| File name: | scan.exe |
| Full analysis: | https://app.any.run/tasks/95793b75-e8b6-4836-a5af-1851472a3603 |
| Verdict: | Malicious activity |
| Threats: | LokiBot was developed in 2015 to steal information from a variety of applications. Despite the age, this malware is still rather popular among cybercriminals. |
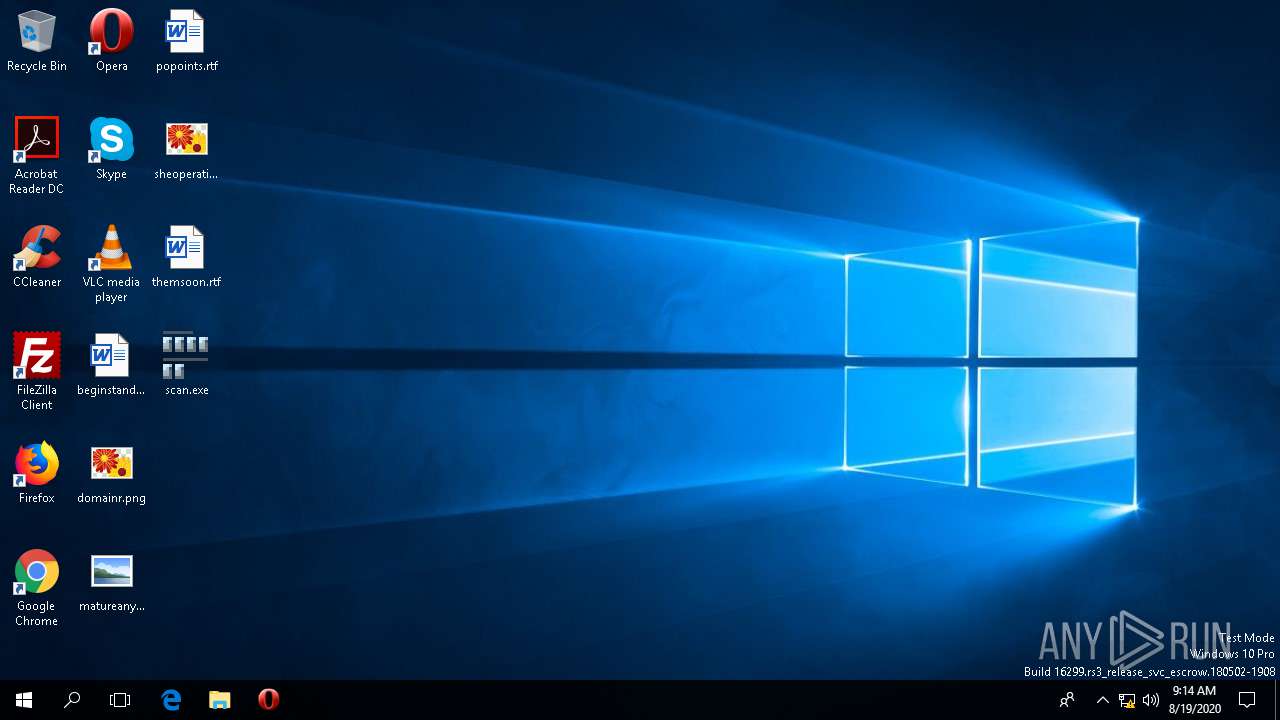
| Analysis date: | August 19, 2020, 09:14:29 |
| OS: | Windows 10 Professional (build: 16299, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 335A7BCF74BE1135ACC44CE81BC377B1 |
| SHA1: | 9E7EA49AD2B48EDFB025F57DA760EEB5F6893328 |
| SHA256: | 19205B465485A095D892160328744D4FEF6804893CA093A6CB4DC2A146353495 |
| SSDEEP: | 12288:oRsEB+1sK7zsg+ZvBI2pgQjpUtX8moeDCsEp6la8hwO3VebJc9n3yGk:ojIB/sg+ZcQdg8bm5lG4kbJclRk |
MALICIOUS
Connects to CnC server
- scan.exe (PID: 4492)
LOKIBOT was detected
- scan.exe (PID: 4492)
Actions looks like stealing of personal data
- scan.exe (PID: 4492)
SUSPICIOUS
Application launched itself
- scan.exe (PID: 312)
Executable content was dropped or overwritten
- scan.exe (PID: 4492)
Creates files in the user directory
- scan.exe (PID: 4492)
Reads the machine GUID from the registry
- scan.exe (PID: 4492)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Borland Delphi 7 (94.6) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (2) |
| .scr | | | Windows screen saver (1.8) |
| .exe | | | Win32 Executable (generic) (0.6) |
| .exe | | | Win16/32 Executable Delphi generic (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 561152 |
| InitializedDataSize: | 196608 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x89dc4 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x00088E0C | 0x00089000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.38702 |
DATA | 0x0008A000 | 0x00001614 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.95485 |
BSS | 0x0008C000 | 0x00000D5D | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0008D000 | 0x00002530 | 0x00002600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.98067 |
.tls | 0x00090000 | 0x00000010 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00091000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.164765 |
.reloc | 0x00092000 | 0x00008C20 | 0x00008E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.65765 |
.rsrc | 0x0009B000 | 0x000230EC | 0x00023200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 7.42226 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 1.37961 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
2 | 2.80231 | 308 | Latin 1 / Western European | UNKNOWN | RT_CURSOR |
3 | 3.00046 | 308 | Latin 1 / Western European | UNKNOWN | RT_CURSOR |
4 | 2.56318 | 308 | Latin 1 / Western European | UNKNOWN | RT_CURSOR |
5 | 2.6949 | 308 | Latin 1 / Western European | UNKNOWN | RT_CURSOR |
6 | 2.62527 | 308 | Latin 1 / Western European | UNKNOWN | RT_CURSOR |
7 | 2.91604 | 308 | Latin 1 / Western European | UNKNOWN | RT_CURSOR |
333 | 6.90408 | 152 | Latin 1 / Western European | English - United States | RT_HTML |
1000 | 7.64884 | 29545 | Latin 1 / Western European | English - United States | RT_BITMAP |
1001 | 7.64723 | 29545 | Latin 1 / Western European | English - United States | RT_BITMAP |
Imports
advapi32.dll |
comctl32.dll |
comdlg32.dll |
gdi32.dll |
kernel32.dll |
ole32.dll |
oleaut32.dll |
user32.dll |
version.dll |
Total processes
90
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 312 | "C:\Users\admin\Desktop\scan.exe" | C:\Users\admin\Desktop\scan.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 4492 | "C:\Users\admin\Desktop\scan.exe" | C:\Users\admin\Desktop\scan.exe | scan.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
180
Read events
176
Write events
4
Delete events
0
Modification events
| (PID) Process: | (4492) scan.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4492) scan.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4492) scan.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (4492) scan.exe | Key: | HKEY_CURRENT_USER\������Н������������������ќ��Ѕ���Ѕ����Й��я�� |
| Operation: | write | Name: | F3F363 |
Value: %APPDATA%\F3F363\3C28B3.exe | |||
Executable files
1
Suspicious files
0
Text files
1
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4492 | scan.exe | C:\Users\admin\AppData\Roaming\F3F363\3C28B3.lck | — | |
MD5:— | SHA256:— | |||
| 4492 | scan.exe | C:\Users\admin\AppData\Roaming\F3F363\3C28B3.hdb | text | |
MD5:— | SHA256:— | |||
| 4492 | scan.exe | C:\Users\admin\AppData\Roaming\F3F363\3C28B3.exe | executable | |
MD5:— | SHA256:— | |||
| 4492 | scan.exe | C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\S-1-5-21-1693682860-607145093-2874071422-1001\0f5007522459c86e95ffcc62f32308f1_bb926e54-e3ca-40fd-ae90-2764341e7792 | dbf | |
MD5:18B8CFC0185C50383AAC0A4F30A9DAC8 | SHA256:913E8CED6A447FE791954D382ABA52D490513C5D2F689B391866C7E561F89A03 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
4
DNS requests
3
Threats
26
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4492 | scan.exe | POST | — | 185.209.1.115:80 | http://babatundesieqwarteg.com/zoro/zoro3/fre.php | LV | — | — | malicious |
4492 | scan.exe | POST | 404 | 185.209.1.115:80 | http://babatundesieqwarteg.com/zoro/zoro3/fre.php | LV | text | 15 b | malicious |
4492 | scan.exe | POST | 404 | 185.209.1.115:80 | http://babatundesieqwarteg.com/zoro/zoro3/fre.php | LV | text | 15 b | malicious |
4492 | scan.exe | POST | 404 | 185.209.1.115:80 | http://babatundesieqwarteg.com/zoro/zoro3/fre.php | LV | binary | 23 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4492 | scan.exe | 185.209.1.115:80 | babatundesieqwarteg.com | — | LV | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ocsp.verisign.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
babatundesieqwarteg.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4492 | scan.exe | A Network Trojan was detected | ET TROJAN LokiBot User-Agent (Charon/Inferno) |
4492 | scan.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M1 |
4492 | scan.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M2 |
4492 | scan.exe | A Network Trojan was detected | ET TROJAN LokiBot Checkin |
4492 | scan.exe | A Network Trojan was detected | MALWARE [PTsecurity] Loki Bot Check-in M2 |
4492 | scan.exe | A Network Trojan was detected | ET TROJAN LokiBot User-Agent (Charon/Inferno) |
4492 | scan.exe | A Network Trojan was detected | ET TROJAN LokiBot Checkin |
4492 | scan.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M1 |
4492 | scan.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M2 |
4492 | scan.exe | A Network Trojan was detected | MALWARE [PTsecurity] Loki Bot Check-in M2 |
4 ETPRO signatures available at the full report