| download: | frank.exe |
| Full analysis: | https://app.any.run/tasks/483c5b6d-10e4-4a2c-87d5-41d342e85c2d |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | November 08, 2018, 15:35:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, RAR self-extracting archive |
| MD5: | 2251D5713E8114609FB6AA3E9BD36673 |
| SHA1: | F9F55191099755FC8C62BA08BDF455BD22CC3A4F |
| SHA256: | 1BE3A2EAA351611C6510F6CB036D07ACDC7B46E4A83B49062951BF14B80C8334 |
| SSDEEP: | 24576:f2O/GlbHgK8GijlJh+z3wmxhKbH3rUO46GyW:6AK8xh03wmxUT3iB |
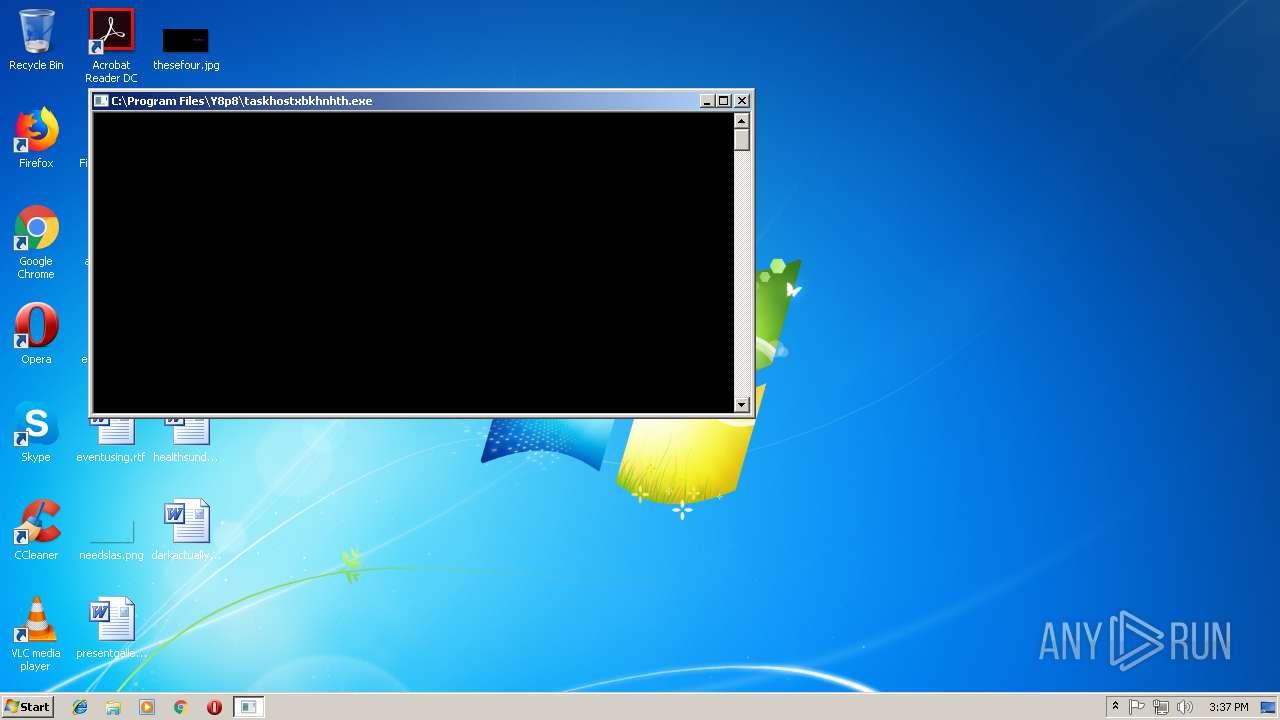
MALICIOUS
Application was dropped or rewritten from another process
- rns.exe (PID: 1672)
- rns.exe (PID: 3164)
- RegSvcs.exe (PID: 3892)
- taskhostxbkhnhth.exe (PID: 1776)
FORMBOOK was detected
- explorer.exe (PID: 1604)
Formbook was detected
- Firefox.exe (PID: 3496)
- cscript.exe (PID: 3480)
Changes the autorun value in the registry
- cscript.exe (PID: 3480)
Connects to CnC server
- explorer.exe (PID: 1604)
Actions looks like stealing of personal data
- cscript.exe (PID: 3480)
Stealing of credential data
- cscript.exe (PID: 3480)
SUSPICIOUS
Drop AutoIt3 executable file
- frank.exe (PID: 1496)
Executable content was dropped or overwritten
- frank.exe (PID: 1496)
- rns.exe (PID: 3164)
- explorer.exe (PID: 1604)
- DllHost.exe (PID: 2376)
Executes scripts
- explorer.exe (PID: 1604)
Starts CMD.EXE for commands execution
- cscript.exe (PID: 3480)
Creates files in the user directory
- cscript.exe (PID: 3480)
Loads DLL from Mozilla Firefox
- cscript.exe (PID: 3480)
Creates files in the program directory
- DllHost.exe (PID: 2376)
INFO
Dropped object may contain Bitcoin addresses
- frank.exe (PID: 1496)
- rns.exe (PID: 1672)
Reads settings of System Certificates
- chrome.exe (PID: 3336)
Application launched itself
- chrome.exe (PID: 3336)
Creates files in the user directory
- Firefox.exe (PID: 3496)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (35.8) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (31.7) |
| .scr | | | Windows screen saver (15) |
| .dll | | | Win32 Dynamic Link Library (generic) (7.5) |
| .exe | | | Win32 Executable (generic) (5.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:06:09 15:19:49+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 74752 |
| InitializedDataSize: | 58880 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xac87 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 09-Jun-2012 13:19:49 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 09-Jun-2012 13:19:49 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001231E | 0x00012400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.55555 |
.rdata | 0x00014000 | 0x00001D15 | 0x00001E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.99401 |
.data | 0x00016000 | 0x00017724 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.54914 |
.CRT | 0x0002E000 | 0x00000020 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.394141 |
.rsrc | 0x0002F000 | 0x0000C2C0 | 0x0000C400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.45727 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.20816 | 1464 | Latin 1 / Western European | English - United States | RT_MANIFEST |
7 | 3.24143 | 556 | Latin 1 / Western European | English - United States | RT_STRING |
8 | 3.26996 | 974 | Latin 1 / Western European | English - United States | RT_STRING |
9 | 3.04375 | 530 | Latin 1 / Western European | English - United States | RT_STRING |
10 | 3.16254 | 776 | Latin 1 / Western European | English - United States | RT_STRING |
11 | 3.06352 | 380 | Latin 1 / Western European | English - United States | RT_STRING |
12 | 2.33959 | 102 | Latin 1 / Western European | English - United States | RT_STRING |
100 | 1.91924 | 20 | Latin 1 / Western European | Process Default Language | RT_GROUP_ICON |
101 | 4.19099 | 2998 | Latin 1 / Western European | English - United States | RT_BITMAP |
ASKNEXTVOL | 3.42597 | 646 | Latin 1 / Western European | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
ole32.dll |
Total processes
49
Monitored processes
16
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1192 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=848,6422127312129028868,12140508893437993133,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=88747EE3A417EED872E1ED9107D35548 --mojo-platform-channel-handle=896 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1496 | "C:\Users\admin\AppData\Local\Temp\frank.exe" | C:\Users\admin\AppData\Local\Temp\frank.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1604 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1672 | "C:\Users\admin\AppData\Local\Temp\90407336\rns.exe" qgx=vbw | C:\Users\admin\AppData\Local\Temp\90407336\rns.exe | — | frank.exe | |||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script Exit code: 0 Version: 3, 3, 14, 5 Modules
| |||||||||||||||
| 1776 | "C:\Program Files\Y8p8\taskhostxbkhnhth.exe" | C:\Program Files\Y8p8\taskhostxbkhnhth.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Services Installation Utility Exit code: 0 Version: 4.6.1055.0 built by: NETFXREL2 Modules
| |||||||||||||||
| 2376 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\system32\DllHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2600 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=848,6422127312129028868,12140508893437993133,131072 --enable-features=PasswordImport --service-pipe-token=3A9B1DAF2F2A94B743C148D999B985ED --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3A9B1DAF2F2A94B743C148D999B985ED --renderer-client-id=5 --mojo-platform-channel-handle=1884 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2688 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1620 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3164 | C:\Users\admin\AppData\Local\Temp\90407336\rns.exe C:\Users\admin\AppData\Local\Temp\90407336\IKMVB | C:\Users\admin\AppData\Local\Temp\90407336\rns.exe | rns.exe | ||||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script Exit code: 0 Version: 3, 3, 14, 5 Modules
| |||||||||||||||
| 3336 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
580
Read events
528
Write events
49
Delete events
3
Modification events
| (PID) Process: | (1496) frank.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1496) frank.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3336) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3336) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3336) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3336) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1604) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | Puebzr |
Value: 000000000400000001000000F5470000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF406408BA7877D40100000000 | |||
| (PID) Process: | (1604) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 0000000027000000320000006A8F1000090000000B000000DCC402007B00370043003500410034003000450046002D0041003000460042002D0034004200460043002D0038003700340041002D004300300046003200450030004200390046004100380045007D005C00410064006F00620065005C004100630072006F0062006100740020005200650061006400650072002000440043005C005200650061006400650072005C004100630072006F0052006400330032002E0065007800650000000000D09866060000000034E82802C05D5A740200000002000000000C00940F000000E8E82802010000000400000001000000010000006B001001D098660605000000D098660602020000E20101AE2B51EA0088E7280239B58D76E20101AE24E82802130000000400000030000000120000001D000000130000001D0000000E00000012000000020000003200000014000000E387EE7A38E82802F3AE5B7400574100E20101AE010000000000000011000000F0443500E8443500A14A52740000000020E800001F51EA7AD0E728028291917520E828028CD800006B51EA7AE4E72802B69C917590D8D4035C0000000401000084F2280244F228026B4E317411000000F0443500E8443500A8EAD403FA4F31740000000074E80000AB5EEA7A24E828028291917574E8280228E8280227959175000000008CD8D40350E82802CD9491758CD8D403FCE8280200D4D403E19491750000000000D4D403FCE8280258E82802000000000E0000002FCA04007B00440036003500320033003100420030002D0042003200460031002D0034003800350037002D0041003400430045002D004100380045003700430036004500410037004400320037007D005C007400610073006B006D00670072002E006500780065000000740020005200650061006400650072002000440043005C005200650061006400650072005C004100630072006F0052006400330032002E0065007800650000000000D09866060000000034E82802C05D5A740200000002000000000C00940F000000E8E82802010000000400000001000000010000006B001001D098660605000000D098660602020000E20101AE2B51EA0088E7280239B58D76E20101AE24E82802130000000400000030000000120000001D000000130000001D0000000E00000012000000020000003200000014000000E387EE7A38E82802F3AE5B7400574100E20101AE010000000000000011000000F0443500E8443500A14A52740000000020E800001F51EA7A24E800006751EA7AD8E728028291917524E828028CD800007351EA7AECE72802B69C917590D8D4034C06000004E8280200D4D40311000000F0443500E844350040B0C37504E8280220D4D40374E80000AB5EEA7A24E828028291917574E8280228E8280227959175000000008CD8D40350E82802CD9491758CD8D403FCE8280200D4D403E19491750000000000D4D403FCE8280258E82802090000000B000000DCC402007B00370043003500410034003000450046002D0041003000460042002D0034004200460043002D0038003700340041002D004300300046003200450030004200390046004100380045007D005C00410064006F00620065005C004100630072006F0062006100740020005200650061006400650072002000440043005C005200650061006400650072005C004100630072006F0052006400330032002E0065007800650000000000D09866060000000034E82802C05D5A740200000002000000000C00940F000000E8E82802010000000400000001000000010000006B001001D098660605000000D098660602020000E20101AE2B51EA0088E7280239B58D76E20101AE24E82802130000000400000030000000120000001D000000130000001D0000000E00000012000000020000003200000014000000E387EE7A38E82802F3AE5B7400574100E20101AE010000000000000011000000F0443500E8443500A14A52740000000020E800001F51EA7AD0E728028291917520E828028CD800006B51EA7AE4E72802B69C917590D8D4035C0000000401000084F2280244F228026B4E317411000000F0443500E8443500A8EAD403FA4F31740000000074E80000AB5EEA7A24E828028291917574E8280228E8280227959175000000008CD8D40350E82802CD9491758CD8D403FCE8280200D4D403E19491750000000000D4D403FCE8280258E82802 | |||
| (PID) Process: | (1604) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{F4E57C4B-2036-45F0-A9AB-443BCFE33D9F}\Count |
| Operation: | write | Name: | P:\Hfref\Choyvp\Qrfxgbc\Tbbtyr Puebzr.yax |
Value: 00000000040000000000000003000000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF406408BA7877D40100000000 | |||
| (PID) Process: | (1604) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{F4E57C4B-2036-45F0-A9AB-443BCFE33D9F}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 0000000022000000000000002100000009000000000000000900000043003A005C00550073006500720073005C005000750062006C00690063005C004400650073006B0074006F0070005C004100630072006F0062006100740020005200650061006400650072002000440043002E006C006E006B0000006C006E006B000000630072006F0062006100740020005200650061006400650072002000440043005C005200650061006400650072005C004100630072006F0052006400330032002E0065007800650000001D020000000085F990758C52F402BCD51D0294D51D028852F402C8D51D02546F9D76BC66AC760000000068DA1D026C31917568DA1D02553E9175337AD50628DD1D0200000000813E917590DA1D0294DA1D028852F402CD78D50656DD1D0200000000337AD506740A91750000000000000000000000000000000000000000000000000000000000000000FFFFFFFF00000000000000000000000091768106A77681069176810600000000000000000000000000000000000000000000000000000000000000009D240000C0ED9D0388D61D0233AB4777C019F5EFFC0B00001027000008000000ED530200BCD61D02F8AA4777ED530200C0ED9D03DCD61D02E8DED4035CD71D0200000000A20100001CD700001360DF7ACCD61D02829191751CD71D02D0D61D02279591750000000074E3D403F8D61D02CD94917574E3D403A4D71D02E8DED403E194917500000000E8DED403A4D71D0200D71D0209000000000000000900000043003A005C00550073006500720073005C005000750062006C00690063005C004400650073006B0074006F0070005C004100630072006F0062006100740020005200650061006400650072002000440043002E006C006E006B0000006C006E006B000000630072006F0062006100740020005200650061006400650072002000440043005C005200650061006400650072005C004100630072006F0052006400330032002E0065007800650000001D020000000085F990758C52F402BCD51D0294D51D028852F402C8D51D02546F9D76BC66AC760000000068DA1D026C31917568DA1D02553E9175337AD50628DD1D0200000000813E917590DA1D0294DA1D028852F402CD78D50656DD1D0200000000337AD506740A91750000000000000000000000000000000000000000000000000000000000000000FFFFFFFF00000000000000000000000091768106A77681069176810600000000000000000000000000000000000000000000000000000000000000009D240000C0ED9D0388D61D0233AB4777C019F5EFFC0B00001027000008000000ED530200BCD61D02F8AA4777ED530200C0ED9D03DCD61D02E8DED4035CD71D0200000000A20100001CD700001360DF7ACCD61D02829191751CD71D02D0D61D02279591750000000074E3D403F8D61D02CD94917574E3D403A4D71D02E8DED403E194917500000000E8DED403A4D71D0200D71D0209000000000000000900000043003A005C00550073006500720073005C005000750062006C00690063005C004400650073006B0074006F0070005C004100630072006F0062006100740020005200650061006400650072002000440043002E006C006E006B0000006C006E006B000000630072006F0062006100740020005200650061006400650072002000440043005C005200650061006400650072005C004100630072006F0052006400330032002E0065007800650000001D020000000085F990758C52F402BCD51D0294D51D028852F402C8D51D02546F9D76BC66AC760000000068DA1D026C31917568DA1D02553E9175337AD50628DD1D0200000000813E917590DA1D0294DA1D028852F402CD78D50656DD1D0200000000337AD506740A91750000000000000000000000000000000000000000000000000000000000000000FFFFFFFF00000000000000000000000091768106A77681069176810600000000000000000000000000000000000000000000000000000000000000009D240000C0ED9D0388D61D0233AB4777C019F5EFFC0B00001027000008000000ED530200BCD61D02F8AA4777ED530200C0ED9D03DCD61D02E8DED4035CD71D0200000000A20100001CD700001360DF7ACCD61D02829191751CD71D02D0D61D02279591750000000074E3D403F8D61D02CD94917574E3D403A4D71D02E8DED403E194917500000000E8DED403A4D71D0200D71D02 | |||
Executable files
5
Suspicious files
109
Text files
108
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1496 | frank.exe | C:\Users\admin\AppData\Local\Temp\90407336\aaq.docx | text | |
MD5:— | SHA256:— | |||
| 1496 | frank.exe | C:\Users\admin\AppData\Local\Temp\90407336\hnq.mp3 | text | |
MD5:— | SHA256:— | |||
| 1496 | frank.exe | C:\Users\admin\AppData\Local\Temp\90407336\xem.bmp | text | |
MD5:— | SHA256:— | |||
| 1496 | frank.exe | C:\Users\admin\AppData\Local\Temp\90407336\nrw.mp3 | text | |
MD5:— | SHA256:— | |||
| 1496 | frank.exe | C:\Users\admin\AppData\Local\Temp\90407336\ftw.txt | text | |
MD5:— | SHA256:— | |||
| 1496 | frank.exe | C:\Users\admin\AppData\Local\Temp\90407336\jug.xl | text | |
MD5:— | SHA256:— | |||
| 1496 | frank.exe | C:\Users\admin\AppData\Local\Temp\90407336\cgm.mp3 | text | |
MD5:— | SHA256:— | |||
| 1496 | frank.exe | C:\Users\admin\AppData\Local\Temp\90407336\hhe.dat | text | |
MD5:— | SHA256:— | |||
| 1496 | frank.exe | C:\Users\admin\AppData\Local\Temp\90407336\gul.ppt | text | |
MD5:— | SHA256:— | |||
| 1496 | frank.exe | C:\Users\admin\AppData\Local\Temp\90407336\efr.bmp | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
15
DNS requests
10
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1604 | explorer.exe | GET | — | 47.52.142.209:80 | http://www.fluorysports.com/aa8/?LhJL=8QtQh+QKR4X7xXWpsWgmLAzc5/T6YCkTzuAoZm2VrSe2knya/26h47lQL8rgD55NpSkKog==&pPv=K2KdTxYP8270tPWP | HK | — | — | malicious |
1604 | explorer.exe | GET | 404 | 162.213.255.220:80 | http://www.nadidetadllar.com/aa8/?LhJL=RHDVyMGFPOescSk8fBVyz7avp6vl173cjAxPM1VuTIfp3KGJQuEcxaOelH6TQ4dkTsIRxg==&pPv=K2KdTxYP8270tPWP&sql=1 | US | html | 327 b | malicious |
1604 | explorer.exe | POST | 404 | 162.213.255.220:80 | http://www.nadidetadllar.com/aa8/ | US | html | 295 b | malicious |
1604 | explorer.exe | POST | — | 162.213.255.220:80 | http://www.nadidetadllar.com/aa8/ | US | — | — | malicious |
1604 | explorer.exe | POST | — | 162.213.255.220:80 | http://www.nadidetadllar.com/aa8/ | US | — | — | malicious |
1604 | explorer.exe | POST | — | 162.213.255.220:80 | http://www.nadidetadllar.com/aa8/ | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3336 | chrome.exe | 216.58.215.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3336 | chrome.exe | 172.217.168.74:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3336 | chrome.exe | 172.217.168.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
3336 | chrome.exe | 216.58.215.238:443 | apis.google.com | Google Inc. | US | whitelisted |
1604 | explorer.exe | 47.52.142.209:80 | www.fluorysports.com | Alibaba (China) Technology Co., Ltd. | HK | malicious |
1604 | explorer.exe | 162.213.255.220:80 | www.nadidetadllar.com | Namecheap, Inc. | US | malicious |
3336 | chrome.exe | 172.217.168.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3336 | chrome.exe | 172.217.168.67:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.gstatic.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.google.de |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
www.genesischemist.win |
| unknown |
www.fluorysports.com |
| malicious |
www.nadidetadllar.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1604 | explorer.exe | A Network Trojan was detected | SC SPYWARE Trojan-Spy.Win32.Noon |
1604 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
1604 | explorer.exe | A Network Trojan was detected | SC SPYWARE Trojan-Spy.Win32.Noon |
1604 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
1604 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
1604 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
1604 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
1604 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (POST) |
4 ETPRO signatures available at the full report