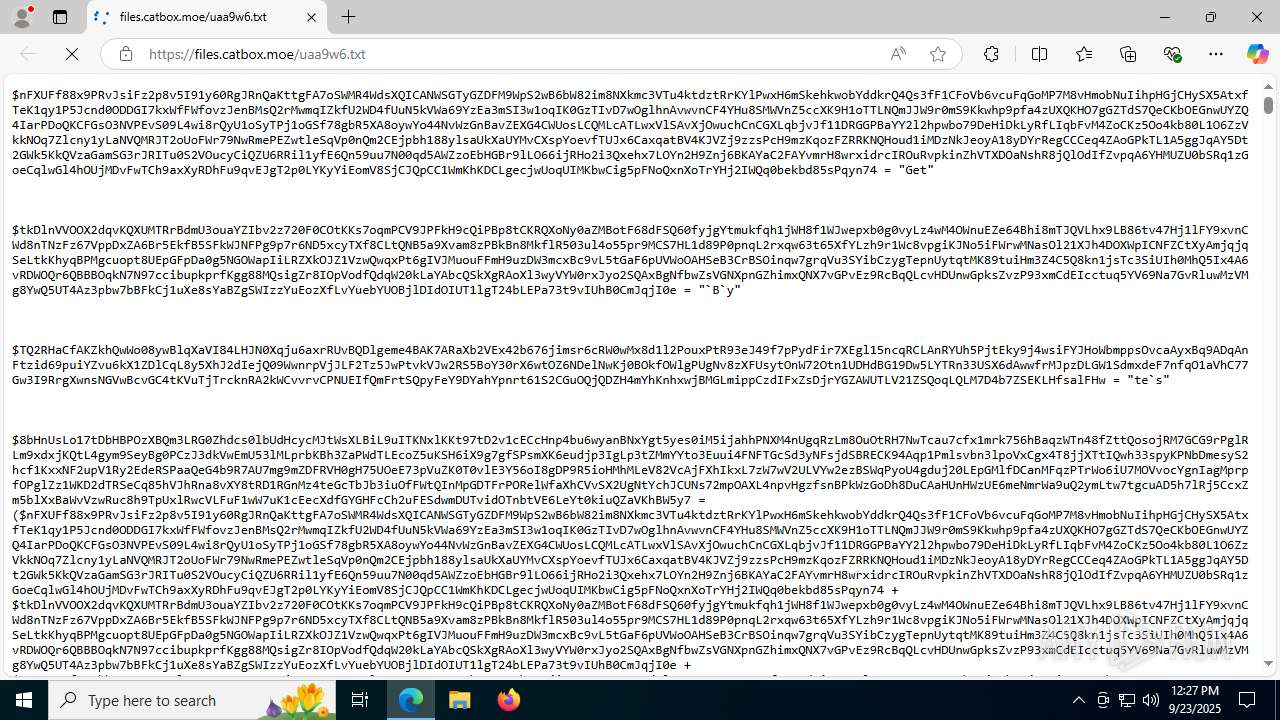
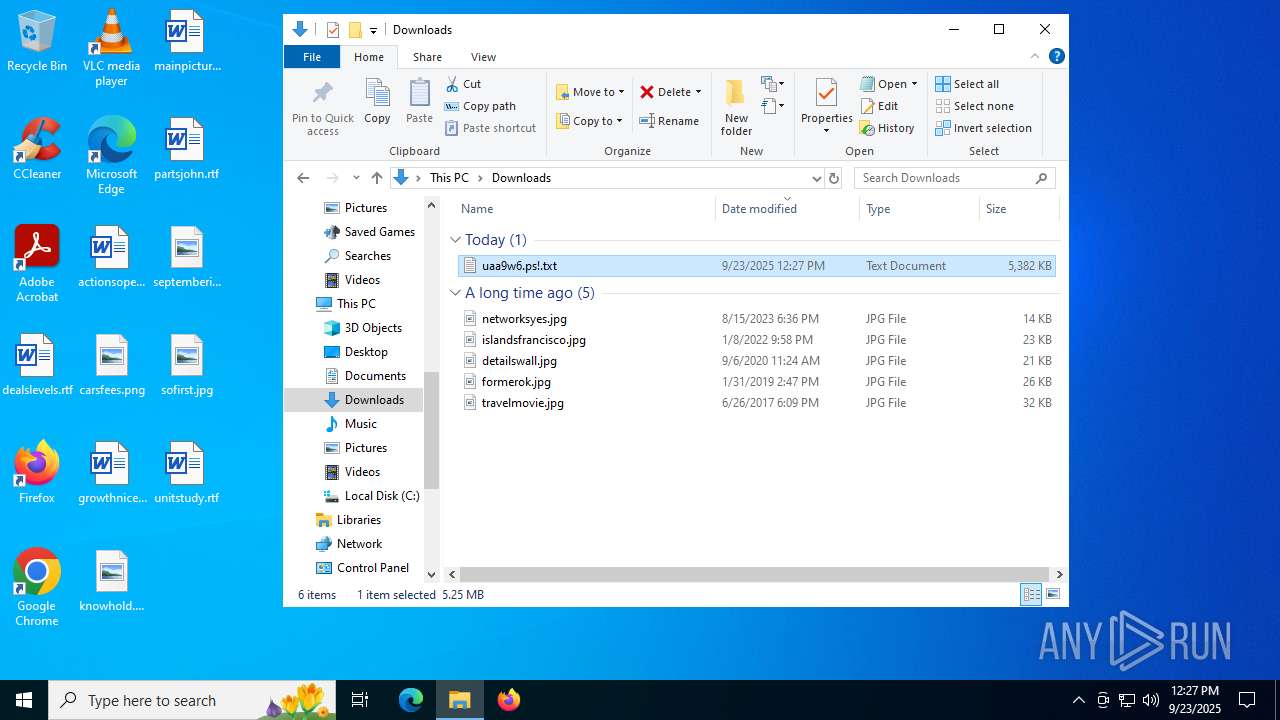
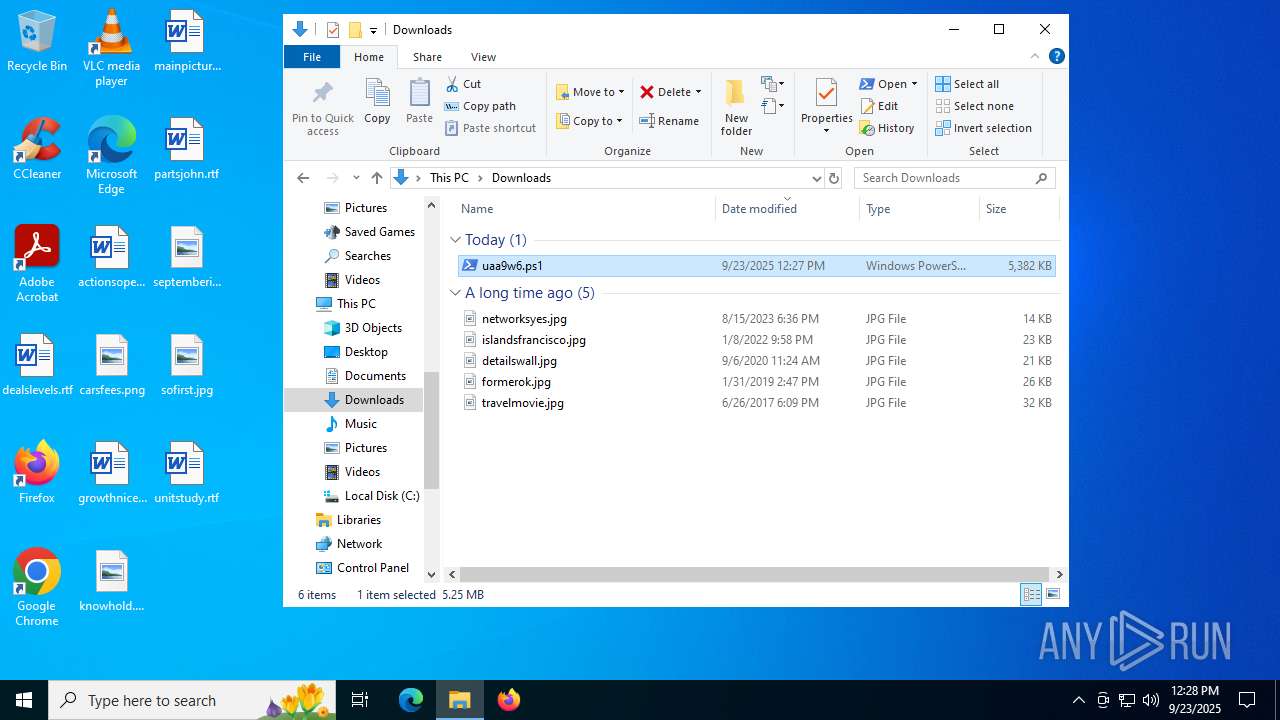
| URL: | https://files.catbox.moe/uaa9w6.txt |
| Full analysis: | https://app.any.run/tasks/7f65fb39-7aa9-4e5b-b078-1d0479407f4e |
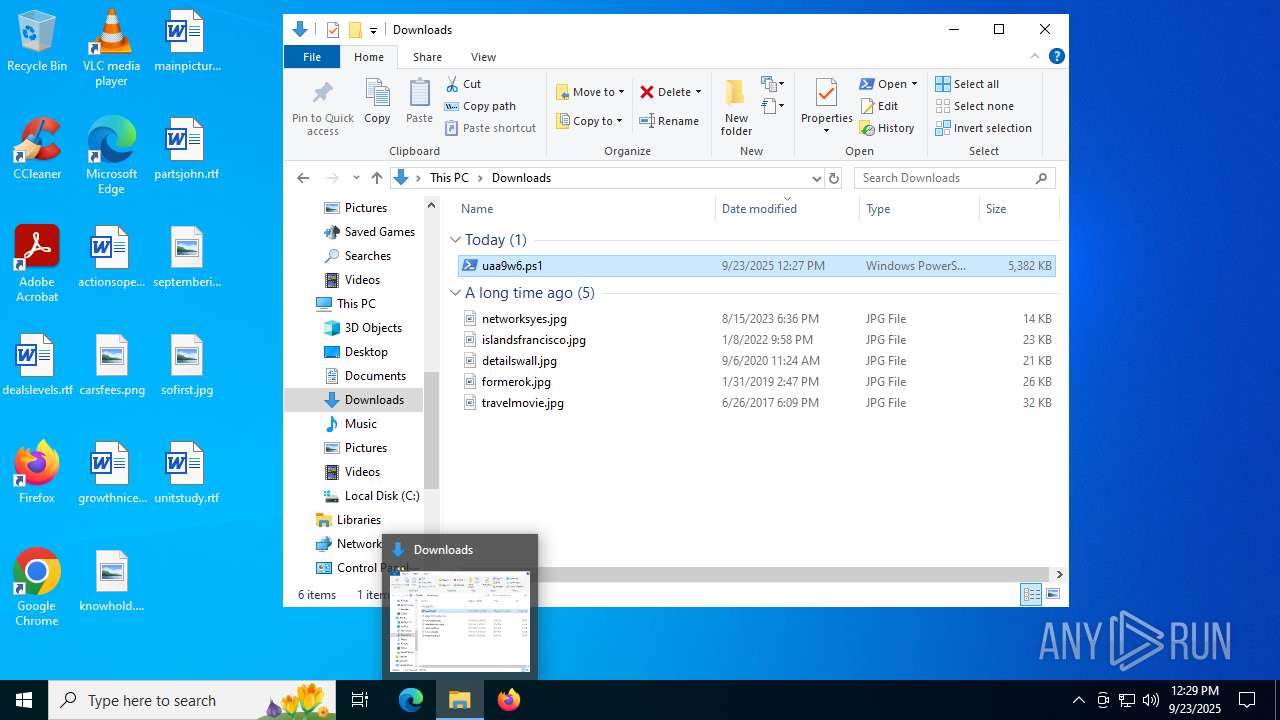
| Verdict: | Malicious activity |
| Threats: | Quasar is a very popular RAT in the world thanks to its code being available in open-source. This malware can be used to control the victim’s computer remotely. |
| Analysis date: | September 23, 2025, 12:26:59 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | F0A1AC8FB1CBE03B3E92A965919B24EC |
| SHA1: | 176F3870410BE349F4FB24044DD13923E1C7A8F3 |
| SHA256: | 1C71E50FA6DFF6B722D25AC394888C42AF25CE11CD068CCEE3306C75668049D9 |
| SSDEEP: | 3:N8MW3aTRdR:2MWiR |
MALICIOUS
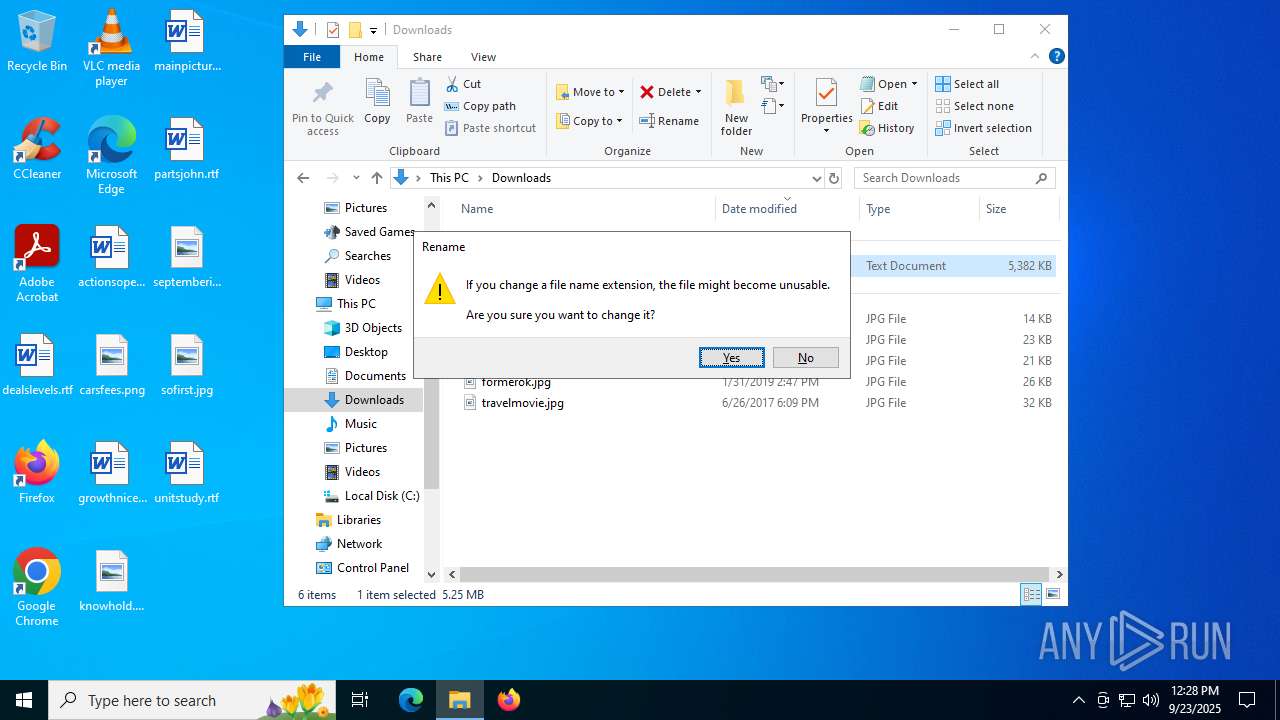
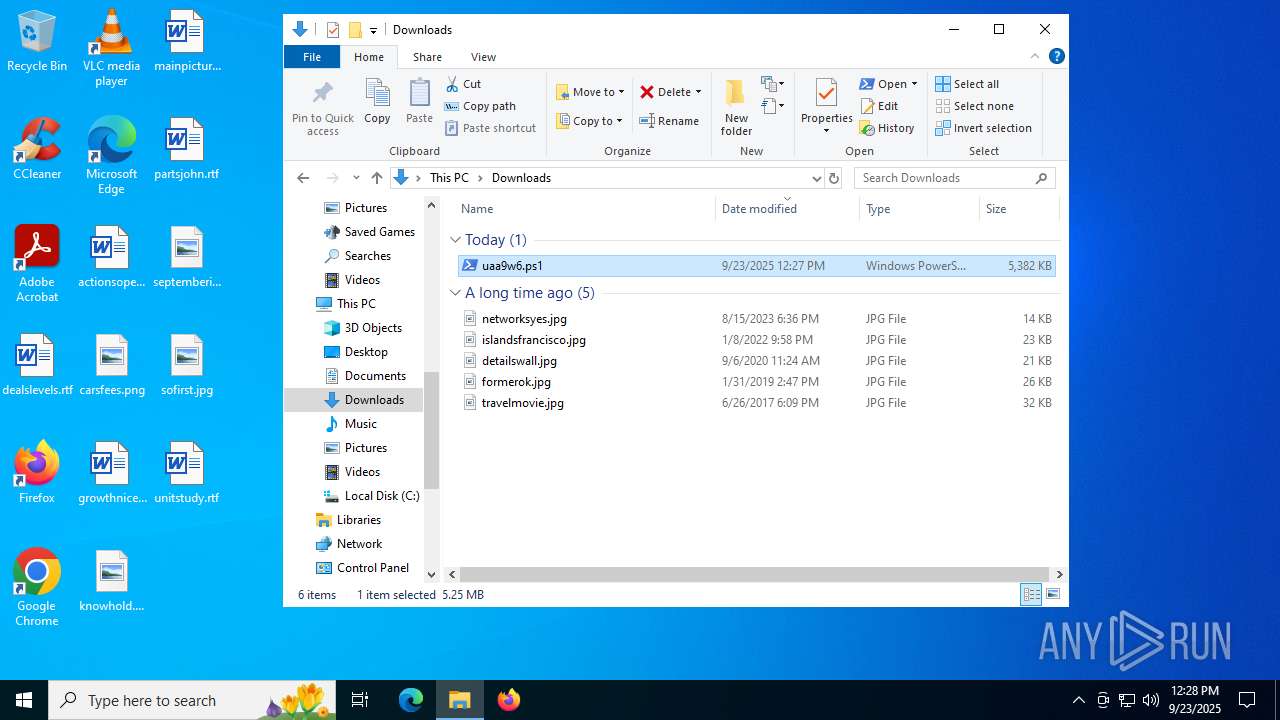
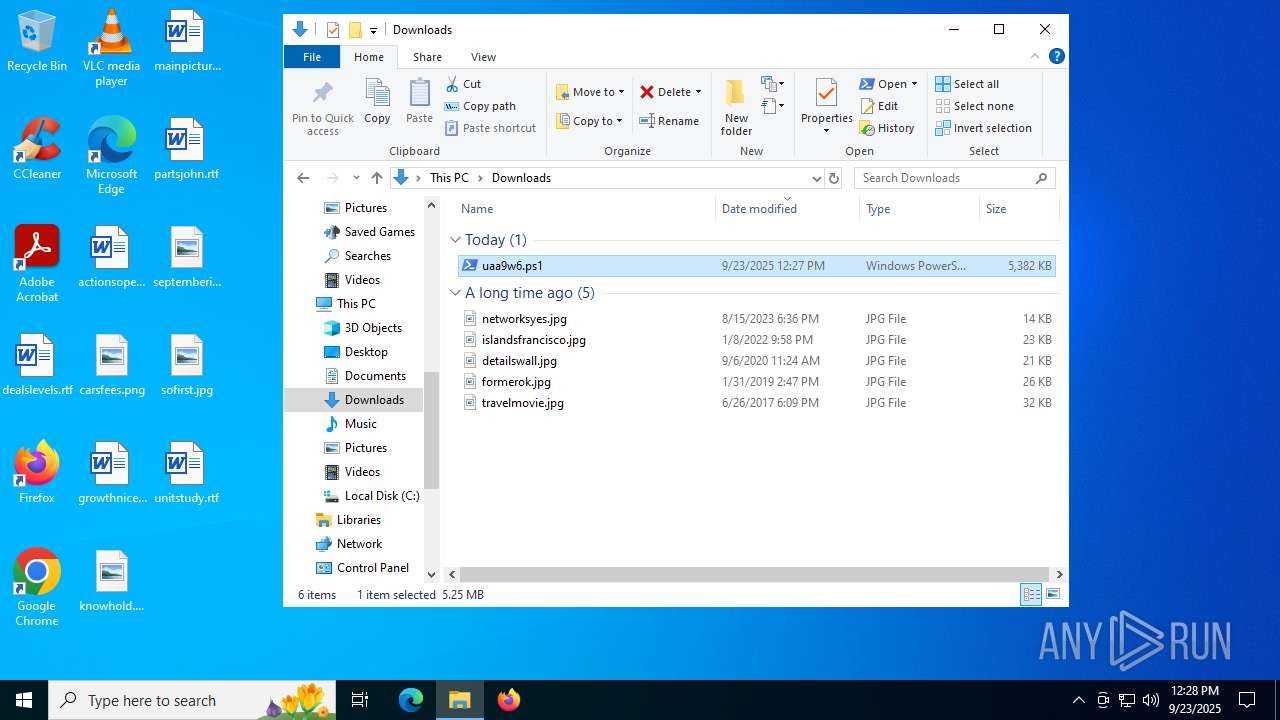
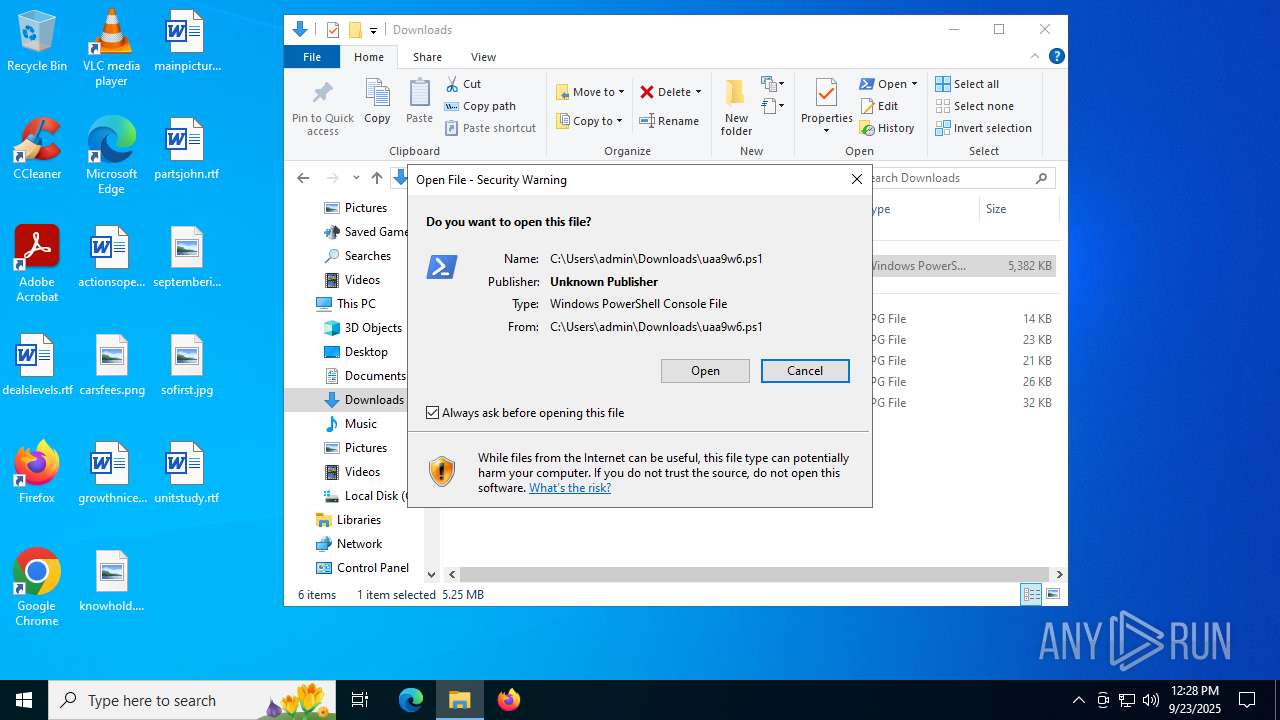
Bypass execution policy to execute commands
- powershell.exe (PID: 4760)
- powershell.exe (PID: 1512)
Registers / Runs the DLL via REGSVR32.EXE
- powershell.exe (PID: 4760)
- powershell.exe (PID: 1512)
QUASAR mutex has been found
- regsvr32.exe (PID: 3620)
Connects to the CnC server
- regsvr32.exe (PID: 3620)
QUASAR has been detected (SURICATA)
- regsvr32.exe (PID: 3620)
SUSPICIOUS
Converts a specified value to a byte (POWERSHELL)
- powershell.exe (PID: 4760)
- powershell.exe (PID: 1512)
Starts POWERSHELL.EXE for commands execution
- regsvr32.exe (PID: 3620)
Process checks specific path in scheduled tasks
- powershell.exe (PID: 72)
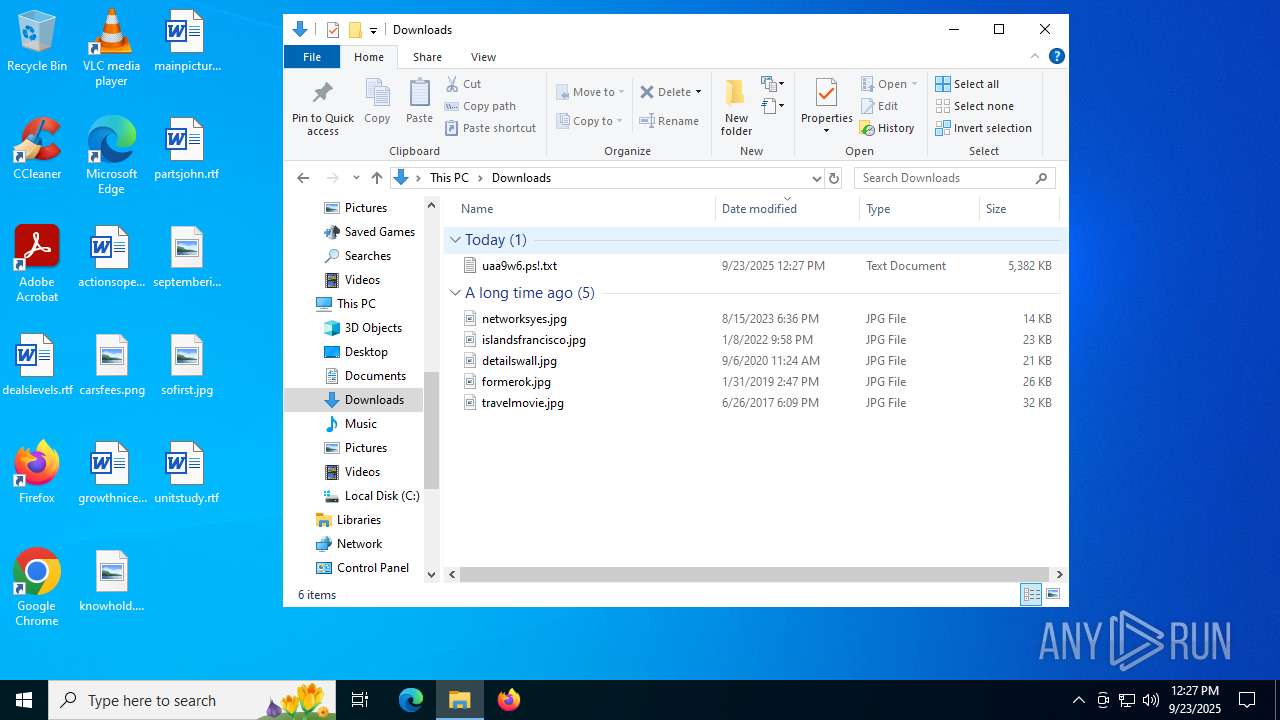
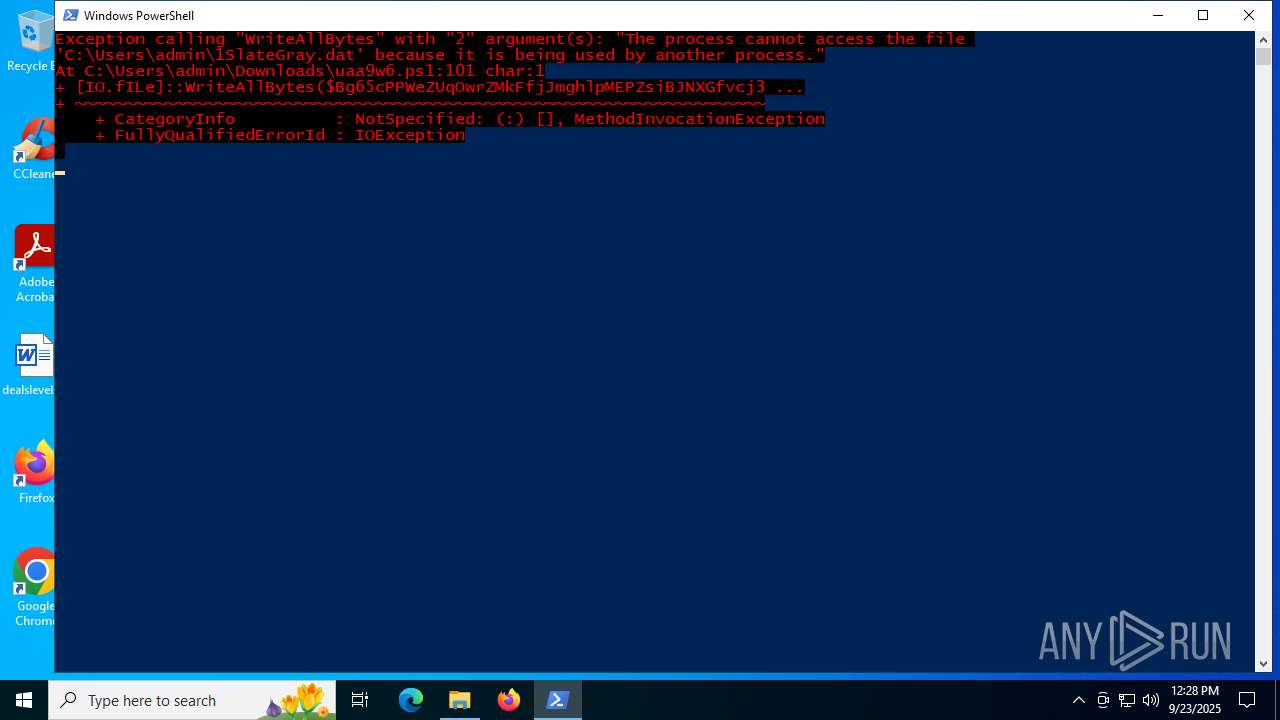
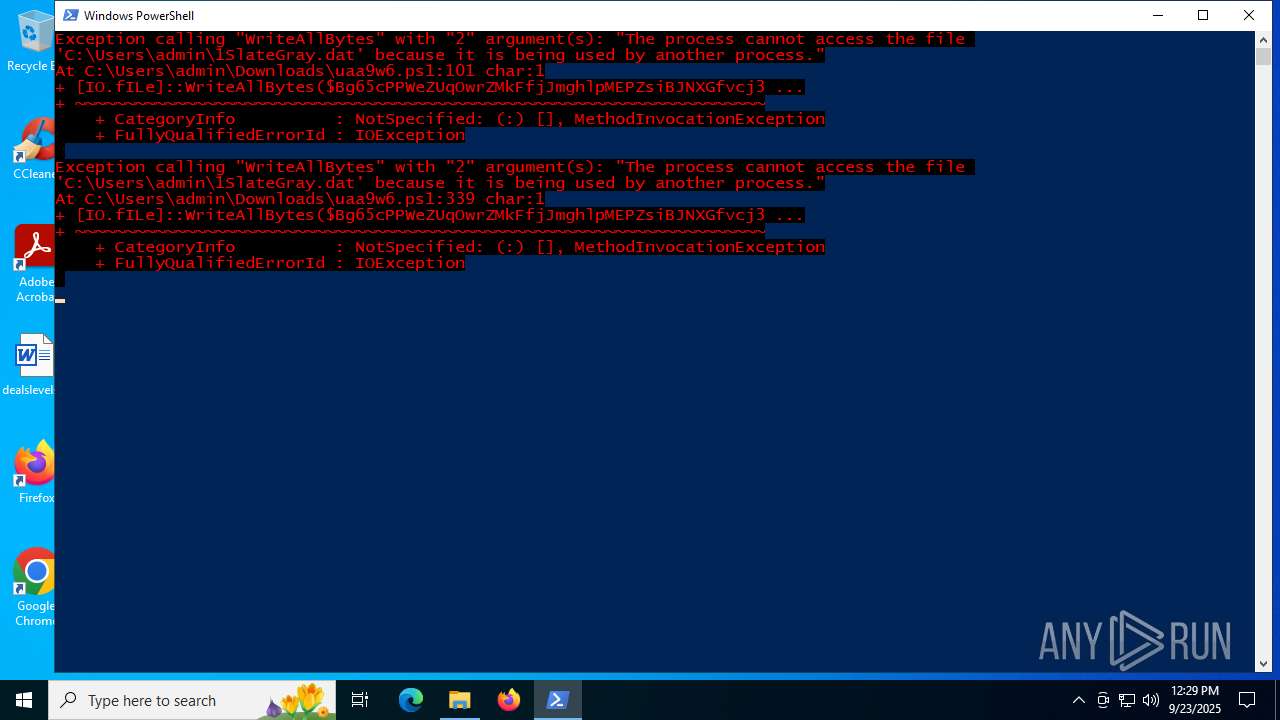
Writes data into a file (POWERSHELL)
- powershell.exe (PID: 4760)
The process hide an interactive prompt from the user
- regsvr32.exe (PID: 3620)
Checks for external IP
- svchost.exe (PID: 2200)
Contacting a server suspected of hosting an CnC
- regsvr32.exe (PID: 3620)
The process executes via Task Scheduler
- regsvr32.exe (PID: 7240)
The process bypasses the loading of PowerShell profile settings
- regsvr32.exe (PID: 3620)
INFO
Application launched itself
- msedge.exe (PID: 1156)
- msedge.exe (PID: 7904)
Checks supported languages
- identity_helper.exe (PID: 7624)
- identity_helper.exe (PID: 8048)
Reads Environment values
- identity_helper.exe (PID: 7624)
- identity_helper.exe (PID: 8048)
Reads the computer name
- identity_helper.exe (PID: 8048)
- identity_helper.exe (PID: 7624)
Gets data length (POWERSHELL)
- powershell.exe (PID: 4760)
- powershell.exe (PID: 1512)
Application based on Rust
- regsvr32.exe (PID: 3620)
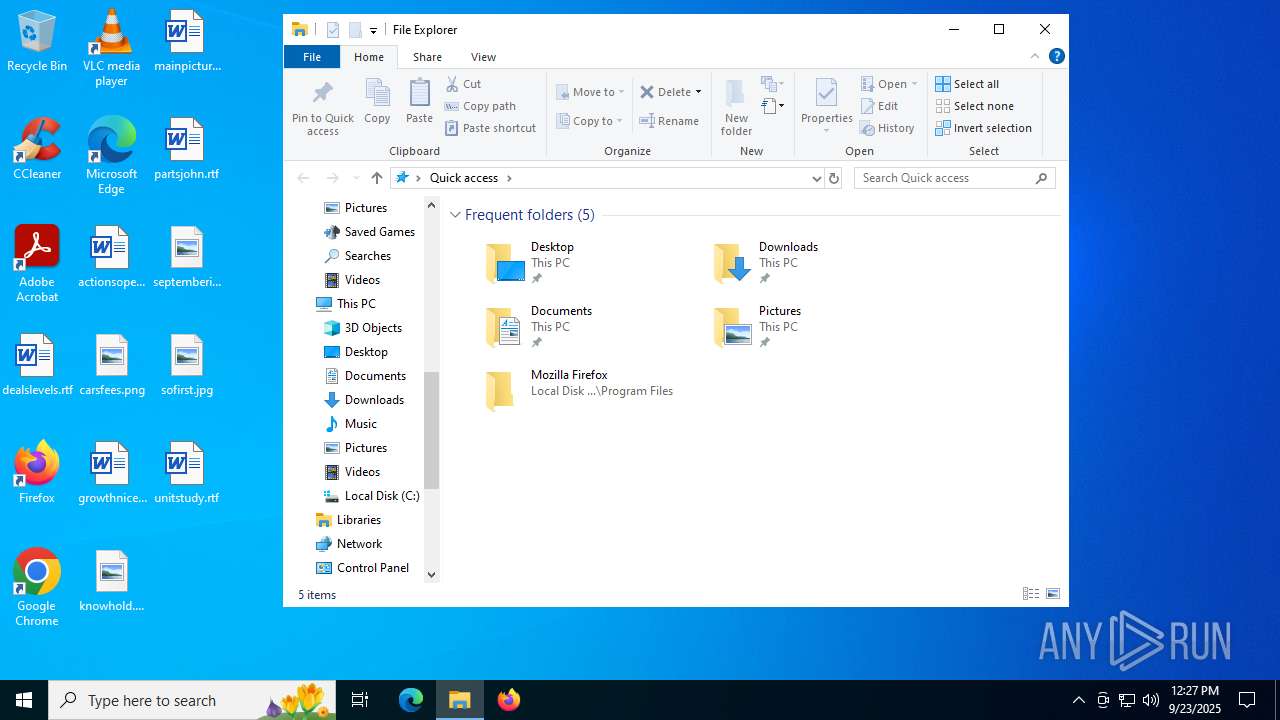
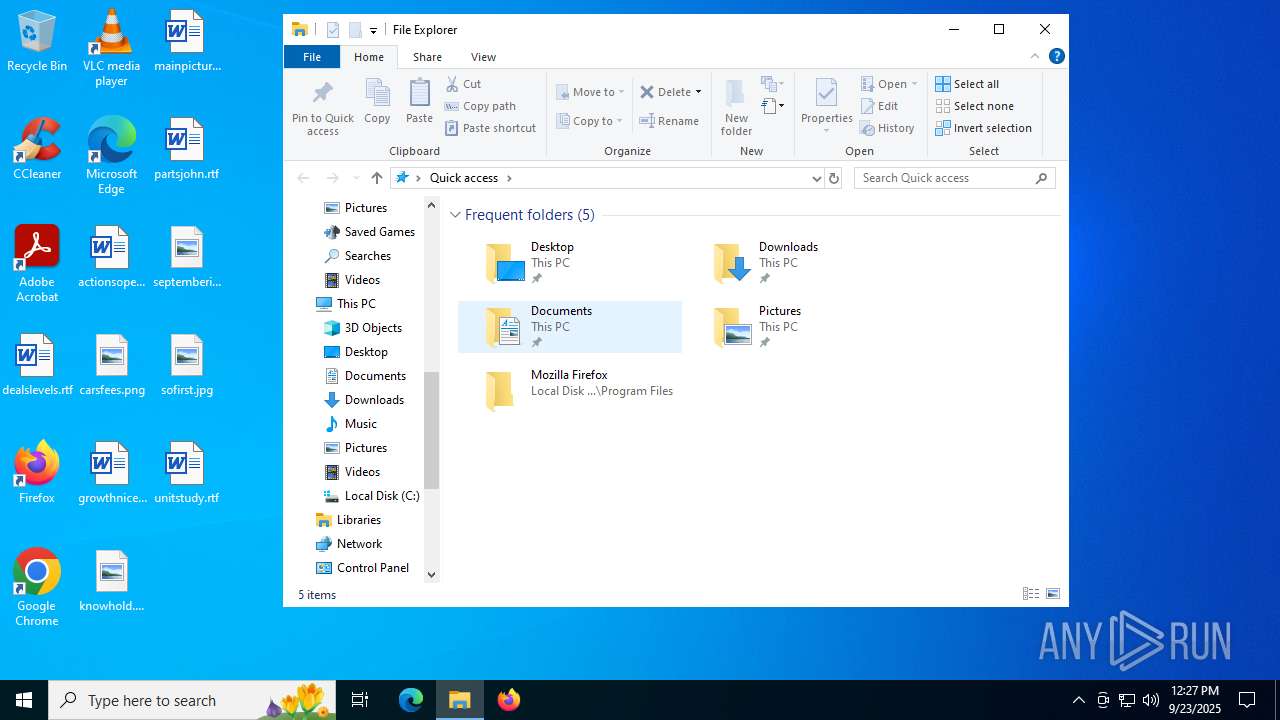
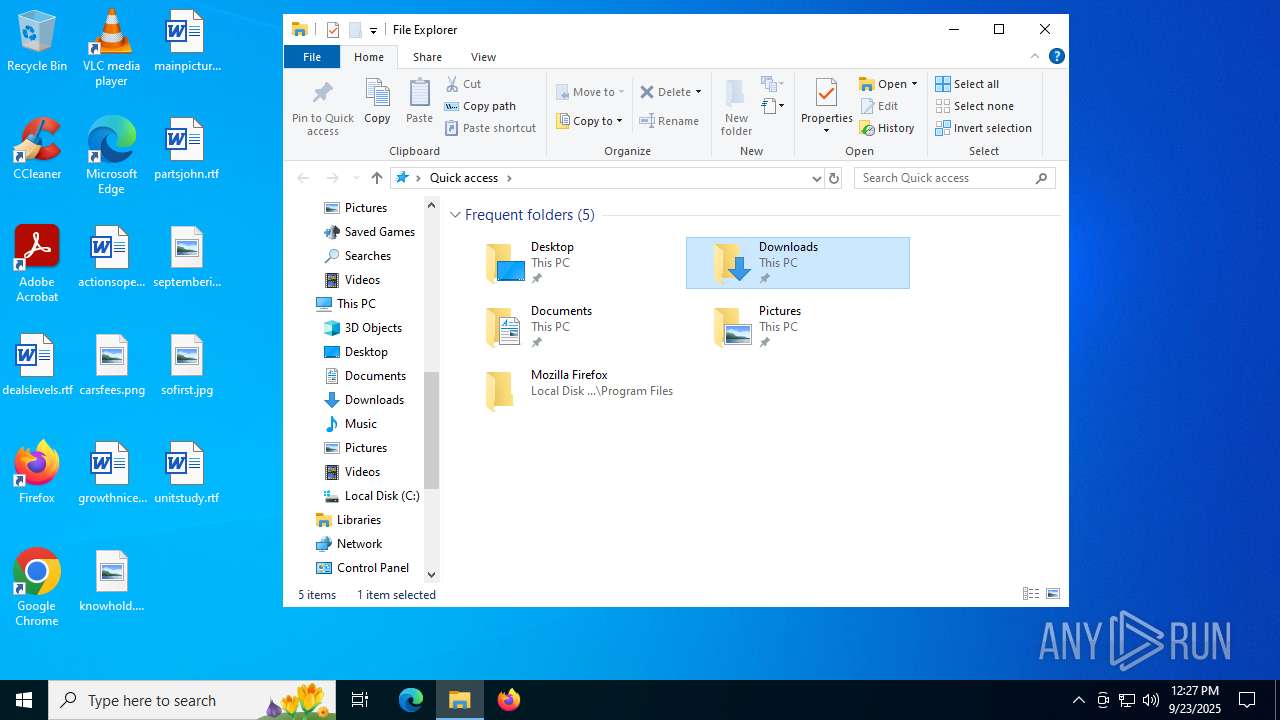
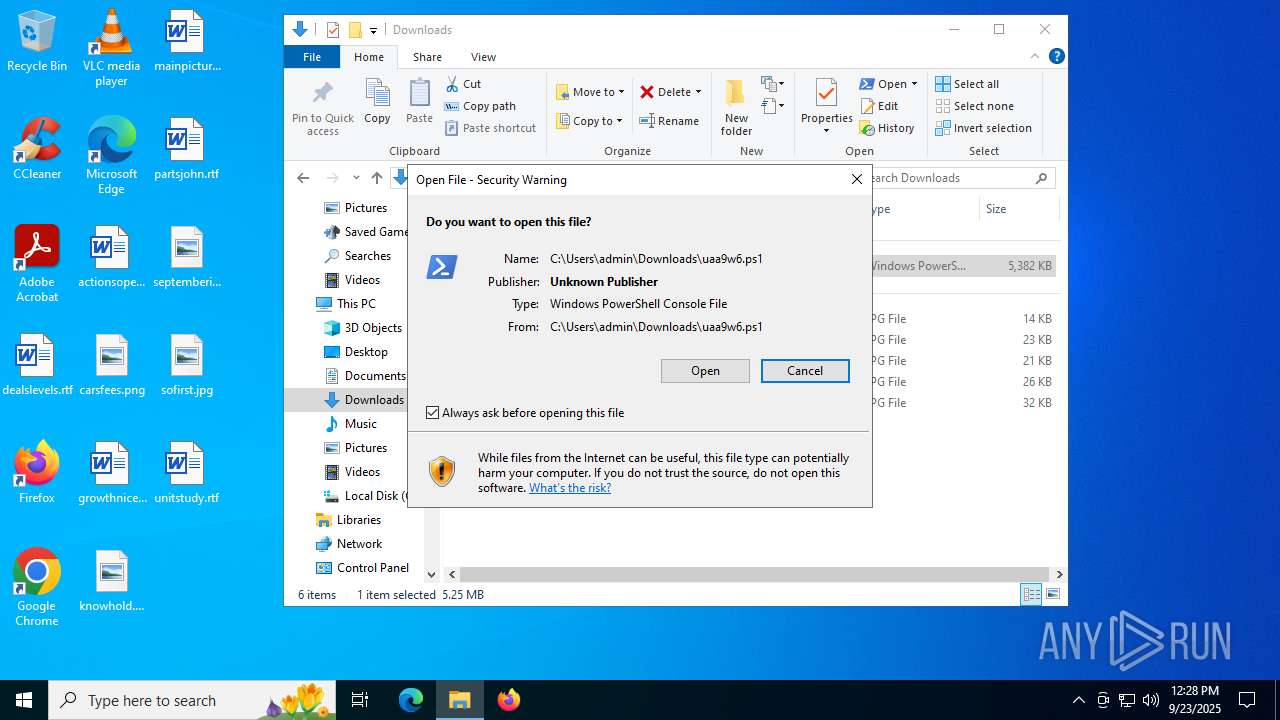
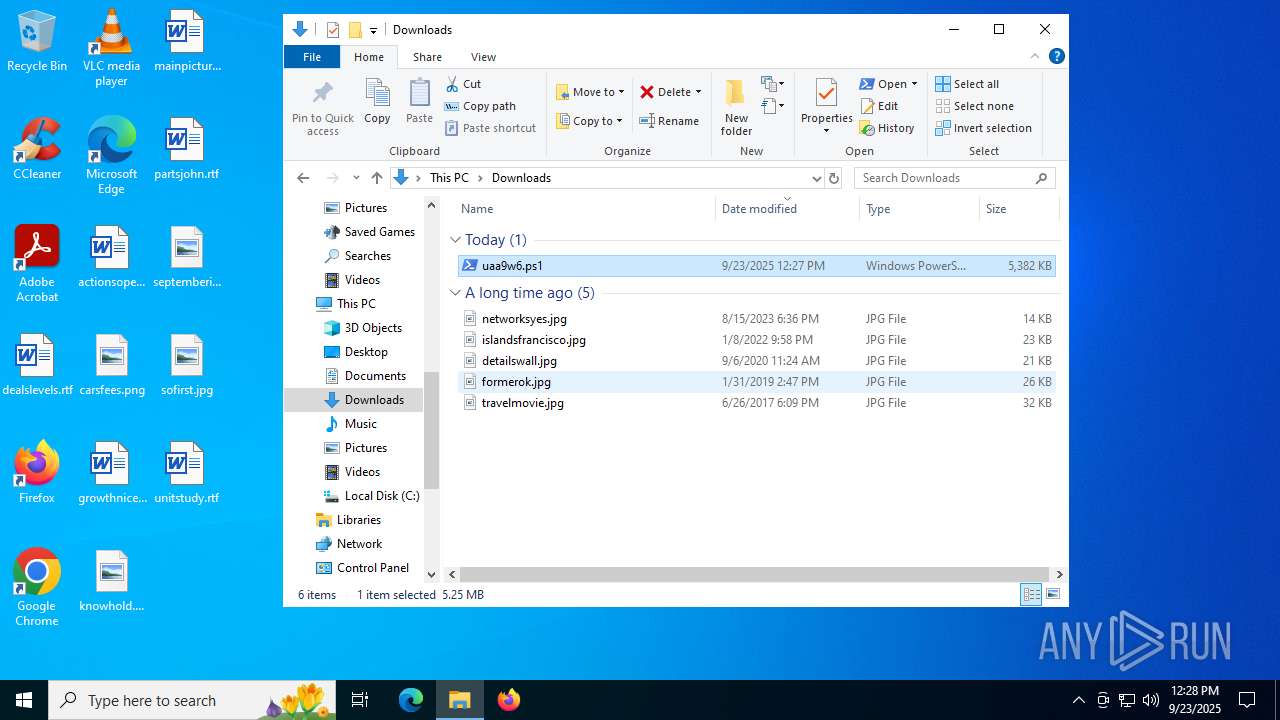
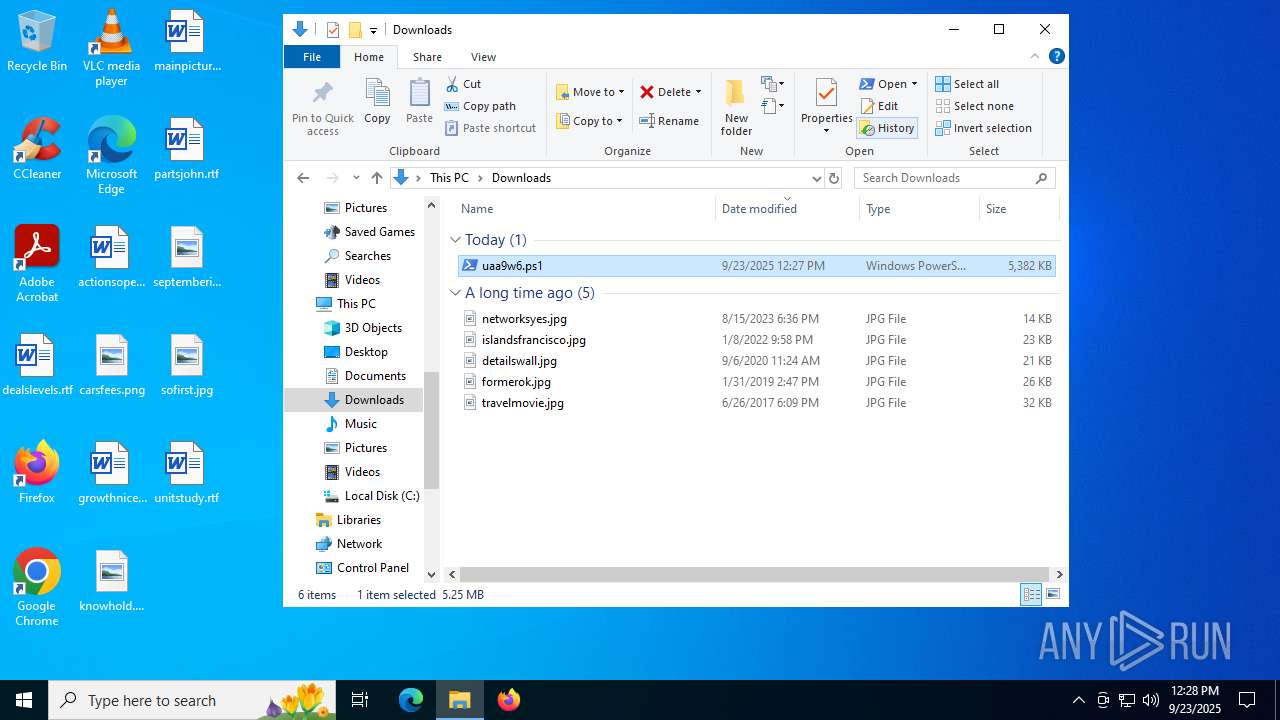
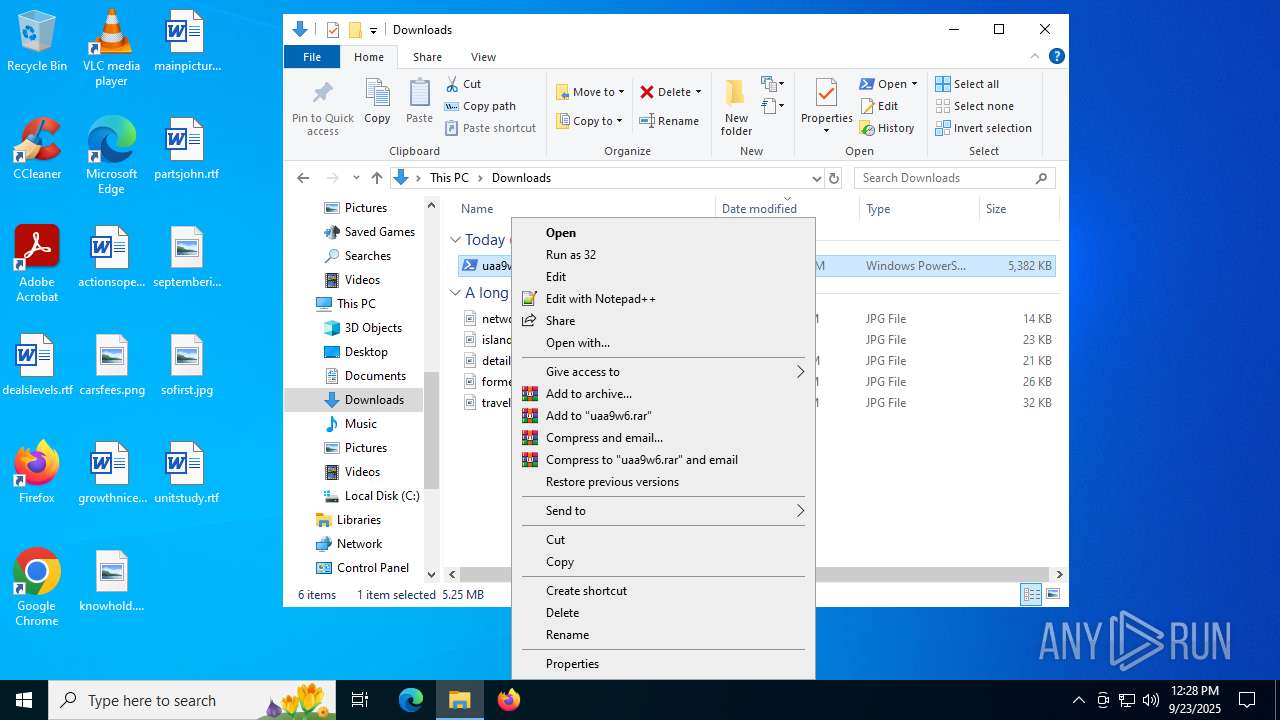
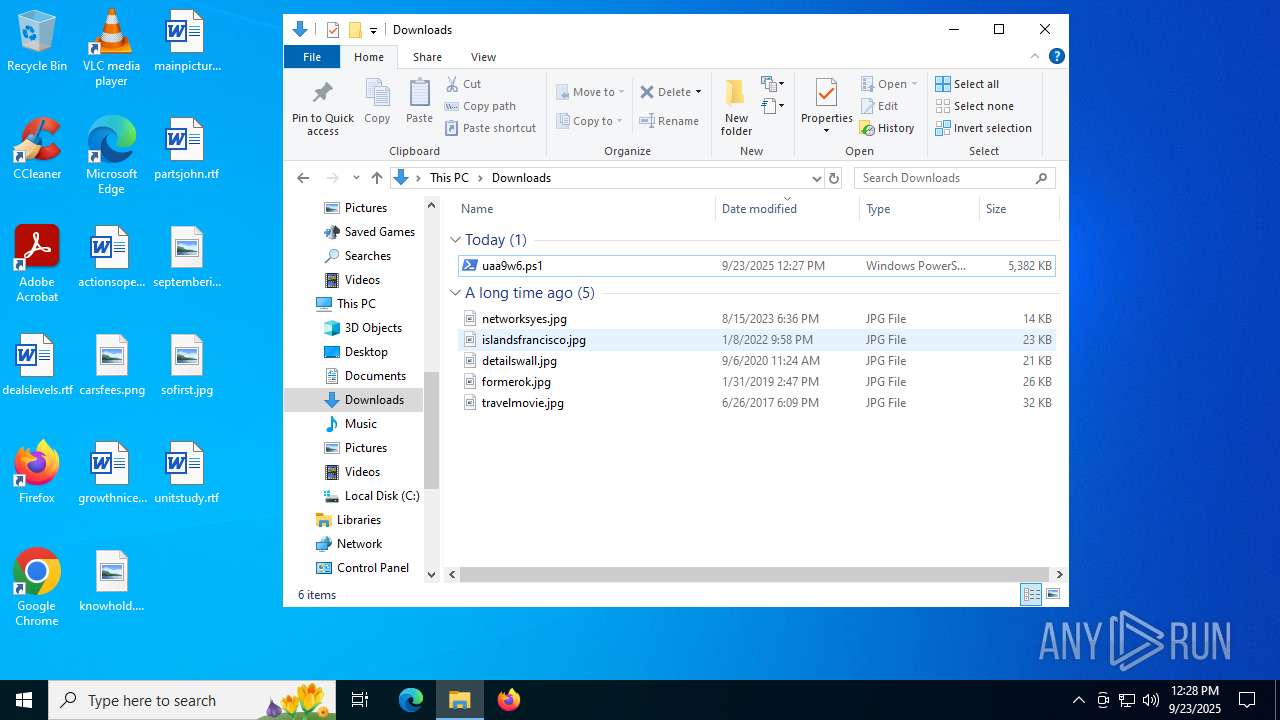
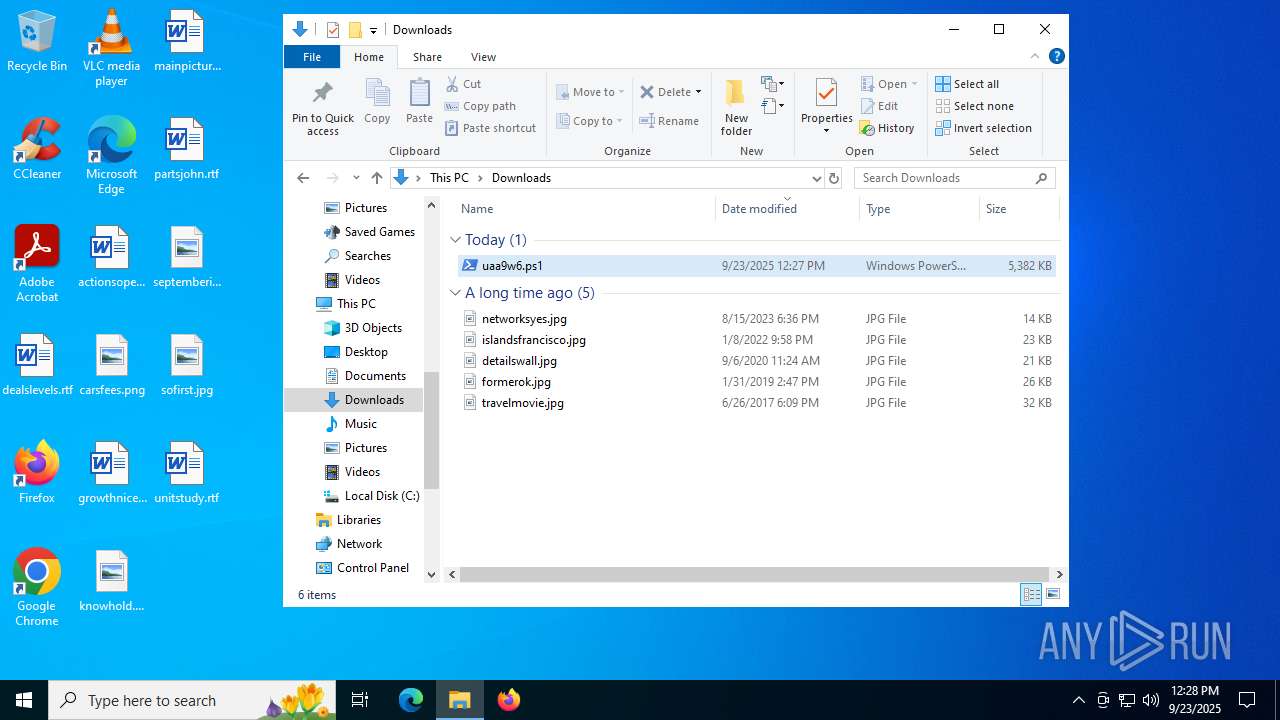
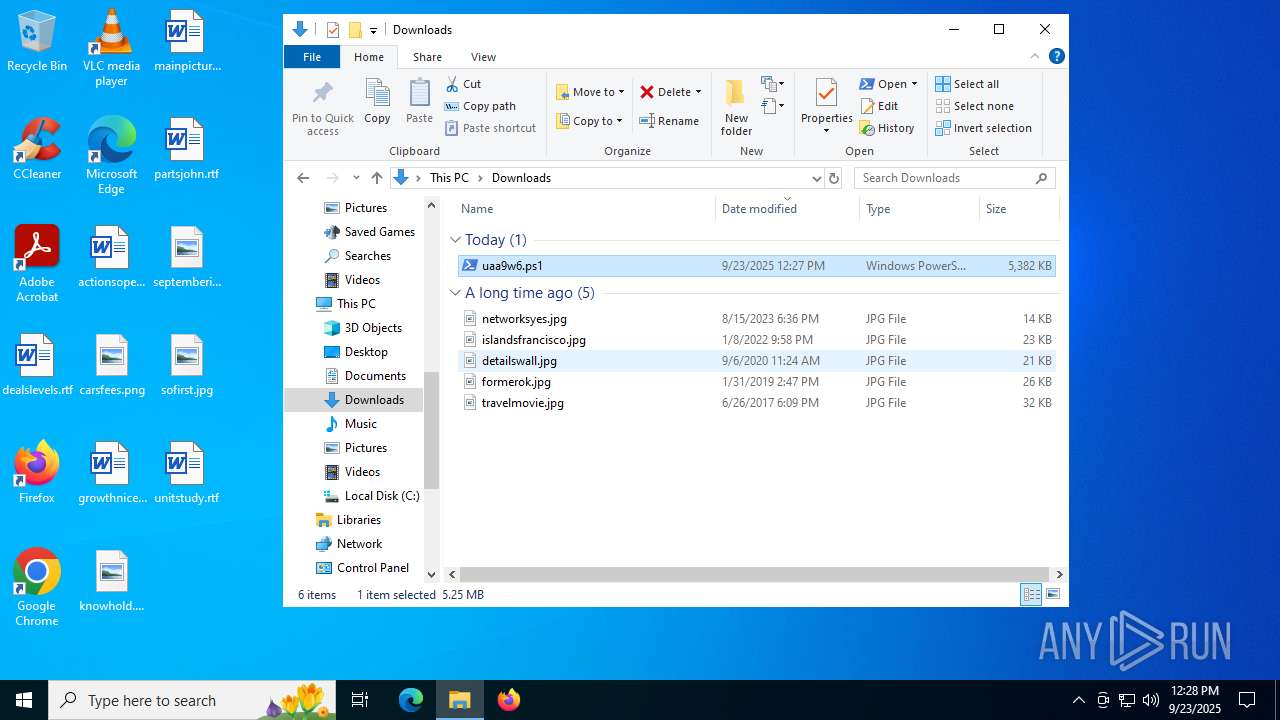
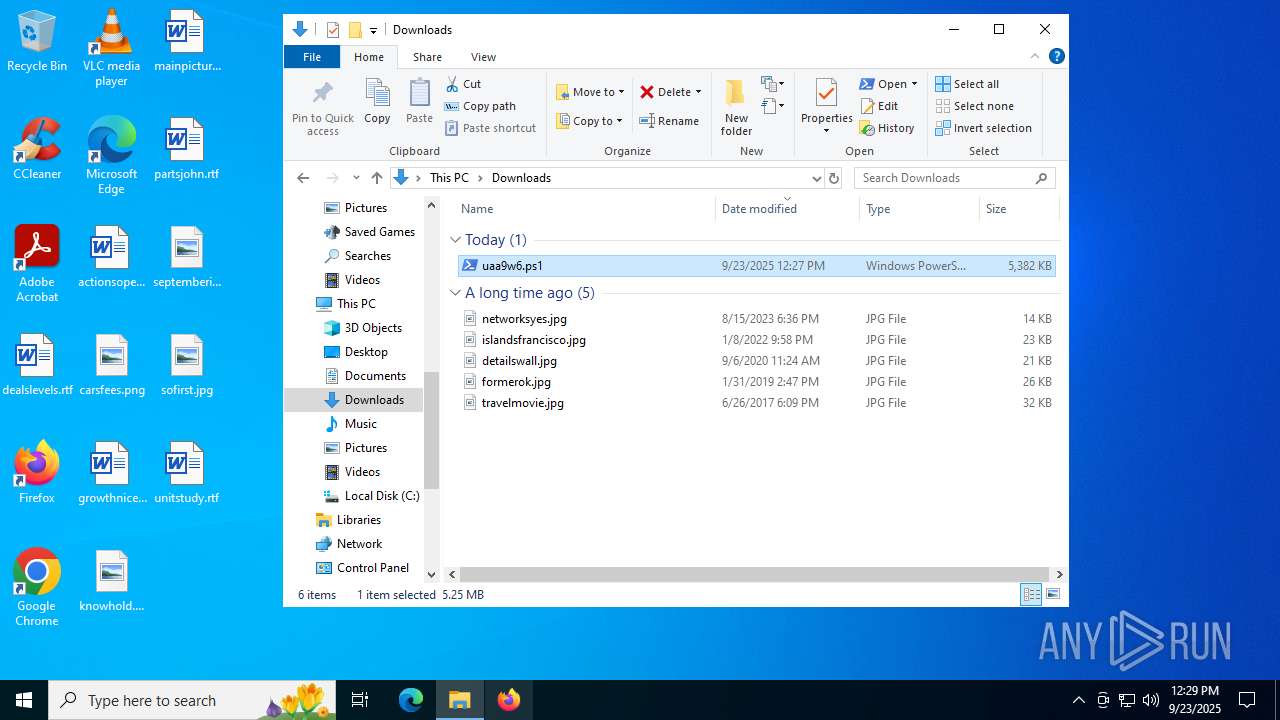
Manual execution by a user
- powershell.exe (PID: 4760)
- powershell.exe (PID: 1512)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 72)
- powershell.exe (PID: 6764)
Reads the software policy settings
- regsvr32.exe (PID: 3620)
- slui.exe (PID: 7428)
Checks proxy server information
- regsvr32.exe (PID: 3620)
- slui.exe (PID: 7428)
Disables trace logs
- regsvr32.exe (PID: 3620)
Creates files in the program directory
- regsvr32.exe (PID: 3620)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 1512)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
194
Monitored processes
56
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 72 | "powershell" -Command "if (Get-ScheduledTask | Where-Object { $_.Actions.Execute -like '*regsvr32.exe' -and $_.Actions.Arguments -eq '/s /i \"C:\Users\admin\1SlateGray.dat\"' }) { exit 0 } else { exit 1 }" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | regsvr32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 536 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 868 | /s /i C:\Users\admin\1SlateGray.dat | C:\Windows\SysWOW64\regsvr32.exe | — | regsvr32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft(C) Register Server Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1156 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --from-ie-to-edge=8 -- "https://files.catbox.moe/uaa9w6.txt" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1512 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ep bypass "C:\Users\admin\Downloads\uaa9w6.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1728 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --pdf-upsell-enabled --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --always-read-main-dll --field-trial-handle=3324,i,3436720255602709715,11177792342054213468,262144 --variations-seed-version --mojo-platform-channel-handle=3340 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1740 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6080,i,5199386761893603637,16075261483505821144,262144 --variations-seed-version --mojo-platform-channel-handle=6108 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2096 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4000,i,3436720255602709715,11177792342054213468,262144 --variations-seed-version --mojo-platform-channel-handle=1624 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2200 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2620 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=5360,i,5199386761893603637,16075261483505821144,262144 --variations-seed-version --mojo-platform-channel-handle=7132 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
47 372
Read events
47 263
Write events
103
Delete events
6
Modification events
| (PID) Process: | (6364) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | L1WatermarkLowPart |
Value: 0 | |||
| (PID) Process: | (6364) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | L1WatermarkHighPart |
Value: 0 | |||
| (PID) Process: | (6364) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 0 | |||
| (PID) Process: | (6364) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 0 | |||
| (PID) Process: | (6364) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (6364) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31206533 | |||
| (PID) Process: | (6364) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6364) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6364) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6364) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
Executable files
17
Suspicious files
315
Text files
88
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1156 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF18def1.TMP | — | |
MD5:— | SHA256:— | |||
| 1156 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1156 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF18df10.TMP | — | |
MD5:— | SHA256:— | |||
| 1156 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1156 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF18dee1.TMP | — | |
MD5:— | SHA256:— | |||
| 1156 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1156 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF18df20.TMP | — | |
MD5:— | SHA256:— | |||
| 1156 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1156 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF18df10.TMP | — | |
MD5:— | SHA256:— | |||
| 1156 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
62
DNS requests
63
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4012 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:dUZdvW4TVstUQacCzYFnv3XSAYEdXcf36AFroUu1CcA&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
5644 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.16.164.106:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4692 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4692 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4692 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
4692 | SIHClient.exe | GET | 200 | 2.16.164.106:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
4692 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | unknown | — | — | whitelisted |
4692 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2432 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4012 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4012 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4012 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4012 | msedge.exe | 108.181.20.35:443 | files.catbox.moe | TELUS Communications | CA | whitelisted |
4012 | msedge.exe | 2.16.241.220:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
files.catbox.moe |
| unknown |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4012 | msedge.exe | Potentially Bad Traffic | ET INFO Observed File Sharing Service Download Domain (files .catbox .moe in TLS SNI) |
4012 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Downloading from a file sharing service is observed |
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
4012 | msedge.exe | Potentially Bad Traffic | ET INFO Observed File Sharing Service Download Domain (files .catbox .moe in TLS SNI) |
— | — | Potentially Bad Traffic | ET INFO Possible Chrome Plugin install |
2200 | svchost.exe | Potentially Bad Traffic | ET INFO External IP Lookup Domain in DNS Lookup (ipwho .is) |
3620 | regsvr32.exe | Domain Observed Used for C2 Detected | REMOTE [ANY.RUN] Possible AsyncRAT/QuasarRAT SSL certificate |
3620 | regsvr32.exe | Domain Observed Used for C2 Detected | ET MALWARE Generic AsyncRAT/zgRAT Style SSL Cert |
3620 | regsvr32.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Malicious SSL Cert (Quasar CnC) |
Process | Message |
|---|---|
regsvr32.exe | Using standard host list mode
|
regsvr32.exe | ClipboardChecker: Initialized with monitoring disabled
|
regsvr32.exe | [CLIENT] Received packet: ClientIdentificationResult (Length: 63 bytes)
|
regsvr32.exe | [CLIENT] Received packet: PingRequest (Length: 40 bytes)
|
regsvr32.exe | [CLIENT] Received packet: GetPreviewImage (Length: 56 bytes)
|
regsvr32.exe | Capturing single desktop image
|
regsvr32.exe | [CLIENT] Received packet: GetMonitors (Length: 76 bytes)
|
regsvr32.exe | 1
|
regsvr32.exe | [CLIENT] Received packet: GetDesktop (Length: 85 bytes)
|
regsvr32.exe | Starting remote desktop session
|