| File name: | svchost.zip |
| Full analysis: | https://app.any.run/tasks/761d2b1a-5144-4c49-b5a3-7a23c3533d86 |
| Verdict: | Malicious activity |
| Threats: | Ramnit is a highly modular banking trojan and worm that evolved from a file-infecting virus into a powerful cybercrime tool. It specializes in financial fraud, credential theft, remote access, and malware delivery, being a serious threat to businesses and individuals. First spotted in 2010, Ramnit became popular after the 2014 takedown of the GameOver Zeus botnet, as cybercriminals sought alternatives for banking fraud. |
| Analysis date: | January 11, 2020, 07:24:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
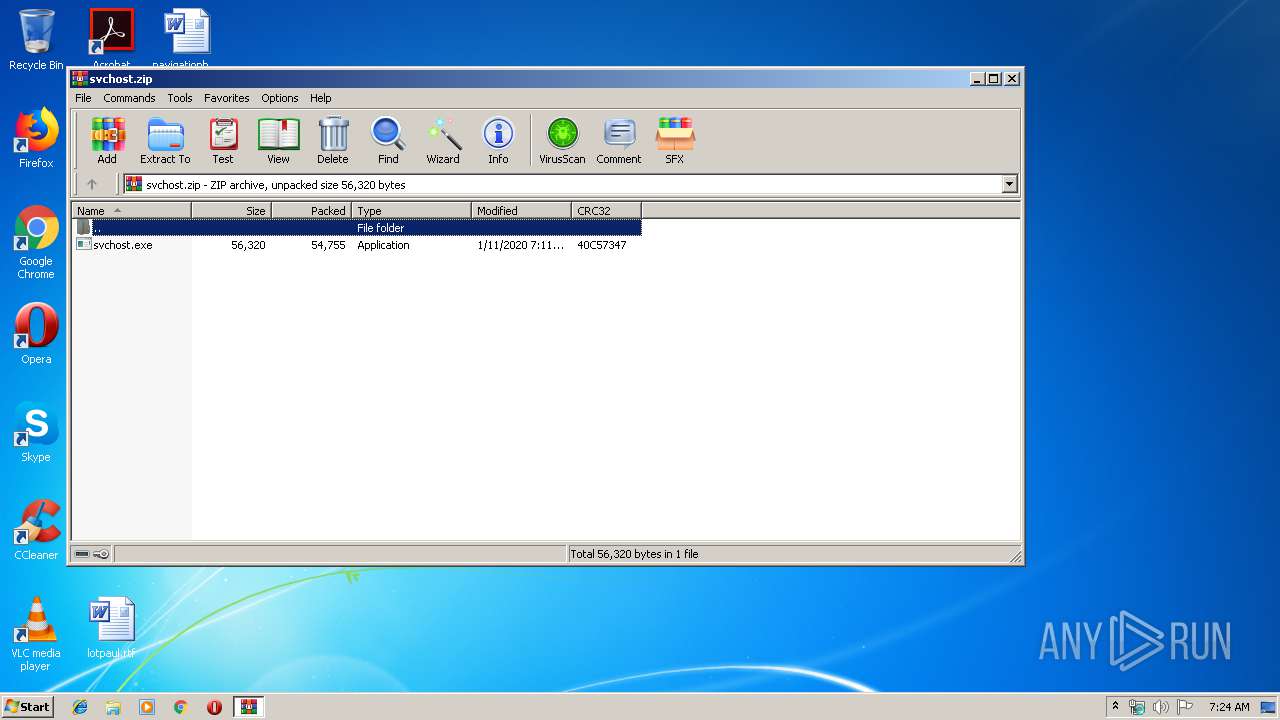
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | EF1E4C04BF60CACA1DFE0386A4F11D97 |
| SHA1: | C6C044EAFC184F275BF1A55DBDD85355C188D9E3 |
| SHA256: | 1FF04ED2CADB8BDA5A42EA75052F5346348CC75F14B4B22A841915D881BA1F7A |
| SSDEEP: | 1536:muaDO+nKjYRotV3nsPFG+5ODTb7MX6DgDTj:PwEYutj+5O7oH |
MALICIOUS
Application was dropped or rewritten from another process
- svchost.exe (PID: 2572)
- DesktopLayer.exe (PID: 3388)
RAMNIT was detected
- iexplore.exe (PID: 1908)
Changes the login/logoff helper path in the registry
- iexplore.exe (PID: 1908)
Connects to CnC server
- iexplore.exe (PID: 1908)
SUSPICIOUS
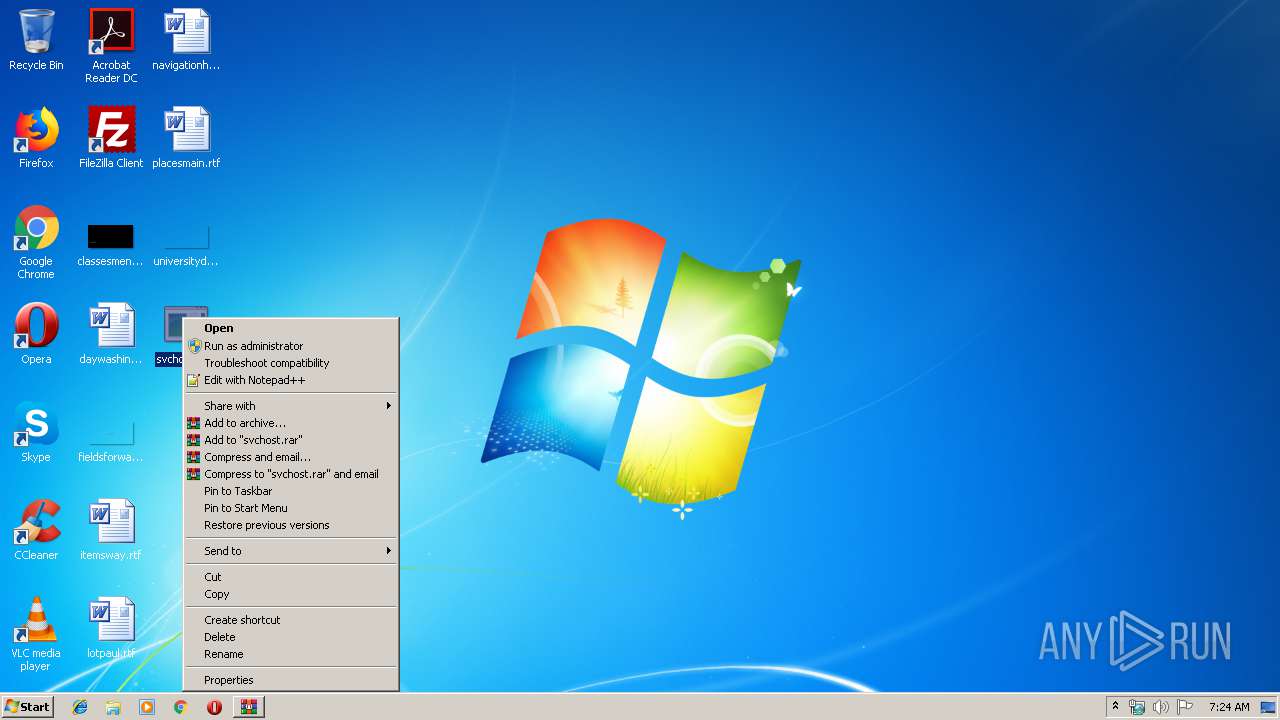
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2456)
- svchost.exe (PID: 2572)
Creates executable files which already exist in Windows
- WinRAR.exe (PID: 2456)
Starts Internet Explorer
- DesktopLayer.exe (PID: 3388)
Creates files in the program directory
- iexplore.exe (PID: 1908)
- svchost.exe (PID: 2572)
INFO
Manual execution by user
- svchost.exe (PID: 2572)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:01:11 15:11:07 |
| ZipCRC: | 0x40c57347 |
| ZipCompressedSize: | 54755 |
| ZipUncompressedSize: | 56320 |
| ZipFileName: | svchost.exe |
Total processes
42
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1908 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | DesktopLayer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
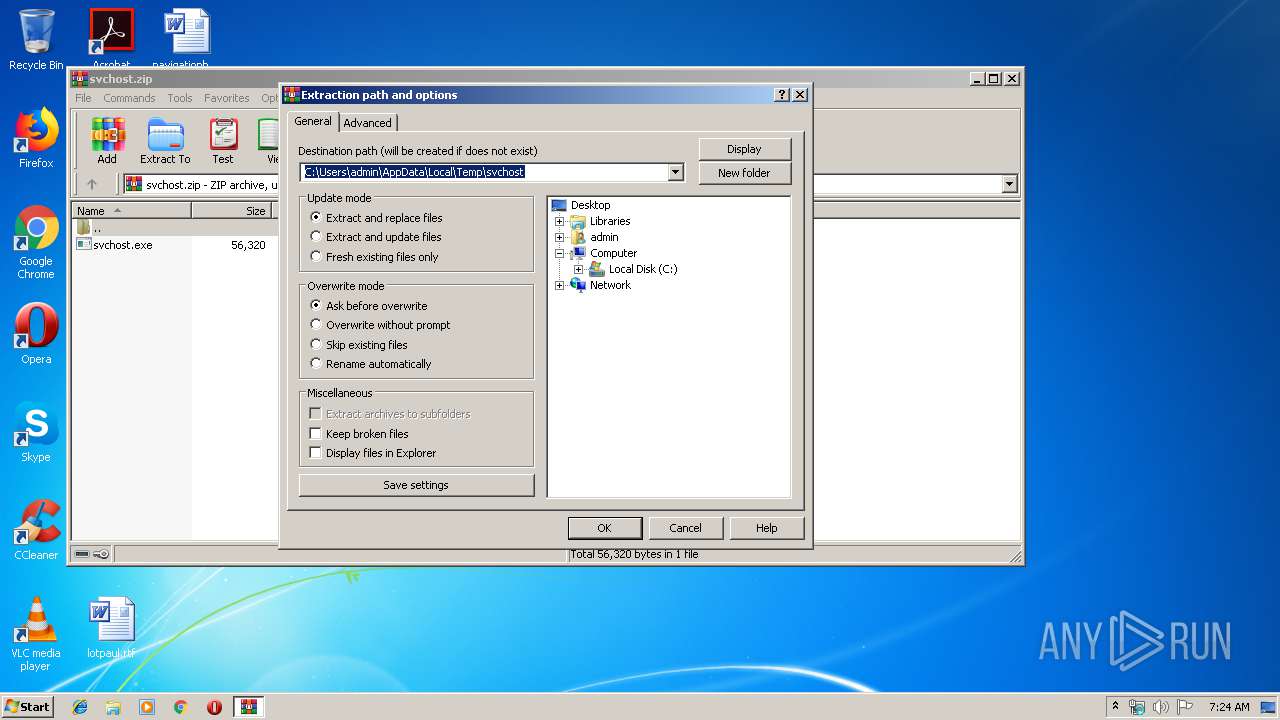
| 2456 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\svchost.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2572 | "C:\Users\admin\Desktop\svchost.exe" | C:\Users\admin\Desktop\svchost.exe | explorer.exe | ||||||||||||
User: admin Company: SOFTWIN S.R.L. Integrity Level: HIGH Description: BitDefender Management Console Exit code: 0 Version: 106.42.73.61 Modules
| |||||||||||||||
| 3388 | "C:\Program Files\Microsoft\DesktopLayer.exe" | C:\Program Files\Microsoft\DesktopLayer.exe | — | svchost.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
534
Read events
523
Write events
11
Delete events
0
Modification events
| (PID) Process: | (2456) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2456) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2456) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2456) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\svchost.zip | |||
| (PID) Process: | (2456) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2456) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2456) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2456) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2456) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
| (PID) Process: | (1908) iexplore.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon |
| Operation: | write | Name: | Userinit |
Value: c:\windows\system32\userinit.exe,,c:\program files\microsoft\desktoplayer.exe | |||
Executable files
2
Suspicious files
2
Text files
39
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1908 | iexplore.exe | C:\Program Files\Adobe\Acrobat Reader DC\Berime.htm | html | |
MD5:CBADF7509F16BF3620AC5A483E4CBB1C | SHA256:1F58F6F2330711369236A596E37B19F695C2677BB363C9A59E3A70AC220E95FB | |||
| 1908 | iexplore.exe | C:\Program Files\Adobe\Acrobat Reader DC\Lisezmoi.htm | html | |
MD5:785EDFA144F16A7F0FC2933A97919641 | SHA256:D6811444120985ACDBFDC5943183733D8CA3C800B1C6009753A81C2E5EF3253B | |||
| 1908 | iexplore.exe | C:\Program Files\Internet Explorer\dmlconf.dat | binary | |
MD5:702B30E090FDADB0D624B7D27879303D | SHA256:87CF81595B02EED7727F06F1E07129F5225D9D08A74461266154CA51C24CCBEE | |||
| 1908 | iexplore.exe | C:\Program Files\Adobe\Acrobat Reader DC\LeesMij.htm | html | |
MD5:306F4A37ABAF653E02812B4CC1E71C1B | SHA256:B6E495D6E2A2CFE5C82361C881311BAB1BAB6C9B8908FED6EEE7F64203DF2B78 | |||
| 1908 | iexplore.exe | C:\Program Files\Adobe\Acrobat Reader DC\IrakHau.htm | html | |
MD5:A6851D600250BF93716FD1721E509697 | SHA256:3B4DE405392B27B611E9D820857D221BE34873A4D28AE2DDBE760C78440011CA | |||
| 1908 | iexplore.exe | C:\Program Files\Adobe\Acrobat Reader DC\LeiaMe.htm | html | |
MD5:37F3D4CB431CEC9AF2F69D87FE8A2F64 | SHA256:590E6DBB8DF77FE6E57894632FA6CB28C7B086704B0E7F9A348A95651310FD8E | |||
| 1908 | iexplore.exe | C:\Program Files\Adobe\Acrobat Reader DC\Leggimi.htm | html | |
MD5:7BFD7D6BB6EAC5462C4F9E370F7A6F80 | SHA256:84E5D8D48334DF15BB9A99C858DA7D56268E14EEC1058F836BF6B4DC9DE41C0D | |||
| 1908 | iexplore.exe | C:\Program Files\Adobe\Acrobat Reader DC\LueMinut.htm | html | |
MD5:06EE95A60459E8B22EA76F1BE1A619E3 | SHA256:8A17F941DBD591C215422998F8D098742D1BF7D736C927F3E37217F545420416 | |||
| 1908 | iexplore.exe | C:\Program Files\Adobe\Acrobat Reader DC\Llegiu-me.htm | html | |
MD5:439C71C59341E5E518D0EABC4099A24B | SHA256:419BCE4CD535A08FD240849436101579FC6A5464690D166E3E7A8EED87F12293 | |||
| 1908 | iexplore.exe | C:\Program Files\Adobe\Acrobat Reader DC\Benioku.htm | html | |
MD5:A491201AB7305E2C71D90CB6CBBEEAA1 | SHA256:826444C3D91CB3694A2256B0D5470553FAAB1B70D0008A3294554875015BF0BC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
2
Threats
5
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1908 | iexplore.exe | 172.217.16.78:80 | google.com | Google Inc. | US | whitelisted |
1908 | iexplore.exe | 72.26.218.70:443 | fget-career.com | Voxel Dot Net, Inc. | NL | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| malicious |
fget-career.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1908 | iexplore.exe | A Network Trojan was detected | ET TROJAN Win32/Ramnit Checkin |
1908 | iexplore.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/Ramnit Checkin |
1908 | iexplore.exe | A Network Trojan was detected | ET TROJAN Win32/Ramnit Checkin |
1908 | iexplore.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/Ramnit Checkin |
1 ETPRO signatures available at the full report