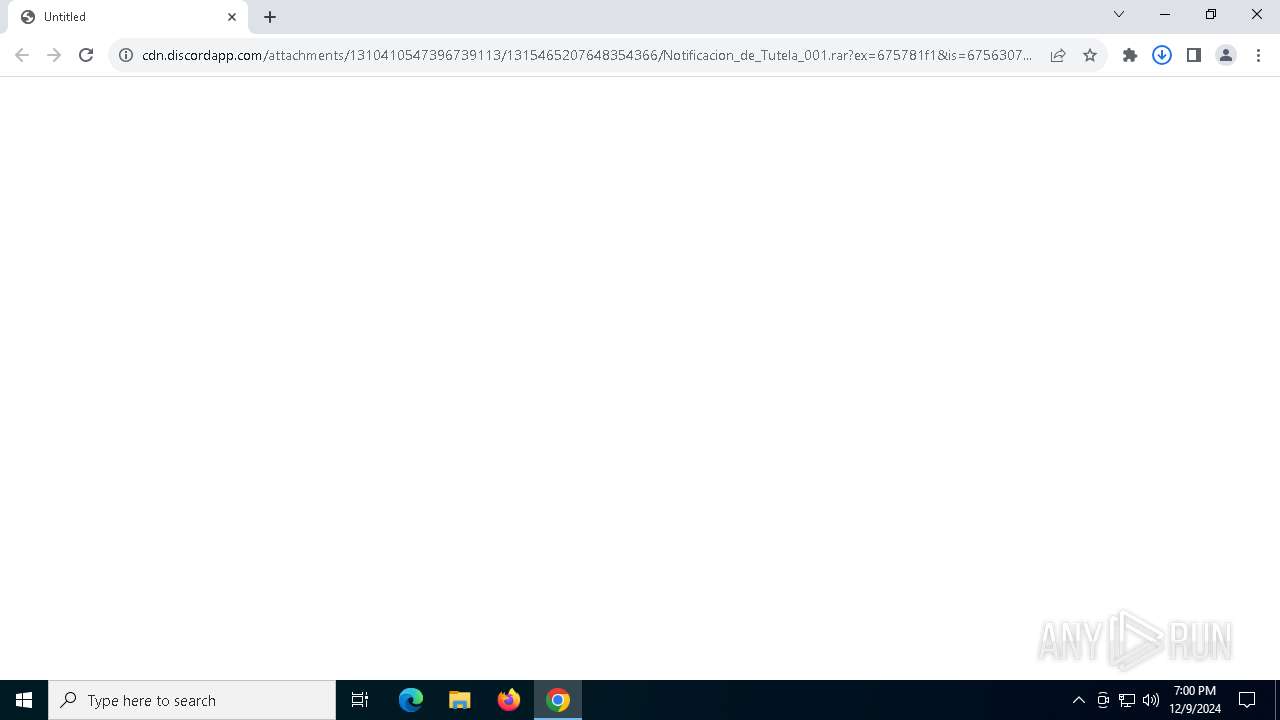
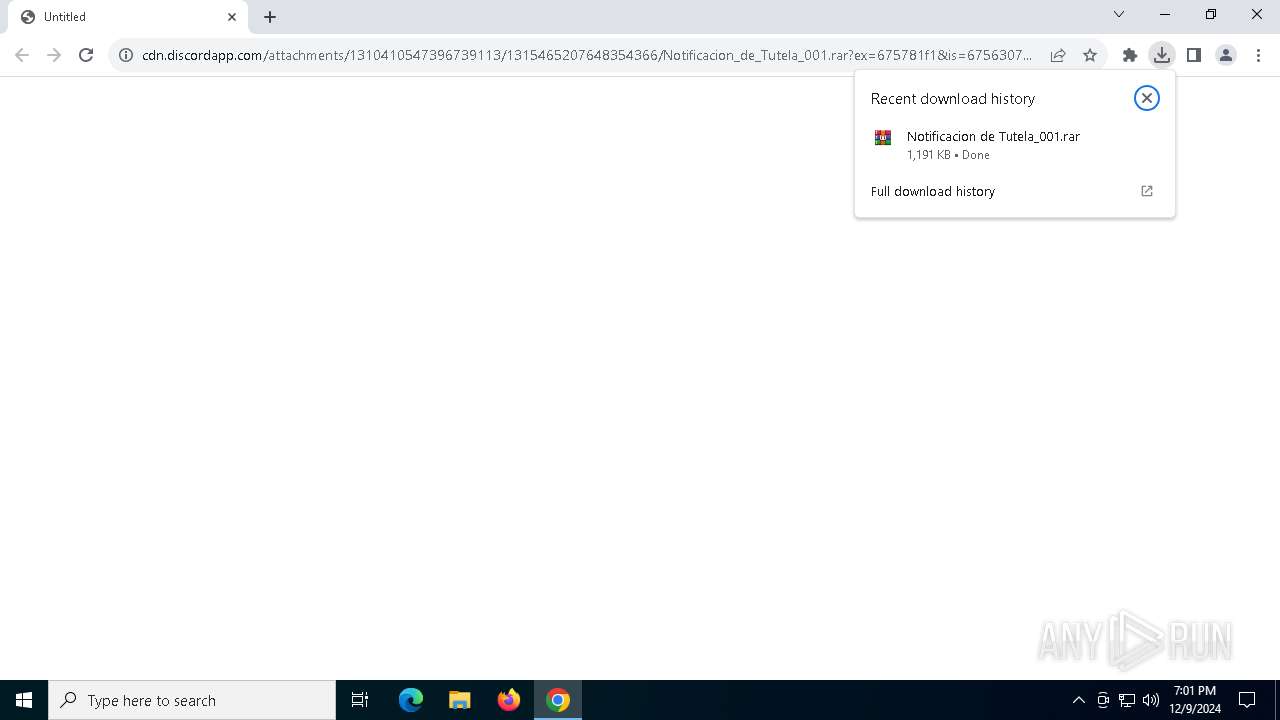
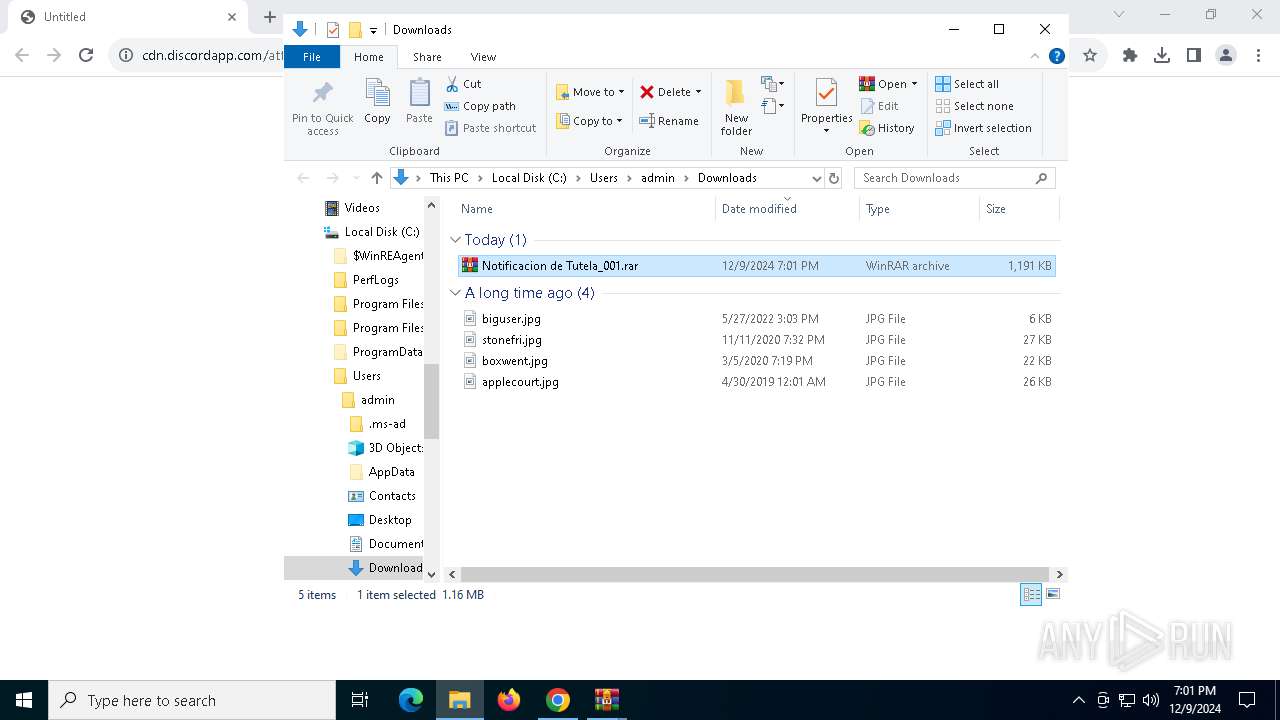
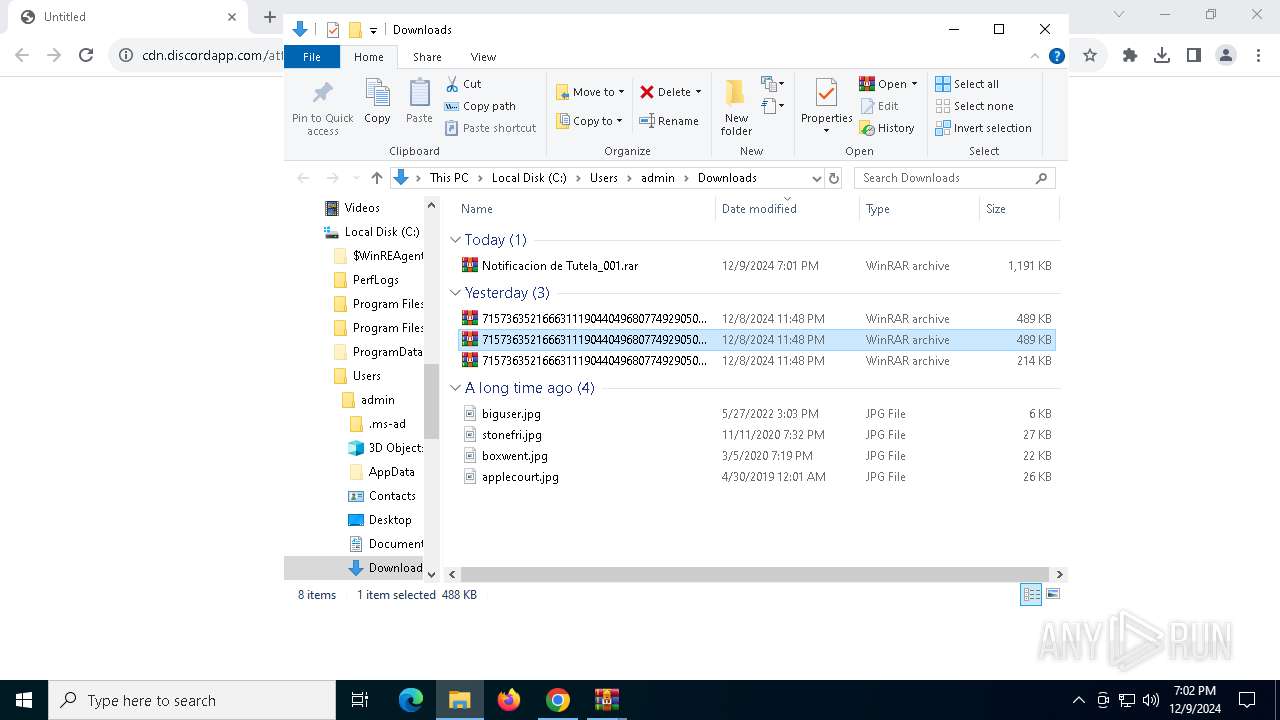
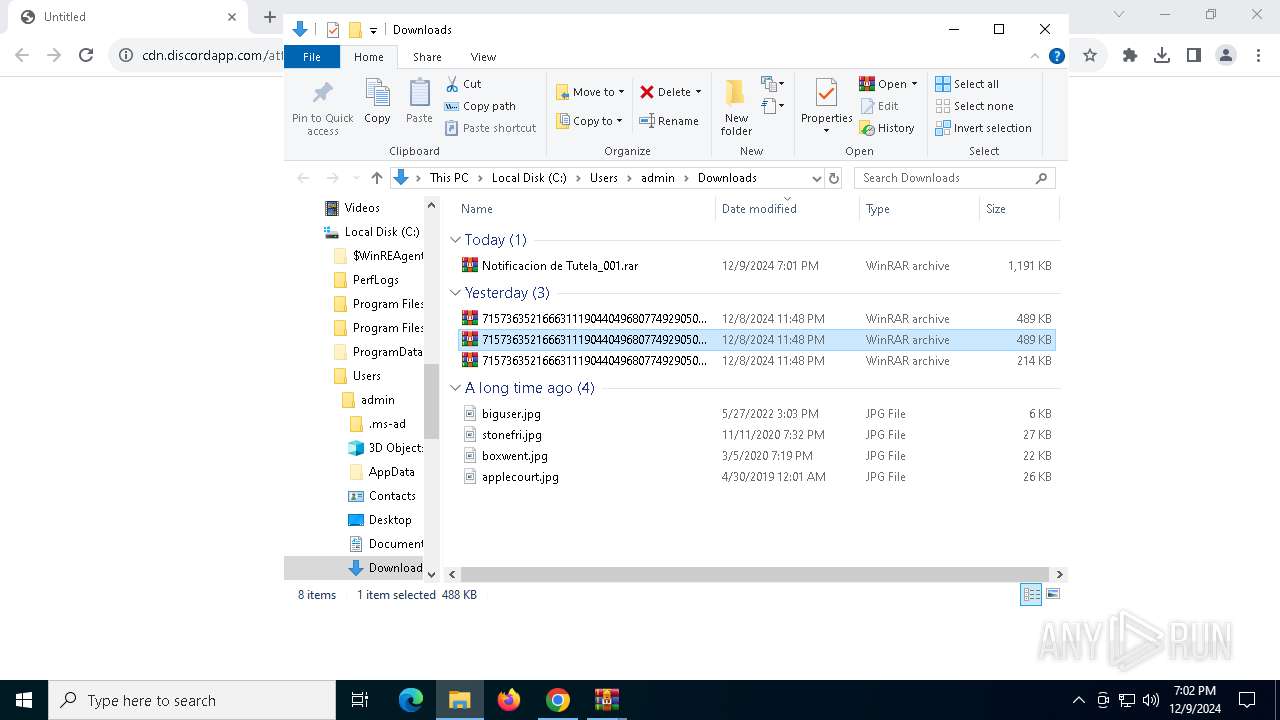
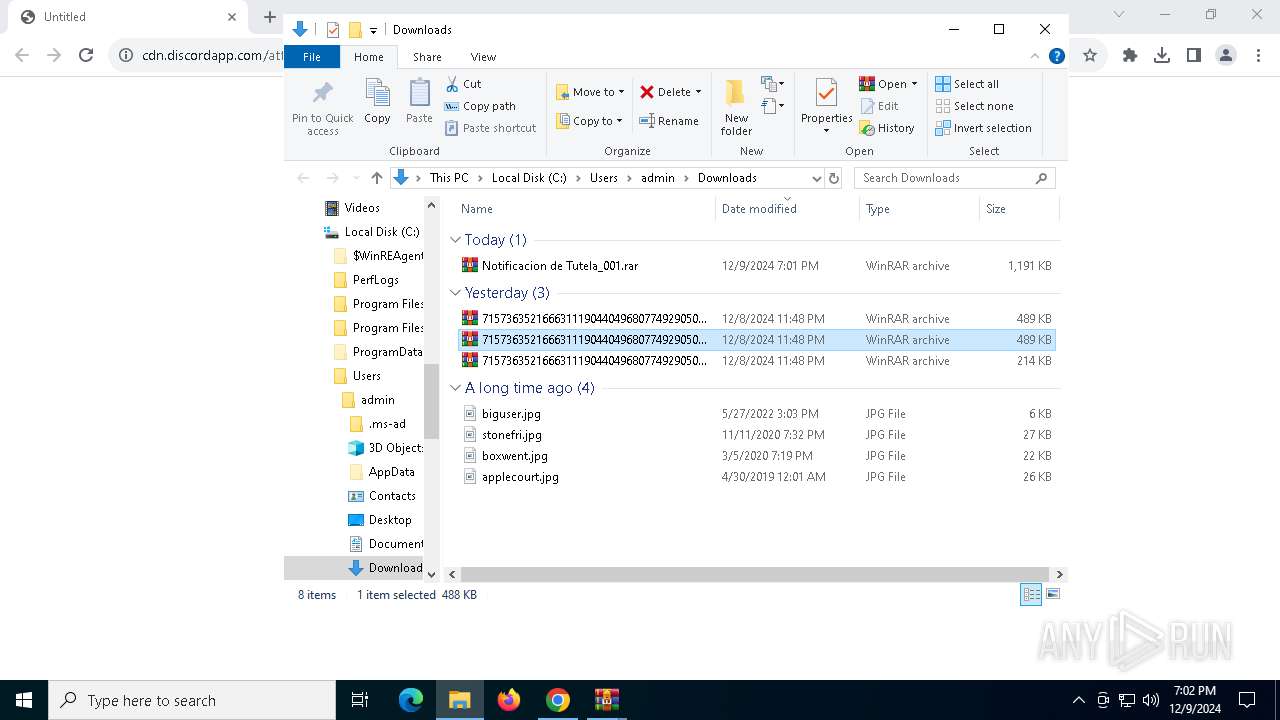
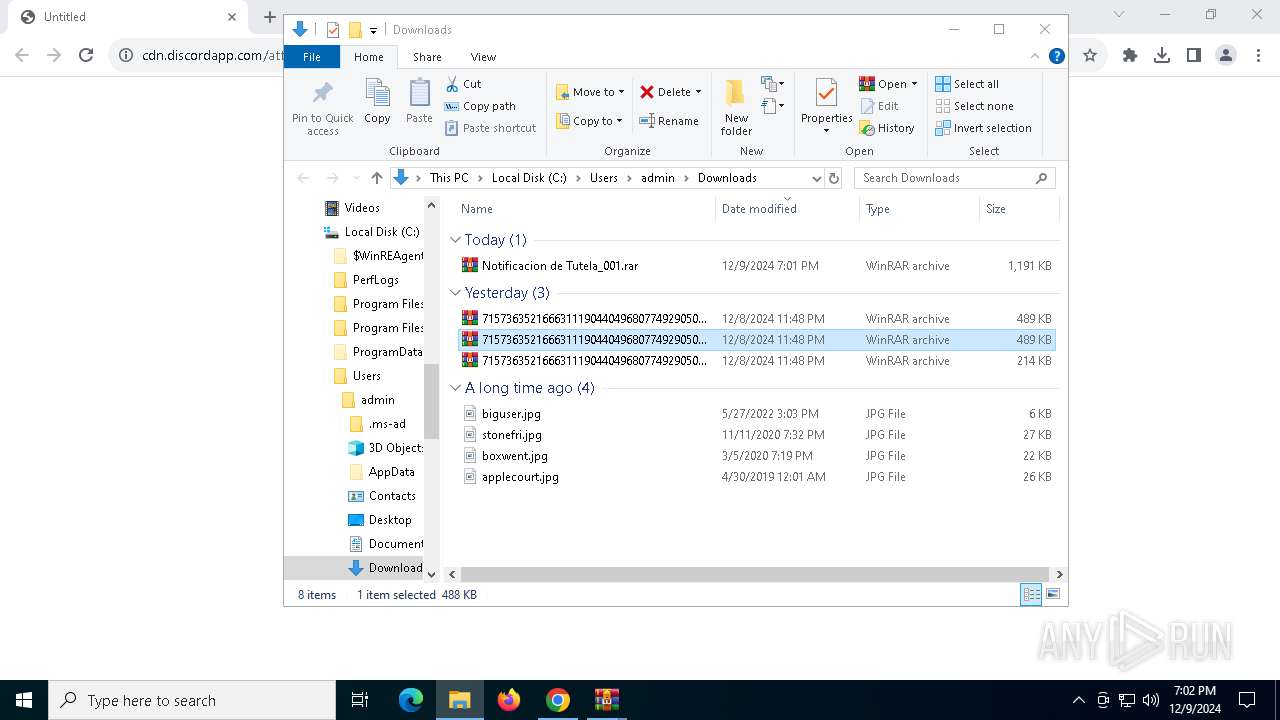
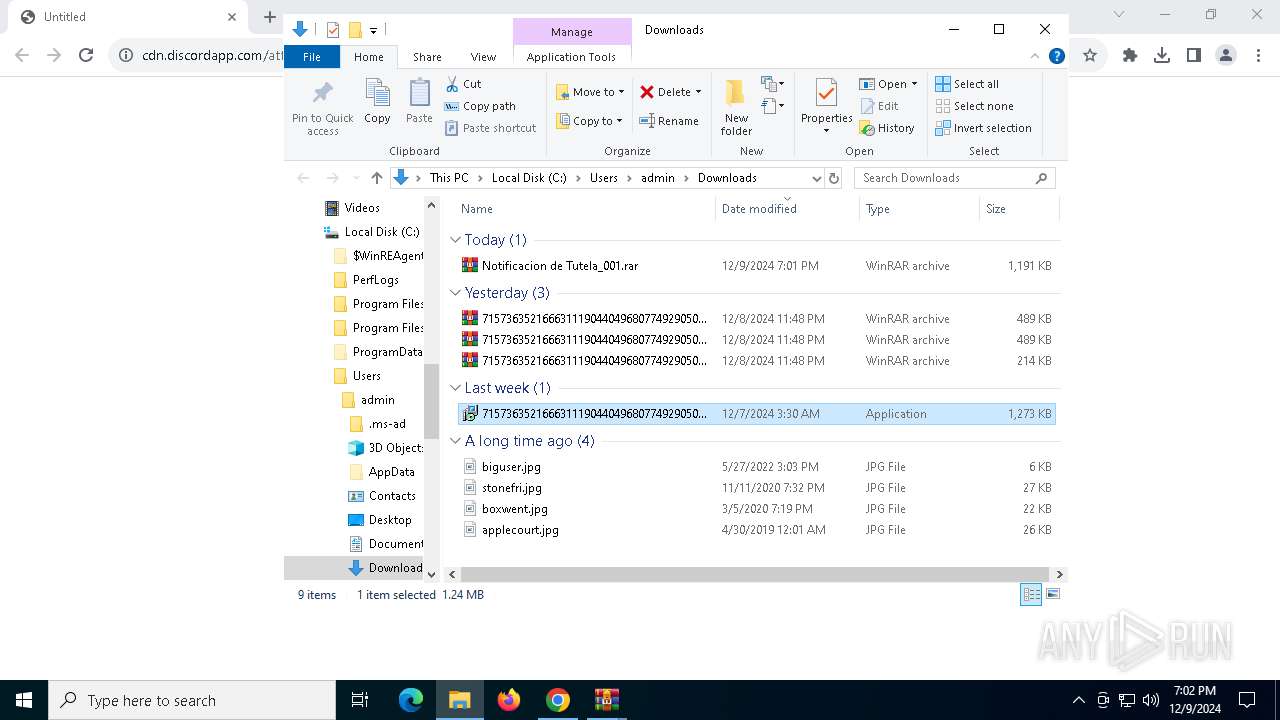
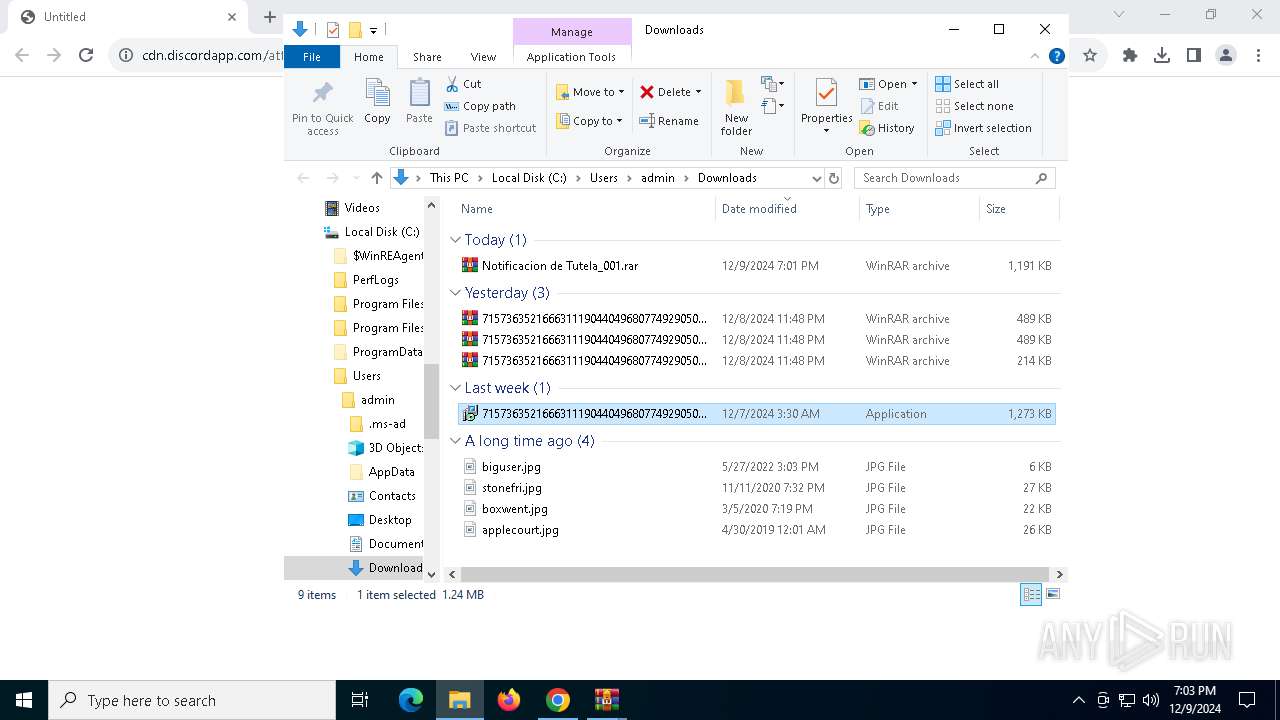
| URL: | https://cdn.discordapp.com/attachments/1310410547396739113/1315465207648354366/Notificacion_de_Tutela_001.rar?ex=675781f1&is=67563071&hm=b66b1c5aadc5634eee79ba979ff36f69154622b69bd57f0c3d737a838a844e72& |
| Full analysis: | https://app.any.run/tasks/44fe9e4b-caf4-40e2-bca9-e9868fb82156 |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | December 09, 2024, 19:00:49 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | AEDA616BC397AF8FB8EB83FC817A0F8C |
| SHA1: | 019308414E12047877A3B18CACAAD72AB09288A4 |
| SHA256: | 1ED19E878CDA447020CD142DB712681E425197E0E4DDF6C7BC77320829034BF5 |
| SSDEEP: | 3:N8cCWdy6//PU1RSbTSW9QaoTRsGEGTCWqVgVP25aY/HUHHBVv6QhchjV2BKn:2cry6XPU23LORZEUqq8T/HwsLL2BKn |
MALICIOUS
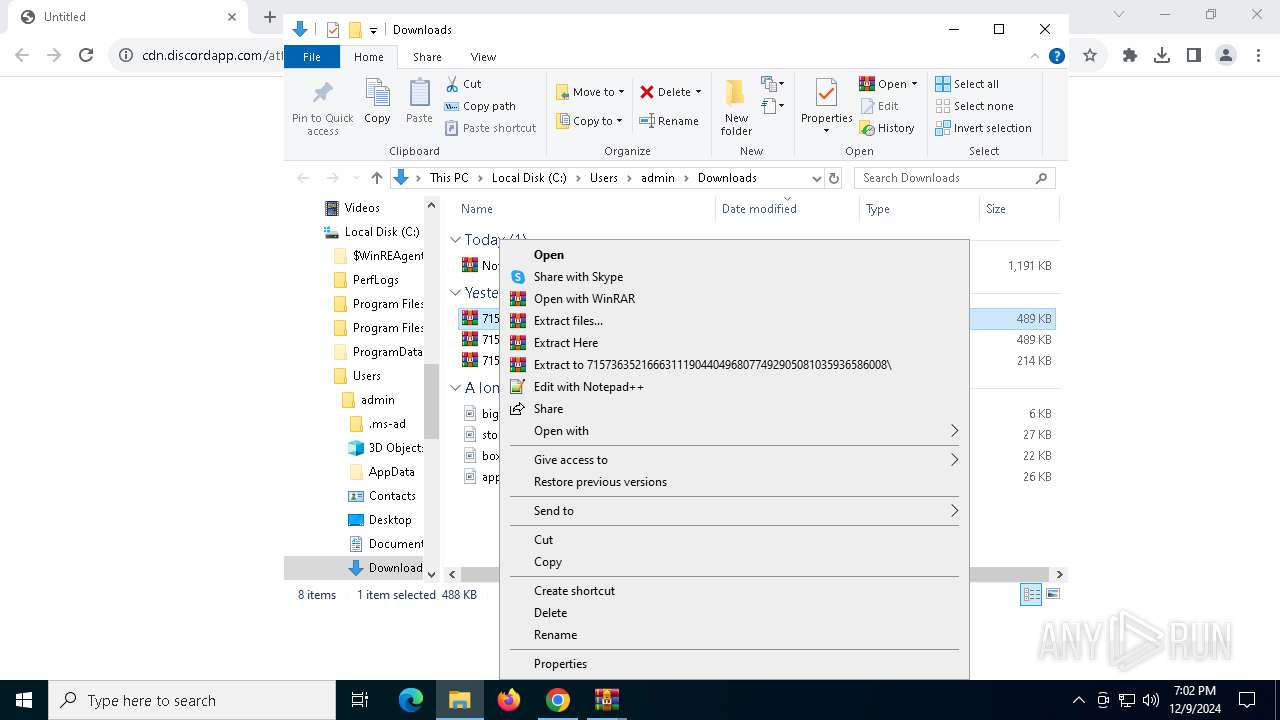
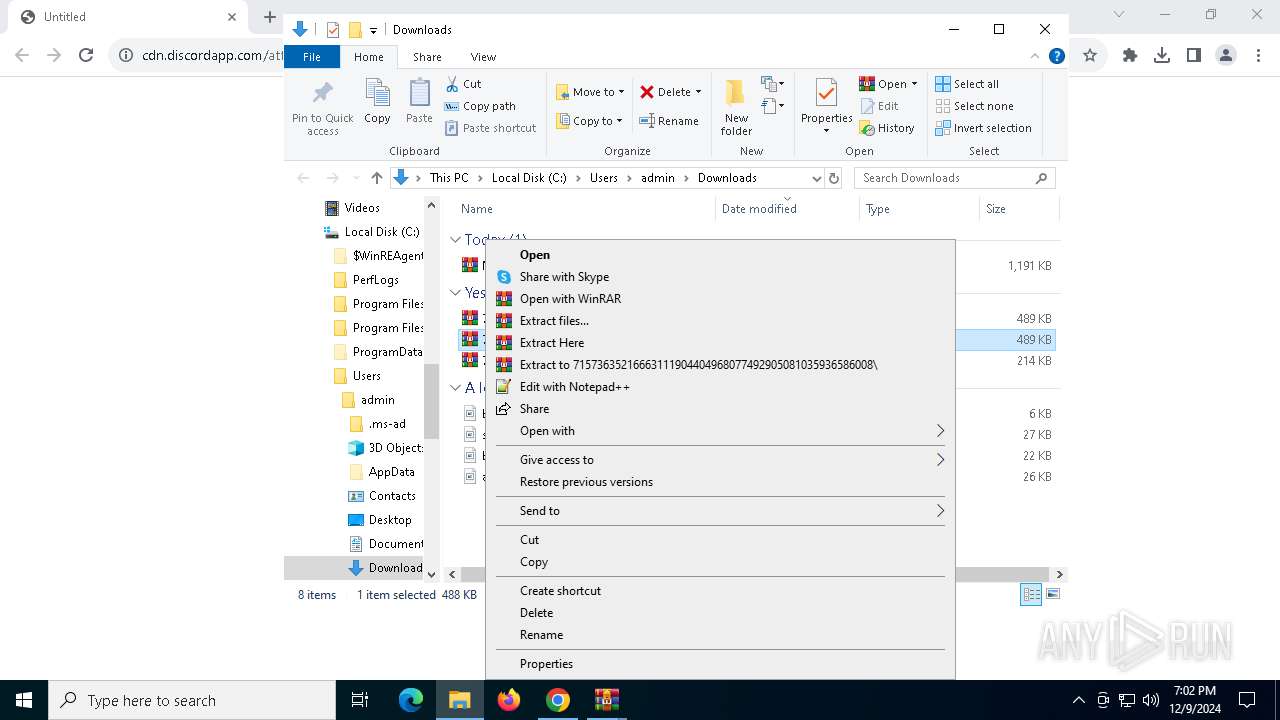
Registers / Runs the DLL via REGSVR32.EXE
- 71573635216663111904404968077492905081035936586008.tmp (PID: 5592)
AMADEY has been detected (SURICATA)
- regsvr32.exe (PID: 7156)
Connects to the CnC server
- regsvr32.exe (PID: 7156)
SUSPICIOUS
Discord domain found in command line (probably downloading payload)
- chrome.exe (PID: 4824)
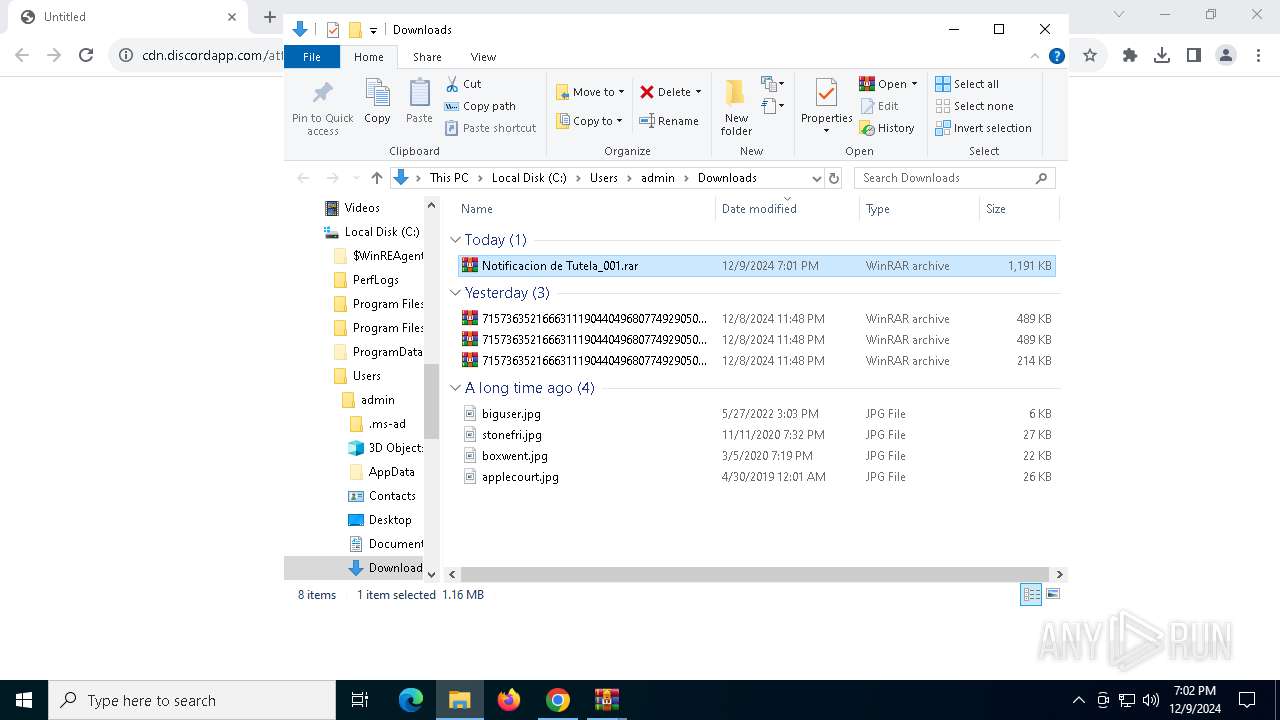
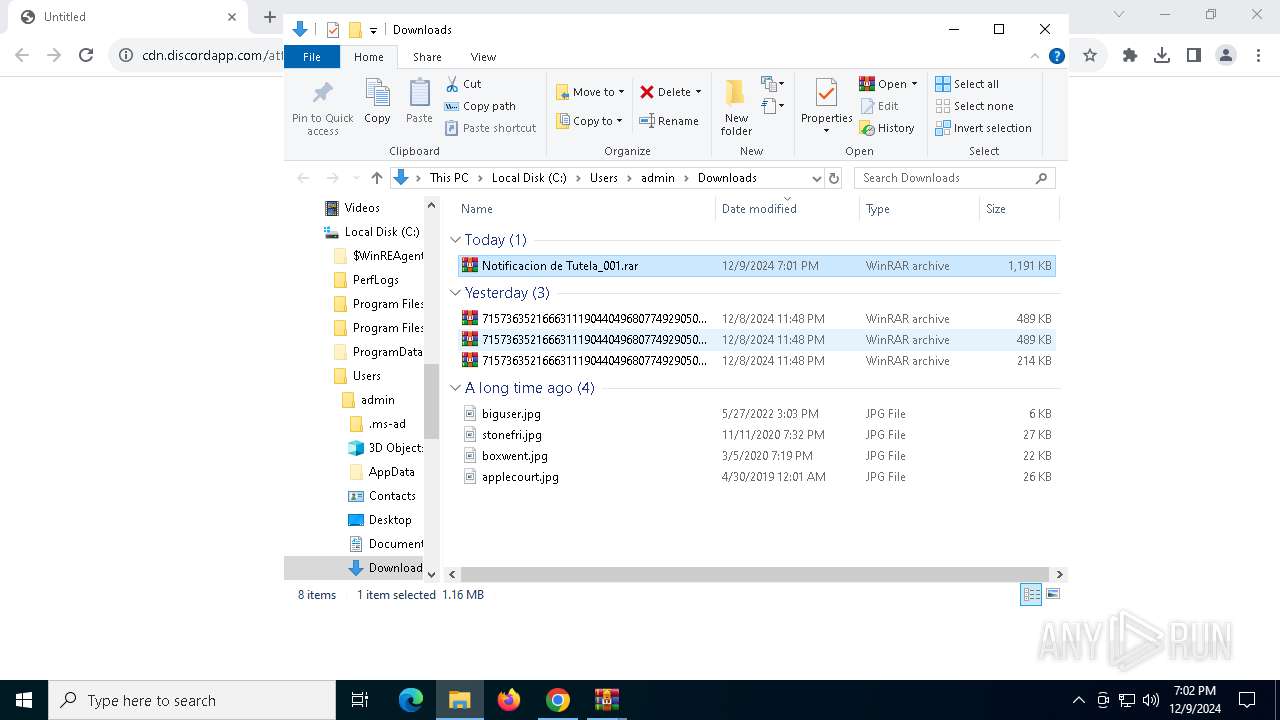
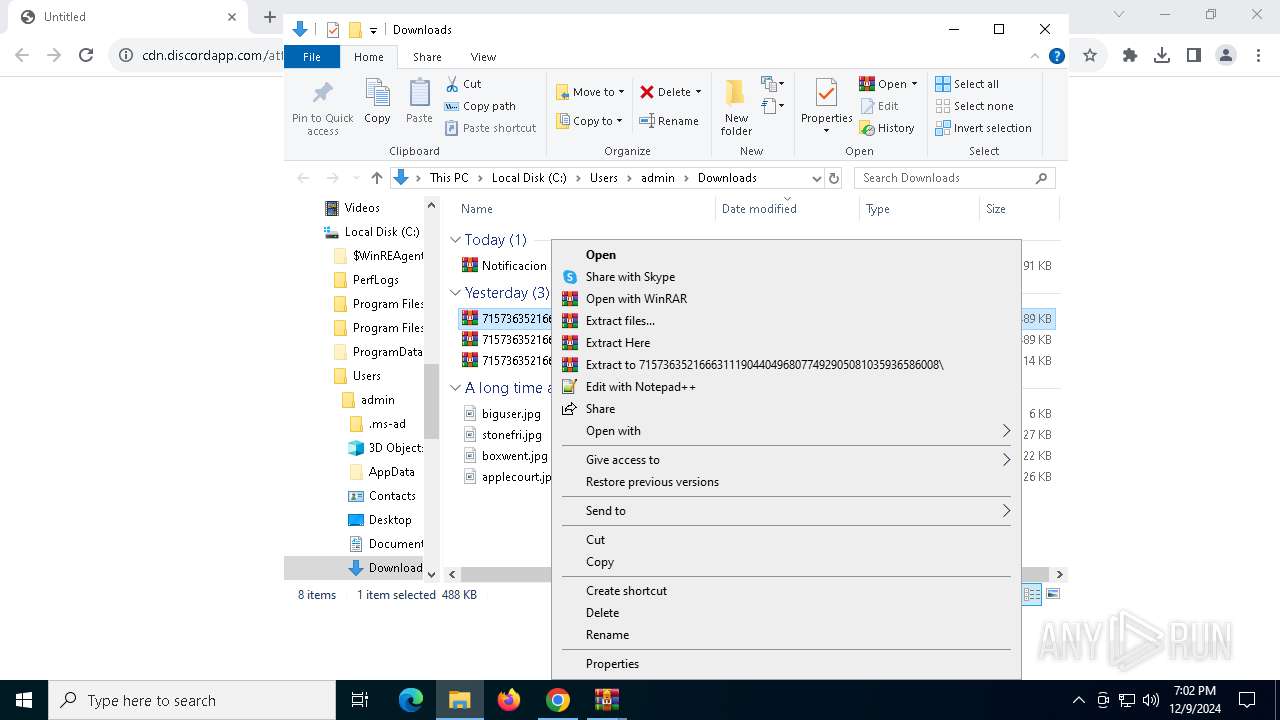
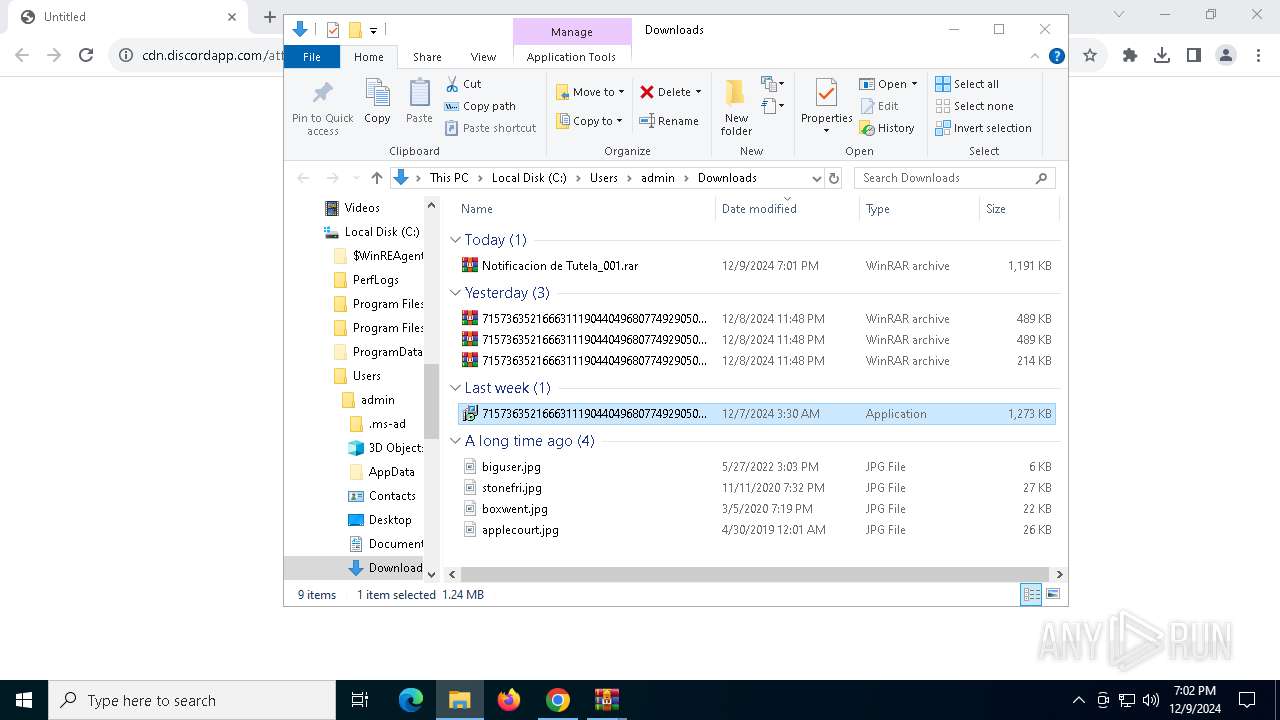
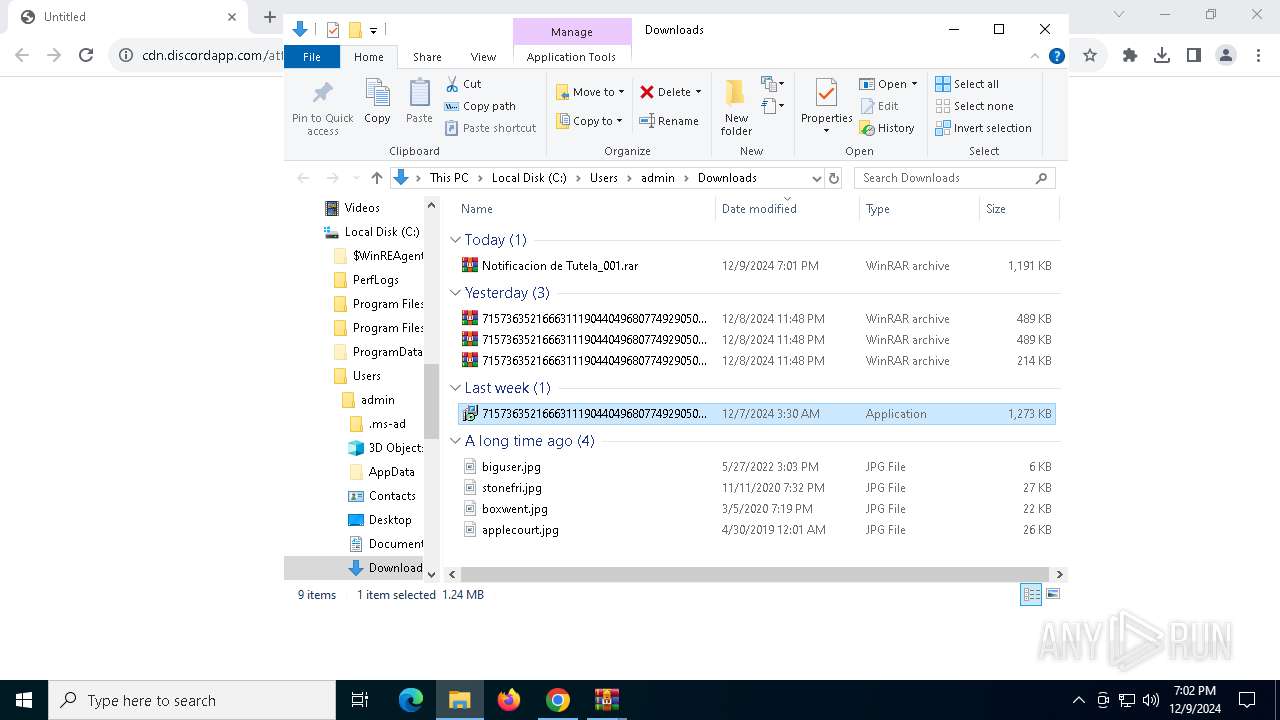
Executable content was dropped or overwritten
- 71573635216663111904404968077492905081035936586008.exe (PID: 3532)
- 71573635216663111904404968077492905081035936586008.tmp (PID: 1576)
- 71573635216663111904404968077492905081035936586008.exe (PID: 4468)
- 71573635216663111904404968077492905081035936586008.tmp (PID: 5592)
Process drops legitimate windows executable
- 71573635216663111904404968077492905081035936586008.tmp (PID: 1576)
- 71573635216663111904404968077492905081035936586008.tmp (PID: 5592)
Reads the Windows owner or organization settings
- 71573635216663111904404968077492905081035936586008.tmp (PID: 1576)
Starts CMD.EXE for commands execution
- 71573635216663111904404968077492905081035936586008.tmp (PID: 1576)
The executable file from the user directory is run by the CMD process
- 71573635216663111904404968077492905081035936586008.exe (PID: 4468)
The process checks if it is being run in the virtual environment
- regsvr32.exe (PID: 7156)
Starts POWERSHELL.EXE for commands execution
- regsvr32.exe (PID: 7156)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 3140)
Contacting a server suspected of hosting an CnC
- regsvr32.exe (PID: 7156)
Connects to the server without a host name
- regsvr32.exe (PID: 7156)
INFO
The process uses the downloaded file
- chrome.exe (PID: 4764)
- powershell.exe (PID: 5456)
Attempting to use instant messaging service
- chrome.exe (PID: 6444)
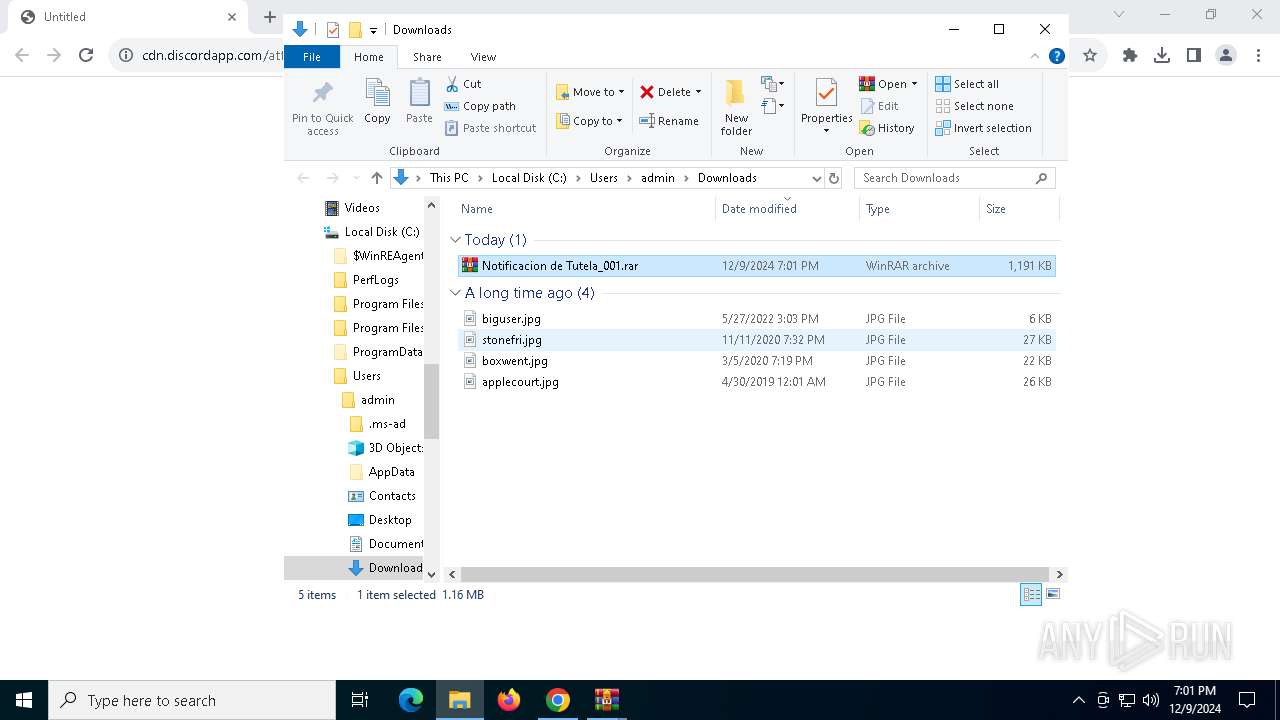
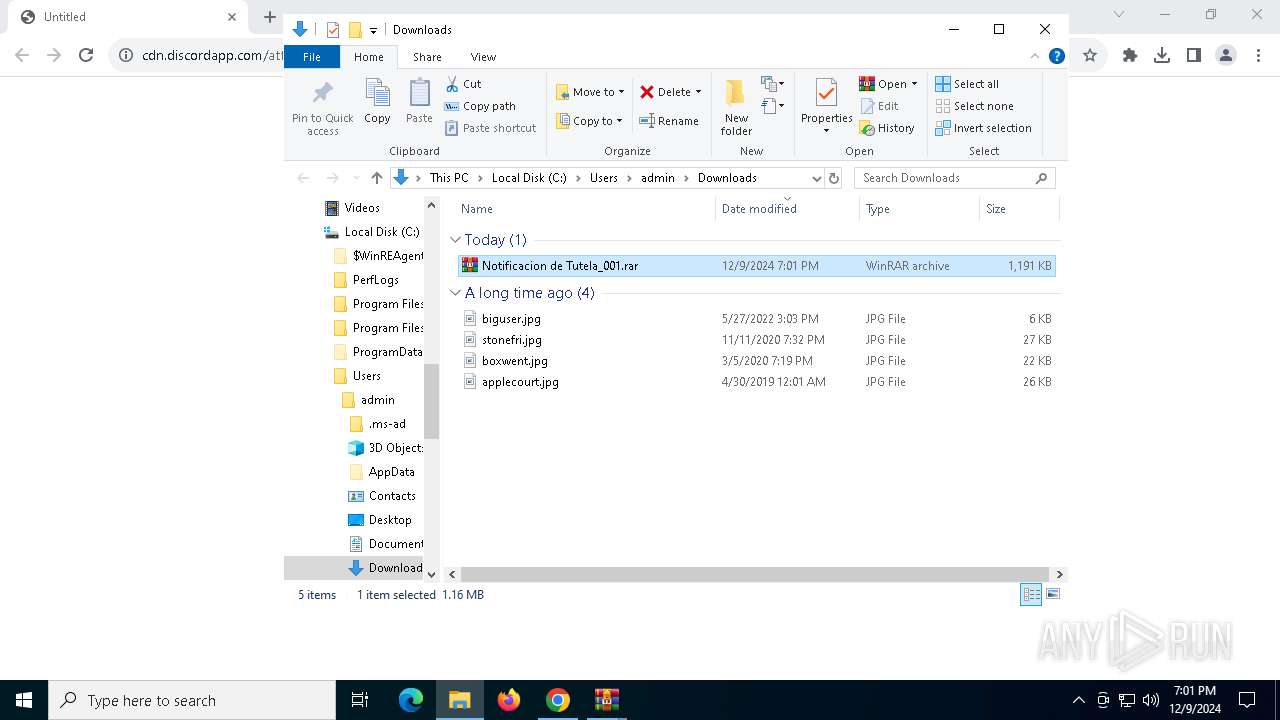
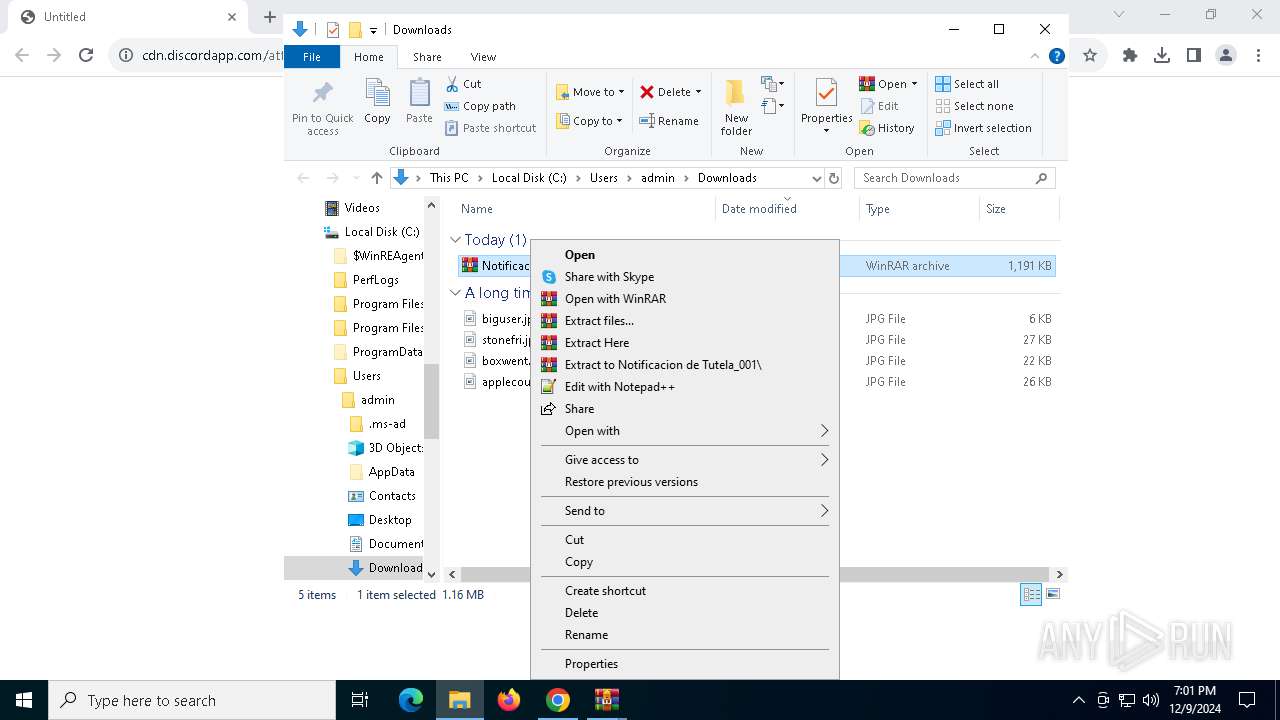
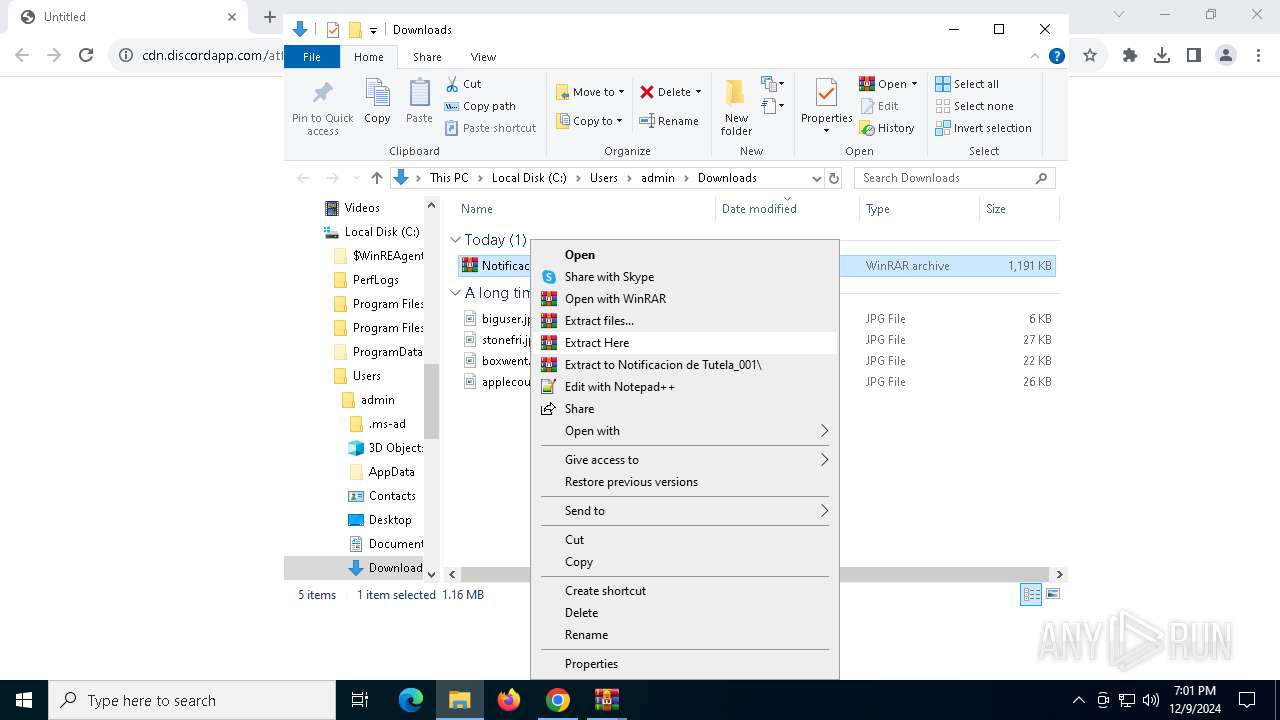
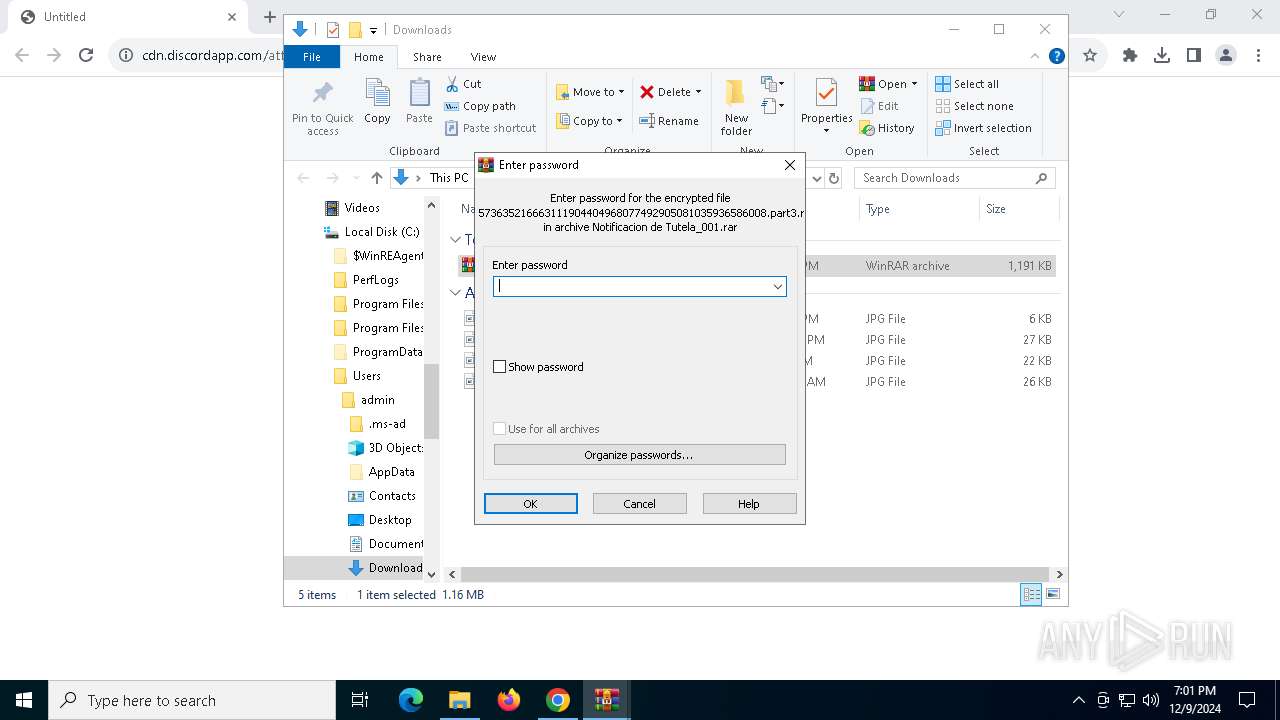
Manual execution by a user
- WinRAR.exe (PID: 4840)
- WinRAR.exe (PID: 5200)
- 71573635216663111904404968077492905081035936586008.exe (PID: 3532)
Executable content was dropped or overwritten
- chrome.exe (PID: 6632)
- WinRAR.exe (PID: 5200)
Reads Microsoft Office registry keys
- chrome.exe (PID: 4824)
Create files in a temporary directory
- 71573635216663111904404968077492905081035936586008.exe (PID: 3532)
- 71573635216663111904404968077492905081035936586008.tmp (PID: 1576)
Checks supported languages
- 71573635216663111904404968077492905081035936586008.exe (PID: 3532)
- 71573635216663111904404968077492905081035936586008.tmp (PID: 1576)
- 71573635216663111904404968077492905081035936586008.exe (PID: 4468)
- 71573635216663111904404968077492905081035936586008.tmp (PID: 5592)
Reads the computer name
- 71573635216663111904404968077492905081035936586008.tmp (PID: 1576)
Application launched itself
- chrome.exe (PID: 4824)
Creates a software uninstall entry
- 71573635216663111904404968077492905081035936586008.tmp (PID: 5592)
Creates files or folders in the user directory
- 71573635216663111904404968077492905081035936586008.tmp (PID: 5592)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 1572)
- powershell.exe (PID: 5456)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
165
Monitored processes
32
Malicious processes
4
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1380 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5192 --field-trial-handle=1900,i,6914856887729494766,15492978358853571436,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1572 | "powershell" -Command "if (Get-ScheduledTask | Where-Object { $_.Actions.Execute -eq 'regsvr32' -and $_.Actions.Arguments -eq '/S /i:INSTALL C:\Users\admin\AppData\Roaming\Seal.dat' }) { exit 0 } else { exit 1 }" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | regsvr32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1576 | "C:\Users\admin\AppData\Local\Temp\is-9PEBK.tmp\71573635216663111904404968077492905081035936586008.tmp" /SL5="$A0368,922702,140800,C:\Users\admin\Downloads\71573635216663111904404968077492905081035936586008.exe" | C:\Users\admin\AppData\Local\Temp\is-9PEBK.tmp\71573635216663111904404968077492905081035936586008.tmp | 71573635216663111904404968077492905081035936586008.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2124 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2600 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\Notificacion de Tutela_001.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | chrome.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 3140 | "cmd.exe" /C timeout /T 3 & "C:\Users\admin\Downloads\71573635216663111904404968077492905081035936586008.exe" /VERYSILENT /SUPPRESSMSGBOXES | C:\Windows\SysWOW64\cmd.exe | — | 71573635216663111904404968077492905081035936586008.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3420 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5124 --field-trial-handle=1900,i,6914856887729494766,15492978358853571436,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 3532 | "C:\Users\admin\Downloads\71573635216663111904404968077492905081035936586008.exe" | C:\Users\admin\Downloads\71573635216663111904404968077492905081035936586008.exe | explorer.exe | ||||||||||||
User: admin Company: Integrity Level: MEDIUM Description: Short Mole Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 3700 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\Notificacion de Tutela_001.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | chrome.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 4468 | "C:\Users\admin\Downloads\71573635216663111904404968077492905081035936586008.exe" /VERYSILENT /SUPPRESSMSGBOXES | C:\Users\admin\Downloads\71573635216663111904404968077492905081035936586008.exe | cmd.exe | ||||||||||||
User: admin Company: Integrity Level: MEDIUM Description: Short Mole Setup Exit code: 0 Version: Modules
| |||||||||||||||
Total events
27 250
Read events
27 175
Write events
65
Delete events
10
Modification events
| (PID) Process: | (4824) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4824) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4824) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4824) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4824) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (4764) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 0100000000000000A7D7CDB16C4ADB01 | |||
| (PID) Process: | (4824) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.rar\OpenWithProgids |
| Operation: | write | Name: | WinRAR |
Value: | |||
| (PID) Process: | (2600) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (2600) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (2600) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
Executable files
12
Suspicious files
90
Text files
40
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4824 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF135cd9.TMP | — | |
MD5:— | SHA256:— | |||
| 4824 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF135cd9.TMP | — | |
MD5:— | SHA256:— | |||
| 4824 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4824 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4824 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF135cd9.TMP | — | |
MD5:— | SHA256:— | |||
| 4824 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF135cd9.TMP | — | |
MD5:— | SHA256:— | |||
| 4824 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4824 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4824 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF135cd9.TMP | — | |
MD5:— | SHA256:— | |||
| 4824 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF135cd9.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
46
DNS requests
34
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2380 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
2380 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/im3uvul45we66nqsfish5fq4yi_2024.12.8.1/jflhchccmppkfebkiaminageehmchikm_2024.12.08.01_all_acje4vglgrlqv4ciry2glhhkjvxq.crx3 | unknown | — | — | whitelisted |
2380 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
2380 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
2380 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
2380 | svchost.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/im3uvul45we66nqsfish5fq4yi_2024.12.8.1/jflhchccmppkfebkiaminageehmchikm_2024.12.08.01_all_acje4vglgrlqv4ciry2glhhkjvxq.crx3 | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.18.121.139:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.200.189.225:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1488 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.18.121.139:80 | crl.microsoft.com | AKAMAI-AS | FR | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.200.189.225:80 | www.microsoft.com | Moratelindo Internet Exchange Point | ID | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 2.16.106.196:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4824 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6444 | chrome.exe | 162.159.134.233:443 | cdn.discordapp.com | CLOUDFLARENET | — | shared |
6444 | chrome.exe | 173.194.79.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
cdn.discordapp.com |
| shared |
accounts.google.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6444 | chrome.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
6444 | chrome.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
7156 | regsvr32.exe | Malware Command and Control Activity Detected | BOTNET [ANY.RUN] Amadey HTTP POST Request (st=s) |
1 ETPRO signatures available at the full report