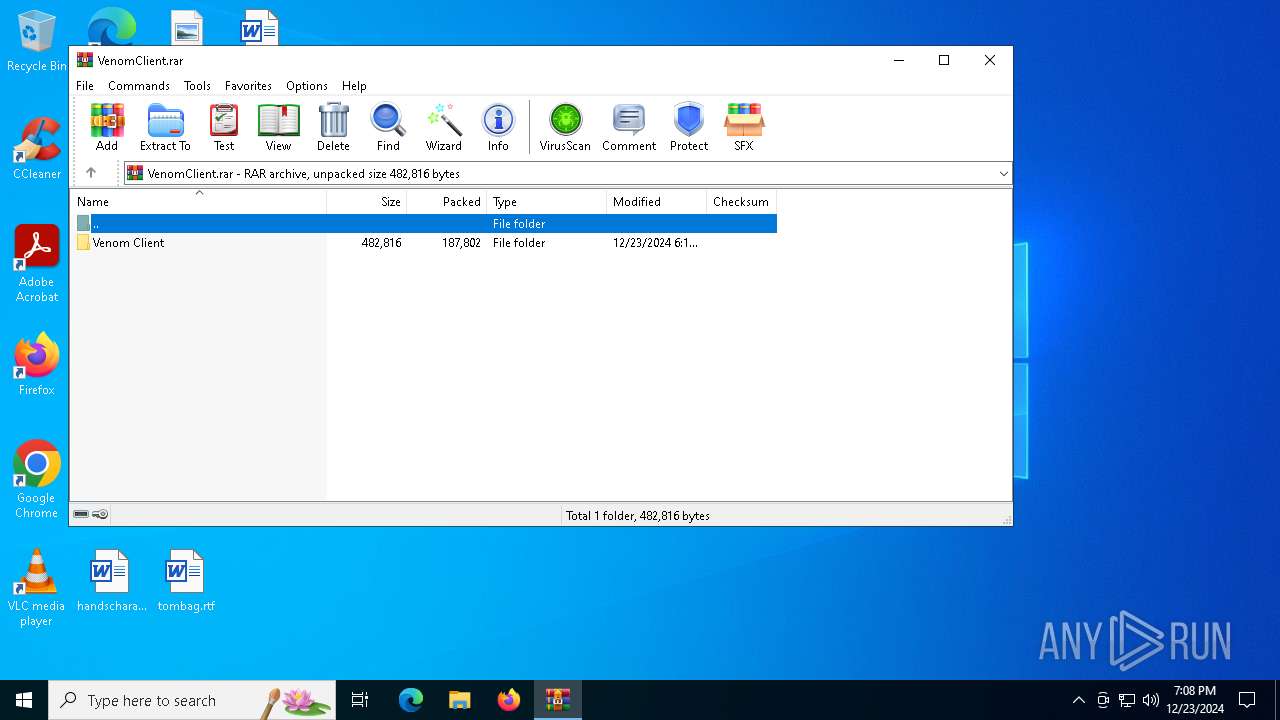
| File name: | VenomClient.rar |
| Full analysis: | https://app.any.run/tasks/d9ce54a8-ed53-4471-9e23-3d3eb48b41d8 |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | December 23, 2024, 19:08:44 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | CBC77B0E97FA86A07B627217F6F3A3BB |
| SHA1: | F8F7EE3E9E49D374CCB553FC152769AA32D3B6BA |
| SHA256: | 1C06C3A8B59C5FBE1FFA91F8BC75191FFFC8E0F0281EE4CA7899E20E3B6ABFB6 |
| SSDEEP: | 6144:X1VFii2pteawtt+ZoiKNiwF6EXAbeD6mxJlz0ADDtB9zimsj9:lbD2ua4tjr30EXARmxJlXD9ziDj9 |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 1684)
Changes the autorun value in the registry
- Venom.exe (PID: 5236)
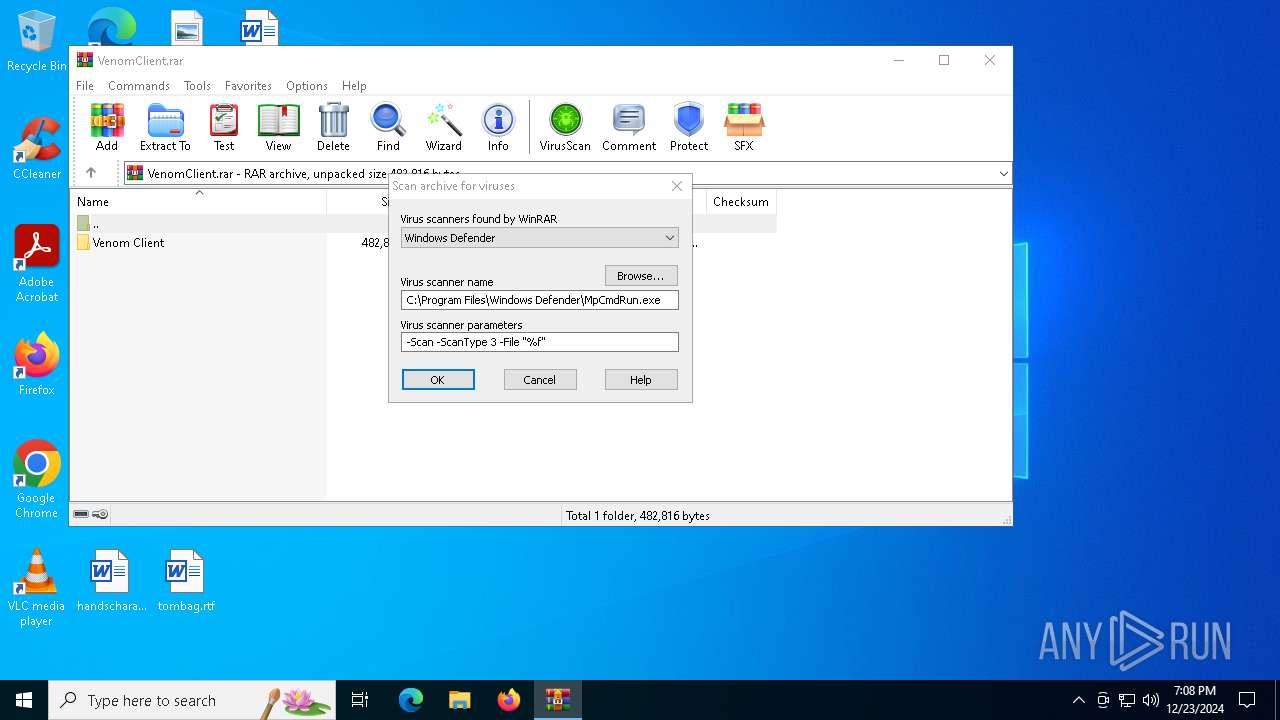
Antivirus name has been found in the command line (generic signature)
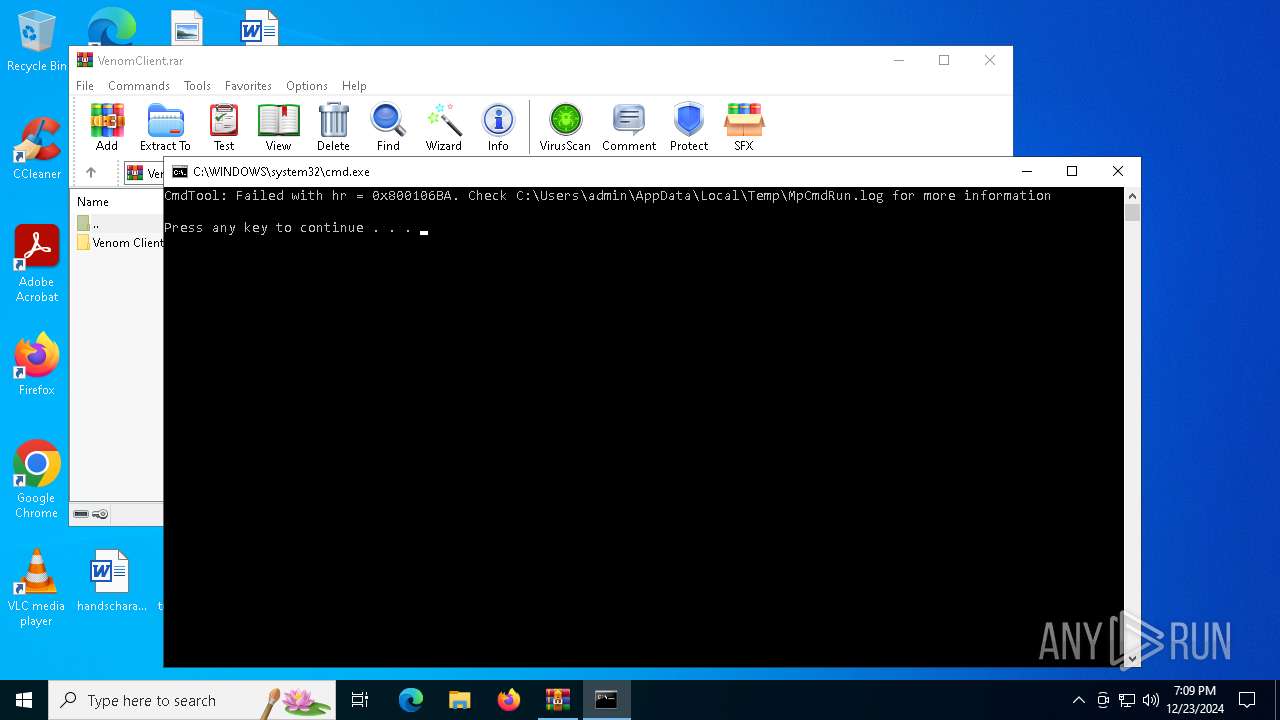
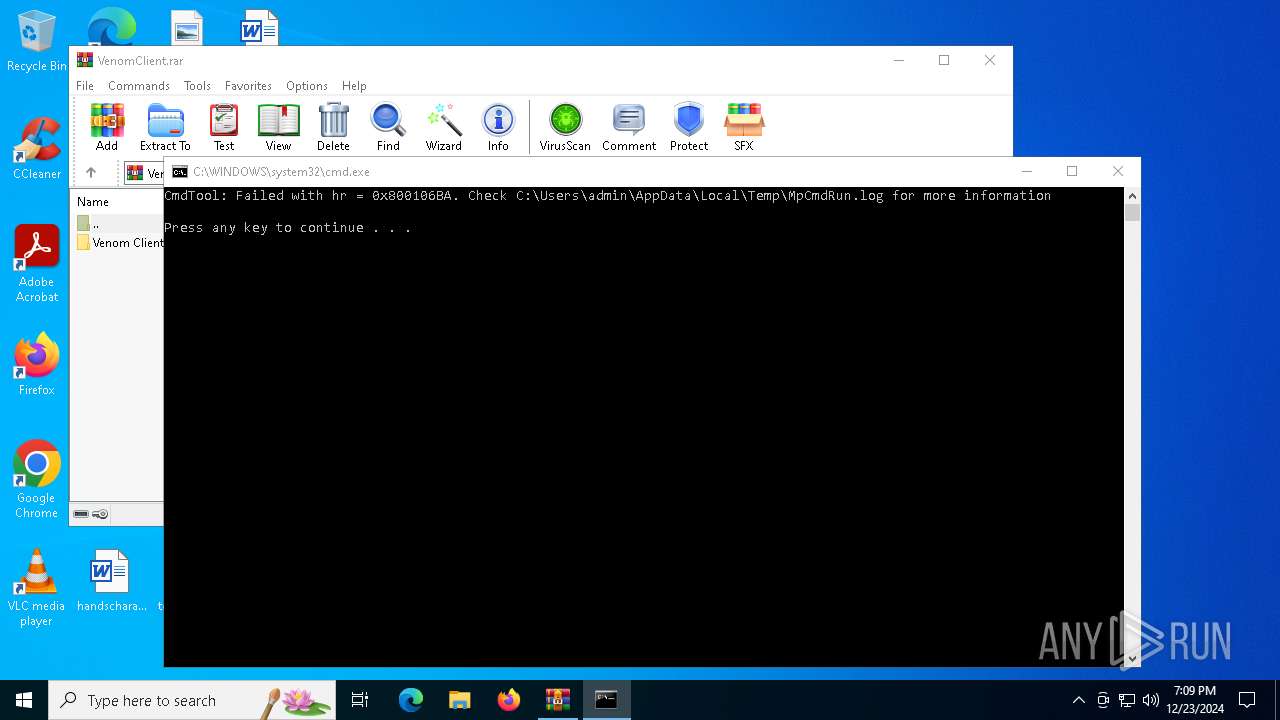
- MpCmdRun.exe (PID: 644)
- MpCmdRun.exe (PID: 828)
ASYNCRAT has been detected (YARA)
- System.exe (PID: 628)
SUSPICIOUS
Starts CMD.EXE for commands execution
- Venom.exe (PID: 5236)
- WinRAR.exe (PID: 1684)
The process creates files with name similar to system file names
- Venom.exe (PID: 5236)
Executable content was dropped or overwritten
- Venom.exe (PID: 5236)
Executing commands from a ".bat" file
- Venom.exe (PID: 5236)
- WinRAR.exe (PID: 1684)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 396)
The executable file from the user directory is run by the CMD process
- System.exe (PID: 628)
Potential Corporate Privacy Violation
- System.exe (PID: 628)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 1684)
Connects to unusual port
- System.exe (PID: 628)
INFO
Reads the computer name
- Venom.exe (PID: 5236)
- System.exe (PID: 628)
- MpCmdRun.exe (PID: 644)
- MpCmdRun.exe (PID: 828)
Checks supported languages
- Venom.exe (PID: 5236)
- System.exe (PID: 628)
- MpCmdRun.exe (PID: 644)
Creates files or folders in the user directory
- Venom.exe (PID: 5236)
Manual execution by a user
- Venom.exe (PID: 5236)
Reads the machine GUID from the registry
- Venom.exe (PID: 5236)
- System.exe (PID: 628)
Reads Environment values
- Venom.exe (PID: 5236)
- System.exe (PID: 628)
Create files in a temporary directory
- Venom.exe (PID: 5236)
- MpCmdRun.exe (PID: 644)
The sample compiled with english language support
- WinRAR.exe (PID: 1684)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1684)
Checks proxy server information
- System.exe (PID: 628)
Reads the software policy settings
- System.exe (PID: 628)
The process uses the downloaded file
- WinRAR.exe (PID: 1684)
Disables trace logs
- System.exe (PID: 628)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AsyncRat
(PID) Process(628) System.exe
C2 (1)null
Ports (1)null
VersionVenom RAT + HVNC + Stealer + Grabber v6.0.3
Options
AutoRuntrue
Mutexwgzvrzpksxgiaglrvq
InstallFolder%AppData%
Certificates
Cert1MIICMjCCAZugAwIBAgIVAKoqmxgwS+6fIGQh+gn8AWTY4iRbMA0GCSqGSIb3DQEBDQUAMGMxETAPBgNVBAMMCFp1bGEgR2VuMRMwEQYDVQQLDApxd3FkYW5jaHVuMR8wHQYDVQQKDBZWZW5vbVJBVCBCeSBxd3FkYW5jaHVuMQswCQYDVQQHDAJTSDELMAkGA1UEBhMCQ04wHhcNMjQwMzEzMTQ1NzI3WhcNMzQxMjIxMTQ1NzI3WjATMREwDwYDVQQDDAhWZW5vbVJBVDCBnzANBgkqhkiG9w0BAQEFAAOB...
Server_Signaturek1fD5pnRMORwkEDXHjWMaWL09XKIkruJCM2l8myiRrGg6aGF8OTd2uZvsVgbdeSKzW2I2Qgjj3lz6W7LQEDllHJ+CK9YfTfU7Y21c9JRREQuGEuEvfLEjLs6isSF3bGvxqmvZqrFL3khVEuCeDwd4KcjNSq4Fg/iYjDhyIg7OHQ=
Keys
AES5c251632e3f0c3fe4b788fbfe50bfd26dade1271817ff66e9cc9a29eaef78308
SaltVenomRATByVenom
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 81970 |
| UncompressedSize: | 244736 |
| OperatingSystem: | Win32 |
| ArchivedFileName: | Venom Client/freeglut.dll |
Total processes
129
Monitored processes
13
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 396 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\tmp6A27.tmp.bat"" | C:\Windows\System32\cmd.exe | — | Venom.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 628 | "C:\Users\admin\AppData\Roaming\System.exe" | C:\Users\admin\AppData\Roaming\System.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Version: 6.0.1 Modules
AsyncRat(PID) Process(628) System.exe C2 (1)null Ports (1)null VersionVenom RAT + HVNC + Stealer + Grabber v6.0.3 Options AutoRuntrue Mutexwgzvrzpksxgiaglrvq InstallFolder%AppData% Certificates Cert1MIICMjCCAZugAwIBAgIVAKoqmxgwS+6fIGQh+gn8AWTY4iRbMA0GCSqGSIb3DQEBDQUAMGMxETAPBgNVBAMMCFp1bGEgR2VuMRMwEQYDVQQLDApxd3FkYW5jaHVuMR8wHQYDVQQKDBZWZW5vbVJBVCBCeSBxd3FkYW5jaHVuMQswCQYDVQQHDAJTSDELMAkGA1UEBhMCQ04wHhcNMjQwMzEzMTQ1NzI3WhcNMzQxMjIxMTQ1NzI3WjATMREwDwYDVQQDDAhWZW5vbVJBVDCBnzANBgkqhkiG9w0BAQEFAAOB... Server_Signaturek1fD5pnRMORwkEDXHjWMaWL09XKIkruJCM2l8myiRrGg6aGF8OTd2uZvsVgbdeSKzW2I2Qgjj3lz6W7LQEDllHJ+CK9YfTfU7Y21c9JRREQuGEuEvfLEjLs6isSF3bGvxqmvZqrFL3khVEuCeDwd4KcjNSq4Fg/iYjDhyIg7OHQ= Keys AES5c251632e3f0c3fe4b788fbfe50bfd26dade1271817ff66e9cc9a29eaef78308 SaltVenomRATByVenom | |||||||||||||||
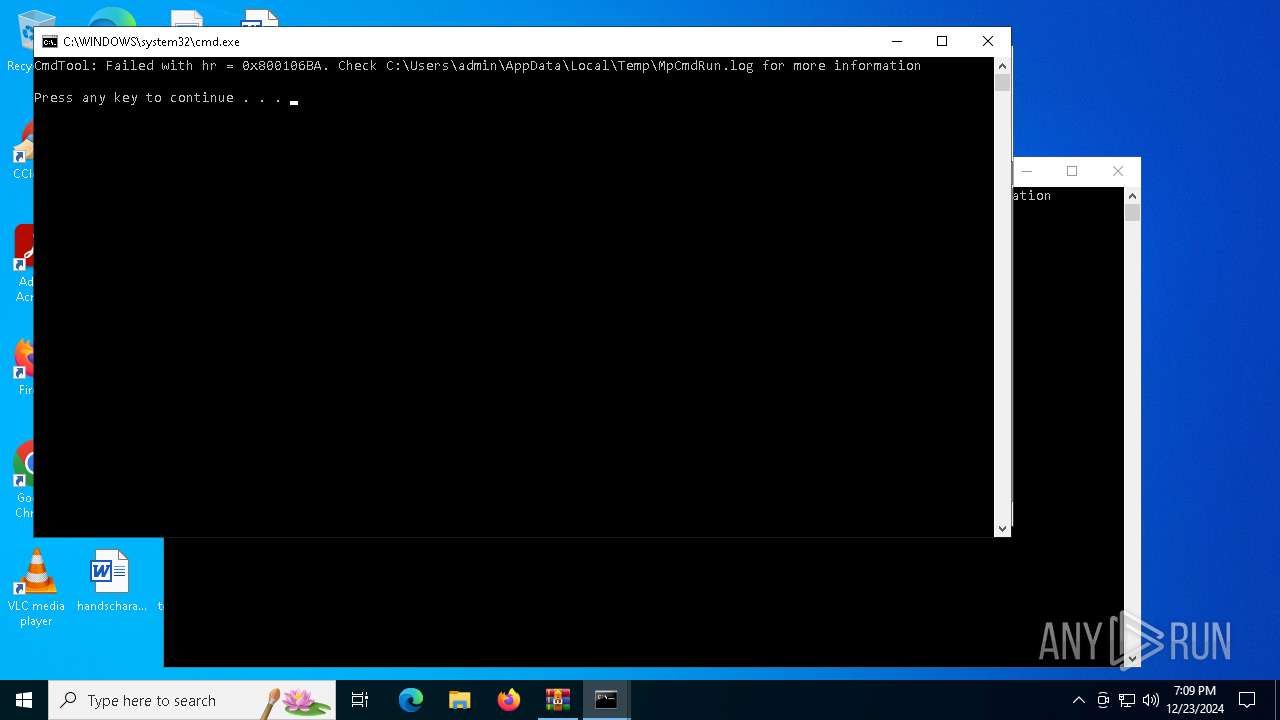
| 644 | "C:\Program Files\Windows Defender\MpCmdRun.exe" -Scan -ScanType 3 -File "C:\Users\admin\AppData\Local\Temp\Rar$VR1684.24936" | C:\Program Files\Windows Defender\MpCmdRun.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Malware Protection Command Line Utility Exit code: 2 Version: 4.18.1909.6 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 736 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 828 | "C:\Program Files\Windows Defender\MpCmdRun.exe" -Scan -ScanType 3 -File "C:\Users\admin\AppData\Local\Temp\Rar$VR1684.27707" | C:\Program Files\Windows Defender\MpCmdRun.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Malware Protection Command Line Utility Exit code: 2 Version: 4.18.1909.6 (WinBuild.160101.0800) Modules
| |||||||||||||||
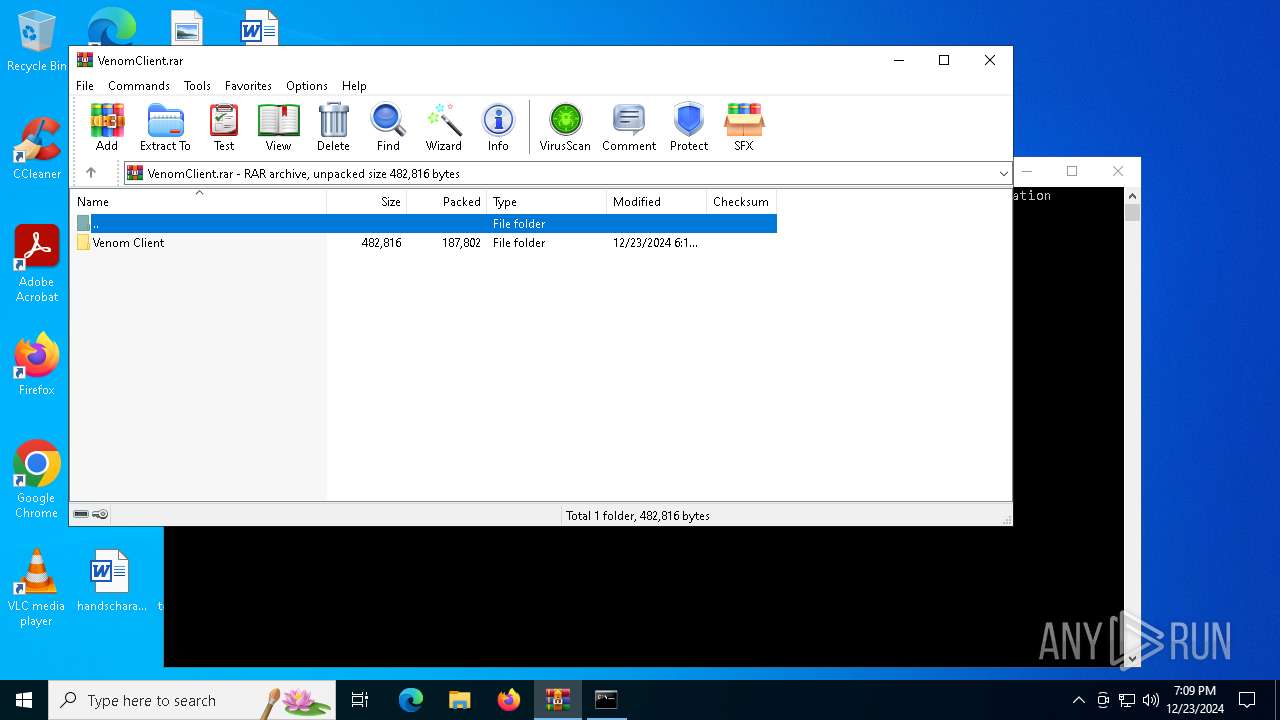
| 1684 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\VenomClient.rar | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4668 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\Rar$VR1684.27707\Rar$Scan36208.bat" " | C:\Windows\System32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4840 | timeout 3 | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4872 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
5 570
Read events
5 545
Write events
25
Delete events
0
Modification events
| (PID) Process: | (1684) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (1684) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (1684) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (1684) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\VenomClient.rar | |||
| (PID) Process: | (1684) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1684) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1684) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1684) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (5236) Venom.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | System |
Value: "C:\Users\admin\AppData\Roaming\System.exe" | |||
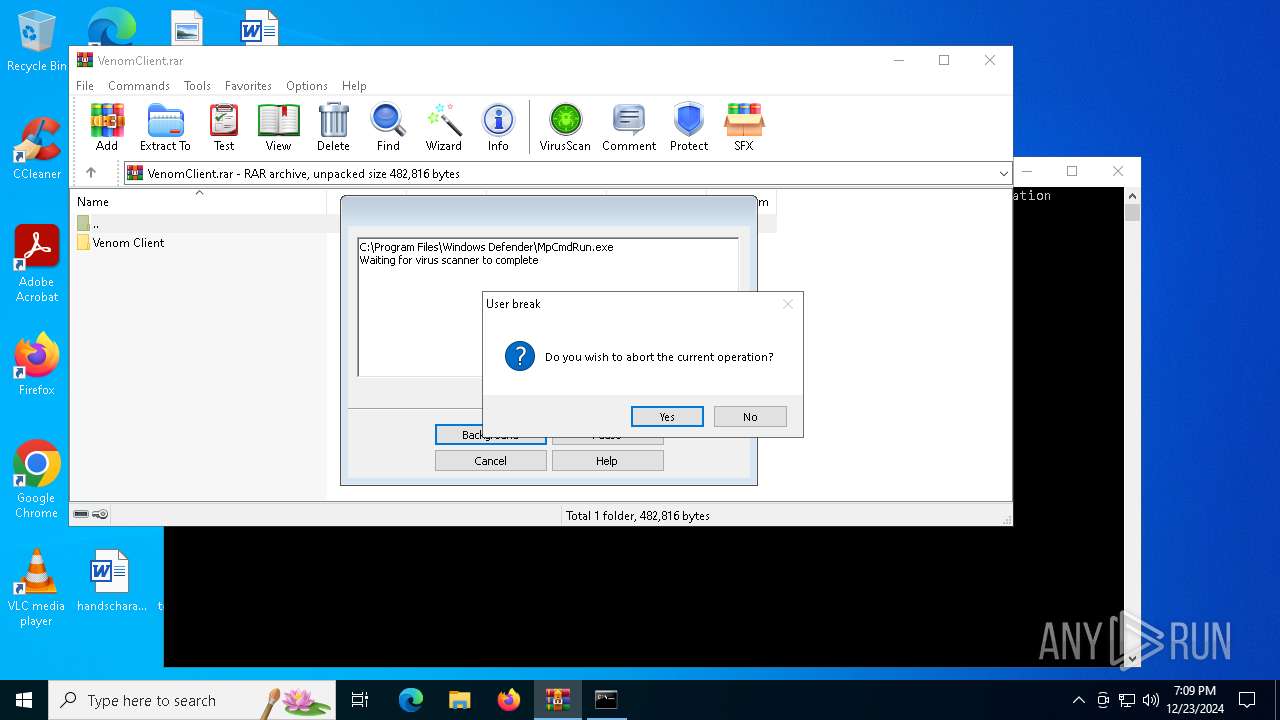
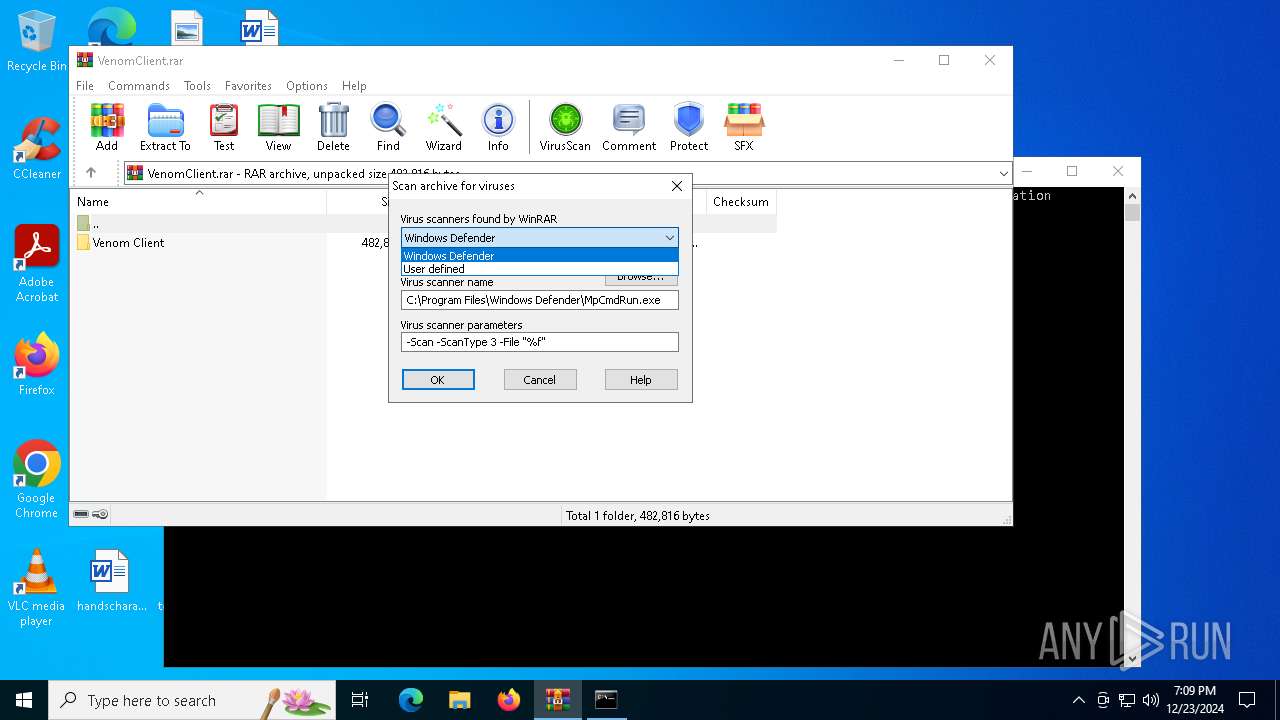
| (PID) Process: | (1684) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\VirusScan |
| Operation: | write | Name: | DefScanner |
Value: Windows Defender | |||
Executable files
7
Suspicious files
0
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5236 | Venom.exe | C:\Users\admin\AppData\Local\Temp\tmp6A27.tmp.bat | text | |
MD5:35B7C2803574BFBD692128308071B6E2 | SHA256:46F3040668030037200E5DE239BD83C6D6CFAE3EC362A430F0228DE3731CEBC2 | |||
| 1684 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR1684.24936\VenomClient.rar\Venom Client\venomsba.dll | executable | |
MD5:51C3D268363828433F676CF8736DD980 | SHA256:6EADFC38C75BC9AE115937AC11551B1008D8705E44D9E07782D01457CFA3ED7E | |||
| 1684 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR1684.24936\VenomClient.rar\Venom Client\Venom.exe | executable | |
MD5:C745590F5B7590F217BB204D27E91A00 | SHA256:DFB98932671339FB633C74180DBA3810D9382E56618D75B3F67AE2BA3206AA1D | |||
| 1684 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR1684.24936\VenomClient.rar\Venom Client\freeglut.dll | executable | |
MD5:8FC8AC1CA784EA5CD3E22A1237F577D7 | SHA256:C4E38871E266CAFC2FD5B27E898AEBA1B5BEEB3F872DD0022266C7CF8273CE3F | |||
| 5236 | Venom.exe | C:\Users\admin\AppData\Roaming\System.exe | executable | |
MD5:C745590F5B7590F217BB204D27E91A00 | SHA256:DFB98932671339FB633C74180DBA3810D9382E56618D75B3F67AE2BA3206AA1D | |||
| 1684 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR1684.27707\VenomClient.rar\Venom Client\Venom.exe | executable | |
MD5:C745590F5B7590F217BB204D27E91A00 | SHA256:DFB98932671339FB633C74180DBA3810D9382E56618D75B3F67AE2BA3206AA1D | |||
| 5236 | Venom.exe | C:\Users\admin\AppData\Roaming\MyData\DataLogs.conf | text | |
MD5:CF759E4C5F14FE3EEC41B87ED756CEA8 | SHA256:C9F9F193409217F73CC976AD078C6F8BF65D3AABCF5FAD3E5A47536D47AA6761 | |||
| 1684 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR1684.24936\Rar$Scan8516.bat | text | |
MD5:E166996FF720505DEB258386872A98DE | SHA256:82BAE5466A33A8A20B5C44BE262D85B787485DEEBA15963A4E31D5BB0CB843C9 | |||
| 644 | MpCmdRun.exe | C:\Users\admin\AppData\Local\Temp\MpCmdRun.log | text | |
MD5:3F7AA1F202D9E994B7B2BA4C76B39D7E | SHA256:DD3F8D1E6D8E89A856E3FDD2A68F9CF93BE082FEAD1A6B4056D7B0EE21D95533 | |||
| 1684 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR1684.27707\VenomClient.rar\Venom Client\freeglut.dll | executable | |
MD5:8FC8AC1CA784EA5CD3E22A1237F577D7 | SHA256:C4E38871E266CAFC2FD5B27E898AEBA1B5BEEB3F872DD0022266C7CF8273CE3F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
44
TCP/UDP connections
59
DNS requests
10
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
880 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 188.114.97.3:443 | https://paste.ee/r/Wp7LQ/0 | unknown | — | — | unknown |
— | — | GET | 200 | 188.114.96.3:443 | https://paste.ee/r/Wp7LQ/0 | unknown | — | — | unknown |
— | — | GET | 200 | 188.114.97.3:443 | https://paste.ee/r/Wp7LQ/0 | unknown | — | — | unknown |
— | — | GET | 200 | 188.114.96.3:443 | https://paste.ee/r/Wp7LQ/0 | unknown | — | — | unknown |
— | — | GET | 200 | 188.114.97.3:443 | https://paste.ee/r/Wp7LQ/0 | unknown | — | — | unknown |
— | — | GET | 200 | 188.114.97.3:443 | https://paste.ee/r/Wp7LQ/0 | unknown | — | — | unknown |
— | — | GET | 200 | 188.114.96.3:443 | https://paste.ee/r/Wp7LQ/0 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
880 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.23.209.135:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
880 | svchost.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
paste.ee |
| shared |
w9o13qj.localto.net |
| malicious |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Misc activity | ET INFO Pastebin-like Service Domain in DNS Lookup (paste .ee) |
628 | System.exe | Potential Corporate Privacy Violation | ET POLICY Pastebin-style Service (paste .ee) in TLS SNI |