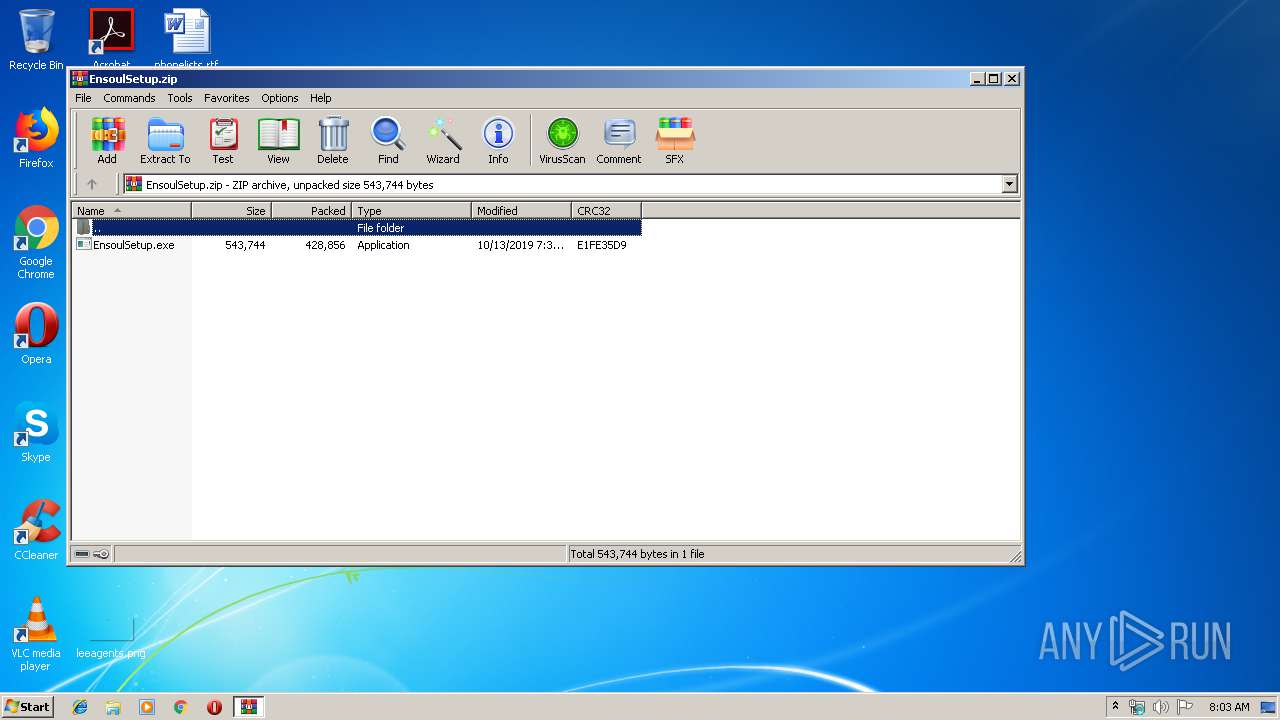
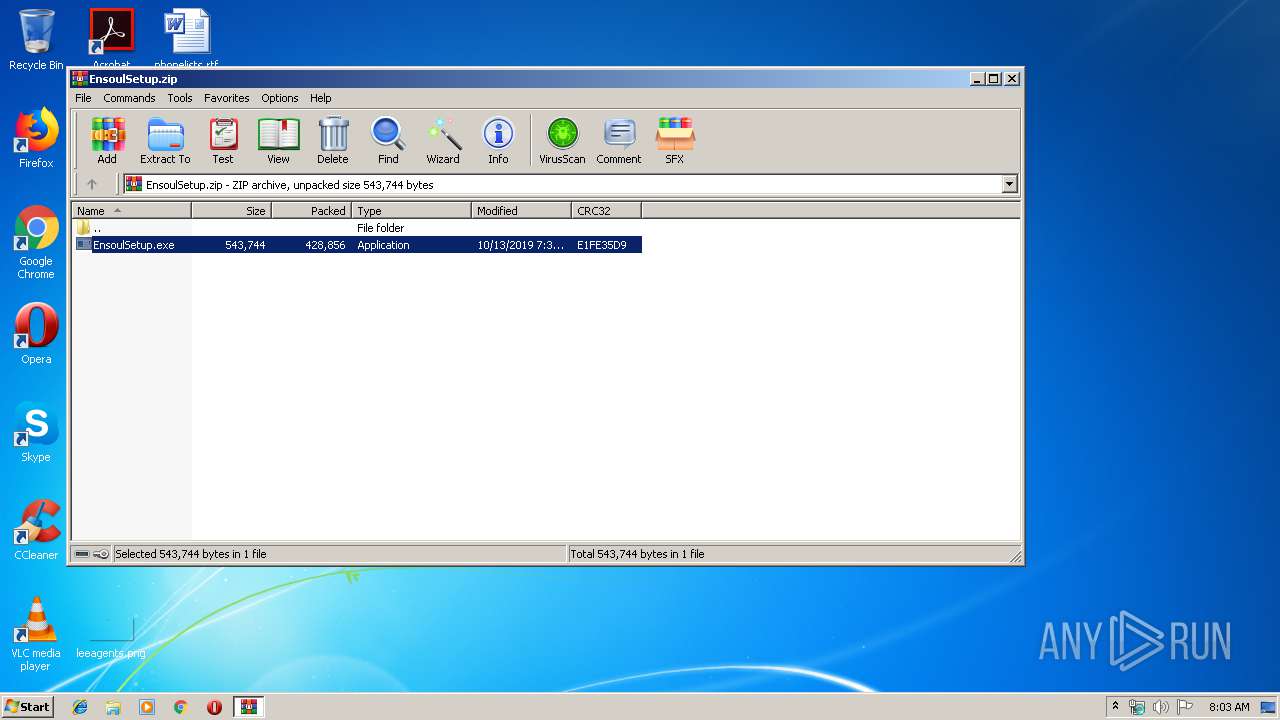
| File name: | EnsoulSetup.zip |
| Full analysis: | https://app.any.run/tasks/076fe394-2372-4386-95d5-1437ace2c285 |
| Verdict: | Malicious activity |
| Threats: | Quasar is a very popular RAT in the world thanks to its code being available in open-source. This malware can be used to control the victim’s computer remotely. |
| Analysis date: | October 14, 2019, 07:03:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 3FCB16438D7670A94277C447C77D8A0F |
| SHA1: | 0B8110465CCBC60D978CF44ACB9BA13458197959 |
| SHA256: | 195574E4E9A81E8200A6994B1C8F63BB7920E0141449FB3AB4A92B548CDFD0E6 |
| SSDEEP: | 12288:HB8AUaX+rS/Q/iFVvNjG1IHXH/voWRsE4rZS3:ifg+PKFt53H/6rZo |
MALICIOUS
Application was dropped or rewritten from another process
- EnsoulSetup.exe (PID: 3920)
- winlog.exe (PID: 1416)
- winlog.exe (PID: 1608)
- EnsoulSetup.exe (PID: 3212)
QUASAR was detected
- EnsoulSetup.exe (PID: 3212)
- winlog.exe (PID: 1416)
Changes the autorun value in the registry
- EnsoulSetup.exe (PID: 3212)
- powershell.exe (PID: 1800)
- winlog.exe (PID: 1416)
- powershell.exe (PID: 2604)
Runs PING.EXE for delay simulation
- cmd.exe (PID: 2236)
SUSPICIOUS
Executes PowerShell scripts
- EnsoulSetup.exe (PID: 3920)
- winlog.exe (PID: 1608)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 944)
- EnsoulSetup.exe (PID: 3920)
- EnsoulSetup.exe (PID: 3212)
- winlog.exe (PID: 1608)
Creates files in the user directory
- EnsoulSetup.exe (PID: 3212)
- powershell.exe (PID: 1800)
- powershell.exe (PID: 2604)
- EnsoulSetup.exe (PID: 3920)
Checks for external IP
- EnsoulSetup.exe (PID: 3212)
- winlog.exe (PID: 1416)
Application launched itself
- winlog.exe (PID: 1608)
- EnsoulSetup.exe (PID: 3920)
Starts CMD.EXE for commands execution
- winlog.exe (PID: 1416)
Starts application with an unusual extension
- cmd.exe (PID: 2236)
Starts itself from another location
- EnsoulSetup.exe (PID: 3212)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:10:13 21:34:06 |
| ZipCRC: | 0xe1fe35d9 |
| ZipCompressedSize: | 428856 |
| ZipUncompressedSize: | 543744 |
| ZipFileName: | EnsoulSetup.exe |
Total processes
47
Monitored processes
10
Malicious processes
5
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 944 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\EnsoulSetup.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1416 | "C:\Users\admin\AppData\Roaming\Winlog\winlog.exe" | C:\Users\admin\AppData\Roaming\Winlog\winlog.exe | winlog.exe | ||||||||||||
User: admin Company: Google Chrome Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 67.0.100.99 Modules
| |||||||||||||||
| 1608 | "C:\Users\admin\AppData\Roaming\Winlog\winlog.exe" | C:\Users\admin\AppData\Roaming\Winlog\winlog.exe | EnsoulSetup.exe | ||||||||||||
User: admin Company: Google Chrome Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 67.0.100.99 Modules
| |||||||||||||||
| 1800 | "powershell.exe" Remove-ItemProperty -Path 'HKCU:\SOFTWARE\Microsoft\Windows\CurrentVersion\Run' -Name 'opsrv';New-ItemProperty -Path 'HKCU:\SOFTWARE\Microsoft\Windows\CurrentVersion\Run' -Name 'opsrv' -Value '"C:\Users\admin\AppData\Roaming\chome_exe\opsrv.exe"' -PropertyType 'String' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | winlog.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2236 | cmd /c ""C:\Users\admin\AppData\Local\Temp\DFdX2jtb50jK.bat" " | C:\Windows\system32\cmd.exe | — | winlog.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2604 | "powershell.exe" Remove-ItemProperty -Path 'HKCU:\SOFTWARE\Microsoft\Windows\CurrentVersion\Run' -Name 'opsrv';New-ItemProperty -Path 'HKCU:\SOFTWARE\Microsoft\Windows\CurrentVersion\Run' -Name 'opsrv' -Value '"C:\Users\admin\AppData\Roaming\chome_exe\opsrv.exe"' -PropertyType 'String' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | EnsoulSetup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3112 | chcp 65001 | C:\Windows\system32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3212 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa944.12613\EnsoulSetup.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa944.12613\EnsoulSetup.exe | EnsoulSetup.exe | ||||||||||||
User: admin Company: Google Chrome Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 67.0.100.99 Modules
| |||||||||||||||
| 3920 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa944.12613\EnsoulSetup.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa944.12613\EnsoulSetup.exe | WinRAR.exe | ||||||||||||
User: admin Company: Google Chrome Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 67.0.100.99 Modules
| |||||||||||||||
| 4060 | ping -n 10 localhost | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | |||||||||||||||
Total events
1 348
Read events
1 192
Write events
154
Delete events
2
Modification events
| (PID) Process: | (944) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (944) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (944) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (944) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\EnsoulSetup.zip | |||
| (PID) Process: | (944) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (944) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (944) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (944) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (944) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (944) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
4
Suspicious files
4
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2604 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\2HSW9V1HTFITYR69TSYQ.temp | — | |
MD5:— | SHA256:— | |||
| 1800 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\8TJLZYWFC8YDJOCKGVZE.temp | — | |
MD5:— | SHA256:— | |||
| 1800 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2604 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF3a69fa.TMP | binary | |
MD5:— | SHA256:— | |||
| 2604 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3212 | EnsoulSetup.exe | C:\Users\admin\AppData\Roaming\Winlog\winlog.exe | executable | |
MD5:— | SHA256:— | |||
| 1416 | winlog.exe | C:\Users\admin\AppData\Local\Temp\DFdX2jtb50jK.bat | text | |
MD5:— | SHA256:— | |||
| 1608 | winlog.exe | C:\Users\admin\AppData\Roaming\chome_exe\opsrv.exe | executable | |
MD5:— | SHA256:— | |||
| 1800 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF3ad576.TMP | binary | |
MD5:— | SHA256:— | |||
| 944 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa944.12613\EnsoulSetup.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
3
DNS requests
2
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1416 | winlog.exe | GET | 200 | 185.194.141.58:80 | http://ip-api.com/json/ | DE | text | 265 b | malicious |
3212 | EnsoulSetup.exe | GET | 200 | 185.194.141.58:80 | http://ip-api.com/json/ | DE | text | 265 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3212 | EnsoulSetup.exe | 185.194.141.58:80 | ip-api.com | netcup GmbH | DE | unknown |
1416 | winlog.exe | 185.194.141.58:80 | ip-api.com | netcup GmbH | DE | unknown |
1416 | winlog.exe | 84.108.213.8:4782 | prrr.duckdns.org | Bezeq International | IL | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ip-api.com |
| malicious |
prrr.duckdns.org |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3212 | EnsoulSetup.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |
3212 | EnsoulSetup.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
3212 | EnsoulSetup.exe | A Network Trojan was detected | REMOTE [PTsecurity] Quasar.RAT IP Lookup |
1416 | winlog.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |
1416 | winlog.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
1416 | winlog.exe | A Network Trojan was detected | REMOTE [PTsecurity] Quasar.RAT IP Lookup |
1080 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
1416 | winlog.exe | A Network Trojan was detected | MALWARE [PTsecurity] Quasar RAT |
1416 | winlog.exe | A Network Trojan was detected | MALWARE [PTsecurity] Quasar RAT |
2 ETPRO signatures available at the full report