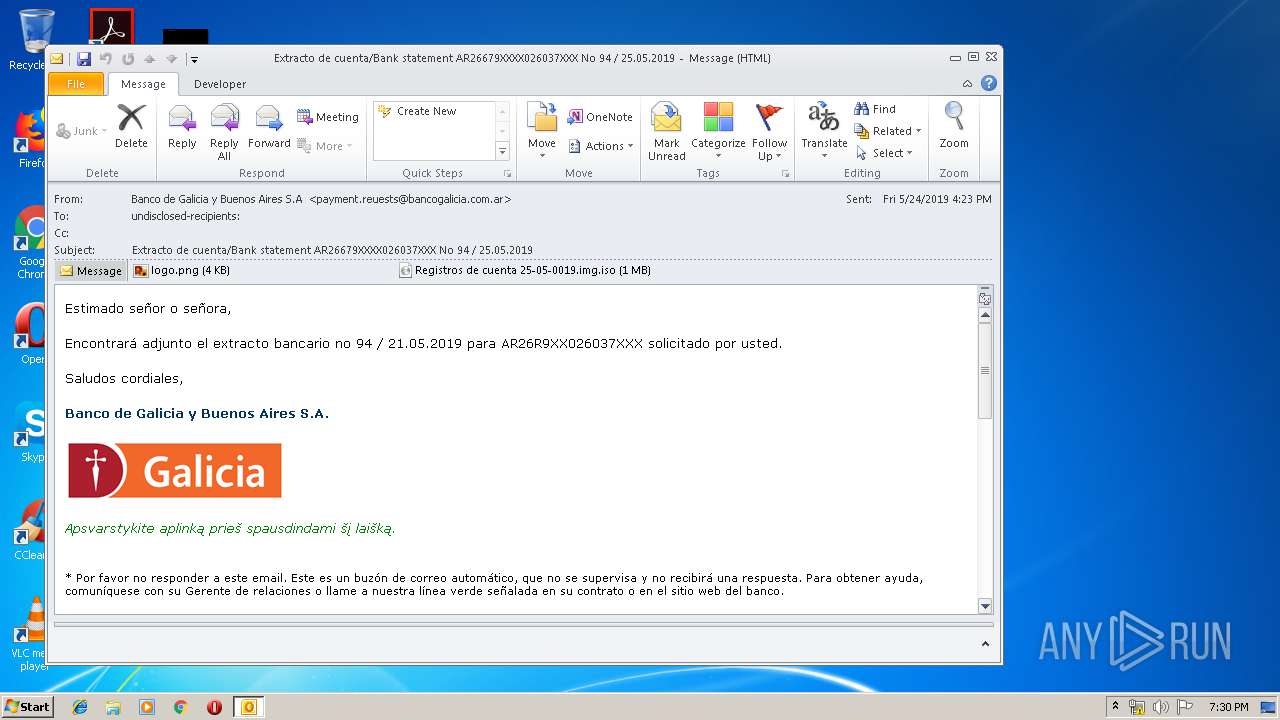
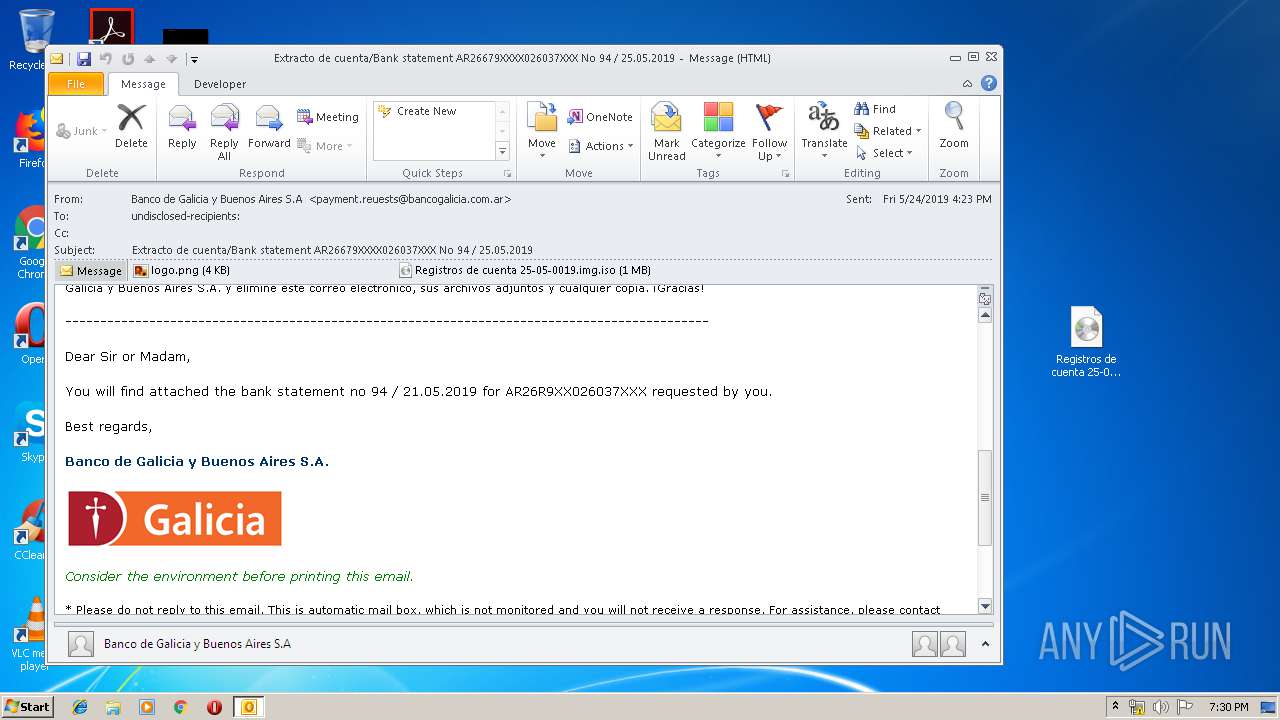
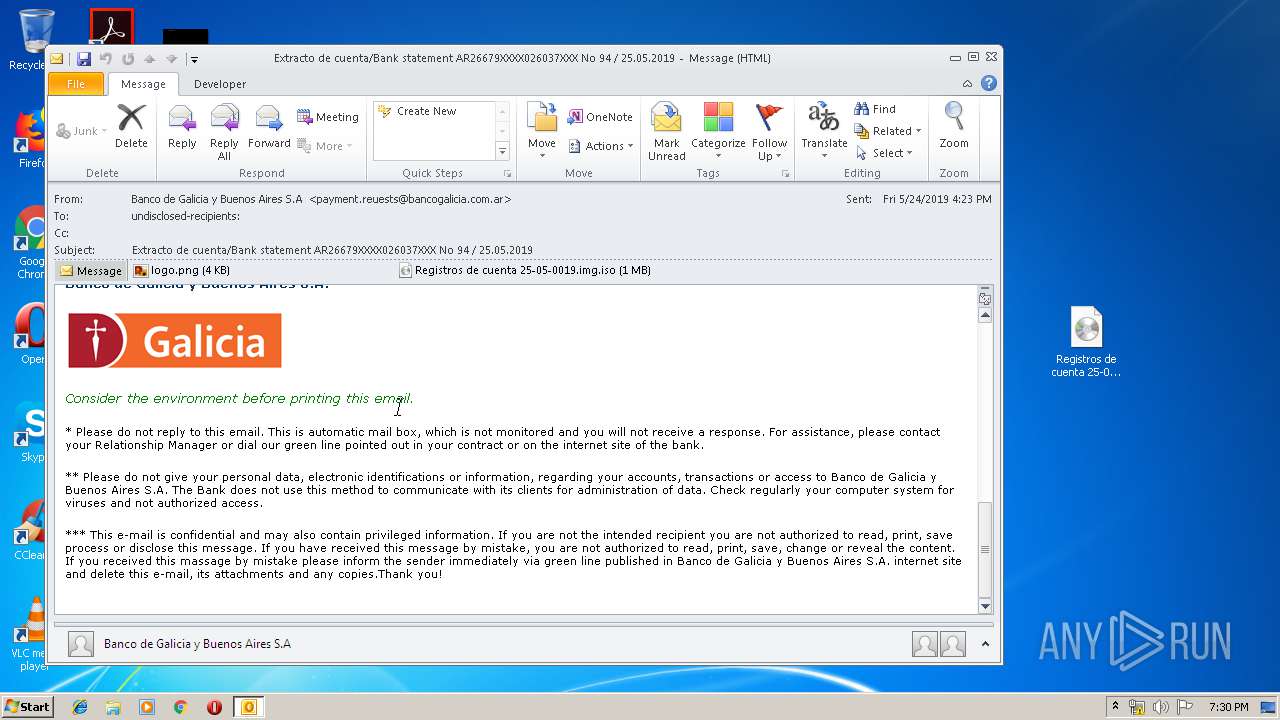
| File name: | sarratta@macro.com.ar_download.eml |
| Full analysis: | https://app.any.run/tasks/180dd476-7b72-40e6-868d-c076414a583a |
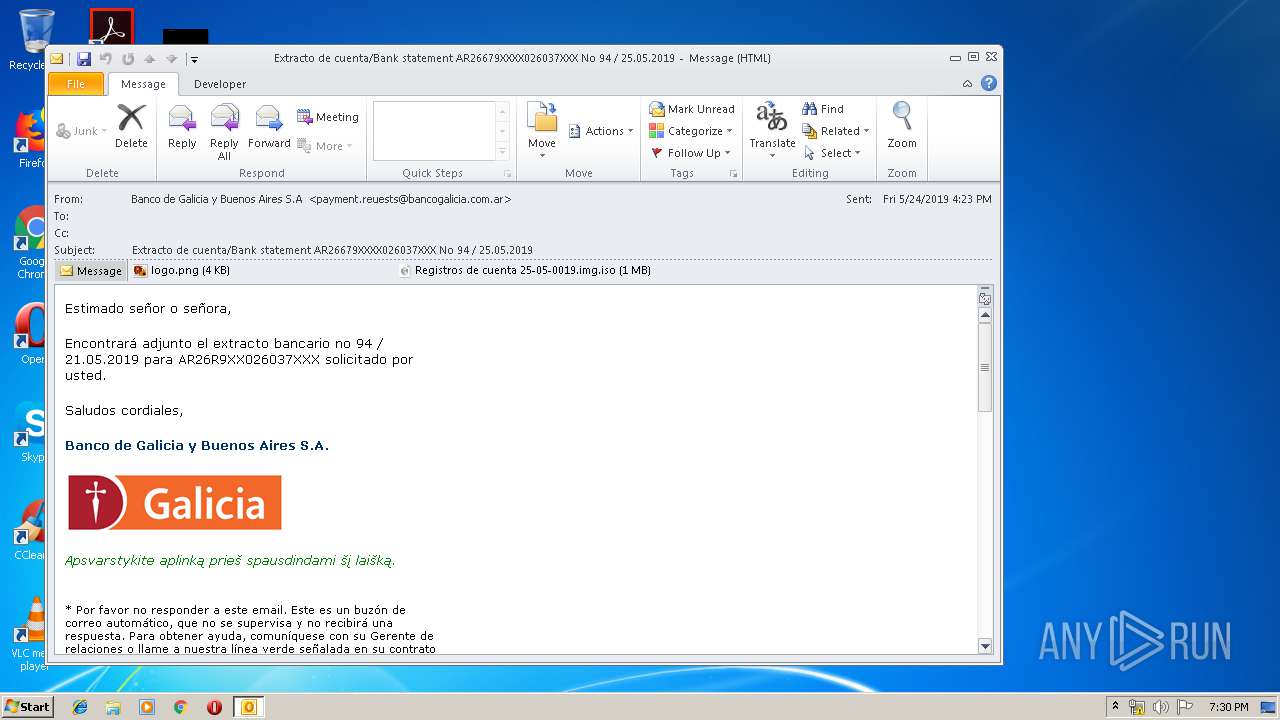
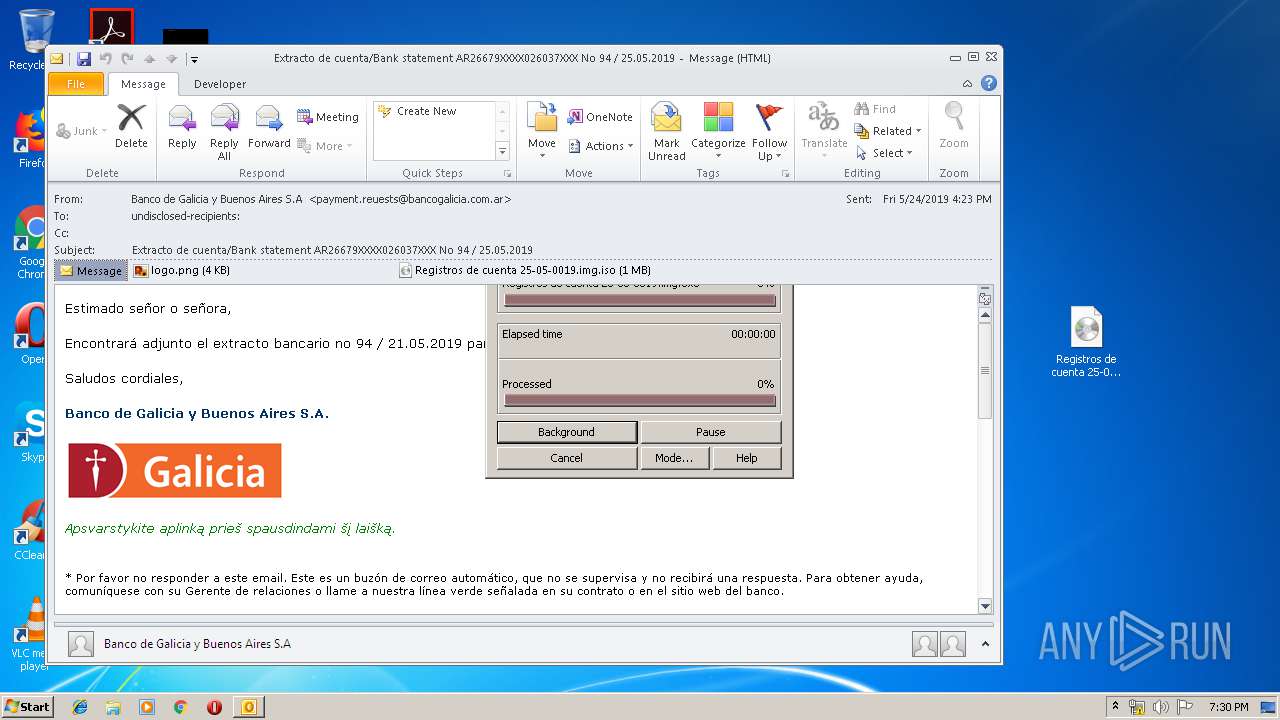
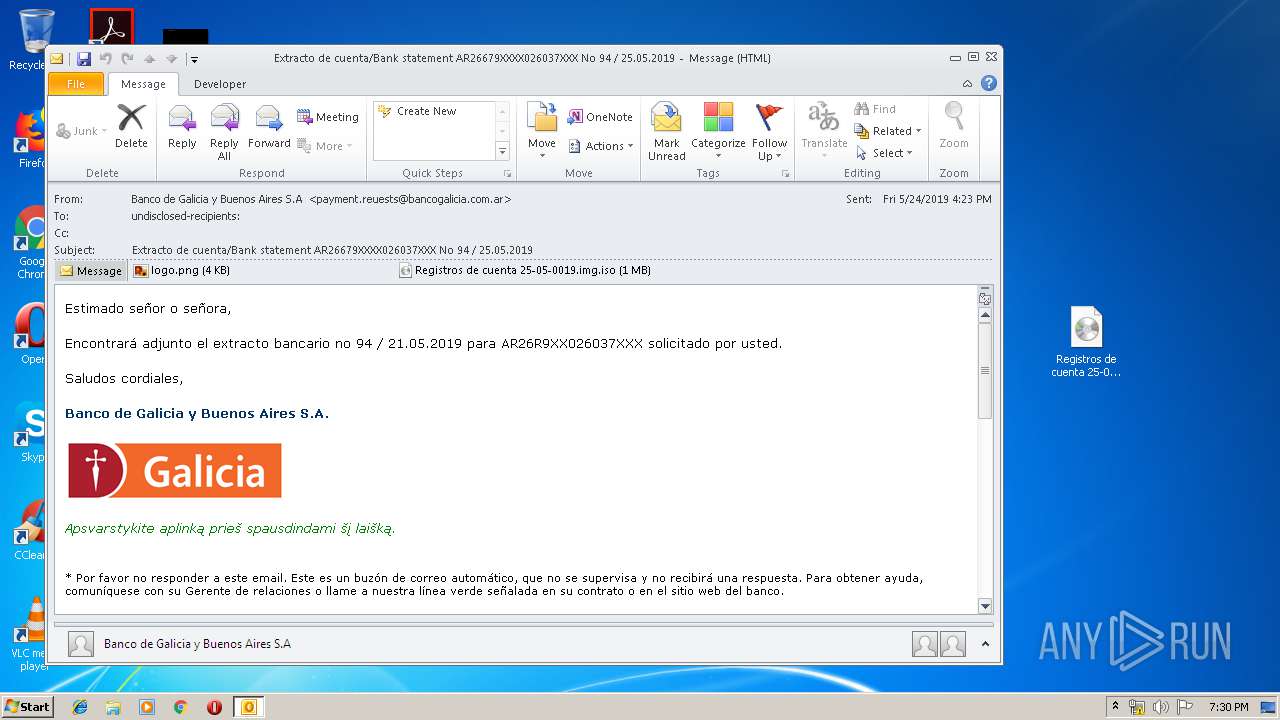
| Verdict: | Malicious activity |
| Threats: | LokiBot was developed in 2015 to steal information from a variety of applications. Despite the age, this malware is still rather popular among cybercriminals. |
| Analysis date: | May 24, 2019, 18:29:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | RFC 822 mail, UTF-8 Unicode text, with CRLF line terminators |
| MD5: | D539A83AABEDFE934686B74D7126227C |
| SHA1: | 4E5F0A6AAA6076E8C5FF8465749CCAD01EE859DA |
| SHA256: | 1C222578E51B729072A8F2C3B2456AF79827DCB90332642D3D6662441A6DD9C4 |
| SSDEEP: | 24576:+QAhGxTvE+AzNysoBZjZOWSEOb9hKQD7dtJ4wd2UqYTD:lDW+yWQJzd2x2D |
MALICIOUS
Writes to a start menu file
- Registros de cuenta 25-05-0019.img.exe (PID: 3324)
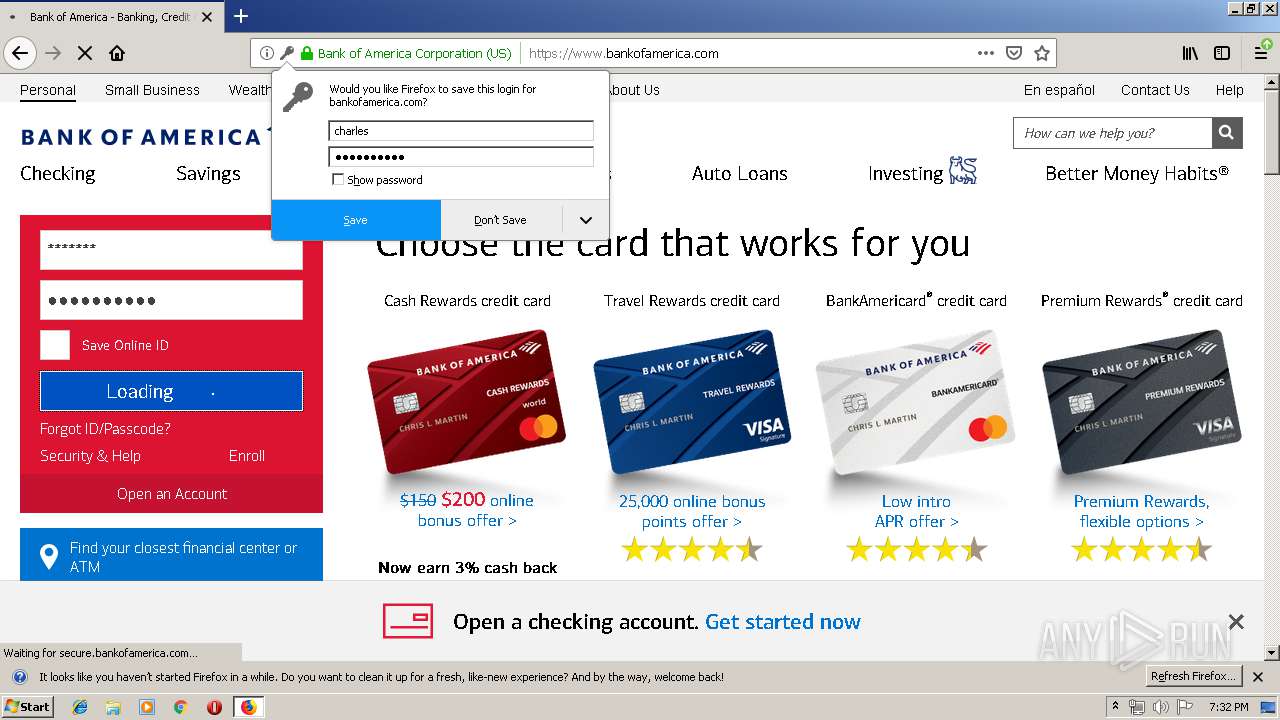
Connects to CnC server
- svchost.exe (PID: 3772)
Application was dropped or rewritten from another process
- Registros de cuenta 25-05-0019.img.exe (PID: 3324)
- svchost.exe (PID: 3772)
Uses SVCHOST.EXE for hidden code execution
- Registros de cuenta 25-05-0019.img.exe (PID: 3324)
LOKIBOT was detected
- svchost.exe (PID: 3772)
Detected artifacts of LokiBot
- svchost.exe (PID: 3772)
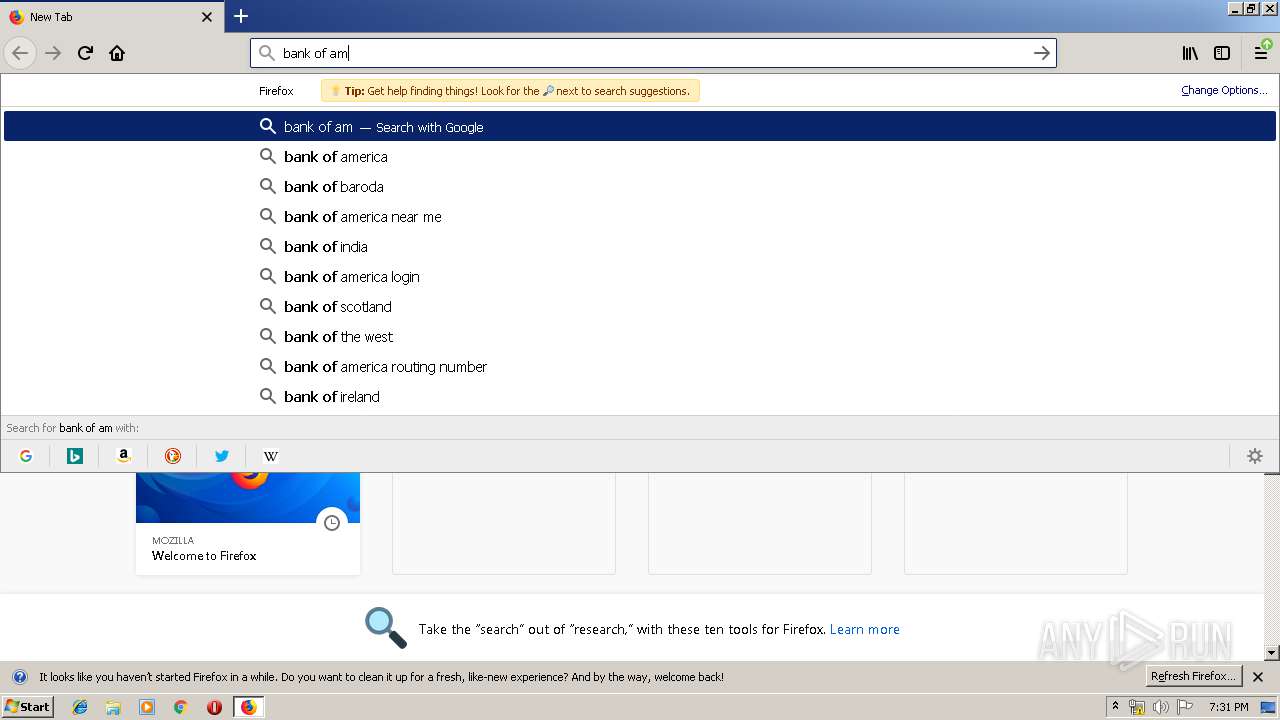
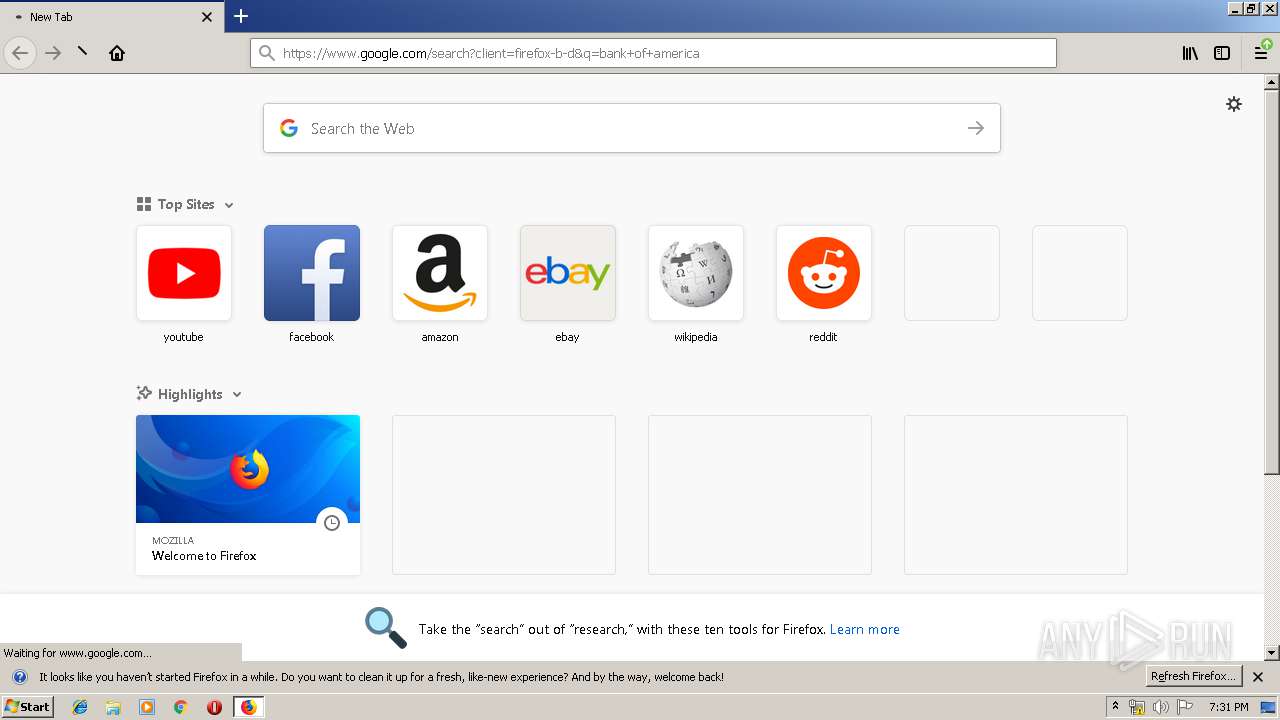
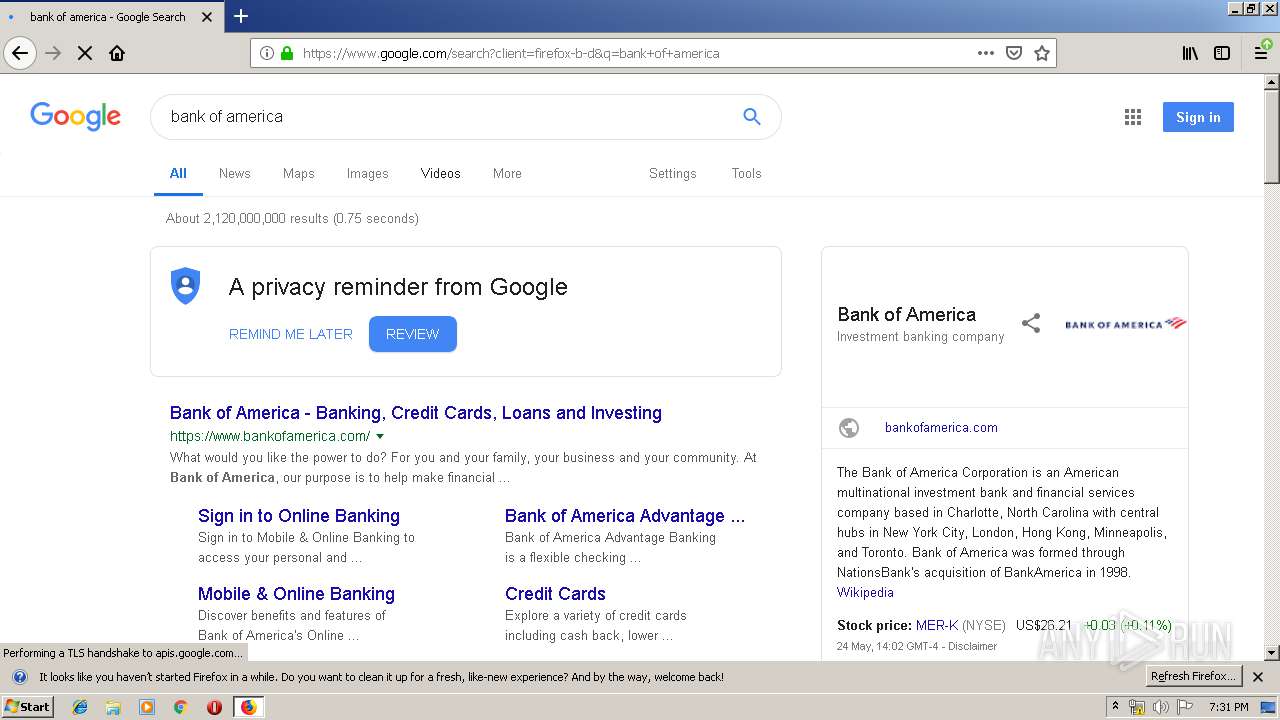
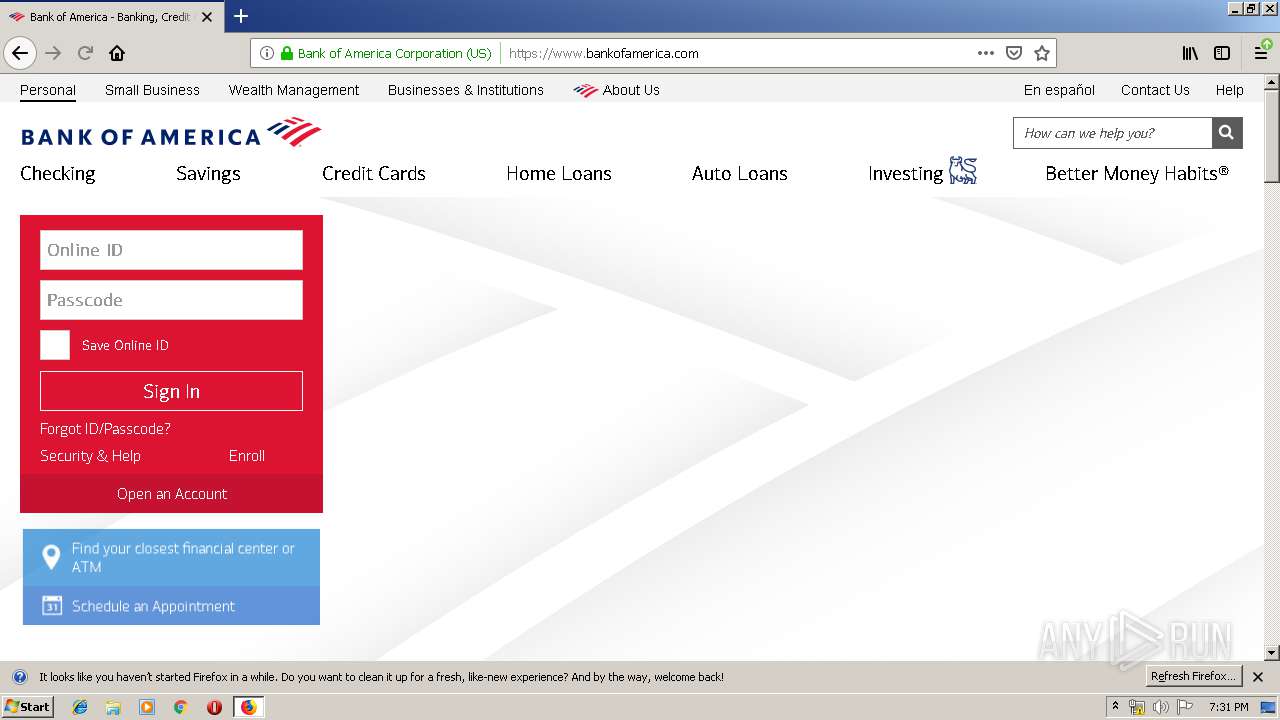
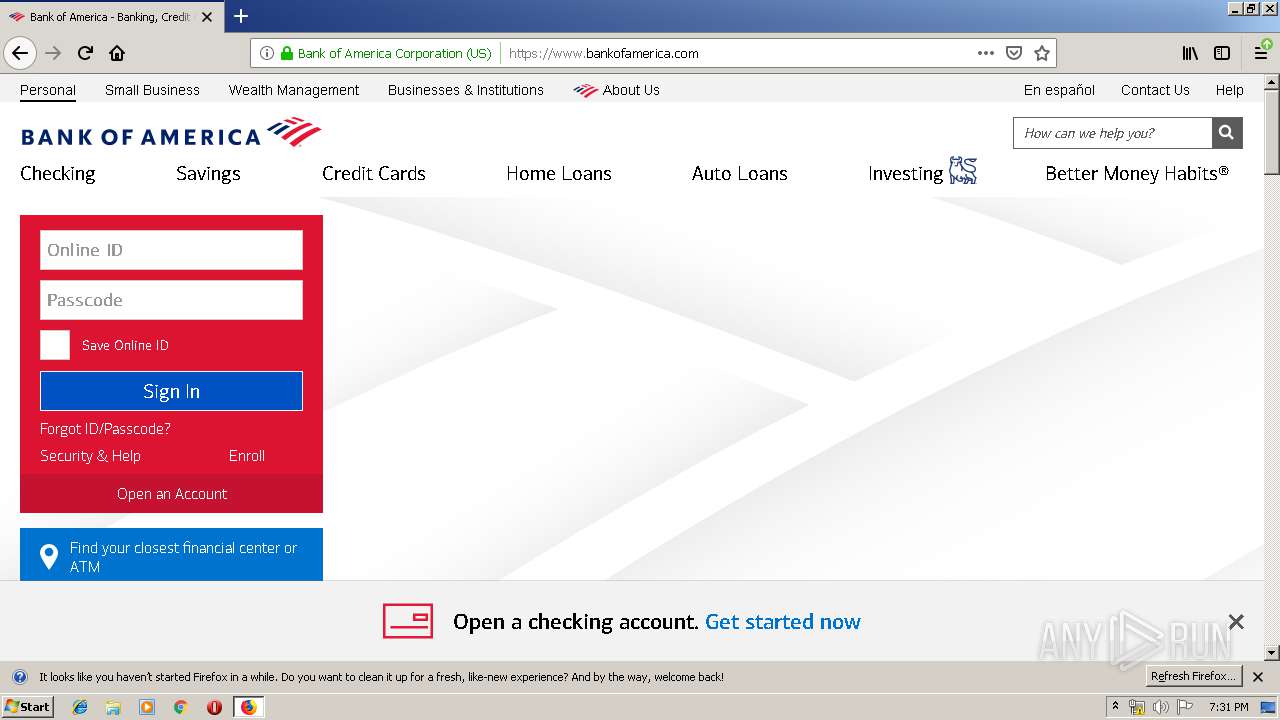
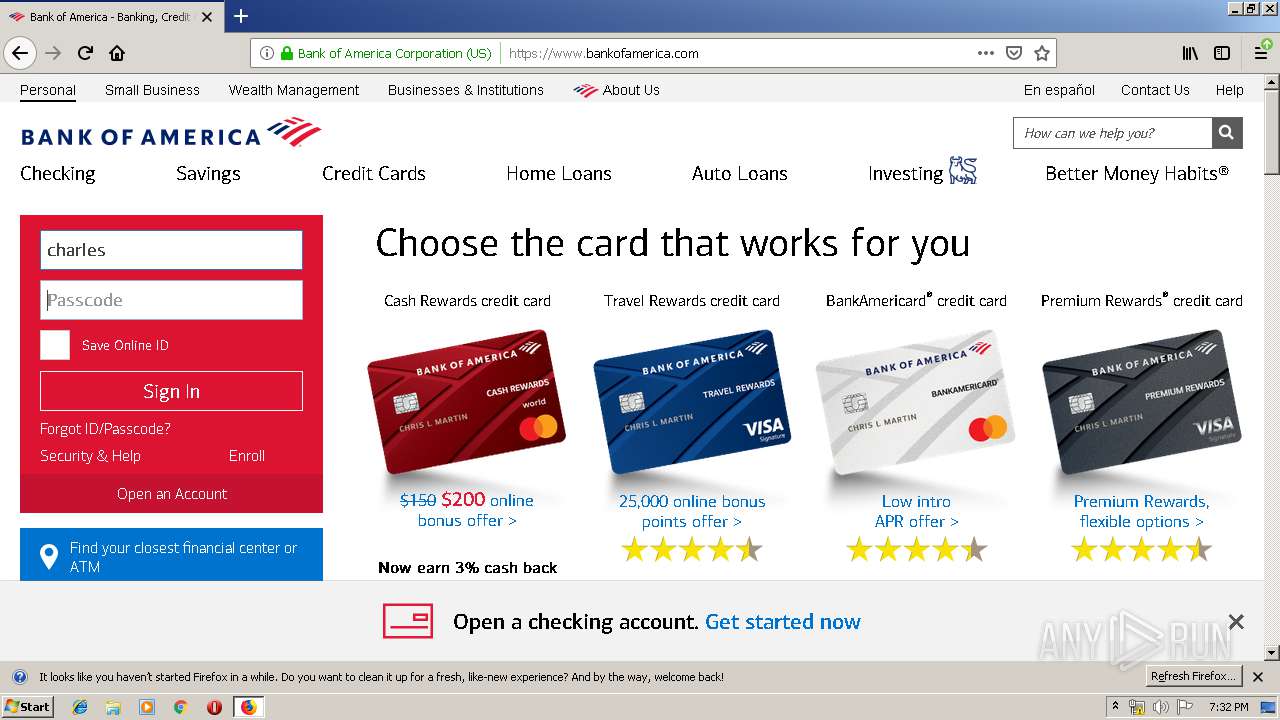
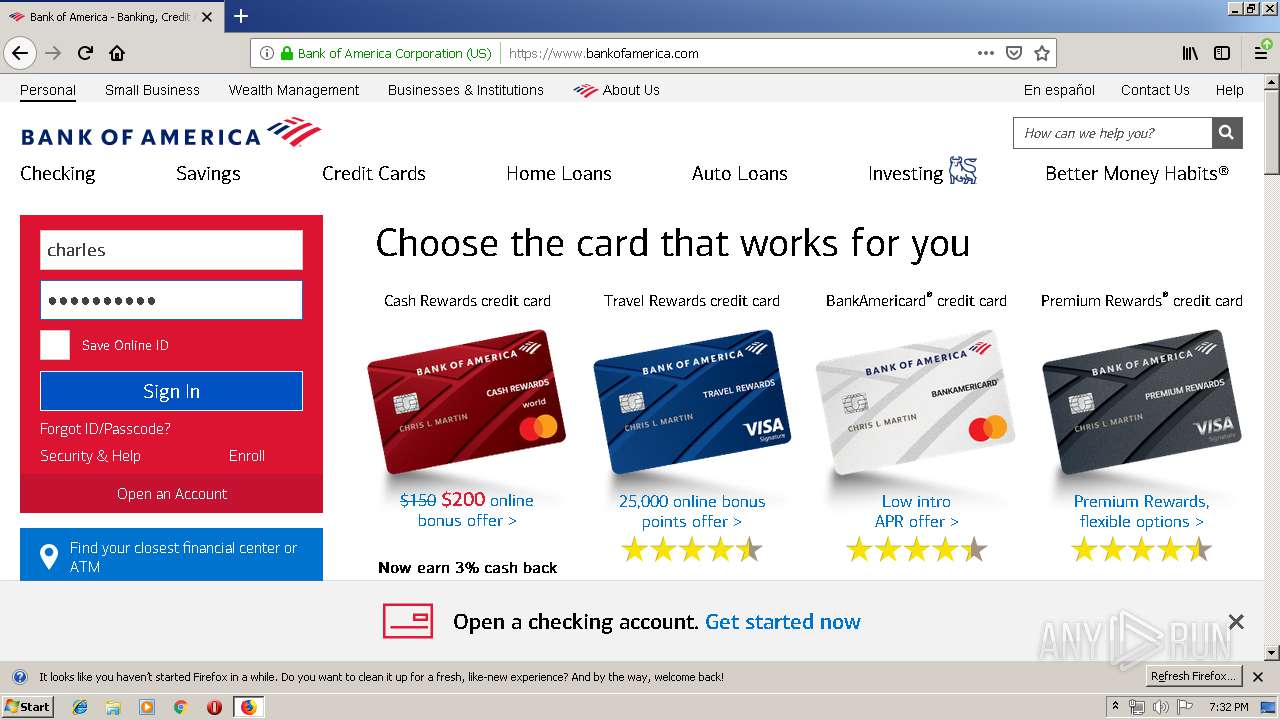
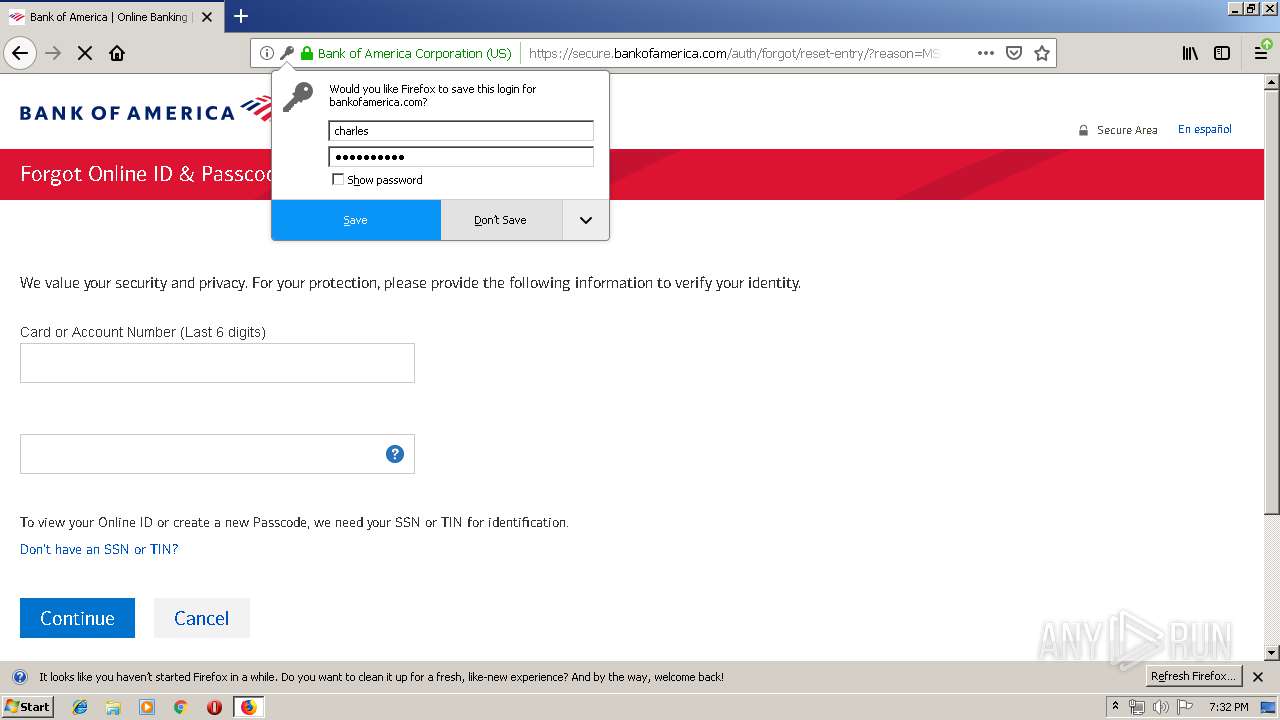
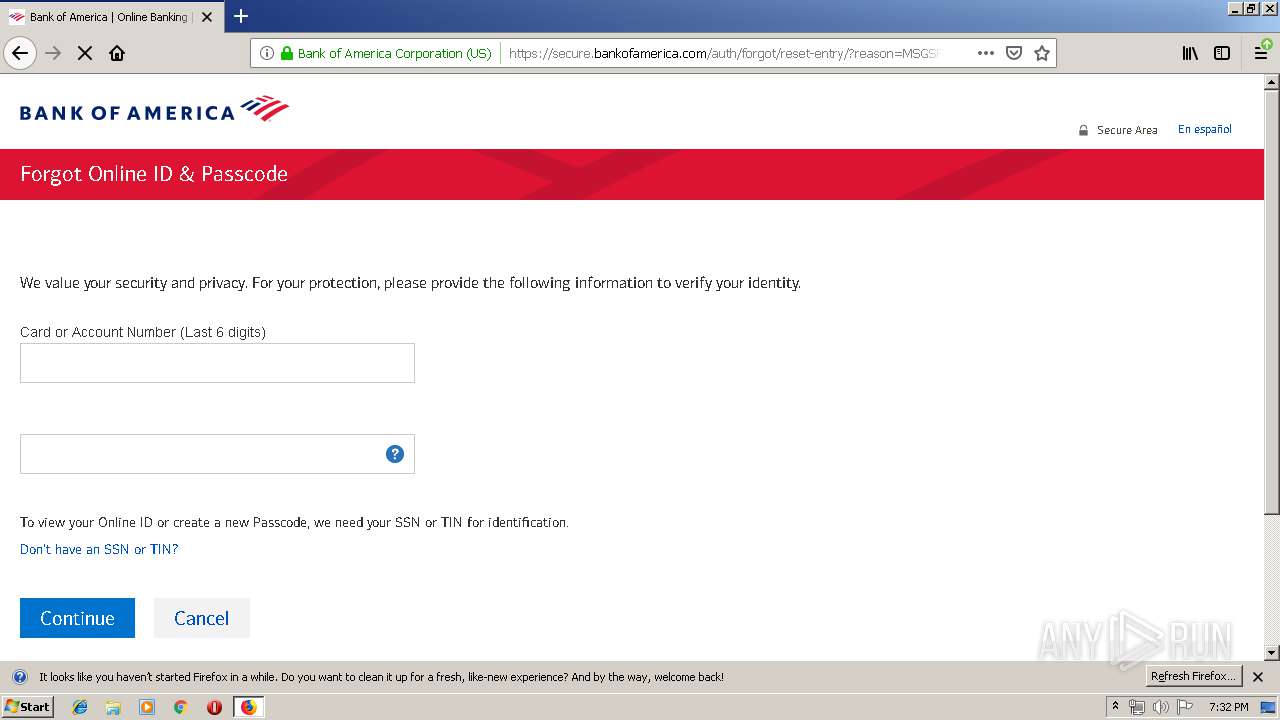
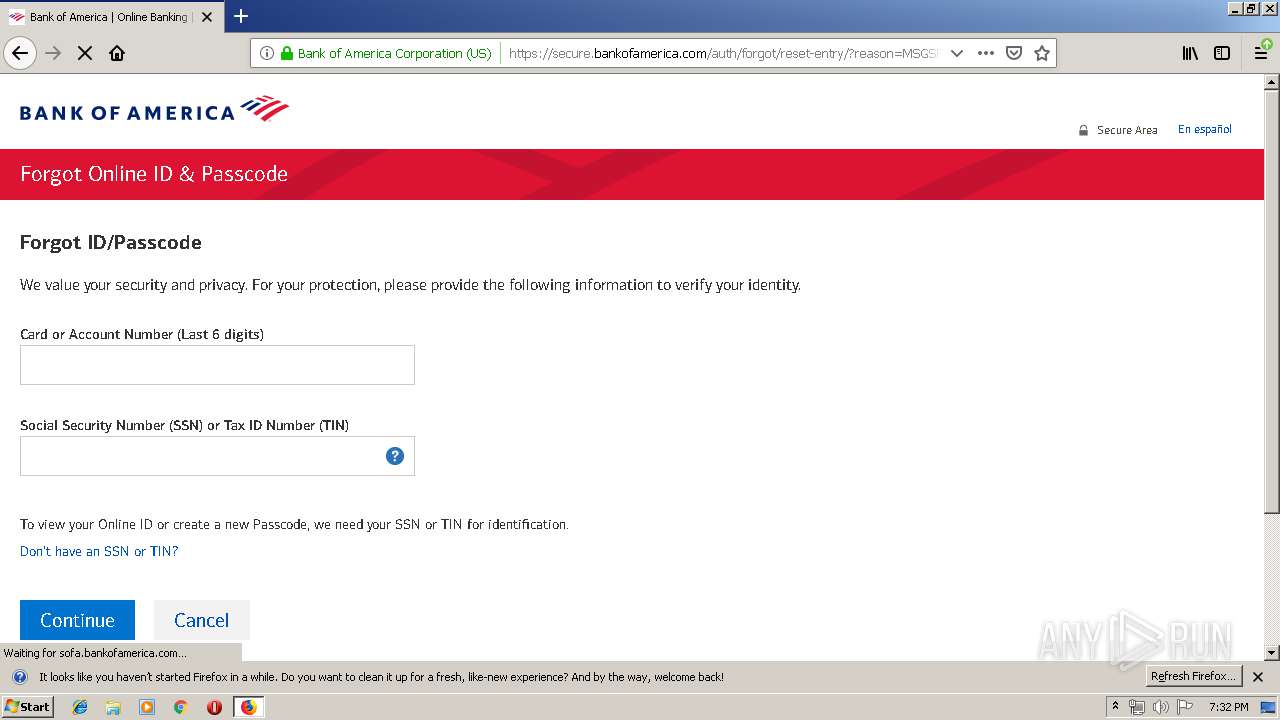
Actions looks like stealing of personal data
- svchost.exe (PID: 3772)
SUSPICIOUS
Creates files in the user directory
- notepad++.exe (PID: 2736)
- OUTLOOK.EXE (PID: 2044)
- Registros de cuenta 25-05-0019.img.exe (PID: 3324)
- svchost.exe (PID: 3772)
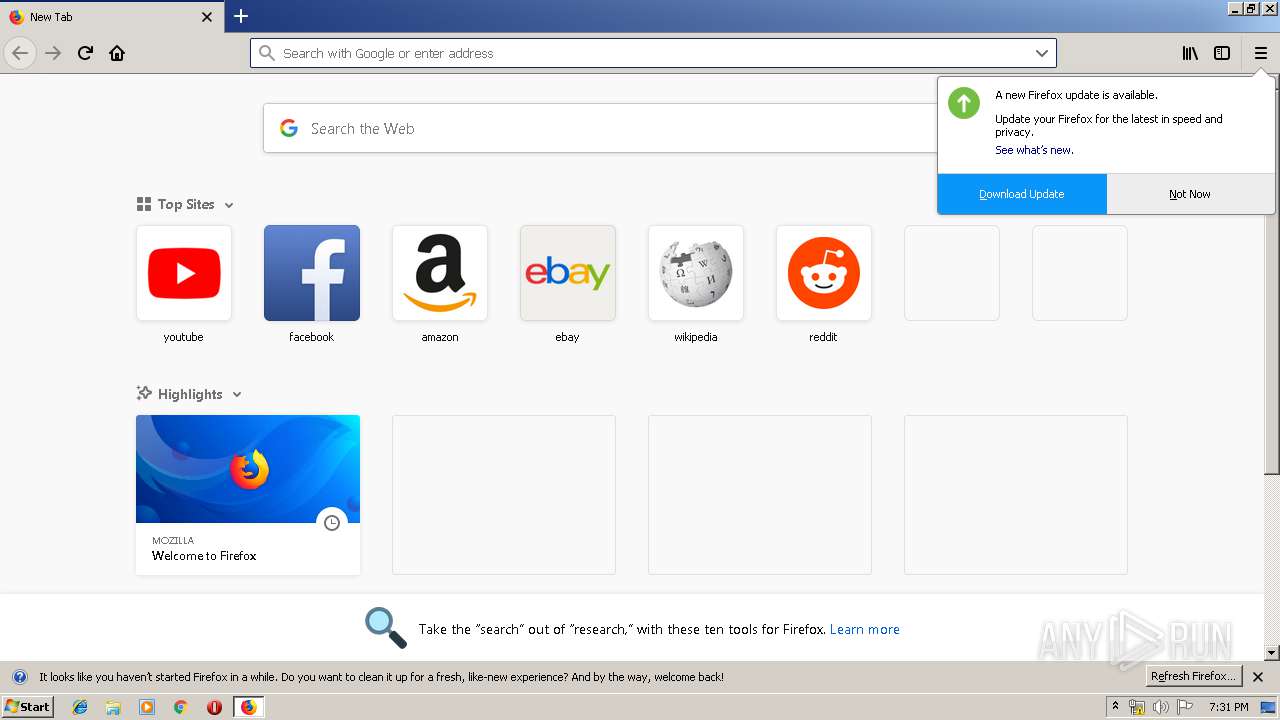
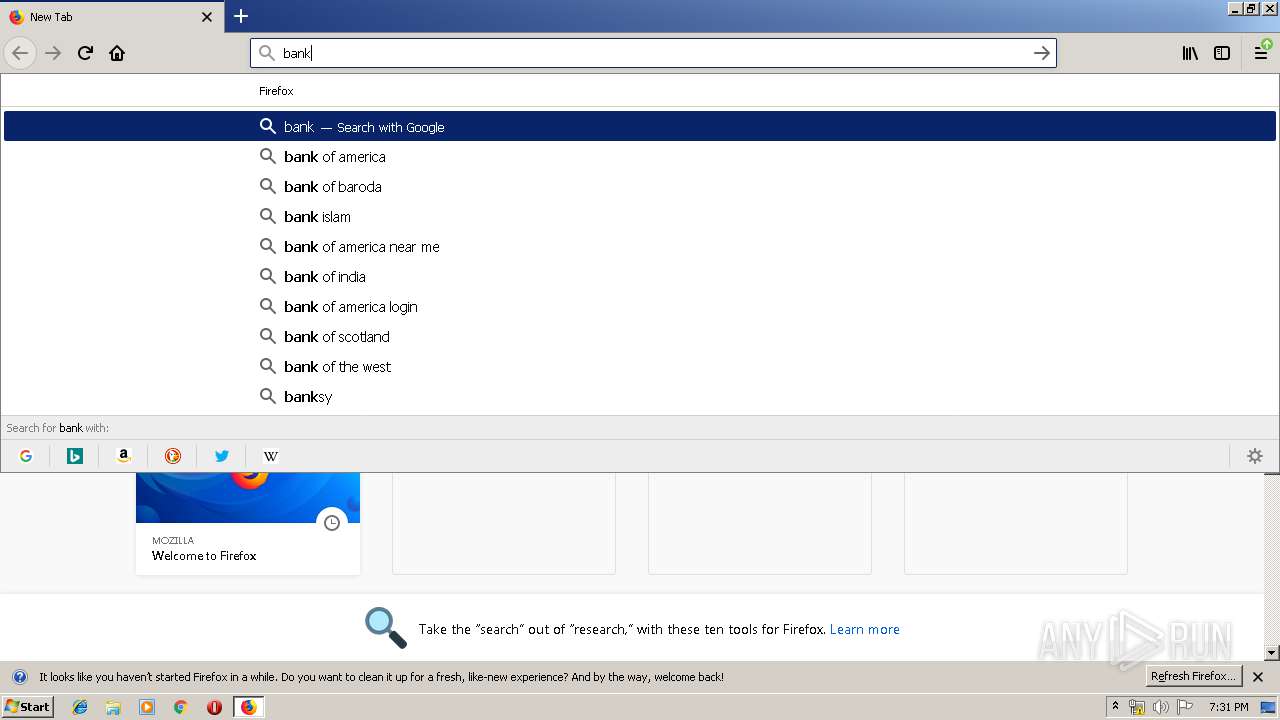
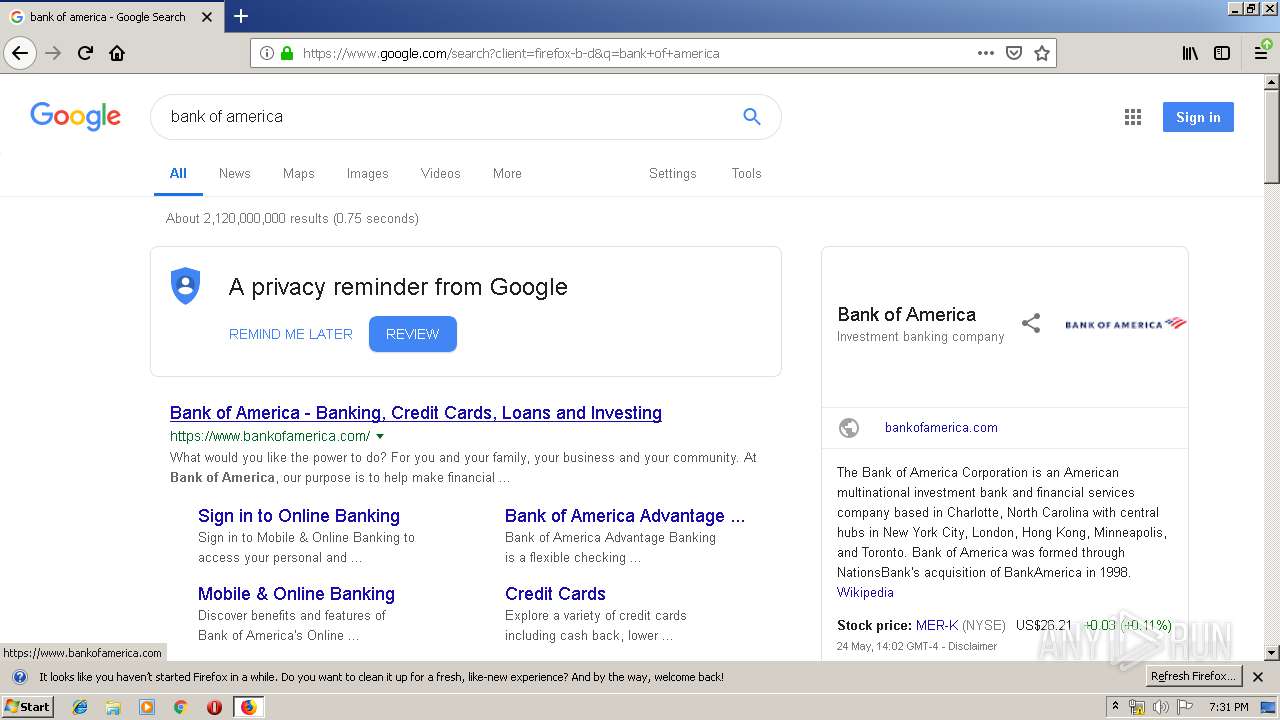
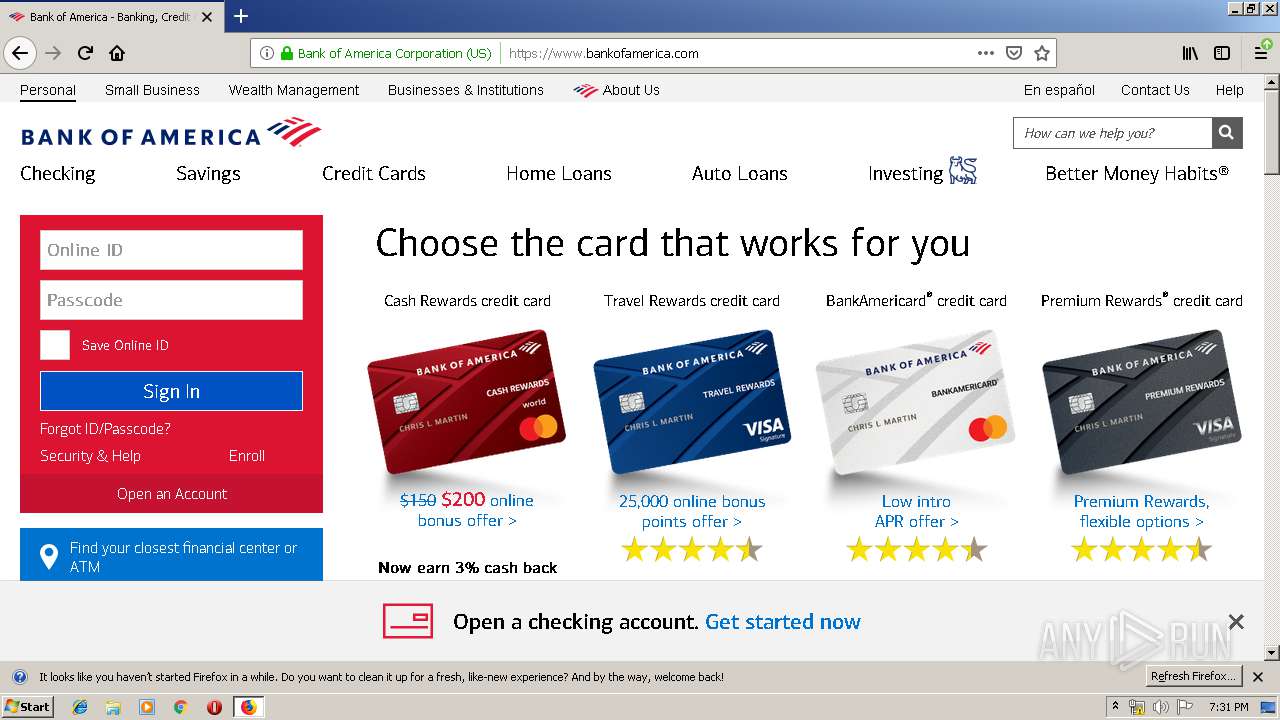
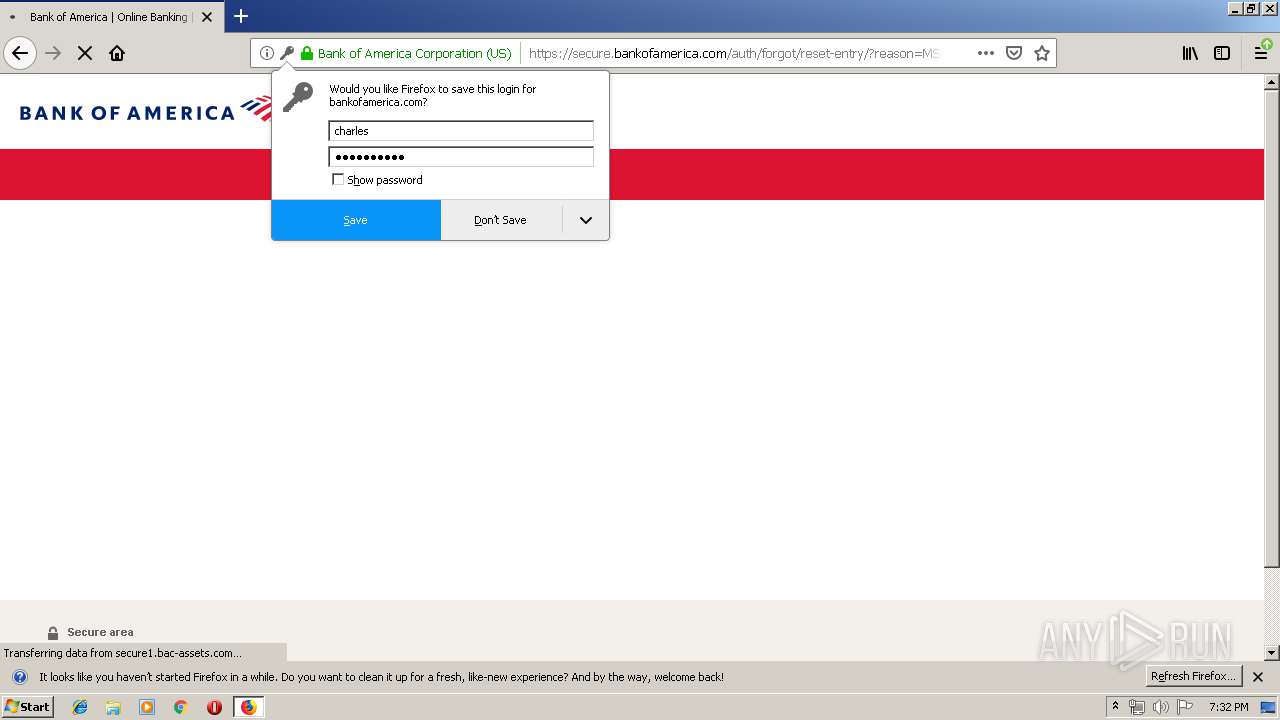
Loads DLL from Mozilla Firefox
- svchost.exe (PID: 3772)
Executable content was dropped or overwritten
- Registros de cuenta 25-05-0019.img.exe (PID: 3324)
- WinRAR.exe (PID: 2444)
- svchost.exe (PID: 3772)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2044)
Creates files in the program directory
- firefox.exe (PID: 3556)
INFO
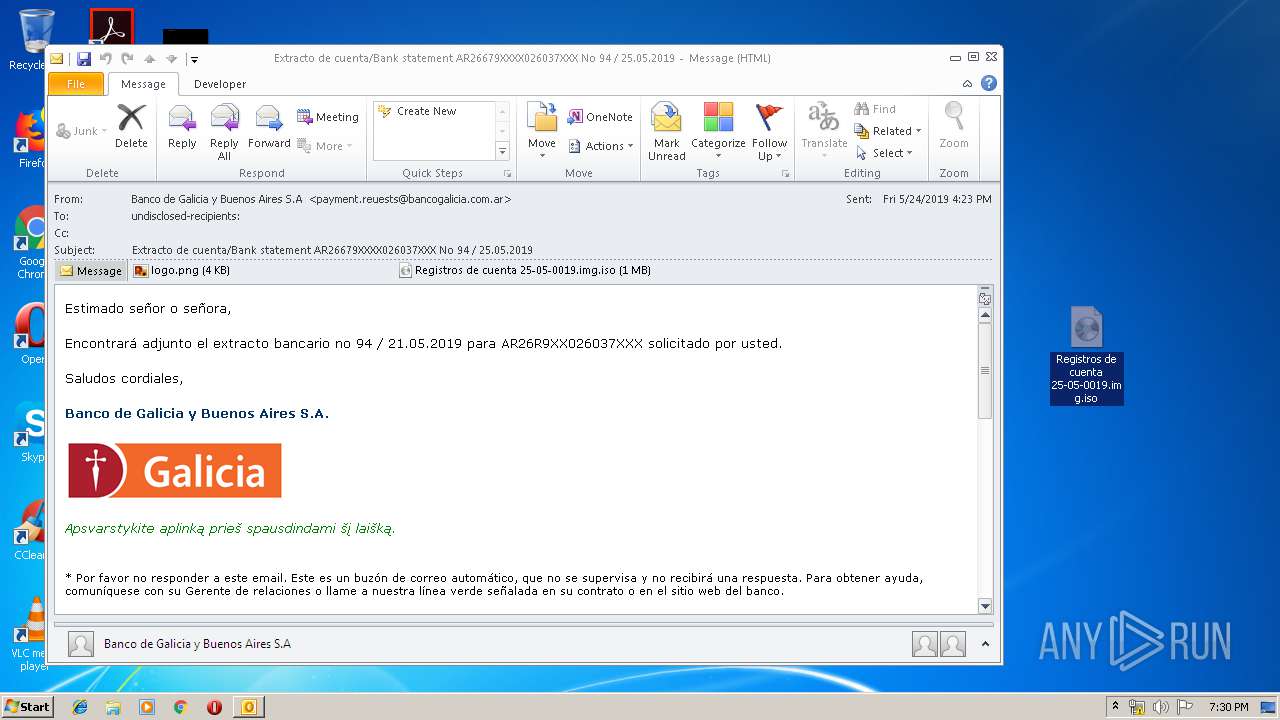
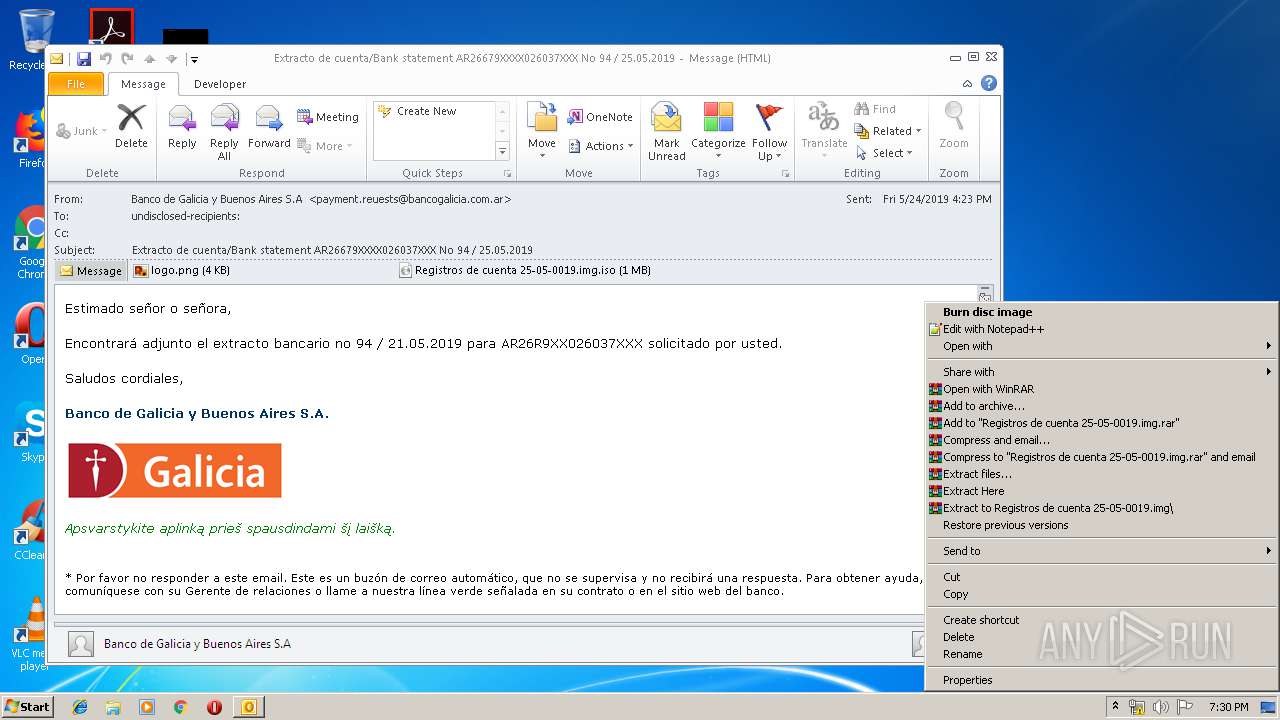
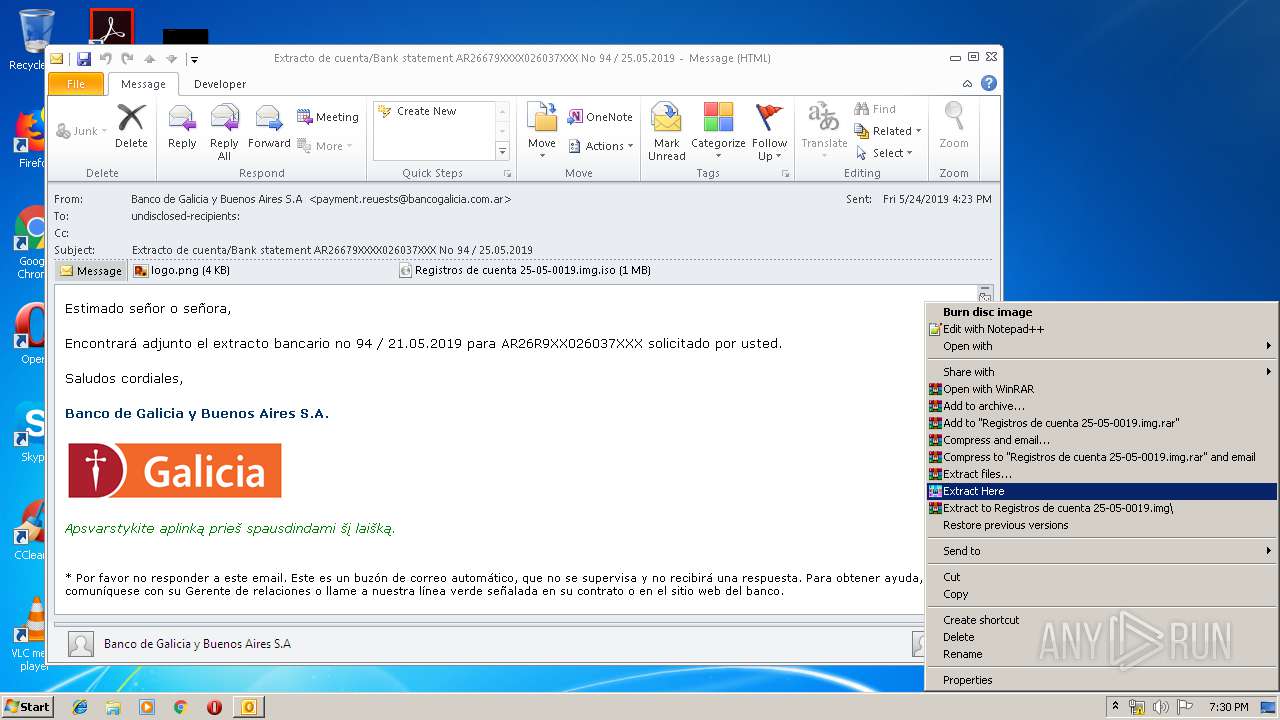
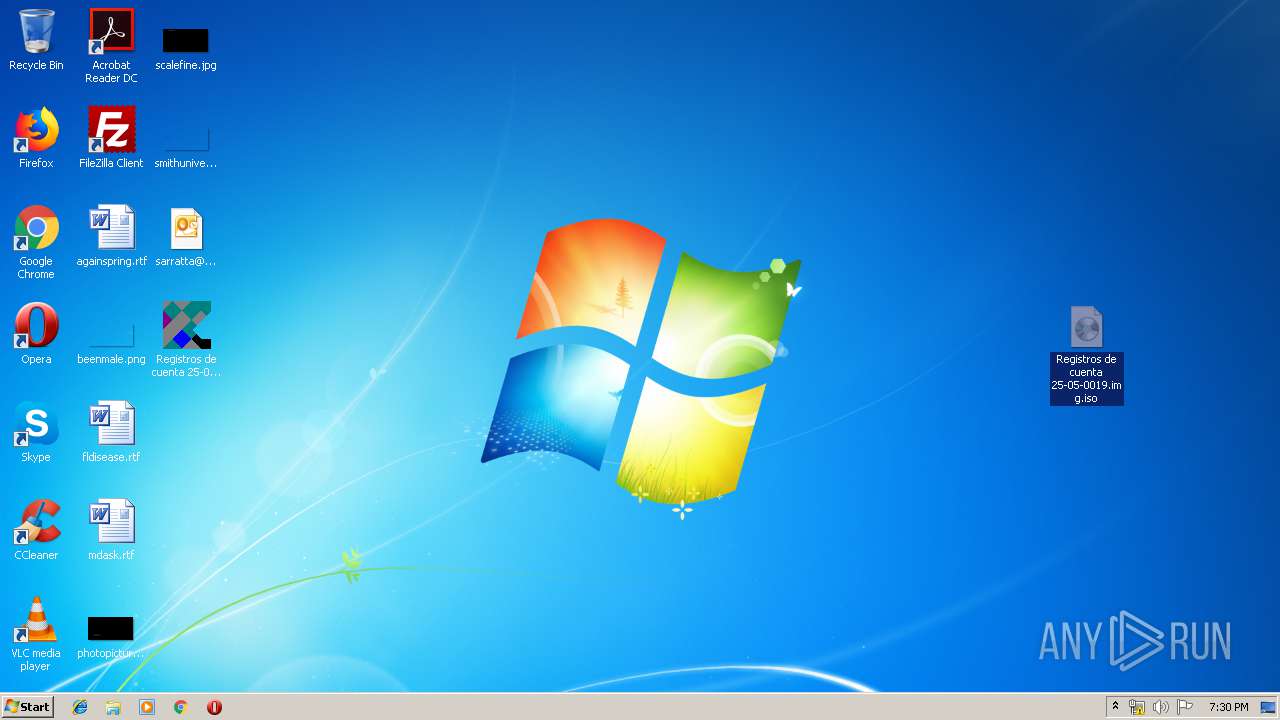
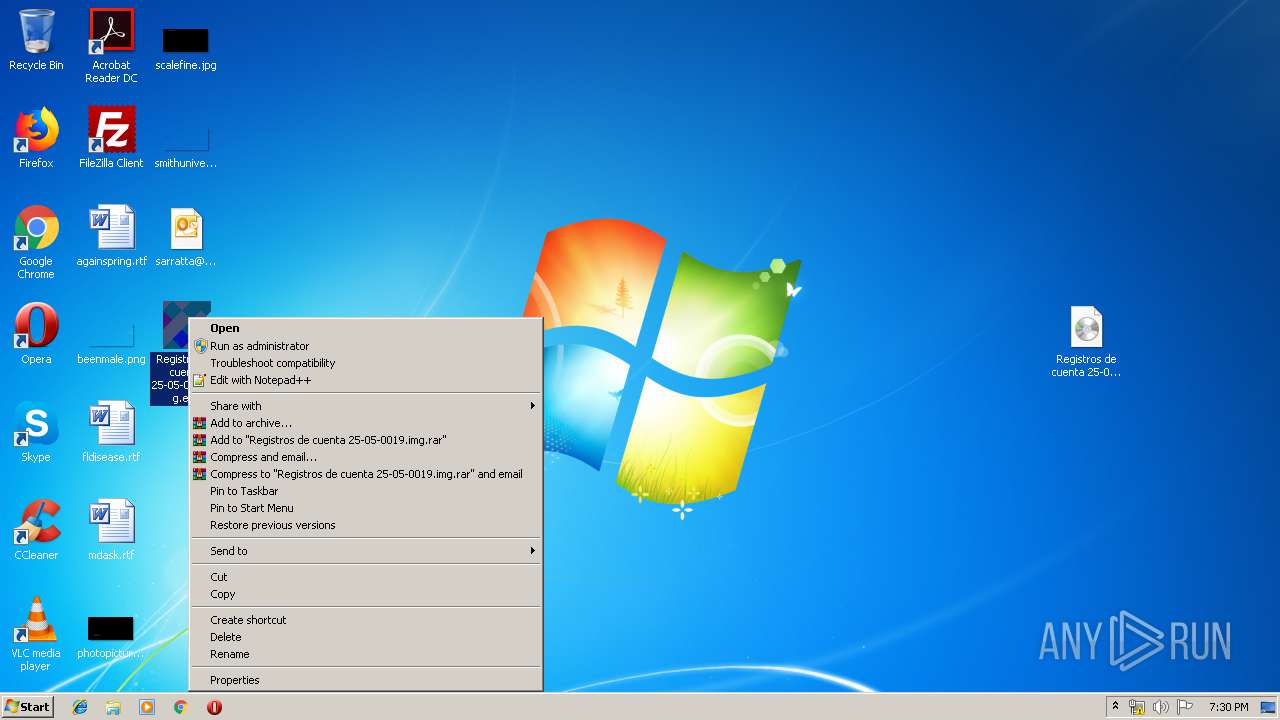
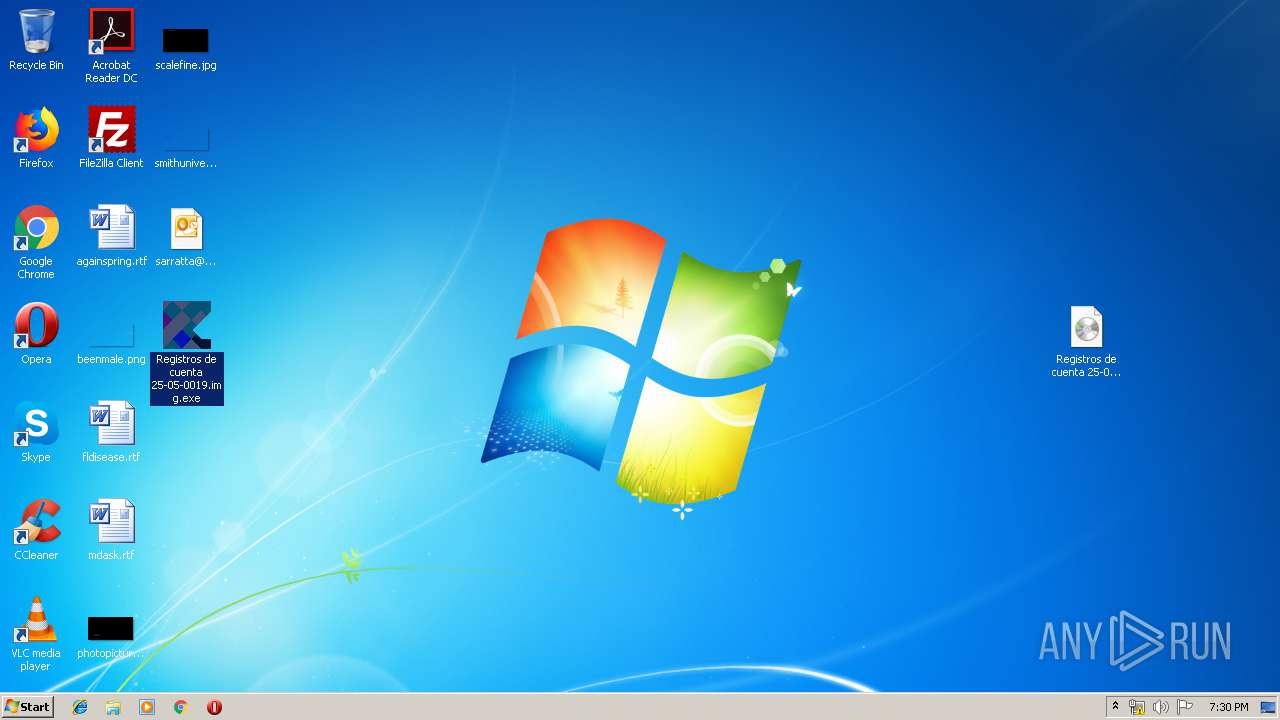
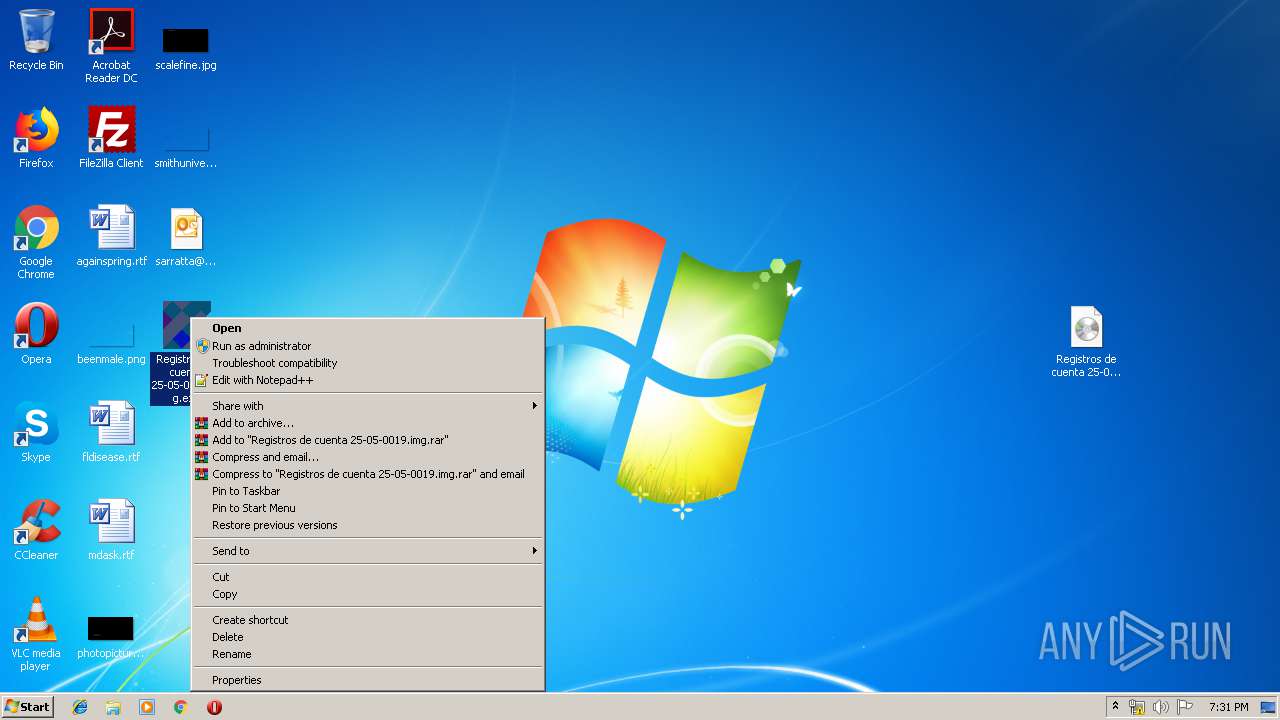
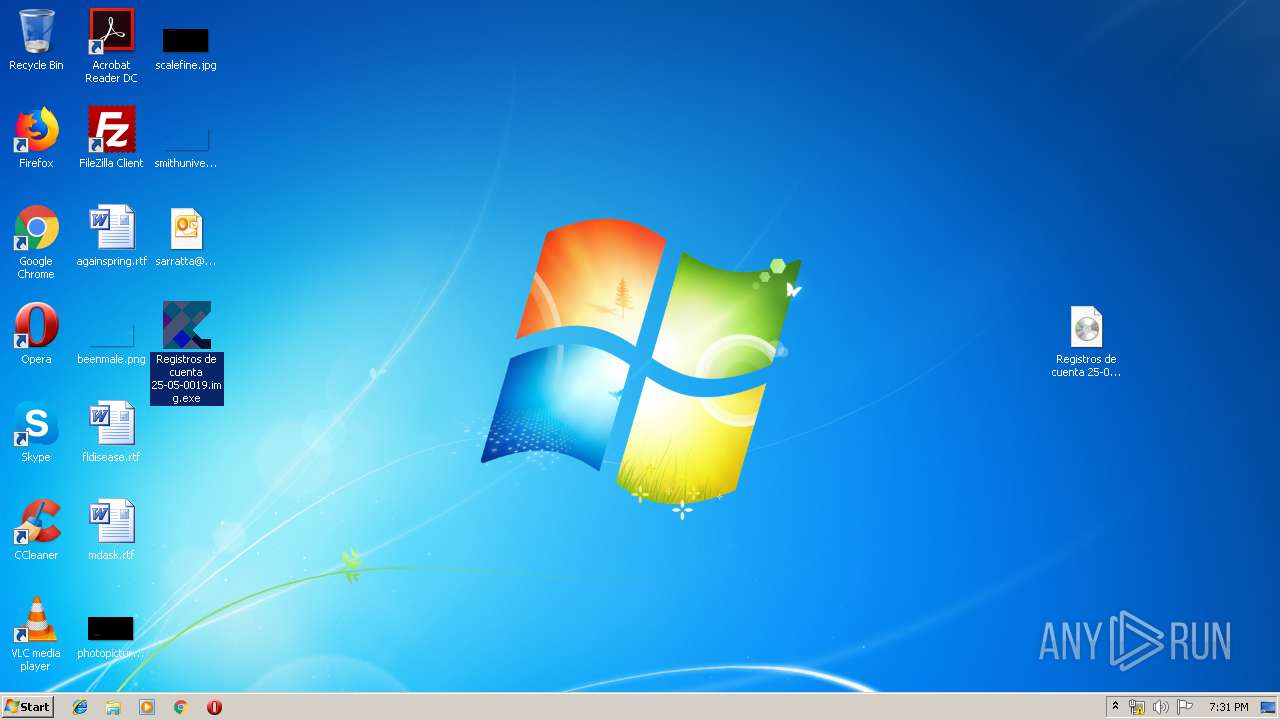
Manual execution by user
- WinRAR.exe (PID: 2444)
- notepad++.exe (PID: 2736)
- Registros de cuenta 25-05-0019.img.exe (PID: 3324)
- firefox.exe (PID: 3556)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2044)
Application launched itself
- firefox.exe (PID: 3556)
Creates files in the user directory
- firefox.exe (PID: 3556)
Reads CPU info
- firefox.exe (PID: 3556)
Writes to a desktop.ini file (may be used to cloak folders)
- firefox.exe (PID: 3252)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 5) (100) |
|---|
Total processes
50
Monitored processes
11
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1520 | "C:\Program Files\Notepad++\updater\gup.exe" -v7.51 | C:\Program Files\Notepad++\updater\gup.exe | notepad++.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: GUP : a free (LGPL) Generic Updater Exit code: 0 Version: 4.1 Modules
| |||||||||||||||
| 2044 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\Desktop\sarratta@macro.com.ar_download.eml" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 2444 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\Registros de cuenta 25-05-0019.img.iso" C:\Users\admin\Desktop\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2708 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3556.20.1128997969\1009536724" -childID 3 -isForBrowser -prefsHandle 2912 -prefMapHandle 3352 -prefsLen 5824 -prefMapSize 180950 -schedulerPrefs 0001,2 -parentBuildID 20190225143501 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3556 "\\.\pipe\gecko-crash-server-pipe.3556" 3408 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 65.0.2 Modules
| |||||||||||||||
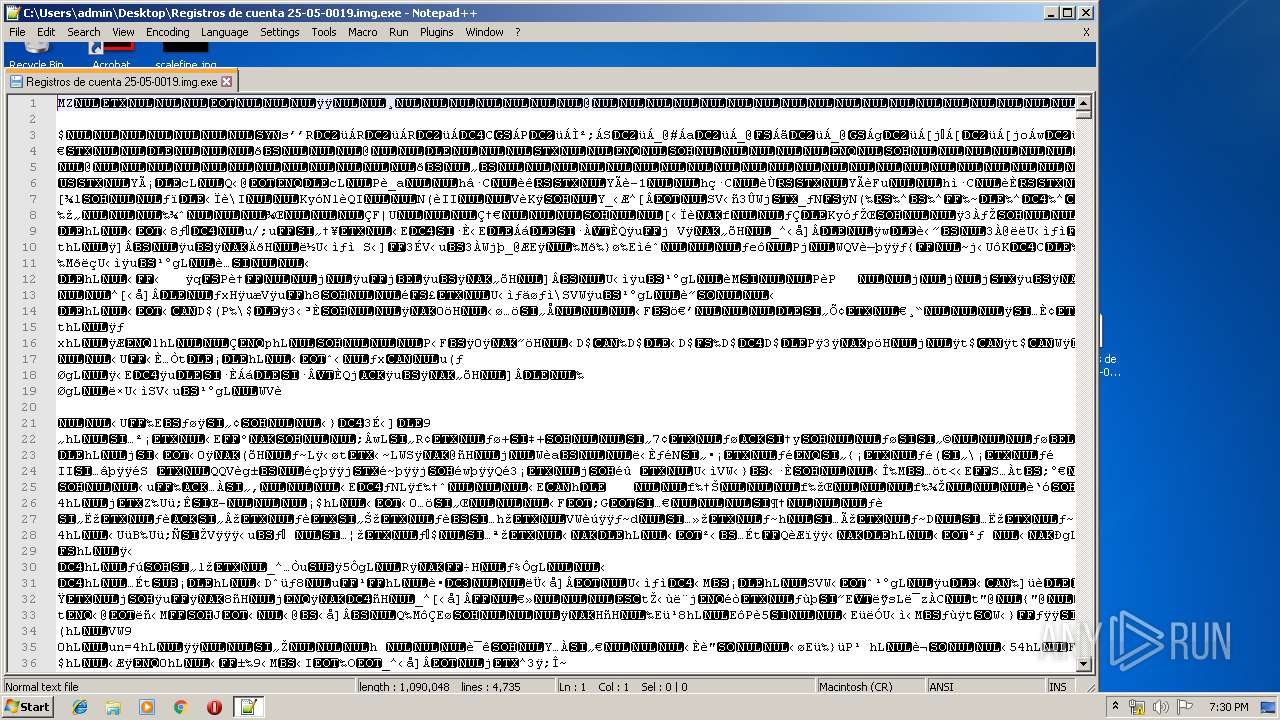
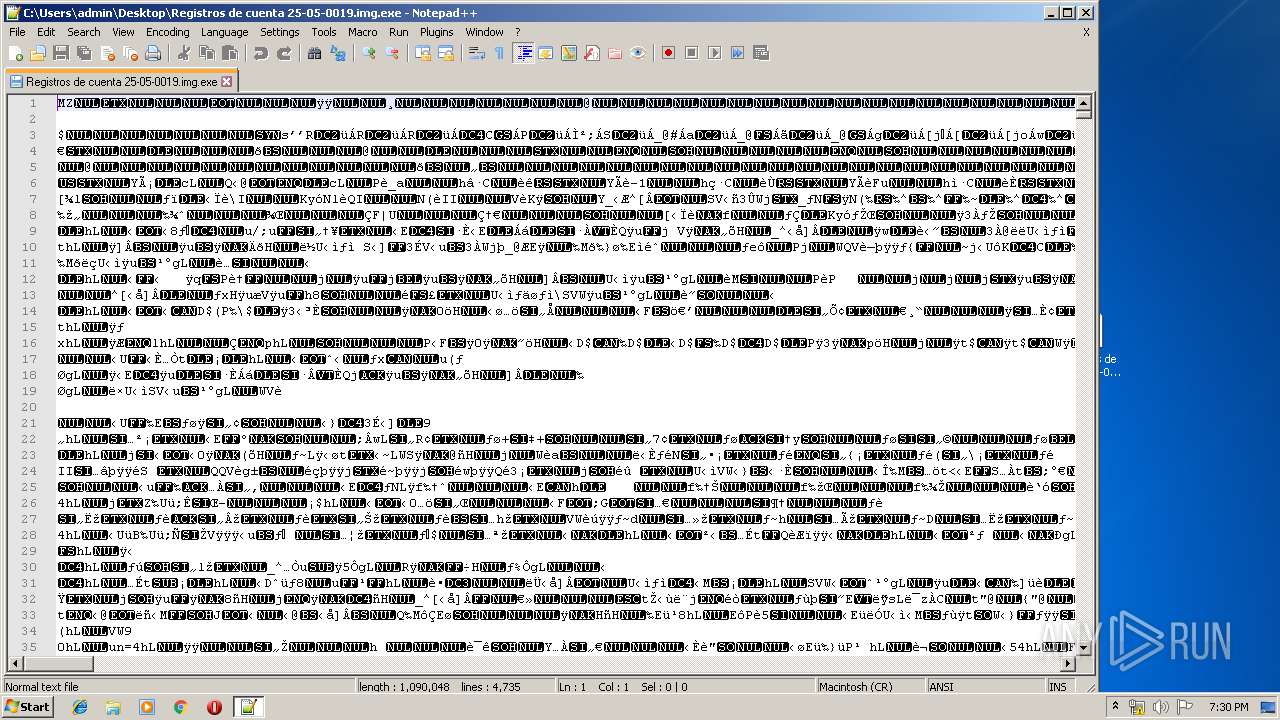
| 2736 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\Desktop\Registros de cuenta 25-05-0019.img.exe" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.51 Modules
| |||||||||||||||
| 3252 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3556.6.100955837\782001809" -childID 1 -isForBrowser -prefsHandle 1616 -prefMapHandle 1292 -prefsLen 1 -prefMapSize 180950 -schedulerPrefs 0001,2 -parentBuildID 20190225143501 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3556 "\\.\pipe\gecko-crash-server-pipe.3556" 1600 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 65.0.2 Modules
| |||||||||||||||
| 3324 | "C:\Users\admin\Desktop\Registros de cuenta 25-05-0019.img.exe" | C:\Users\admin\Desktop\Registros de cuenta 25-05-0019.img.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3556 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | explorer.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 65.0.2 Modules
| |||||||||||||||
| 3608 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3556.13.466209989\1530012926" -childID 2 -isForBrowser -prefsHandle 2476 -prefMapHandle 2124 -prefsLen 216 -prefMapSize 180950 -schedulerPrefs 0001,2 -parentBuildID 20190225143501 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3556 "\\.\pipe\gecko-crash-server-pipe.3556" 2620 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 65.0.2 Modules
| |||||||||||||||
| 3680 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3556.0.1672634293\1943459682" -parentBuildID 20190225143501 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - "C:\Users\admin\AppData\LocalLow\Mozilla\Temp-{ce348e4c-7d33-445e-89f9-60108c51bcaf}" 3556 "\\.\pipe\gecko-crash-server-pipe.3556" 1092 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 65.0.2 Modules
| |||||||||||||||
Total events
1 342
Read events
1 198
Write events
125
Delete events
19
Modification events
| (PID) Process: | (2044) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2044) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2044) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | zh< |
Value: 7A683C00FC070000010000000000000000000000 | |||
| (PID) Process: | (2044) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: FC0700003AAA09BB5E12D50100000000 | |||
| (PID) Process: | (2044) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (2044) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 220052160 | |||
| (PID) Process: | (2044) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (2044) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (2044) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (2044) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1320681493 | |||
Executable files
3
Suspicious files
209
Text files
100
Unknown types
84
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2044 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR4AB.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2044 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\tmpBF0.tmp | — | |
MD5:— | SHA256:— | |||
| 2044 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{CFC9DA24-31F2-4656-A9B0-959572213F7E}.tmp | — | |
MD5:— | SHA256:— | |||
| 2044 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DFFE6C34A7596F7EC7.TMP | — | |
MD5:— | SHA256:— | |||
| 2044 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DF440075E1F5CB8538.TMP | — | |
MD5:— | SHA256:— | |||
| 2044 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{592B3BFF-3947-4952-83E0-469BBEE63E2F}.tmp | — | |
MD5:— | SHA256:— | |||
| 2044 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2444 | WinRAR.exe | C:\Users\admin\Desktop\Registros de cuenta 25-05-0019.img.exe | executable | |
MD5:— | SHA256:— | |||
| 2044 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_AvailabilityOptions_2_42626922B85F1B40AD9E3CFCF67CFAC5.dat | xml | |
MD5:EEAA832C12F20DE6AAAA9C7B77626E72 | SHA256:C4C9A90F2C961D9EE79CF08FBEE647ED7DE0202288E876C7BAAD00F4CA29CA16 | |||
| 2044 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\~Outlook Data File - NoMail.pst.tmp | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
36
TCP/UDP connections
91
DNS requests
172
Threats
37
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2044 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
3772 | svchost.exe | POST | — | 104.27.185.208:80 | http://vbih.tk/V1/five/fre.php | US | — | — | malicious |
3556 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3556 | firefox.exe | POST | 200 | 216.58.206.3:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
3556 | firefox.exe | POST | 200 | 216.58.206.3:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
3556 | firefox.exe | POST | 200 | 216.58.206.3:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
3772 | svchost.exe | POST | — | 104.27.185.208:80 | http://vbih.tk/V1/five/fre.php | US | — | — | malicious |
— | — | GET | 200 | 2.16.186.35:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | unknown | der | 1.37 Kb | whitelisted |
3556 | firefox.exe | POST | 200 | 216.58.206.3:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
3556 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1520 | gup.exe | 37.59.28.236:443 | notepad-plus-plus.org | OVH SAS | FR | whitelisted |
— | — | 2.16.186.35:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | — | whitelisted |
3556 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3556 | firefox.exe | 95.100.39.8:80 | detectportal.firefox.com | Akamai International B.V. | DE | whitelisted |
3556 | firefox.exe | 52.85.184.36:443 | snippets.cdn.mozilla.net | Amazon.com, Inc. | US | unknown |
3556 | firefox.exe | 52.36.109.121:443 | shavar.services.mozilla.com | Amazon.com, Inc. | US | unknown |
— | — | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3556 | firefox.exe | 54.244.6.221:443 | aus5.mozilla.org | Amazon.com, Inc. | US | unknown |
3556 | firefox.exe | 172.217.22.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2044 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
notepad-plus-plus.org |
| whitelisted |
isrg.trustid.ocsp.identrust.com |
| whitelisted |
vbih.tk |
| malicious |
detectportal.firefox.com |
| whitelisted |
aus5.mozilla.org |
| whitelisted |
balrog-aus5.r53-2.services.mozilla.com |
| whitelisted |
a1089.dscd.akamai.net |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
cs9.wac.phicdn.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3772 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Loki/Pony Bot Artifact Check-in |
3772 | svchost.exe | A Network Trojan was detected | ET TROJAN LokiBot User-Agent (Charon/Inferno) |
3772 | svchost.exe | A Network Trojan was detected | ET TROJAN LokiBot Checkin |
3772 | svchost.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
3772 | svchost.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M1 |
3772 | svchost.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M2 |
3772 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Loki Bot Check-in M2 |
3772 | svchost.exe | A Network Trojan was detected | ET TROJAN LokiBot User-Agent (Charon/Inferno) |
3772 | svchost.exe | A Network Trojan was detected | ET TROJAN LokiBot Checkin |
3772 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Loki/Pony Bot Artifact Check-in |
4 ETPRO signatures available at the full report
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|