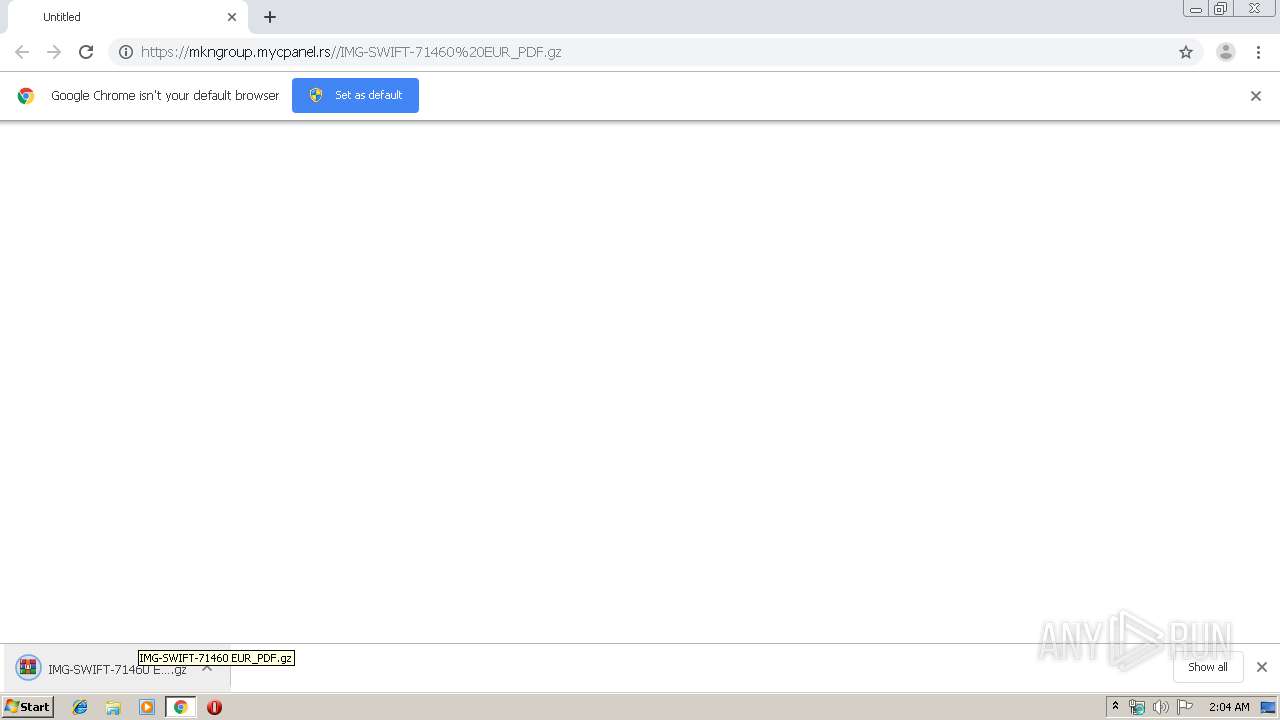
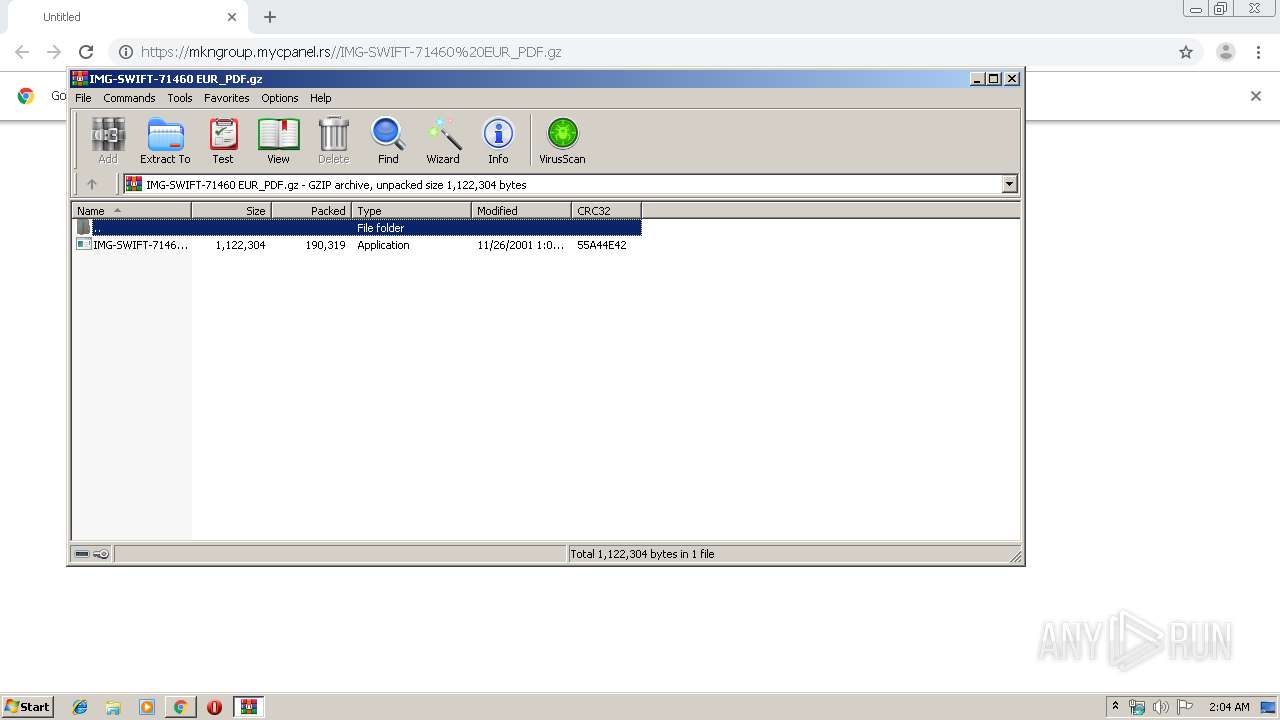
| URL: | https://mkngroup.mycpanel.rs//IMG-SWIFT-71460%20EUR_PDF.gz |
| Full analysis: | https://app.any.run/tasks/ecb398fd-6b9f-461f-98d3-4eb06b8e7c4d |
| Verdict: | Malicious activity |
| Threats: | LokiBot was developed in 2015 to steal information from a variety of applications. Despite the age, this malware is still rather popular among cybercriminals. |
| Analysis date: | August 26, 2019, 01:04:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | A367F51A6A5998C7E7A087D7B903CFB7 |
| SHA1: | BA883DAE8ADC294B5854FD059923A8C362E296E0 |
| SHA256: | 19FB401C95EED4334C5AFCC1D9B88B639E8618C10372CE43E2BDECE97046EC34 |
| SSDEEP: | 3:N8VCaQVNH+XNPI2ysNMKV9ehM:2oxNeedM |
MALICIOUS
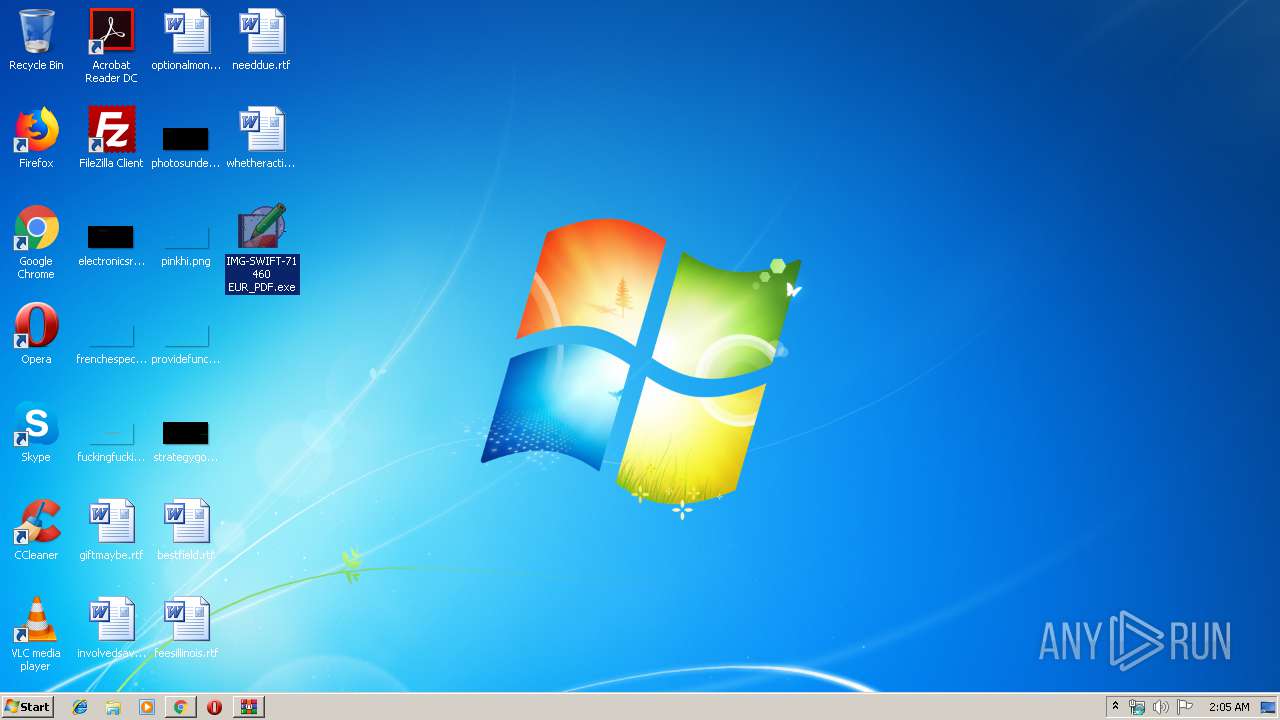
Application was dropped or rewritten from another process
- IMG-SWIFT-71460 EUR_PDF.exe (PID: 2792)
- IMG-SWIFT-71460 EUR_PDF.exe (PID: 3312)
Detected artifacts of LokiBot
- IMG-SWIFT-71460 EUR_PDF.exe (PID: 3312)
Connects to CnC server
- IMG-SWIFT-71460 EUR_PDF.exe (PID: 3312)
LOKIBOT was detected
- IMG-SWIFT-71460 EUR_PDF.exe (PID: 3312)
Actions looks like stealing of personal data
- IMG-SWIFT-71460 EUR_PDF.exe (PID: 3312)
SUSPICIOUS
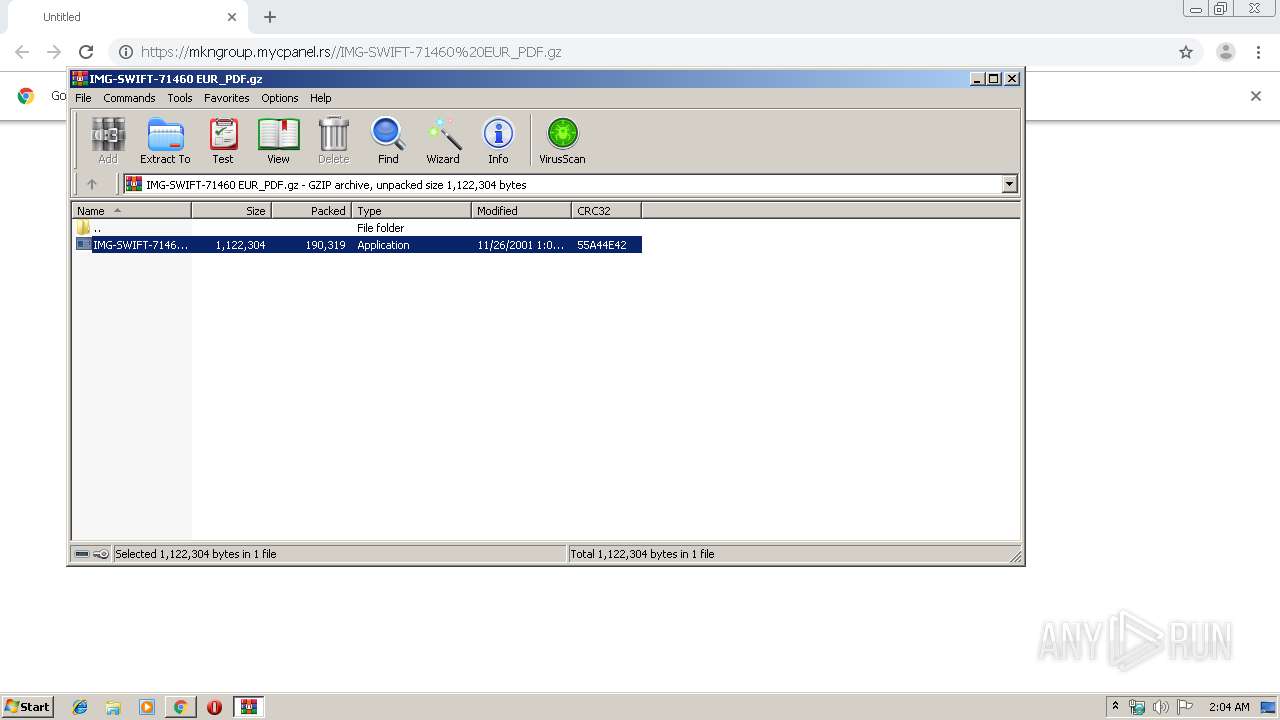
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2200)
- IMG-SWIFT-71460 EUR_PDF.exe (PID: 3312)
Application launched itself
- IMG-SWIFT-71460 EUR_PDF.exe (PID: 2792)
Loads DLL from Mozilla Firefox
- IMG-SWIFT-71460 EUR_PDF.exe (PID: 3312)
Creates files in the user directory
- IMG-SWIFT-71460 EUR_PDF.exe (PID: 3312)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3460)
INFO
Creates files in the user directory
- chrome.exe (PID: 3460)
Application launched itself
- chrome.exe (PID: 3460)
Reads Internet Cache Settings
- chrome.exe (PID: 3460)
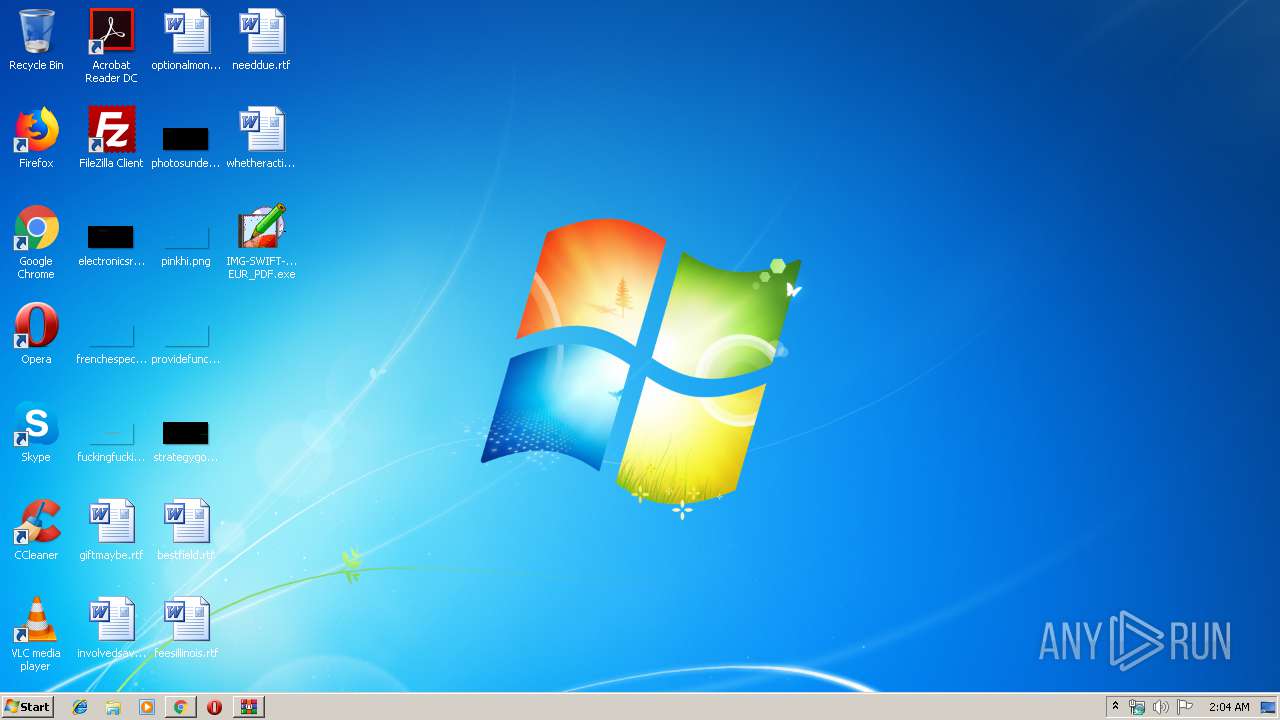
Manual execution by user
- IMG-SWIFT-71460 EUR_PDF.exe (PID: 2792)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
59
Monitored processes
24
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6fe6a9d0,0x6fe6a9e0,0x6fe6a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
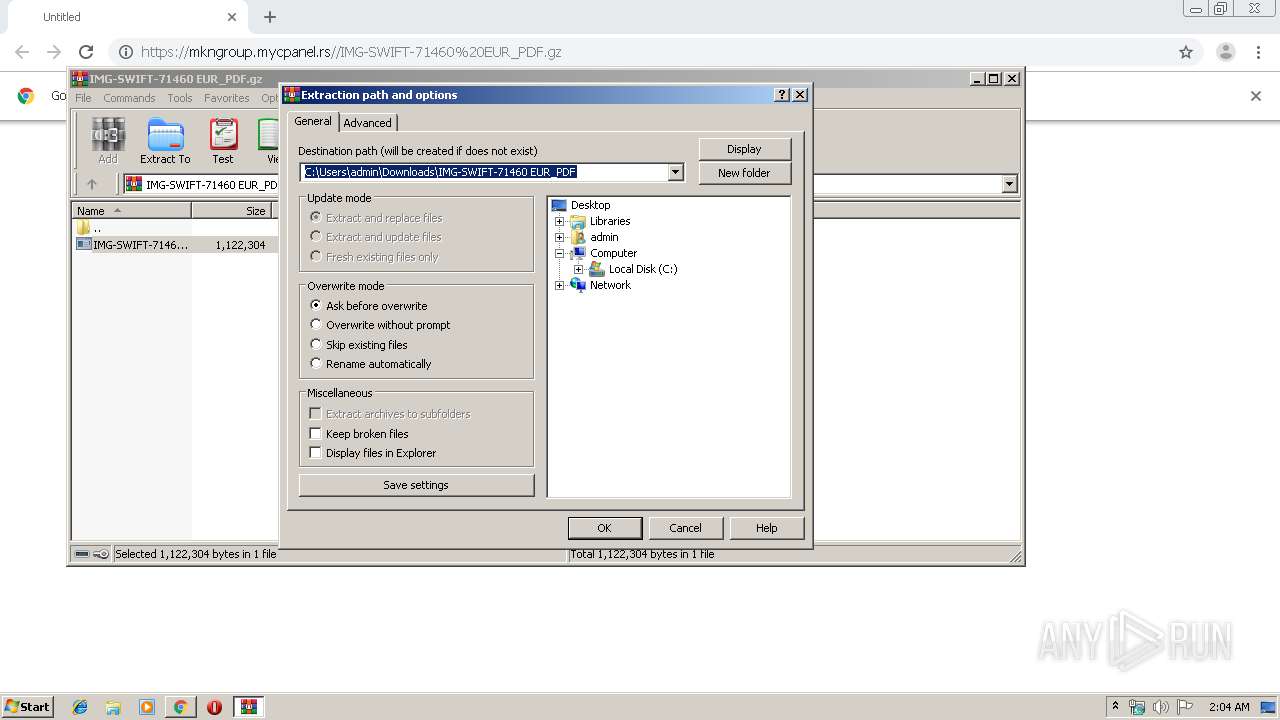
| 2200 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\IMG-SWIFT-71460 EUR_PDF.gz" | C:\Program Files\WinRAR\WinRAR.exe | chrome.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2288 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,13895931101989397078,12340450996666135279,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3145935457023058698 --mojo-platform-channel-handle=896 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2500 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,13895931101989397078,12340450996666135279,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6134173981864228135 --mojo-platform-channel-handle=3824 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2608 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1028,13895931101989397078,12340450996666135279,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=5990913680859380642 --mojo-platform-channel-handle=1036 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2776 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,13895931101989397078,12340450996666135279,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15187661669440926640 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2196 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2792 | "C:\Users\admin\Desktop\IMG-SWIFT-71460 EUR_PDF.exe" | C:\Users\admin\Desktop\IMG-SWIFT-71460 EUR_PDF.exe | — | explorer.exe | |||||||||||
User: admin Company: CassiopeazodiacoCrambly Integrity Level: MEDIUM Exit code: 0 Version: 1.01.0009 Modules
| |||||||||||||||
| 2872 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,13895931101989397078,12340450996666135279,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13584834651241764890 --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3964 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2880 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,13895931101989397078,12340450996666135279,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=1784443606060418859 --mojo-platform-channel-handle=1540 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2884 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1028,13895931101989397078,12340450996666135279,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=11395177377704247223 --mojo-platform-channel-handle=4152 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 400
Read events
1 305
Write events
91
Delete events
4
Modification events
| (PID) Process: | (3460) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3460) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3460) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3460) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3460) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3360) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3460-13211255075811250 |
Value: 259 | |||
| (PID) Process: | (3460) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3460) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3460) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (3460) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
2
Suspicious files
28
Text files
181
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF169918.TMP | — | |
MD5:— | SHA256:— | |||
| 3460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\abcf923d-ec79-4ef6-80d4-7abbfc107464.tmp | — | |
MD5:— | SHA256:— | |||
| 3460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\MANIFEST-000001 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
23
DNS requests
14
Threats
44
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3312 | IMG-SWIFT-71460 EUR_PDF.exe | POST | — | 194.209.228.127:80 | http://termexpo.ch/wp-admin/five/fre.php | CH | — | — | malicious |
3312 | IMG-SWIFT-71460 EUR_PDF.exe | POST | — | 194.209.228.127:80 | http://termexpo.ch/wp-admin/five/fre.php | CH | — | — | malicious |
2880 | chrome.exe | GET | 302 | 216.58.210.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 516 b | whitelisted |
3312 | IMG-SWIFT-71460 EUR_PDF.exe | POST | — | 194.209.228.127:80 | http://termexpo.ch/wp-admin/five/fre.php | CH | — | — | malicious |
3312 | IMG-SWIFT-71460 EUR_PDF.exe | POST | — | 194.209.228.127:80 | http://termexpo.ch/wp-admin/five/fre.php | CH | — | — | malicious |
3312 | IMG-SWIFT-71460 EUR_PDF.exe | POST | — | 194.209.228.127:80 | http://termexpo.ch/wp-admin/five/fre.php | CH | — | — | malicious |
3312 | IMG-SWIFT-71460 EUR_PDF.exe | POST | — | 194.209.228.127:80 | http://termexpo.ch/wp-admin/five/fre.php | CH | — | — | malicious |
3312 | IMG-SWIFT-71460 EUR_PDF.exe | POST | — | 194.209.228.127:80 | http://termexpo.ch/wp-admin/five/fre.php | CH | — | — | malicious |
2880 | chrome.exe | GET | 200 | 74.125.4.167:80 | http://r2---sn-aigzrne7.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.217.117.157&mm=28&mn=sn-aigzrne7&ms=nvh&mt=1566781577&mv=m&mvi=1&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2880 | chrome.exe | 94.127.7.166:443 | mkngroup.mycpanel.rs | Serbia BroadBand-Srpske Kablovske mreze d.o.o. | RS | unknown |
2880 | chrome.exe | 216.58.205.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2880 | chrome.exe | 172.217.22.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
2880 | chrome.exe | 216.58.206.14:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
2880 | chrome.exe | 172.217.18.164:443 | www.google.com | Google Inc. | US | whitelisted |
2880 | chrome.exe | 172.217.22.67:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3312 | IMG-SWIFT-71460 EUR_PDF.exe | 194.209.228.127:80 | termexpo.ch | Swisscom (Switzerland) Ltd | CH | malicious |
2880 | chrome.exe | 216.58.207.42:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2880 | chrome.exe | 172.217.22.46:443 | clients1.google.com | Google Inc. | US | whitelisted |
2880 | chrome.exe | 172.217.18.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
mkngroup.mycpanel.rs |
| unknown |
accounts.google.com |
| shared |
sb-ssl.google.com |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
termexpo.ch |
| malicious |
www.gstatic.com |
| whitelisted |
clients1.google.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3312 | IMG-SWIFT-71460 EUR_PDF.exe | A Network Trojan was detected | ET TROJAN LokiBot User-Agent (Charon/Inferno) |
3312 | IMG-SWIFT-71460 EUR_PDF.exe | A Network Trojan was detected | ET TROJAN LokiBot Checkin |
3312 | IMG-SWIFT-71460 EUR_PDF.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M1 |
3312 | IMG-SWIFT-71460 EUR_PDF.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M2 |
3312 | IMG-SWIFT-71460 EUR_PDF.exe | A Network Trojan was detected | MALWARE [PTsecurity] Loki Bot Check-in M2 |
3312 | IMG-SWIFT-71460 EUR_PDF.exe | A Network Trojan was detected | ET TROJAN LokiBot User-Agent (Charon/Inferno) |
3312 | IMG-SWIFT-71460 EUR_PDF.exe | A Network Trojan was detected | ET TROJAN LokiBot Checkin |
3312 | IMG-SWIFT-71460 EUR_PDF.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M1 |
3312 | IMG-SWIFT-71460 EUR_PDF.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M2 |
3312 | IMG-SWIFT-71460 EUR_PDF.exe | A Network Trojan was detected | MALWARE [PTsecurity] Loki Bot Check-in M2 |
7 ETPRO signatures available at the full report