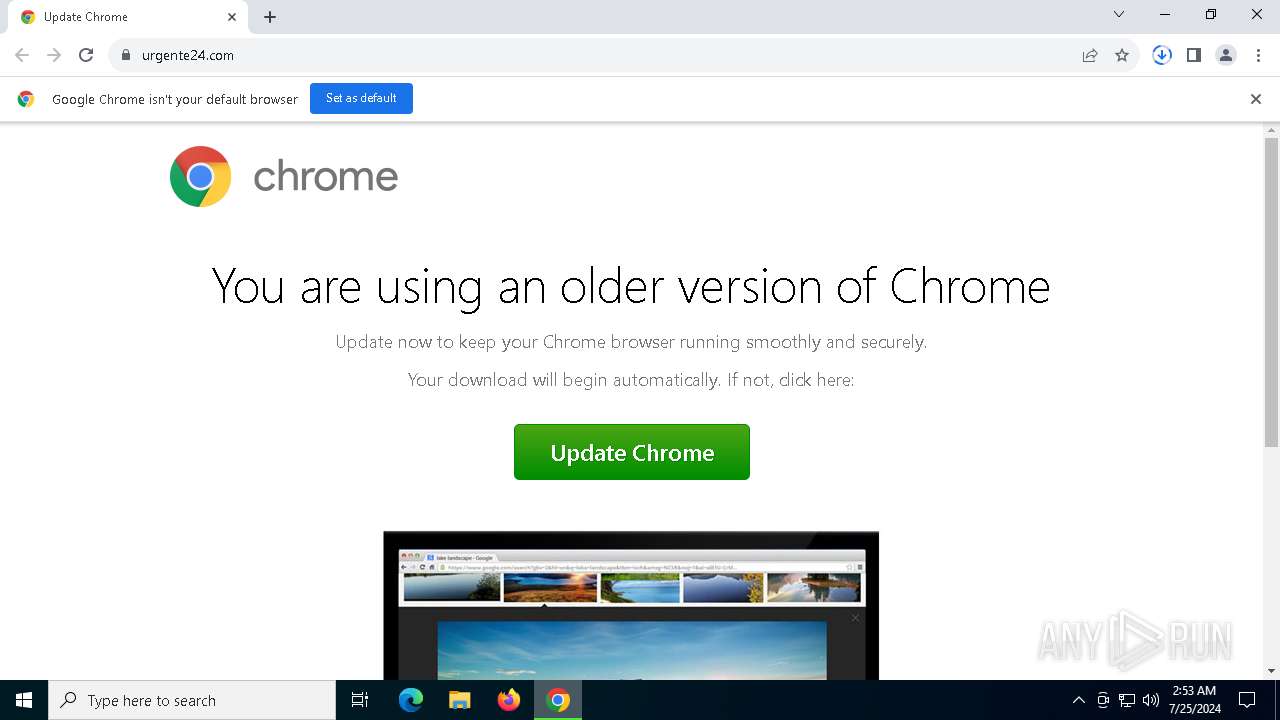
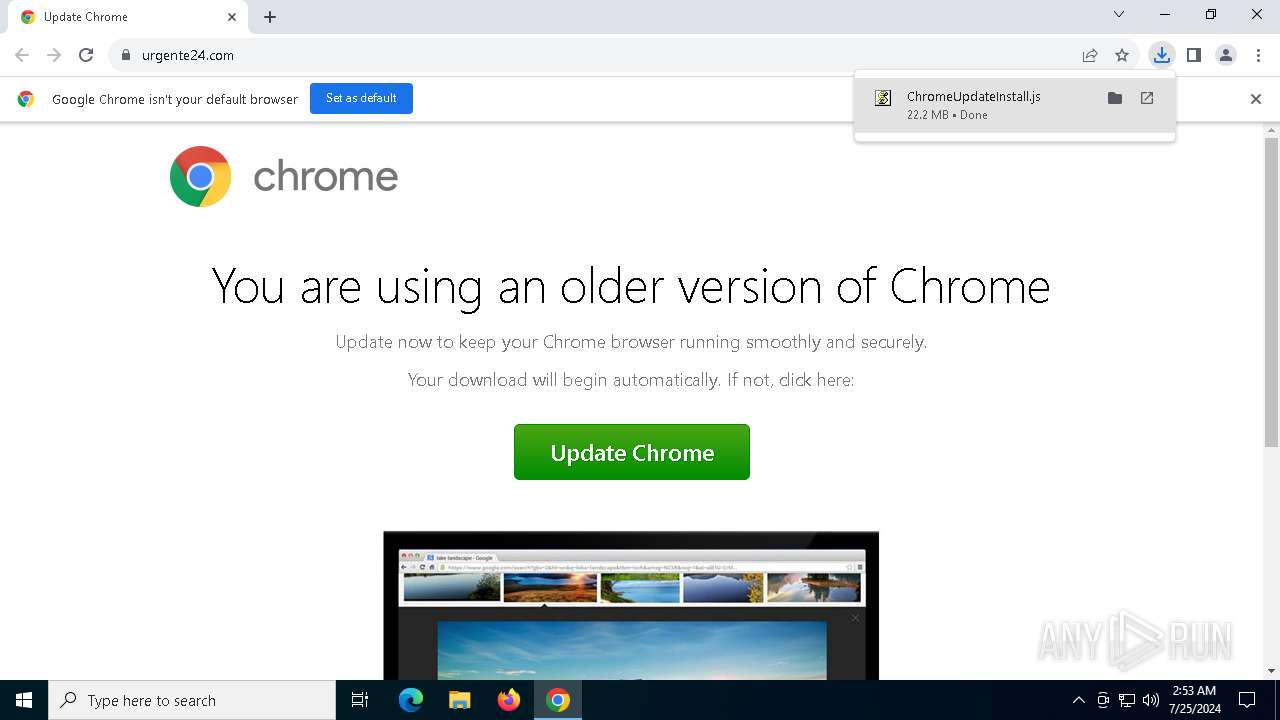
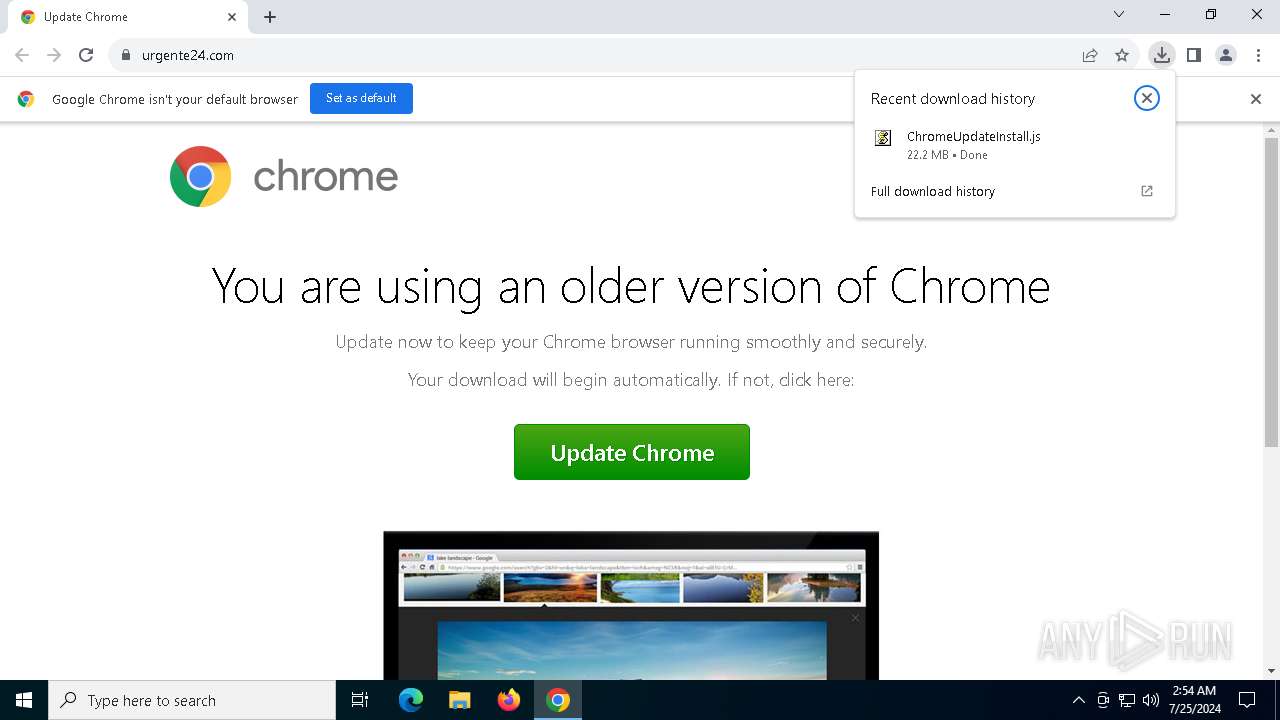
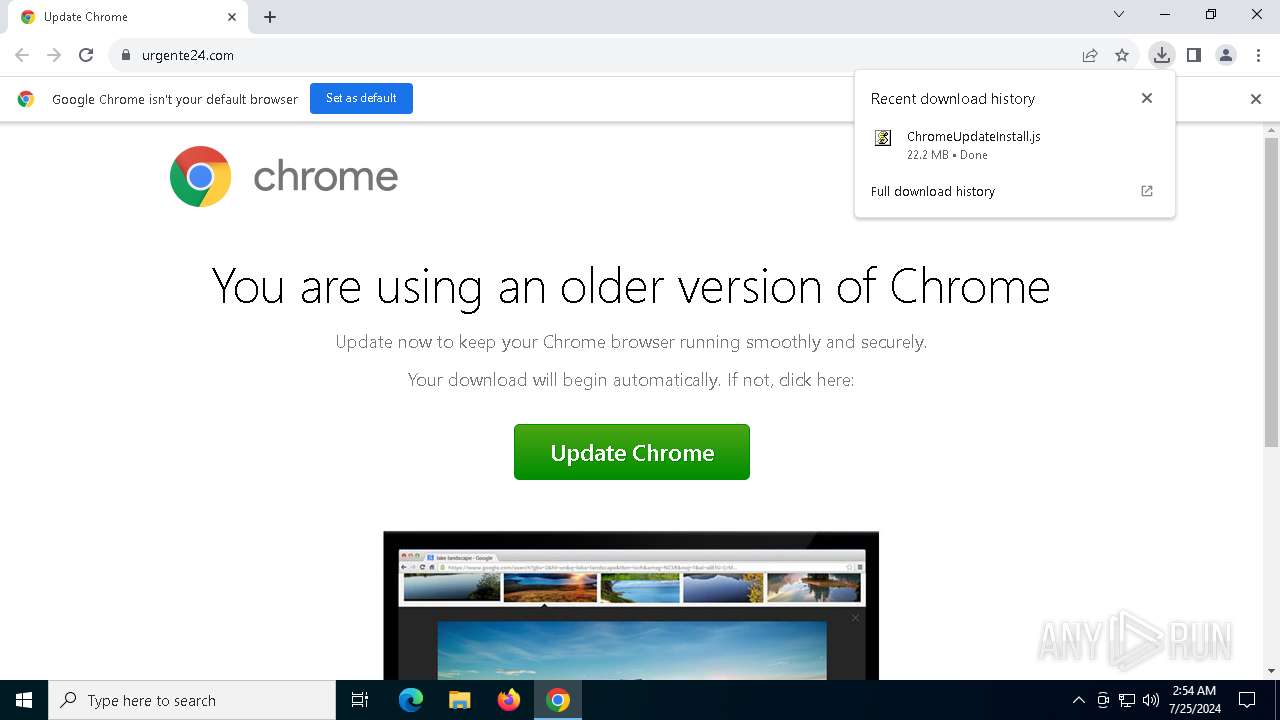
| URL: | https://urgente24.com/ |
| Full analysis: | https://app.any.run/tasks/48a0474e-4a61-46e9-a097-b5b36ced511f |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | July 25, 2024, 02:53:31 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 07428946BEBCAF6D6EDE5912C9A1E236 |
| SHA1: | 4D1AC82F5B894D999DF12AC169B1BB226836CACE |
| SHA256: | 1CA8DA6C096AF9C3EE52F54EC505261D66EB2F93E716ABC7D75CFFA155BEA4AD |
| SSDEEP: | 3:N8futKn:2zn |
MALICIOUS
Gets path to any of the special folders (SCRIPT)
- wscript.exe (PID: 8000)
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 8000)
Accesses environment variables (SCRIPT)
- wscript.exe (PID: 8000)
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 8000)
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 8000)
Scans artifacts that could help determine the target
- wscript.exe (PID: 8000)
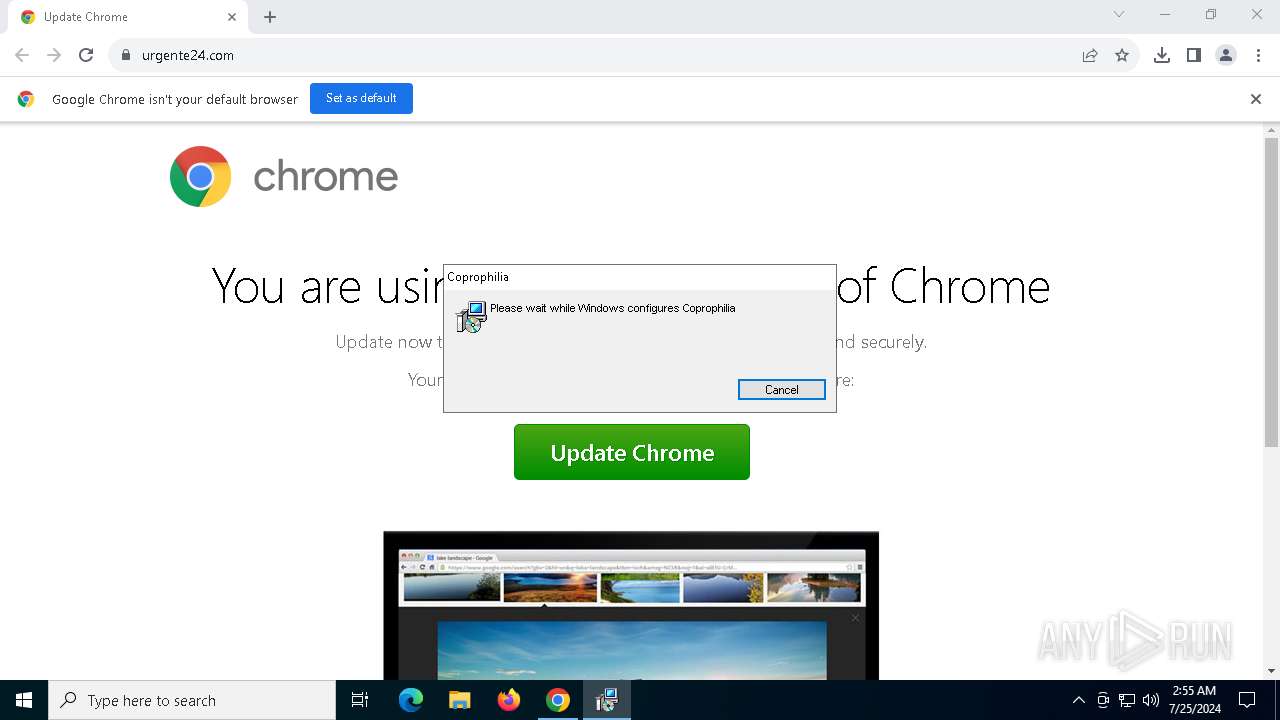
Drops the executable file immediately after the start
- wscript.exe (PID: 8000)
- msiexec.exe (PID: 6376)
- ScreenShot.exe (PID: 256)
Gets script object from HTTP/HTTPS (SCRIPT)
- wscript.exe (PID: 8000)
Stealers network behavior
- explorer.exe (PID: 2776)
LUMMA has been detected (SURICATA)
- explorer.exe (PID: 2776)
LUMMA has been detected (YARA)
- explorer.exe (PID: 2776)
Actions looks like stealing of personal data
- explorer.exe (PID: 2776)
SUSPICIOUS
Checks whether a specific file exists (SCRIPT)
- wscript.exe (PID: 8000)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 8000)
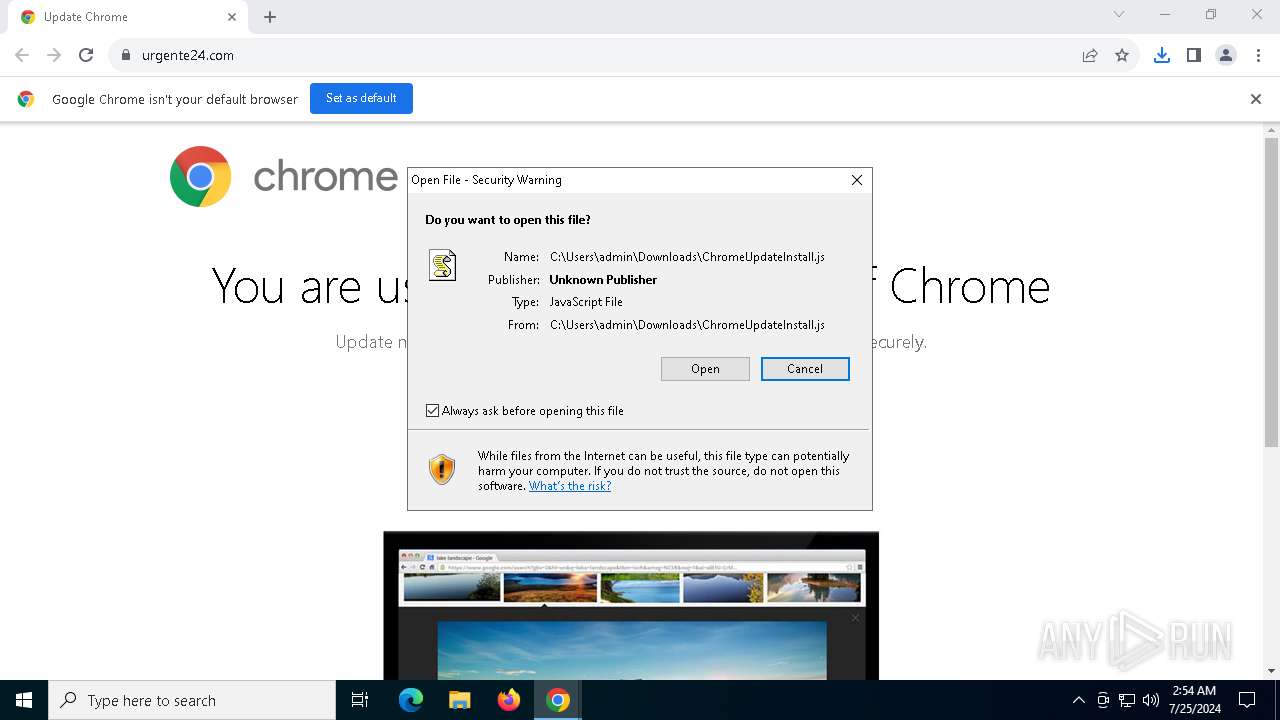
The process executes JS scripts
- chrome.exe (PID: 6928)
Adds, changes, or deletes HTTP request header (SCRIPT)
- wscript.exe (PID: 8000)
Creates a Stream, which may work with files, input/output devices, pipes, or TCP/IP sockets (SCRIPT)
- wscript.exe (PID: 8000)
Saves data to a binary file (SCRIPT)
- wscript.exe (PID: 8000)
Writes binary data to a Stream object (SCRIPT)
- wscript.exe (PID: 8000)
Executes as Windows Service
- VSSVC.exe (PID: 7872)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 6376)
Executable content was dropped or overwritten
- wscript.exe (PID: 8000)
- ScreenShot.exe (PID: 256)
Starts itself from another location
- ScreenShot.exe (PID: 256)
Runs shell command (SCRIPT)
- wscript.exe (PID: 8000)
Starts CMD.EXE for commands execution
- ScreenShot.exe (PID: 4584)
INFO
Reads Microsoft Office registry keys
- chrome.exe (PID: 6928)
The process uses the downloaded file
- chrome.exe (PID: 6928)
- chrome.exe (PID: 7832)
Application launched itself
- chrome.exe (PID: 6928)
Checks proxy server information
- slui.exe (PID: 7496)
- wscript.exe (PID: 8000)
Reads the software policy settings
- slui.exe (PID: 7496)
- explorer.exe (PID: 2776)
Executable content was dropped or overwritten
- msiexec.exe (PID: 6376)
Checks supported languages
- msiexec.exe (PID: 6376)
- ScreenShot.exe (PID: 256)
- ScreenShot.exe (PID: 4584)
Reads the computer name
- ScreenShot.exe (PID: 256)
- ScreenShot.exe (PID: 4584)
- msiexec.exe (PID: 6376)
Creates files or folders in the user directory
- msiexec.exe (PID: 6376)
- ScreenShot.exe (PID: 256)
Creates a software uninstall entry
- msiexec.exe (PID: 6376)
Create files in a temporary directory
- ScreenShot.exe (PID: 4584)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Lumma
(PID) Process(2776) explorer.exe
C2 (9)callosallsaospz.shop
indexterityszcoxp.shop
lariatedzugspd.shop
upknittsoappz.shop
shepherdlyopzc.shop
outpointsozp.shop
spliceszongsop.shop
liernessfornicsa.shop
unseaffarignsk.shop
Total processes
170
Monitored processes
28
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 256 | "C:\Users\admin\AppData\Local\Trindle\ScreenShot.exe" | C:\Users\admin\AppData\Local\Trindle\ScreenShot.exe | msiexec.exe | ||||||||||||
User: admin Company: IObit Integrity Level: MEDIUM Description: ScreenShot Exit code: 0 Version: 1.0.0.57 Modules
| |||||||||||||||
| 1112 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=122.0.6261.70 --initial-client-data=0x21c,0x220,0x224,0x1f8,0x228,0x7fff0709dc40,0x7fff0709dc4c,0x7fff0709dc58 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2192 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=4024 --field-trial-handle=1924,i,15527316088874852637,8806758701208748698,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2776 | C:\WINDOWS\SysWOW64\explorer.exe | C:\Windows\SysWOW64\explorer.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
Lumma(PID) Process(2776) explorer.exe C2 (9)callosallsaospz.shop indexterityszcoxp.shop lariatedzugspd.shop upknittsoappz.shop shepherdlyopzc.shop outpointsozp.shop spliceszongsop.shop liernessfornicsa.shop unseaffarignsk.shop | |||||||||||||||
| 3856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4020 --field-trial-handle=1924,i,15527316088874852637,8806758701208748698,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 3968 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgABAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=1920 --field-trial-handle=1924,i,15527316088874852637,8806758701208748698,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 4584 | C:\Users\admin\AppData\Roaming\TlsLoadv5\ScreenShot.exe | C:\Users\admin\AppData\Roaming\TlsLoadv5\ScreenShot.exe | — | ScreenShot.exe | |||||||||||
User: admin Company: IObit Integrity Level: MEDIUM Description: ScreenShot Exit code: 1 Version: 1.0.0.57 Modules
| |||||||||||||||
| 5928 | C:\WINDOWS\SysWOW64\cmd.exe | C:\Windows\SysWOW64\cmd.exe | — | ScreenShot.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6376 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6440 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
21 867
Read events
21 507
Write events
335
Delete events
25
Modification events
| (PID) Process: | (6928) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6928) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6928) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (6928) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (6928) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6928) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (6928) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6928) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (6928) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6928) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
17
Suspicious files
121
Text files
28
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6928 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6928 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RFe18e3.TMP | — | |
MD5:— | SHA256:— | |||
| 6928 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6928 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6928 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6928 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6928 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RFe1902.TMP | — | |
MD5:— | SHA256:— | |||
| 6928 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6928 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\1f154760-9dfd-4238-9822-c0087e1bc4ac.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 6928 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFe18d3.TMP | text | |
MD5:139F545948FC1F10256A27E3C2CEF062 | SHA256:9399CC6F9C335015E086DB37208B1816A7831221A005B04AC83C4F86CC04230D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
27
TCP/UDP connections
106
DNS requests
85
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4216 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adskukgbhfrd2i7eionvmtejc3ga_20240715.653820789.14/obedbbhbpmojnkanicioggnmelmoomoc_20240715.653820789.14_all_ENUS500000_ac4yidnnw6fbnfm765kmepjhj57a.crx3 | unknown | — | — | whitelisted |
5368 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5272 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1148 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5776 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
4216 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adskukgbhfrd2i7eionvmtejc3ga_20240715.653820789.14/obedbbhbpmojnkanicioggnmelmoomoc_20240715.653820789.14_all_ENUS500000_ac4yidnnw6fbnfm765kmepjhj57a.crx3 | unknown | — | — | whitelisted |
8000 | wscript.exe | GET | 200 | 142.250.185.163:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
8000 | wscript.exe | GET | 200 | 142.250.185.163:80 | http://c.pki.goog/r/r4.crl | unknown | — | — | whitelisted |
4216 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adskukgbhfrd2i7eionvmtejc3ga_20240715.653820789.14/obedbbhbpmojnkanicioggnmelmoomoc_20240715.653820789.14_all_ENUS500000_ac4yidnnw6fbnfm765kmepjhj57a.crx3 | unknown | — | — | whitelisted |
4216 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adskukgbhfrd2i7eionvmtejc3ga_20240715.653820789.14/obedbbhbpmojnkanicioggnmelmoomoc_20240715.653820789.14_all_ENUS500000_ac4yidnnw6fbnfm765kmepjhj57a.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6012 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
3952 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3360 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4212 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
— | — | 184.86.251.19:443 | — | Akamai International B.V. | DE | unknown |
4204 | svchost.exe | 4.209.33.156:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
7016 | chrome.exe | 74.125.133.84:443 | accounts.google.com | GOOGLE | US | unknown |
6928 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7016 | chrome.exe | 104.18.0.59:443 | urgente24.com | CLOUDFLARENET | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
urgente24.com |
| whitelisted |
accounts.google.com |
| whitelisted |
www.bing.com |
| whitelisted |
usuarios.urgente24.com |
| whitelisted |
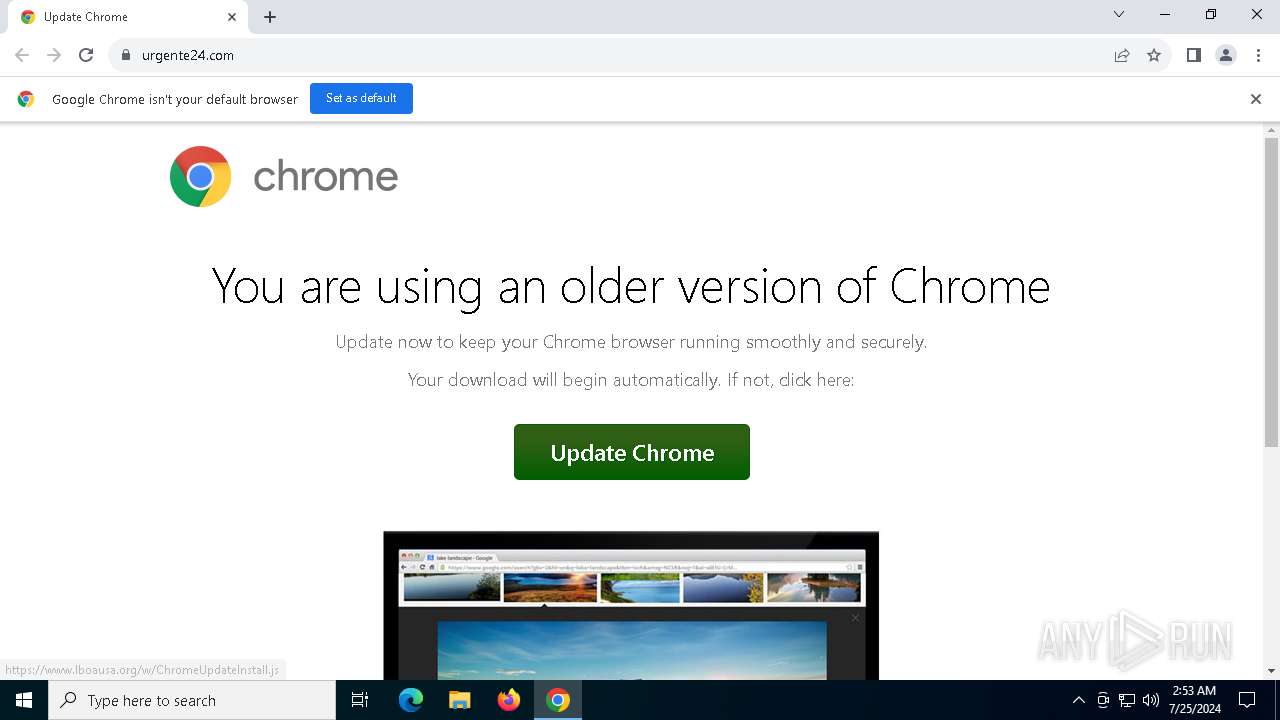
www.lboausa.org |
| unknown |
www.googletagmanager.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2284 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2776 | explorer.exe | A Network Trojan was detected | STEALER [ANY.RUN] Lumma Stealer TLS Connection |