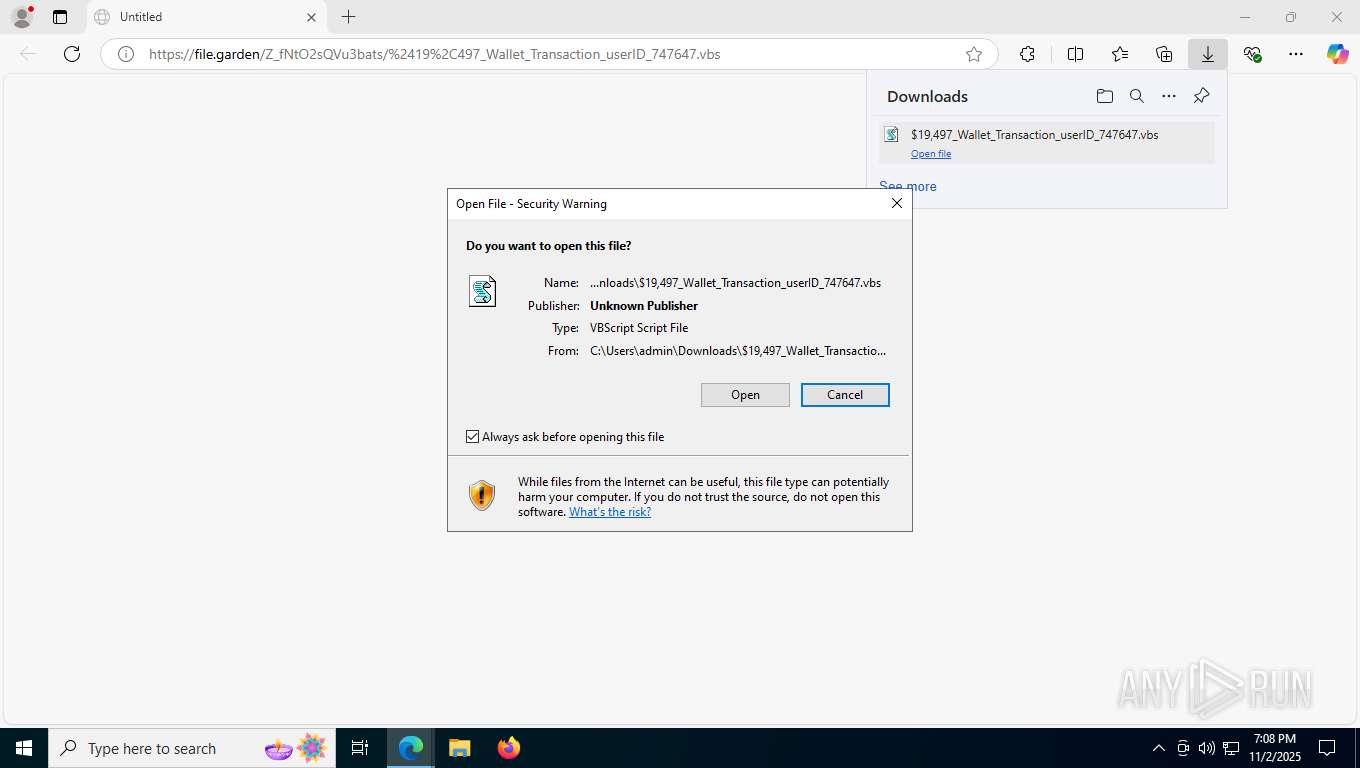
| URL: | https://file.garden/Z_fNtO2sQVu3bats/%2419%2C497_Wallet_Transaction_userID_747647.vbs |
| Full analysis: | https://app.any.run/tasks/080e7b70-70e4-4993-bd65-27f1226d1f07 |
| Verdict: | Malicious activity |
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
| Analysis date: | November 02, 2025, 19:08:10 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 70DD58B9A300F9C625D11B034D8864DE |
| SHA1: | B761E1D89B6AA8BB55D99BB1F733E5E2AC15CCDC |
| SHA256: | 2034288A25327F387535F788E10A4356E6AAC41E38E9872A28E3C34204BB7F6A |
| SSDEEP: | 3:N8VForMjzQyBF48naXELaMKOcXA6WLi:2YQjzQ4FjLayFTLi |
MALICIOUS
Gets TEMP folder path (SCRIPT)
- wscript.exe (PID: 8944)
- wscript.exe (PID: 2184)
Accesses environment variables (SCRIPT)
- wscript.exe (PID: 8944)
- wscript.exe (PID: 2184)
Uses base64 encoding (SCRIPT)
- wscript.exe (PID: 8944)
- wscript.exe (PID: 2184)
Detects the decoding of a binary file from Base64 (SCRIPT)
- wscript.exe (PID: 8944)
- wscript.exe (PID: 2184)
XMRig has been detected
- out.exe (PID: 800)
- WinTemp-v4.exe (PID: 7308)
- out.exe (PID: 8900)
Adds process to the Windows Defender exclusion list
- WinTemp-v4.exe (PID: 7308)
Known privilege escalation attack
- dllhost.exe (PID: 7248)
Changes Windows Defender settings
- WinTemp-v4.exe (PID: 7308)
Changes the autorun value in the registry
- WinTemp-v4.exe (PID: 7308)
Starts REAGENTC.EXE to disable the Windows Recovery Environment
- ReAgentc.exe (PID: 8224)
MINER has been detected (SURICATA)
- cmd.exe (PID: 8448)
Connects to the CnC server
- cmd.exe (PID: 8448)
SUSPICIOUS
The process executes VB scripts
- msedge.exe (PID: 7464)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 8944)
- wscript.exe (PID: 2184)
Creates XML DOM element (SCRIPT)
- wscript.exe (PID: 8944)
- wscript.exe (PID: 2184)
Sets XML DOM element text (SCRIPT)
- wscript.exe (PID: 8944)
- wscript.exe (PID: 2184)
Writes binary data to a Stream object (SCRIPT)
- wscript.exe (PID: 8944)
- wscript.exe (PID: 2184)
Creates a Stream, which may work with files, input/output devices, pipes, or TCP/IP sockets (SCRIPT)
- wscript.exe (PID: 8944)
- wscript.exe (PID: 2184)
Saves data to a binary file (SCRIPT)
- wscript.exe (PID: 8944)
- wscript.exe (PID: 2184)
Executable content was dropped or overwritten
- wscript.exe (PID: 8944)
- out.exe (PID: 800)
- WinTemp-v4.exe (PID: 7308)
Runs shell command (SCRIPT)
- wscript.exe (PID: 8944)
- wscript.exe (PID: 2184)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 8944)
- WinTemp-v4.exe (PID: 7308)
- wscript.exe (PID: 2184)
The executable file from the user directory is run by the CMD process
- out.exe (PID: 800)
- out.exe (PID: 8900)
Starts POWERSHELL.EXE for commands execution
- WinTemp-v4.exe (PID: 7308)
Script adds exclusion process to Windows Defender
- WinTemp-v4.exe (PID: 7308)
Script adds exclusion path to Windows Defender
- WinTemp-v4.exe (PID: 7308)
Uses ICACLS.EXE to modify access control lists
- cmd.exe (PID: 8972)
- cmd.exe (PID: 6420)
Takes ownership (TAKEOWN.EXE)
- cmd.exe (PID: 9208)
Uses powercfg.exe to modify the power settings
- WinTemp-v4.exe (PID: 7308)
Hides command output
- cmd.exe (PID: 8848)
Reads security settings of Internet Explorer
- WinTemp-v4.exe (PID: 7308)
Checks for external IP
- WinTemp-v4.exe (PID: 7308)
Potential Corporate Privacy Violation
- cmd.exe (PID: 8448)
Connects to unusual port
- cmd.exe (PID: 8448)
- WinTemp-v4.exe (PID: 7308)
INFO
Application launched itself
- msedge.exe (PID: 7464)
Launching a file from the Downloads directory
- msedge.exe (PID: 7464)
Create files in a temporary directory
- out.exe (PID: 800)
- WinTemp-v4.exe (PID: 7308)
Checks supported languages
- out.exe (PID: 800)
- WinTemp-v4.exe (PID: 7308)
- out.exe (PID: 8900)
Reads security settings of Internet Explorer
- dllhost.exe (PID: 7248)
Reads the machine GUID from the registry
- out.exe (PID: 800)
- WinTemp-v4.exe (PID: 7308)
Reads the computer name
- out.exe (PID: 800)
- WinTemp-v4.exe (PID: 7308)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7264)
- powershell.exe (PID: 8844)
- powershell.exe (PID: 9028)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7264)
- powershell.exe (PID: 8844)
- powershell.exe (PID: 9028)
Checks transactions between databases Windows and Oracle
- out.exe (PID: 800)
Uses Task Scheduler to autorun other applications (AUTOMATE)
- WinTemp-v4.exe (PID: 7308)
Launching a file from a Registry key
- WinTemp-v4.exe (PID: 7308)
Creates files or folders in the user directory
- WinTemp-v4.exe (PID: 7308)
Checks proxy server information
- WinTemp-v4.exe (PID: 7308)
Reads the software policy settings
- WinTemp-v4.exe (PID: 7308)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
218
Monitored processes
70
Malicious processes
8
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 224 | powercfg /change standby-timeout-ac 0 | C:\Windows\System32\powercfg.exe | — | WinTemp-v4.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Power Settings Command-Line Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 680 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=1452,i,8857775693644629539,11401651993889457012,262144 --variations-seed-version --mojo-platform-channel-handle=6060 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 752 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=1420,i,8857775693644629539,11401651993889457012,262144 --variations-seed-version --mojo-platform-channel-handle=6576 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 800 | C:\Users\admin\AppData\Local\Temp\out.exe | C:\Users\admin\AppData\Local\Temp\out.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1552 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1664 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1844 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2184 | "C:\WINDOWS\System32\WScript.exe" "C:\Users\admin\Downloads\$19,497_Wallet_Transaction_userID_747647.vbs" | C:\Windows\System32\wscript.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 2544 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --disable-quic --onnx-enabled-for-ee --string-annotations --always-read-main-dll --field-trial-handle=5176,i,8857775693644629539,11401651993889457012,262144 --variations-seed-version --mojo-platform-channel-handle=5228 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 | |||||||||||||||
| 2580 | powercfg /change monitor-timeout-dc 0 | C:\Windows\System32\powercfg.exe | — | WinTemp-v4.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Power Settings Command-Line Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
21 024
Read events
20 948
Write events
16
Delete events
60
Modification events
| (PID) Process: | (7248) dllhost.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (7308) WinTemp-v4.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | v4 |
Value: C:\Users\admin\AppData\Local\Microsoft\Windows\Explorer\Win-v43.exe | |||
| (PID) Process: | (8224) ReAgentc.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\11000001 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (8224) ReAgentc.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\11000001 |
| Operation: | write | Name: | Element |
Value: 0000000000000000000000000000000006000000000000004800000000000000715E5C2FA985EB1190A89A9B763584210000000000000000745E5C2FA985EB1190A89A9B7635842100000000000000000000000000000000 | |||
| (PID) Process: | (8224) ReAgentc.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\12000002 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (8224) ReAgentc.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\12000002 |
| Operation: | write | Name: | Element |
Value: \EFI\Microsoft\Boot\bootmgfw.efi | |||
| (PID) Process: | (8224) ReAgentc.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{872a075f-9aa9-11f0-b4fb-806e6f6e6963}\Elements\11000001 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (7308) WinTemp-v4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\$SHconfig\startup |
| Operation: | write | Name: | v4 |
Value: C:\Windows\Win-v41.exe | |||
| (PID) Process: | (8224) ReAgentc.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{872a075f-9aa9-11f0-b4fb-806e6f6e6963}\Elements\11000001 |
| Operation: | write | Name: | Element |
Value: 0000000000000000000000000000000006000000000000004800000000000000715E5C2FA985EB1190A89A9B763584210000000000000000745E5C2FA985EB1190A89A9B7635842100000000000000000000000000000000 | |||
| (PID) Process: | (8224) ReAgentc.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{872a075f-9aa9-11f0-b4fb-806e6f6e6963}\Elements\12000002 |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
13
Suspicious files
218
Text files
55
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7464 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1621d5.TMP | — | |
MD5:— | SHA256:— | |||
| 7464 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF1621d5.TMP | — | |
MD5:— | SHA256:— | |||
| 7464 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1621e4.TMP | — | |
MD5:— | SHA256:— | |||
| 7464 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF1621e4.TMP | — | |
MD5:— | SHA256:— | |||
| 7464 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1621d5.TMP | — | |
MD5:— | SHA256:— | |||
| 7464 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7464 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7464 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7464 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7464 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
58
DNS requests
42
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7788 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:v3Mj6DtPEg7KSDglk71l5HYqzibhYWo_fpM2fbhx8FM&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 101 b | whitelisted |
1384 | svchost.exe | GET | 200 | 162.159.142.9:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | binary | 471 b | whitelisted |
5596 | MoUsoCoreWorker.exe | GET | 200 | 23.55.110.211:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
8616 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.3.crl | NL | binary | 813 b | whitelisted |
8616 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | NL | binary | 814 b | whitelisted |
8616 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.3.crl | NL | binary | 401 b | whitelisted |
7308 | WinTemp-v4.exe | GET | 200 | 104.18.20.213:80 | http://r12.c.lencr.org/124.crl | unknown | binary | 170 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1384 | svchost.exe | 20.190.159.71:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2388 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5596 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7788 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7788 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7788 | msedge.exe | 95.101.74.26:443 | copilot.microsoft.com | Akamai International B.V. | NL | whitelisted |
7788 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7788 | msedge.exe | 188.114.97.3:443 | file.garden | CLOUDFLARENET | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
login.live.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
file.garden |
| unknown |
copilot.microsoft.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
www.bing.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
7308 | WinTemp-v4.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 33 |
7308 | WinTemp-v4.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 6 |
2276 | svchost.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
7308 | WinTemp-v4.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |
8448 | cmd.exe | Potential Corporate Privacy Violation | ET INFO Cryptocurrency Miner Checkin |
— | — | Possibly Unwanted Program Detected | ET ADWARE_PUP User-Agent (HTTP) |
— | — | Device Retrieving External IP Address Detected | SUSPICIOUS [ANY.RUN] An IP address was received from the server as a result of an HTTP request |
— | — | Device Retrieving External IP Address Detected | SUSPICIOUS [ANY.RUN] An IP address was received from the server as a result of an HTTP request |
— | — | Device Retrieving External IP Address Detected | SUSPICIOUS [ANY.RUN] An IP address was received from the server as a result of an HTTP request |