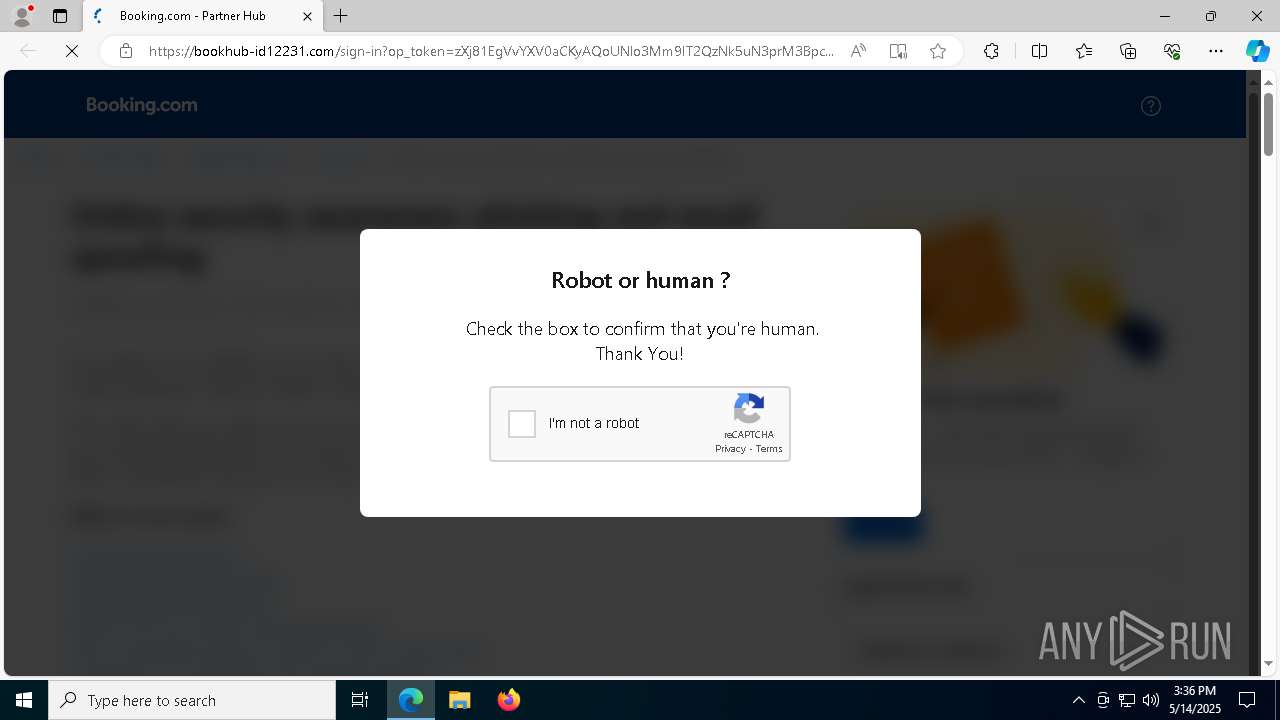
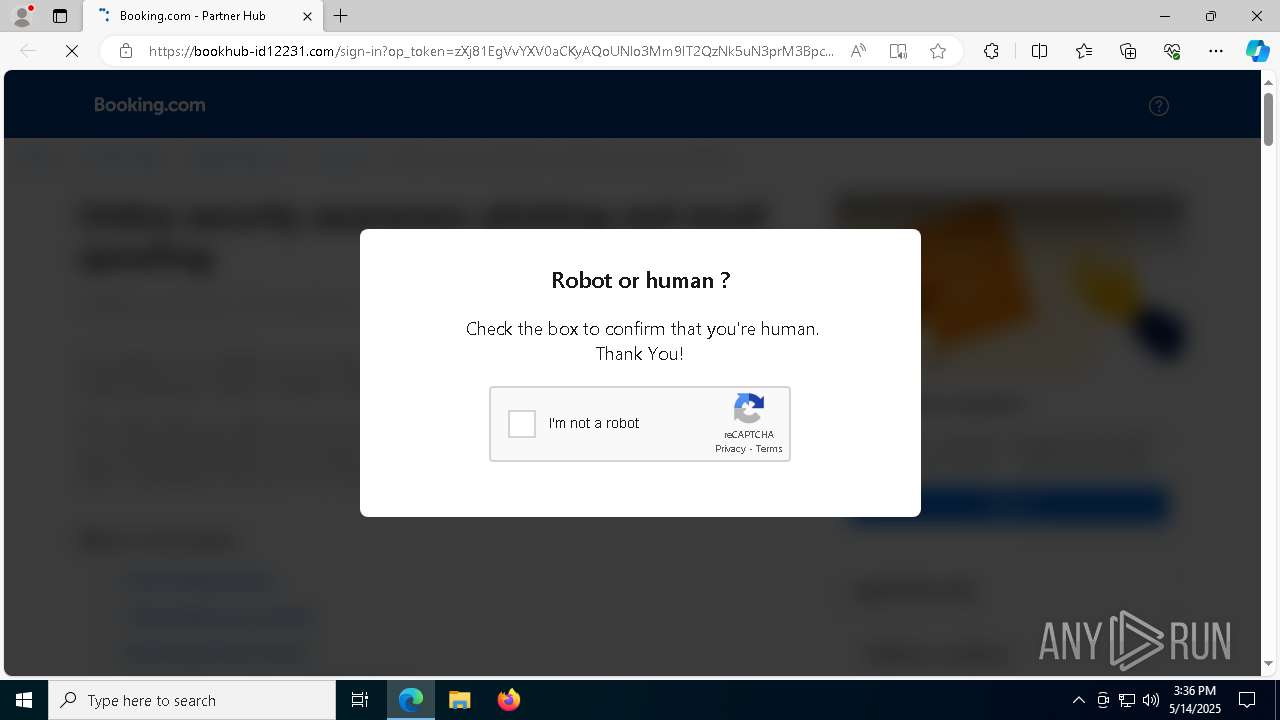
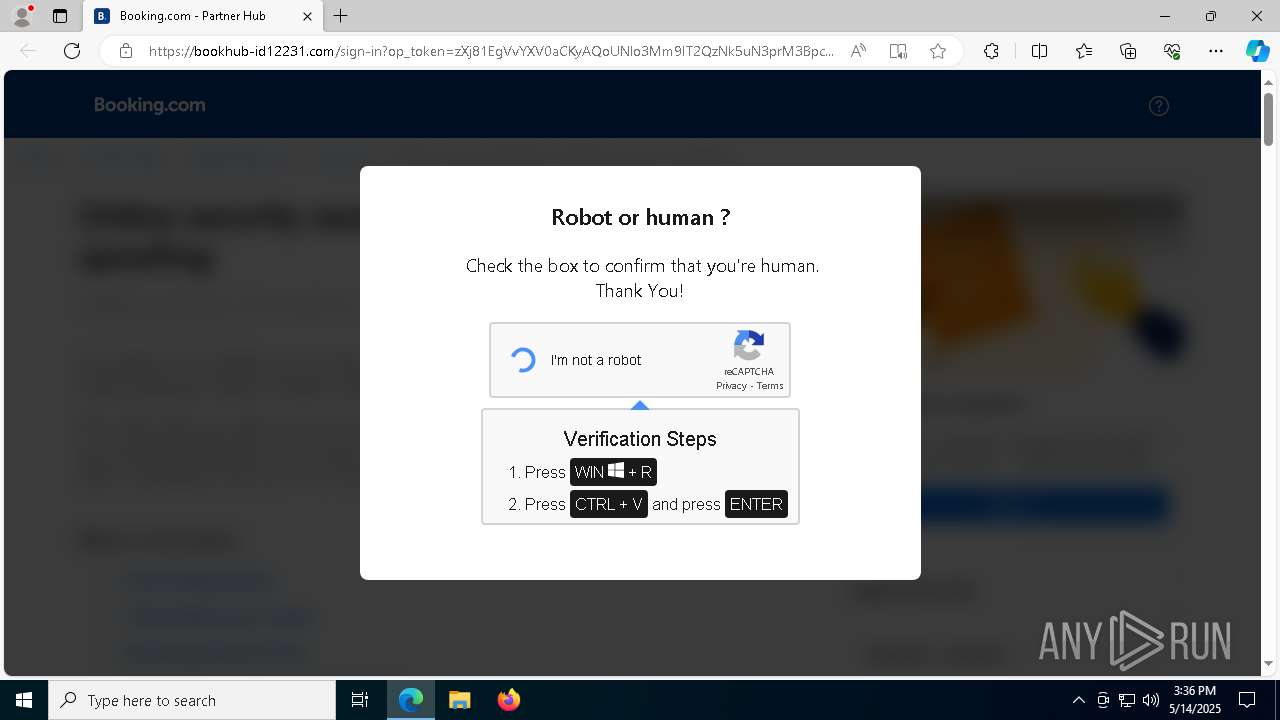
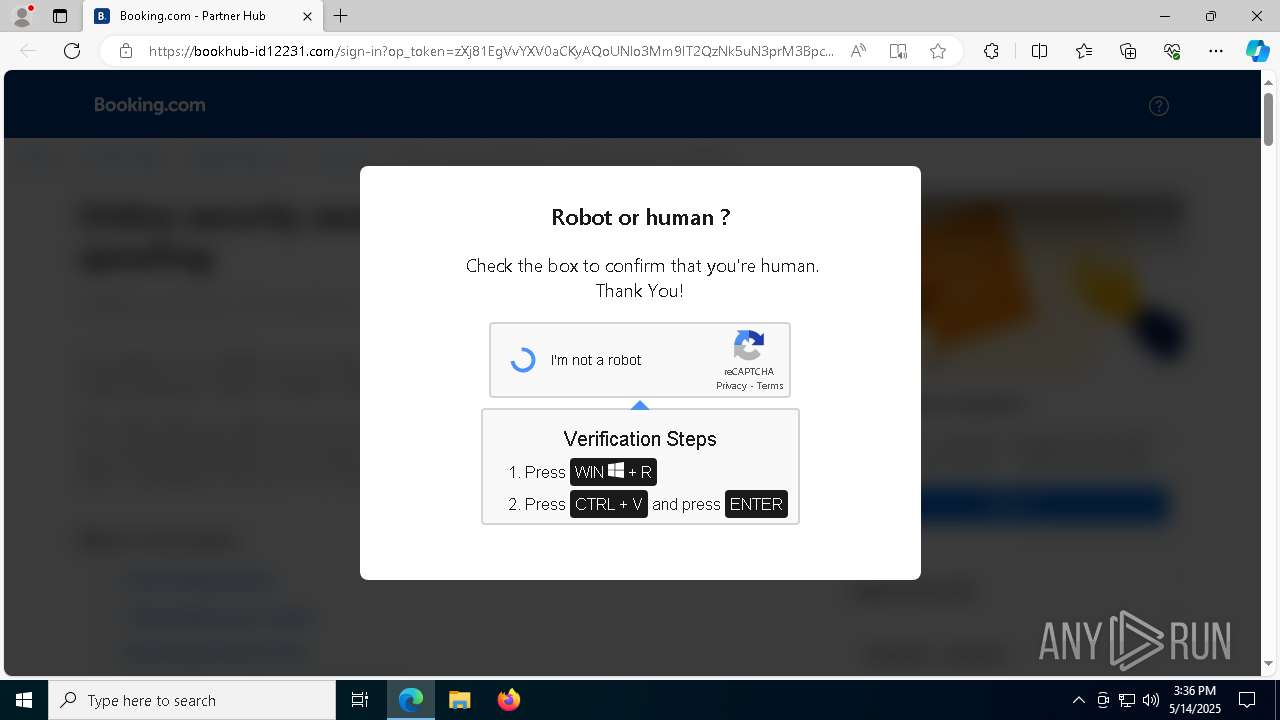
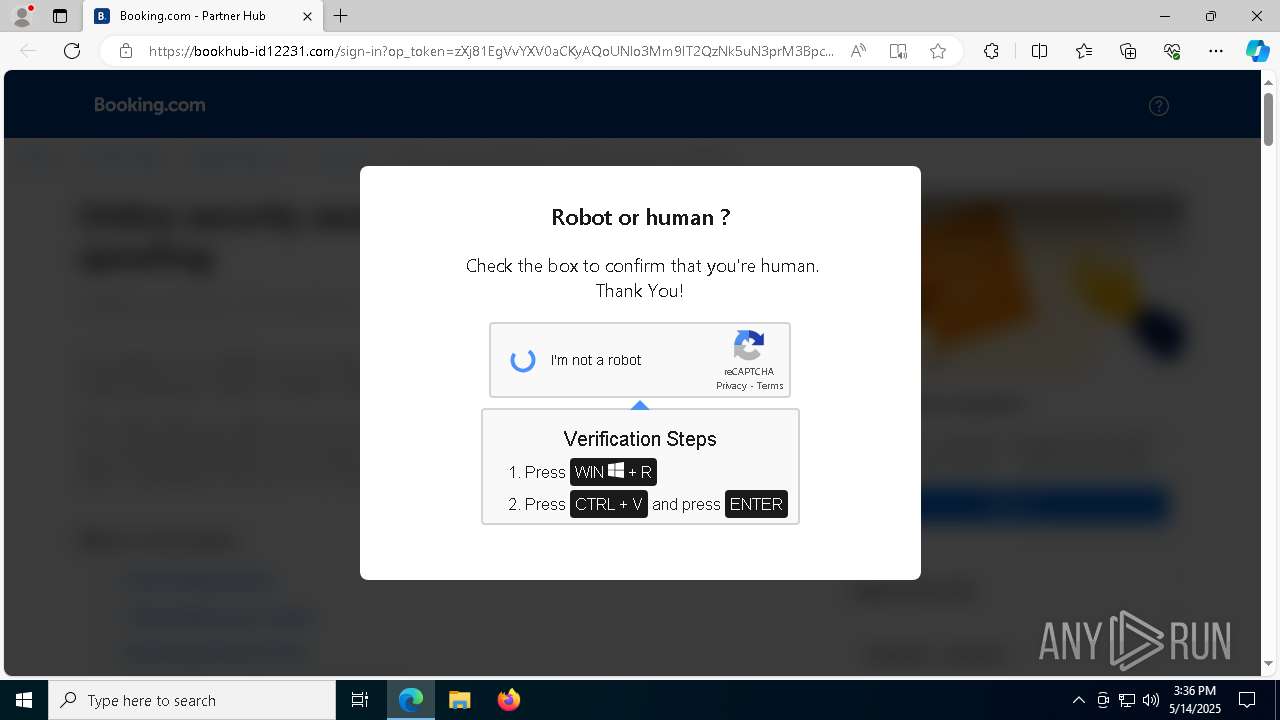
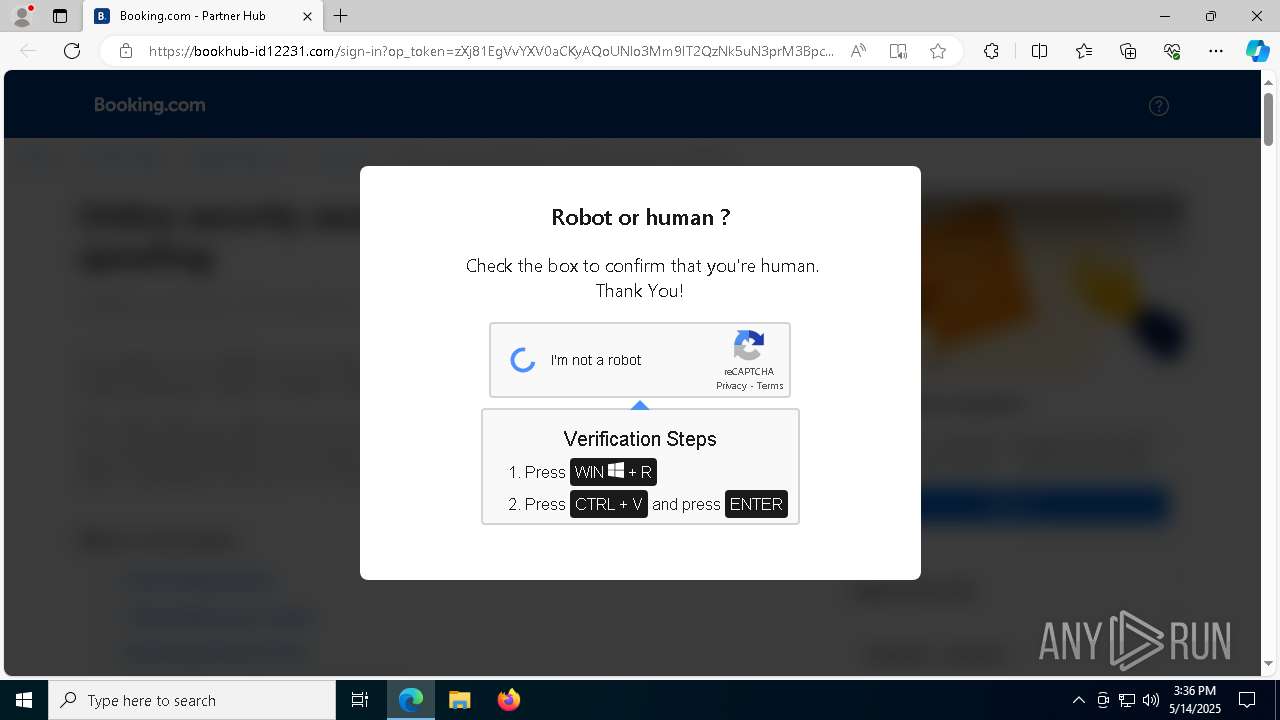
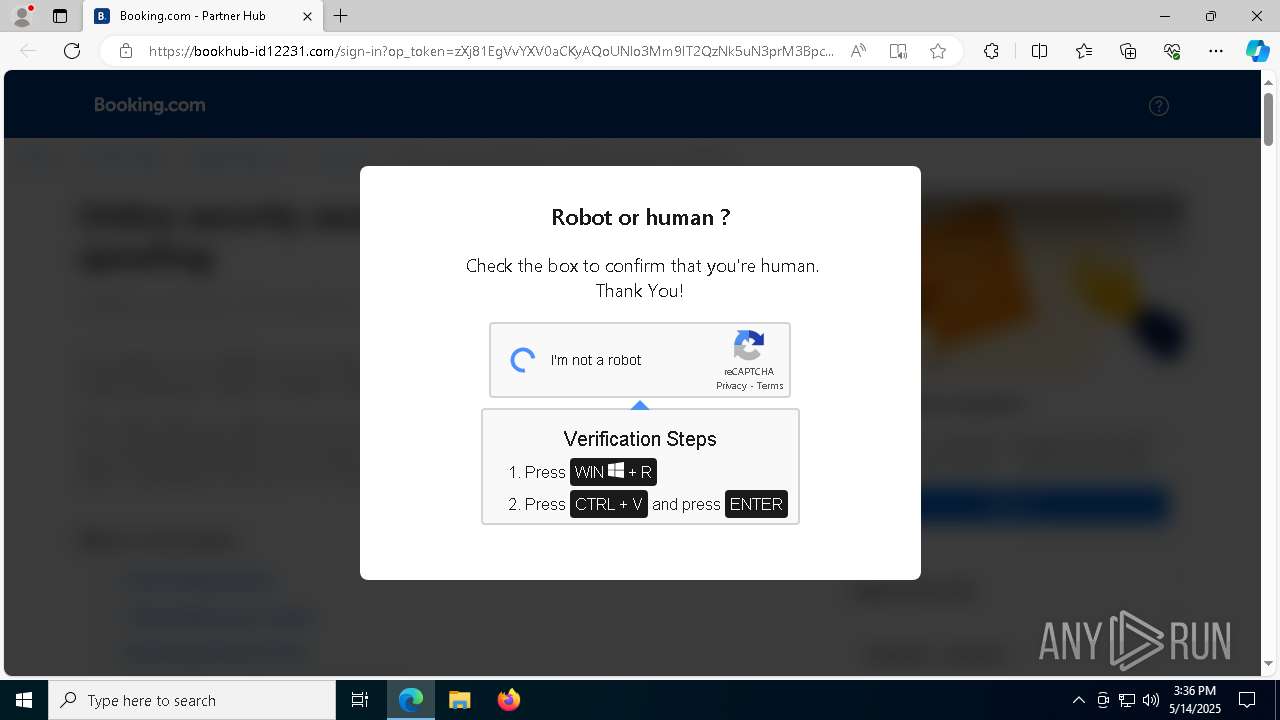
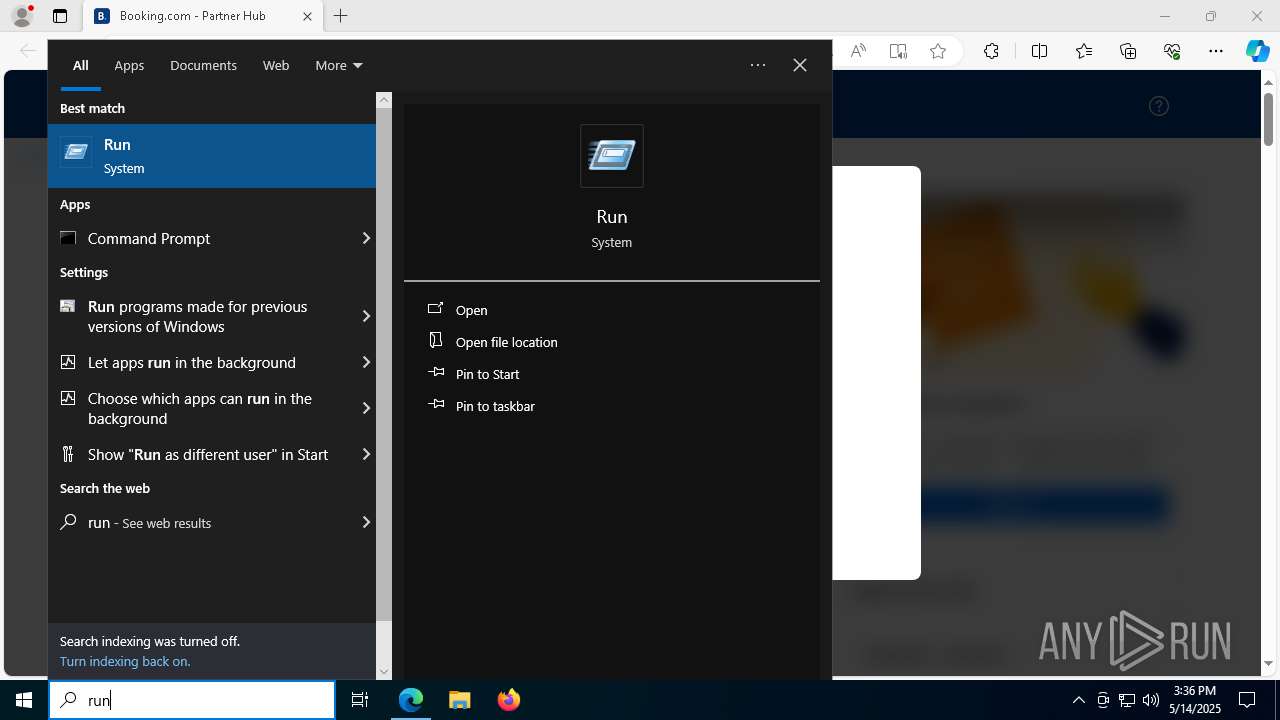
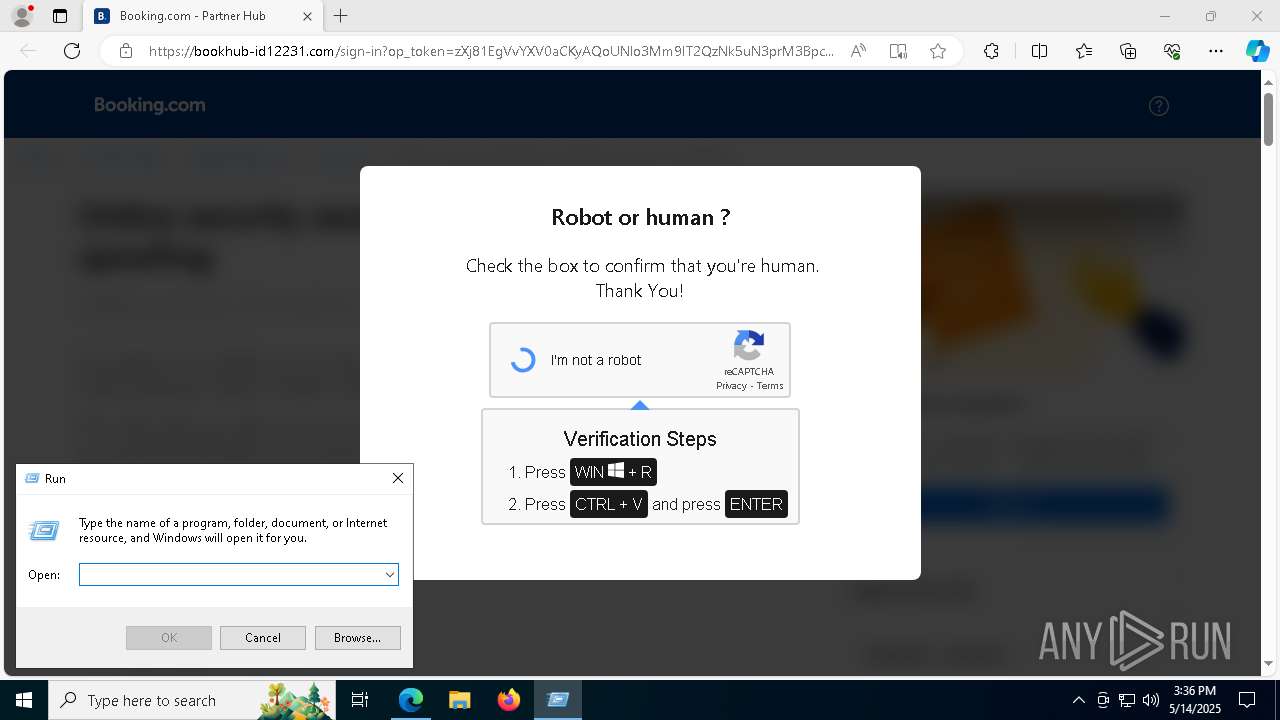
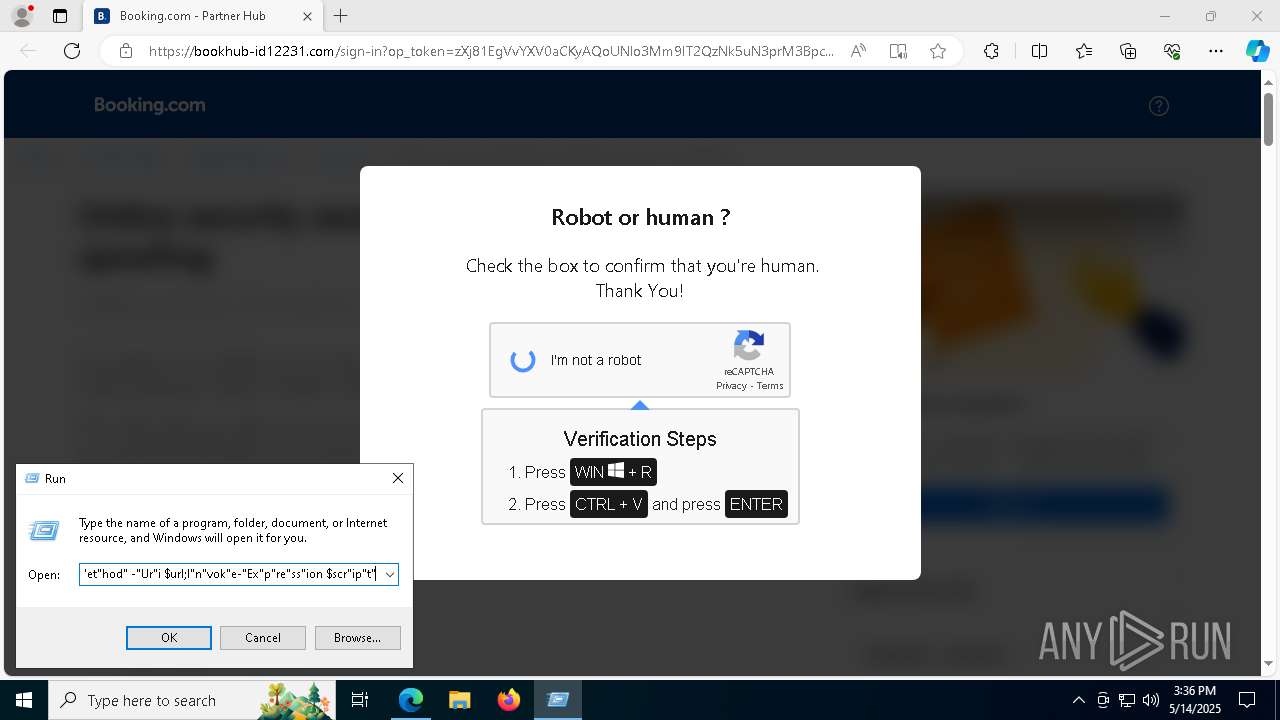
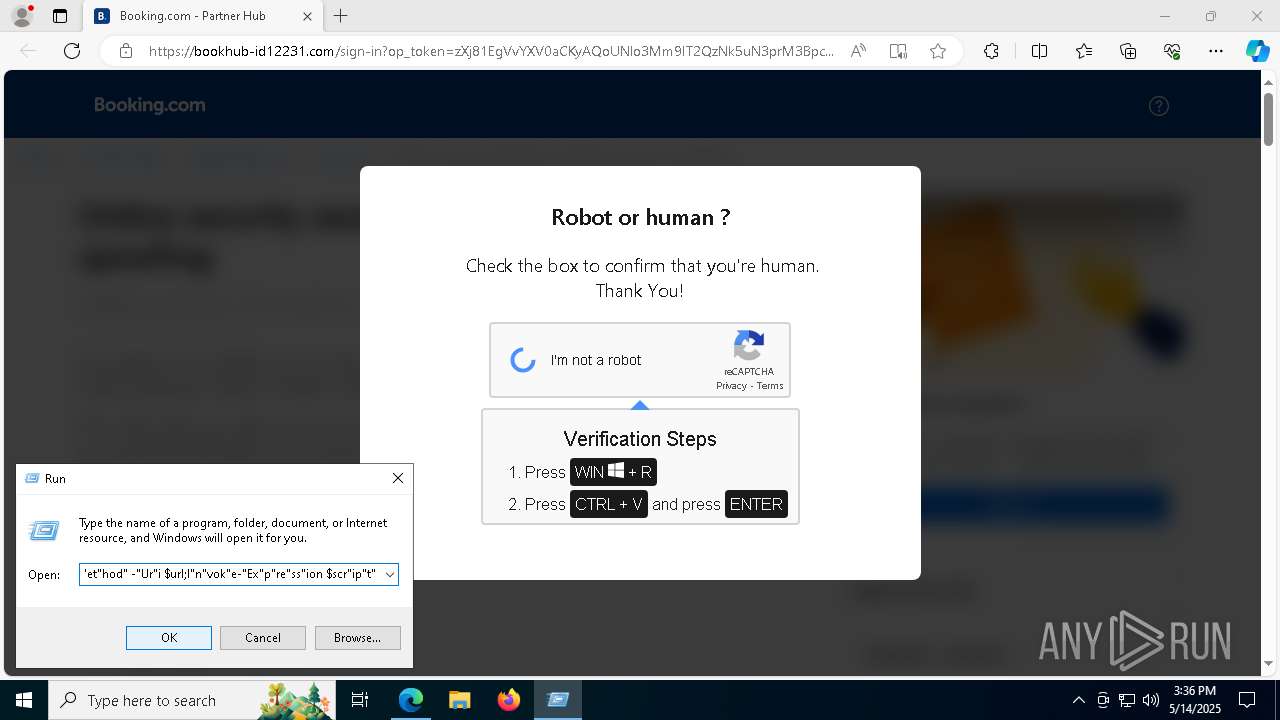
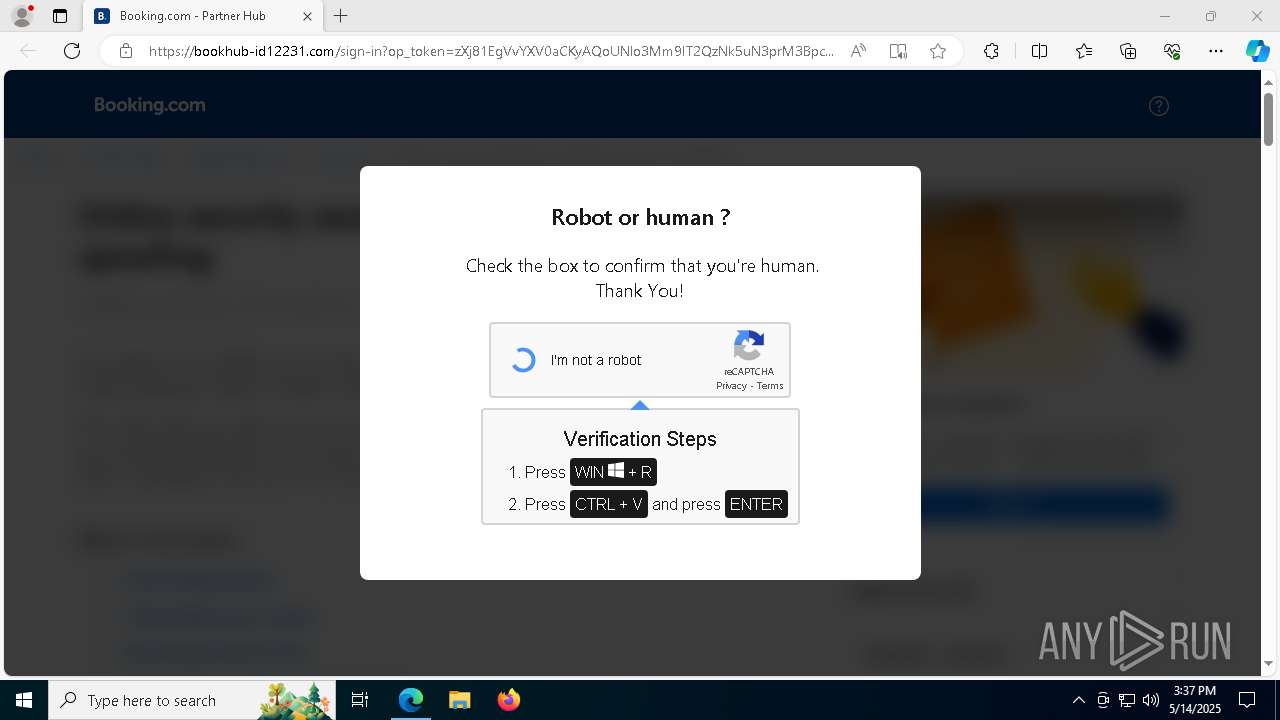
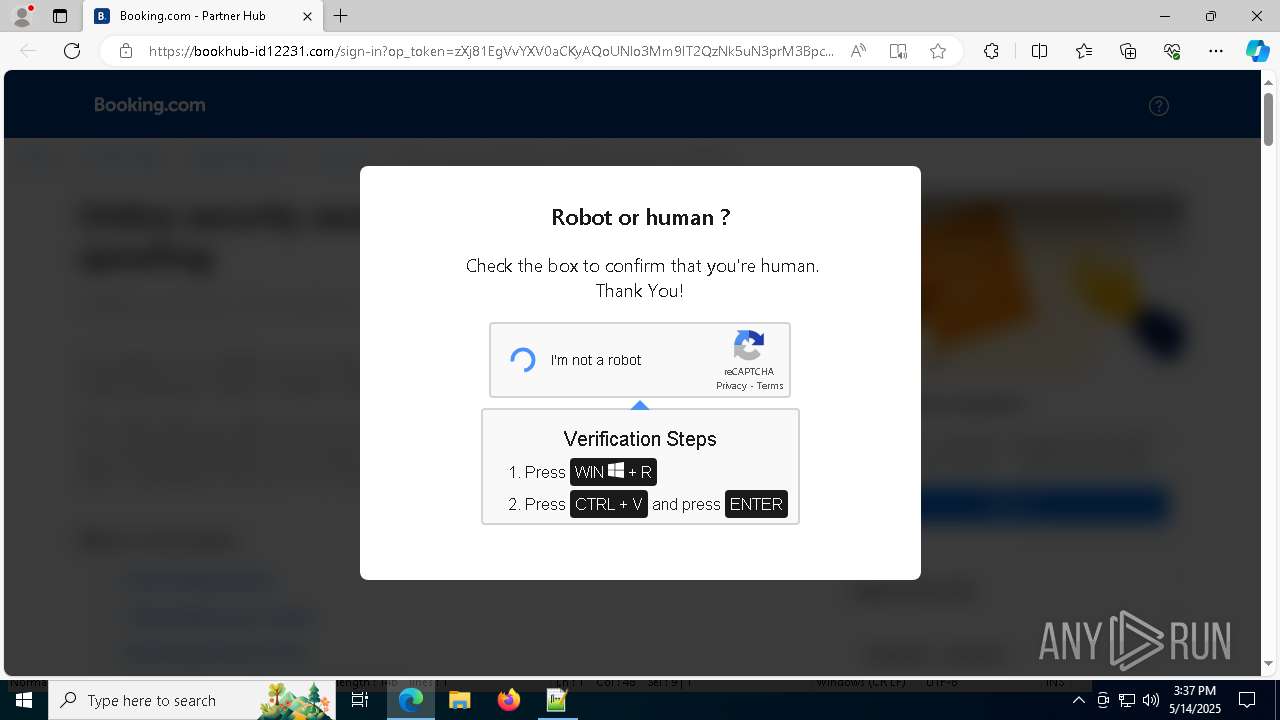
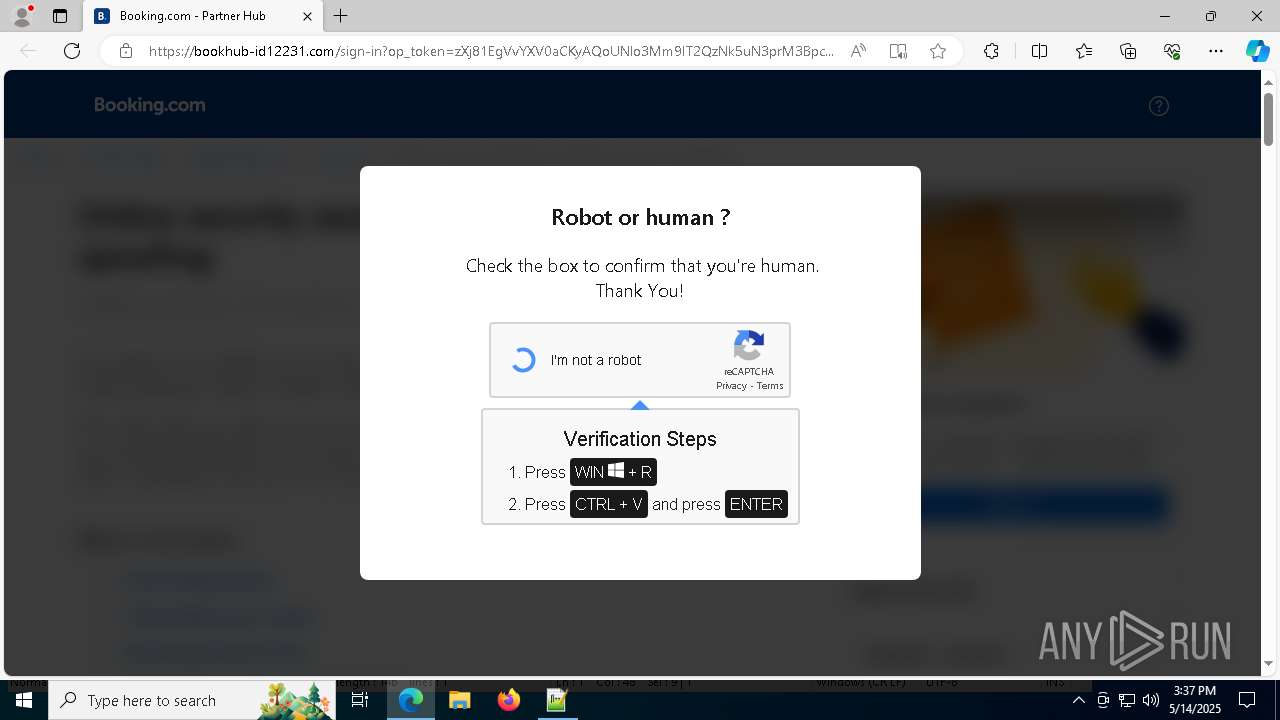
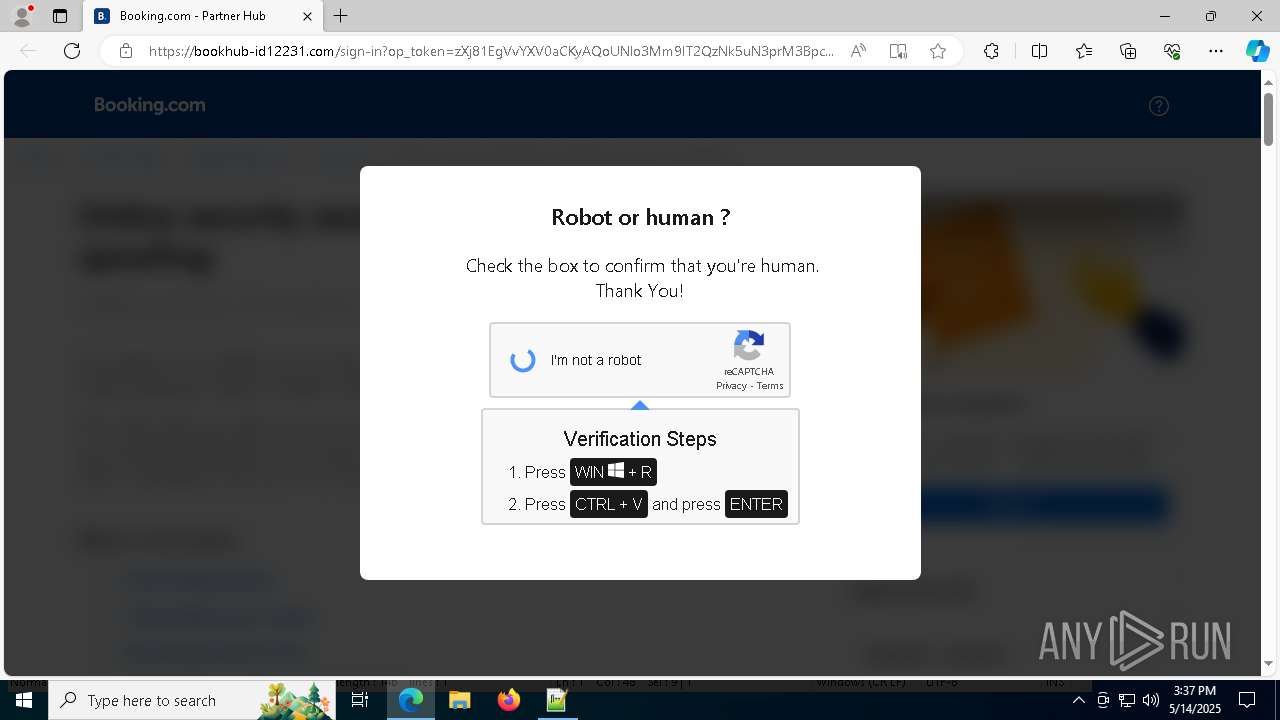
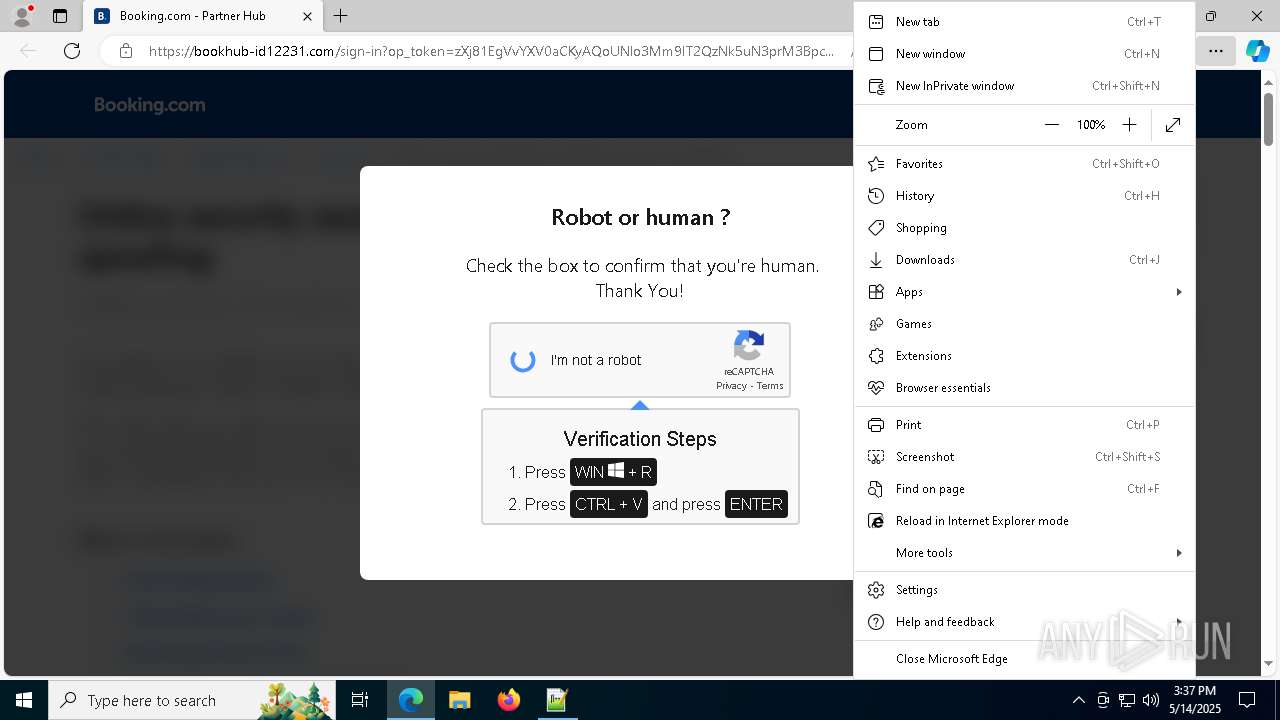
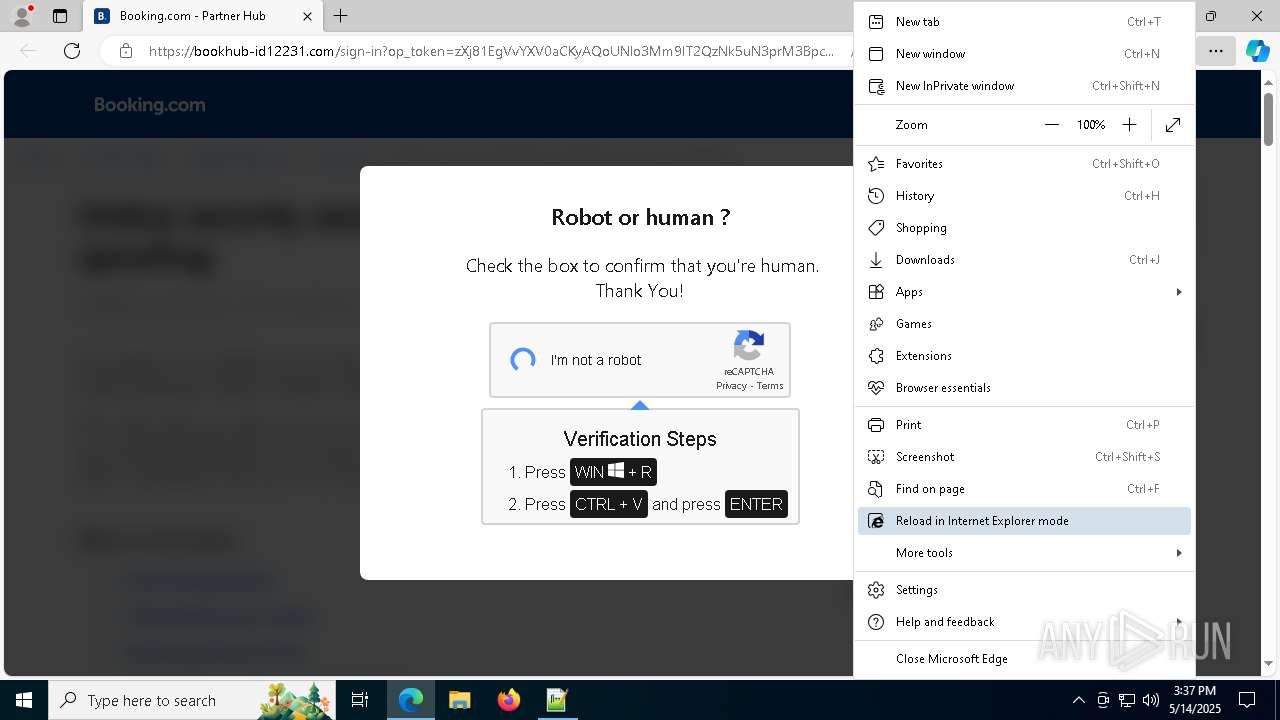
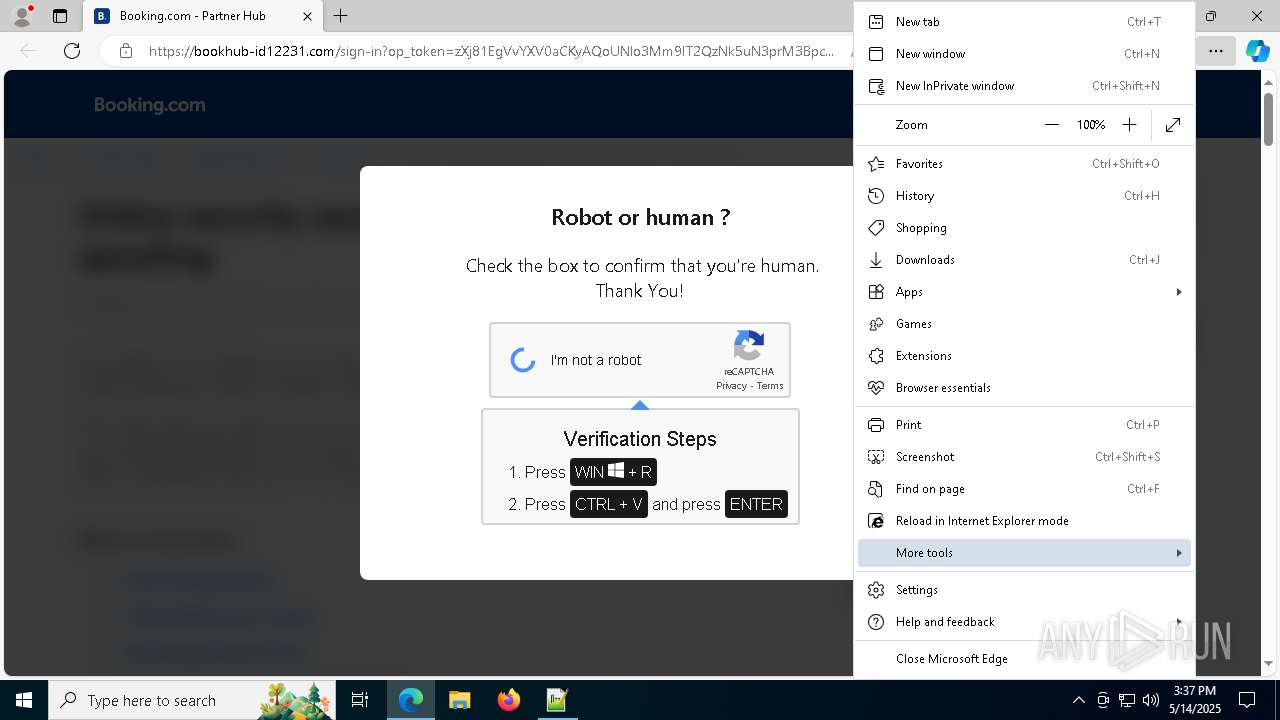
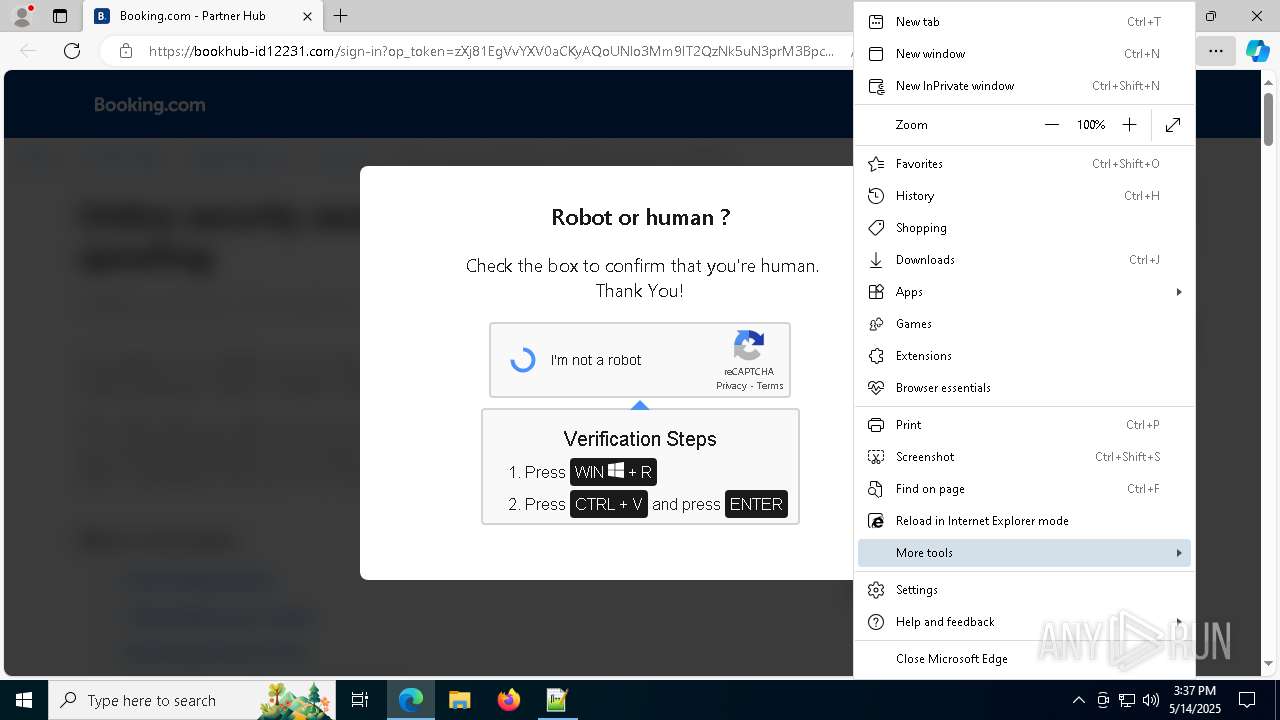
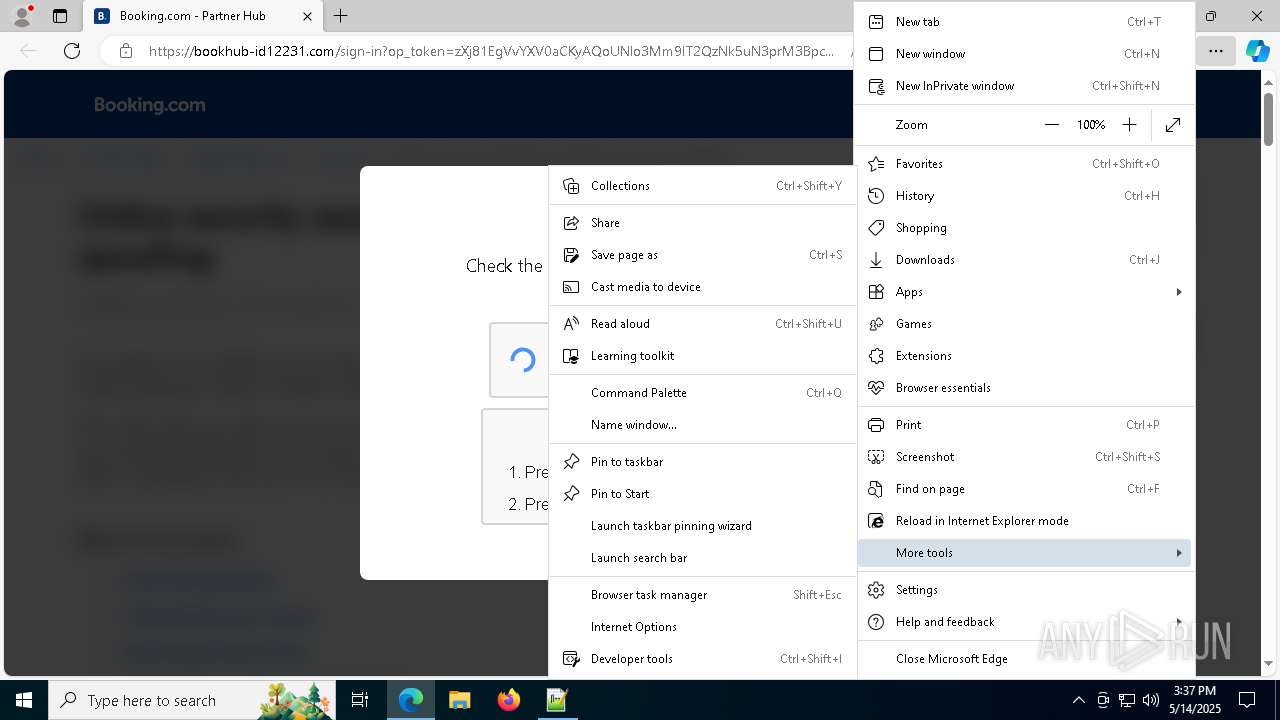
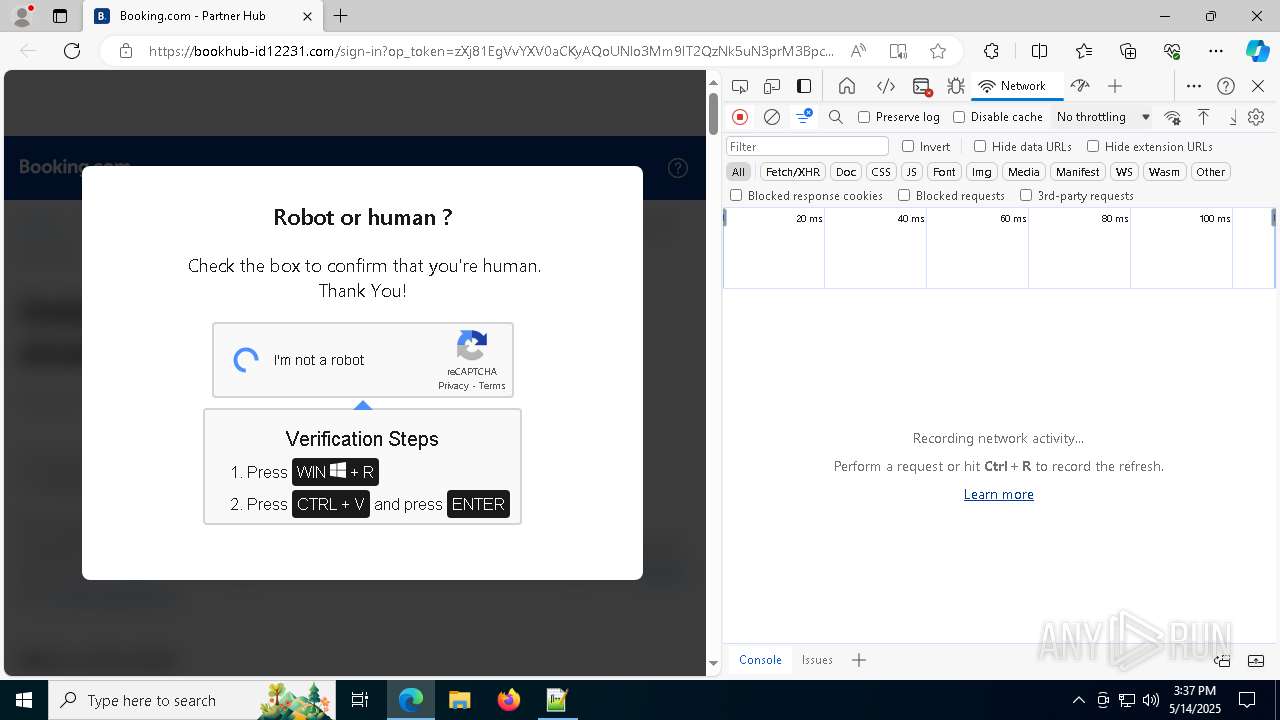
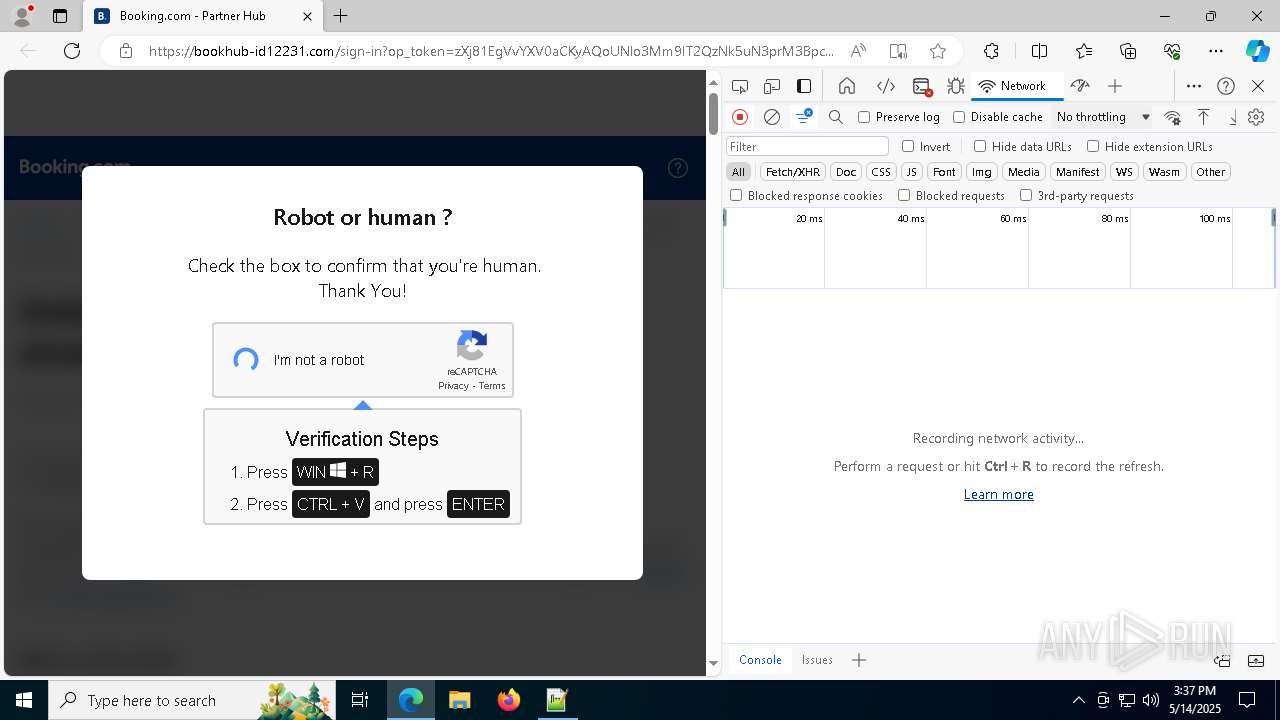
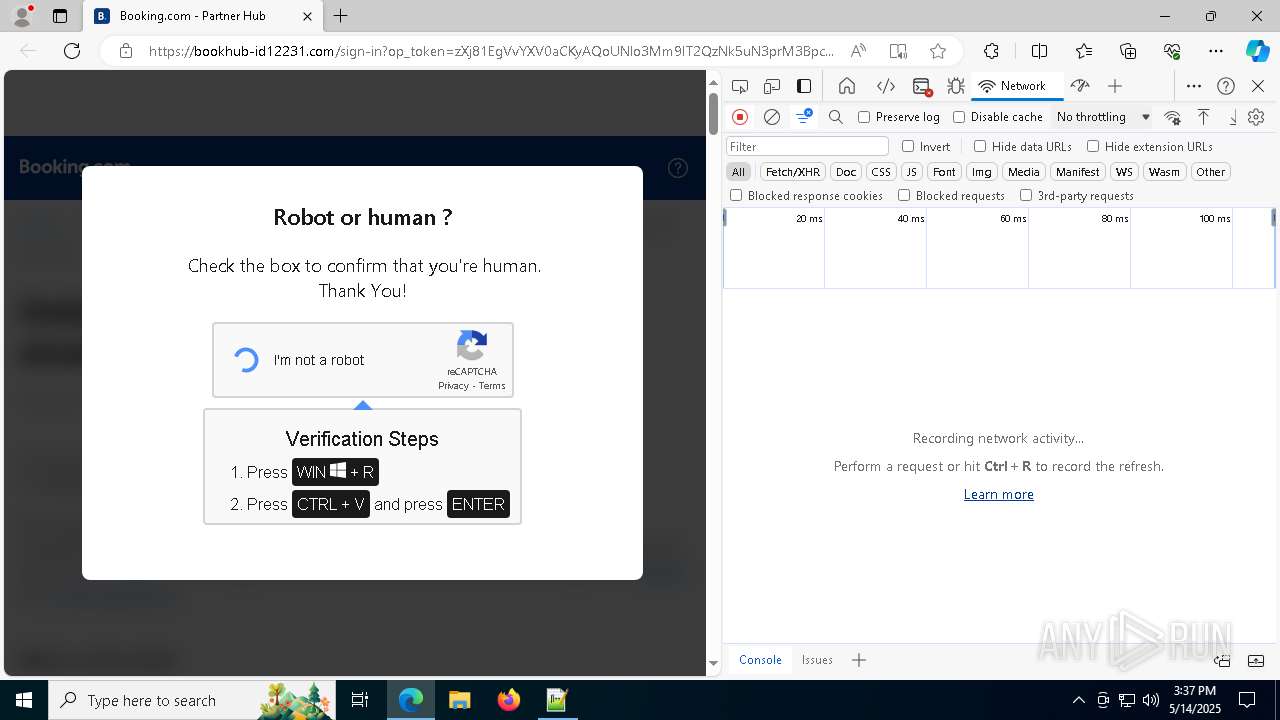
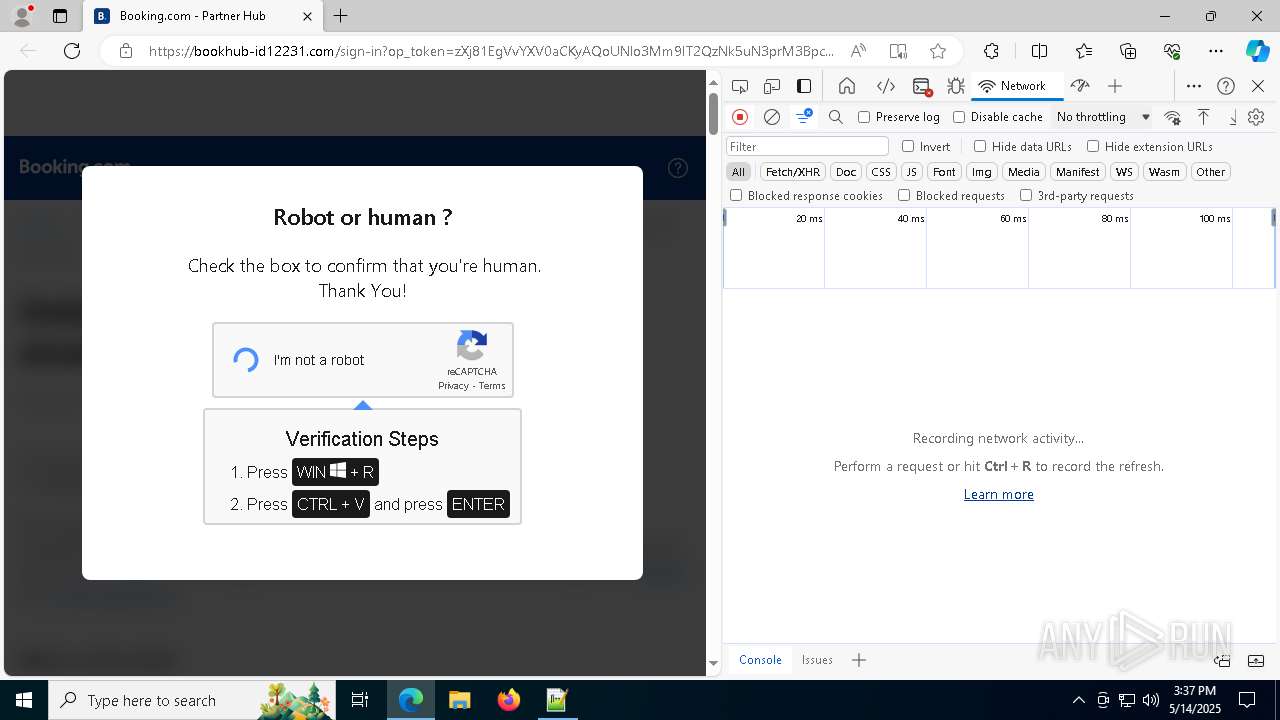
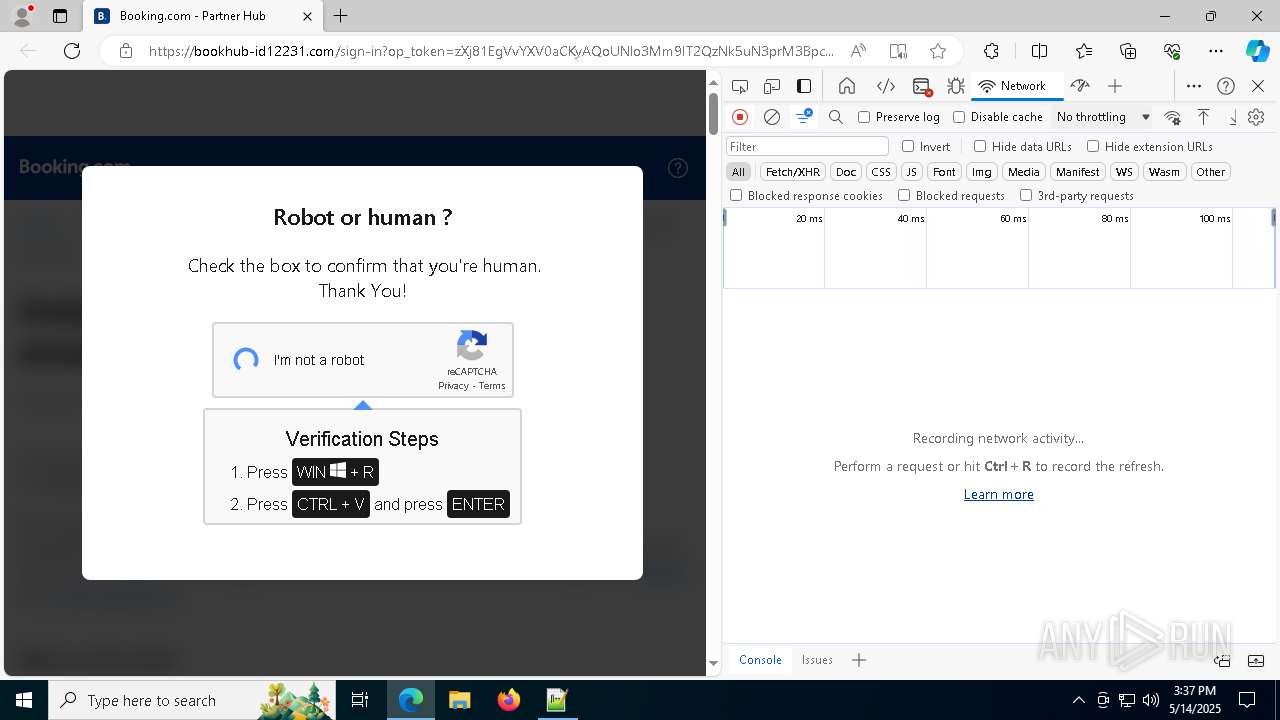
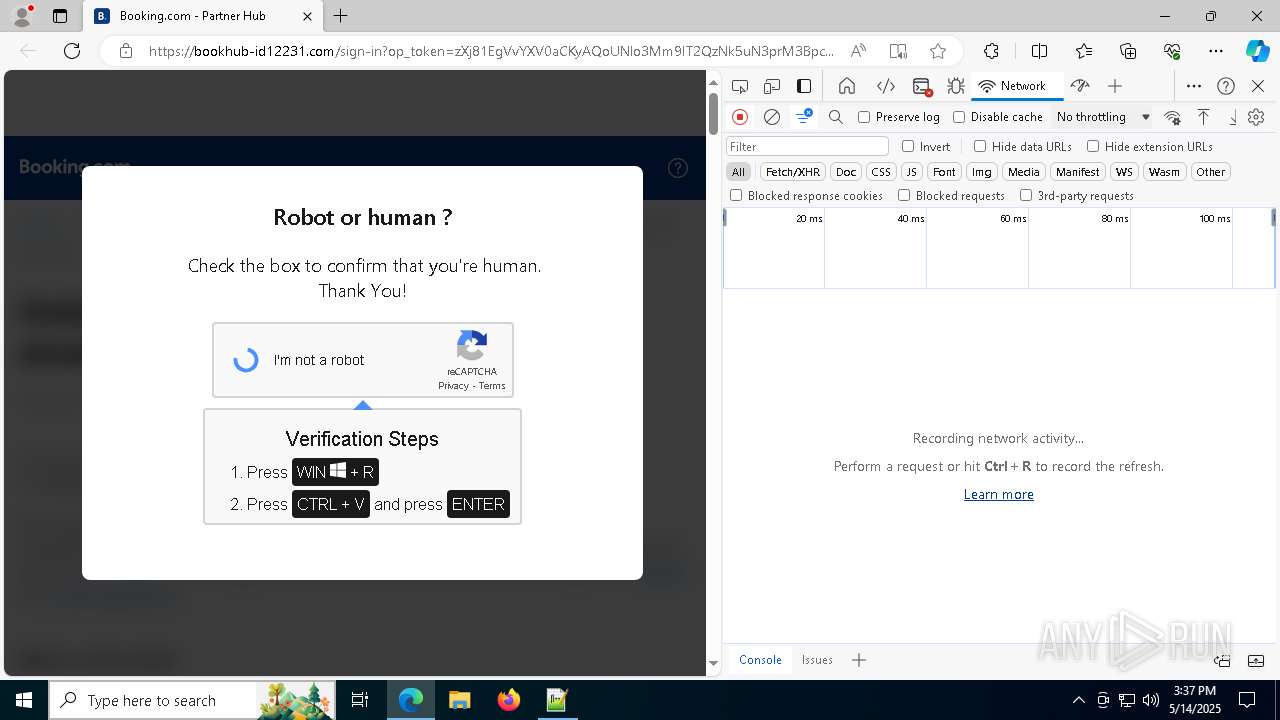
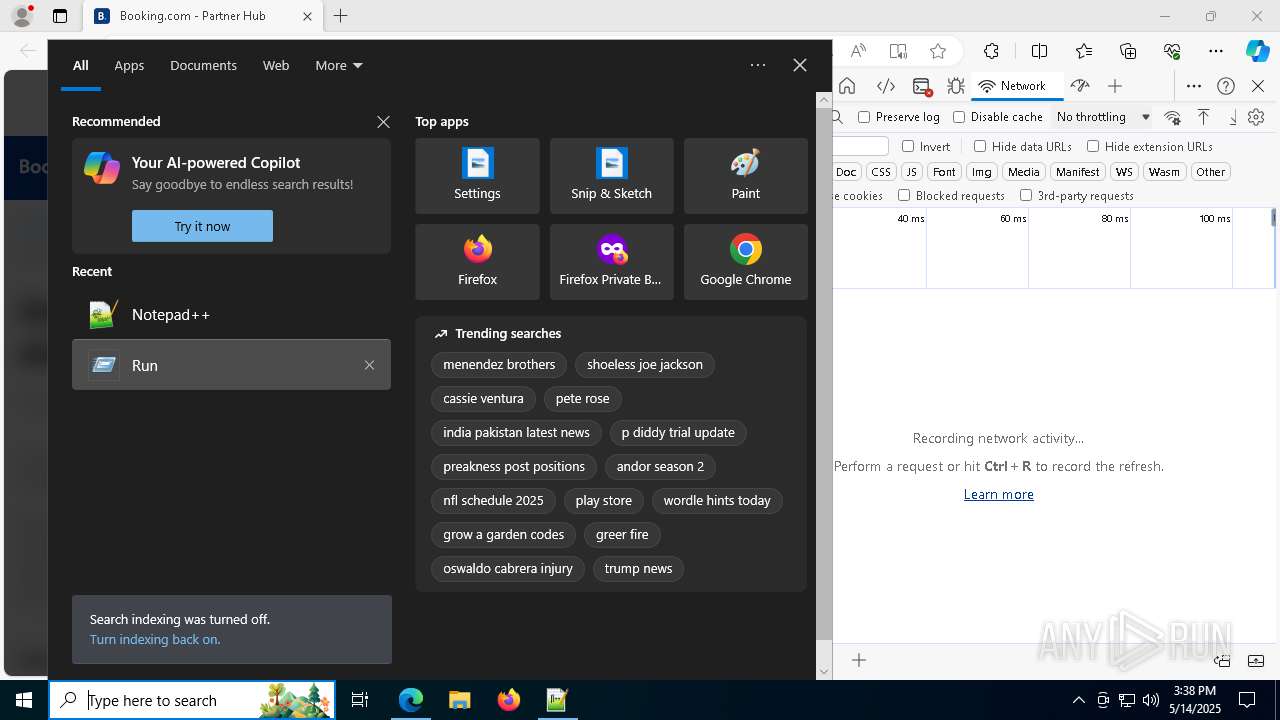
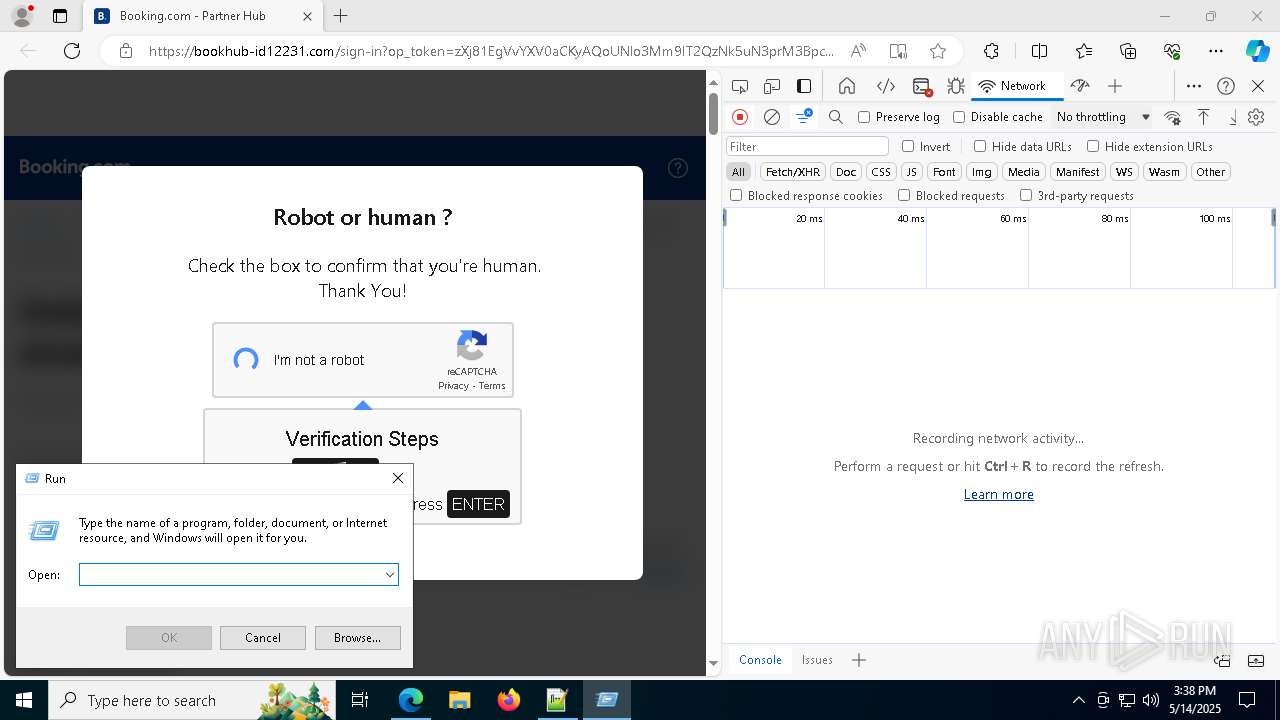
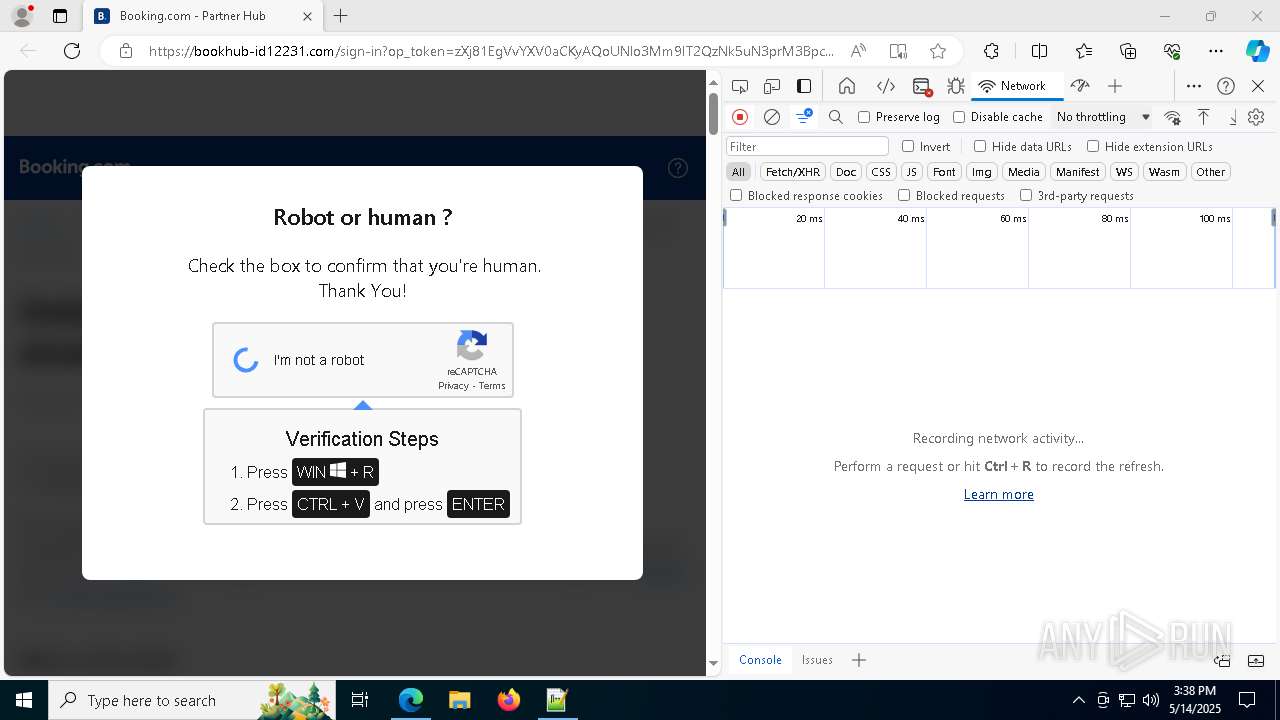
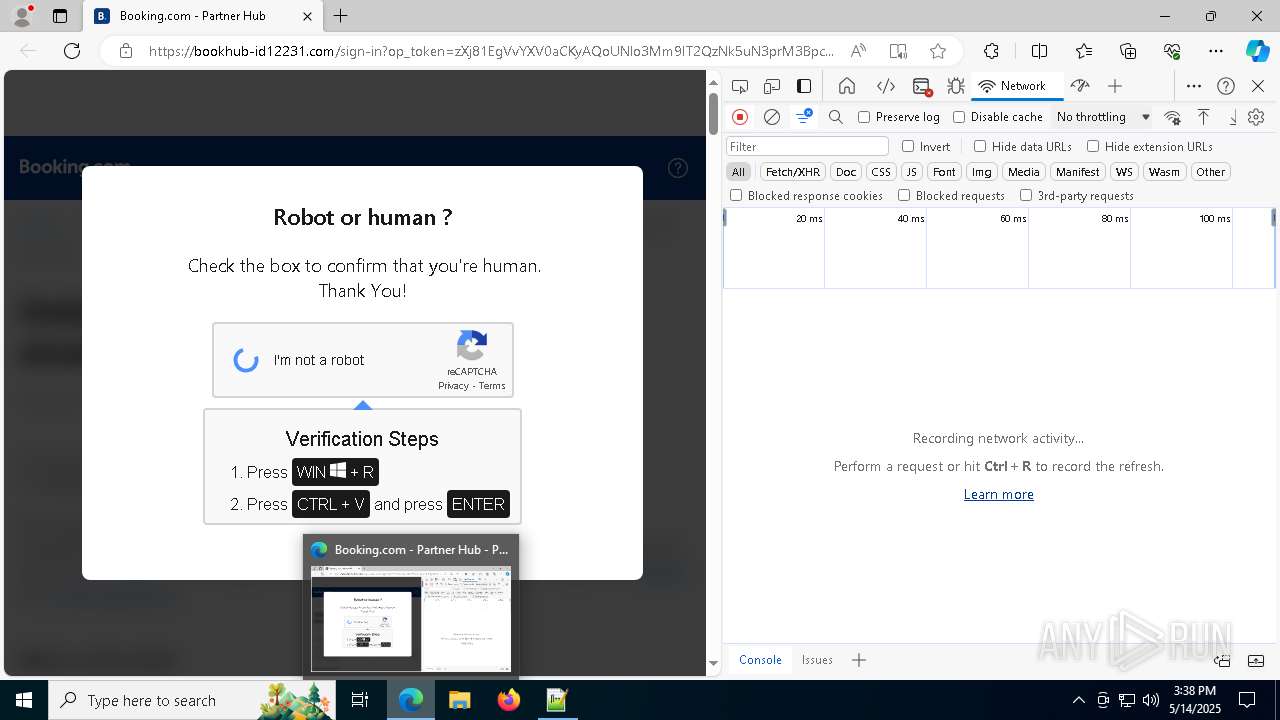
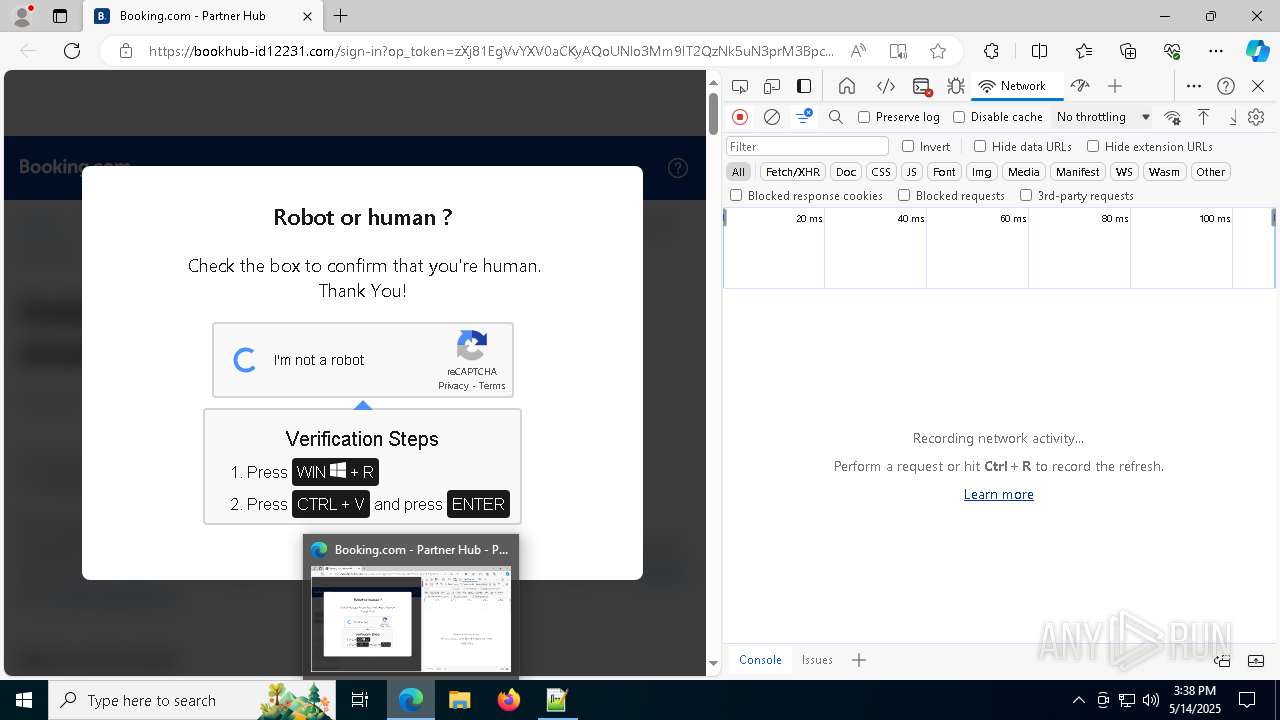
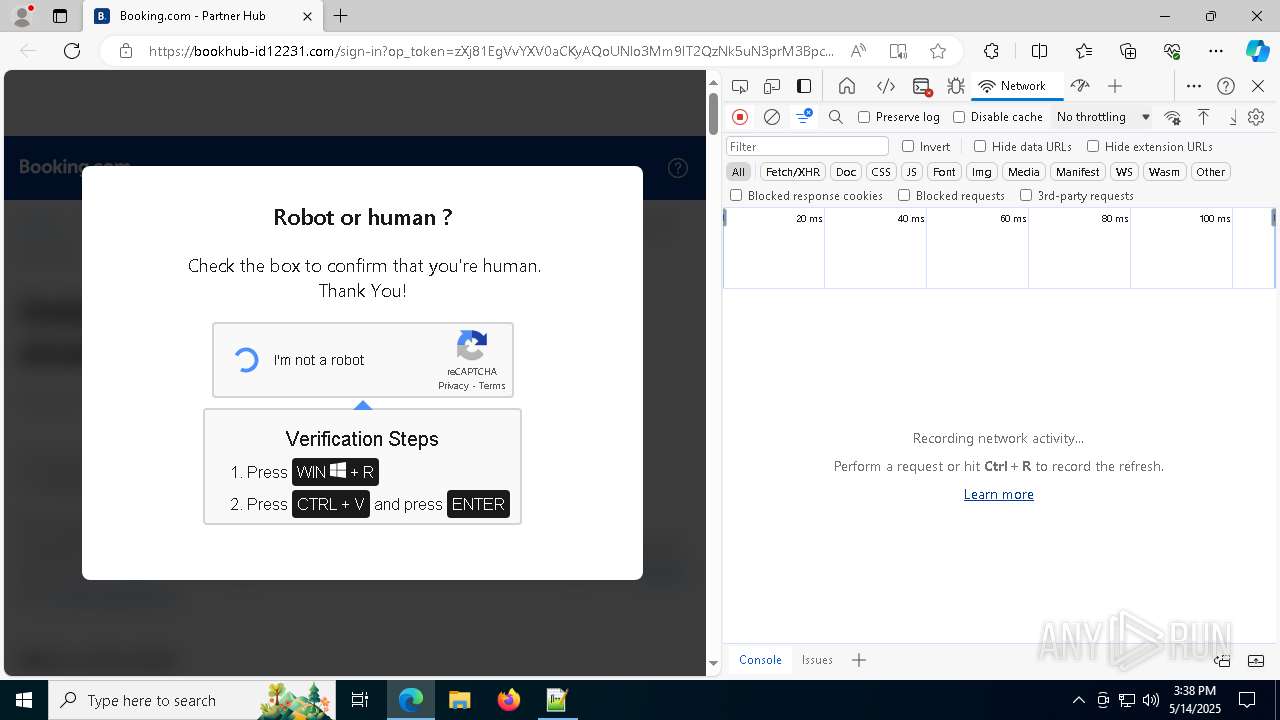
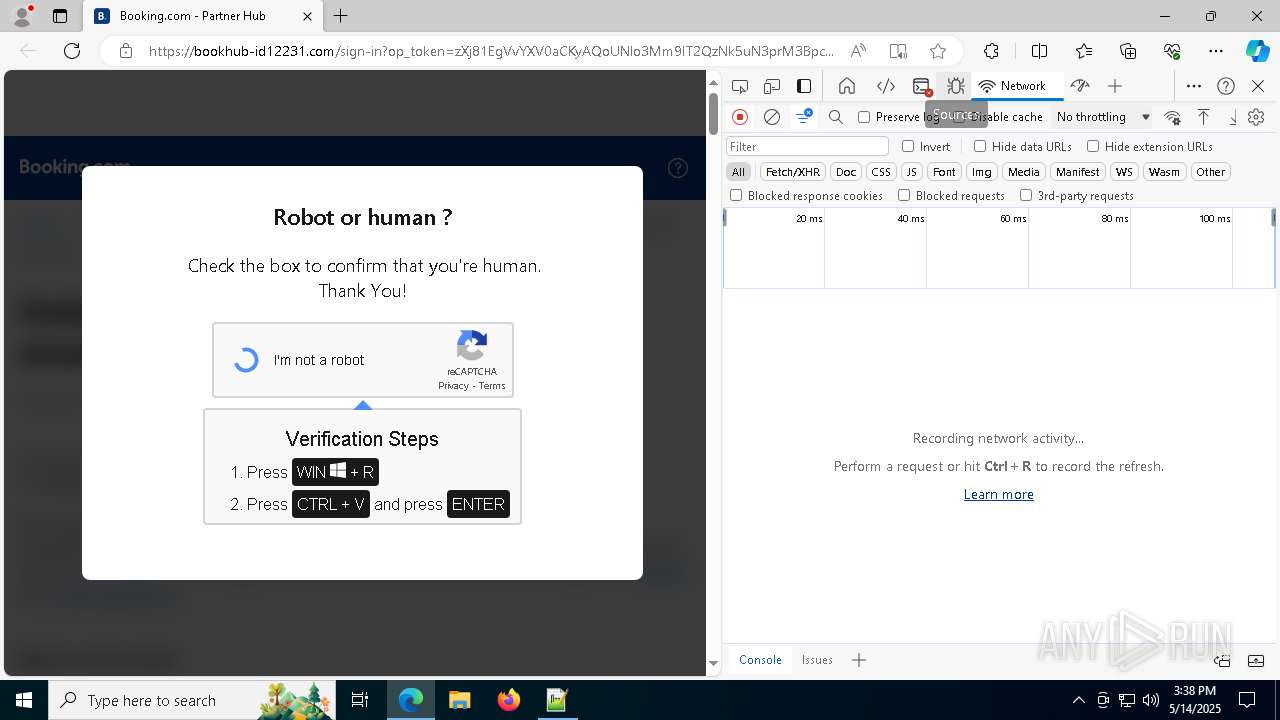
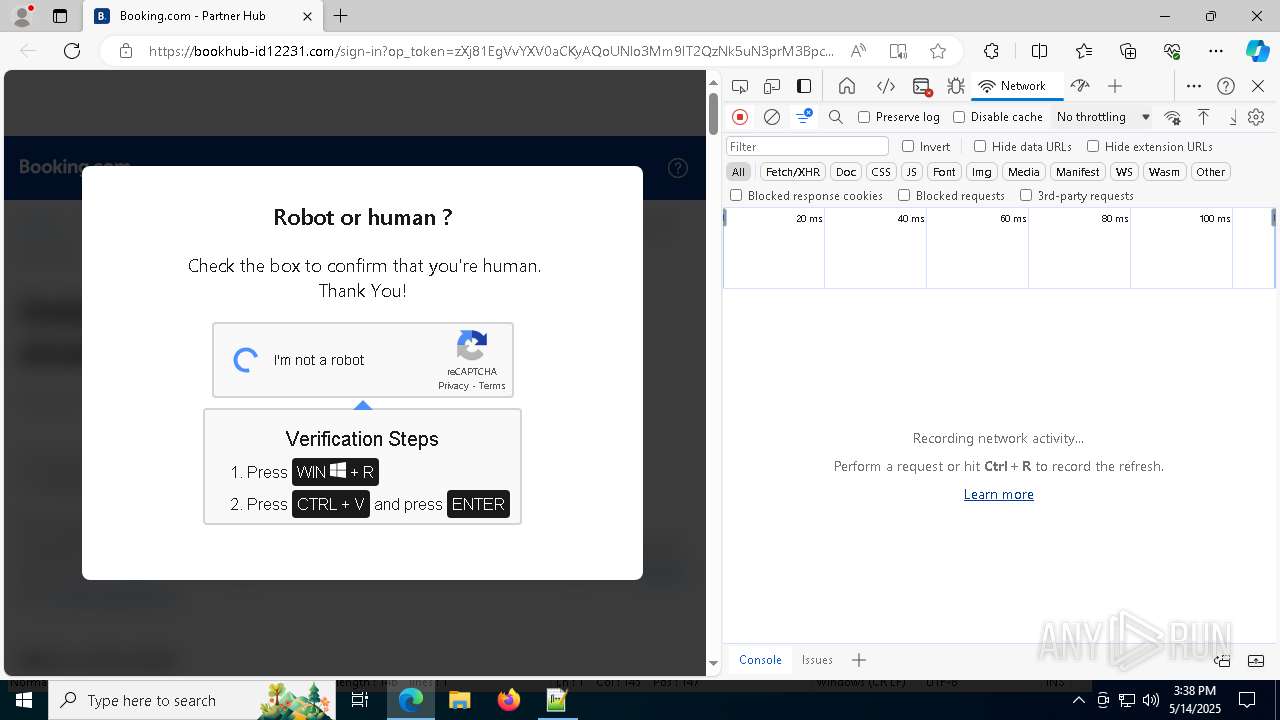
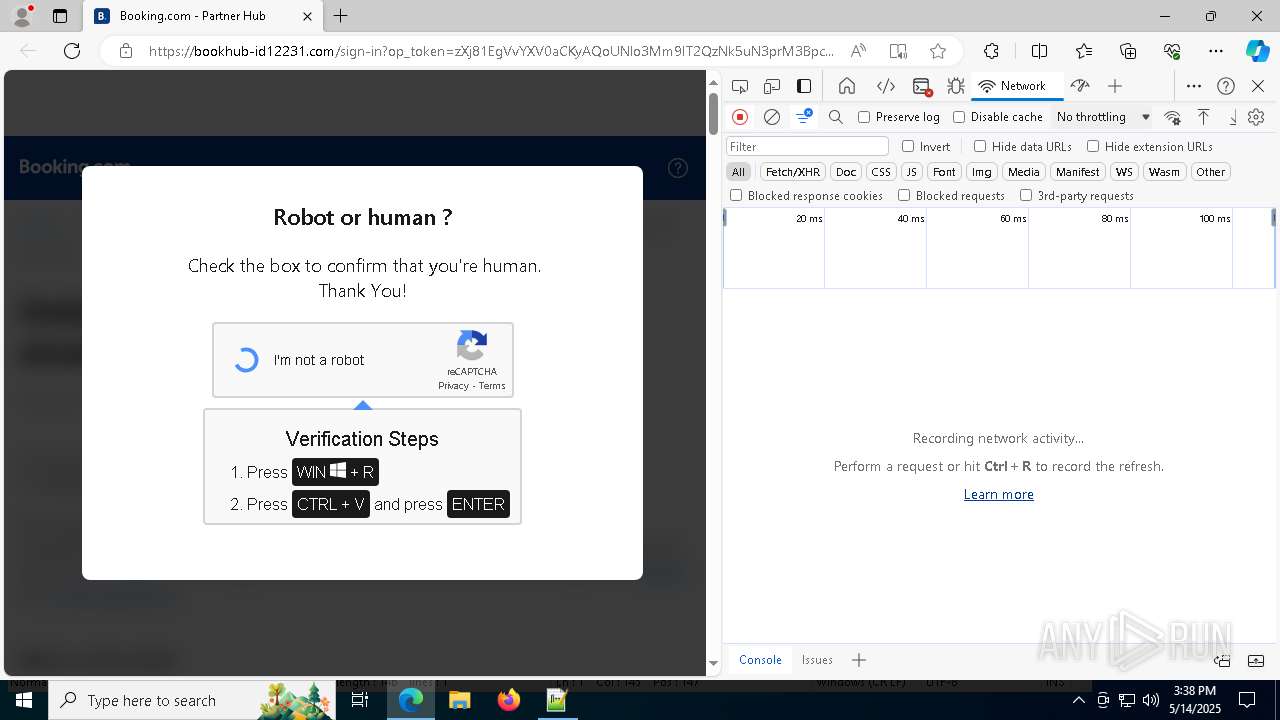
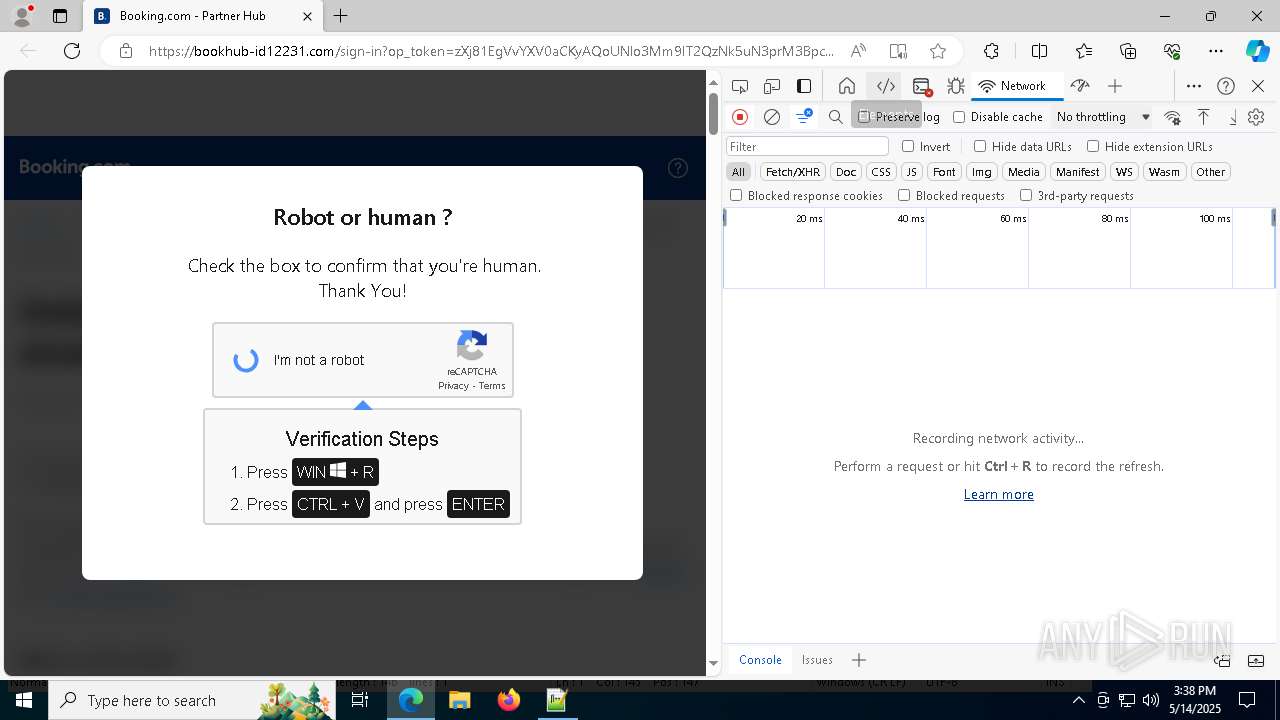
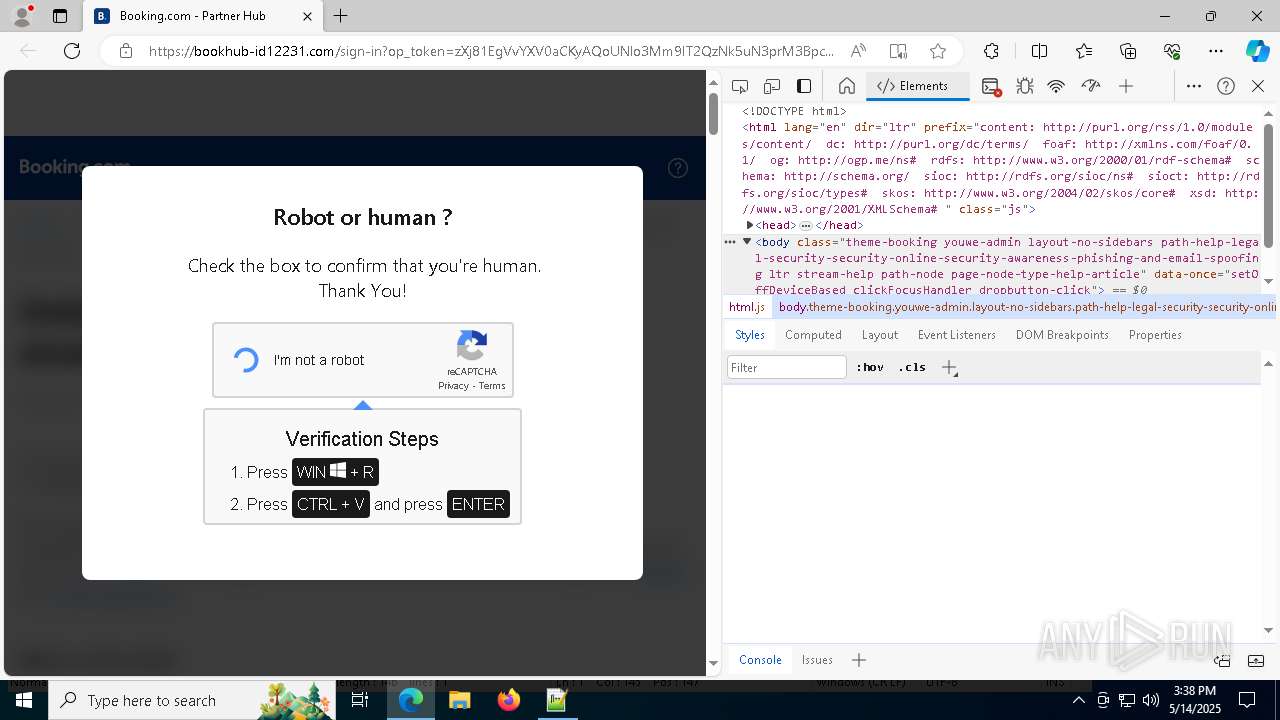
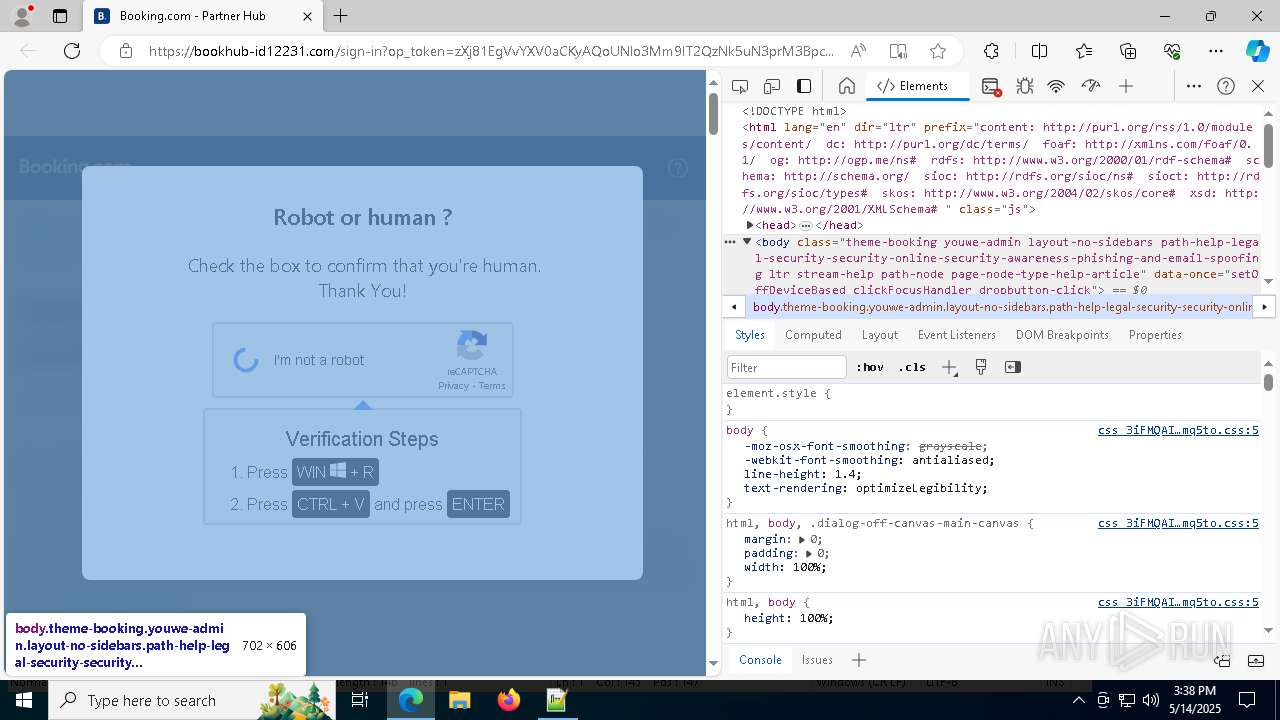
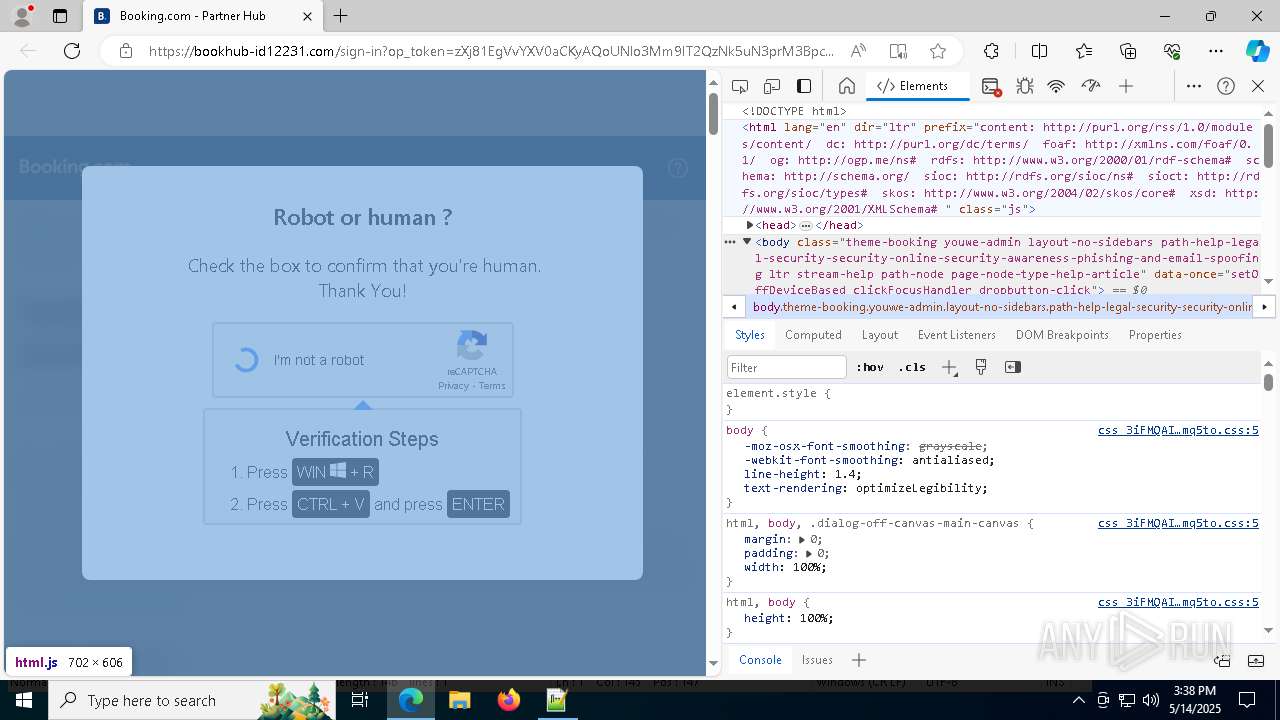
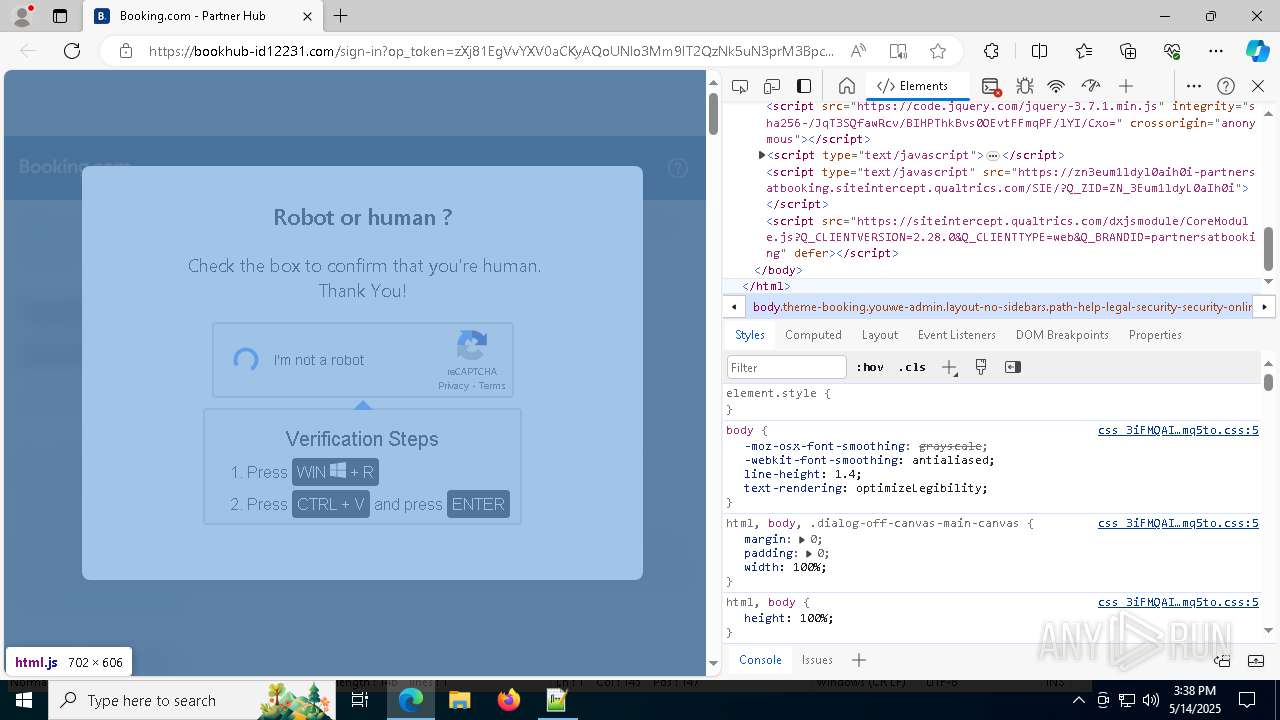
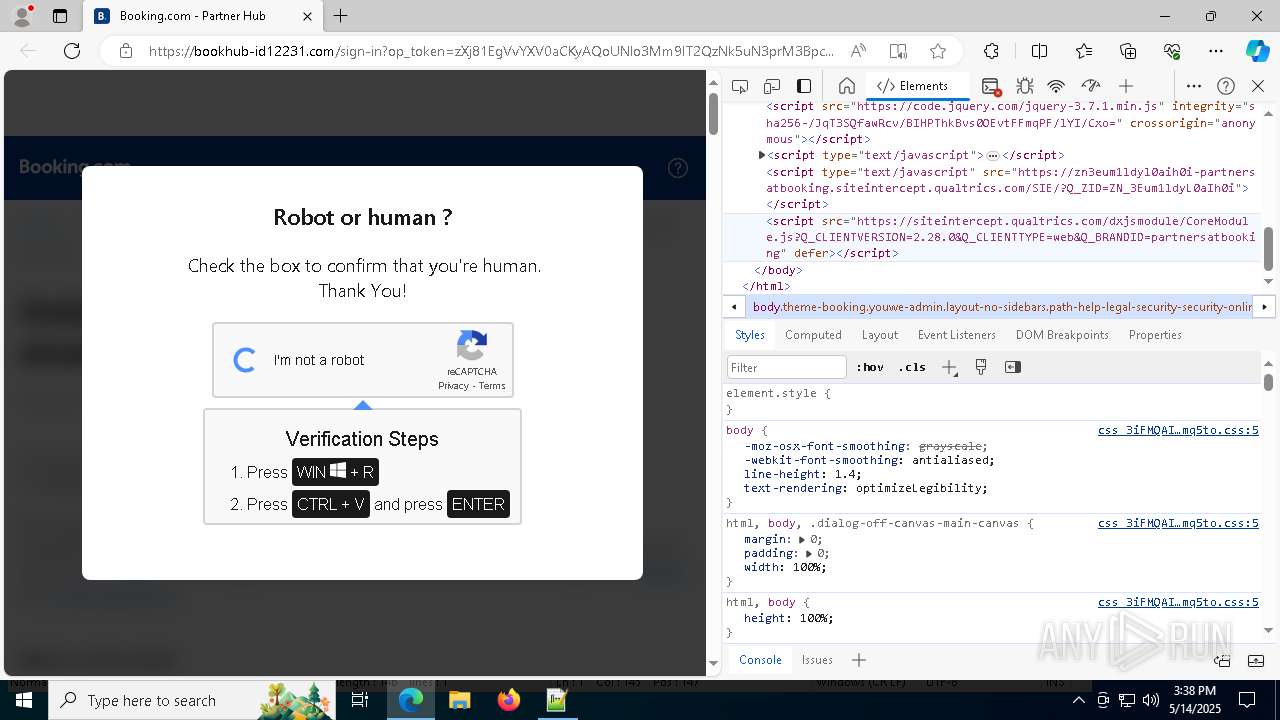
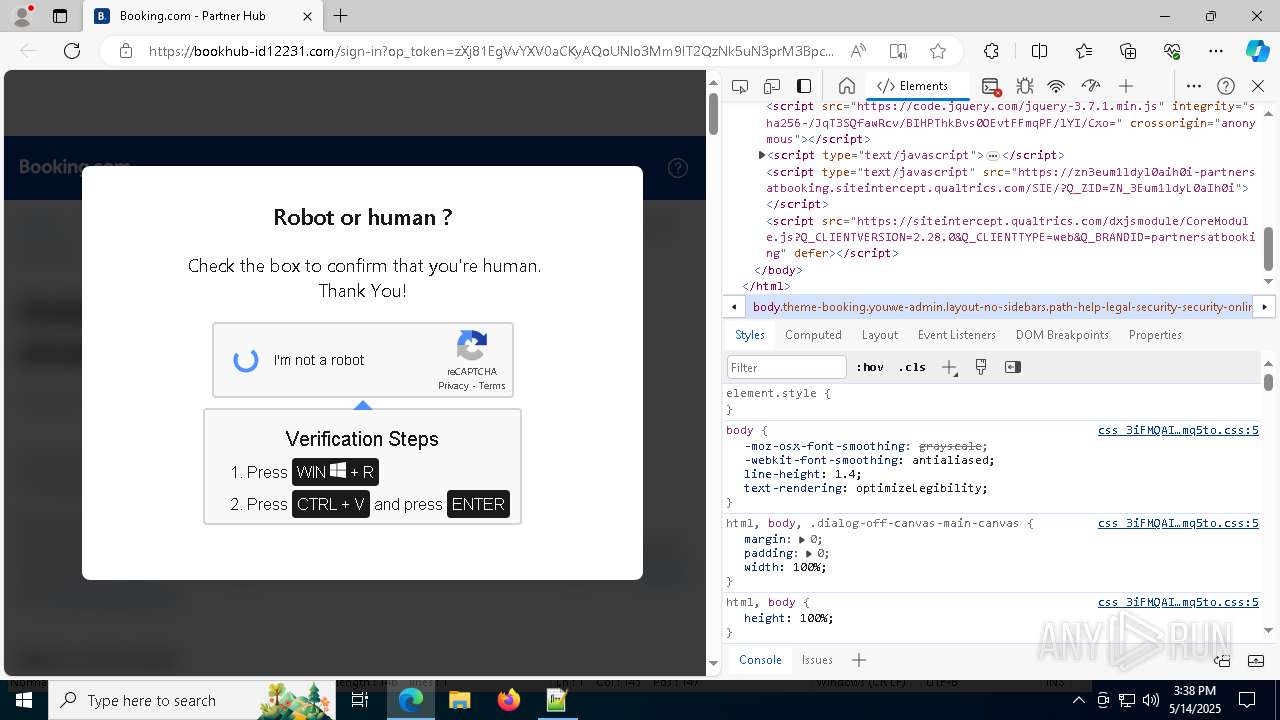
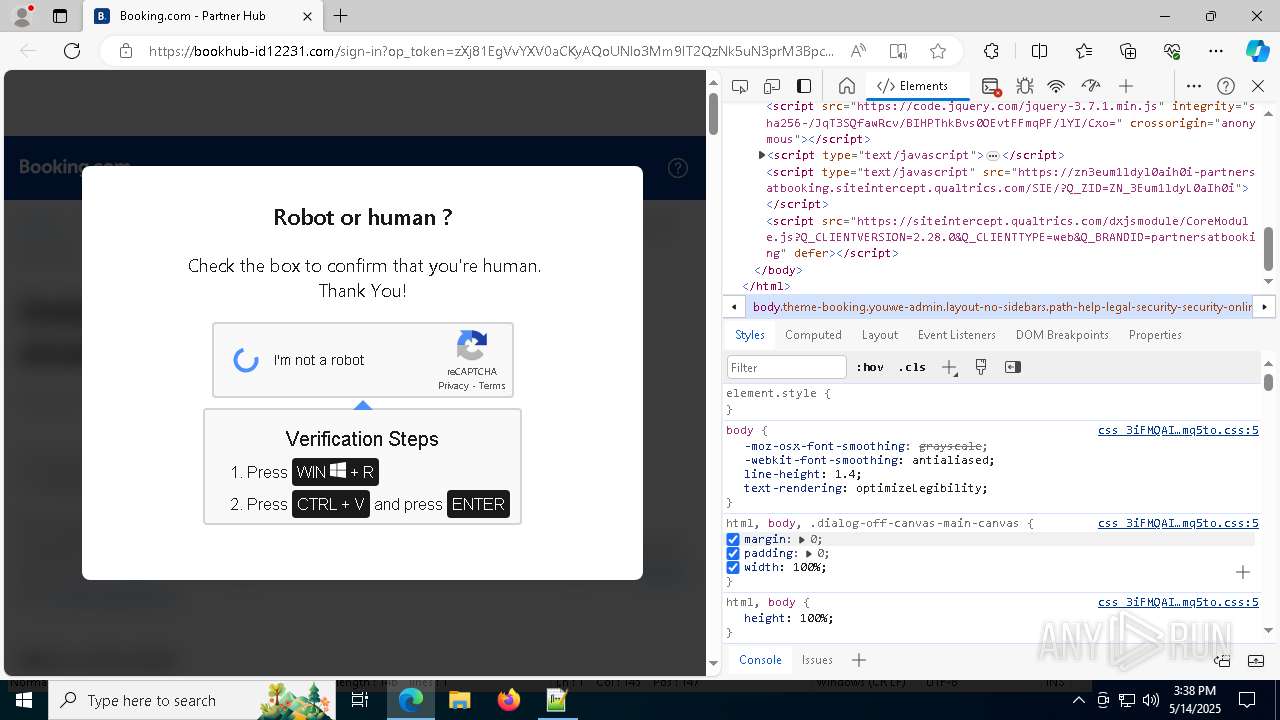
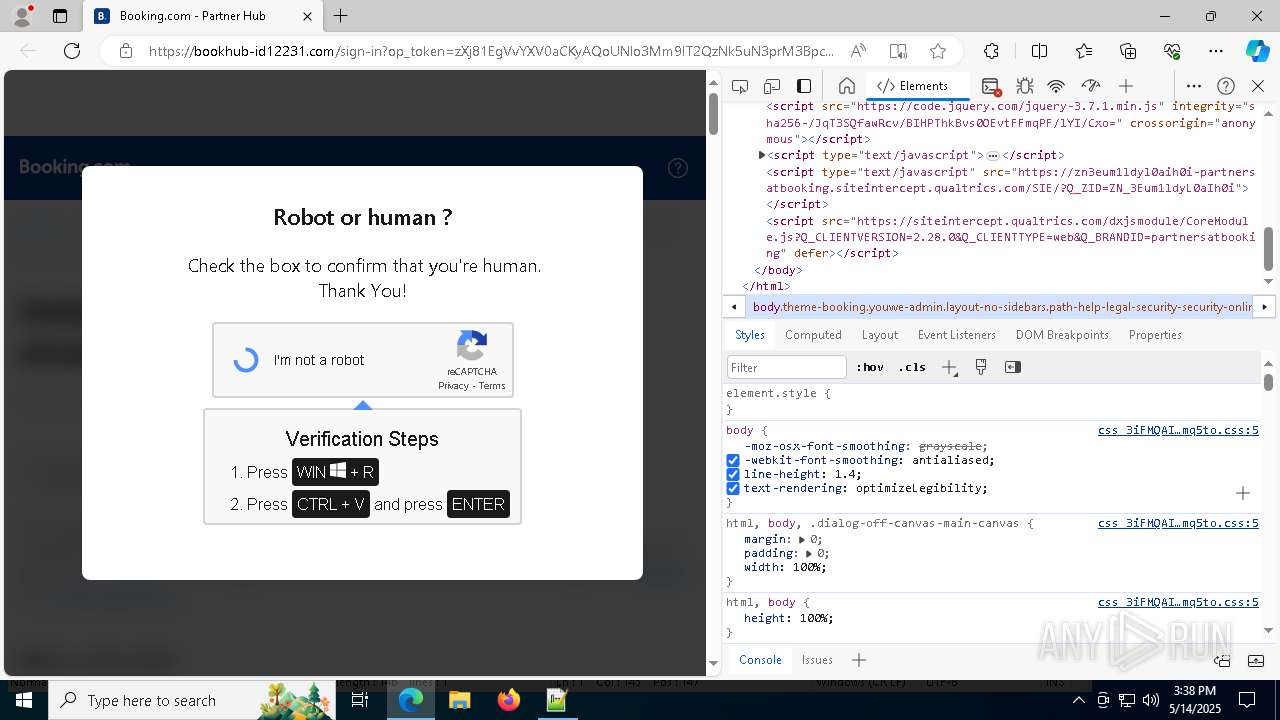
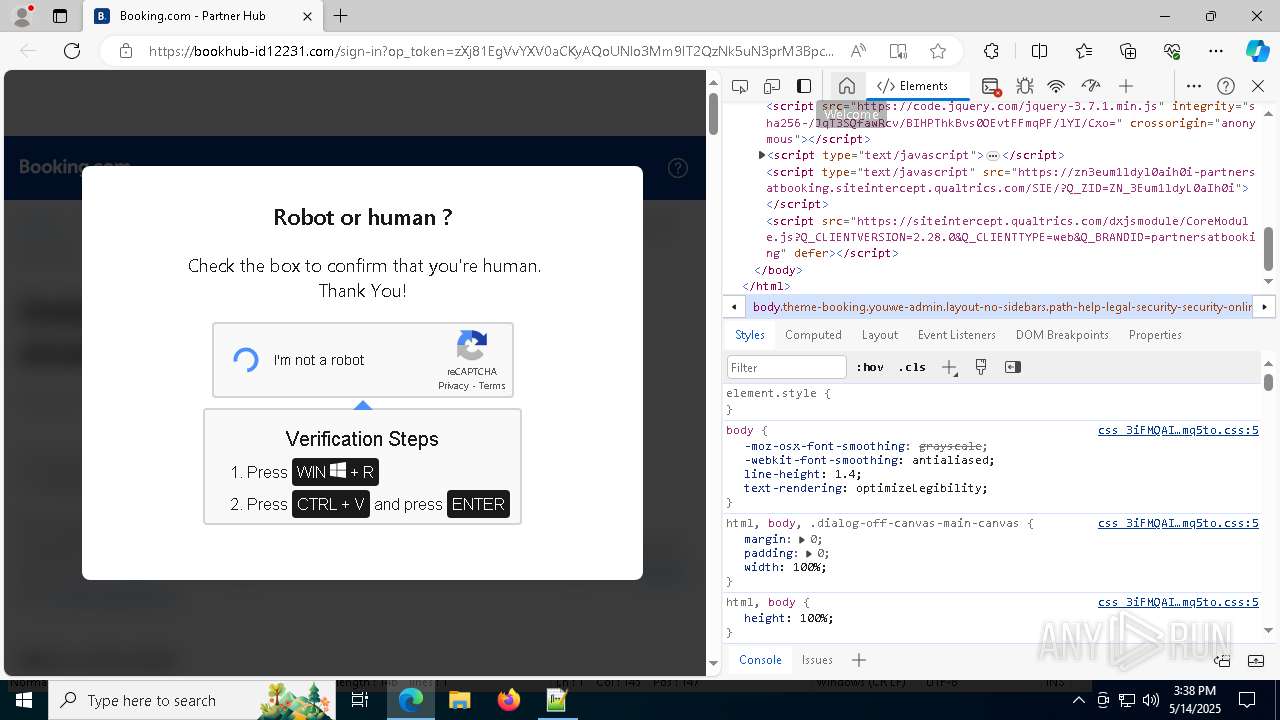
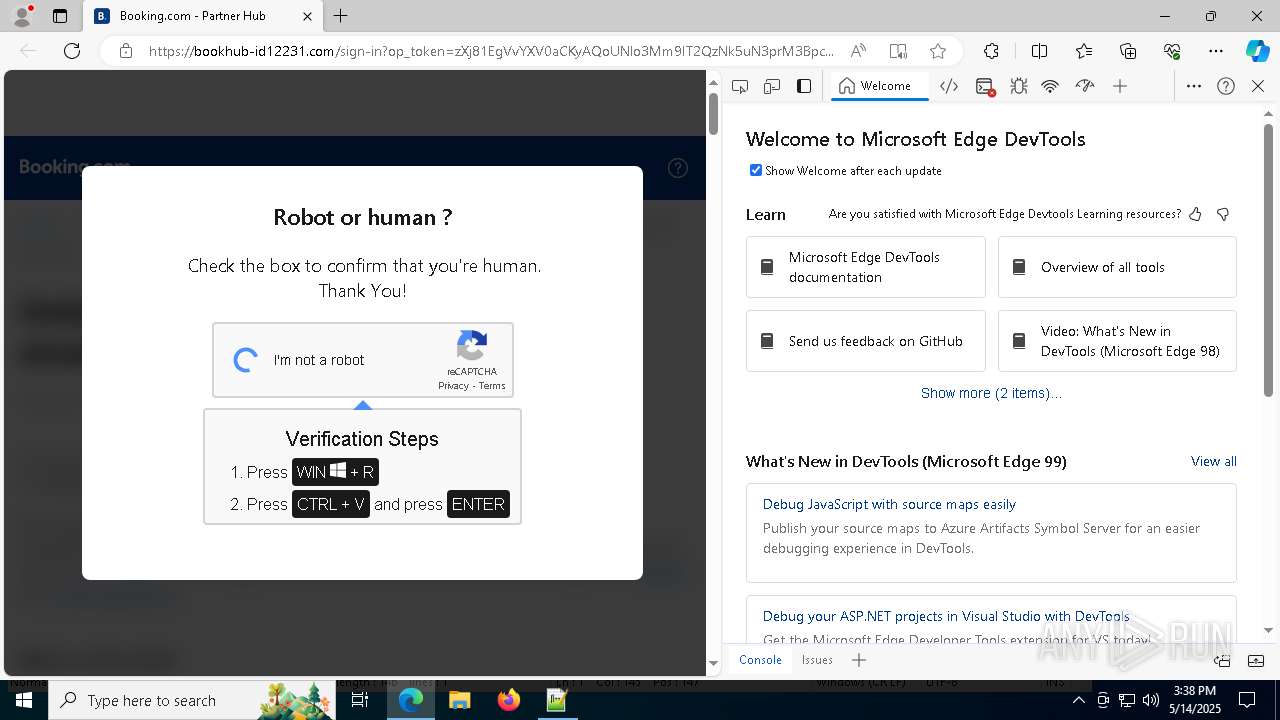
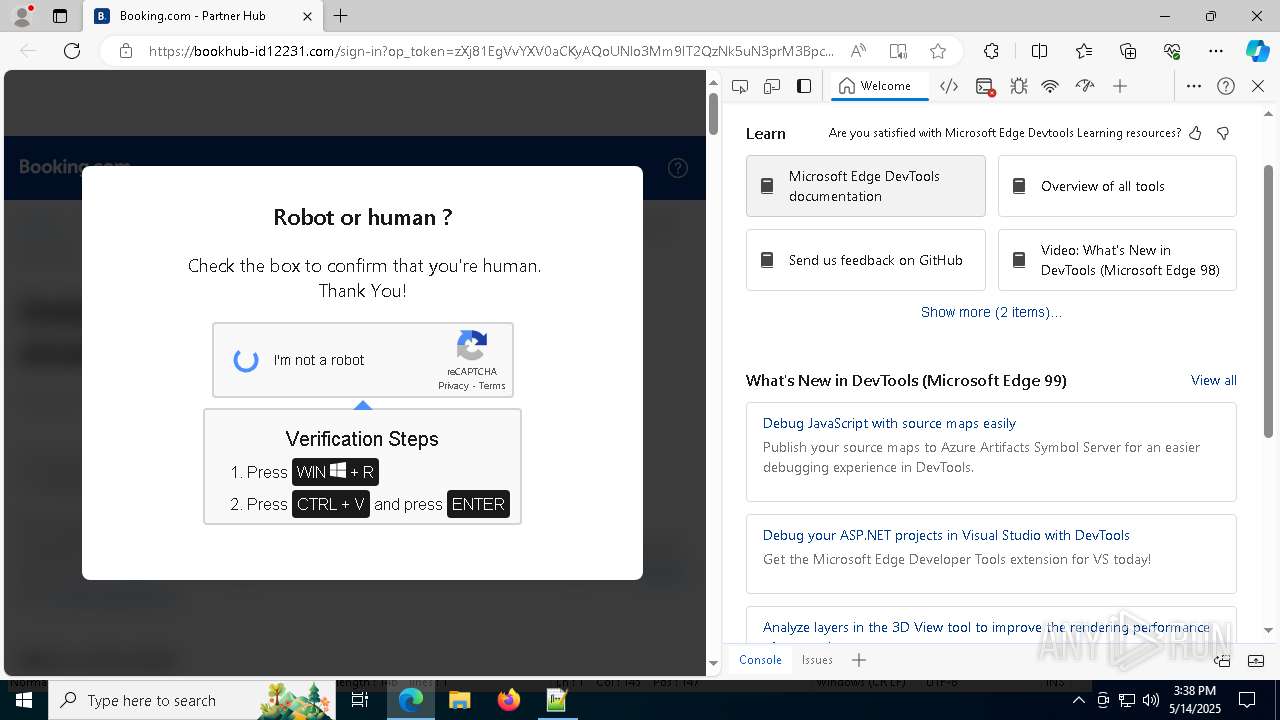
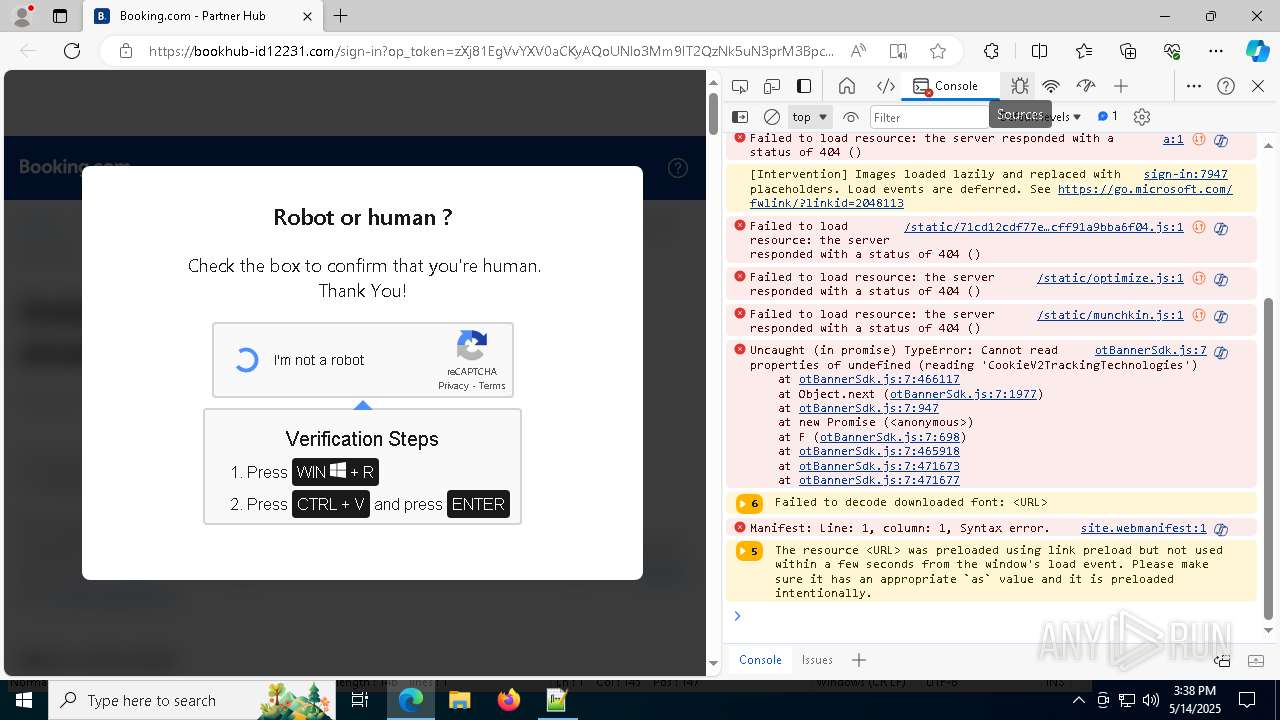
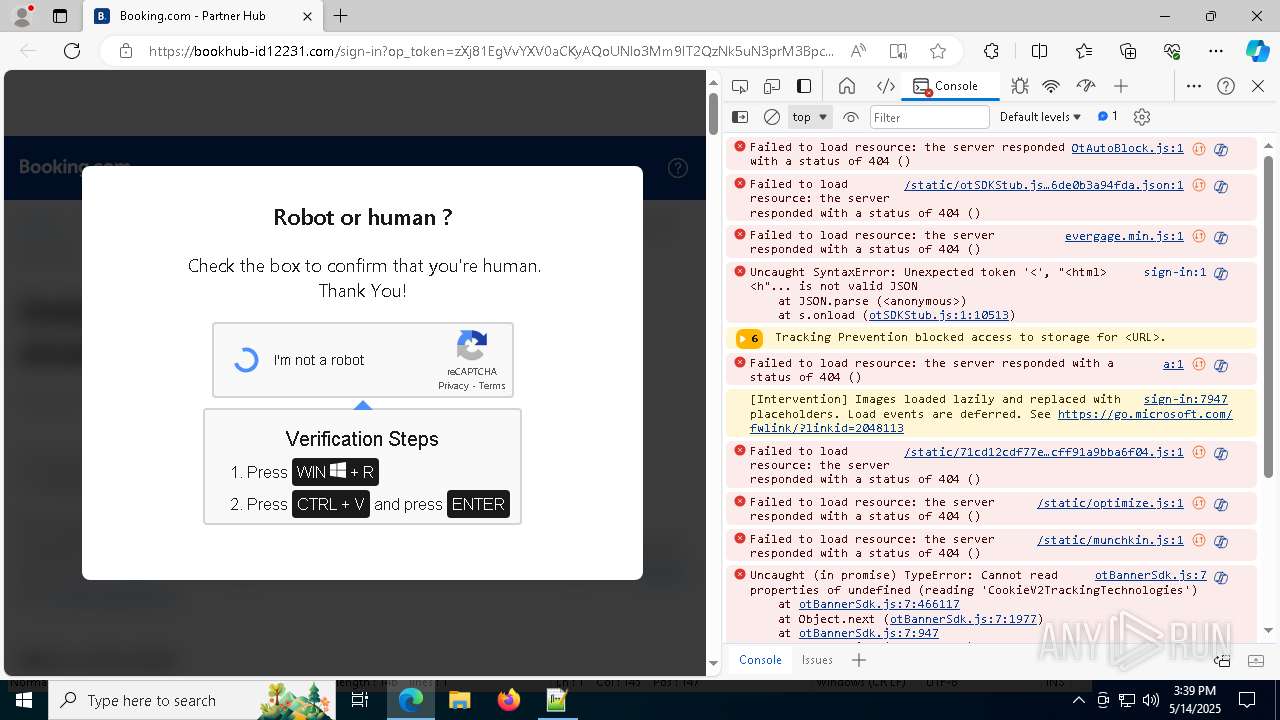
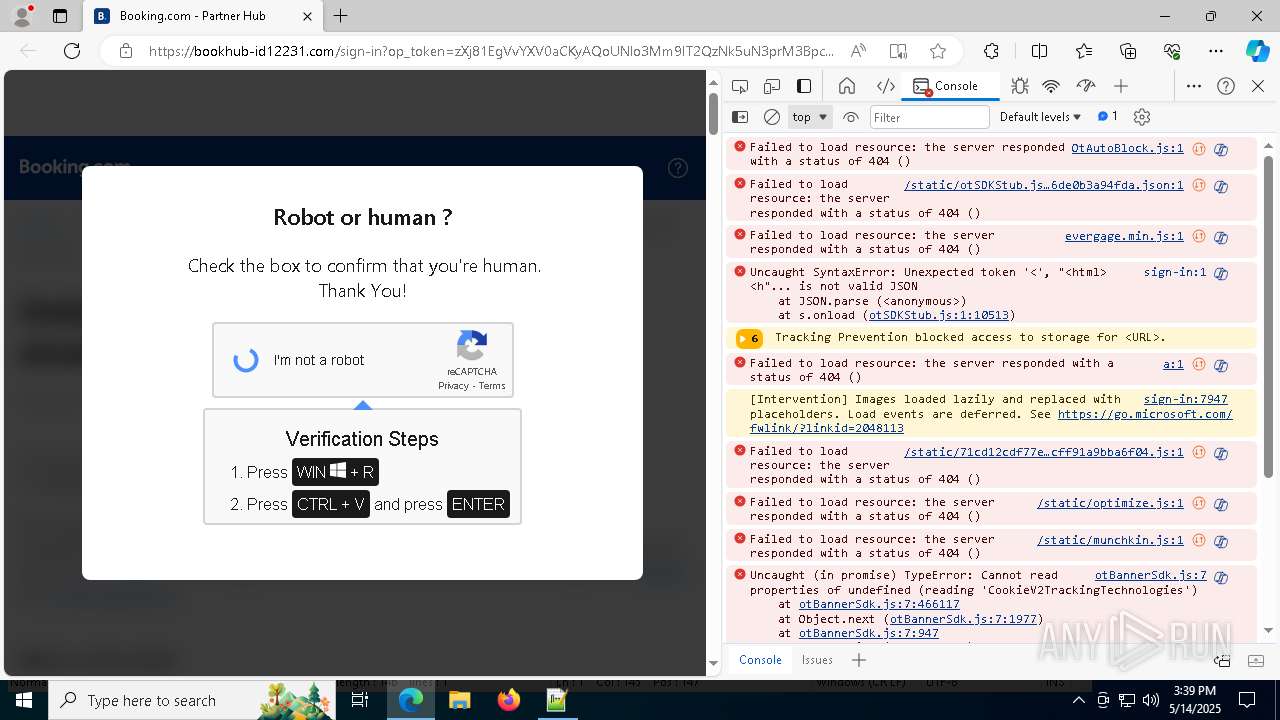
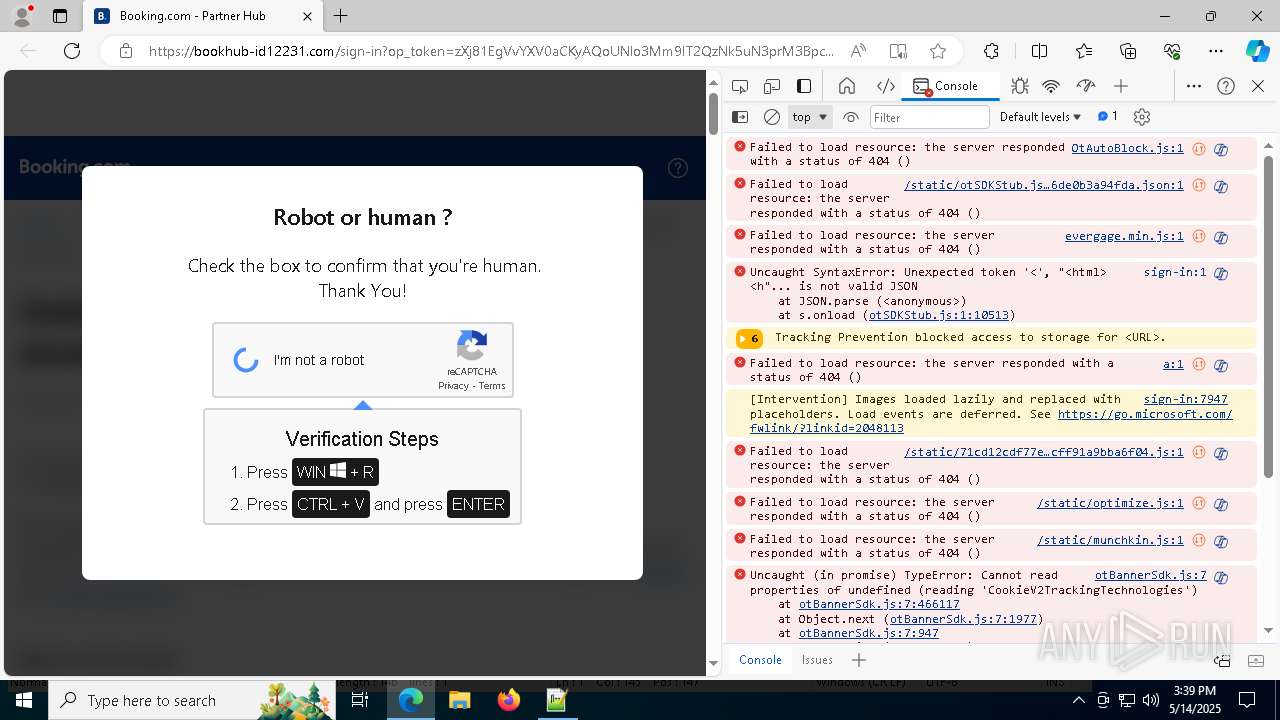
| URL: | bookhub-id12231.com |
| Full analysis: | https://app.any.run/tasks/53d3631f-68c5-490d-95d1-4382157a4efc |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | May 14, 2025, 15:36:02 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | CD0279E7E7EE30566BEB459DD4F8648F |
| SHA1: | 8AE431C267430961B02BFA32AB72DAF556C24CA0 |
| SHA256: | 1B1941A056AC444608F75A45ACEC529CB7DD82B372370F8F58BD461563377705 |
| SSDEEP: | 3:dxBb1KI:dHbAI |
MALICIOUS
Adds path to the Windows Defender exclusion list
- cbe92.exe (PID: 8048)
- cmd.exe (PID: 2236)
- cbe92.exe (PID: 5008)
- cmd.exe (PID: 1388)
ASYNCRAT has been detected (SURICATA)
- tybd7.exe (PID: 7596)
Changes Windows Defender settings
- cmd.exe (PID: 1388)
- cmd.exe (PID: 2236)
ASYNCRAT has been detected (YARA)
- tybd7.exe (PID: 7596)
SUSPICIOUS
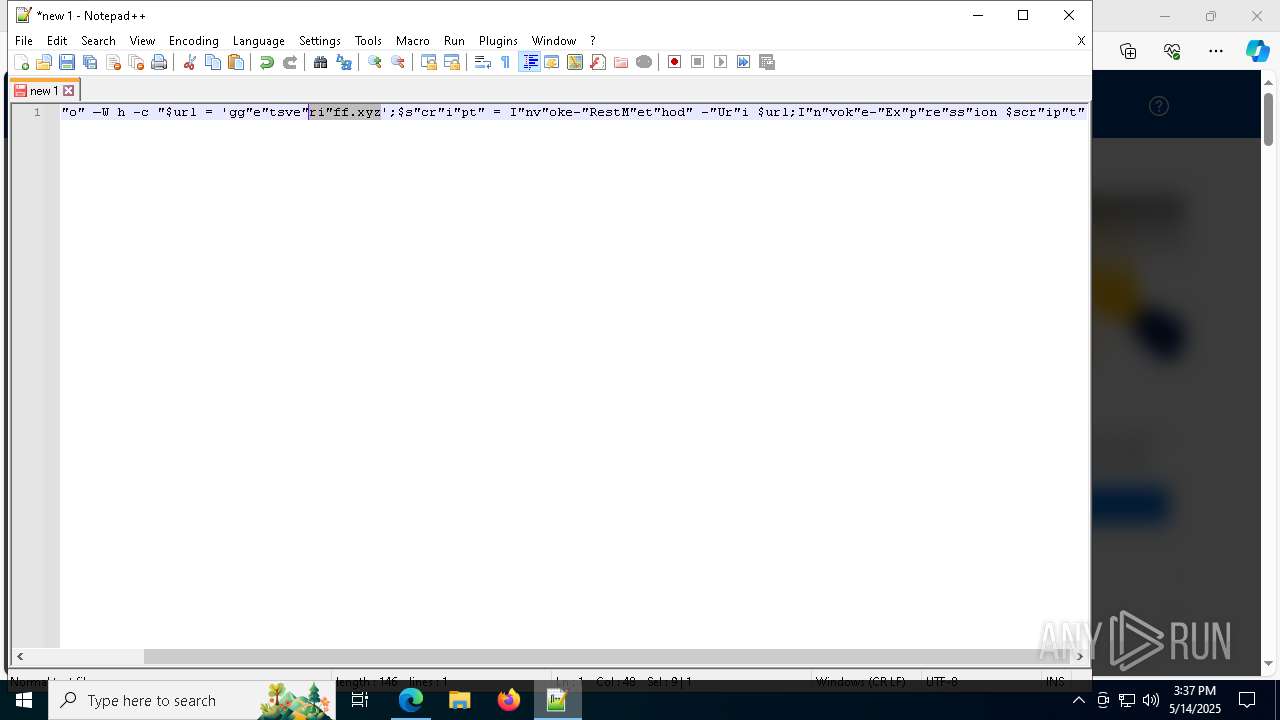
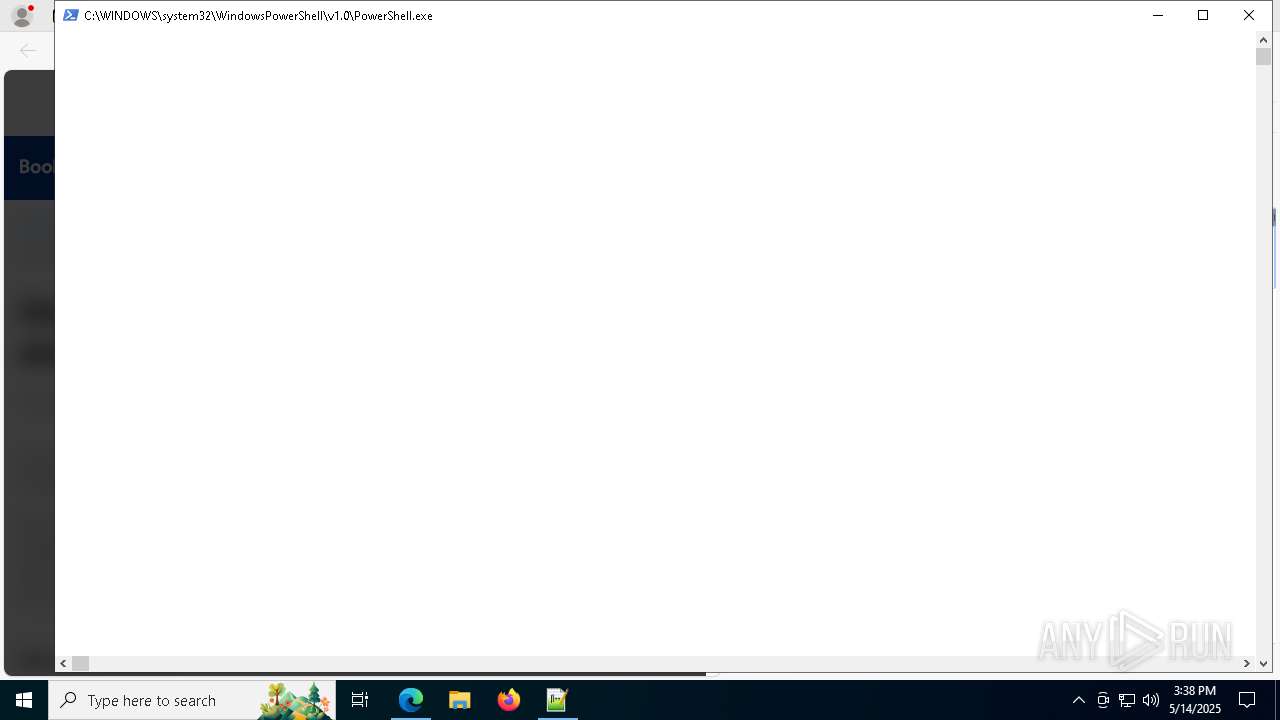
Process requests binary or script from the Internet
- powershell.exe (PID: 6036)
- curl.exe (PID: 7600)
- powershell.exe (PID: 1116)
- curl.exe (PID: 6852)
Executable content was dropped or overwritten
- powershell.exe (PID: 6036)
- curl.exe (PID: 7600)
Reads the date of Windows installation
- cbe92.exe (PID: 8048)
Starts CMD.EXE for commands execution
- cbe92.exe (PID: 8048)
- cbe92.exe (PID: 5008)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 2236)
- cmd.exe (PID: 1388)
Potential Corporate Privacy Violation
- powershell.exe (PID: 6036)
- curl.exe (PID: 7600)
- curl.exe (PID: 6852)
- powershell.exe (PID: 1116)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2236)
- cmd.exe (PID: 1388)
Reads security settings of Internet Explorer
- cbe92.exe (PID: 8048)
Execution of CURL command
- cbe92.exe (PID: 8048)
- cbe92.exe (PID: 5008)
Connects to unusual port
- tybd7.exe (PID: 7596)
Contacting a server suspected of hosting an CnC
- tybd7.exe (PID: 7596)
Uses WMIC.EXE to obtain computer system information
- tybd7.exe (PID: 7596)
INFO
Reads the computer name
- identity_helper.exe (PID: 6132)
- cbe92.exe (PID: 8048)
- curl.exe (PID: 7600)
Application launched itself
- msedge.exe (PID: 1852)
Checks supported languages
- identity_helper.exe (PID: 6132)
- cbe92.exe (PID: 8048)
- curl.exe (PID: 7600)
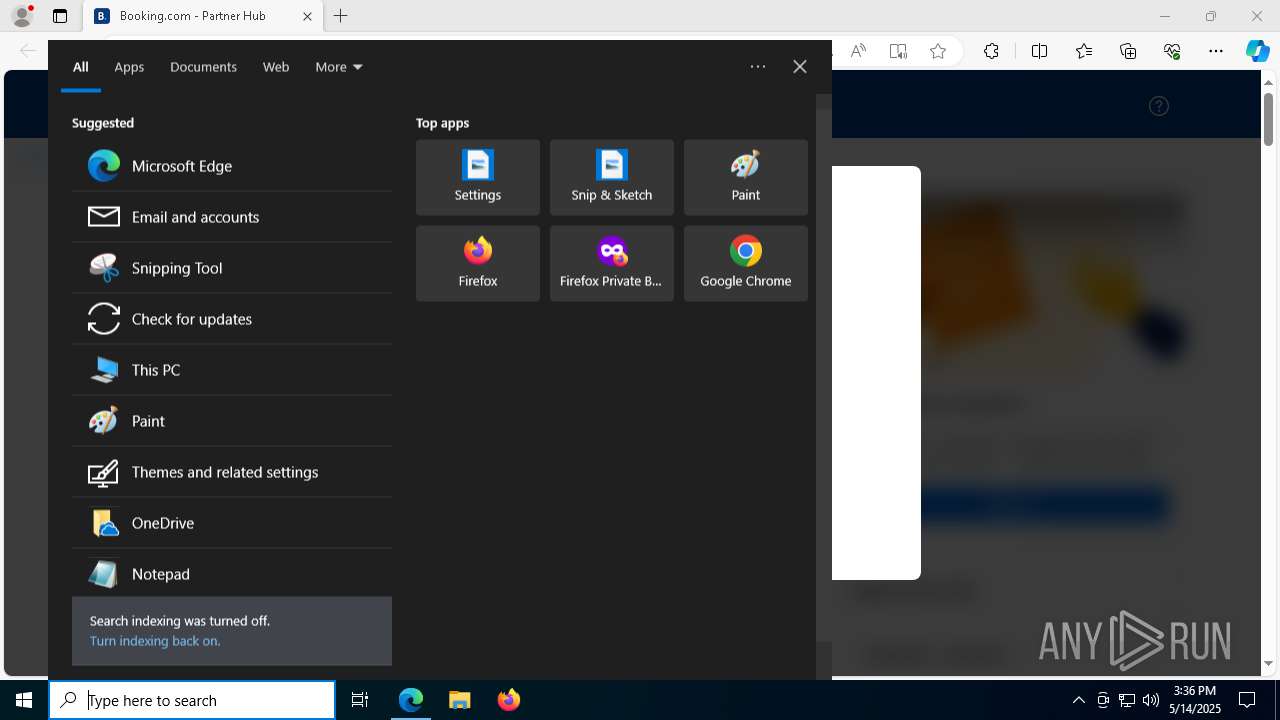
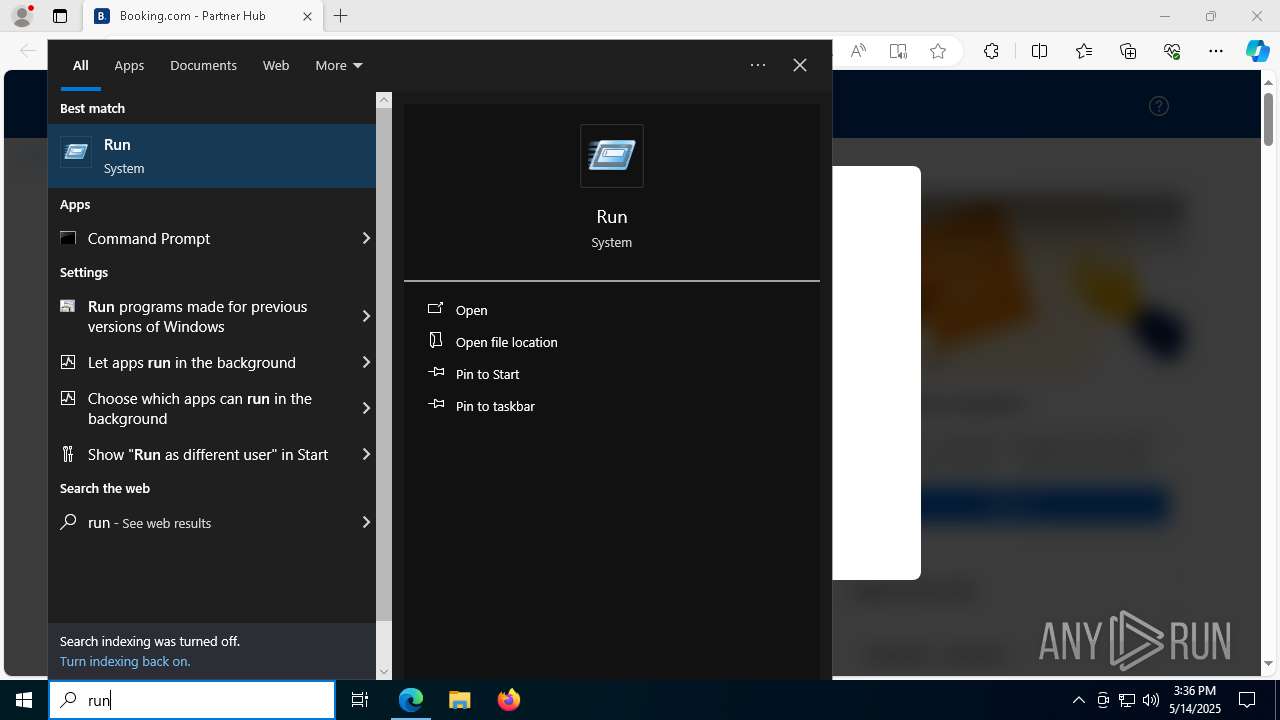
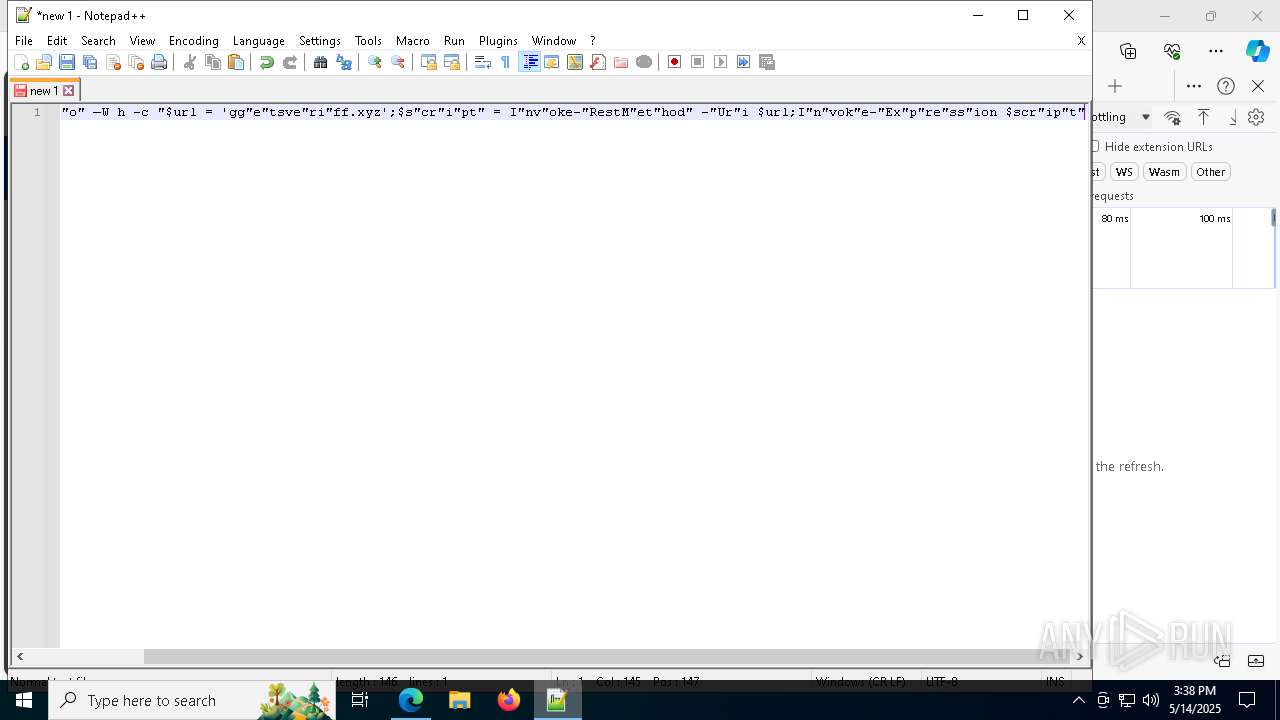
Manual execution by a user
- powershell.exe (PID: 6036)
- notepad++.exe (PID: 5400)
- powershell.exe (PID: 1116)
Checks proxy server information
- powershell.exe (PID: 6036)
Reads Environment values
- identity_helper.exe (PID: 6132)
Disables trace logs
- powershell.exe (PID: 6036)
Process checks computer location settings
- cbe92.exe (PID: 8048)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7844)
Execution of CURL command
- cmd.exe (PID: 5680)
- cmd.exe (PID: 6072)
Executable content was dropped or overwritten
- msedge.exe (PID: 1056)
The sample compiled with english language support
- msedge.exe (PID: 1056)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AsyncRat
(PID) Process(7596) tybd7.exe
C2 (20)hsjafklweqmn.click
qweiozmnxvla.click
lkjzmxnqpwer.click
asdkjczxmeuw.click
zxvnqwejlkgh.click
mznvqiweurty.click
plmzxqwieruo.click
vxmnsdkjweqz.click
qpwalskdjzmx.click
zmxncvaoiwqe.click
xnzwoeirplad.click
qwenmzlxktyu.click
nmasdqwpeiru.click
qowuensmzxcv.click
wqemzxncpiou.click
zbqwmnzxopru.click
xpoiwnzqlaks.click
qpeuwmxnzvka.click
zcnvqpweoriu.click
lksmzqwenxop.click
Ports (1)7777
VersionLoaderPanel
Options
AutoRunfalse
Mutexgtyyopygoktauikhohh
InstallFolder%AppData%
Certificates
Cert1MIICMDCCAZmgAwIBAgIVALJH4bdfPPE5dyMevD9KJERdSx3xMA0GCSqGSIb3DQEBDQUAMGQxFTATBgNVBAMMDExvYWRlciBQYW5lbDETMBEGA1UECwwKcXdxZGFuY2h1bjEcMBoGA1UECgwTRGNSYXQgQnkgcXdxZGFuY2h1bjELMAkGA1UEBwwCU0gxCzAJBgNVBAYTAkNOMB4XDTI0MDczMDE2NDgyM1oXDTM1MDUwOTE2NDgyM1owEDEOMAwGA1UEAwwFRGNSYXQwgZ8wDQYJKoZIhvcNAQEBBQADgY0A...
Server_SignatureYlcdsPpKf11Hcp9qDaJrUQs5j2AxY6xgII8uWL2m7KZXKwMnTXAZomPx5X7u6Tc/YncDJCnsMHalwe9SkKLF+CSYONacxvQBplBXWUxD6Dru9KZ20fHUoplm4QrI789zZX8VqvU+Linwu43caEoZQdIkahIjtmX4hsARxzuLavk=
Keys
AESec7decd80617706721f853787f64b4588146586209029b7039884b7c3be7d885
SaltLoaderPanel
Total processes
216
Monitored processes
80
Malicious processes
8
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 644 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5616 --field-trial-handle=2372,i,18303682705603189929,10954997815341675176,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 660 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5776 --field-trial-handle=2372,i,18303682705603189929,10954997815341675176,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 684 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6880 --field-trial-handle=2372,i,18303682705603189929,10954997815341675176,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 720 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_xpay_wallet.mojom.EdgeXPayWalletService --lang=en-US --service-sandbox-type=utility --no-appcompat-clear --mojo-platform-channel-handle=5596 --field-trial-handle=2372,i,18303682705603189929,10954997815341675176,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 812 | "C:\Windows\Temp\tybd7.exe" | C:\Windows\Temp\tybd7.exe | — | cmd.exe | |||||||||||
User: admin Company: CxApp Integrity Level: MEDIUM Description: CxApp Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 856 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=3880 --field-trial-handle=2372,i,18303682705603189929,10954997815341675176,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 968 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=7052 --field-trial-handle=2372,i,18303682705603189929,10954997815341675176,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1040 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=3880 --field-trial-handle=2372,i,18303682705603189929,10954997815341675176,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1052 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=40 --mojo-platform-channel-handle=2304 --field-trial-handle=2372,i,18303682705603189929,10954997815341675176,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1056 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5760 --field-trial-handle=2372,i,18303682705603189929,10954997815341675176,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
34 311
Read events
34 295
Write events
16
Delete events
0
Modification events
| (PID) Process: | (1852) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1852) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1852) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1852) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (1852) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 31996797B0932F00 | |||
| (PID) Process: | (1852) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: A2478C97B0932F00 | |||
| (PID) Process: | (1852) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197200 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {5EAE7A97-337C-401E-A04F-4B2993231754} | |||
| (PID) Process: | (1852) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197200 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {EE1BCA66-7EBB-47D7-85AE-0C176F202362} | |||
| (PID) Process: | (1852) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197200 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {49AB5517-251A-411E-91BF-44CC0717102F} | |||
| (PID) Process: | (1852) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197200 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {745C8BB1-148B-452E-AE75-ED3389128016} | |||
Executable files
13
Suspicious files
377
Text files
75
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1852 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10c8b1.TMP | — | |
MD5:— | SHA256:— | |||
| 1852 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1852 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10c8b1.TMP | — | |
MD5:— | SHA256:— | |||
| 1852 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1852 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10c8c0.TMP | — | |
MD5:— | SHA256:— | |||
| 1852 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1852 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10c8c0.TMP | — | |
MD5:— | SHA256:— | |||
| 1852 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1852 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10c91e.TMP | — | |
MD5:— | SHA256:— | |||
| 1852 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
42
TCP/UDP connections
113
DNS requests
127
Threats
22
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
516 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6036 | powershell.exe | GET | 200 | 212.113.122.89:80 | http://getsveriff.xyz/rvxlgh7/cwe.exe | unknown | — | — | malicious |
— | — | GET | 200 | 23.48.23.159:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7976 | svchost.exe | HEAD | 200 | 23.50.131.73:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1747697096&P2=404&P3=2&P4=gwKlWiOVp1aJeCNdoCYyrndm1XkG7QD7zT8LTGAFgOcC7QRRR%2fwZJzpm6v%2f9fC6i8dTDVznhGDmz5ZpThh38fQ%3d%3d | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
516 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.48.23.159:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7320 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1852 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7320 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7320 | msedge.exe | 13.107.246.44:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
client.wns.windows.com |
| whitelisted |
bookhub-id12231.com |
| unknown |
business.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7320 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
7320 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
7320 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
7320 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
6036 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
6036 | powershell.exe | A Network Trojan was detected | ET HUNTING SUSPICIOUS Firesale gTLD EXE DL with no Referer June 13 2016 |
6036 | powershell.exe | Potentially Bad Traffic | ET MALWARE Terse alphanumeric executable downloader high likelihood of being hostile |
6036 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
6036 | powershell.exe | Misc activity | ET INFO Request for EXE via Powershell |
6036 | powershell.exe | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |