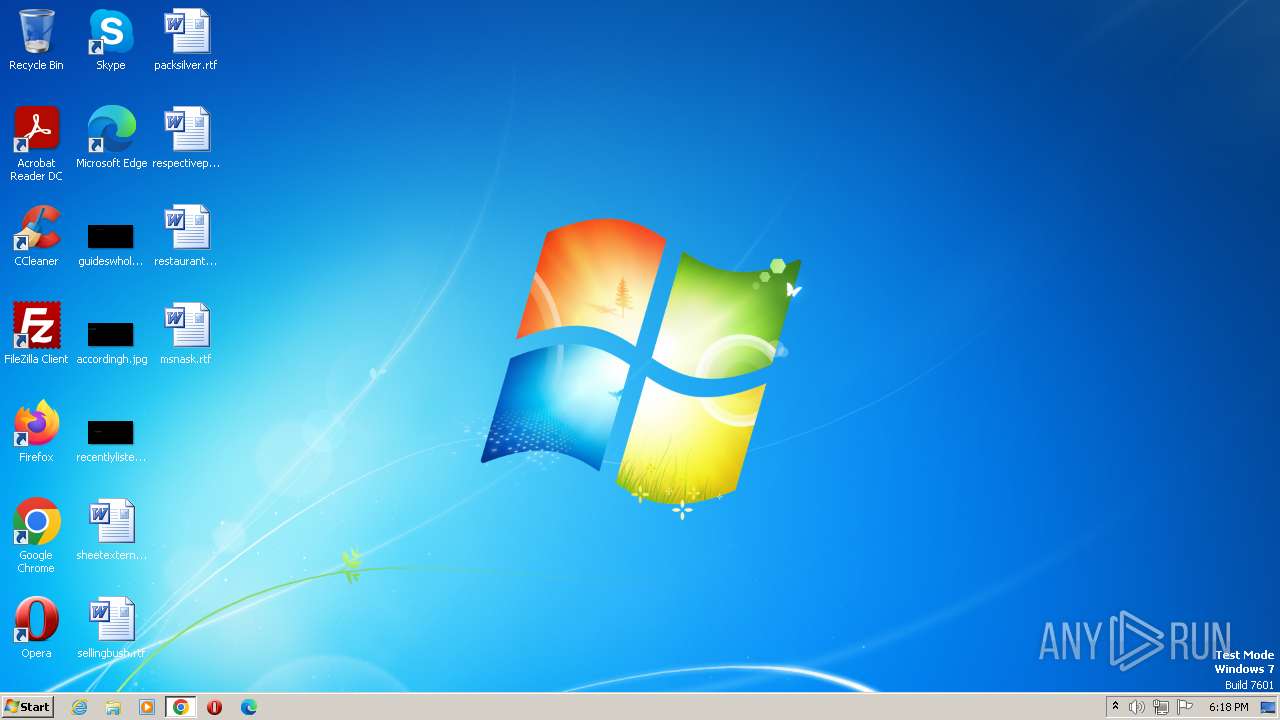
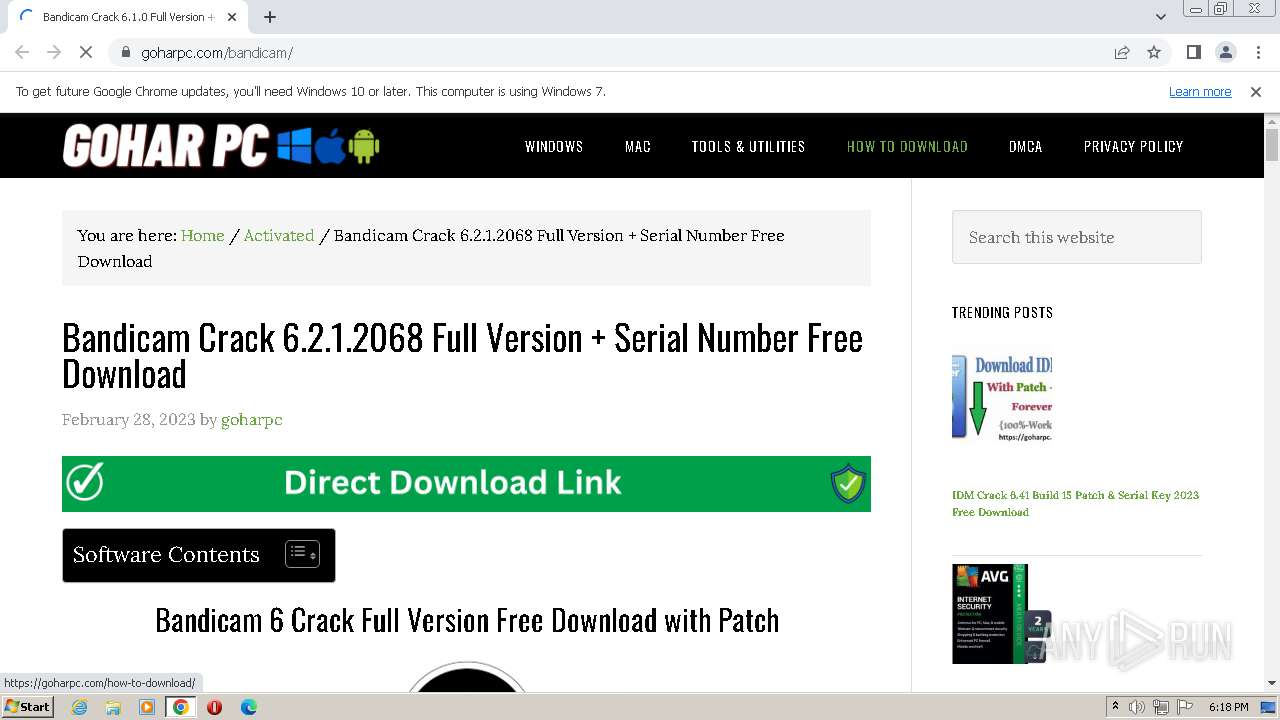
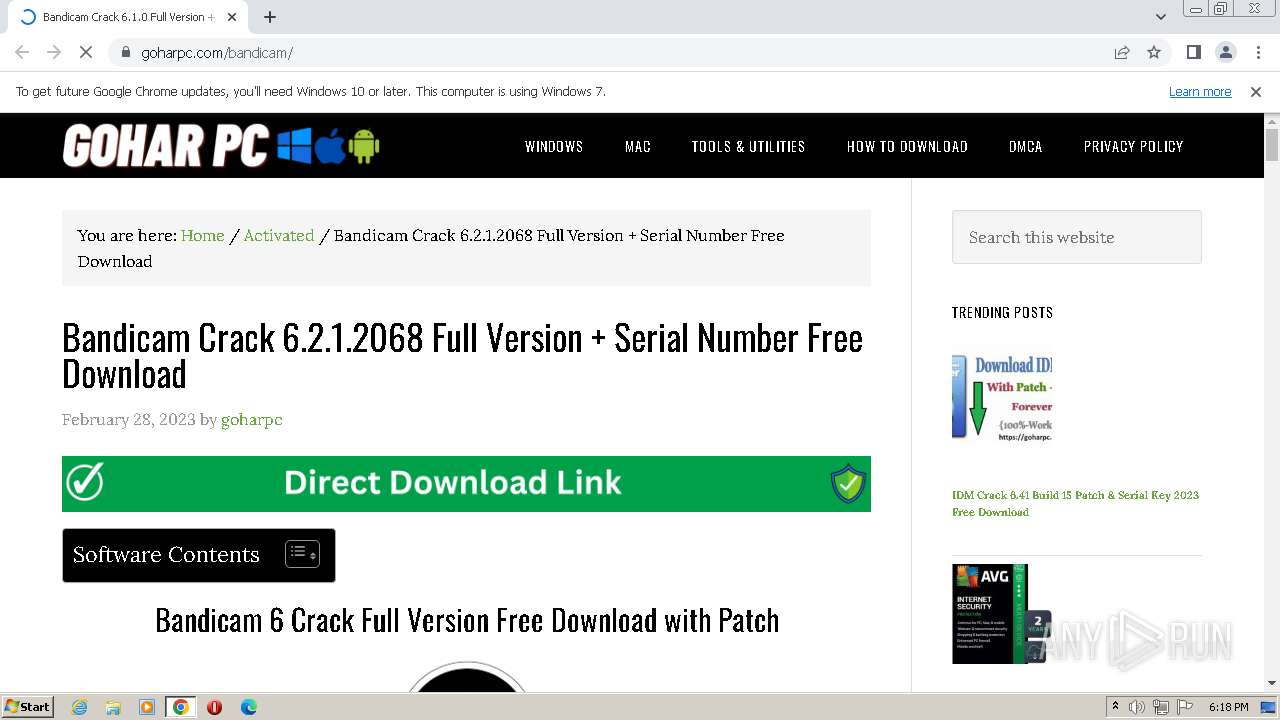
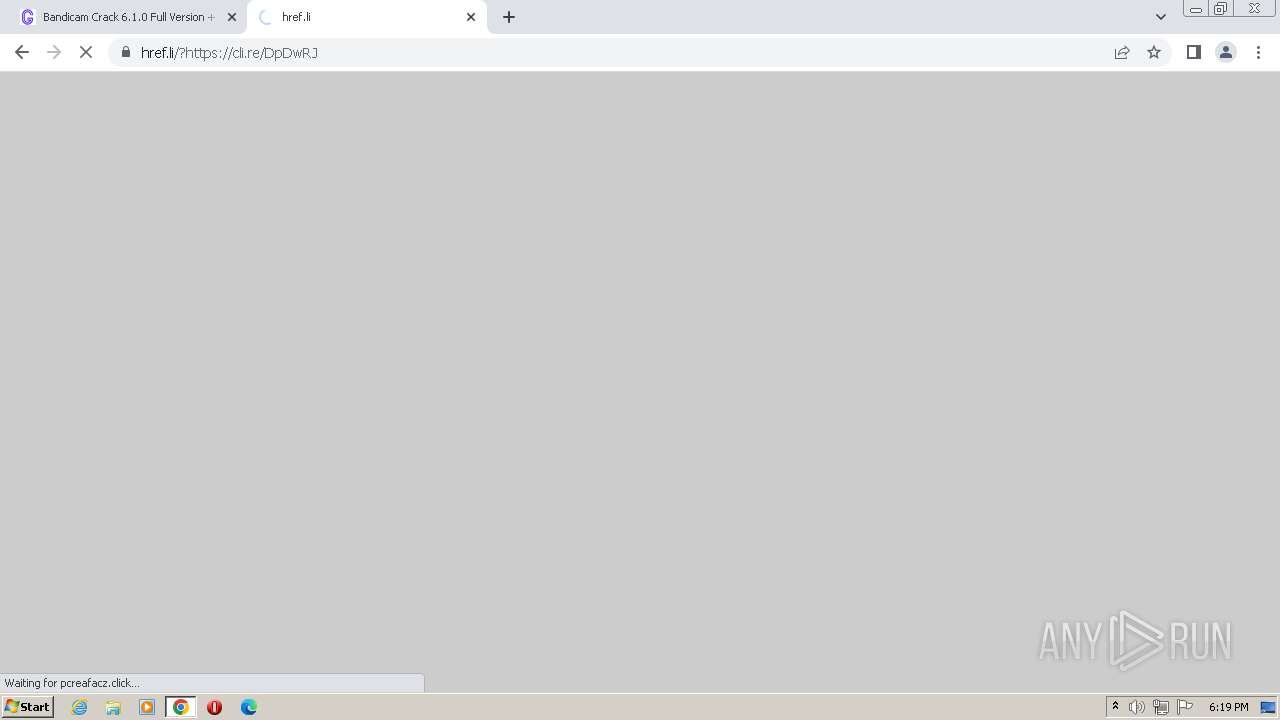
| URL: | https://goharpc.com/bandicam/ |
| Full analysis: | https://app.any.run/tasks/20f4969c-37e2-4626-891a-d535f9a32ad2 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | August 10, 2023, 17:17:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 9458406BD727572AB0919B1148CC5055 |
| SHA1: | 45118BD256B22EC88155968D2586BDE8F8C3E109 |
| SHA256: | 1A350D856E80C6F0297B0C2552F5CF208E14B24D0383F42CF12BD254C33CF1D3 |
| SSDEEP: | 3:N8rAGL4Bk3:2EGL4Bk3 |
MALICIOUS
LUMMA detected by memory dumps
- jsc.exe (PID: 1572)
Application was dropped or rewritten from another process
- Setup.exe (PID: 2028)
LUMMA was detected
- jsc.exe (PID: 1572)
Actions looks like stealing of personal data
- jsc.exe (PID: 1572)
SUSPICIOUS
Reads the Internet Settings
- jsc.exe (PID: 1572)
Reads browser cookies
- jsc.exe (PID: 1572)
INFO
Application launched itself
- chrome.exe (PID: 3488)
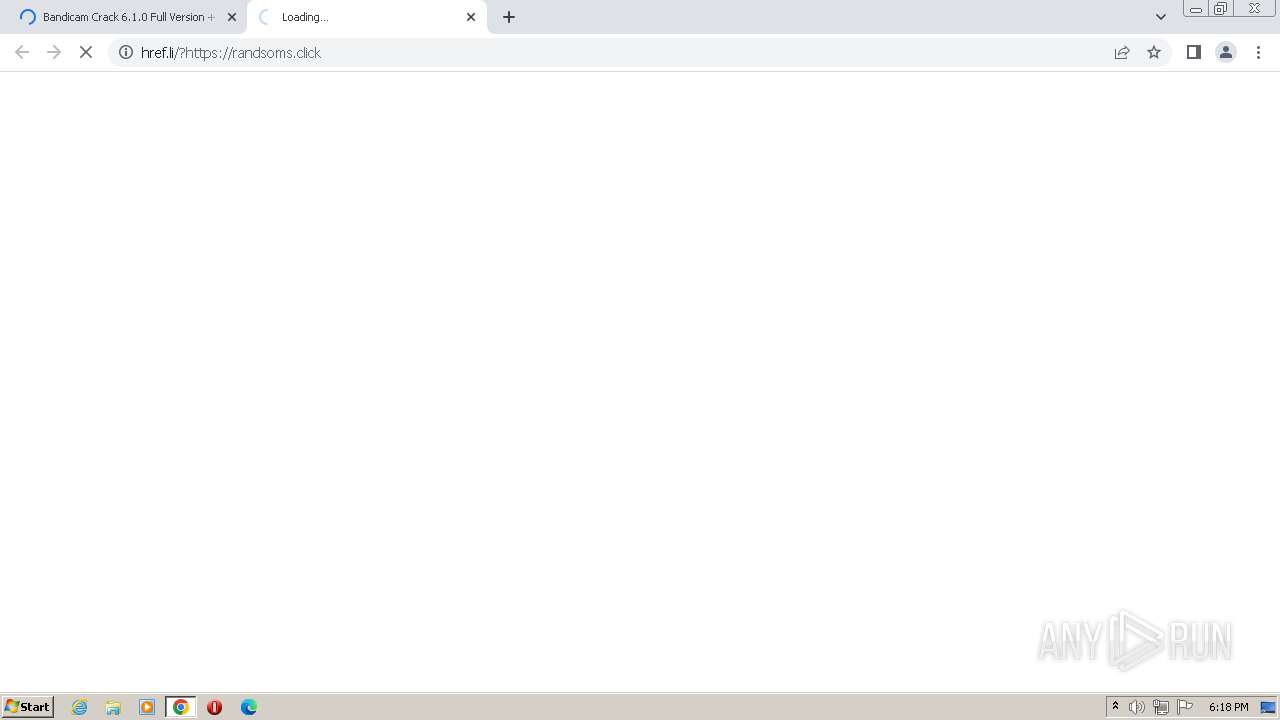
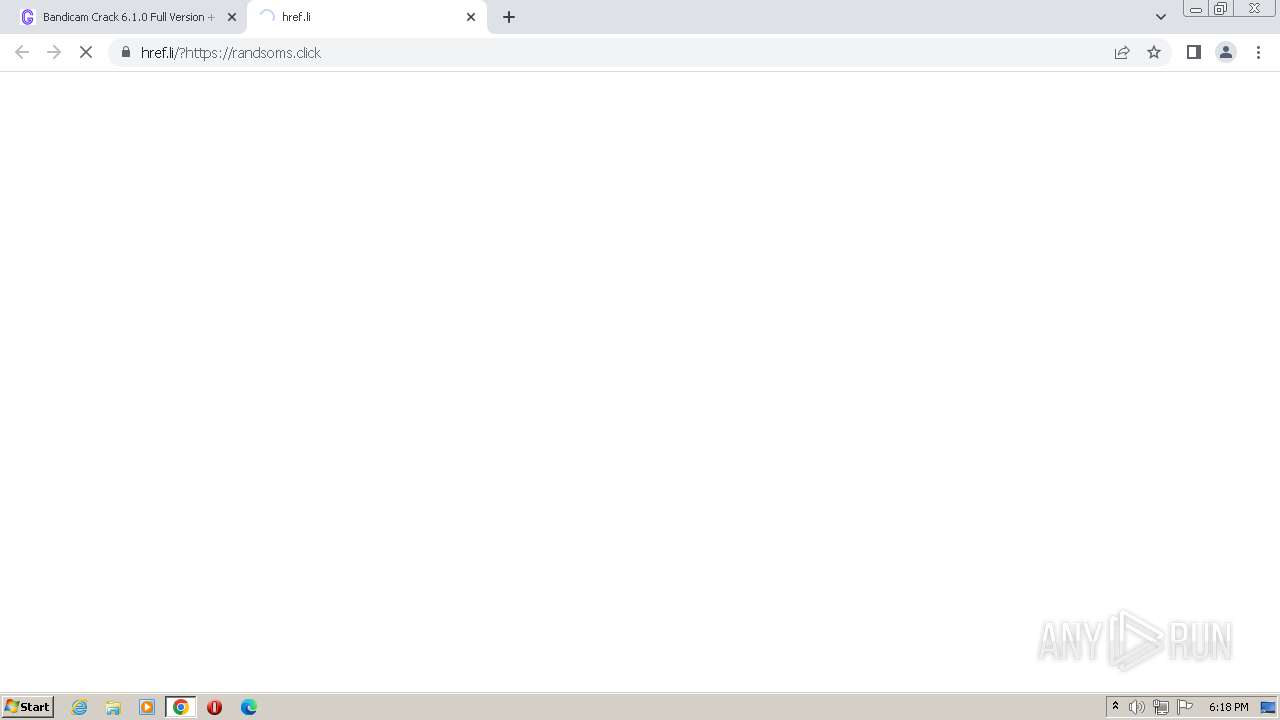
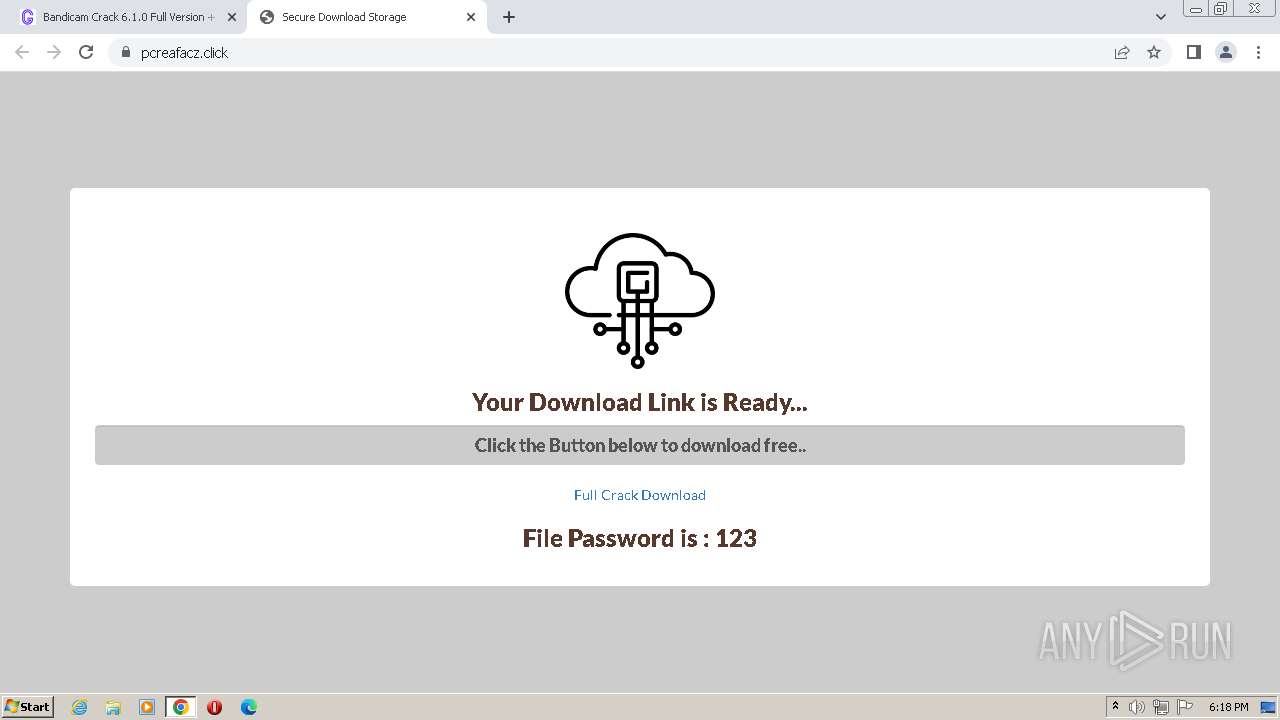
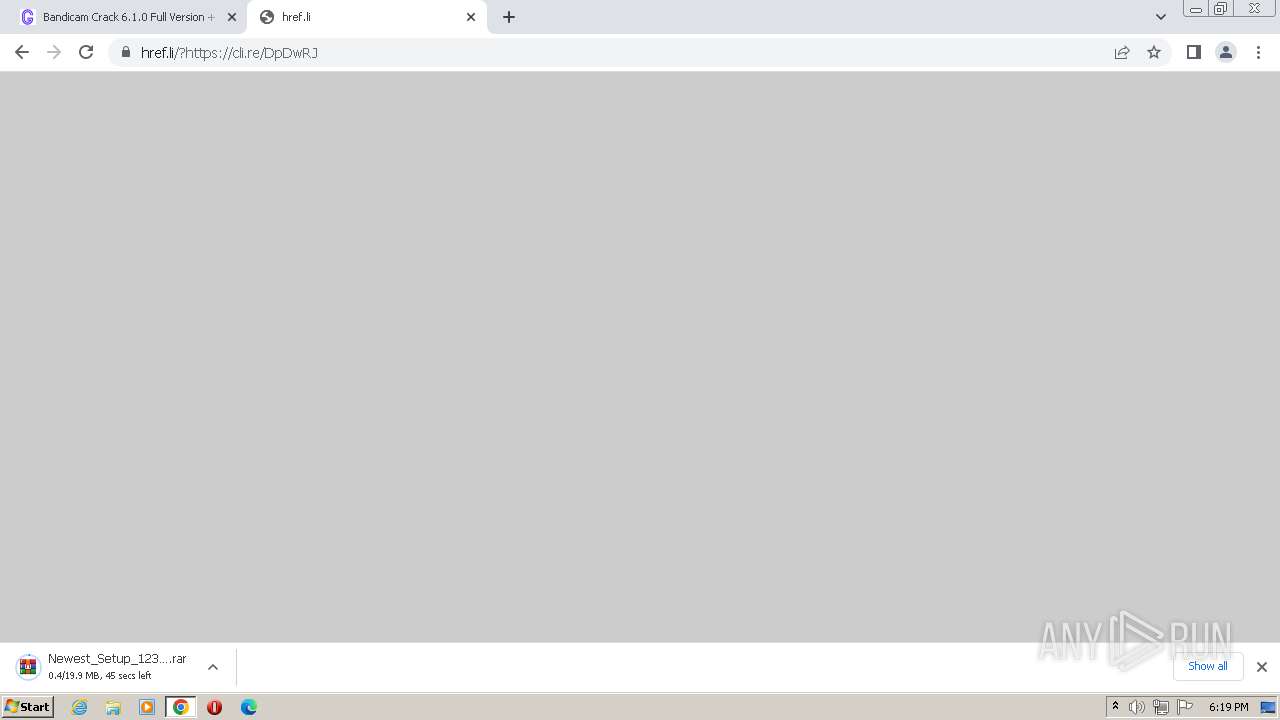
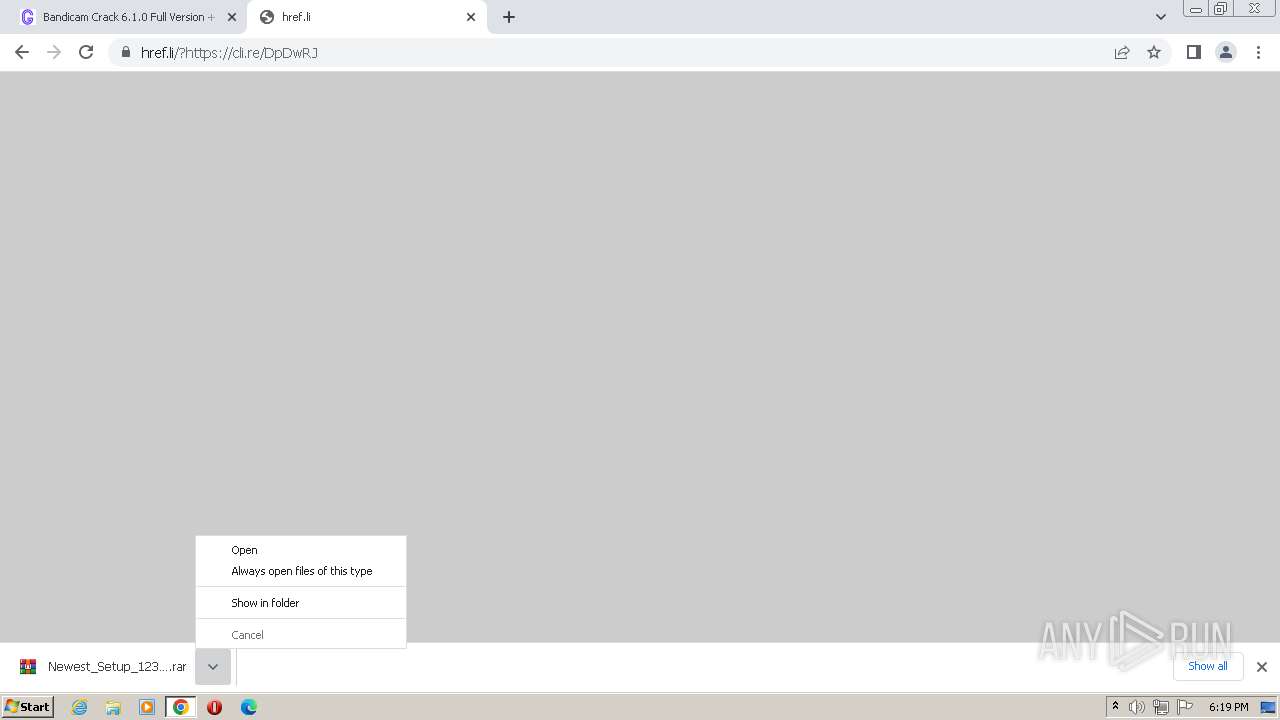
The process uses the downloaded file
- chrome.exe (PID: 596)
- chrome.exe (PID: 528)
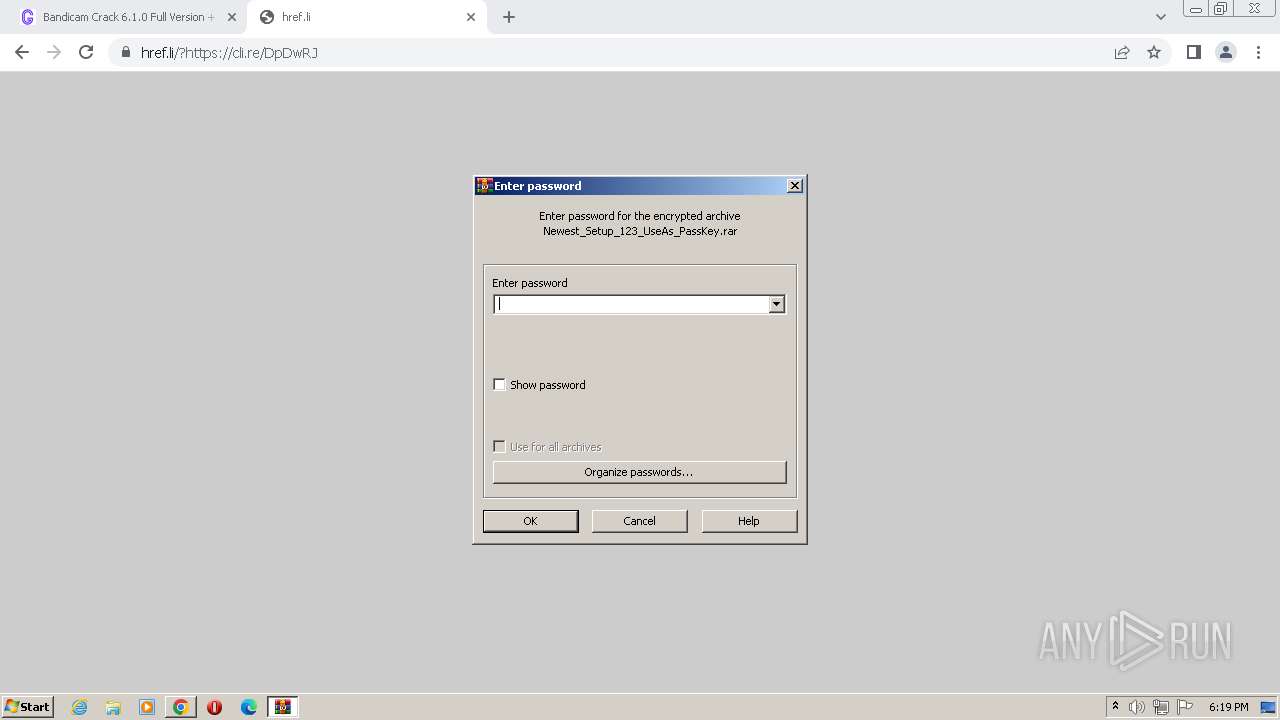
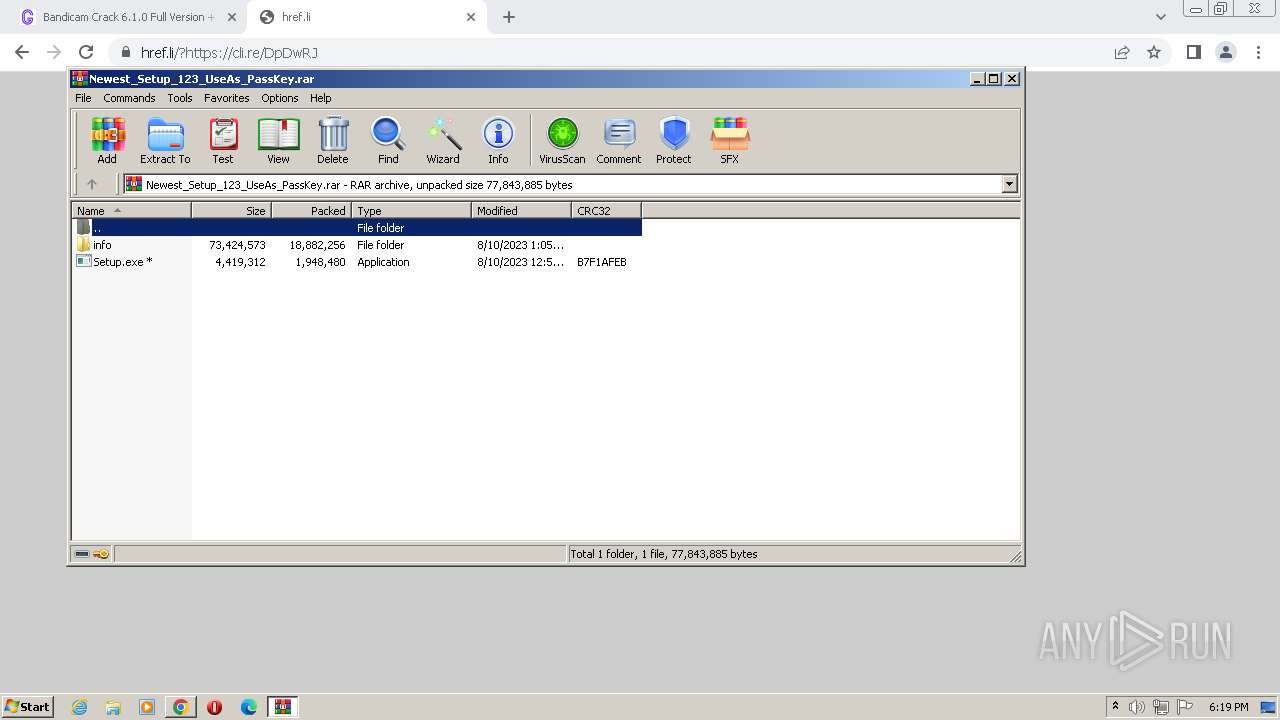
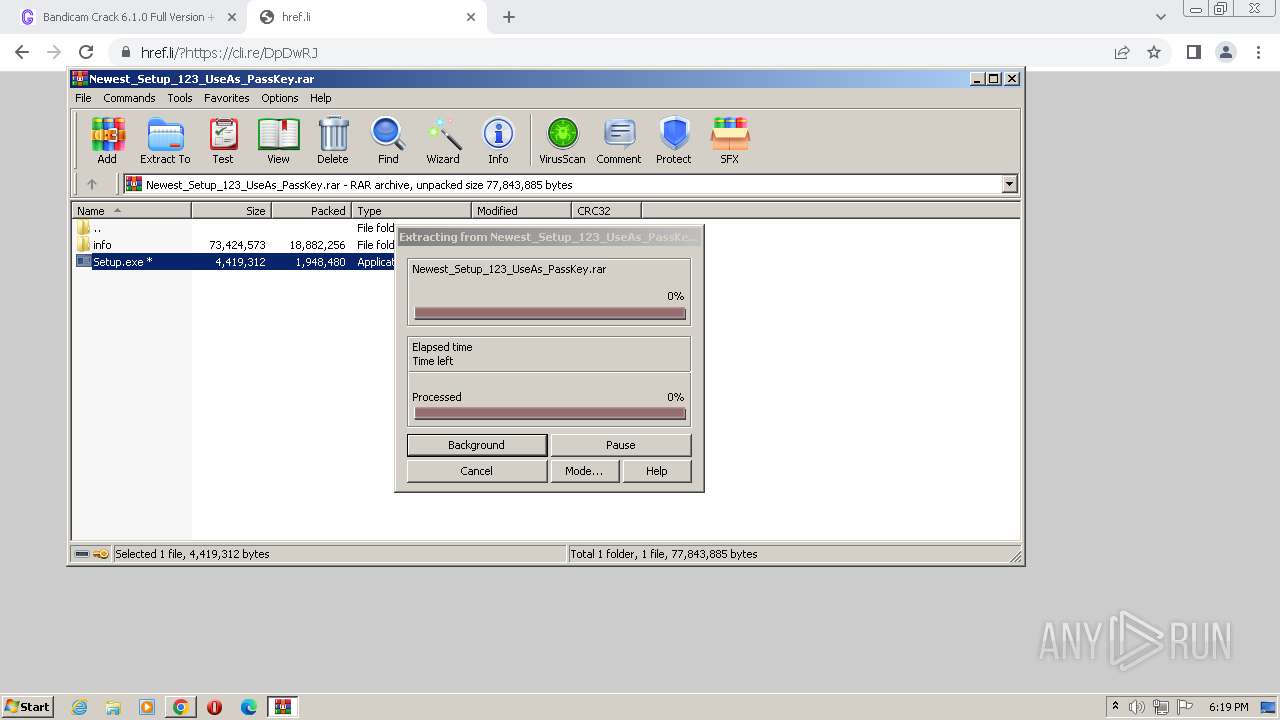
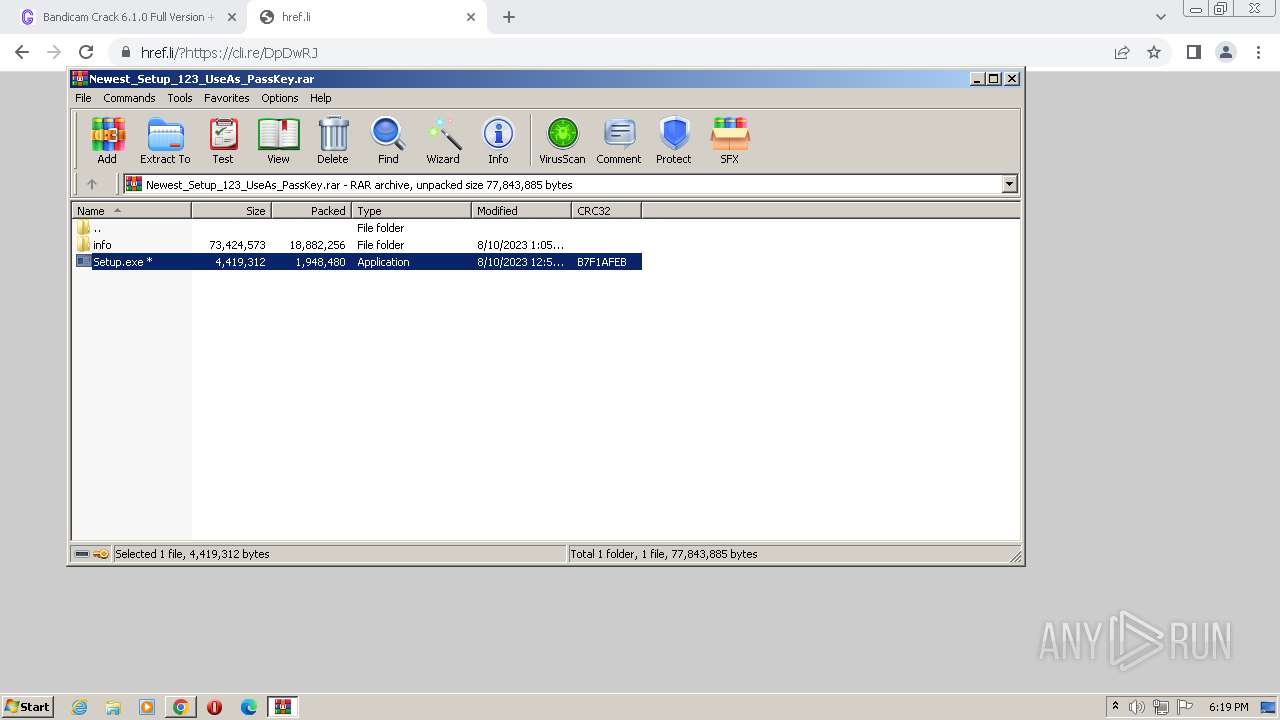
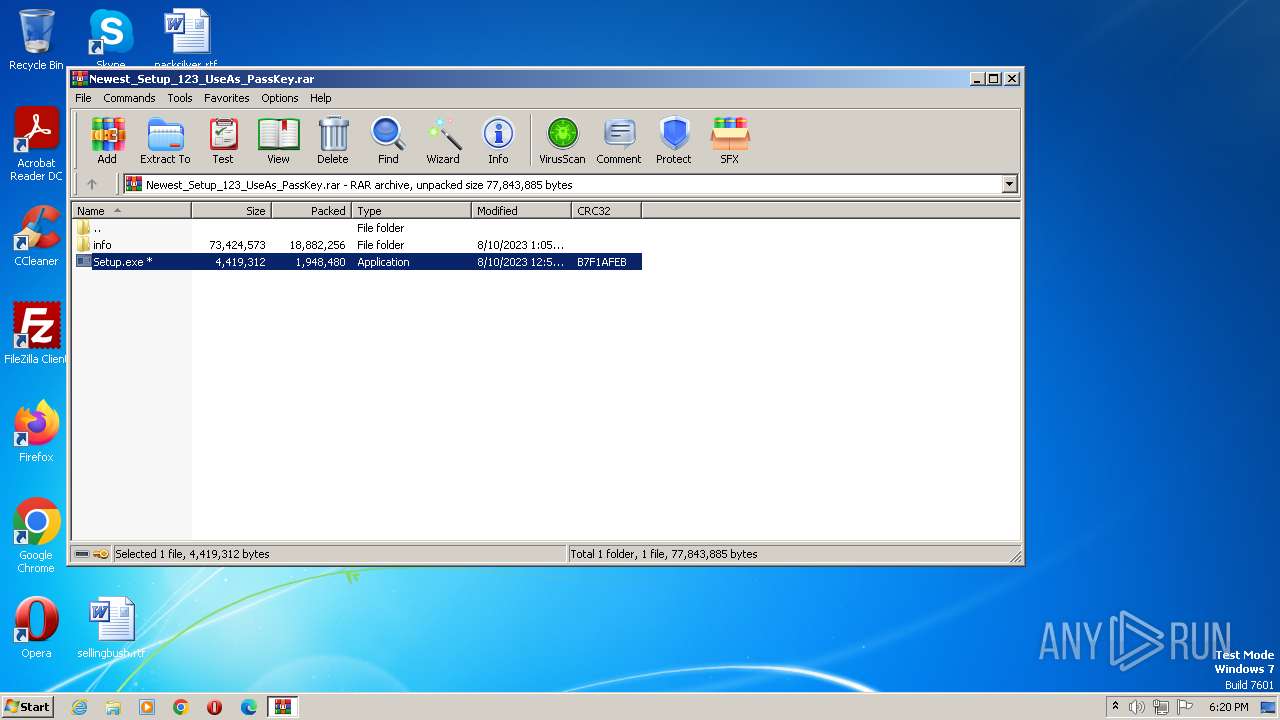
- WinRAR.exe (PID: 3784)
- chrome.exe (PID: 2120)
- chrome.exe (PID: 788)
Checks supported languages
- Setup.exe (PID: 2028)
- jsc.exe (PID: 1572)
Reads the computer name
- Setup.exe (PID: 2028)
- jsc.exe (PID: 1572)
The process checks LSA protection
- Setup.exe (PID: 2028)
- jsc.exe (PID: 1572)
Reads the machine GUID from the registry
- Setup.exe (PID: 2028)
- jsc.exe (PID: 1572)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3784)
Creates files or folders in the user directory
- jsc.exe (PID: 1572)
Checks proxy server information
- jsc.exe (PID: 1572)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Lumma
(PID) Process(1572) jsc.exe
C2winhttp.dll/c2sock
Options
LummaIDKjGtqi--PPI
Total processes
66
Monitored processes
30
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 528 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=4224 --field-trial-handle=1120,i,271646416771058667,7612744705895945399,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 572 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --mojo-platform-channel-handle=1420 --field-trial-handle=1120,i,271646416771058667,7612744705895945399,131072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 596 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3956 --field-trial-handle=1120,i,271646416771058667,7612744705895945399,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 788 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=4336 --field-trial-handle=1120,i,271646416771058667,7612744705895945399,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 860 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=12 --mojo-platform-channel-handle=3992 --field-trial-handle=1120,i,271646416771058667,7612744705895945399,131072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1032 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=14 --mojo-platform-channel-handle=3832 --field-trial-handle=1120,i,271646416771058667,7612744705895945399,131072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1496 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=11 --mojo-platform-channel-handle=1400 --field-trial-handle=1120,i,271646416771058667,7612744705895945399,131072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1572 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\jsc.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\jsc.exe | Setup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: jsc.exe Exit code: 0 Version: 12.0.51209.34209 built by: FX452RTMGDR Modules
Lumma(PID) Process(1572) jsc.exe C2winhttp.dll/c2sock Options LummaIDKjGtqi--PPI | |||||||||||||||
| 1600 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=1476 --field-trial-handle=1120,i,271646416771058667,7612744705895945399,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2024 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --mojo-platform-channel-handle=3692 --field-trial-handle=1120,i,271646416771058667,7612744705895945399,131072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
6 235
Read events
6 106
Write events
129
Delete events
0
Modification events
| (PID) Process: | (3488) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3488) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3488) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3488) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3488) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3488) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (3488) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3488) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3488) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (3488) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
Executable files
125
Suspicious files
77
Text files
85
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3488 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RFf990a.TMP | — | |
MD5:— | SHA256:— | |||
| 3488 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3488 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RFf9a43.TMP | text | |
MD5:561161B0FF5BCA89BF47F8AC972A7499 | SHA256:ECCA5CCFA0BEED7581B39FCE03D0FD3B694DF0F92BFFF780F702118AD51FC17D | |||
| 3488 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFf990a.TMP | text | |
MD5:D5C9ECBD2DCA29D89266782824D7AF99 | SHA256:D22D1243ACC064A30823180D0E583C853E9395367C78C2AD9DE59A463904F702 | |||
| 3488 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:29B82603A20A26A3F99DB34525AF7448 | SHA256:9601A054A9C6AA6A65CEFAA229046476C1A089989FA6441DAD71D39F6794B980 | |||
| 3488 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old~RFf9b4c.TMP | text | |
MD5:7C1C23F006788D107F8A01B852CC6701 | SHA256:9FA4E627077EDCBEC8AAA1ED2DD5538E630790893F88F02F1E9CC863E6A27848 | |||
| 3488 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RFfa03e.TMP | — | |
MD5:— | SHA256:— | |||
| 3488 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3488 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFf992a.TMP | text | |
MD5:CDCC923CEC2CD9228330551E6946A9C2 | SHA256:592F4750166BE662AA88728F9969537163FEC5C3E95E81537C8C6917F8D0929E | |||
| 3488 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
78
DNS requests
71
Threats
29
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1572 | jsc.exe | POST | — | 104.21.32.18:80 | http://scoollovers.xyz/c2sock | US | — | — | malicious |
1572 | jsc.exe | POST | — | 104.21.32.18:80 | http://scoollovers.xyz/c2sock | US | — | — | malicious |
868 | svchost.exe | HEAD | — | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/llpgpkajxaiz2l2qpnpif2ag3i_405/lmelglejhemejginpboagddgdfbepgmp_405_all_ZZ_kvlkmoepxco6zj7cec2ig44nh4.crx3 | US | — | — | whitelisted |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/llpgpkajxaiz2l2qpnpif2ag3i_405/lmelglejhemejginpboagddgdfbepgmp_405_all_ZZ_kvlkmoepxco6zj7cec2ig44nh4.crx3 | US | binary | 5.32 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2728 | chrome.exe | 172.217.16.205:443 | accounts.google.com | GOOGLE | US | whitelisted |
2728 | chrome.exe | 142.250.184.200:443 | www.googletagmanager.com | — | — | suspicious |
2728 | chrome.exe | 216.239.32.178:443 | www.google-analytics.com | — | — | suspicious |
3488 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2728 | chrome.exe | 188.114.97.3:443 | goharpc.com | CLOUDFLARENET | NL | malicious |
2728 | chrome.exe | 172.217.18.4:443 | www.google.com | GOOGLE | US | whitelisted |
2728 | chrome.exe | 142.250.186.35:443 | fonts.gstatic.com | GOOGLE | US | whitelisted |
2728 | chrome.exe | 172.217.23.106:443 | content-autofill.googleapis.com | GOOGLE | US | whitelisted |
2728 | chrome.exe | 192.0.76.3:443 | stats.wp.com | AUTOMATTIC | US | suspicious |
2728 | chrome.exe | 142.250.186.110:443 | www.youtube.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
goharpc.com |
| malicious |
fonts.gstatic.com |
| whitelisted |
stats.wp.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
www.youtube.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
pixel.wp.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
region1.google-analytics.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2728 | chrome.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
2728 | chrome.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
1572 | jsc.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
1572 | jsc.exe | Malware Command and Control Activity Detected | ET MALWARE [ANY.RUN] Win32/Lumma Stealer Configuration Request Attempt |
1572 | jsc.exe | Malware Command and Control Activity Detected | STEALER [ANY.RUN] Win32/Lumma Stealer Configuration Request Attempt |
1572 | jsc.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
1572 | jsc.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
1572 | jsc.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
1572 | jsc.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
1572 | jsc.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |