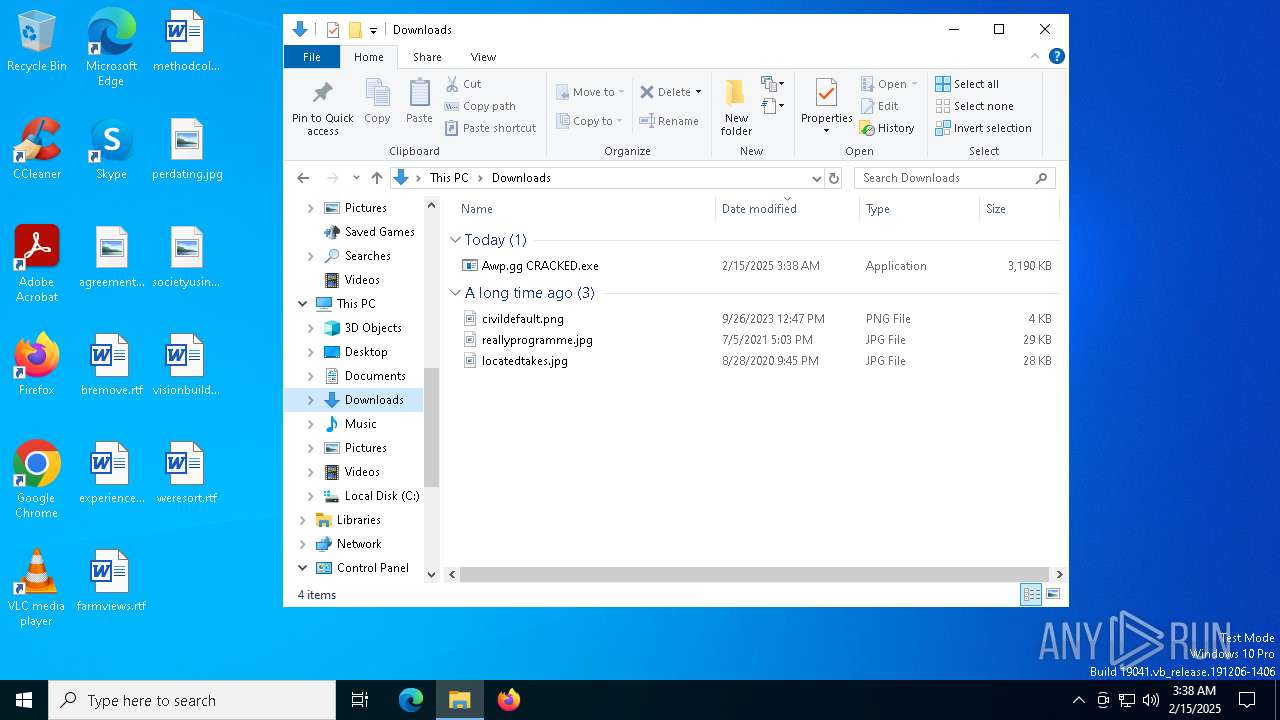
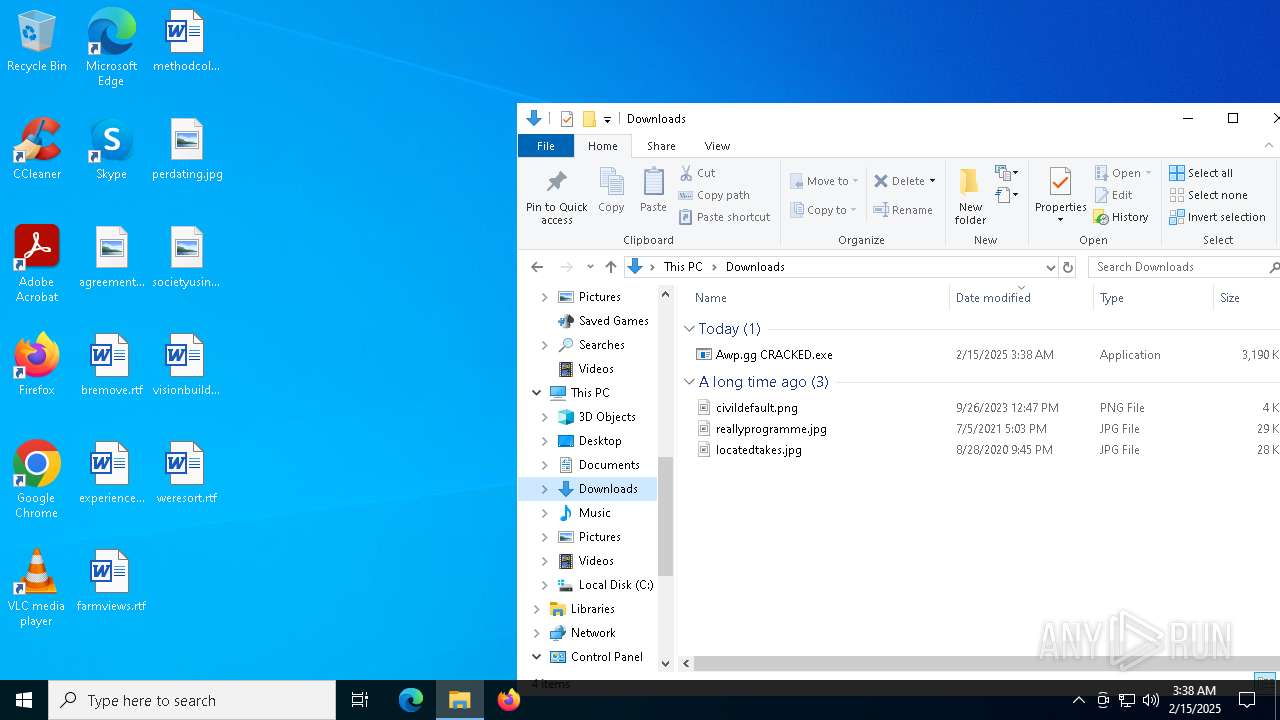
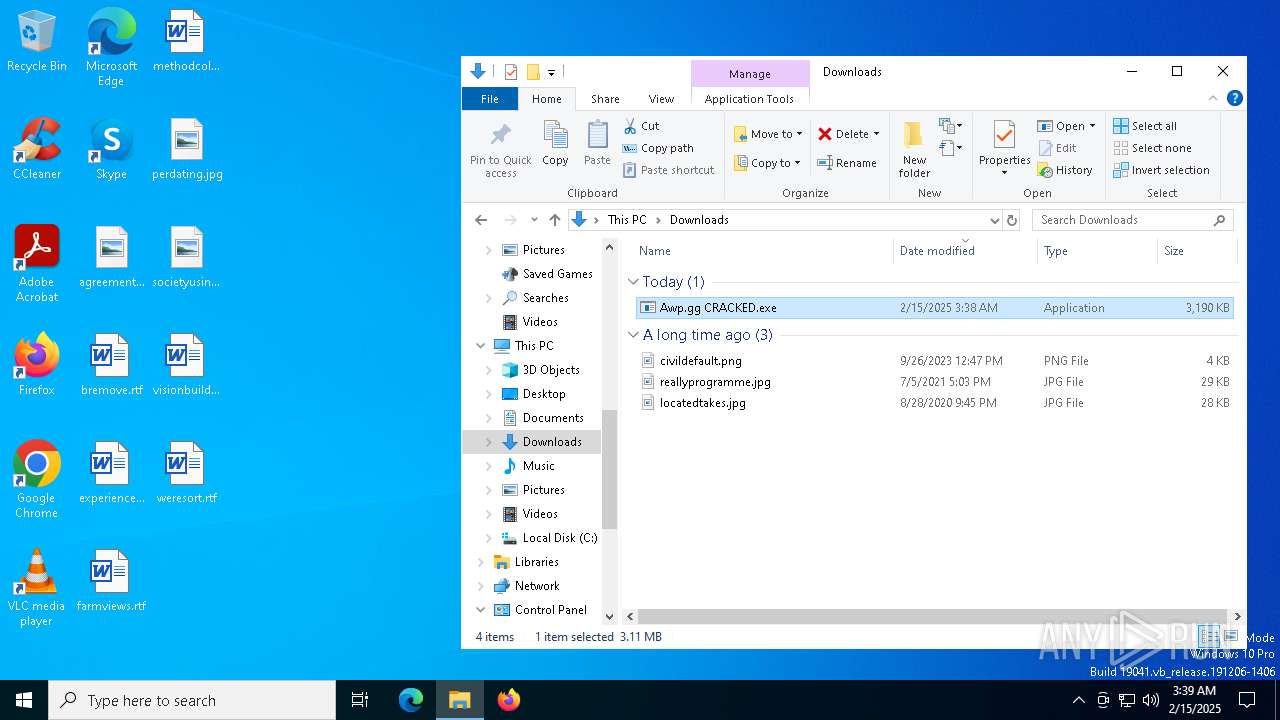
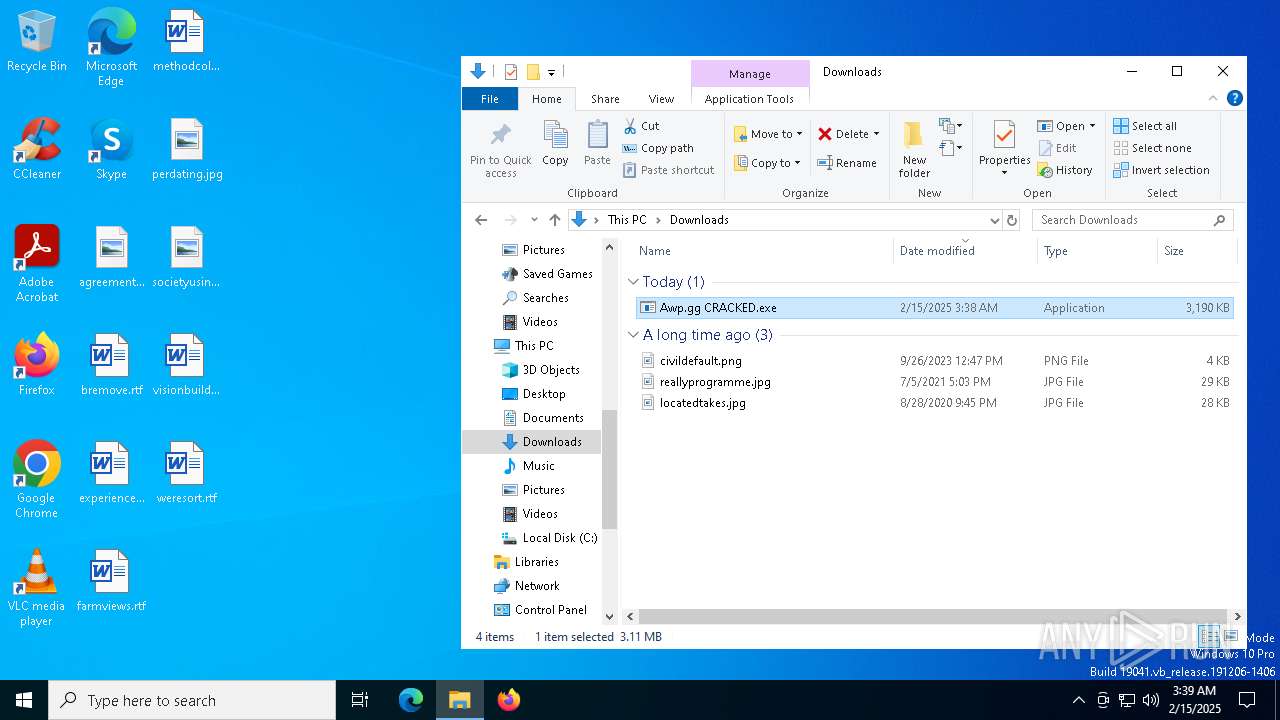
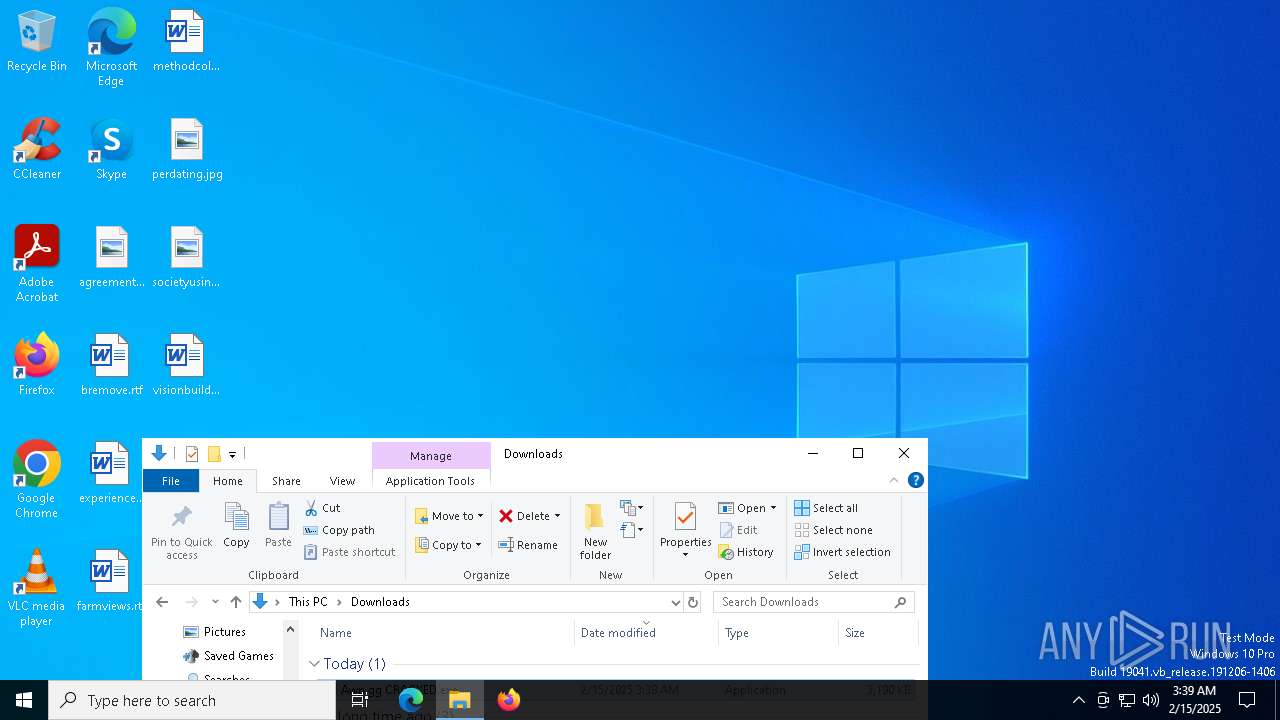
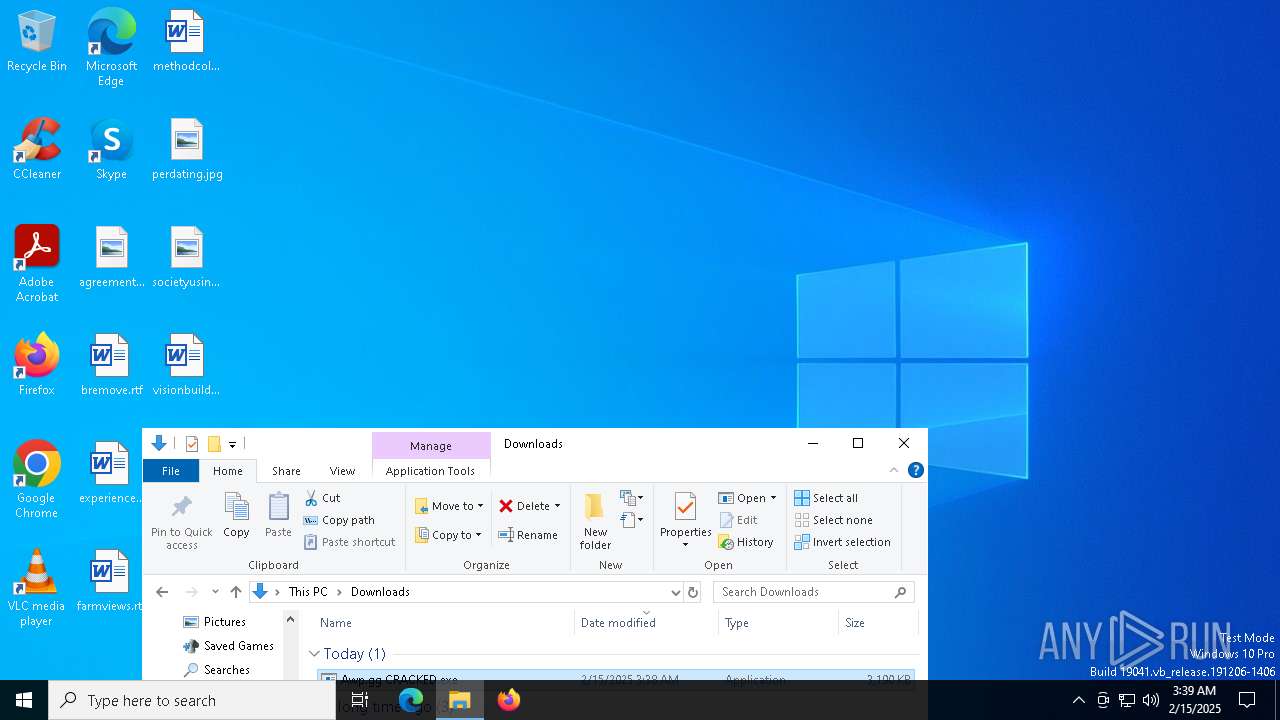
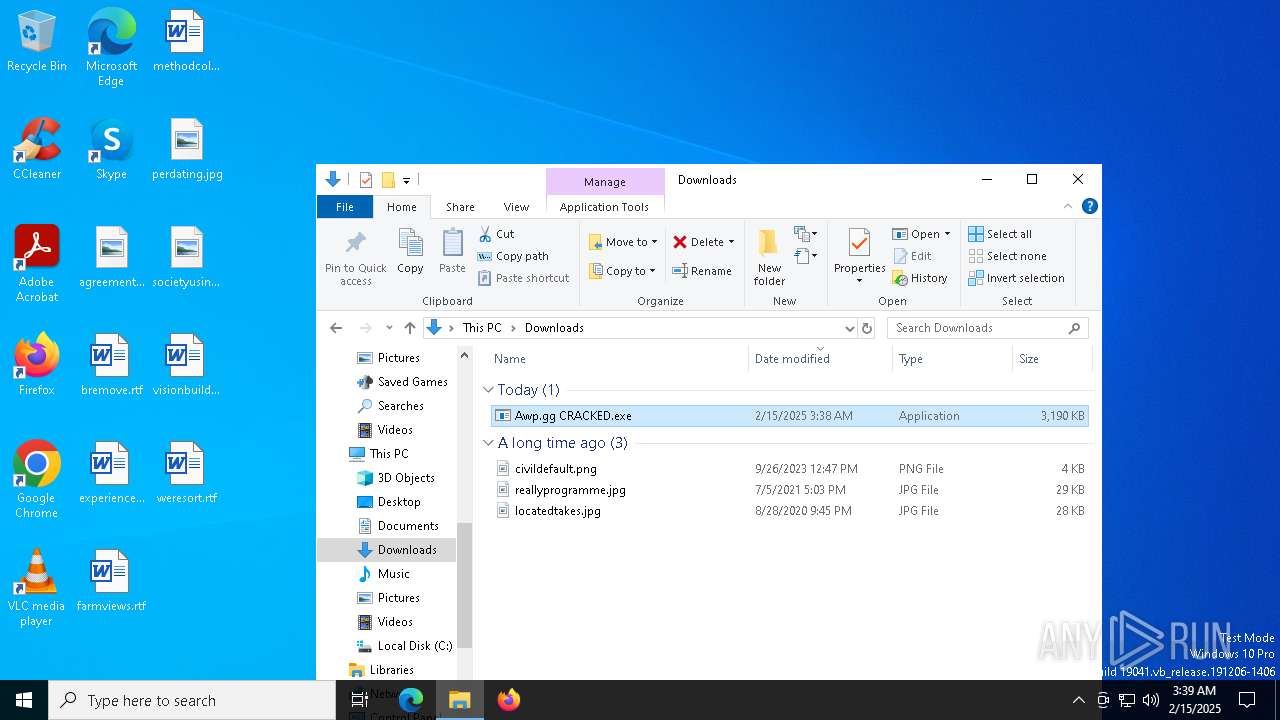
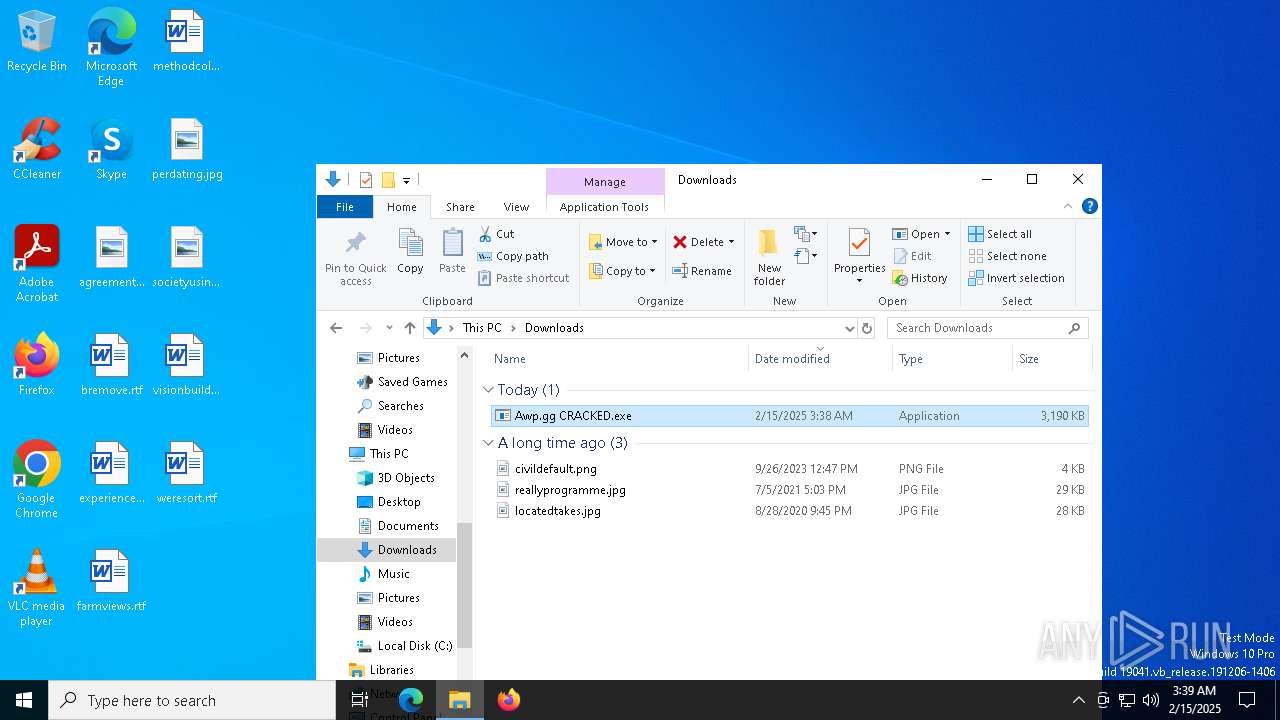
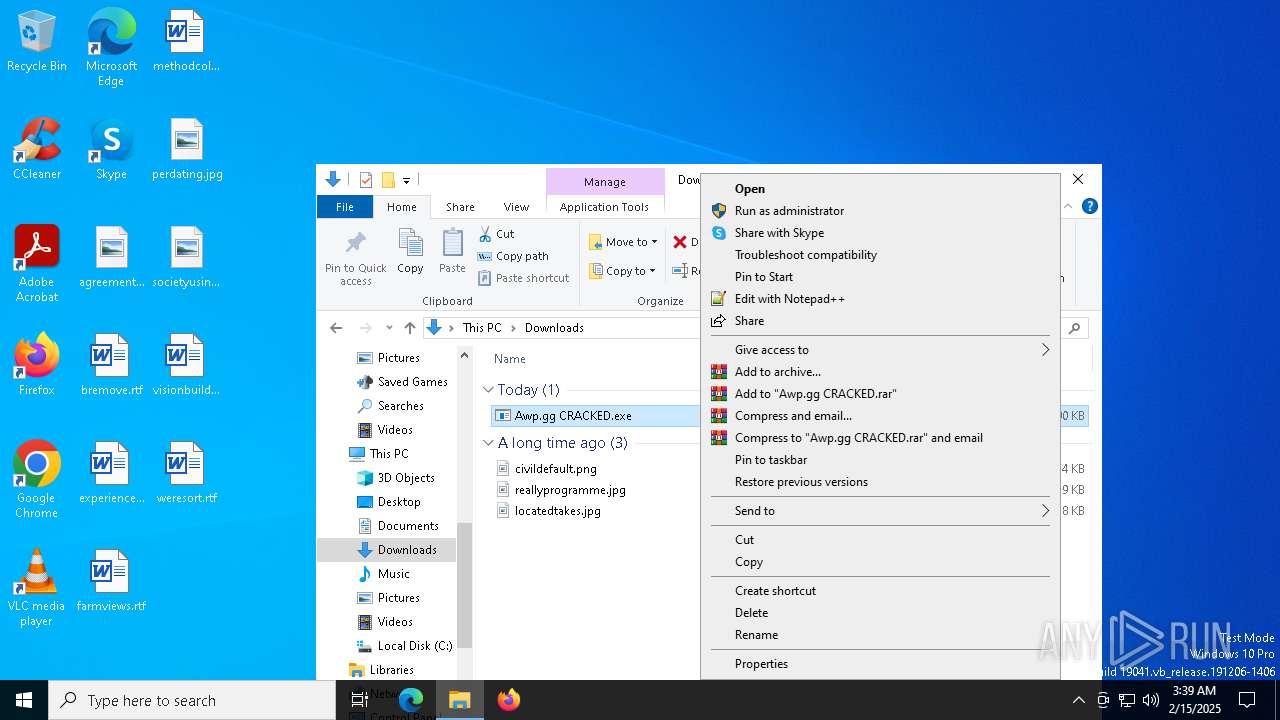
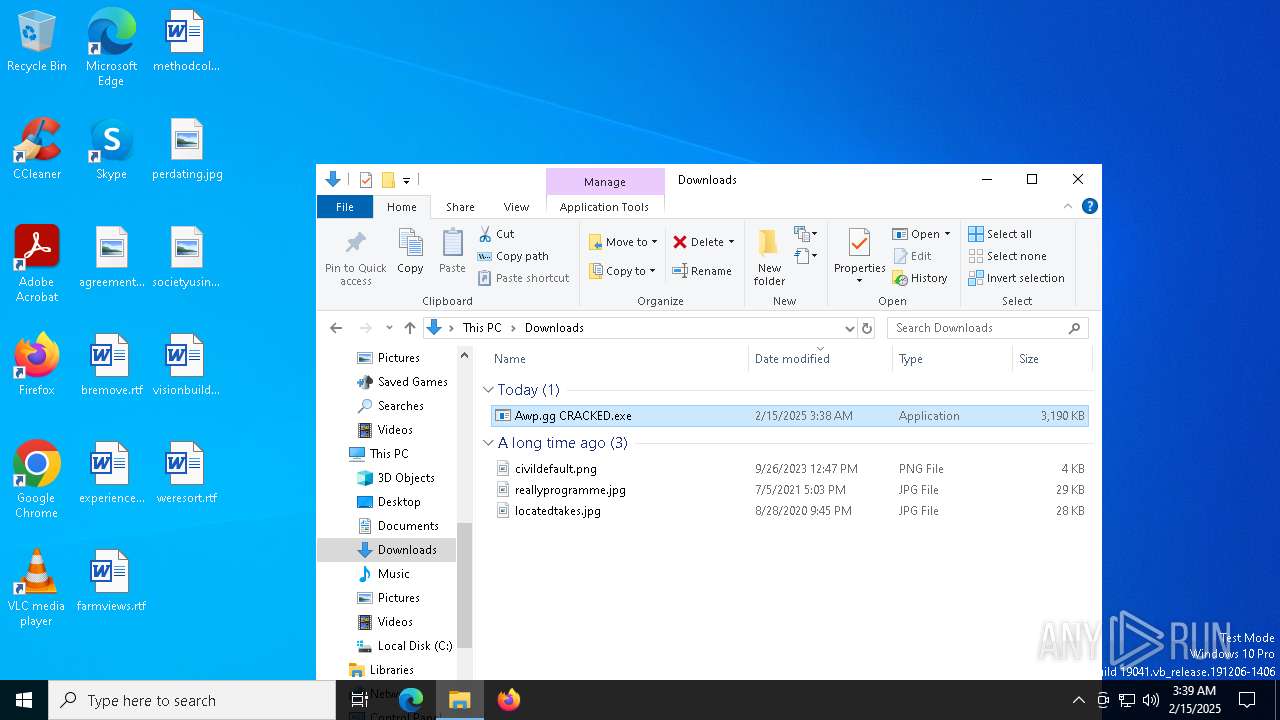
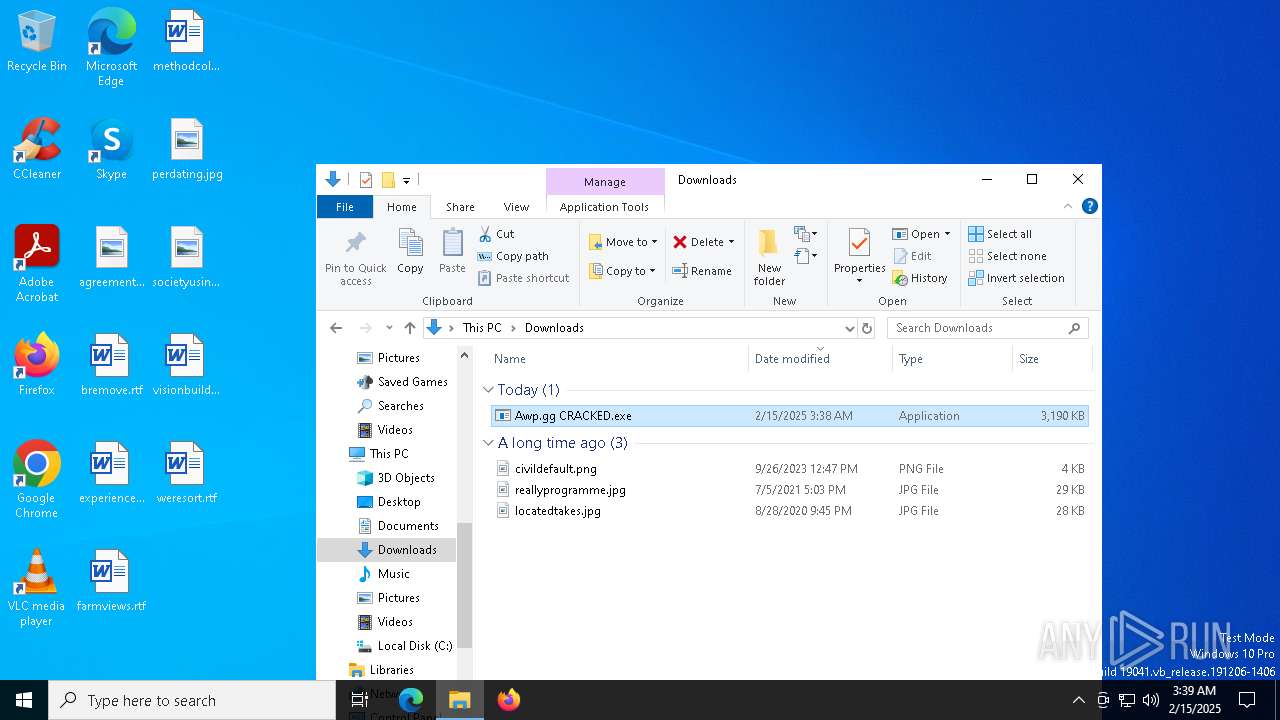
| File name: | Awp.gg CRACKED.exe |
| Full analysis: | https://app.any.run/tasks/7b0e61da-0fe2-4e46-9946-b5ab7ca4f54c |
| Verdict: | Malicious activity |
| Threats: | Quasar is a very popular RAT in the world thanks to its code being available in open-source. This malware can be used to control the victim’s computer remotely. |
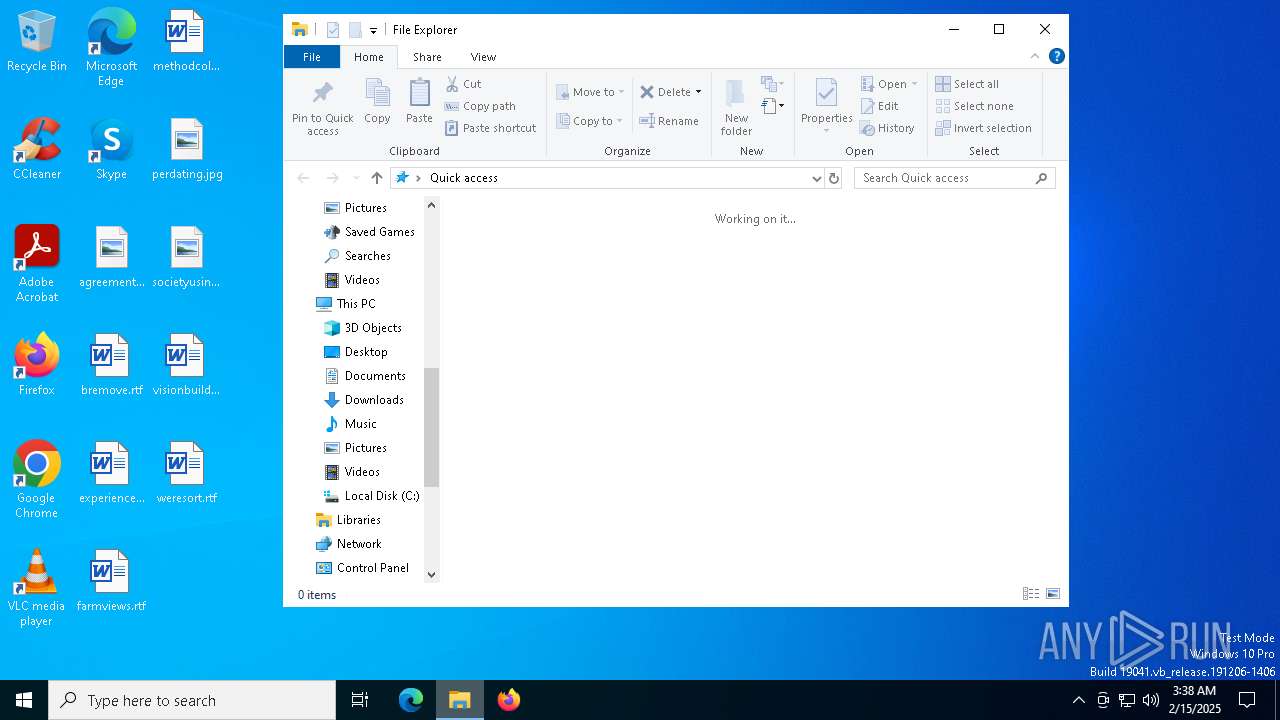
| Analysis date: | February 15, 2025, 03:38:23 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | B622196E254ED84E5B1F59F1AAC2CFB1 |
| SHA1: | F77A050AAFF00D2CC3DA7F11FB35E0BD2C0338BE |
| SHA256: | 1D55A256B3519B624F19C81A9B9F0477D8AD45A967F853E723A921194EE585F0 |
| SSDEEP: | 49152:lfEcsT90z2NkvSCmRf7uY1+DVlYZ+hHjGmt/3DgbA6LbULy2uReUbtIGDrMxhGCt:V2NkKCmRf7uY1+DVlYZ+hHaIDgXCHN |
MALICIOUS
Changes the autorun value in the registry
- Awp.gg CRACKED.exe (PID: 6192)
- Solora.exe (PID: 6240)
QUASAR has been detected (YARA)
- Solora.exe (PID: 6240)
SUSPICIOUS
Executable content was dropped or overwritten
- Awp.gg CRACKED.exe (PID: 6192)
Starts itself from another location
- Awp.gg CRACKED.exe (PID: 6192)
There is functionality for taking screenshot (YARA)
- Solora.exe (PID: 6240)
INFO
Reads Environment values
- Awp.gg CRACKED.exe (PID: 6192)
- Solora.exe (PID: 6240)
- Awp.gg CRACKED.exe (PID: 4716)
- Awp.gg CRACKED.exe (PID: 624)
- Awp.gg CRACKED.exe (PID: 5684)
Checks supported languages
- Awp.gg CRACKED.exe (PID: 6192)
- Solora.exe (PID: 6240)
- Awp.gg CRACKED.exe (PID: 4716)
- Awp.gg CRACKED.exe (PID: 5684)
- Awp.gg CRACKED.exe (PID: 624)
Reads the computer name
- Awp.gg CRACKED.exe (PID: 6192)
- Solora.exe (PID: 6240)
- Awp.gg CRACKED.exe (PID: 4716)
- Awp.gg CRACKED.exe (PID: 5684)
- Awp.gg CRACKED.exe (PID: 624)
Creates files or folders in the user directory
- Awp.gg CRACKED.exe (PID: 6192)
Reads the machine GUID from the registry
- Awp.gg CRACKED.exe (PID: 6192)
- Solora.exe (PID: 6240)
- Awp.gg CRACKED.exe (PID: 4716)
- Awp.gg CRACKED.exe (PID: 624)
- Awp.gg CRACKED.exe (PID: 5684)
Manual execution by a user
- Awp.gg CRACKED.exe (PID: 5684)
- Awp.gg CRACKED.exe (PID: 624)
- Awp.gg CRACKED.exe (PID: 4716)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Quasar
(PID) Process(6240) Solora.exe
Version1.4.1
C2 (2)192.168.1.19:4782
Sub_DirSubDir
Install_NameSolora.exe
Mutexcbd5bb11-a5b0-4dee-8e4b-bb4f3dacc71d
StartupWindows Defender
TagOffice04
LogDirLogs
SignatureREoGhCjgXL4NdT0ZLPCn5MbcrLc8a3m4FK9P/FX4XEnBngwFC2weRuEolFjVtBIh6Wlrx2D2LmzK6MrmBB+rU0ubQQhHJMFHSLO4zOtL+JZGfFn5ShR30ZTppjI5e4+jLujWaUFP6RNhjJAMW/jrZ3Pb5mec0jD3ojnfsERcK5yYhENuw7hm9IUkyxFxmhNlY95/pNnq0Px0ZtobRpZpxa9CaTAp40kVFng7a6LUPaWapQd1uLnSf0i3j6WGE5bvXcdmlkt5o8syklrqJUhCqCya/q9Xiin+TYsRW2BqiN8l...
CertificateMIIE9DCCAtygAwIBAgIQAJUVu7SA1VRQI6x3oZMGzzANBgkqhkiG9w0BAQ0FADAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMCAXDTI0MTIxMjIxMTcyNFoYDzk5OTkxMjMxMjM1OTU5WjAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEAmaTdK0MZJHT9PAvTzggomYuPDBLy1+m4LmiKmE3ToHkRTR+RJd4Q82F47+RhCnEguM0tgW/j...
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (56.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21.3) |
| .scr | | | Windows screen saver (10.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:03:12 16:16:39+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 3261952 |
| InitializedDataSize: | 3584 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x31e41e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.4.1.0 |
| ProductVersionNumber: | 1.4.1.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | Quasar Client |
| FileVersion: | 1.4.1 |
| InternalName: | Client.exe |
| LegalCopyright: | Copyright © MaxXor 2023 |
| LegalTrademarks: | - |
| OriginalFileName: | Client.exe |
| ProductName: | Quasar |
| ProductVersion: | 1.4.1 |
| AssemblyVersion: | 1.4.1.0 |
Total processes
133
Monitored processes
6
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 624 | "C:\Users\admin\Downloads\Awp.gg CRACKED.exe" | C:\Users\admin\Downloads\Awp.gg CRACKED.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Quasar Client Exit code: 2 Version: 1.4.1 Modules
| |||||||||||||||
| 4716 | "C:\Users\admin\Downloads\Awp.gg CRACKED.exe" | C:\Users\admin\Downloads\Awp.gg CRACKED.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Quasar Client Exit code: 2 Version: 1.4.1 Modules
| |||||||||||||||
| 5684 | "C:\Users\admin\Downloads\Awp.gg CRACKED.exe" | C:\Users\admin\Downloads\Awp.gg CRACKED.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Quasar Client Exit code: 2 Version: 1.4.1 Modules
| |||||||||||||||
| 6192 | "C:\Users\admin\Downloads\Awp.gg CRACKED.exe" | C:\Users\admin\Downloads\Awp.gg CRACKED.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Quasar Client Exit code: 3 Version: 1.4.1 Modules
| |||||||||||||||
| 6240 | "C:\Users\admin\AppData\Roaming\SubDir\Solora.exe" | C:\Users\admin\AppData\Roaming\SubDir\Solora.exe | Awp.gg CRACKED.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Quasar Client Version: 1.4.1 Modules
Quasar(PID) Process(6240) Solora.exe Version1.4.1 C2 (2)192.168.1.19:4782 Sub_DirSubDir Install_NameSolora.exe Mutexcbd5bb11-a5b0-4dee-8e4b-bb4f3dacc71d StartupWindows Defender TagOffice04 LogDirLogs SignatureREoGhCjgXL4NdT0ZLPCn5MbcrLc8a3m4FK9P/FX4XEnBngwFC2weRuEolFjVtBIh6Wlrx2D2LmzK6MrmBB+rU0ubQQhHJMFHSLO4zOtL+JZGfFn5ShR30ZTppjI5e4+jLujWaUFP6RNhjJAMW/jrZ3Pb5mec0jD3ojnfsERcK5yYhENuw7hm9IUkyxFxmhNlY95/pNnq0Px0ZtobRpZpxa9CaTAp40kVFng7a6LUPaWapQd1uLnSf0i3j6WGE5bvXcdmlkt5o8syklrqJUhCqCya/q9Xiin+TYsRW2BqiN8l... CertificateMIIE9DCCAtygAwIBAgIQAJUVu7SA1VRQI6x3oZMGzzANBgkqhkiG9w0BAQ0FADAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMCAXDTI0MTIxMjIxMTcyNFoYDzk5OTkxMjMxMjM1OTU5WjAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEAmaTdK0MZJHT9PAvTzggomYuPDBLy1+m4LmiKmE3ToHkRTR+RJd4Q82F47+RhCnEguM0tgW/j... | |||||||||||||||
| 6824 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
1 117
Read events
1 115
Write events
2
Delete events
0
Modification events
| (PID) Process: | (6192) Awp.gg CRACKED.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Windows Defender |
Value: "C:\Users\admin\AppData\Roaming\SubDir\Solora.exe" | |||
| (PID) Process: | (6240) Solora.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Windows Defender |
Value: "C:\Users\admin\AppData\Roaming\SubDir\Solora.exe" | |||
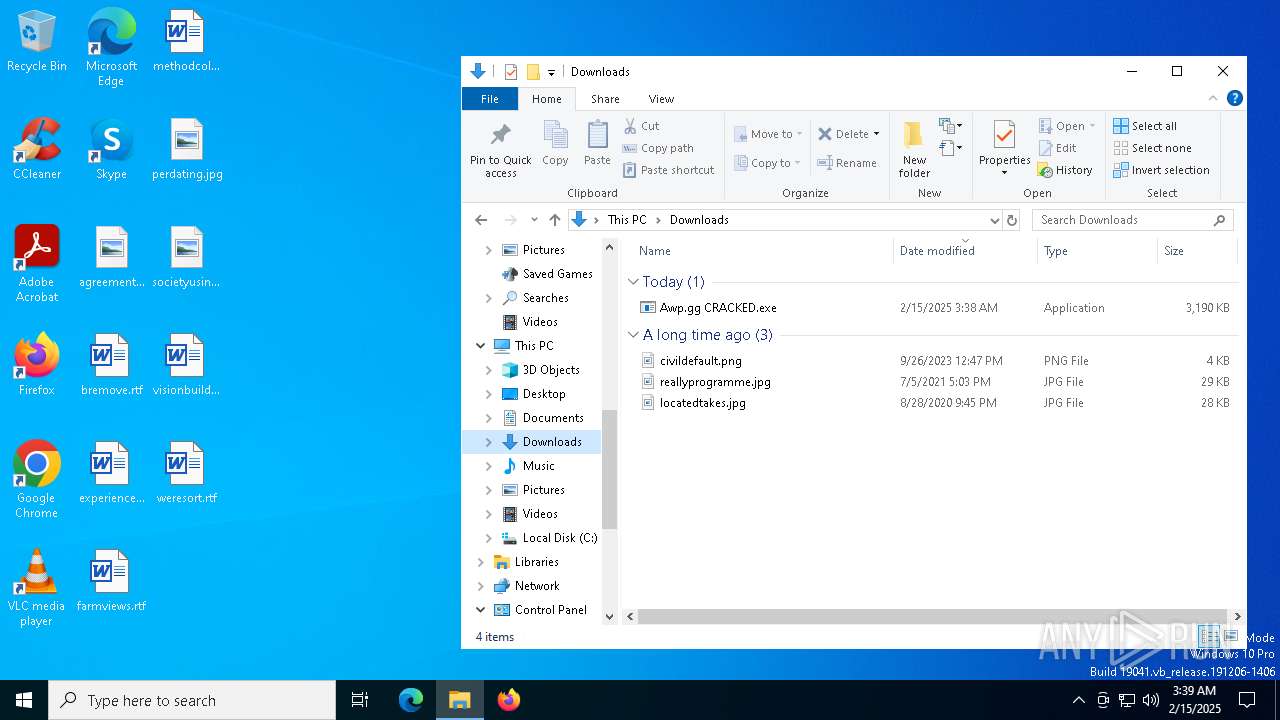
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6192 | Awp.gg CRACKED.exe | C:\Users\admin\AppData\Roaming\SubDir\Solora.exe | executable | |
MD5:B622196E254ED84E5B1F59F1AAC2CFB1 | SHA256:1D55A256B3519B624F19C81A9B9F0477D8AD45A967F853E723A921194EE585F0 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
37
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3040 | svchost.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6256 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6256 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6384 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
3040 | svchost.exe | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5064 | SearchApp.exe | 104.126.37.145:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
1076 | svchost.exe | 184.30.18.9:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 192.168.100.210:49689 | — | — | — | unknown |
1176 | svchost.exe | 40.126.31.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |