| File name: | ac9f5a051227302049aa5136a26f30a3707db55c.rl |
| Full analysis: | https://app.any.run/tasks/50c33638-b9ca-408d-b7f4-922afde81060 |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
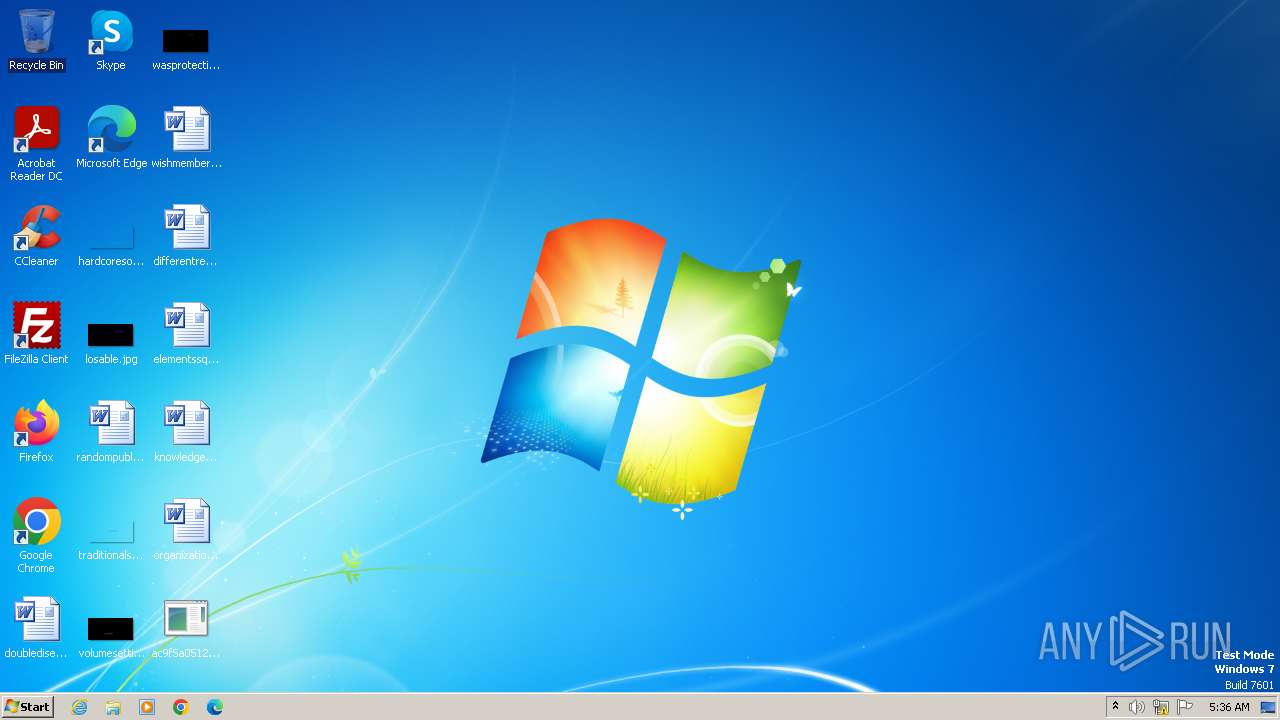
| Analysis date: | December 02, 2023, 05:36:51 |
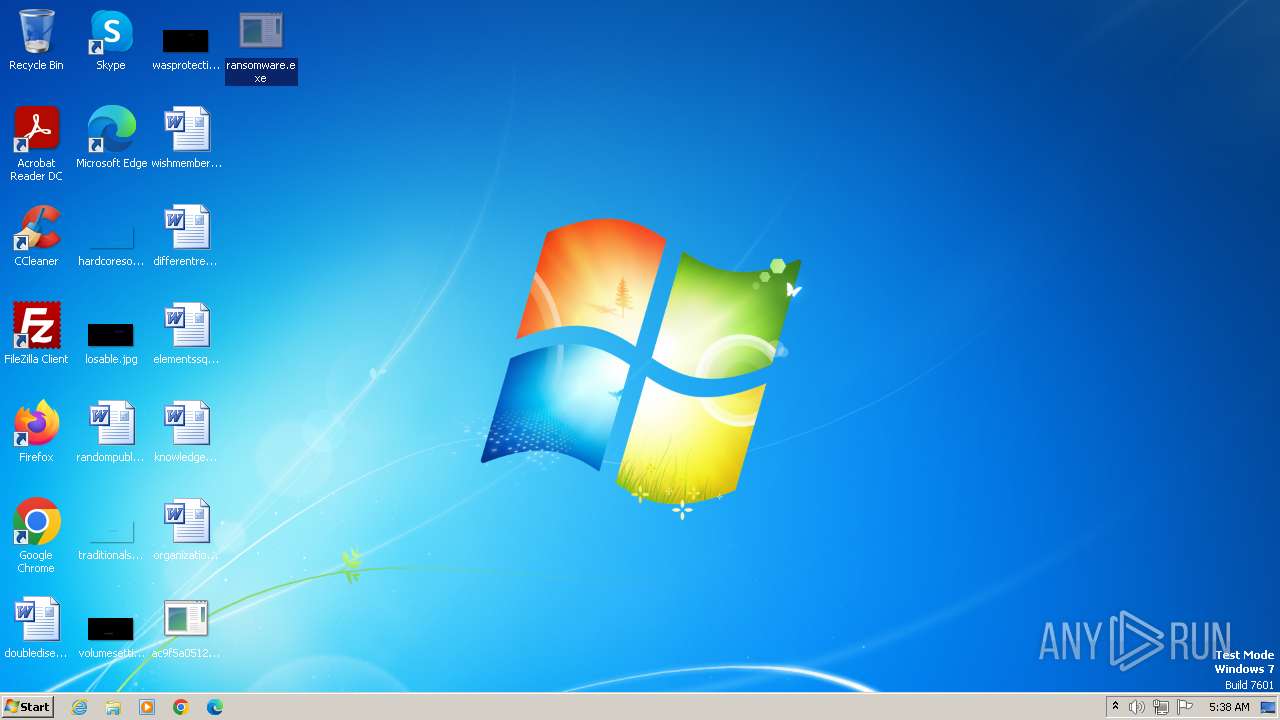
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 8EAB5E4D034FDE42EB31ADD0CB923A97 |
| SHA1: | AC9F5A051227302049AA5136A26F30A3707DB55C |
| SHA256: | 1BE1EB3FC904FC5A9E9E555E3FA4A2B6A5A299917D5AFA9A1570079195387FA3 |
| SSDEEP: | 24576:7Jk/D9Goasb2G5v0pioDiFh8zil1KE3YRRAiag9lTKLB3eYC:7Jk/pGoaU2G5v0YGiFh8zil1KE3YRRAe |
MALICIOUS
Drops the executable file immediately after the start
- ac9f5a051227302049aa5136a26f30a3707db55c.rl.exe (PID: 2644)
- RegAsm.exe (PID: 3980)
- ransomware.exe (PID: 1608)
AGENTTESLA has been detected (YARA)
- RegAsm.exe (PID: 3980)
Steals credentials from Web Browsers
- RegAsm.exe (PID: 3980)
Actions looks like stealing of personal data
- RegAsm.exe (PID: 3980)
- svchost.exe (PID: 3140)
Connects to the CnC server
- RegAsm.exe (PID: 3980)
Create files in the Startup directory
- svchost.exe (PID: 3140)
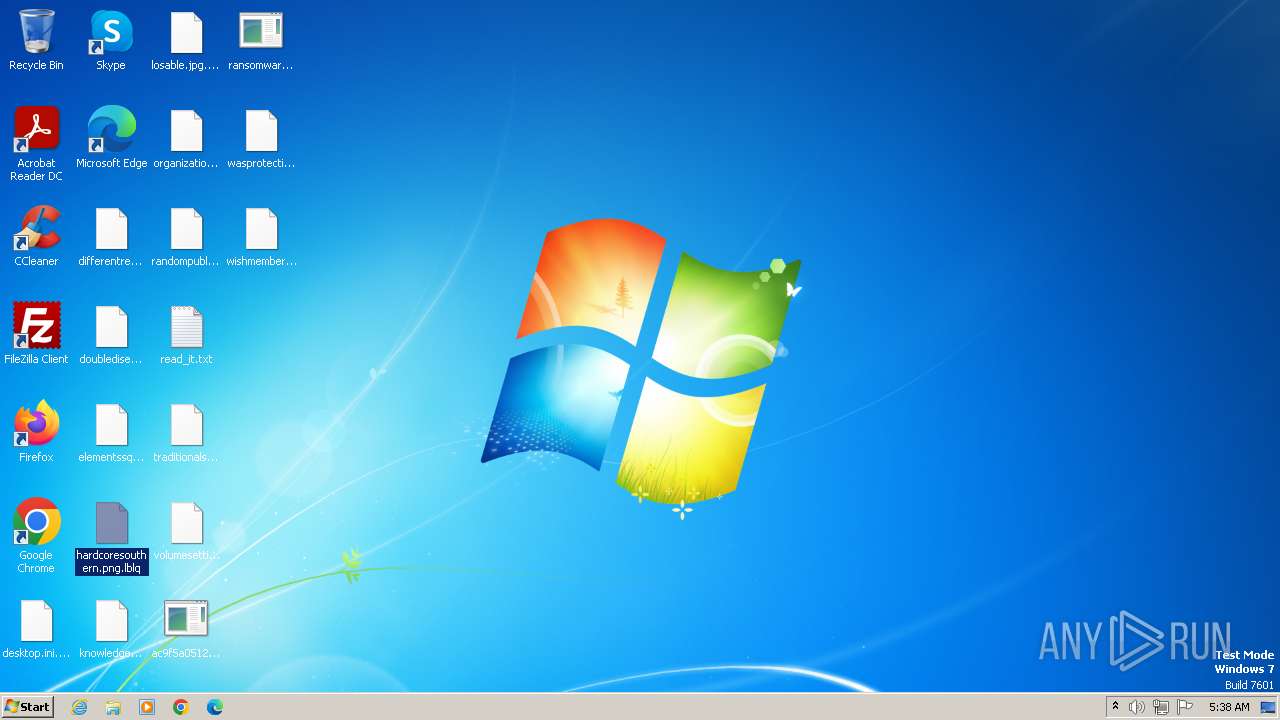
Renames files like ransomware
- svchost.exe (PID: 3140)
SUSPICIOUS
Process drops legitimate windows executable
- RegAsm.exe (PID: 3980)
Reads the Internet Settings
- RegAsm.exe (PID: 3980)
- ransomware.exe (PID: 1608)
Accesses Microsoft Outlook profiles
- RegAsm.exe (PID: 3980)
Connects to SMTP port
- RegAsm.exe (PID: 3980)
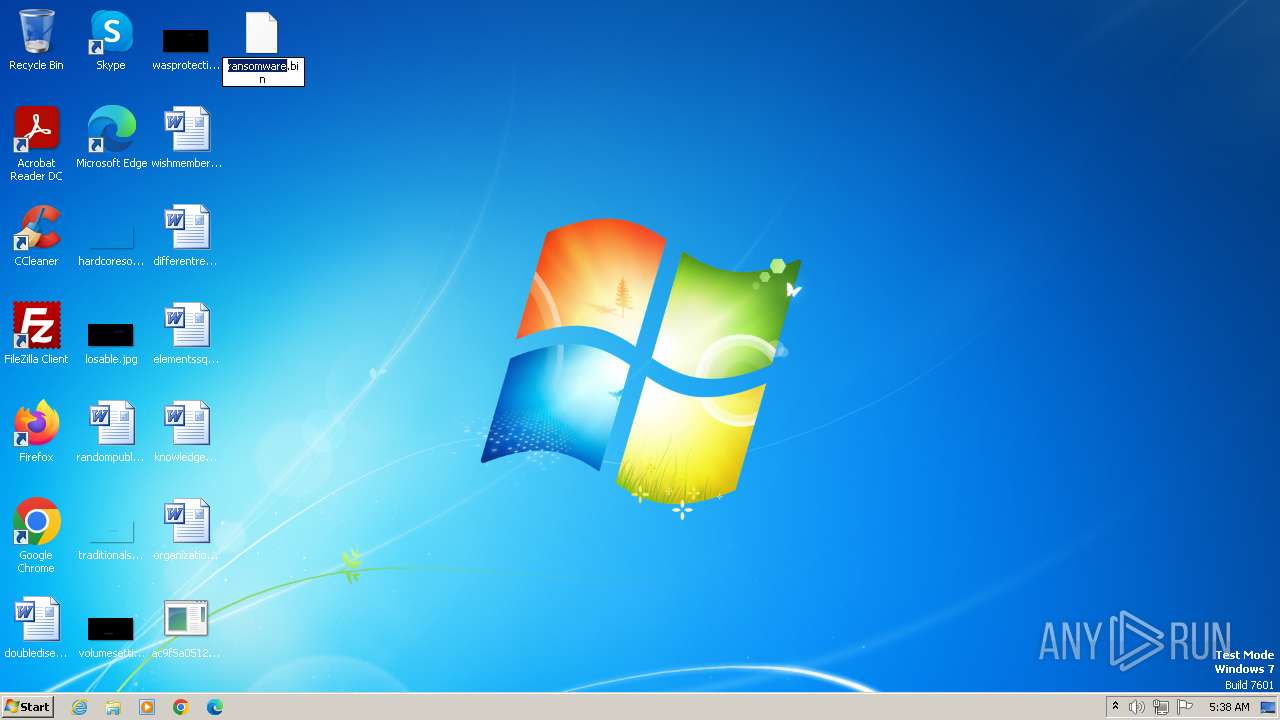
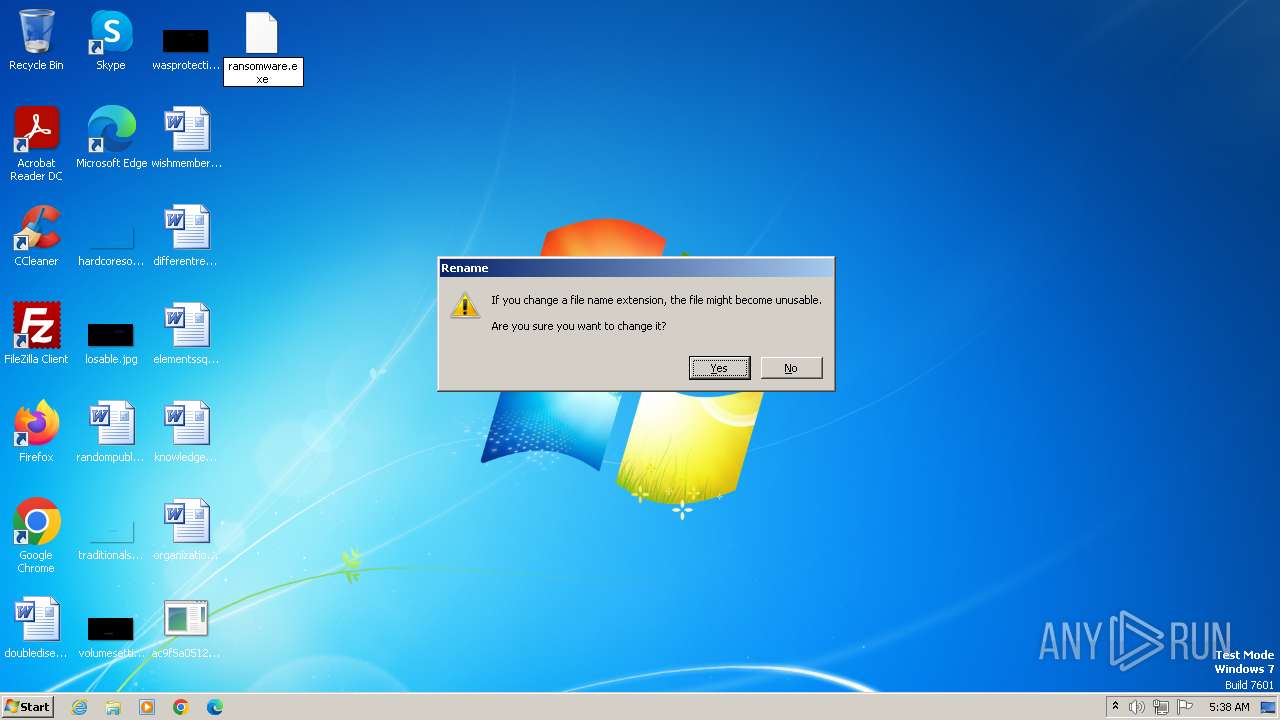
Starts itself from another location
- ransomware.exe (PID: 1608)
The process creates files with name similar to system file names
- ransomware.exe (PID: 1608)
Write to the desktop.ini file (may be used to cloak folders)
- svchost.exe (PID: 3140)
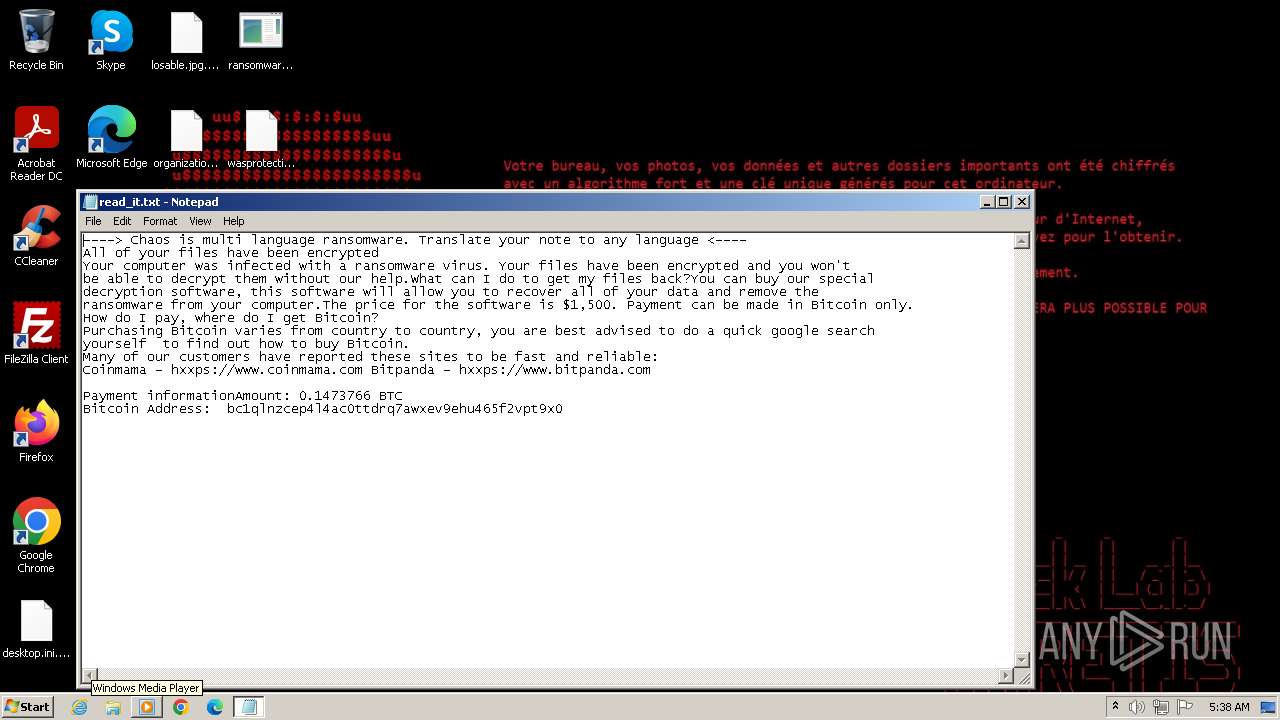
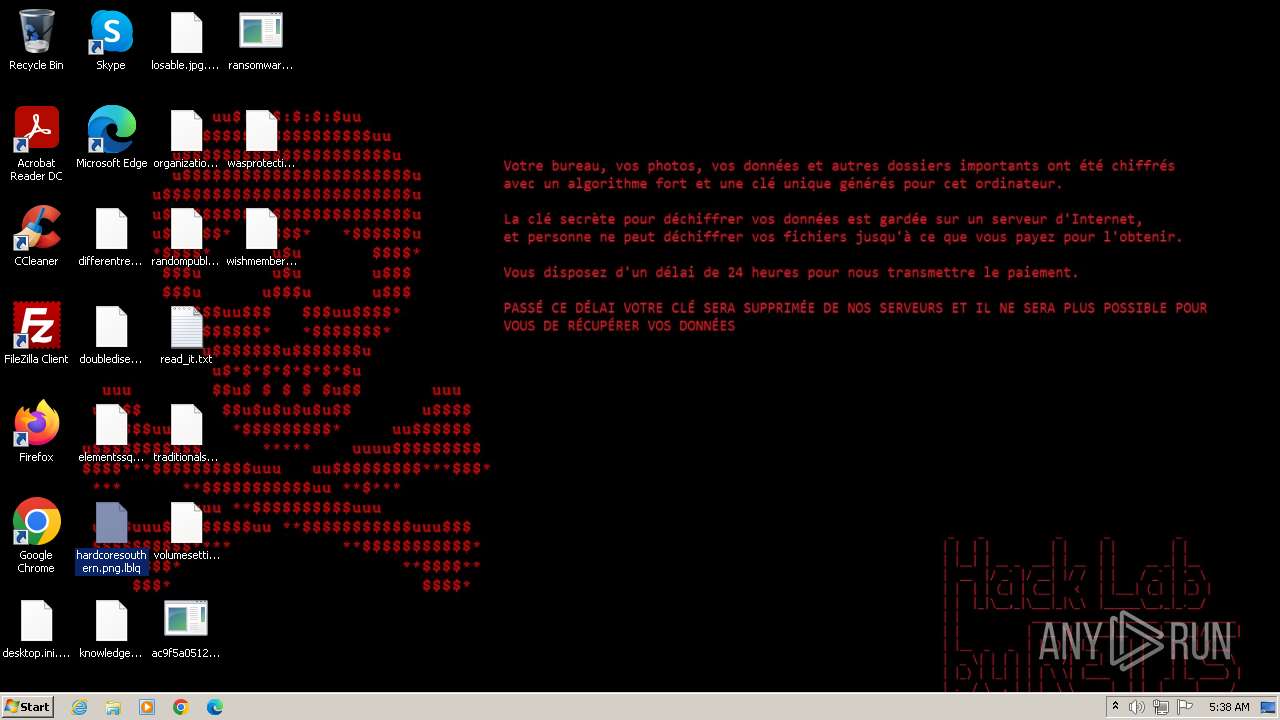
Start notepad (likely ransomware note)
- svchost.exe (PID: 3140)
INFO
Reads the computer name
- ac9f5a051227302049aa5136a26f30a3707db55c.rl.exe (PID: 2644)
- wmpnscfg.exe (PID: 1116)
- RegAsm.exe (PID: 3980)
- svchost.exe (PID: 3140)
- ransomware.exe (PID: 1608)
Checks supported languages
- ac9f5a051227302049aa5136a26f30a3707db55c.rl.exe (PID: 2644)
- RegAsm.exe (PID: 3980)
- wmpnscfg.exe (PID: 1116)
- ransomware.exe (PID: 1608)
- svchost.exe (PID: 3140)
Reads the machine GUID from the registry
- ac9f5a051227302049aa5136a26f30a3707db55c.rl.exe (PID: 2644)
- RegAsm.exe (PID: 3980)
- svchost.exe (PID: 3140)
Reads Environment values
- RegAsm.exe (PID: 3980)
Creates files or folders in the user directory
- ac9f5a051227302049aa5136a26f30a3707db55c.rl.exe (PID: 2644)
- RegAsm.exe (PID: 3980)
- ransomware.exe (PID: 1608)
- svchost.exe (PID: 3140)
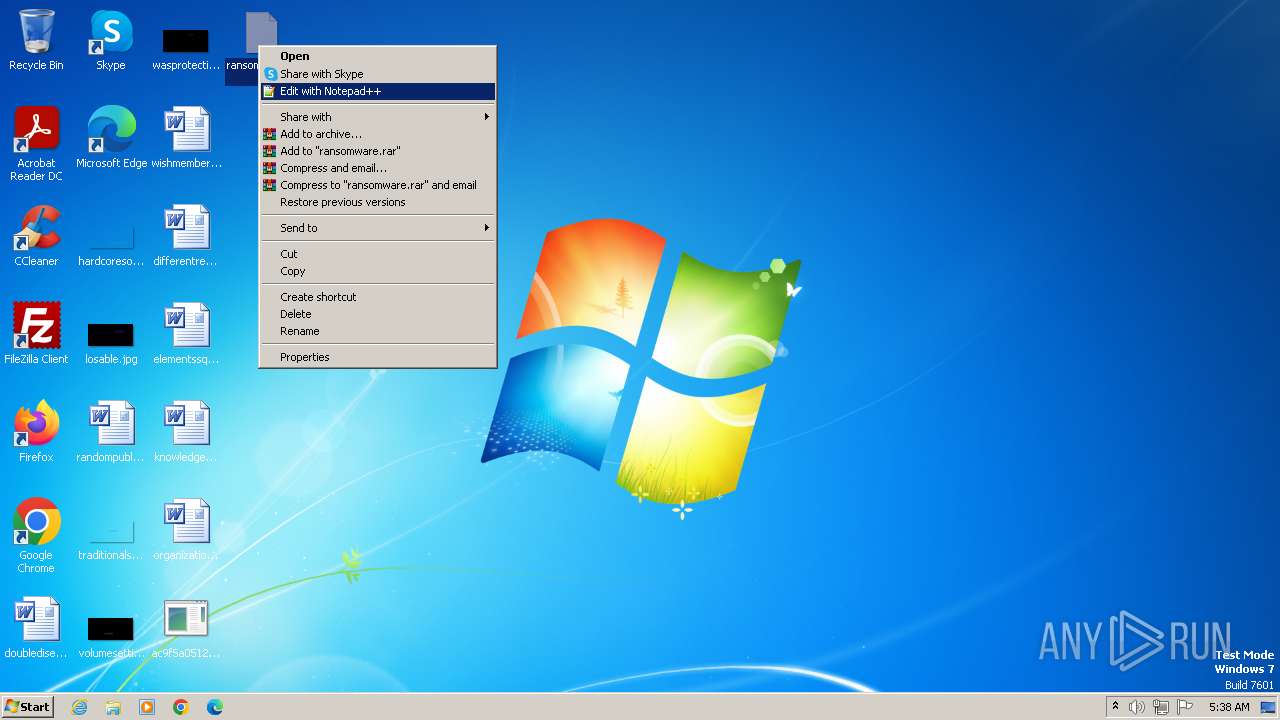
Manual execution by a user
- wmpnscfg.exe (PID: 1116)
- ransomware.exe (PID: 1608)
Create files in a temporary directory
- svchost.exe (PID: 3140)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AgentTesla
(PID) Process(3980) RegAsm.exe
Protocolsmtp
Hostmail.asiaparadisehotel.com
Port587
Usernameasia@asiaparadisehotel.com
Password^b2ycDldex$@
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:12:01 14:48:08+01:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 635392 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x9d14e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | 1.0.0.0 |
| InternalName: | Aabbatli.exe |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFileName: | Aabbatli.exe |
| ProductName: | - |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
45
Monitored processes
6
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1116 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1608 | "C:\Users\admin\Desktop\ransomware.exe" | C:\Users\admin\Desktop\ransomware.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 1 Version: 0.0.0.0 Modules
| |||||||||||||||
| 2644 | "C:\Users\admin\Desktop\ac9f5a051227302049aa5136a26f30a3707db55c.rl.exe" | C:\Users\admin\Desktop\ac9f5a051227302049aa5136a26f30a3707db55c.rl.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3140 | "C:\Users\admin\AppData\Roaming\svchost.exe" | C:\Users\admin\AppData\Roaming\svchost.exe | ransomware.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
| 3980 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe | ac9f5a051227302049aa5136a26f30a3707db55c.rl.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 4.8.3761.0 built by: NET48REL1 Modules
AgentTesla(PID) Process(3980) RegAsm.exe Protocolsmtp Hostmail.asiaparadisehotel.com Port587 Usernameasia@asiaparadisehotel.com Password^b2ycDldex$@ | |||||||||||||||
| 3996 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Roaming\read_it.txt | C:\Windows\System32\notepad.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
4 815
Read events
4 807
Write events
8
Delete events
0
Modification events
| (PID) Process: | (1608) ransomware.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1608) ransomware.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1608) ransomware.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1608) ransomware.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
3
Suspicious files
0
Text files
723
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1608 | ransomware.exe | C:\Users\admin\AppData\Roaming\svchost.exe | executable | |
MD5:761E82385AC656CDB40C5B9189AB0CF2 | SHA256:B902F48739FA84BE97815B796681A7B337C7BBCAD14D436AEB6BA93B9FE5AEBD | |||
| 3140 | svchost.exe | C:\Users\admin\Desktop\desktop.ini | text | |
MD5:A08B6BB225AEAB57B3E28626DFA15BF3 | SHA256:8A5DCB22D882DA5F5A65FB709D926E36AB490757CA86E11AF238803BD84A0927 | |||
| 3980 | RegAsm.exe | C:\Users\admin\AppData\Roaming\TlKsFB\TlKsFB.exe | executable | |
MD5:8FE9545E9F72E460723F484C304314AD | SHA256:D2F0B87E2D2707685C4D35F8F05B42FB8326EF4E70D16097B8837DABA06AC961 | |||
| 3140 | svchost.exe | C:\Users\admin\Desktop\desktop.ini.x99t | text | |
MD5:A08B6BB225AEAB57B3E28626DFA15BF3 | SHA256:8A5DCB22D882DA5F5A65FB709D926E36AB490757CA86E11AF238803BD84A0927 | |||
| 3140 | svchost.exe | C:\Users\admin\Desktop\differentrecord.rtf.m5kb | text | |
MD5:C1CF2C59068760C702316EB582313B67 | SHA256:7C787B932CB5673CDD77FB6DE01FAB79150BC52CC3D539D4161FCFD583E54D11 | |||
| 3140 | svchost.exe | C:\Users\admin\Desktop\differentrecord.rtf | text | |
MD5:C1CF2C59068760C702316EB582313B67 | SHA256:7C787B932CB5673CDD77FB6DE01FAB79150BC52CC3D539D4161FCFD583E54D11 | |||
| 3140 | svchost.exe | C:\Users\admin\Desktop\read_it.txt | text | |
MD5:4217B8B83CE3C3F70029A056546F8FD0 | SHA256:7D767E907BE373C680D1F7884D779588EB643BEBB3F27BF3B5ED4864AA4D8121 | |||
| 3140 | svchost.exe | C:\Users\admin\Desktop\doubledisease.rtf | text | |
MD5:08B5AE2ADC62CB251087645DB8B6DD6F | SHA256:82C9B5468393AE6842761C447615590B1F77DDC2ED42B3367B7342DC437EA65D | |||
| 3140 | svchost.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\svchost.url | text | |
MD5:83660DEB1A47E0B191FDA82BDFD61827 | SHA256:87089BD6FEDDA43B5E4D738B5BF246BA1B2E5C248B9220F0D1E742B827F30B0D | |||
| 3140 | svchost.exe | C:\Users\admin\Desktop\elementssquare.rtf | text | |
MD5:57CE70803D897E60636611226EDAA5E4 | SHA256:A099563C98F38E1F375716F6959E2C991E48EBCAAE48EFBB8D106B2EDCD7D311 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
6
DNS requests
4
Threats
6
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3980 | RegAsm.exe | 173.231.16.77:443 | api.ipify.org | WEBNX | US | unknown |
3980 | RegAsm.exe | 112.213.92.100:587 | mail.asiaparadisehotel.com | SUPERDATA | VN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.ipify.org |
| shared |
mail.asiaparadisehotel.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
1080 | svchost.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
1080 | svchost.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
3980 | RegAsm.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |
2 ETPRO signatures available at the full report