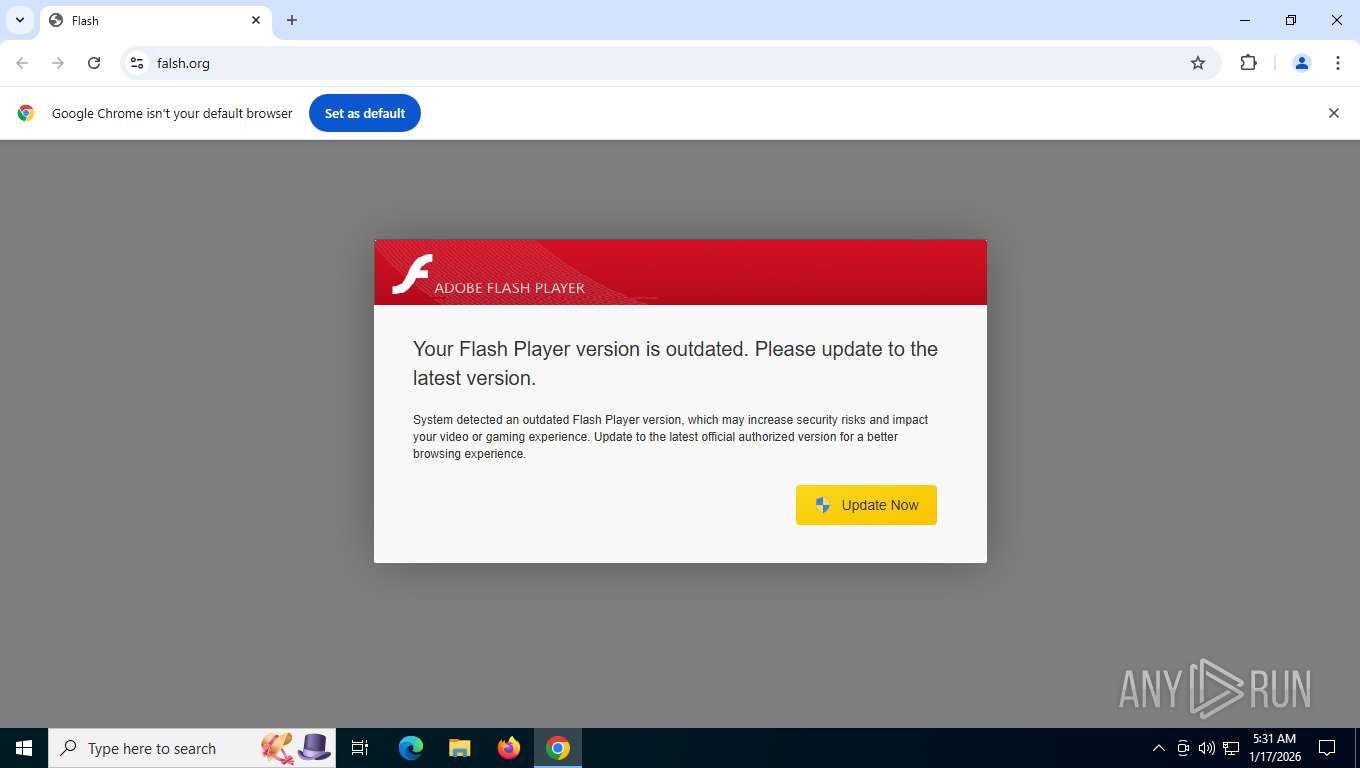
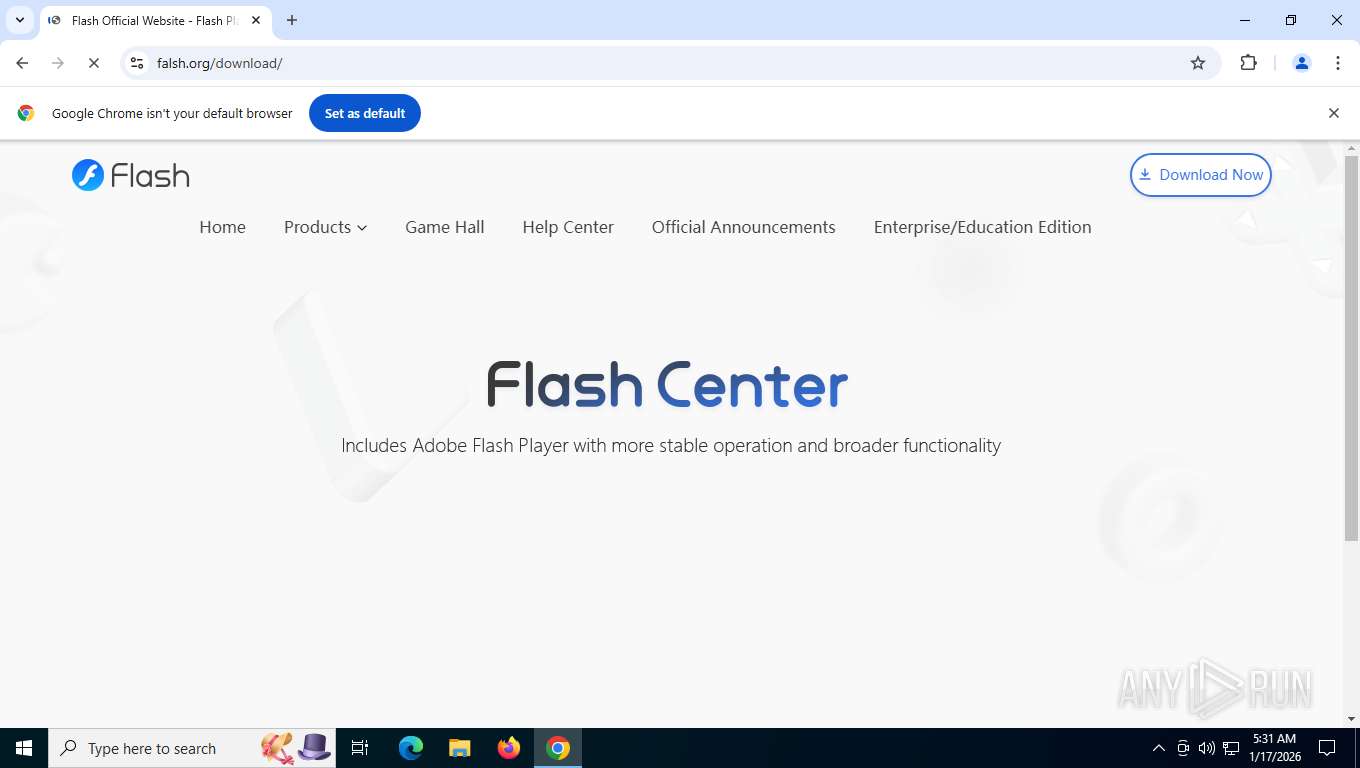
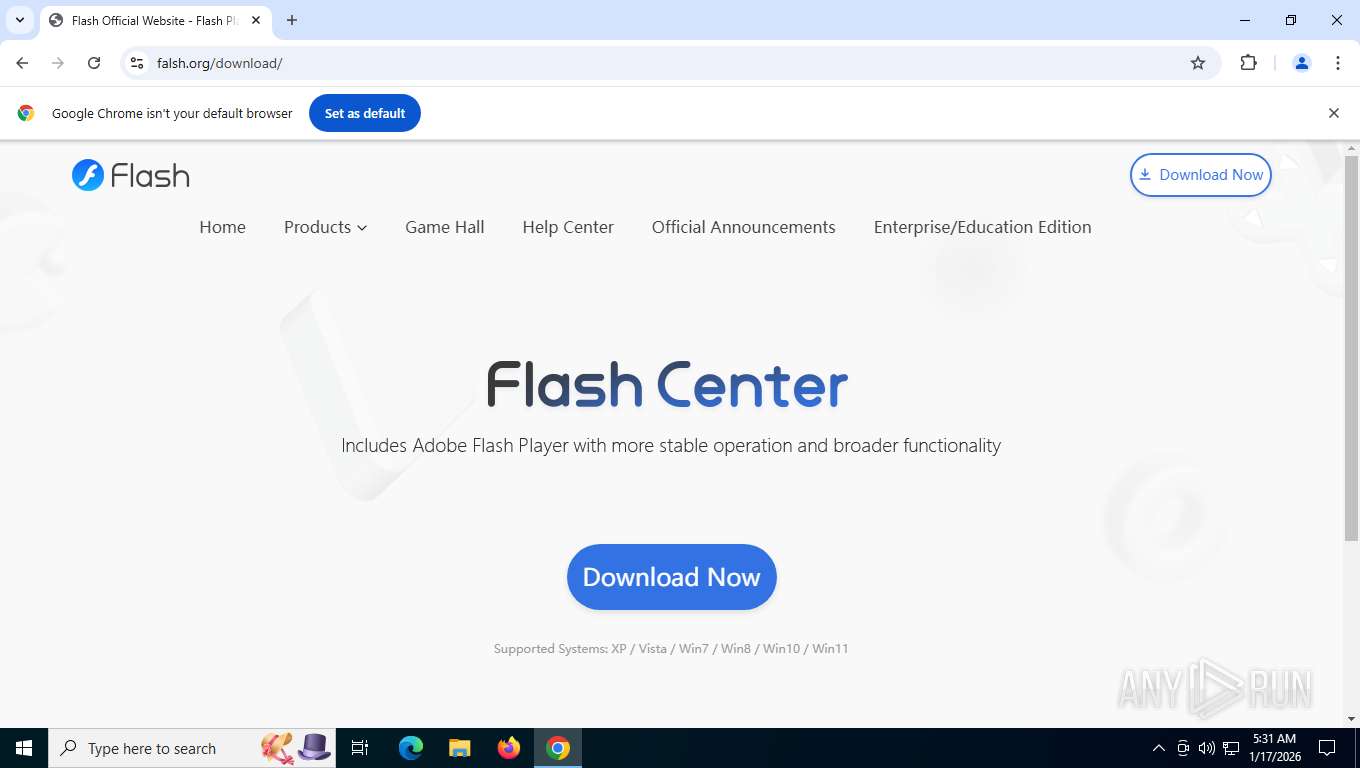
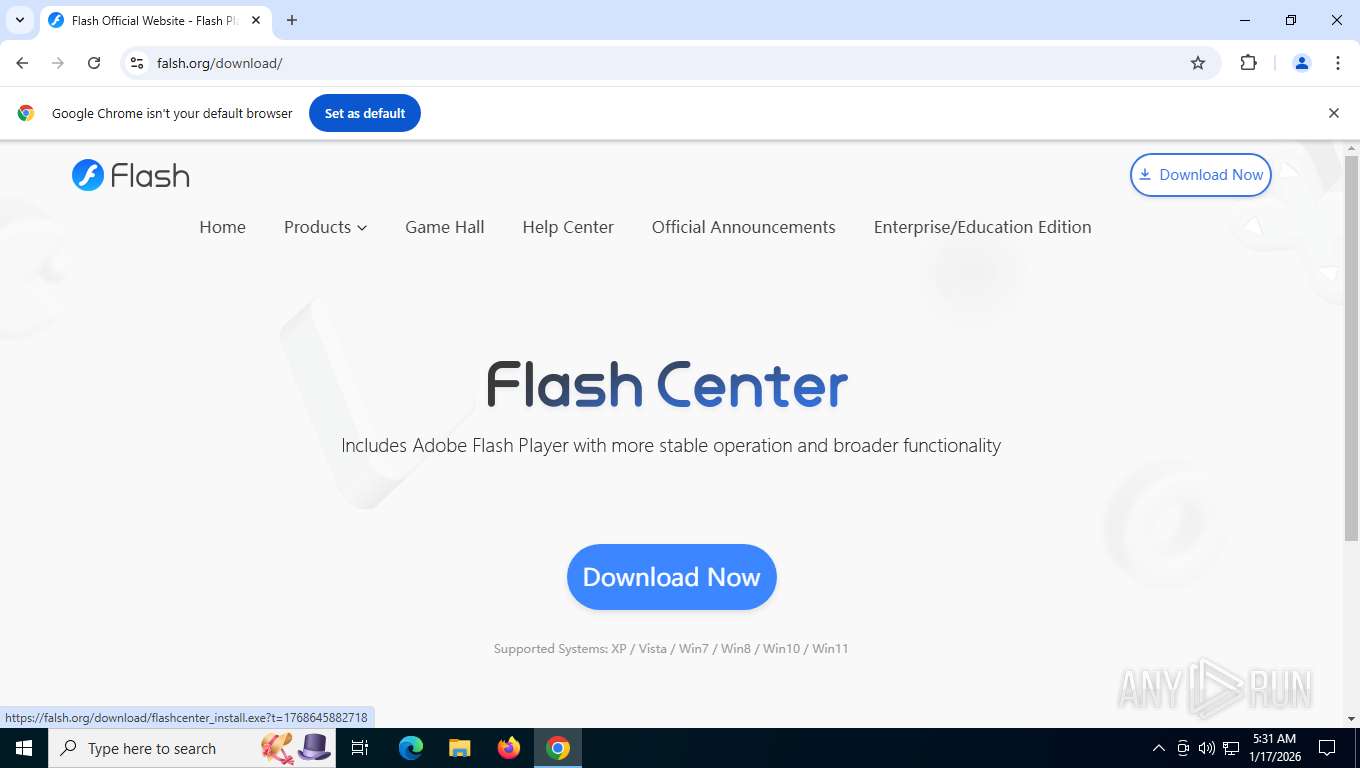
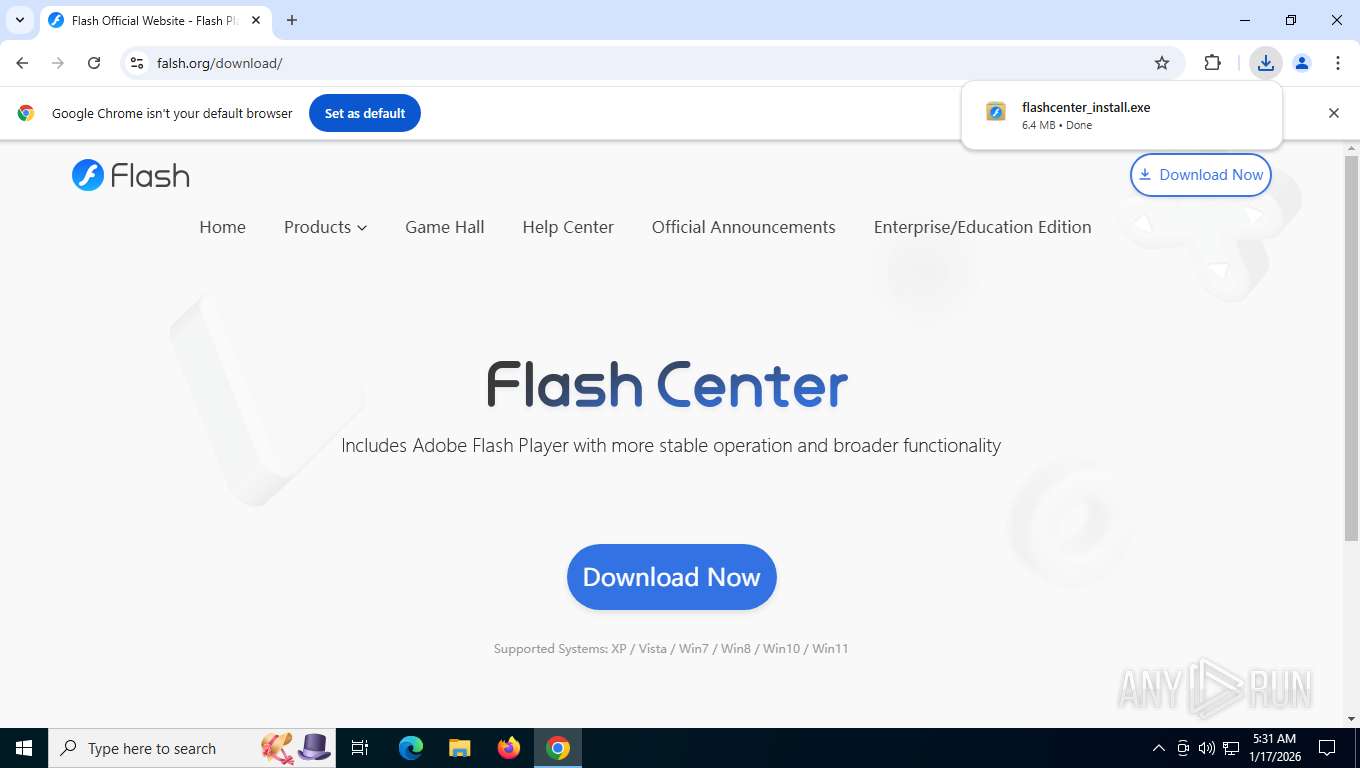
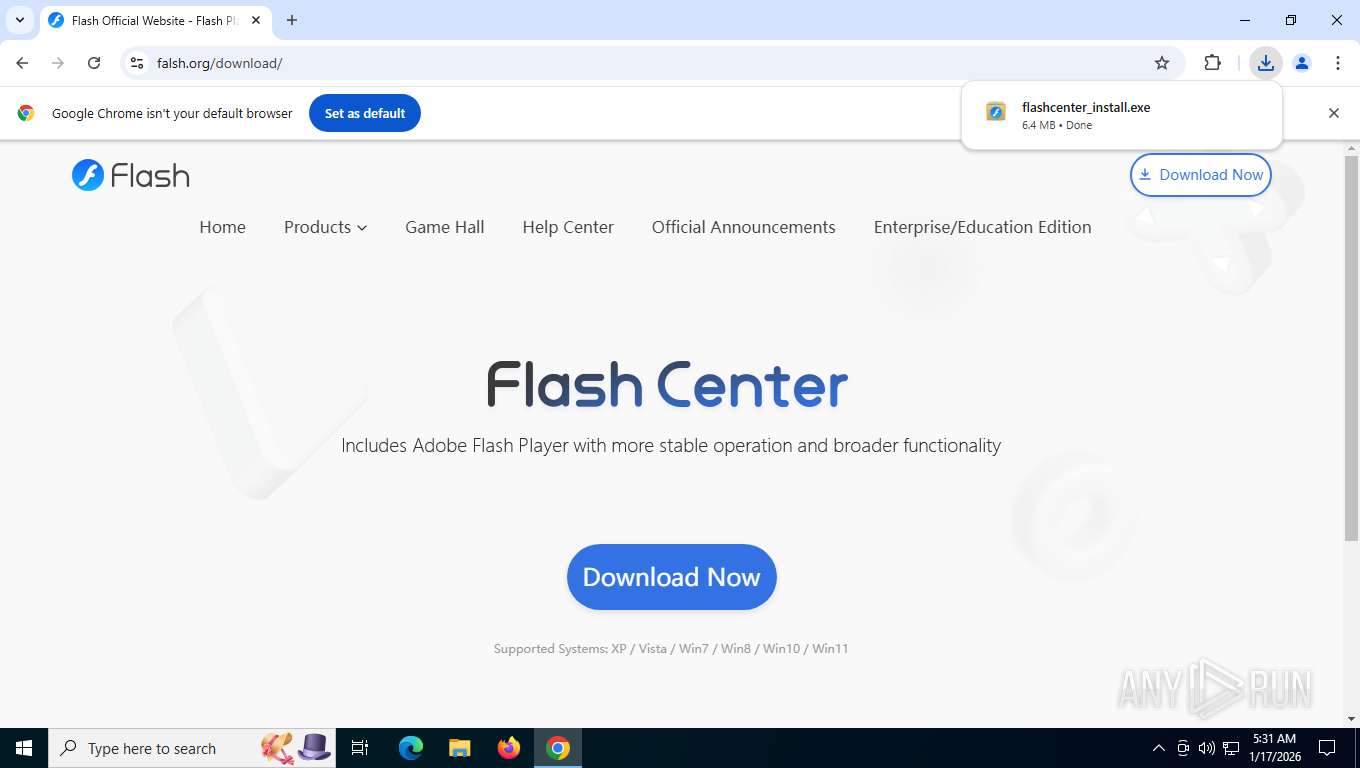
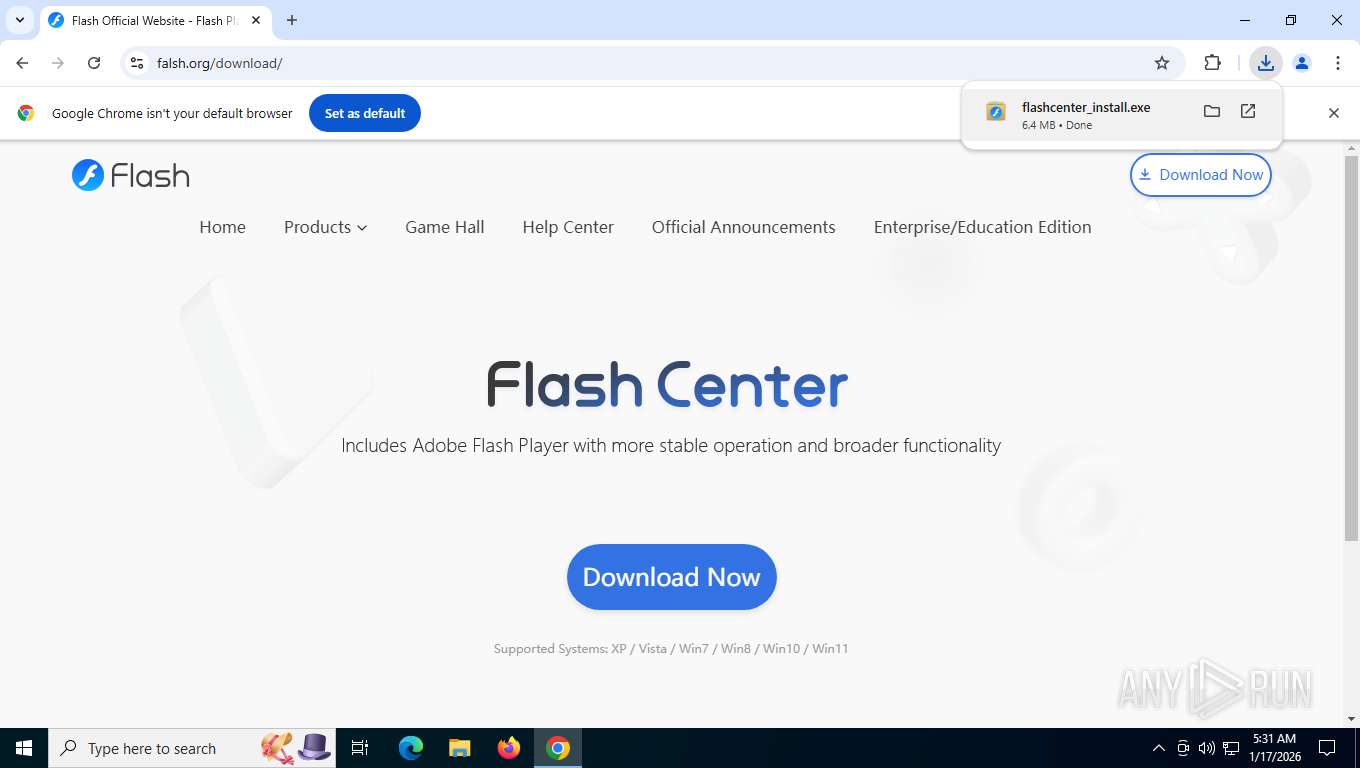
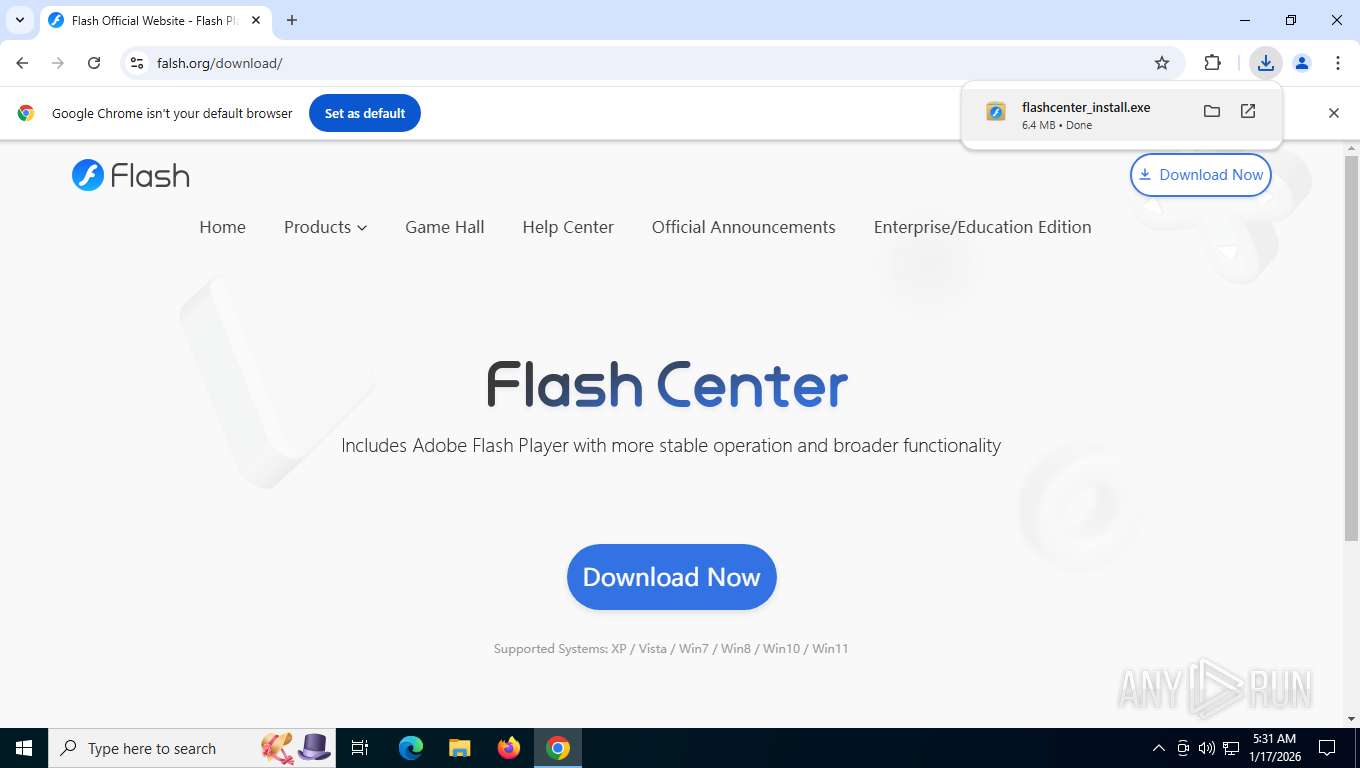
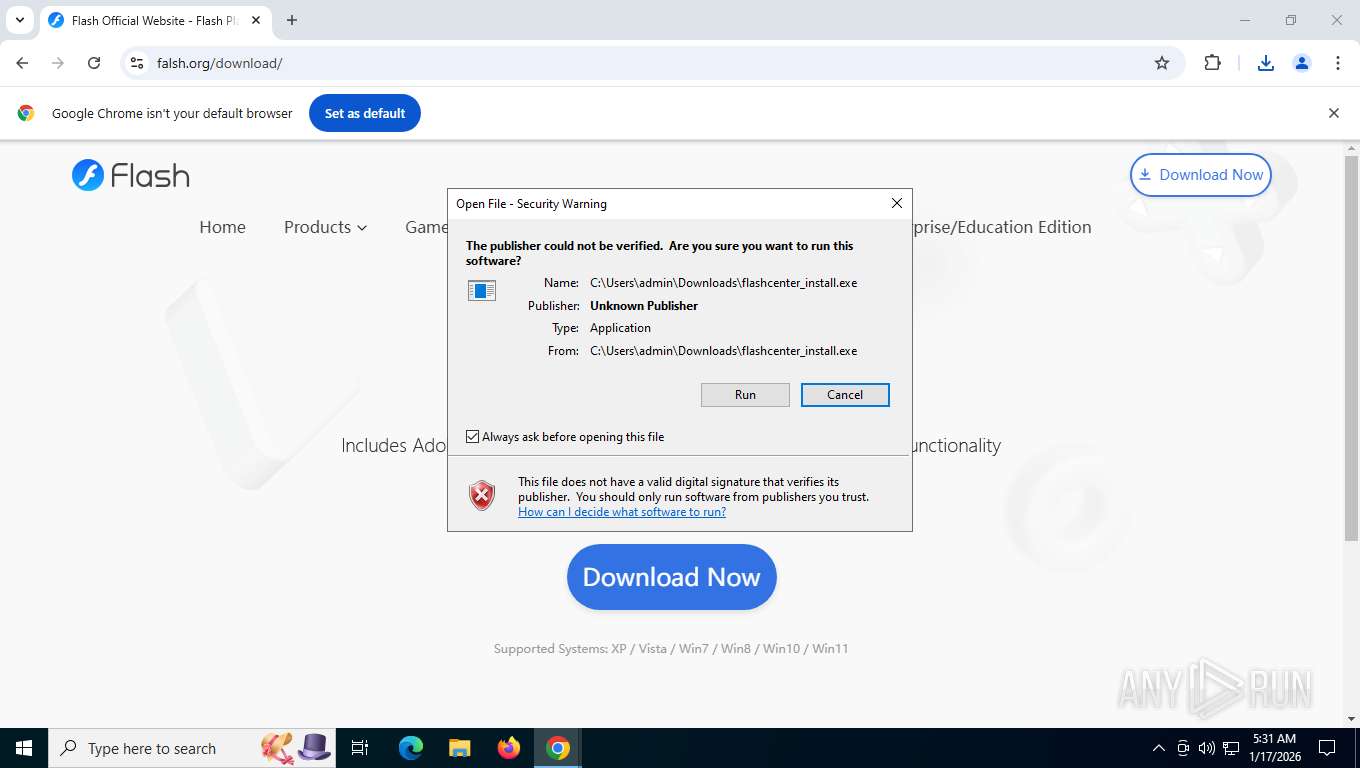
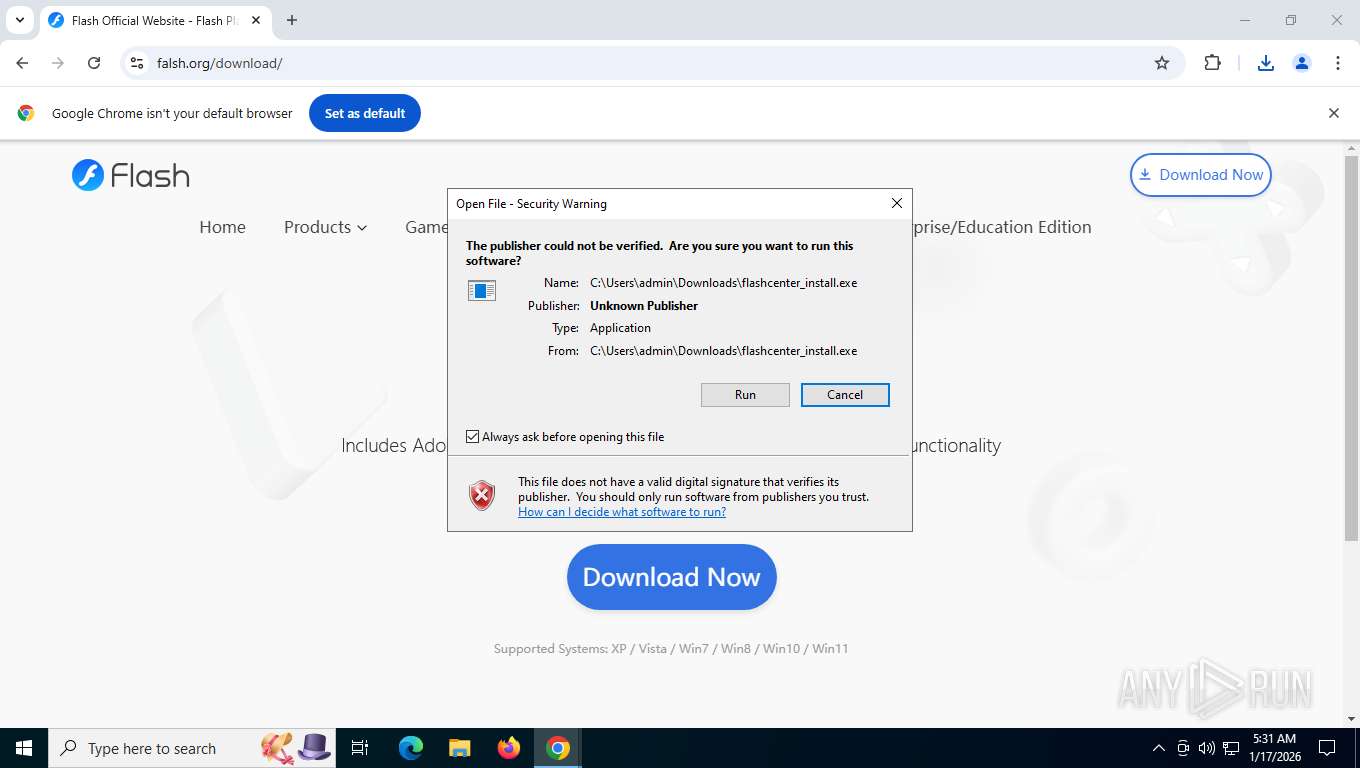
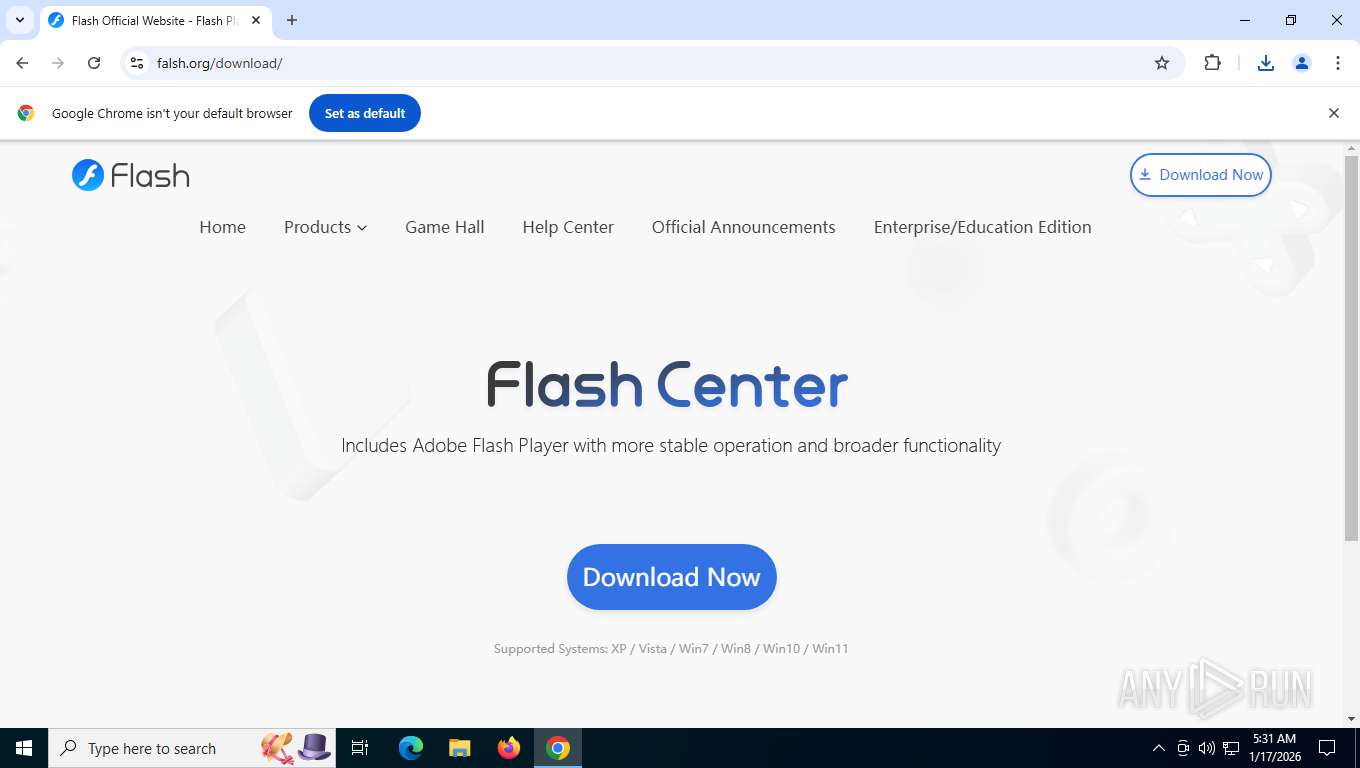
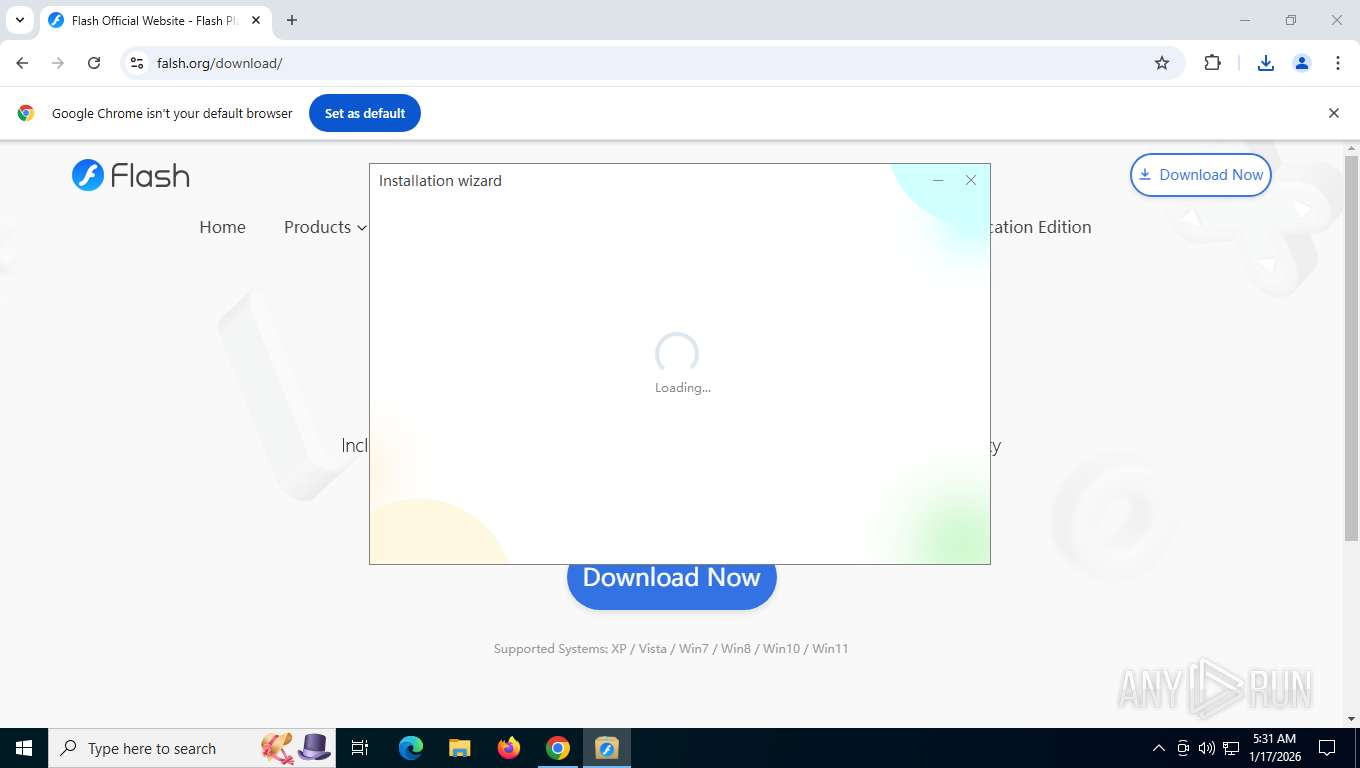
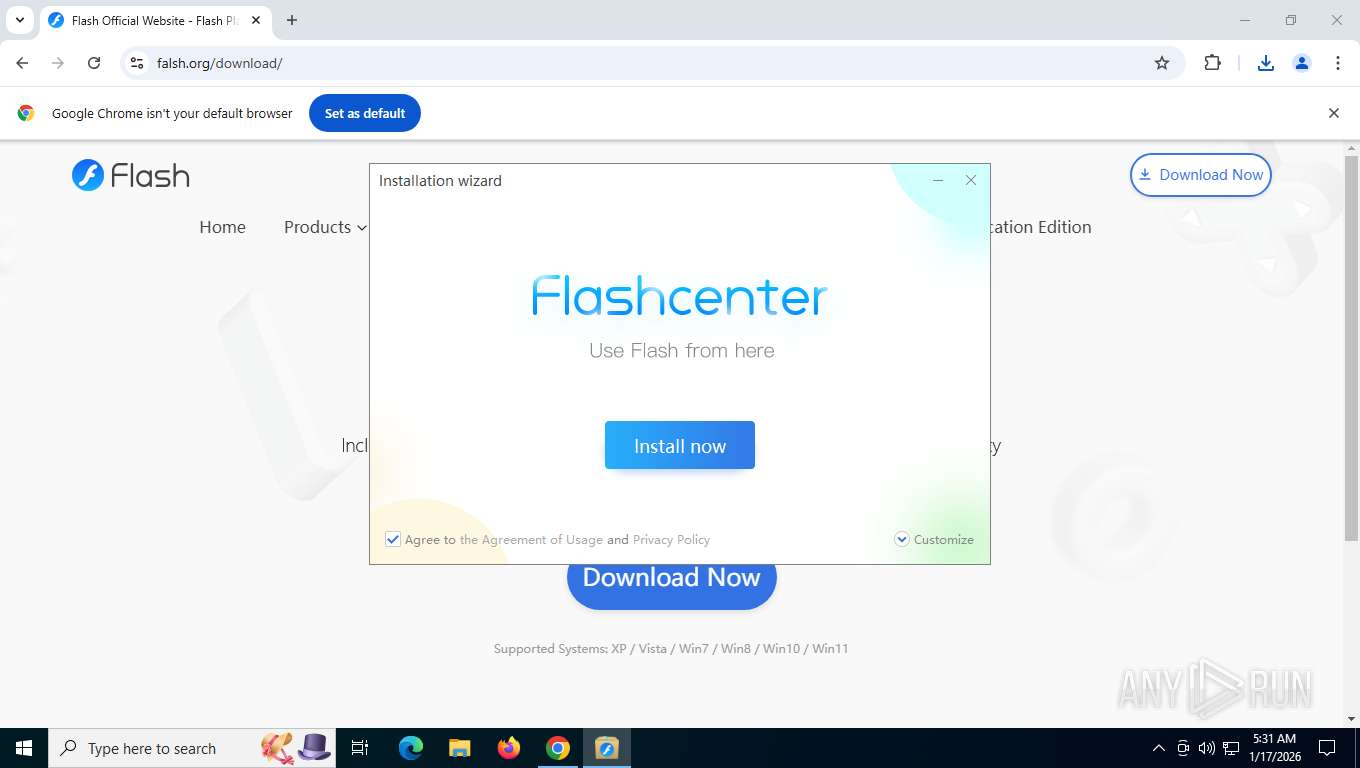
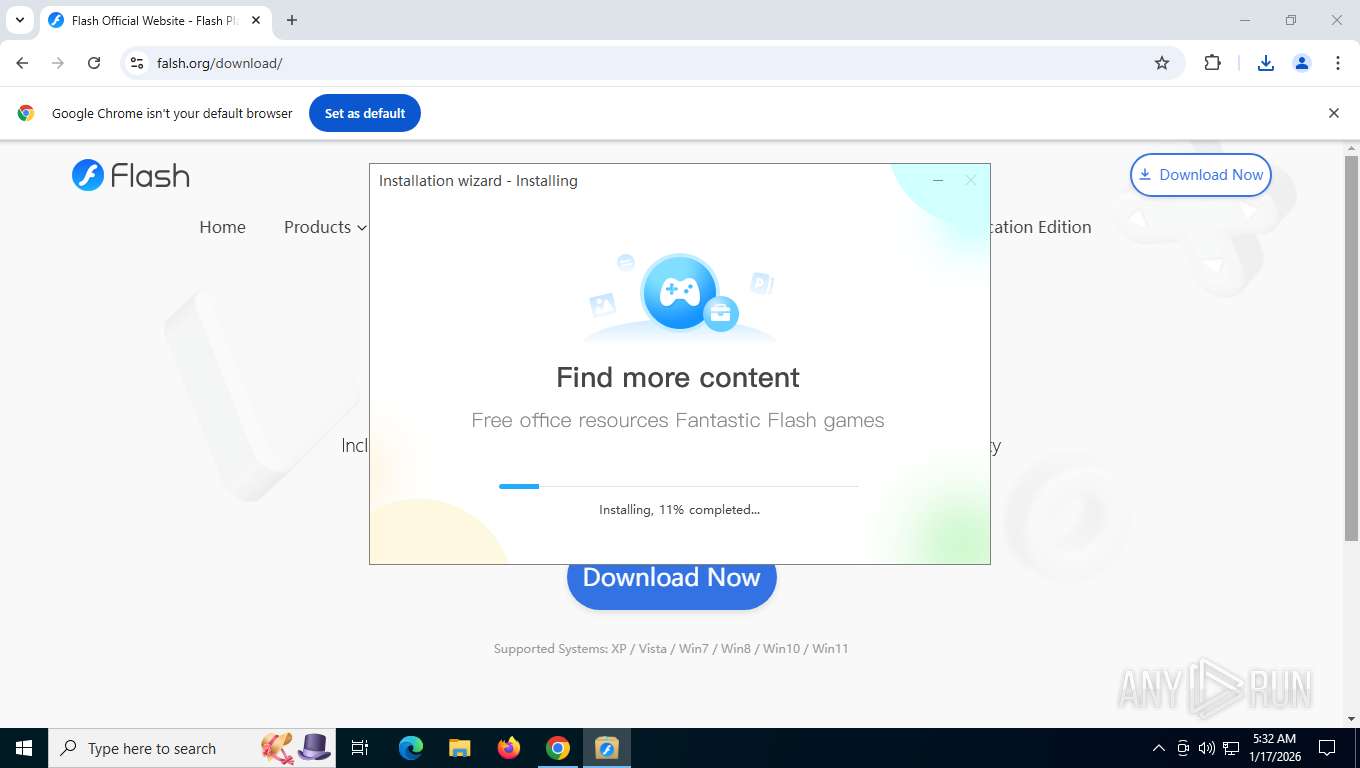
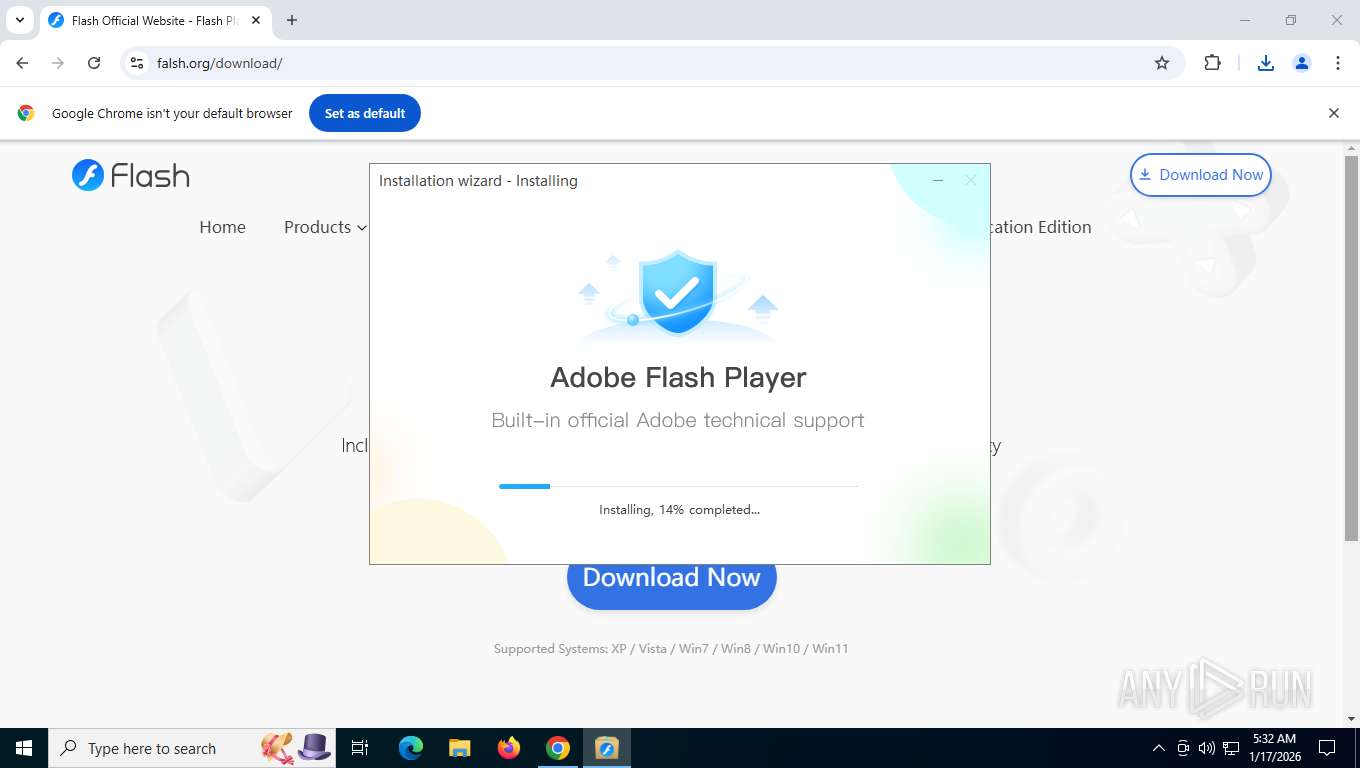
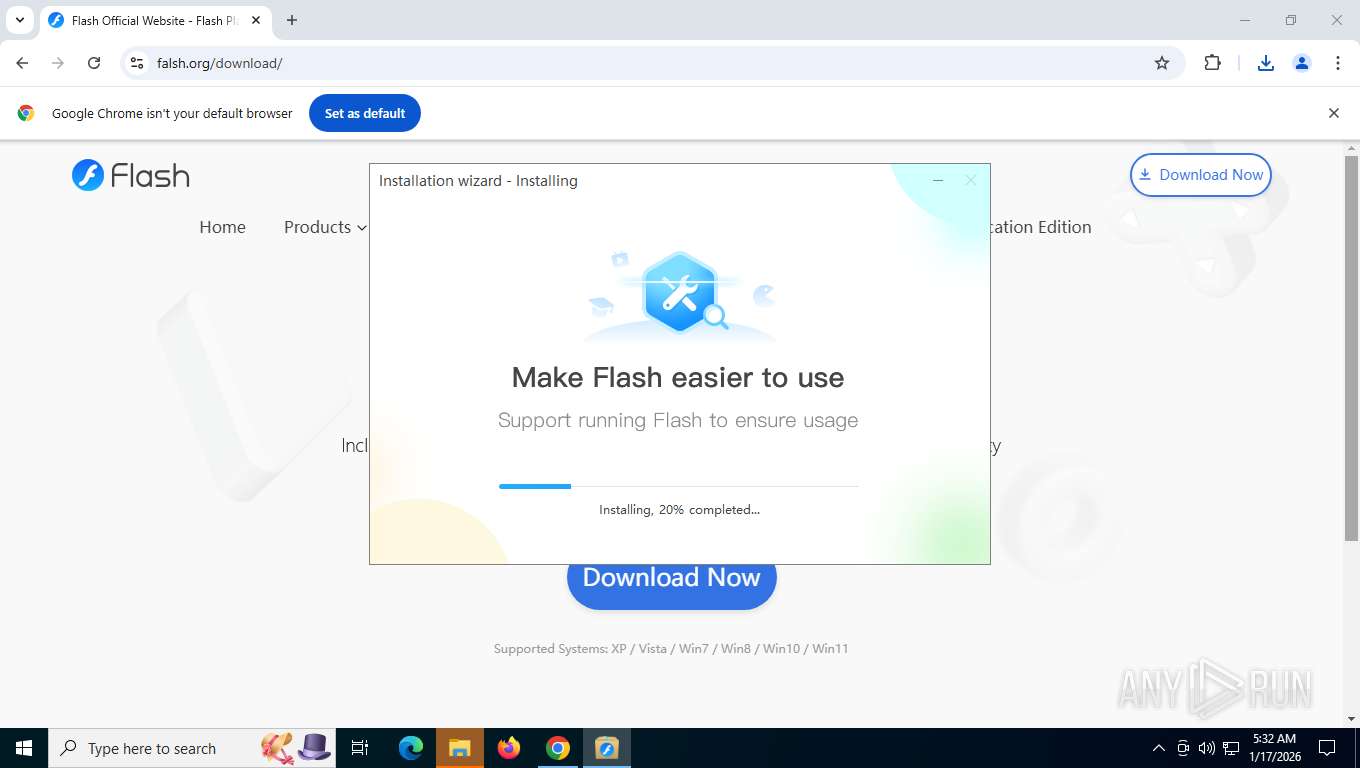
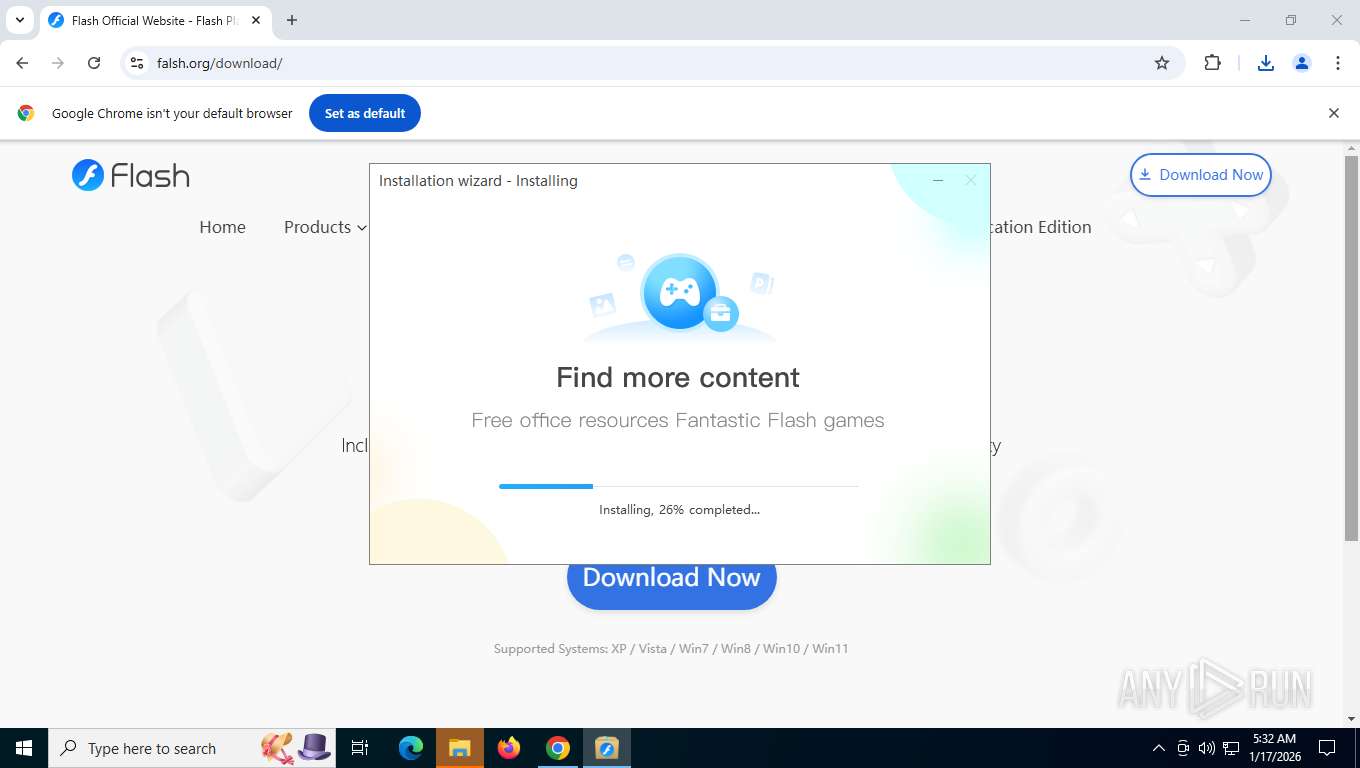
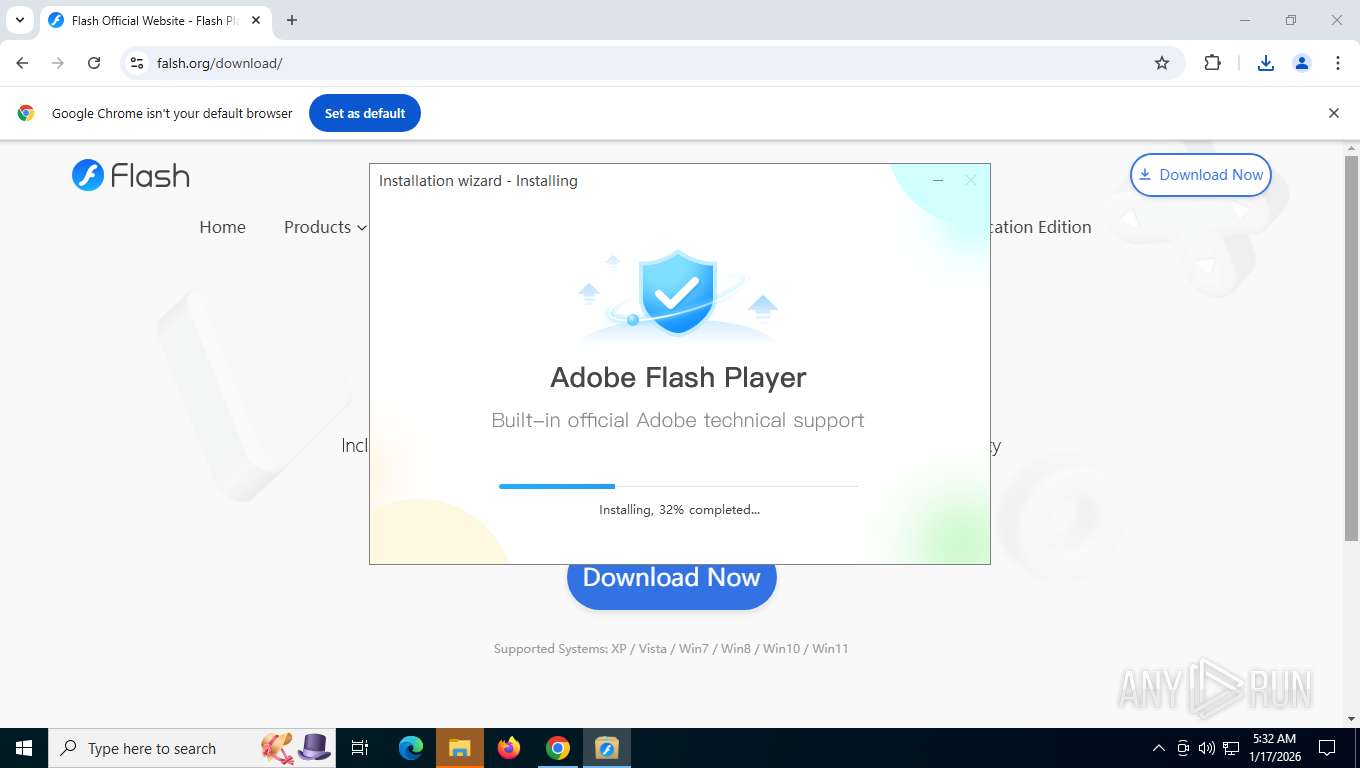
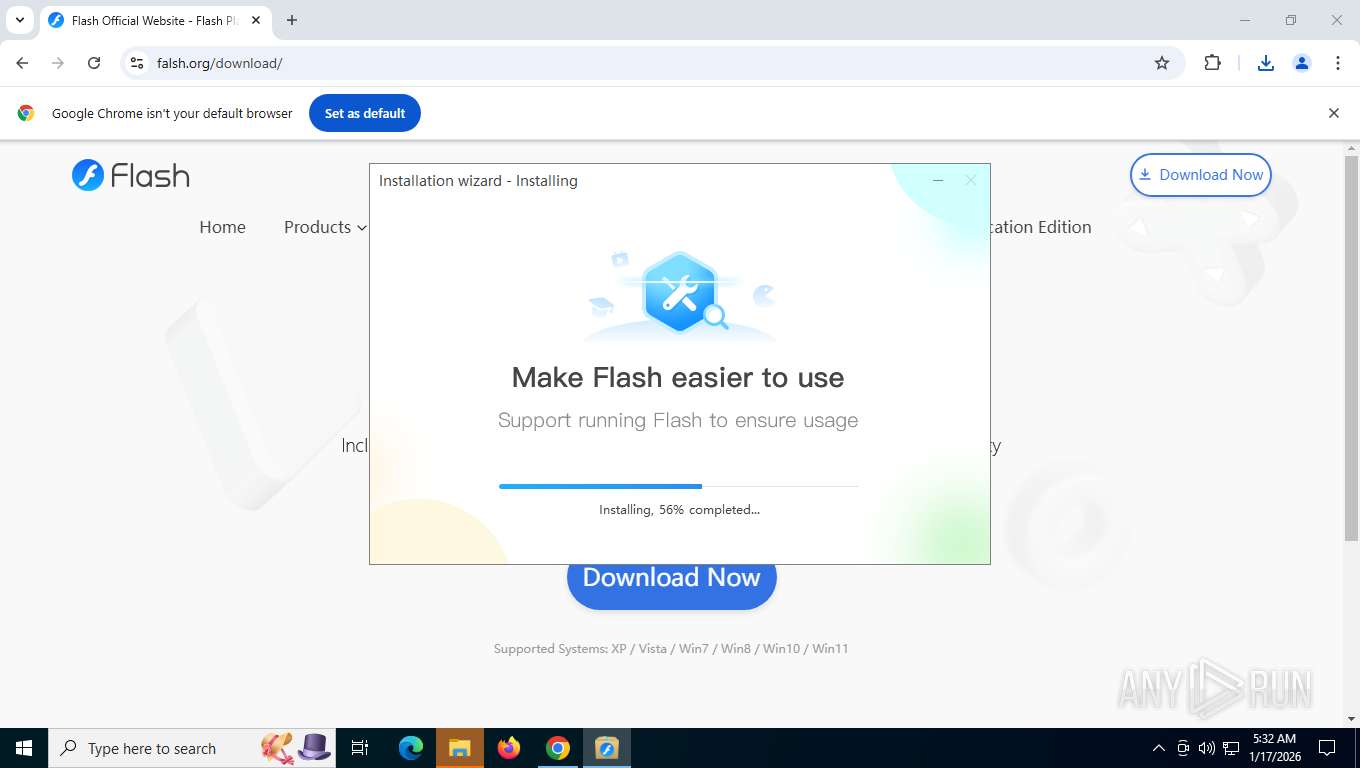
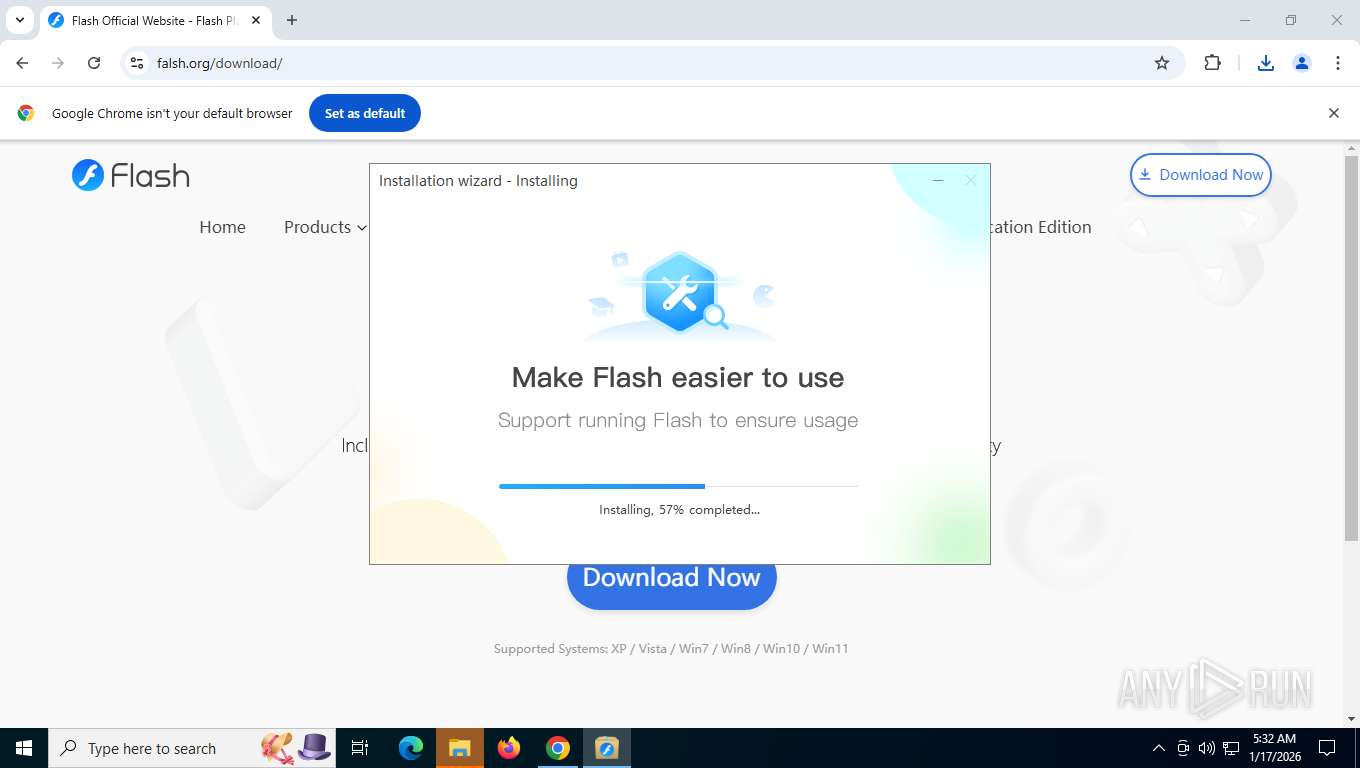
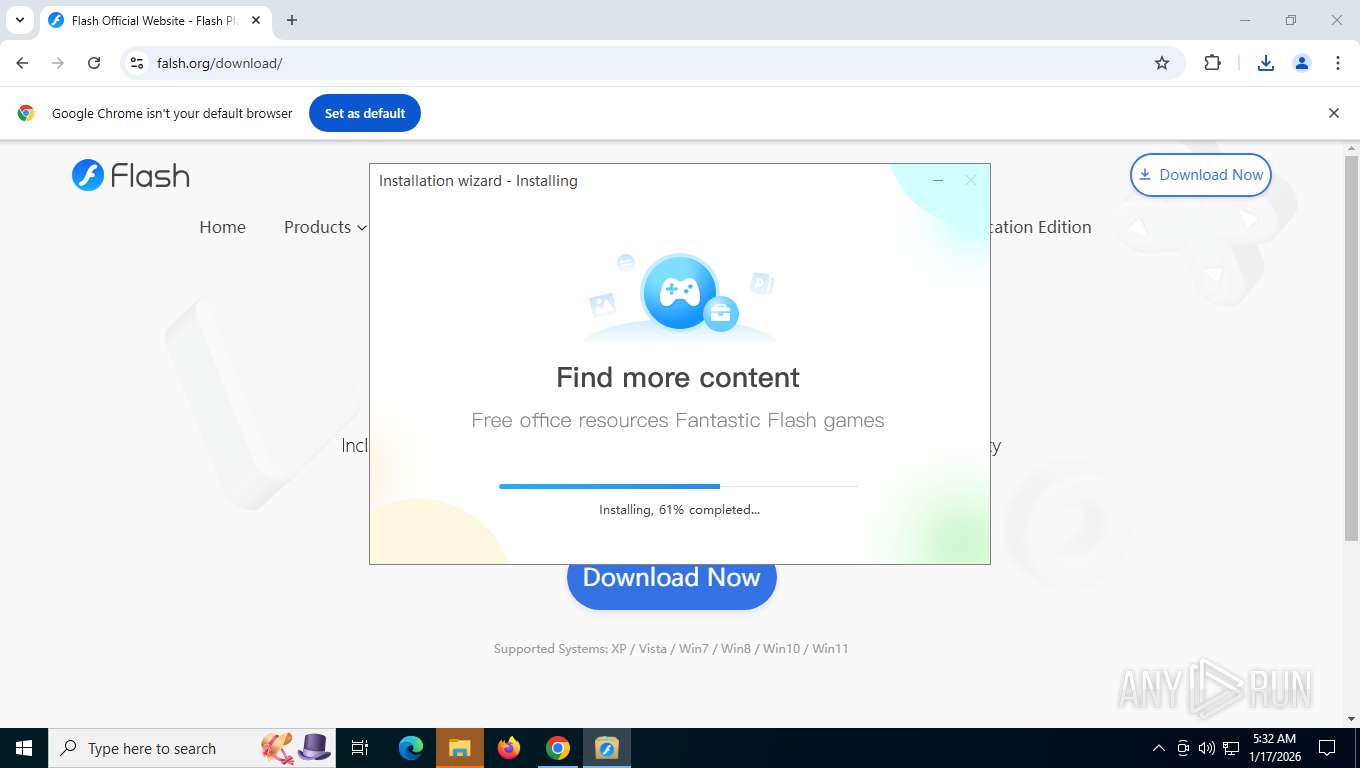
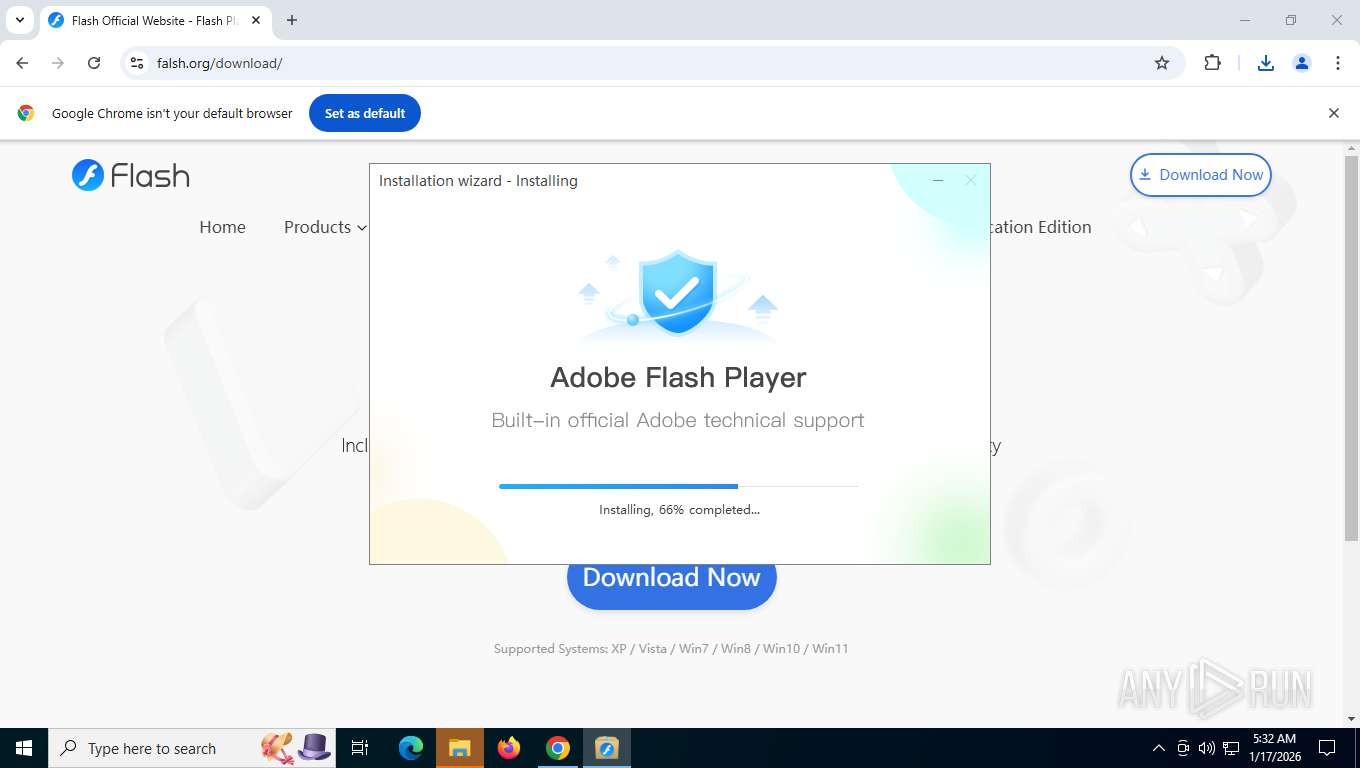
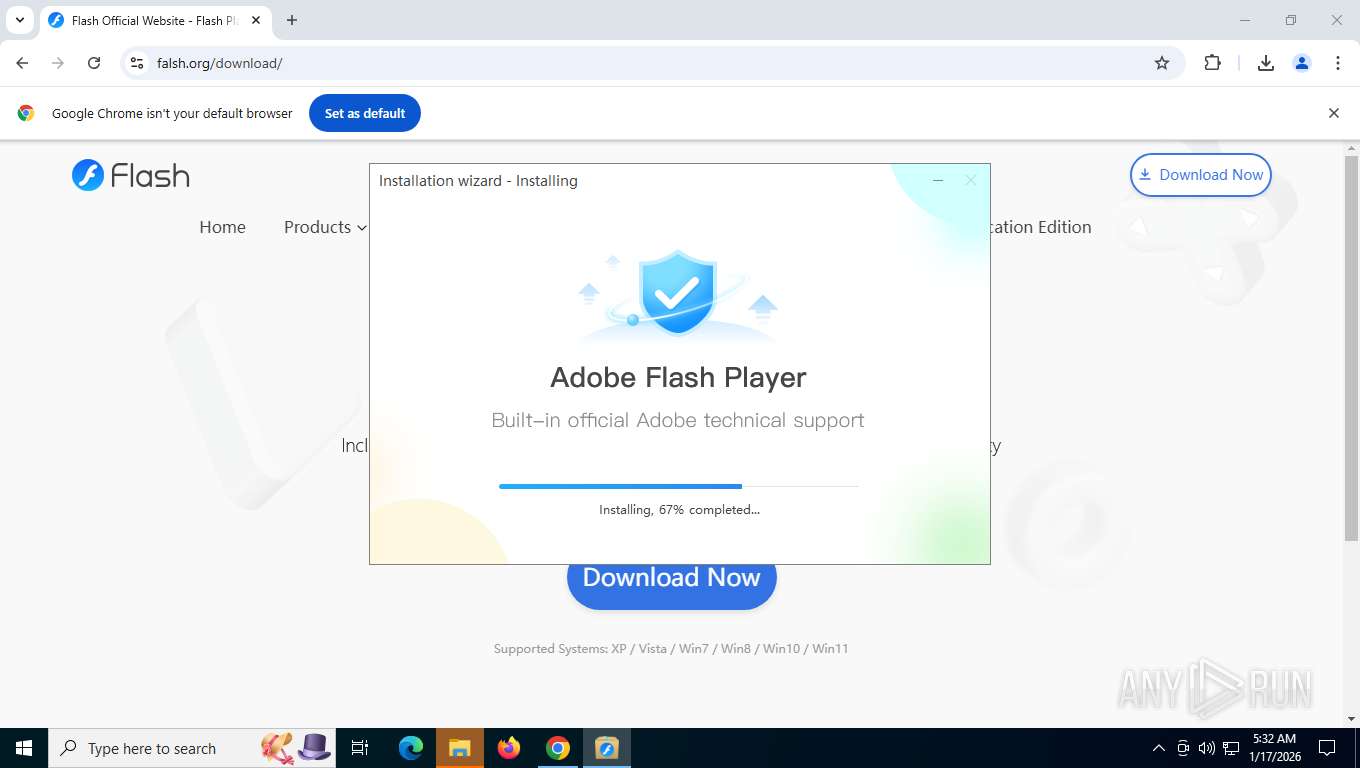
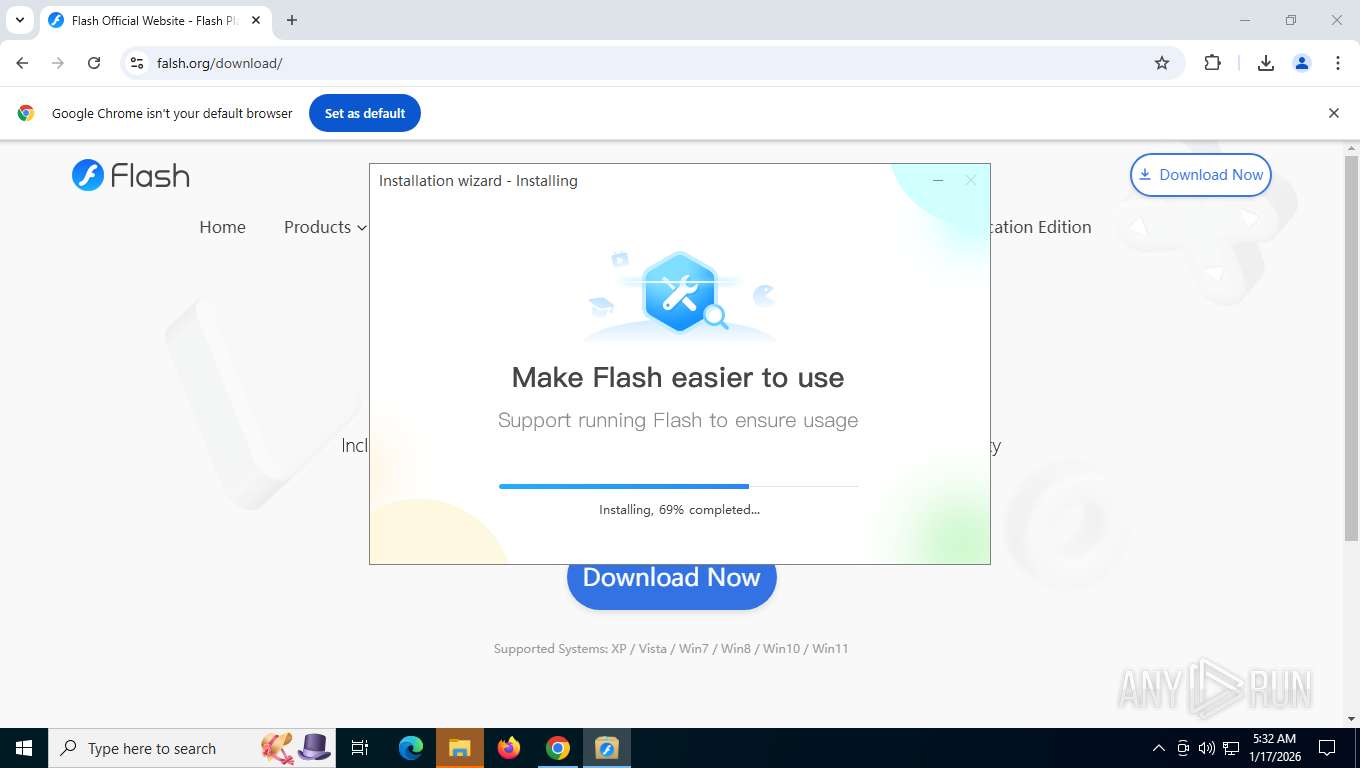
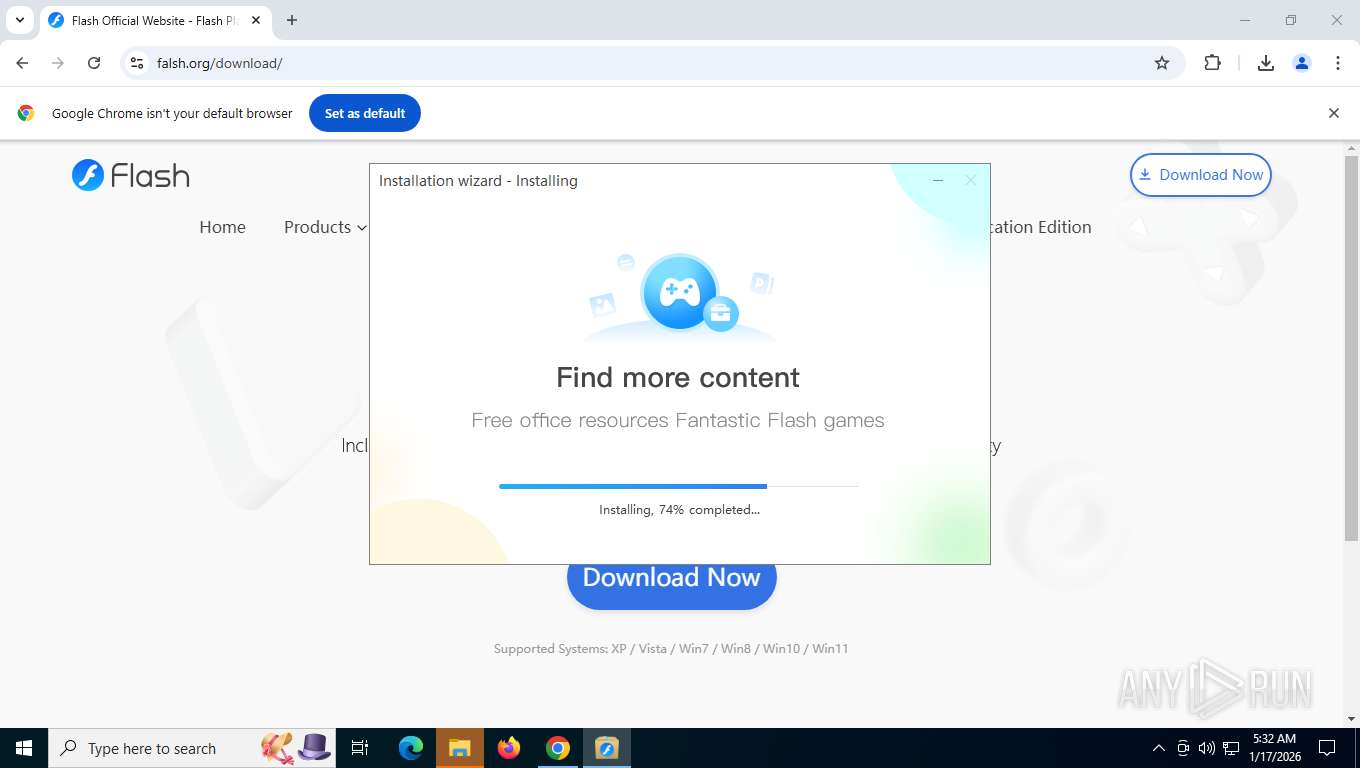
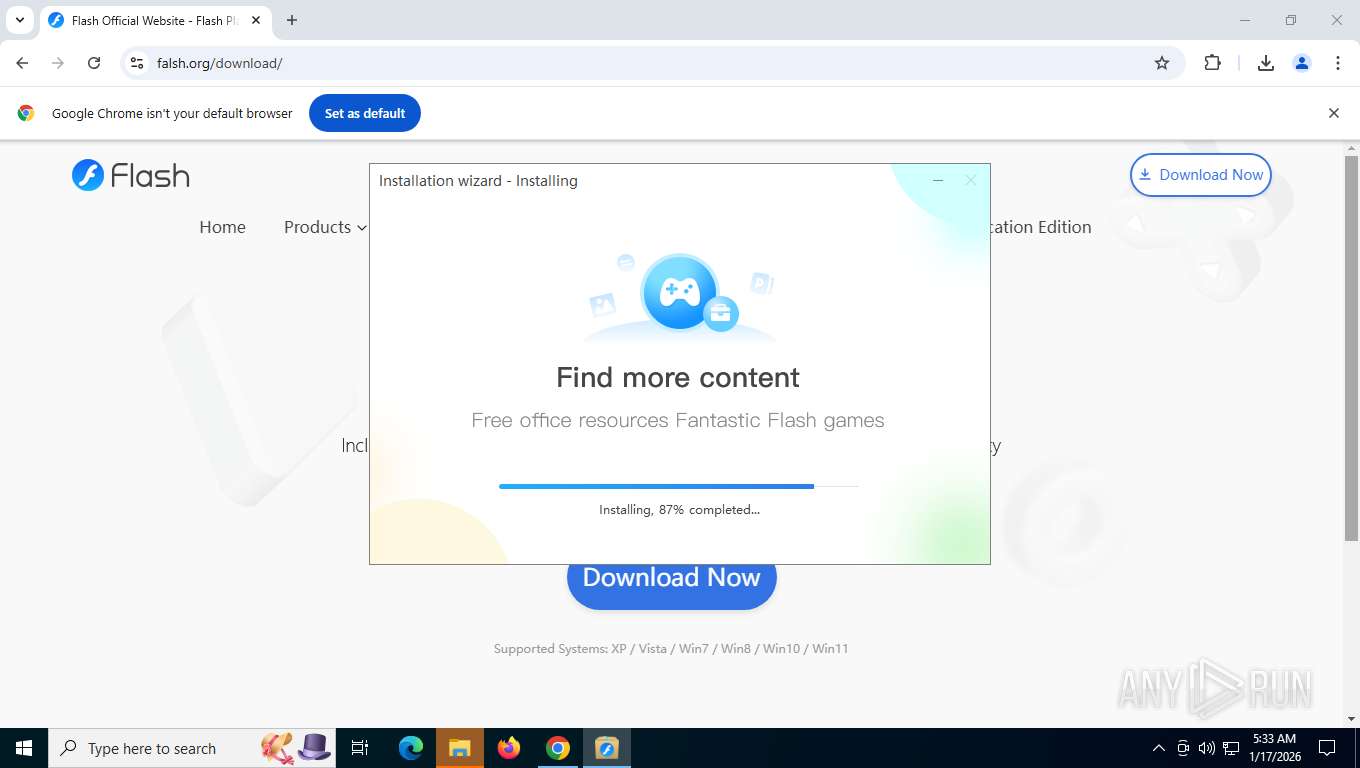
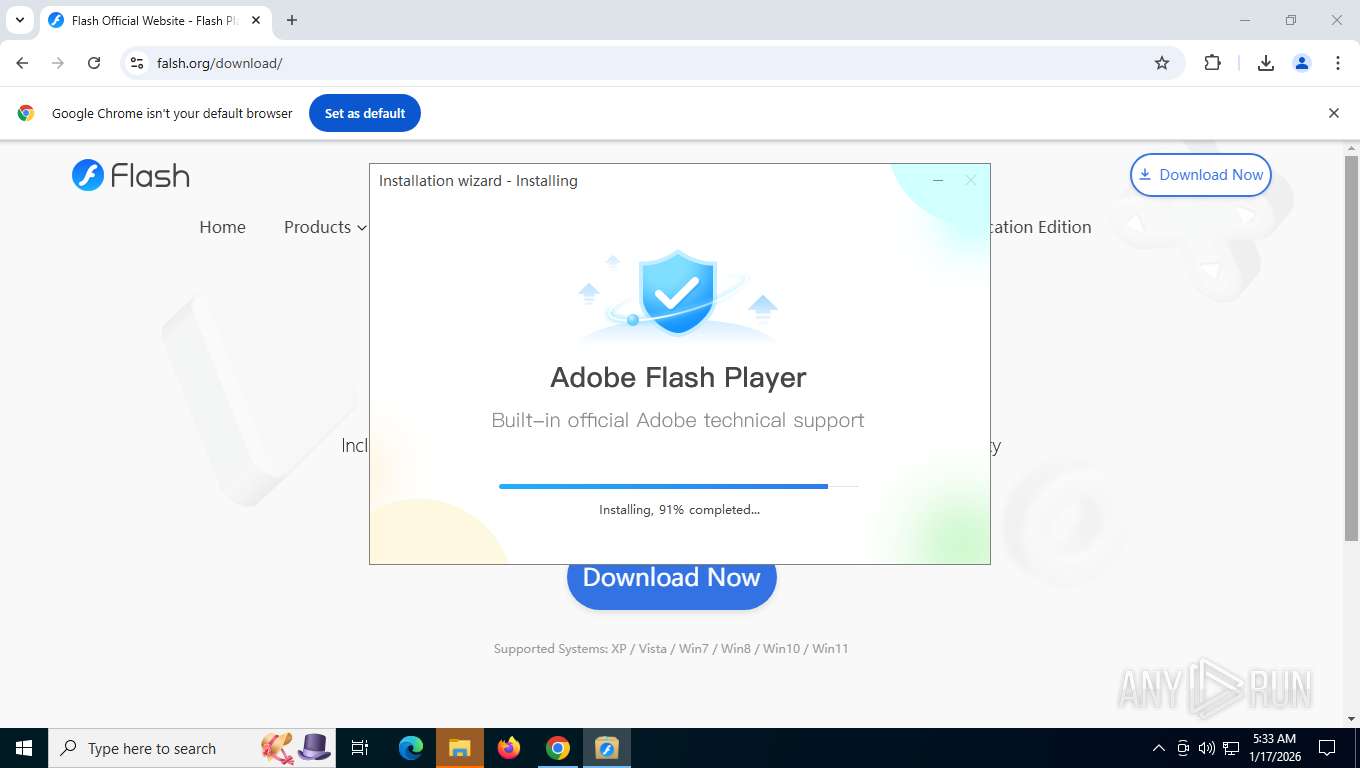
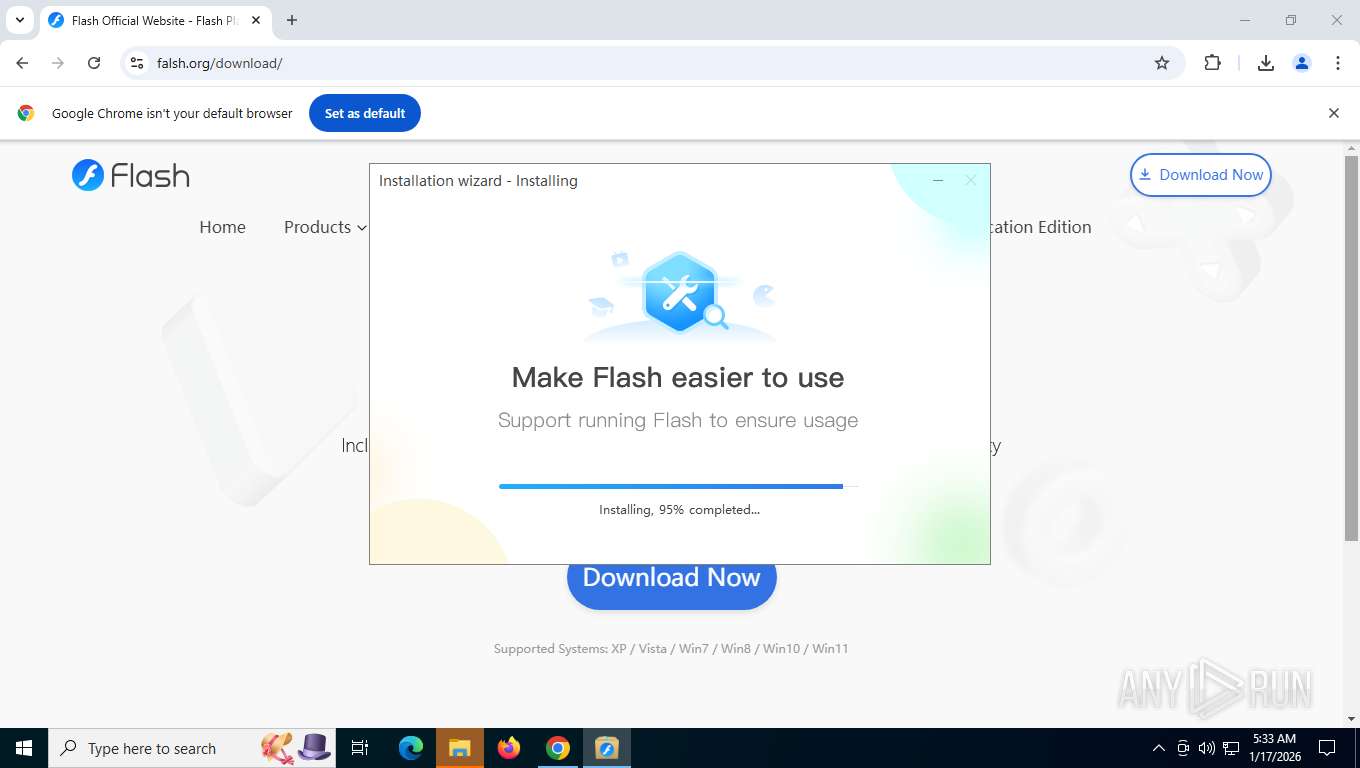
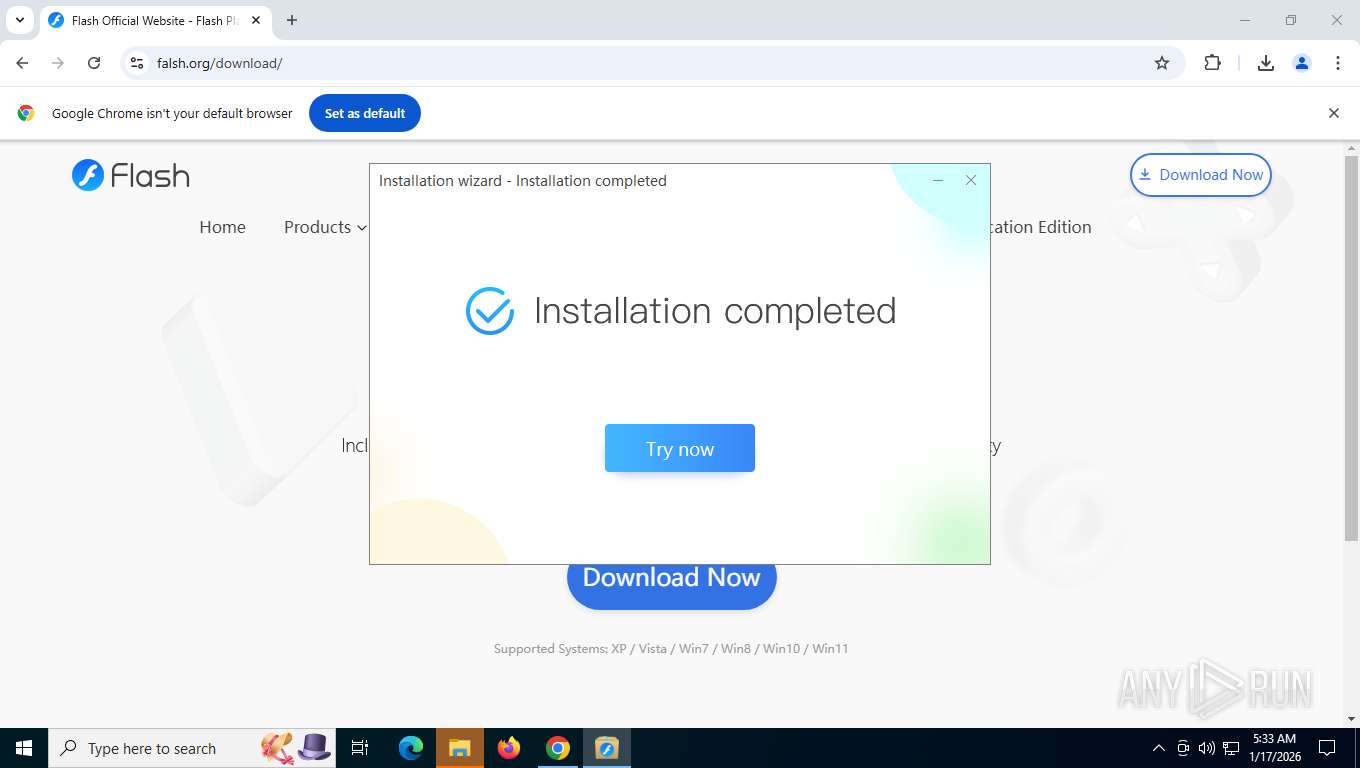
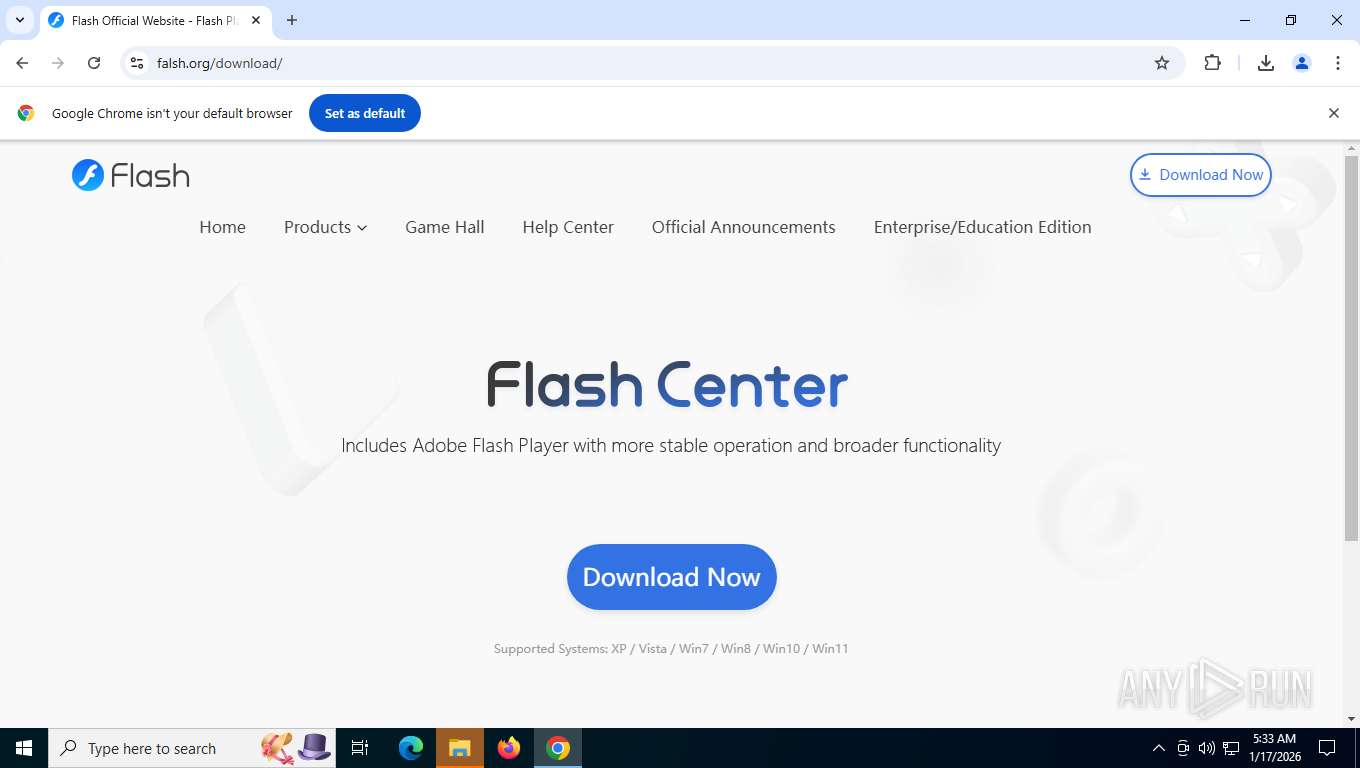
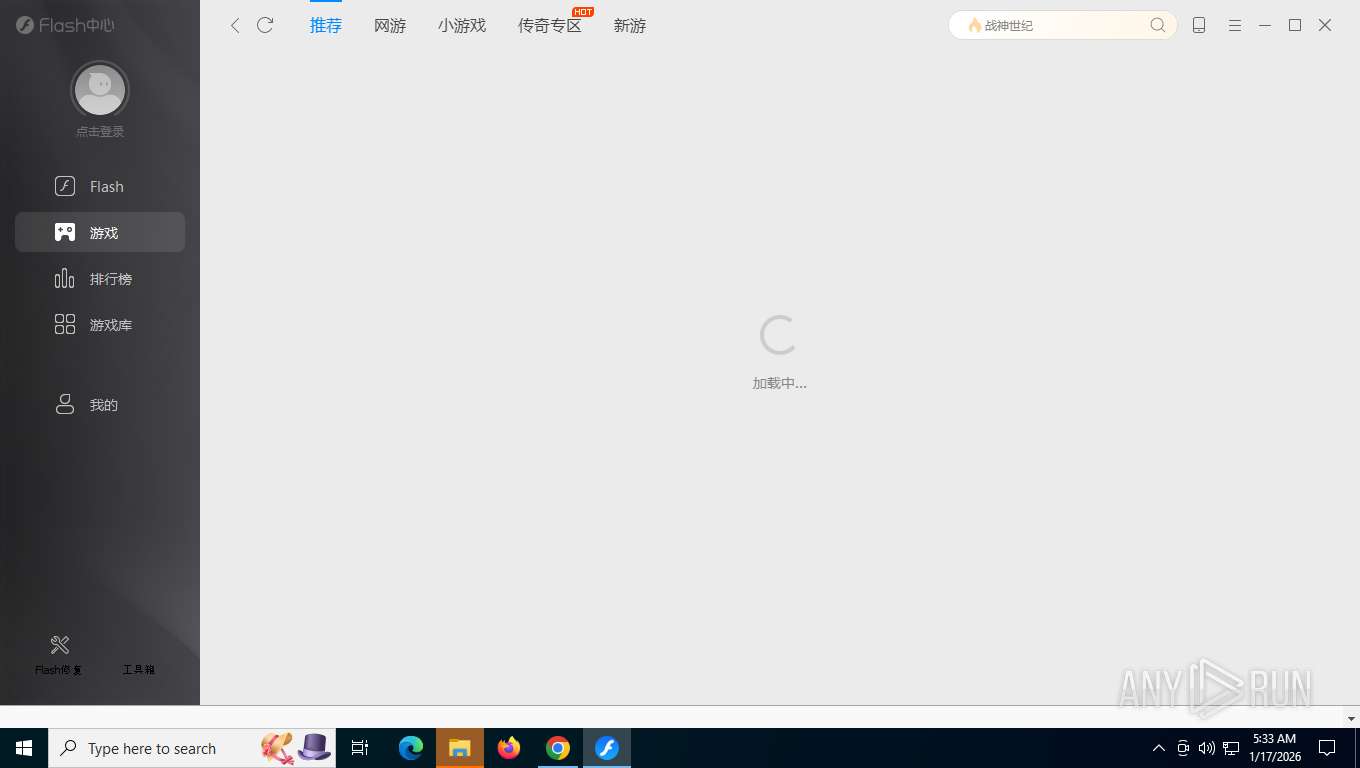
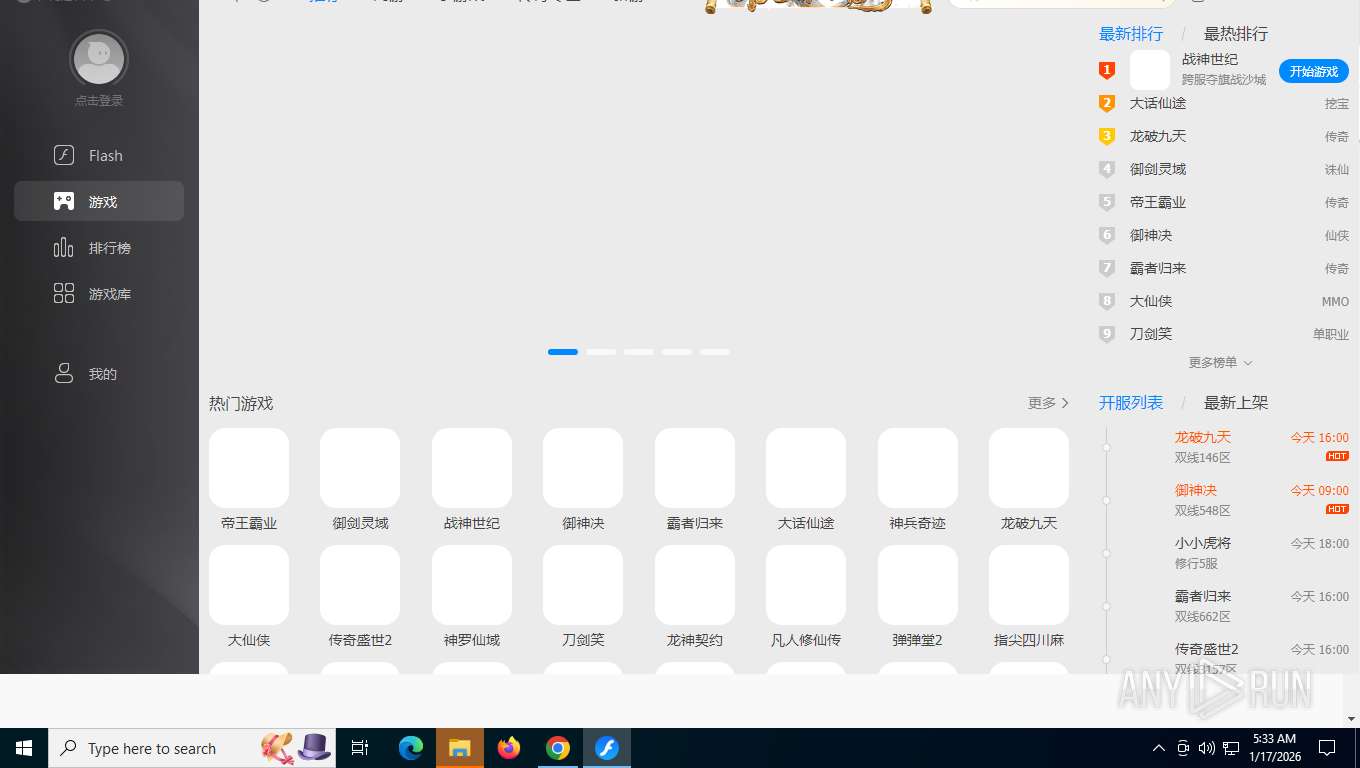
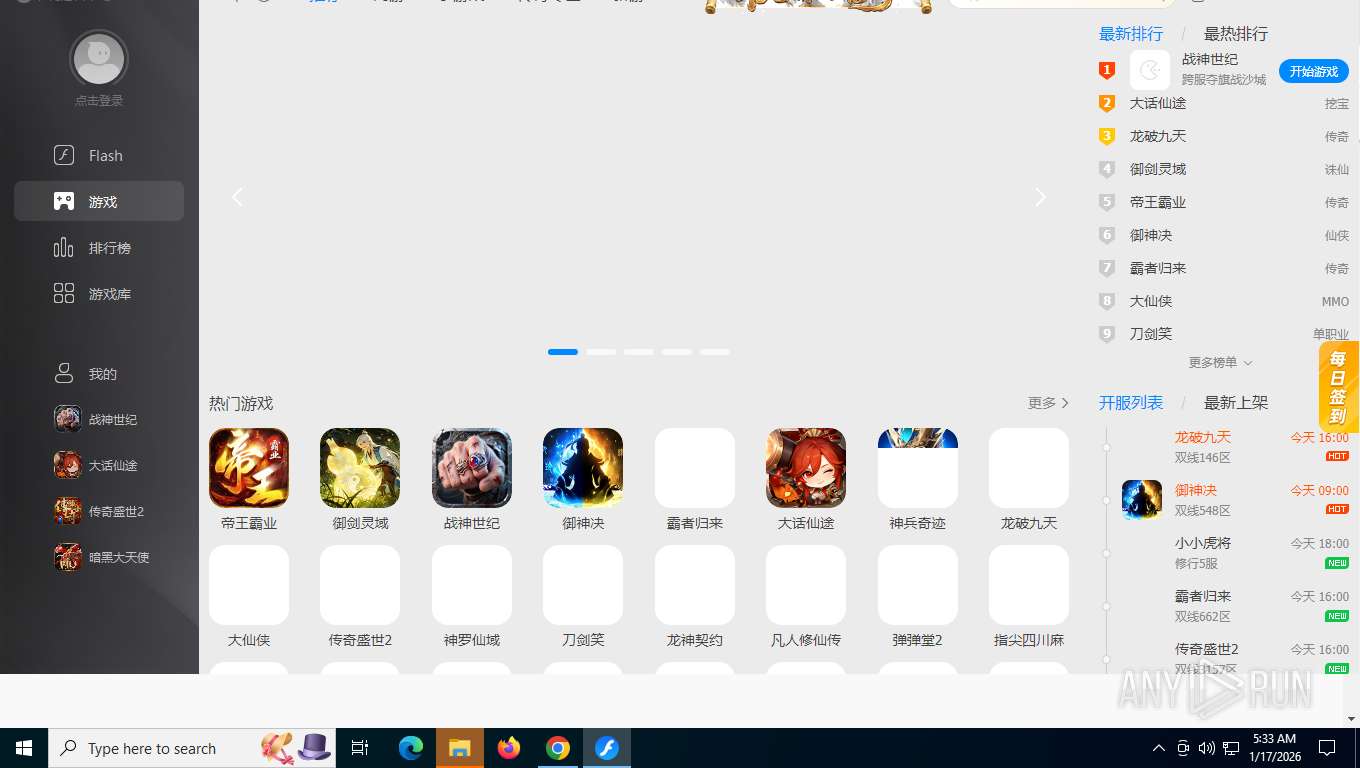
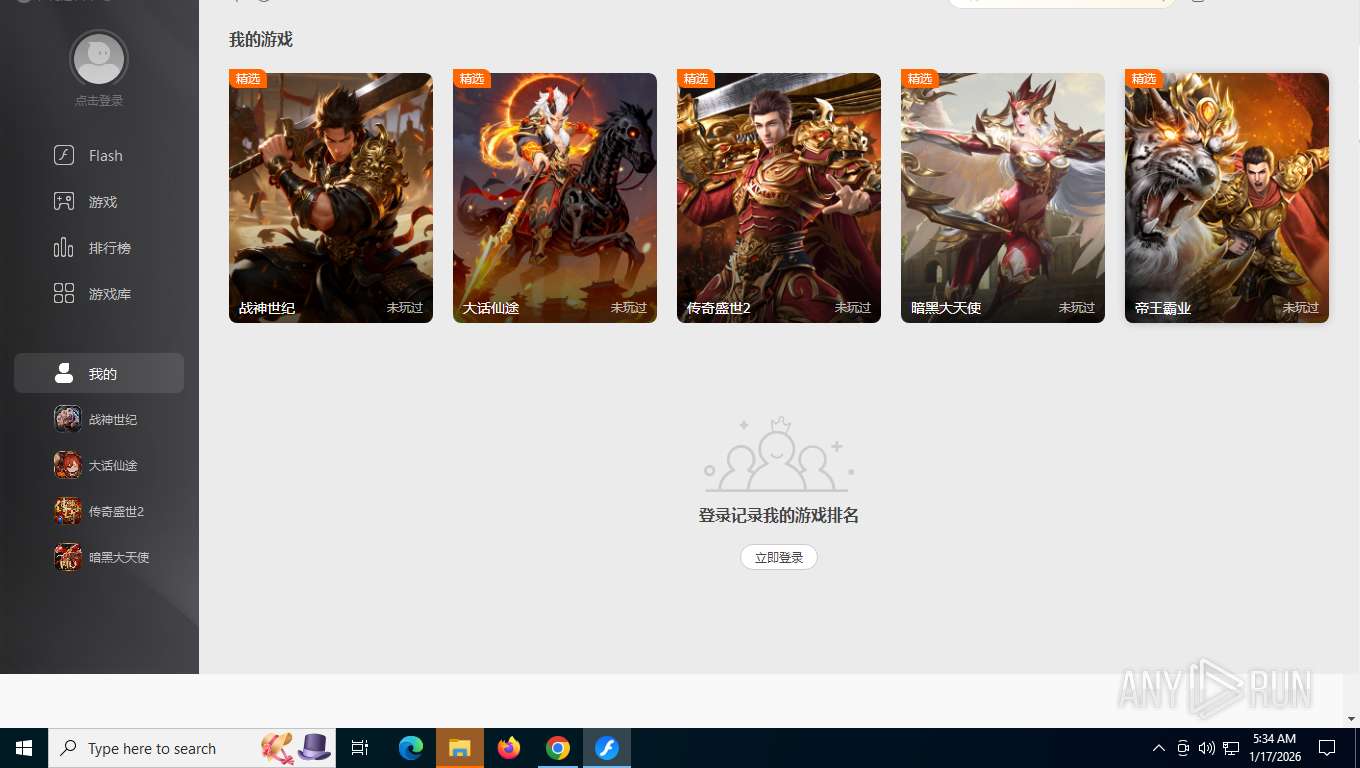
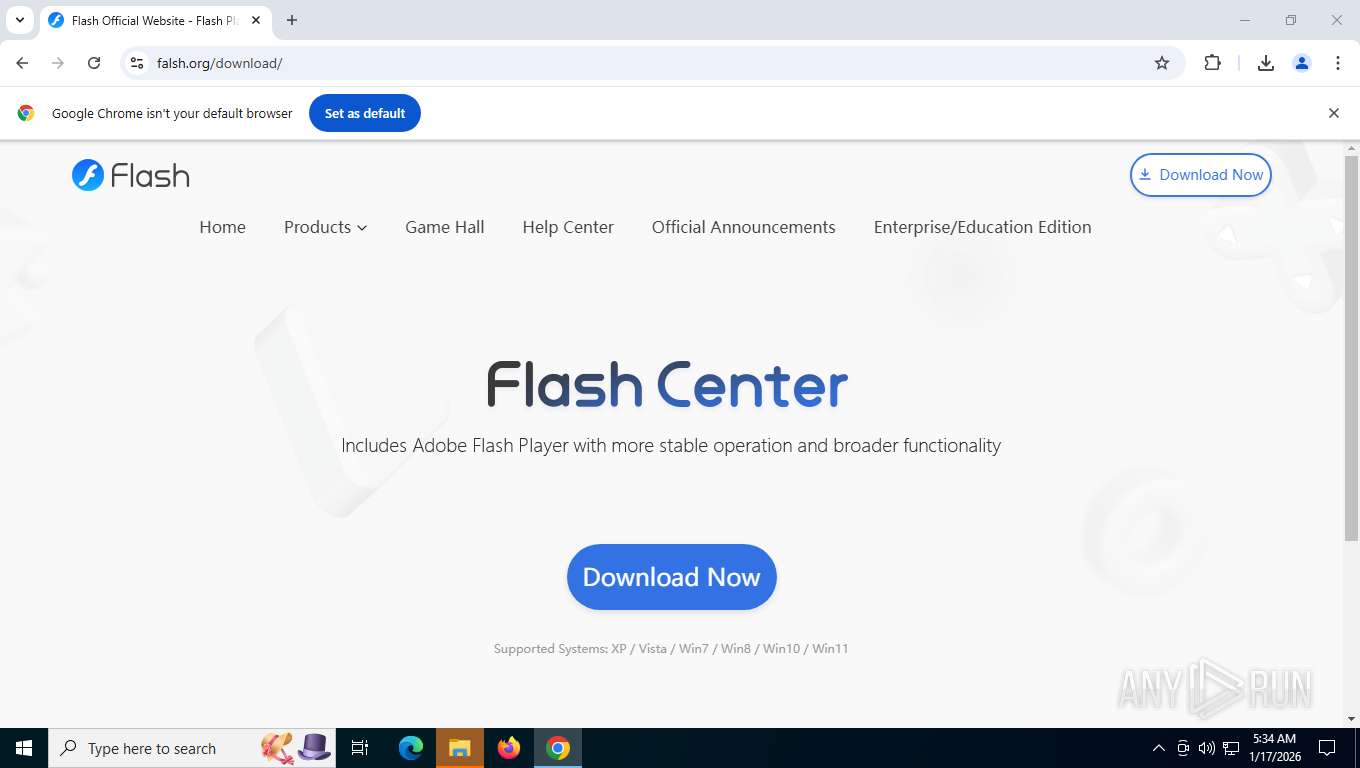
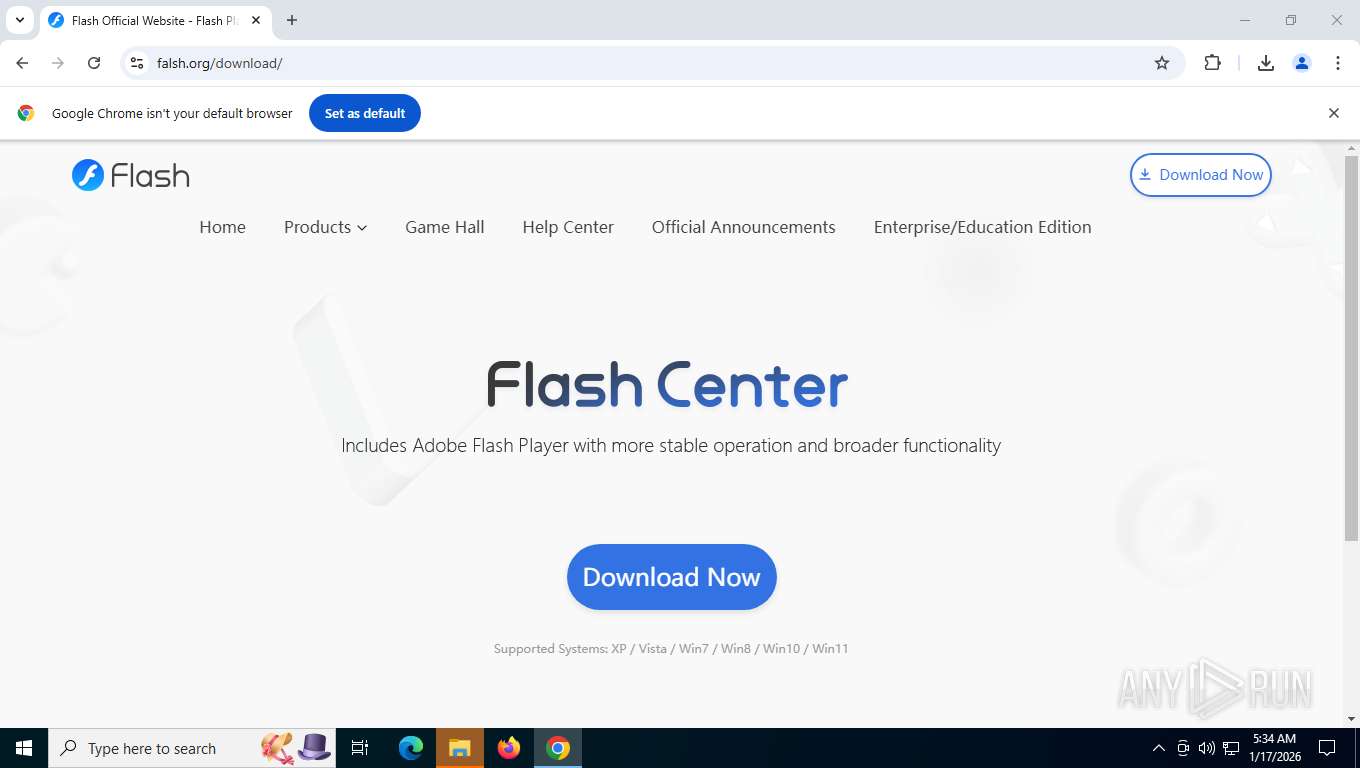
| URL: | falsh.org |
| Full analysis: | https://app.any.run/tasks/29a80357-0f3d-46ba-b3dc-d07a758e66b4 |
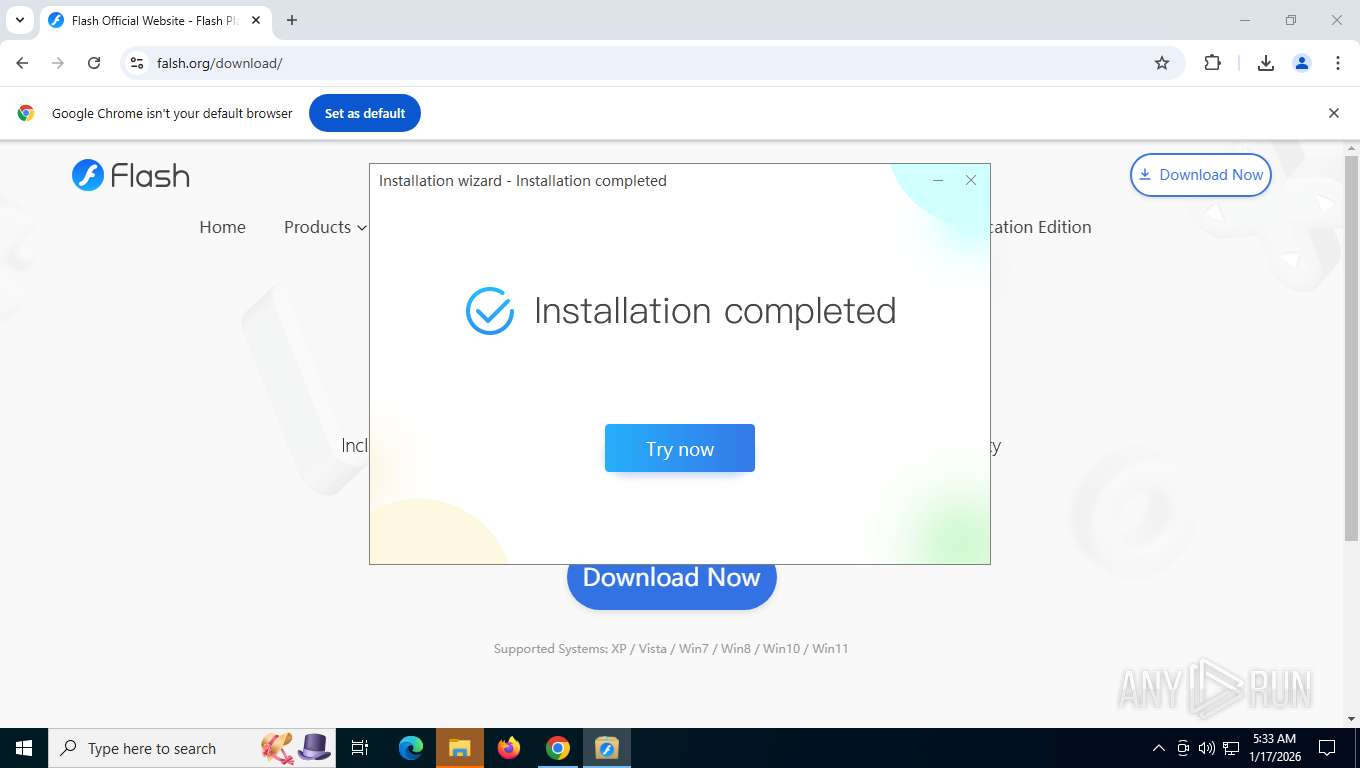
| Verdict: | Malicious activity |
| Threats: | Cobalt Strike is a legitimate penetration software toolkit developed by Forta. But its cracked versions are widely adopted by bad actors, who use it as a C2 system of choice for targeted attacks. |
| Analysis date: | January 17, 2026, 10:31:08 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 7723FC28DD8785773986355B93FAA2B7 |
| SHA1: | 5217B2F235FDAF5C79DEAC20ED2F66770BAA88C8 |
| SHA256: | 198E6BB37288C2ECACD64E4F6E93EDCF6B937AAB7B2678F49C3E6555F1ADEBFE |
| SSDEEP: | 3:lLMC:2C |
MALICIOUS
PHISHING has been detected (SURICATA)
- chrome.exe (PID: 7860)
Changes settings of System certificates
- flash.exe (PID: 1088)
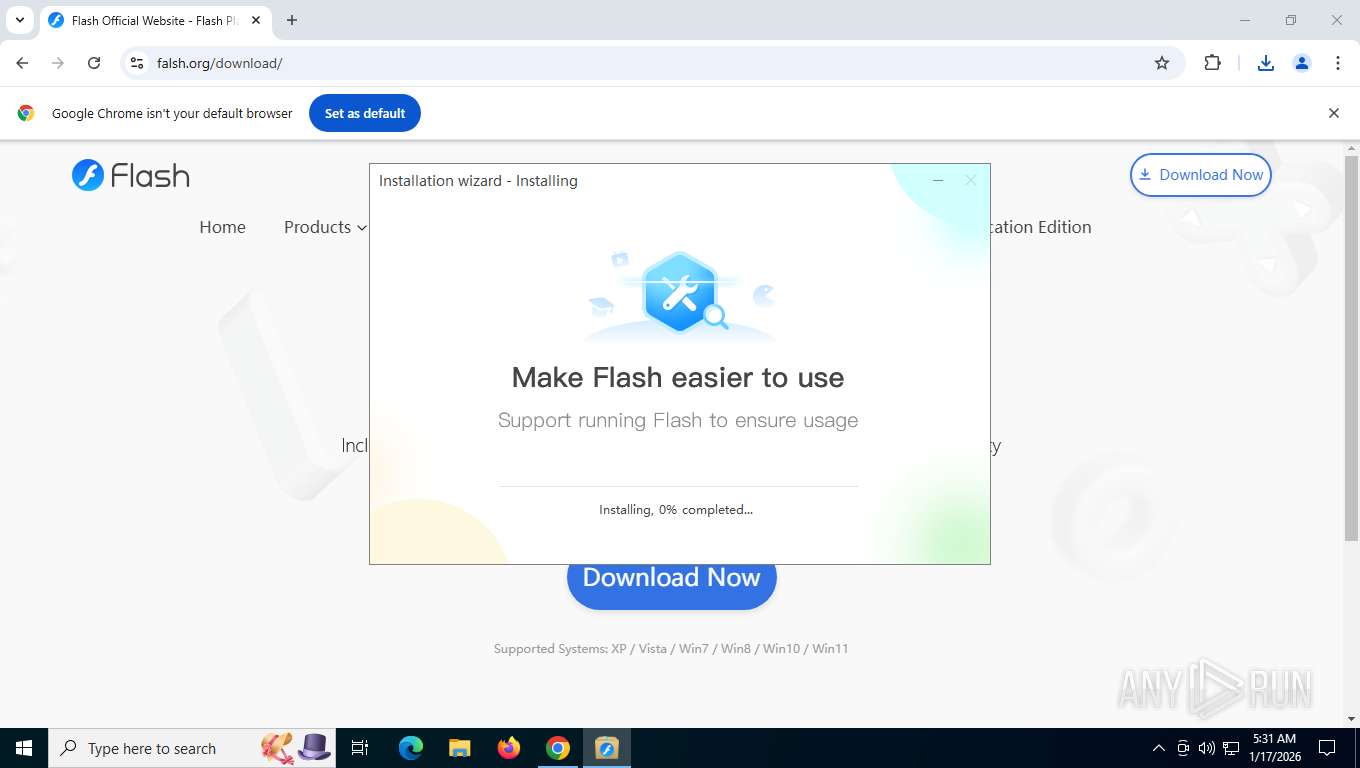
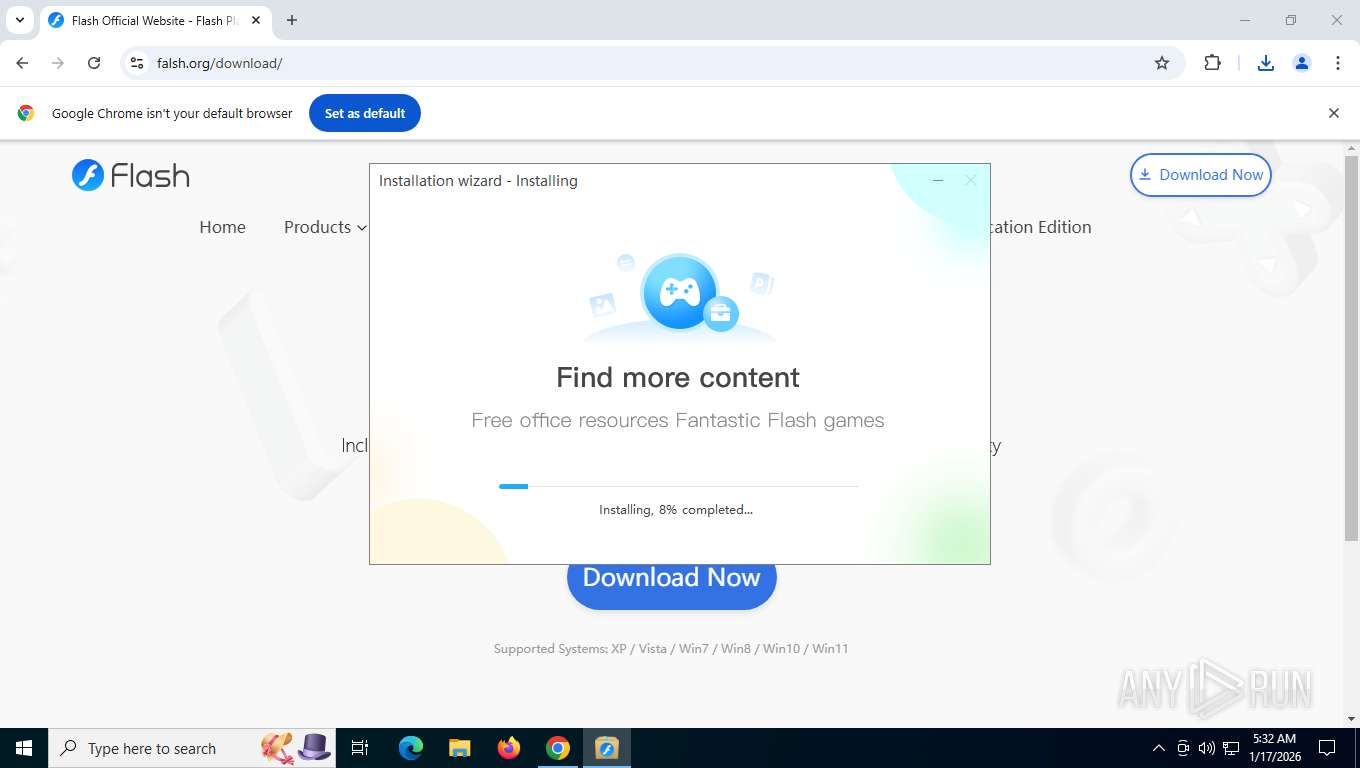
COBALTSTRIKE has been detected (YARA)
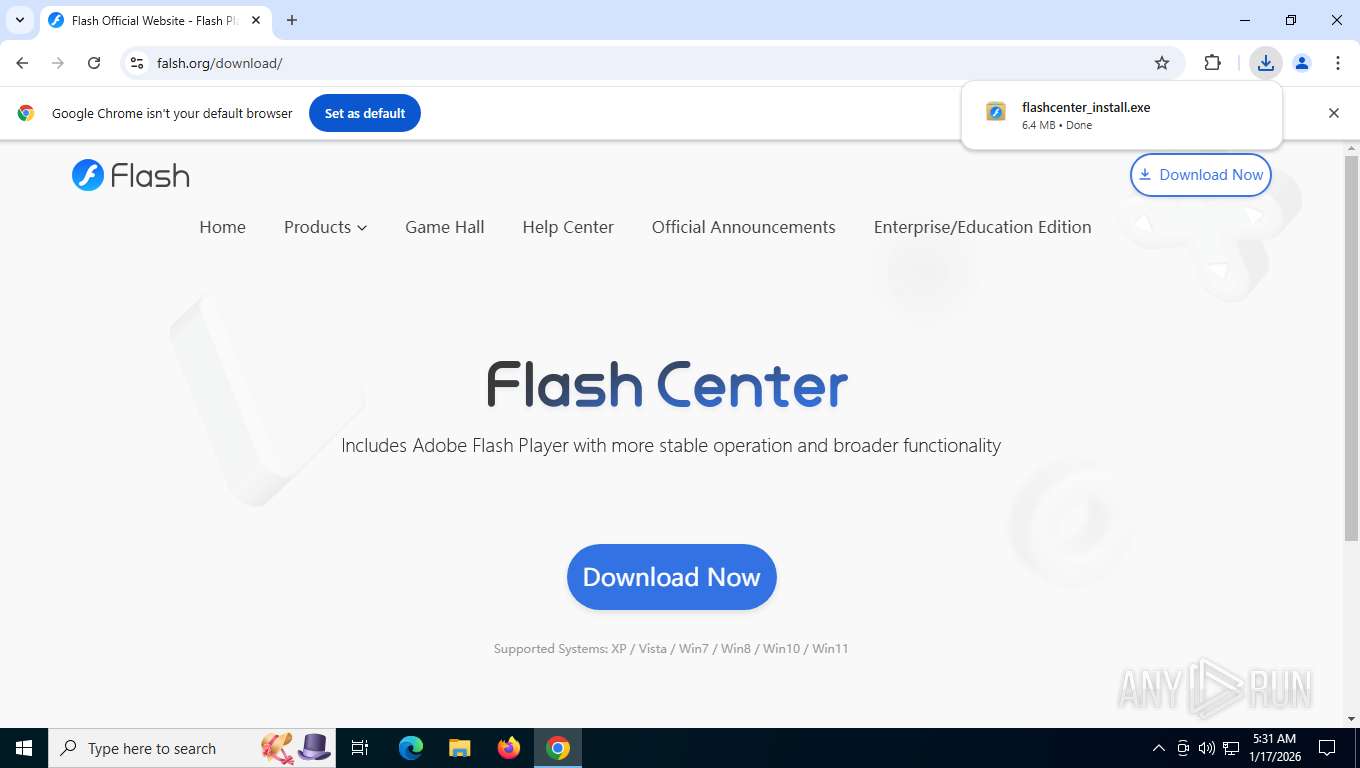
- flashcenter_install.exe (PID: 8148)
- copy.exe (PID: 3380)
SUSPICIOUS
Likely accesses (executes) a file from the Public directory
- flash.exe (PID: 4864)
- copy.exe (PID: 3380)
- flash.exe (PID: 1088)
Executable content was dropped or overwritten
- flashcenter_install.exe (PID: 8148)
- flash.exe (PID: 4864)
- 2DD5FDE0-0B2E-416E-A9DB-69E1DE8D34E7 (PID: 2144)
- 4F23E4DF-7FE9-4BF0-BE1E-6A42023ED049 (PID: 2424)
- InstallFlashPlayer.exe (PID: 7072)
- 9EAE2BD9-AAA9-4CAE-A4EB-789D2F55BC14 (PID: 5104)
- InstallFlashPlayer.exe (PID: 4508)
- InstallFlashPlayer.exe (PID: 6096)
- flash.exe (PID: 1088)
Starts itself from another location
- flashcenter_install.exe (PID: 8148)
Reads security settings of Internet Explorer
- flash.exe (PID: 4864)
- flashcenter_install.exe (PID: 8148)
- copy.exe (PID: 3380)
- flash.exe (PID: 1088)
- 2DD5FDE0-0B2E-416E-A9DB-69E1DE8D34E7 (PID: 2144)
- 4F23E4DF-7FE9-4BF0-BE1E-6A42023ED049 (PID: 2424)
- InstallFlashPlayer.exe (PID: 7072)
- 9EAE2BD9-AAA9-4CAE-A4EB-789D2F55BC14 (PID: 5104)
- InstallFlashPlayer.exe (PID: 4508)
- InstallFlashPlayer.exe (PID: 6096)
- FlashCenterSvc.exe (PID: 5448)
- FlashHelperService.exe (PID: 7460)
- FlashCenter.exe (PID: 3332)
Application launched itself
- flash.exe (PID: 4864)
- FCBrowser.exe (PID: 3344)
Reads Microsoft Outlook installation path
- flash.exe (PID: 4864)
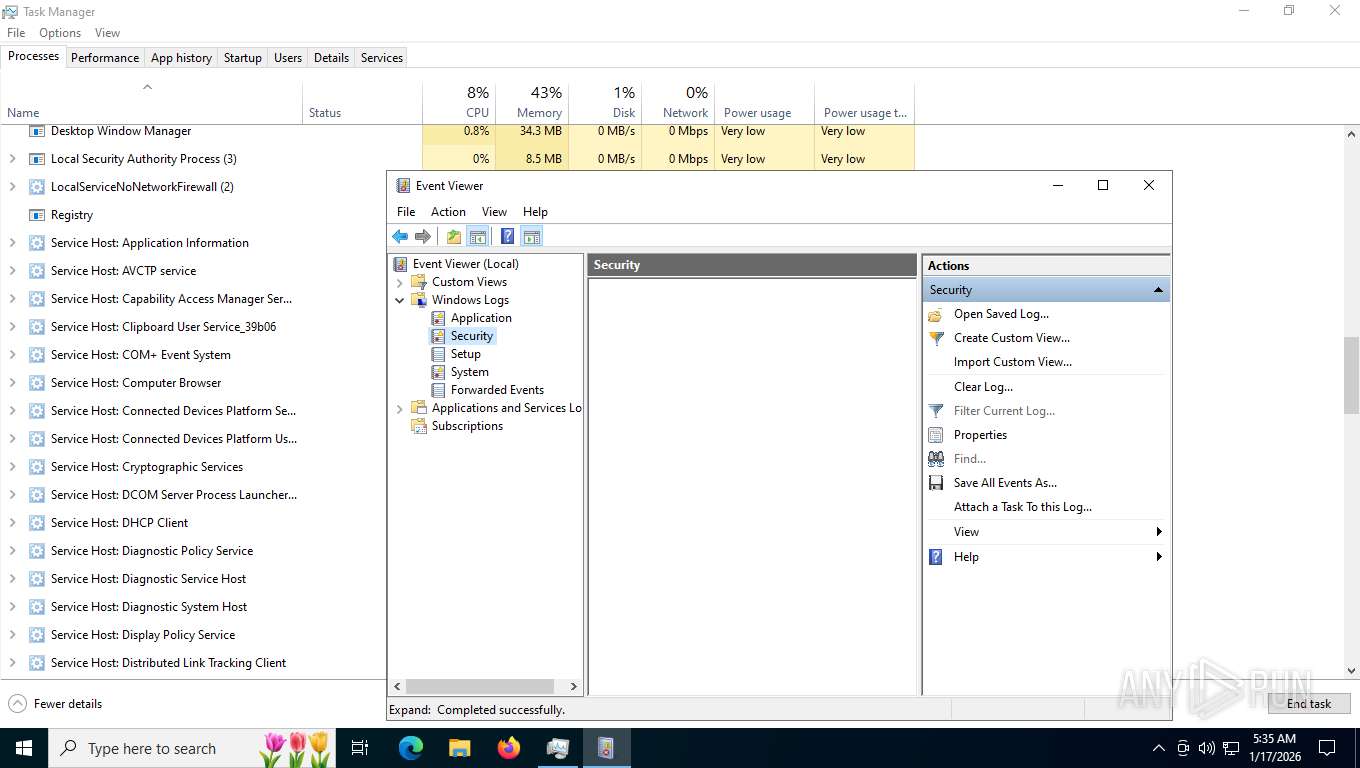
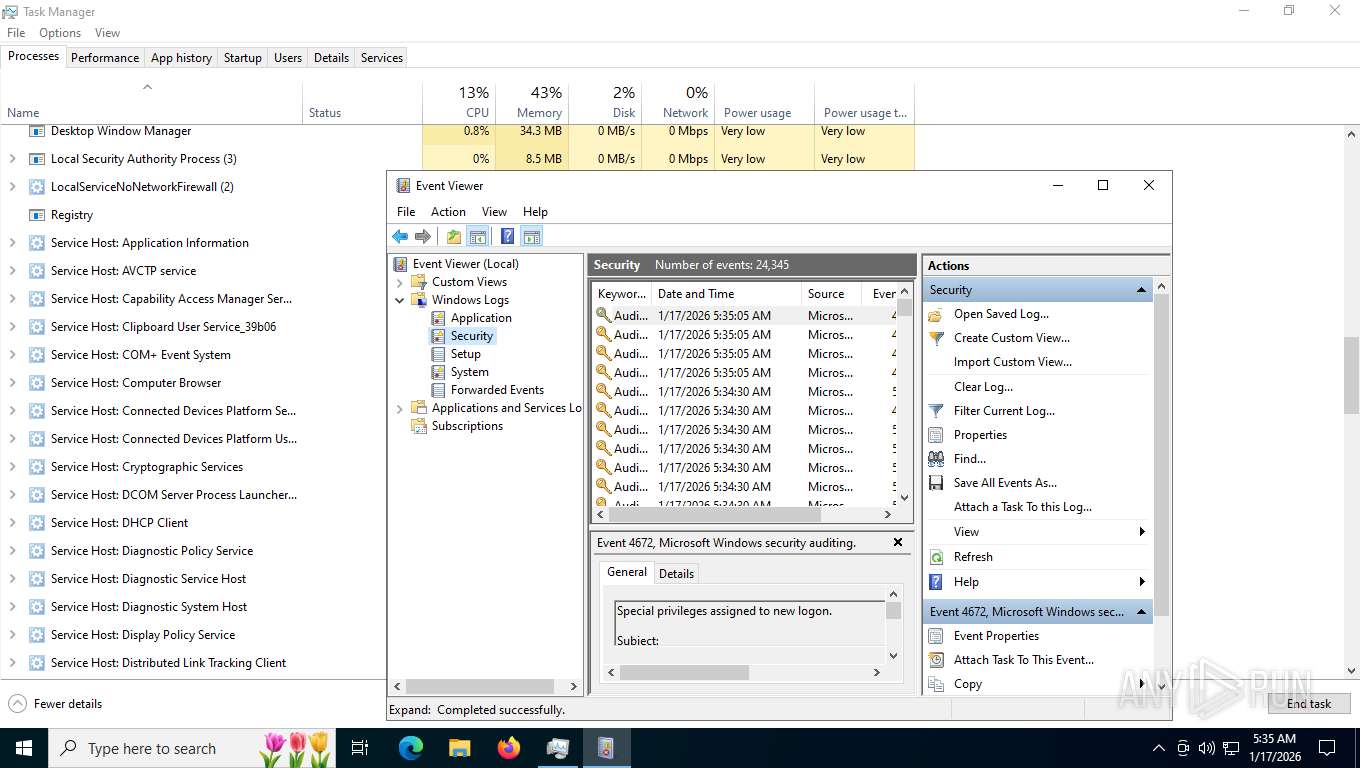
Reads Internet Explorer settings
- flash.exe (PID: 4864)
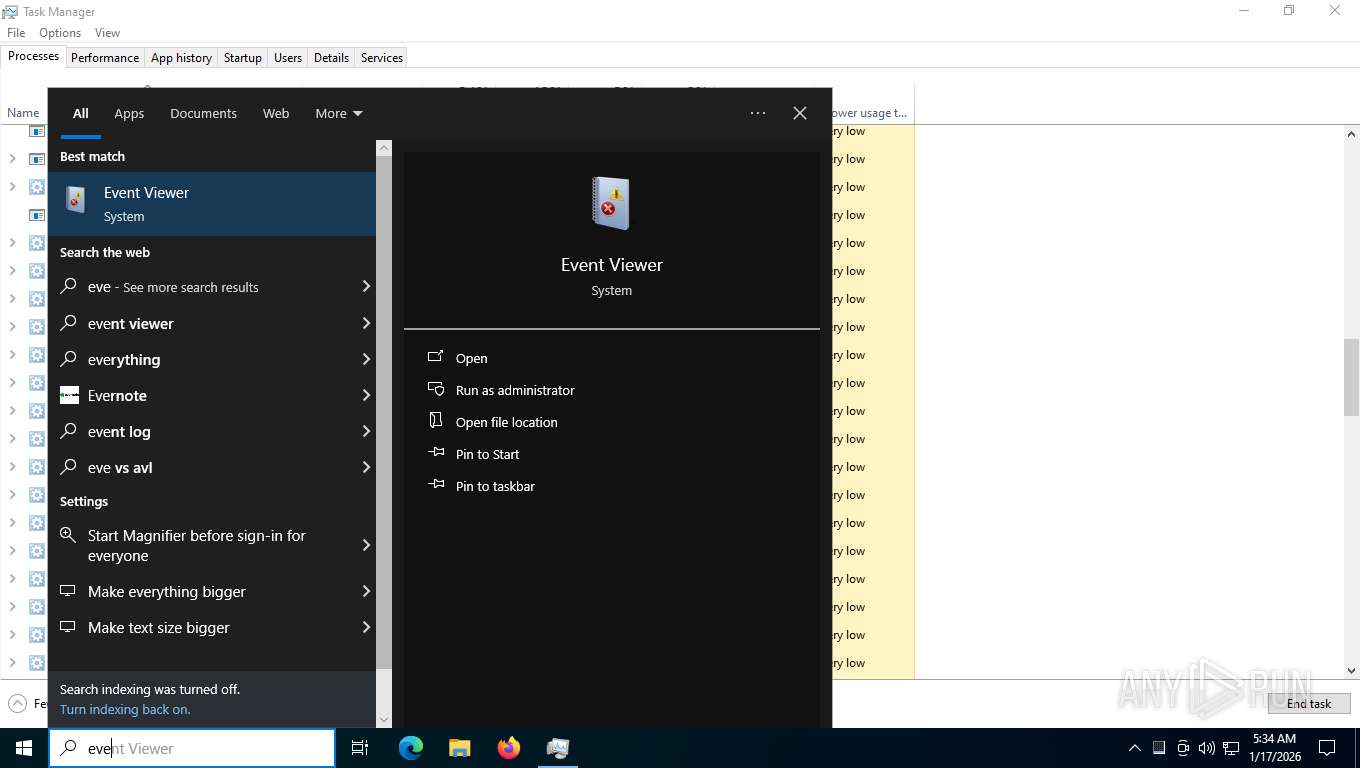
- mmc.exe (PID: 2684)
Connects to unusual port
- copy.exe (PID: 3380)
- flashcenter_install.exe (PID: 8148)
Adds/modifies Windows certificates
- flash.exe (PID: 1088)
Malware-specific behavior (creating "System.dll" in Temp)
- 2DD5FDE0-0B2E-416E-A9DB-69E1DE8D34E7 (PID: 2144)
Starts application with an unusual extension
- flash.exe (PID: 1088)
The process creates files with name similar to system file names
- 2DD5FDE0-0B2E-416E-A9DB-69E1DE8D34E7 (PID: 2144)
- FCBrowser.exe (PID: 3344)
Reads the date of Windows installation
- 2DD5FDE0-0B2E-416E-A9DB-69E1DE8D34E7 (PID: 2144)
- InstallFlashPlayer.exe (PID: 7072)
- InstallFlashPlayer.exe (PID: 6096)
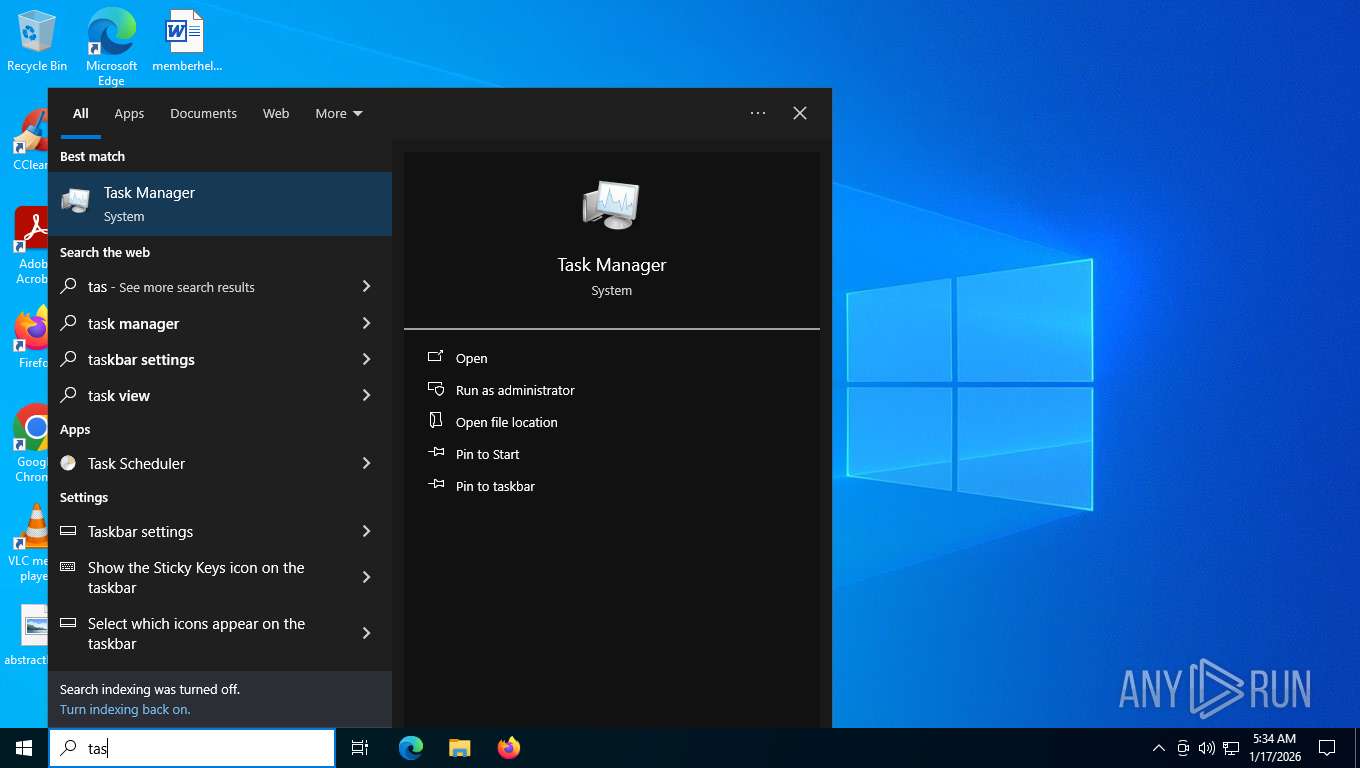
Uses TASKKILL.EXE to kill process
- 2DD5FDE0-0B2E-416E-A9DB-69E1DE8D34E7 (PID: 2144)
Drops 7-zip archiver for unpacking
- 2DD5FDE0-0B2E-416E-A9DB-69E1DE8D34E7 (PID: 2144)
Process drops legitimate windows executable
- 2DD5FDE0-0B2E-416E-A9DB-69E1DE8D34E7 (PID: 2144)
The process drops C-runtime libraries
- 2DD5FDE0-0B2E-416E-A9DB-69E1DE8D34E7 (PID: 2144)
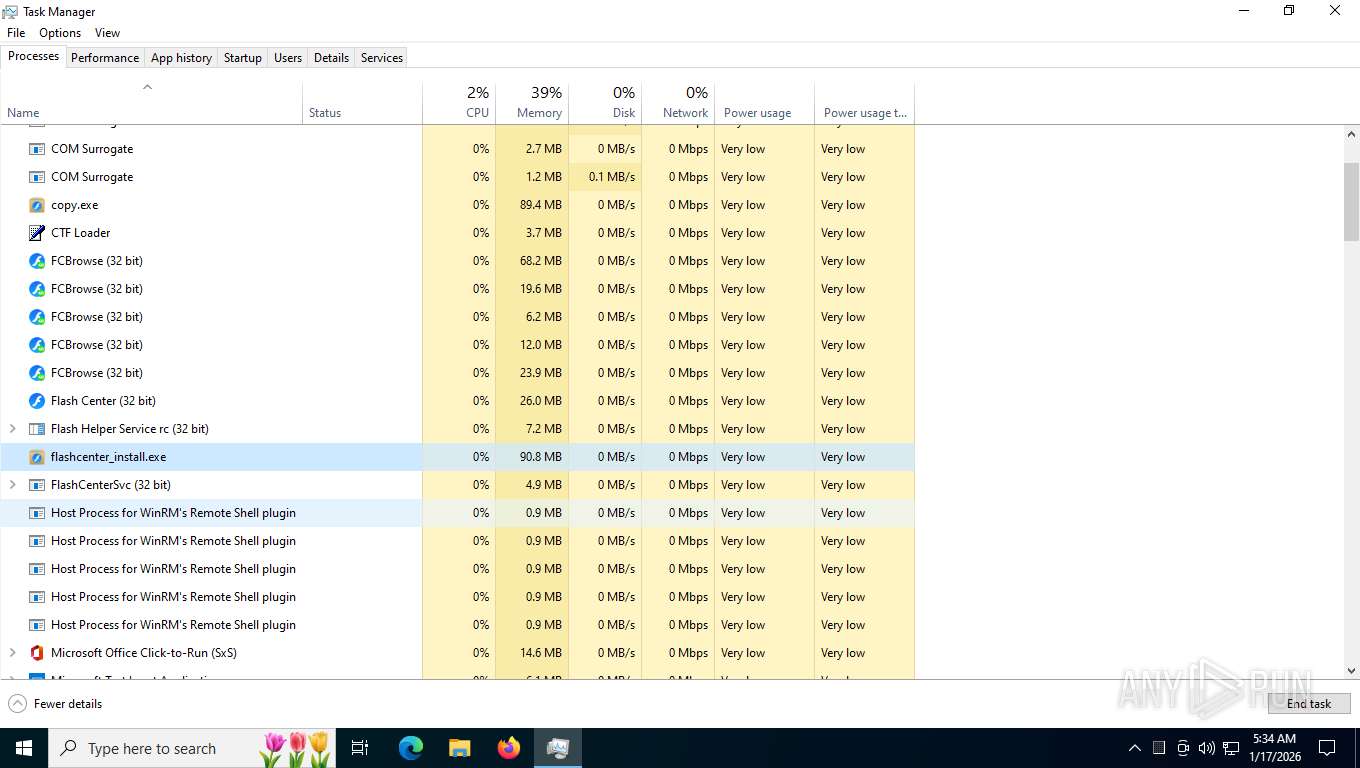
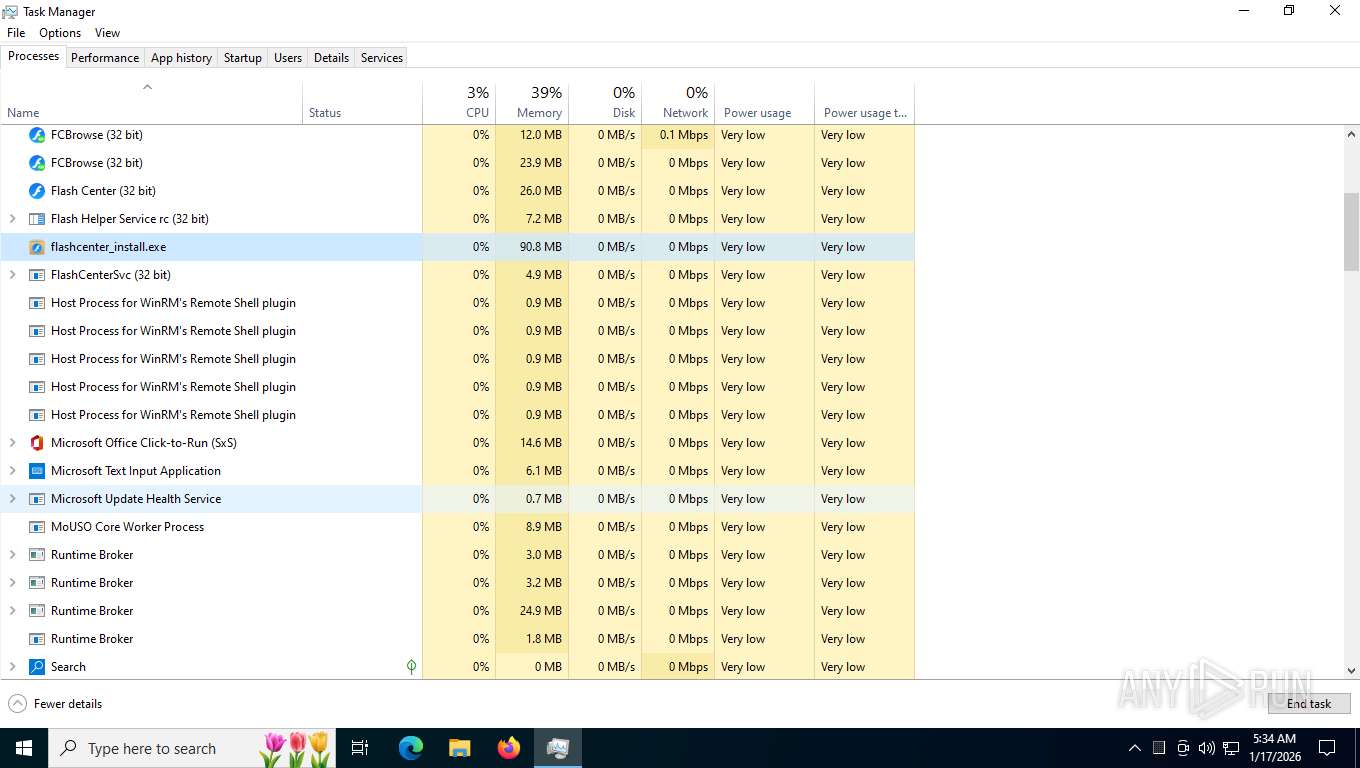
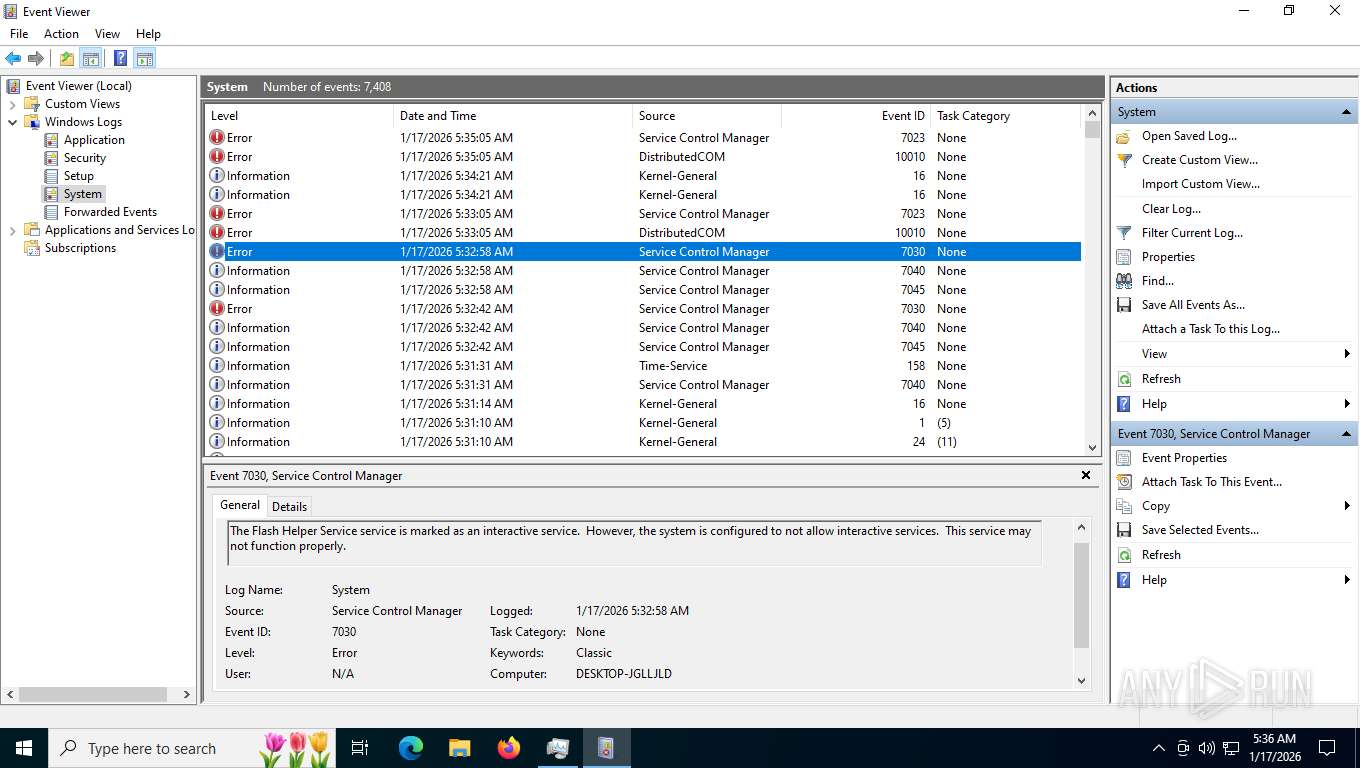
Executes as Windows Service
- FlashCenterSvc.exe (PID: 5448)
- FlashHelperService.exe (PID: 7460)
Disables SEHOP
- InstallFlashPlayer.exe (PID: 7072)
- 4F23E4DF-7FE9-4BF0-BE1E-6A42023ED049 (PID: 2424)
- InstallFlashPlayer.exe (PID: 4508)
- InstallFlashPlayer.exe (PID: 6096)
Hides command output
- cmd.exe (PID: 2392)
- cmd.exe (PID: 8188)
- cmd.exe (PID: 1412)
- cmd.exe (PID: 7364)
- cmd.exe (PID: 1780)
Starts CMD.EXE for commands execution
- InstallFlashPlayer.exe (PID: 7072)
- 4F23E4DF-7FE9-4BF0-BE1E-6A42023ED049 (PID: 2424)
- InstallFlashPlayer.exe (PID: 6096)
- 9EAE2BD9-AAA9-4CAE-A4EB-789D2F55BC14 (PID: 5104)
- InstallFlashPlayer.exe (PID: 4508)
Creates/Modifies COM task schedule object
- InstallFlashPlayer.exe (PID: 6096)
- InstallFlashPlayer.exe (PID: 4508)
Searches for installed software
- flash.exe (PID: 4864)
- FlashCenterSvc.exe (PID: 5448)
- FlashHelperService.exe (PID: 7460)
There is functionality for taking screenshot (YARA)
- FCBrowser.exe (PID: 3344)
- FlashCenter.exe (PID: 3332)
- FCBrowser.exe (PID: 800)
- FCBrowser.exe (PID: 2228)
- FCBrowser.exe (PID: 3004)
INFO
Application launched itself
- chrome.exe (PID: 7592)
Drops script file
- chrome.exe (PID: 7592)
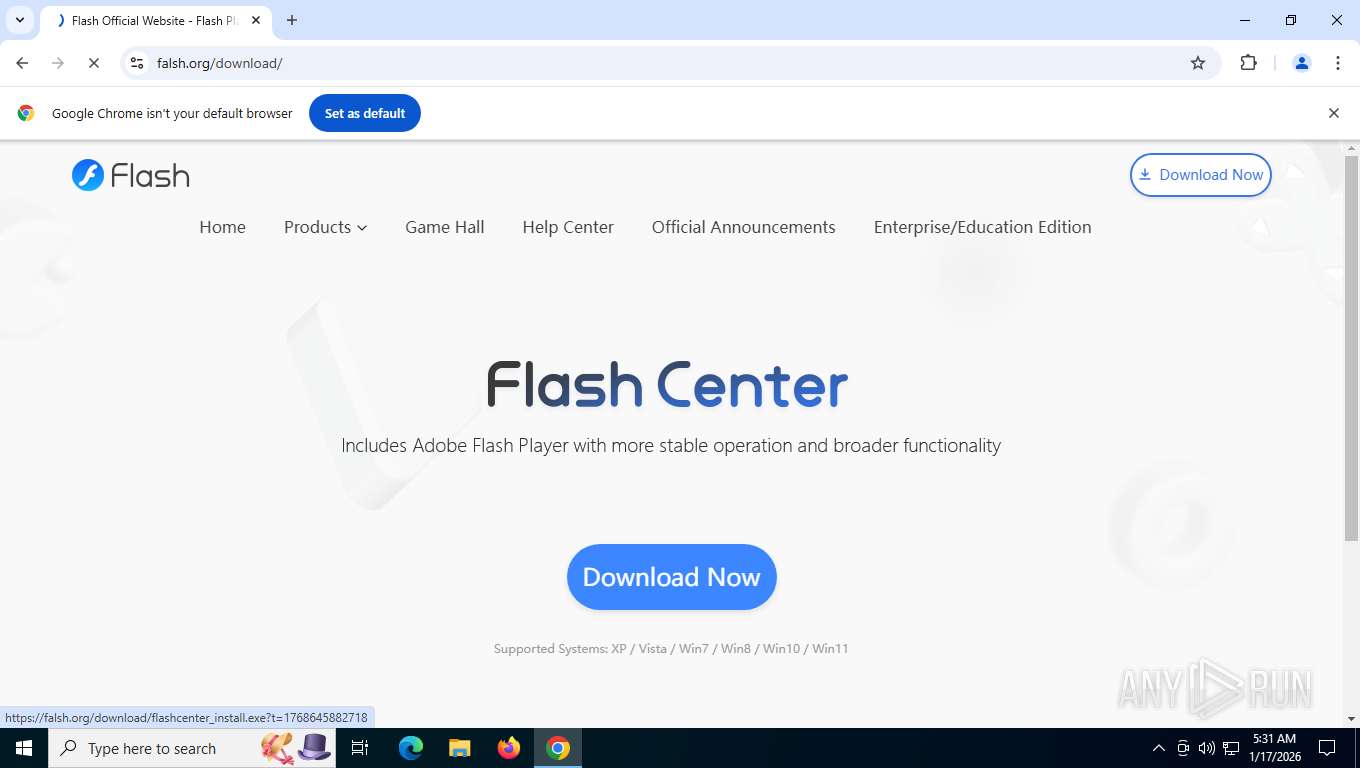
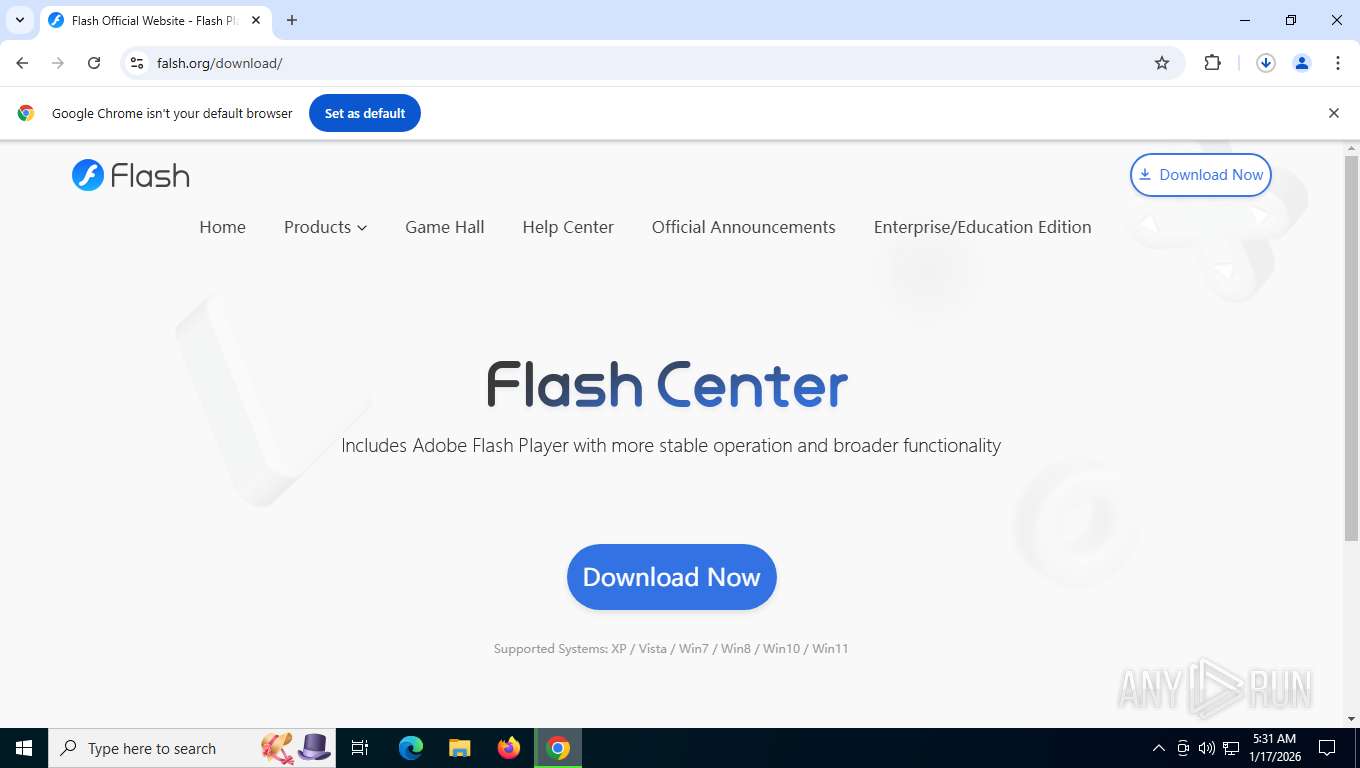
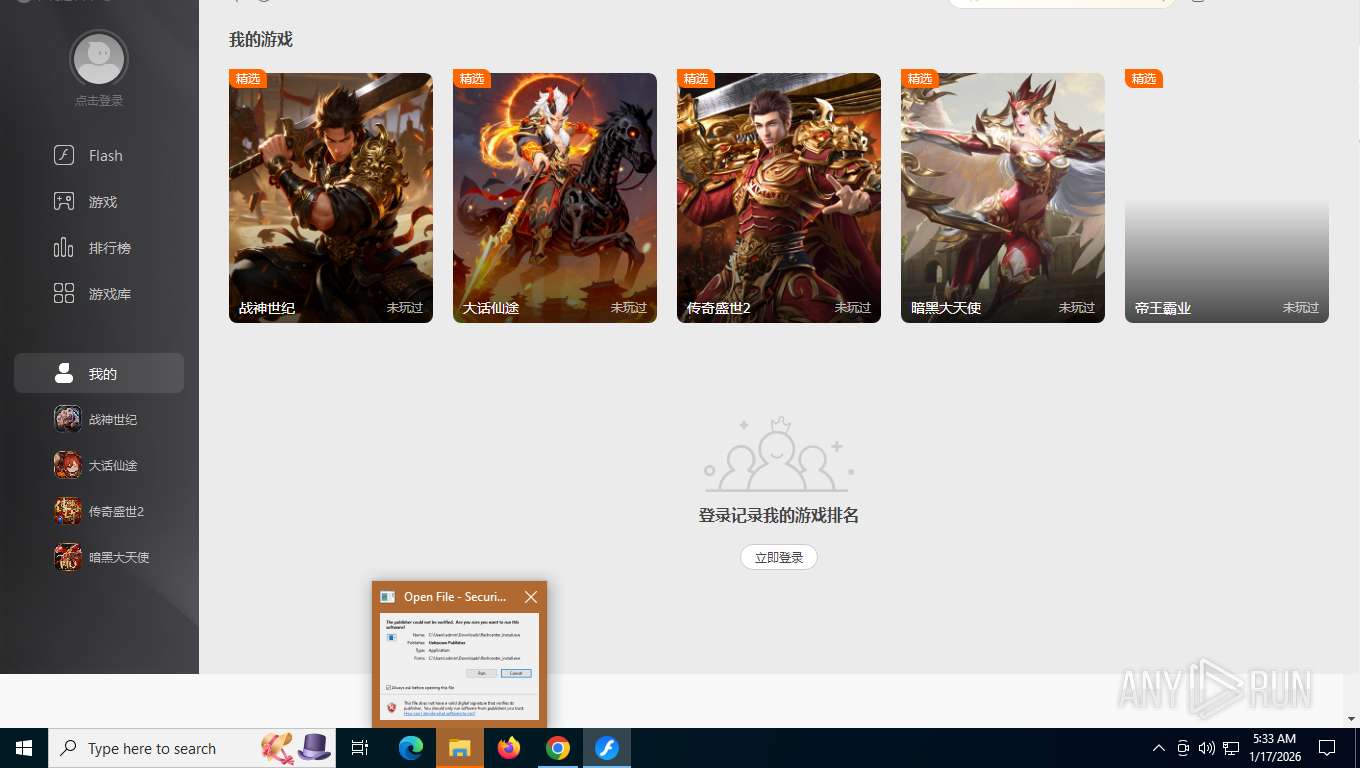
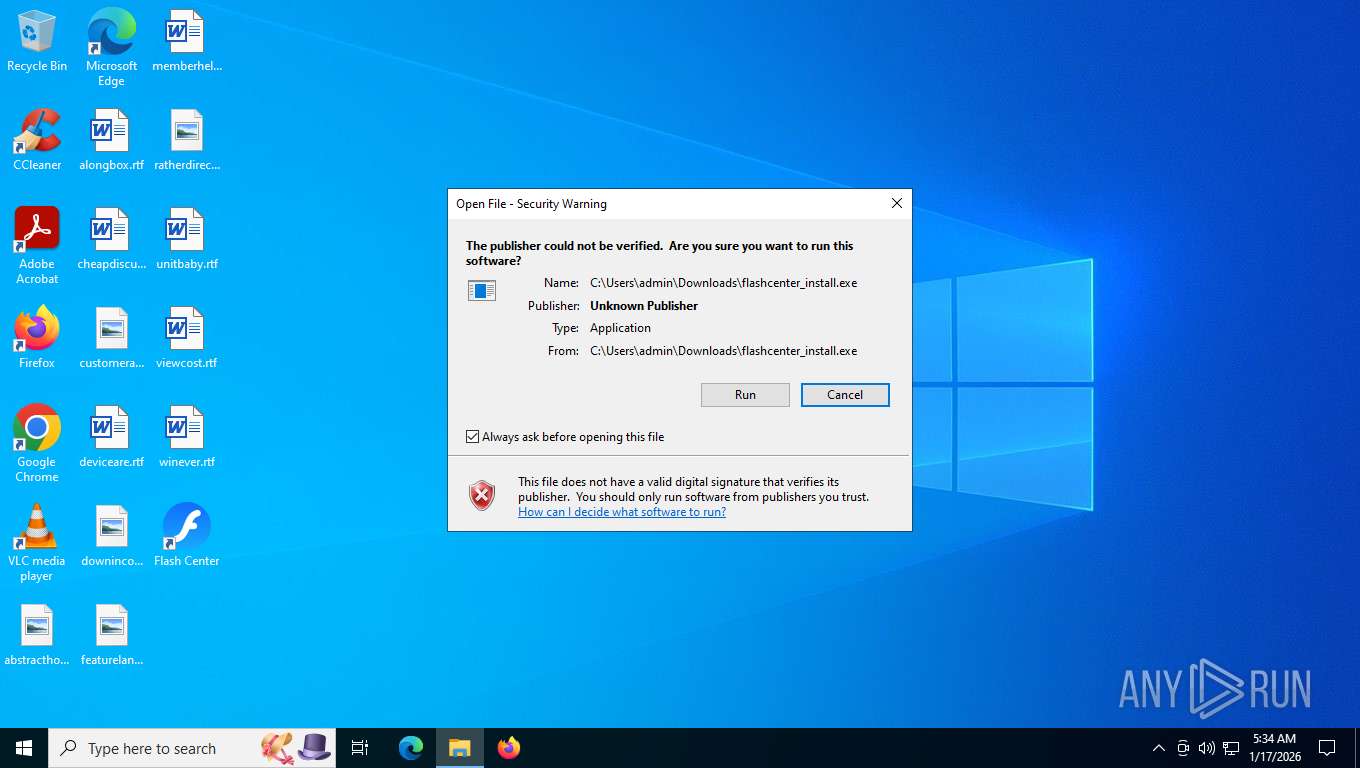
Launching a file from the Downloads directory
- chrome.exe (PID: 7592)
Executable content was dropped or overwritten
- chrome.exe (PID: 7592)
Reads the computer name
- flashcenter_install.exe (PID: 8148)
- flash.exe (PID: 4864)
- copy.exe (PID: 3380)
- flash.exe (PID: 1088)
- 2DD5FDE0-0B2E-416E-A9DB-69E1DE8D34E7 (PID: 2144)
- FlashCenterSvc.exe (PID: 6056)
- FlashCenterSvc.exe (PID: 5448)
- 4F23E4DF-7FE9-4BF0-BE1E-6A42023ED049 (PID: 2424)
- InstallFlashPlayer.exe (PID: 7072)
- FlashPlayerUpdateService.exe (PID: 5868)
- InstallFlashPlayer.exe (PID: 4508)
- 9EAE2BD9-AAA9-4CAE-A4EB-789D2F55BC14 (PID: 5104)
- InstallFlashPlayer.exe (PID: 6096)
- FlashHelperService.exe (PID: 7460)
- FlashHelperService.exe (PID: 6728)
- FlashCenter.exe (PID: 3332)
- FCLogin.exe (PID: 7232)
- FCBrowser.exe (PID: 3344)
- FCBrowser.exe (PID: 800)
- FCBrowser.exe (PID: 3004)
- FCBrowser.exe (PID: 4332)
- TextInputHost.exe (PID: 7356)
- FCBrowser.exe (PID: 8024)
Checks supported languages
- flashcenter_install.exe (PID: 8148)
- flash.exe (PID: 4864)
- copy.exe (PID: 3380)
- flash.exe (PID: 1088)
- 2DD5FDE0-0B2E-416E-A9DB-69E1DE8D34E7 (PID: 2144)
- FlashCenterSvc.exe (PID: 6056)
- FlashCenterSvc.exe (PID: 5448)
- 4F23E4DF-7FE9-4BF0-BE1E-6A42023ED049 (PID: 2424)
- InstallFlashPlayer.exe (PID: 7072)
- 9EAE2BD9-AAA9-4CAE-A4EB-789D2F55BC14 (PID: 5104)
- FlashPlayerUpdateService.exe (PID: 5868)
- InstallFlashPlayer.exe (PID: 4508)
- InstallFlashPlayer.exe (PID: 6096)
- FlashHelperService.exe (PID: 6728)
- FlashHelperService.exe (PID: 7460)
- FlashCenter.exe (PID: 3332)
- FCBrowser.exe (PID: 3344)
- FCLogin.exe (PID: 7232)
- FCBrowser.exe (PID: 3004)
- FCBrowser.exe (PID: 800)
- FCBrowser.exe (PID: 4332)
- TextInputHost.exe (PID: 7356)
- FCBrowser.exe (PID: 2228)
- FCBrowser.exe (PID: 8024)
Reads the machine GUID from the registry
- flashcenter_install.exe (PID: 8148)
- copy.exe (PID: 3380)
- flash.exe (PID: 1088)
- flash.exe (PID: 4864)
- 2DD5FDE0-0B2E-416E-A9DB-69E1DE8D34E7 (PID: 2144)
- 4F23E4DF-7FE9-4BF0-BE1E-6A42023ED049 (PID: 2424)
- 9EAE2BD9-AAA9-4CAE-A4EB-789D2F55BC14 (PID: 5104)
- InstallFlashPlayer.exe (PID: 4508)
- InstallFlashPlayer.exe (PID: 6096)
- FlashCenterSvc.exe (PID: 5448)
- FlashHelperService.exe (PID: 7460)
- FlashCenter.exe (PID: 3332)
- FCBrowser.exe (PID: 3004)
The sample compiled with english language support
- flashcenter_install.exe (PID: 8148)
- flash.exe (PID: 4864)
- 2DD5FDE0-0B2E-416E-A9DB-69E1DE8D34E7 (PID: 2144)
- 4F23E4DF-7FE9-4BF0-BE1E-6A42023ED049 (PID: 2424)
- InstallFlashPlayer.exe (PID: 7072)
- 9EAE2BD9-AAA9-4CAE-A4EB-789D2F55BC14 (PID: 5104)
- InstallFlashPlayer.exe (PID: 4508)
- InstallFlashPlayer.exe (PID: 6096)
Create files in a temporary directory
- flash.exe (PID: 4864)
- 2DD5FDE0-0B2E-416E-A9DB-69E1DE8D34E7 (PID: 2144)
Creates files or folders in the user directory
- flash.exe (PID: 4864)
- flash.exe (PID: 1088)
- 2DD5FDE0-0B2E-416E-A9DB-69E1DE8D34E7 (PID: 2144)
- 4F23E4DF-7FE9-4BF0-BE1E-6A42023ED049 (PID: 2424)
- InstallFlashPlayer.exe (PID: 4508)
- FlashCenter.exe (PID: 3332)
- FCBrowser.exe (PID: 3344)
- FCBrowser.exe (PID: 3004)
- FCLogin.exe (PID: 7232)
Process checks computer location settings
- flash.exe (PID: 4864)
- 2DD5FDE0-0B2E-416E-A9DB-69E1DE8D34E7 (PID: 2144)
- 4F23E4DF-7FE9-4BF0-BE1E-6A42023ED049 (PID: 2424)
- InstallFlashPlayer.exe (PID: 7072)
- 9EAE2BD9-AAA9-4CAE-A4EB-789D2F55BC14 (PID: 5104)
- InstallFlashPlayer.exe (PID: 4508)
- InstallFlashPlayer.exe (PID: 6096)
- FCBrowser.exe (PID: 2228)
Checks proxy server information
- flashcenter_install.exe (PID: 8148)
- copy.exe (PID: 3380)
- flash.exe (PID: 4864)
- flash.exe (PID: 1088)
- 2DD5FDE0-0B2E-416E-A9DB-69E1DE8D34E7 (PID: 2144)
- 4F23E4DF-7FE9-4BF0-BE1E-6A42023ED049 (PID: 2424)
- 9EAE2BD9-AAA9-4CAE-A4EB-789D2F55BC14 (PID: 5104)
- InstallFlashPlayer.exe (PID: 4508)
- slui.exe (PID: 6932)
- FlashCenter.exe (PID: 3332)
- FCBrowser.exe (PID: 3344)
The sample compiled with chinese language support
- flash.exe (PID: 4864)
- 2DD5FDE0-0B2E-416E-A9DB-69E1DE8D34E7 (PID: 2144)
- flash.exe (PID: 1088)
Detects GO elliptic curve encryption (YARA)
- flashcenter_install.exe (PID: 8148)
- copy.exe (PID: 3380)
UPX packer has been detected
- flash.exe (PID: 4864)
- flash.exe (PID: 1088)
Application based on Golang
- flashcenter_install.exe (PID: 8148)
- copy.exe (PID: 3380)
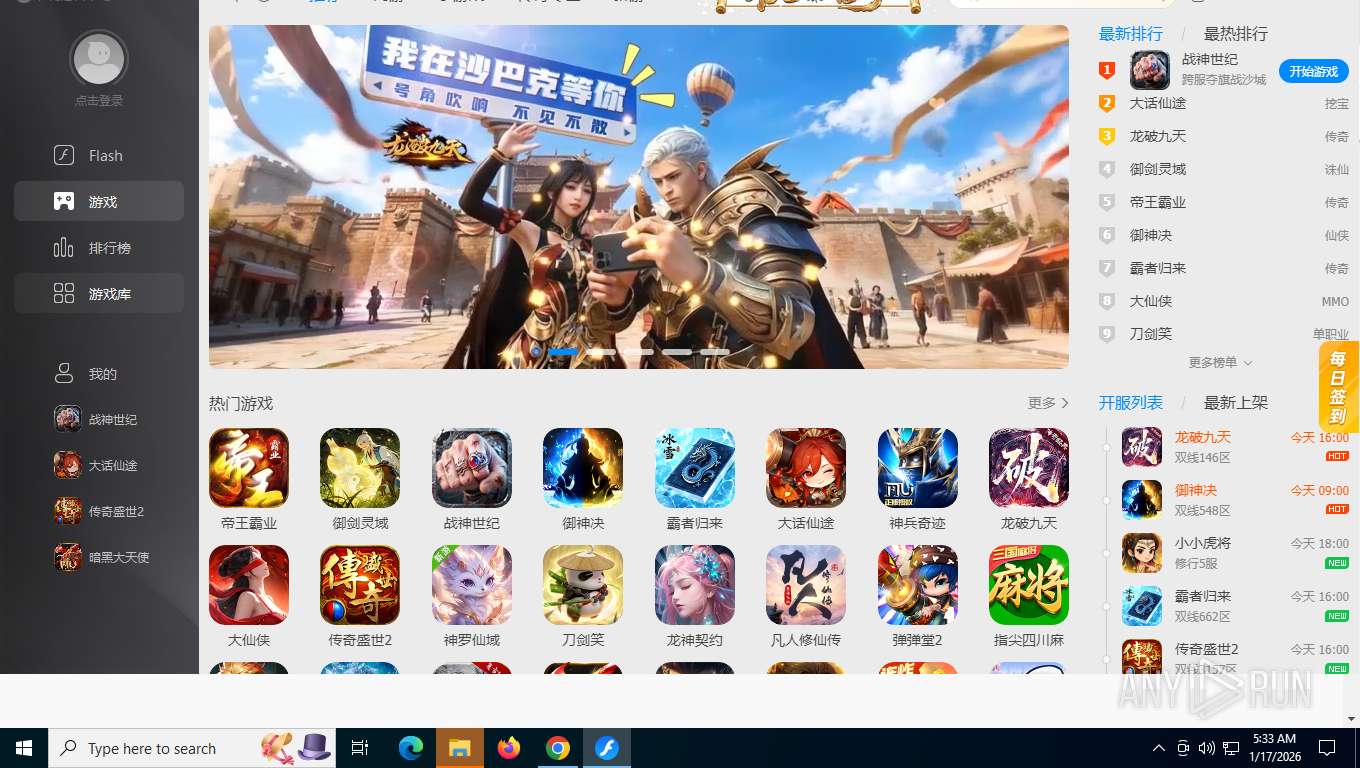
Creates files in the program directory
- 2DD5FDE0-0B2E-416E-A9DB-69E1DE8D34E7 (PID: 2144)
- mmc.exe (PID: 2684)
Creates a software uninstall entry
- 2DD5FDE0-0B2E-416E-A9DB-69E1DE8D34E7 (PID: 2144)
- InstallFlashPlayer.exe (PID: 4508)
- FlashHelperService.exe (PID: 7460)
Process checks whether UAC notifications are on
- 4F23E4DF-7FE9-4BF0-BE1E-6A42023ED049 (PID: 2424)
- InstallFlashPlayer.exe (PID: 7072)
- 9EAE2BD9-AAA9-4CAE-A4EB-789D2F55BC14 (PID: 5104)
- InstallFlashPlayer.exe (PID: 4508)
- InstallFlashPlayer.exe (PID: 6096)
Creating file in SysWOW64
- 4F23E4DF-7FE9-4BF0-BE1E-6A42023ED049 (PID: 2424)
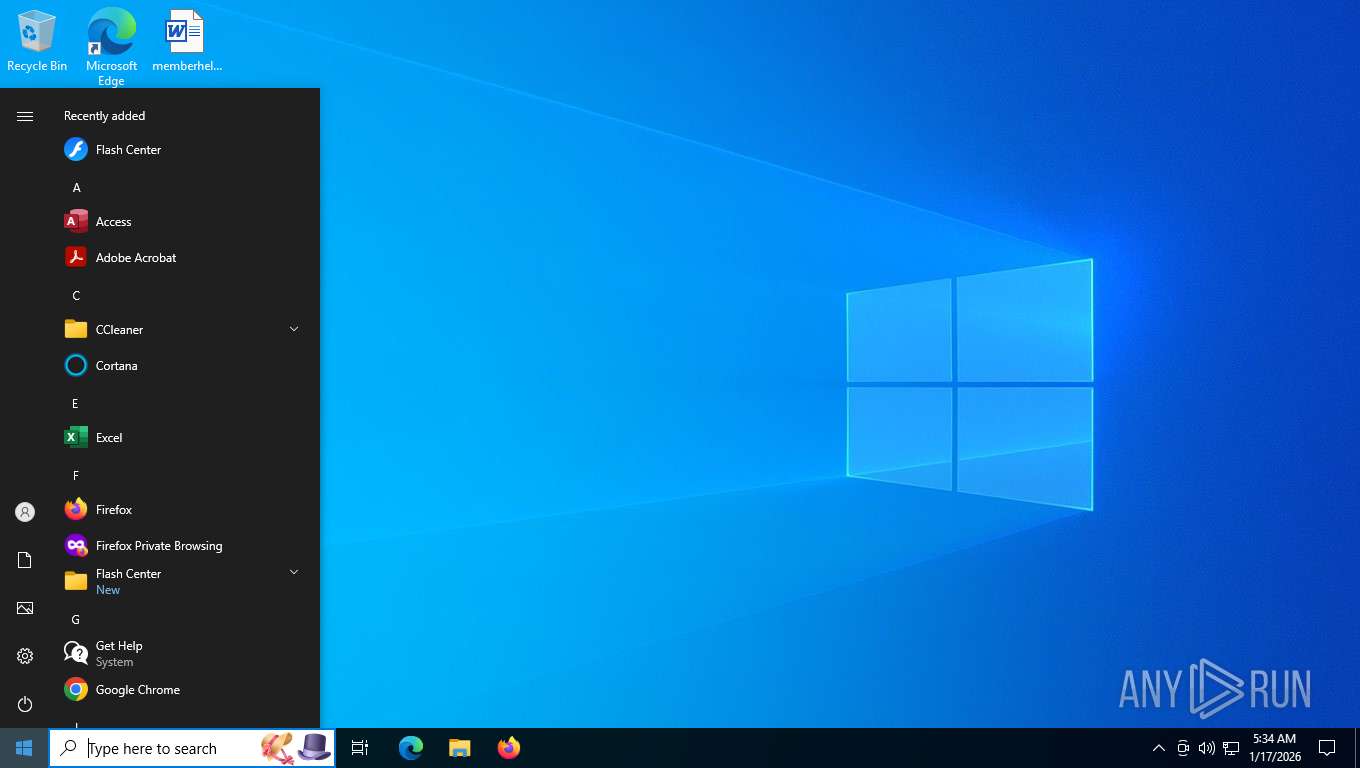
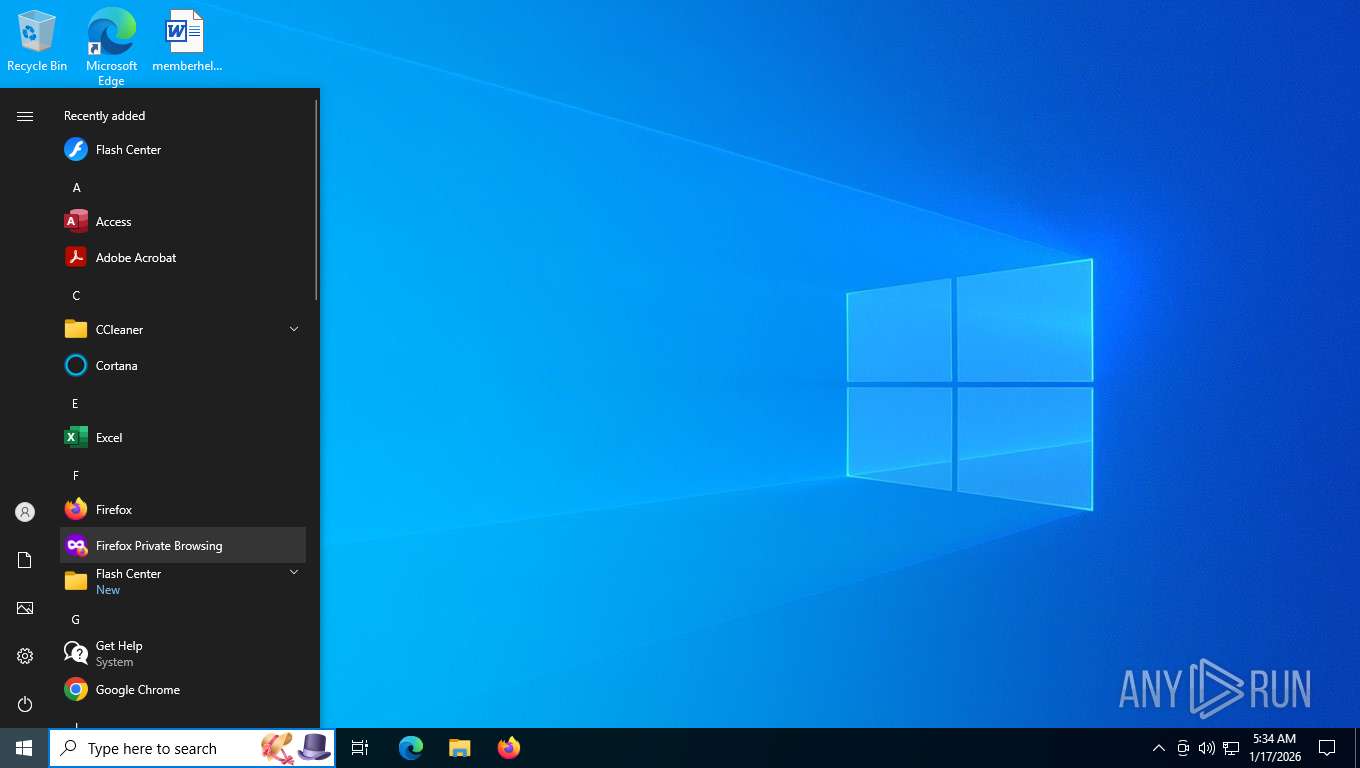
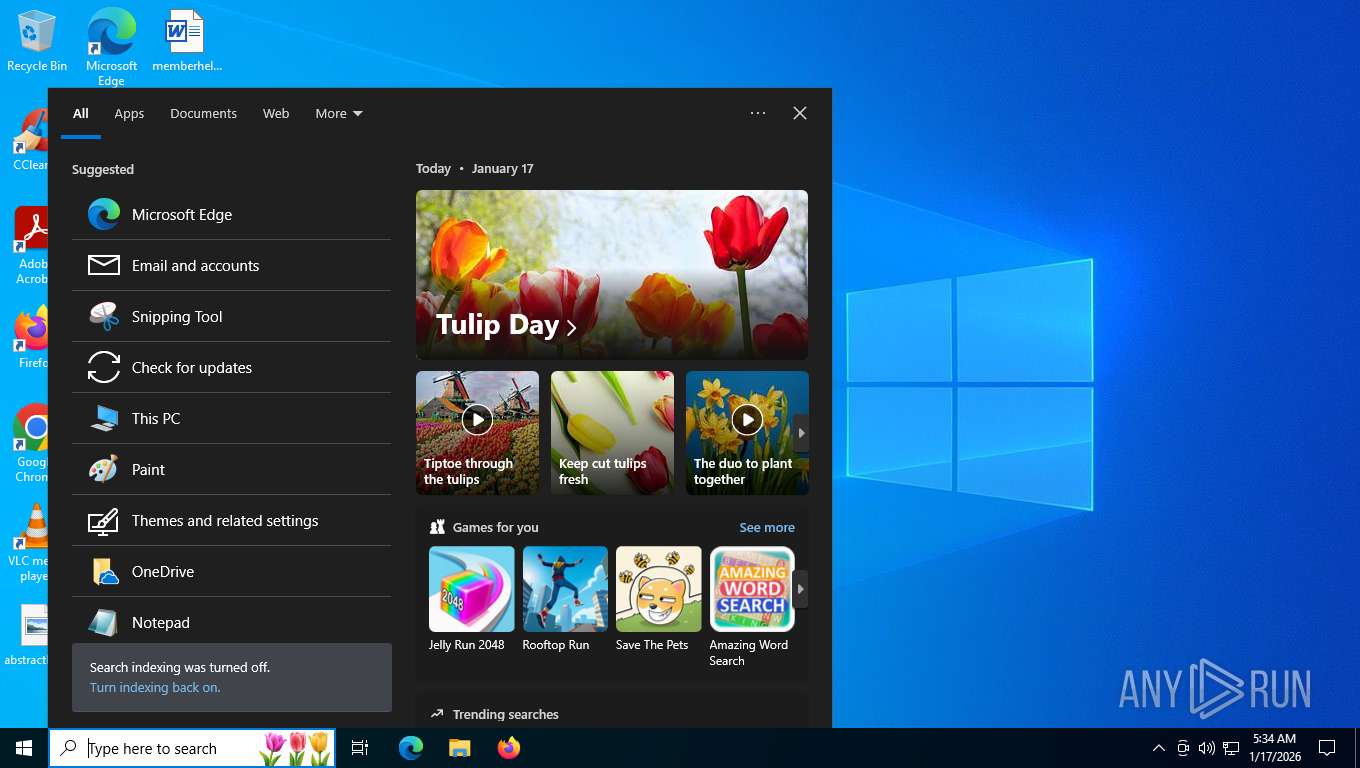
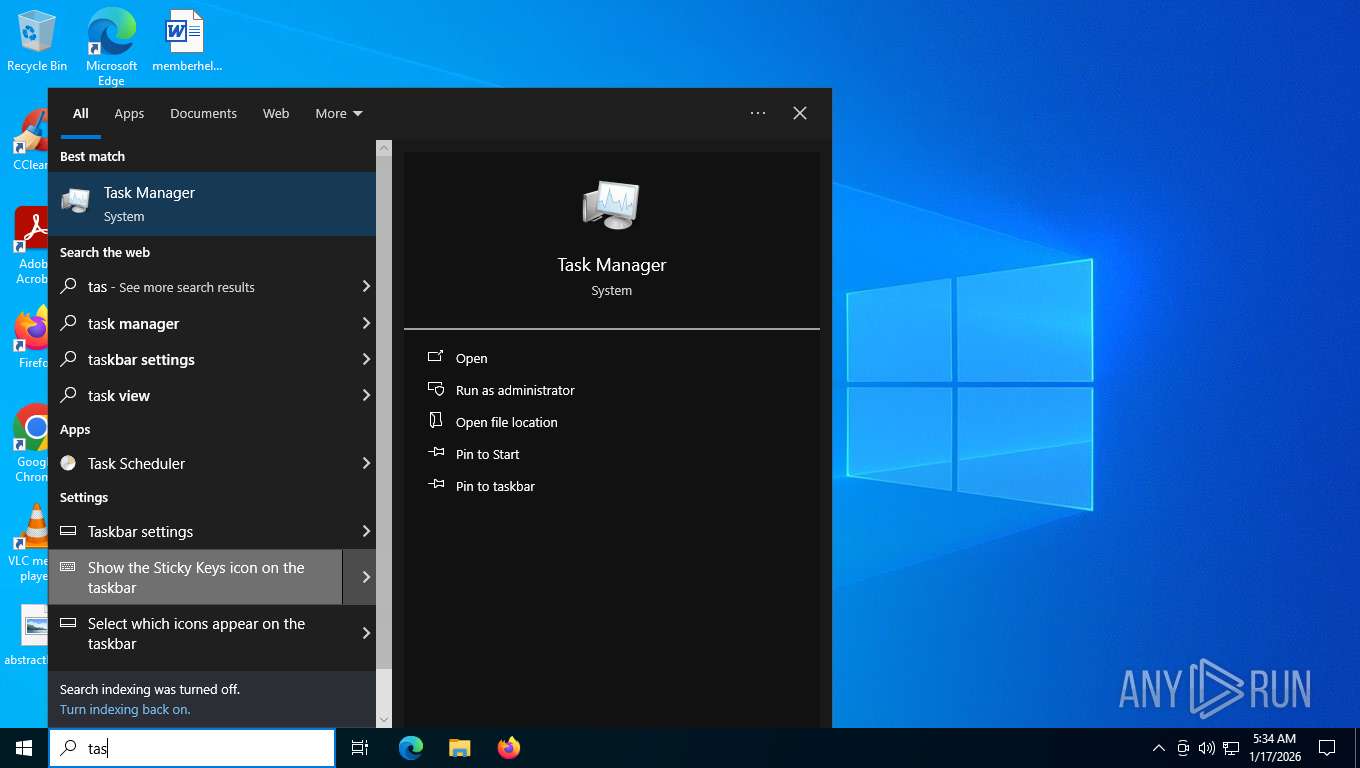
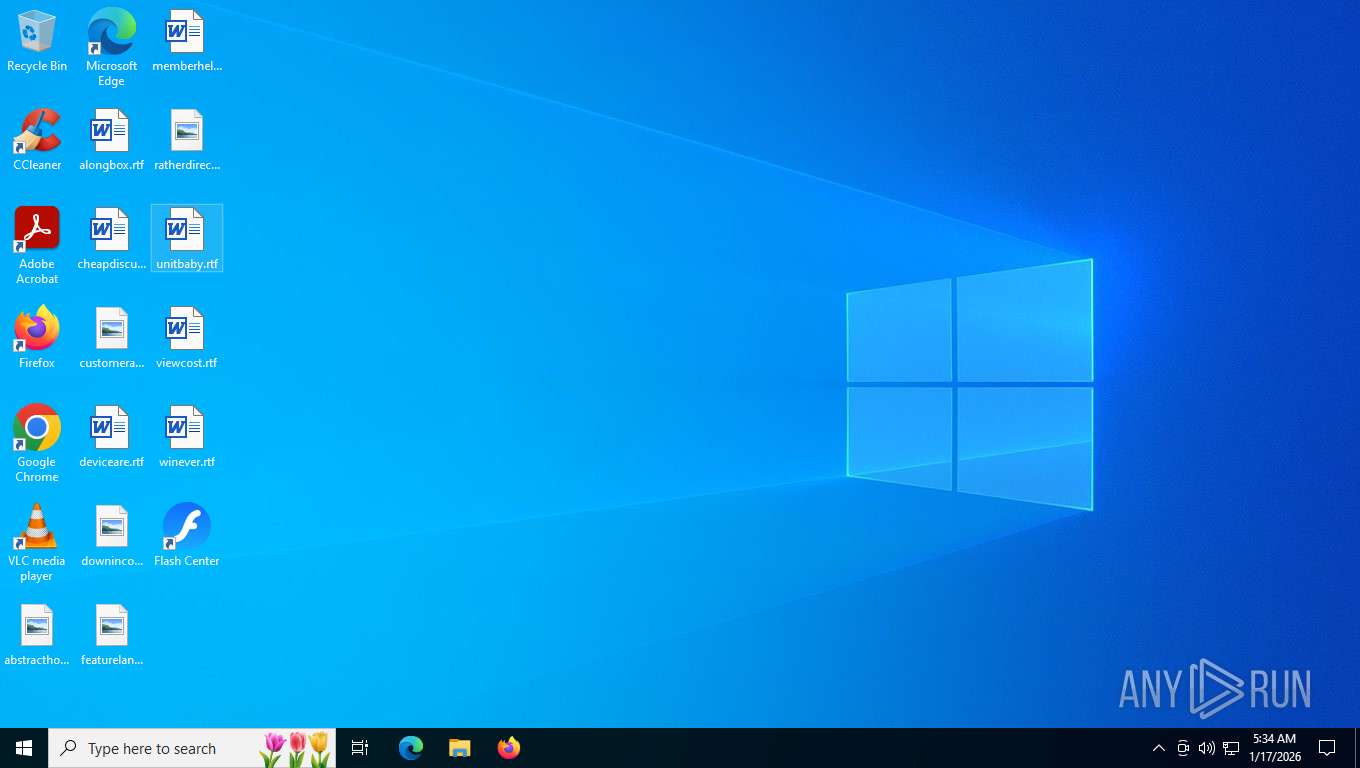
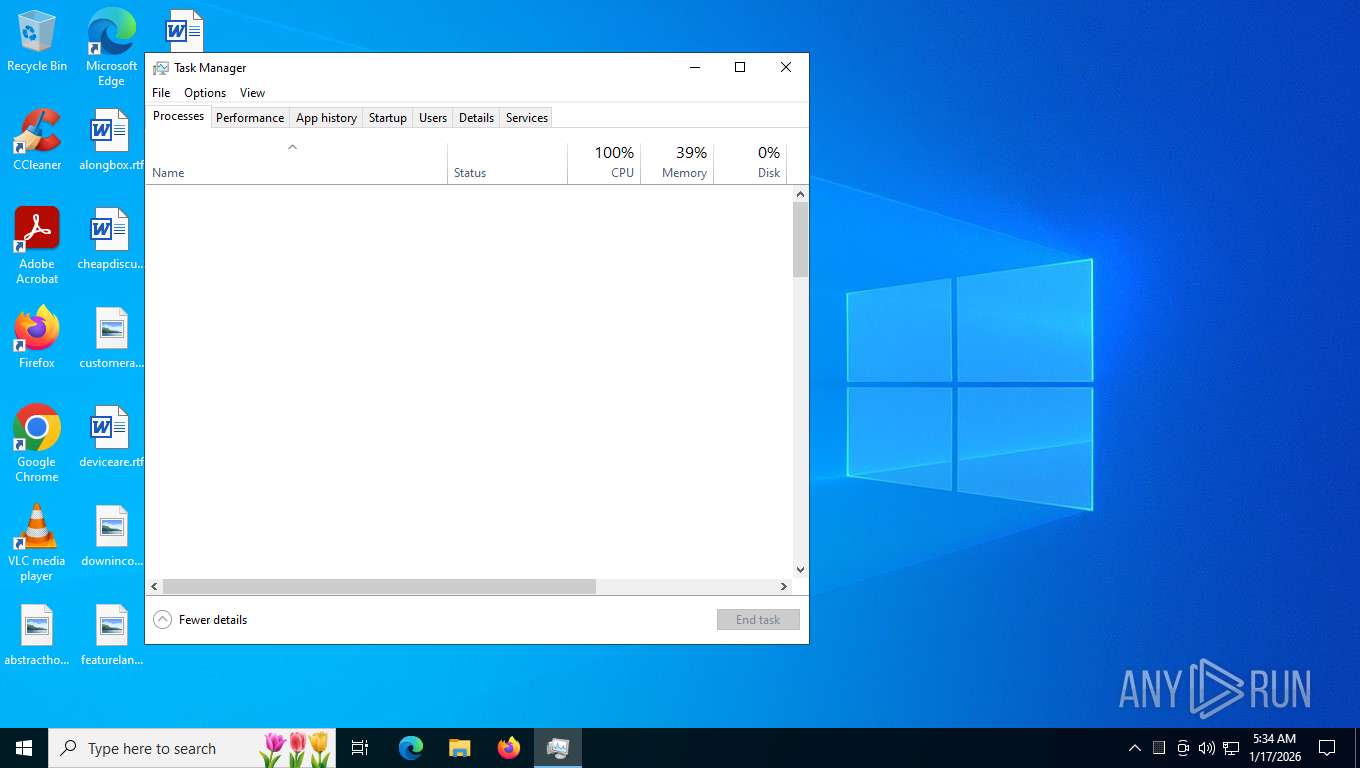
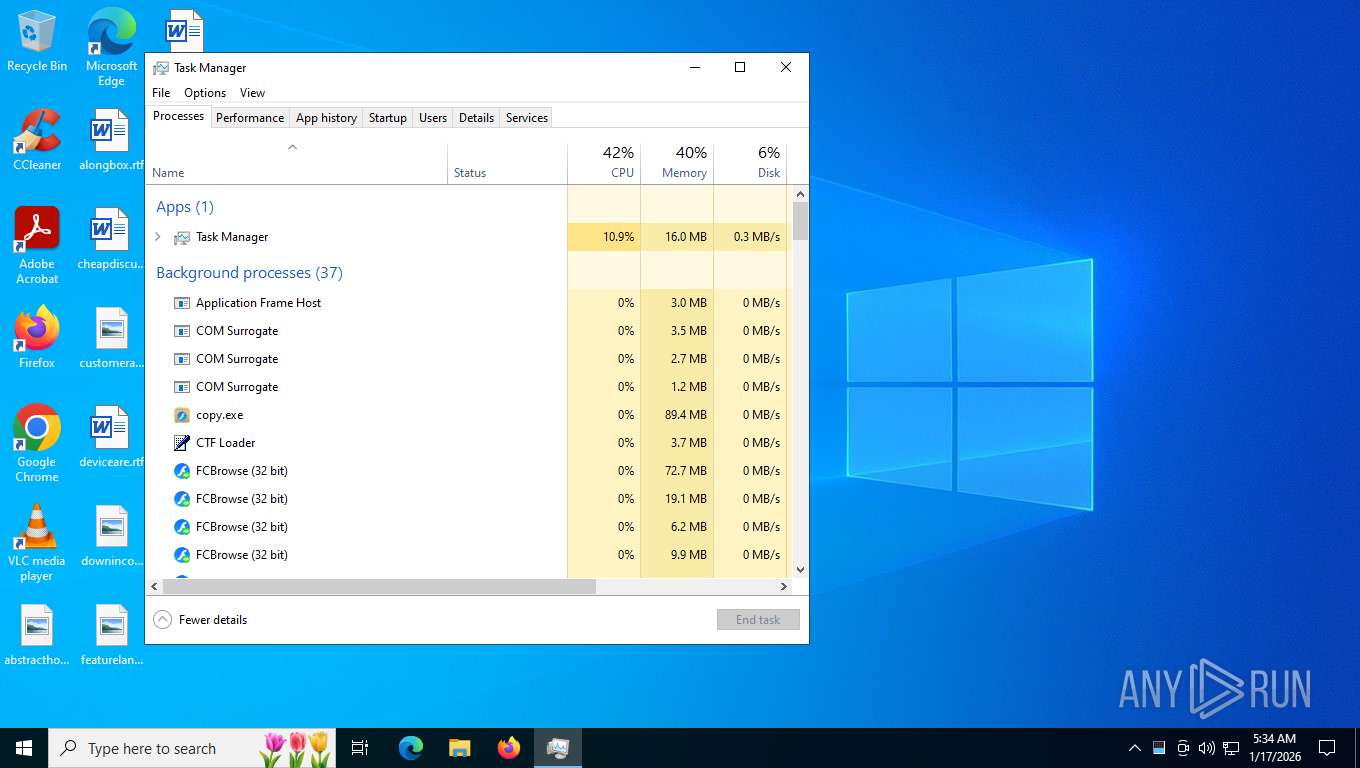
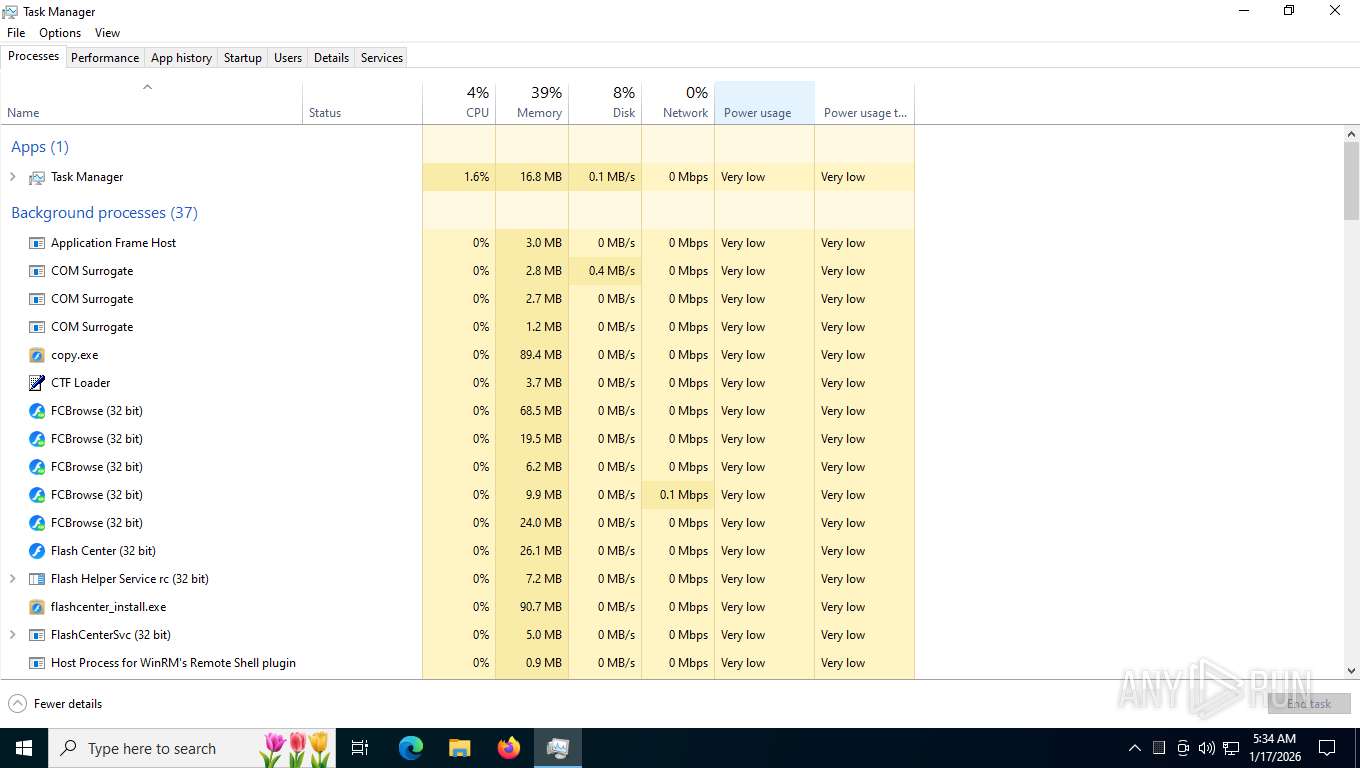
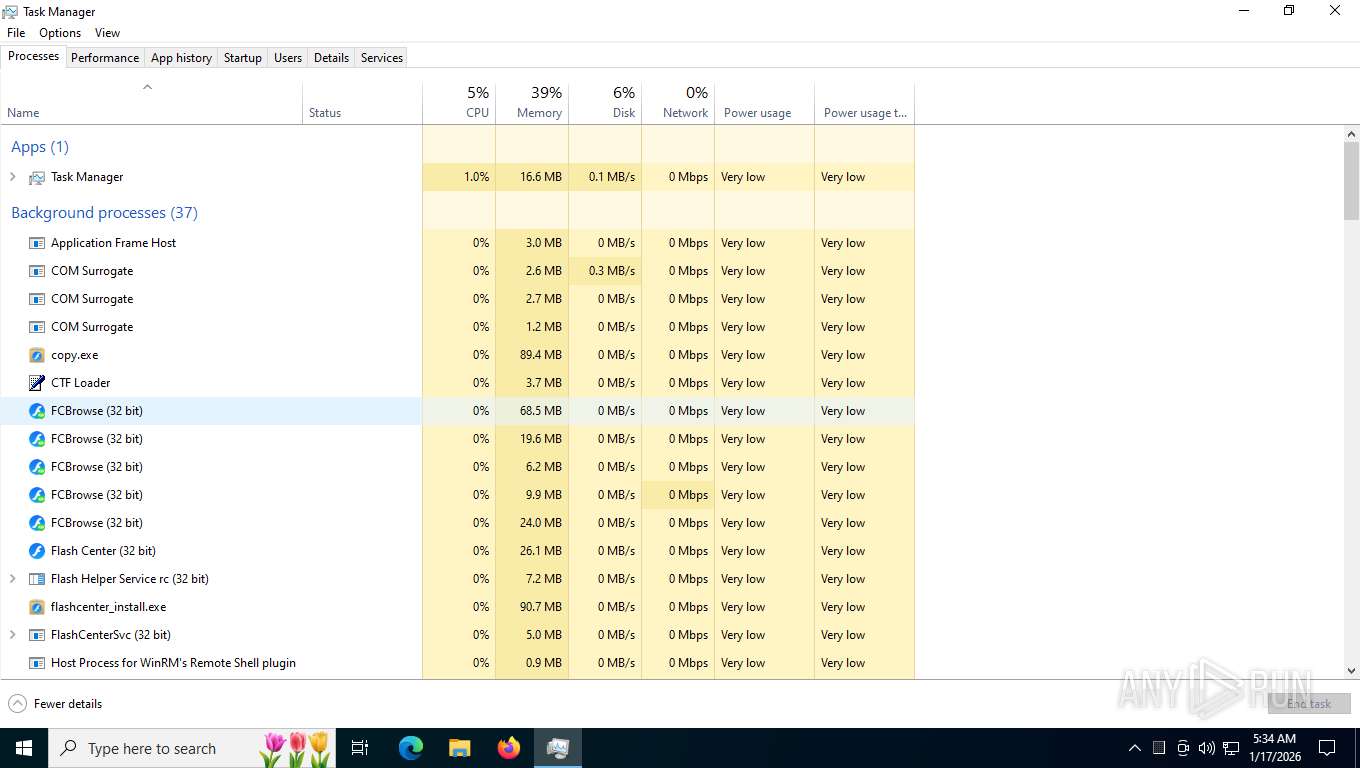
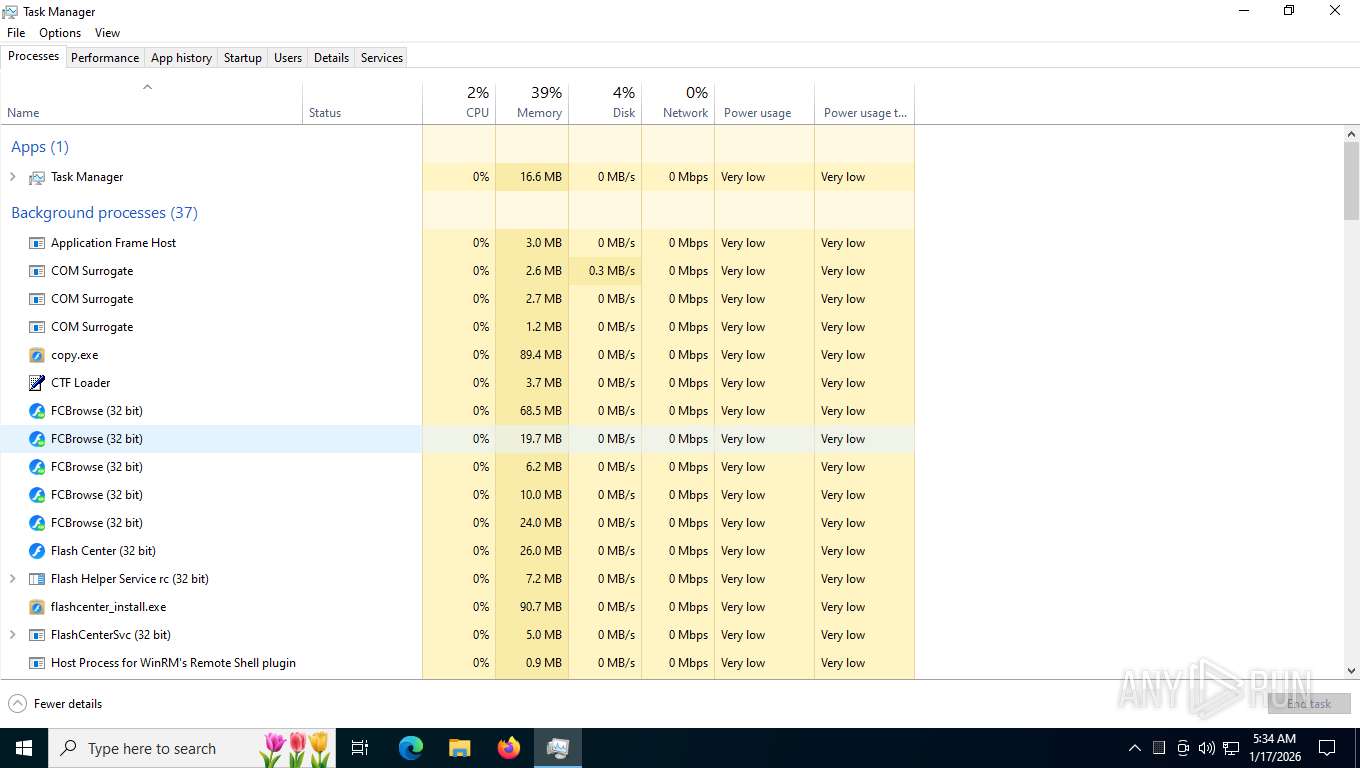
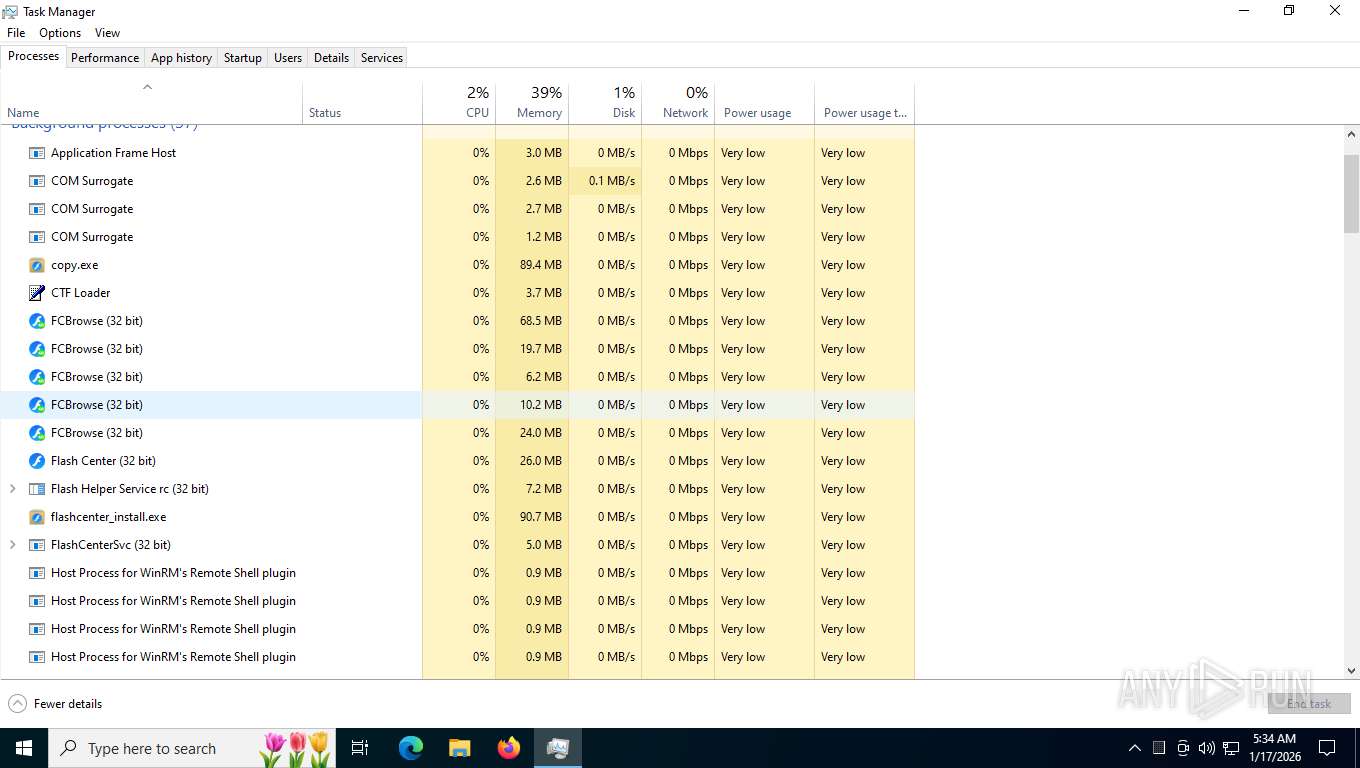
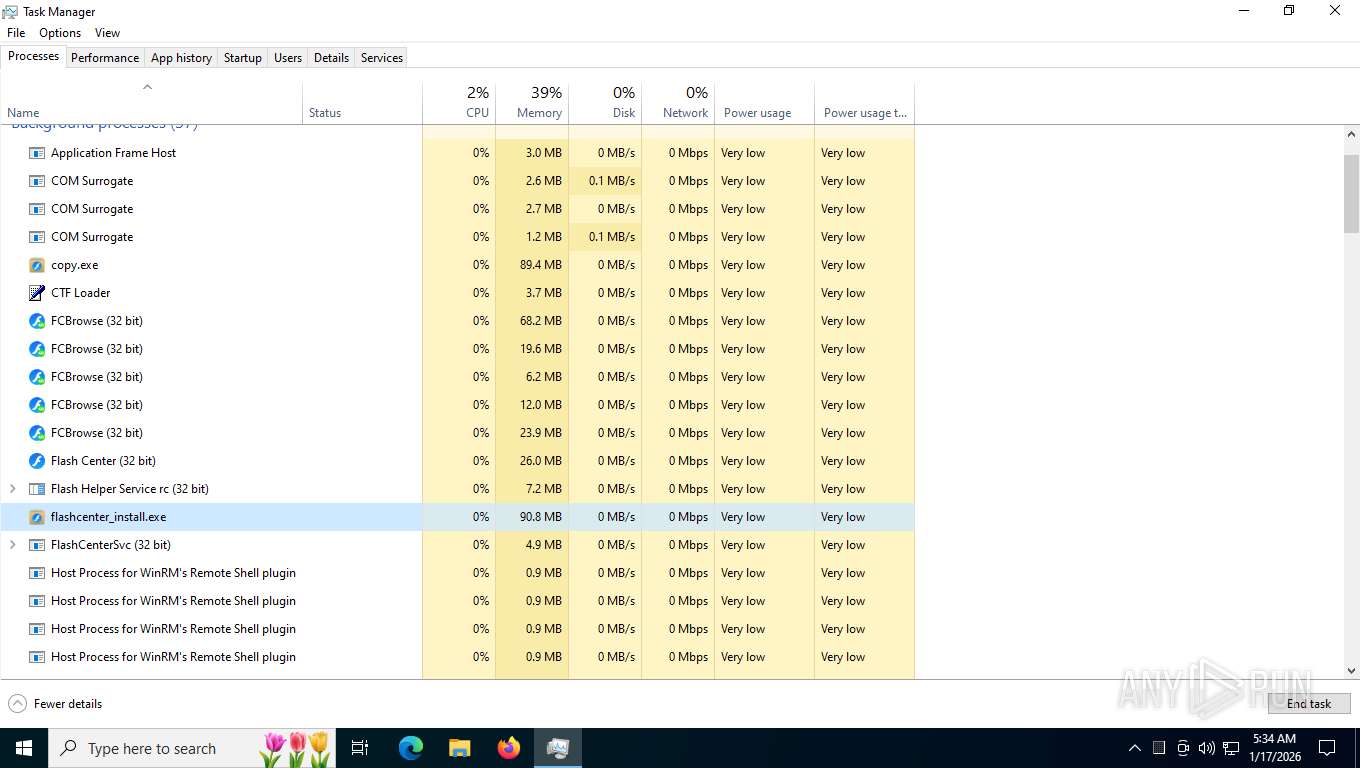
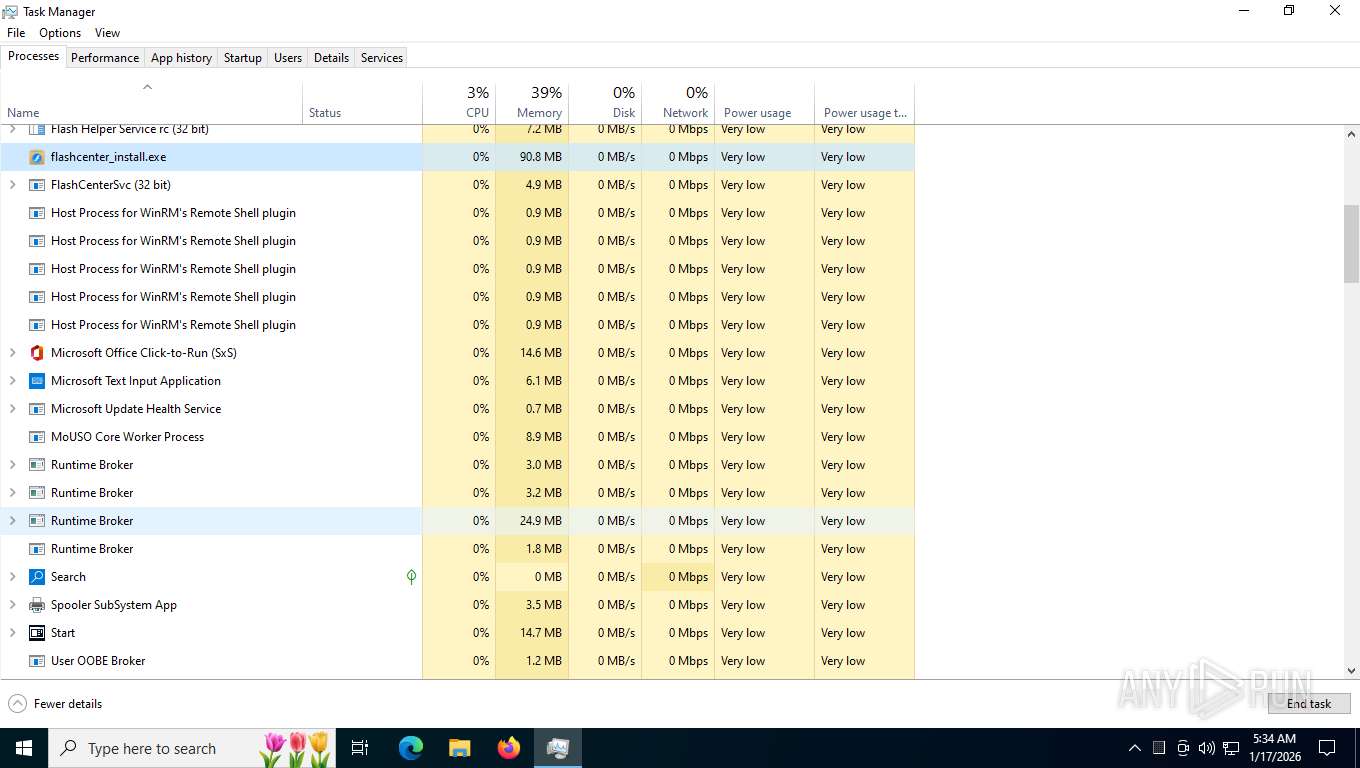
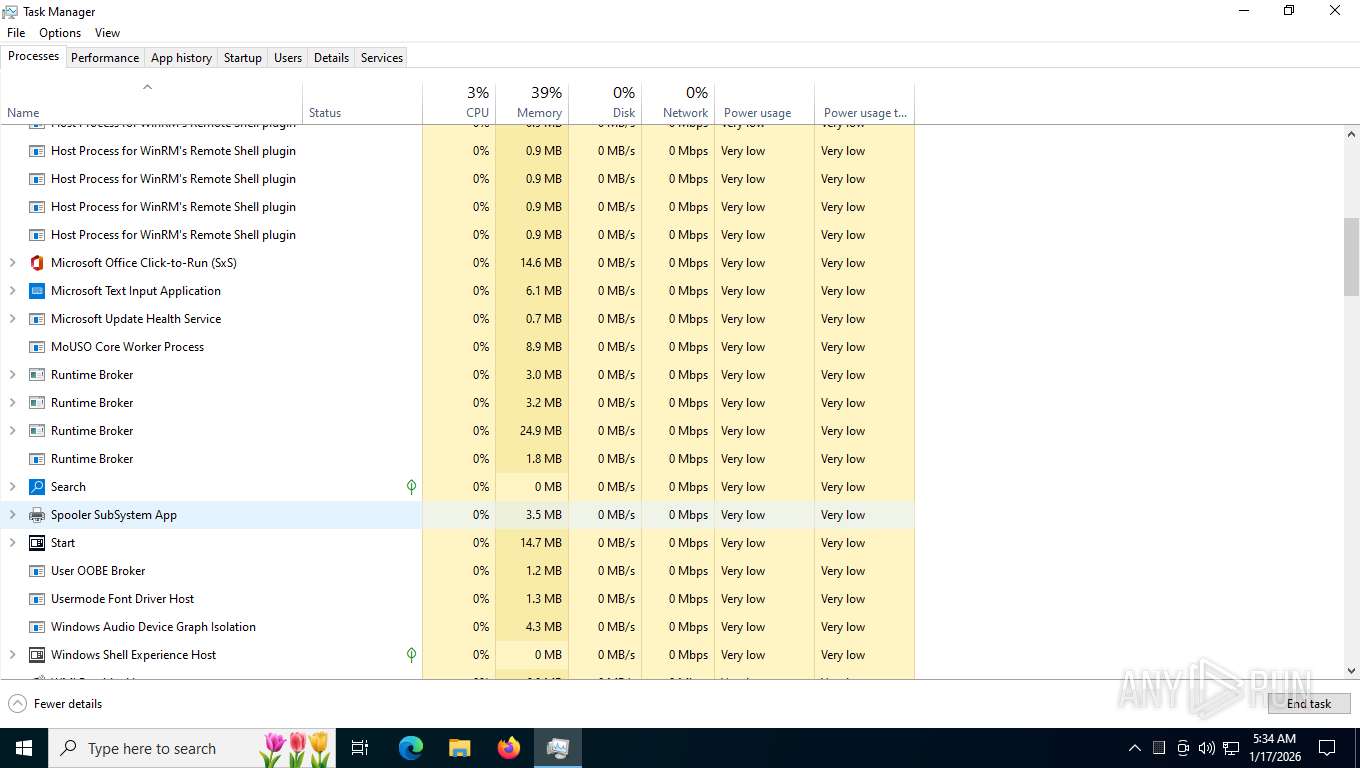
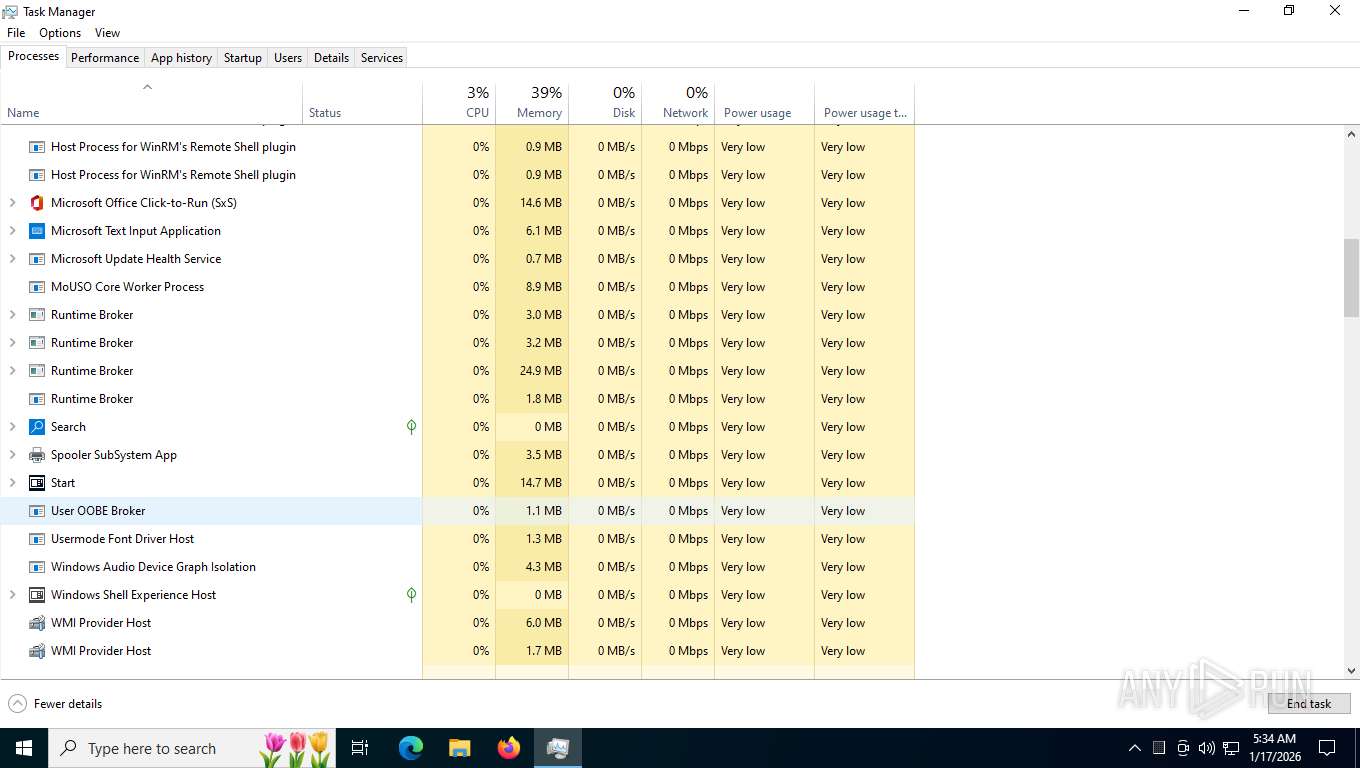
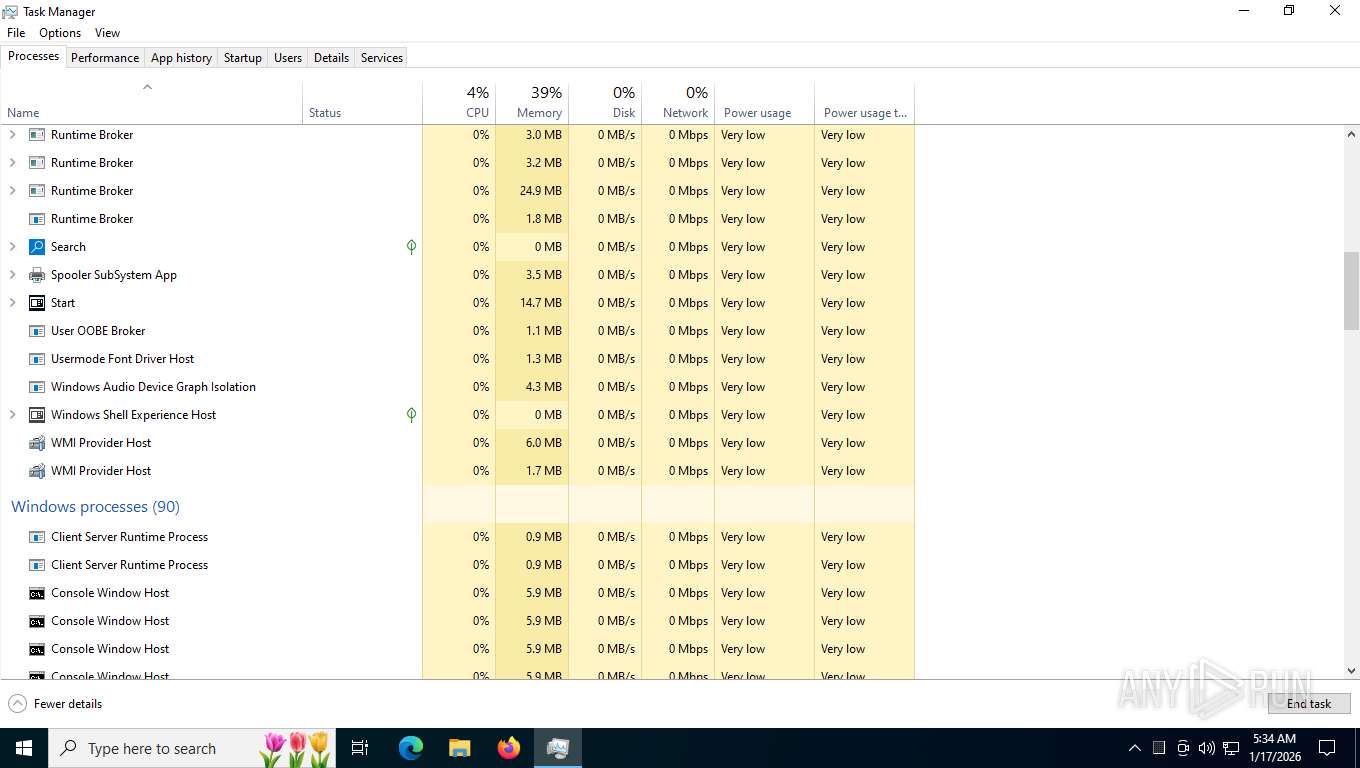
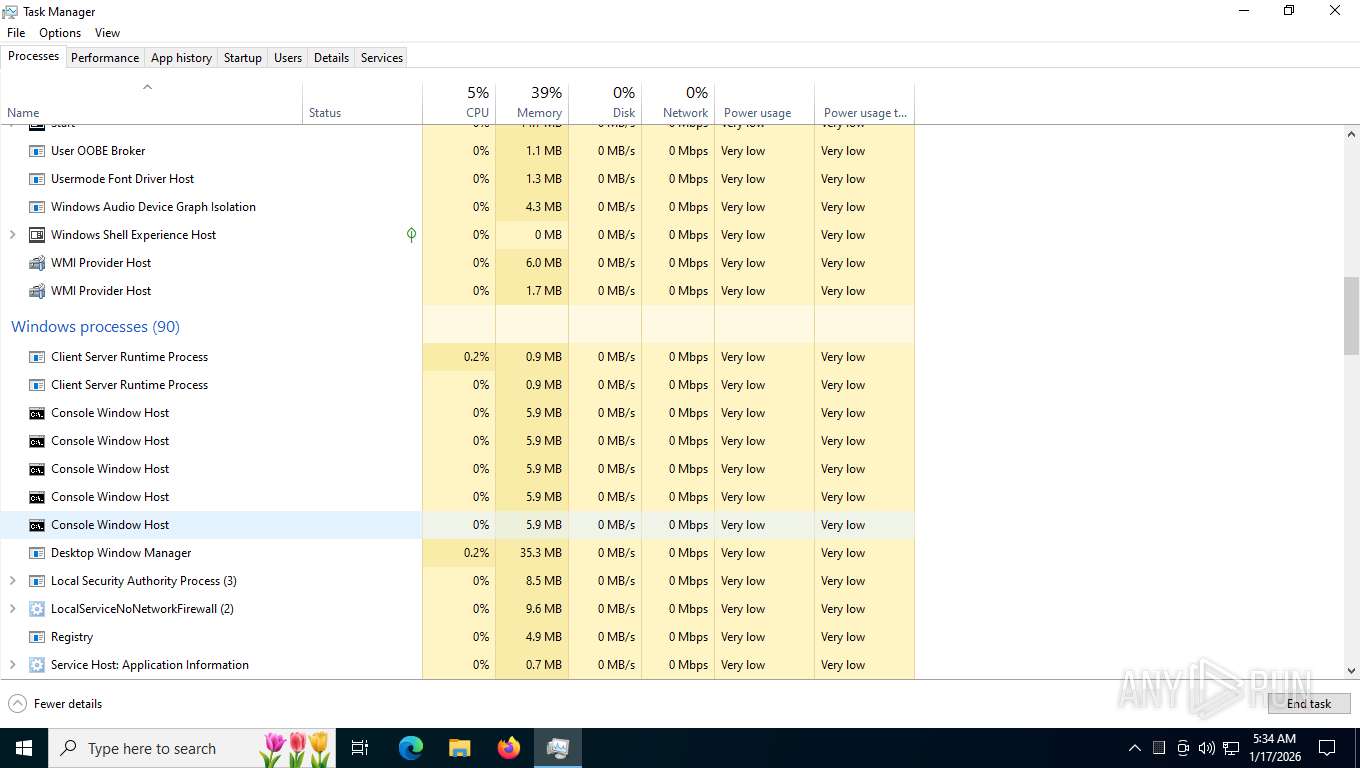
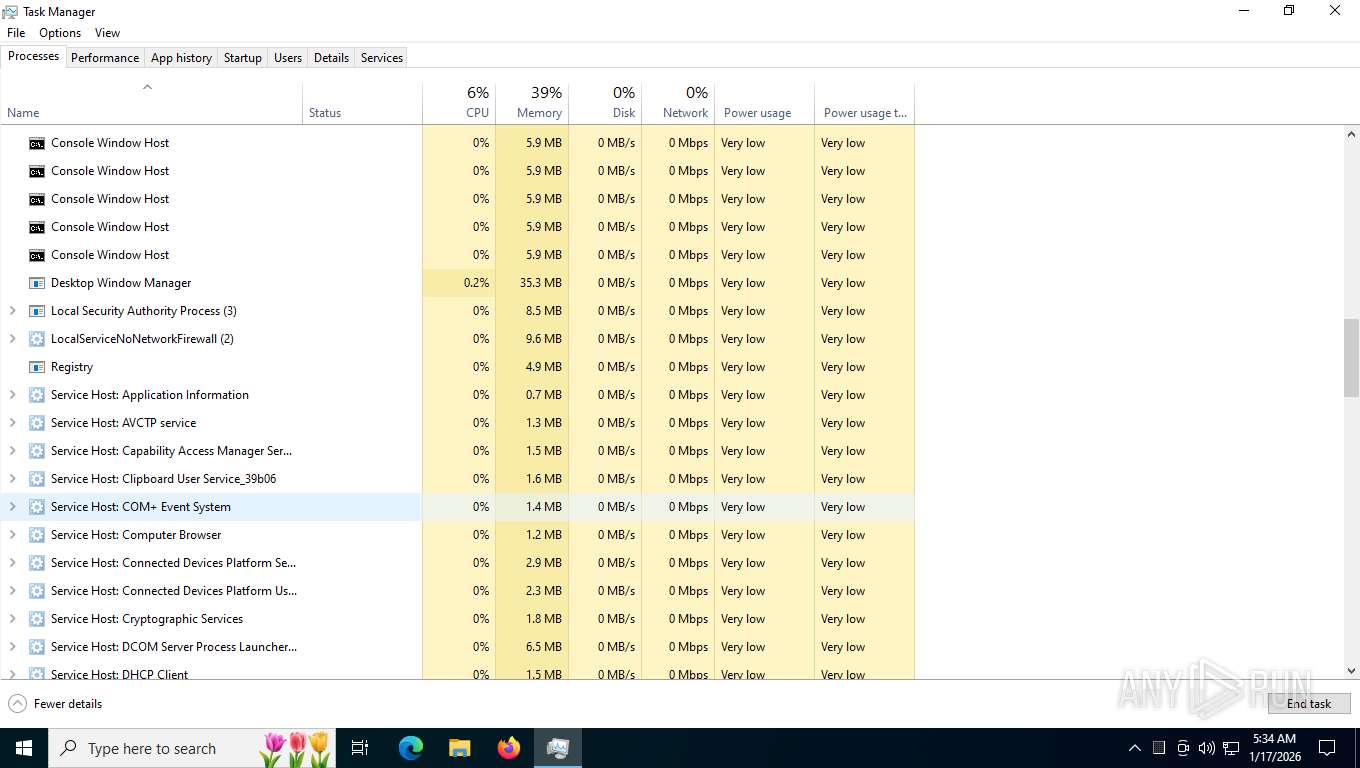
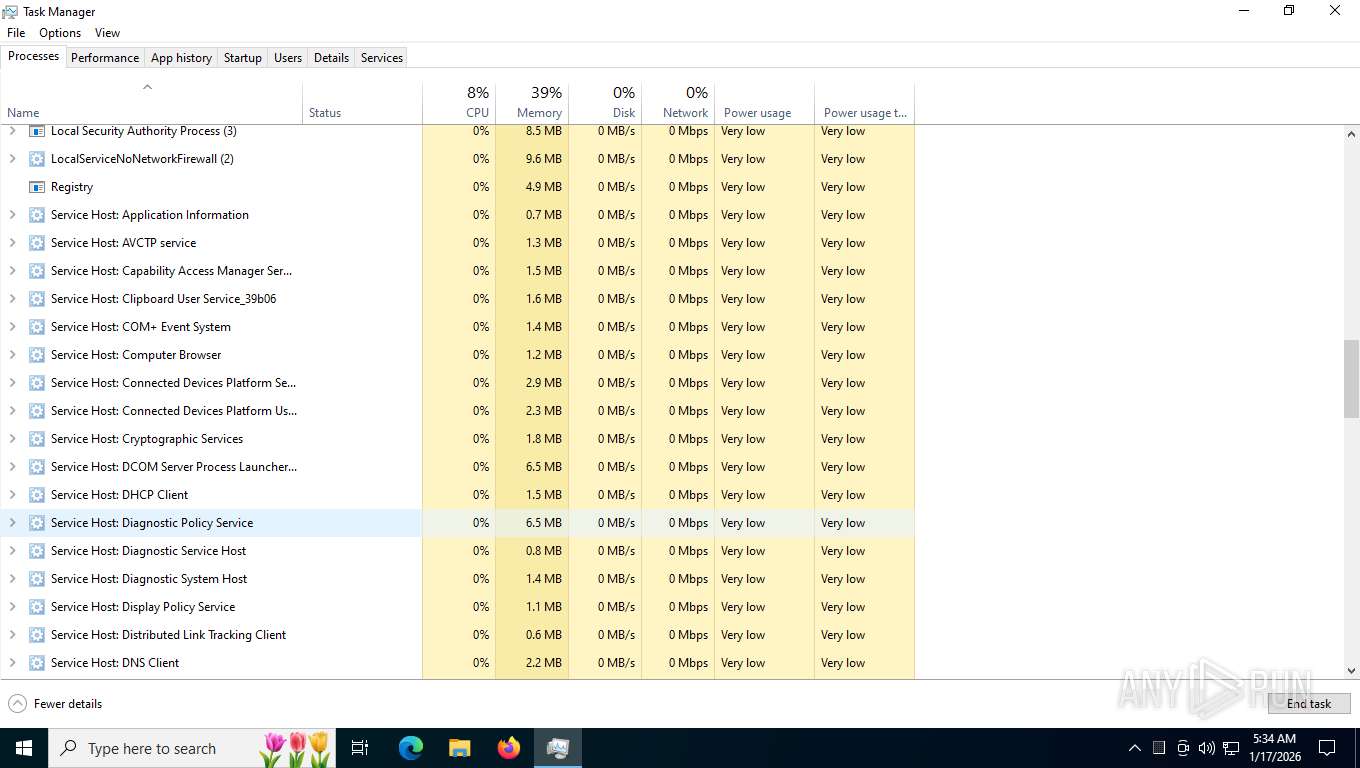
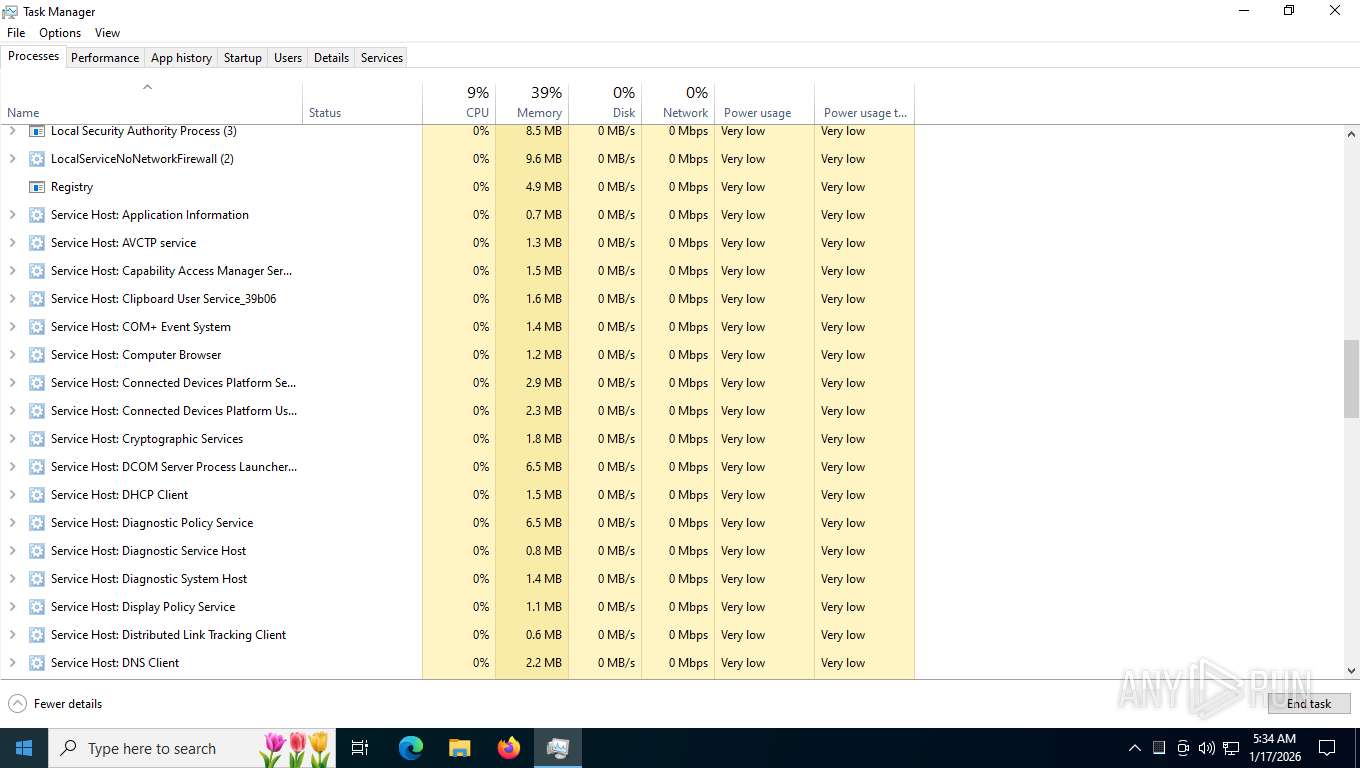
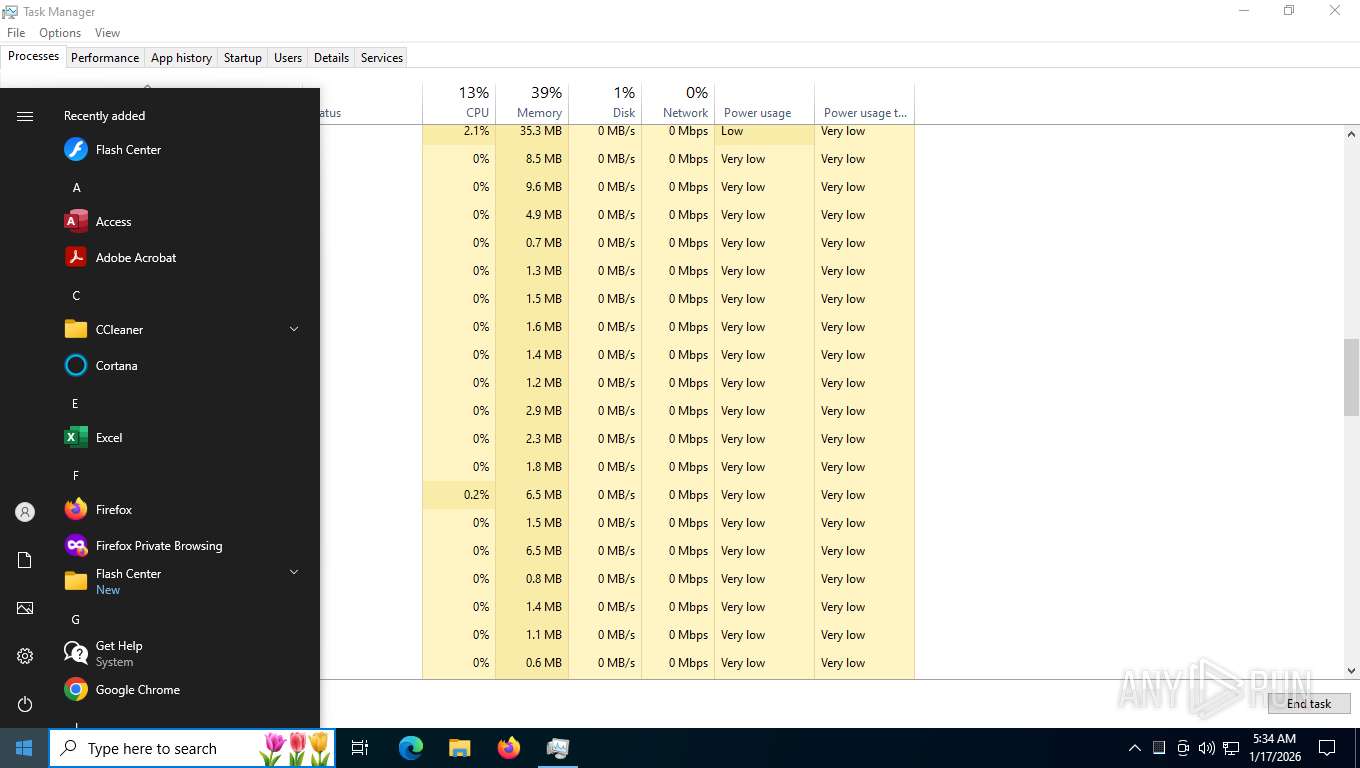
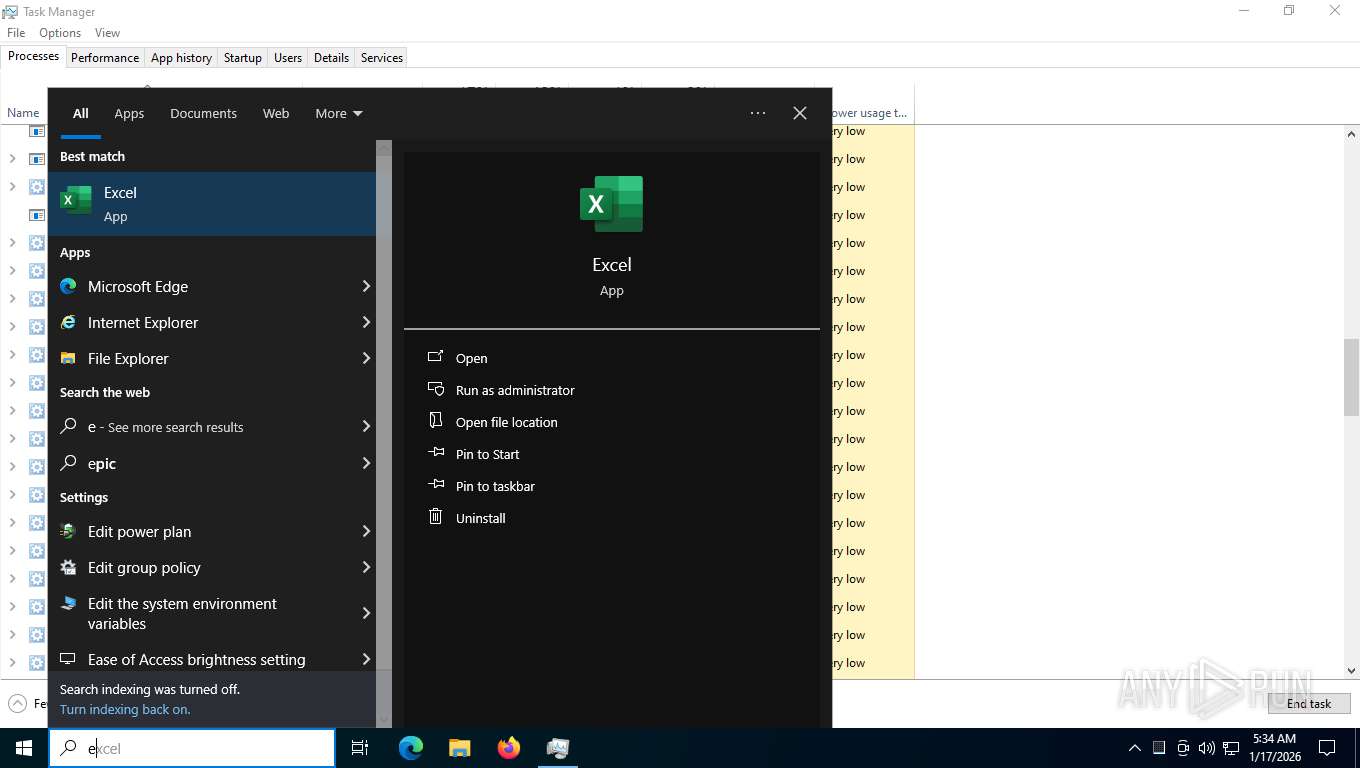
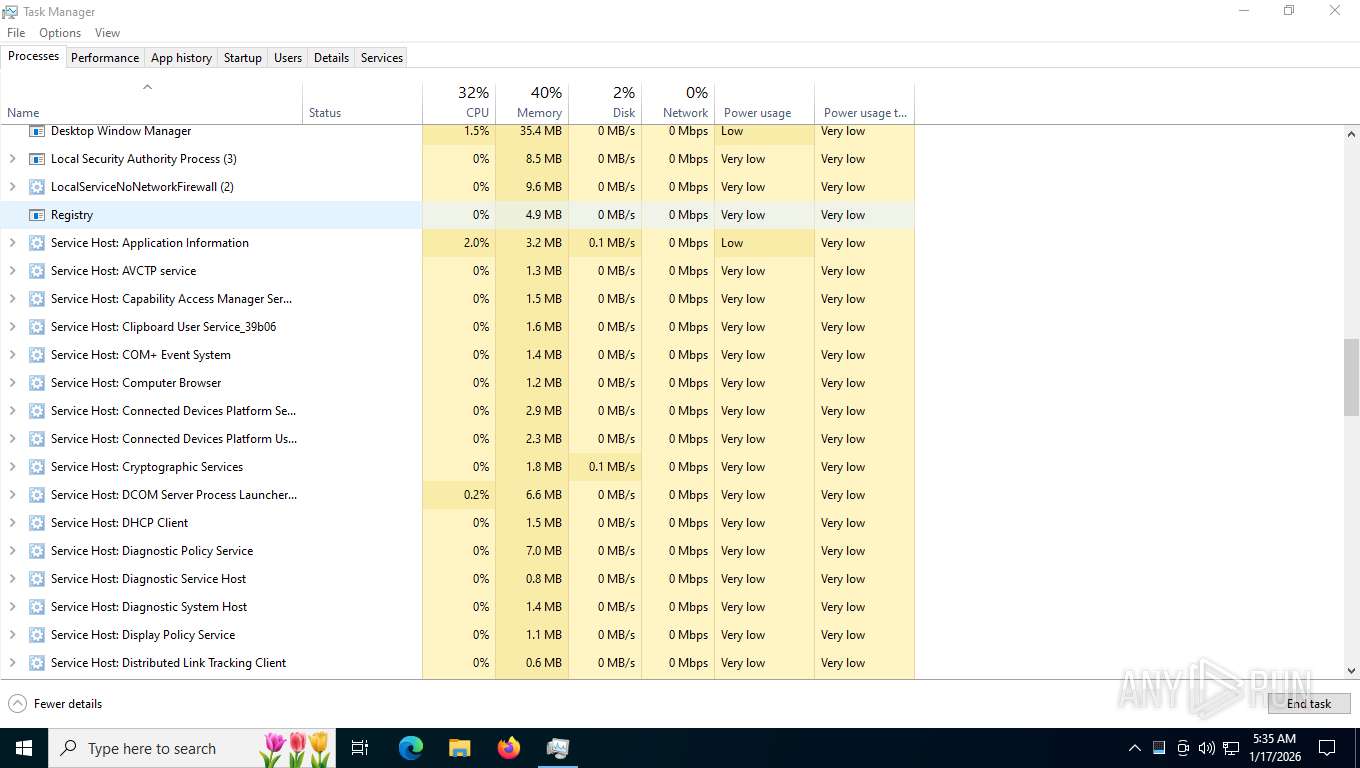
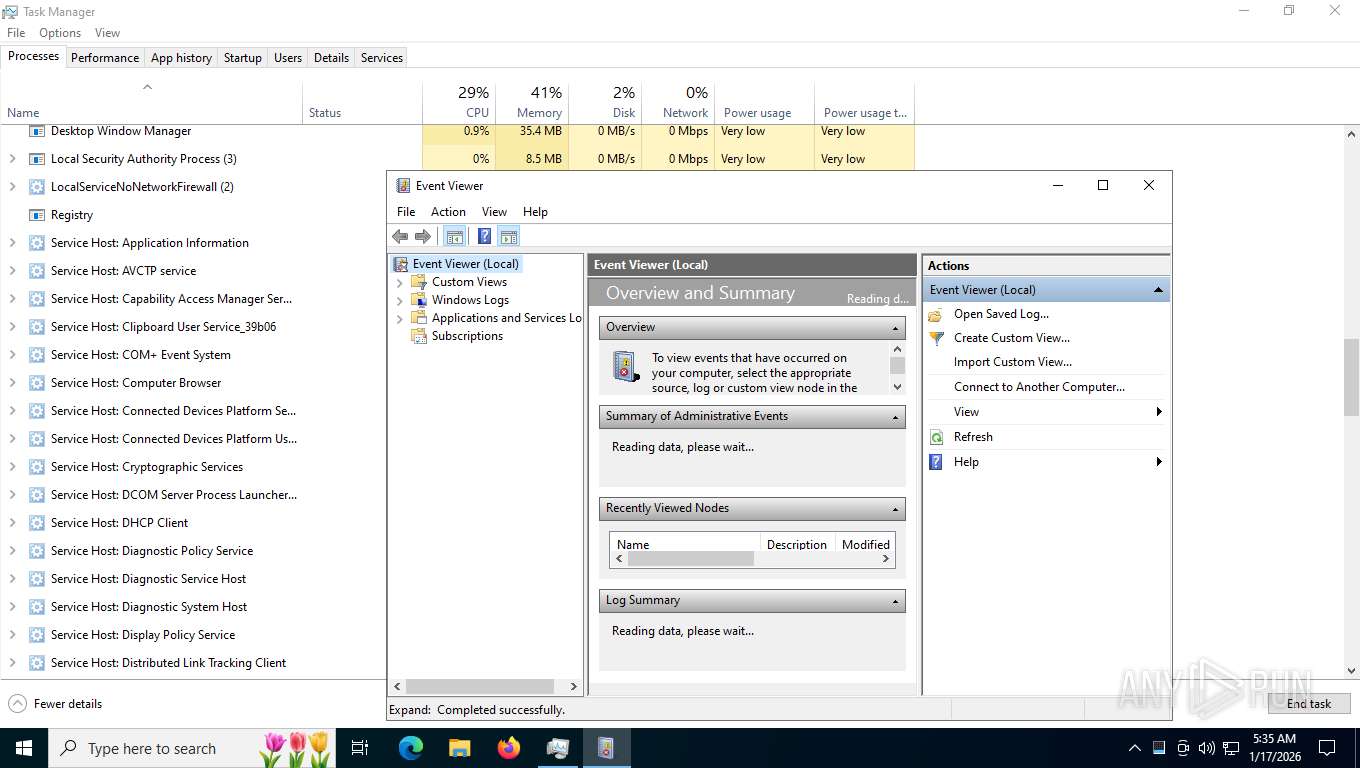
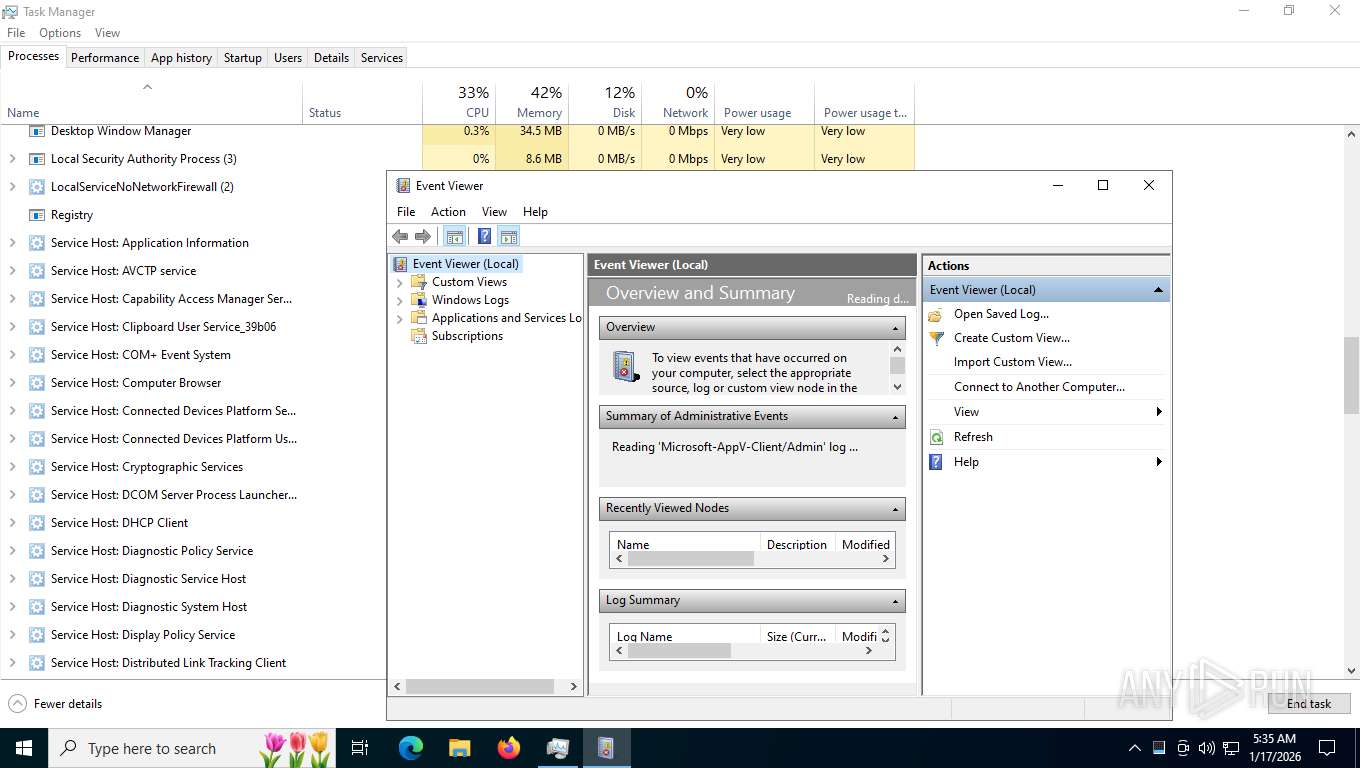
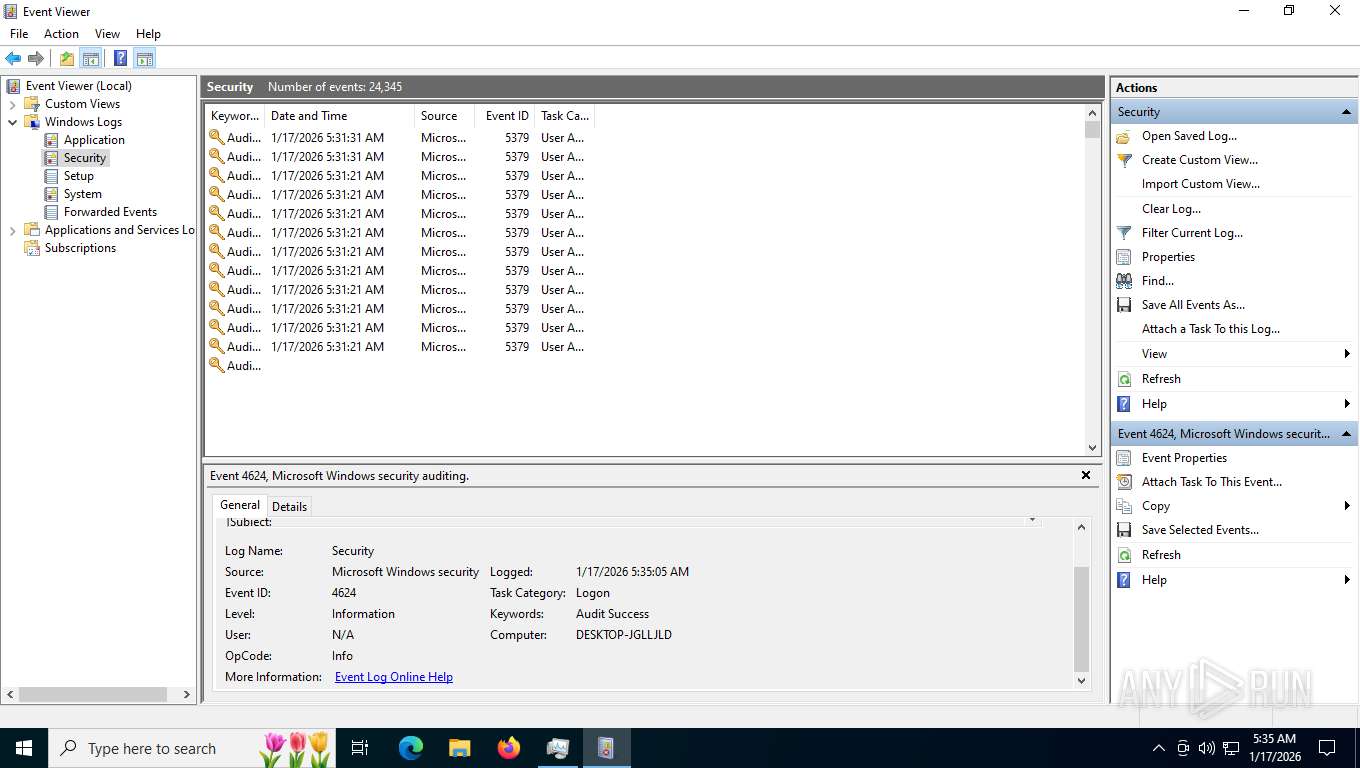
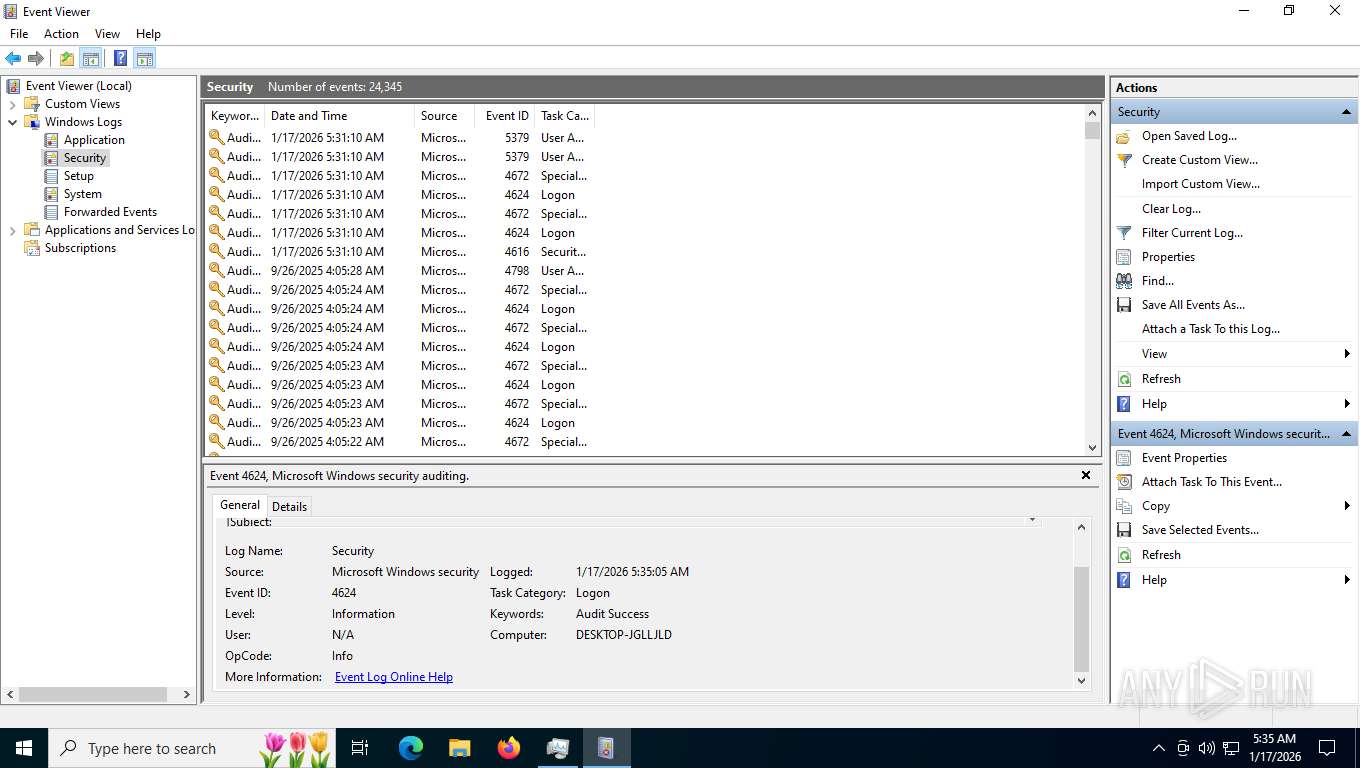
Manual execution by a user
- Taskmgr.exe (PID: 7816)
- Taskmgr.exe (PID: 7900)
- mmc.exe (PID: 2684)
- mmc.exe (PID: 7928)
Reads security settings of Internet Explorer
- Taskmgr.exe (PID: 7900)
- mmc.exe (PID: 2684)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
252
Monitored processes
93
Malicious processes
9
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
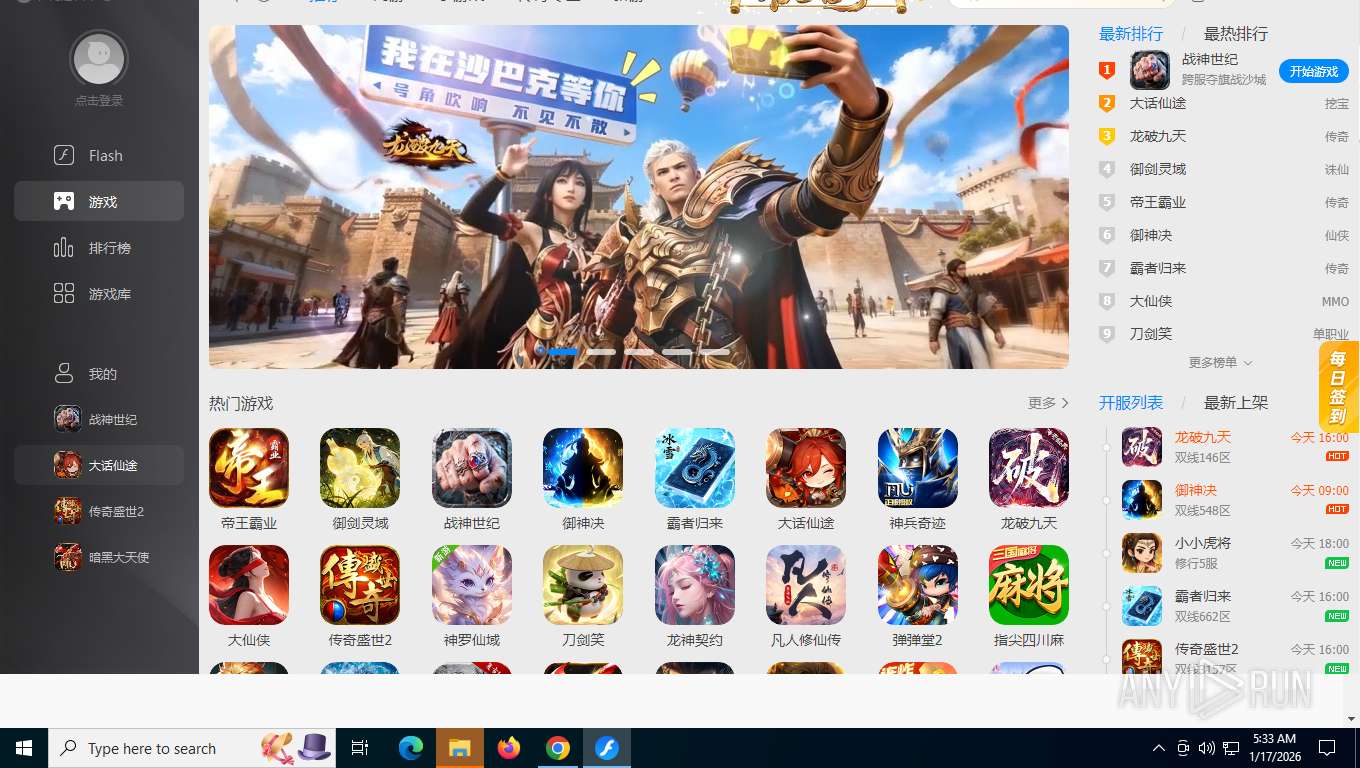
| 800 | "C:\Program Files (x86)\FlashCenter\FCBrowser.exe" --type=gpu-process --field-trial-handle=1816,17445149089644190158,13576866833897559164,131072 --enable-features=CastMediaRouteProvider,CookieDeprecationMessages,CrossOriginEmbedderPolicy,CrossOriginOpenerPolicy,DocumentPolicy,FeaturePolicyForClientHints,OriginIsolationHeader,OriginPolicy,UserAgentClientHint --disable-features=OutOfBlinkCors --no-sandbox --log-file="C:\Program Files (x86)\FlashCenter\debug.log" --log-severity=disable --user-agent="Mozilla/5.0 (Windows NT 10; W0W64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/83.0.4103.97 Safari/537.36 FCBrowser/3.8.4.9 FCVersion/3.8.4.9" --lang=zh-CN --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --log-file="C:\Program Files (x86)\FlashCenter\debug.log" --mojo-platform-channel-handle=1824 /prefetch:2 | C:\Program Files (x86)\FlashCenter\FCBrowser.exe | — | FCBrowser.exe | |||||||||||
User: admin Company: Chongqing Zhongcheng Network Technology Co., Ltd Integrity Level: HIGH Description: FCBrowse Version: 3.8.4.9 Modules
| |||||||||||||||
| 1080 | taskkill /F /IM "FCBrowserManager.exe" | C:\Windows\SysWOW64\taskkill.exe | — | 2DD5FDE0-0B2E-416E-A9DB-69E1DE8D34E7 | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1088 | "C:\users\public\music\flash.exe" --pipename={AFDD1549-70C1-40B3-AB98-E9F6693B6C3A} --type=web --pid=4864 --isrunbyfc=false | C:\Users\Public\Music\flash.exe | flash.exe | ||||||||||||
User: admin Company: Adobe Inc Integrity Level: HIGH Description: Adobe Download Manager Exit code: 0 Version: 3.0.0.779s Modules
| |||||||||||||||
| 1412 | "C:\WINDOWS\system32\cmd.exe" /c del "C:\WINDOWS\system32\Macromed\Temp\{58156E61-BC9C-460D-BFEA-A831FAD4B529}\InstallFlashPlayer.exe" >> NUL | C:\Windows\System32\cmd.exe | — | InstallFlashPlayer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1780 | "C:\WINDOWS\system32\cmd.exe" /c del "C:\Users\admin\AppData\Local\Adobe\0B7EA111-511D-4C73-B127-81235B44F5D9\3A5493D9-0355-4DD2-8A28-2DE34E241149\9EAE2BD9-AAA9-4CAE-A4EB-789D2F55BC14" >> NUL | C:\Windows\SysWOW64\cmd.exe | — | 9EAE2BD9-AAA9-4CAE-A4EB-789D2F55BC14 | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1848 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --string-annotations --field-trial-handle=4984,i,15672900476520135910,11554273429689138297,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=5252 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2144 | "C:\Users\admin\AppData\Local\Adobe\0B7EA111-511D-4C73-B127-81235B44F5D9\1AAEA9CB-04C3-4105-B1CC-4253085E358A\2DD5FDE0-0B2E-416E-A9DB-69E1DE8D34E7" /S=0 /InstallPath="C:\Program Files (x86)\FlashCenter" /TaskBarShortcut=1 /Bootup=1 /DeskShortcut=1 /SetDefaultProgram=0 | C:\Users\admin\AppData\Local\Adobe\0B7EA111-511D-4C73-B127-81235B44F5D9\1AAEA9CB-04C3-4105-B1CC-4253085E358A\2DD5FDE0-0B2E-416E-A9DB-69E1DE8D34E7 | flash.exe | ||||||||||||
User: admin Company: Chongqing Zhongcheng Network Technology Co., Ltd Integrity Level: HIGH Description: FlashCenter Installer Exit code: 0 Version: 3.8.4.9 Modules
| |||||||||||||||
| 2228 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | taskkill.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2228 | "C:\Program Files (x86)\FlashCenter\FCBrowser.exe" --type=renderer --no-sandbox --autoplay-policy=no-user-gesture-required --enable-experimental-web-platform-features --force-device-scale-factor=1 --log-file="C:\Program Files (x86)\FlashCenter\debug.log" --override-plugin-power-saver-for-testing=never --field-trial-handle=1816,17445149089644190158,13576866833897559164,131072 --enable-features=CastMediaRouteProvider,CookieDeprecationMessages,CrossOriginEmbedderPolicy,CrossOriginOpenerPolicy,DocumentPolicy,FeaturePolicyForClientHints,OriginIsolationHeader,OriginPolicy,UserAgentClientHint --disable-features=OutOfBlinkCors --lang=zh-CN --log-file="C:\Program Files (x86)\FlashCenter\debug.log" --log-severity=disable --user-agent="Mozilla/5.0 (Windows NT 10; W0W64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/83.0.4103.97 Safari/537.36 FCBrowser/3.8.4.9 FCVersion/3.8.4.9" --enable-system-flash --enable-print-preview --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=4 --mojo-platform-channel-handle=2528 /prefetch:1 | C:\Program Files (x86)\FlashCenter\FCBrowser.exe | — | FCBrowser.exe | |||||||||||
User: admin Company: Chongqing Zhongcheng Network Technology Co., Ltd Integrity Level: HIGH Description: FCBrowse Version: 3.8.4.9 Modules
| |||||||||||||||
| 2292 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
45 726
Read events
45 537
Write events
169
Delete events
20
Modification events
| (PID) Process: | (4864) flash.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4864) flash.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4864) flash.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1088) flash.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates |
| Operation: | delete value | Name: | 8094640EB5A7A1CA119C1FDDD59F810263A7FBD1 |
Value: | |||
| (PID) Process: | (1088) flash.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\8094640EB5A7A1CA119C1FDDD59F810263A7FBD1 |
| Operation: | write | Name: | Blob |
Value: 0400000001000000100000004FDD07E4D42264391E0C3742EAD1C6AE7A000000010000000C000000300A06082B06010505070309140000000100000014000000AE6C05A39313E2A2E7E2D71CD6C7F07FC86753A06200000001000000200000002CABEAFE37D06CA22ABA7391C0033D25982952C453647349763A3AB5AD6CCF69090000000100000056000000305406082B0601050507030206082B06010505070303060A2B0601040182370A030C060A2B0601040182370A030406082B0601050507030406082B0601050507030906082B0601050507030106082B06010505070308190000000100000010000000CB9DD0FCEAAA492F75CE292C21BBFBDD0300000001000000140000008094640EB5A7A1CA119C1FDDD59F810263A7FBD10F0000000100000030000000EA09C51D4C3A334CE4ACD2BC08C6A9BE352E334F45C4FCCFCAB63EDB9F82DC87D4BD2ED2FADAE11163FB954809984FF153000000010000007E000000307C301F06092B06010401A032010130123010060A2B0601040182373C0101030200C0301F06092B06010401A032010230123010060A2B0601040182373C0101030200C0301B060567810C010130123010060A2B0601040182373C0101030200C0301B060567810C010330123010060A2B0601040182373C0101030200C00B000000010000003000000047006C006F00620061006C005300690067006E00200052006F006F00740020004300410020002D0020005200360000007F0000000100000016000000301406082B0601050507030306082B060105050703091D0000000100000010000000521F5C98970D19A8E515EF6EEB6D48EF7E00000001000000080000000080C82B6886D701200000000100000087050000308205833082036BA003020102020E45E6BB038333C3856548E6FF4551300D06092A864886F70D01010C0500304C3120301E060355040B1317476C6F62616C5369676E20526F6F74204341202D20523631133011060355040A130A476C6F62616C5369676E311330110603550403130A476C6F62616C5369676E301E170D3134313231303030303030305A170D3334313231303030303030305A304C3120301E060355040B1317476C6F62616C5369676E20526F6F74204341202D20523631133011060355040A130A476C6F62616C5369676E311330110603550403130A476C6F62616C5369676E30820222300D06092A864886F70D01010105000382020F003082020A02820201009507E873CA66F9EC14CA7B3CF70D08F1B4450B2C82B448C6EB5B3CAE83B841923314A46F7FE92ACCC6B0886BC5B689D1C6B2FF14CE511421EC4ADD1B5AC6D687EE4D3A1506ED64660B9280CA44DE73944EF3A7897F4F786308C812506D42662F4DB979284D521A8A1A80B719810E7EC48ABC644C211C4368D73D3C8AC5B266D5909AB73106C5BEE26D3206A61EF9B9EBAAA3B8BFBE826350D0F01889DFE40F79F5EAA21F2AD2702E7BE7BC93BB6D53E2487C8C100738FF66B277617EE0EA8C3CAAB4A4F6F3954A12076DFD8CB289CFD0A06177C85874B0D4233AF75D3ACAA2DB9D09DE5D442D90F181CD5792FA7EBC50046334DF6B9318BE6B36B239E4AC2436B7F0EFB61C135793B6DEB2F8E285B773A2B835AA45F2E09D36A16F548AF172566E2E88C55142441594EEA3C538969B4E4E5A0B47F30636497730BC7137E5A6EC210875FCE661163F77D5D99197840A6CD4024D74C014EDFD39FB83F25E14A104B00BE9FEEE8FE16E0BB208B36166096AB1063A659659C0F035FDC9DA288D1A118770810AA89A751D9E3A8605009EDB80D625F9DC059E27594C76395BEAF9A5A1D8830FD1FFDF3011F985CF3348F5CA6D64142C7A584FD34B0849C595641A630E793DF5B38CCA58AD9C4245796E0E87195C54B165B6BF8C9BDC13E90D6FB82EDC676EC98B11B584148A0019708379919791D41A27BF371E3207D814633C284CAF0203010001A3633061300E0603551D0F0101FF040403020106300F0603551D130101FF040530030101FF301D0603551D0E04160414AE6C05A39313E2A2E7E2D71CD6C7F07FC86753A0301F0603551D23041830168014AE6C05A39313E2A2E7E2D71CD6C7F07FC86753A0300D06092A864886F70D01010C050003820201008325EDE8D1FD9552CD9EC004A09169E65CD084DEDCADA24FE84778D66598A95BA83C877C028AD16EB71673E65FC05498D574BEC1CDE21191AD23183DDDE1724496B4955EC07B8E99781643135657B3A2B33BB577DC4072ACA3EB9B353EB10821A1E7C443377932BEB5E79C2C4CBC4329998E30D3AC21E0E31DFAD80733765400222AB94D202E7068DAE553FC835CD39DF2FF440C4466F2D2E3BD46001A6D02BA255D8DA13151DD54461C4DDB9996EF1A1C045CA615EF78E079FE5DDB3EAA4C55FD9A15A96FE1A6FBDF7030E9C3EE4246EDC2930589FA7D637B3FD071817C00E898AE0E7834C325FBAF0A9F206BDD3B138F128CE2411A487A73A07769C7B65C7F82C81EFE581B282BA86CAD5E6DC005D27BB7EB80FE2537FE029B68AC425DC3EEF5CCDCF05075D236699CE67B04DF6E0669B6DE0A09485987EB7B14607A64AA6943EF91C74CEC18DD6CEF532D8C99E15EF2723ECF54C8BD67ECA40F4C45FFD3B93023074C8F10BF8696D9995AB499571CA4CCBB158953BA2C050FE4C49E19B11834D54C9DBAEDF71FAF24950478A803BBEE81E5DA5F7C8B4AA1907425A7B33E4BC82C56BDC7C8EF38E25C92F079F79C84BA742D6101207E7ED1F24F07595F8B2D4352EB460C94E1F566477977D5545B1FAD2437CB455A4EA04448C8D8B099C5158409F6D64949C065B8E61A716EA0A8F182E8453E6CD602D70A6783055AC9A410 | |||
| (PID) Process: | (1088) flash.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\8094640EB5A7A1CA119C1FDDD59F810263A7FBD1 |
| Operation: | write | Name: | Blob |
Value: 5C0000000100000004000000001000007E00000001000000080000000080C82B6886D7011D0000000100000010000000521F5C98970D19A8E515EF6EEB6D48EF7F0000000100000016000000301406082B0601050507030306082B060105050703090B000000010000003000000047006C006F00620061006C005300690067006E00200052006F006F00740020004300410020002D00200052003600000053000000010000007E000000307C301F06092B06010401A032010130123010060A2B0601040182373C0101030200C0301F06092B06010401A032010230123010060A2B0601040182373C0101030200C0301B060567810C010130123010060A2B0601040182373C0101030200C0301B060567810C010330123010060A2B0601040182373C0101030200C00F0000000100000030000000EA09C51D4C3A334CE4ACD2BC08C6A9BE352E334F45C4FCCFCAB63EDB9F82DC87D4BD2ED2FADAE11163FB954809984FF10300000001000000140000008094640EB5A7A1CA119C1FDDD59F810263A7FBD1190000000100000010000000CB9DD0FCEAAA492F75CE292C21BBFBDD090000000100000056000000305406082B0601050507030206082B06010505070303060A2B0601040182370A030C060A2B0601040182370A030406082B0601050507030406082B0601050507030906082B0601050507030106082B060105050703086200000001000000200000002CABEAFE37D06CA22ABA7391C0033D25982952C453647349763A3AB5AD6CCF69140000000100000014000000AE6C05A39313E2A2E7E2D71CD6C7F07FC86753A07A000000010000000C000000300A06082B060105050703090400000001000000100000004FDD07E4D42264391E0C3742EAD1C6AE200000000100000087050000308205833082036BA003020102020E45E6BB038333C3856548E6FF4551300D06092A864886F70D01010C0500304C3120301E060355040B1317476C6F62616C5369676E20526F6F74204341202D20523631133011060355040A130A476C6F62616C5369676E311330110603550403130A476C6F62616C5369676E301E170D3134313231303030303030305A170D3334313231303030303030305A304C3120301E060355040B1317476C6F62616C5369676E20526F6F74204341202D20523631133011060355040A130A476C6F62616C5369676E311330110603550403130A476C6F62616C5369676E30820222300D06092A864886F70D01010105000382020F003082020A02820201009507E873CA66F9EC14CA7B3CF70D08F1B4450B2C82B448C6EB5B3CAE83B841923314A46F7FE92ACCC6B0886BC5B689D1C6B2FF14CE511421EC4ADD1B5AC6D687EE4D3A1506ED64660B9280CA44DE73944EF3A7897F4F786308C812506D42662F4DB979284D521A8A1A80B719810E7EC48ABC644C211C4368D73D3C8AC5B266D5909AB73106C5BEE26D3206A61EF9B9EBAAA3B8BFBE826350D0F01889DFE40F79F5EAA21F2AD2702E7BE7BC93BB6D53E2487C8C100738FF66B277617EE0EA8C3CAAB4A4F6F3954A12076DFD8CB289CFD0A06177C85874B0D4233AF75D3ACAA2DB9D09DE5D442D90F181CD5792FA7EBC50046334DF6B9318BE6B36B239E4AC2436B7F0EFB61C135793B6DEB2F8E285B773A2B835AA45F2E09D36A16F548AF172566E2E88C55142441594EEA3C538969B4E4E5A0B47F30636497730BC7137E5A6EC210875FCE661163F77D5D99197840A6CD4024D74C014EDFD39FB83F25E14A104B00BE9FEEE8FE16E0BB208B36166096AB1063A659659C0F035FDC9DA288D1A118770810AA89A751D9E3A8605009EDB80D625F9DC059E27594C76395BEAF9A5A1D8830FD1FFDF3011F985CF3348F5CA6D64142C7A584FD34B0849C595641A630E793DF5B38CCA58AD9C4245796E0E87195C54B165B6BF8C9BDC13E90D6FB82EDC676EC98B11B584148A0019708379919791D41A27BF371E3207D814633C284CAF0203010001A3633061300E0603551D0F0101FF040403020106300F0603551D130101FF040530030101FF301D0603551D0E04160414AE6C05A39313E2A2E7E2D71CD6C7F07FC86753A0301F0603551D23041830168014AE6C05A39313E2A2E7E2D71CD6C7F07FC86753A0300D06092A864886F70D01010C050003820201008325EDE8D1FD9552CD9EC004A09169E65CD084DEDCADA24FE84778D66598A95BA83C877C028AD16EB71673E65FC05498D574BEC1CDE21191AD23183DDDE1724496B4955EC07B8E99781643135657B3A2B33BB577DC4072ACA3EB9B353EB10821A1E7C443377932BEB5E79C2C4CBC4329998E30D3AC21E0E31DFAD80733765400222AB94D202E7068DAE553FC835CD39DF2FF440C4466F2D2E3BD46001A6D02BA255D8DA13151DD54461C4DDB9996EF1A1C045CA615EF78E079FE5DDB3EAA4C55FD9A15A96FE1A6FBDF7030E9C3EE4246EDC2930589FA7D637B3FD071817C00E898AE0E7834C325FBAF0A9F206BDD3B138F128CE2411A487A73A07769C7B65C7F82C81EFE581B282BA86CAD5E6DC005D27BB7EB80FE2537FE029B68AC425DC3EEF5CCDCF05075D236699CE67B04DF6E0669B6DE0A09485987EB7B14607A64AA6943EF91C74CEC18DD6CEF532D8C99E15EF2723ECF54C8BD67ECA40F4C45FFD3B93023074C8F10BF8696D9995AB499571CA4CCBB158953BA2C050FE4C49E19B11834D54C9DBAEDF71FAF24950478A803BBEE81E5DA5F7C8B4AA1907425A7B33E4BC82C56BDC7C8EF38E25C92F079F79C84BA742D6101207E7ED1F24F07595F8B2D4352EB460C94E1F566477977D5545B1FAD2437CB455A4EA04448C8D8B099C5158409F6D64949C065B8E61A716EA0A8F182E8453E6CD602D70A6783055AC9A410 | |||
| (PID) Process: | (2144) 2DD5FDE0-0B2E-416E-A9DB-69E1DE8D34E7 | Key: | HKEY_CURRENT_USER\SOFTWARE\FlashCenter\UserData |
| Operation: | write | Name: | zcid2 |
Value: B4F2EF8E40D23AEB8FF7D50D06DAA6B2 | |||
| (PID) Process: | (2144) 2DD5FDE0-0B2E-416E-A9DB-69E1DE8D34E7 | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\FlashCenter |
| Operation: | write | Name: | DisplayName |
Value: FlashCenter | |||
| (PID) Process: | (2144) 2DD5FDE0-0B2E-416E-A9DB-69E1DE8D34E7 | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\FlashCenter |
| Operation: | write | Name: | UninstallString |
Value: C:\Program Files (x86)\FlashCenter\FlashCenterUninst.exe | |||
| (PID) Process: | (2144) 2DD5FDE0-0B2E-416E-A9DB-69E1DE8D34E7 | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\FlashCenter |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files (x86)\FlashCenter\FlashCenter.exe | |||
Executable files
128
Suspicious files
132
Text files
425
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7592 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old~RFfdf1c.TMP | — | |
MD5:— | SHA256:— | |||
| 7592 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7592 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RFfdf2b.TMP | — | |
MD5:— | SHA256:— | |||
| 7592 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7592 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old~RFfdf2b.TMP | — | |
MD5:— | SHA256:— | |||
| 7592 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7592 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RFfdf3b.TMP | — | |
MD5:— | SHA256:— | |||
| 7592 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RFfdf3b.TMP | — | |
MD5:— | SHA256:— | |||
| 7592 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SignalDB\LOG.old~RFfdf3b.TMP | — | |
MD5:— | SHA256:— | |||
| 7592 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
330
TCP/UDP connections
172
DNS requests
86
Threats
17
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7860 | chrome.exe | GET | 200 | 142.250.185.106:443 | https://safebrowsingohttpgateway.googleapis.com/v1/ohttp/hpkekeyconfig?key=AIzaSyA2KlwBX3mkFo30om9LUFYQhpqLoa_BNhE | unknown | binary | 41 b | whitelisted |
7860 | chrome.exe | GET | 200 | 142.251.140.174:80 | http://clients2.google.com/time/1/current?cup2key=8:WHT1ix3XpKeg11dUj72gEGakQYDP3KIatu34CnY4kNk&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
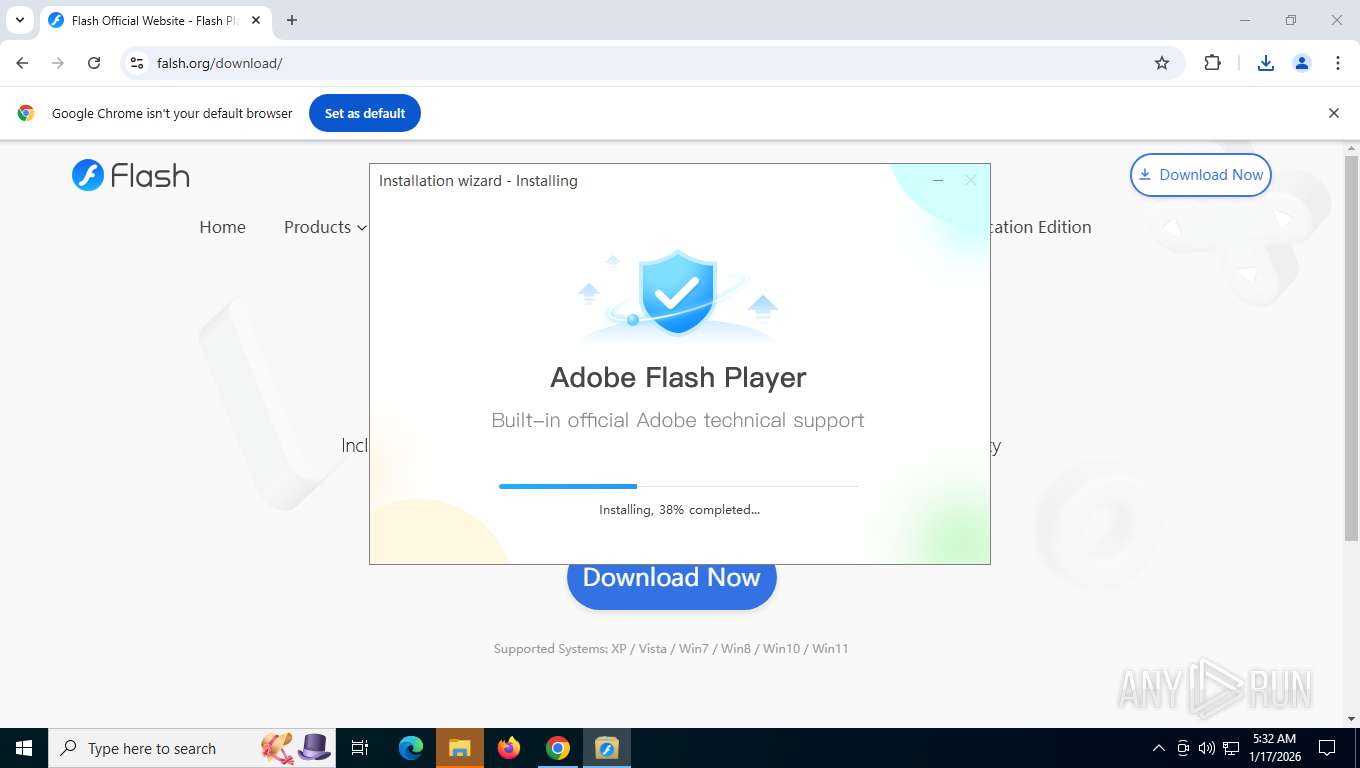
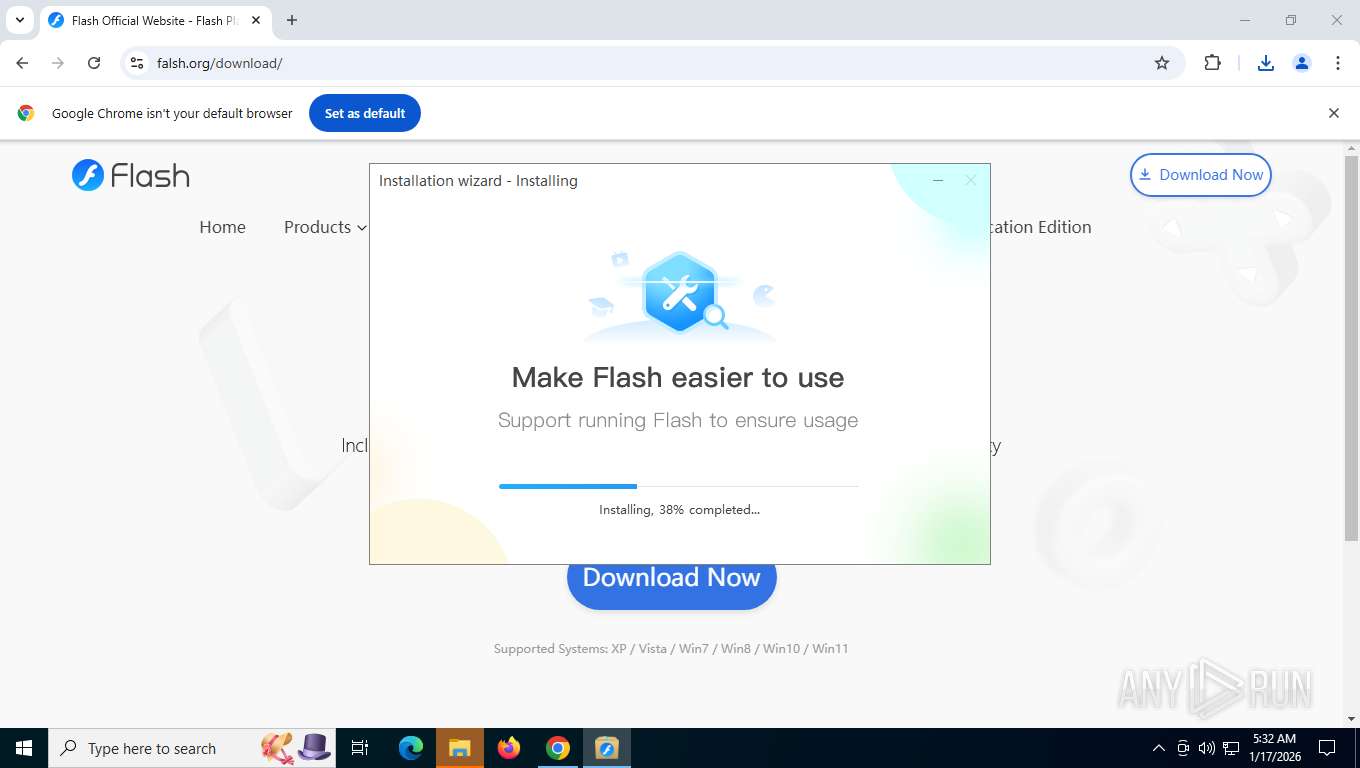
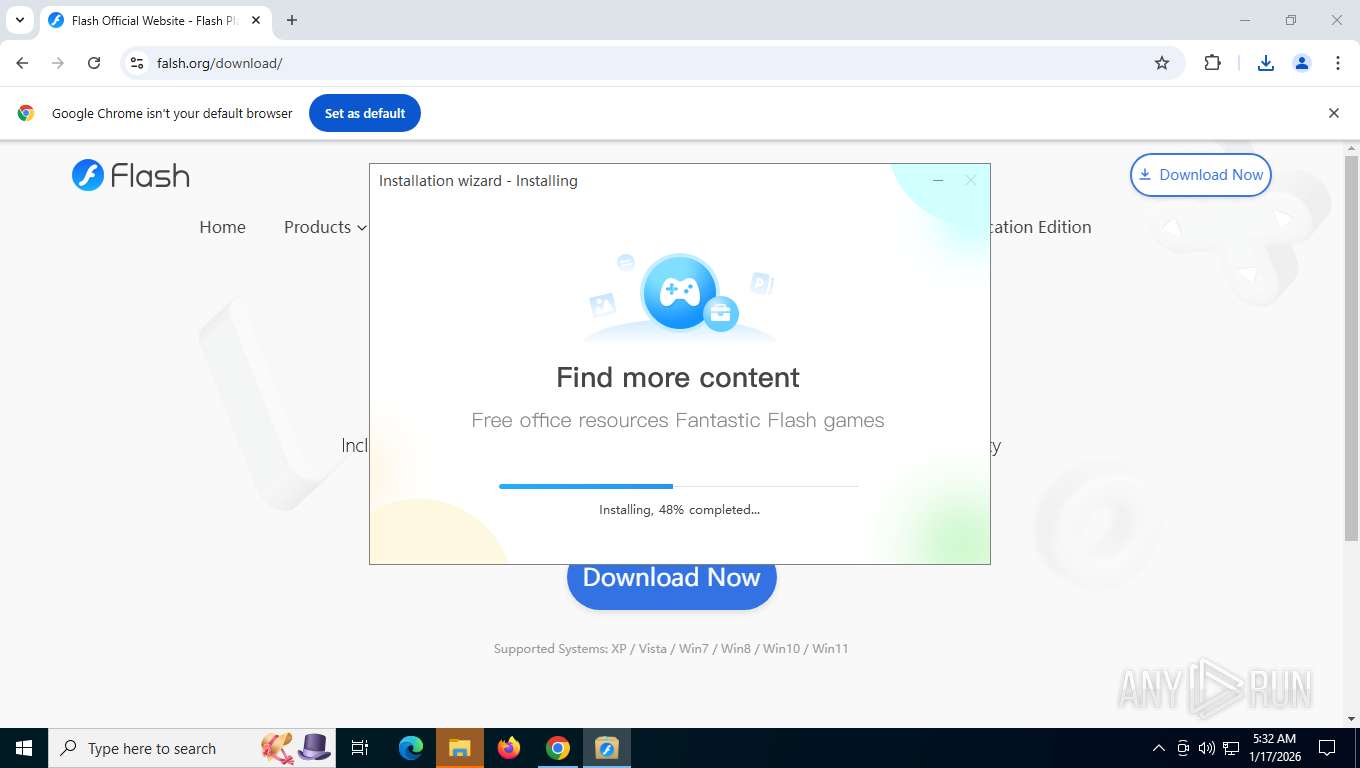
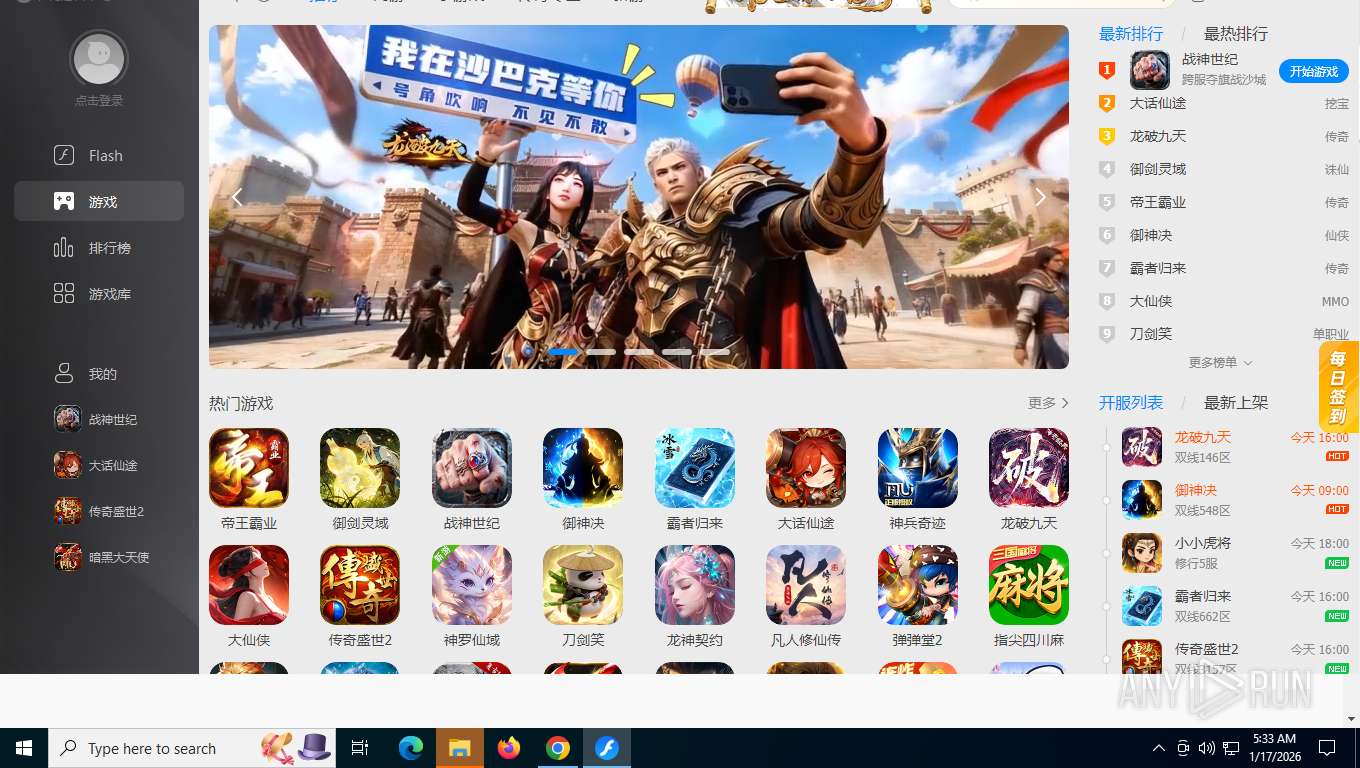
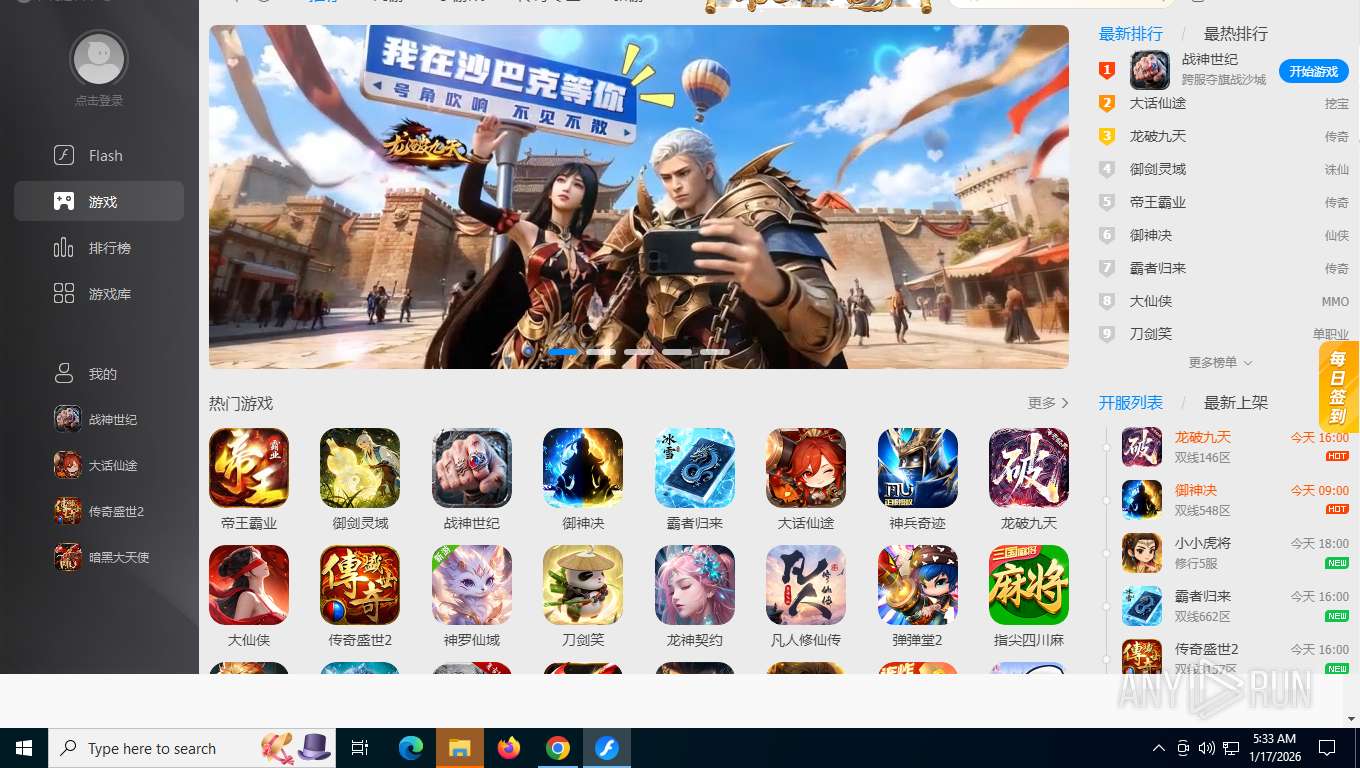
7860 | chrome.exe | GET | 200 | 188.114.97.3:443 | https://falsh.org/ | unknown | html | 191 b | unknown |
7860 | chrome.exe | POST | 200 | 142.251.168.84:443 | https://accounts.google.com/ListAccounts?gpsia=1&source=ChromiumBrowser&json=standard | unknown | text | 17 b | whitelisted |
7860 | chrome.exe | GET | 200 | 188.114.97.3:443 | https://falsh.org/flash.js | unknown | html | 46.3 Kb | unknown |
7860 | chrome.exe | GET | 200 | 188.114.97.3:443 | https://falsh.org/favicon.ico | unknown | html | 191 b | unknown |
7860 | chrome.exe | GET | 200 | 104.17.25.14:443 | https://cdnjs.cloudflare.com/ajax/libs/jquery/2.0.0/jquery.min.js | unknown | text | 81.1 Kb | unknown |
7860 | chrome.exe | GET | 200 | 104.17.25.14:443 | https://cdnjs.cloudflare.com/ajax/libs/layer/3.1.1/theme/default/layer.css?v=3.1.1 | unknown | text | 14.0 Kb | unknown |
7860 | chrome.exe | GET | 200 | 104.16.175.226:443 | https://cdn.jsdelivr.net/npm/bootstrap@3.3.7/dist/css/bootstrap.min.css | unknown | text | 118 Kb | whitelisted |
7860 | chrome.exe | GET | 200 | 104.17.25.14:443 | https://cdnjs.cloudflare.com/ajax/libs/layer/3.1.1/layer.js | unknown | text | 21.6 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5636 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
6768 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3656 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
7860 | chrome.exe | 142.251.140.174:80 | clients2.google.com | GOOGLE | US | whitelisted |
7860 | chrome.exe | 142.250.185.106:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
7860 | chrome.exe | 142.251.168.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
7860 | chrome.exe | 188.114.97.3:443 | falsh.org | CLOUDFLARENET | US | whitelisted |
7860 | chrome.exe | 104.17.25.14:443 | cdnjs.cloudflare.com | CLOUDFLARENET | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
falsh.org |
| malicious |
accounts.google.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
cdn.jsdelivr.net |
| whitelisted |
client.wns.windows.com |
| whitelisted |
www.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7860 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7860 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7860 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7860 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7860 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7860 | chrome.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing Domain (falsh .org) |
7860 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
— | — | Potentially Bad Traffic | ET INFO PE EXE or DLL Windows file download HTTP |
2292 | svchost.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Cloudflare Tunneling Service observed (.trycloudflare .com) |
Process | Message |
|---|---|
FlashCenter.exe | QObject::connect: Cannot connect CUrlEvent::signalUrlFinished(QString) to (nullptr)::(nullptr)
|
FlashCenter.exe | QObject::connect: Cannot connect CUrlEvent::signalUrlError(QString) to (nullptr)::(nullptr)
|
FlashCenter.exe | QObject::connect: Cannot connect CUrlEvent::signalUrlSSLError(QString) to (nullptr)::(nullptr)
|
FlashCenter.exe | QObject::connect: Cannot connect CUrlEvent::signalUrlFinished(QString) to (nullptr)::(nullptr)
|
FlashCenter.exe | QObject::connect: Cannot connect CUrlEvent::signalUrlError(QString) to (nullptr)::(nullptr)
|
FlashCenter.exe | QObject::connect: Cannot connect CUrlEvent::signalUrlSSLError(QString) to (nullptr)::(nullptr)
|
FlashCenter.exe | QString::arg: Argument missing: QPushButton{font: 9pt "Microsoft YaHei UI";color:#444444;background-color:#FFFFFF;text-align:left;padding-left:16px;width:128px;height:32px;border: 0px; },
|
FlashCenter.exe | QObject::connect: Cannot connect CUrlEvent::signalUrlFinished(QString) to (nullptr)::(nullptr)
|
FlashCenter.exe | QObject::connect: Cannot connect CUrlEvent::signalUrlError(QString) to (nullptr)::(nullptr)
|
FlashCenter.exe | QObject::connect: Cannot connect CUrlEvent::signalUrlSSLError(QString) to (nullptr)::(nullptr)
|