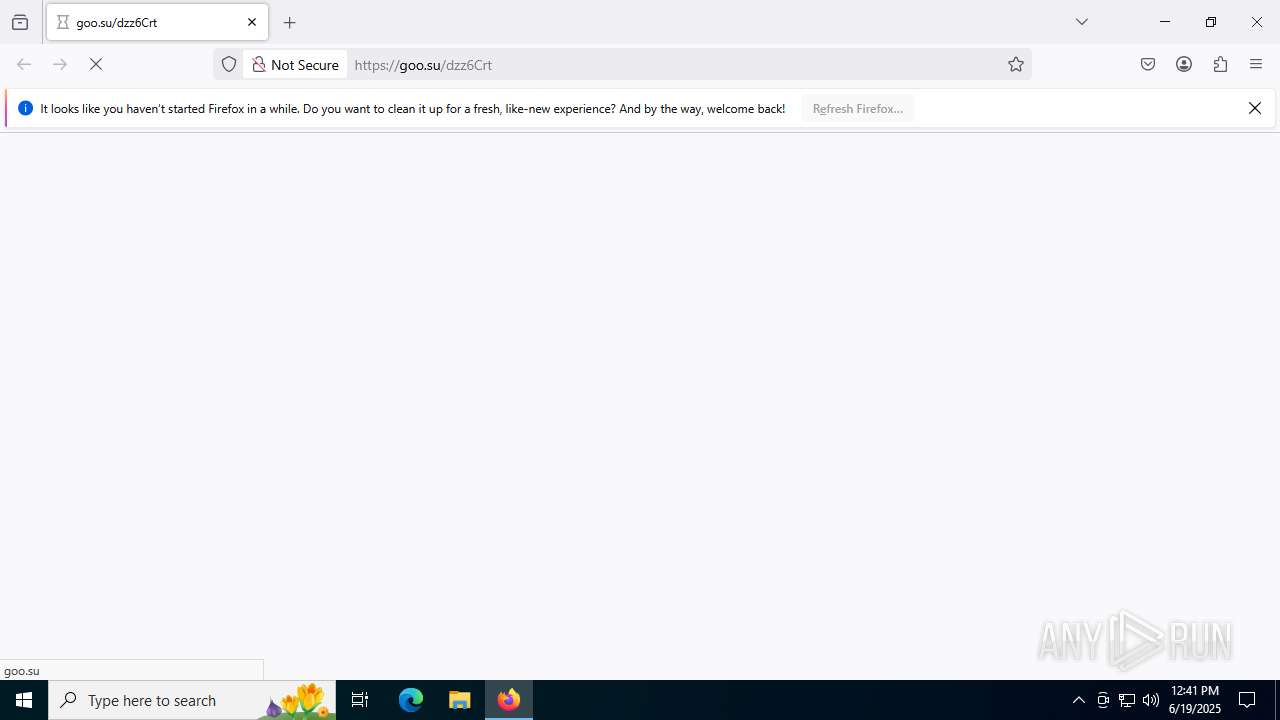
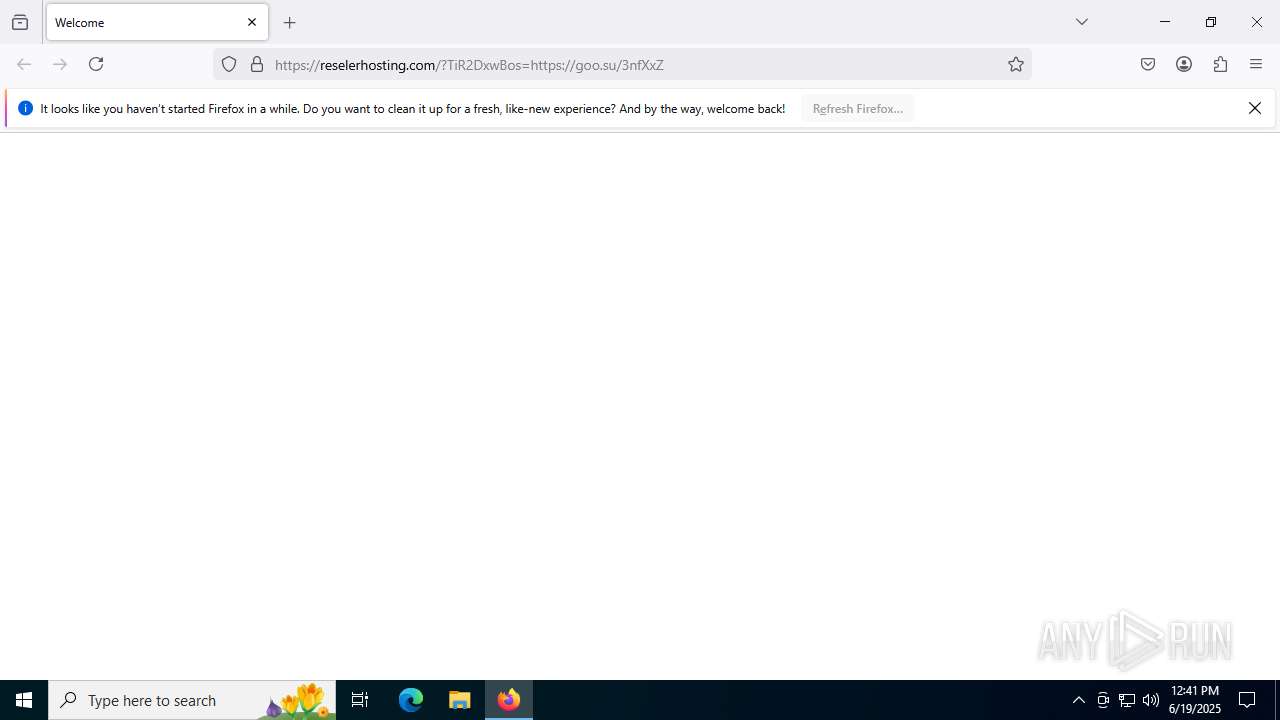
| URL: | https://goo.su/dzz6Crt |
| Full analysis: | https://app.any.run/tasks/d7449359-20bf-4fe6-89c8-4b44d8d6e52f |
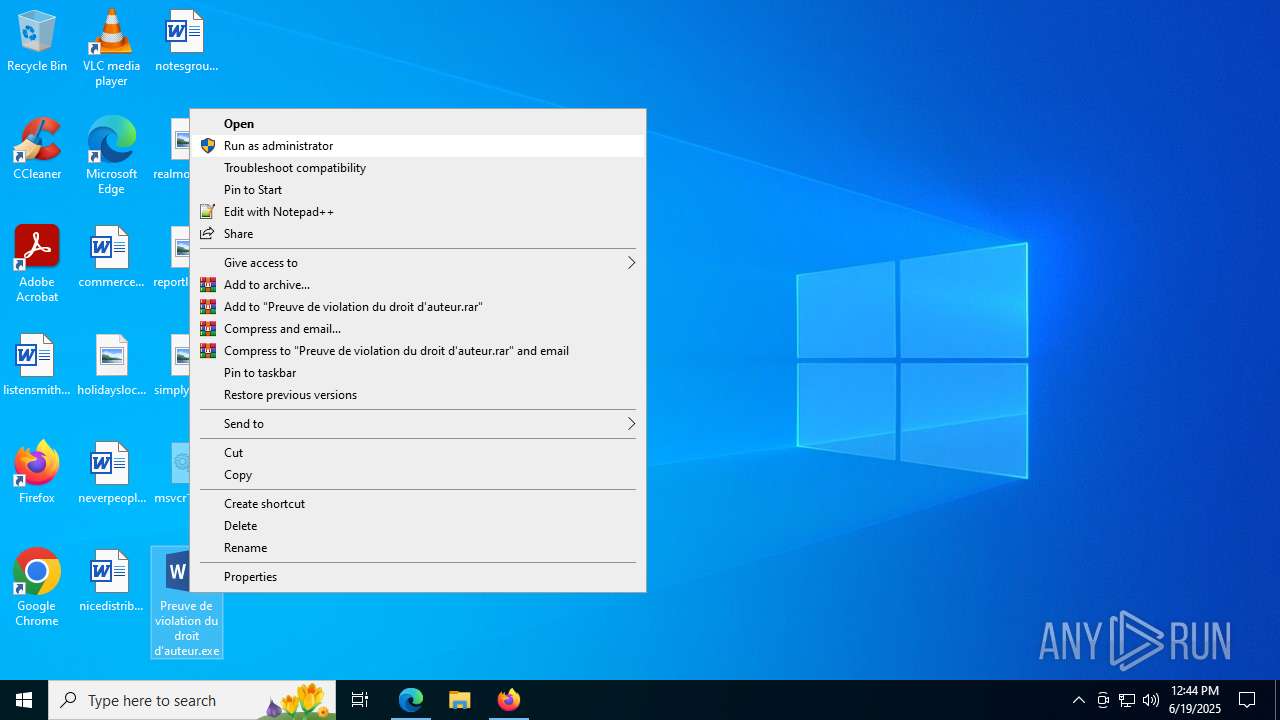
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | June 19, 2025, 12:41:35 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
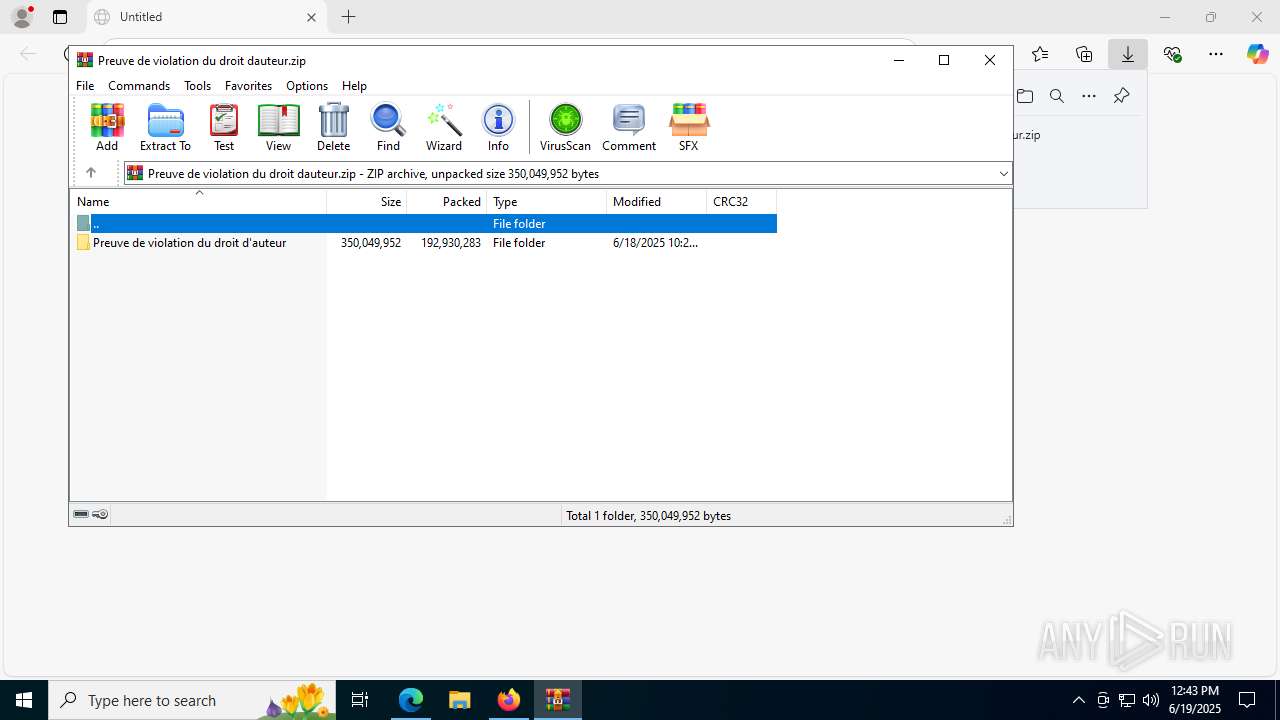
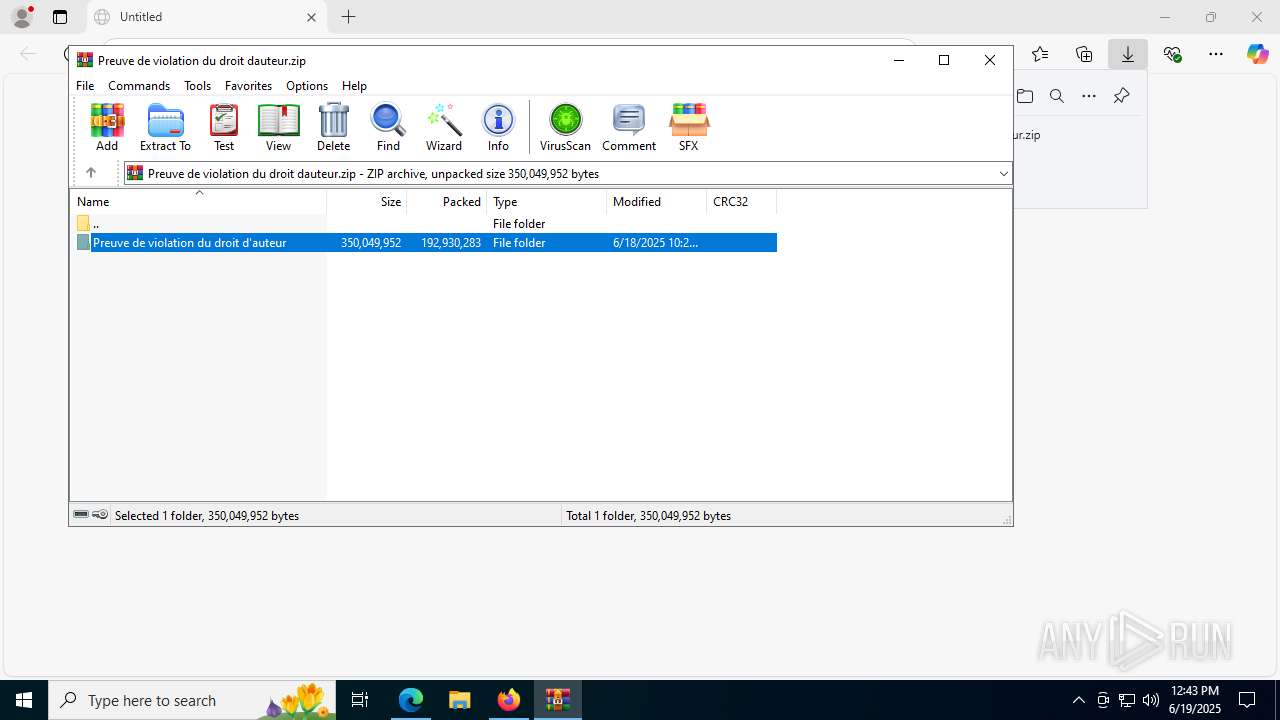
| MD5: | 23A327095A9EF9D95A6C8B99F757E8CF |
| SHA1: | 16F0EE8B8253861E236C3352EDE001255CED3B05 |
| SHA256: | 1FAA3E92AF1DB0889DA9686E19CD6F746391EE3E9CF138F15114D1065B26BDB2 |
| SSDEEP: | 3:N8rQXKBaBn:2UaBg |
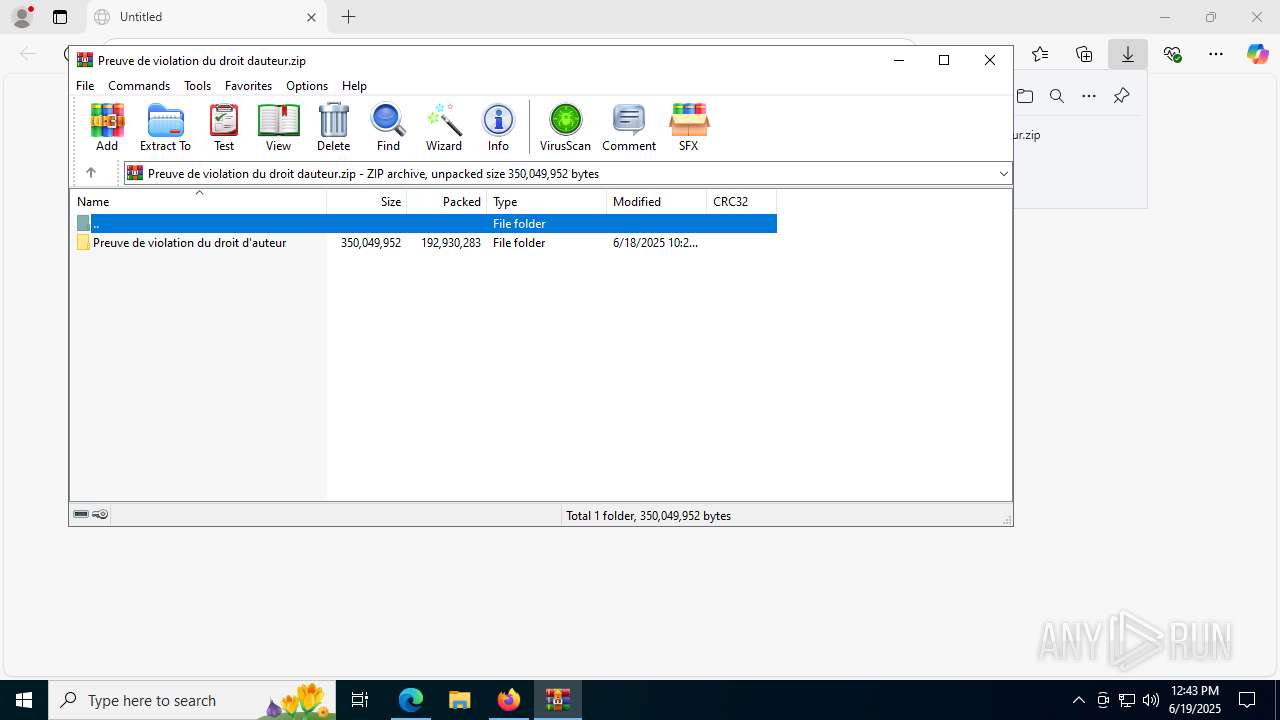
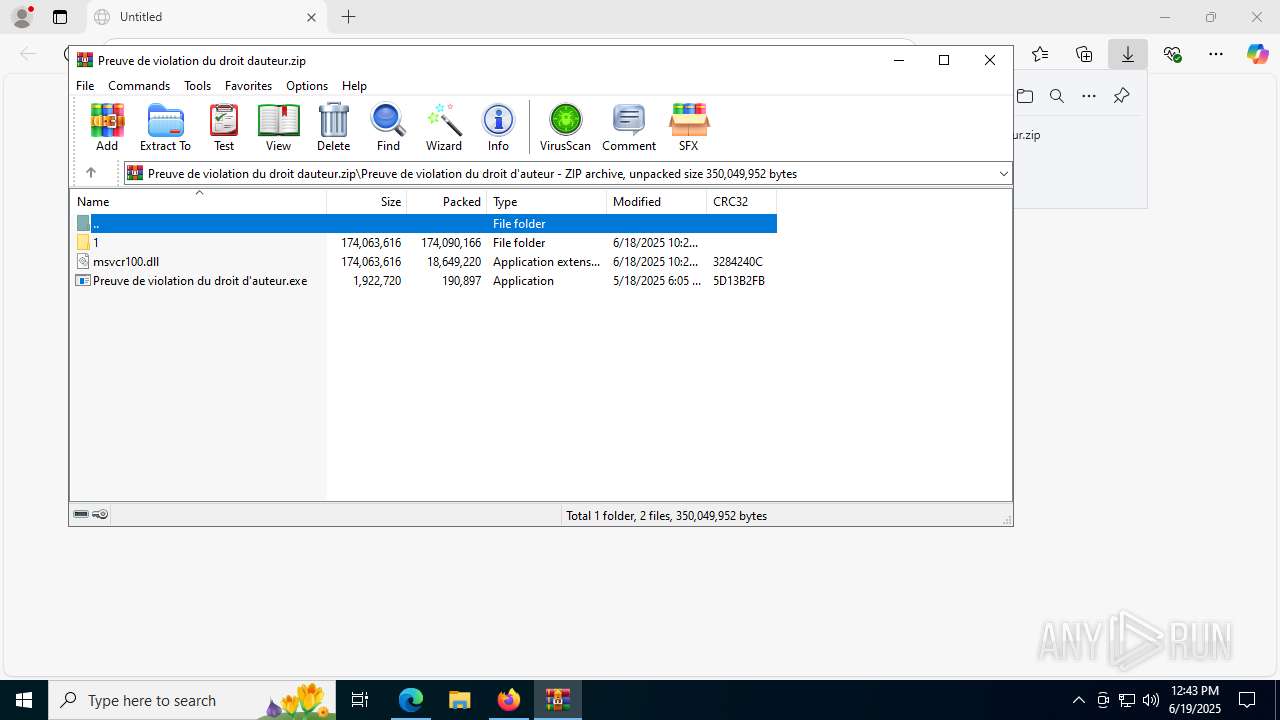
MALICIOUS
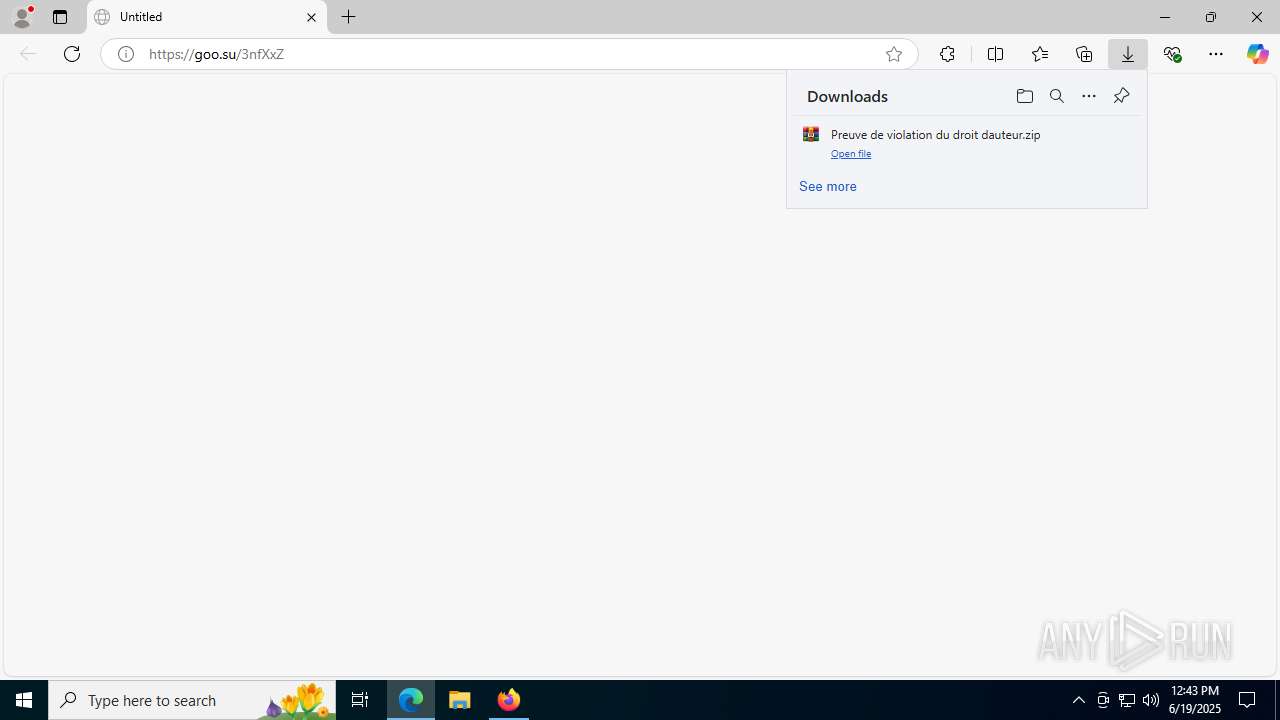
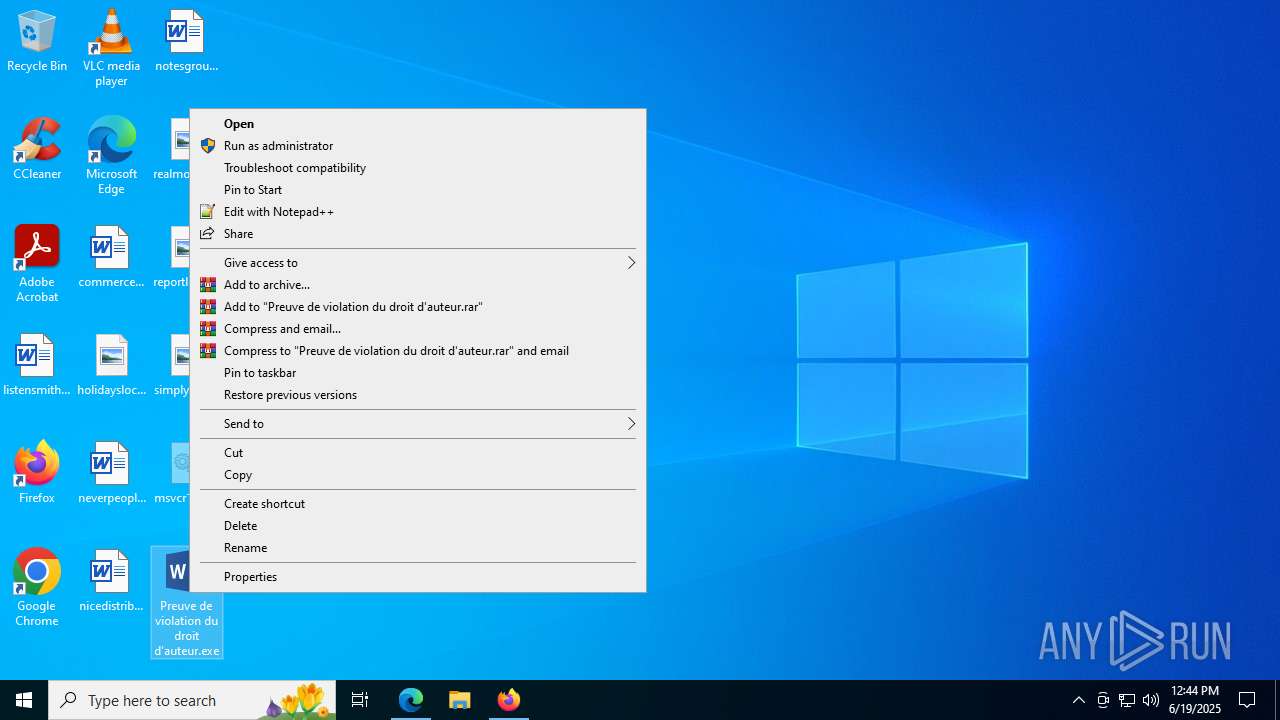
Executing a file with an untrusted certificate
- Preuve de violation du droit d'auteur.exe (PID: 8700)
- Preuve de violation du droit d'auteur.exe (PID: 8628)
- Preuve de violation du droit d'auteur.exe (PID: 4100)
- Preuve de violation du droit d'auteur.exe (PID: 8524)
- Preuve de violation du droit d'auteur.exe (PID: 480)
- Preuve de violation du droit d'auteur.exe (PID: 2380)
Actions looks like stealing of personal data
- OOBE-Maintenance.exe (PID: 8296)
- csc.exe (PID: 3836)
RHADAMANTHYS has been detected (YARA)
- OOBE-Maintenance.exe (PID: 8296)
Changes the autorun value in the registry
- reg.exe (PID: 7920)
- nO]}PY872.exe (PID: 8272)
- reg.exe (PID: 5768)
Starts Visual C# compiler
- nO]}PY872.exe (PID: 8272)
ASYNCRAT has been detected (SURICATA)
- csc.exe (PID: 3836)
SUSPICIOUS
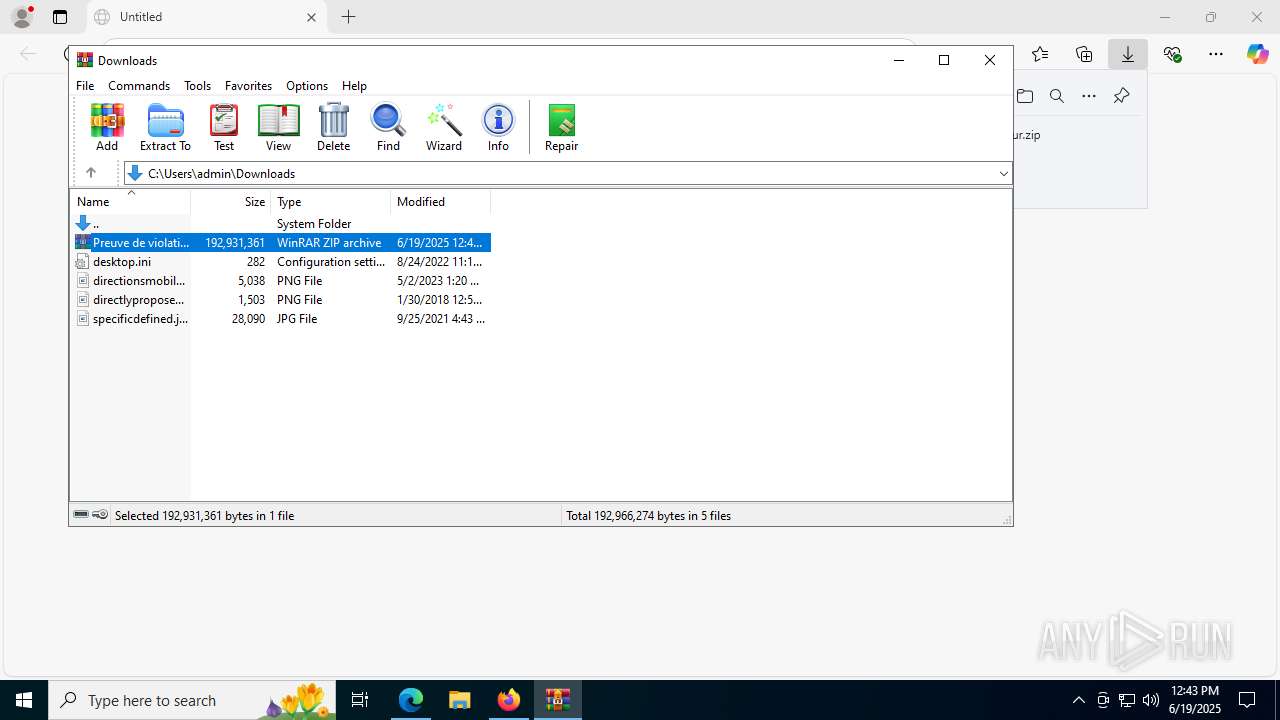
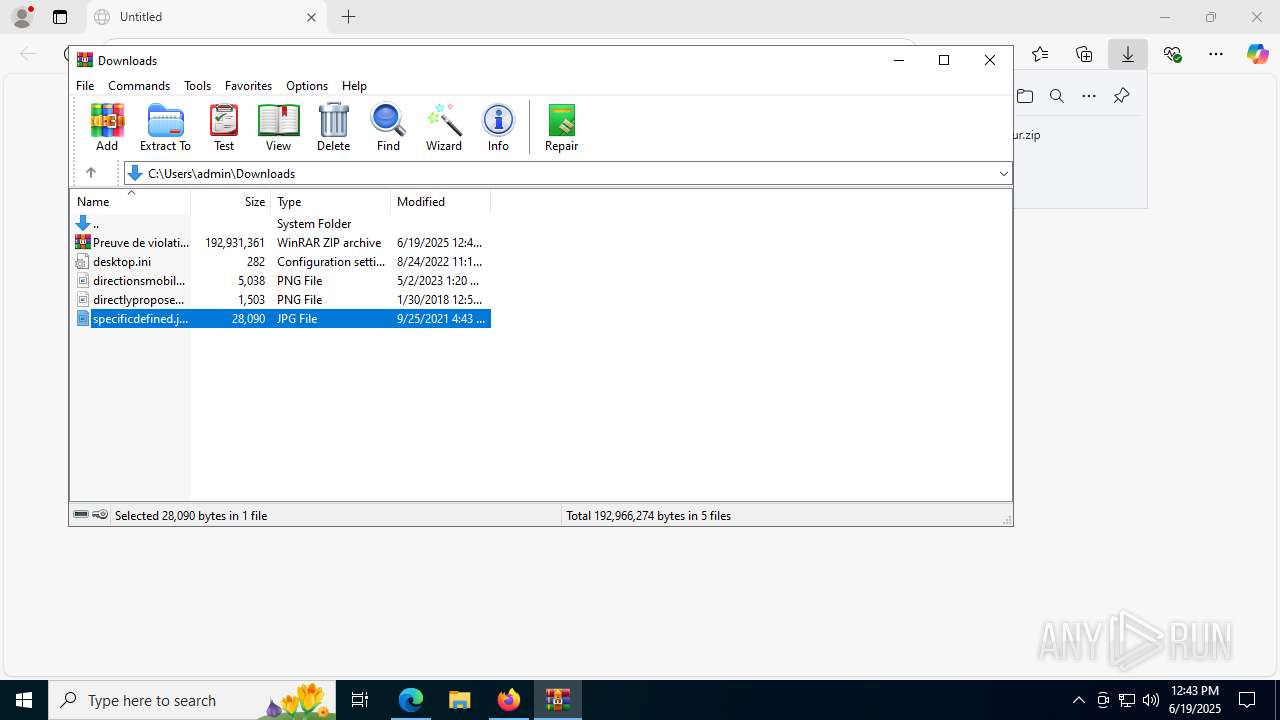
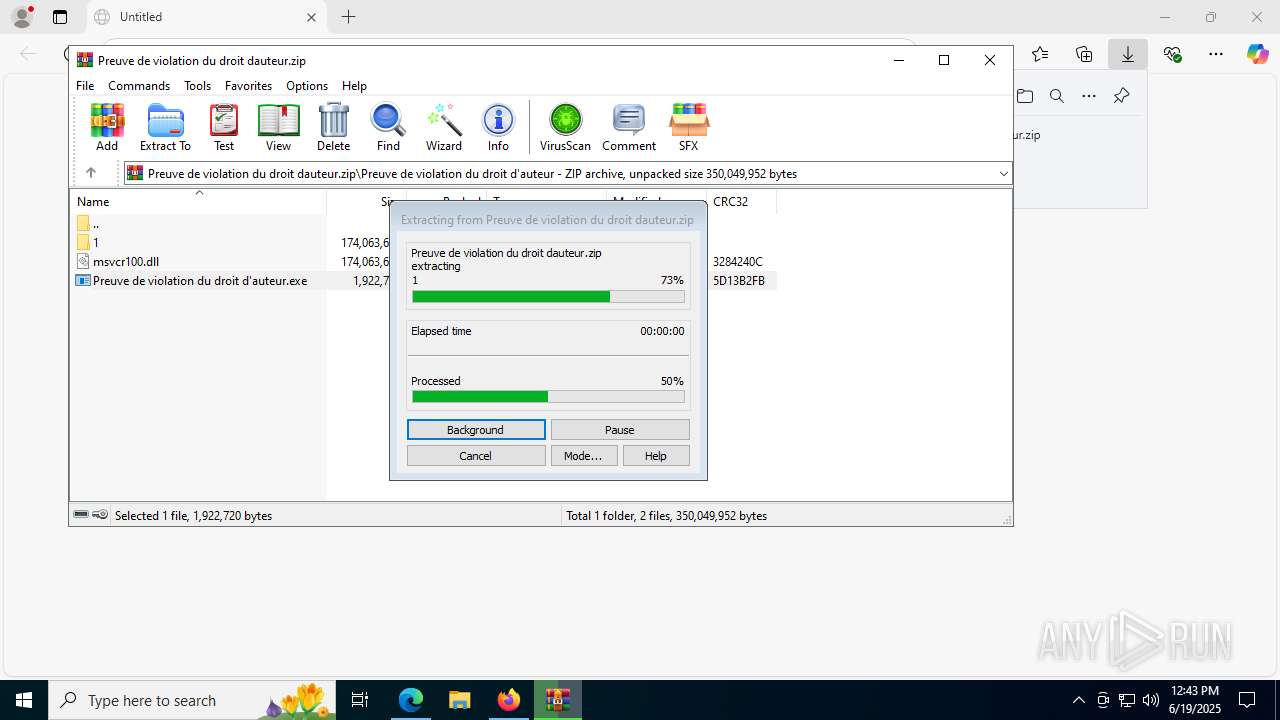
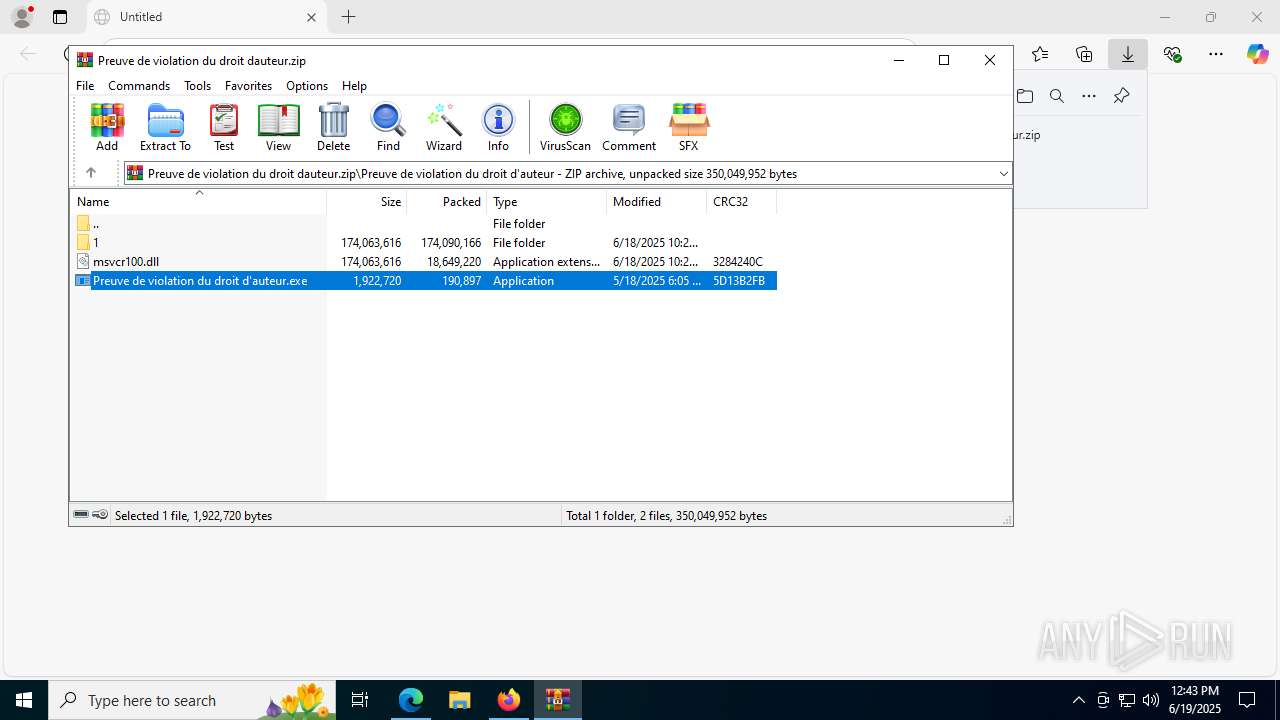
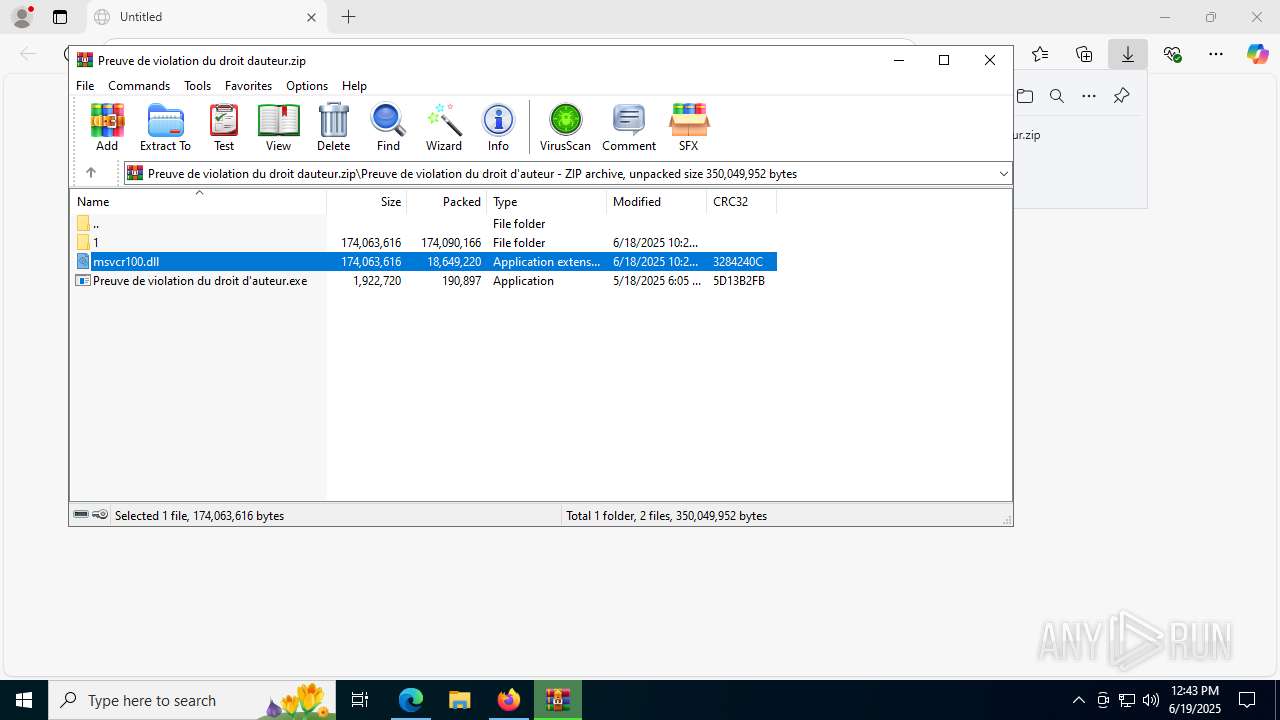
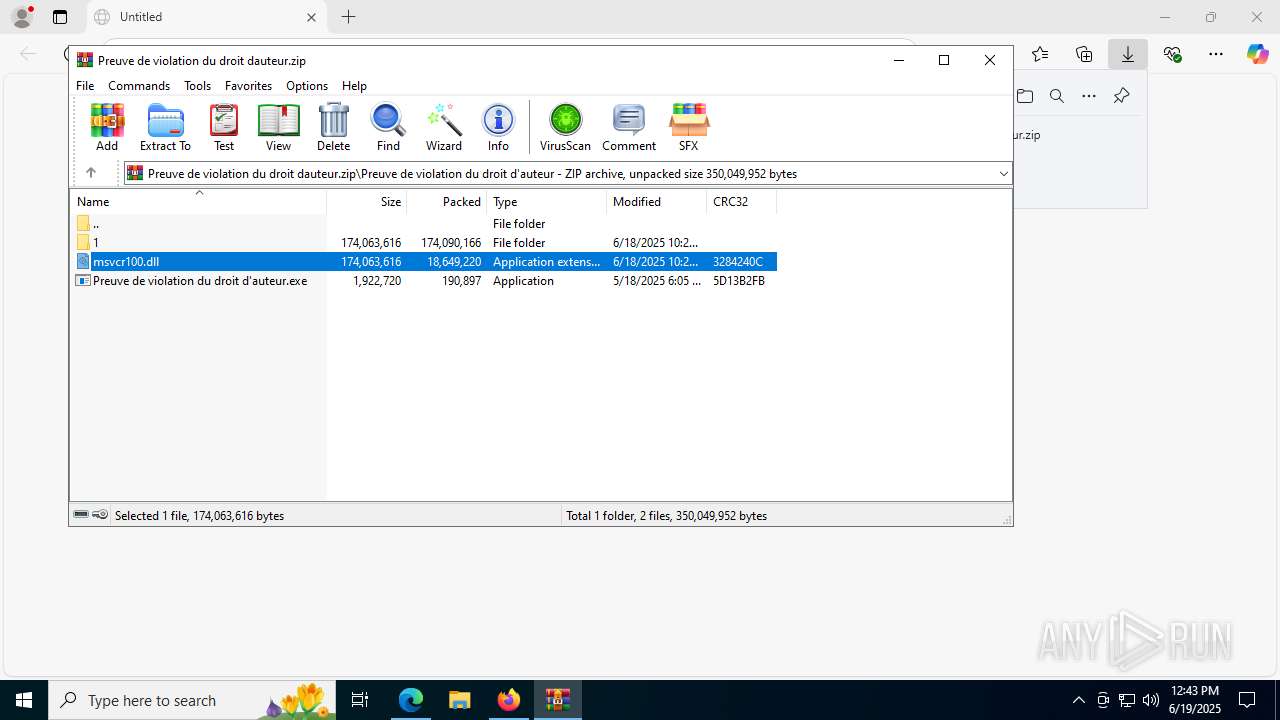
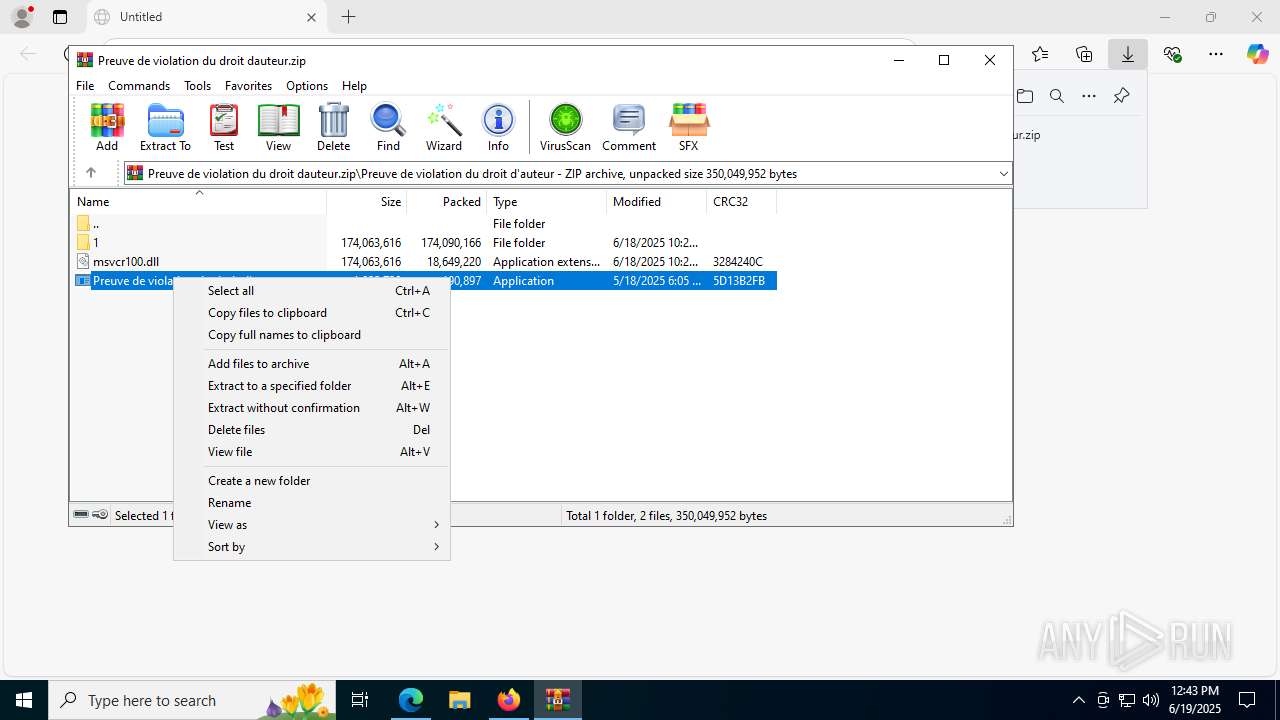
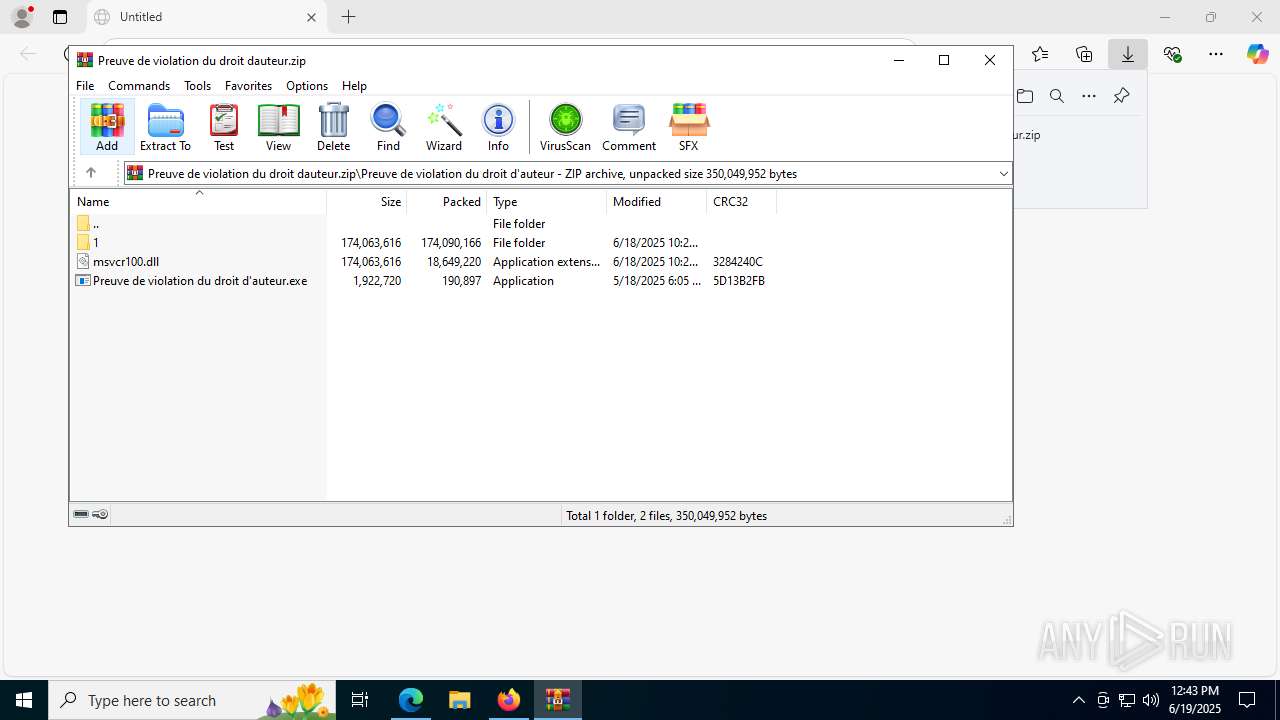
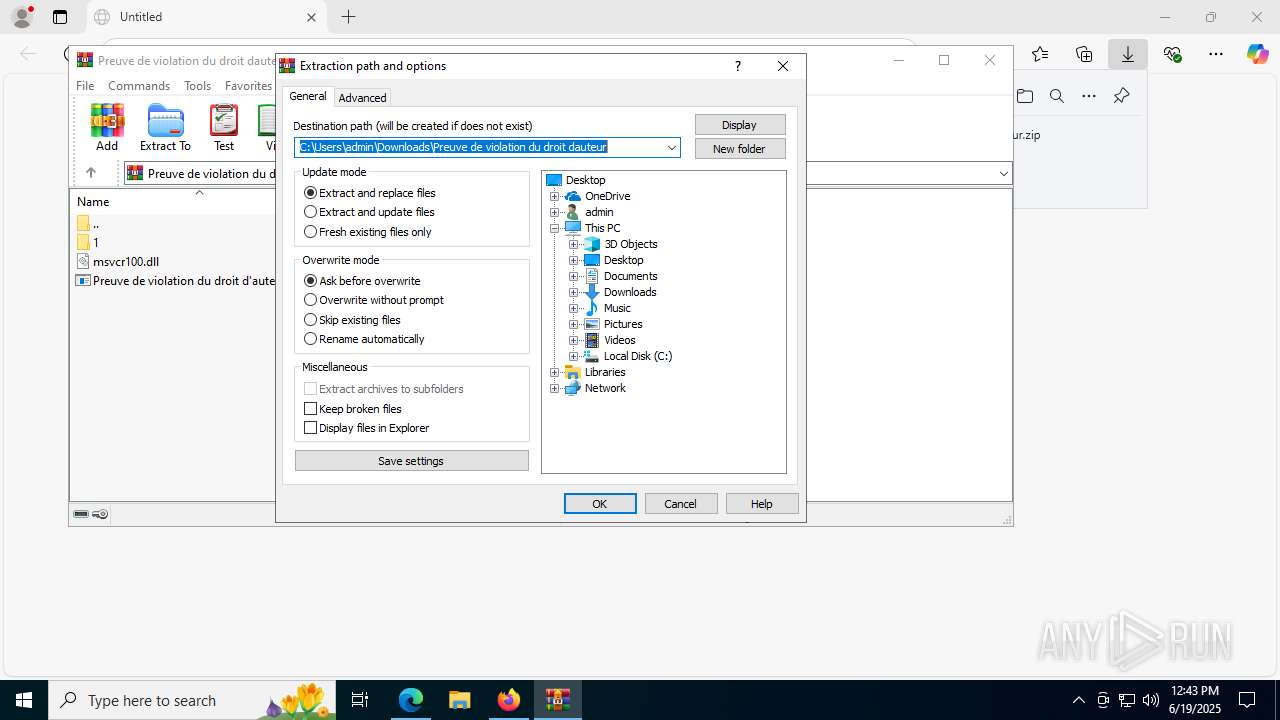
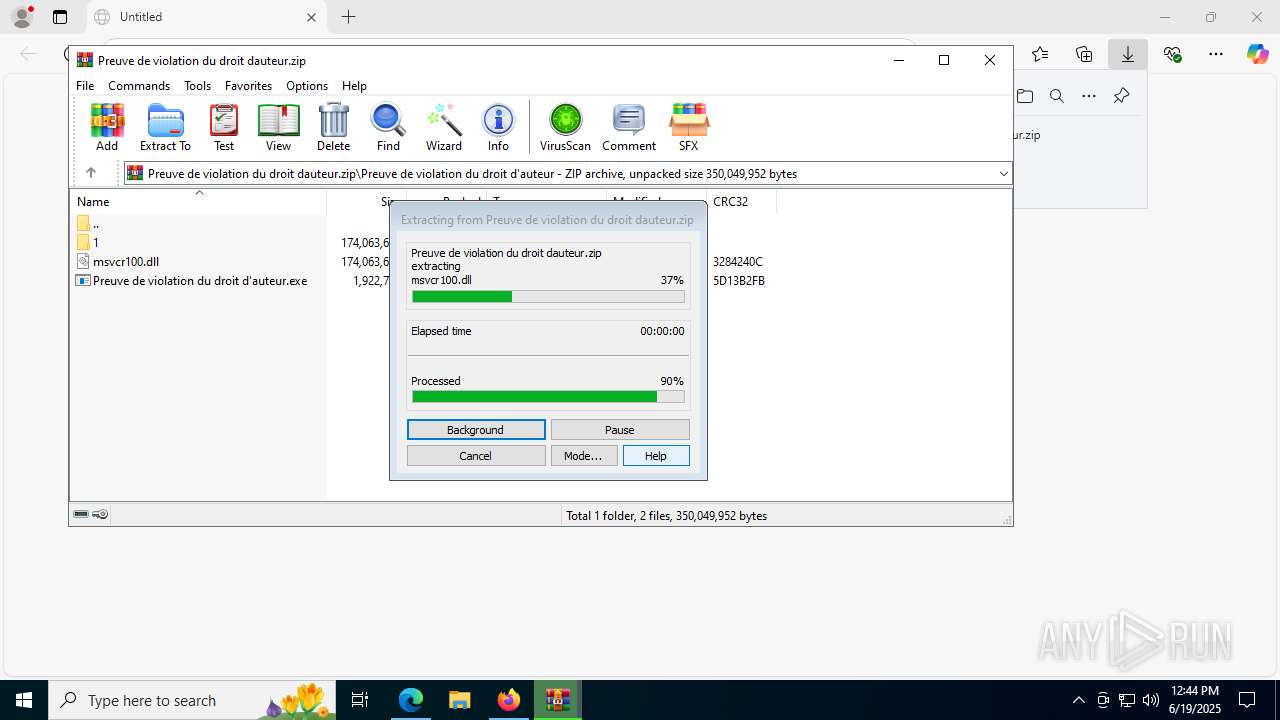
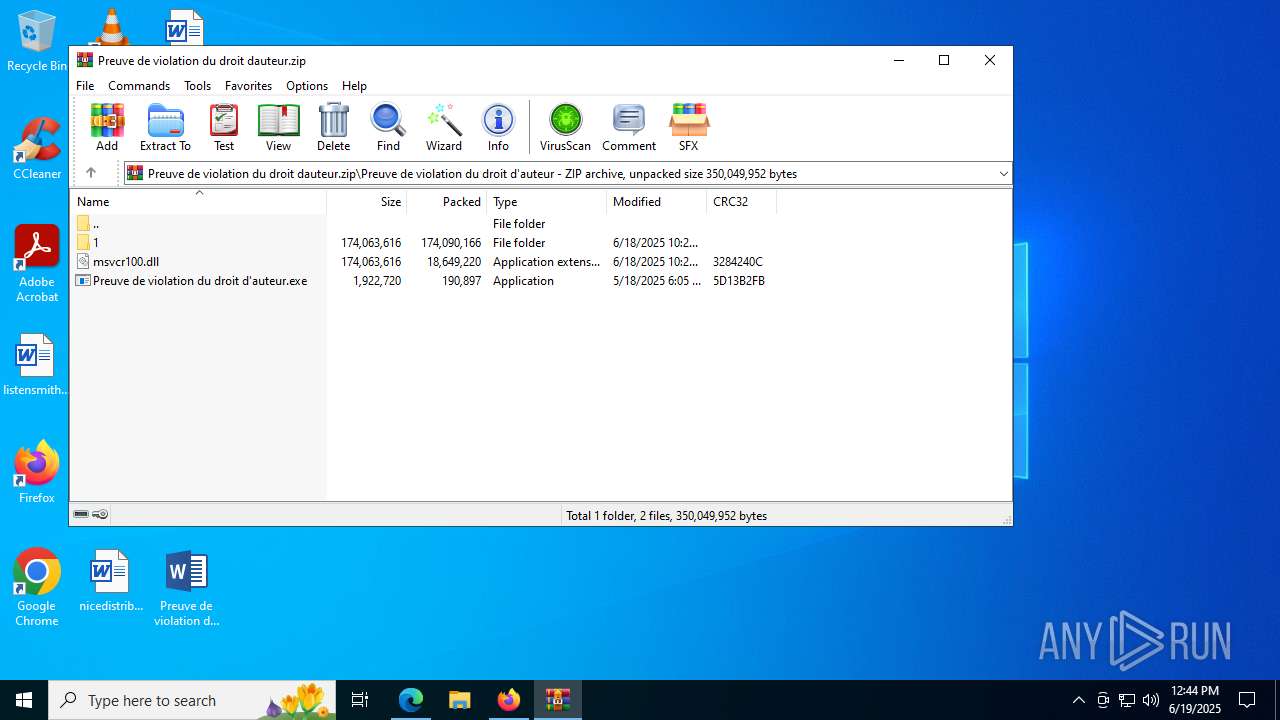
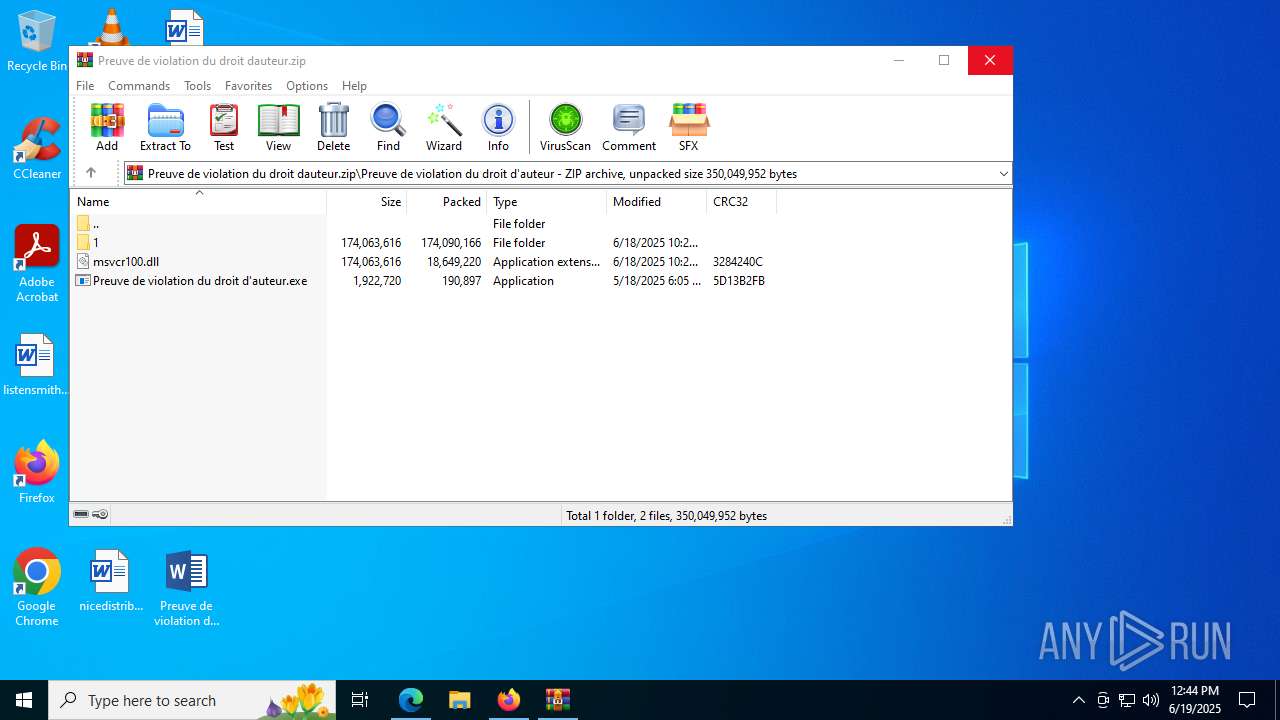
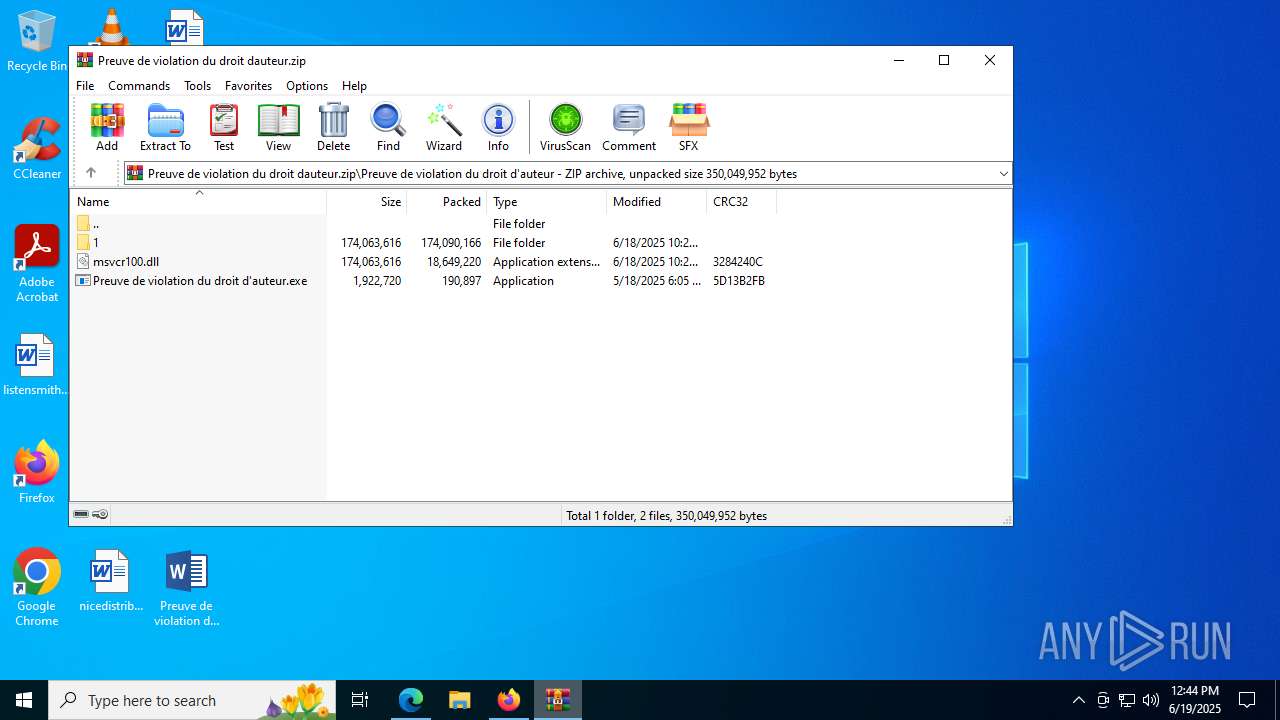
Process drops legitimate windows executable
- WinRAR.exe (PID: 7000)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 7000)
- msedge.exe (PID: 4192)
Starts a Microsoft application from unusual location
- Preuve de violation du droit d'auteur.exe (PID: 8700)
- Preuve de violation du droit d'auteur.exe (PID: 8628)
- Preuve de violation du droit d'auteur.exe (PID: 480)
- Preuve de violation du droit d'auteur.exe (PID: 4100)
- Preuve de violation du droit d'auteur.exe (PID: 8524)
- Preuve de violation du droit d'auteur.exe (PID: 2380)
Application launched itself
- Preuve de violation du droit d'auteur.exe (PID: 8700)
- Preuve de violation du droit d'auteur.exe (PID: 8628)
- Preuve de violation du droit d'auteur.exe (PID: 480)
Executes application which crashes
- Preuve de violation du droit d'auteur.exe (PID: 4100)
- Preuve de violation du droit d'auteur.exe (PID: 8524)
- Preuve de violation du droit d'auteur.exe (PID: 2380)
- OOBE-Maintenance.exe (PID: 8296)
- nO]}PY872.exe (PID: 8272)
The process checks if it is being run in the virtual environment
- OpenWith.exe (PID: 6236)
Connects to unusual port
- OpenWith.exe (PID: 6236)
- OOBE-Maintenance.exe (PID: 8296)
- wmpnscfg.exe (PID: 1056)
- dllhost.exe (PID: 6376)
- csc.exe (PID: 3836)
Multiple wallet extension IDs have been found
- OOBE-Maintenance.exe (PID: 8296)
Starts CMD.EXE for commands execution
- Preuve de violation du droit d'auteur.exe (PID: 8700)
- Preuve de violation du droit d'auteur.exe (PID: 8628)
- Preuve de violation du droit d'auteur.exe (PID: 480)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 4088)
- cmd.exe (PID: 1164)
- cmd.exe (PID: 4860)
Loads DLL from Mozilla Firefox
- OOBE-Maintenance.exe (PID: 8296)
Reads Mozilla Firefox installation path
- msedge.exe (PID: 4192)
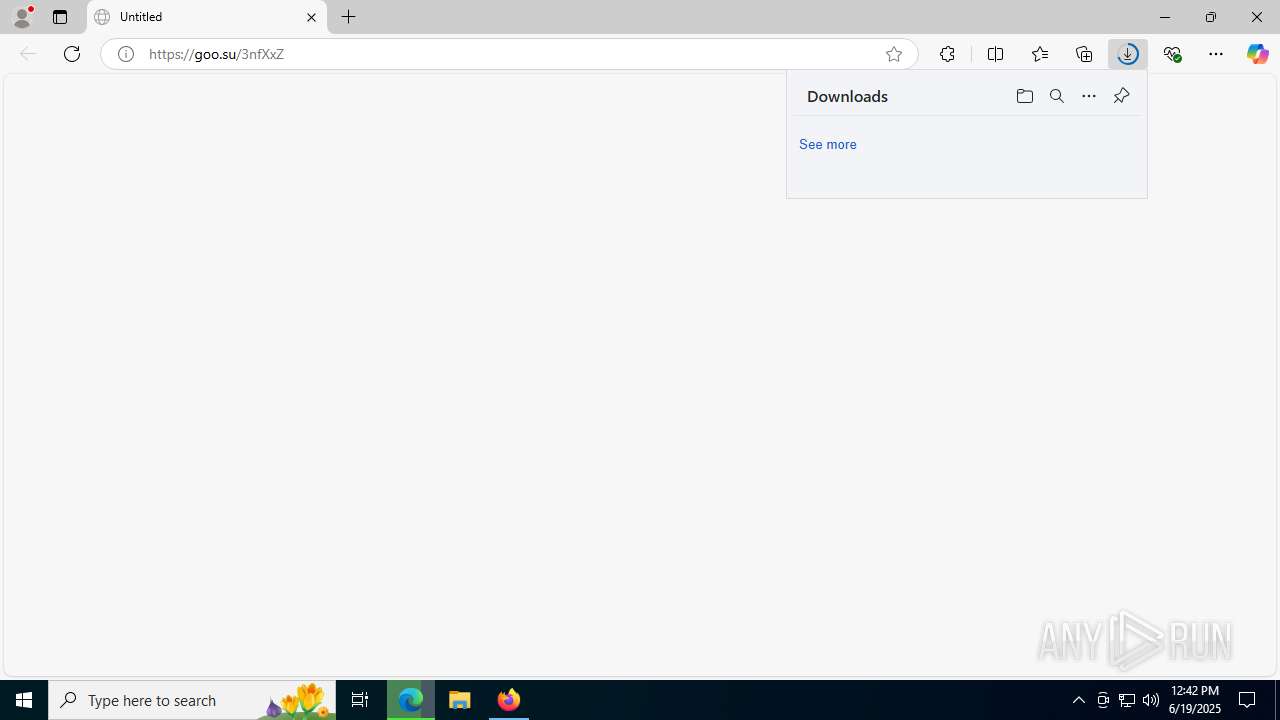
Executable content was dropped or overwritten
- OOBE-Maintenance.exe (PID: 8296)
- nO]}PY872.exe (PID: 8272)
Contacting a server suspected of hosting an CnC
- csc.exe (PID: 3836)
INFO
Application launched itself
- firefox.exe (PID: 3756)
- firefox.exe (PID: 1324)
- msedge.exe (PID: 8048)
- chrome.exe (PID: 8932)
- msedge.exe (PID: 4192)
Reads Microsoft Office registry keys
- firefox.exe (PID: 1324)
- msedge.exe (PID: 8048)
- OpenWith.exe (PID: 6688)
- WinRAR.exe (PID: 7000)
Manual execution by a user
- msedge.exe (PID: 8048)
- Preuve de violation du droit d'auteur.exe (PID: 480)
- OpenWith.exe (PID: 6236)
- OOBE-Maintenance.exe (PID: 8296)
- Preuve de violation du droit d'auteur.exe (PID: 8628)
Reads Environment values
- identity_helper.exe (PID: 9080)
- chrome.exe (PID: 8932)
- msedge.exe (PID: 4192)
Checks supported languages
- identity_helper.exe (PID: 9080)
- Preuve de violation du droit d'auteur.exe (PID: 8700)
- Preuve de violation du droit d'auteur.exe (PID: 8628)
- Preuve de violation du droit d'auteur.exe (PID: 4100)
- Preuve de violation du droit d'auteur.exe (PID: 480)
- Preuve de violation du droit d'auteur.exe (PID: 8524)
- chrome.exe (PID: 8932)
- msedge.exe (PID: 4192)
- Preuve de violation du droit d'auteur.exe (PID: 2380)
- wmpnscfg.exe (PID: 1056)
- nO]}PY872.exe (PID: 8272)
- csc.exe (PID: 3836)
Reads the computer name
- identity_helper.exe (PID: 9080)
- chrome.exe (PID: 8932)
- msedge.exe (PID: 4192)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7000)
- firefox.exe (PID: 1324)
Checks proxy server information
- slui.exe (PID: 9188)
- chrome.exe (PID: 8932)
- msedge.exe (PID: 4192)
Reads the software policy settings
- slui.exe (PID: 9188)
- csc.exe (PID: 3836)
Create files in a temporary directory
- OOBE-Maintenance.exe (PID: 8296)
- chrome.exe (PID: 8932)
- msedge.exe (PID: 4192)
Reads the machine GUID from the registry
- chrome.exe (PID: 8932)
- wmpnscfg.exe (PID: 1056)
- csc.exe (PID: 3836)
Process checks computer location settings
- chrome.exe (PID: 8932)
- msedge.exe (PID: 4192)
Process checks whether UAC notifications are on
- msedge.exe (PID: 4192)
The sample compiled with english language support
- firefox.exe (PID: 1324)
Launching a file from a Registry key
- reg.exe (PID: 7920)
- reg.exe (PID: 5768)
- nO]}PY872.exe (PID: 8272)
Creates files or folders in the user directory
- OOBE-Maintenance.exe (PID: 8296)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Rhadamanthys
(PID) Process(8296) OOBE-Maintenance.exe
C2 (1)https://hello-hayoutoa21.xyz:8866/gateway/lgxqbh0n.0sd66
Total processes
278
Monitored processes
118
Malicious processes
7
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 480 | "C:\Users\admin\Desktop\Preuve de violation du droit d'auteur.exe" | C:\Users\admin\Desktop\Preuve de violation du droit d'auteur.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Word Exit code: 2165481582 Version: 15.0.4569.1504 Modules
| |||||||||||||||
| 760 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -isForBrowser -prefsHandle 3936 -prefsLen 44823 -prefMapHandle 3940 -prefMapSize 272997 -jsInitHandle 3944 -jsInitLen 247456 -parentBuildID 20250227124745 -ipcHandle 3952 -initialChannelId {8107a9b1-5cbb-425f-b640-f145179e7814} -parentPid 1324 -crashReporter "\\.\pipe\gecko-crash-server-pipe.1324" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 5 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 136.0 Modules
| |||||||||||||||
| 1040 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --extension-process --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=10 --field-trial-handle=3868,i,7692355262794350123,18258658495199655890,262144 --variations-seed-version --mojo-platform-channel-handle=3876 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1056 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | OOBE-Maintenance.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Version: 12.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1068 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | OOBE-Maintenance.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 27768 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1164 | cmd.exe /C reg add "HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\Run" /v "CriticalUpdater3" /t REG_SZ /d "rundll32.exe \"C:\Users\admin\Documents\Sensor57380.dll\",EntryPoint" /f & exit | C:\Windows\SysWOW64\cmd.exe | — | Preuve de violation du droit d'auteur.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1180 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=2524,i,5839716830681305496,17787457773810218188,262144 --variations-seed-version --mojo-platform-channel-handle=2516 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1268 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --always-read-main-dll --field-trial-handle=4020,i,854377730345549860,18160594760234845381,262144 --variations-seed-version --mojo-platform-channel-handle=4004 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
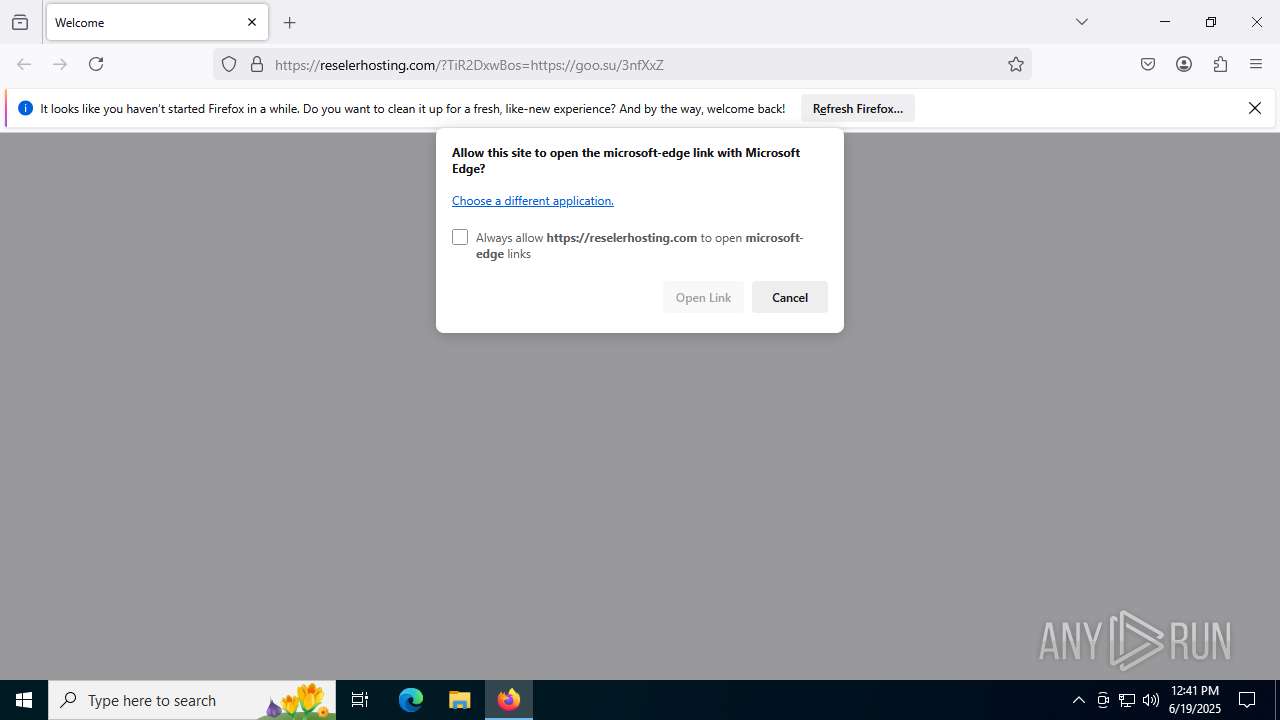
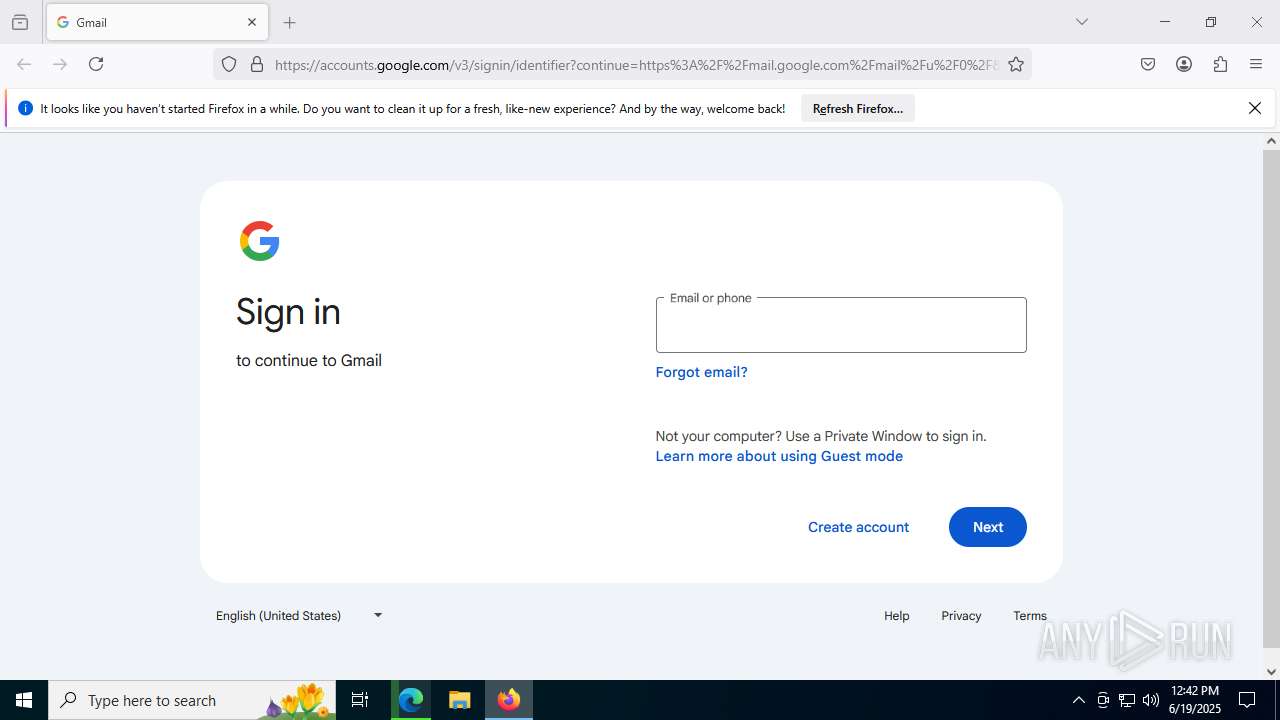
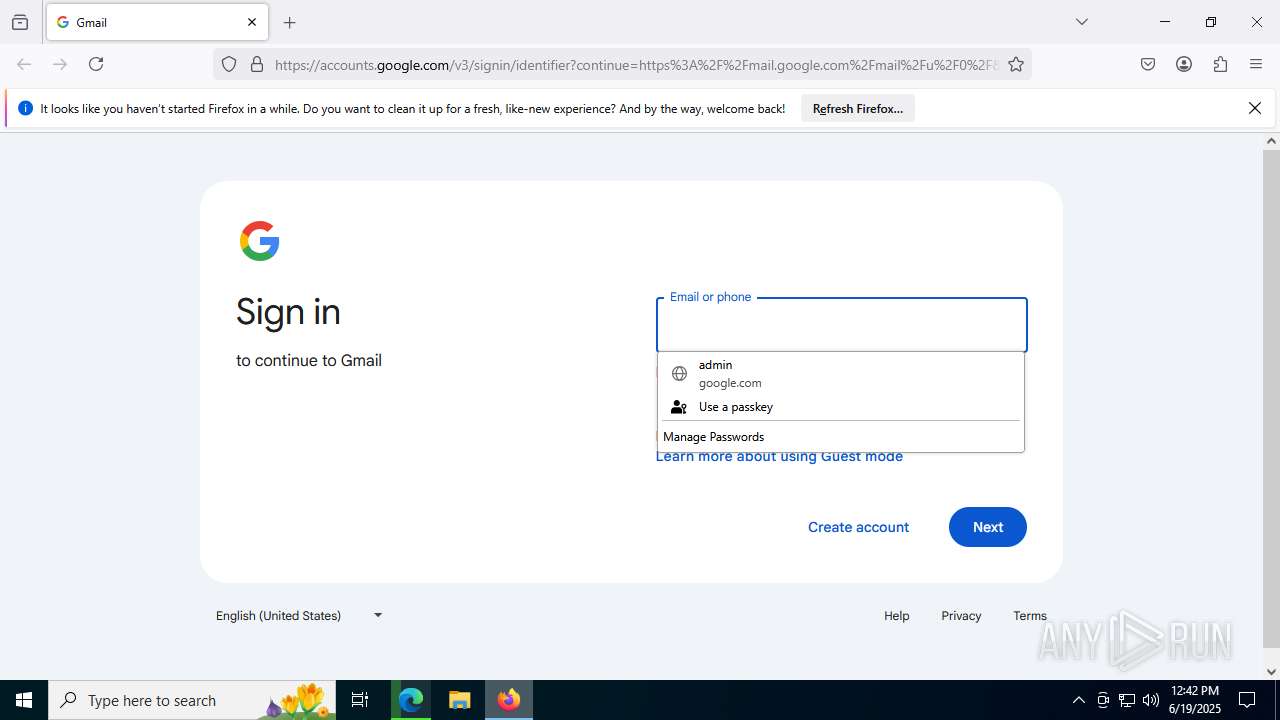
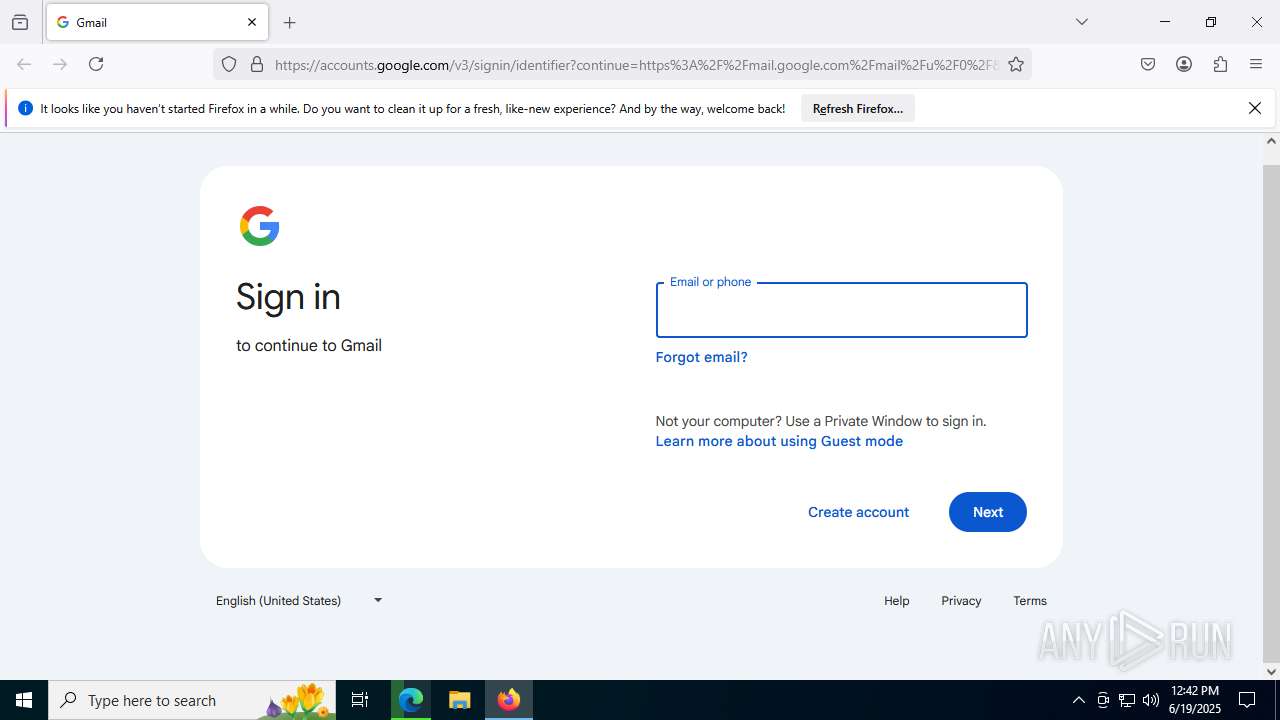
| 1324 | "C:\Program Files\Mozilla Firefox\firefox.exe" https://goo.su/dzz6Crt | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 136.0 Modules
| |||||||||||||||
| 1560 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6432,i,5839716830681305496,17787457773810218188,262144 --variations-seed-version --mojo-platform-channel-handle=5936 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
39 068
Read events
38 984
Write events
70
Delete events
14
Modification events
| (PID) Process: | (1324) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (8048) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (8048) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (8048) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (8048) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393954 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {E4486059-3932-4DC4-B25F-6910A6A0C09C} | |||
| (PID) Process: | (8048) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (8048) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 0B0EB45A82962F00 | |||
| (PID) Process: | (8048) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393954 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {D5C9C297-8287-4ACA-B81C-A8A03D84055E} | |||
| (PID) Process: | (8048) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 24EAD95A82962F00 | |||
| (PID) Process: | (8048) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
Executable files
8
Suspicious files
350
Text files
158
Unknown types
268
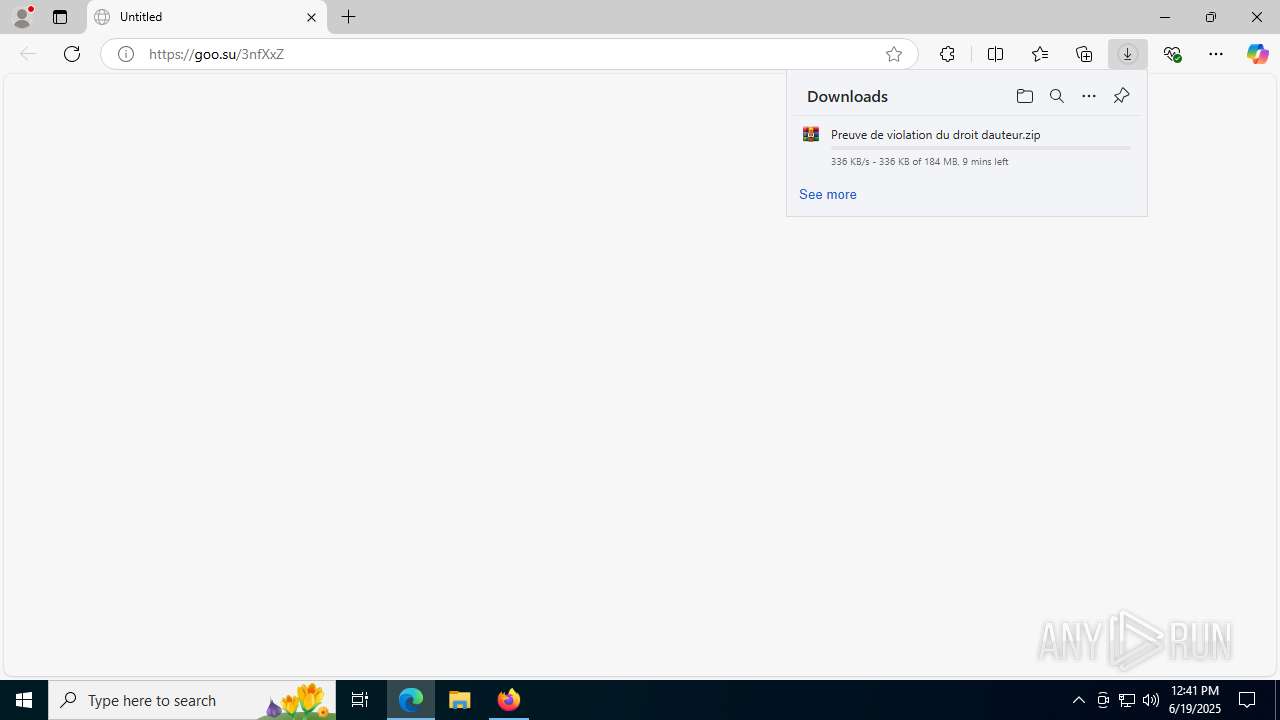
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1324 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 1324 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs.js | text | |
MD5:A15CE099996615F08EA6ED1A092036A3 | SHA256:608AD35EF5428E2236F85EFB42B244F597FC5EBE1E8A30232A4C4E37F4BBC037 | |||
| 1324 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\protections.sqlite-journal | binary | |
MD5:D59582ABEDC760963620793909CE1D36 | SHA256:6A3F81A53AE3C75ED1C3852D4F676741AF67A2766456D211488C81C369CD35A5 | |||
| 1324 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\bounce-tracking-protection.sqlite-journal | binary | |
MD5:5F16E0C8222991A47B690111644FCB61 | SHA256:6F62B31187084650480040BA7DE5A6C807ED94E837FA0629B72BD221147DD6A8 | |||
| 1324 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\datareporting\glean\db\data.safe.tmp | dbf | |
MD5:EFCC9E68E66381B0D3A720A07507C821 | SHA256:0B0AB1E02E6E3991414BA1817EF69A56090206F49E16266C9F6B4E6E3E3C4B8F | |||
| 1324 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\datareporting\glean\db\data.safe.bin | dbf | |
MD5:EFCC9E68E66381B0D3A720A07507C821 | SHA256:0B0AB1E02E6E3991414BA1817EF69A56090206F49E16266C9F6B4E6E3E3C4B8F | |||
| 1324 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\2918063365piupsah.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 1324 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\activity-stream.contile.json | binary | |
MD5:884935BC0D9FE1AF6F7F2FD5AB900C11 | SHA256:9597B0B43FA48C17B309B21D6E92604D619A25EC9D96ABC7FA39B5693131C055 | |||
| 1324 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs-1.js | text | |
MD5:A15CE099996615F08EA6ED1A092036A3 | SHA256:608AD35EF5428E2236F85EFB42B244F597FC5EBE1E8A30232A4C4E37F4BBC037 | |||
| 1324 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-wal | binary | |
MD5:4B57A335639E079B001E3BA27ECA6440 | SHA256:A77911FAB215F149F90F17858EBD39AC43CDEF0D7BD1262B2C99D81416D6BBFE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
55
TCP/UDP connections
185
DNS requests
274
Threats
29
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1324 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
1324 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
1324 | firefox.exe | POST | 200 | 142.250.185.99:80 | http://o.pki.goog/s/wr3/FIY | unknown | — | — | whitelisted |
1324 | firefox.exe | POST | 200 | 142.250.185.99:80 | http://o.pki.goog/s/wr3/azY | unknown | — | — | whitelisted |
1324 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
1324 | firefox.exe | POST | 200 | 142.250.185.99:80 | http://o.pki.goog/s/wr3/azY | unknown | — | — | whitelisted |
1324 | firefox.exe | POST | 200 | 142.250.185.99:80 | http://o.pki.goog/s/wr3/azY | unknown | — | — | whitelisted |
1324 | firefox.exe | POST | 200 | 142.250.185.99:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
1324 | firefox.exe | POST | 200 | 2.16.206.143:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
1324 | firefox.exe | POST | 200 | 2.16.206.143:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1508 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1324 | firefox.exe | 34.160.144.191:443 | content-signature-2.cdn.mozilla.net | GOOGLE | US | whitelisted |
1324 | firefox.exe | 104.26.3.56:443 | goo.su | CLOUDFLARENET | US | suspicious |
1324 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
1324 | firefox.exe | 34.36.137.203:443 | contile.services.mozilla.com | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
1324 | firefox.exe | 34.149.100.209:443 | firefox.settings.services.mozilla.com | GOOGLE | US | whitelisted |
1324 | firefox.exe | 142.250.185.99:80 | o.pki.goog | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
content-signature-2.cdn.mozilla.net |
| whitelisted |
content-signature-chains.prod.autograph.services.mozaws.net |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
goo.su |
| unknown |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
spocs.getpocket.com |
| whitelisted |
mc.prod.ads.prod.webservices.mozgcp.net |
| whitelisted |
firefox.settings.services.mozilla.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2200 | svchost.exe | Misc activity | ET INFO Observed URL Shortener Service Domain in DNS Lookup (goo .su) |
2200 | svchost.exe | Misc activity | ET INFO Observed URL Shortener Service Domain in DNS Lookup (goo .su) |
2200 | svchost.exe | Misc activity | ET INFO Observed URL Shortener Service Domain in DNS Lookup (goo .su) |
2200 | svchost.exe | Misc activity | INFO [ANY.RUN] Possible short link service (goo .su) |
2200 | svchost.exe | Misc activity | INFO [ANY.RUN] Possible short link service (goo .su) |
2200 | svchost.exe | Misc activity | INFO [ANY.RUN] Possible short link service (goo .su) |
1324 | firefox.exe | Misc activity | ET INFO Observed URL Shortener Service Domain (goo .su in TLS SNI) |
1324 | firefox.exe | Misc activity | ET INFO Observed URL Shortener Service Domain (goo .su in TLS SNI) |
5724 | msedge.exe | Misc activity | ET INFO Observed URL Shortener Service Domain in DNS Lookup (goo .su) |
5724 | msedge.exe | Misc activity | INFO [ANY.RUN] Possible short link service (goo .su) |
Process | Message |
|---|---|
chrome.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\chr98B7.tmp directory exists )
|
msedge.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\chrB5C5.tmp directory exists )
|