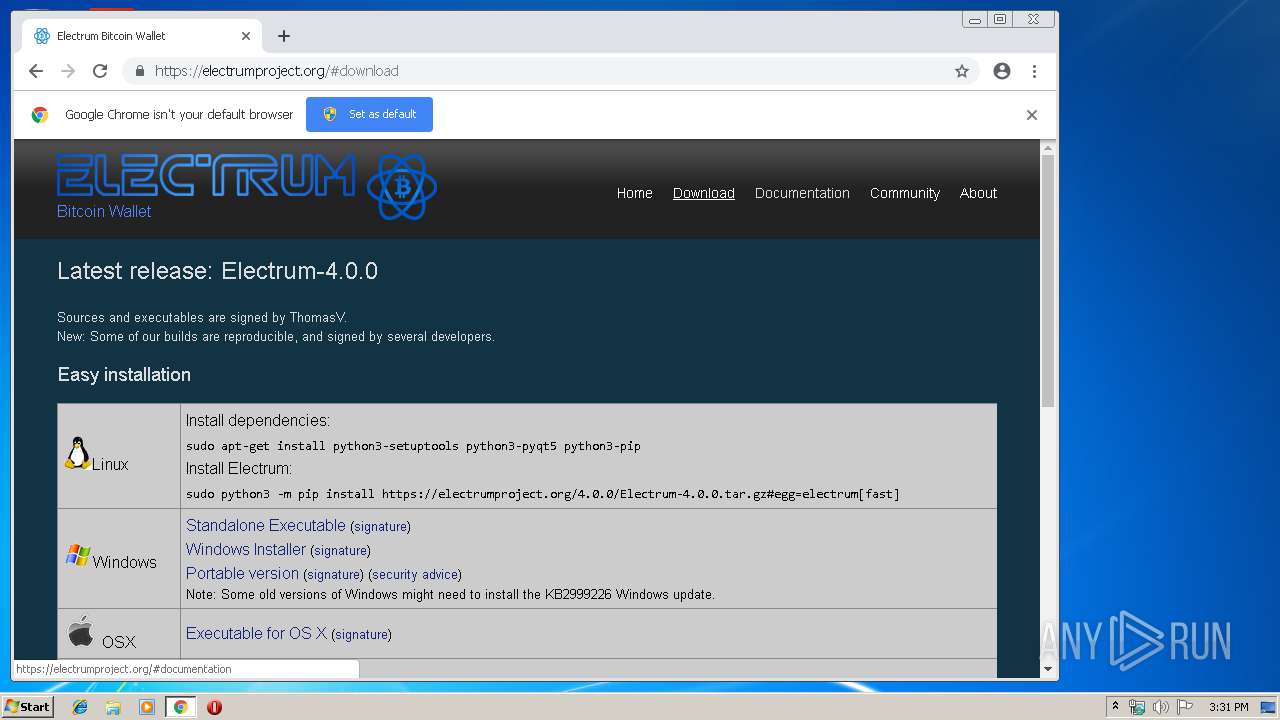
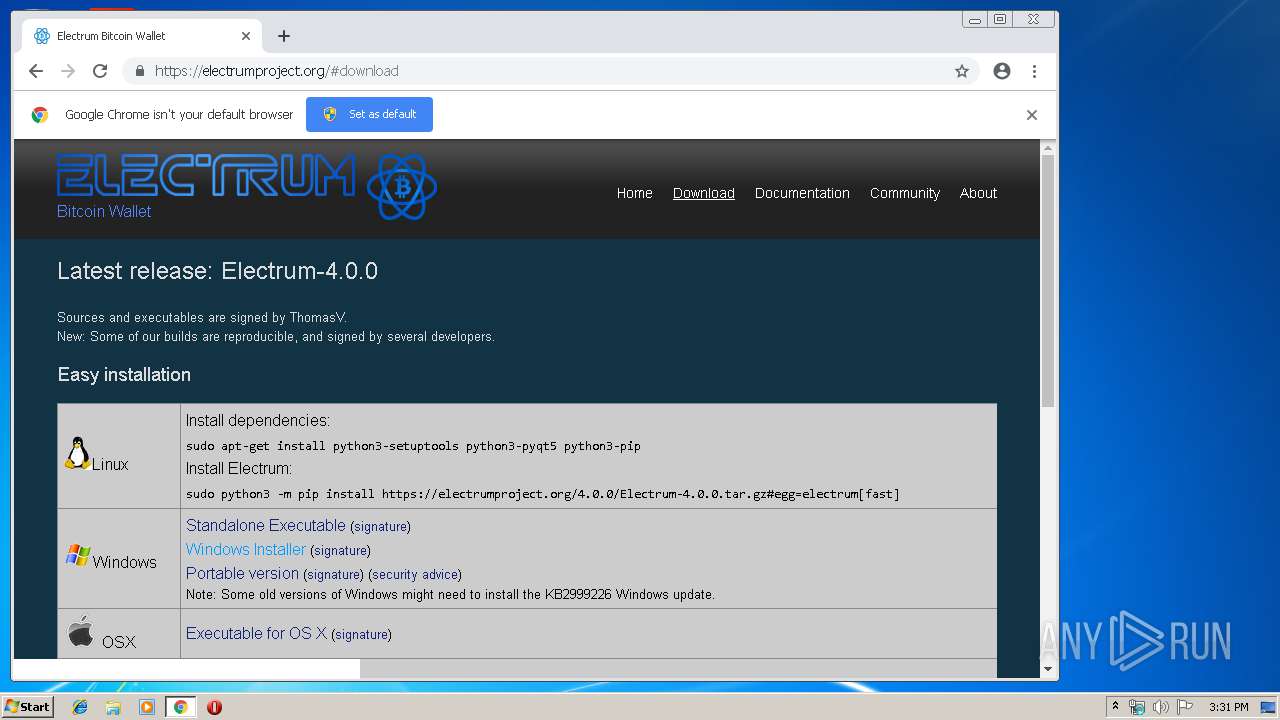
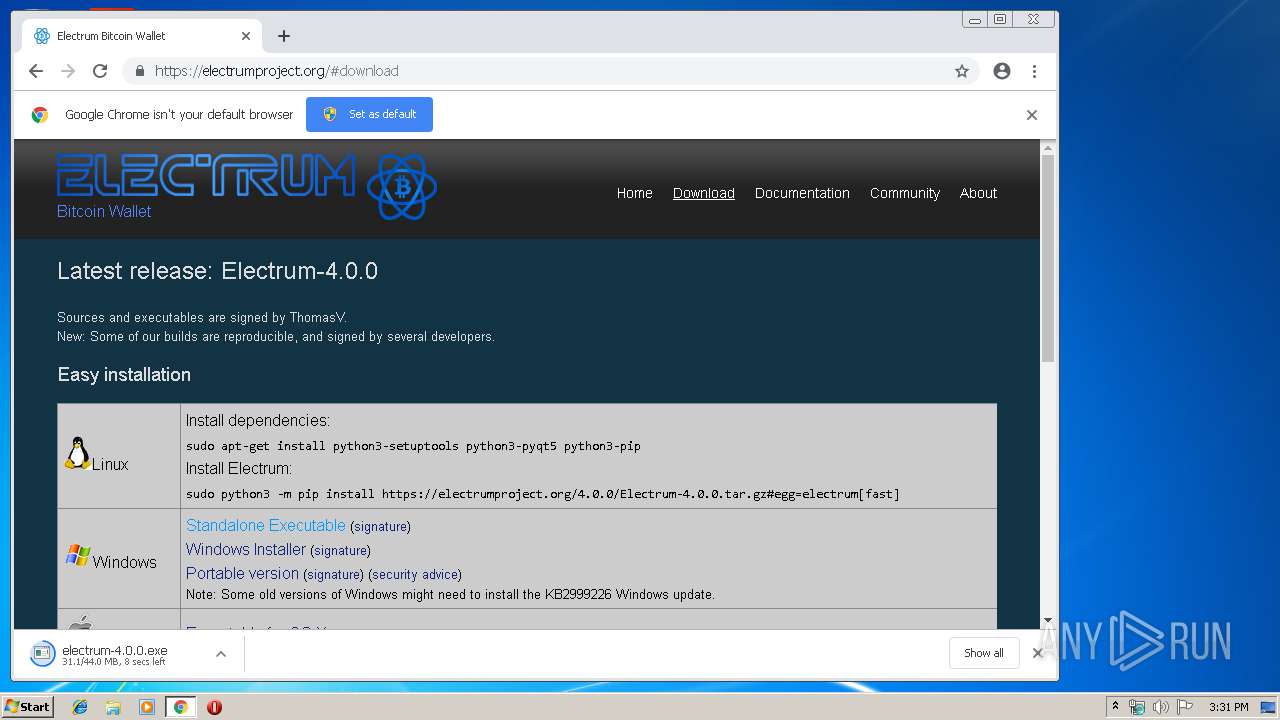
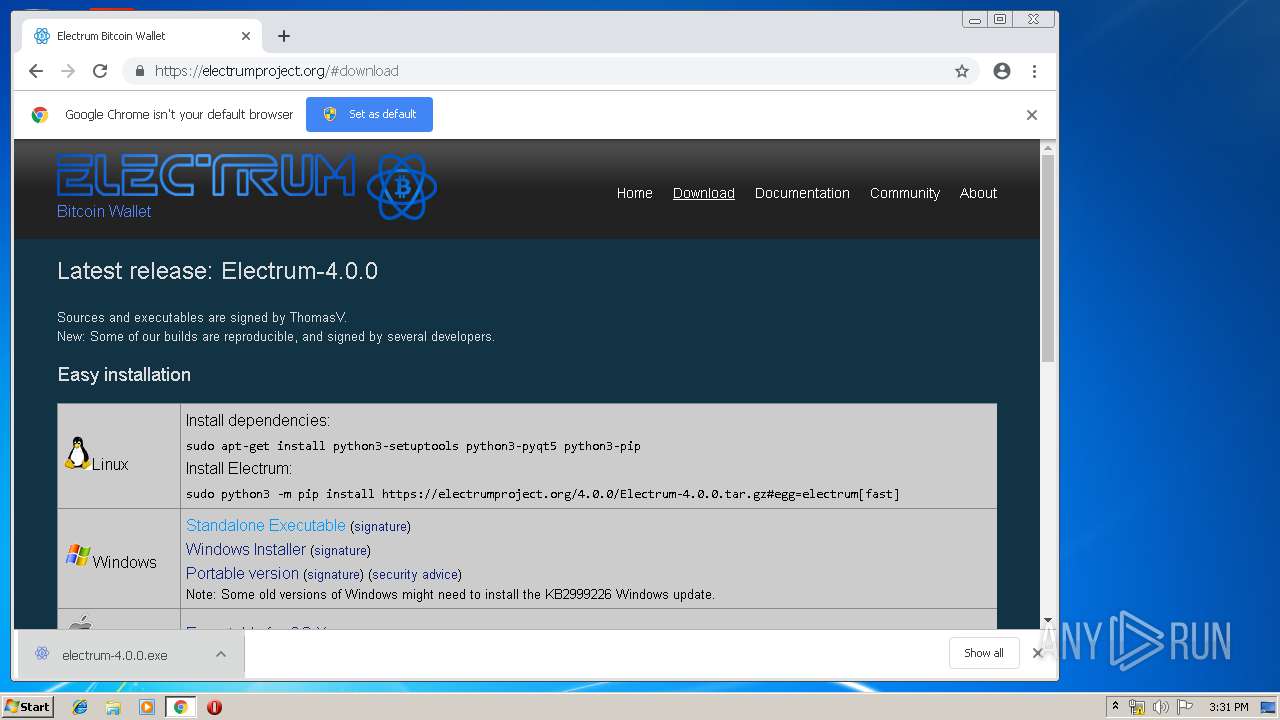
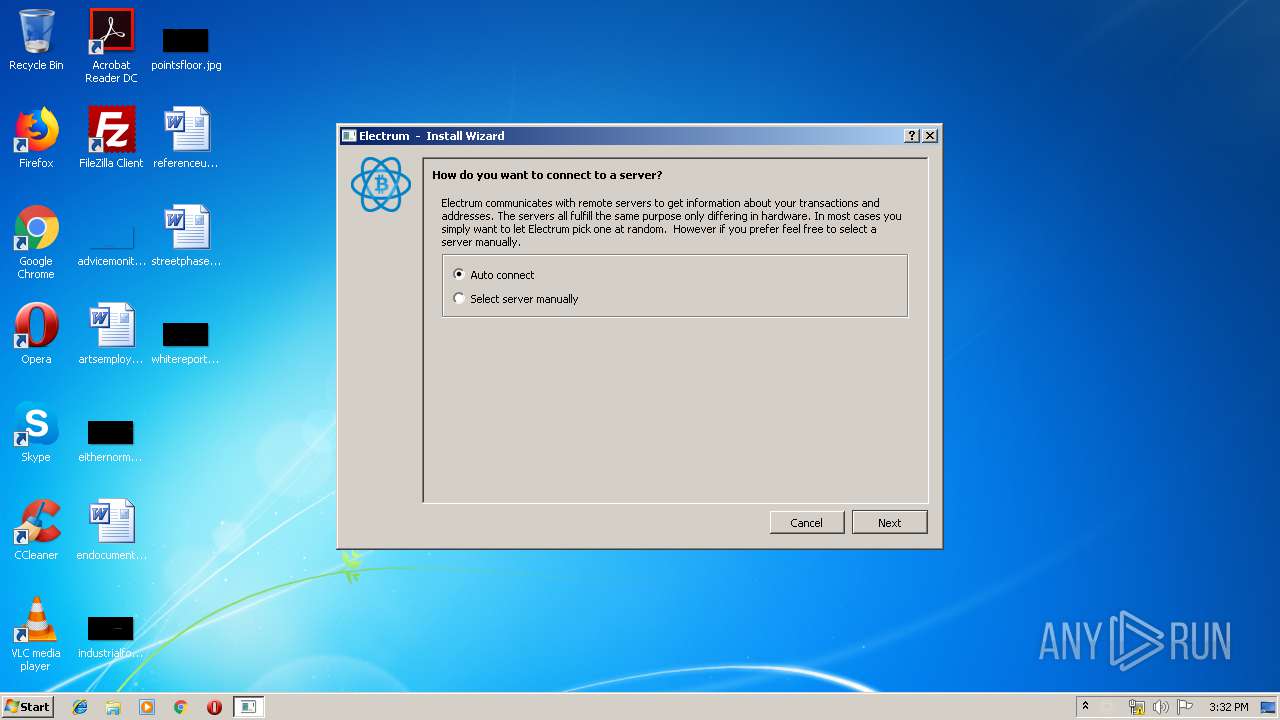
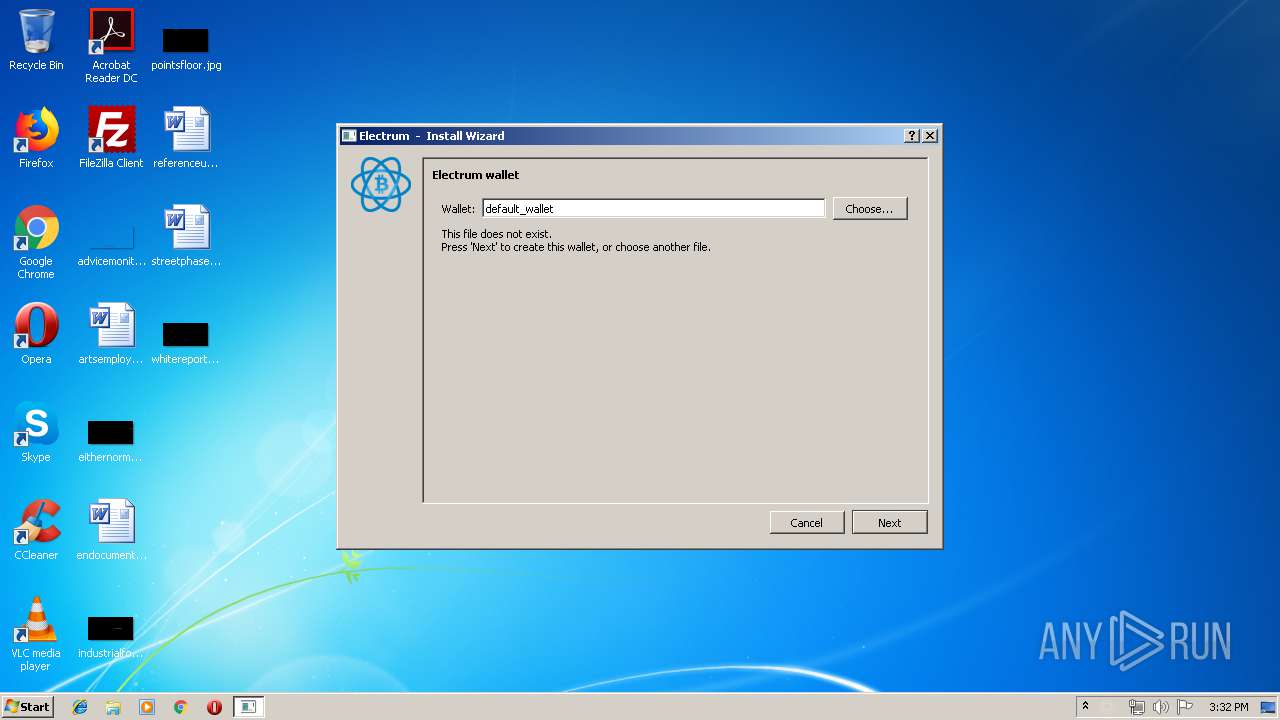
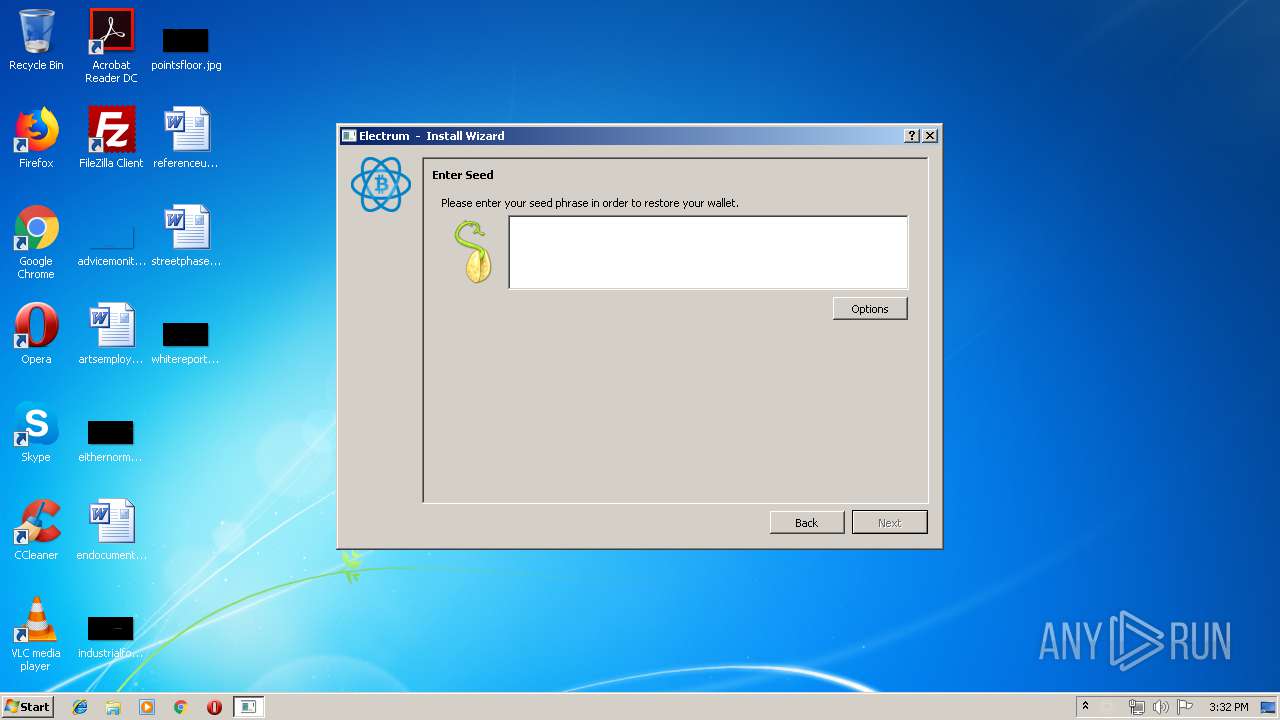
| URL: | https://electrumproject.org/#download |
| Full analysis: | https://app.any.run/tasks/b93d5e30-d572-4d0d-a9c6-4f4cf545f3d6 |
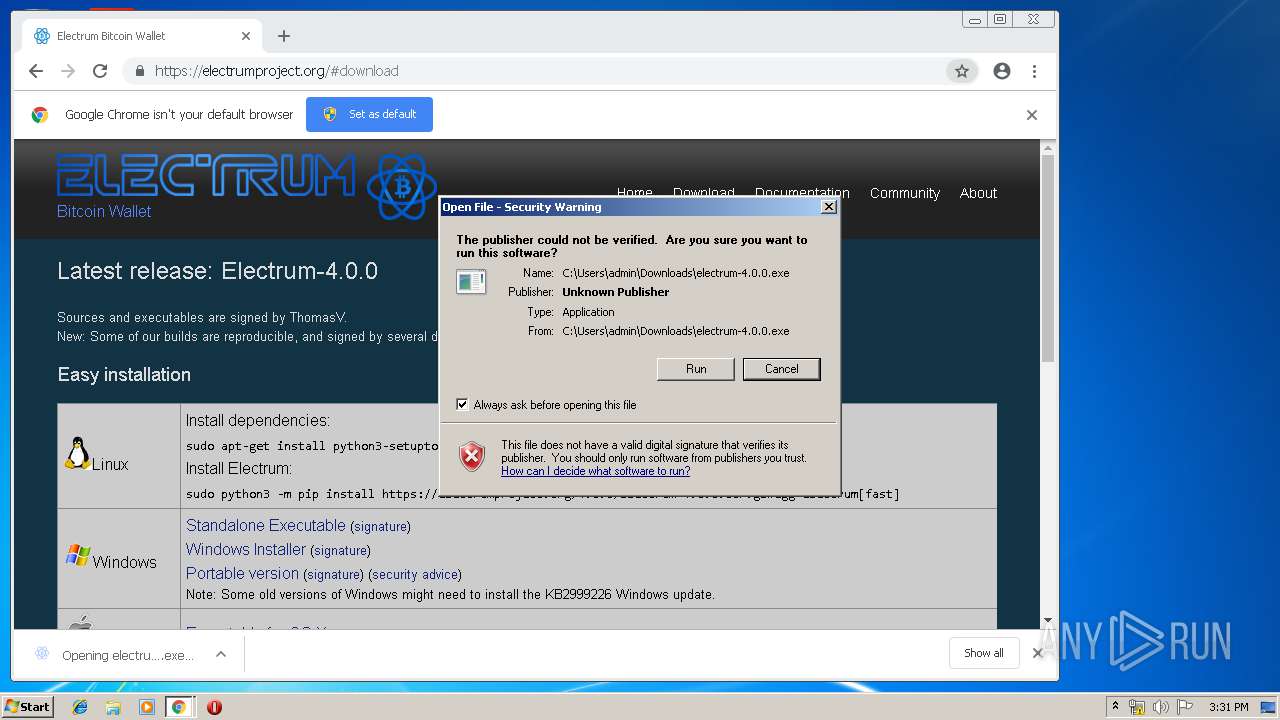
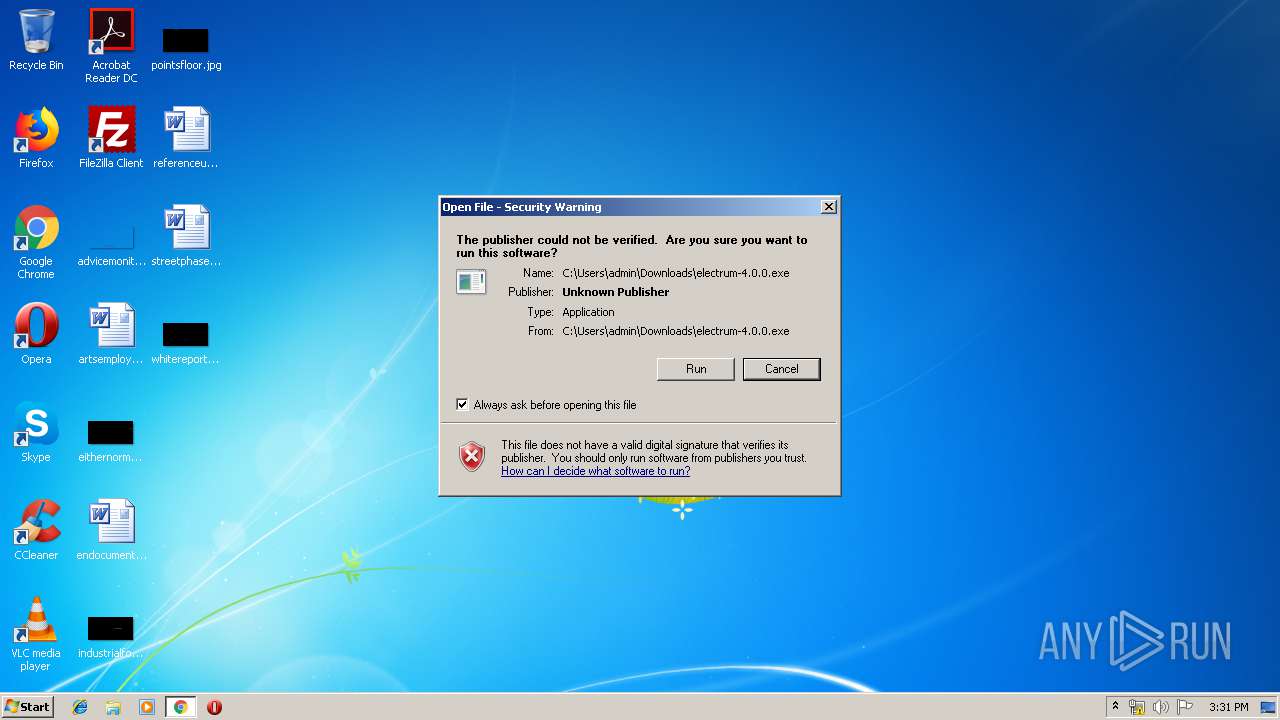
| Verdict: | Malicious activity |
| Threats: | TrickBot is an advanced banking trojan that attackers can use to steal payment credentials from the victims. It can redirect the victim to a fake banking cabinet and retrieve credentials typed in on the webpage. |
| Analysis date: | March 21, 2019, 15:30:38 |
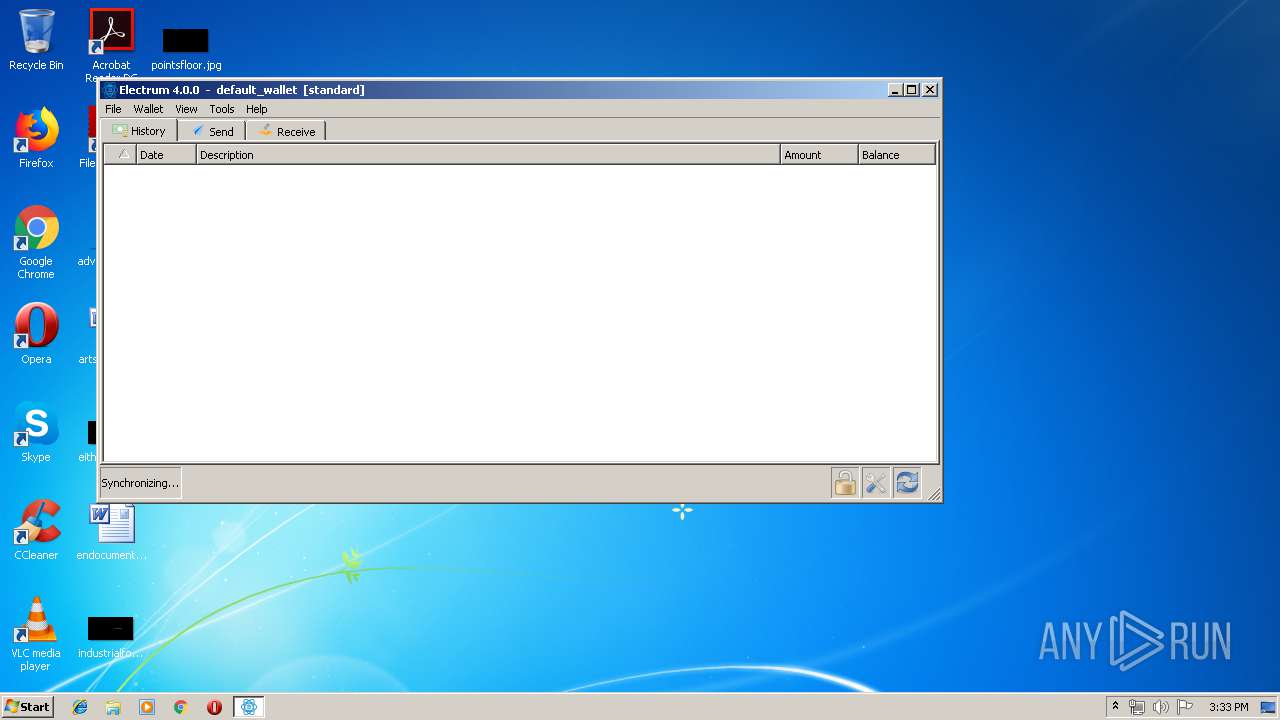
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 2B57917A65EEA3896E221E4D477F4854 |
| SHA1: | 013153F755EB1370B4E62ED617A5947F55810E65 |
| SHA256: | 1AB91A43EB021BECDCDD09471237CD8C0CF6039B5E671674FD4DD3BEA0B4F04C |
| SSDEEP: | 3:N8WRXQoal+X8FJp:2dbt |
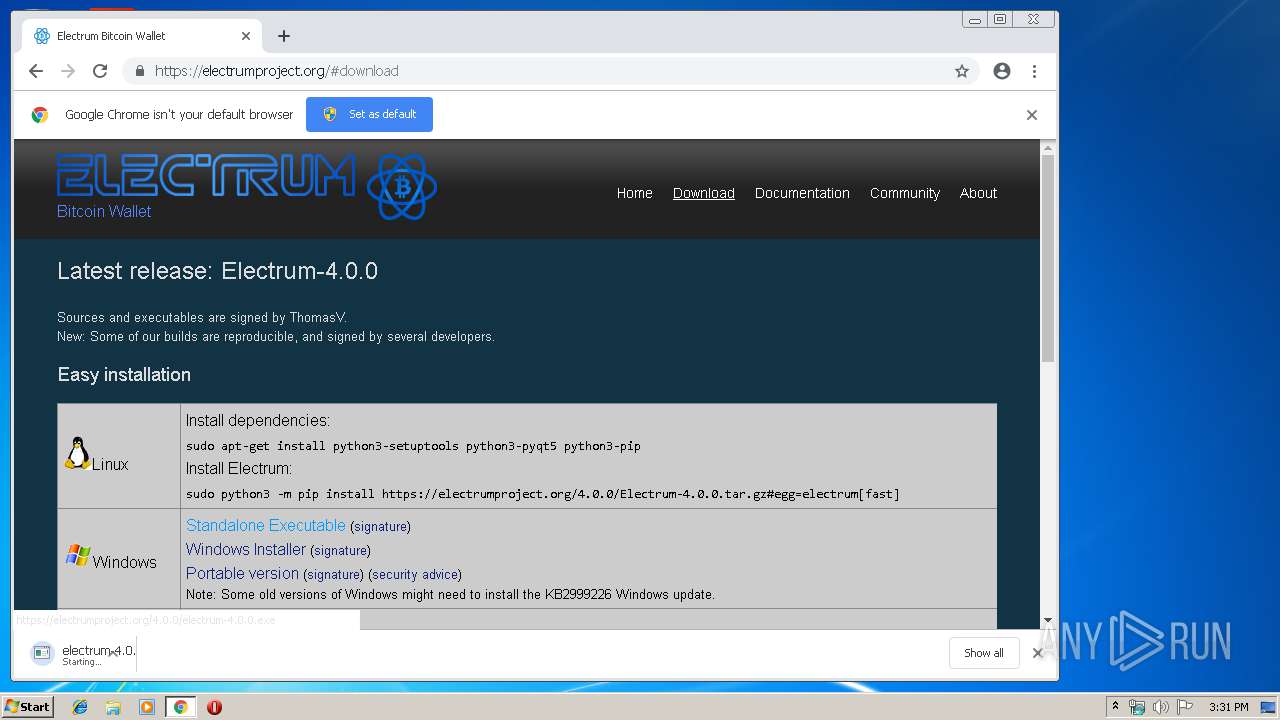
MALICIOUS
Application was dropped or rewritten from another process
- electrum-4.0.0.exe (PID: 3320)
- electrum-4.0.0.exe (PID: 2932)
Loads dropped or rewritten executable
- electrum-4.0.0.exe (PID: 2932)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2864)
Application launched itself
- electrum-4.0.0.exe (PID: 3320)
Loads Python modules
- electrum-4.0.0.exe (PID: 2932)
Connects to unusual port
- electrum-4.0.0.exe (PID: 2932)
Executable content was dropped or overwritten
- chrome.exe (PID: 2864)
- electrum-4.0.0.exe (PID: 3320)
Creates files in the user directory
- electrum-4.0.0.exe (PID: 2932)
Starts CMD.EXE for commands execution
- electrum-4.0.0.exe (PID: 2932)
Connects to server without host name
- electrum-4.0.0.exe (PID: 2932)
INFO
Application launched itself
- iexplore.exe (PID: 1848)
- chrome.exe (PID: 2864)
Creates files in the user directory
- iexplore.exe (PID: 764)
Changes internet zones settings
- iexplore.exe (PID: 1848)
Reads Internet Cache Settings
- iexplore.exe (PID: 764)
Reads internet explorer settings
- iexplore.exe (PID: 764)
Dropped object may contain TOR URL's
- electrum-4.0.0.exe (PID: 3320)
Dropped object may contain Bitcoin addresses
- electrum-4.0.0.exe (PID: 3320)
- electrum-4.0.0.exe (PID: 2932)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
53
Monitored processes
23
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 764 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1848 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 828 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,15366321787870771490,5466768733474765356,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=2283018228521565100 --mojo-platform-channel-handle=2700 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1452 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,15366321787870771490,5466768733474765356,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=17083866075048037307 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17083866075048037307 --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2768 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=956,15366321787870771490,5466768733474765356,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=13448778796210310089 --mojo-platform-channel-handle=960 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,15366321787870771490,5466768733474765356,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=14357655240900331729 --mojo-platform-channel-handle=1516 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1744 | fsutil sparse setflag "C:\Users\admin\AppData\Roaming\Electrum\blockchain_headers" 1 | C:\Windows\system32\fsutil.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: fsutil.exe Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1848 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1868 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,15366321787870771490,5466768733474765356,131072 --enable-features=PasswordImport --service-pipe-token=1256967438190603402 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1256967438190603402 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2268 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,15366321787870771490,5466768733474765356,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12061858957072206687 --mojo-platform-channel-handle=3344 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2260 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,15366321787870771490,5466768733474765356,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15549968702105971261 --mojo-platform-channel-handle=3356 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
1 535
Read events
1 379
Write events
150
Delete events
6
Modification events
| (PID) Process: | (1848) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1848) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1848) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1848) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (1848) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1848) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000006E000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1848) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {4FBE27B7-4BEE-11E9-A302-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (1848) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (1848) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 1 | |||
| (PID) Process: | (1848) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070300040015000F001E0035007802 | |||
Executable files
201
Suspicious files
492
Text files
1 096
Unknown types
101
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1848 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFFD16625279F6C95F.TMP | — | |
MD5:— | SHA256:— | |||
| 1848 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFEC1548E415B47E38.TMP | — | |
MD5:— | SHA256:— | |||
| 1848 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF88BB3B6E9357B30C.TMP | — | |
MD5:— | SHA256:— | |||
| 1848 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF9CB03E9FF7DF692A.TMP | — | |
MD5:— | SHA256:— | |||
| 1848 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{4FBE27B7-4BEE-11E9-A302-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 2864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
74
DNS requests
73
Threats
116
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1604 | chrome.exe | GET | 200 | 217.146.165.205:80 | http://r2---sn-oun-1gie.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=136.0.0.150&mm=28&mn=sn-oun-1gie&ms=nvh&mt=1553182162&mv=m&pl=20&shardbypass=yes | CH | crx | 842 Kb | whitelisted |
1604 | chrome.exe | GET | 302 | 172.217.23.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 502 b | whitelisted |
2932 | electrum-4.0.0.exe | POST | 200 | 91.211.88.65:80 | http://91.211.88.65/pdata.php | unknown | — | — | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1604 | chrome.exe | 172.217.22.46:443 | clients2.google.com | Google Inc. | US | whitelisted |
1604 | chrome.exe | 172.217.23.174:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
1604 | chrome.exe | 93.171.158.14:443 | electrumproject.org | Mulgin Alexander Sergeevich | UA | unknown |
1604 | chrome.exe | 217.146.165.205:80 | r2---sn-oun-1gie.gvt1.com | NTS workspace AG | CH | whitelisted |
1604 | chrome.exe | 172.217.22.78:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
2932 | electrum-4.0.0.exe | 91.211.88.65:50002 | electrum.electrumxm.com | — | — | suspicious |
1848 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
764 | iexplore.exe | 93.171.158.14:443 | electrumproject.org | Mulgin Alexander Sergeevich | UA | unknown |
1604 | chrome.exe | 172.217.18.100:443 | www.google.com | Google Inc. | US | whitelisted |
1604 | chrome.exe | 216.58.208.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
electrumproject.org |
| unknown |
www.google.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1604 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |
2932 | electrum-4.0.0.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
2932 | electrum-4.0.0.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
2932 | electrum-4.0.0.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
2932 | electrum-4.0.0.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
2932 | electrum-4.0.0.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
2932 | electrum-4.0.0.exe | A Network Trojan was detected | MALWARE TEST [PTsecurity] Blacklist Malicious SSL certificate detected (Trickbot) |
2932 | electrum-4.0.0.exe | A Network Trojan was detected | MALWARE TEST [PTsecurity] Blacklist Malicious SSL certificate detected (Trickbot) |
2932 | electrum-4.0.0.exe | A Network Trojan was detected | MALWARE TEST [PTsecurity] Blacklist Malicious SSL certificate detected (Trickbot) |
2932 | electrum-4.0.0.exe | A Network Trojan was detected | MALWARE TEST [PTsecurity] Blacklist Malicious SSL certificate detected (Trickbot) |
1 ETPRO signatures available at the full report
Process | Message |
|---|---|
electrum-4.0.0.exe | QWindowsEGLStaticContext::create: Could not initialize EGL display: error 0x3001
|
electrum-4.0.0.exe | QWindowsEGLStaticContext::create: When using ANGLE, check if d3dcompiler_4x.dll is available
|