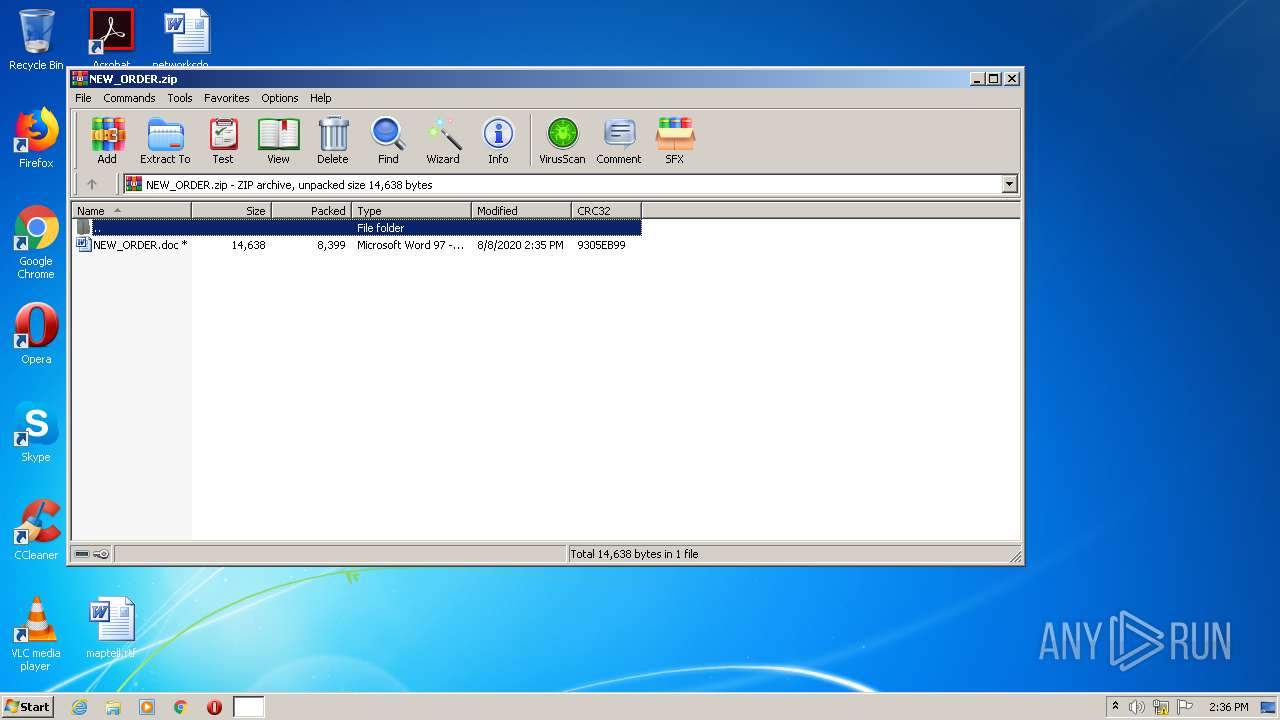
| File name: | NEW_ORDER.zip |
| Full analysis: | https://app.any.run/tasks/ad9108a3-d918-43a9-8ebc-6bbb12dbb95f |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | August 08, 2020, 13:36:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 3A222E89F530A0C89F3E60099D10A9C4 |
| SHA1: | 92BD2B8EA98CCC5AB616E660963E0E4C8400CA59 |
| SHA256: | 20286DCA7A649BFC31E5F48CFB112B22675E7CEB7443E7D5DD86B711C5A450D0 |
| SSDEEP: | 192:+zX7zuHcR/O2gtEG9w3gvJhn4r0yEOmBuHPIeSXlbLZQn/5h:8X7zIi/gV5vr4r0pOguvUVbLZq/5h |
MALICIOUS
Equation Editor starts application (CVE-2017-11882)
- EQNEDT32.EXE (PID: 3212)
Application was dropped or rewritten from another process
- simonyi4536.exe (PID: 868)
- simonyi4536.exe (PID: 2860)
Downloads executable files from the Internet
- EQNEDT32.EXE (PID: 3212)
Changes the autorun value in the registry
- simonyi4536.exe (PID: 2860)
AGENTTESLA was detected
- simonyi4536.exe (PID: 2860)
Actions looks like stealing of personal data
- simonyi4536.exe (PID: 2860)
SUSPICIOUS
Reads Internet Cache Settings
- EQNEDT32.EXE (PID: 3212)
Creates files in the user directory
- EQNEDT32.EXE (PID: 3212)
- simonyi4536.exe (PID: 2860)
Executed via COM
- EQNEDT32.EXE (PID: 3212)
Executable content was dropped or overwritten
- EQNEDT32.EXE (PID: 3212)
- simonyi4536.exe (PID: 2860)
Application launched itself
- simonyi4536.exe (PID: 868)
Reads the cookies of Google Chrome
- simonyi4536.exe (PID: 2860)
Reads the cookies of Mozilla Firefox
- simonyi4536.exe (PID: 2860)
INFO
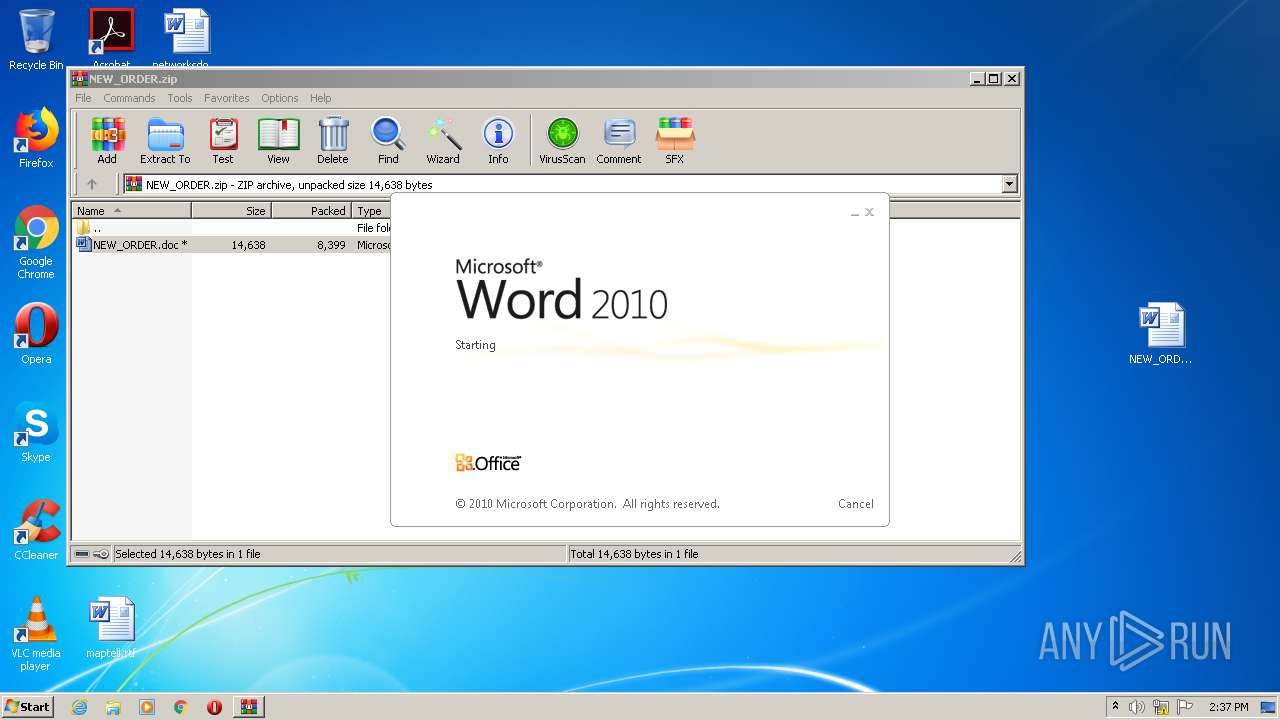
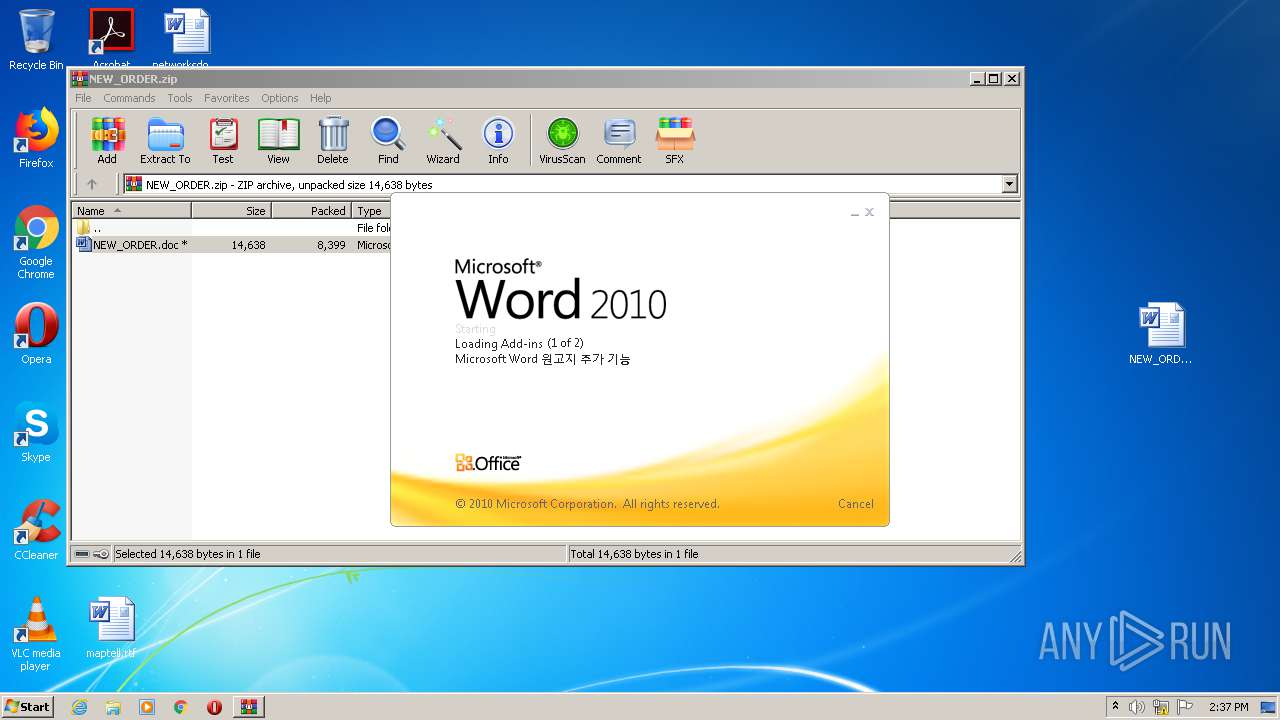
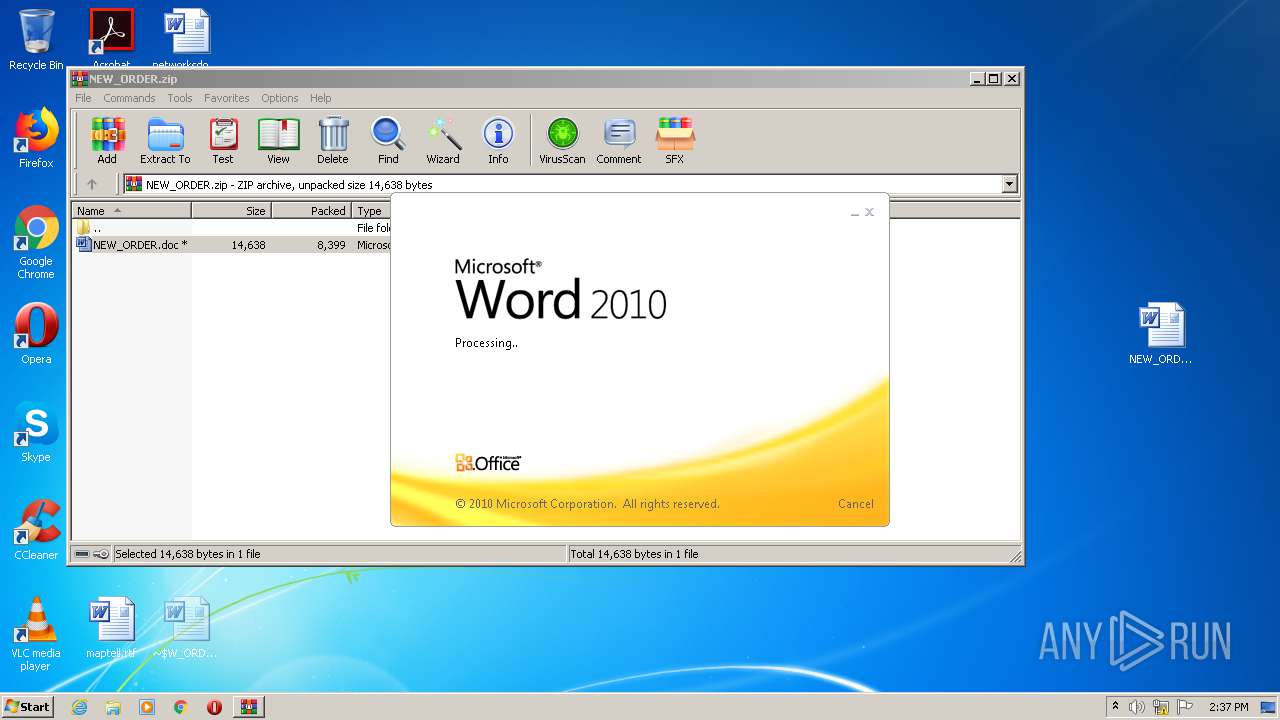
Manual execution by user
- WINWORD.EXE (PID: 2900)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2900)
Creates files in the user directory
- WINWORD.EXE (PID: 2900)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:08:08 22:35:23 |
| ZipCRC: | 0x9305eb99 |
| ZipCompressedSize: | 8399 |
| ZipUncompressedSize: | 14638 |
| ZipFileName: | NEW_ORDER.doc |
Total processes
44
Monitored processes
5
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 868 | "C:\Users\admin\AppData\Roaming\simonyi4536.exe" | C:\Users\admin\AppData\Roaming\simonyi4536.exe | — | EQNEDT32.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Description: 2048 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
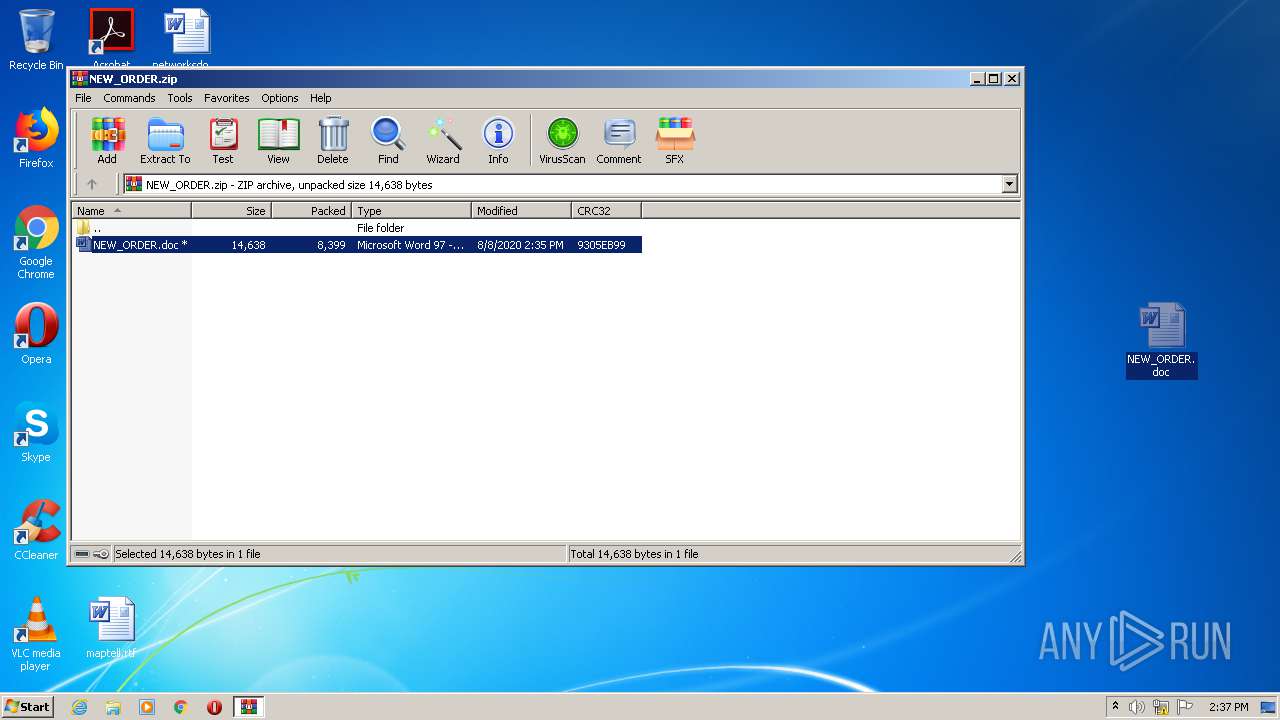
| 2272 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\NEW_ORDER.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2860 | "C:\Users\admin\AppData\Roaming\simonyi4536.exe" | C:\Users\admin\AppData\Roaming\simonyi4536.exe | simonyi4536.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: 2048 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2900 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\NEW_ORDER.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3212 | "C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE" -Embedding | C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE | svchost.exe | ||||||||||||
User: admin Company: Design Science, Inc. Integrity Level: MEDIUM Description: Microsoft Equation Editor Exit code: 0 Version: 00110900 Modules
| |||||||||||||||
Total events
1 916
Read events
1 201
Write events
571
Delete events
144
Modification events
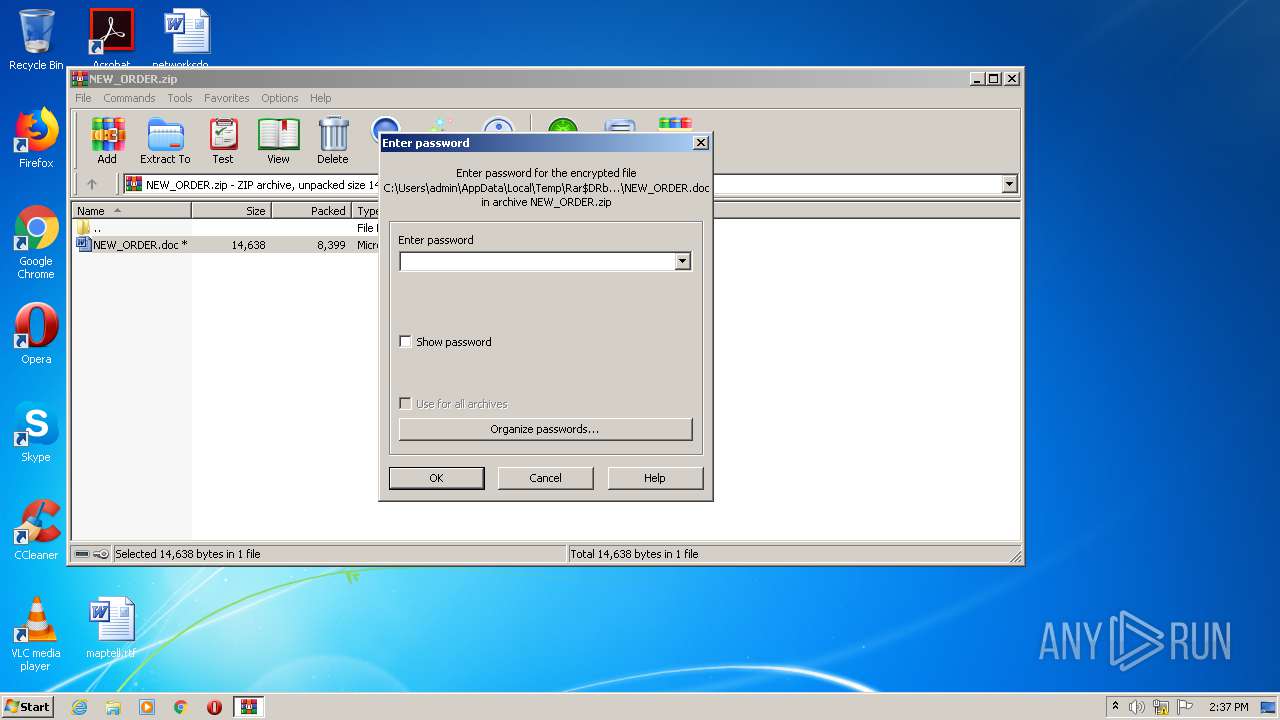
| (PID) Process: | (2272) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2272) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2272) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\137\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2272) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\137\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (2272) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\NEW_ORDER.zip | |||
| (PID) Process: | (2272) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2272) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2272) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2272) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2272) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
3
Suspicious files
0
Text files
2
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2272 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2272.15296\NEW_ORDER.doc | — | |
MD5:— | SHA256:— | |||
| 2900 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR1ECC.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2860 | simonyi4536.exe | C:\Users\admin\AppData\Roaming\mmghsc3w.3ud\Chrome\Default\Cookies | — | |
MD5:— | SHA256:— | |||
| 2860 | simonyi4536.exe | C:\Users\admin\AppData\Roaming\mmghsc3w.3ud\Firefox\Profiles\qldyz51w.default\cookies.sqlite | — | |
MD5:— | SHA256:— | |||
| 2900 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 2900 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3212 | EQNEDT32.EXE | C:\Users\admin\AppData\Roaming\simonyi4536.exe | executable | |
MD5:— | SHA256:— | |||
| 2900 | WINWORD.EXE | C:\Users\admin\Desktop\~$W_ORDER.doc | pgc | |
MD5:— | SHA256:— | |||
| 3212 | EQNEDT32.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\simonxz[1].exe | executable | |
MD5:— | SHA256:— | |||
| 2900 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\NEW_ORDER.doc.LNK | lnk | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
3
DNS requests
2
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3212 | EQNEDT32.EXE | GET | 200 | 194.180.224.87:80 | http://abass.ir/simonxz/simonxz.exe | unknown | executable | 867 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3212 | EQNEDT32.EXE | 194.180.224.87:80 | abass.ir | — | — | malicious |
2860 | simonyi4536.exe | 199.79.63.24:587 | bh-58.webhostbox.net | PDR | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
abass.ir |
| whitelisted |
bh-58.webhostbox.net |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3212 | EQNEDT32.EXE | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2860 | simonyi4536.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
2860 | simonyi4536.exe | A Network Trojan was detected | SPYWARE [PTsecurity] AgentTesla Exfiltration |
2860 | simonyi4536.exe | A Network Trojan was detected | AV TROJAN Win.Keylogger.AgentTesla SMTP Activity |
2860 | simonyi4536.exe | A Network Trojan was detected | SPYWARE [PTsecurity] AgentTesla Exfiltration |
2860 | simonyi4536.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
2860 | simonyi4536.exe | A Network Trojan was detected | SPYWARE [PTsecurity] AgentTesla Exfiltration |
2860 | simonyi4536.exe | A Network Trojan was detected | AV TROJAN Win.Keylogger.AgentTesla SMTP Activity |
2860 | simonyi4536.exe | A Network Trojan was detected | SPYWARE [PTsecurity] AgentTesla Exfiltration |
4 ETPRO signatures available at the full report