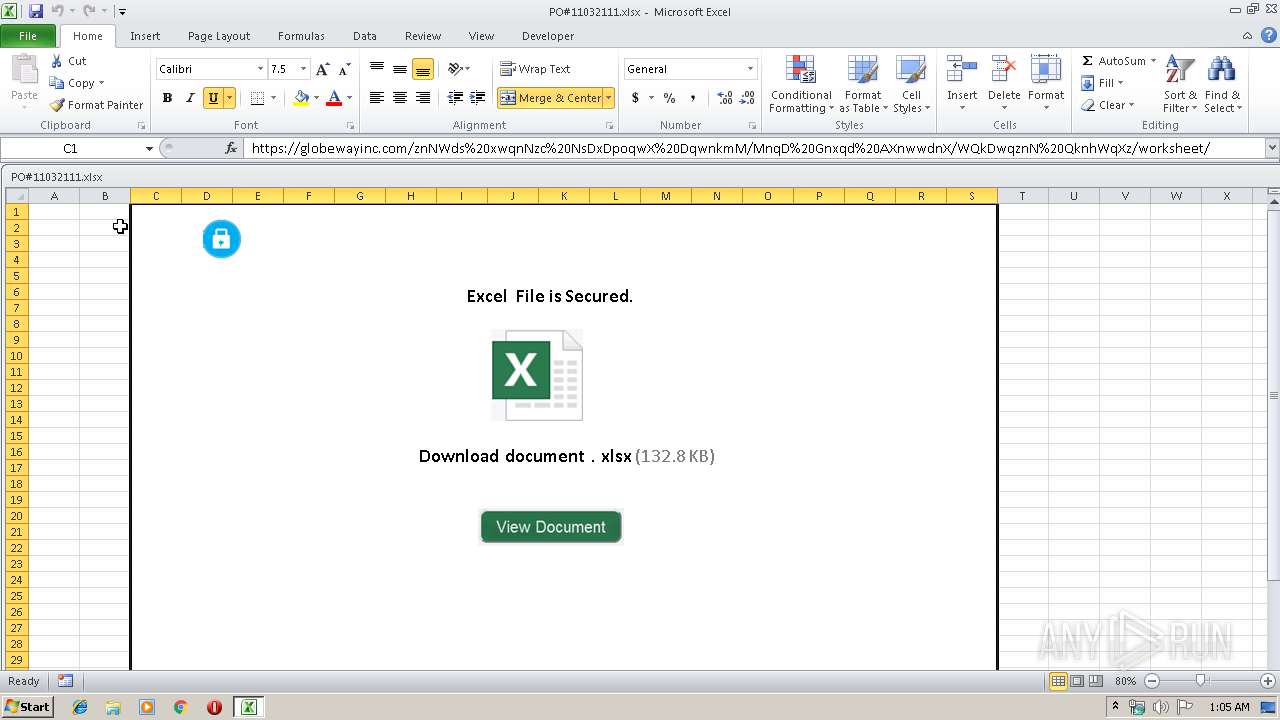
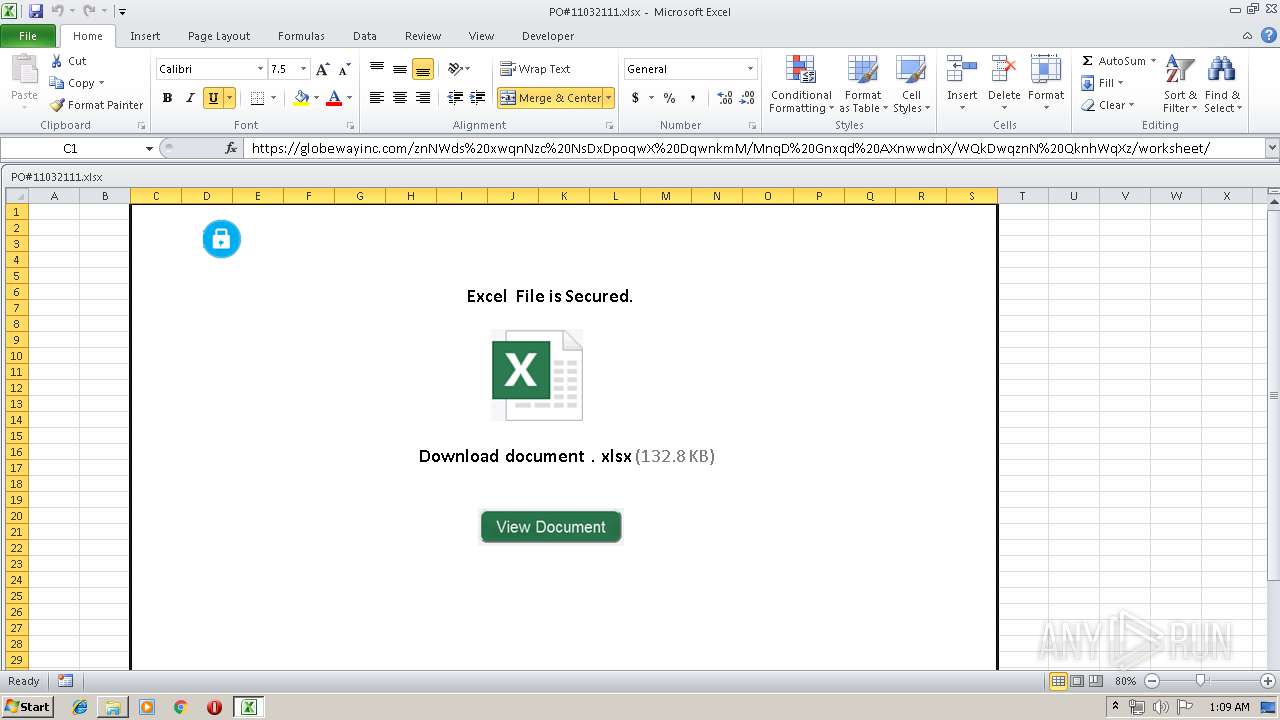
| File name: | PO#11032111.xlsx |
| Full analysis: | https://app.any.run/tasks/a62e5c7f-05d1-42a9-8678-2f79b6c5d5a9 |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | May 24, 2019, 00:05:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.spreadsheetml.sheet |
| File info: | Microsoft Excel 2007+ |
| MD5: | 61D75B4B394E43537A2247BDA730FC80 |
| SHA1: | F06BEE5F3E431CFB55D2815444263729D57F04A1 |
| SHA256: | 1FFBE617F9887BB0F09565A1034B2B031B90F41388922B7E4C3BF879A6533106 |
| SSDEEP: | 384:I45lAxBP+FgpMUF91hDDWhAp0Q+gJkAY2C8c/aIawJ9PpOxPE:h5l8BP+SMo1hDDWhAp0ZgJk0C8cRasPH |
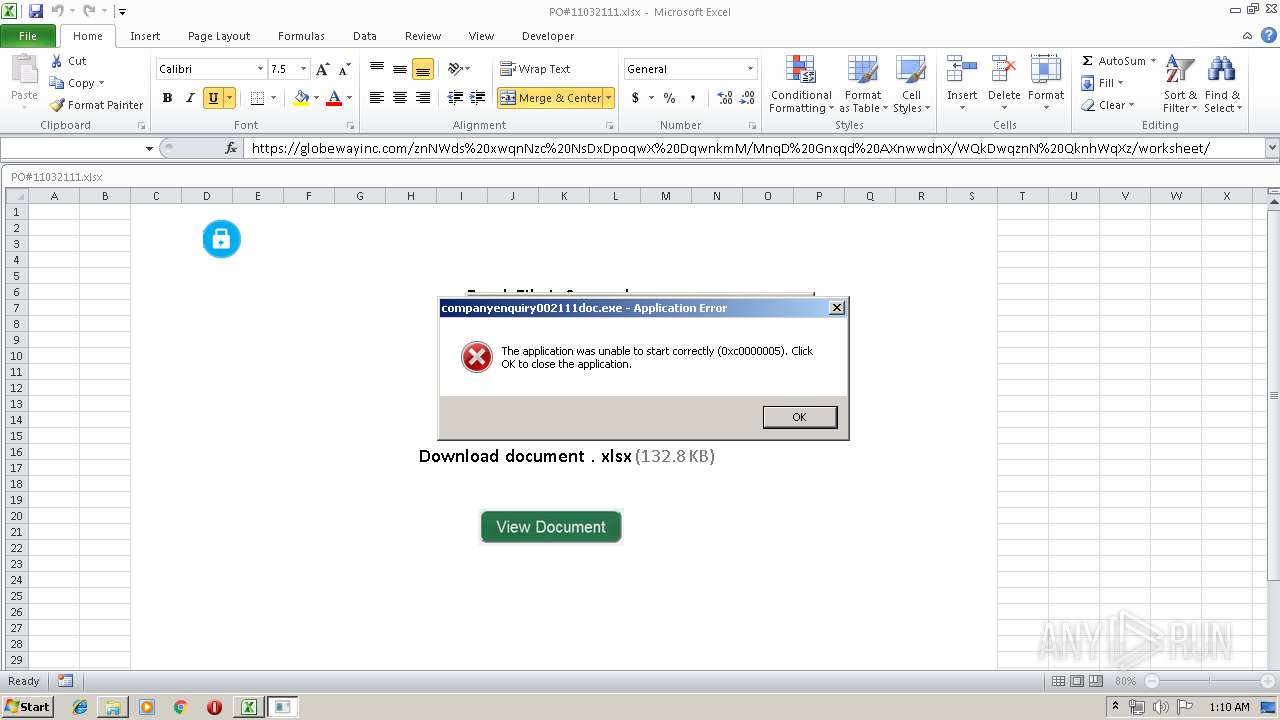
MALICIOUS
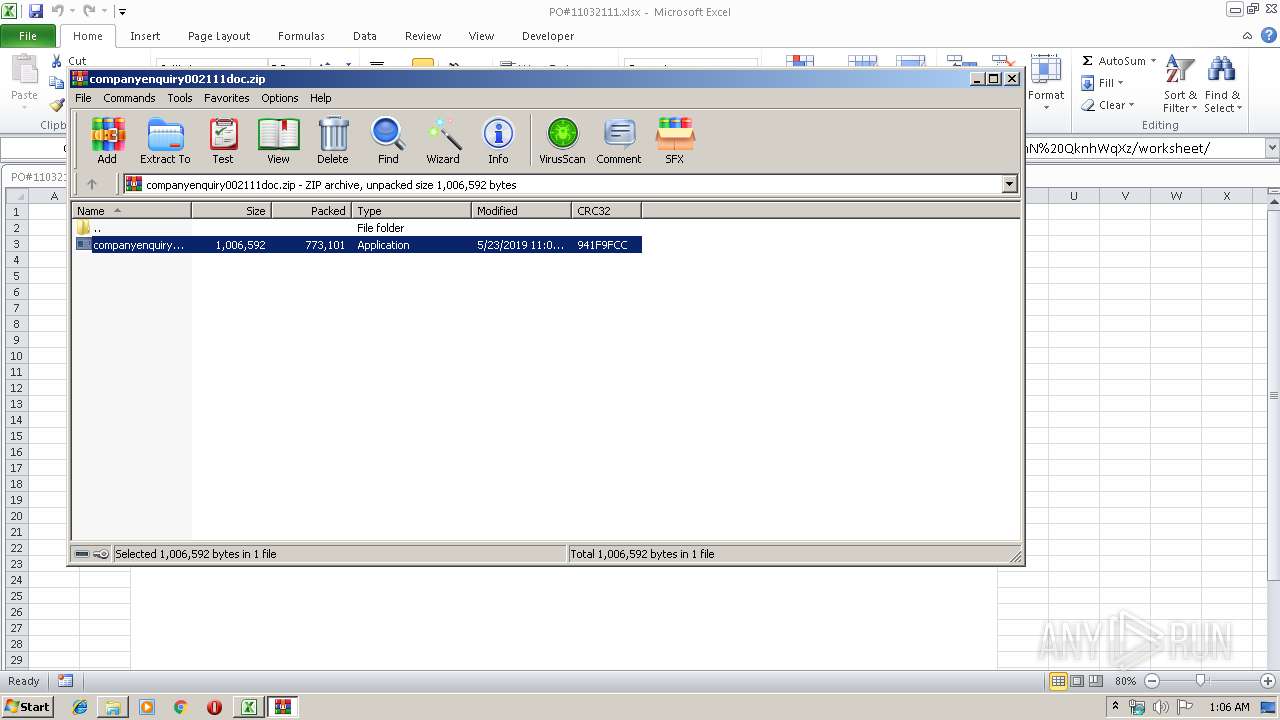
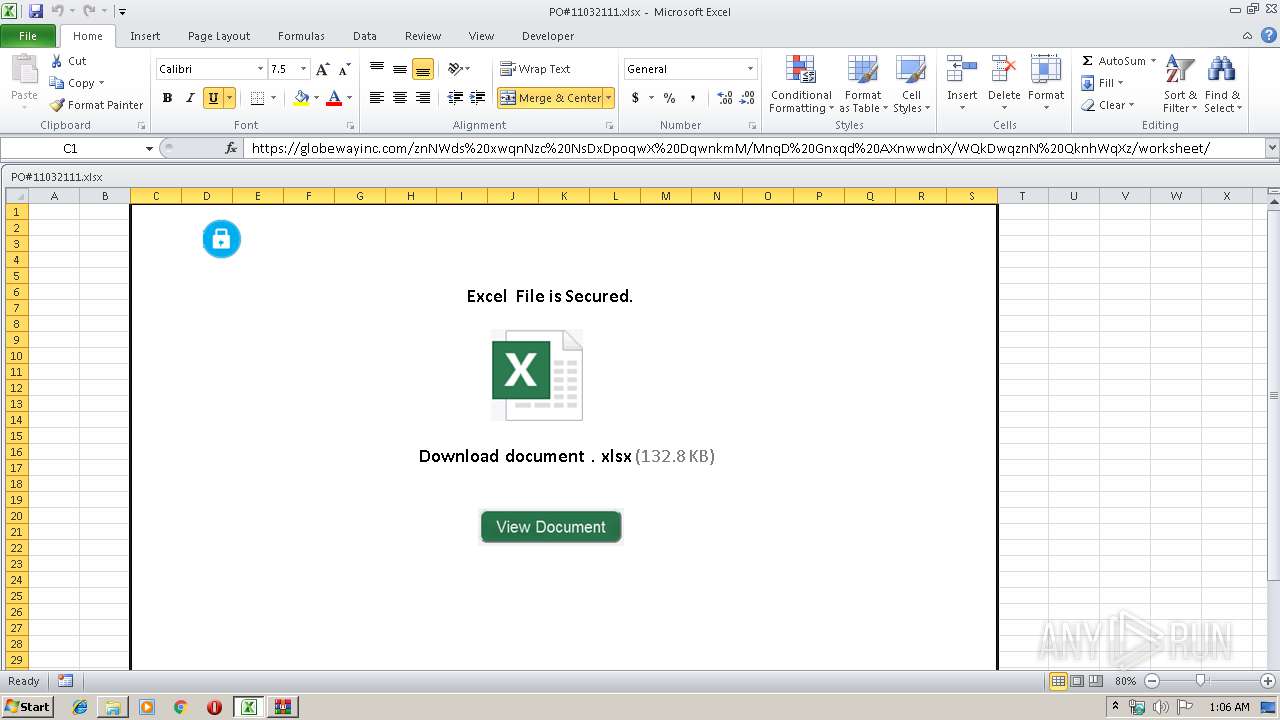
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 2828)
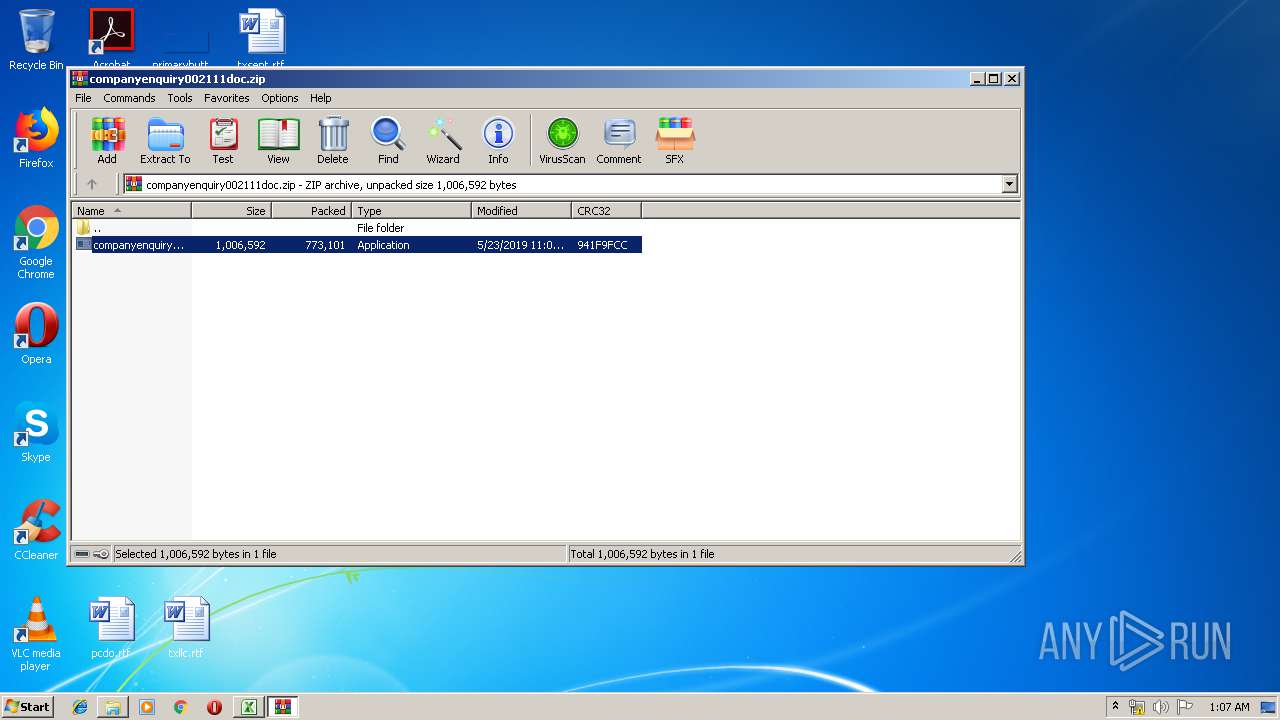
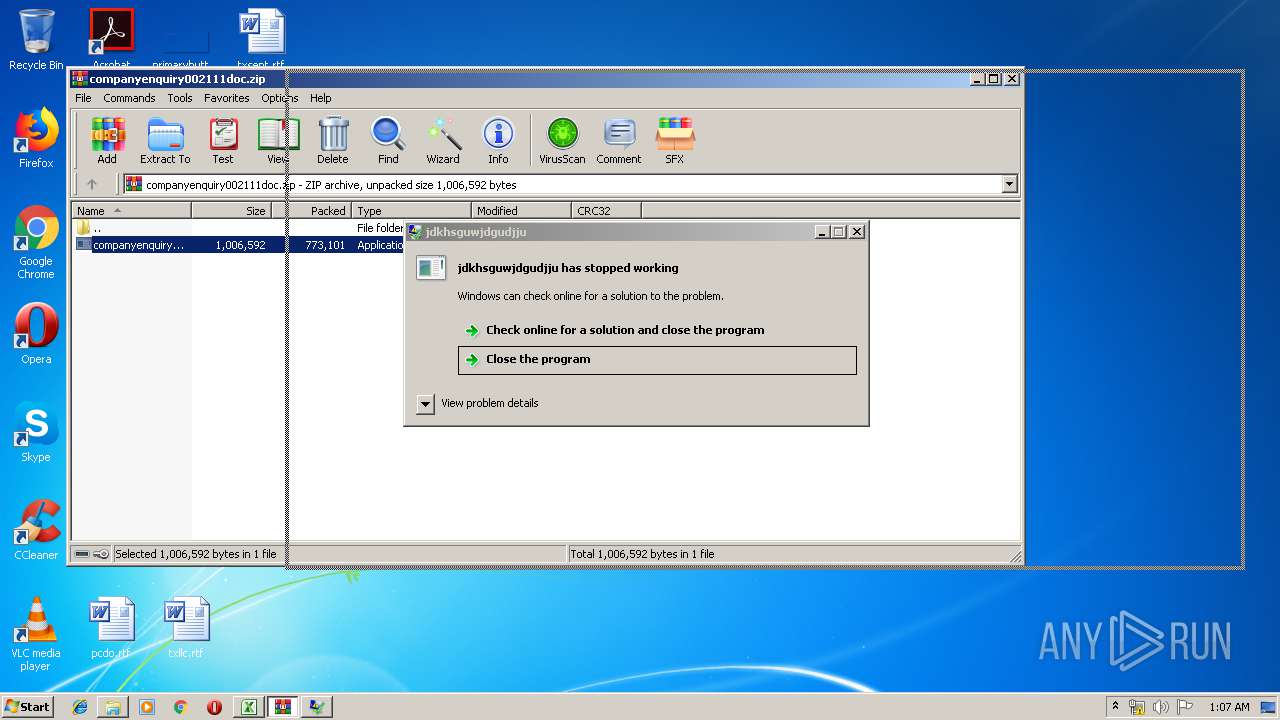
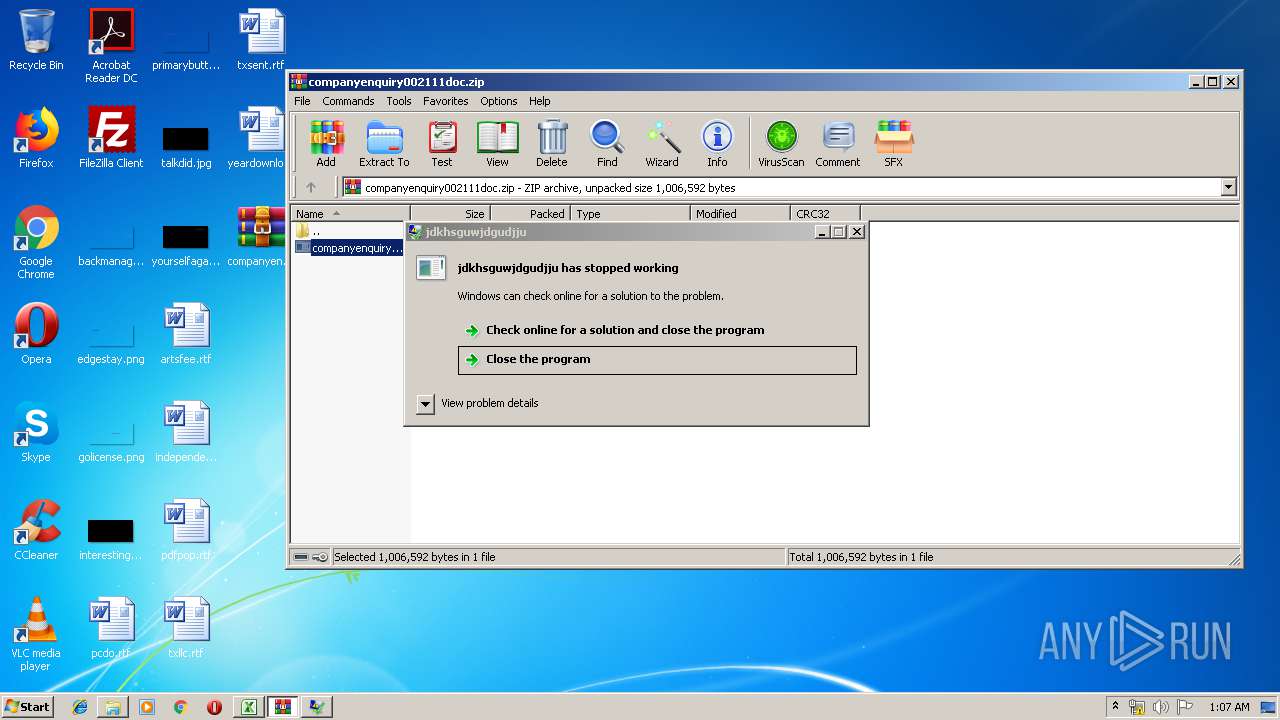
Application was dropped or rewritten from another process
- companyenquiry002111doc.exe (PID: 2952)
- companyenquiry002111doc.exe (PID: 3324)
- companyenquiry002111doc.exe (PID: 2440)
- companyenquiry002111doc.exe (PID: 2768)
- companyenquiry002111doc.exe (PID: 2460)
- companyenquiry002111doc.exe (PID: 2816)
Actions looks like stealing of personal data
- companyenquiry002111doc.exe (PID: 2440)
AGENTTESLA was detected
- companyenquiry002111doc.exe (PID: 2440)
SUSPICIOUS
Reads Internet Cache Settings
- EXCEL.EXE (PID: 2828)
Starts Internet Explorer
- EXCEL.EXE (PID: 2828)
Application launched itself
- companyenquiry002111doc.exe (PID: 3324)
- companyenquiry002111doc.exe (PID: 2952)
- companyenquiry002111doc.exe (PID: 2768)
- companyenquiry002111doc.exe (PID: 2816)
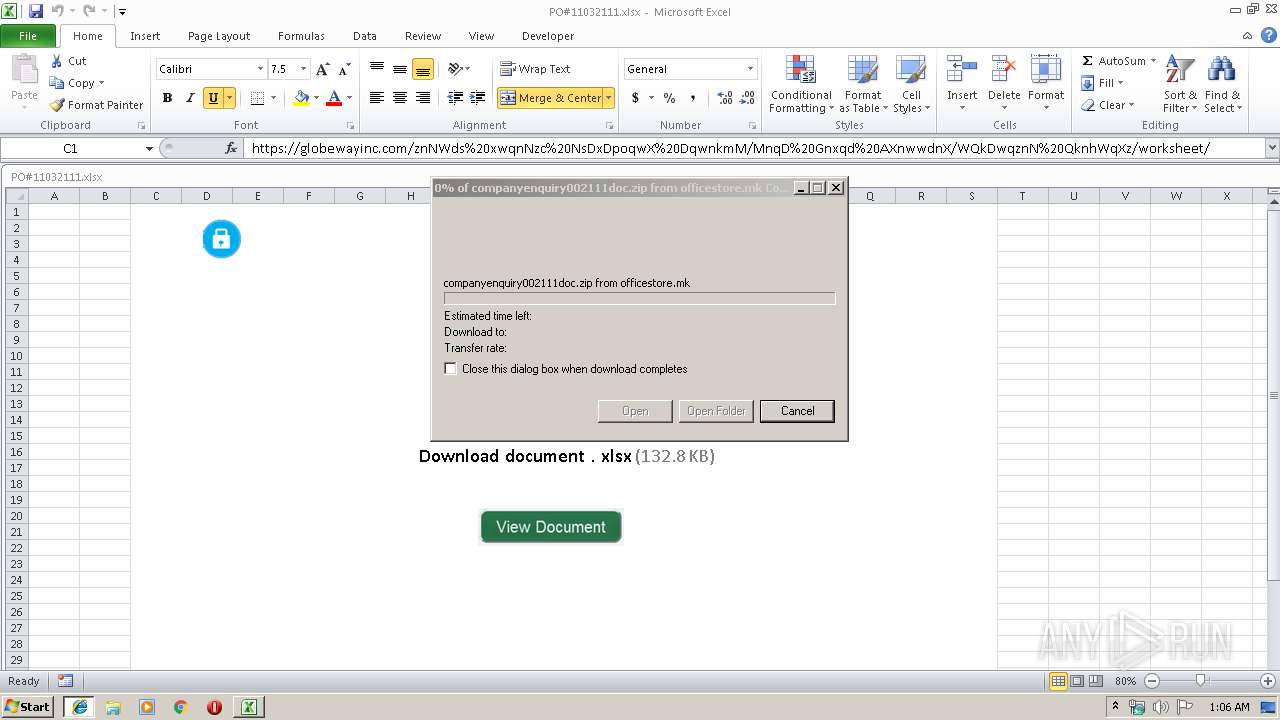
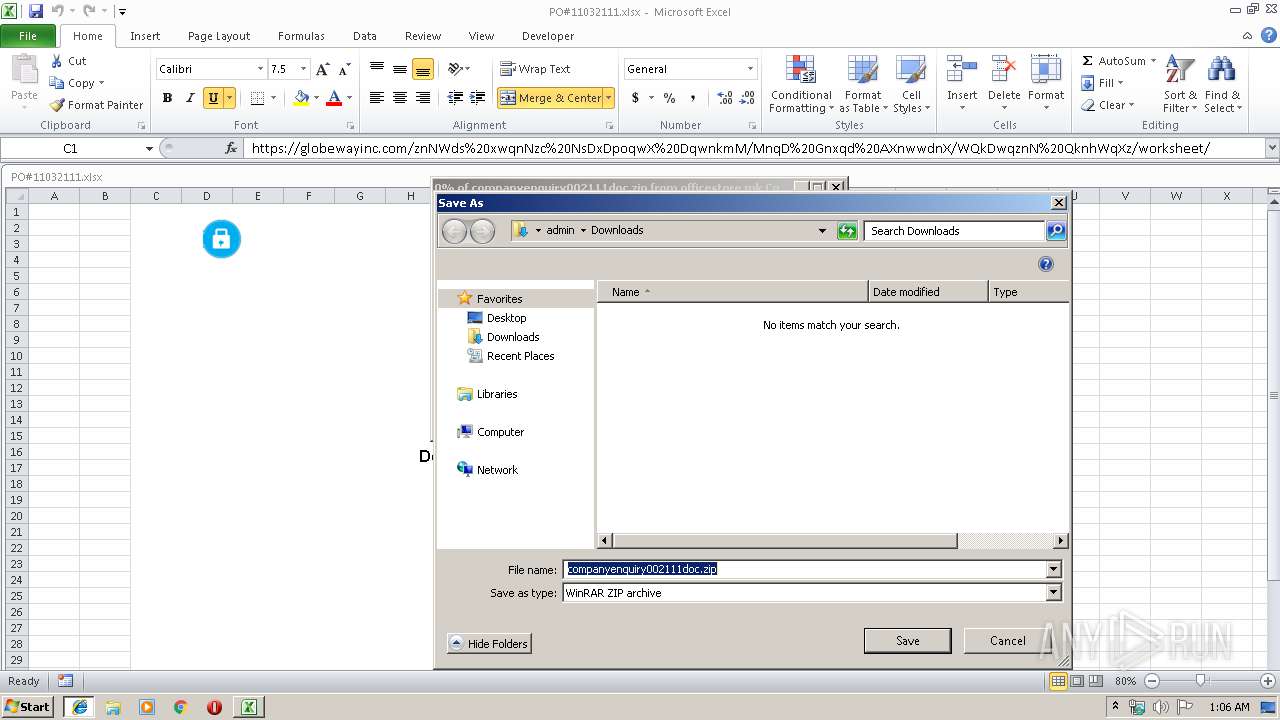
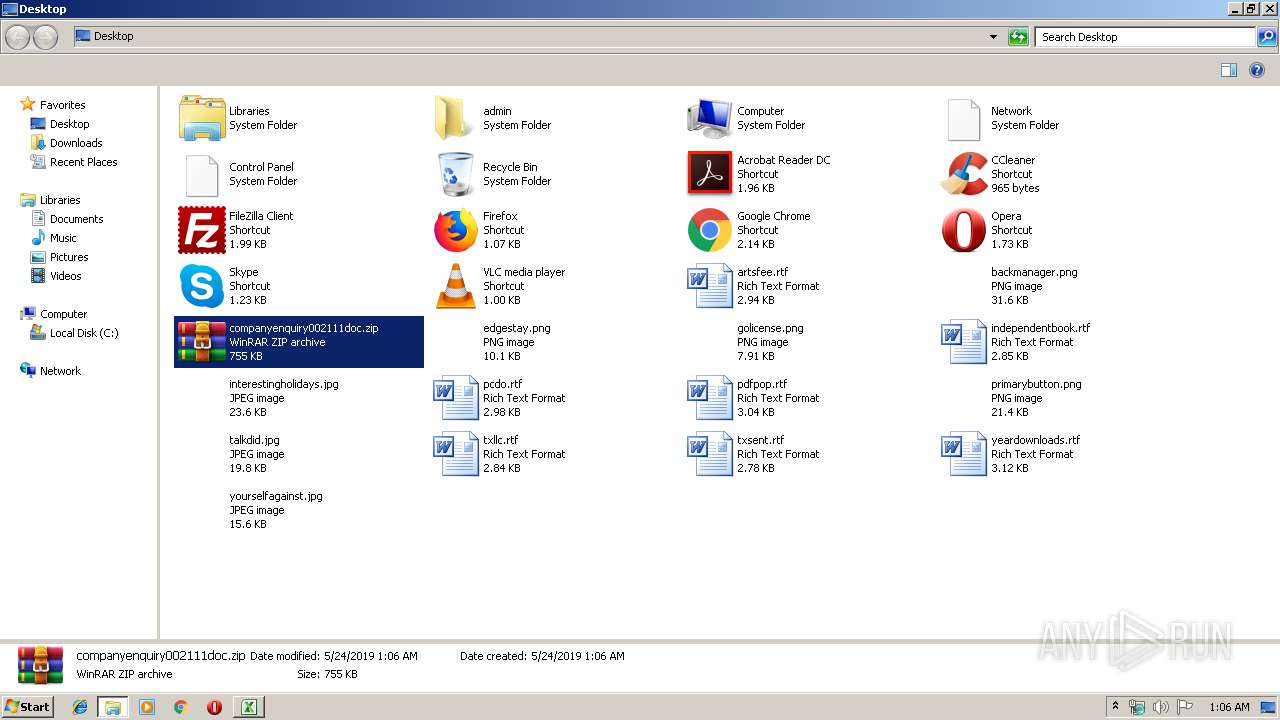
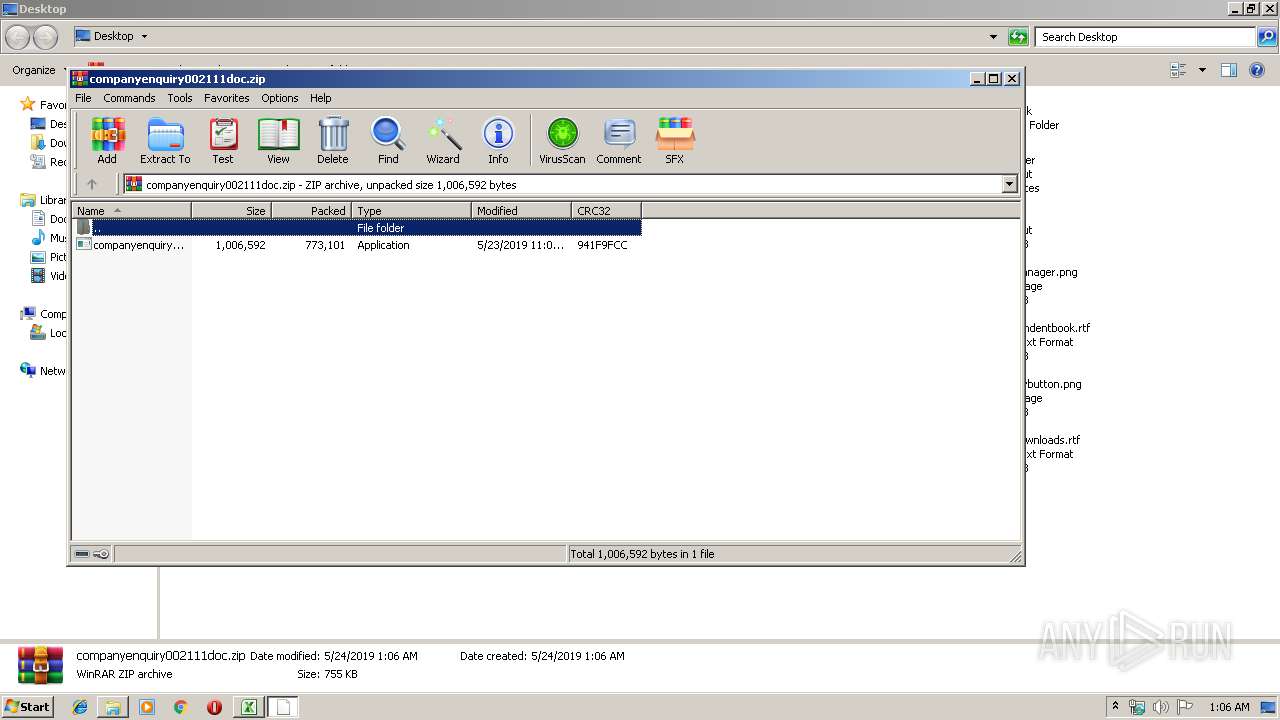
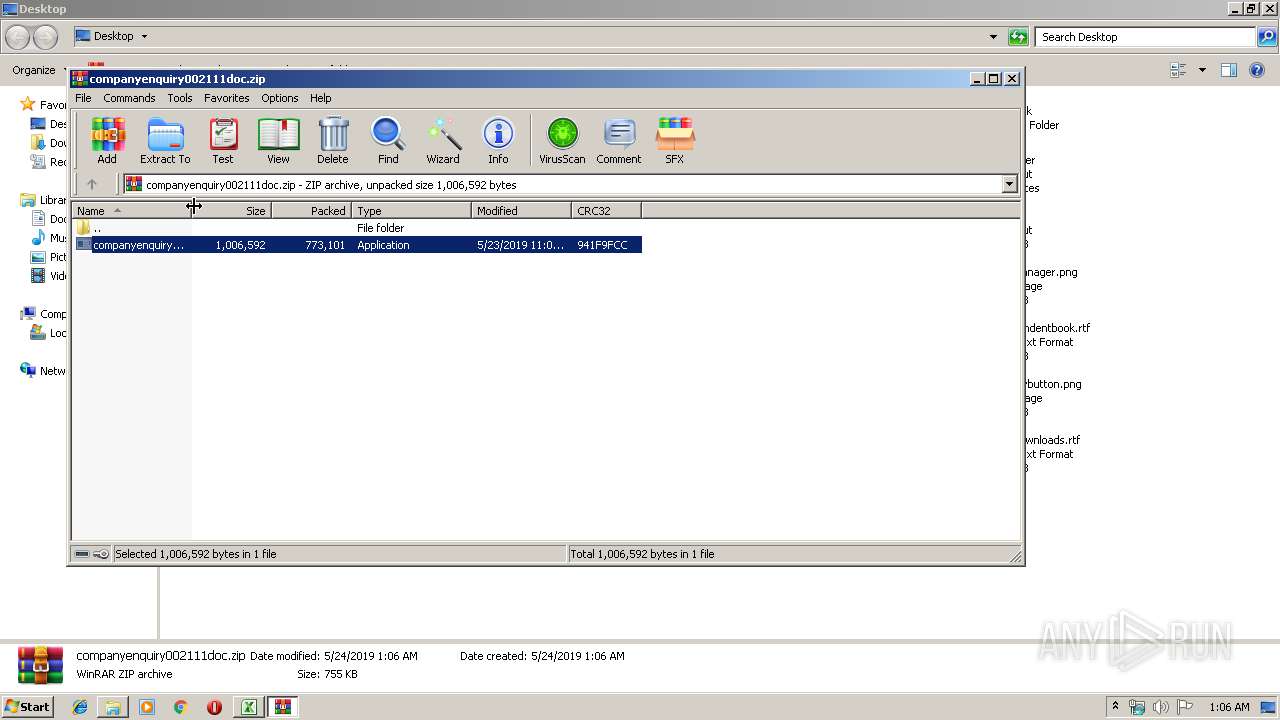
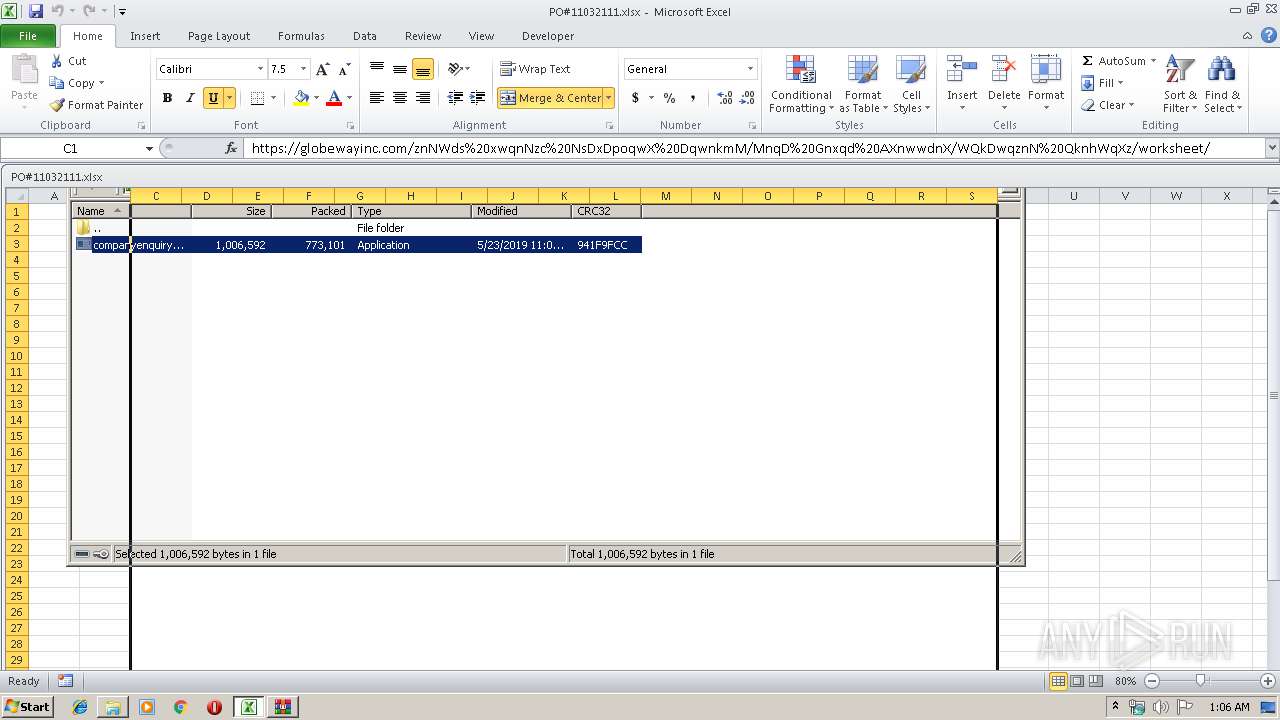
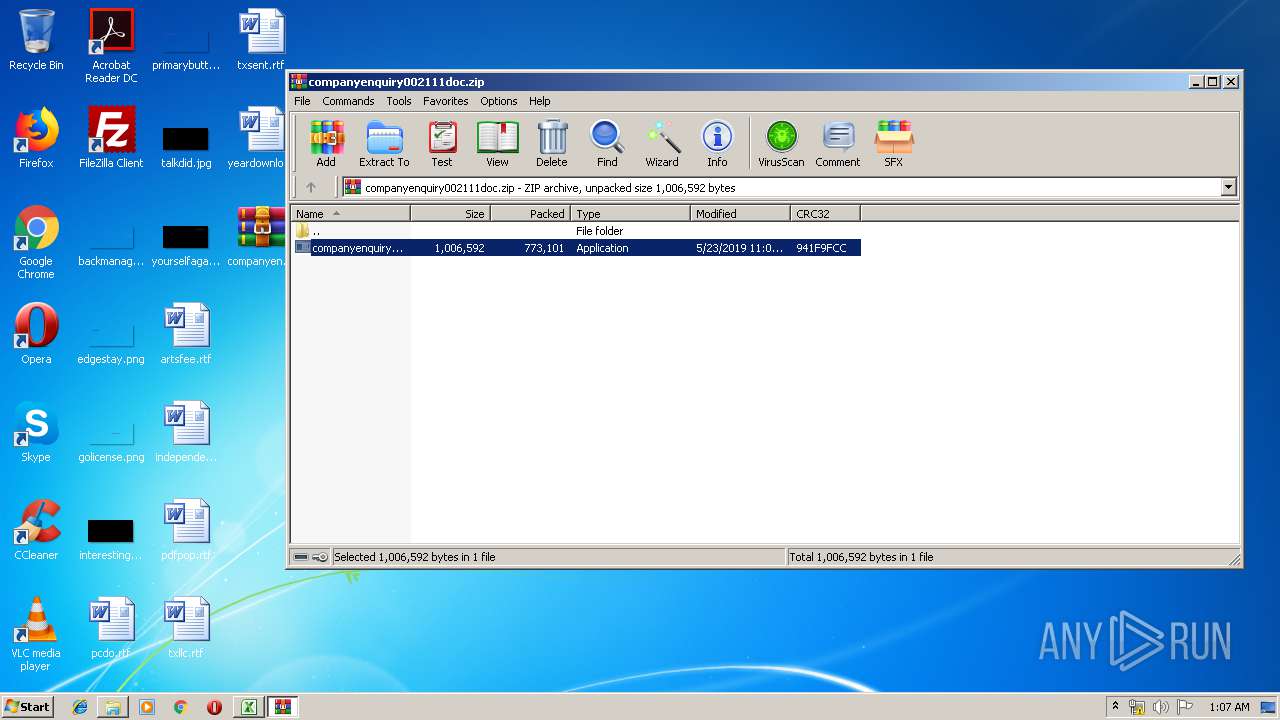
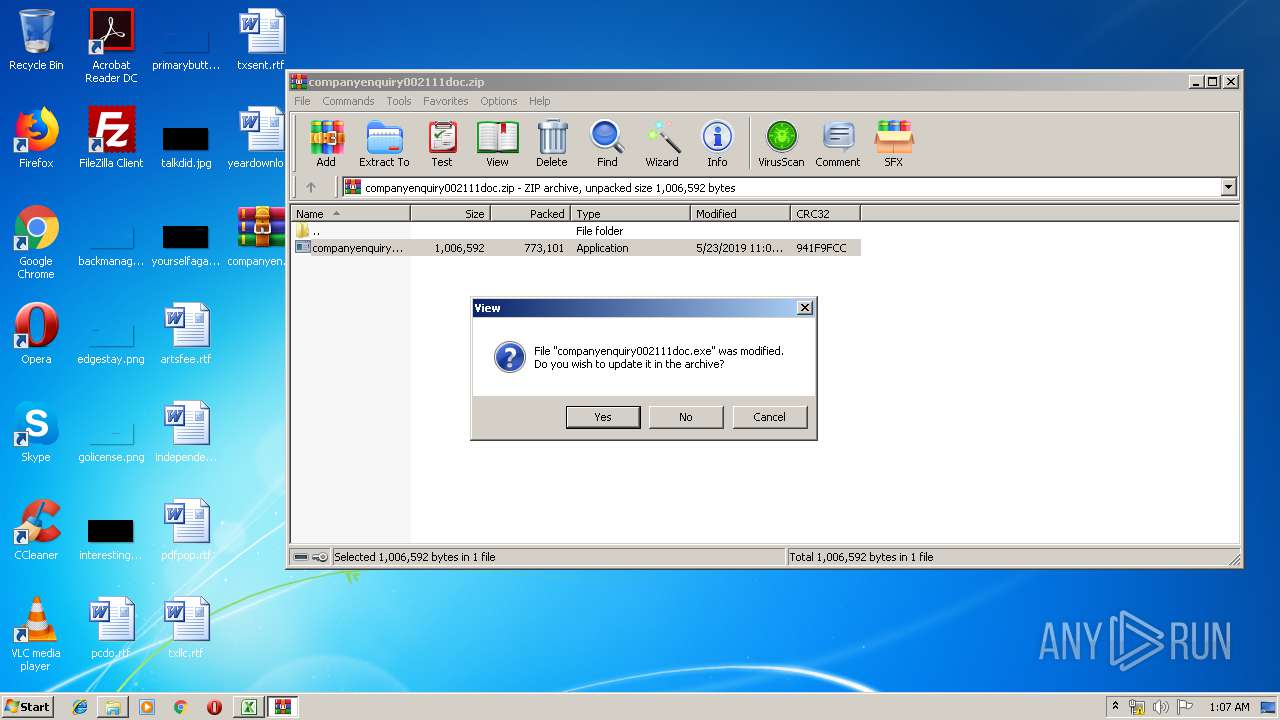
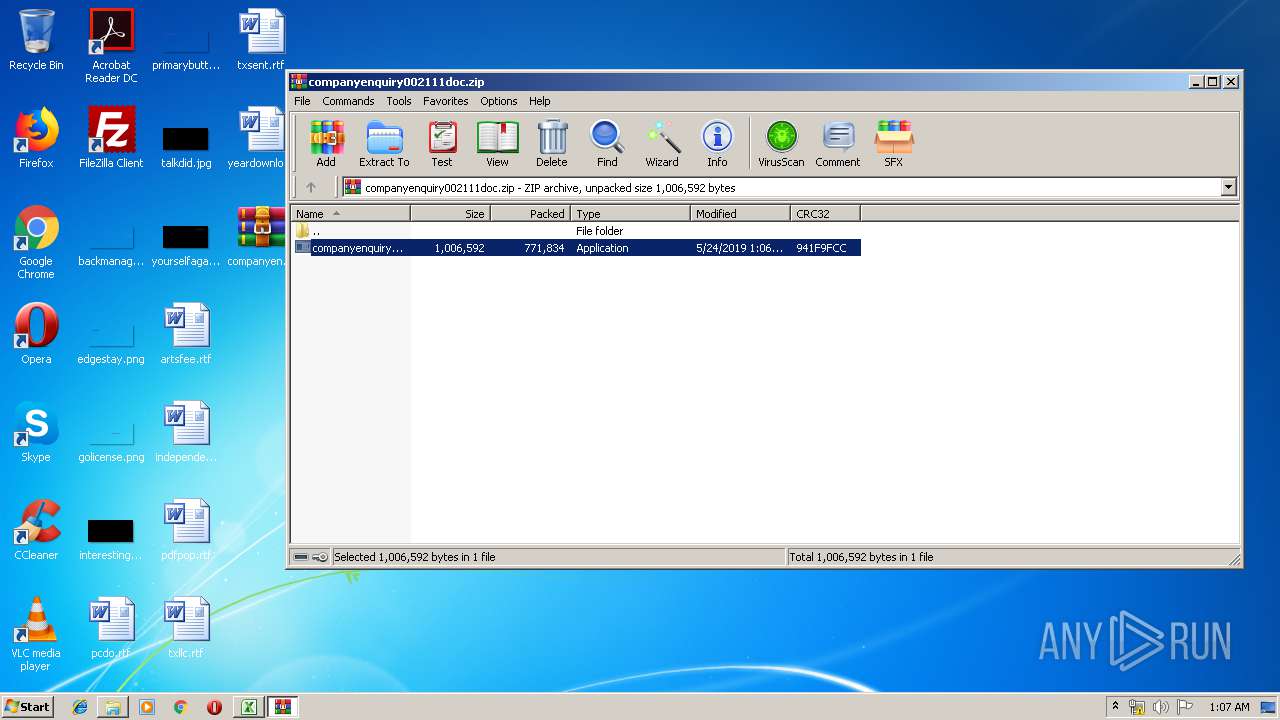
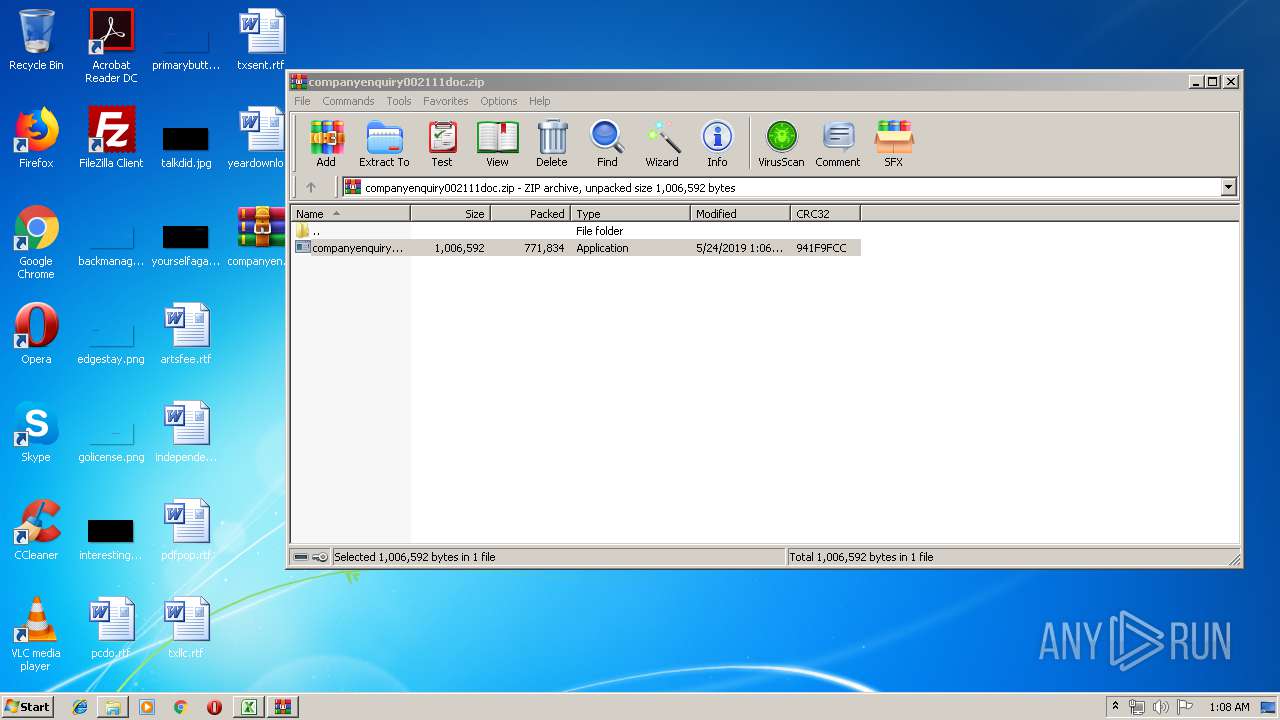
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3928)
Reads Windows Product ID
- companyenquiry002111doc.exe (PID: 2440)
Starts CMD.EXE for commands execution
- companyenquiry002111doc.exe (PID: 2952)
- companyenquiry002111doc.exe (PID: 2768)
Reads Environment values
- companyenquiry002111doc.exe (PID: 2440)
Checks for external IP
- companyenquiry002111doc.exe (PID: 2440)
INFO
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 2828)
Creates files in the user directory
- EXCEL.EXE (PID: 2828)
- iexplore.exe (PID: 2824)
Changes internet zones settings
- iexplore.exe (PID: 2492)
Reads Internet Cache Settings
- iexplore.exe (PID: 2824)
- iexplore.exe (PID: 2492)
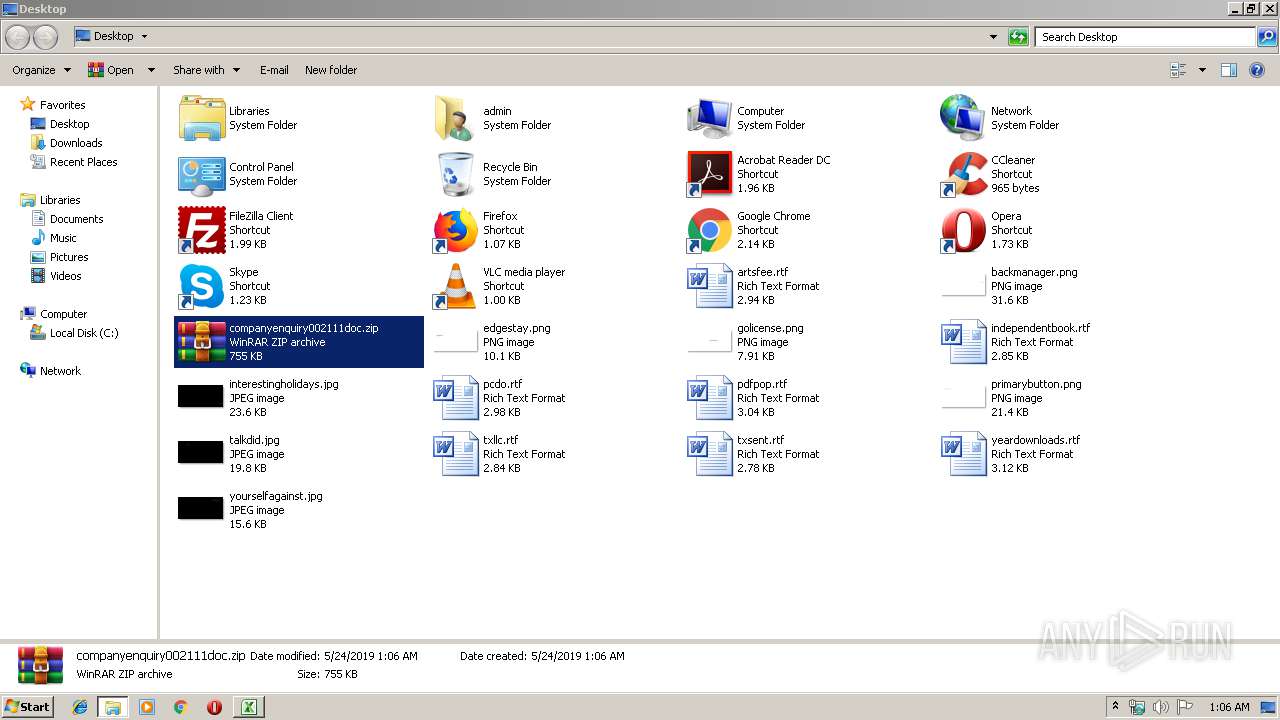
Manual execution by user
- WinRAR.exe (PID: 3928)
- companyenquiry002111doc.exe (PID: 2768)
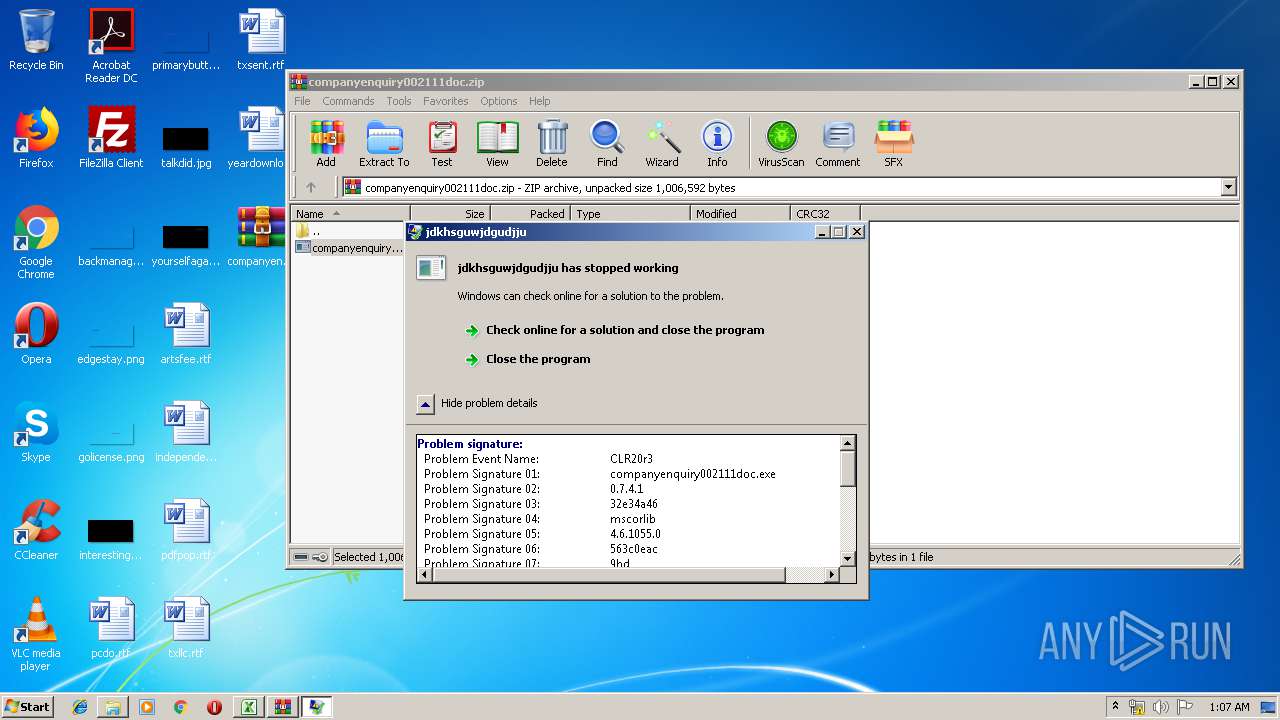
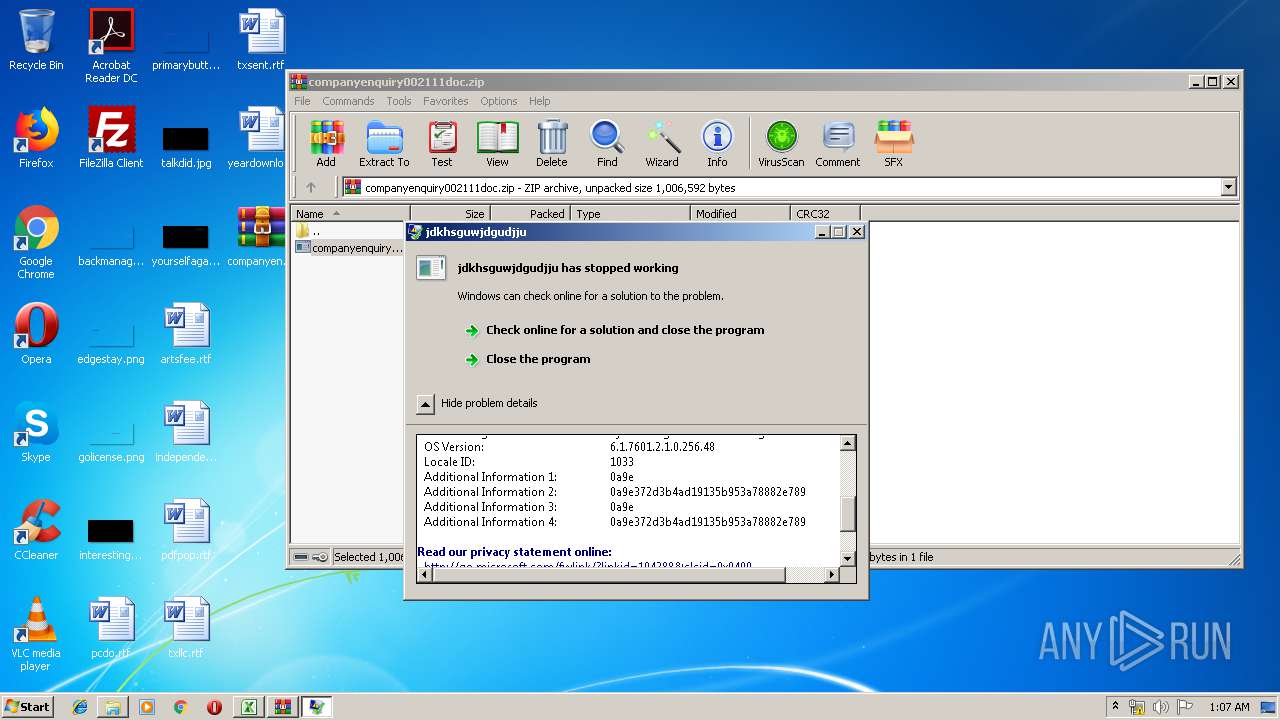
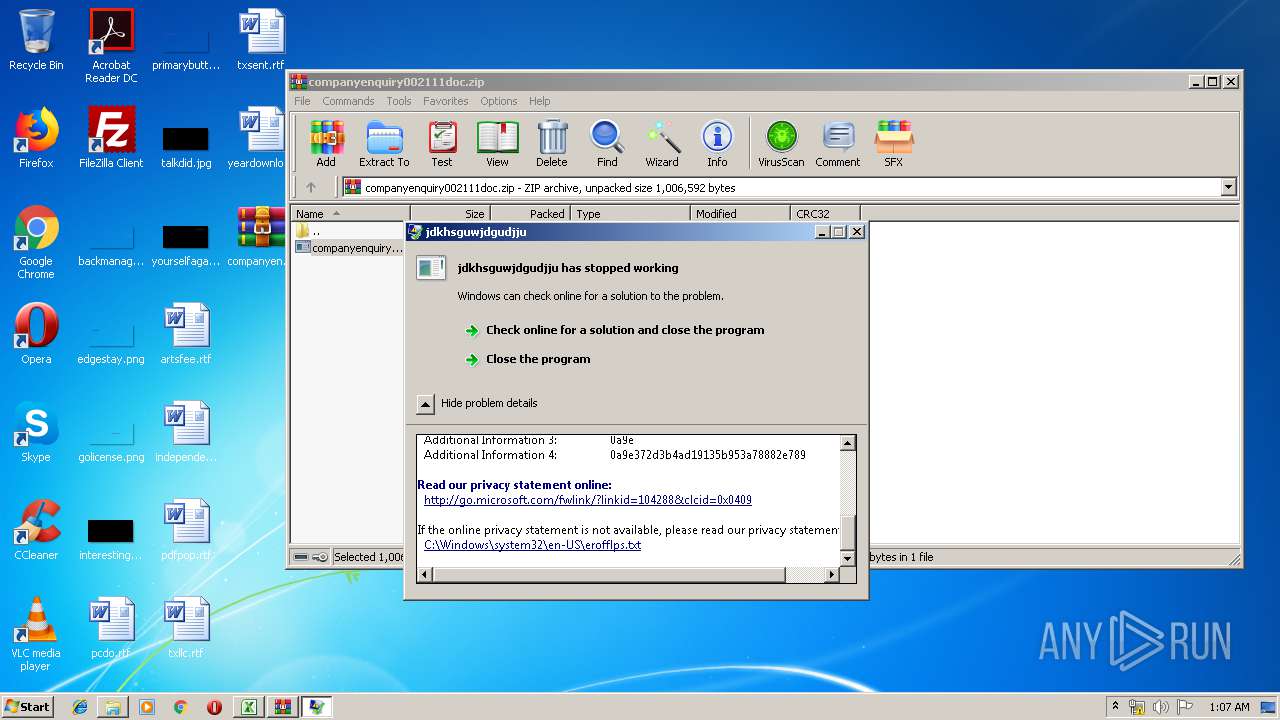
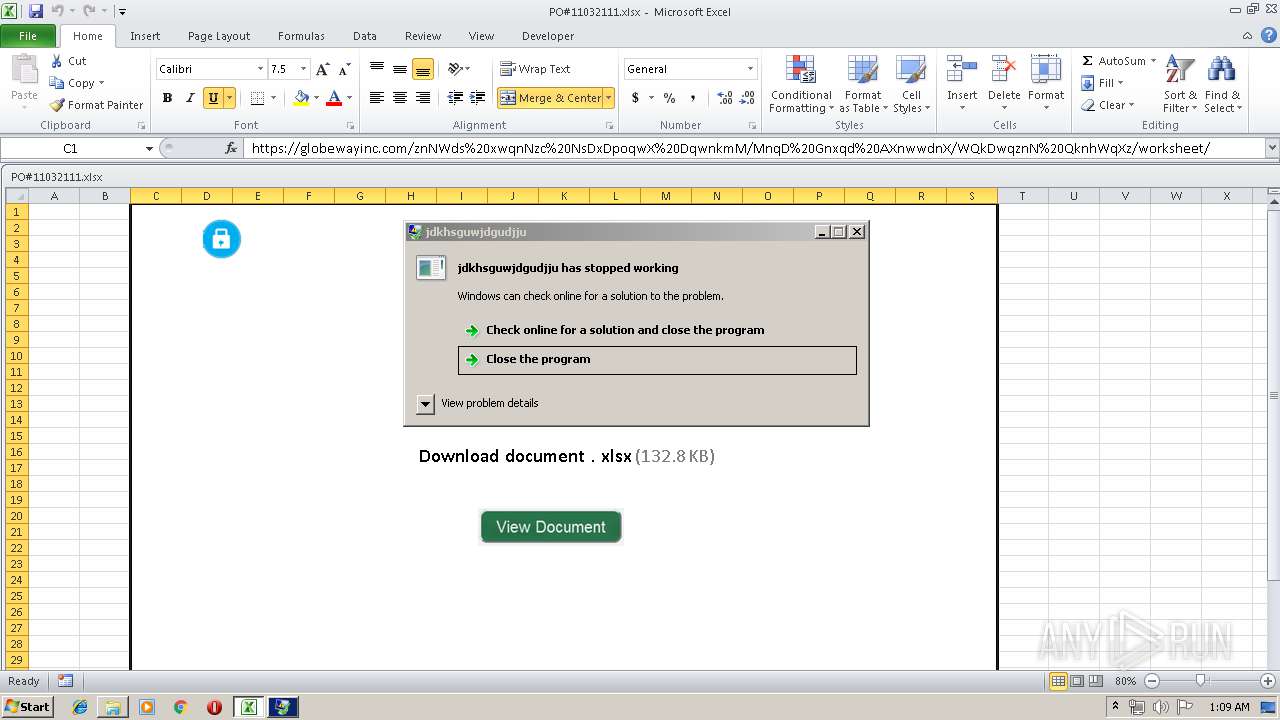
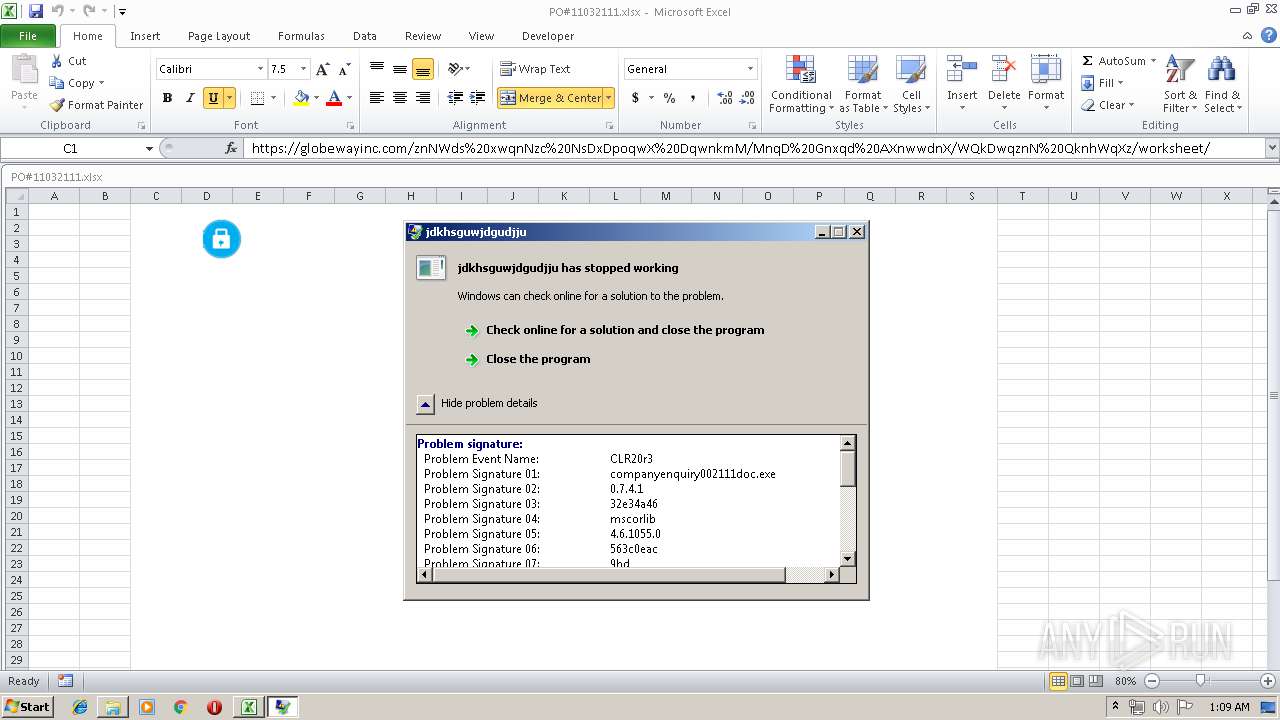
Application was crashed
- companyenquiry002111doc.exe (PID: 2952)
- companyenquiry002111doc.exe (PID: 2460)
- companyenquiry002111doc.exe (PID: 2768)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xlsx | | | Excel Microsoft Office Open XML Format document (61.2) |
|---|---|---|
| .zip | | | Open Packaging Conventions container (31.5) |
| .zip | | | ZIP compressed archive (7.2) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0006 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0x8546296f |
| ZipCompressedSize: | 408 |
| ZipUncompressedSize: | 1726 |
| ZipFileName: | [Content_Types].xml |
XML
| Application: | Microsoft Excel |
|---|---|
| DocSecurity: | None |
| ScaleCrop: | No |
| HeadingPairs: |
|
| TitlesOfParts: |
|
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 14.03 |
| LastModifiedBy: | USER |
| CreateDate: | 2016:08:23 21:52:25Z |
| ModifyDate: | 2019:05:23 22:14:04Z |
XMP
| Creator: | Double-Dee |
|---|
Total processes
63
Monitored processes
14
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2140 | "C:\Windows\System32\cmd.exe" /C type nul > "C:\Users\admin\Desktop\companyenquiry002111doc.exe:Zone.Identifier" | C:\Windows\System32\cmd.exe | — | companyenquiry002111doc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2440 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3928.39979\companyenquiry002111doc.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3928.39979\companyenquiry002111doc.exe | companyenquiry002111doc.exe | ||||||||||||
User: admin Company: dsdtyukfdrtyhdtyukg Integrity Level: MEDIUM Description: jdkhsguwjdgudjju Exit code: 0 Version: 0.7.4.1 Modules
| |||||||||||||||
| 2460 | "C:\Users\admin\Desktop\companyenquiry002111doc.exe" | C:\Users\admin\Desktop\companyenquiry002111doc.exe | companyenquiry002111doc.exe | ||||||||||||
User: admin Company: dsdtyukfdrtyhdtyukg Integrity Level: MEDIUM Description: jdkhsguwjdgudjju Exit code: 3221225477 Version: 0.7.4.1 Modules
| |||||||||||||||
| 2492 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | EXCEL.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2748 | "C:\Windows\System32\cmd.exe" /C type nul > "C:\Users\admin\Desktop\companyenquiry002111doc.exe:Zone.Identifier" | C:\Windows\System32\cmd.exe | — | companyenquiry002111doc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2768 | "C:\Users\admin\Desktop\companyenquiry002111doc.exe" | C:\Users\admin\Desktop\companyenquiry002111doc.exe | explorer.exe | ||||||||||||
User: admin Company: dsdtyukfdrtyhdtyukg Integrity Level: MEDIUM Description: jdkhsguwjdgudjju Exit code: 3762504530 Version: 0.7.4.1 Modules
| |||||||||||||||
| 2816 | "C:\Users\admin\Desktop\companyenquiry002111doc.exe" | C:\Users\admin\Desktop\companyenquiry002111doc.exe | — | companyenquiry002111doc.exe | |||||||||||
User: admin Company: dsdtyukfdrtyhdtyukg Integrity Level: MEDIUM Description: jdkhsguwjdgudjju Exit code: 0 Version: 0.7.4.1 Modules
| |||||||||||||||
| 2824 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2492 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2828 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2952 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3928.39979\companyenquiry002111doc.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3928.39979\companyenquiry002111doc.exe | WinRAR.exe | ||||||||||||
User: admin Company: dsdtyukfdrtyhdtyukg Integrity Level: MEDIUM Description: jdkhsguwjdgudjju Exit code: 3762504530 Version: 0.7.4.1 Modules
| |||||||||||||||
Total events
2 370
Read events
2 155
Write events
199
Delete events
16
Modification events
| (PID) Process: | (2828) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | gv? |
Value: 67763F000C0B0000010000000000000000000000 | |||
| (PID) Process: | (2828) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2828) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2828) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel |
| Operation: | write | Name: | MTTT |
Value: 0C0B00009E8ED375C411D50100000000 | |||
| (PID) Process: | (2828) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete value | Name: | gv? |
Value: 67763F000C0B0000010000000000000000000000 | |||
| (PID) Process: | (2828) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2828) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2828) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2828) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2828) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\DocumentRecovery\14EA21 |
| Operation: | write | Name: | 14EA21 |
Value: 040000000C0B00003200000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C0050004F002300310031003000330032003100310031002E0078006C0073007800000000002200000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C0001000000000000007080A076C411D50121EA140021EA140000000000AC020000001000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
2
Suspicious files
4
Text files
10
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2828 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVRE647.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2828 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\companyenquiry002111doc[1].zip | — | |
MD5:— | SHA256:— | |||
| 2492 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2492 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2492 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFA84EF9705382697C.TMP | — | |
MD5:— | SHA256:— | |||
| 2492 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF0F2A7C5A29C44920.TMP | — | |
MD5:— | SHA256:— | |||
| 2492 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{BC16529F-7DB7-11E9-B3B3-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 3928 | WinRAR.exe | C:\Users\admin\Desktop\__rzi_3928.48024 | — | |
MD5:— | SHA256:— | |||
| 2824 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
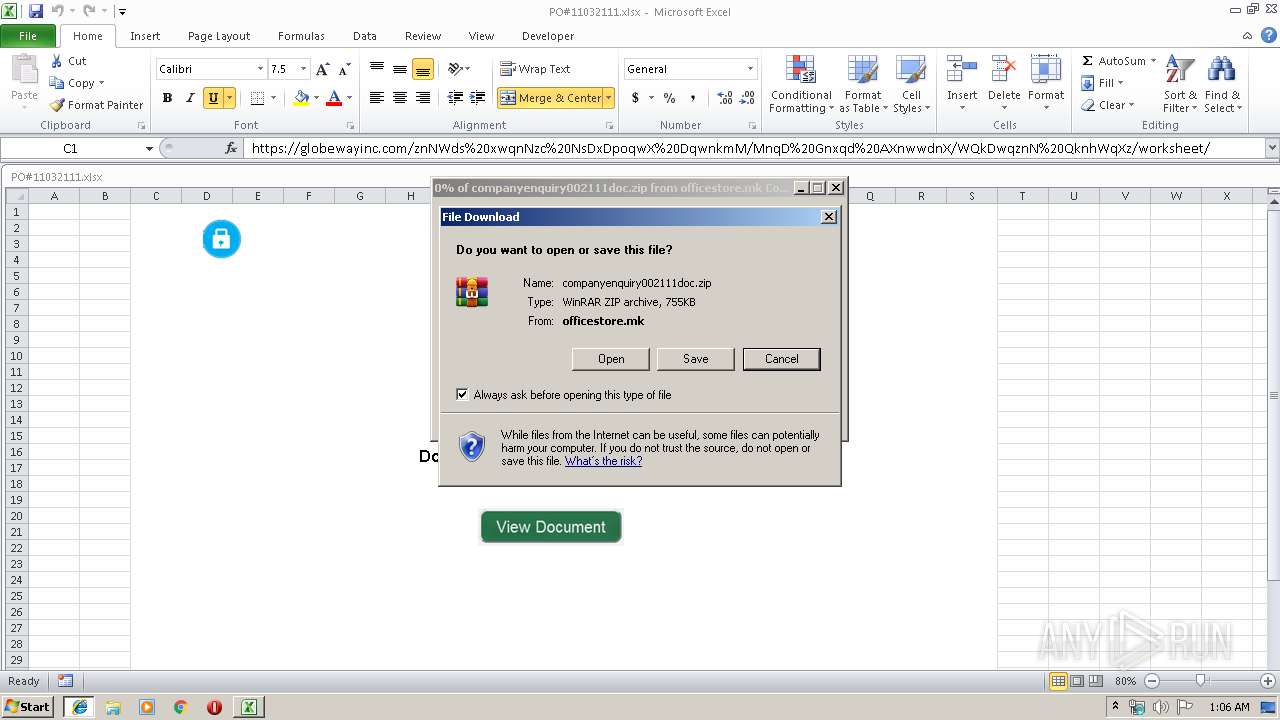
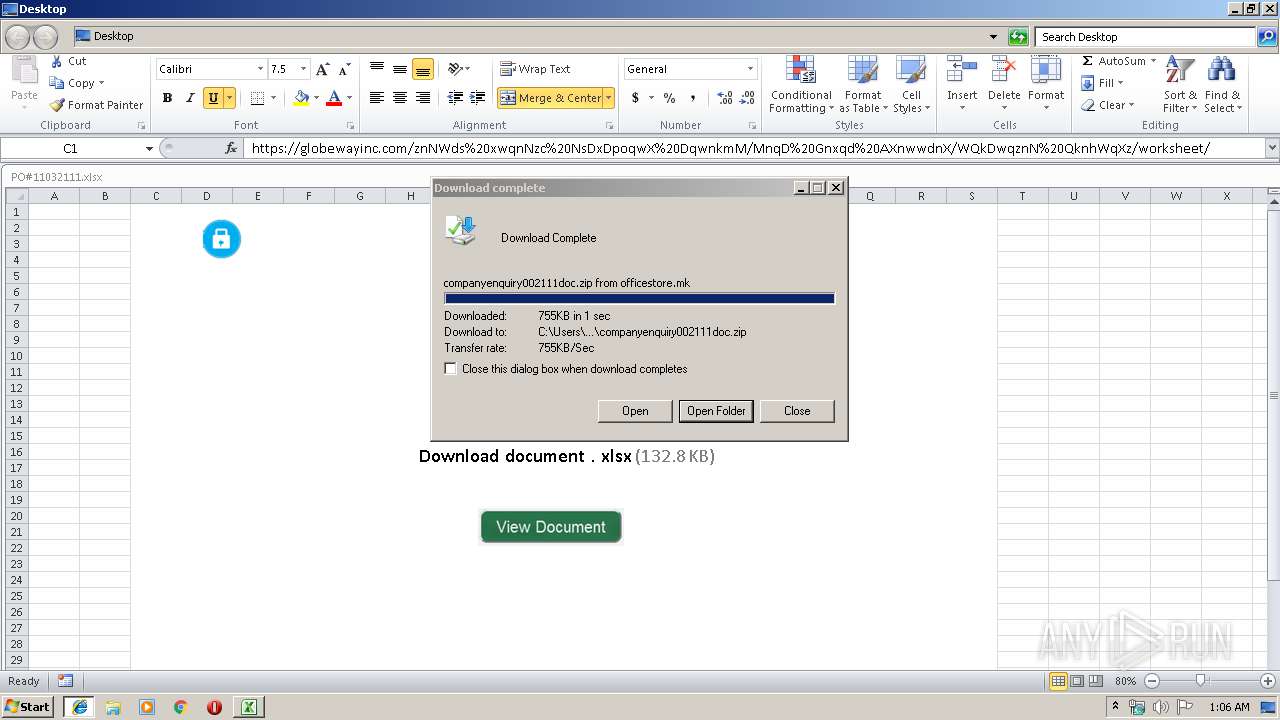
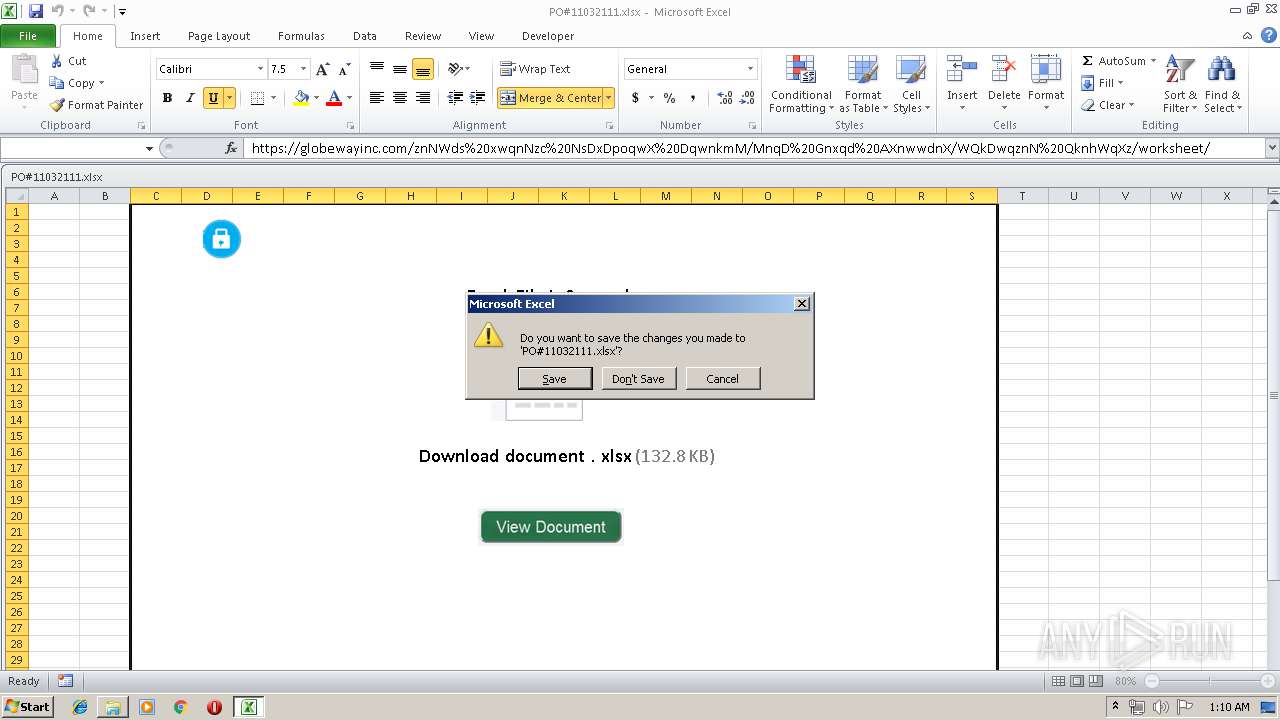
| 2824 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\33B23X27\companyenquiry002111doc[1].zip | compressed | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
5
DNS requests
4
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
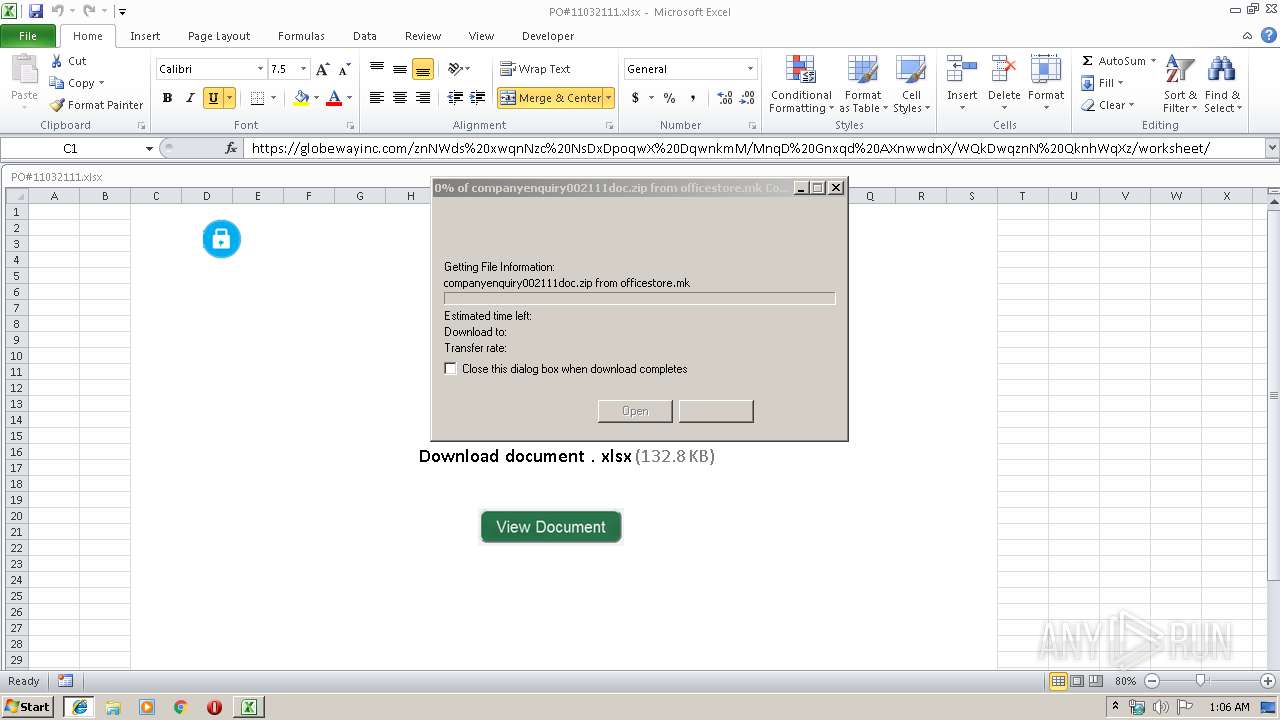
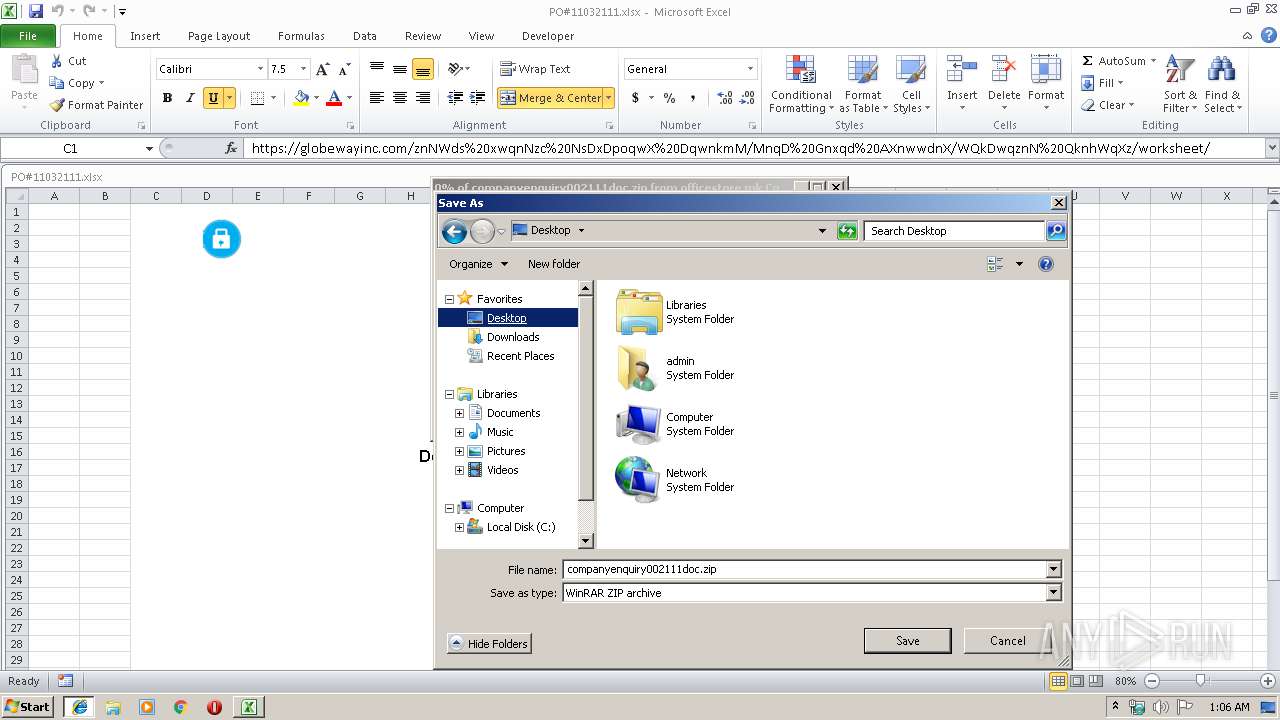
2828 | EXCEL.EXE | GET | — | 88.99.251.203:80 | http://officestore.mk/companyenquiry002111doc.zip | DE | — | — | malicious |
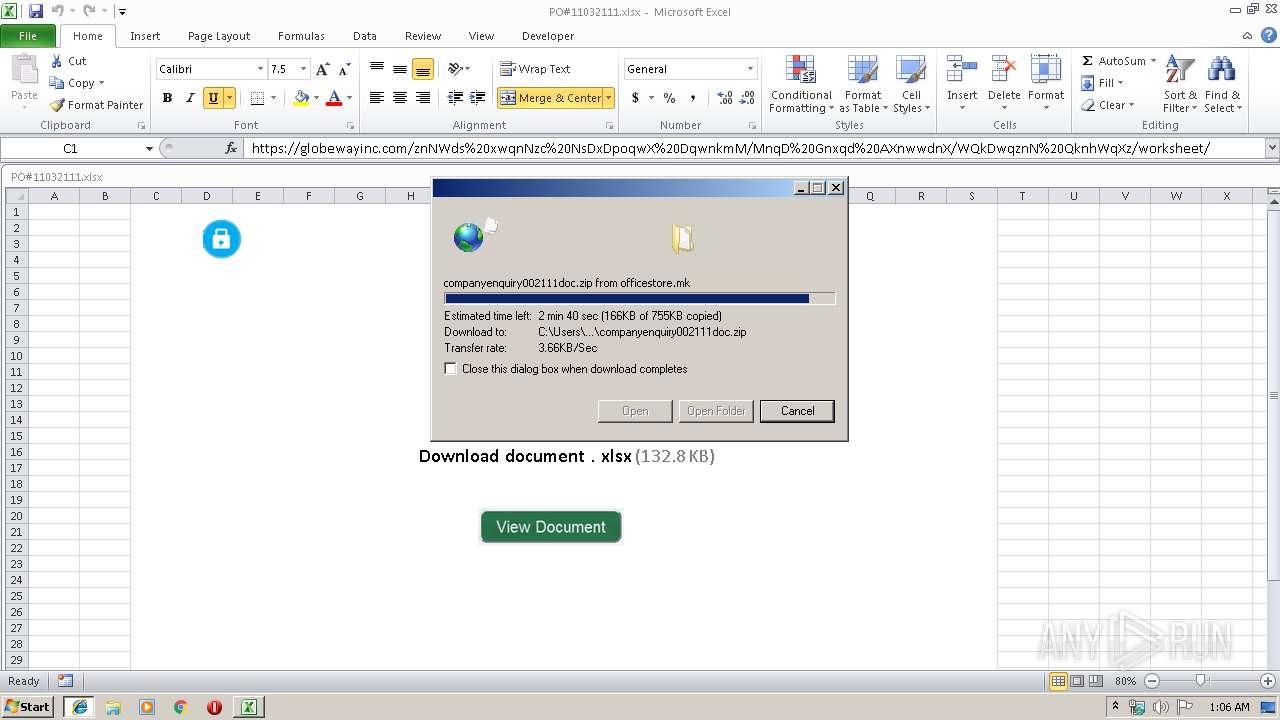
2824 | iexplore.exe | GET | 200 | 88.99.251.203:80 | http://officestore.mk/companyenquiry002111doc.zip | DE | compressed | 755 Kb | malicious |
2440 | companyenquiry002111doc.exe | GET | 200 | 52.202.139.131:80 | http://checkip.amazonaws.com/ | US | text | 12 b | malicious |
2492 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2824 | iexplore.exe | 88.99.251.203:80 | officestore.mk | Hetzner Online GmbH | DE | malicious |
2440 | companyenquiry002111doc.exe | 94.141.22.139:587 | mail.donatomartinelli.com | KPNQWest Italia S.p.a. | IT | unknown |
2828 | EXCEL.EXE | 88.99.251.203:80 | officestore.mk | Hetzner Online GmbH | DE | malicious |
2492 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2440 | companyenquiry002111doc.exe | 52.202.139.131:80 | checkip.amazonaws.com | Amazon.com, Inc. | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
officestore.mk |
| malicious |
www.bing.com |
| whitelisted |
mail.donatomartinelli.com |
| unknown |
checkip.amazonaws.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2440 | companyenquiry002111doc.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
2440 | companyenquiry002111doc.exe | A Network Trojan was detected | MALWARE [PTsecurity] AgentTesla IP Check |
2 ETPRO signatures available at the full report