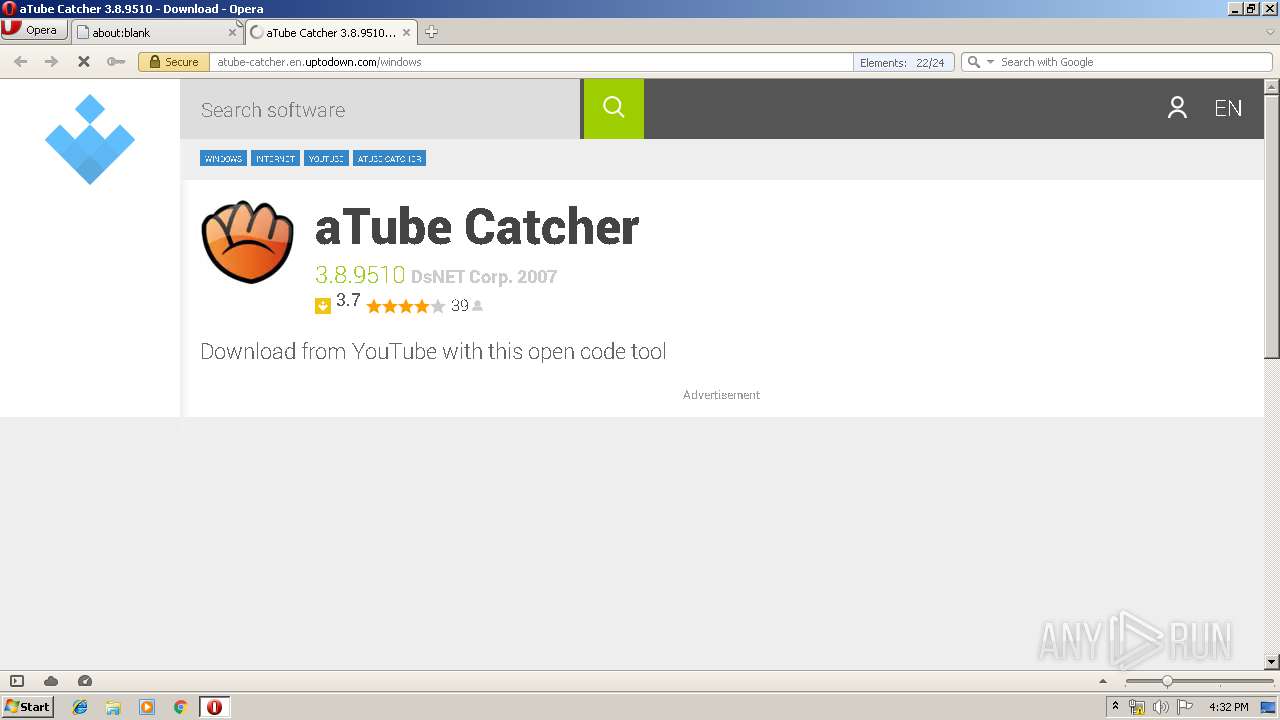
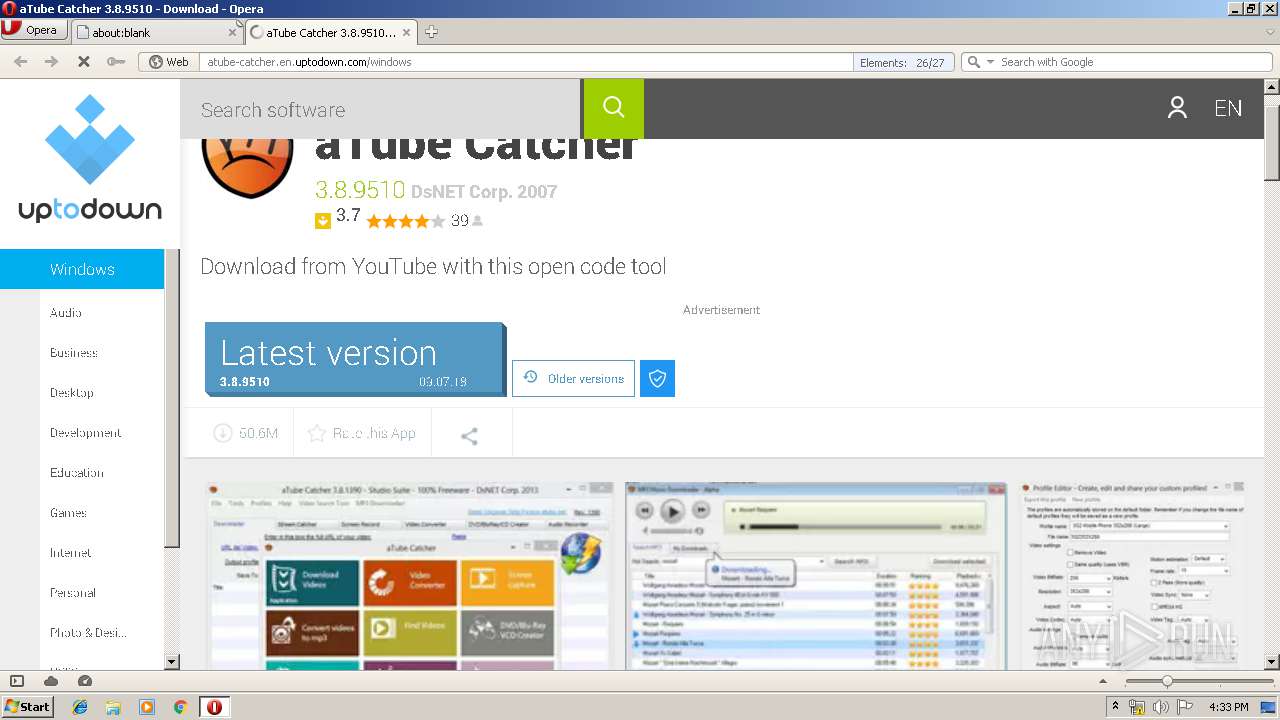
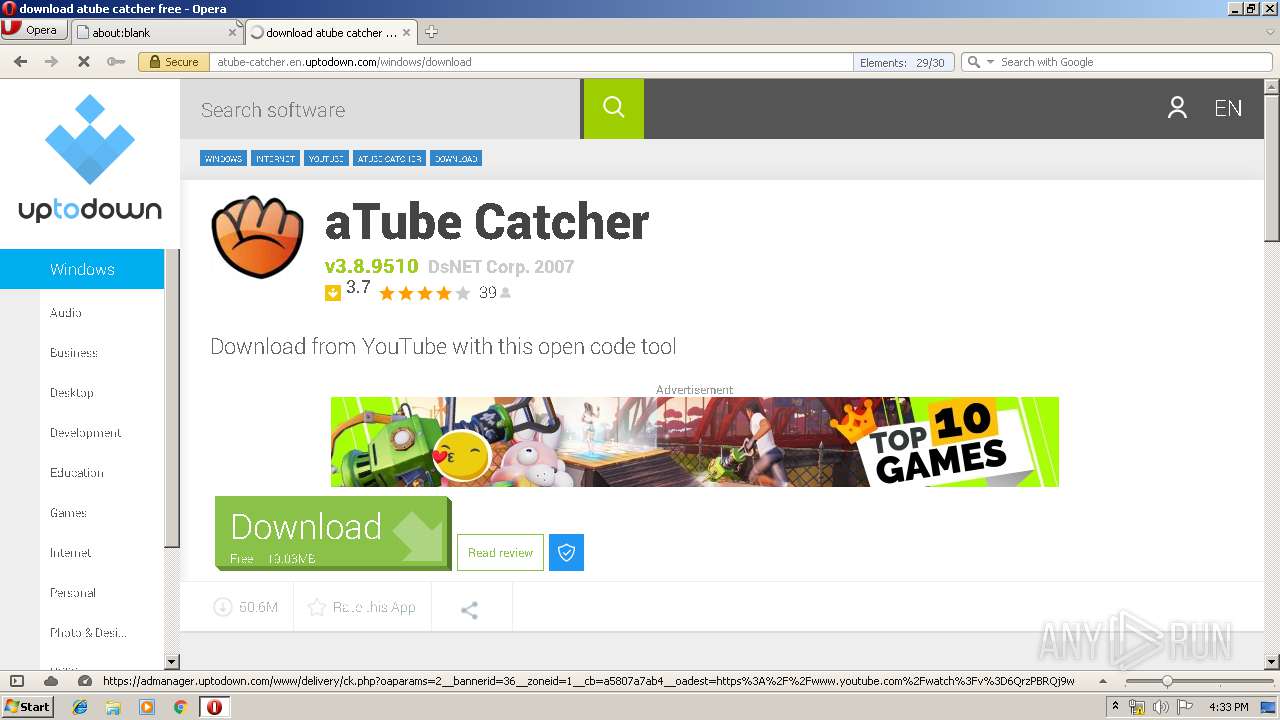
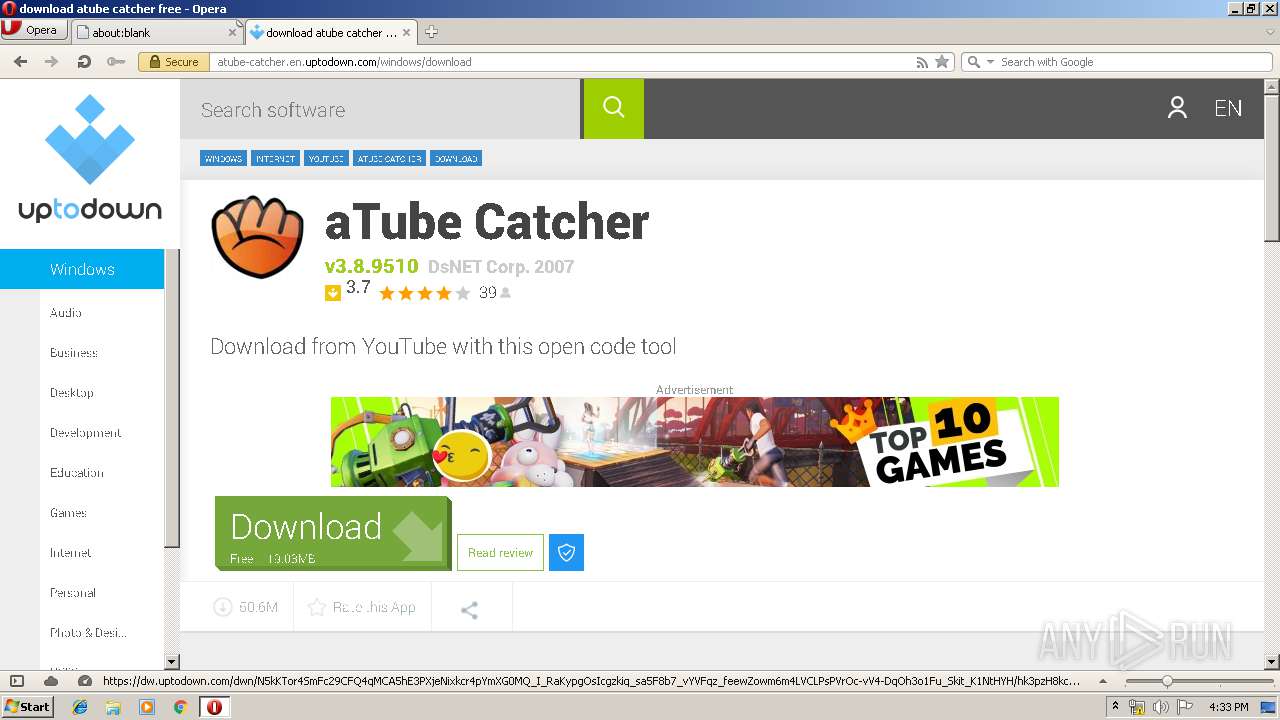
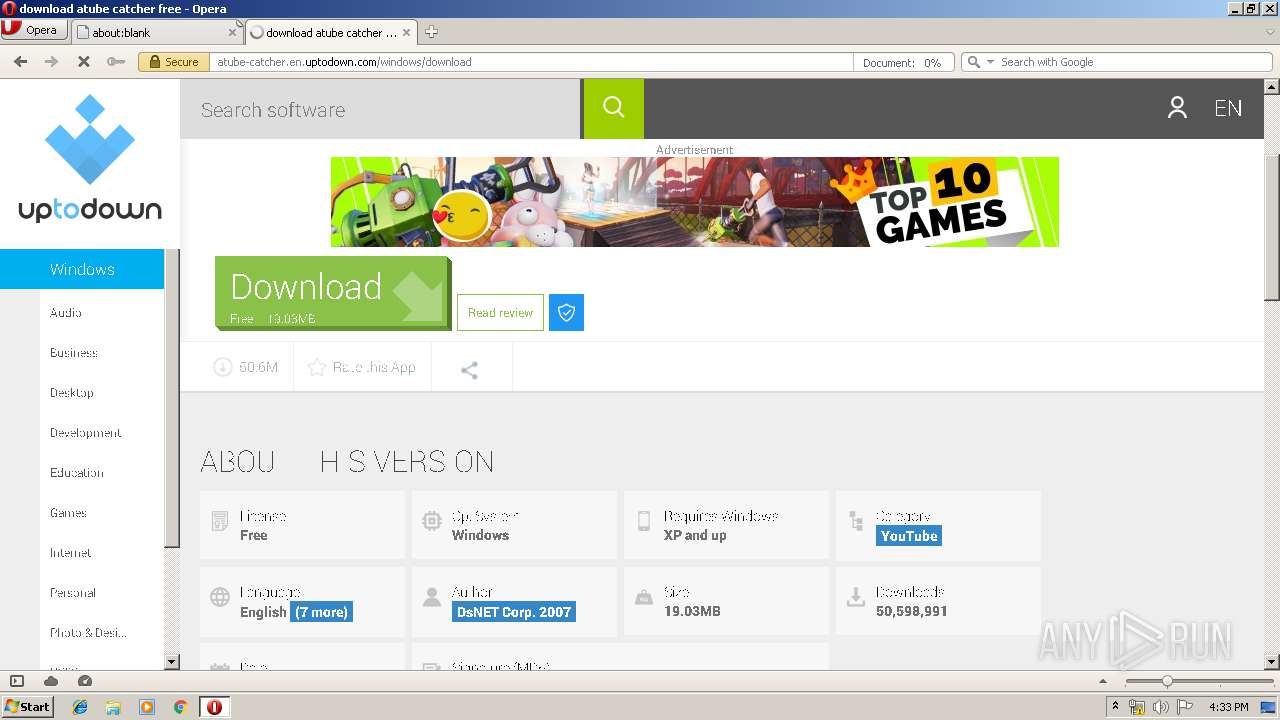
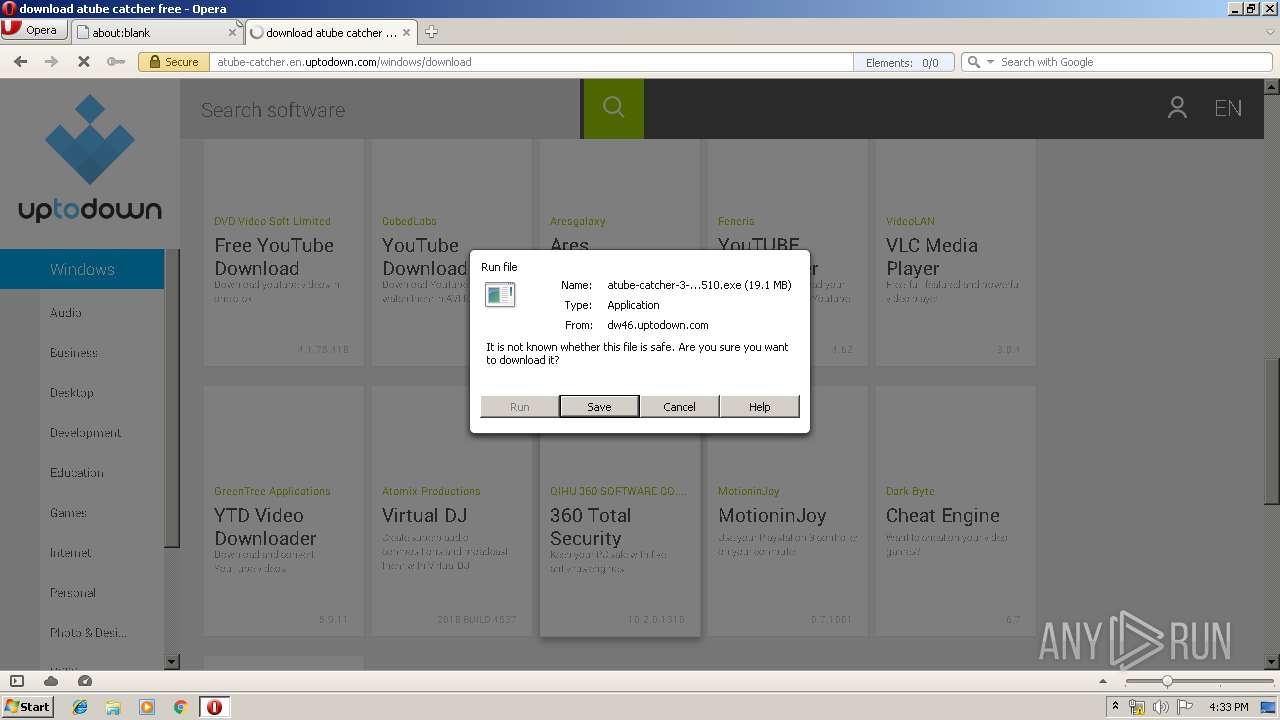
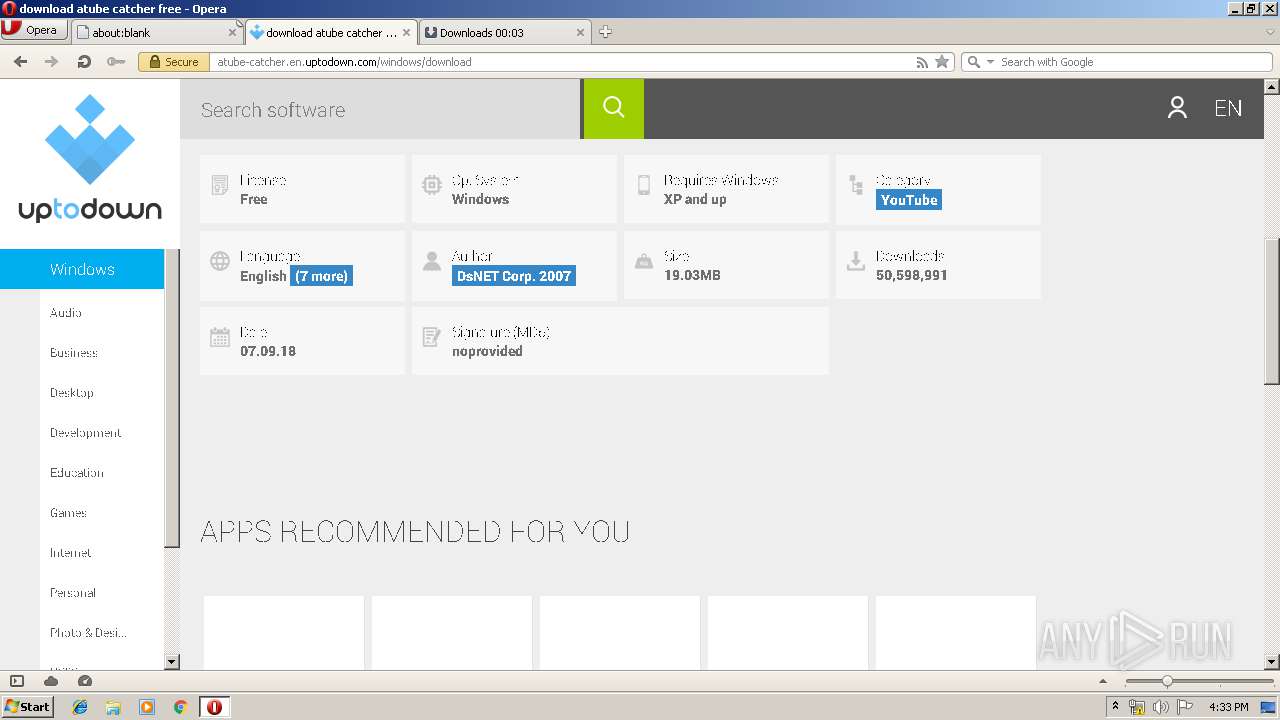
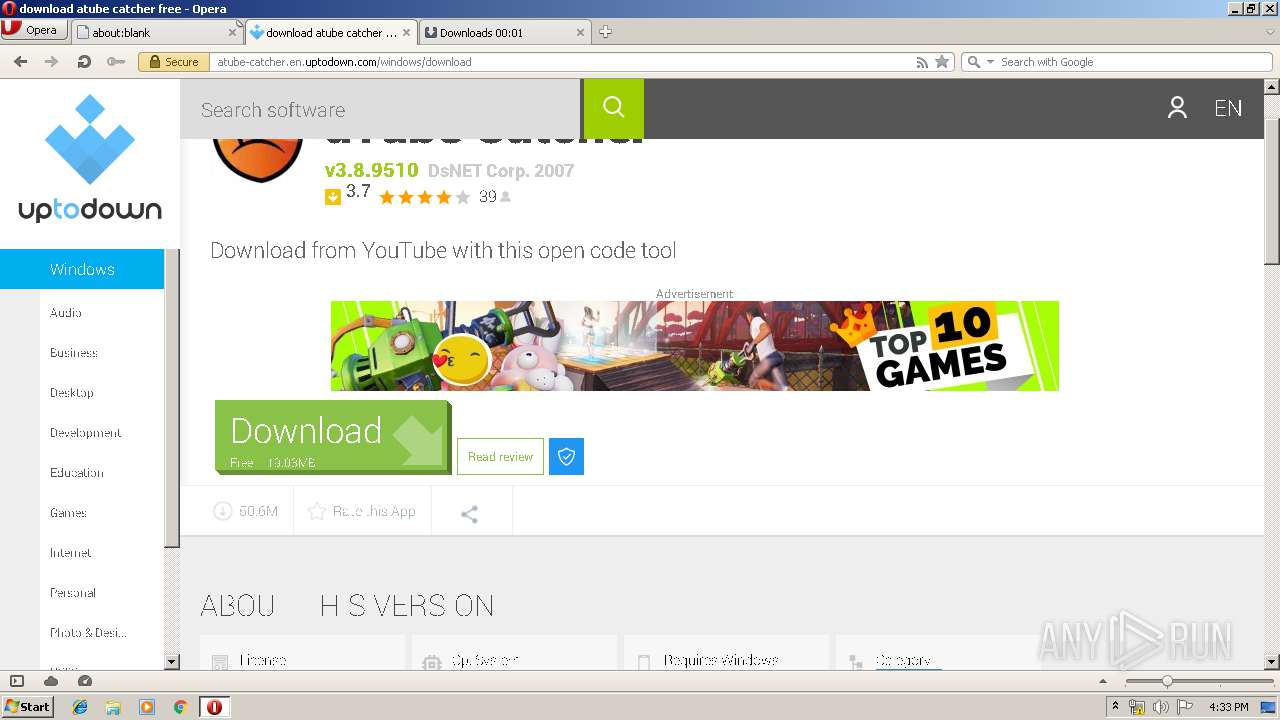
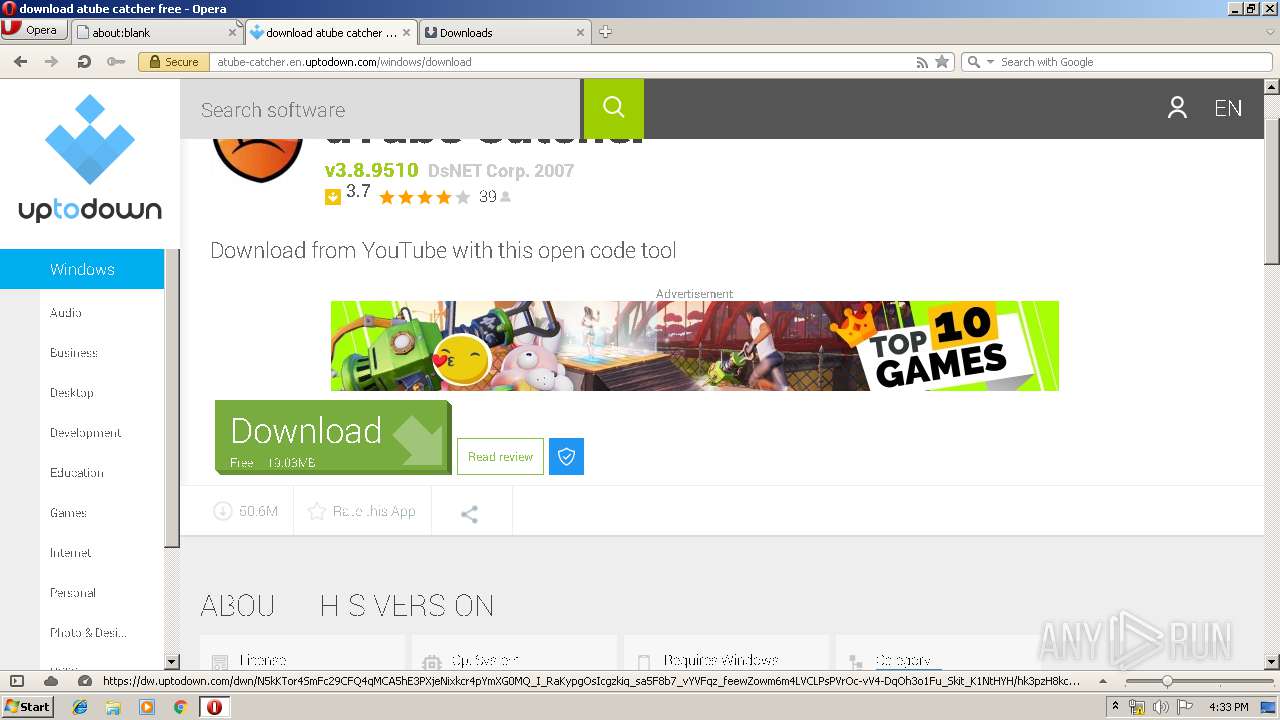
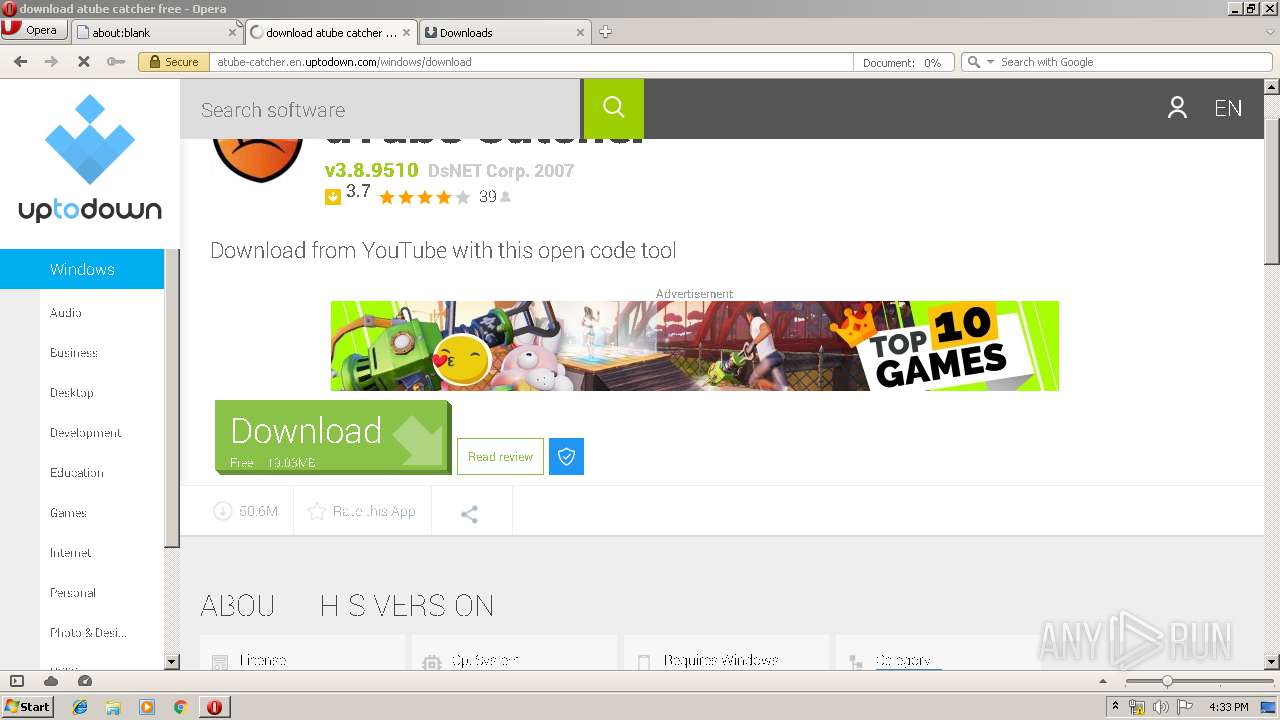
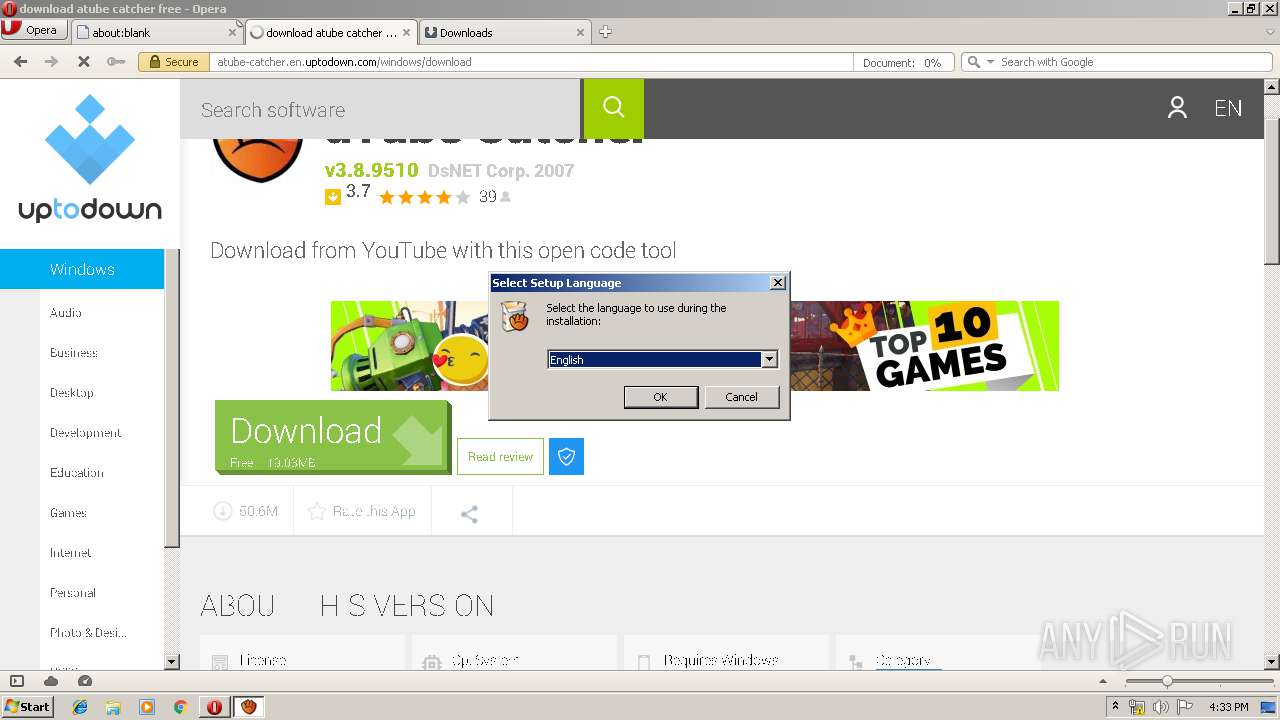
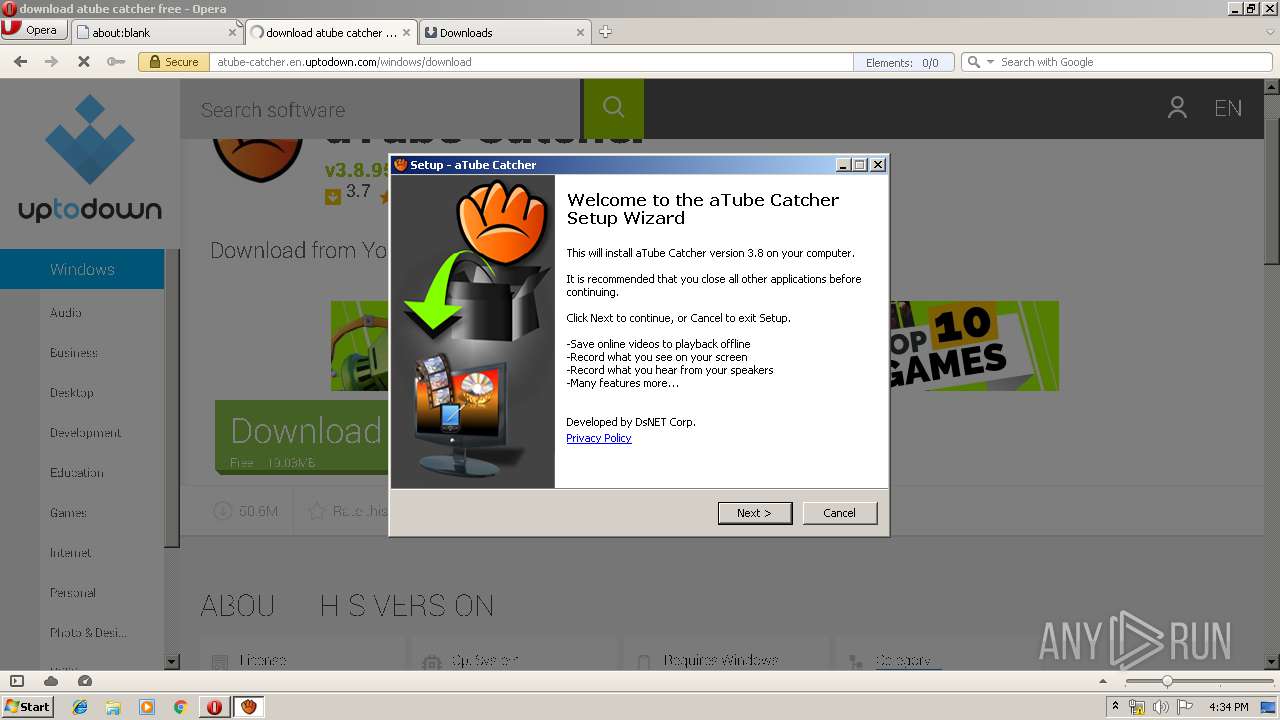
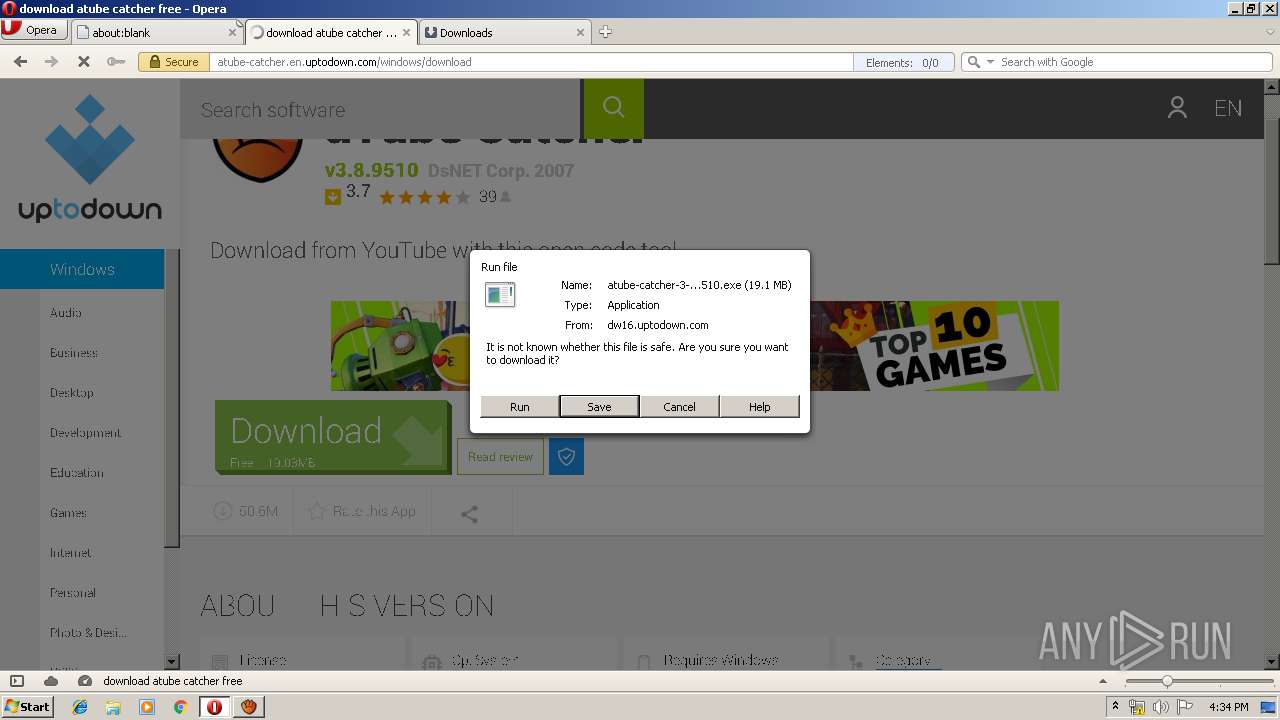
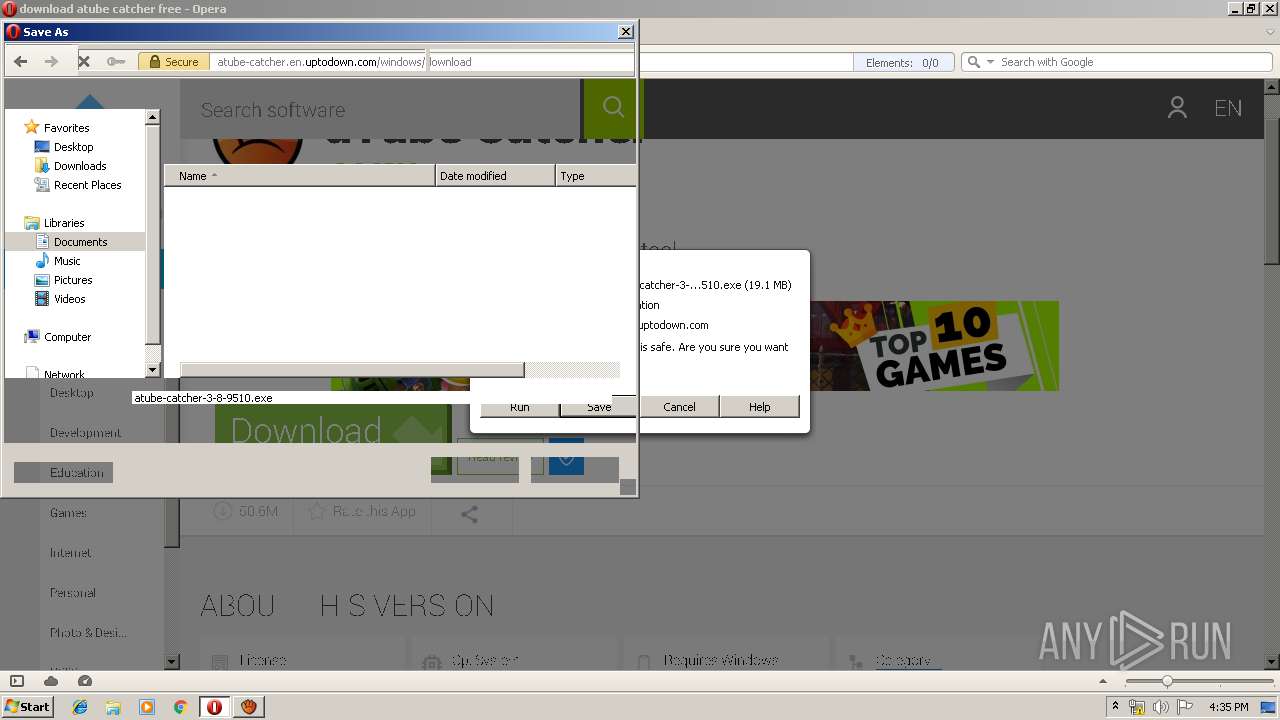
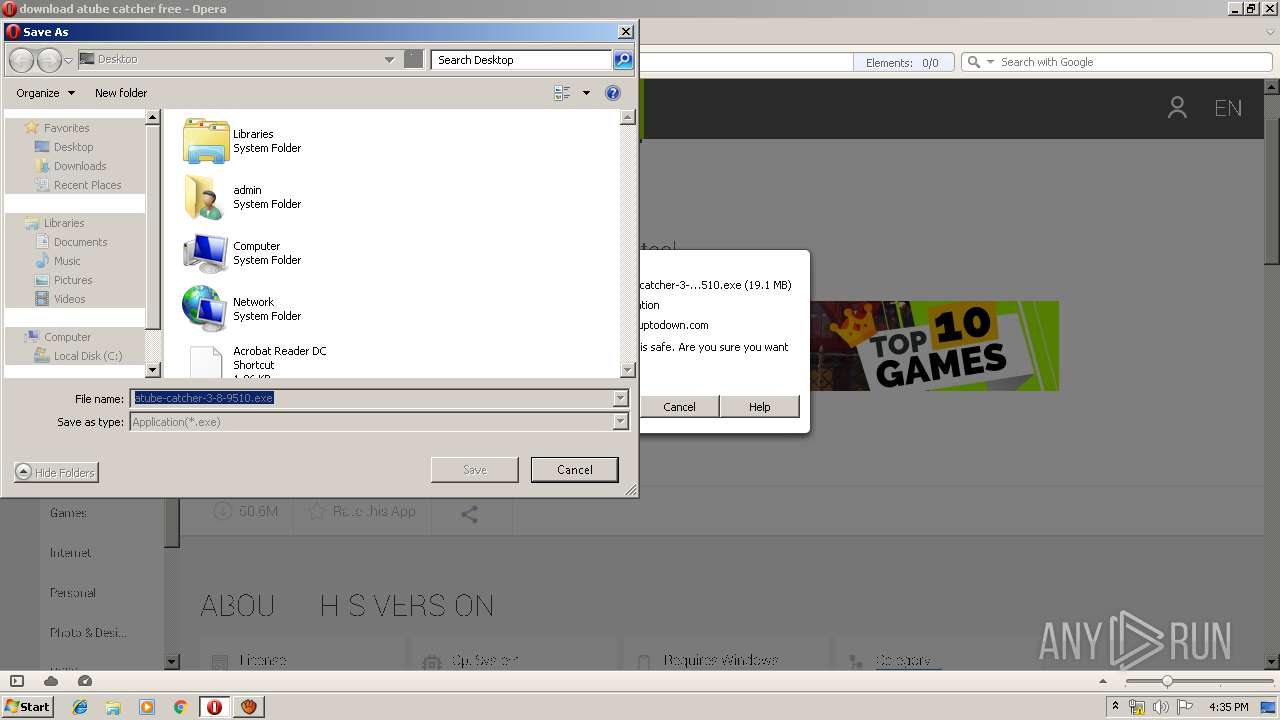
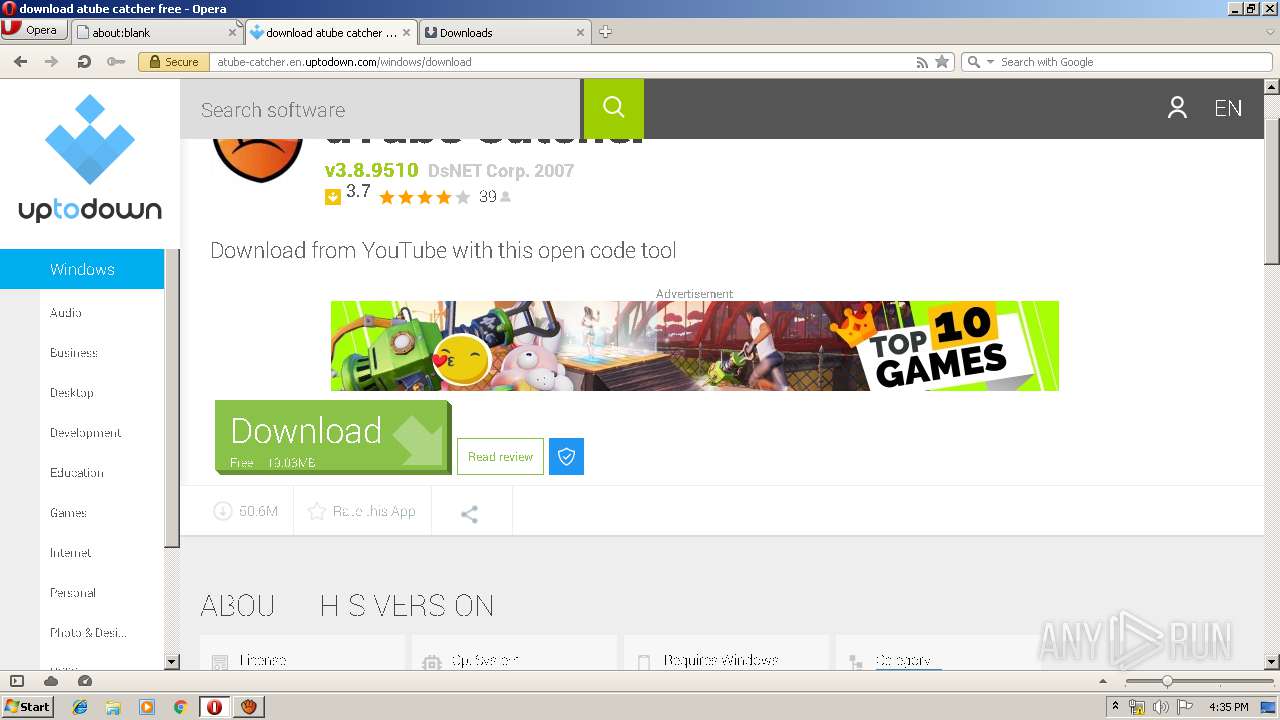
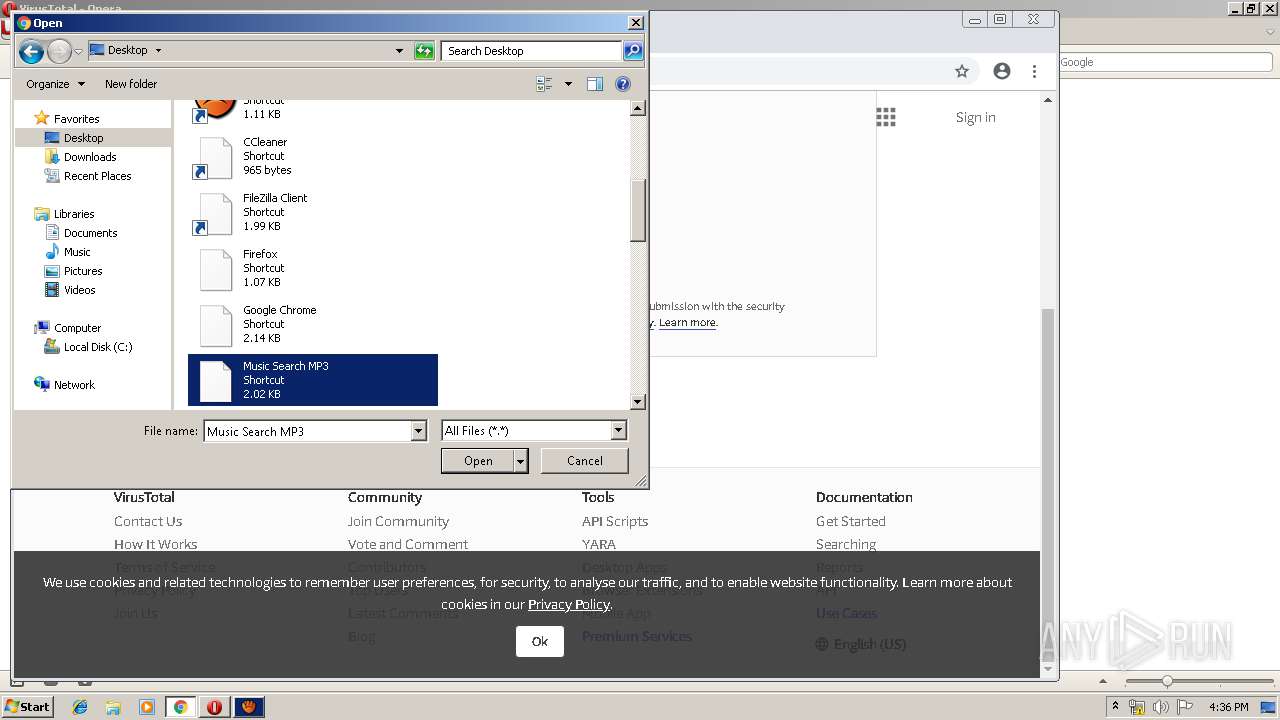
| URL: | https://atube-catcher.en.uptodown.com/windows |
| Full analysis: | https://app.any.run/tasks/fc539a74-474f-45f2-bd3c-a3a68970c76d |
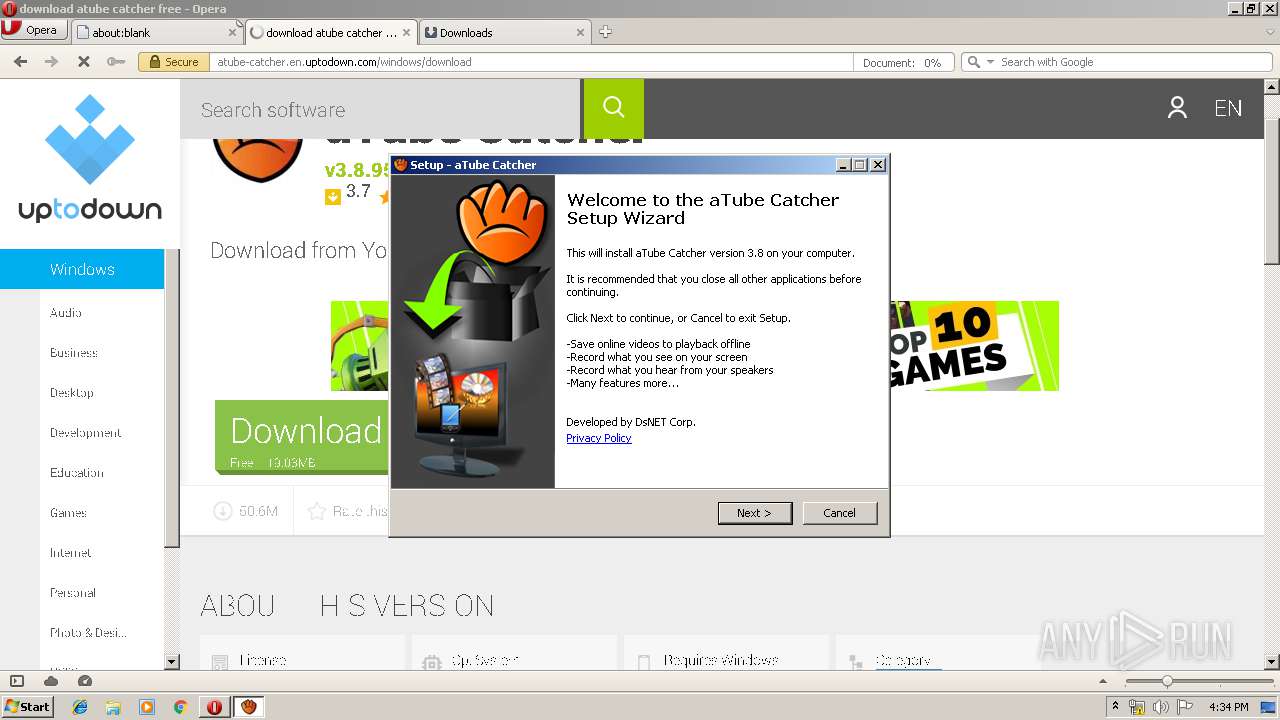
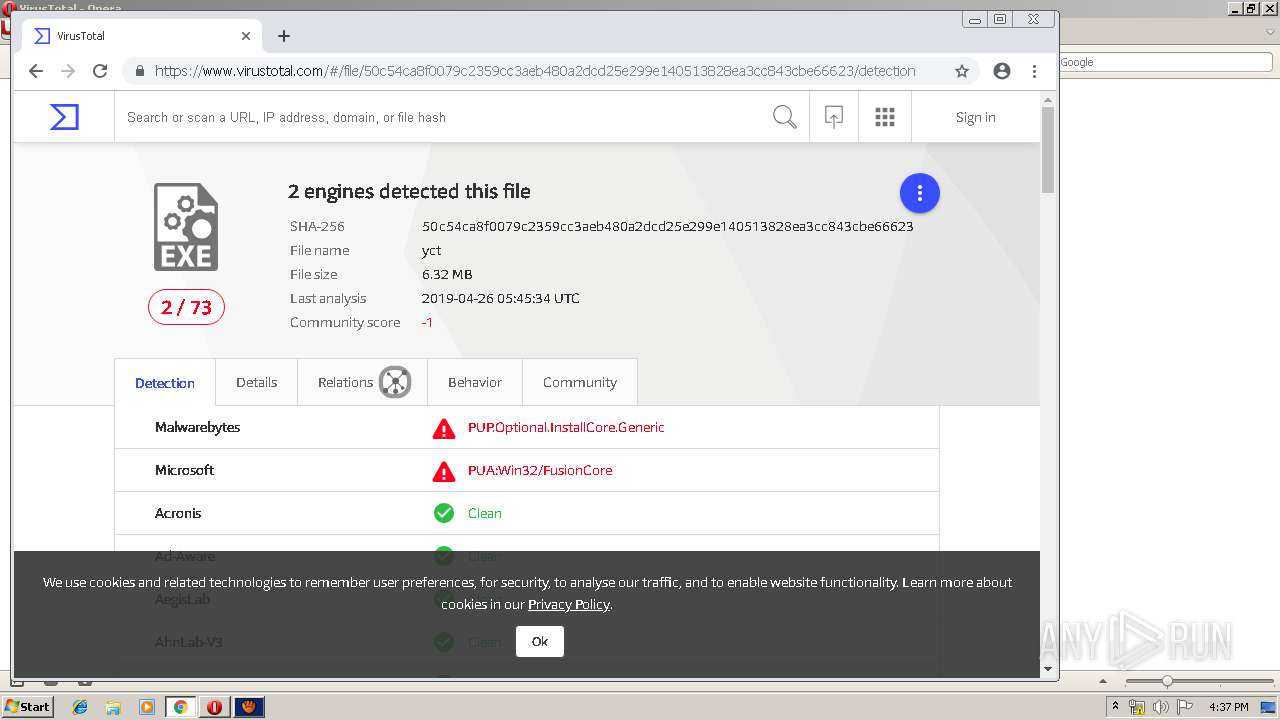
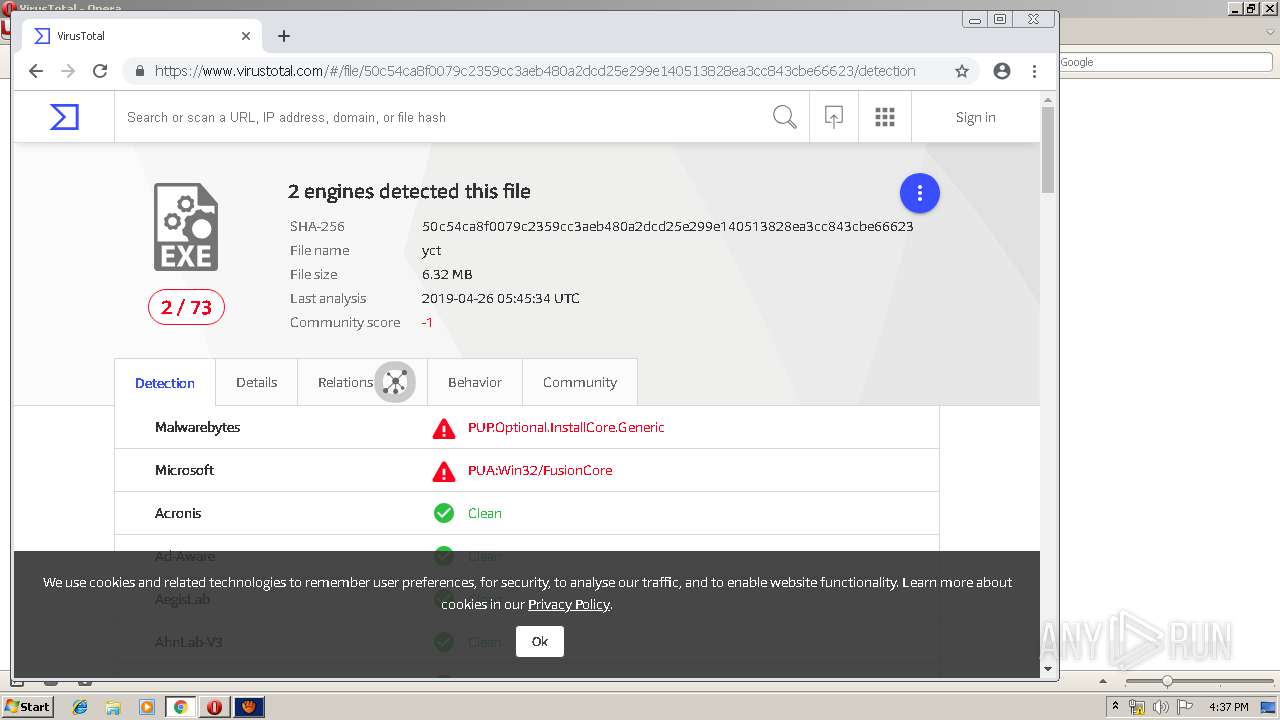
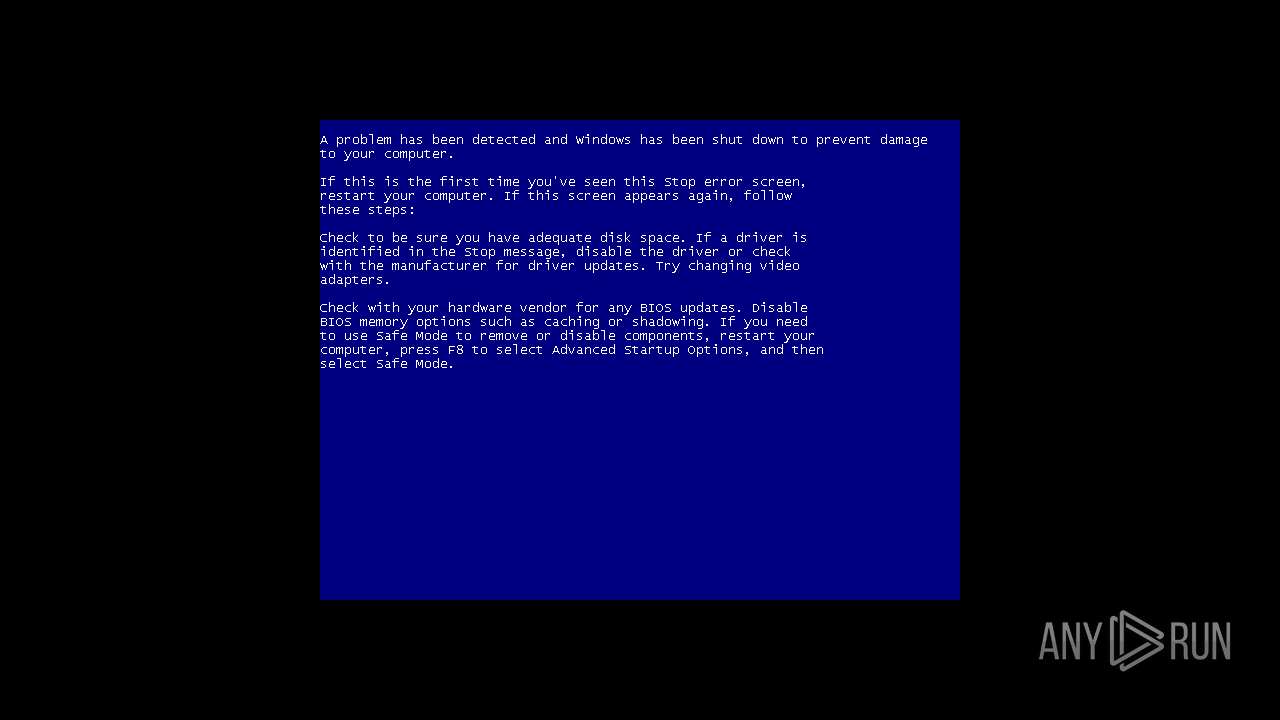
| Verdict: | Malicious activity |
| Threats: | Adware is a form of malware that targets users with unwanted advertisements, often disrupting their browsing experience. It typically infiltrates systems through software bundling, malicious websites, or deceptive downloads. Once installed, it may track user activity, collect sensitive data, and display intrusive ads, including pop-ups or banners. Some advanced adware variants can bypass security measures and establish persistence on devices, making removal challenging. Additionally, adware can create vulnerabilities that other malware can exploit, posing a significant risk to user privacy and system security. |
| Analysis date: | April 30, 2019, 15:32:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | C4D3032F35506C40227284A283EAE990 |
| SHA1: | 4372B607B1F3B2CED3D5A73BDAFC1EF5F463AE4A |
| SHA256: | 1A93540798AD08008EE8732D952BC1C987271EC00844841D66187CEABC1A2315 |
| SSDEEP: | 3:N8rNGEgXkVsbd3SMm:2+XcU3Sf |
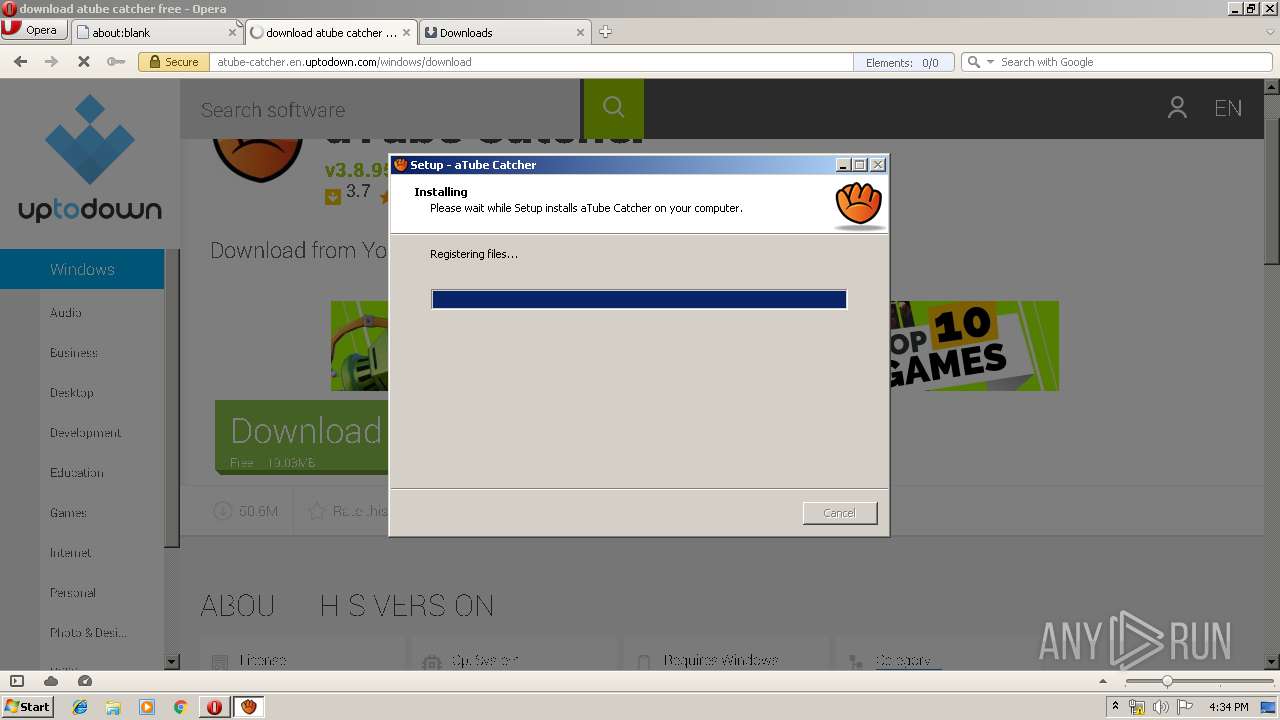
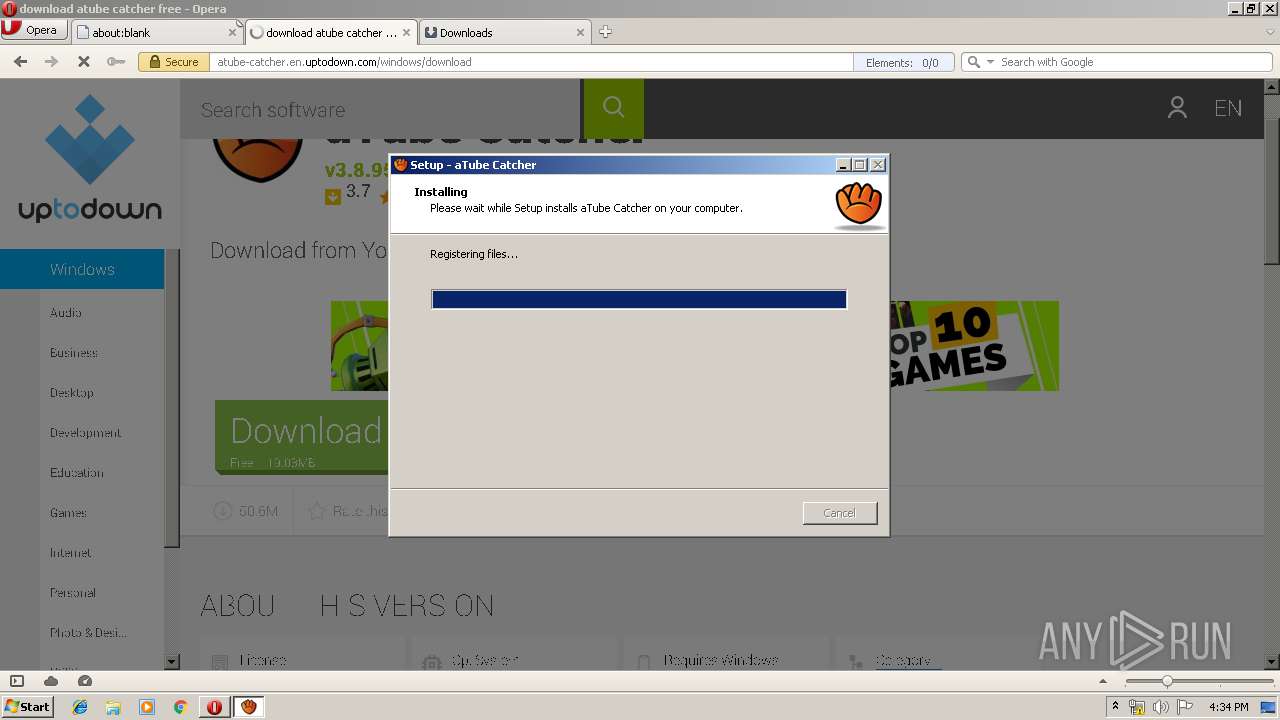
MALICIOUS
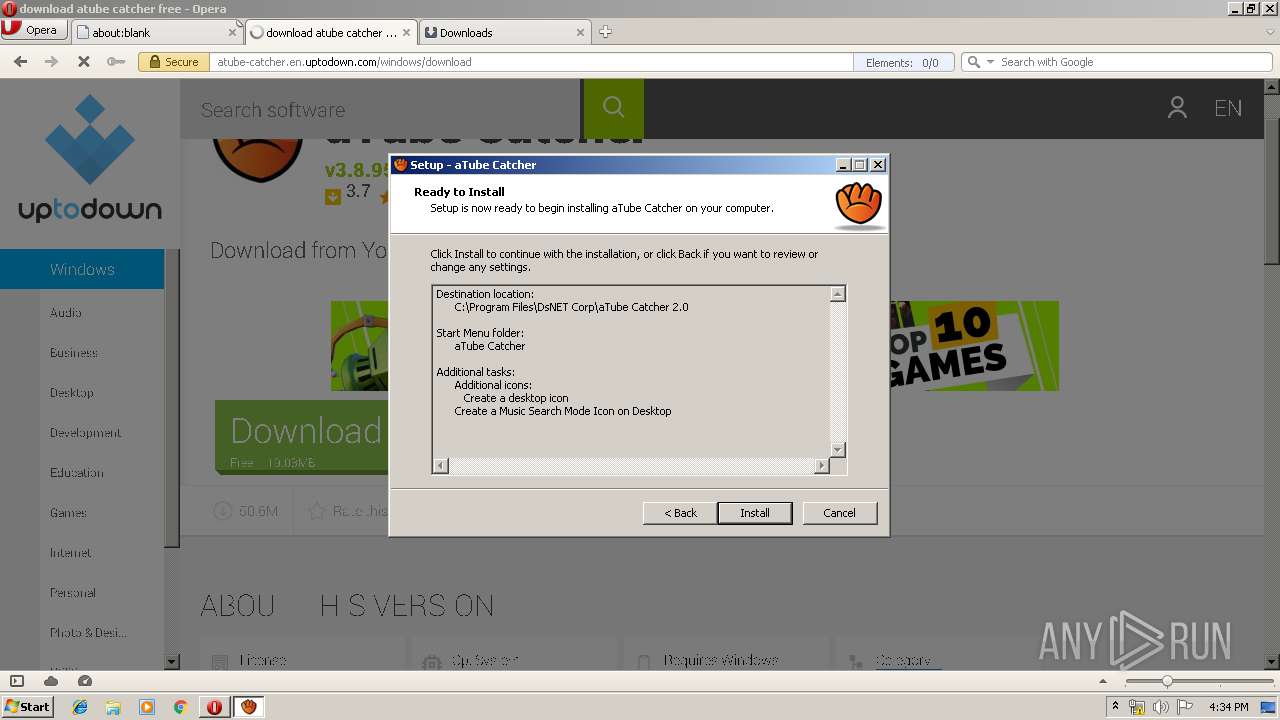
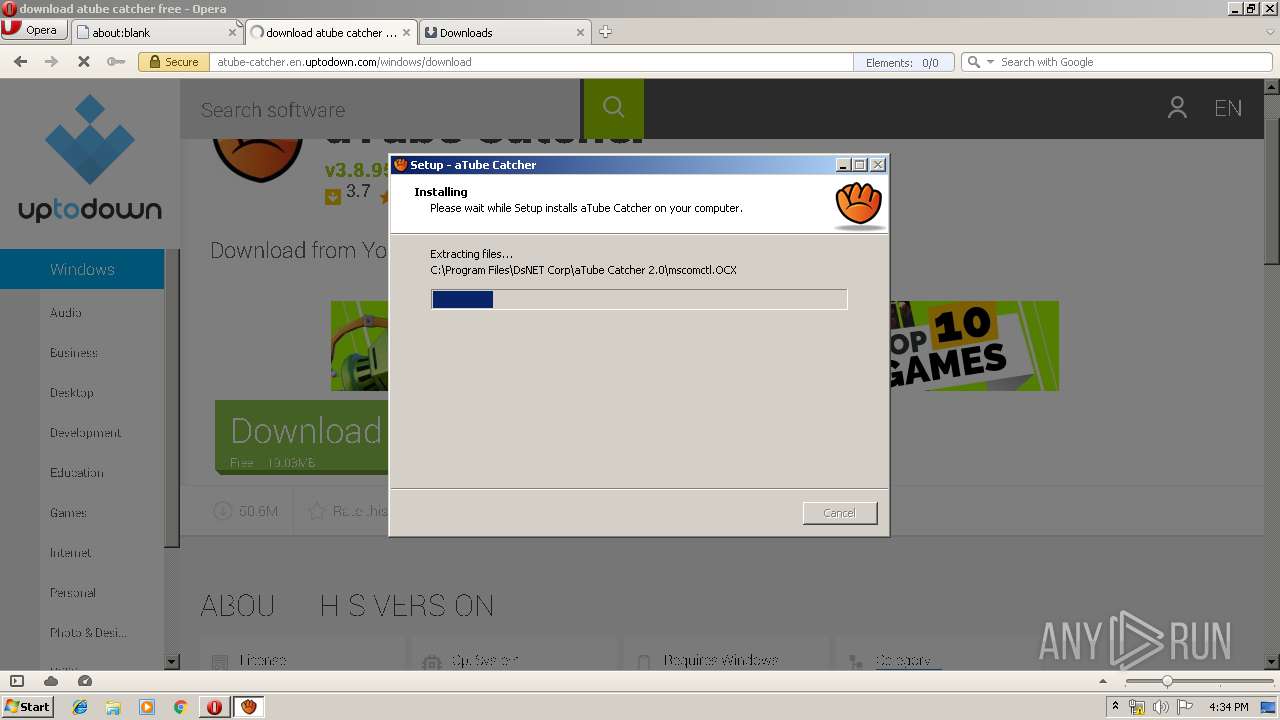
Application was dropped or rewritten from another process
- atube-catcher-3-8-9510.exe (PID: 1724)
- atube-catcher-3-8-9510.exe (PID: 1728)
- cookie_mmm_irs_ppi_902_451_o.exe (PID: 2496)
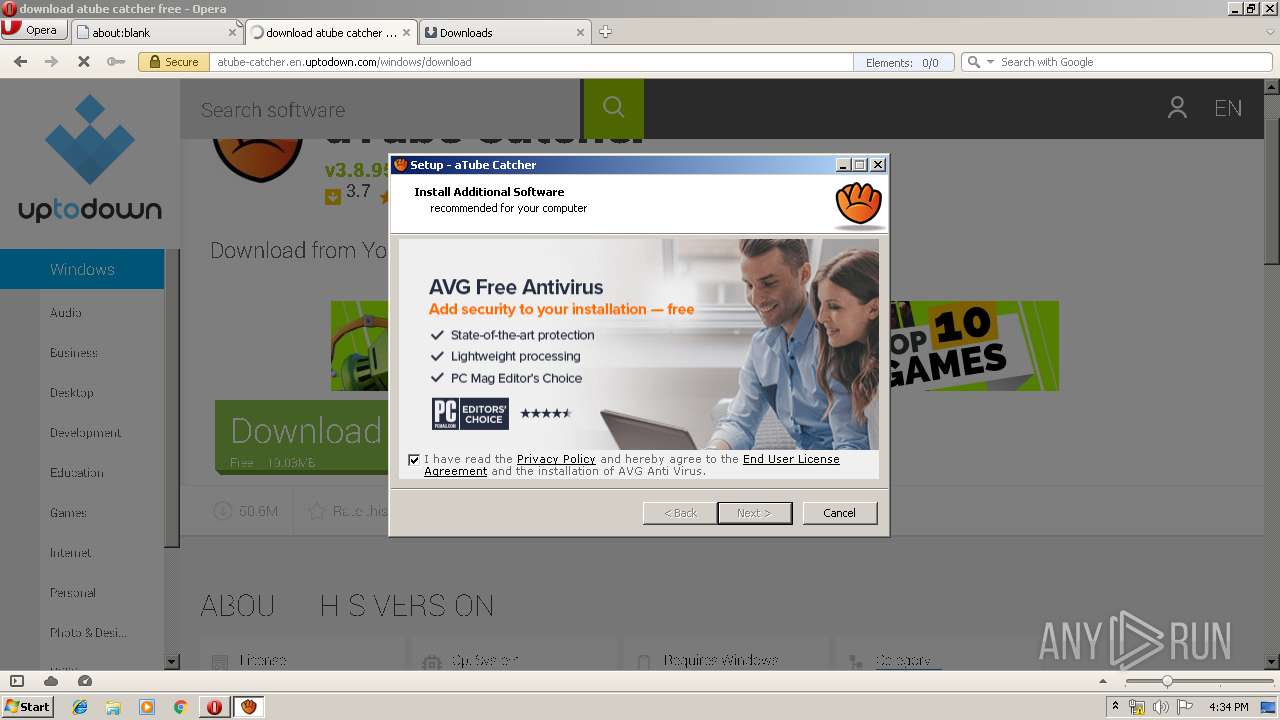
- avg_antivirus_free_setup.exe (PID: 2192)
- instup.exe (PID: 3064)
- instup.exe (PID: 3580)
- sbr.exe (PID: 2996)
- AvEmUpdate.exe (PID: 1640)
- AvEmUpdate.exe (PID: 1336)
- AvEmUpdate.exe (PID: 2684)
- AvEmUpdate.exe (PID: 1444)
- avBugReport.exe (PID: 3288)
- overseer.exe (PID: 3528)
- instup.exe (PID: 3704)
- AVGSvc.exe (PID: 3304)
- wsc_proxy.exe (PID: 2688)
- RegSvr.exe (PID: 2356)
- RegSvr.exe (PID: 1472)
- eWorker.exe (PID: 3900)
- aswRunDll.exe (PID: 3292)
- SetupInf.exe (PID: 2104)
- SetupInf.exe (PID: 3632)
- SetupInf.exe (PID: 388)
- SetupInf.exe (PID: 3732)
- engsup.exe (PID: 1760)
- engsup.exe (PID: 544)
- aswEngSrv.exe (PID: 3476)
- wsc_proxy.exe (PID: 3576)
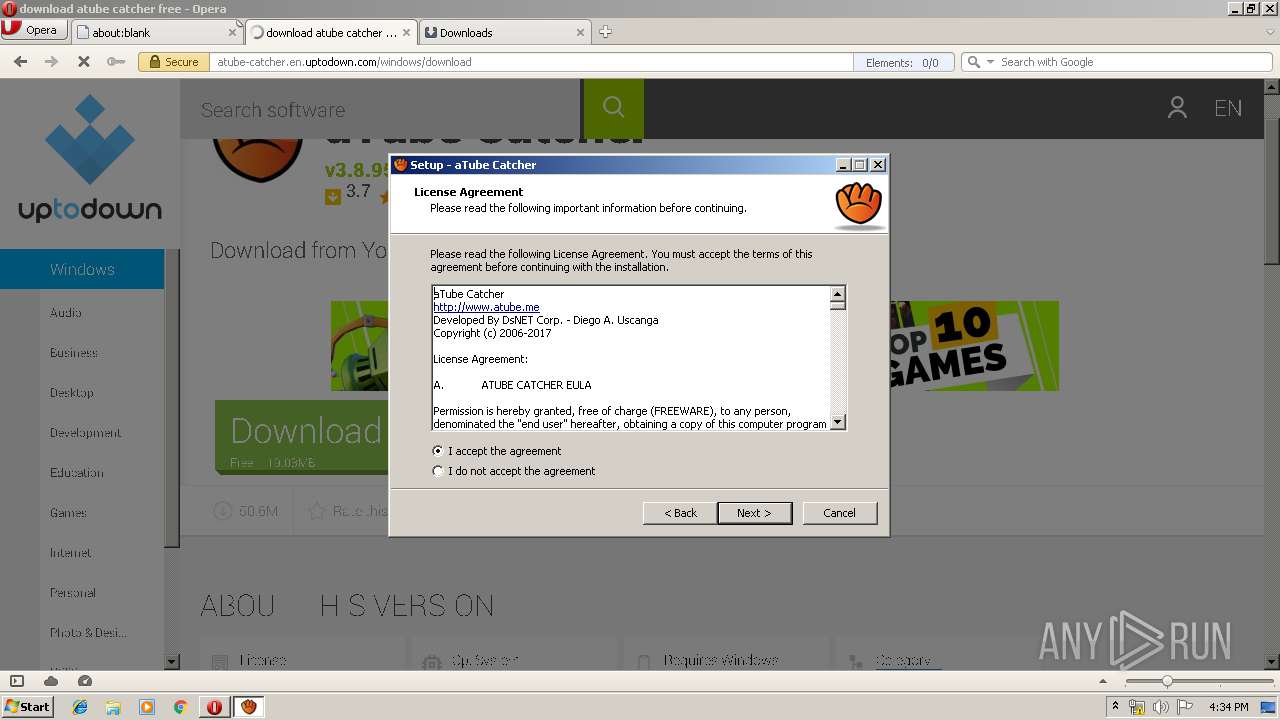
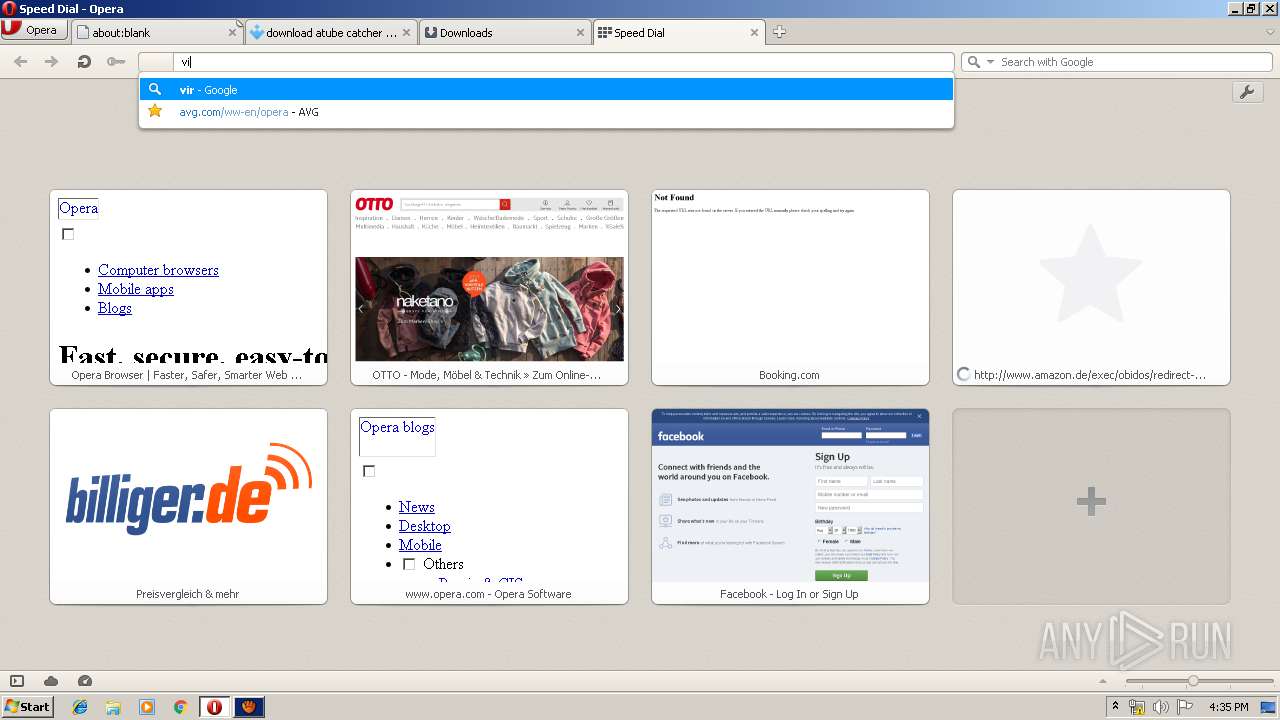
INSTALLCORE was detected
- atube-catcher-3-8-9510.tmp (PID: 3648)
Connects to CnC server
- atube-catcher-3-8-9510.tmp (PID: 3648)
Loads dropped or rewritten executable
- regsvr32.exe (PID: 2816)
- regsvr32.exe (PID: 2400)
- regsvr32.exe (PID: 2556)
- regsvr32.exe (PID: 1660)
- regsvr32.exe (PID: 2184)
- regsvr32.exe (PID: 864)
- regsvr32.exe (PID: 992)
- regsvr32.exe (PID: 4076)
- regsvr32.exe (PID: 1872)
- instup.exe (PID: 3064)
- regsvr32.exe (PID: 900)
- regsvr32.exe (PID: 3316)
- regsvr32.exe (PID: 3436)
- regsvr32.exe (PID: 1000)
- regsvr32.exe (PID: 1136)
- regsvr32.exe (PID: 3892)
- regsvr32.exe (PID: 2108)
- regsvr32.exe (PID: 2448)
- regsvr32.exe (PID: 728)
- regsvr32.exe (PID: 3808)
- regsvr32.exe (PID: 3564)
- regsvr32.exe (PID: 3496)
- regsvr32.exe (PID: 3400)
- regsvr32.exe (PID: 2708)
- regsvr32.exe (PID: 3704)
- regsvr32.exe (PID: 3640)
- regsvr32.exe (PID: 1360)
- instup.exe (PID: 3580)
- AvEmUpdate.exe (PID: 1640)
- AvEmUpdate.exe (PID: 1336)
- AvEmUpdate.exe (PID: 2684)
- AvEmUpdate.exe (PID: 1444)
- avBugReport.exe (PID: 3288)
- RegSvr.exe (PID: 2356)
- RegSvr.exe (PID: 1472)
- aswRunDll.exe (PID: 3292)
- engsup.exe (PID: 1760)
- AVGSvc.exe (PID: 3304)
- engsup.exe (PID: 544)
- instup.exe (PID: 3704)
- chrome.exe (PID: 2152)
- chrome.exe (PID: 2940)
- aswEngSrv.exe (PID: 3476)
- chrome.exe (PID: 2204)
Registers / Runs the DLL via REGSVR32.EXE
- atube-catcher-3-8-9510.tmp (PID: 3648)
Changes settings of System certificates
- instup.exe (PID: 3064)
- AVGSvc.exe (PID: 3304)
Downloads executable files from the Internet
- cookie_mmm_irs_ppi_902_451_o.exe (PID: 2496)
- AvEmUpdate.exe (PID: 1336)
Changes the autorun value in the registry
- instup.exe (PID: 3580)
- rundll32.exe (PID: 3504)
Loads the Task Scheduler COM API
- AvEmUpdate.exe (PID: 1336)
- overseer.exe (PID: 3528)
- AvEmUpdate.exe (PID: 1640)
SUSPICIOUS
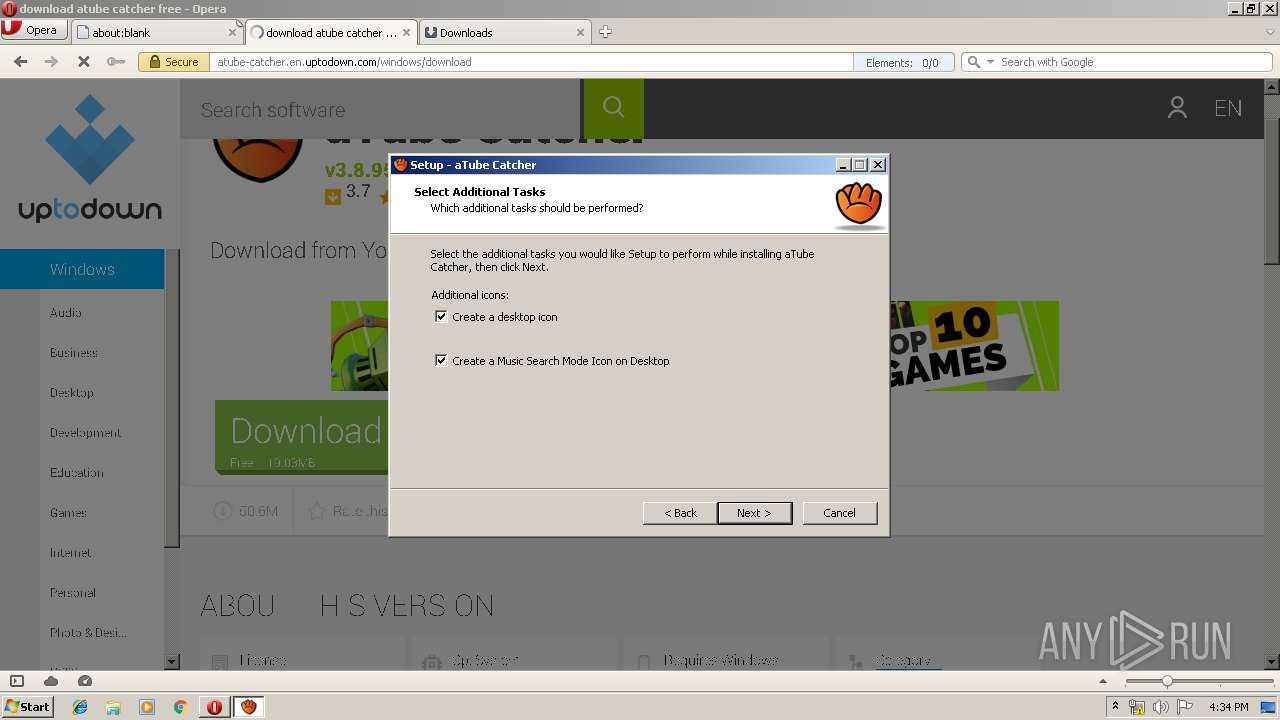
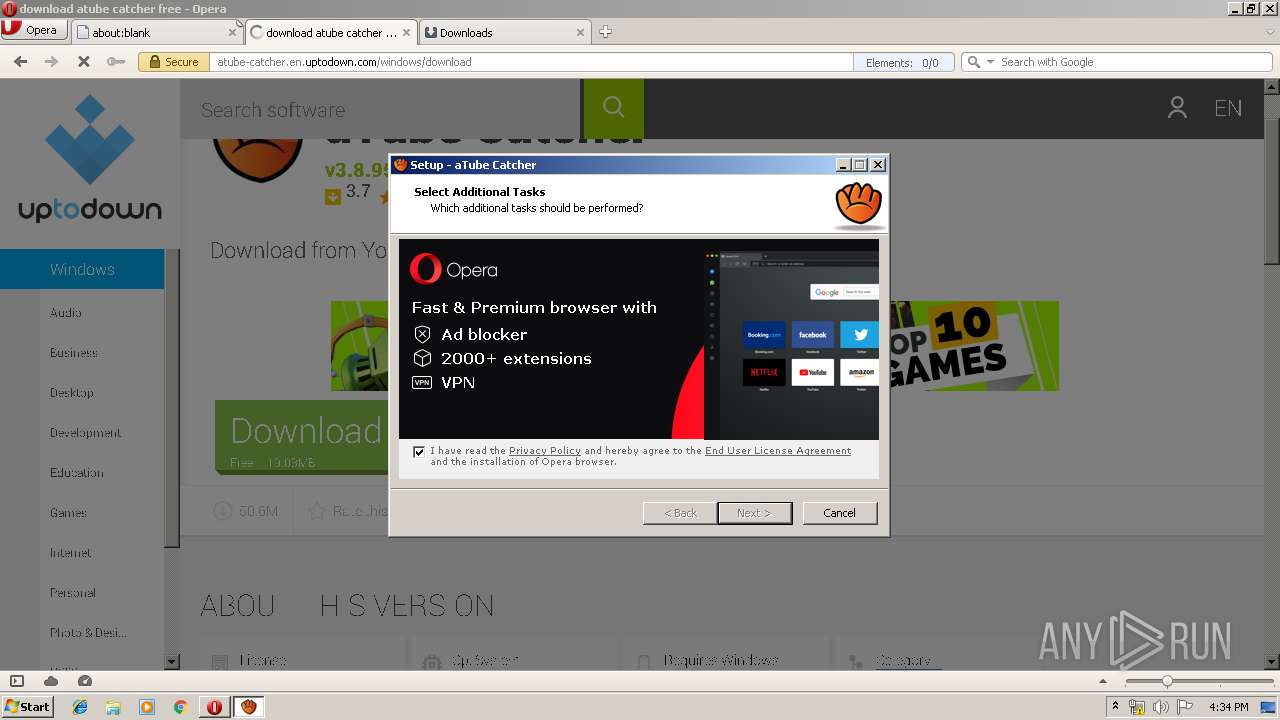
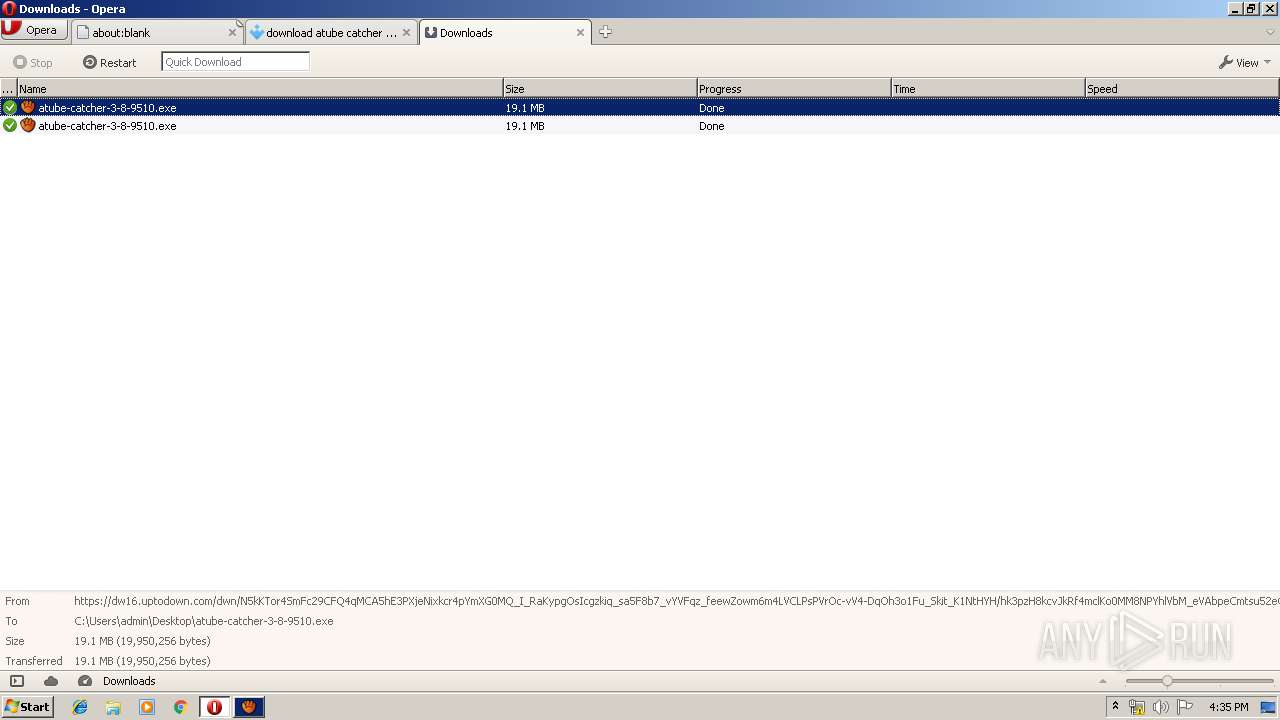
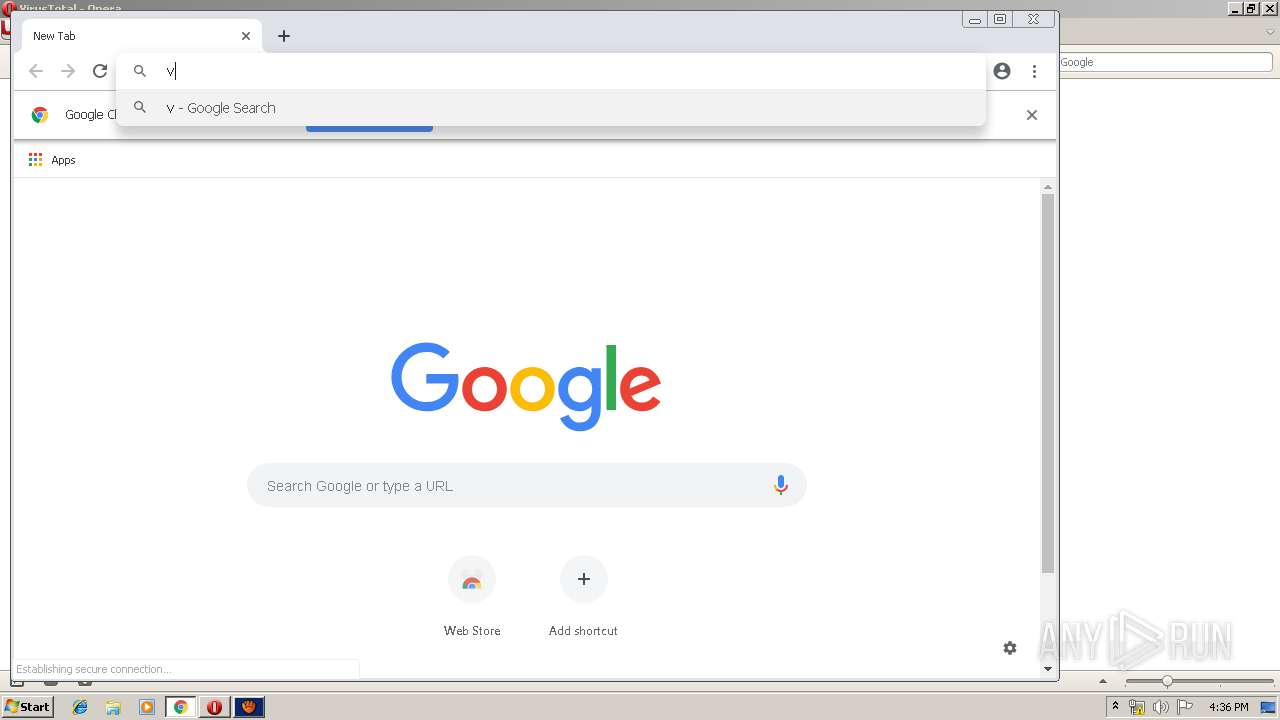
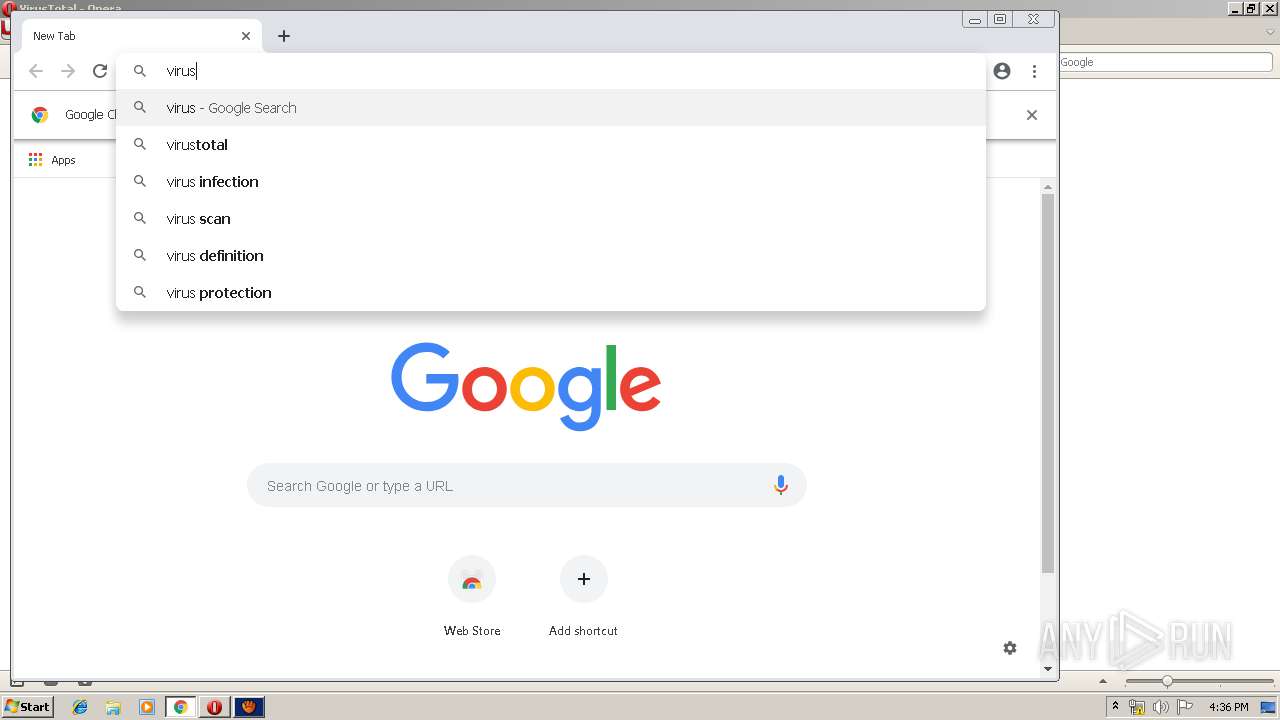
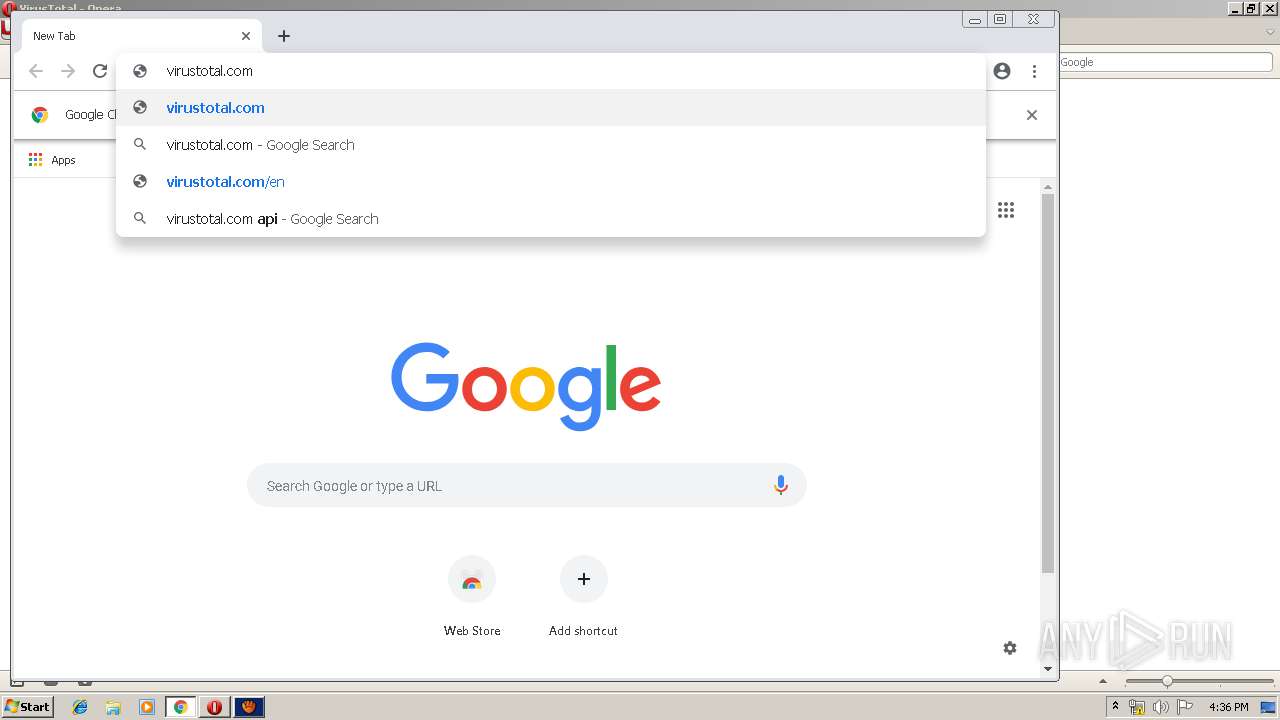
Executable content was dropped or overwritten
- opera.exe (PID: 2208)
- atube-catcher-3-8-9510.exe (PID: 1728)
- atube-catcher-3-8-9510.tmp (PID: 3648)
- atube-catcher-3-8-9510.exe (PID: 1724)
- cmd.exe (PID: 3892)
- cookie_mmm_irs_ppi_902_451_o.exe (PID: 2496)
- avg_antivirus_free_setup.exe (PID: 2192)
- instup.exe (PID: 3064)
- instup.exe (PID: 3580)
- rundll32.exe (PID: 3504)
- AvEmUpdate.exe (PID: 1336)
- instup.exe (PID: 3704)
- AVGSvc.exe (PID: 3304)
Reads the Windows organization settings
- atube-catcher-3-8-9510.tmp (PID: 3648)
Reads Environment values
- atube-catcher-3-8-9510.tmp (PID: 3648)
- AVGSvc.exe (PID: 3304)
Reads the machine GUID from the registry
- atube-catcher-3-8-9510.tmp (PID: 3648)
Reads Windows owner or organization settings
- atube-catcher-3-8-9510.tmp (PID: 3648)
Reads Windows Product ID
- atube-catcher-3-8-9510.tmp (PID: 3648)
Reads internet explorer settings
- atube-catcher-3-8-9510.tmp (PID: 3648)
Reads CPU info
- atube-catcher-3-8-9510.tmp (PID: 3648)
Reads the date of Windows installation
- atube-catcher-3-8-9510.tmp (PID: 3648)
Uses TASKKILL.EXE to kill process
- atube-catcher-3-8-9510.tmp (PID: 3648)
Low-level read access rights to disk partition
- cookie_mmm_irs_ppi_902_451_o.exe (PID: 2496)
- avg_antivirus_free_setup.exe (PID: 2192)
- instup.exe (PID: 3064)
- instup.exe (PID: 3580)
- AvEmUpdate.exe (PID: 1336)
- AvEmUpdate.exe (PID: 2684)
- AvEmUpdate.exe (PID: 1444)
- avBugReport.exe (PID: 3288)
- overseer.exe (PID: 3528)
- AVGSvc.exe (PID: 3304)
- instup.exe (PID: 3704)
- wsc_proxy.exe (PID: 2688)
Starts CMD.EXE for commands execution
- atube-catcher-3-8-9510.tmp (PID: 3648)
- cmd.exe (PID: 4068)
Application launched itself
- cmd.exe (PID: 4068)
- AvEmUpdate.exe (PID: 1336)
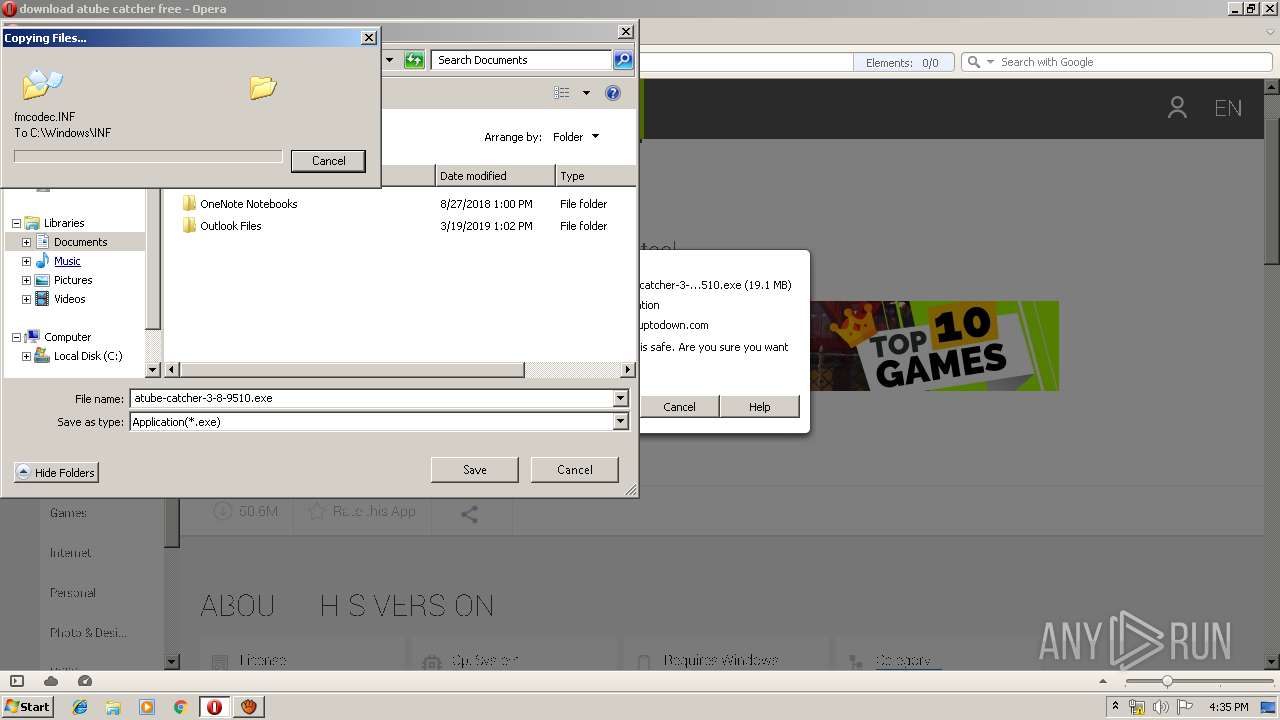
Creates files in the Windows directory
- atube-catcher-3-8-9510.tmp (PID: 3648)
- regsvr32.exe (PID: 2400)
- cookie_mmm_irs_ppi_902_451_o.exe (PID: 2496)
- avg_antivirus_free_setup.exe (PID: 2192)
- instup.exe (PID: 3064)
- instup.exe (PID: 3580)
- rundll32.exe (PID: 3504)
- AvEmUpdate.exe (PID: 1336)
- AVGSvc.exe (PID: 3304)
Creates COM task schedule object
- regsvr32.exe (PID: 2816)
- regsvr32.exe (PID: 2400)
- regsvr32.exe (PID: 2184)
- regsvr32.exe (PID: 2448)
- regsvr32.exe (PID: 728)
- regsvr32.exe (PID: 1000)
- regsvr32.exe (PID: 3496)
- regsvr32.exe (PID: 3316)
- regsvr32.exe (PID: 900)
- regsvr32.exe (PID: 3436)
- regsvr32.exe (PID: 1136)
- regsvr32.exe (PID: 2108)
- regsvr32.exe (PID: 3564)
- regsvr32.exe (PID: 3400)
- regsvr32.exe (PID: 2708)
- regsvr32.exe (PID: 3704)
- regsvr32.exe (PID: 3640)
- RegSvr.exe (PID: 2356)
- RegSvr.exe (PID: 1472)
- instup.exe (PID: 3580)
Creates files in the program directory
- avg_antivirus_free_setup.exe (PID: 2192)
- instup.exe (PID: 3064)
- AvEmUpdate.exe (PID: 1336)
- instup.exe (PID: 3580)
- avBugReport.exe (PID: 3288)
- engsup.exe (PID: 1760)
- instup.exe (PID: 3704)
- wsc_proxy.exe (PID: 2688)
- AvEmUpdate.exe (PID: 1640)
- engsup.exe (PID: 544)
- AVGSvc.exe (PID: 3304)
Adds / modifies Windows certificates
- instup.exe (PID: 3064)
Removes files from Windows directory
- instup.exe (PID: 3064)
- instup.exe (PID: 3580)
- rundll32.exe (PID: 3504)
- AvEmUpdate.exe (PID: 1336)
- avg_antivirus_free_setup.exe (PID: 2192)
Searches for installed software
- atube-catcher-3-8-9510.tmp (PID: 3648)
Starts itself from another location
- instup.exe (PID: 3064)
Uses RUNDLL32.EXE to load library
- atube-catcher-3-8-9510.tmp (PID: 3648)
Creates a software uninstall entry
- instup.exe (PID: 3580)
Modifies the open verb of a shell class
- instup.exe (PID: 3580)
Creates files in the driver directory
- instup.exe (PID: 3580)
- AvEmUpdate.exe (PID: 1336)
Creates or modifies windows services
- instup.exe (PID: 3580)
Reads the cookies of Google Chrome
- engsup.exe (PID: 544)
Reads the cookies of Mozilla Firefox
- engsup.exe (PID: 544)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2488)
INFO
Application was dropped or rewritten from another process
- atube-catcher-3-8-9510.tmp (PID: 2604)
- atube-catcher-3-8-9510.tmp (PID: 3648)
Loads dropped or rewritten executable
- atube-catcher-3-8-9510.tmp (PID: 3648)
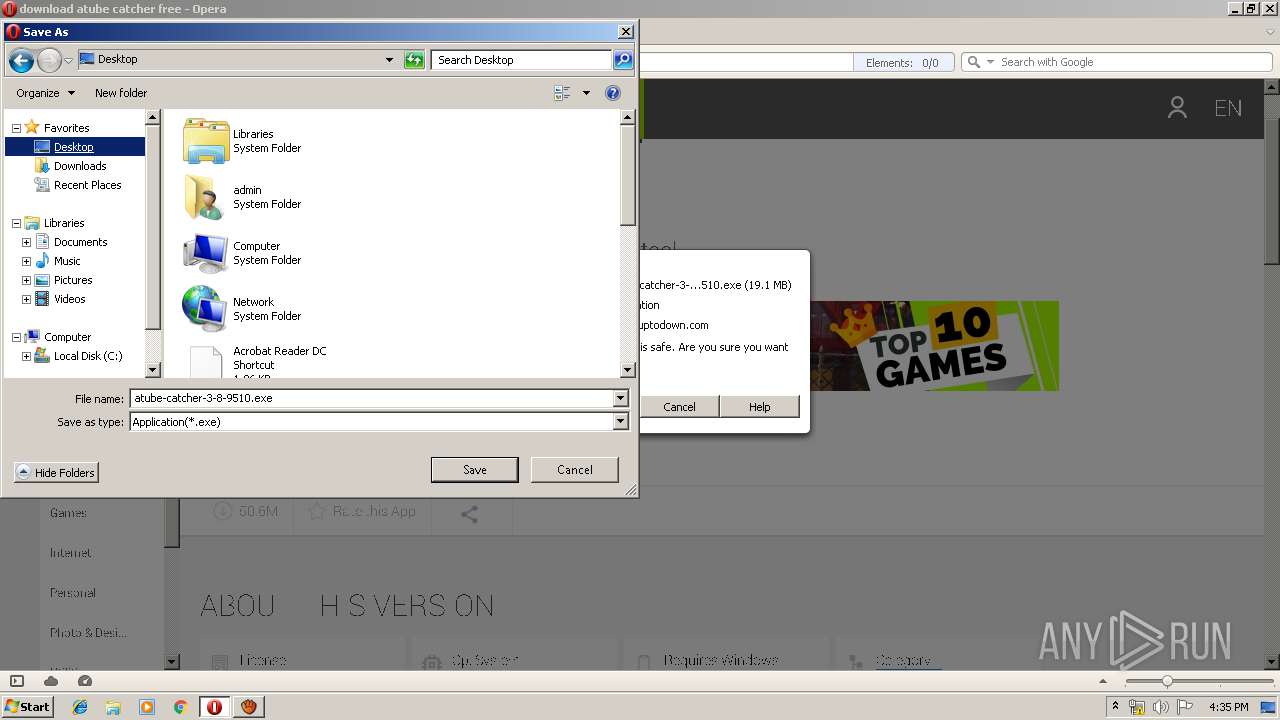
Creates files in the user directory
- opera.exe (PID: 2208)
Dropped object may contain Bitcoin addresses
- atube-catcher-3-8-9510.tmp (PID: 3648)
- instup.exe (PID: 3580)
Creates files in the program directory
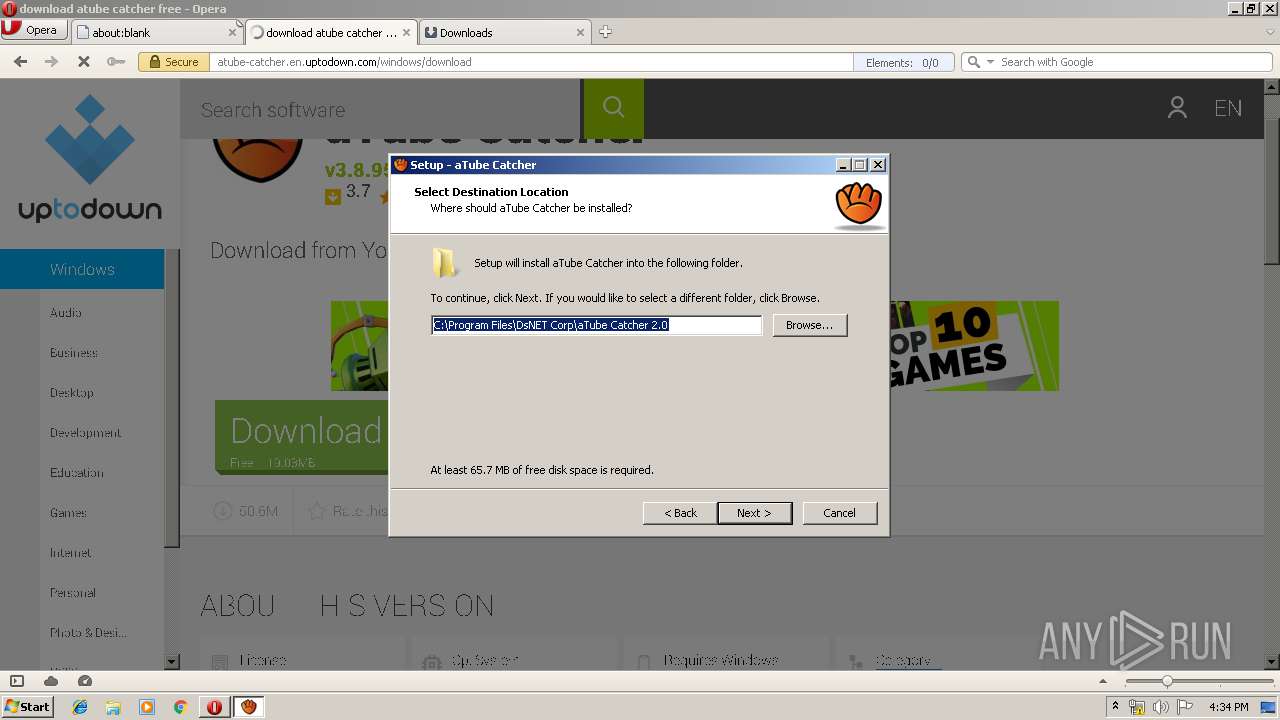
- atube-catcher-3-8-9510.tmp (PID: 3648)
Creates a software uninstall entry
- atube-catcher-3-8-9510.tmp (PID: 3648)
Application launched itself
- chrome.exe (PID: 2488)
Reads settings of System Certificates
- chrome.exe (PID: 2488)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
139
Monitored processes
94
Malicious processes
31
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 388 | "C:\Program Files\AVG\Antivirus\SetupInf.exe" /catalog:avgVmm.cat /uninstall | C:\Program Files\AVG\Antivirus\SetupInf.exe | — | instup.exe | |||||||||||
User: admin Company: AVG Technologies CZ, s.r.o. Integrity Level: HIGH Description: AVG Antivirus Installer Exit code: 0 Version: 19.4.4318.0 Modules
| |||||||||||||||
| 408 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=944,9151866637662974181,10945245389449120561,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=249875208116199373 --mojo-platform-channel-handle=4280 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 544 | "C:\Program Files\AVG\Antivirus\defs\19042903\engsup.exe" /avg /get_download_cookie /get_latest_ga_client_id /get_latest_gclid | C:\Program Files\AVG\Antivirus\defs\19042903\engsup.exe | — | instup.exe | |||||||||||
User: admin Company: AVG Technologies CZ, s.r.o. Integrity Level: HIGH Description: AVG Antivirus vps tool Exit code: 2 Version: 18.0.531.0 Modules
| |||||||||||||||
| 728 | "C:\Windows\system32\regsvr32.exe" /s "C:\Program Files\DsNET Corp\aTube Catcher 2.0\ExButton.dll" | C:\Windows\system32\regsvr32.exe | — | atube-catcher-3-8-9510.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 864 | "C:\Windows\system32\regsvr32.exe" /s "C:\Program Files\DsNET Corp\aTube Catcher 2.0\DSNTabCtrl.ocx" | C:\Windows\system32\regsvr32.exe | — | atube-catcher-3-8-9510.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 900 | "C:\Windows\system32\regsvr32.exe" /s "C:\Windows\system32\DartCertificate.dll" | C:\Windows\system32\regsvr32.exe | — | atube-catcher-3-8-9510.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 916 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=944,9151866637662974181,10945245389449120561,131072 --enable-features=PasswordImport --service-pipe-token=1568350653276620767 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1568350653276620767 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2100 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 992 | "C:\Windows\system32\regsvr32.exe" /s "C:\Program Files\DsNET Corp\aTube Catcher 2.0\dsnaic.ocx" | C:\Windows\system32\regsvr32.exe | — | atube-catcher-3-8-9510.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1000 | "C:\Windows\system32\regsvr32.exe" /s "C:\Program Files\DsNET Corp\aTube Catcher 2.0\DSNCLiteTimer.dll" | C:\Windows\system32\regsvr32.exe | — | atube-catcher-3-8-9510.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1136 | "C:\Windows\system32\regsvr32.exe" /s "C:\Program Files\DsNET Corp\aTube Catcher 2.0\StarBurnX12.dll" | C:\Windows\system32\regsvr32.exe | atube-catcher-3-8-9510.tmp | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
14 147
Read events
4 282
Write events
9 754
Delete events
111
Modification events
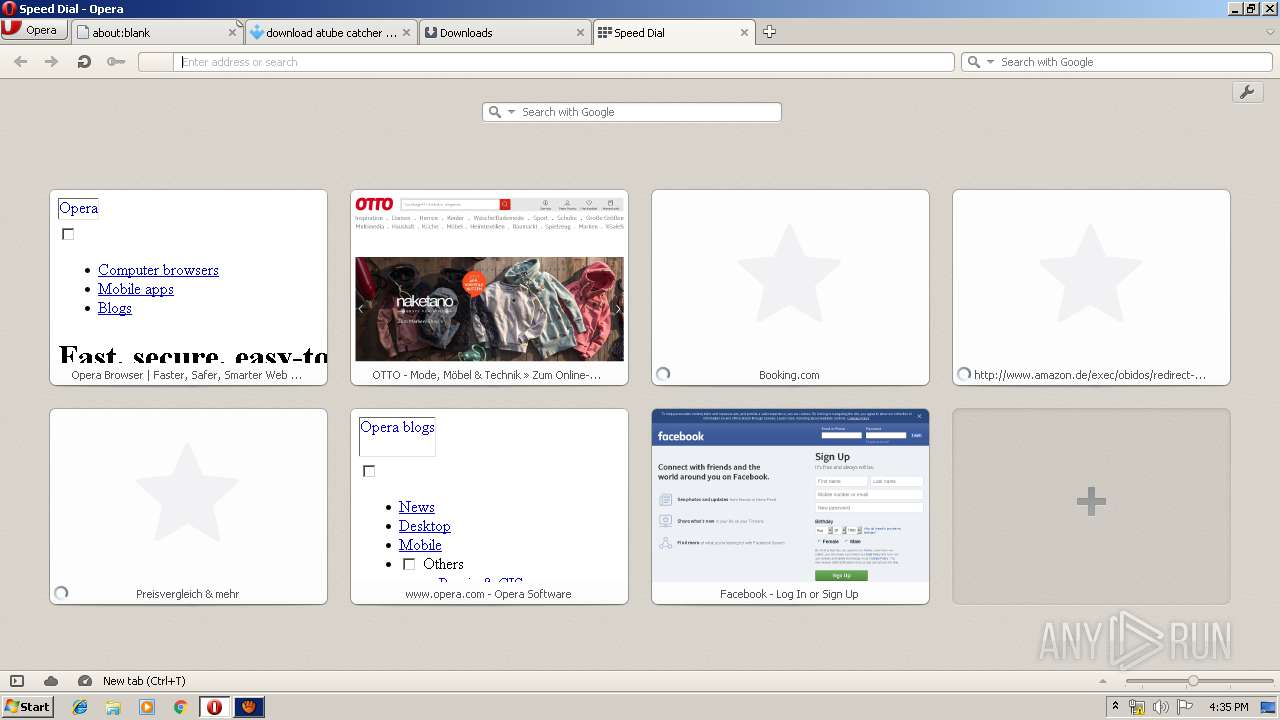
| (PID) Process: | (2208) opera.exe | Key: | HKEY_CURRENT_USER\Software\Opera Software |
| Operation: | write | Name: | Last CommandLine v2 |
Value: C:\Program Files\Opera\opera.exe https://atube-catcher.en.uptodown.com/windows | |||
| (PID) Process: | (2208) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2208) opera.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2208) opera.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3648) atube-catcher-3-8-9510.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 400E000022034D206AFFD401 | |||
| (PID) Process: | (3648) atube-catcher-3-8-9510.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 726BB94D0C0896DD817B1C43D716DB65F52F8592E997C359CB05CBAED0893F34 | |||
| (PID) Process: | (3648) atube-catcher-3-8-9510.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (3648) atube-catcher-3-8-9510.tmp | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3648) atube-catcher-3-8-9510.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3648) atube-catcher-3-8-9510.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
475
Suspicious files
288
Text files
889
Unknown types
87
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2208 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\opr6C71.tmp | — | |
MD5:— | SHA256:— | |||
| 2208 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr6C82.tmp | — | |
MD5:— | SHA256:— | |||
| 2208 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr6D00.tmp | — | |
MD5:— | SHA256:— | |||
| 2208 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\tasks.xml | xml | |
MD5:77490D80EDFC003A47A033B9C9EF6E44 | SHA256:301D1A4F71F4AD6F5A90F045BCD015F9680B59DC43F0E5FCFE496CCD36F09669 | |||
| 2208 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\cache\sesn\opr00002.tmp | woff | |
MD5:AEF1A9B003D289A1414393581265736C | SHA256:0F1CB1E0603C674DDEE7039B4D4538A4BE1C6F29EA5E9784729D91505410C0C0 | |||
| 2208 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\0ZVBR5JY7K8E25QXYTRW.temp | — | |
MD5:— | SHA256:— | |||
| 2208 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opssl6.dat | binary | |
MD5:E9EE63115EC2BF6B0C6B0BC7A60667EF | SHA256:133CE700BF256E38B674D5C9E72A51B6D7A02B33BD397BDE5324ACEACD9492B9 | |||
| 2208 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\operaprefs.ini | text | |
MD5:94E75F6FC06CAF8A9354724DEBD30CE7 | SHA256:B77F8E766326A1F2E4B550AA1D0773C4A9E9FE33AB9E23772D50481EA1CD692C | |||
| 2208 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\cache\sesn\opr00001.tmp | woff | |
MD5:8E31FF68F04E2E392797F7A31BEF62B4 | SHA256:8FE23E5013516BA46BBC925CC89C715FA0BBD55AB6059DDAE29FF8CF2AFCB4A4 | |||
| 2208 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\opr7A7E.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
190
TCP/UDP connections
422
DNS requests
179
Threats
31
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2208 | opera.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/DigiCertGlobalRootCA.crl | US | der | 581 b | whitelisted |
2208 | opera.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEAOXQPQlVpLtFek%2BmcpabOk%3D | US | der | 471 b | whitelisted |
2208 | opera.exe | GET | 200 | 216.58.206.3:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDYccUblrGAlwEAAAAAL%2BwO | US | der | 470 b | whitelisted |
3648 | atube-catcher-3-8-9510.tmp | HEAD | 200 | 146.185.27.45:80 | http://cdneu.repositoryconecptsoftware.com/ofr/Solululadul/icut_v2_2.cis | GB | — | — | malicious |
2208 | opera.exe | GET | 200 | 66.225.197.197:80 | http://crl4.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 543 b | whitelisted |
2208 | opera.exe | GET | 200 | 151.139.128.14:80 | http://crl.usertrust.com/AddTrustExternalCARoot.crl | US | der | 673 b | whitelisted |
2208 | opera.exe | GET | 200 | 2.16.106.113:80 | http://ocsp.comodoca.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBR64T7ooMQqLLQoy%2BemBUYZQOKh6QQUkK9qOpRaC9iQ6hJWc99DtDoo2ucCEQDhRD4cn6K7ZZgJB8vr8cHG | unknown | der | 472 b | whitelisted |
2208 | opera.exe | GET | 200 | 216.58.206.3:80 | http://ocsp.pki.goog/GTSGIAG3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT27bBjYjKBmjX2jXWgnQJKEapsrQQUd8K4UJpndnaxLcKG0IOgfqZ%2BuksCEFay0aSyEt1zBZA74mn5sPo%3D | US | der | 471 b | whitelisted |
2208 | opera.exe | GET | 200 | 216.58.206.3:80 | http://ocsp.pki.goog/GTSGIAG3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT27bBjYjKBmjX2jXWgnQJKEapsrQQUd8K4UJpndnaxLcKG0IOgfqZ%2BuksCEAasQb69UoQdNZpM7kfKQNc%3D | US | der | 471 b | whitelisted |
2208 | opera.exe | GET | 200 | 216.58.206.3:80 | http://crl.pki.goog/gsr2/gsr2.crl | US | der | 546 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2208 | opera.exe | 82.145.215.40:443 | certs.opera.com | Opera Software AS | — | whitelisted |
2208 | opera.exe | 93.184.220.29:80 | crl3.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2208 | opera.exe | 79.137.69.229:443 | admanager.uptodown.com | OVH SAS | PL | unknown |
2208 | opera.exe | 66.225.197.197:80 | crl4.digicert.com | CacheNetworks, Inc. | US | whitelisted |
2208 | opera.exe | 151.139.128.14:80 | crl.comodoca.com | Highwinds Network Group, Inc. | US | suspicious |
2208 | opera.exe | 2.16.106.113:80 | ocsp.comodoca.com | Akamai International B.V. | — | whitelisted |
2208 | opera.exe | 172.217.22.78:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
2208 | opera.exe | 74.125.206.155:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
2208 | opera.exe | 216.58.206.3:80 | crl.pki.goog | Google Inc. | US | whitelisted |
2208 | opera.exe | 172.217.23.174:443 | www.youtube.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
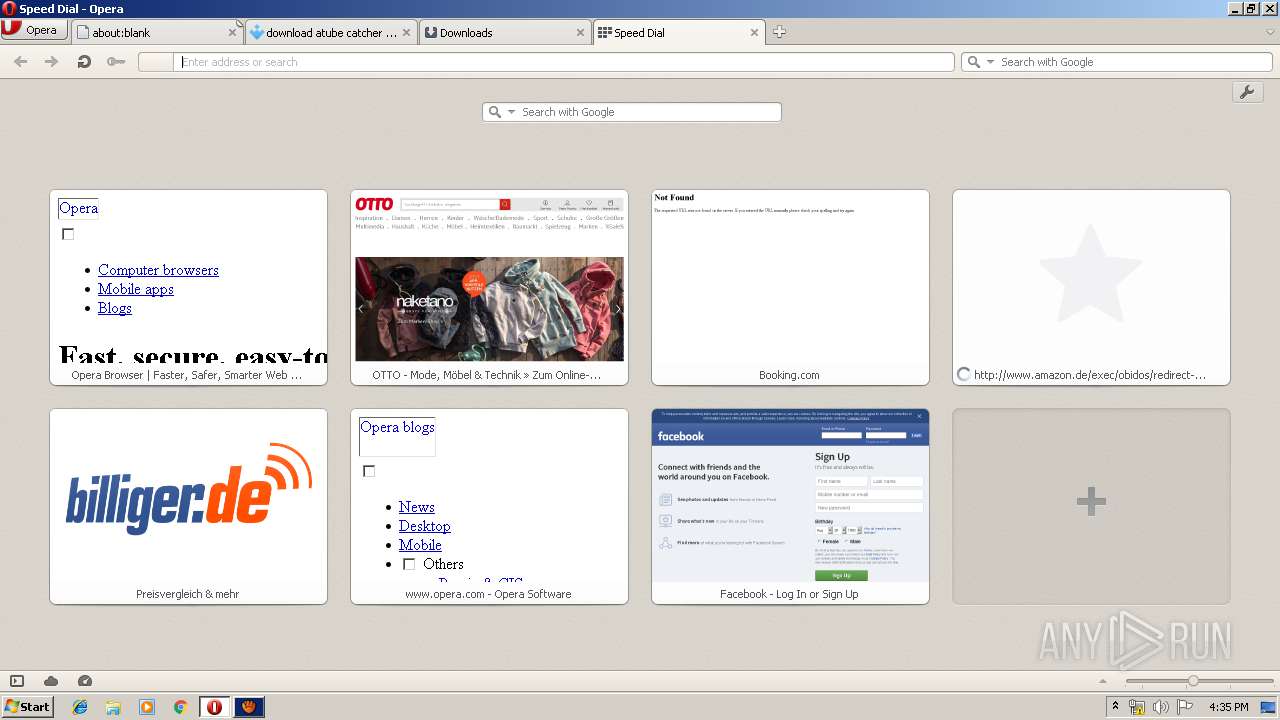
atube-catcher.en.uptodown.com |
| malicious |
sitecheck2.opera.com |
| whitelisted |
certs.opera.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
crl4.digicert.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
stc.utdstc.com |
| suspicious |
img.utdstc.com |
| whitelisted |
admanager.uptodown.com |
| unknown |
crl.comodoca.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
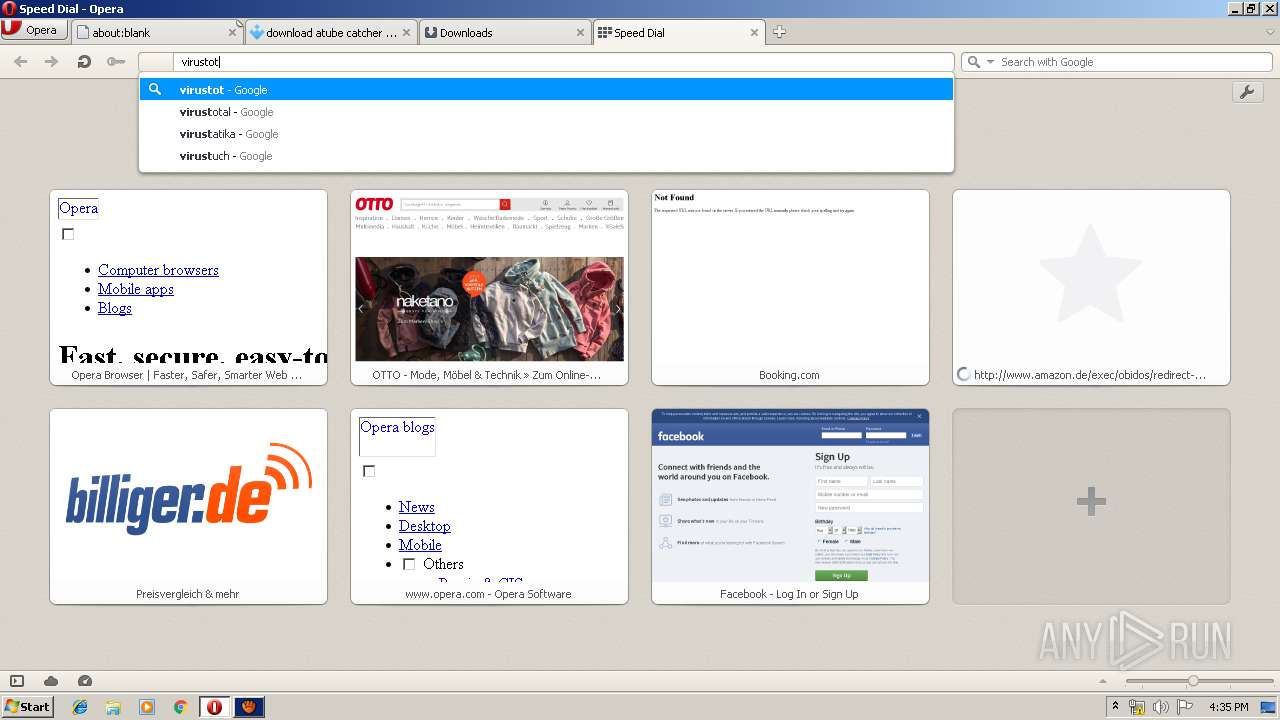
3648 | atube-catcher-3-8-9510.tmp | Misc activity | ADWARE [PTsecurity] PUP.Optional.InstallCore Artifact M2 |
3648 | atube-catcher-3-8-9510.tmp | Misc activity | ADWARE [PTsecurity] PUP.Optional.InstallCore Artifact M1 |
3648 | atube-catcher-3-8-9510.tmp | Misc activity | ADWARE [PTsecurity] PUP.Optional.InstallCore Artifact M3 |
2496 | cookie_mmm_irs_ppi_902_451_o.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1336 | AvEmUpdate.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
26 ETPRO signatures available at the full report
Process | Message |
|---|---|
regsvr32.exe | 16:34:34:972.090 [02356] : [InitDebug]: Level=0
|
regsvr32.exe | HKCR
{
NoRemove AppID
{
'{3DD7EA49-B5E1-4493-895D-C73562138FC0}' = s 'StarBurnXLib'
'StarBurnX12.DLL'
{
val AppID = s '{3DD7EA49-B5E1-4493-895D-C73562138FC0}'
'Version' = s '[!output TYPELIB_VERSION_MAJOR].[!output TYPELIB_VERSION_MINOR]'
}
}
}
|
regsvr32.exe | HKCR
{
StarBurnX.DriveSpeed.12 = s 'DriveSpeed Class'
{
CLSID = s '{E0EEE430-80D8-42D7-8D83-F046AECD7536}'
}
StarBurnX.DriveSpeed = s 'DriveSpeed Class'
{
CLSID = s '{E0EEE430-80D8-42D7-8D83-F046AECD7536}'
CurVer = s 'StarBurnX.DriveSpeed.12'
}
NoRemove CLSID
{
ForceRemove {E0EEE430-80D8-42D7-8D83-F046AECD7536} = s 'DriveSpeed Class'
{
ProgID = s 'StarBurnX.DriveSpeed.12'
VersionIndependentProgID = s 'StarBurnX.DriveSpeed'
ForceRemove 'Programmable'
InprocServer32 = s 'C:\Program Files\DsNET Corp\aTube Catcher 2.0\StarBurnX12.dll'
{
val ThreadingModel = s 'Free'
}
'TypeLib' = s '{93CBA48A-1C58-4648-B22D-8F3588CB8D95}'
'Version' = s '12.0'
}
}
}
|
regsvr32.exe | HKCR
{
StarBurnX.DriveSpeeds.12 = s 'DriveSpeeds Class'
{
CLSID = s '{7169A231-64EC-4702-98AB-05ABB6D882A9}'
}
StarBurnX.DriveSpeeds = s 'DriveSpeeds Class'
{
CLSID = s '{7169A231-64EC-4702-98AB-05ABB6D882A9}'
CurVer = s 'StarBurnX.DriveSpeeds.12'
}
NoRemove CLSID
{
ForceRemove {7169A231-64EC-4702-98AB-05ABB6D882A9} = s 'DriveSpeeds Class'
{
ProgID = s 'StarBurnX.DriveSpeeds.12'
VersionIndependentProgID = s 'StarBurnX.DriveSpeeds'
ForceRemove 'Programmable'
InprocServer32 = s 'C:\Program Files\DsNET Corp\aTube Catcher 2.0\StarBurnX12.dll'
{
val ThreadingModel = s 'Free'
}
'TypeLib' = s '{93CBA48A-1C58-4648-B22D-8F3588CB8D95}'
'Version' = s '12.0'
}
}
}
|
regsvr32.exe | HKCR
{
StarBurnX.DriveInfo.12 = s 'DriveInfo Class'
{
CLSID = s '{996C8DFD-8CE6-43B2-9414-CB6132485363}'
}
StarBurnX.DriveInfo = s 'DriveInfo Class'
{
CLSID = s '{996C8DFD-8CE6-43B2-9414-CB6132485363}'
CurVer = s 'StarBurnX.DriveInfo.12'
}
NoRemove CLSID
{
ForceRemove {996C8DFD-8CE6-43B2-9414-CB6132485363} = s 'DriveInfo Class'
{
ProgID = s 'StarBurnX.DriveInfo.12'
VersionIndependentProgID = s 'StarBurnX.DriveInfo'
ForceRemove 'Programmable'
InprocServer32 = s 'C:\Program Files\DsNET Corp\aTube Catcher 2.0\StarBurnX12.dll'
{
val ThreadingModel = s 'Free'
}
'TypeLib' = s '{93CBA48A-1C58-4648-B22D-8F3588CB8D95}'
'Version' = s '12.0'
}
}
}
|
regsvr32.exe | HKCR
{
StarBurnX.Track.12 = s 'Track Class'
{
CLSID = s '{F750BC9F-72CE-45C6-9D1F-BFEFB0765918}'
}
StarBurnX.Track = s 'Track Class'
{
CLSID = s '{F750BC9F-72CE-45C6-9D1F-BFEFB0765918}'
CurVer = s 'StarBurnX.Track.12'
}
NoRemove CLSID
{
ForceRemove {F750BC9F-72CE-45C6-9D1F-BFEFB0765918} = s 'Track Class'
{
ProgID = s 'StarBurnX.Track.12'
VersionIndependentProgID = s 'StarBurnX.Track'
ForceRemove 'Programmable'
InprocServer32 = s 'C:\Program Files\DsNET Corp\aTube Catcher 2.0\StarBurnX12.dll'
{
val ThreadingModel = s 'Free'
}
'TypeLib' = s '{93CBA48A-1C58-4648-B22D-8F3588CB8D95}'
'Version' = s '12.0'
}
}
}
|
regsvr32.exe | HKCR
{
StarBurnX.Tracks.12 = s 'Tracks Class'
{
CLSID = s '{AE860CE7-C15E-4B9C-BA5B-2EB38369E4AF}'
}
StarBurnX.Tracks = s 'Tracks Class'
{
CLSID = s '{AE860CE7-C15E-4B9C-BA5B-2EB38369E4AF}'
CurVer = s 'StarBurnX.Tracks.12'
}
NoRemove CLSID
{
ForceRemove {AE860CE7-C15E-4B9C-BA5B-2EB38369E4AF} = s 'Tracks Class'
{
ProgID = s 'StarBurnX.Tracks.12'
VersionIndependentProgID = s 'StarBurnX.Tracks'
ForceRemove 'Programmable'
InprocServer32 = s 'C:\Program Files\DsNET Corp\aTube Catcher 2.0\StarBurnX12.dll'
{
val ThreadingModel = s 'Free'
}
'TypeLib' = s '{93CBA48A-1C58-4648-B22D-8F3588CB8D95}'
'Version' = s '12.0'
}
}
}
|
regsvr32.exe | HKCR
{
StarBurnX.Session.12 = s 'Session Class'
{
CLSID = s '{80E026F0-CE90-4F15-986A-45317268AB5A}'
}
StarBurnX.Session = s 'Session Class'
{
CLSID = s '{80E026F0-CE90-4F15-986A-45317268AB5A}'
CurVer = s 'StarBurnX.Session.12'
}
NoRemove CLSID
{
ForceRemove {80E026F0-CE90-4F15-986A-45317268AB5A} = s 'Session Class'
{
ProgID = s 'StarBurnX.Session.12'
VersionIndependentProgID = s 'StarBurnX.Session'
ForceRemove 'Programmable'
InprocServer32 = s 'C:\Program Files\DsNET Corp\aTube Catcher 2.0\StarBurnX12.dll'
{
val ThreadingModel = s 'Free'
}
'TypeLib' = s '{93CBA48A-1C58-4648-B22D-8F3588CB8D95}'
'Version' = s '12.0'
}
}
}
|
regsvr32.exe | HKCR
{
StarBurnX.Sessions.12 = s 'Sessions Class'
{
CLSID = s '{4EE12AA6-A781-490F-96DA-783969C58A1A}'
}
StarBurnX.Sessions = s 'Sessions Class'
{
CLSID = s '{4EE12AA6-A781-490F-96DA-783969C58A1A}'
CurVer = s 'StarBurnX.Sessions.12'
}
NoRemove CLSID
{
ForceRemove {4EE12AA6-A781-490F-96DA-783969C58A1A} = s 'Sessions Class'
{
ProgID = s 'StarBurnX.Sessions.12'
VersionIndependentProgID = s 'StarBurnX.Sessions'
ForceRemove 'Programmable'
InprocServer32 = s 'C:\Program Files\DsNET Corp\aTube Catcher 2.0\StarBurnX12.dll'
{
val ThreadingModel = s 'Free'
}
'TypeLib' = s '{93CBA48A-1C58-4648-B22D-8F3588CB8D95}'
'Version' = s '12.0'
}
}
}
|
regsvr32.exe | HKCR
{
StarBurnX.DiscInfo.12 = s 'DiscInfo Class'
{
CLSID = s '{DE9B465F-0405-41B9-8C20-B6F0CACCC713}'
}
StarBurnX.DiscInfo = s 'DiscInfo Class'
{
CLSID = s '{DE9B465F-0405-41B9-8C20-B6F0CACCC713}'
CurVer = s 'StarBurnX.DiscInfo.12'
}
NoRemove CLSID
{
ForceRemove {DE9B465F-0405-41B9-8C20-B6F0CACCC713} = s 'DiscInfo Class'
{
ProgID = s 'StarBurnX.DiscInfo.12'
VersionIndependentProgID = s 'StarBurnX.DiscInfo'
ForceRemove 'Programmable'
InprocServer32 = s 'C:\Program Files\DsNET Corp\aTube Catcher 2.0\StarBurnX12.dll'
{
val ThreadingModel = s 'Free'
}
'TypeLib' = s '{93CBA48A-1C58-4648-B22D-8F3588CB8D95}'
'Version' = s '12.0'
}
}
}
|