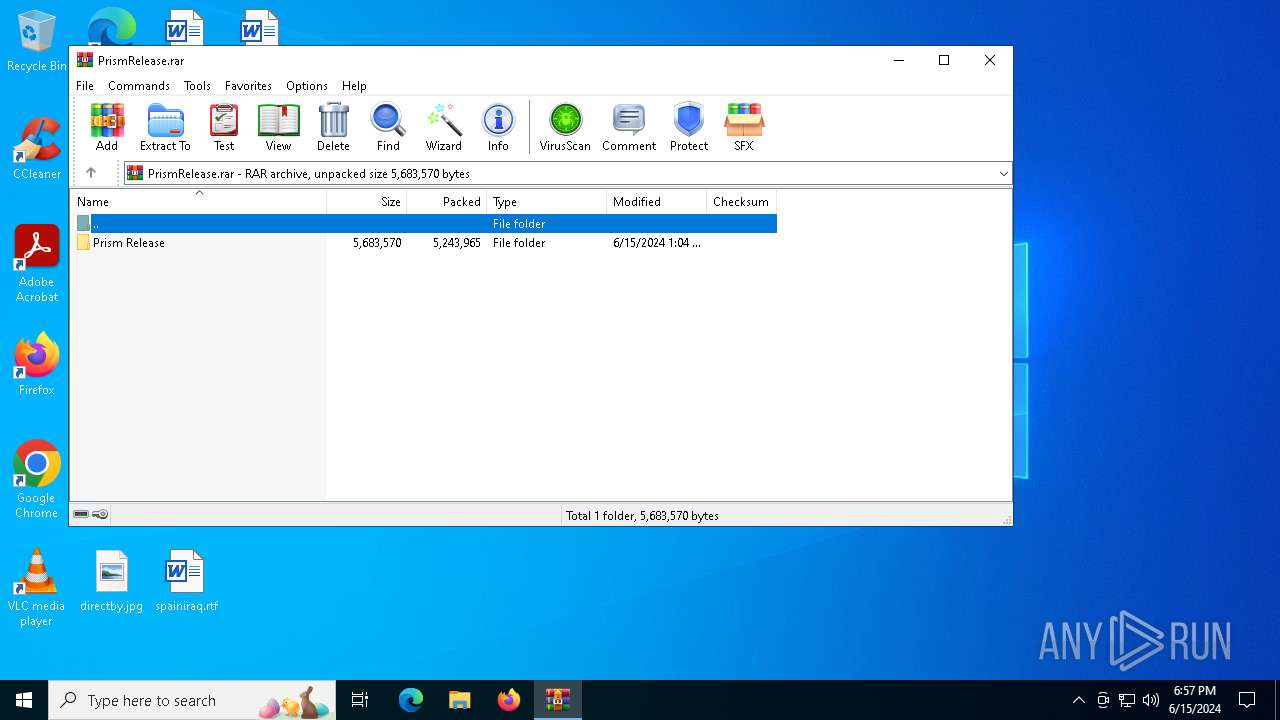
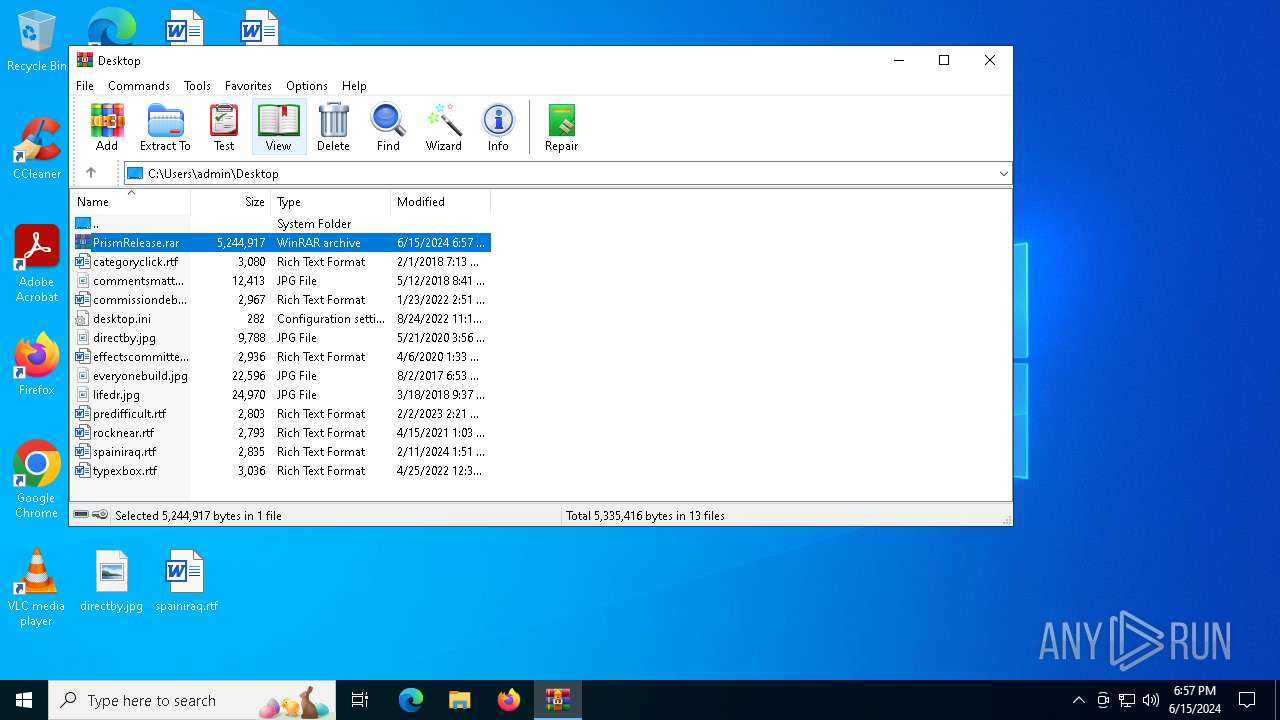
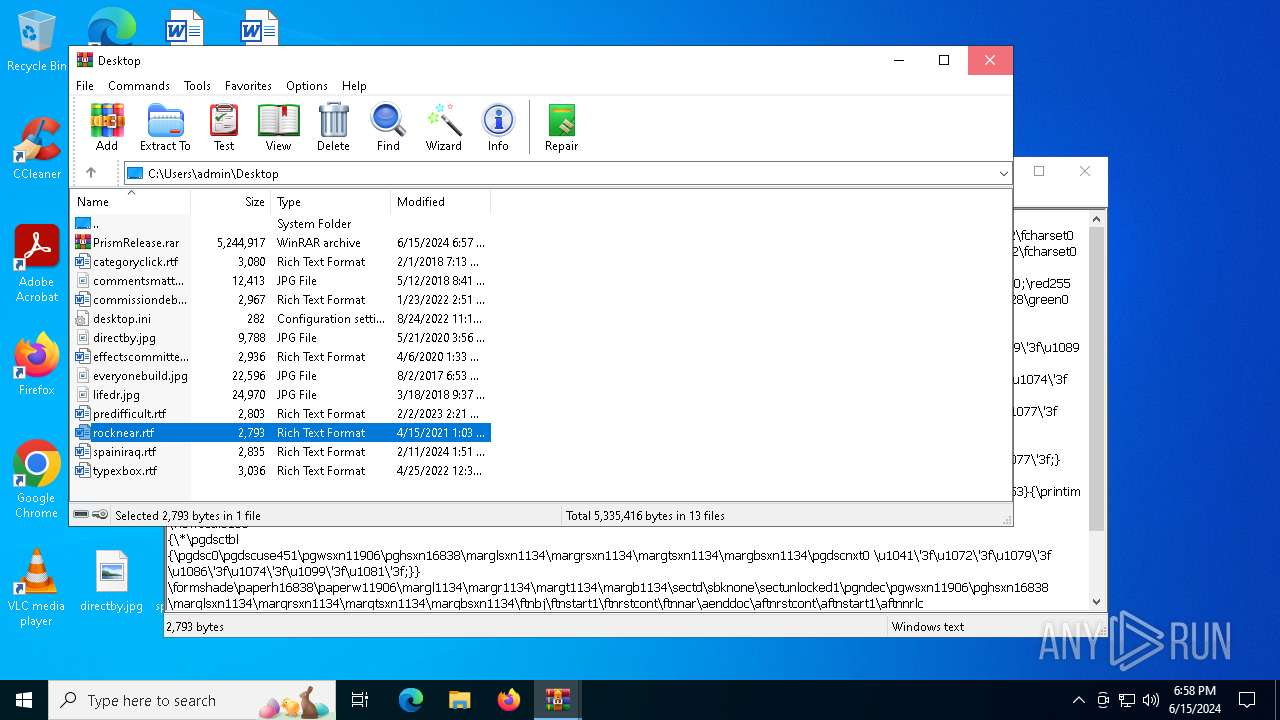
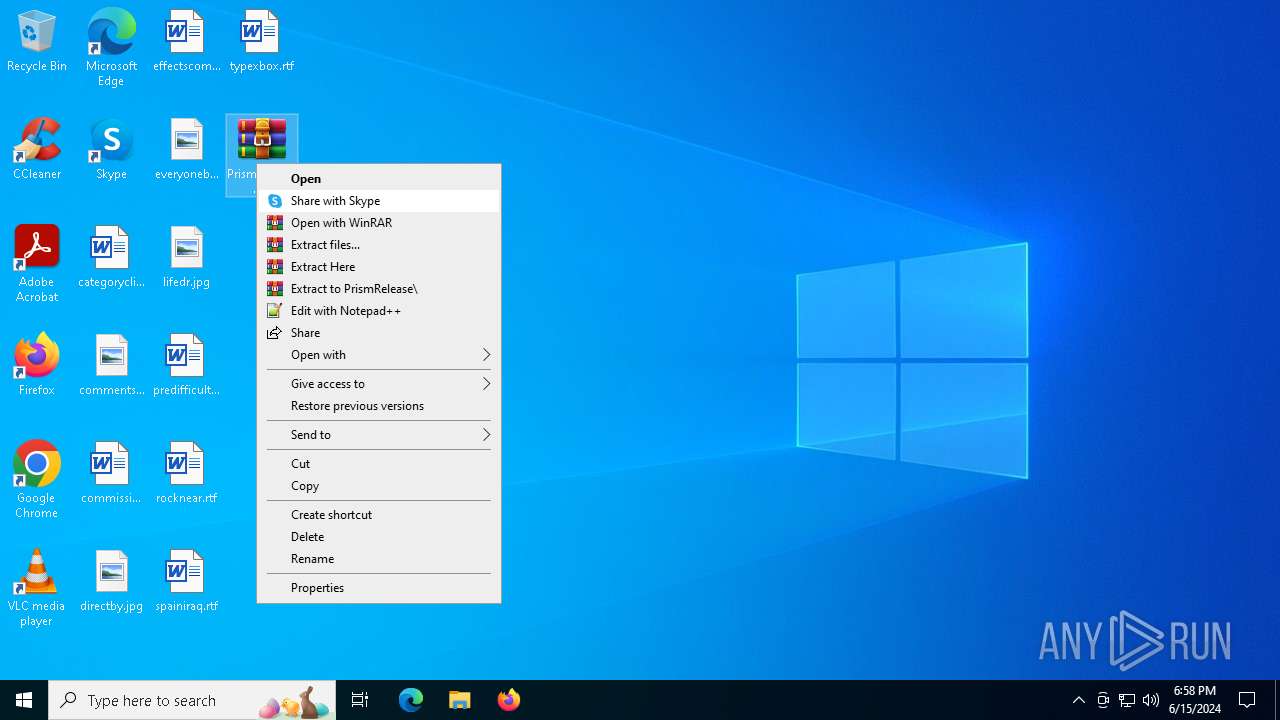
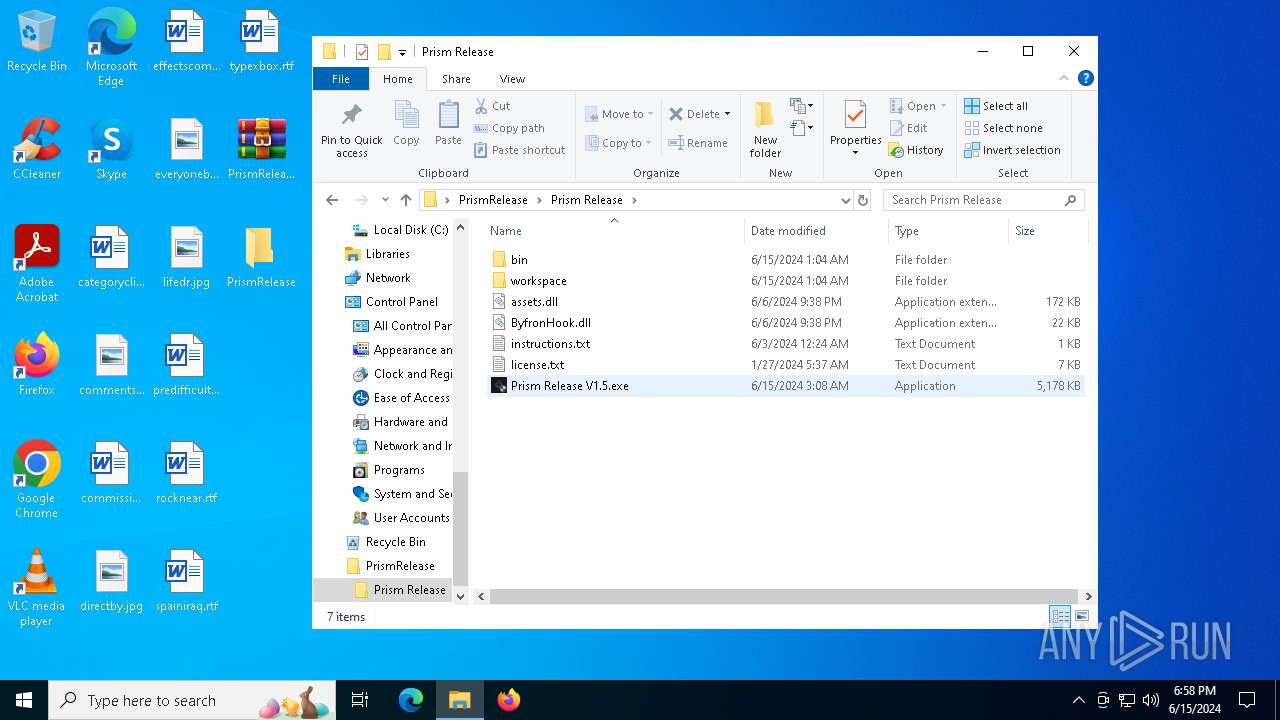
| File name: | PrismRelease.rar |
| Full analysis: | https://app.any.run/tasks/4814b473-d7b5-403d-9ce5-bd9c2bcb2ece |
| Verdict: | Malicious activity |
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
| Analysis date: | June 15, 2024, 18:57:28 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 2457EB120E8FBEF34C97CEF775362CC9 |
| SHA1: | 547D2A58C06FEBE45BA1F0DEABDF68B759F40029 |
| SHA256: | 1F4FBB86E1E513B8BED2FA7A011D094E9F4DBB213E7AE8C34693C6F5343442C3 |
| SSDEEP: | 98304:rmaVnBH+BeIfSatKA2SGgEZ5vb+uNReXyn5VNj0HqzVYOQe5yMGaMZysAHp6YU0p:WEYEruy |
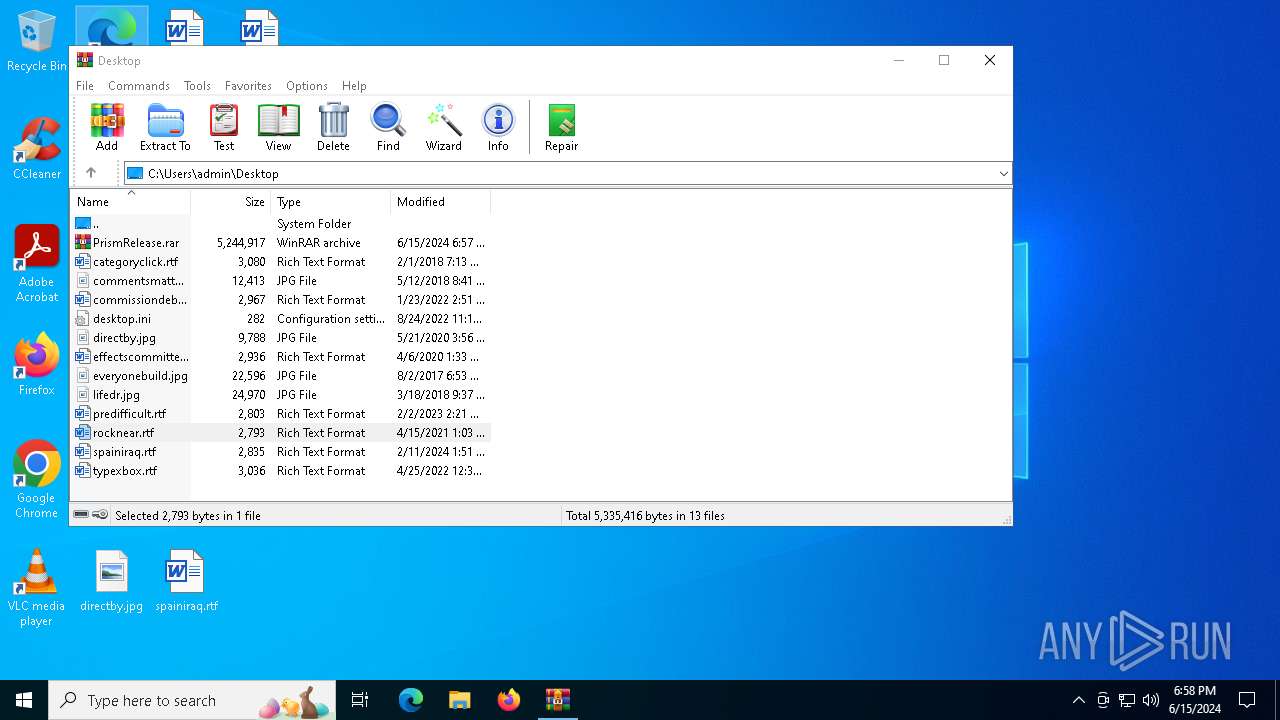
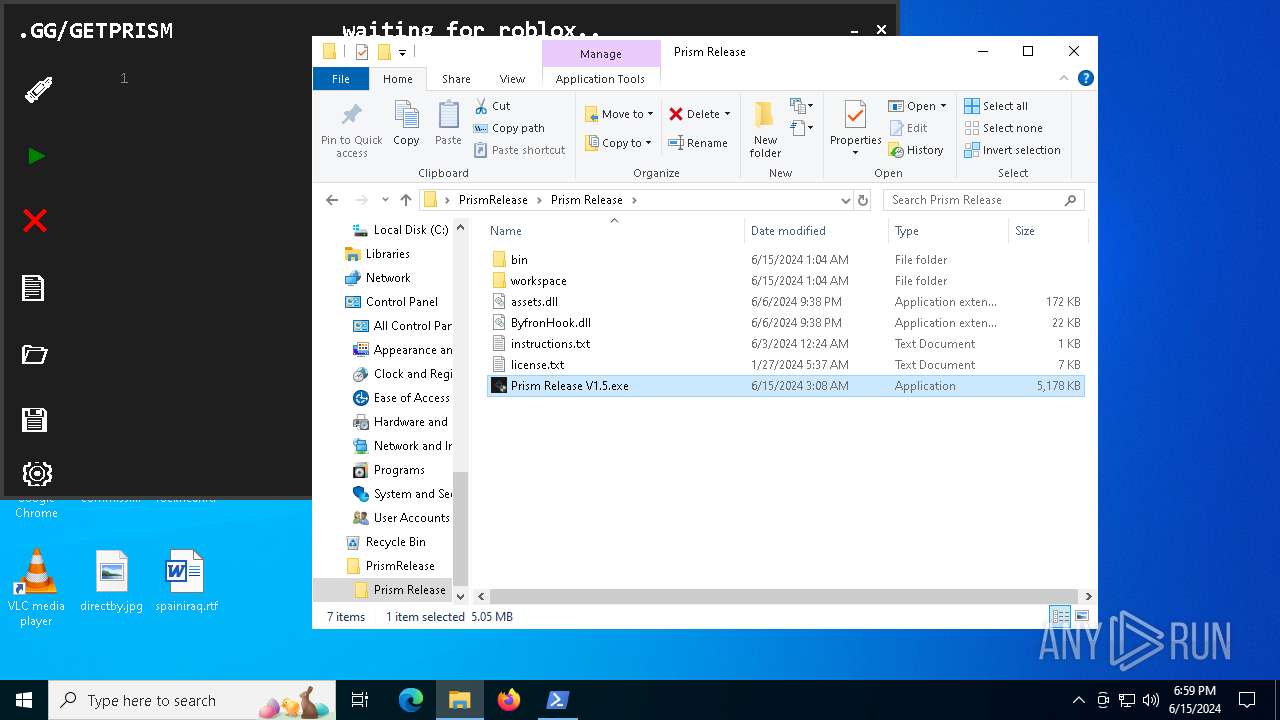
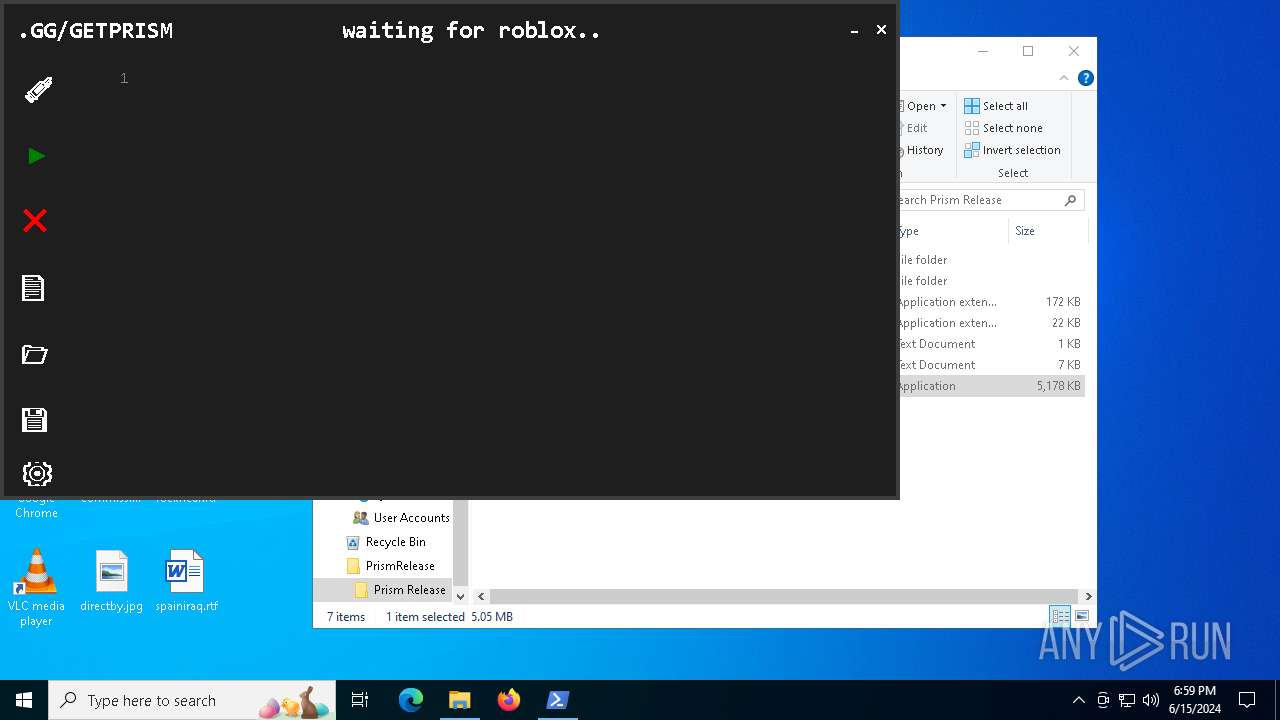
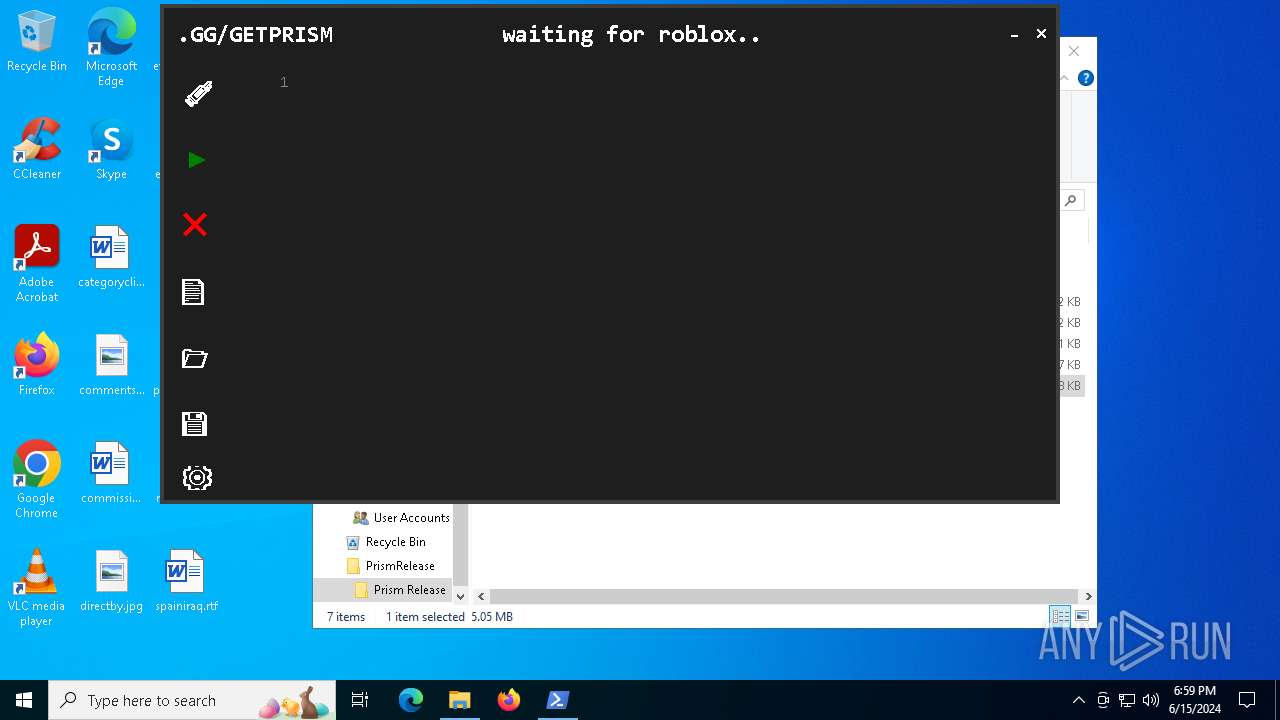
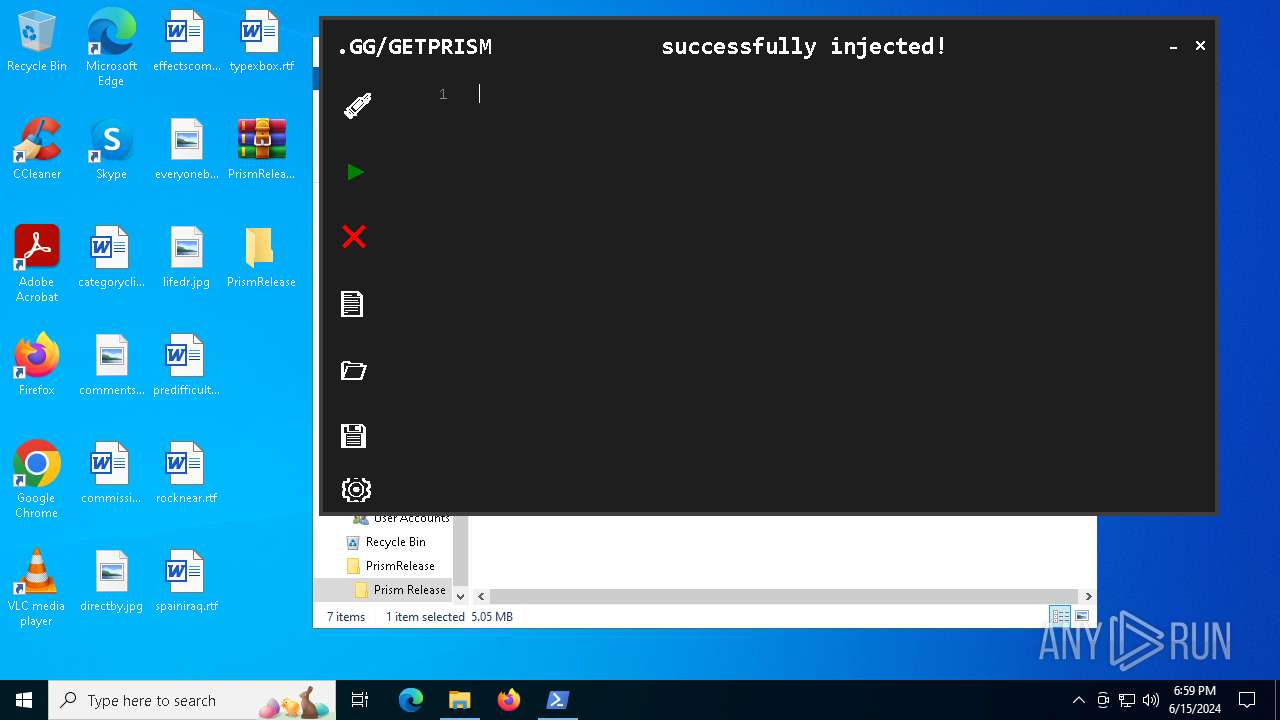
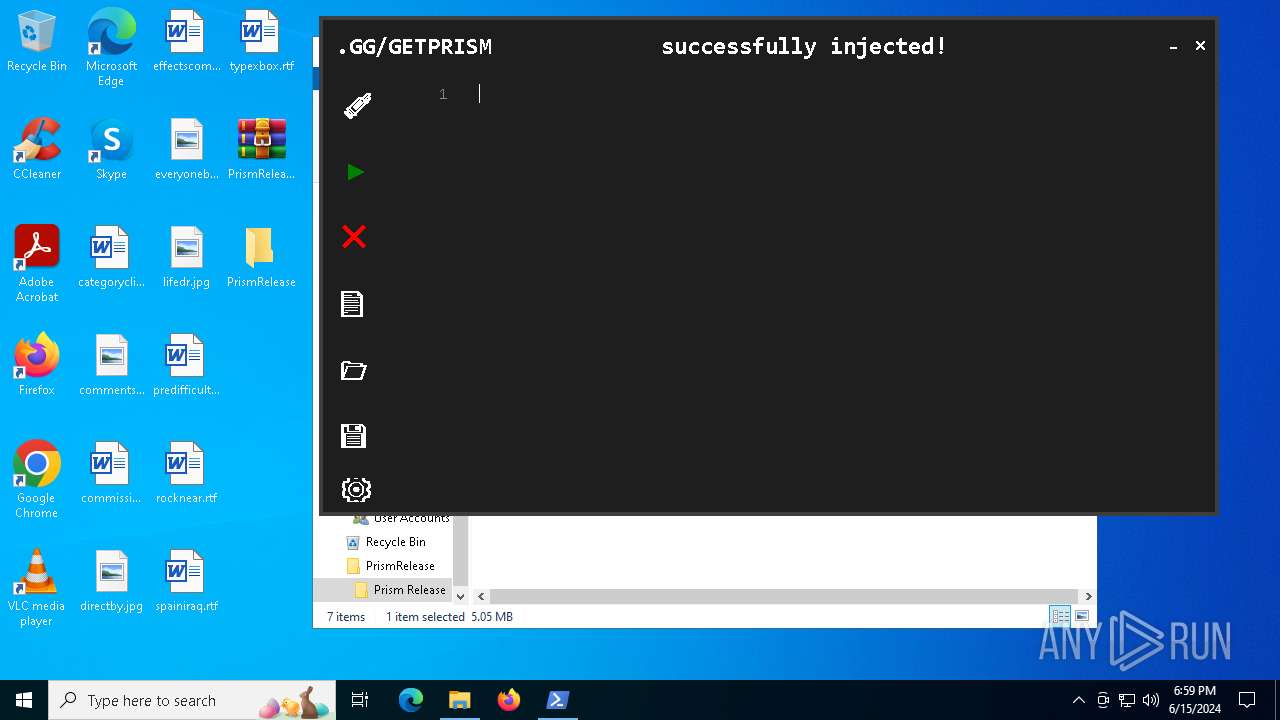
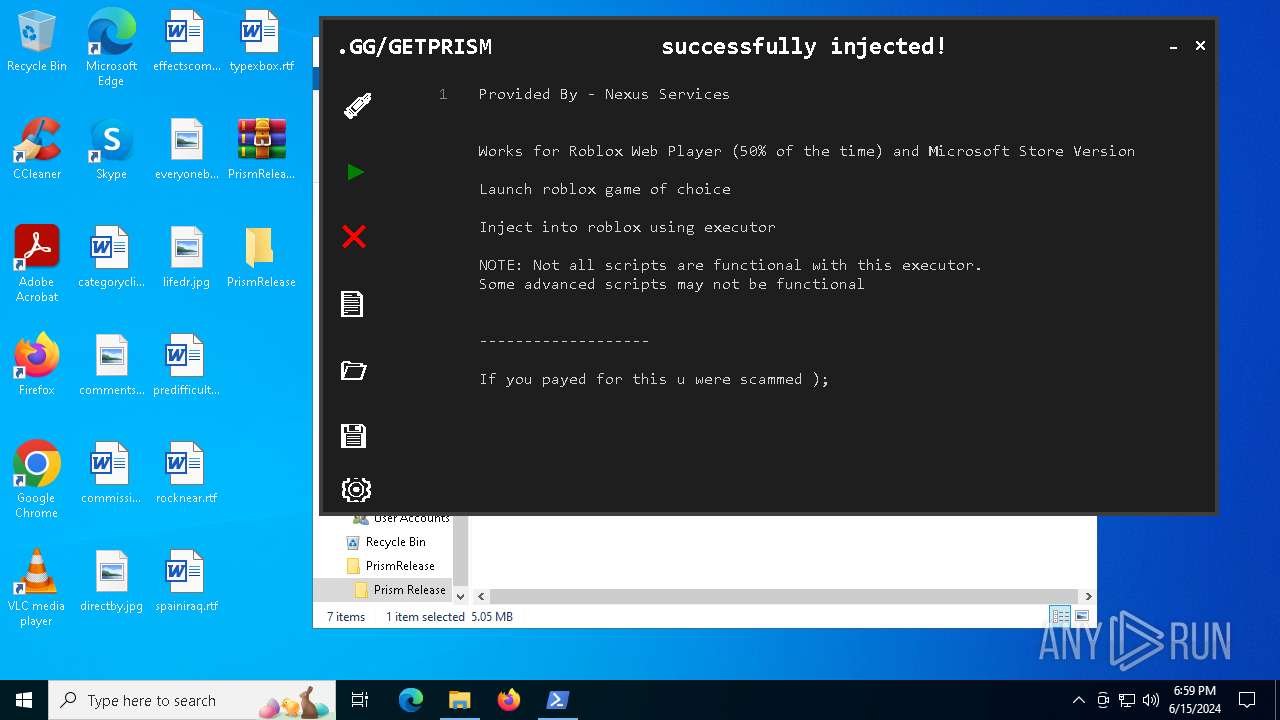
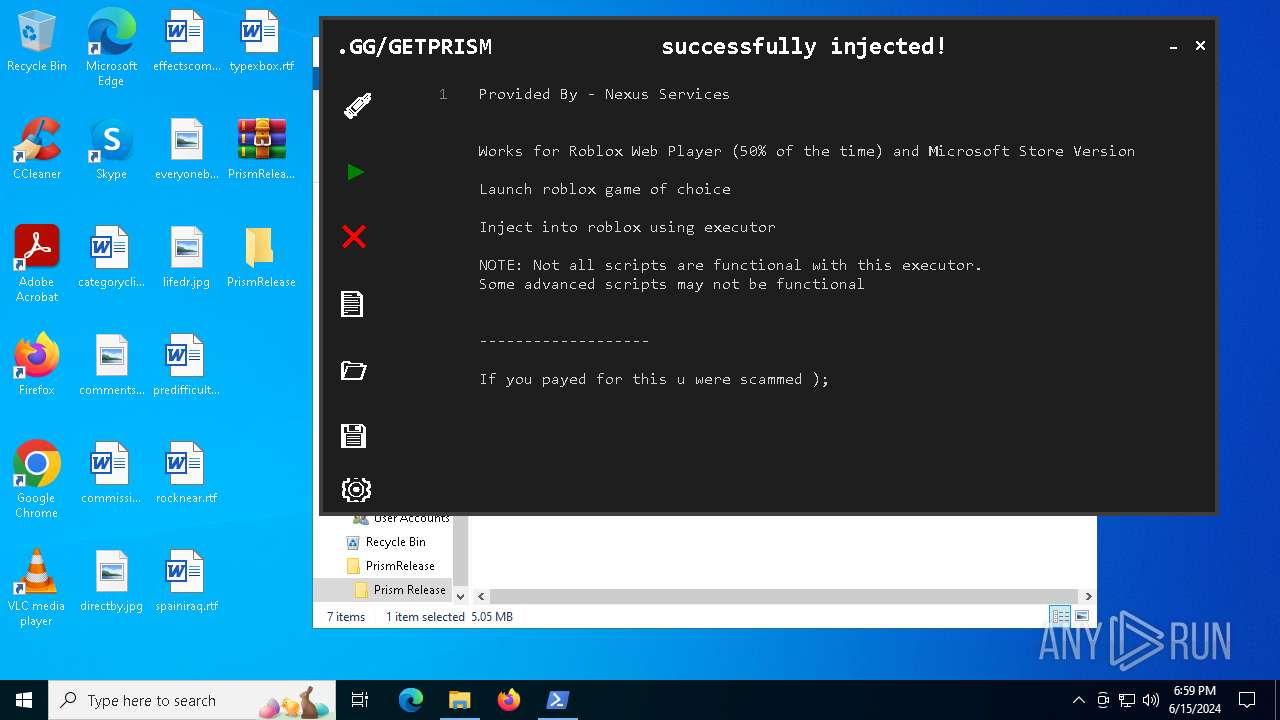
MALICIOUS
Drops the executable file immediately after the start
- WinRAR.exe (PID: 6296)
- Prism Release V1.5.exe (PID: 6972)
- Prism Executor.exe (PID: 6164)
- dllhost.exe (PID: 7132)
- hjjtns.exe (PID: 7164)
- kanilzbpgdul.exe (PID: 1188)
- wjhsvc.exe (PID: 5444)
Adds path to the Windows Defender exclusion list
- dllhost.exe (PID: 7132)
Bypass execution policy to execute commands
- powershell.exe (PID: 5716)
- powershell.exe (PID: 5520)
- powershell.exe (PID: 6576)
- powershell.exe (PID: 1412)
Uses Task Scheduler to run other applications
- dllhost.exe (PID: 7132)
Changes the autorun value in the registry
- dllhost.exe (PID: 7132)
Create files in the Startup directory
- dllhost.exe (PID: 7132)
Changes powershell execution policy (Bypass)
- dllhost.exe (PID: 7132)
Adds process to the Windows Defender exclusion list
- dllhost.exe (PID: 7132)
XWORM has been detected (SURICATA)
- dllhost.exe (PID: 7132)
Connects to the CnC server
- dllhost.exe (PID: 7132)
XWORM has been detected (YARA)
- dllhost.exe (PID: 7132)
SUSPICIOUS
Reads security settings of Internet Explorer
- Prism Release V1.5.exe (PID: 6972)
- dllhost.exe (PID: 7132)
- TextInputHost.exe (PID: 6976)
- nexusloader.exe (PID: 4428)
- wjhsvc.exe (PID: 5444)
Reads the date of Windows installation
- Prism Release V1.5.exe (PID: 6972)
- dllhost.exe (PID: 7132)
Starts POWERSHELL.EXE for commands execution
- Prism Release V1.5.exe (PID: 6972)
- dllhost.exe (PID: 7132)
BASE64 encoded PowerShell command has been detected
- Prism Release V1.5.exe (PID: 6972)
Base64-obfuscated command line is found
- Prism Release V1.5.exe (PID: 6972)
Executable content was dropped or overwritten
- Prism Release V1.5.exe (PID: 6972)
- Prism Executor.exe (PID: 6164)
- dllhost.exe (PID: 7132)
- hjjtns.exe (PID: 7164)
- kanilzbpgdul.exe (PID: 1188)
- wjhsvc.exe (PID: 5444)
The process creates files with name similar to system file names
- Prism Release V1.5.exe (PID: 6972)
- wjhsvc.exe (PID: 5444)
Process drops legitimate windows executable
- Prism Release V1.5.exe (PID: 6972)
- Prism Executor.exe (PID: 6164)
- dllhost.exe (PID: 7132)
- wjhsvc.exe (PID: 5444)
Process drops python dynamic module
- Prism Executor.exe (PID: 6164)
- wjhsvc.exe (PID: 5444)
The process drops C-runtime libraries
- Prism Executor.exe (PID: 6164)
- wjhsvc.exe (PID: 5444)
Script adds exclusion path to Windows Defender
- dllhost.exe (PID: 7132)
Script adds exclusion process to Windows Defender
- dllhost.exe (PID: 7132)
Checks for external IP
- dllhost.exe (PID: 7132)
Loads Python modules
- nexusloader.exe (PID: 4428)
- svchost.exe (PID: 3408)
Connects to unusual port
- dllhost.exe (PID: 7132)
Contacting a server suspected of hosting an CnC
- dllhost.exe (PID: 7132)
Uses powercfg.exe to modify the power settings
- hjjtns.exe (PID: 7164)
- kanilzbpgdul.exe (PID: 1188)
Starts SC.EXE for service management
- hjjtns.exe (PID: 7164)
Drops a system driver (possible attempt to evade defenses)
- kanilzbpgdul.exe (PID: 1188)
Executes as Windows Service
- kanilzbpgdul.exe (PID: 1188)
Starts CMD.EXE for commands execution
- svchost.exe (PID: 3408)
INFO
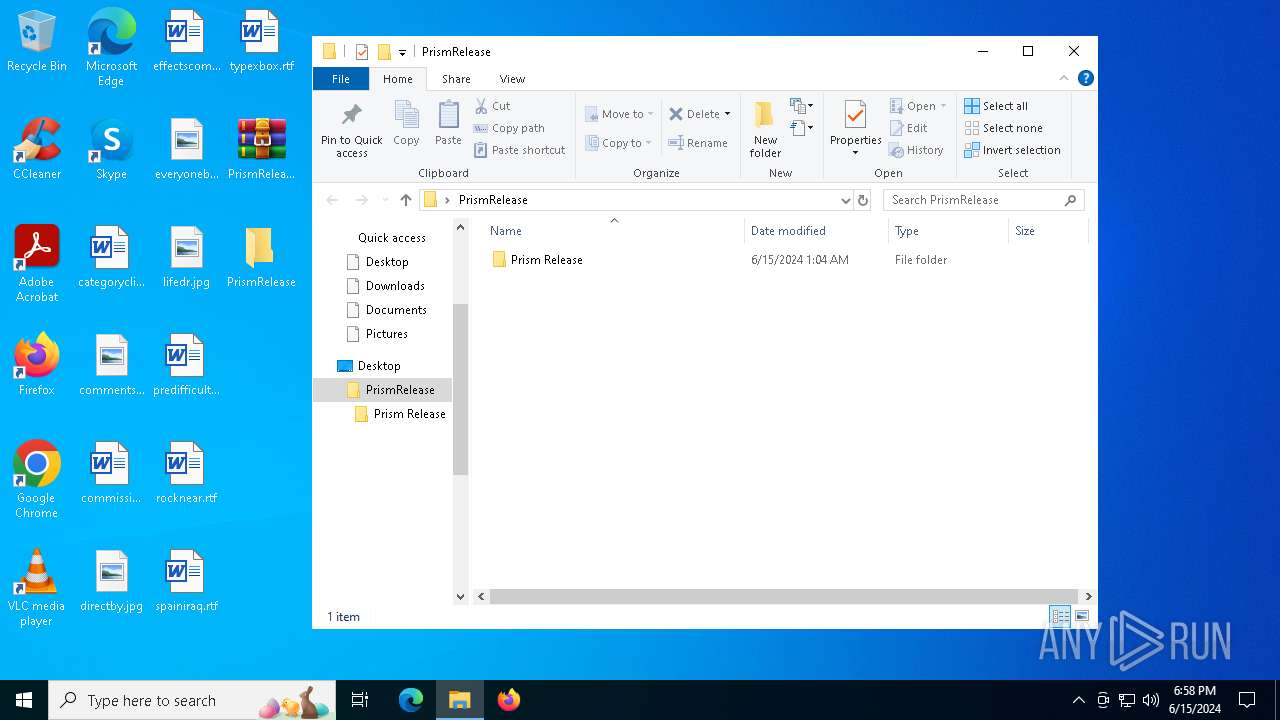
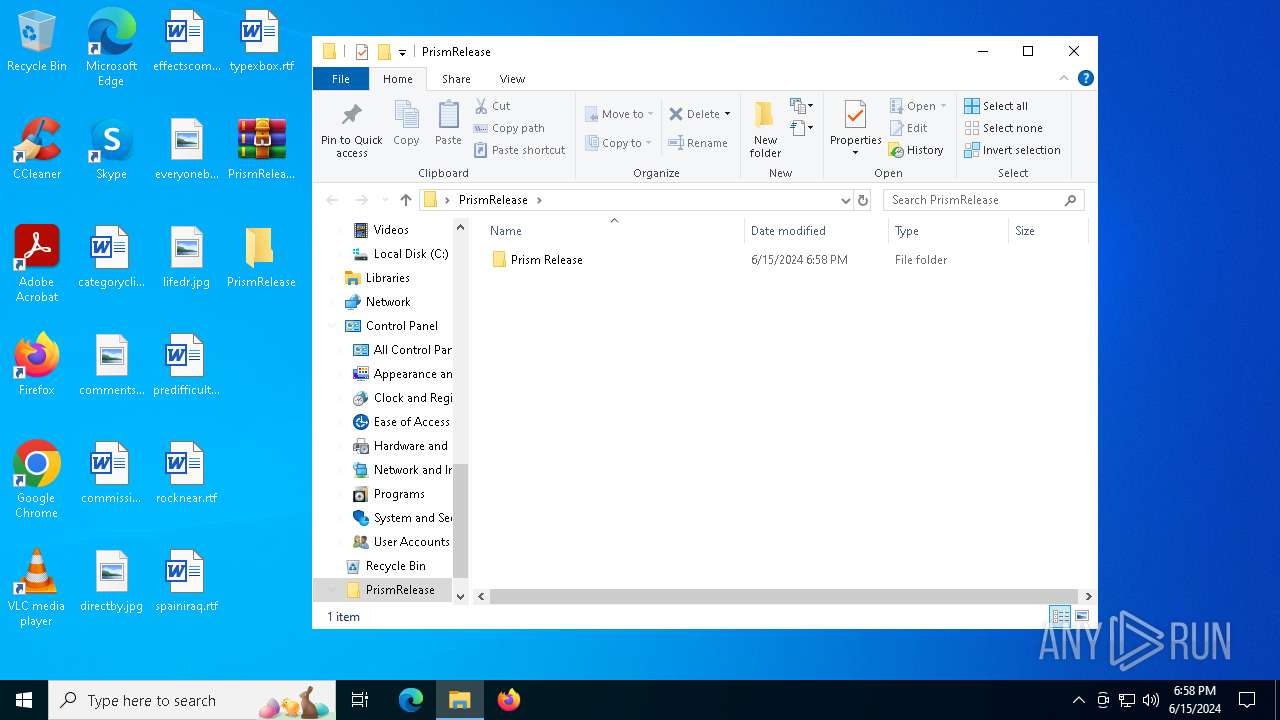
Manual execution by a user
- WinRAR.exe (PID: 6784)
- Prism Release V1.5.exe (PID: 6924)
- Prism Release V1.5.exe (PID: 6972)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6784)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 6784)
Checks supported languages
- Prism Release V1.5.exe (PID: 6972)
- dllhost.exe (PID: 7132)
- Prism Executor.exe (PID: 6164)
- nexusloader.exe (PID: 4428)
- TextInputHost.exe (PID: 6976)
- hjjtns.exe (PID: 7164)
- svchost.exe (PID: 3408)
- kanilzbpgdul.exe (PID: 1188)
- wjhsvc.exe (PID: 5444)
Reads the computer name
- Prism Release V1.5.exe (PID: 6972)
- dllhost.exe (PID: 7132)
- nexusloader.exe (PID: 4428)
- TextInputHost.exe (PID: 6976)
- svchost.exe (PID: 3408)
- wjhsvc.exe (PID: 5444)
Process checks computer location settings
- Prism Release V1.5.exe (PID: 6972)
- dllhost.exe (PID: 7132)
Create files in a temporary directory
- Prism Executor.exe (PID: 6164)
- dllhost.exe (PID: 7132)
- wjhsvc.exe (PID: 5444)
Reads the machine GUID from the registry
- dllhost.exe (PID: 7132)
- nexusloader.exe (PID: 4428)
- svchost.exe (PID: 3408)
Checks proxy server information
- dllhost.exe (PID: 7132)
Reads Environment values
- dllhost.exe (PID: 7132)
Disables trace logs
- dllhost.exe (PID: 7132)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7076)
- powershell.exe (PID: 5716)
- powershell.exe (PID: 6576)
- powershell.exe (PID: 1412)
- powershell.exe (PID: 5520)
Creates files in the program directory
- dllhost.exe (PID: 7132)
- hjjtns.exe (PID: 7164)
Creates files or folders in the user directory
- dllhost.exe (PID: 7132)
Checks operating system version
- svchost.exe (PID: 3408)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
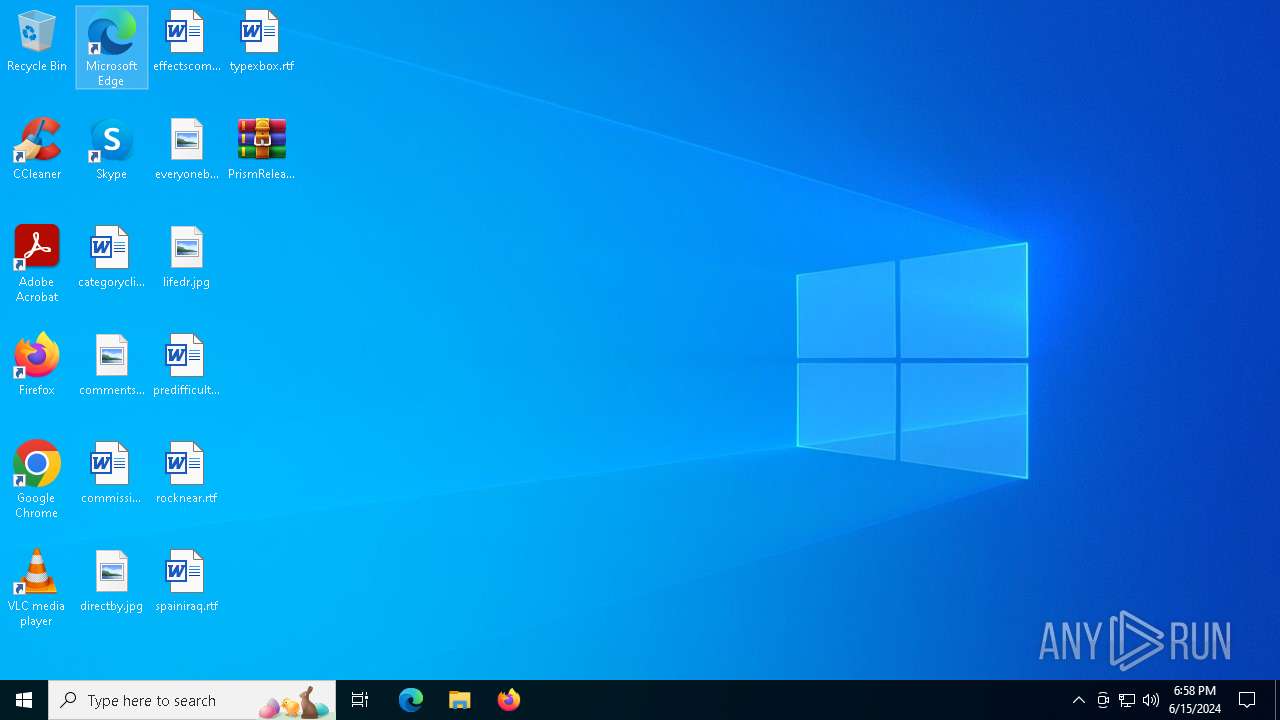
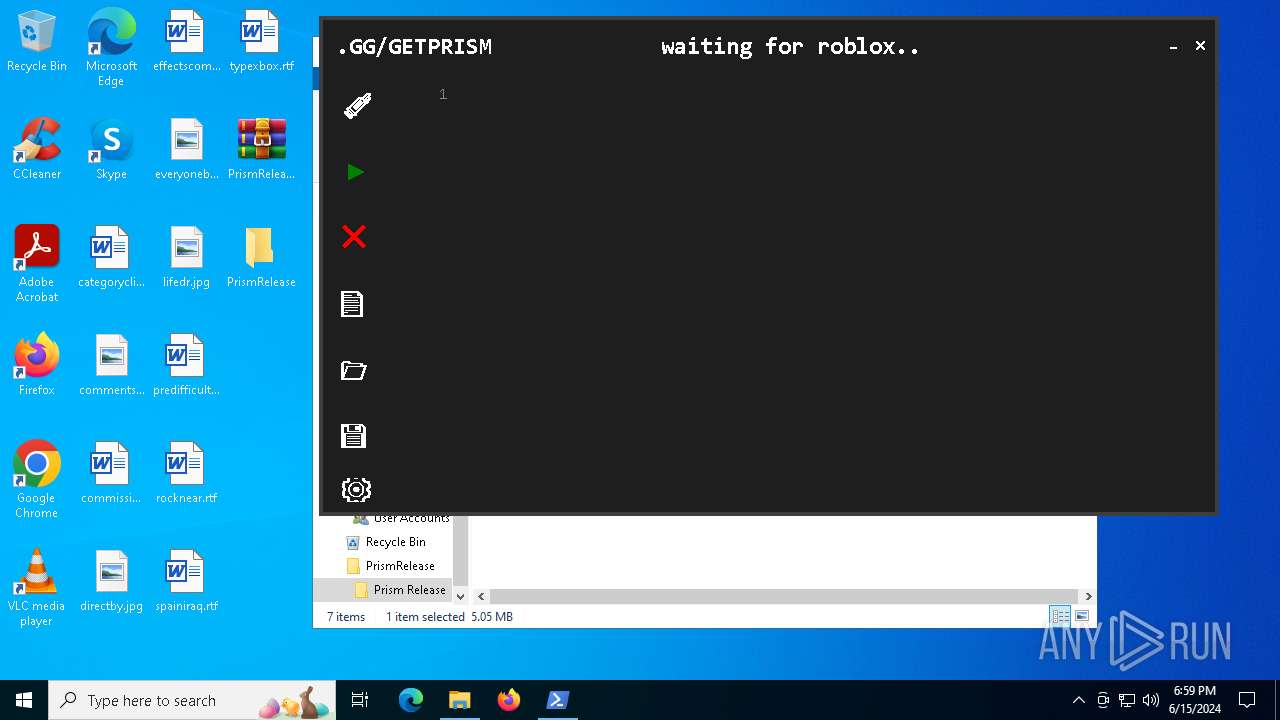
XWorm
(PID) Process(7132) dllhost.exe
C291.92.241.69:5555
Keys
AES<123456789>
Options
Splitter<Xwormmm>
Sleep time3
USB drop namefkogffre
MutexGxtawApxNQLtF8fL
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
173
Monitored processes
55
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 588 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1120 | C:\WINDOWS\system32\powercfg.exe /x -hibernate-timeout-ac 0 | C:\Windows\System32\powercfg.exe | — | kanilzbpgdul.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Power Settings Command-Line Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1188 | C:\ProgramData\hvforlxxtnuo\kanilzbpgdul.exe | C:\ProgramData\hvforlxxtnuo\kanilzbpgdul.exe | services.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 1412 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ExecutionPolicy Bypass Add-MpPreference -ExclusionProcess 'dllhost.exe' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | dllhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1572 | svchost.exe | C:\Windows\System32\svchost.exe | kanilzbpgdul.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1676 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powercfg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2008 | C:\WINDOWS\system32\cmd.exe /c "ver" | C:\Windows\System32\cmd.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2492 | C:\WINDOWS\system32\sc.exe stop eventlog | C:\Windows\System32\sc.exe | — | hjjtns.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 1051 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2916 | C:\WINDOWS\system32\powercfg.exe /x -hibernate-timeout-ac 0 | C:\Windows\System32\powercfg.exe | — | hjjtns.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Power Settings Command-Line Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3408 | "C:\Users\admin\AppData\Local\Temp\wjhsvc.exe" | C:\Users\admin\AppData\Local\Temp\onefile_5444_133629515763966935\svchost.exe | — | wjhsvc.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
66 186
Read events
65 962
Write events
205
Delete events
19
Modification events
| (PID) Process: | (6296) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (6296) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (6296) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (6296) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\PrismRelease.rar | |||
| (PID) Process: | (6296) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6296) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6296) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6296) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6296) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
| (PID) Process: | (6296) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
Executable files
110
Suspicious files
15
Text files
936
Unknown types
0
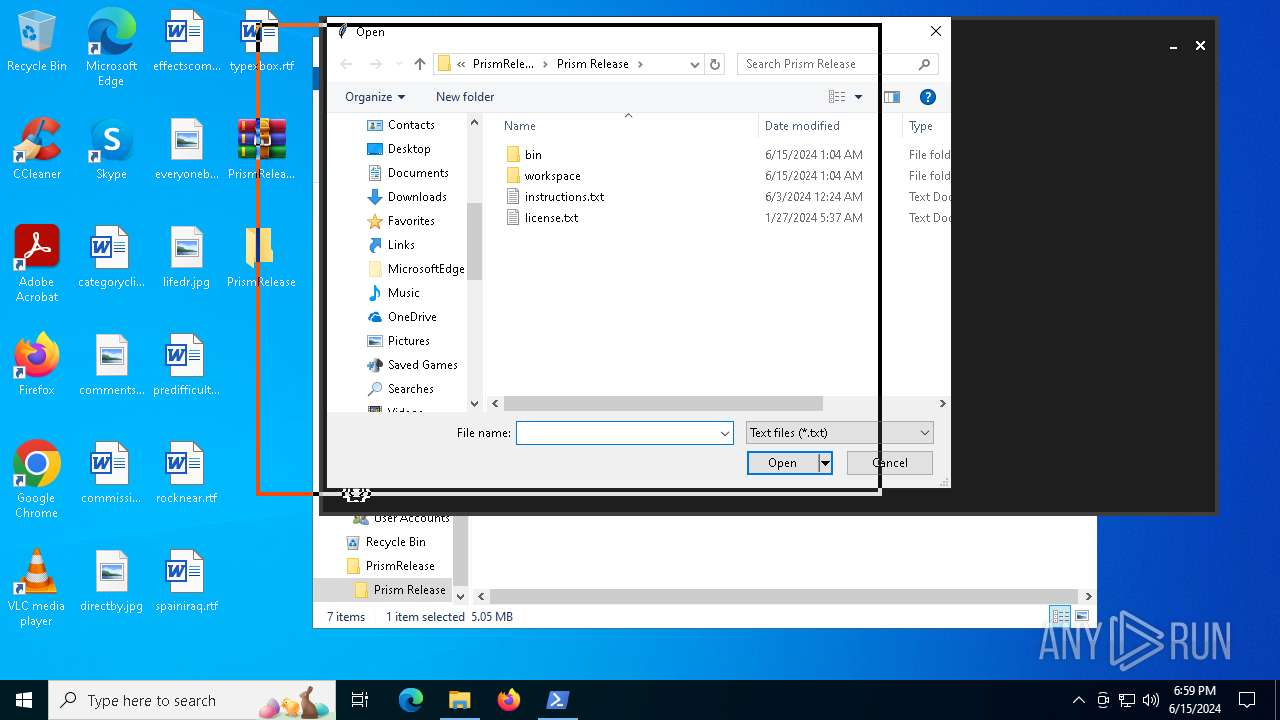
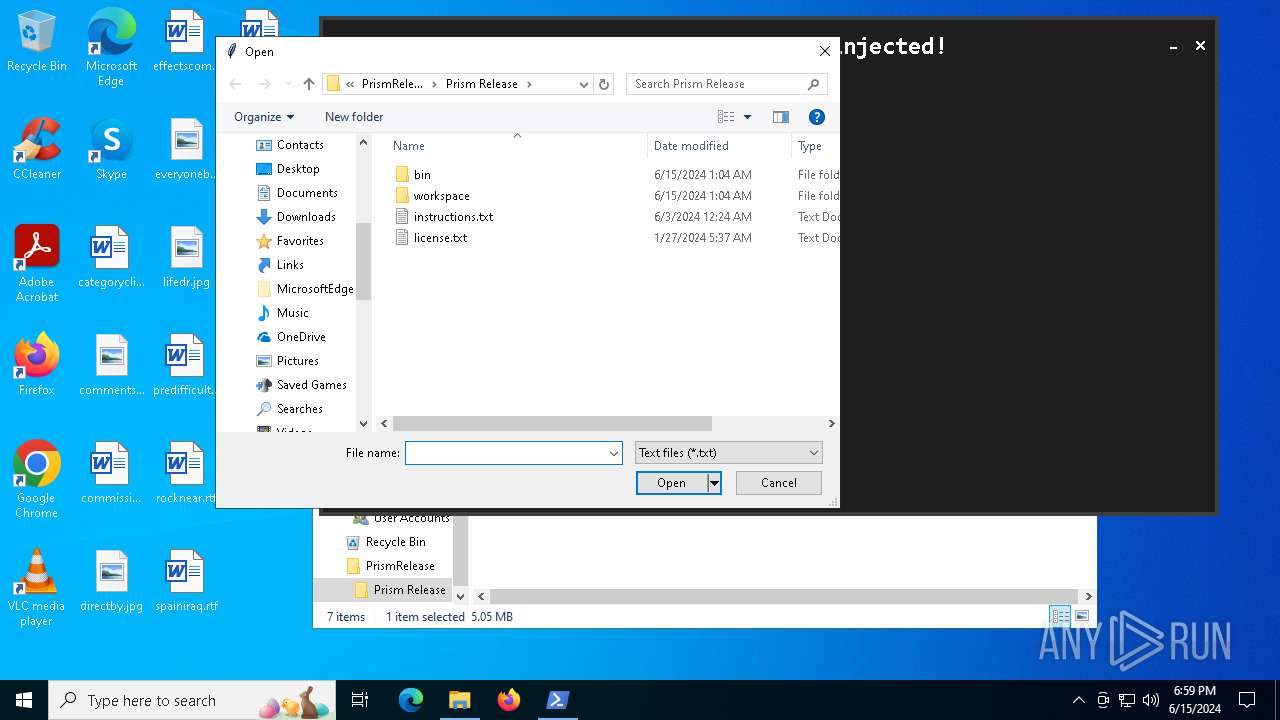
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
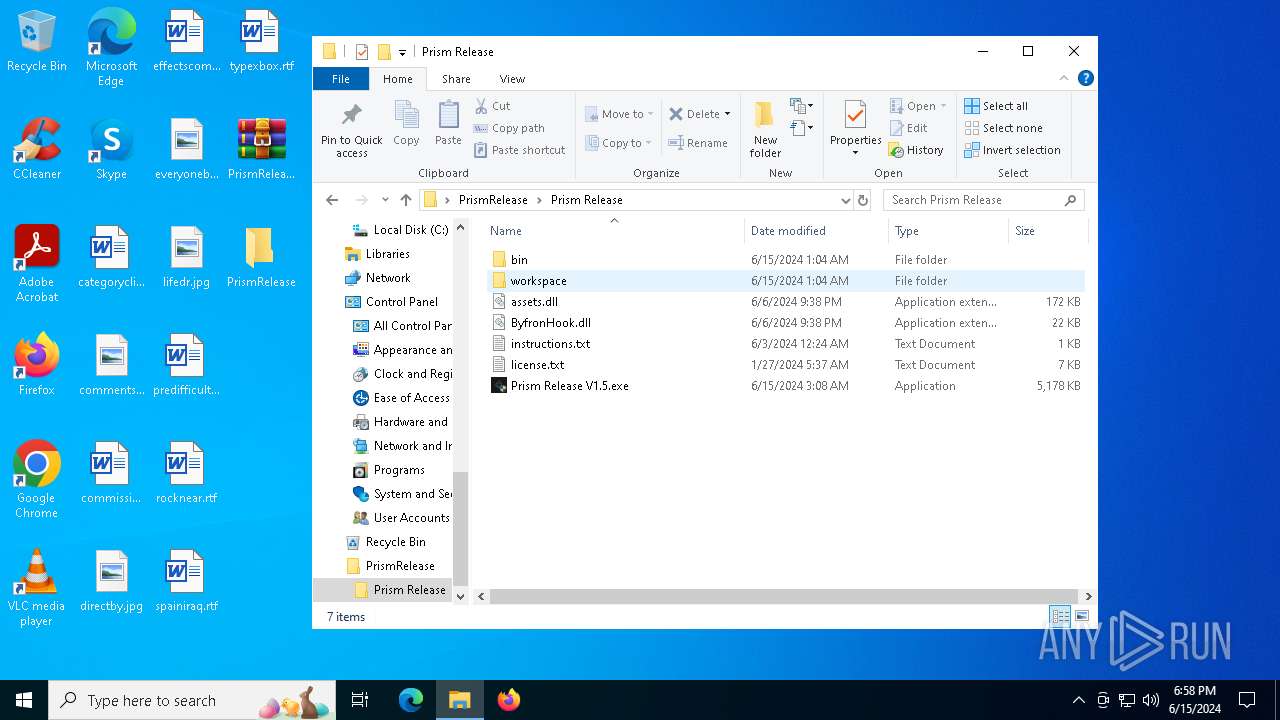
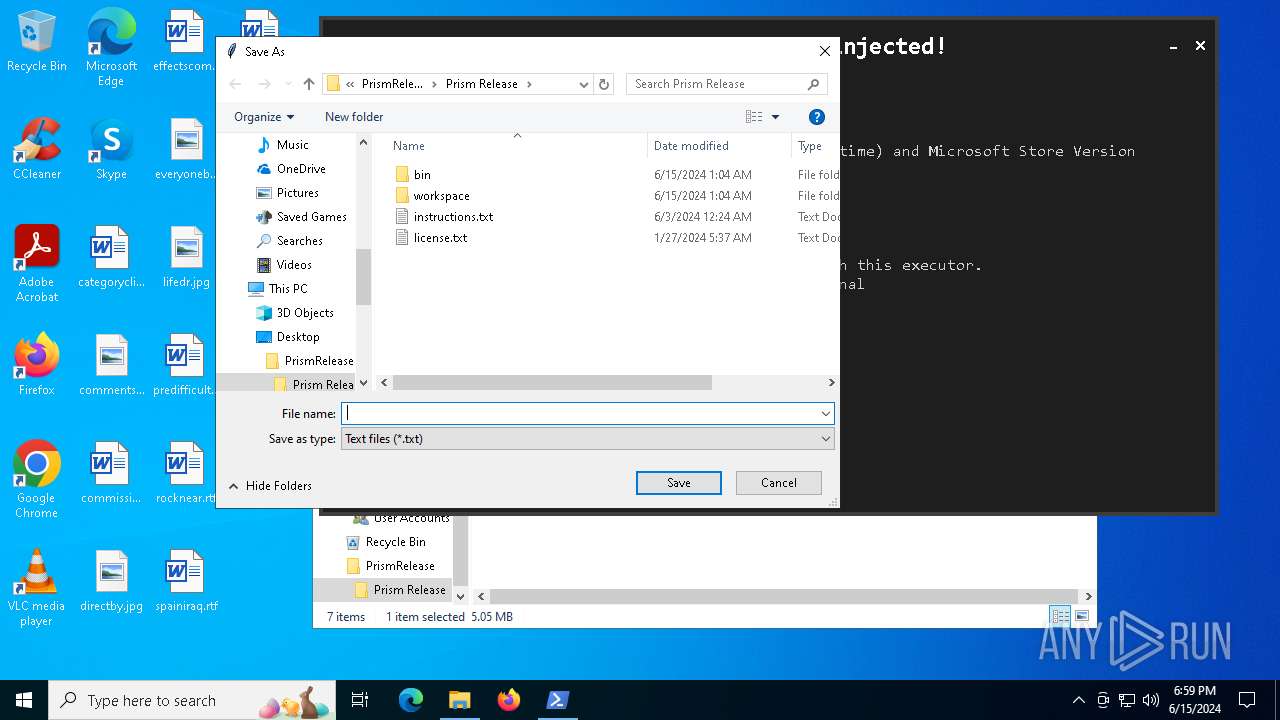
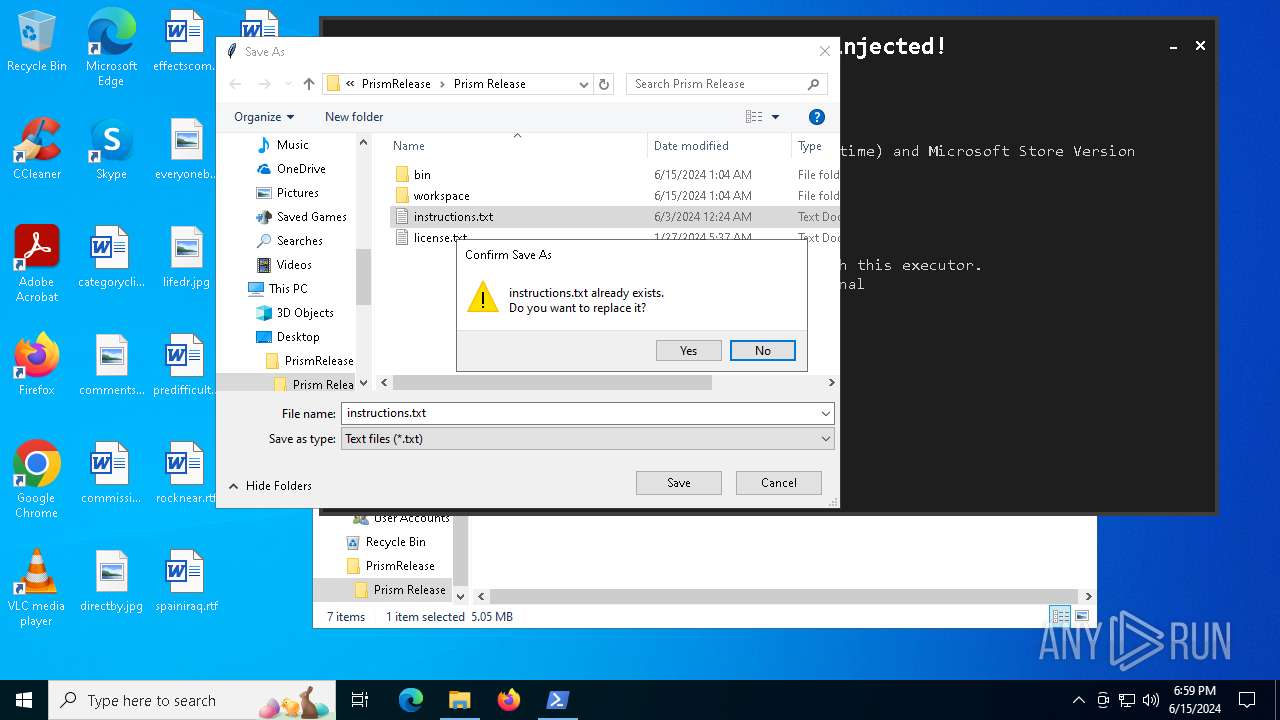
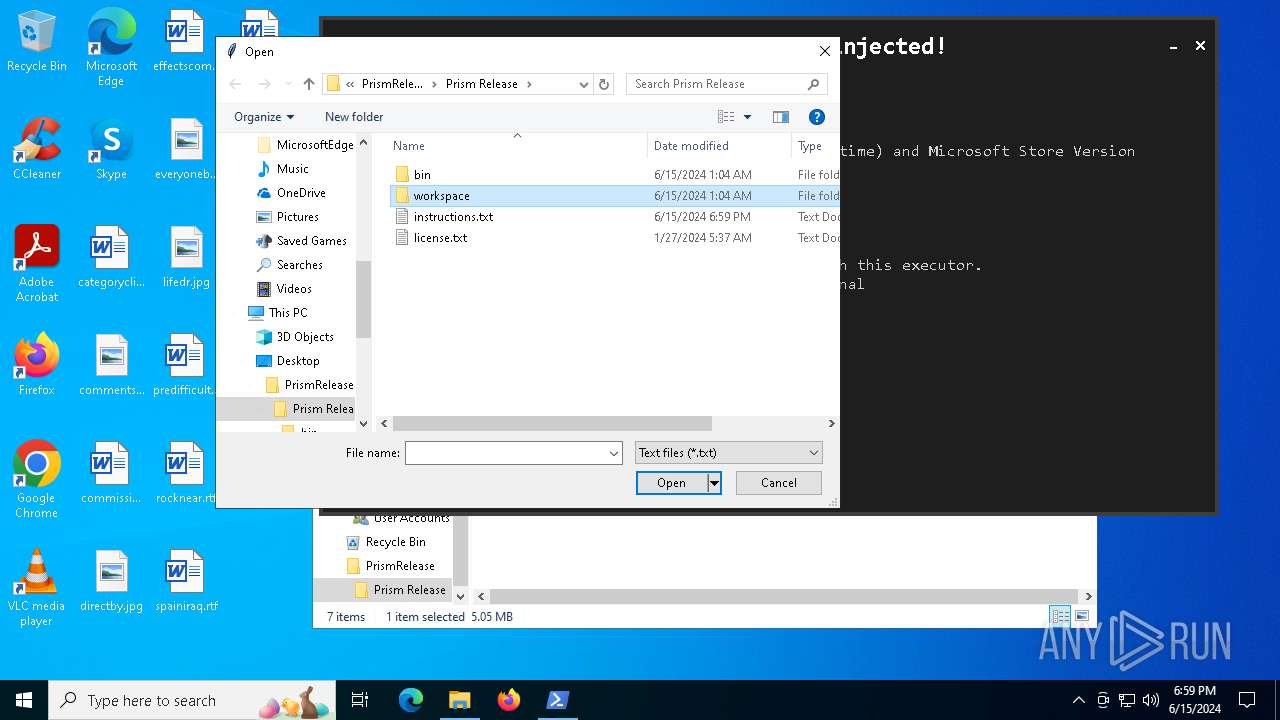
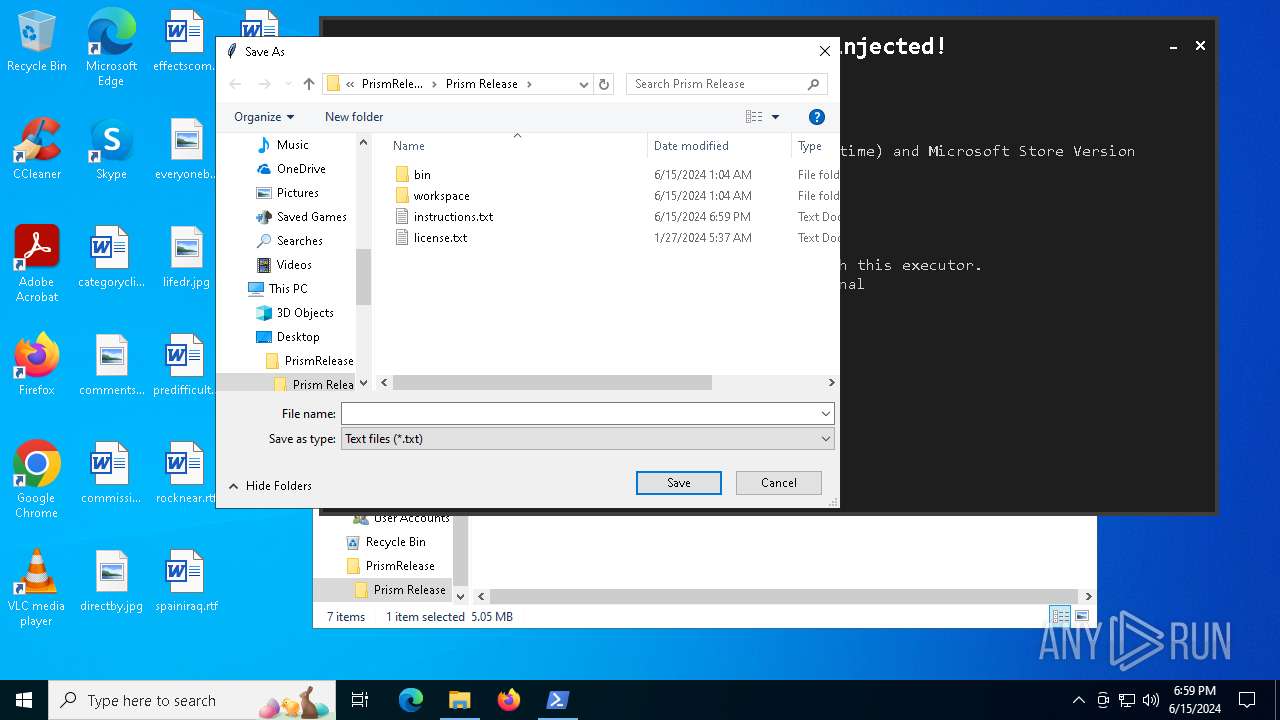
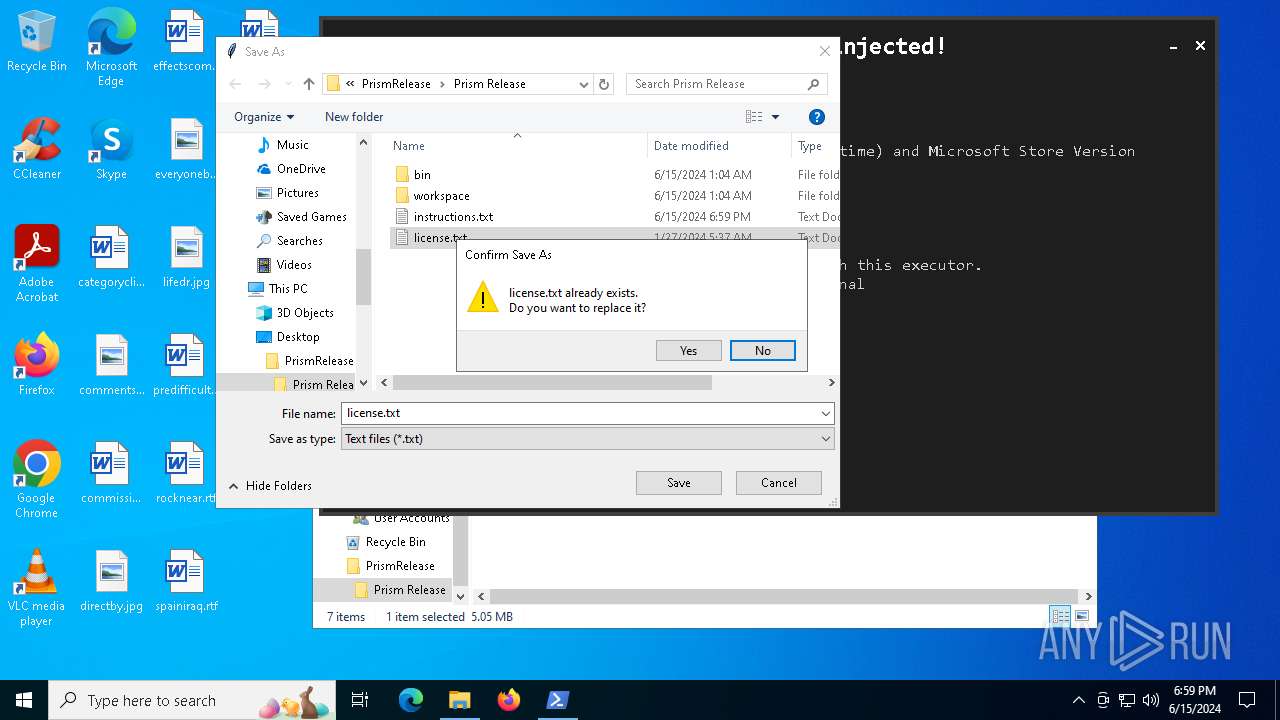
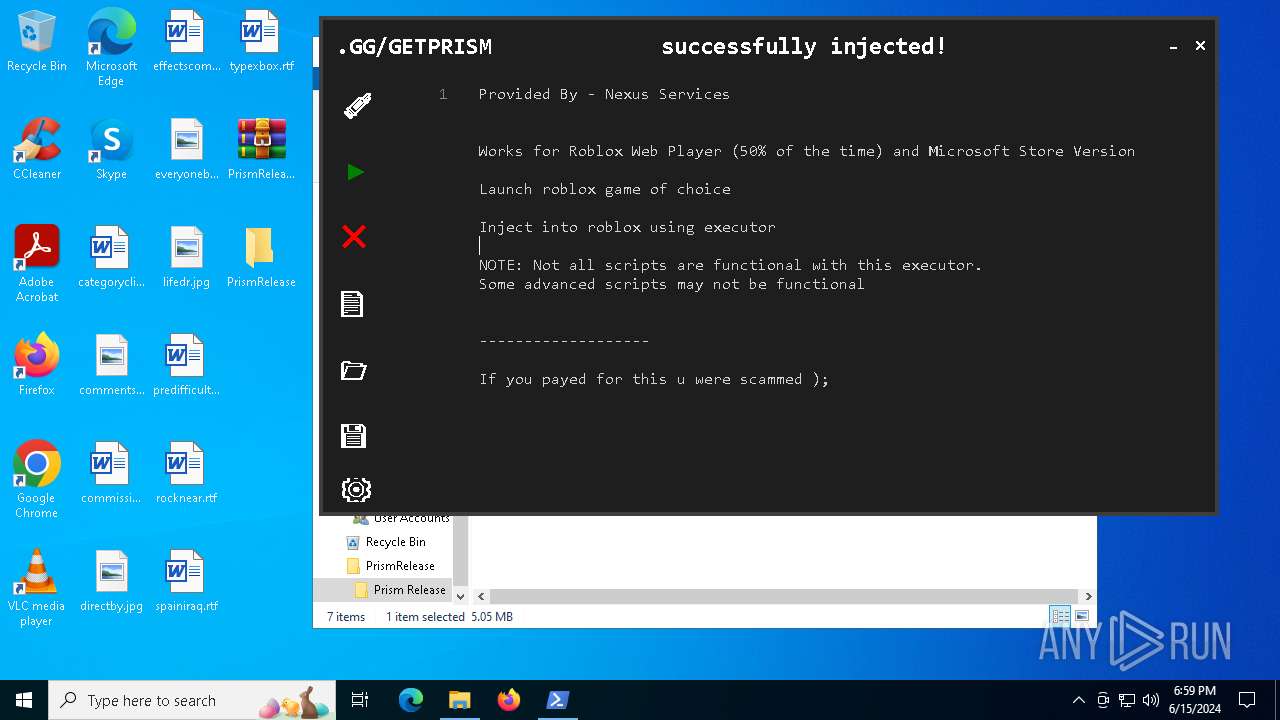
| 6784 | WinRAR.exe | C:\Users\admin\Desktop\PrismRelease\Prism Release\instructions.txt | text | |
MD5:8A23BCAC9550C179F65025E505B4EA64 | SHA256:1795B27A75858A67A0C93BCE21B77D6FD89213079CE4BB8AA09B1CCA99BE5619 | |||
| 6784 | WinRAR.exe | C:\Users\admin\Desktop\PrismRelease\Prism Release\ByfronHook.dll | binary | |
MD5:4E3E92823CAEAC1203BEAA5A35D6DAFC | SHA256:3811858DA4B1F5E7F40D1237D7189DDCA3989FA0D7B07E87C538F92975B893D2 | |||
| 6784 | WinRAR.exe | C:\Users\admin\Desktop\PrismRelease\Prism Release\assets.dll | binary | |
MD5:BCC0B07DE0A24F9701FC97D154ECD660 | SHA256:672CB16128DEA50E21FD2D98889E2D6A2264B654304A3F4248EBDF4C546F734A | |||
| 6972 | Prism Release V1.5.exe | C:\Users\admin\dllhost.exe | executable | |
MD5:4A7F75343AAA5A4D8D18ADD50CCF3139 | SHA256:34BE6A934FD45752E788F9BA20943C8E52D91732D76E9F30A5176E98DCCD956E | |||
| 6784 | WinRAR.exe | C:\Users\admin\Desktop\PrismRelease\Prism Release\license.txt | text | |
MD5:0B09566254B011D989DECF0E23A902EB | SHA256:A19D58AAAB15C4D0019E569D1C073D1B5286FDD37DBEEE7A58A7D1AE76045AE1 | |||
| 6164 | Prism Executor.exe | C:\Users\admin\AppData\Local\Temp\onefile_6164_133629515149199413\select.pyd | executable | |
MD5:78D421A4E6B06B5561C45B9A5C6F86B1 | SHA256:F1694CE82DA997FAA89A9D22D469BFC94ABB0F2063A69EC9B953BC085C2CB823 | |||
| 6164 | Prism Executor.exe | C:\Users\admin\AppData\Local\Temp\onefile_6164_133629515149199413\tcl\history.tcl | text | |
MD5:E8FD468CCD2EE620544FE204BDE2A59D | SHA256:9B6E400EB85440EC64AB66B4AC111546585740C9CA61FD156400D7153CBAD9F4 | |||
| 6784 | WinRAR.exe | C:\Users\admin\Desktop\PrismRelease\Prism Release\workspace\Saved Scripts.txt | text | |
MD5:9AAB6209B47A96431718754D4BAC5BEA | SHA256:D2D792F0D9BDB064F665174877454EA83F32AA0A571D223C062FB2107352481B | |||
| 6784 | WinRAR.exe | C:\Users\admin\Desktop\PrismRelease\Prism Release\Prism Release V1.5.exe | executable | |
MD5:AC80F970A7AE1C07663ABDD11D752D34 | SHA256:B61CA7C42FEF43547C7892C76A925EC4A846373BFCDE20426C913A4390F71001 | |||
| 6972 | Prism Release V1.5.exe | C:\Users\admin\Prism Executor.exe | executable | |
MD5:FA819E23D8FEE4EA89AAAEA55E0B28F5 | SHA256:BB4FBBF322982321C56AC48CB7939EF7CB823B510A184C41E284F2CDF1BAB68C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
27
DNS requests
7
Threats
31
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2392 | svchost.exe | GET | 200 | 2.19.122.202:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
5140 | MoUsoCoreWorker.exe | GET | 200 | 2.19.122.202:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
3708 | RUXIMICS.exe | GET | 200 | 2.19.122.202:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
2392 | svchost.exe | GET | 200 | 23.36.69.232:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
3708 | RUXIMICS.exe | GET | 200 | 23.36.69.232:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
5140 | MoUsoCoreWorker.exe | GET | 200 | 23.36.69.232:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
7132 | dllhost.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=hosting | unknown | — | — | unknown |
— | — | GET | 200 | 2.19.120.32:443 | https://www.bing.com/rb/18/jnc,nj/6hU_LneafI_NFLeDvM367ebFaKQ.js?bu=DyIrb3t-gQF4cnWyAbUBK6UBK7gB&or=w | unknown | s | 21.3 Kb | unknown |
— | — | POST | 200 | 20.44.10.122:443 | https://self.events.data.microsoft.com/OneCollector/1.0/ | unknown | binary | 9 b | unknown |
— | — | GET | 200 | 2.19.120.21:443 | https://www.bing.com/manifest/threshold.appcache | unknown | text | 3.36 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2392 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
3708 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
5140 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
2392 | svchost.exe | 2.19.122.202:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
5140 | MoUsoCoreWorker.exe | 2.19.122.202:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
3708 | RUXIMICS.exe | 2.19.122.202:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
2392 | svchost.exe | 23.36.69.232:80 | www.microsoft.com | AKAMAI-AS | US | unknown |
3708 | RUXIMICS.exe | 23.36.69.232:80 | www.microsoft.com | AKAMAI-AS | US | unknown |
5140 | MoUsoCoreWorker.exe | 23.36.69.232:80 | www.microsoft.com | AKAMAI-AS | US | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
ip-api.com |
| shared |
www.bing.com |
| whitelisted |
pool.hashvault.pro |
| unknown |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7132 | dllhost.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
7132 | dllhost.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External Hosting Lookup by ip-api |
7132 | dllhost.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] Xworm Network Packet |
2184 | svchost.exe | Crypto Currency Mining Activity Detected | ET COINMINER CoinMiner Domain in DNS Lookup (pool .hashvault .pro) |
27 ETPRO signatures available at the full report