| File name: | spdodoma file |
| Full analysis: | https://app.any.run/tasks/955b18f8-703e-405c-bdf6-3499b1d44ff2 |
| Verdict: | Malicious activity |
| Threats: | LokiBot was developed in 2015 to steal information from a variety of applications. Despite the age, this malware is still rather popular among cybercriminals. |
| Analysis date: | December 14, 2024, 04:56:35 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 89A540C5020696145C39F95831062D9A |
| SHA1: | 982F4B68DE9E748EED54EFF90EB9B4D9BC7D5310 |
| SHA256: | 195A93F95CB67C7A9DEC944517DADBA693262322AFEF87C9DB7AE1CE5DD13F45 |
| SSDEEP: | 3072:ihZ0ojlaGFp+MsXrEAXIYZmKlId+xp0zd6yQyqrZVKOifjgMXD+MsFIOe3vGhg2+:WlVF6XrDFZQ4kUyxqrZo7dDfsSVS |
MALICIOUS
Actions looks like stealing of personal data
- spdodoma file.exe (PID: 5876)
Scans artifacts that could help determine the target
- spdodoma file.exe (PID: 5876)
Uses Task Scheduler to run other applications
- spdodoma file.exe (PID: 4592)
Steals credentials from Web Browsers
- spdodoma file.exe (PID: 5876)
Lokibot is detected
- spdodoma file.exe (PID: 5876)
SUSPICIOUS
Reads security settings of Internet Explorer
- spdodoma file.exe (PID: 4592)
- spdodoma file.exe (PID: 5876)
Executable content was dropped or overwritten
- spdodoma file.exe (PID: 4592)
- spdodoma file.exe (PID: 5876)
Application launched itself
- spdodoma file.exe (PID: 4592)
INFO
Checks supported languages
- spdodoma file.exe (PID: 4592)
- spdodoma file.exe (PID: 5876)
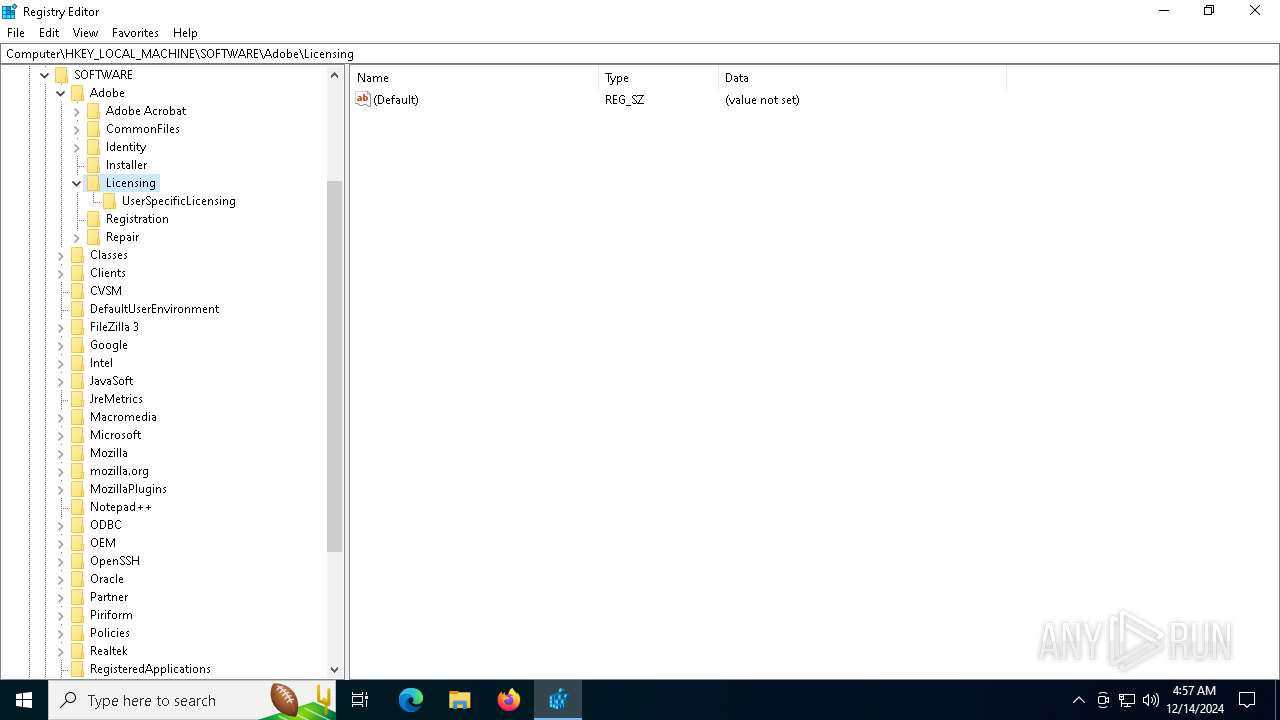
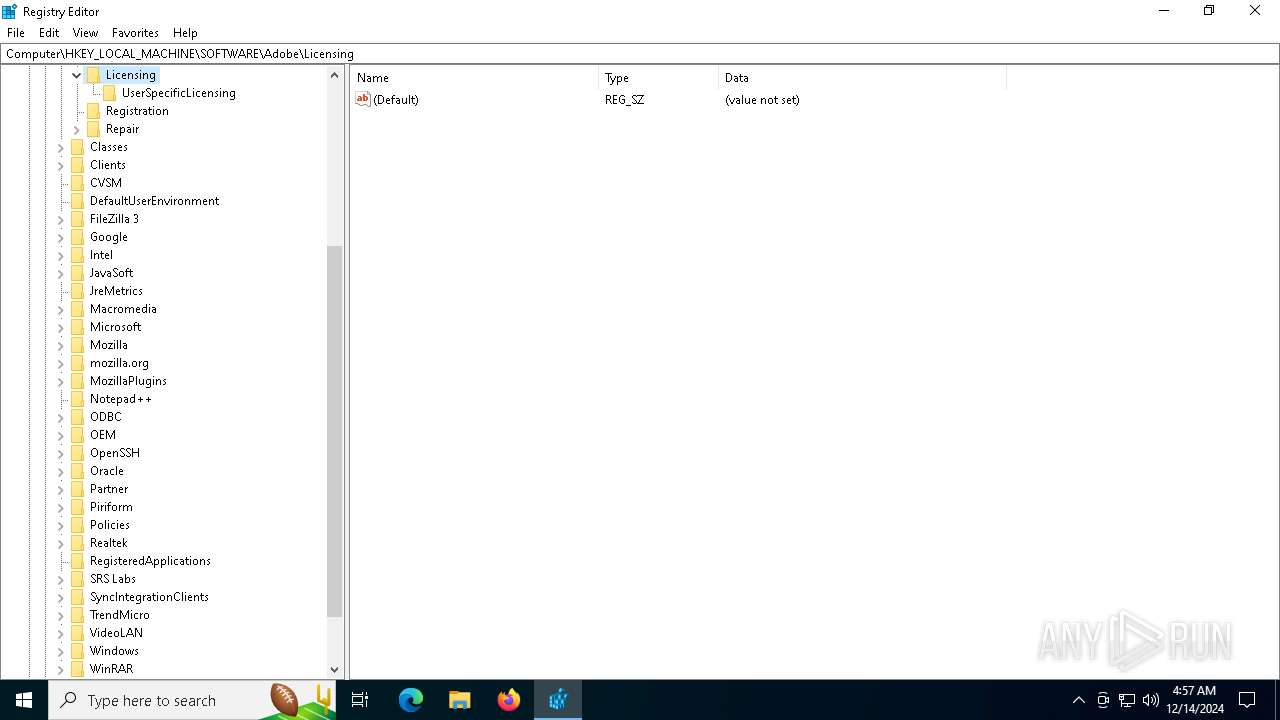
Reads the machine GUID from the registry
- spdodoma file.exe (PID: 4592)
- spdodoma file.exe (PID: 5876)
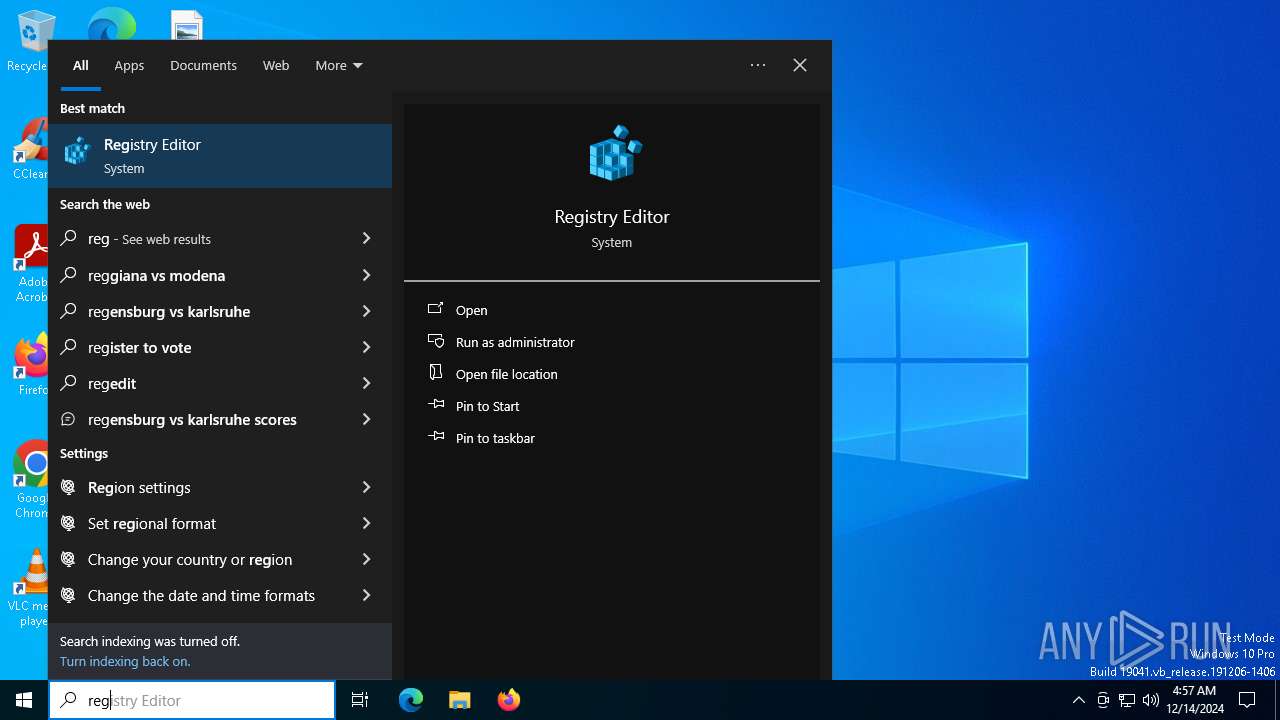
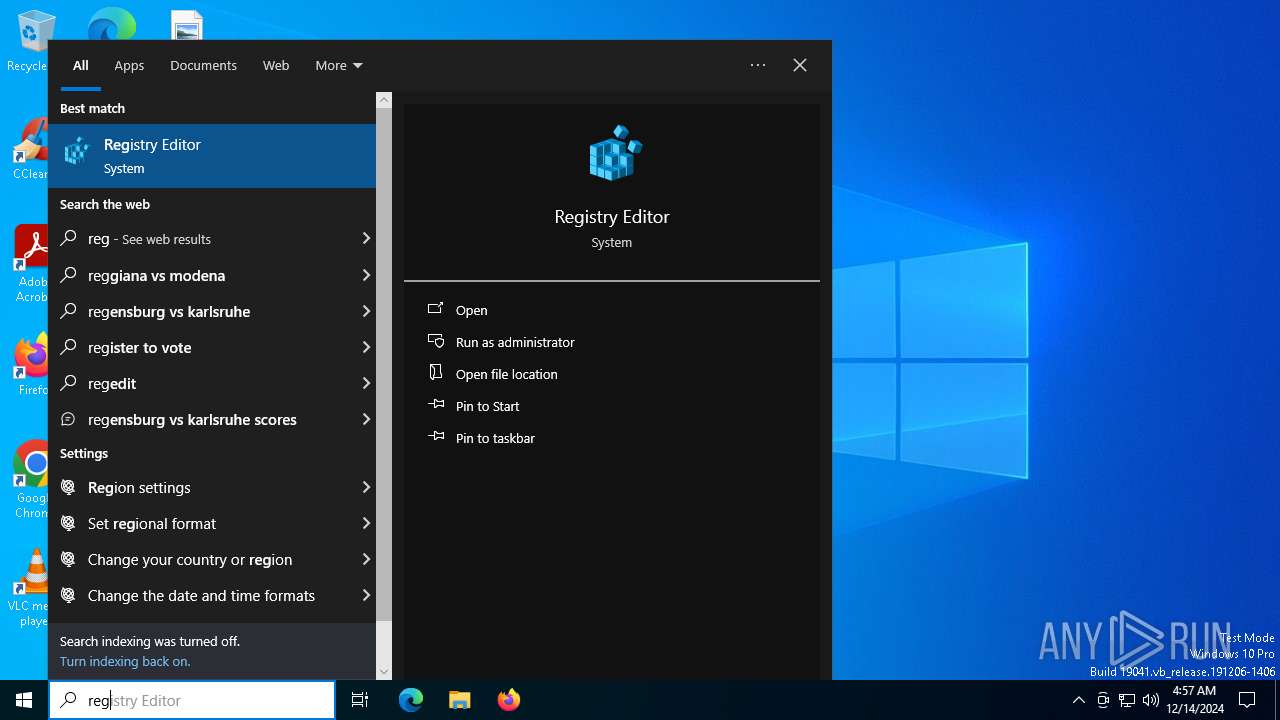
Manual execution by a user
- EXCEL.EXE (PID: 7156)
- regedit.exe (PID: 6844)
- regedit.exe (PID: 6764)
Create files in a temporary directory
- spdodoma file.exe (PID: 4592)
Reads the computer name
- spdodoma file.exe (PID: 4592)
- spdodoma file.exe (PID: 5876)
Creates files or folders in the user directory
- spdodoma file.exe (PID: 4592)
- spdodoma file.exe (PID: 5876)
The process uses the downloaded file
- spdodoma file.exe (PID: 4592)
Reads Microsoft Office registry keys
- spdodoma file.exe (PID: 5876)
Process checks computer location settings
- spdodoma file.exe (PID: 4592)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:06:14 21:34:40+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 207872 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x34be6 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | Blobs |
| FileVersion: | 1.0.0.0 |
| InternalName: | xdVjexggnmq.exe |
| LegalCopyright: | Copyright © 2016 |
| LegalTrademarks: | - |
| OriginalFileName: | xdVjexggnmq.exe |
| ProductName: | Blobs |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
139
Monitored processes
7
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 4592 | "C:\Users\admin\AppData\Local\Temp\spdodoma file.exe" | C:\Users\admin\AppData\Local\Temp\spdodoma file.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Blobs Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 5876 | "{path}" | C:\Users\admin\AppData\Local\Temp\spdodoma file.exe | spdodoma file.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Blobs Version: 1.0.0.0 Modules
| |||||||||||||||
| 6520 | "C:\Windows\System32\schtasks.exe" /Create /TN "Updates\InXkDgYILVBq" /XML "C:\Users\admin\AppData\Local\Temp\tmpD7D5.tmp" | C:\Windows\SysWOW64\schtasks.exe | — | spdodoma file.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6524 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | schtasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6764 | "C:\WINDOWS\regedit.exe" | C:\Windows\regedit.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Editor Exit code: 3221226540 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6844 | "C:\WINDOWS\regedit.exe" | C:\Windows\regedit.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Editor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7156 | "C:\Program Files\Microsoft Office\root\Office16\EXCEL.EXE" | C:\Program Files\Microsoft Office\root\Office16\EXCEL.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Version: 16.0.16026.20146 Modules
| |||||||||||||||
Total events
8 312
Read events
7 923
Write events
370
Delete events
19
Modification events
| (PID) Process: | (7156) EXCEL.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\ClientTelemetry\Sampling |
| Operation: | write | Name: | 1 |
Value: 01D014000000001000B24E9A3E02000000000000000600000000000000 | |||
| (PID) Process: | (7156) EXCEL.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common |
| Operation: | write | Name: | SessionId |
Value: B1F454B03AE5F140A0A42C7DB0A7C114 | |||
| (PID) Process: | (7156) EXCEL.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Excel |
| Operation: | write | Name: | FontInfoCache |
Value: 6000000060000000F5FFFFFF0000000000000000000000009001000000000000000000205400610068006F006D00610000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000050000001B000000000000000D0000000B000000020000000200000000000000330000000000000000000000F5FFFFFF0000000000000000000000009001000000000000000000205300650067006F006500200055004900000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000060000001C000000000000000D0000000B000000020000000200000000000000330000000000000000000000F5FFFFFF000000000000000000000000BC02000000000000000000205400610068006F006D006100000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000600000020000000000000000D0000000B000000020000000200000000000000330000000000000000000000F3FFFFFF0000000000000000000000009001000000000000000000005400610068006F006D00610000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000060000002000000000000000100000000D000000030000000300000000000000330000000000000000000000F3FFFFFF000000000000000000000000E803000000000000000000005400610068006F006D00610000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000070000002600000000000000100000000D000000030000000300000000000000330000000000000000000000F1FFFFFF000000000000000000000000900100000000000000000000430061006C0069006200720069000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000080000001A00000000000000120000000E000000040000000300000000000000330000000000000000000000F3FFFFFF0000000000000000000000009001000000000000000000005300650067006F006500200055004900000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000070000002100000000000000110000000E000000030000000400000000000000330000000000000000000000F3FFFFFF000000000000000000000000BC02000000000000000000005300650067006F006500200055004900000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000080000002100000000000000110000000E000000030000000400000000000000330000000000000000000000F3FFFFFF0000000000000000000000009001000000000000000000205300650067006F006500200055004900000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000070000002100000000000000110000000E000000030000000400000000000000330000000000000000000000F3FFFFFF000000000000000000000000BC02000000000000000000205300650067006F006500200055004900000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000080000002100000000000000110000000E000000030000000400000000000000330000000000000000000000F5FFFFFF0000000000000000000000009001000000000000000000205300650067006F006500200055004900000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000060000001C000000000000000D0000000B000000020000000200000000000000330000000000000000000000F1FFFFFF000000000000000000000000900100000000000000000000430061006C0069006200720069000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000080000001A00000000000000120000000E000000040000000300000000000000330000000000000000000000F5FFFFFF0000000000000000000000009001000000000000000000205300650067006F006500200055004900000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000060000001C000000000000000D0000000B000000020000000200000000000000330000000000000000000000F5FFFFFF0000000000000000000000009001000000000000000000205400610068006F006D00610000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000050000001B000000000000000D0000000B000000020000000200000000000000330000000000000000000000F5FFFFFF000000000000000000000000BC02000000000000000000205300650067006F006500200055004900000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000060000001C000000000000000D0000000B000000020000000200000000000000330000000000000000000000F1FFFFFF000000000000000000000000900100000000000000000000430061006C0069006200720069000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000080000001A00000000000000120000000E000000040000000300000000000000330000000000000000000000F3FFFFFF000000000000000000000000BC02000000000000000000005300650067006F006500200055004900000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000080000002100000000000000110000000E000000030000000400000000000000330000000000000000000000 | |||
| (PID) Process: | (7156) EXCEL.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\Internet\WebServiceCache\AllUsers\officeclient.microsoft.com\config16--lcid=1033&syslcid=1033&uilcid=1033&build=16.0.16026&crev=3\0 |
| Operation: | write | Name: | StartDate |
Value: 90ADC9A2E44DDB01 | |||
| (PID) Process: | (7156) EXCEL.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\Internet\WebServiceCache\AllUsers\officeclient.microsoft.com\config16--lcid=1033&syslcid=1033&uilcid=1033&build=16.0.16026&crev=3\0 |
| Operation: | write | Name: | EndDate |
Value: 906D33CDAD4EDB01 | |||
| (PID) Process: | (7156) EXCEL.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\CrashPersistence\EXCEL\7156 |
| Operation: | write | Name: | 0 |
Value: 0B0E109CF8F07F67CE79428D5A186E1925C739230046DF83AF94CABCD3ED016A04102400449A7D64B29D01008500A907556E6B6E6F776EC906022222CA0DC2190000C91003783634C511F437D2120965007800630065006C002E00650078006500C51620C517808004C91808323231322D44656300 | |||
| (PID) Process: | (7156) EXCEL.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | en-US |
Value: 2 | |||
| (PID) Process: | (7156) EXCEL.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | de-de |
Value: 2 | |||
| (PID) Process: | (7156) EXCEL.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | fr-fr |
Value: 2 | |||
| (PID) Process: | (7156) EXCEL.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | es-es |
Value: 2 | |||
Executable files
2
Suspicious files
21
Text files
801
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7156 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\Personalization\Content\Anonymous\Insights.json.tmp | binary | |
MD5:6EE9B773776D2631DD1ABDBC88D05C7A | SHA256:11BAC73BF2E42F44C2EDAA3B474A1711392EEF879193EA1C08C6771336DB4B4A | |||
| 7156 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\DTS\en-US{173A0789-860E-43ED-9DF1-FAEFC8A369EF}\{CC30882F-8BCB-49B9-A12D-0A6F69AC03FC}mt11414620.png | image | |
MD5:E37661AB4A1AEB408D06DDA183117349 | SHA256:0AF5FC368F802B927A820673ACFDE18B22B15DA0CE865203C065604939875A3F | |||
| 7156 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\Personalization\Governance\Anonymous\floodgatecampaigns.json | binary | |
MD5:5EE35AA126592AE4AABC07570116D00C | SHA256:C6D020938C65326BDA1CEFA93BCBD68EB8D3EA56827C9F90F18D92014D0E5CFE | |||
| 7156 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\DTS\en-US{173A0789-860E-43ED-9DF1-FAEFC8A369EF}\{0CDE6E2A-18C3-4E52-9D3F-47A1FF910680}mt10000137.png | image | |
MD5:DE55D11D4C4071BB9F1B2A91487F41BE | SHA256:57733C40F13A9C7F44584AA52F0C1D1DB26C41C0AF73FD3EDD47C3288B85E892 | |||
| 7156 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\FontCache\4\Catalog\ListAll.Json | binary | |
MD5:C37972CBD8748E2CA6DA205839B16444 | SHA256:D4CFBB0E8B9D3E36ECE921B9B51BD37EF1D3195A9CFA1C4586AEA200EB3434A7 | |||
| 7156 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\WebServiceCache\AllUsers\officeclient.microsoft.com\923227A1-A945-416E-86C5-F8C7A865548E | xml | |
MD5:8C8A1A41BB2315191FA474D88F17062C | SHA256:2C5BCEE2DF1D3B1434C4622A97E23B9EDE6576E81358A6E5021AB151F6E8C7F9 | |||
| 7156 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\FontCache\4\PreviewFont\flat_officeFontsPreview_4_40.ttf | pi2 | |
MD5:4296A064B917926682E7EED650D4A745 | SHA256:E04E41C74D6C78213BA1588BACEE64B42C0EDECE85224C474A714F39960D8083 | |||
| 7156 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\DTS\en-US{173A0789-860E-43ED-9DF1-FAEFC8A369EF}\{0B3316E7-8895-4777-9774-2BB558FDC03B}mt16400647.png | image | |
MD5:D3590428E83DC27B626978EC0867477A | SHA256:6B7382E1BF3F58C62F21300DA74F13C649C46BC0FC244188371BA55C56B6117D | |||
| 7156 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\Personalization\Governance\Anonymous\floodgatecampaigns.json.tmp | binary | |
MD5:5EE35AA126592AE4AABC07570116D00C | SHA256:C6D020938C65326BDA1CEFA93BCBD68EB8D3EA56827C9F90F18D92014D0E5CFE | |||
| 7156 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\089d66ba04a8cec4bdc5267f42f39cf84278bb67.tbres | binary | |
MD5:65465C84C49F0E1FA70C85A926164A03 | SHA256:3FFA212FD8142FC28DCCBD64D4517D804487F725F17F74E53B7B9AC4B1CAA67D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
62
DNS requests
42
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
556 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
4504 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7156 | EXCEL.EXE | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
7156 | EXCEL.EXE | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4504 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 104.126.37.131:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
1176 | svchost.exe | 20.190.159.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |