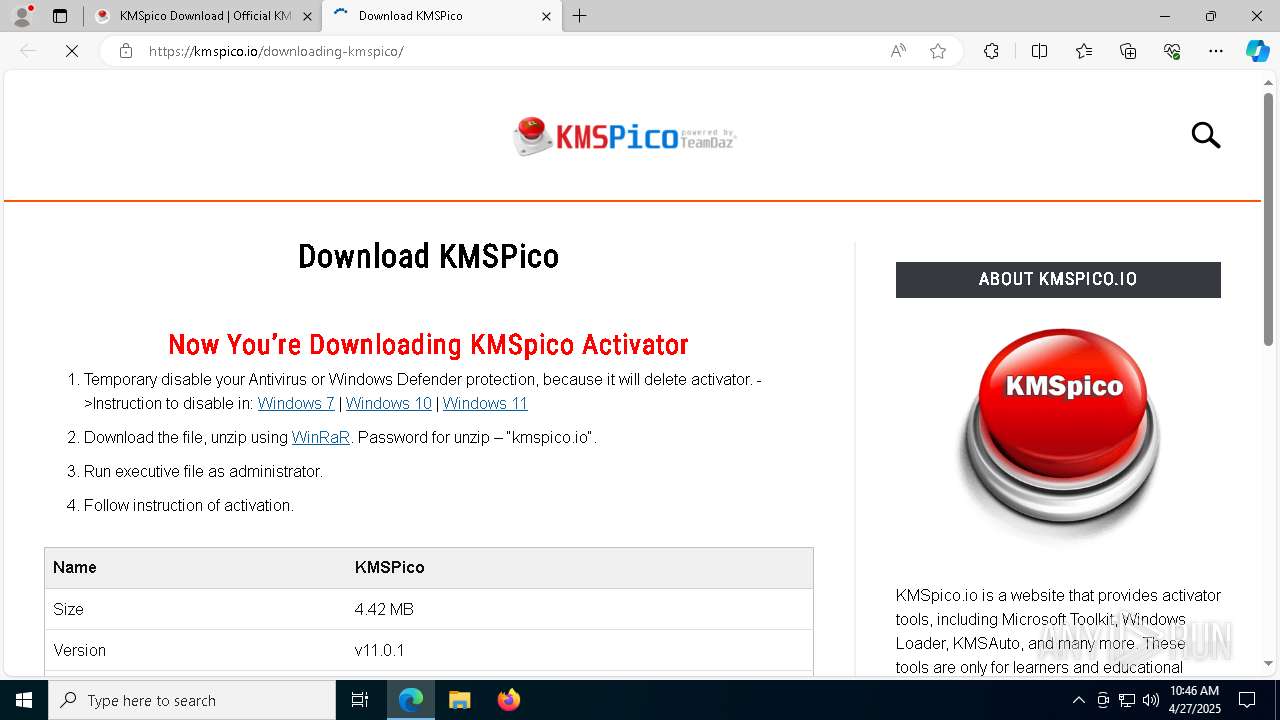
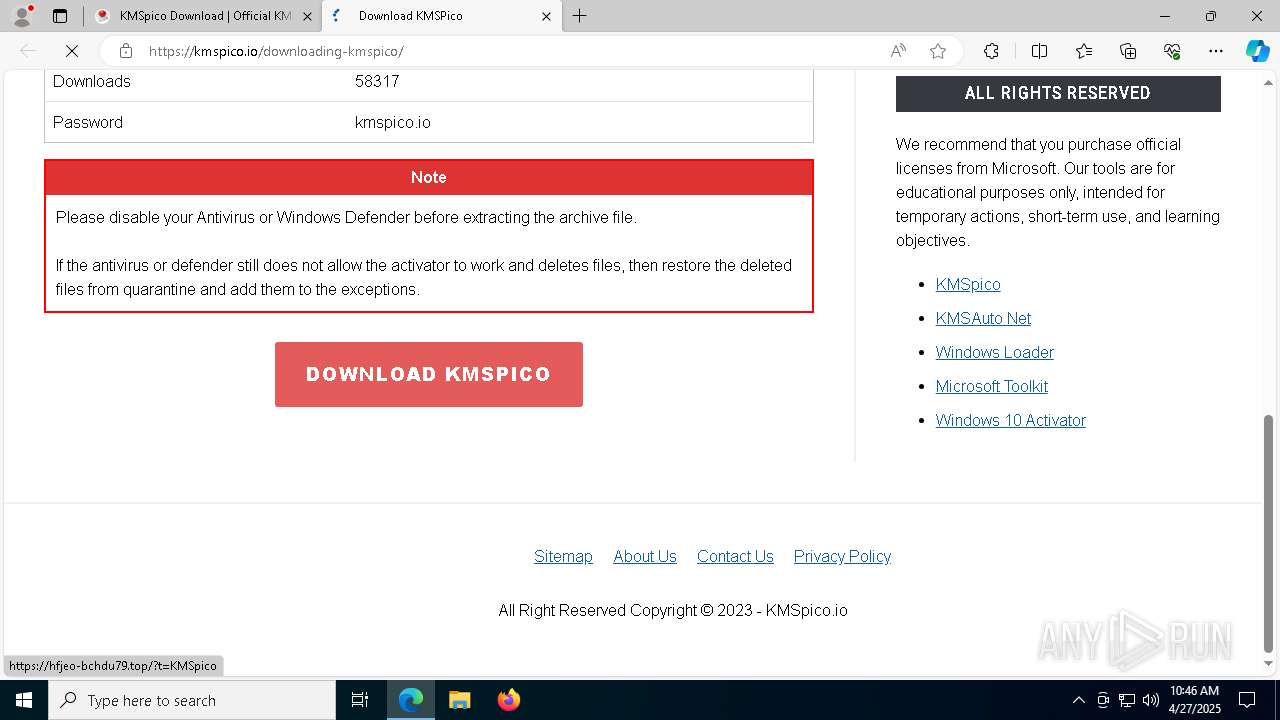
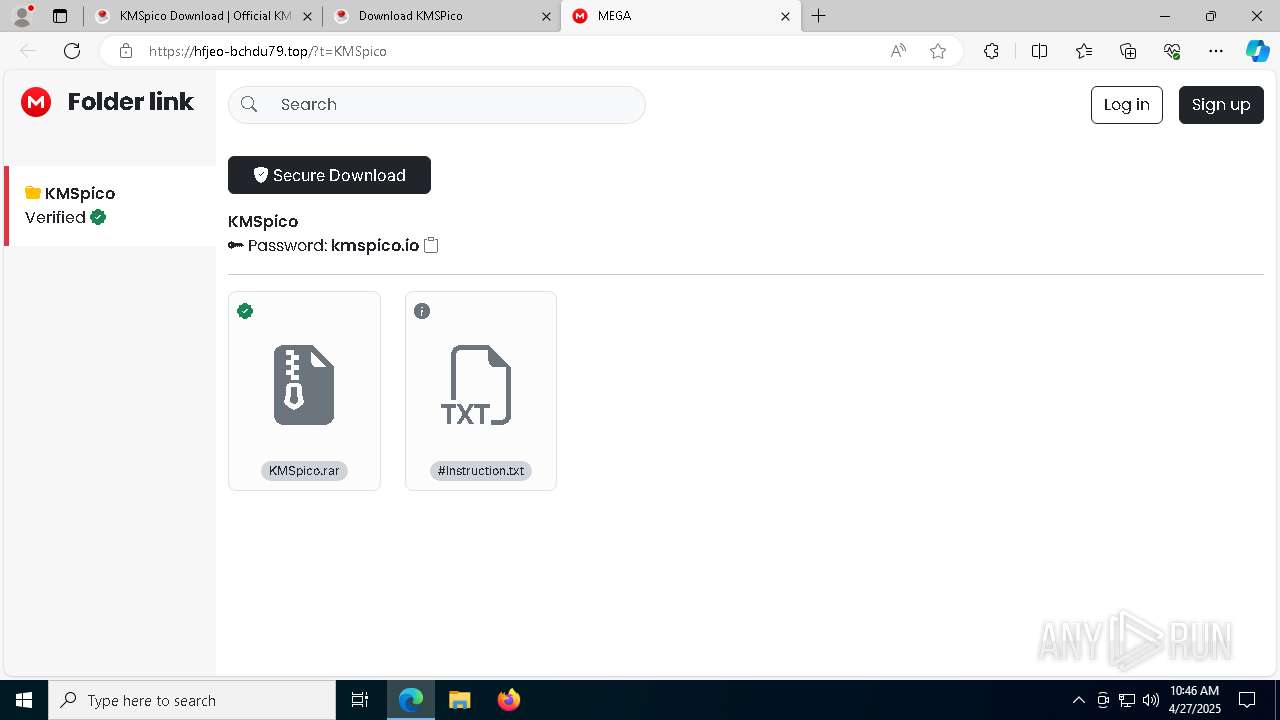
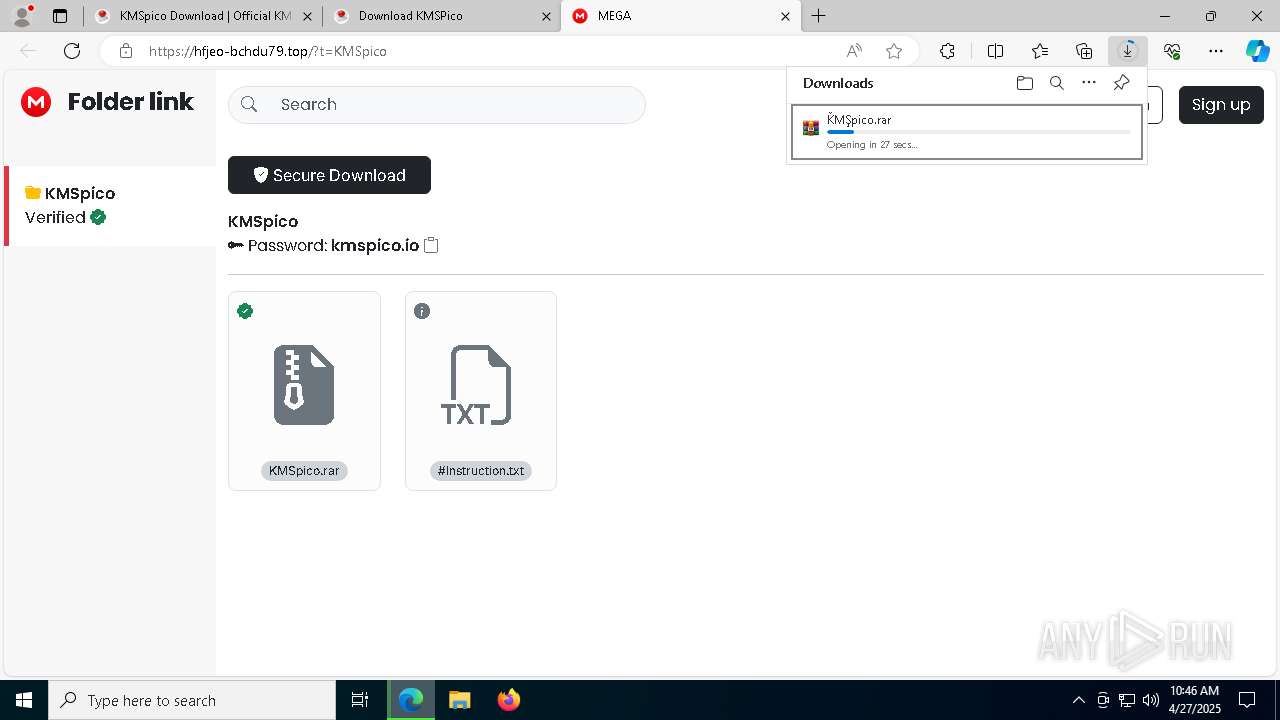
| URL: | https://kmspico.io/ |
| Full analysis: | https://app.any.run/tasks/64739be7-2326-4de7-88c1-32724e0a3b7f |
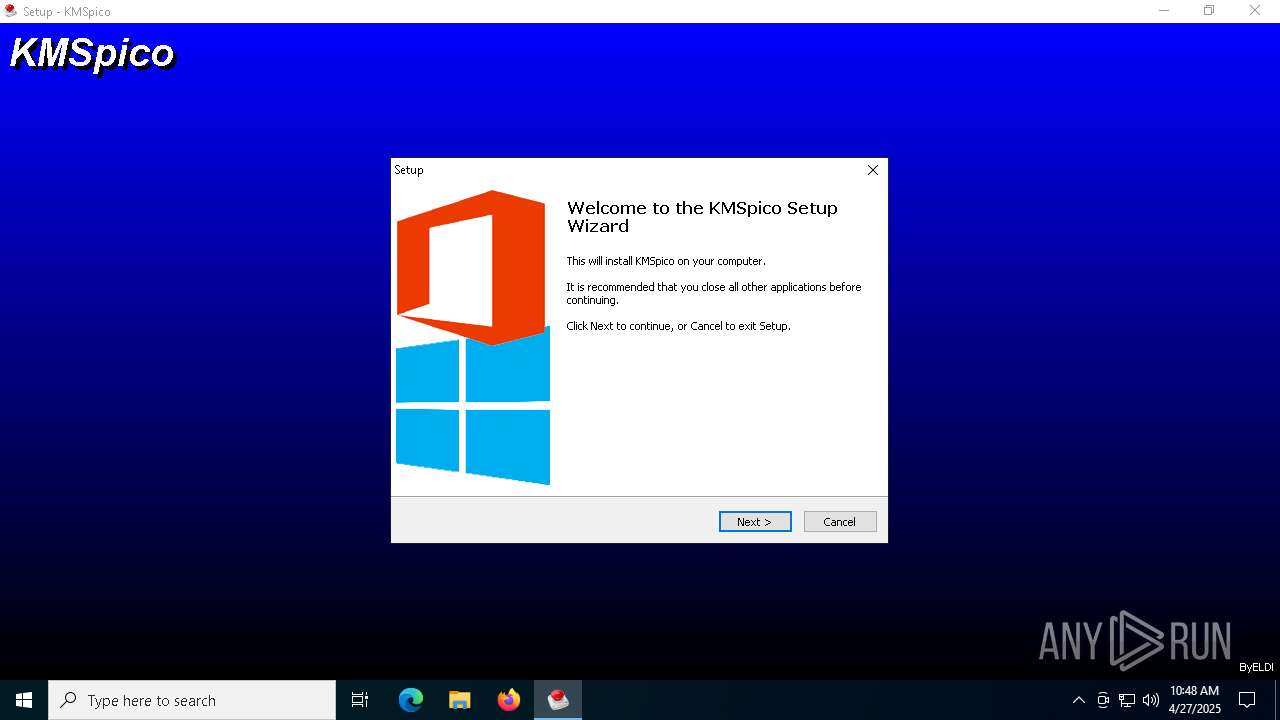
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | April 27, 2025, 10:45:42 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | EFF322499A6DC1C2A439874DC93541A6 |
| SHA1: | C53ABAFB84B7A2FC0CD9EBC363346F9EF06BEADB |
| SHA256: | 1E2A39CD89239D282E8C4600F88A0C88E89487619655E62341DE25B81A44DB32 |
| SSDEEP: | 3:N8N/JKn:2dEn |
MALICIOUS
Connects to the CnC server
- msedge.exe (PID: 7440)
- svchost.exe (PID: 2196)
GENERIC has been found (auto)
- KMSpico.tmp (PID: 7816)
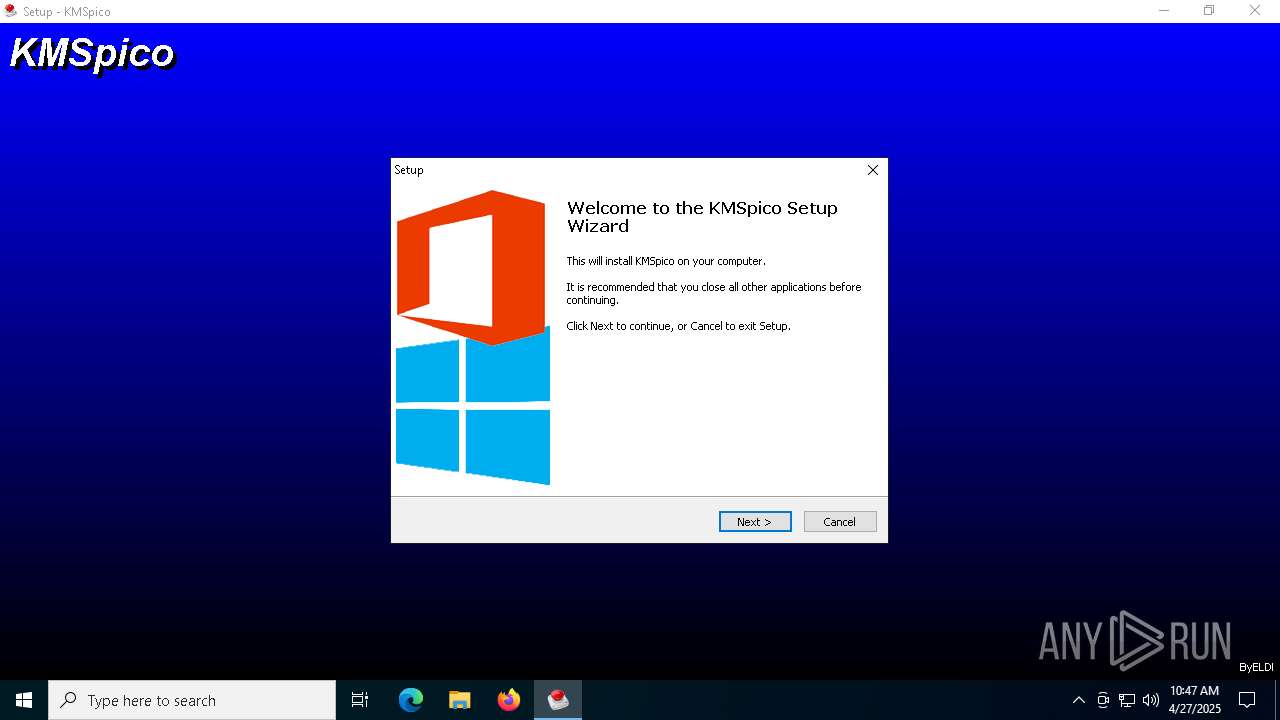
Executing a file with an untrusted certificate
- KMSpico.exe (PID: 4464)
- KMSpico.exe (PID: 7720)
- core.exe (PID: 7600)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2196)
LUMMA has been detected (YARA)
- core.exe (PID: 7600)
SUSPICIOUS
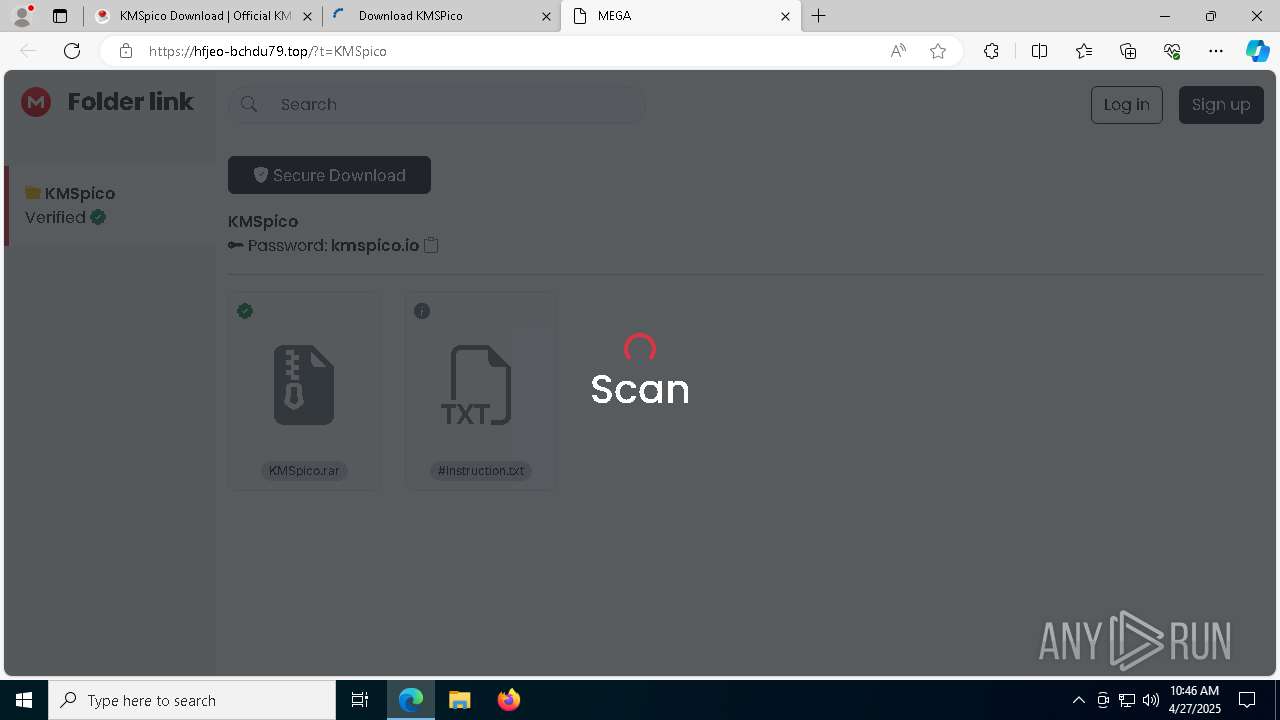
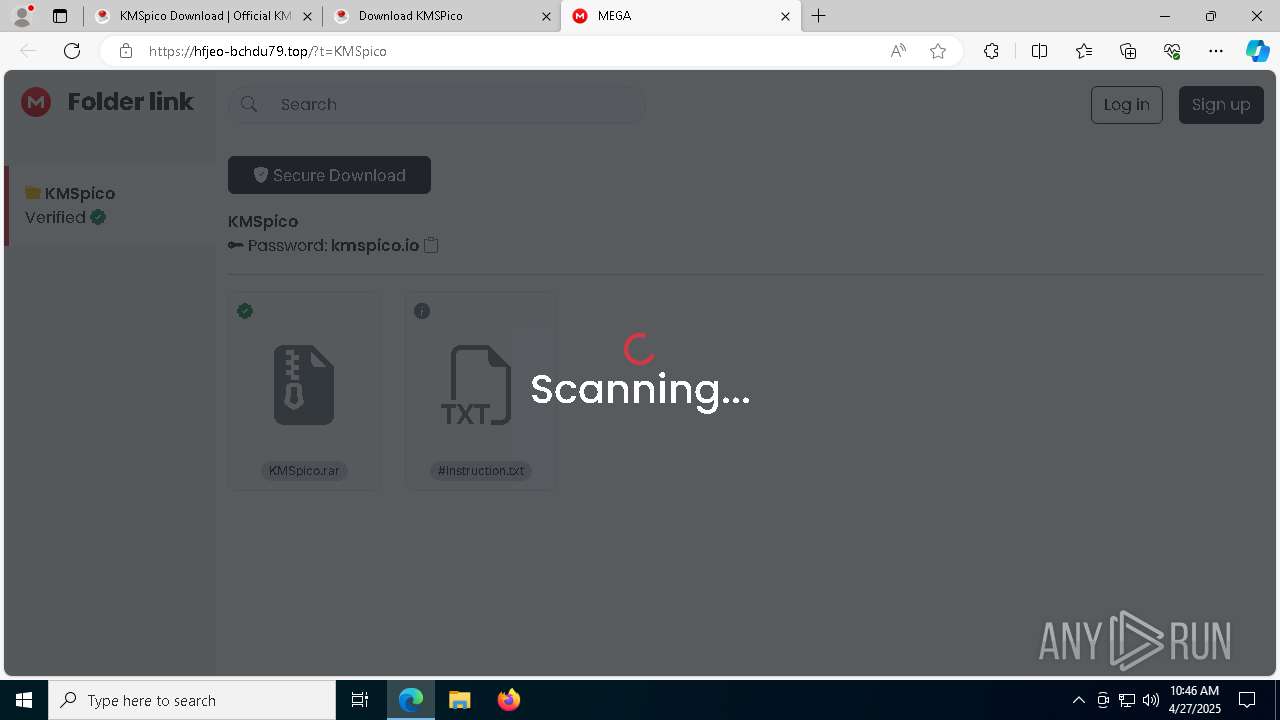
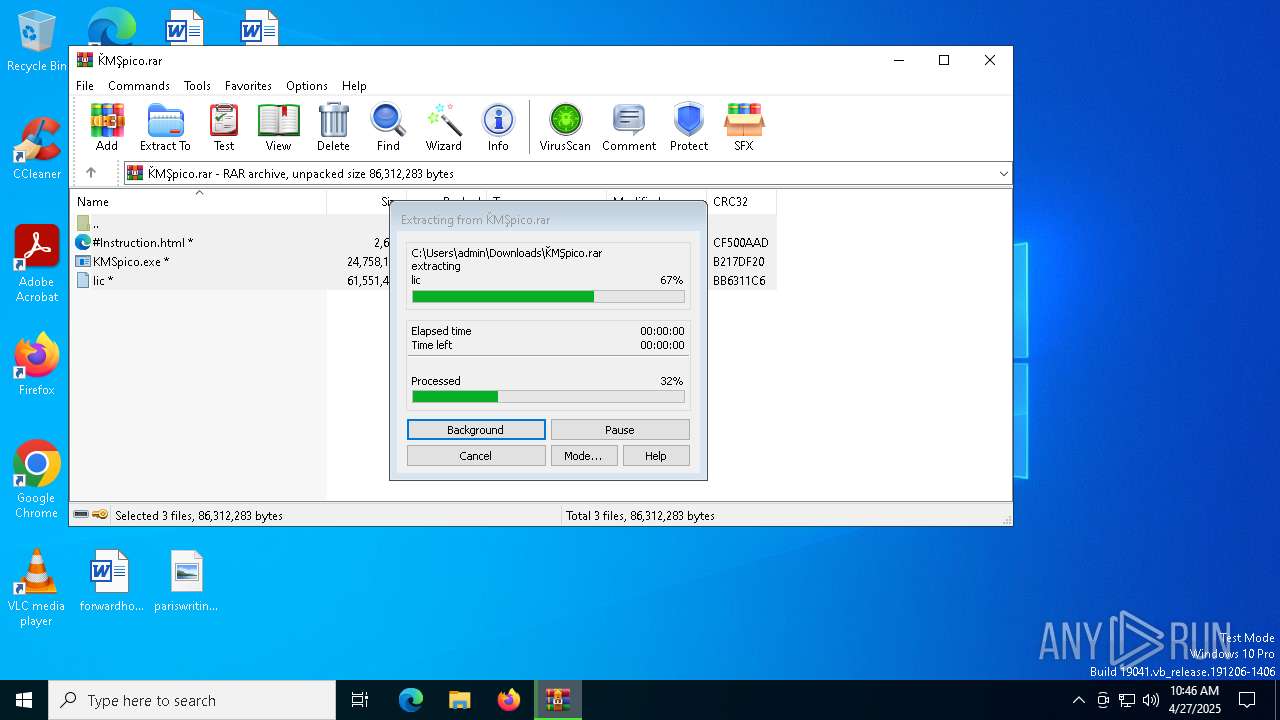
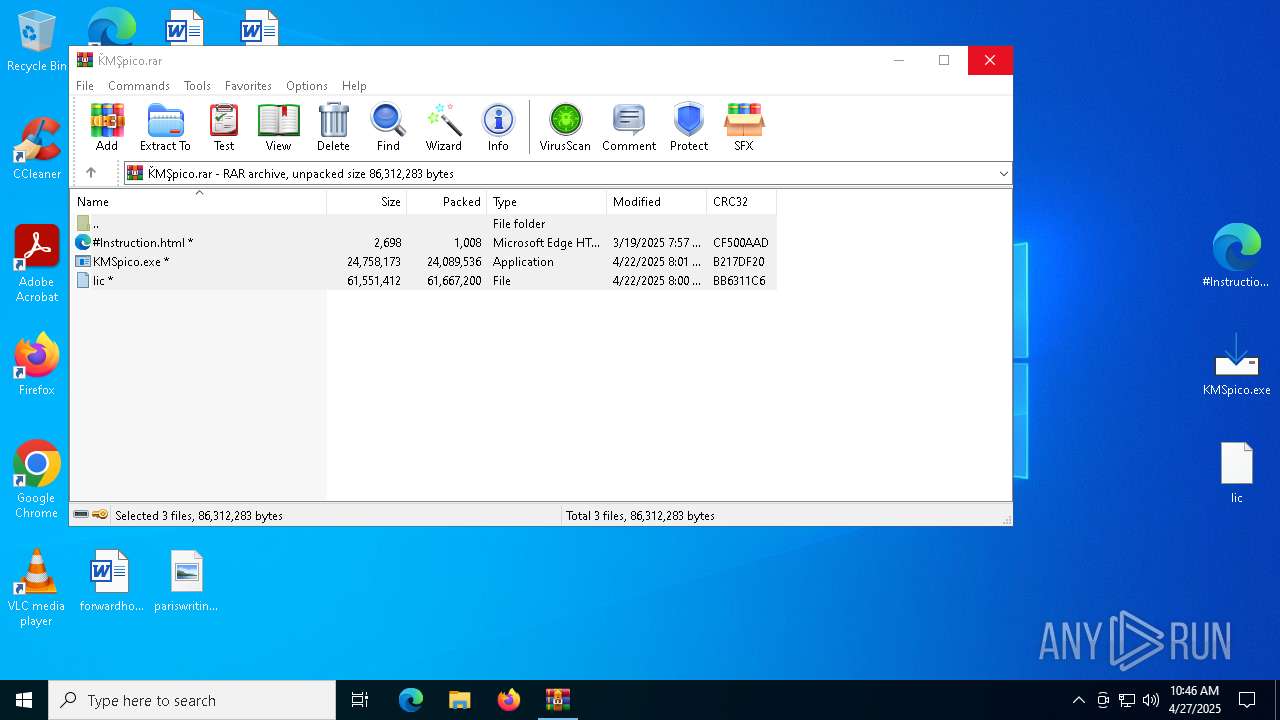
Executable content was dropped or overwritten
- KMSpico.tmp (PID: 7816)
- KMSpico.exe (PID: 4628)
- KMSpico.exe (PID: 4464)
- KMSpico.exe (PID: 7720)
- KMSpico.tmp (PID: 7744)
Reads the Windows owner or organization settings
- KMSpico.tmp (PID: 7816)
- KMSpico.tmp (PID: 7744)
Reads security settings of Internet Explorer
- KMSpico.tmp (PID: 7816)
- KMSpico.tmp (PID: 7928)
Process drops legitimate windows executable
- KMSpico.tmp (PID: 7744)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2196)
INFO
Application launched itself
- msedge.exe (PID: 7200)
- msedge.exe (PID: 5260)
Reads Environment values
- identity_helper.exe (PID: 8012)
- identity_helper.exe (PID: 5244)
Reads the computer name
- identity_helper.exe (PID: 8012)
- identity_helper.exe (PID: 5244)
- KMSpico.tmp (PID: 7816)
- KMSpico.tmp (PID: 7928)
- KMSpico.tmp (PID: 7744)
- core.exe (PID: 7600)
Reads Microsoft Office registry keys
- msedge.exe (PID: 7200)
Checks supported languages
- identity_helper.exe (PID: 8012)
- identity_helper.exe (PID: 5244)
- KMSpico.exe (PID: 4628)
- KMSpico.tmp (PID: 7816)
- KMSpico.tmp (PID: 7928)
- KMSpico.exe (PID: 4464)
- KMSpico.exe (PID: 7720)
- KMSpico.tmp (PID: 7744)
- core.exe (PID: 7600)
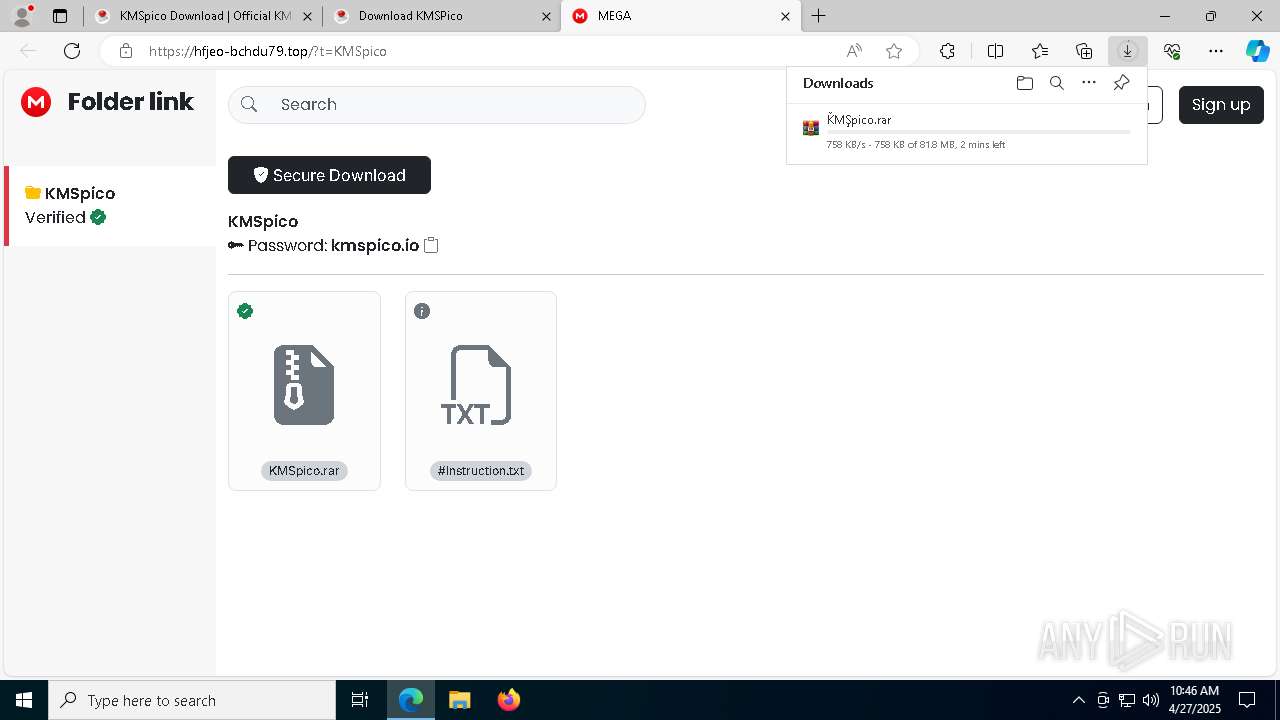
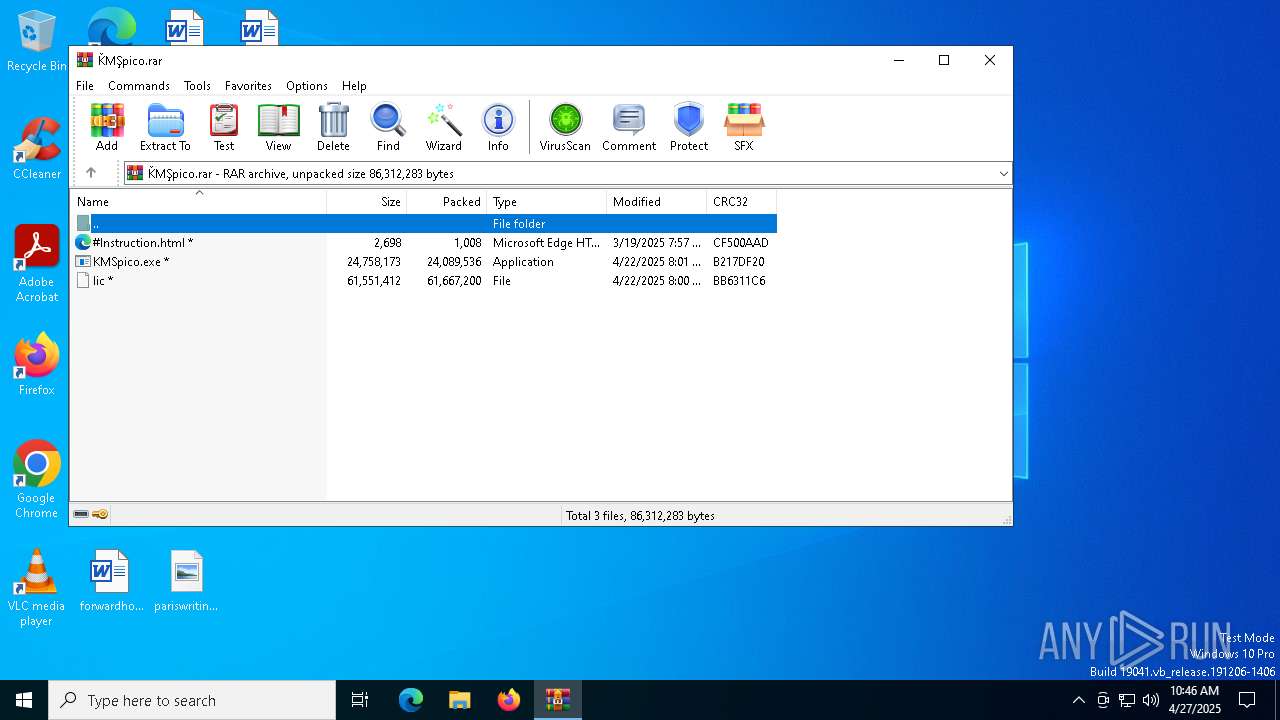
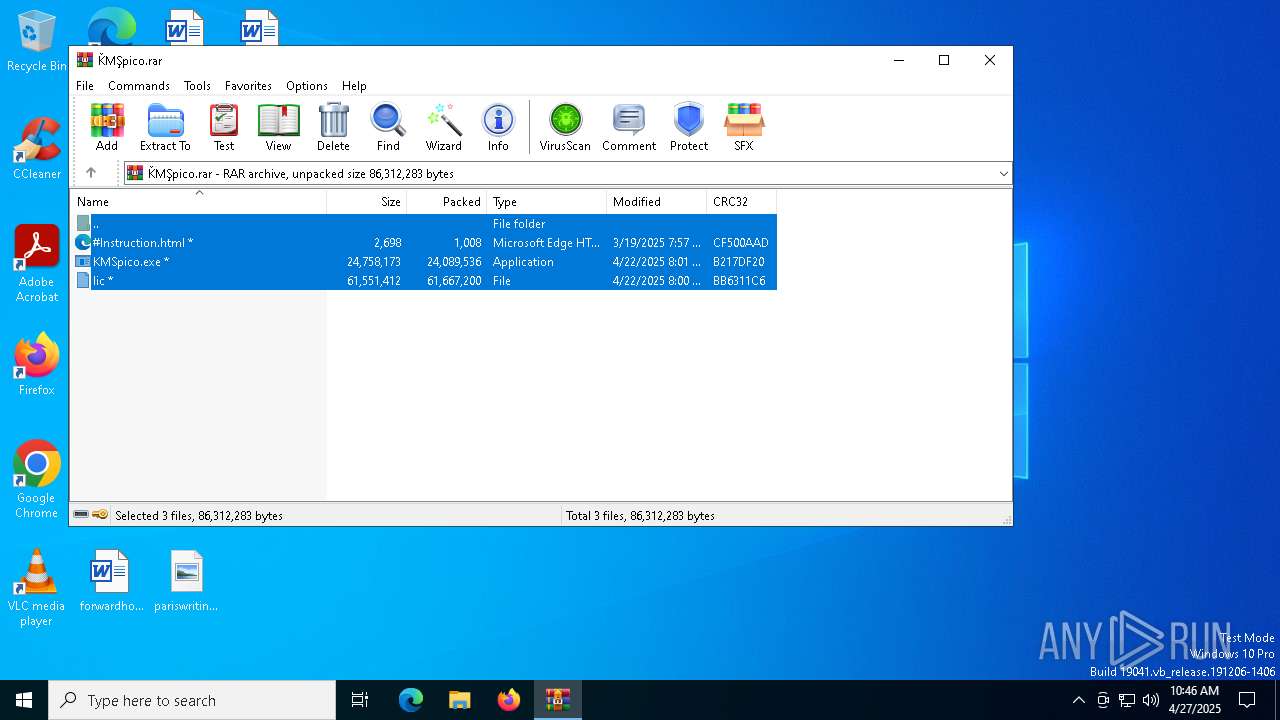
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2344)
Manual execution by a user
- KMSpico.exe (PID: 4628)
Create files in a temporary directory
- KMSpico.exe (PID: 4628)
- KMSpico.tmp (PID: 7816)
- KMSpico.exe (PID: 4464)
- KMSpico.exe (PID: 7720)
- KMSpico.tmp (PID: 7744)
Creates files or folders in the user directory
- KMSpico.tmp (PID: 7816)
Compiled with Borland Delphi (YARA)
- KMSpico.exe (PID: 4628)
- KMSpico.tmp (PID: 7816)
- KMSpico.tmp (PID: 7928)
- KMSpico.tmp (PID: 7744)
Detects InnoSetup installer (YARA)
- KMSpico.exe (PID: 4628)
- KMSpico.tmp (PID: 7816)
- KMSpico.exe (PID: 4464)
- KMSpico.tmp (PID: 7928)
- KMSpico.exe (PID: 7720)
- KMSpico.tmp (PID: 7744)
Reads the software policy settings
- slui.exe (PID: 7184)
- core.exe (PID: 7600)
Process checks computer location settings
- KMSpico.tmp (PID: 7816)
- KMSpico.tmp (PID: 7928)
Creates a software uninstall entry
- KMSpico.tmp (PID: 7816)
The sample compiled with english language support
- KMSpico.tmp (PID: 7744)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
213
Monitored processes
76
Malicious processes
7
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 780 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6820 --field-trial-handle=2444,i,13976218461890432442,3822344928939579270,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 864 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4308 --field-trial-handle=2444,i,13976218461890432442,3822344928939579270,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1052 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --onnx-enabled-for-ee --no-appcompat-clear --mojo-platform-channel-handle=5404 --field-trial-handle=2444,i,13976218461890432442,3822344928939579270,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1056 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6100 --field-trial-handle=2444,i,13976218461890432442,3822344928939579270,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1088 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://kmspico.io/" | C:\Program Files\Internet Explorer\iexplore.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1660 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6684 --field-trial-handle=2444,i,13976218461890432442,3822344928939579270,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2092 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=5244 --field-trial-handle=2344,i,8931658027200829596,2078873078705316936,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2288 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --extension-process --renderer-sub-type=extension --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=3552 --field-trial-handle=2344,i,8931658027200829596,2078873078705316936,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
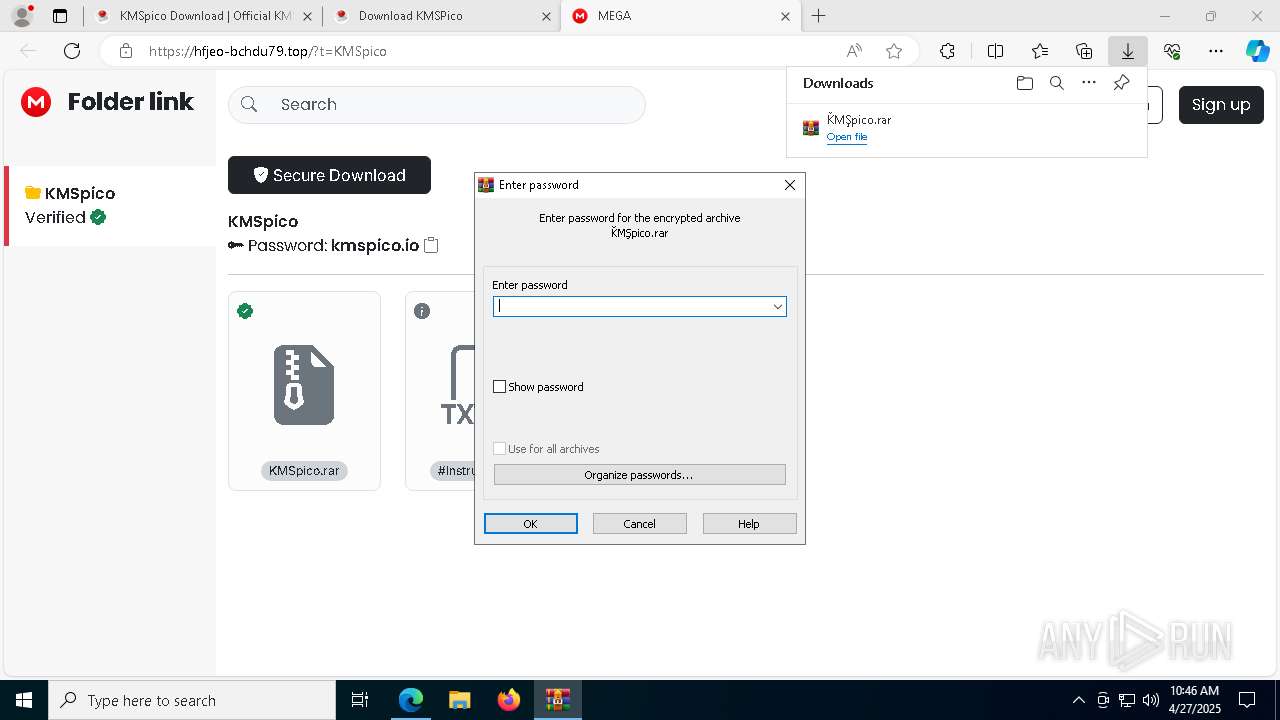
| 2344 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\ǨMŞpico.rar" | C:\Program Files\WinRAR\WinRAR.exe | msedge.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
13 352
Read events
13 265
Write events
87
Delete events
0
Modification events
| (PID) Process: | (1088) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1088) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1088) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1088) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1088) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (1088) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | DisableFirstRunCustomize |
Value: 1 | |||
| (PID) Process: | (7200) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7200) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7200) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7200) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
Executable files
27
Suspicious files
410
Text files
104
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7200 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b4db.TMP | — | |
MD5:— | SHA256:— | |||
| 7200 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b4db.TMP | — | |
MD5:— | SHA256:— | |||
| 7200 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b4db.TMP | — | |
MD5:— | SHA256:— | |||
| 7200 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7200 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7200 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7200 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b509.TMP | — | |
MD5:— | SHA256:— | |||
| 7200 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7200 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b529.TMP | — | |
MD5:— | SHA256:— | |||
| 7200 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
43
TCP/UDP connections
111
DNS requests
124
Threats
24
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3884 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.164:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7440 | msedge.exe | GET | 200 | 45.12.1.24:80 | http://kmspico.io/wp-content/uploads/2020/10/download-kmspico.png | unknown | — | — | malicious |
7440 | msedge.exe | GET | 200 | 45.12.1.24:80 | http://kmspico.io/wp-content/uploads/2020/10/kmspico-activator-1024x703.png | unknown | — | — | malicious |
7440 | msedge.exe | GET | 200 | 45.12.1.24:80 | http://kmspico.io/wp-content/uploads/2020/10/kmspico-software-1024x553.png | unknown | — | — | malicious |
7440 | msedge.exe | GET | 200 | 45.12.1.24:80 | http://kmspico.io/wp-content/uploads/2020/10/how-to-install-kmspico-1024x590.png | unknown | — | — | malicious |
7440 | msedge.exe | GET | 200 | 45.12.1.24:80 | http://kmspico.io/wp-content/uploads/2020/10/kmspico-windows-10-1024x576.png | unknown | — | — | malicious |
7440 | msedge.exe | GET | 200 | 45.12.1.24:80 | http://kmspico.io/wp-content/uploads/2020/10/kmspico-official-download-1024x574.png | unknown | — | — | malicious |
7440 | msedge.exe | GET | 200 | 45.12.1.24:80 | http://kmspico.io/wp-content/uploads/2020/10/kmspico-windows-10-activator-1.png | unknown | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.164:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7200 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7440 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7440 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7440 | msedge.exe | 45.12.1.24:443 | kmspico.io | Virtual Systems LLC | UA | malicious |
7440 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
kmspico.io |
| malicious |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7440 | msedge.exe | Misc Attack | ET Threatview.io High Confidence Cobalt Strike C2 IP group 12 |
7440 | msedge.exe | Misc Attack | ET Threatview.io High Confidence Cobalt Strike C2 IP group 13 |
7440 | msedge.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
7440 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7440 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
7440 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7440 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
7440 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7440 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7440 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |