| File name: | abf616c8-f805-ed87-0caa-ebb5e53d4391.eml |
| Full analysis: | https://app.any.run/tasks/ab3600a8-3594-4e46-8a8e-2abc329a4d1f |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | December 05, 2022, 17:26:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | RFC 822 mail, ASCII text, with CRLF line terminators |
| MD5: | 74D5EF95127671DFDAF8685731DBA177 |
| SHA1: | 68C028E760747BB3D11172749B1F5AD4BDCD136F |
| SHA256: | 19B4F4F7AE7E3F16E6BA52CA11A9118522CDFBFF326A039555294872B74AEB38 |
| SSDEEP: | 12288:h1IoH/NVBlnXbS8d0UWNlb/3IktBCyqxUdAQesrH4yZ6JwzgfqBjHc+QP:hpfABPIkaUdwsrpZfgfqBw+QP |
MALICIOUS
Application was dropped or rewritten from another process
- pago 89336.exe (PID: 3780)
- pago 89336.exe (PID: 2920)
Steals credentials from Web Browsers
- pago 89336.exe (PID: 2920)
AGENTTESLA detected by memory dumps
- pago 89336.exe (PID: 2920)
SUSPICIOUS
Detected use of alternative data streams (AltDS)
- OUTLOOK.EXE (PID: 2056)
Application launched itself
- pago 89336.exe (PID: 3780)
Reads settings of System Certificates
- pago 89336.exe (PID: 2920)
Reads the Internet Settings
- pago 89336.exe (PID: 2920)
Adds/modifies Windows certificates
- pago 89336.exe (PID: 2920)
INFO
Checks supported languages
- pago 89336.exe (PID: 3780)
- pago 89336.exe (PID: 2920)
Reads the computer name
- pago 89336.exe (PID: 3780)
- pago 89336.exe (PID: 2920)
Manual execution by a user
- WinRAR.exe (PID: 3176)
Reads Environment values
- pago 89336.exe (PID: 2920)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 5) (100) |
|---|
Total processes
41
Monitored processes
4
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
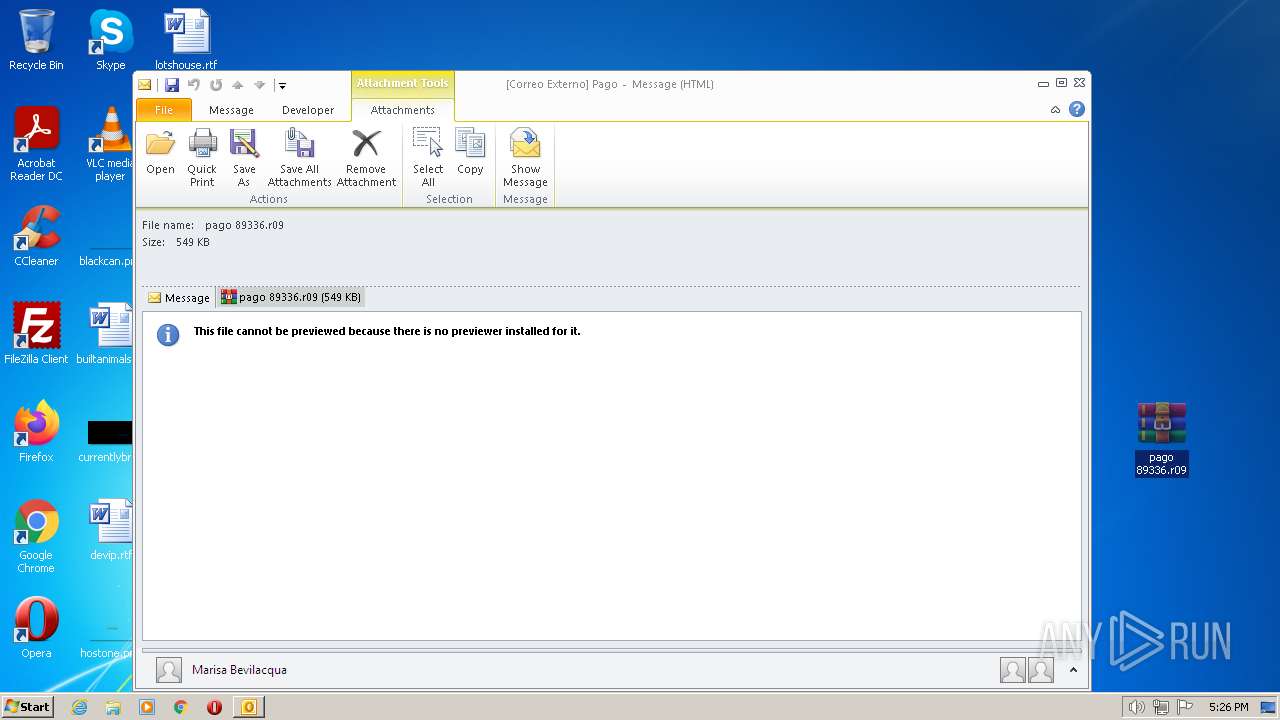
| 2056 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\abf616c8-f805-ed87-0caa-ebb5e53d4391.eml" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 2920 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3176.20355\pago 89336.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3176.20355\pago 89336.exe | pago 89336.exe | ||||||||||||
User: admin Company: MagnaSolution Integrity Level: MEDIUM Description: Leather Worker Exit code: 0 Version: 1.3.0.0 Modules
| |||||||||||||||
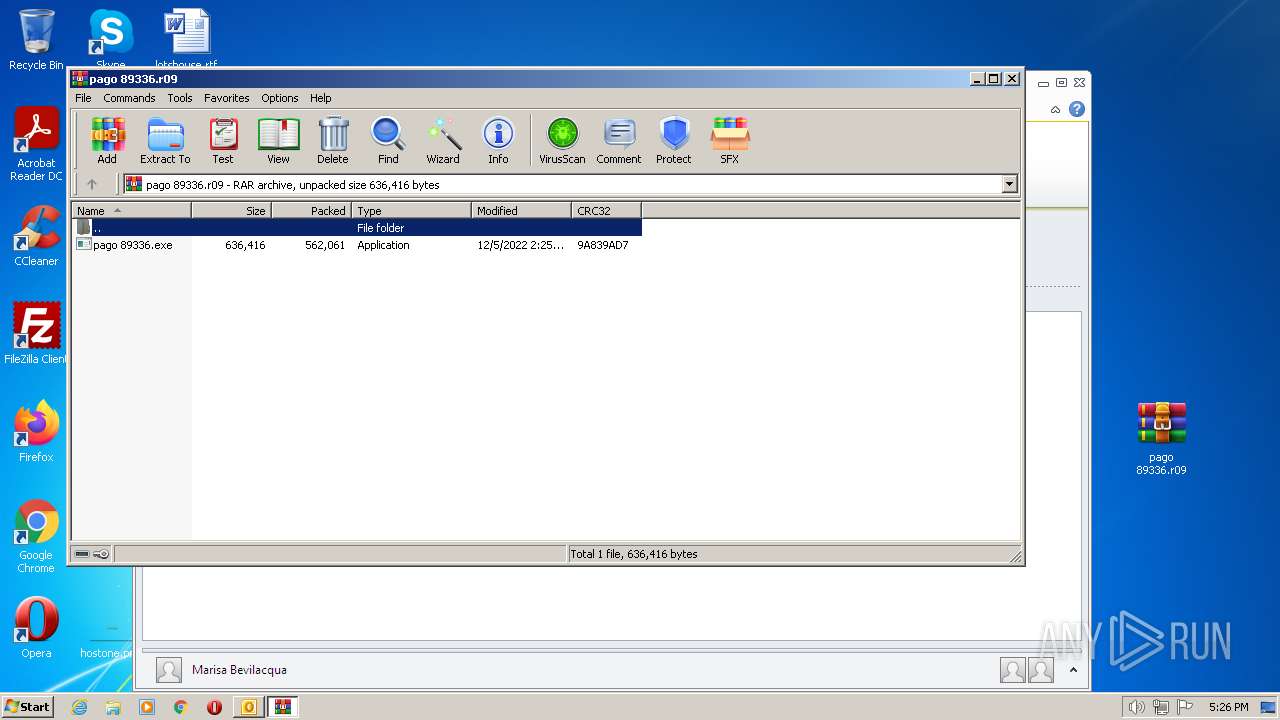
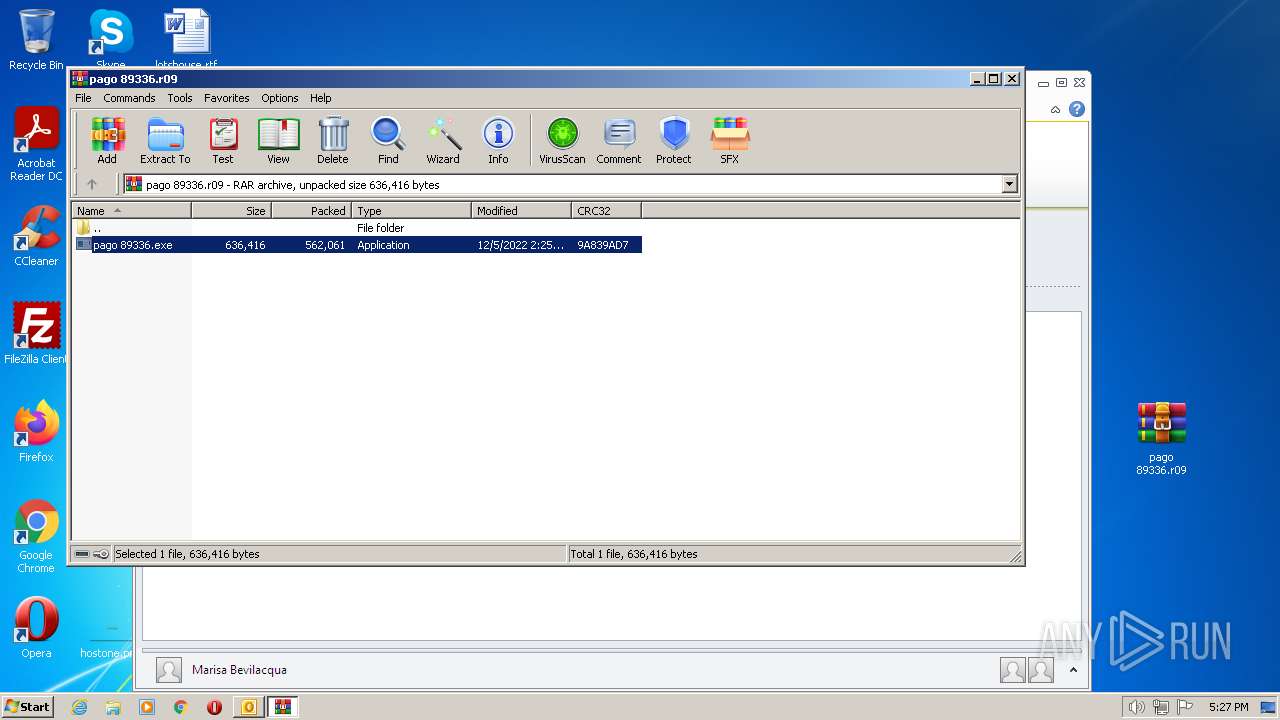
| 3176 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\pago 89336.r09" | C:\Program Files\WinRAR\WinRAR.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3780 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3176.20355\pago 89336.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3176.20355\pago 89336.exe | — | WinRAR.exe | |||||||||||
User: admin Company: MagnaSolution Integrity Level: MEDIUM Description: Leather Worker Exit code: 0 Version: 1.3.0.0 Modules
| |||||||||||||||
Total events
9 928
Read events
9 304
Write events
602
Delete events
22
Modification events
| (PID) Process: | (2056) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2056) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2056) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2056) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2056) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2056) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2056) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2056) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2056) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (2056) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
1
Suspicious files
6
Text files
12
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2056 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVREC49.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2056 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook Data File - NoMail.pst | — | |
MD5:— | SHA256:— | |||
| 2056 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\tmpED25.tmp | binary | |
MD5:— | SHA256:— | |||
| 2056 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
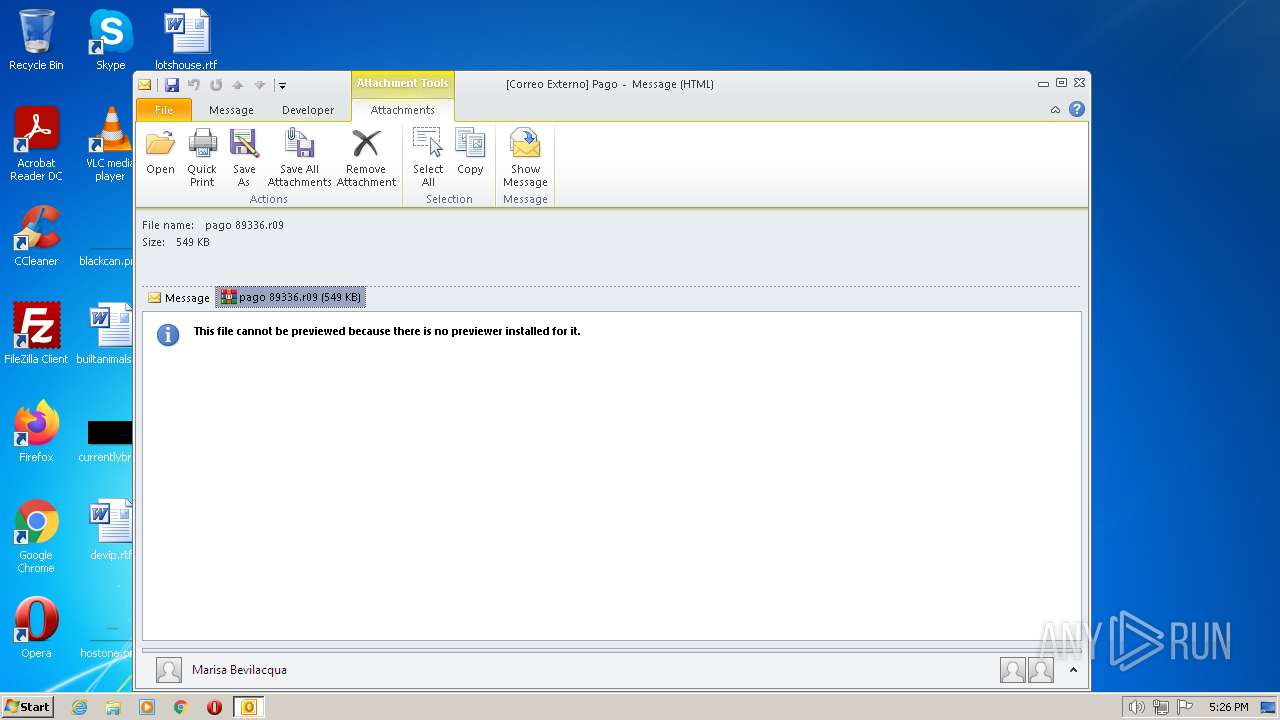
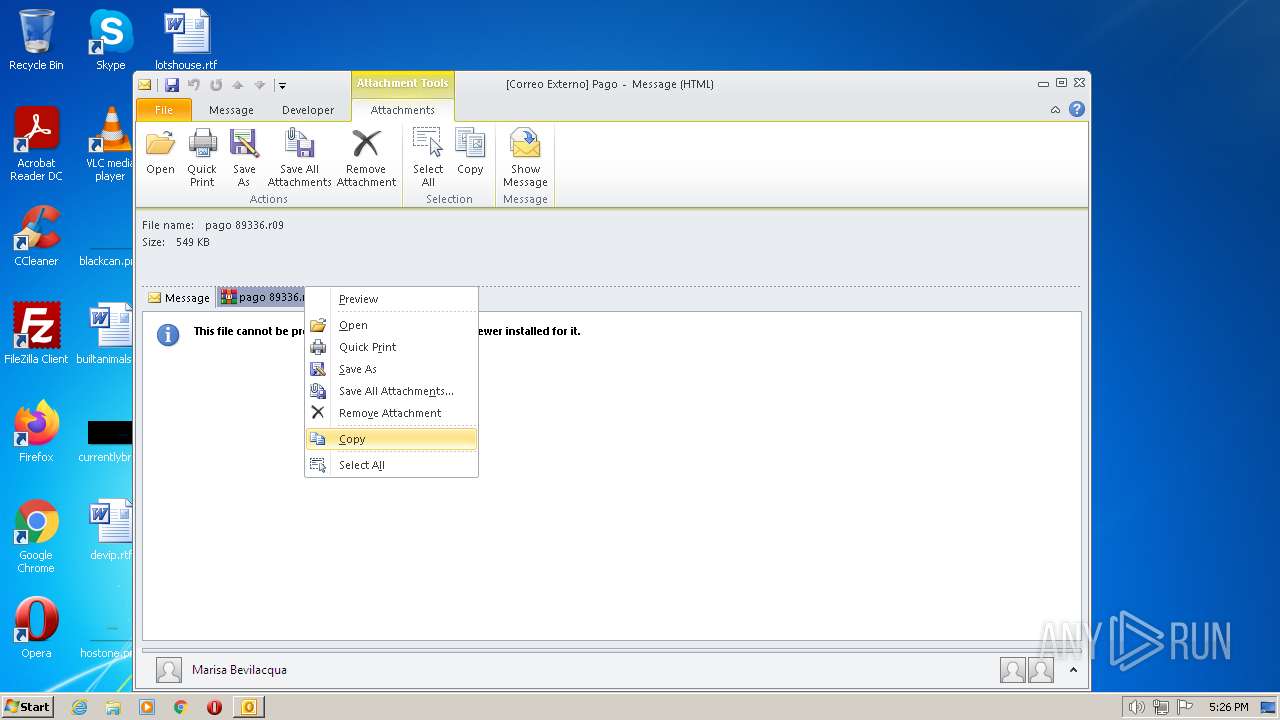
| 2056 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\8LJHU5SD\pago 89336.r09 | compressed | |
MD5:— | SHA256:— | |||
| 2056 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\8LJHU5SD\pago 89336 (2).r09 | compressed | |
MD5:— | SHA256:— | |||
| 2920 | pago 89336.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:— | SHA256:— | |||
| 2056 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3176 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3176.20355\pago 89336.exe | executable | |
MD5:— | SHA256:— | |||
| 2056 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_WorkHours_1_69F8C583A83A284192DFF828FC443DA6.dat | xml | |
MD5:807EF0FC900FEB3DA82927990083D6E7 | SHA256:4411E7DC978011222764943081500FFF0E43CBF7CCD44264BD1AB6306CA68913 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
3
DNS requests
4
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2920 | pago 89336.exe | GET | 200 | 95.140.236.128:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?15a1ed1750f5a05b | GB | compressed | 61.4 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2056 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2920 | pago 89336.exe | 78.140.195.54:587 | mail2.bpk-spb.ru | JSC Severen-Telecom | RU | malicious |
2920 | pago 89336.exe | 95.140.236.128:80 | ctldl.windowsupdate.com | LLNW | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
dns.msftncsi.com |
| shared |
mail2.bpk-spb.ru |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2920 | pago 89336.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |