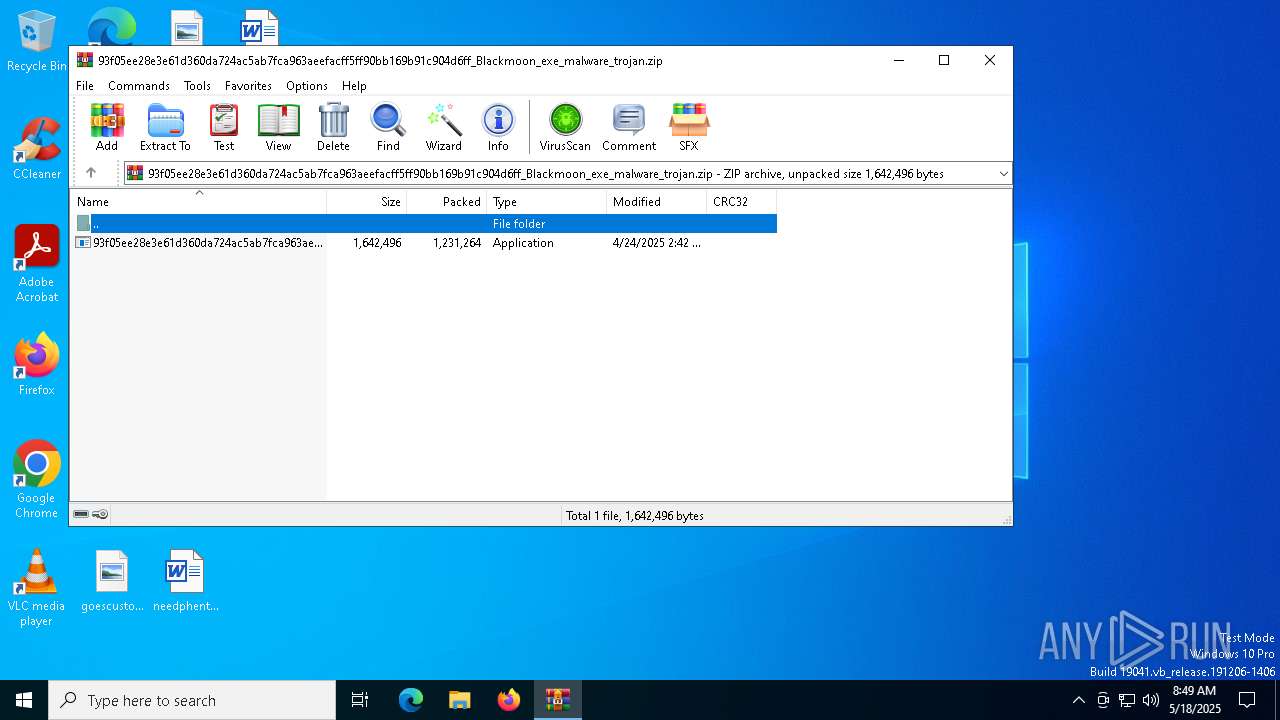
| File name: | 93f05ee28e3e61d360da724ac5ab7fca963aeefacff5ff90bb169b91c904d6ff_Blackmoon_exe_malware_trojan.zip |
| Full analysis: | https://app.any.run/tasks/709f68be-da1c-4852-9307-3ee6b95d117e |
| Verdict: | Malicious activity |
| Threats: | BlackMoon also known as KrBanker is a trojan aimed at stealing payment credentials. It specializes in man-in-the-browser (MitB) attacks, web injection, and credential theft to compromise users' online banking accounts. It was first noticed in early 2014 attacking banks in South Korea and has impressively evolved since by adding a number of new infiltration techniques and information stealing methods. |
| Analysis date: | May 18, 2025, 08:49:45 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
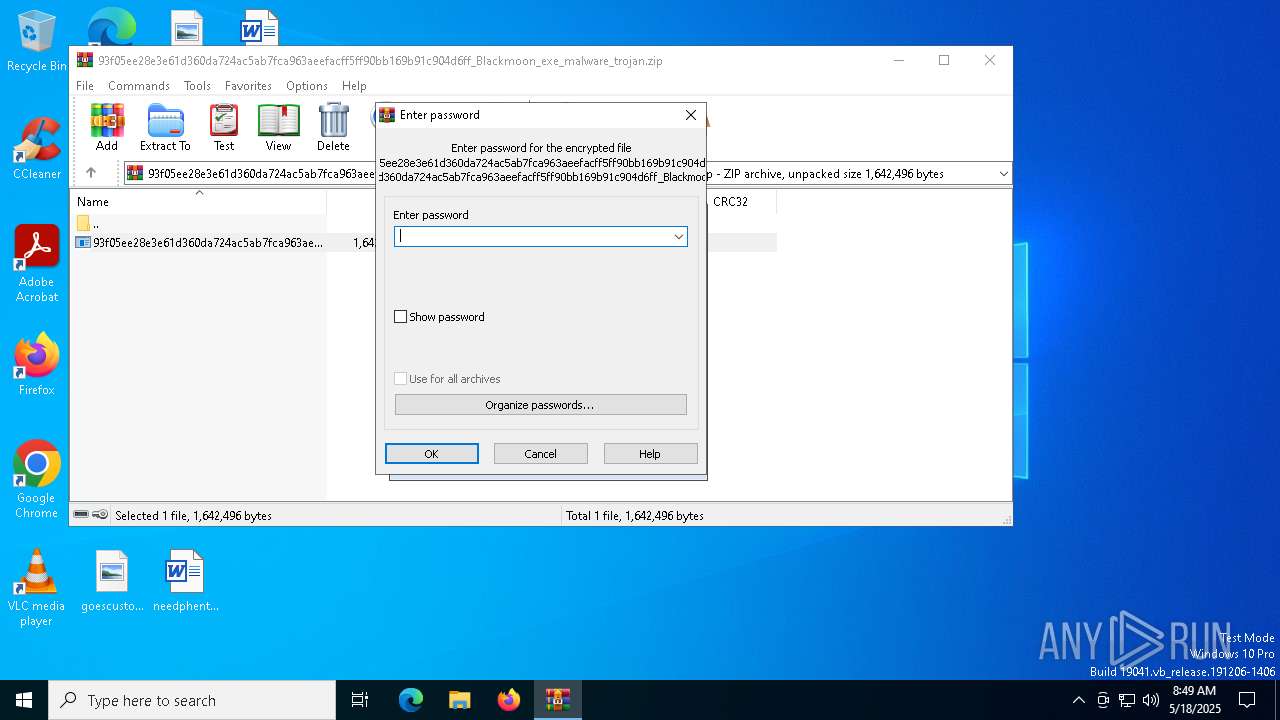
| File info: | Zip archive data, at least v5.1 to extract, compression method=AES Encrypted |
| MD5: | A96642E4FF1BD47476920CDE326199D5 |
| SHA1: | 05F960BACA305A301B710146B803E4089FA04BE0 |
| SHA256: | 1A80348EBE05A63B7EFBDDDFA779C9444EE473AC504636D0646ADAF5FC9A7531 |
| SSDEEP: | 49152:AKK3NpkQ6ljbE2BA5DRfhbUubNDGLYYdjRhFwwmy5e7jblB/pFwn1fVepkBB+KSt:Q3yljbnA5VnbNgVIwal/F61fQkBBWqi7 |
MALICIOUS
BLACKMOON has been found (auto)
- WinRAR.exe (PID: 4696)
- 93f05ee28e3e61d360da724ac5ab7fca963aeefacff5ff90bb169b91c904d6ff.exe (PID: 7644)
Generic archive extractor
- WinRAR.exe (PID: 4696)
BLACKMOON has been detected (YARA)
- 93f05ee28e3e61d360da724ac5ab7fca963aeefacff5ff90bb169b91c904d6ff.exe (PID: 7644)
SUSPICIOUS
Executable content was dropped or overwritten
- 93f05ee28e3e61d360da724ac5ab7fca963aeefacff5ff90bb169b91c904d6ff.exe (PID: 7644)
Reads security settings of Internet Explorer
- 93f05ee28e3e61d360da724ac5ab7fca963aeefacff5ff90bb169b91c904d6ff.exe (PID: 7644)
- 93f05ee28e3e61d360da724ac5ab7fca963aeefacff5ff90bb169b91c904d6ff.exe (PID: 7696)
There is functionality for taking screenshot (YARA)
- 93f05ee28e3e61d360da724ac5ab7fca963aeefacff5ff90bb169b91c904d6ff.exe (PID: 7644)
- 93f05ee28e3e61d360da724ac5ab7fca963aeefacff5ff90bb169b91c904d6ff.exe (PID: 7696)
Application launched itself
- 93f05ee28e3e61d360da724ac5ab7fca963aeefacff5ff90bb169b91c904d6ff.exe (PID: 7644)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4696)
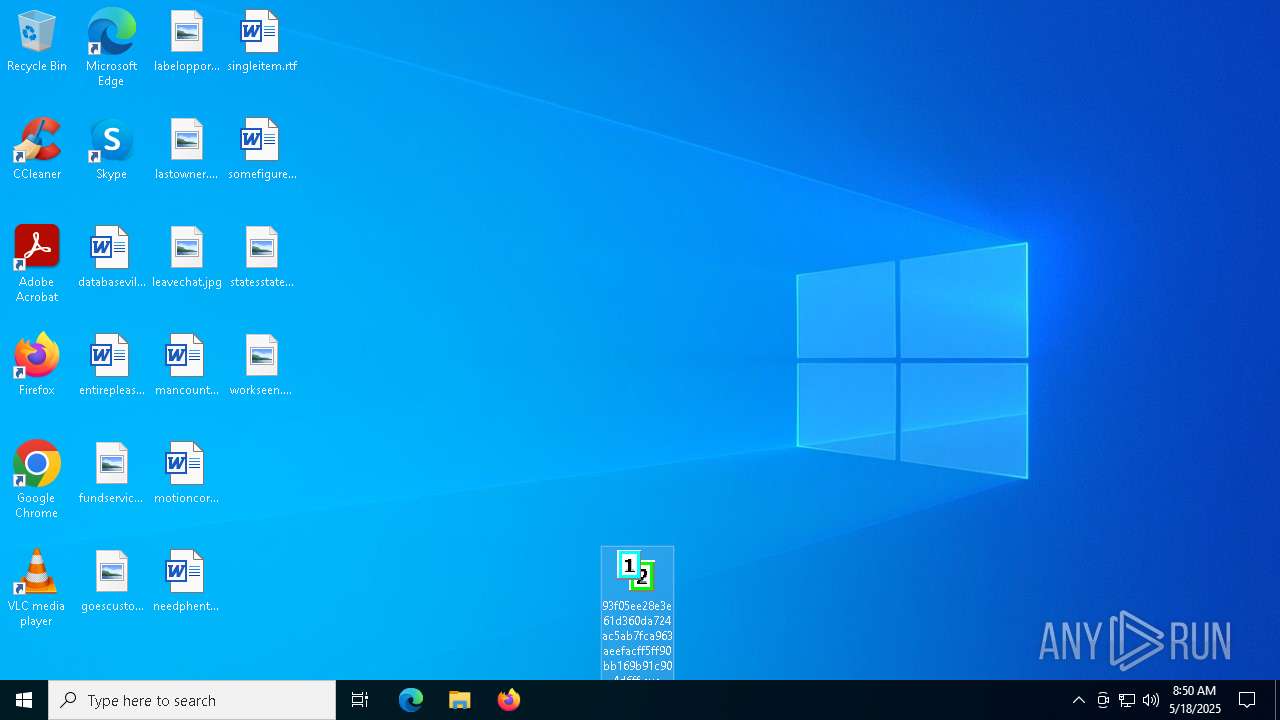
Manual execution by a user
- 93f05ee28e3e61d360da724ac5ab7fca963aeefacff5ff90bb169b91c904d6ff.exe (PID: 7644)
Create files in a temporary directory
- 93f05ee28e3e61d360da724ac5ab7fca963aeefacff5ff90bb169b91c904d6ff.exe (PID: 7644)
The sample compiled with chinese language support
- WinRAR.exe (PID: 4696)
- 93f05ee28e3e61d360da724ac5ab7fca963aeefacff5ff90bb169b91c904d6ff.exe (PID: 7644)
Checks supported languages
- 93f05ee28e3e61d360da724ac5ab7fca963aeefacff5ff90bb169b91c904d6ff.exe (PID: 7644)
- 93f05ee28e3e61d360da724ac5ab7fca963aeefacff5ff90bb169b91c904d6ff.exe (PID: 7696)
Process checks computer location settings
- 93f05ee28e3e61d360da724ac5ab7fca963aeefacff5ff90bb169b91c904d6ff.exe (PID: 7644)
Reads the computer name
- 93f05ee28e3e61d360da724ac5ab7fca963aeefacff5ff90bb169b91c904d6ff.exe (PID: 7644)
- 93f05ee28e3e61d360da724ac5ab7fca963aeefacff5ff90bb169b91c904d6ff.exe (PID: 7696)
Compiled with Borland Delphi (YARA)
- 93f05ee28e3e61d360da724ac5ab7fca963aeefacff5ff90bb169b91c904d6ff.exe (PID: 7644)
- 93f05ee28e3e61d360da724ac5ab7fca963aeefacff5ff90bb169b91c904d6ff.exe (PID: 7696)
UPX packer has been detected
- 93f05ee28e3e61d360da724ac5ab7fca963aeefacff5ff90bb169b91c904d6ff.exe (PID: 7644)
Reads the software policy settings
- slui.exe (PID: 7212)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0003 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2025:04:24 02:42:58 |
| ZipCRC: | 0xb2e5c0ee |
| ZipCompressedSize: | 1231264 |
| ZipUncompressedSize: | 1642496 |
| ZipFileName: | 93f05ee28e3e61d360da724ac5ab7fca963aeefacff5ff90bb169b91c904d6ff.exe |
Total processes
133
Monitored processes
6
Malicious processes
2
Suspicious processes
0
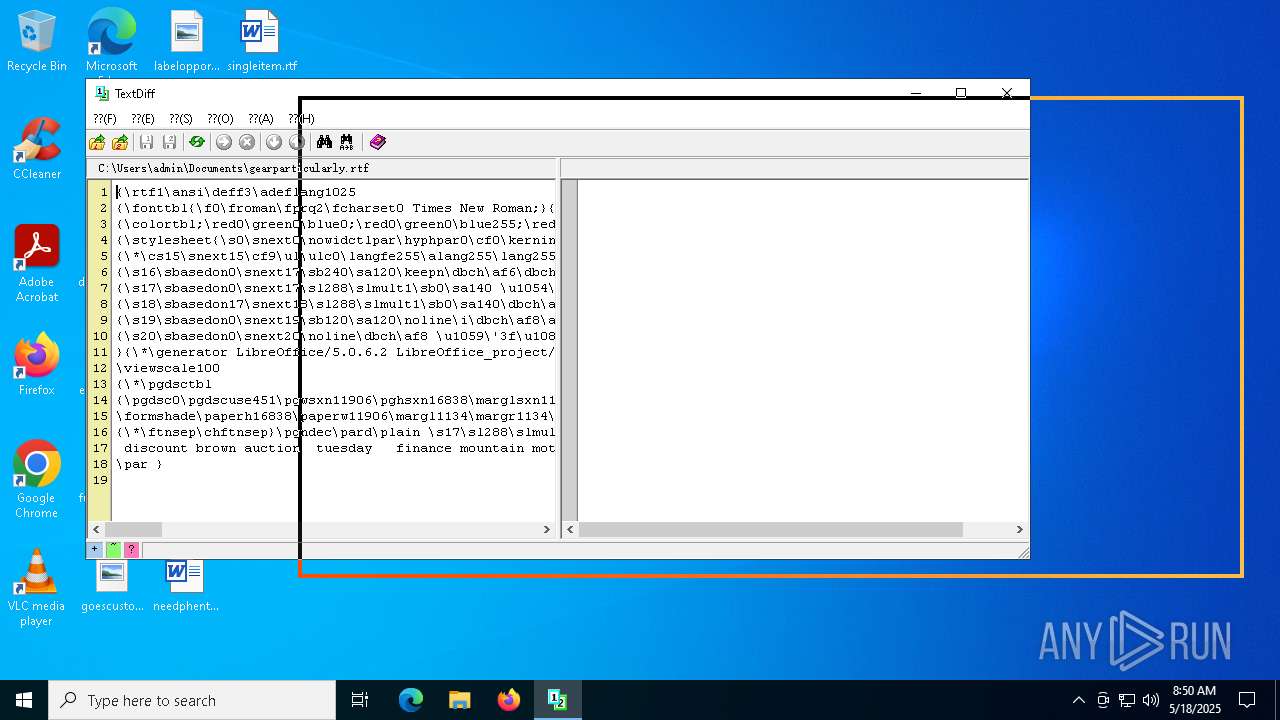
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
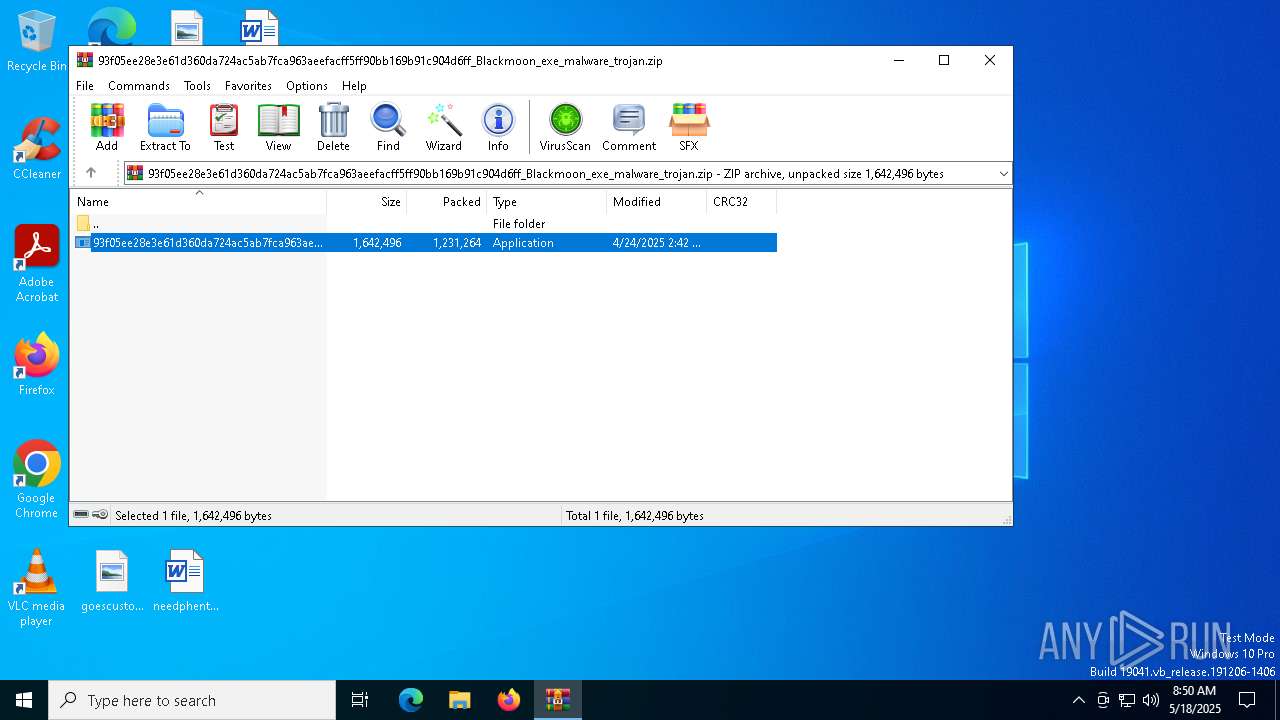
| 4696 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\93f05ee28e3e61d360da724ac5ab7fca963aeefacff5ff90bb169b91c904d6ff_Blackmoon_exe_malware_trojan.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 7180 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7212 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7644 | "C:\Users\admin\Desktop\93f05ee28e3e61d360da724ac5ab7fca963aeefacff5ff90bb169b91c904d6ff.exe" | C:\Users\admin\Desktop\93f05ee28e3e61d360da724ac5ab7fca963aeefacff5ff90bb169b91c904d6ff.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Version: 1.0.0.0 Modules
| |||||||||||||||
| 7696 | "C:\Users\admin\Desktop\93f05ee28e3e61d360da724ac5ab7fca963aeefacff5ff90bb169b91c904d6ff.exe" | C:\Users\admin\Desktop\93f05ee28e3e61d360da724ac5ab7fca963aeefacff5ff90bb169b91c904d6ff.exe | — | 93f05ee28e3e61d360da724ac5ab7fca963aeefacff5ff90bb169b91c904d6ff.exe | |||||||||||
User: admin Integrity Level: MEDIUM Version: 1.0.0.0 Modules
| |||||||||||||||
| 8004 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
4 132
Read events
4 072
Write events
58
Delete events
2
Modification events
| (PID) Process: | (4696) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (4696) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (4696) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (4696) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\93f05ee28e3e61d360da724ac5ab7fca963aeefacff5ff90bb169b91c904d6ff_Blackmoon_exe_malware_trojan.zip | |||
| (PID) Process: | (4696) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4696) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4696) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4696) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4696) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (4696) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
Executable files
4
Suspicious files
0
Text files
4
Unknown types
0
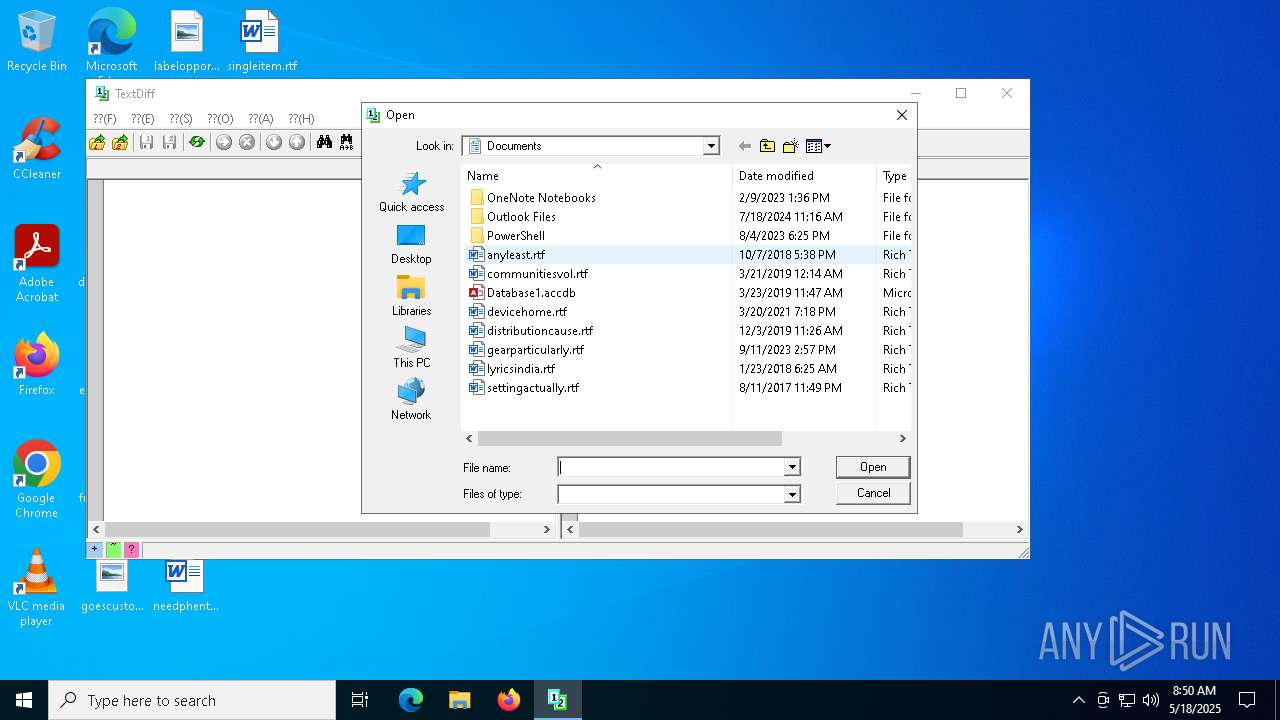
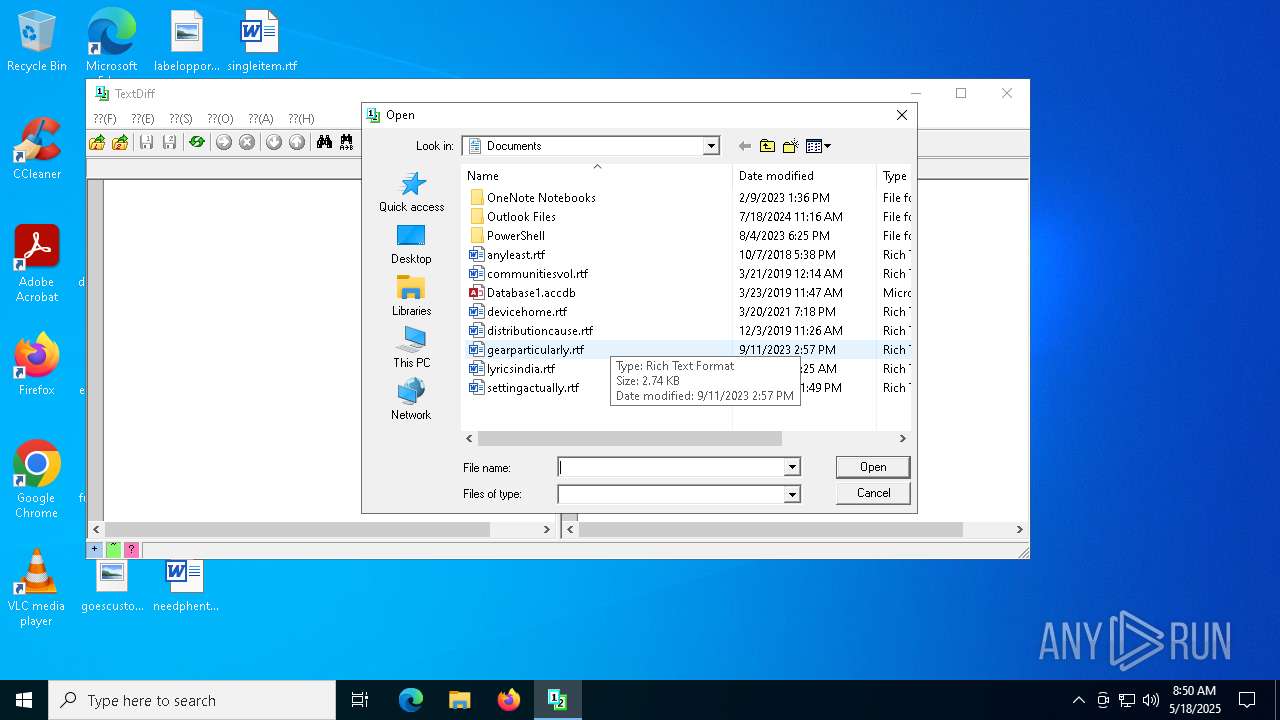
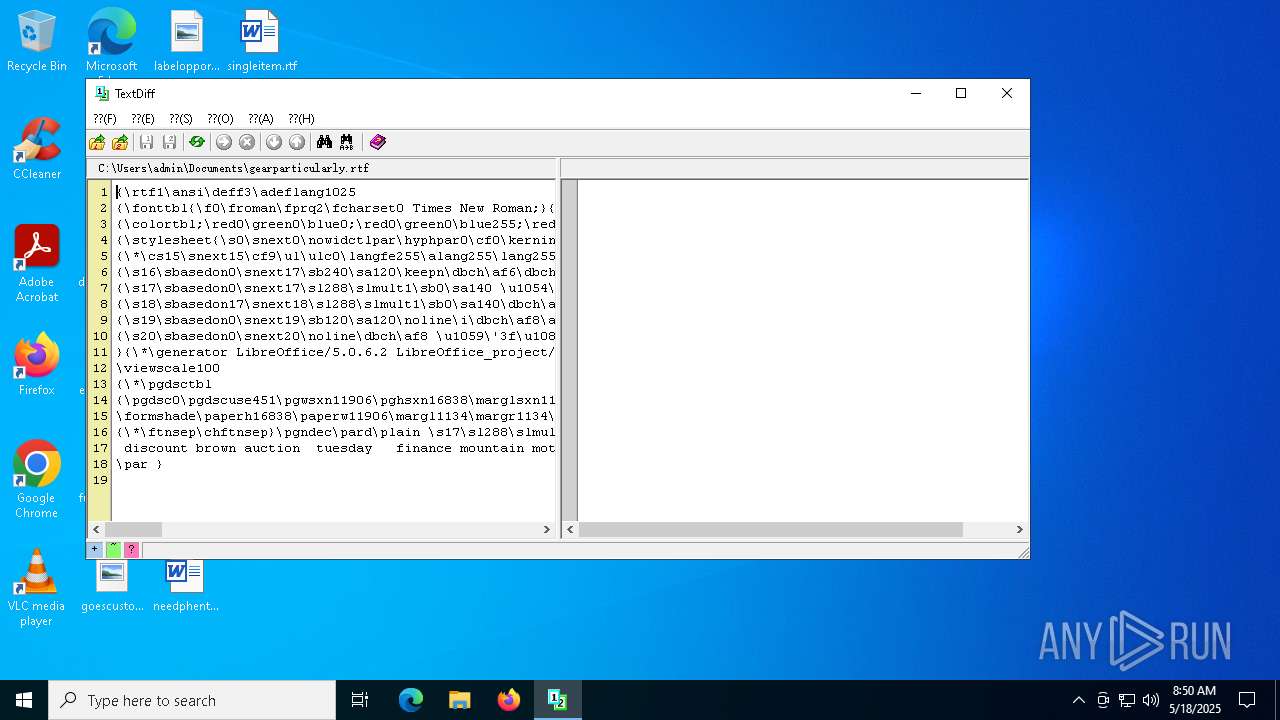
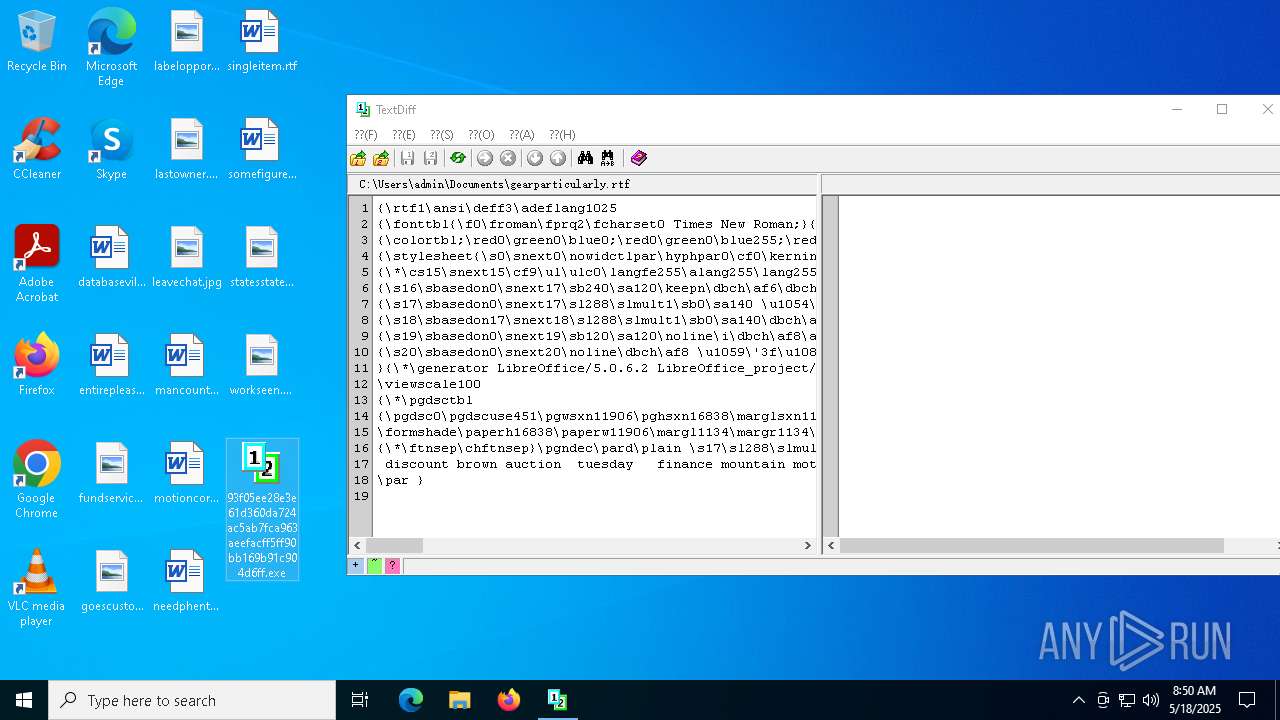
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4696 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb4696.792\93f05ee28e3e61d360da724ac5ab7fca963aeefacff5ff90bb169b91c904d6ff.exe | executable | |
MD5:4CE94DA16ED39AA167FEF5EF3D81DD80 | SHA256:93F05EE28E3E61D360DA724AC5AB7FCA963AEEFACFF5FF90BB169B91C904D6FF | |||
| 7644 | 93f05ee28e3e61d360da724ac5ab7fca963aeefacff5ff90bb169b91c904d6ff.exe | C:\Users\admin\AppData\Local\Temp\sczss.log | text | |
MD5:E13ED68574E9A1900C2A7C758B93A648 | SHA256:844EC5874ADD510CD261FBE9484D78B04D627C3BD93FB9C6CD3B47428D217CE9 | |||
| 7644 | 93f05ee28e3e61d360da724ac5ab7fca963aeefacff5ff90bb169b91c904d6ff.exe | C:\Users\admin\AppData\Local\Temp\NewFile.tmp | executable | |
MD5:E76C0C6D030D0A8967F58DEC9AA70A85 | SHA256:E2FC2D91F49AA0C78A0EFC5D5E810B09E437349EF029C976A6F1590F50DB7392 | |||
| 7644 | 93f05ee28e3e61d360da724ac5ab7fca963aeefacff5ff90bb169b91c904d6ff.exe | C:\Users\admin\AppData\Local\Temp\sczs.log | text | |
MD5:B6F42F37ED0E0272F7E288DBF5DC48A6 | SHA256:4043E4D891B44988902C70DDD597EA403CE4134BBABDD9D0548583DC36E463AB | |||
| 7644 | 93f05ee28e3e61d360da724ac5ab7fca963aeefacff5ff90bb169b91c904d6ff.exe | C:\Users\admin\AppData\Local\Temp\zbys.tmp | text | |
MD5:6EE43FDE01180169355C545C33FBF421 | SHA256:70FE6DBA5D744501D61B4F93615CEF8C567BB7612AFC904CF3BD02286F84A8AA | |||
| 7644 | 93f05ee28e3e61d360da724ac5ab7fca963aeefacff5ff90bb169b91c904d6ff.exe | C:\Users\admin\AppData\Local\Temp\03889359\ilicvzvl.tmp | executable | |
MD5:4CE94DA16ED39AA167FEF5EF3D81DD80 | SHA256:93F05EE28E3E61D360DA724AC5AB7FCA963AEEFACFF5FF90BB169B91C904D6FF | |||
| 7644 | 93f05ee28e3e61d360da724ac5ab7fca963aeefacff5ff90bb169b91c904d6ff.exe | C:\Users\admin\AppData\Local\Temp\sjwjm.tmp | text | |
MD5:764E59756DC17BBC1A4EB305128934DF | SHA256:F4272D1170471A4C3EEEB6C65E6E34BB5BFED887BFDA6004AB627E9EDFA3ADAC | |||
| 7644 | 93f05ee28e3e61d360da724ac5ab7fca963aeefacff5ff90bb169b91c904d6ff.exe | C:\Users\admin\Desktop\93f05ee28e3e61d360da724ac5ab7fca963aeefacff5ff90bb169b91c904d6ff.exe | executable | |
MD5:79B8440148C745CD6588FCE092E23464 | SHA256:1A4EF39C722115F7FB99EE68ADDDF67990A15AF08EA840E2E9950D3CCF1F3838 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
20
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.216.77.37:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7784 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7784 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 23.216.77.37:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
6544 | svchost.exe | 40.126.31.1:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |